| File name: | sample.doc |
| Full analysis: | https://app.any.run/tasks/1f2acd5d-4ba7-49c9-9d4c-689ec25a7d4f |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2026, 19:03:46 |
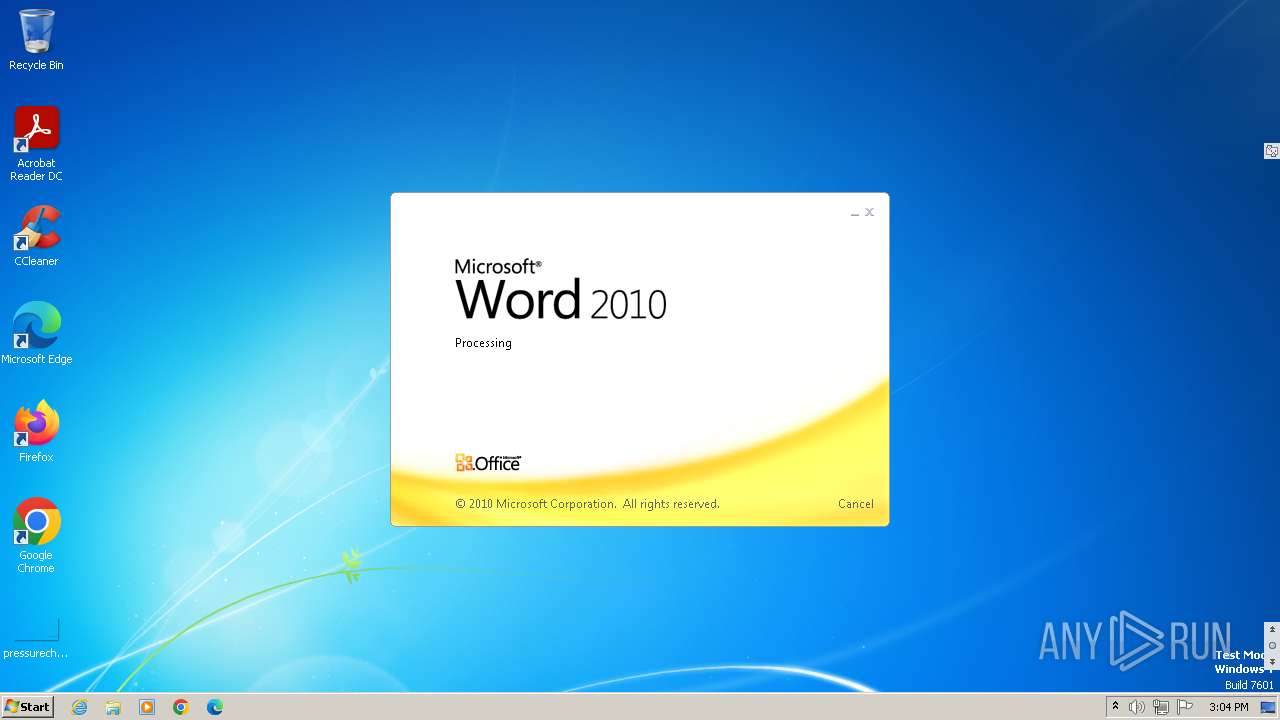
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 52945AF1DEF85B171870B31FA4782E52 |
| SHA1: | 06727FFDA60359236A8029E0B3E8A0FD11C23313 |
| SHA256: | 4A24048F81AFBE9FB62E7A6A49ADBD1FAF41F266B5F9FEECDCEB567AEC096784 |
| SSDEEP: | 192:AEhM7fIUU09264wptGheab8h7Z/c+8poF1d3jvvtl59rGxjPQDasYBcG7h+:AqWfIz092hwLGAabkcfa7pr1lzyxjPQ9 |
MALICIOUS
PHISHING has been detected (SURICATA)
- svchost.exe (PID: 1092)
WebDav connection (SURICATA)
- svchost.exe (PID: 844)
Changes settings of System certificates
- svchost.exe (PID: 1092)
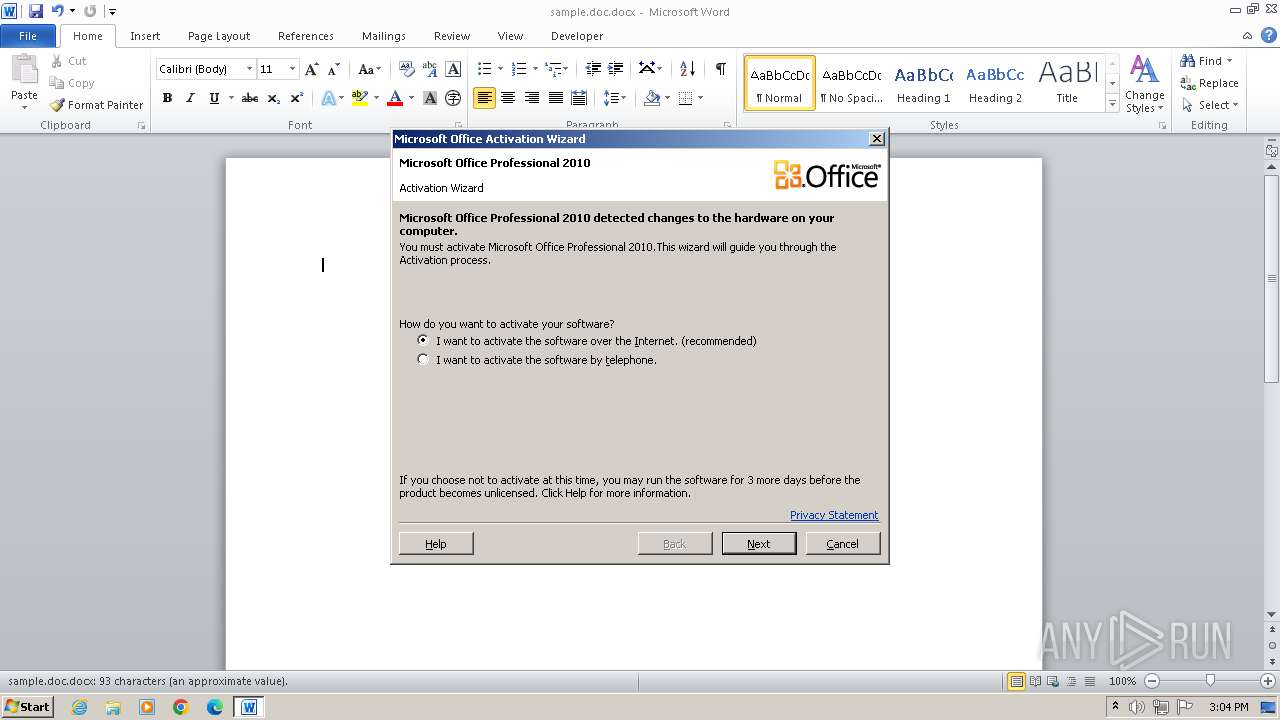
CVE-2022-30190 detected
- WINWORD.EXE (PID: 1868)
SUSPICIOUS
Abuses WebDav for code execution
- svchost.exe (PID: 844)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 844)
Using the short paths format
- WINWORD.EXE (PID: 1868)
INFO
Suspicious URL found
- WINWORD.EXE (PID: 1868)
Reads Internet Explorer settings
- WINWORD.EXE (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docx | | | Word Microsoft Office Open XML Format document (52.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (38.8) |
| .zip | | | ZIP compressed archive (8.8) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2022:05:26 23:08:14 |
| ZipCRC: | 0x6cd2a4df |
| ZipCompressedSize: | 340 |
| ZipUncompressedSize: | 1312 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | - |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | - |
| Paragraphs: | - |
| ScaleCrop: | No |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | - |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | KIS2 |
| RevisionNumber: | 3 |
| CreateDate: | 2022:05:25 13:14:00Z |
| ModifyDate: | 2022:05:25 13:14:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | KIS2 |
| Description: | - |
Total processes
45
Monitored processes
3
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | C:\Windows\system32\svchost.exe -k LocalService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1092 | C:\Windows\system32\svchost.exe -k NetworkService | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n C:\Users\admin\AppData\Local\Temp\sample.doc.docx | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
14 320
Read events
13 869
Write events
204
Delete events
247
Modification events
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | tj9 |
