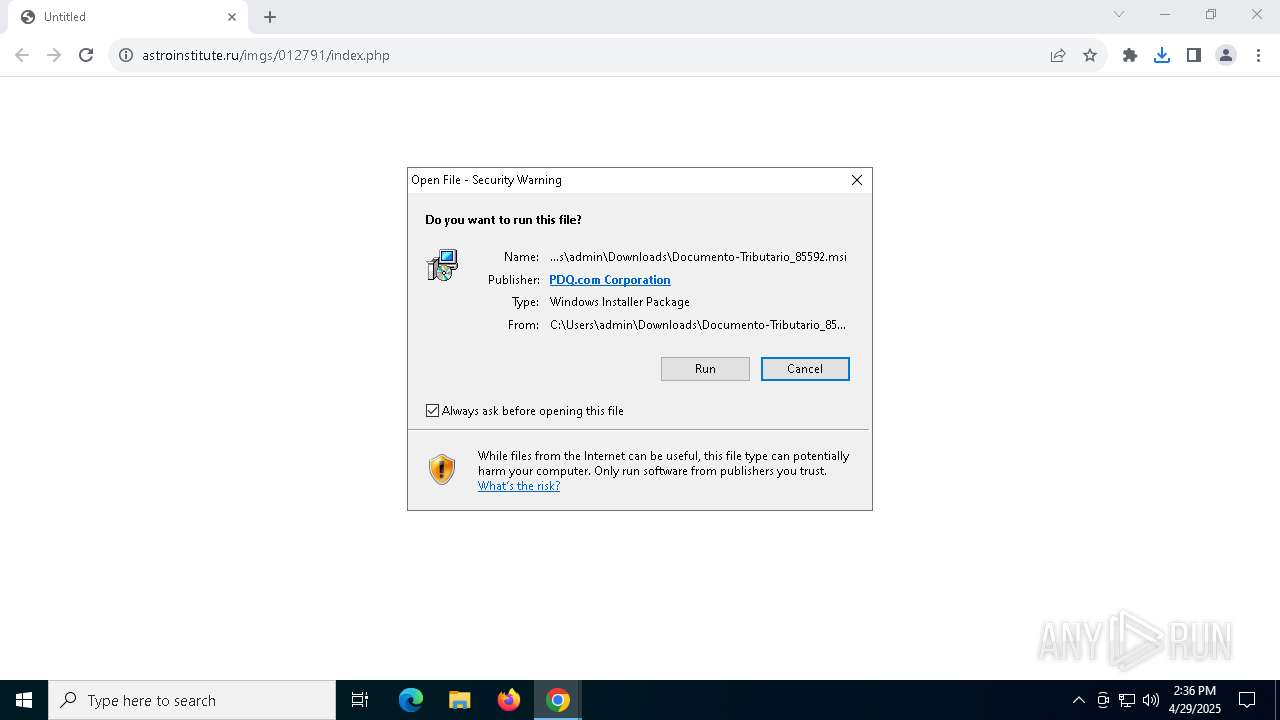
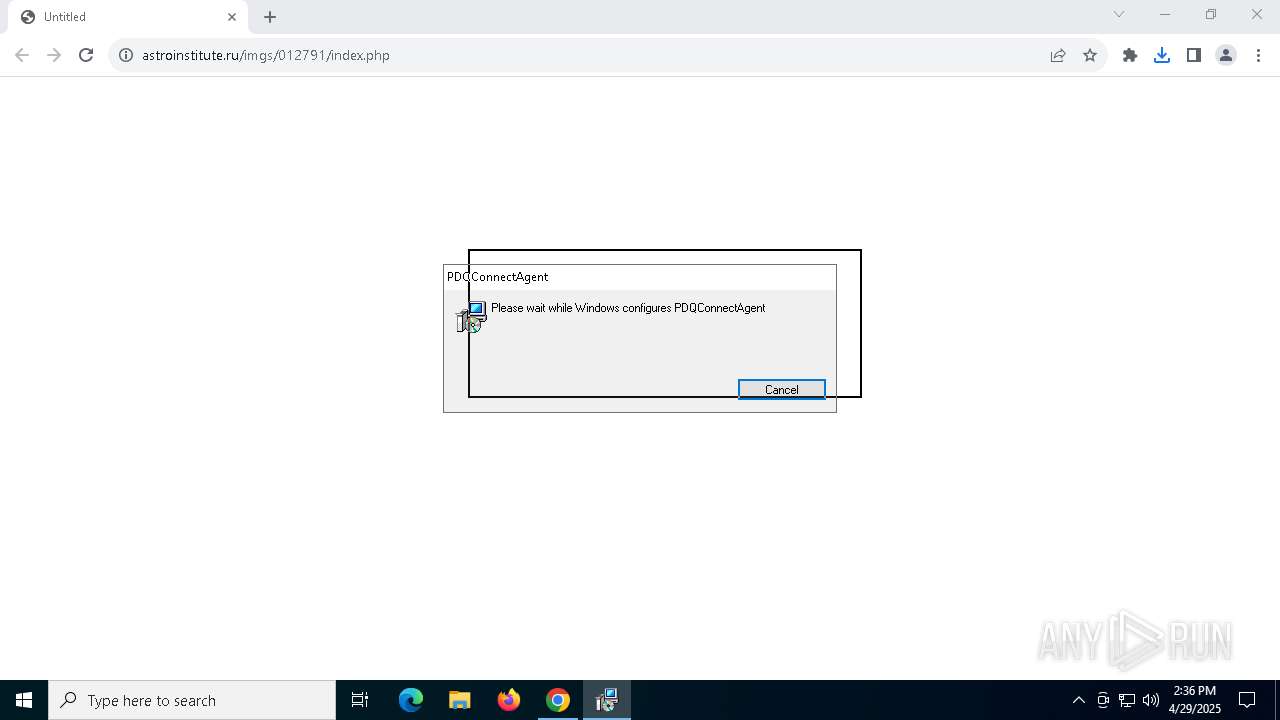
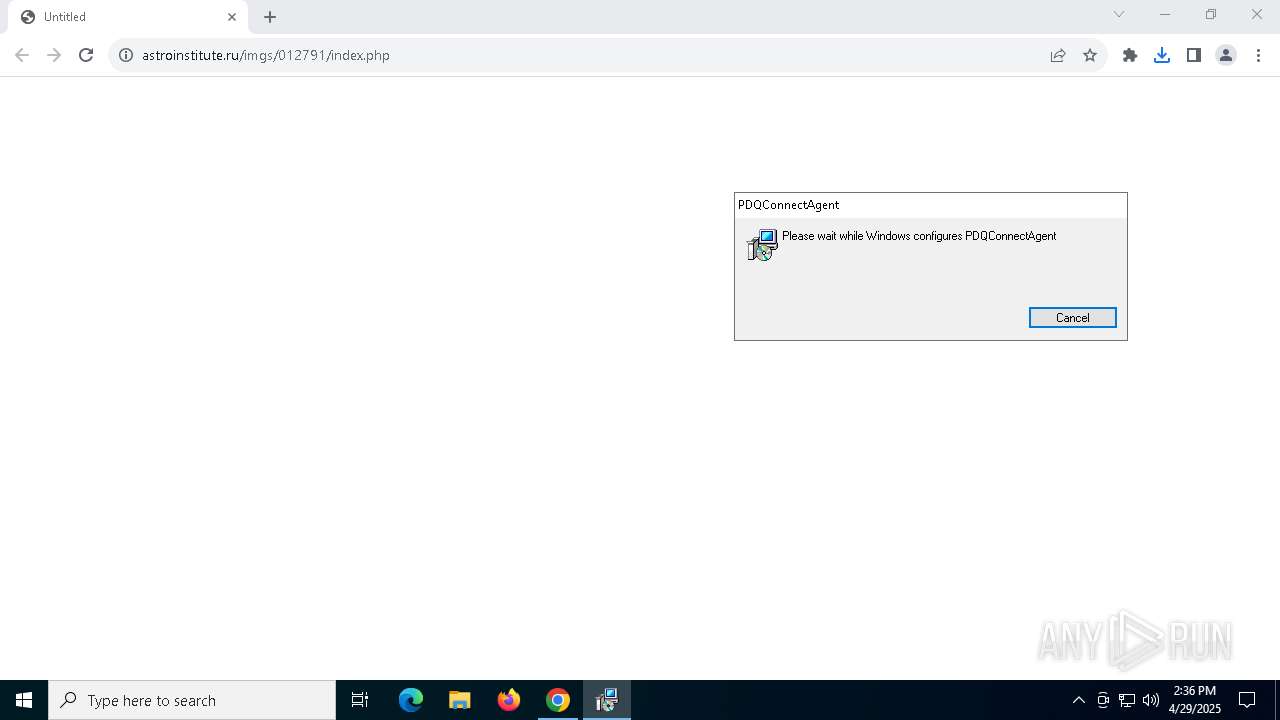
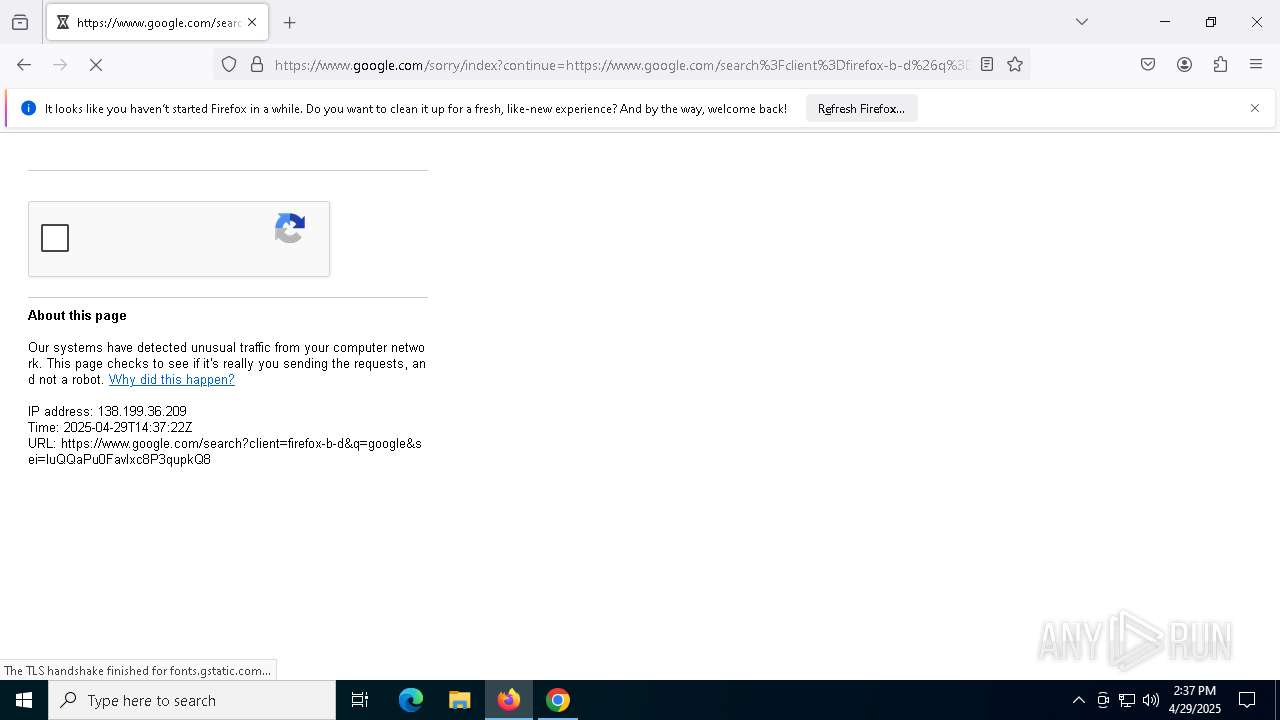
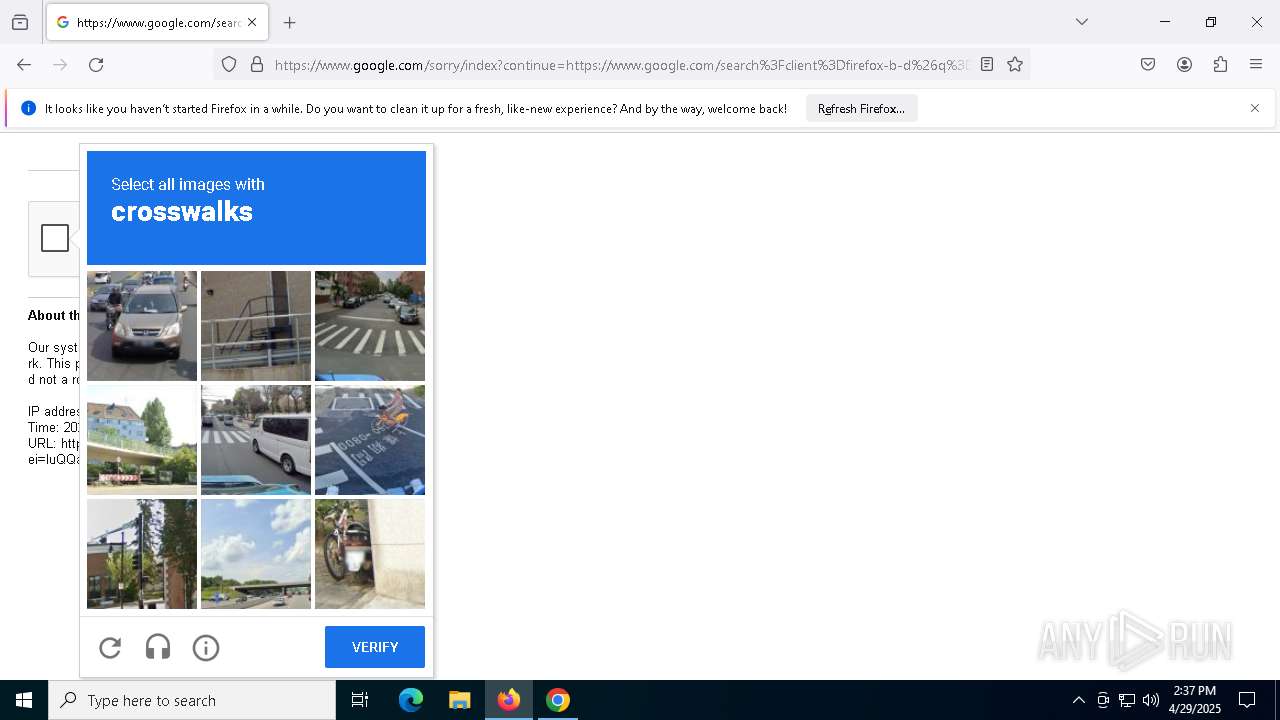
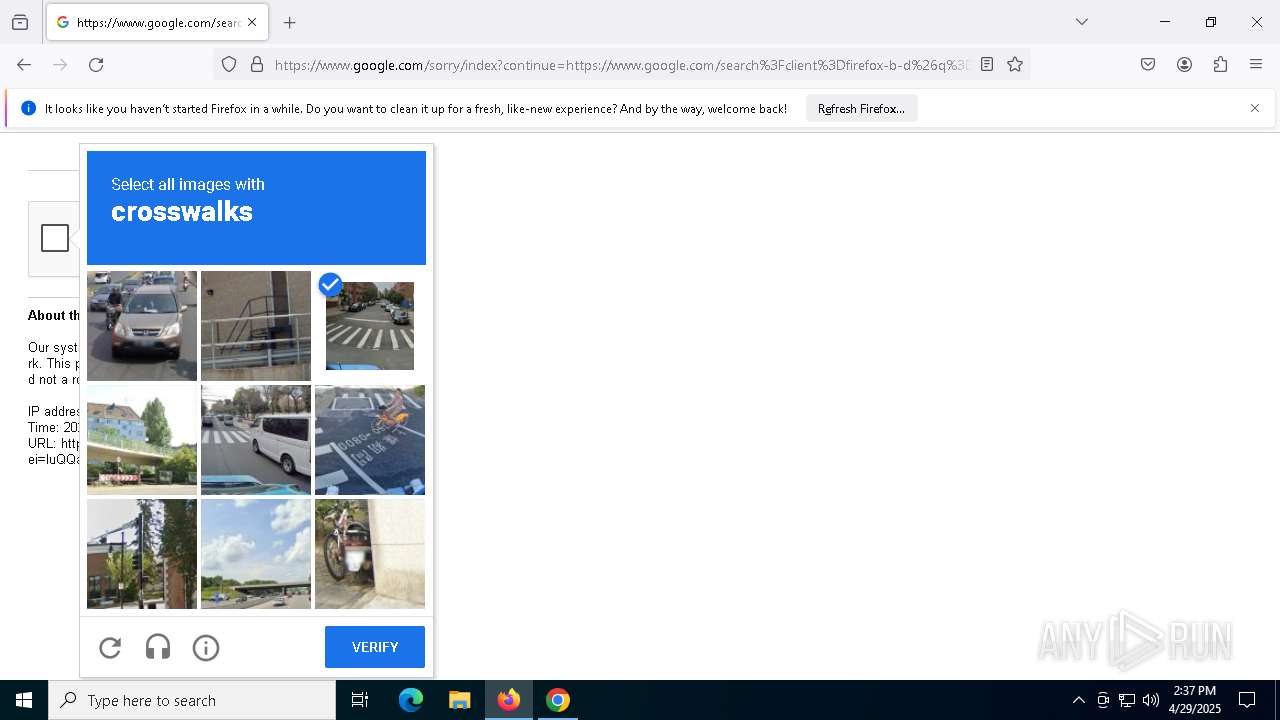
| URL: | https://astroinstitute.ru/imgs/012791/index.php |
| Full analysis: | https://app.any.run/tasks/85925f79-e0a0-4046-aa80-e9e38704b424 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 14:36:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 41E5F8130EC1A927F13B6F08AB271998 |
| SHA1: | 5F3609375888995205F44C43CCDE597A9B5212A1 |
| SHA256: | 4A1C0DC74B05FC68786AB70D1AEC86ACB0B3935B61F4560279B72BCBC064A13B |
| SSDEEP: | 3:N8jHyroJVOU8KPHn:2T+uQUrHn |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 7740)
- powershell.exe (PID: 4180)
- powershell.exe (PID: 7664)
- powershell.exe (PID: 5084)
- powershell.exe (PID: 2064)
- powershell.exe (PID: 6676)
- powershell.exe (PID: 9072)
Changes powershell execution policy (Bypass)
- pdq-connect-agent.exe (PID: 7588)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 8076)
- pdq-connect-agent.exe (PID: 7588)
- pdq-connect-updater.exe (PID: 3008)
