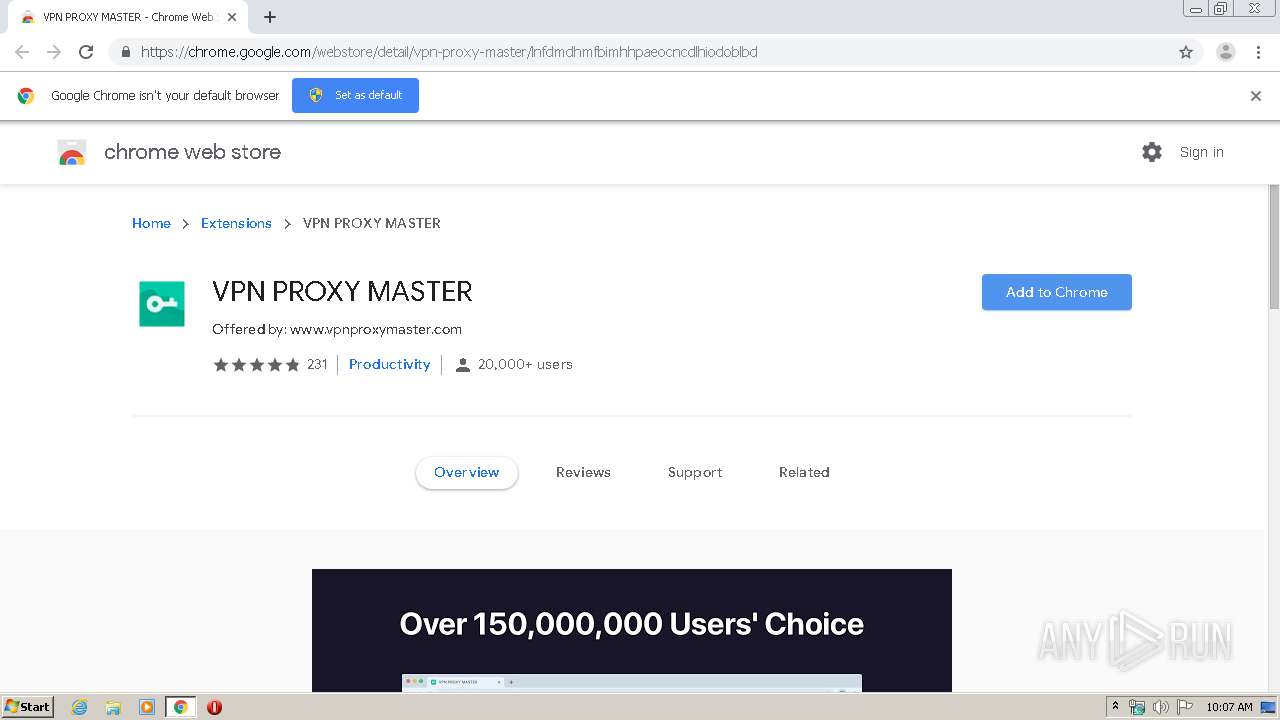
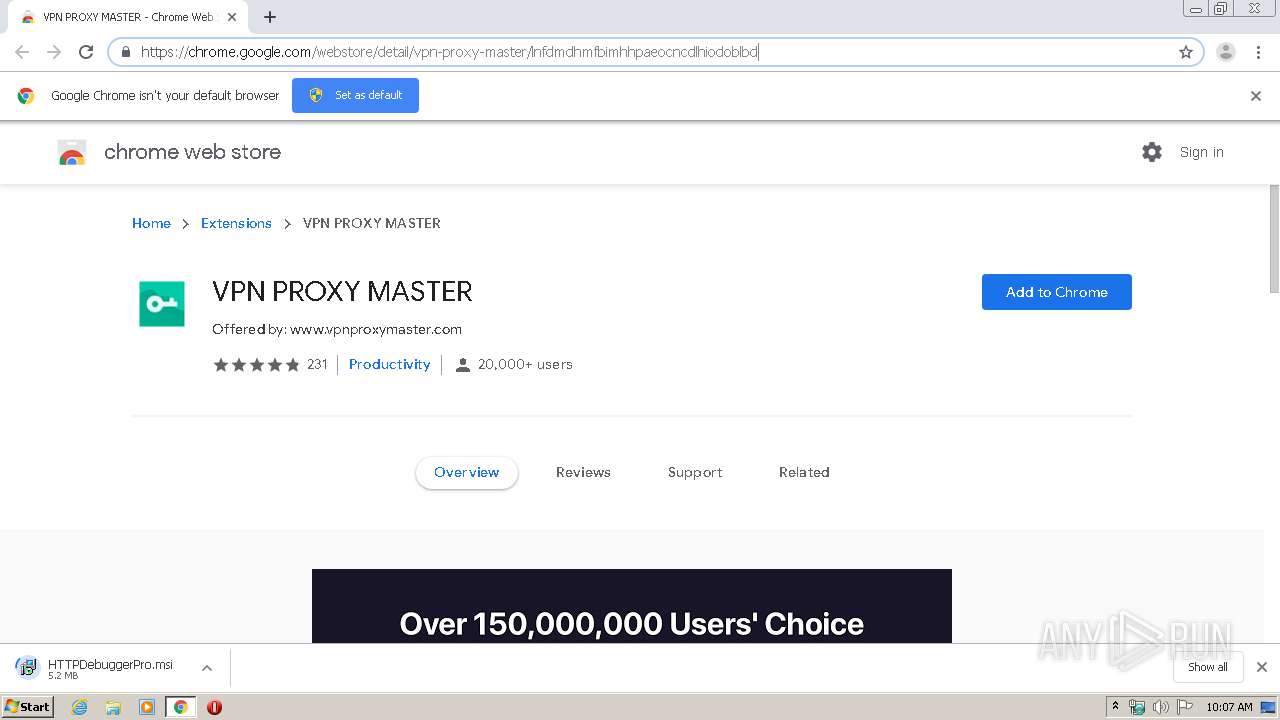
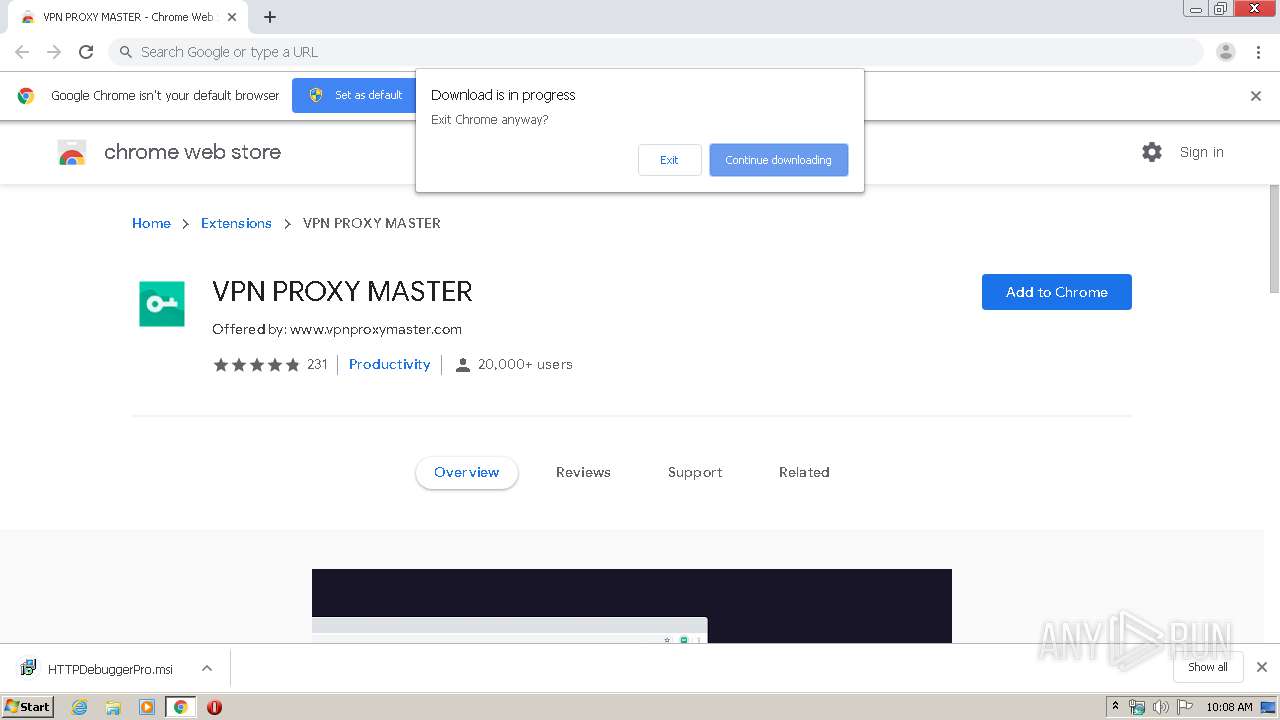
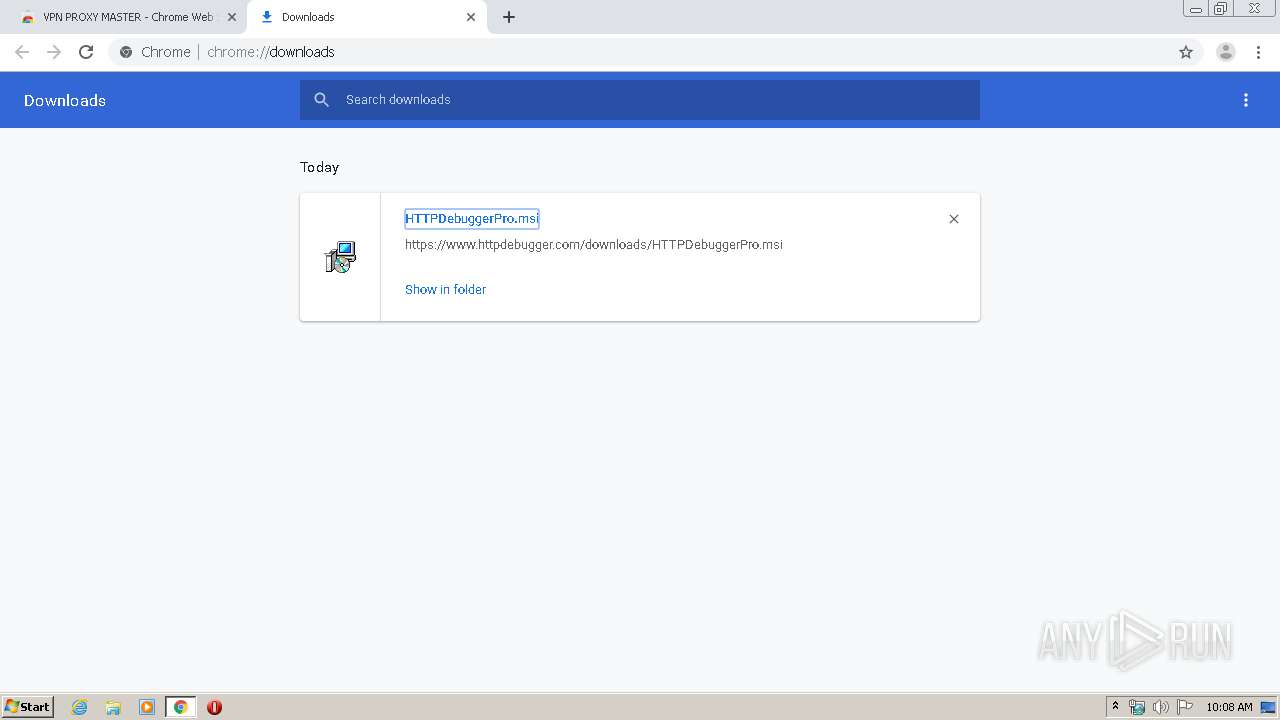
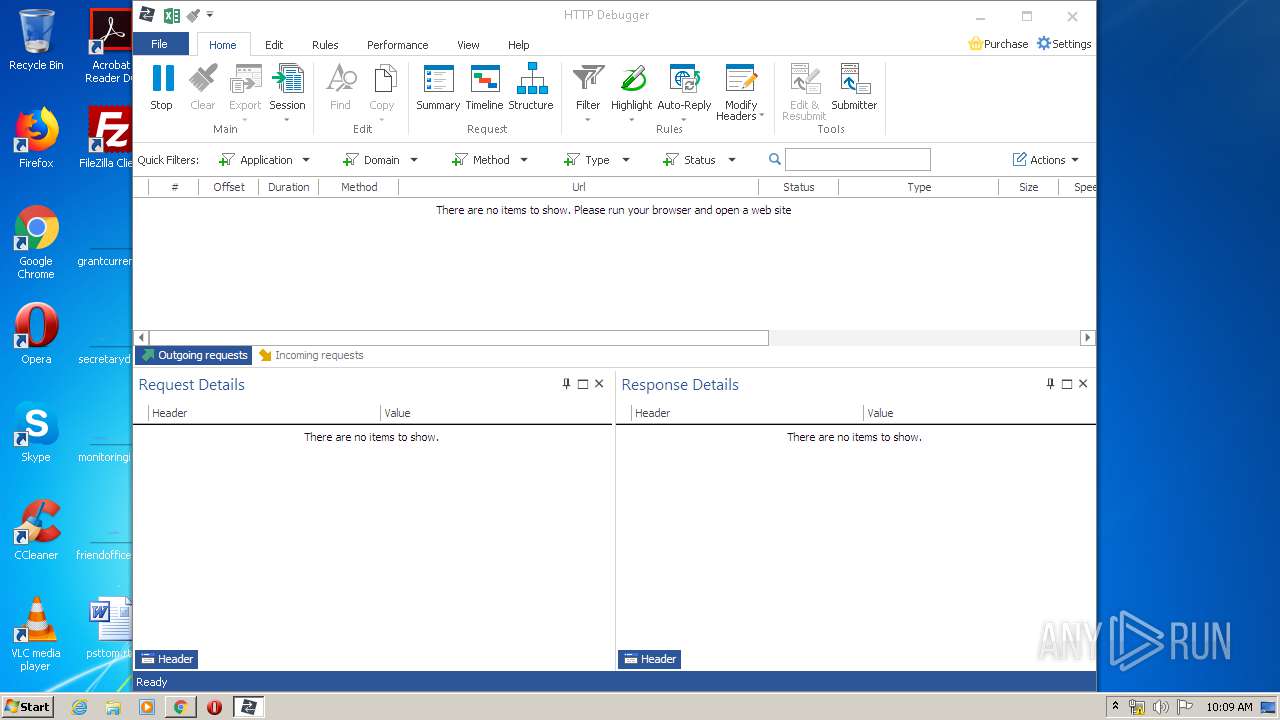
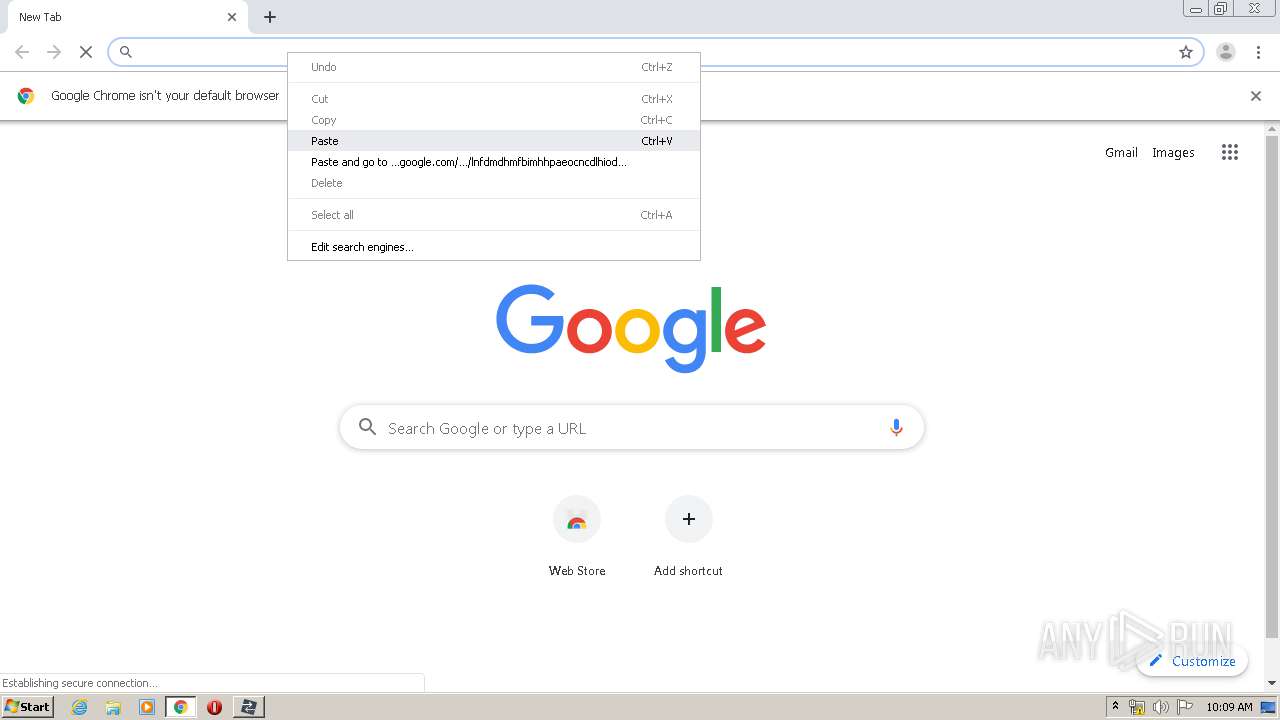
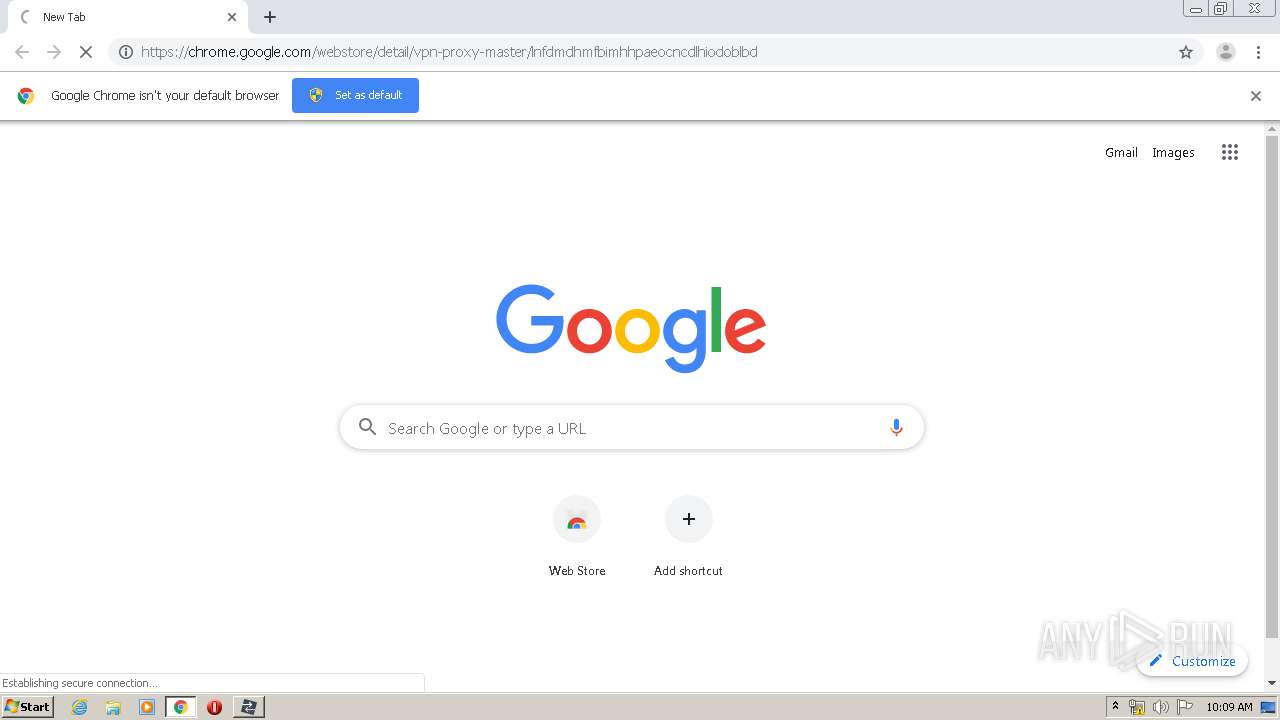
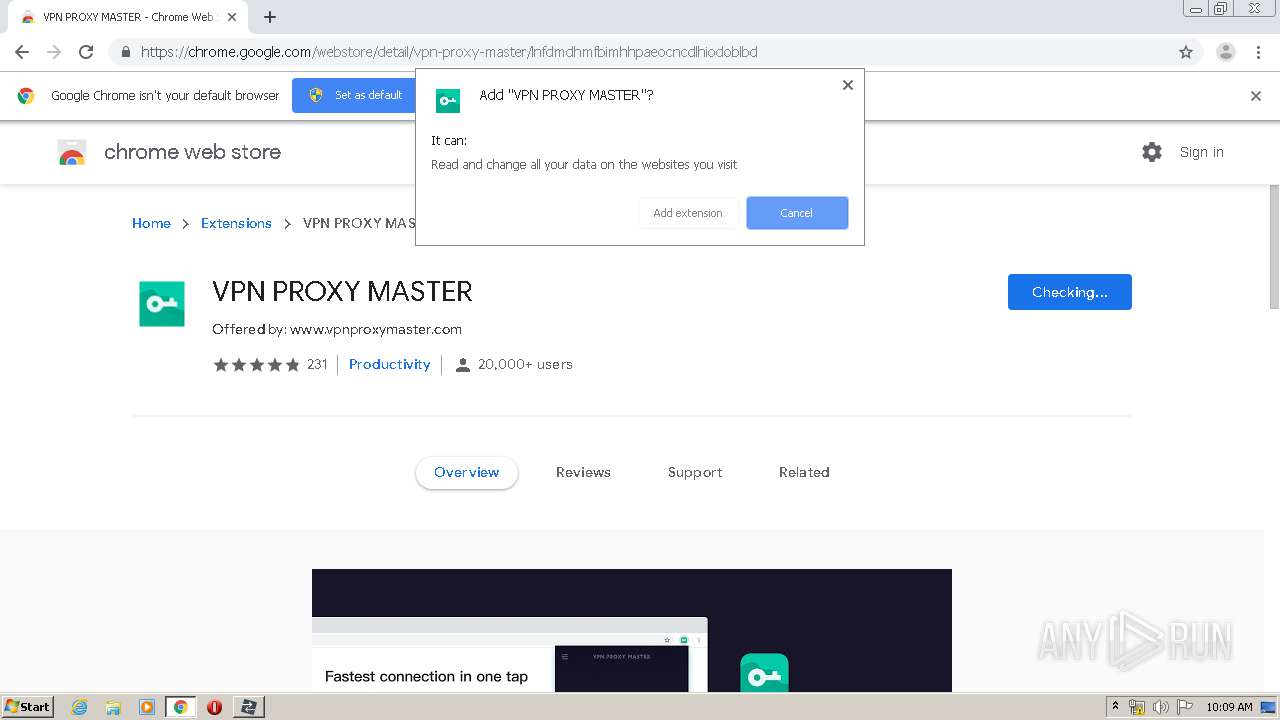
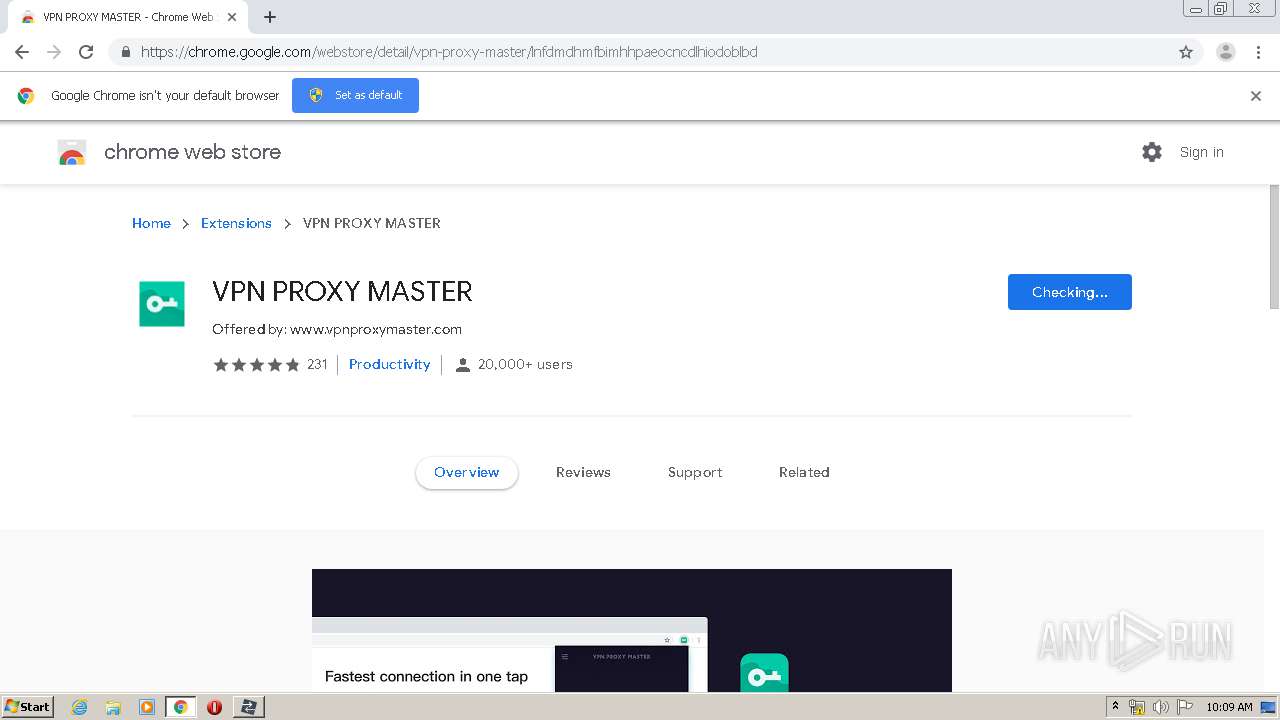
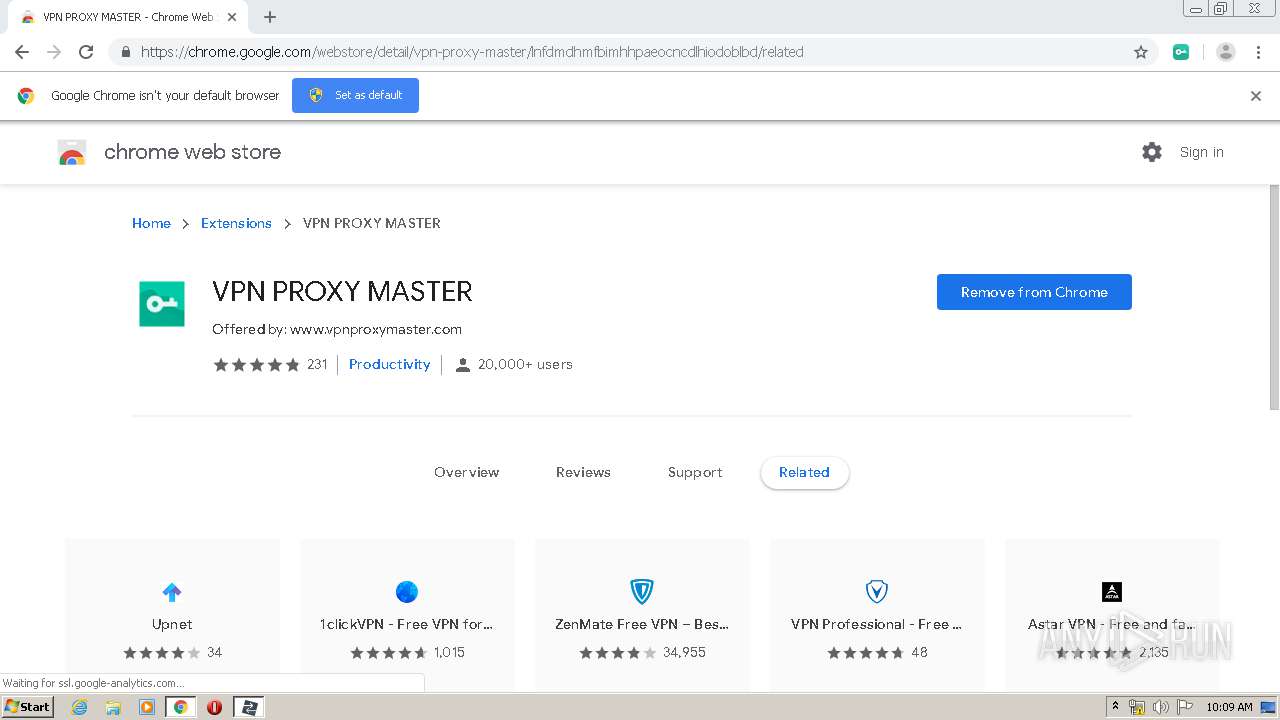