Value: 746A39004C070000010000000000000000000000 | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109F10021400000000000F01FEC\Usage |
| Operation: | write | Name: | StemmerFiles_1042 |
Value: | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 4C0700004E7C961D41C1DC0100000000 | |||
| (PID) Process: | (1868) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LCCache\Themes\1033 |
| Operation: | delete value | Name: | NextUpdate |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDED4.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1092 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\TarE50F.tmp | binary | |
MD5:E4B65A98063D5A8B8BBAF332FFBF7EE8 | SHA256:400800C461437E5E304EC4A597ACC79436E522AFD0ACB7E32CC01FF26D3133DC | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-CNRY.FSD | binary | |
MD5:A84DB12A9C2F46BA375BD8FBEC6E51F6 | SHA256:359D7AB1AD475A040939E2959D07026750B250E056D30DF3D66EDDD63556A066 | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\K01TJA8Z.txt | binary | |
MD5:B61D661127B44E224C441C82C39D806B | SHA256:9AACF0D65C1387DFA6DC353ACFAFDE41C772DE7E51471C2ADDE5E7CD5595462C | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-CNRY.FSD | binary | |
MD5:C4A7A724A2E12B869E588CB6B231413C | SHA256:2683BF488B754591F5A920D1F153530CDE3CB919F482E3F3BCAB01A563B38557 | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSF-CTBL.FSF | binary | |
MD5:D471A0BB5F0B8A9AC834E0172491B7F9 | SHA256:418B6AE0A39787583DCD77DA0ED040F8C3DDA03410E71D04C235EE6E736F298F | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{8F8B7D73-E1D3-4181-AF9D-EB13BF27F831} | binary | |
MD5:C4A7A724A2E12B869E588CB6B231413C | SHA256:2683BF488B754591F5A920D1F153530CDE3CB919F482E3F3BCAB01A563B38557 | |||
| 1092 | svchost.exe | C:\Windows\ServiceProfiles\NetworkService\AppData\Local\Temp\CabE50E.tmp | binary | |
MD5:5F036F91E86E30F749961506951D51EB | SHA256:0300E9DDB527990E8B59D06E9CCF3EC2BD92D3BBD0EF4FBA69D6336E4195E82D | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77D842187CC213F947719E62683B4052 | binary | |
MD5:2699DFFE5EAE0E5587265D0500C07F98 | SHA256:134A9B2EB51780E8BAEFAD79E3BB20BF18E4DAB3C3D24B21CA8A0DA2870DD4E1 | |||
| 1868 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{2D9BA3AD-1276-44C5-86F8-904E85920D33} | binary | |
MD5:A84DB12A9C2F46BA375BD8FBEC6E51F6 | SHA256:359D7AB1AD475A040939E2959D07026750B250E056D30DF3D66EDDD63556A066 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
17
DNS requests
6