Application launched itself
- msiexec.exe (PID: 7988)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 4068)
- msiexec.exe (PID: 3676)
- msiexec.exe (PID: 7388)
Executable content was dropped or overwritten
- rundll32.exe (PID: 1012)
- rundll32.exe (PID: 7928)
- rundll32.exe (PID: 8140)
- rundll32.exe (PID: 5084)
- rundll32.exe (PID: 3332)
- pdq-connect-agent.exe (PID: 7588)
- rundll32.exe (PID: 2772)
- rundll32.exe (PID: 7872)
Windows service management via SC.EXE
- sc.exe (PID: 7468)
Starts SC.EXE for service management
- rundll32.exe (PID: 3332)
PDQConnect is probably used for system patching and software deployment
- sc.exe (PID: 7468)
The process bypasses the loading of PowerShell profile settings
- pdq-connect-agent.exe (PID: 7588)
The process hide an interactive prompt from the user
- pdq-connect-agent.exe (PID: 7588)
Starts POWERSHELL.EXE for commands execution
- pdq-connect-agent.exe (PID: 7588)
The process hides Powershell's copyright startup banner
- pdq-connect-agent.exe (PID: 7588)
INFO
Reads the software policy settings
- msiexec.exe (PID: 7932)
Reads the computer name
- msiexec.exe (PID: 7988)
Reads Microsoft Office registry keys