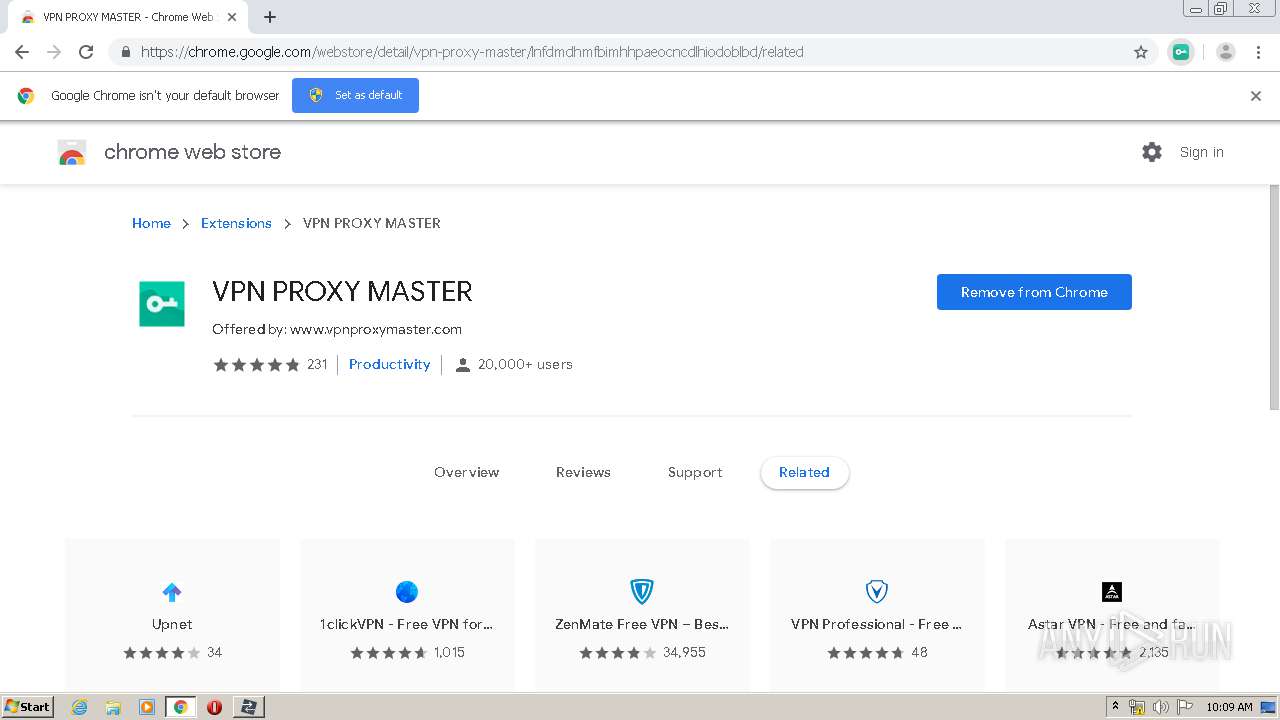
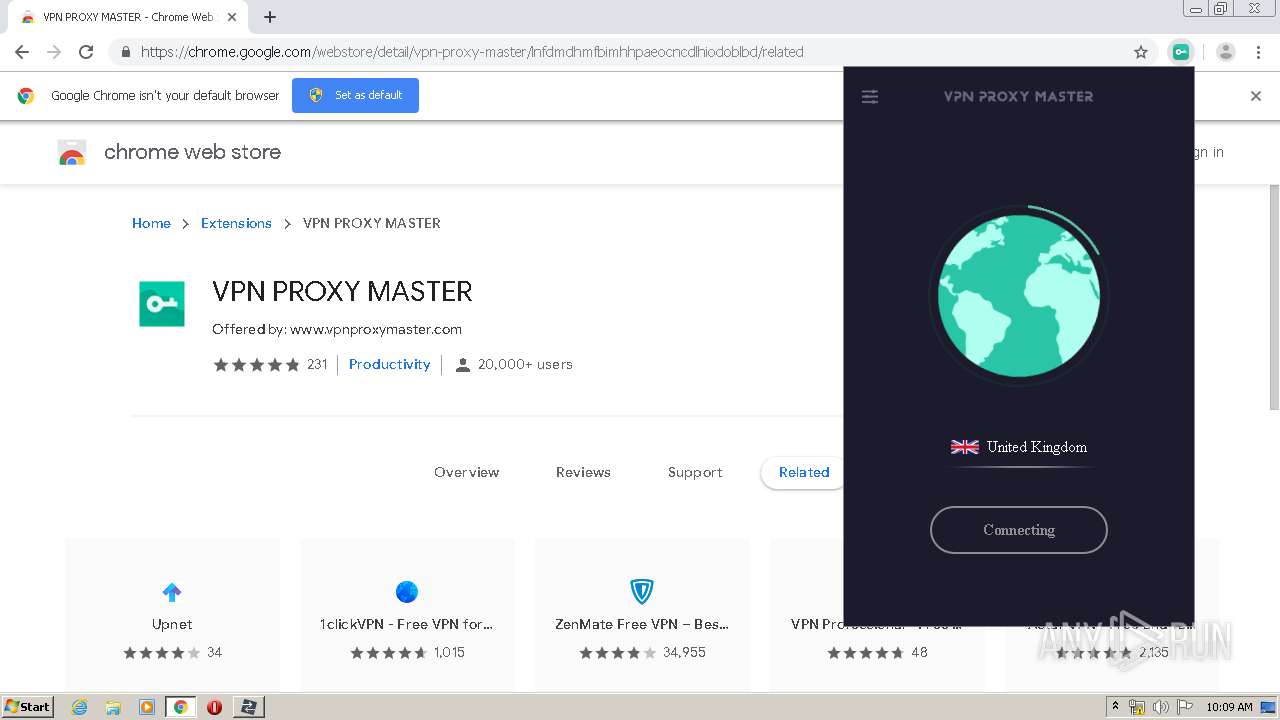
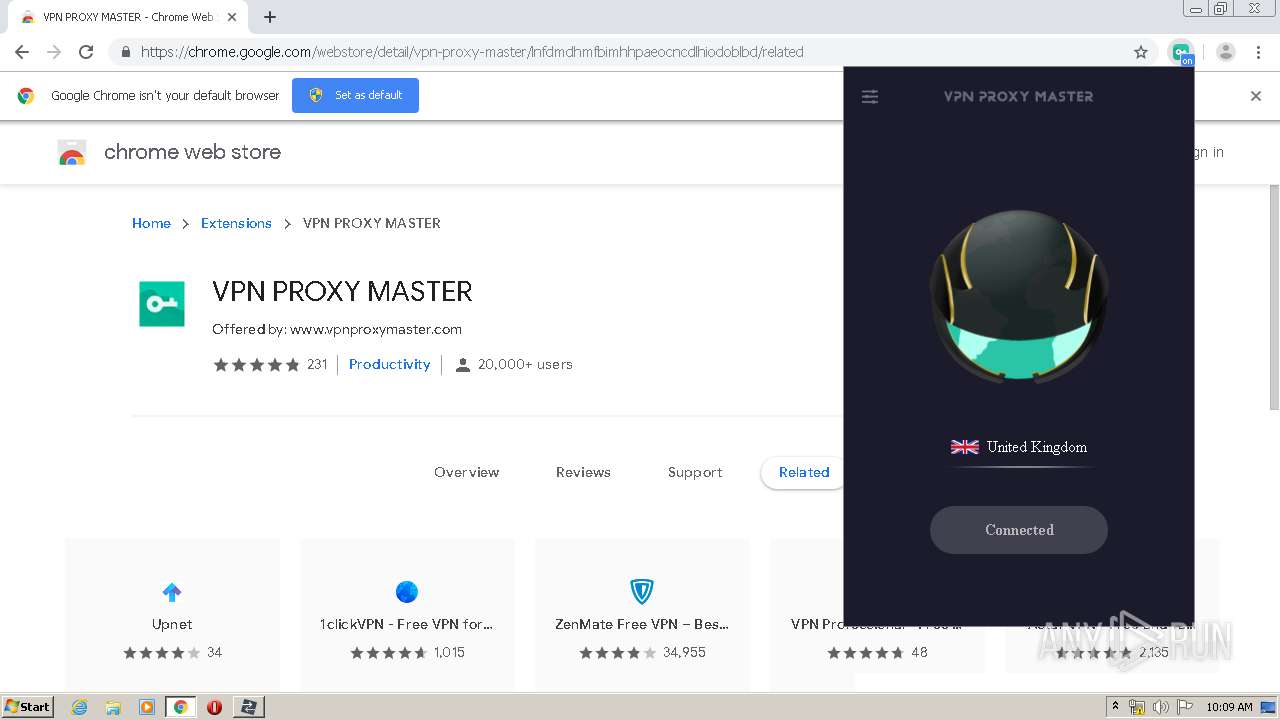
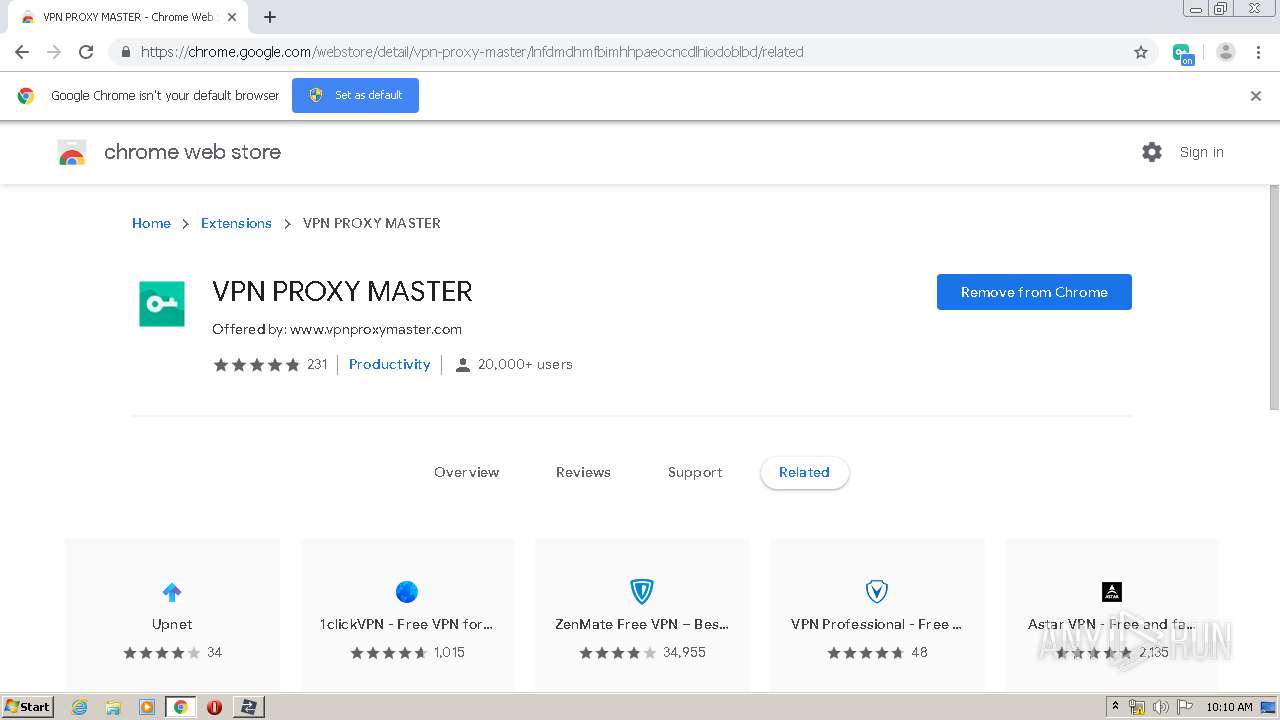
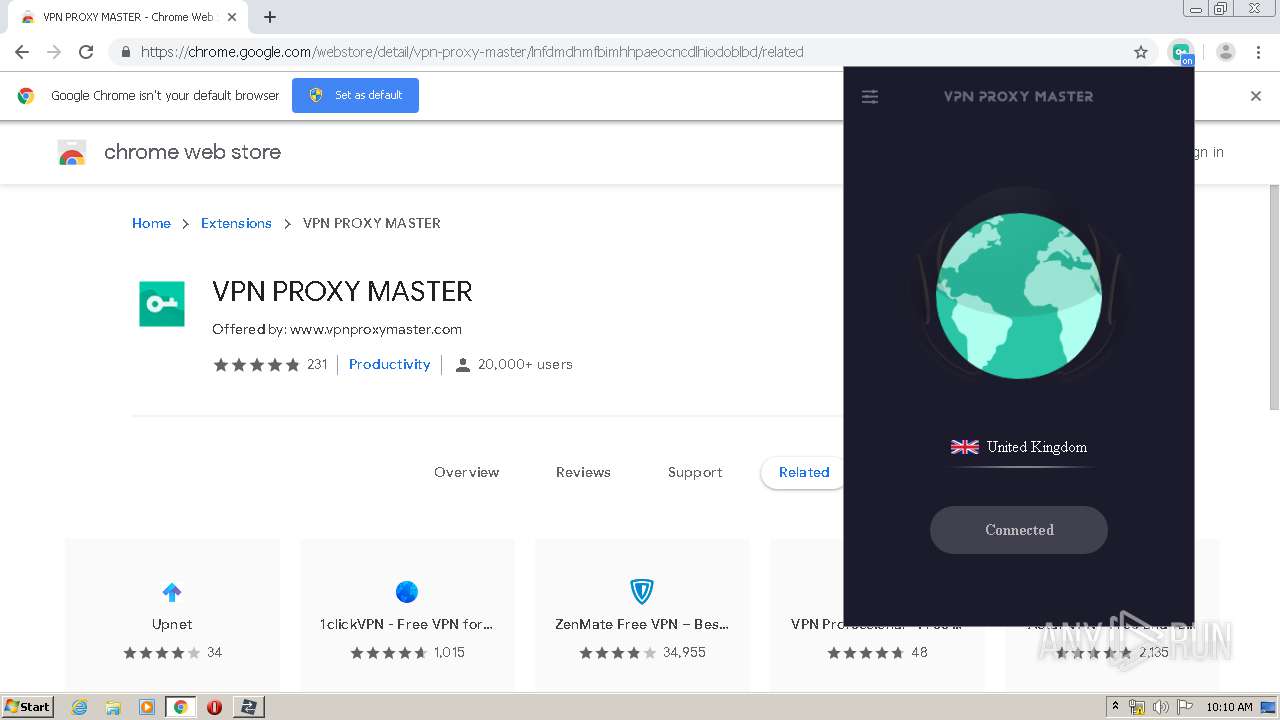
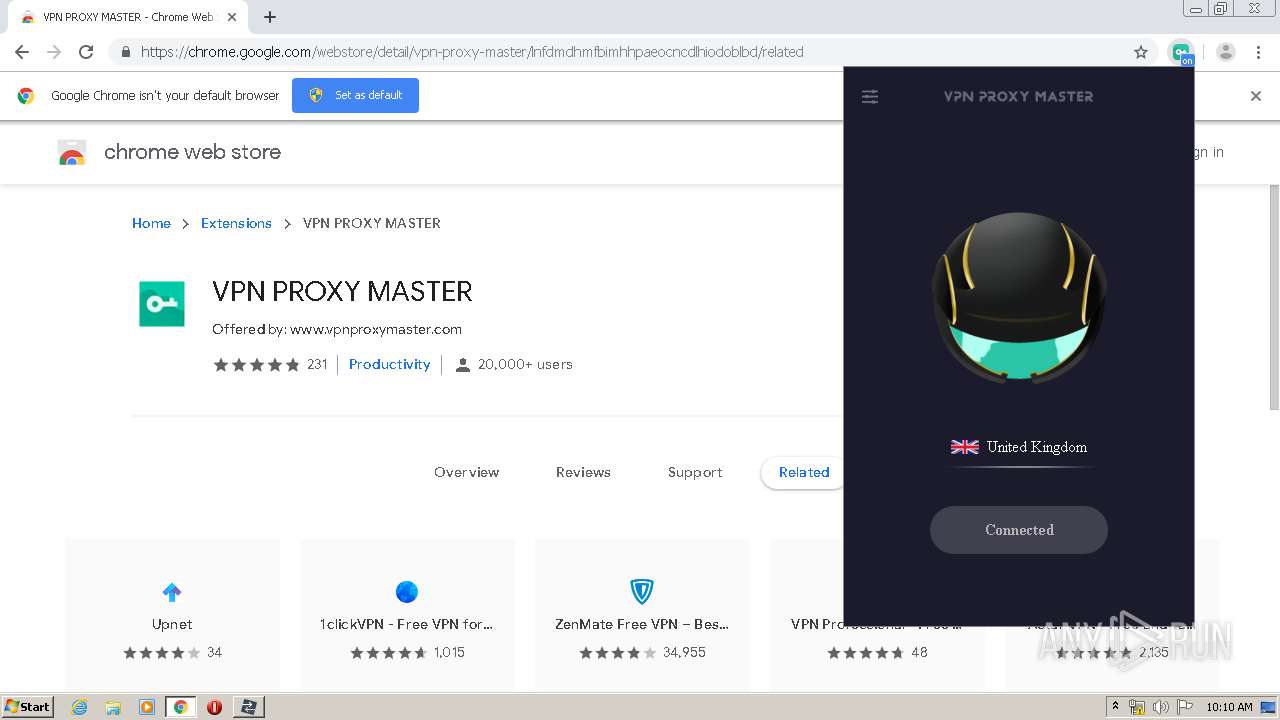
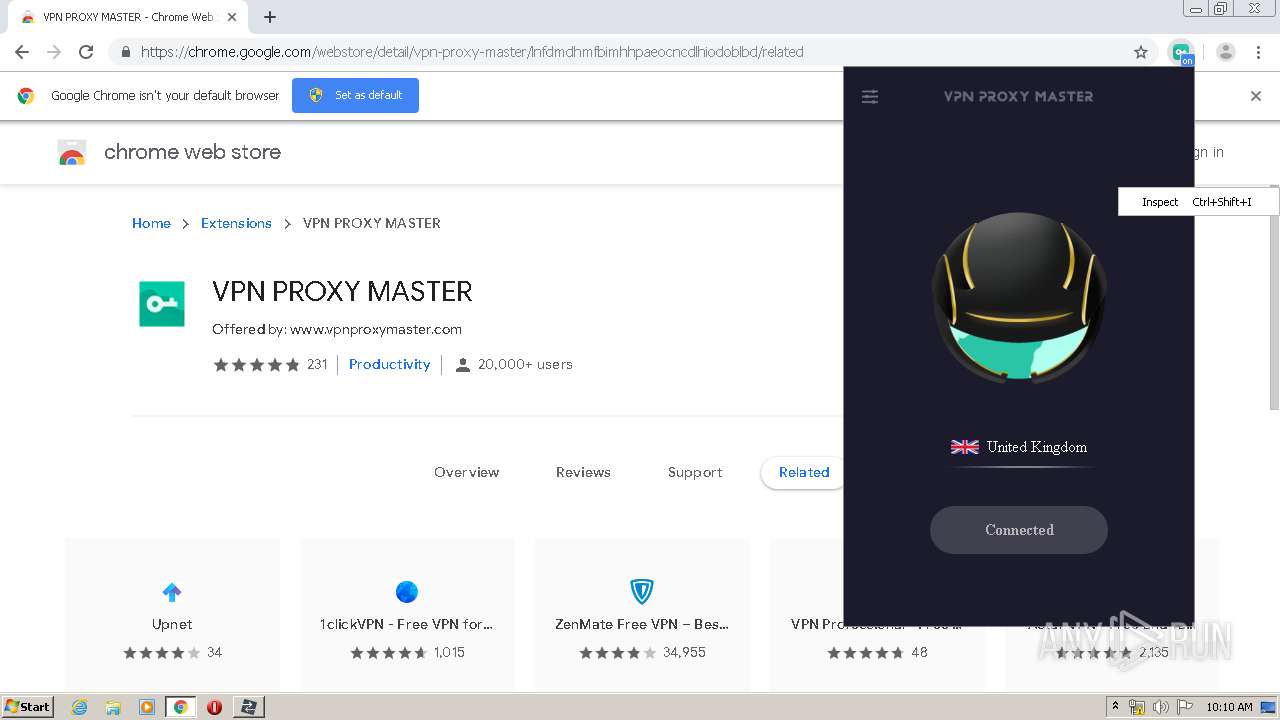
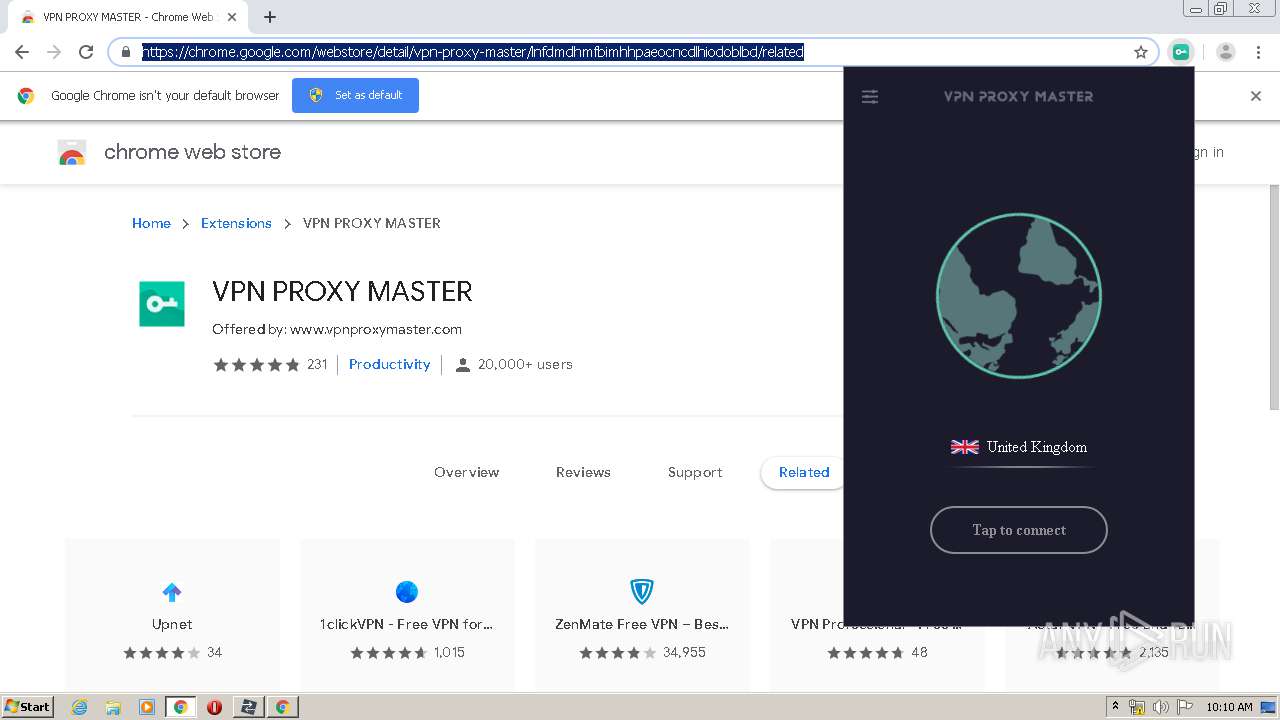
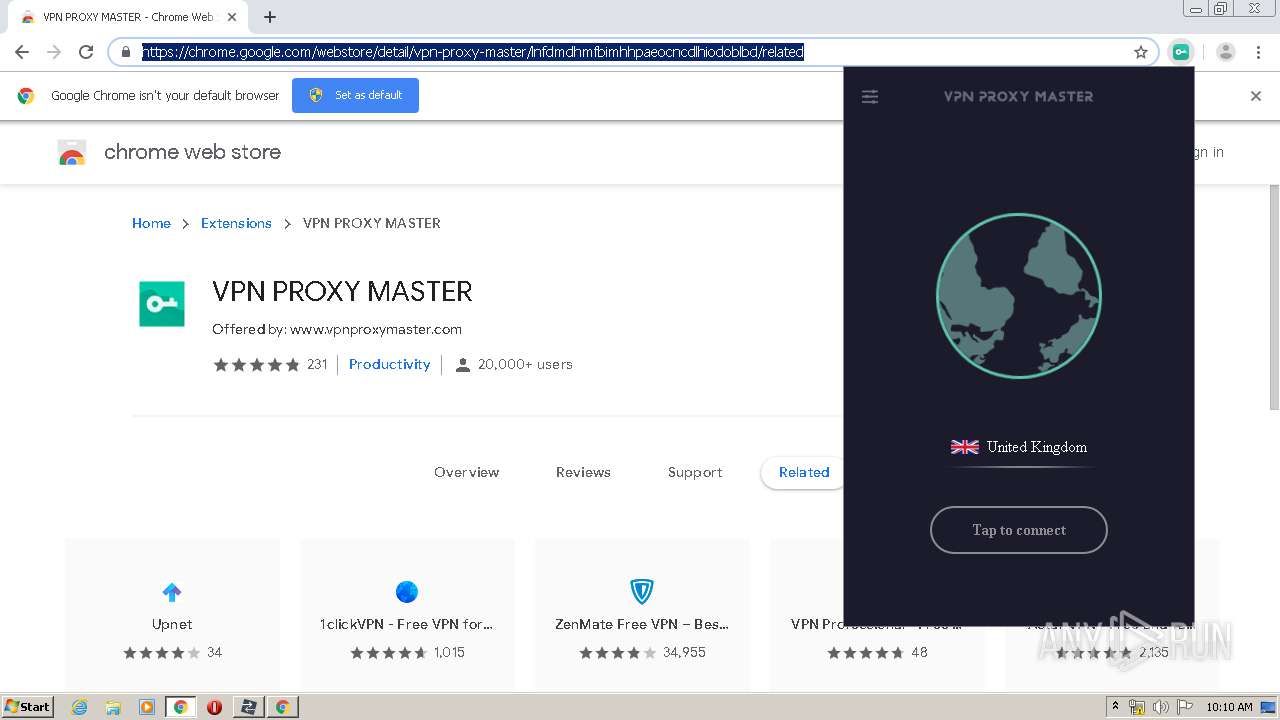