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1868 | WINWORD.EXE | HEAD | 302 | 212.92.105.216:443 | https://www.xmlformats.com/office/word/2022/wordprocessingDrawing/RDF842l.html | NL | — | — | unknown |
1868 | WINWORD.EXE | HEAD | 302 | 212.92.105.216:443 | https://www.xmlformats.com/office/word/2022/wordprocessingDrawing/RDF842l.html | NL | — | — | unknown |
1868 | WINWORD.EXE | GET | 200 | 91.81.129.182:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?34cb6b4d89e67673 | IT | binary | 4.87 Kb | unknown |
1868 | WINWORD.EXE | GET | 200 | 23.222.81.129:80 | http://x1.c.lencr.org/ | US | binary | 734 b | whitelisted |
1868 | WINWORD.EXE | GET | 200 | 104.18.21.213:80 | http://r12.c.lencr.org/44.crl | US | binary | 212 Kb | whitelisted |
1868 | WINWORD.EXE | OPTIONS | 302 | 212.92.105.216:443 | https://www.xmlformats.com/office/word/2022/wordprocessingDrawing/ | NL | — | 11 b | unknown |
844 | svchost.exe | OPTIONS | 302 | 212.92.105.216:443 | https://www.xmlformats.com/office/word/2022 | NL | — | 11 b | unknown |
1868 | WINWORD.EXE | GET | 200 | 212.92.105.216:443 | https://www.xmlformats.com/office/word/2022/wordprocessingDrawing/RDF842l.html | NL | — | 531 b | unknown |
1868 | WINWORD.EXE | HEAD | — | 208.91.196.145:80 | http://survey-smiles.com/ | VG | — | — | unknown |
1868 | WINWORD.EXE | GET | 200 | 212.92.105.216:443 | https://www.xmlformats.com/office/word/2022/wordprocessingDrawing/RDF842l.html | NL | binary | 531 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
1092 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
1868 | WINWORD.EXE | 212.92.105.216:443 | www.xmlformats.com | NFORCE | NL | malicious |
1868 | WINWORD.EXE | 91.81.129.182:80 | ctldl.windowsupdate.com | VODAFONE-IT-ASN | IT | whitelisted |
1868 | WINWORD.EXE | 23.222.81.129:80 | x1.c.lencr.org | AKAMAI-AS | US | whitelisted |
1868 | WINWORD.EXE | 104.18.21.213:80 | r12.c.lencr.org | CLOUDFLARENET | US | whitelisted |
844 | svchost.exe | 212.92.105.216:443 | www.xmlformats.com | NFORCE | NL | malicious |
1868 | WINWORD.EXE | 208.91.196.145:80 | survey-smiles.com | CONFLUENCE-NETWORK-INC | VG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.xmlformats.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r12.c.lencr.org |
| whitelisted |
survey-smiles.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1868 | WINWORD.EXE | Misc activity | ET USER_AGENTS Microsoft Office Existence Discovery User-Agent |
844 | svchost.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] WebDAV connection not with MS service M2 |
1 ETPRO signatures available at the full report