- chrome.exe (PID: 5972)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7988)
- chrome.exe (PID: 9024)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7932)
Checks supported languages
- msiexec.exe (PID: 7988)
Manages system restore points
- SrTasks.exe (PID: 7436)
Application launched itself
- chrome.exe (PID: 5972)
- firefox.exe (PID: 7736)
- firefox.exe (PID: 4980)
PDQCONNECT has been detected
- msiexec.exe (PID: 3676)
- rundll32.exe (PID: 3332)
- pdq-connect-agent.exe (PID: 7588)
The sample compiled with english language support
- msiexec.exe (PID: 7988)
- chrome.exe (PID: 9024)
Manual execution by a user
- firefox.exe (PID: 7736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
193
Monitored processes
59
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4696 -parentBuildID 20240213221259 -sandboxingKind 0 -prefsHandle 4892 -prefMapHandle 4888 -prefsLen 36588 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e2be2347-4ad7-4645-9fdc-41723c46beb1} 4980 "\\.\pipe\gecko-crash-server-pipe.4980" 1c85ab50710 utility | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 123.0 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3068 --field-trial-handle=1884,i,12419309593503747993,18196946633185152842,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1012 | rundll32.exe "C:\WINDOWS\Installer\MSI3E3E.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1130140 2 WixSharp!WixSharp.ManagedProjectActions.WixSharp_InitRuntime_Action | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3460 --field-trial-handle=1884,i,12419309593503747993,18196946633185152842,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1388 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2076 --field-trial-handle=1884,i,12419309593503747993,18196946633185152842,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2064 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2972 --field-trial-handle=1884,i,12419309593503747993,18196946633185152842,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2284 | "msiexec" /i C:\ProgramData\PDQ\PDQConnectAgent\Updates\PDQConnectUpdater-5.6.16.msi /quiet /qn /norestart /L*V C:\ProgramData\PDQ\PDQConnectAgent\Updates\updater_install.log | C:\Windows\System32\msiexec.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
63 003
Read events
62 618