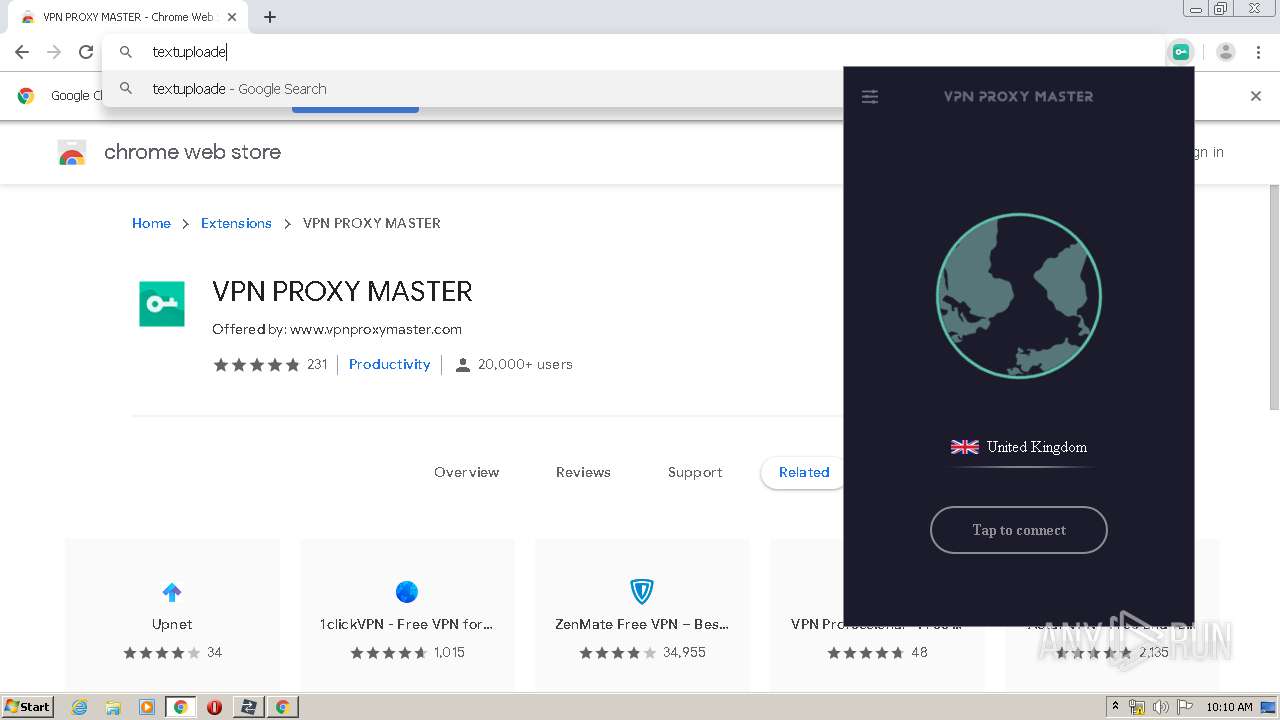
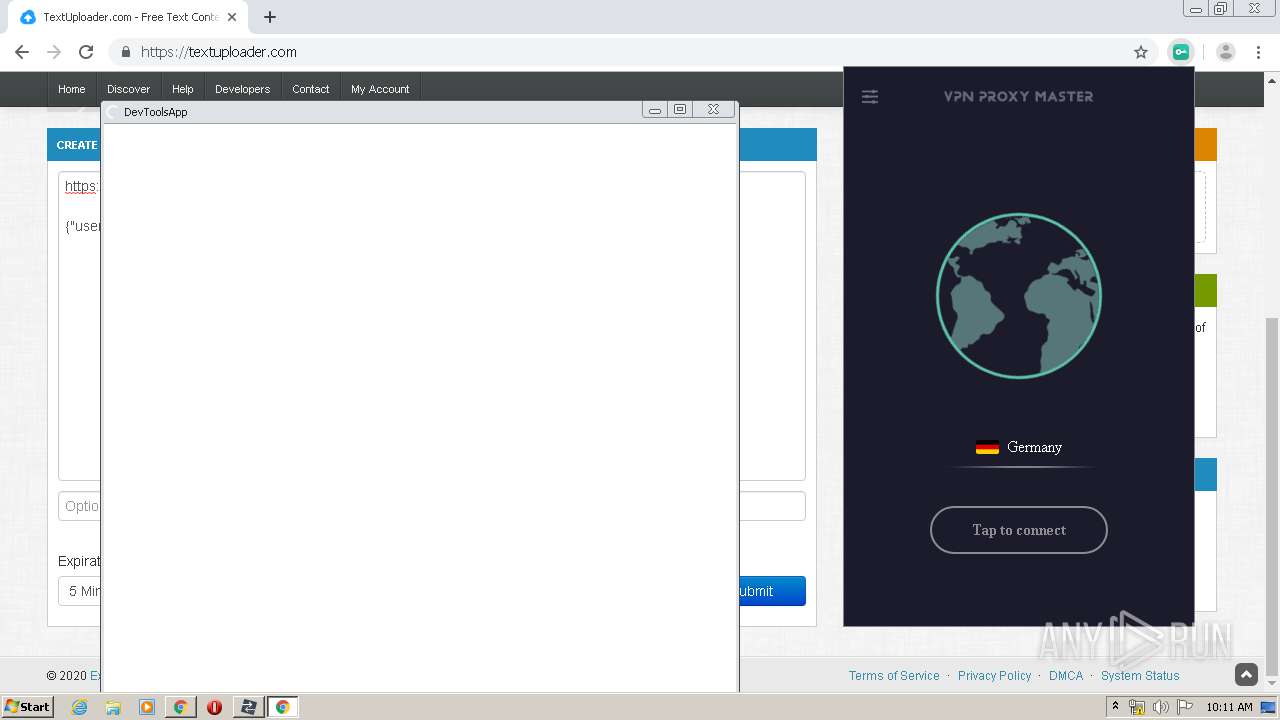
| URL: | https://chrome.google.com/webstore/detail/vpn-proxy-master/lnfdmdhmfbimhhpaeocncdlhiodoblbd |
| Full analysis: | https://app.any.run/tasks/509eec86-b442-4c39-9599-1a42e9c817bd |
| Verdict: | Malicious activity |
| Analysis date: | March 28, 2020, 10:07:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9C8032601DB4EABE9941F051D3DFB830 |
| SHA1: | 4FB9CC00B2C4239D4A14E9547E8B74D2DF432409 |
| SHA256: | 4A11E6A520F3F344E7D0645AFAFEE25C9FE475BFFE35A44A96BA2BF8FAB7FB05 |
| SSDEEP: | 3:N8Qa9t3u0A2RKelJWYIBSOBIIvxfBKpHB:2Qa9c01RneBSuIefB4h |
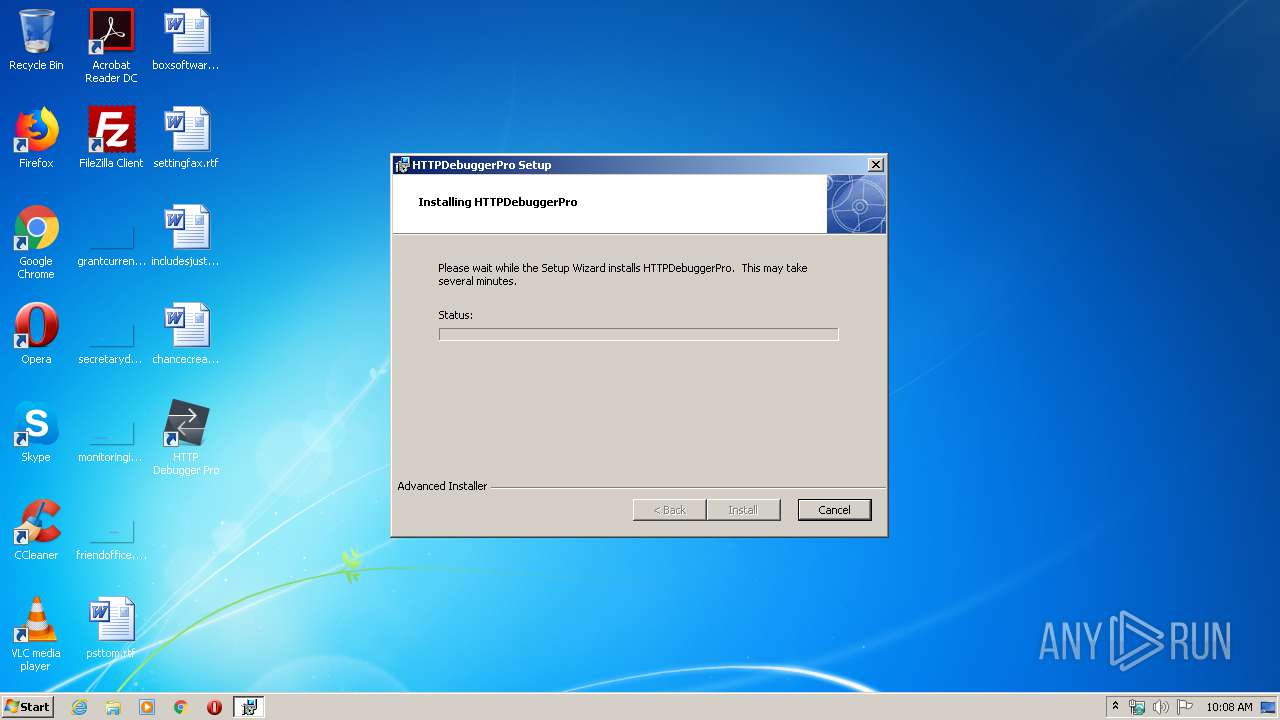
MALICIOUS
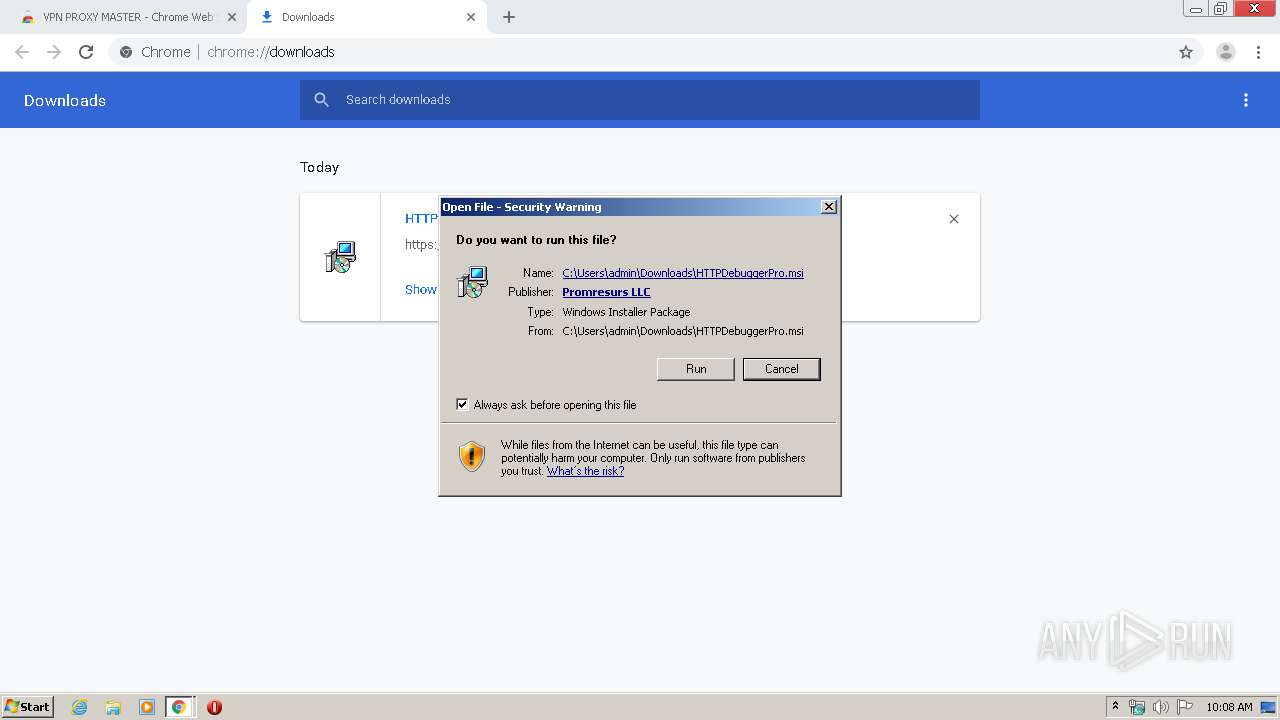
Application was dropped or rewritten from another process