Write events
359
Delete events
26
Modification events
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000E356921114B9DB01 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.msi\OpenWithProgids |
| Operation: | write | Name: | Msi.Package |
Value: | |||
| (PID) Process: | (7988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000033BD8B1614B9DB01341F00007C1F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000033BD8B1614B9DB01341F00007C1F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7988) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000E027051714B9DB01341F00007C1F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
41
Suspicious files
269
Text files
76
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c16d.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c16d.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c17d.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c17d.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c19c.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
111
DNS requests
125
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5972 | chrome.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.73:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5972 | chrome.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEA5NZ%2FZDFskqO3oXzEaXao8%3D | unknown | — | — | whitelisted |
5972 | chrome.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhtVltVOu8OqBzmsd%2B%2FeFfks3xTQQUvGsiZZ2MaObmHgXx2HIl1LjgSMACEAvcoEuhCK%2FAlHGPdKmo6gs%3D | unknown | — | — | whitelisted |
7588 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7588 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3272 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
3272 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.73:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5972 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1616 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
1616 | chrome.exe | 5.188.118.95:443 | astroinstitute.ru | OOO Network of data-centers Selectel | RU | unknown |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1616 | chrome.exe | 142.250.186.78:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
astroinstitute.ru |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare R2 Storage (r2 .cloudflarestorage .com) |