- HTTPDebuggerSvc.exe (PID: 3344)
- HTTPDebuggerSvc.exe (PID: 3964)
- certutil.exe (PID: 2052)
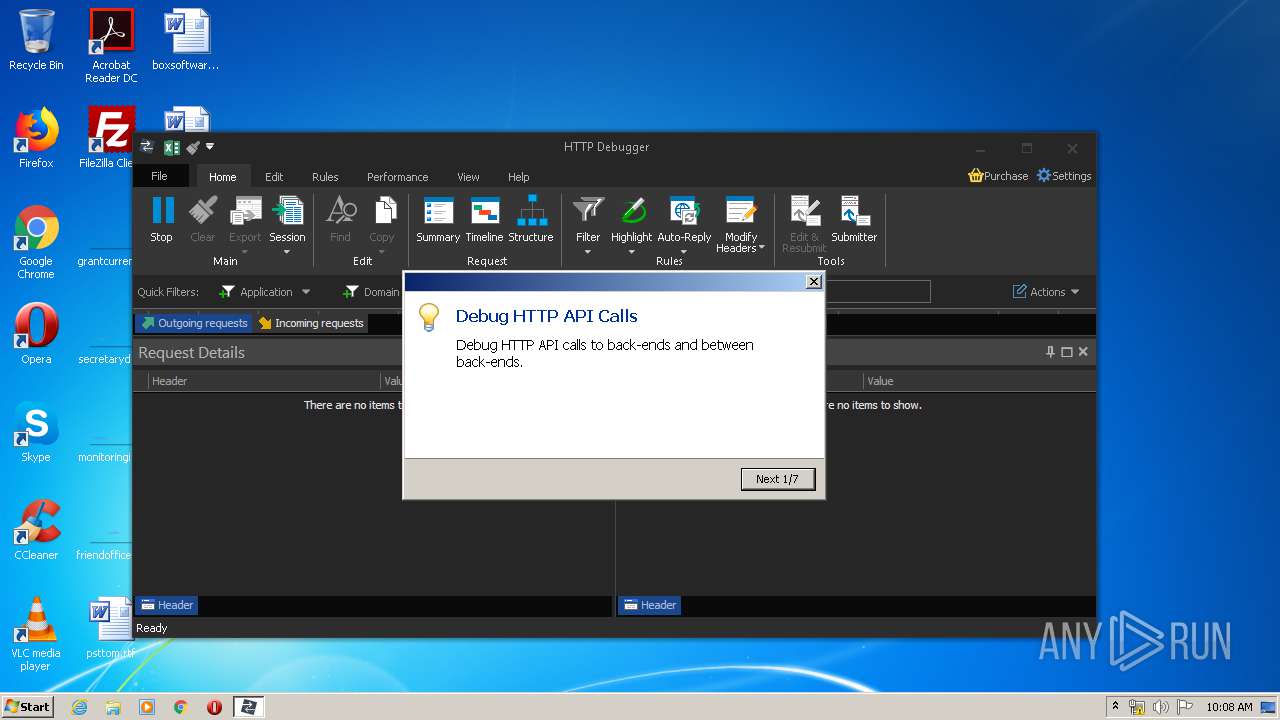
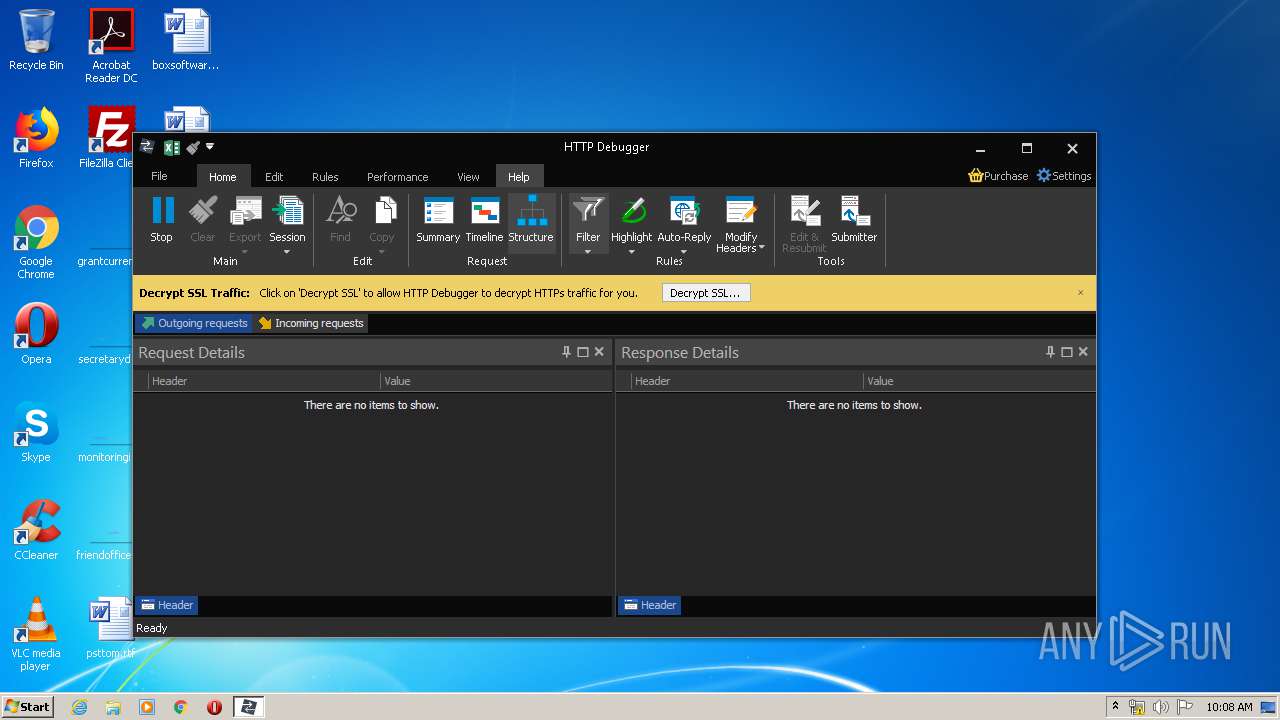
- HTTPDebuggerUI.exe (PID: 3240)
Loads dropped or rewritten executable
- HTTPDebuggerUI.exe (PID: 3240)
- MsiExec.exe (PID: 2764)
- certutil.exe (PID: 2052)
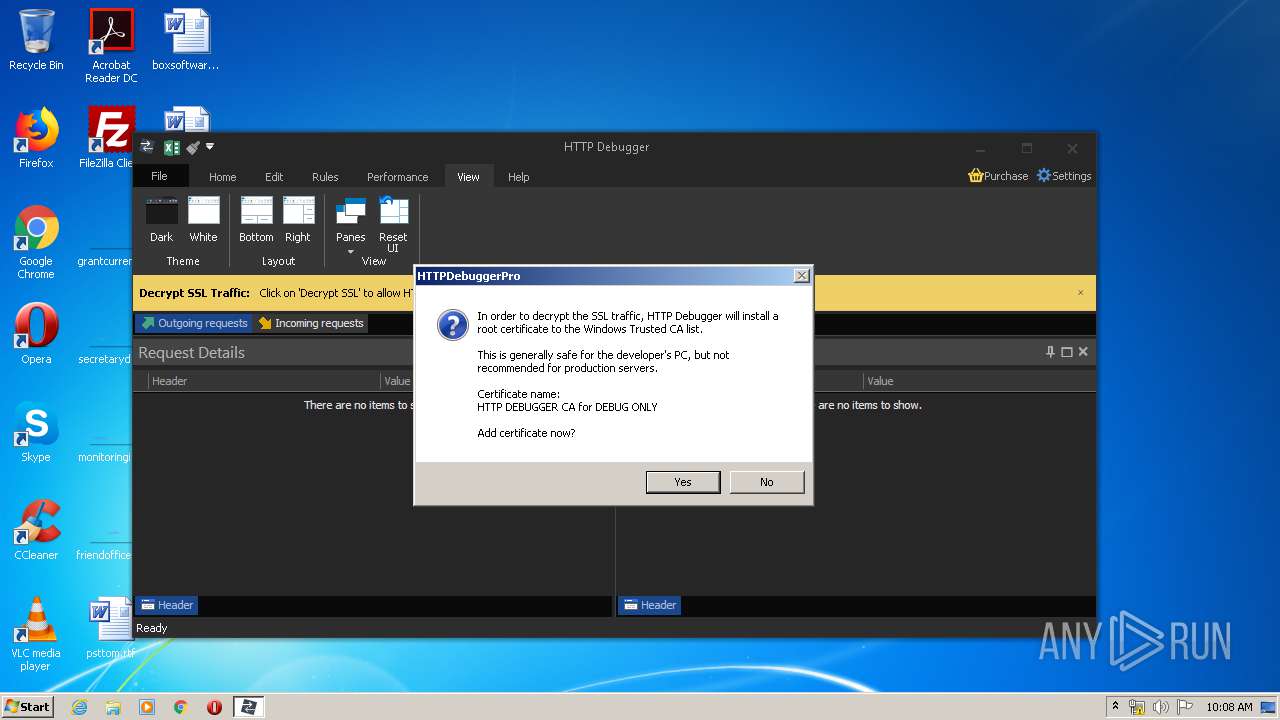
Changes settings of System certificates
- HTTPDebuggerSvc.exe (PID: 3344)
SUSPICIOUS
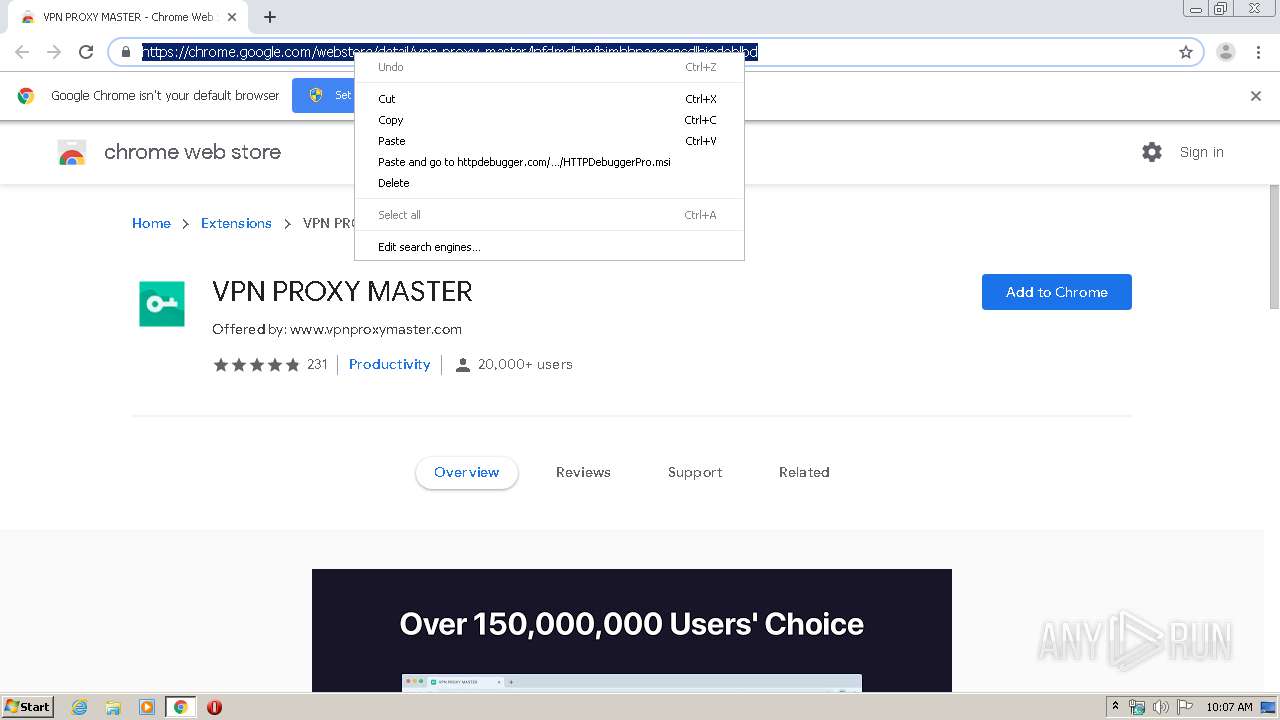
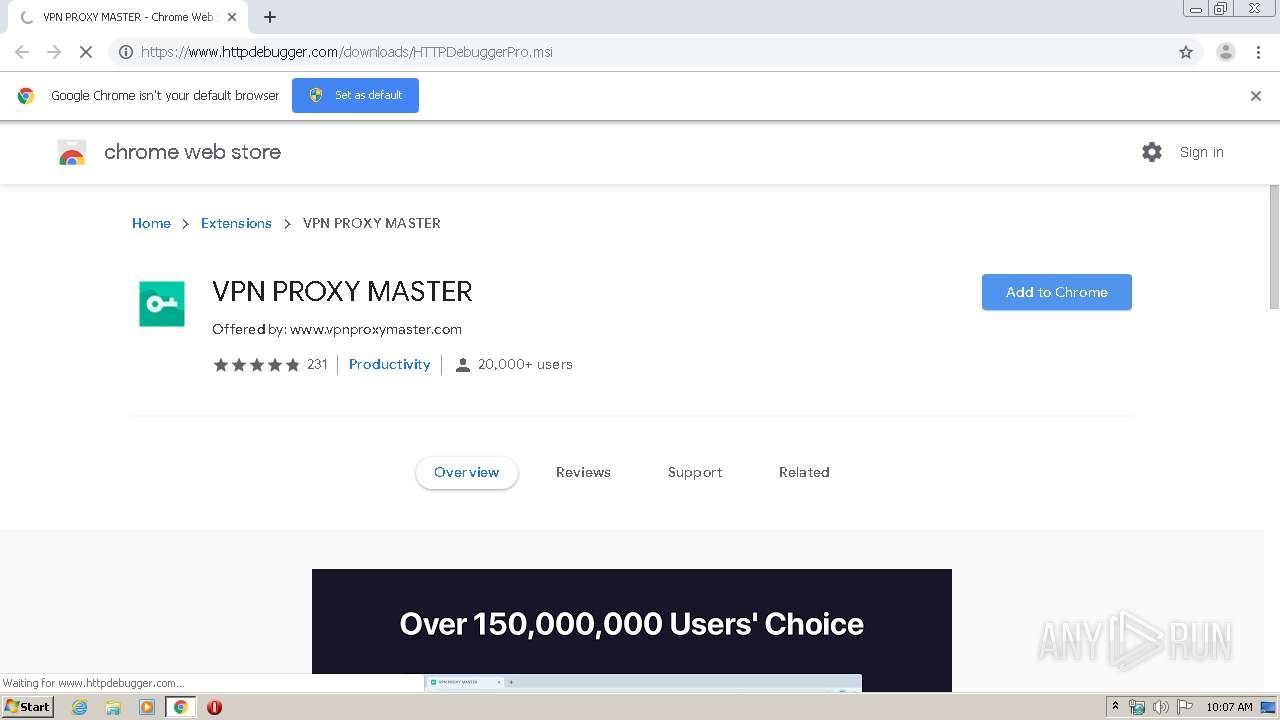
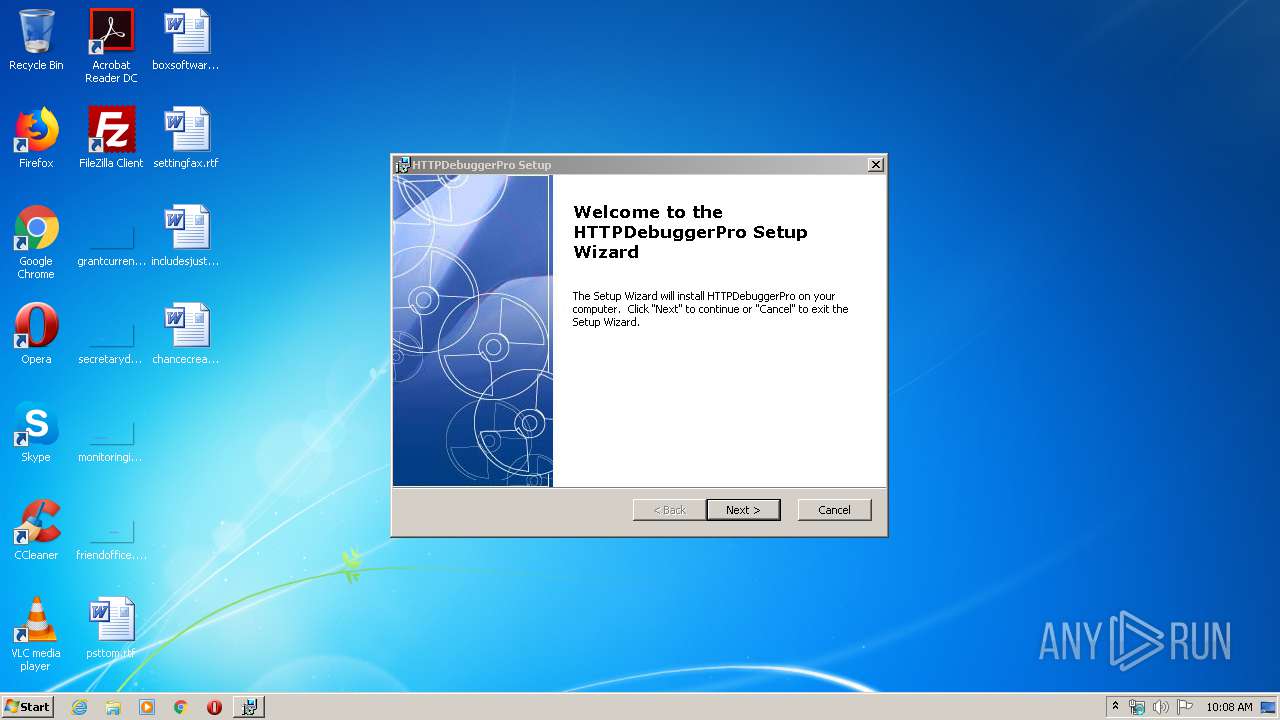
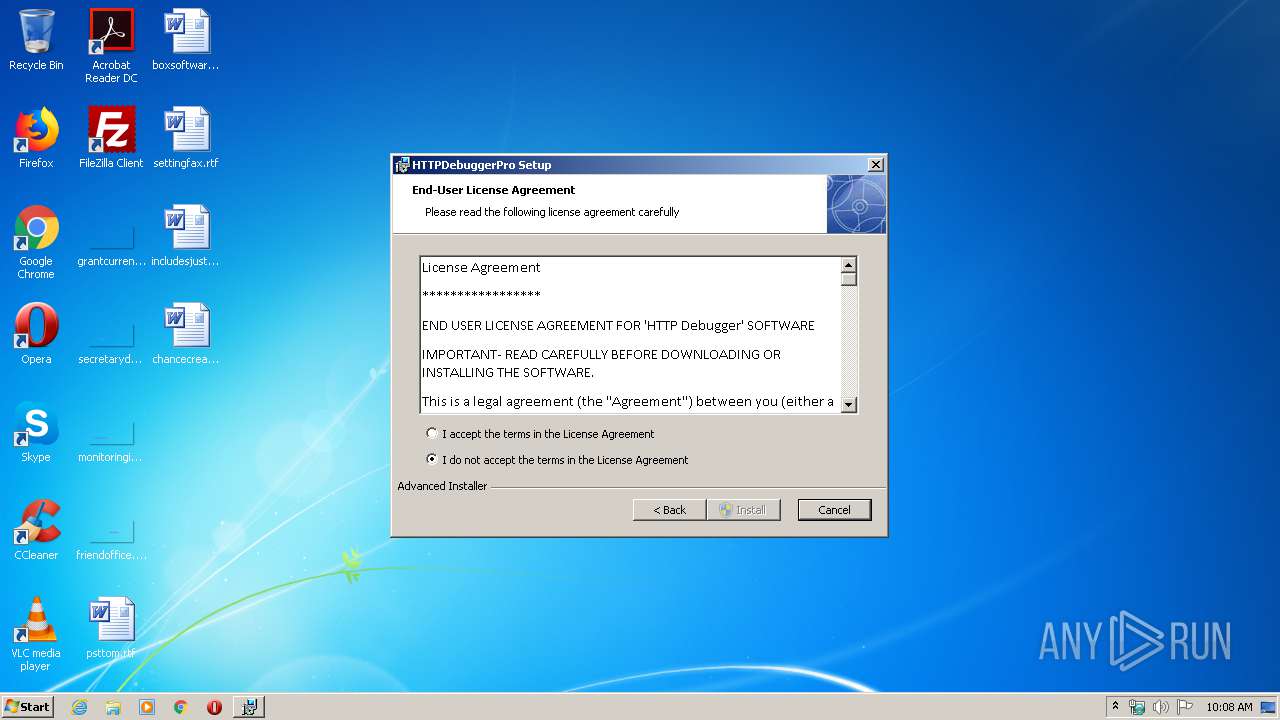
Starts Microsoft Installer
- chrome.exe (PID: 2728)
Executed as Windows Service
- vssvc.exe (PID: 3828)
- HTTPDebuggerSvc.exe (PID: 3344)
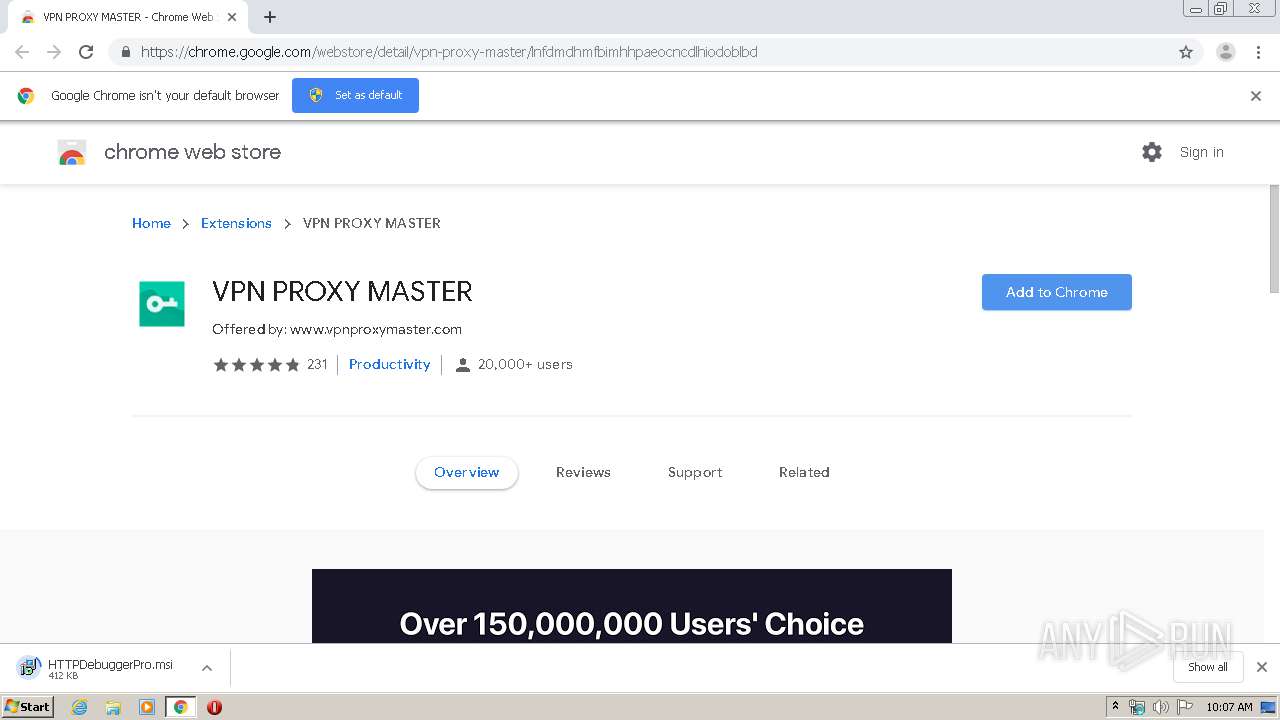
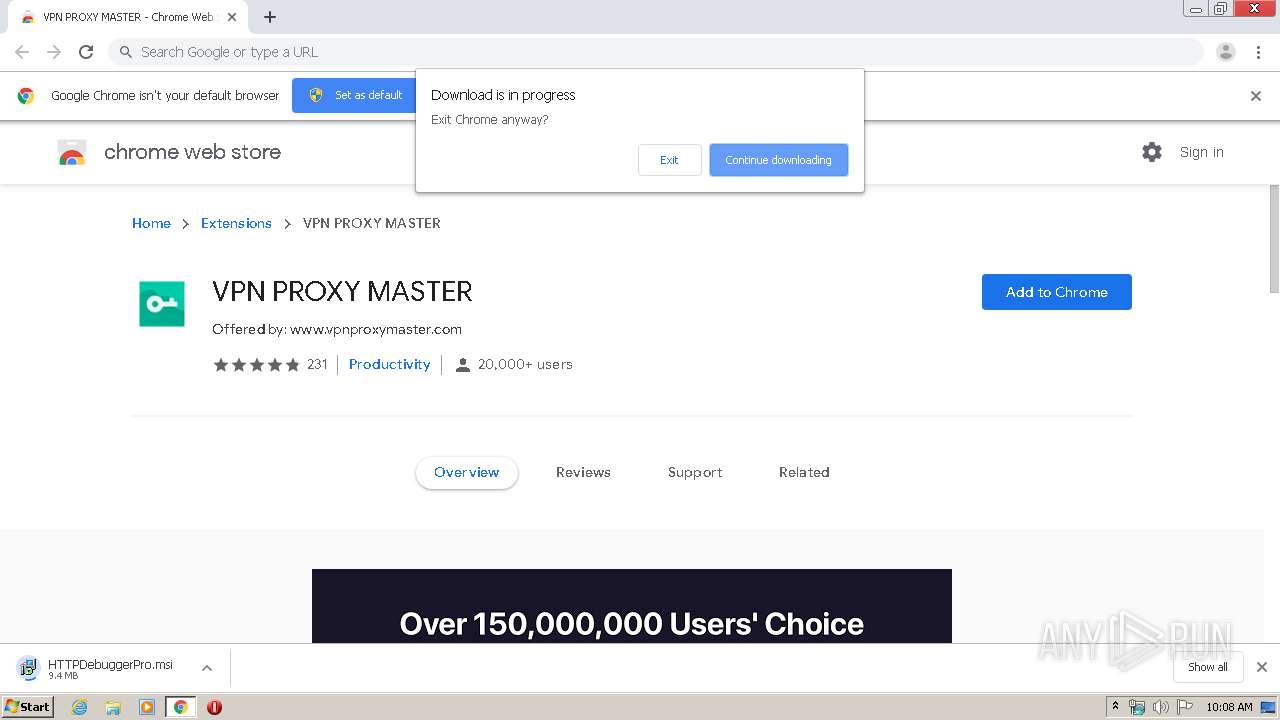
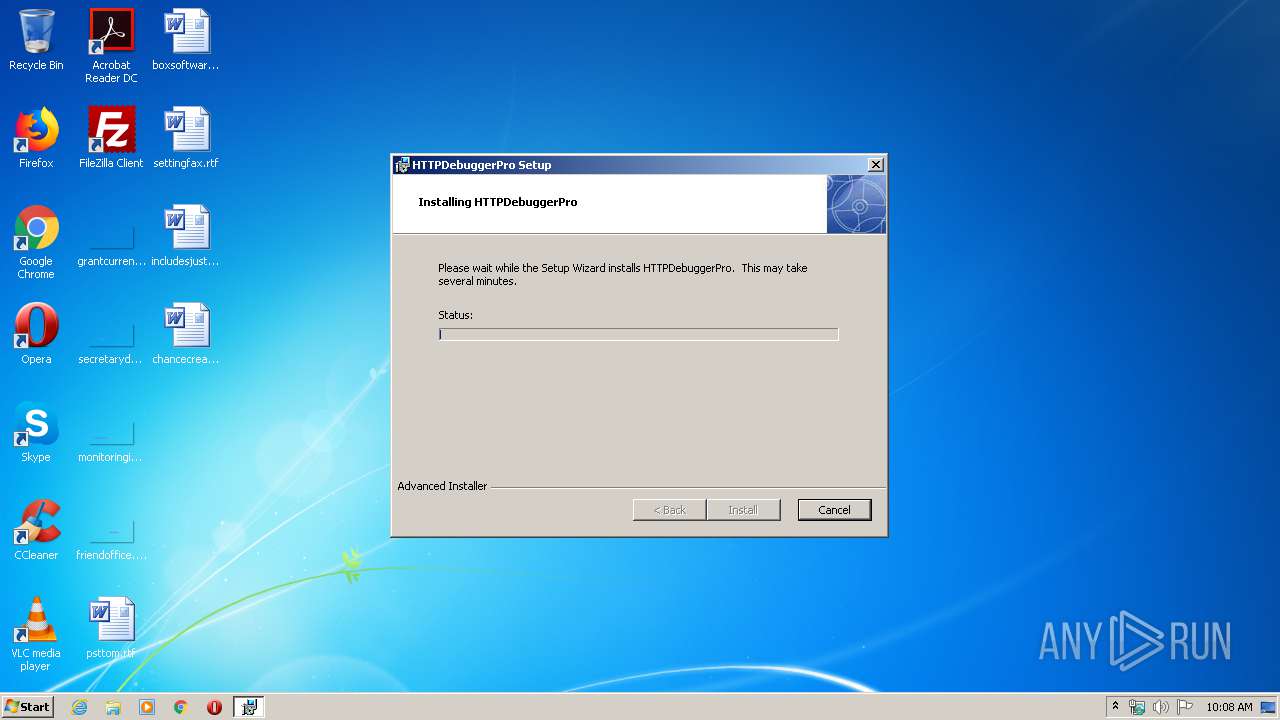
Executable content was dropped or overwritten
- msiexec.exe (PID: 576)
- msiexec.exe (PID: 2668)
- HTTPDebuggerSvc.exe (PID: 3344)
Creates COM task schedule object
- MsiExec.exe (PID: 2764)
Creates files in the program directory
- HTTPDebuggerSvc.exe (PID: 3344)
Creates or modifies windows services
- HTTPDebuggerSvc.exe (PID: 3344)
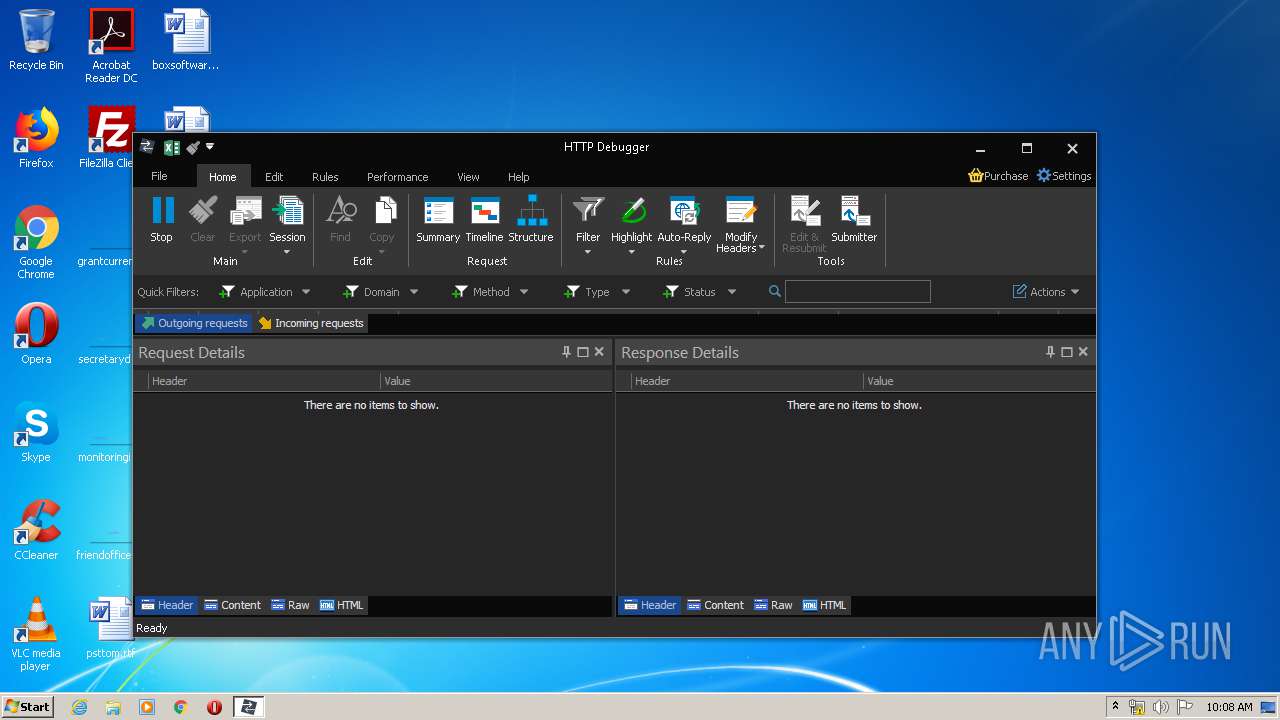
Reads Internet Cache Settings
- HTTPDebuggerUI.exe (PID: 3240)
Reads internet explorer settings
- HTTPDebuggerUI.exe (PID: 3240)
Creates files in the Windows directory
- HTTPDebuggerSvc.exe (PID: 3344)
Creates files in the driver directory
- HTTPDebuggerSvc.exe (PID: 3344)
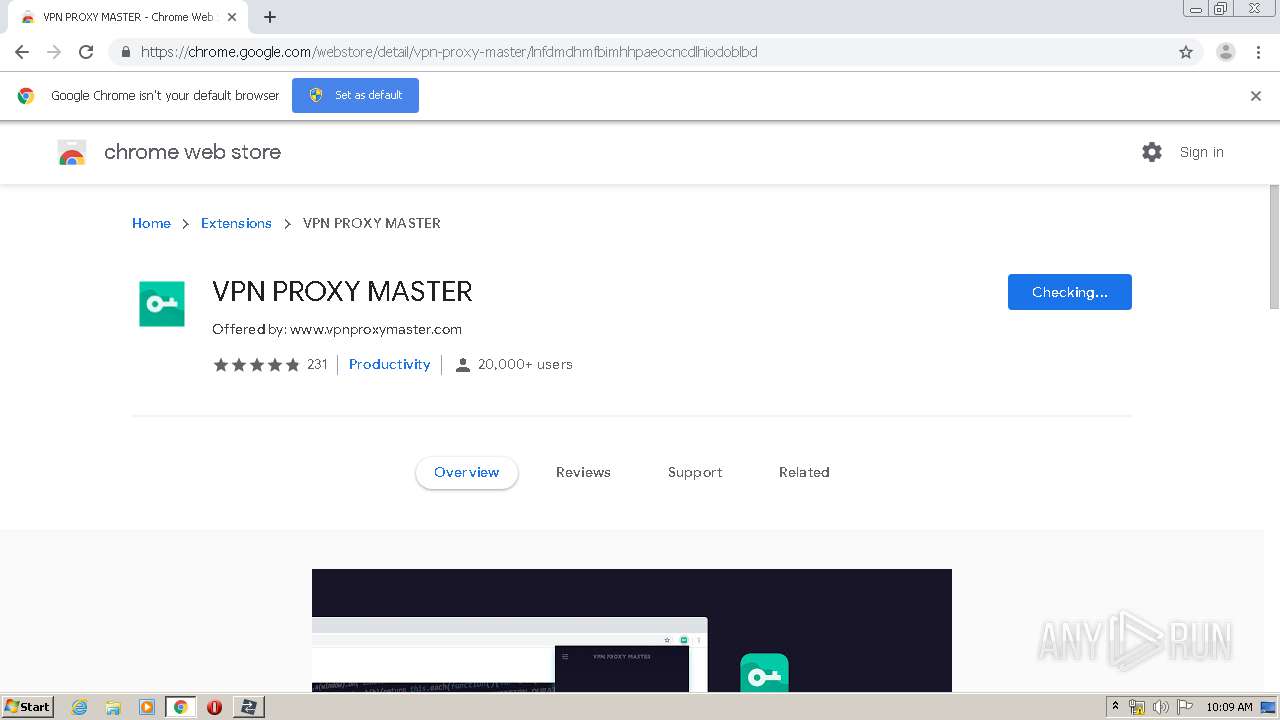
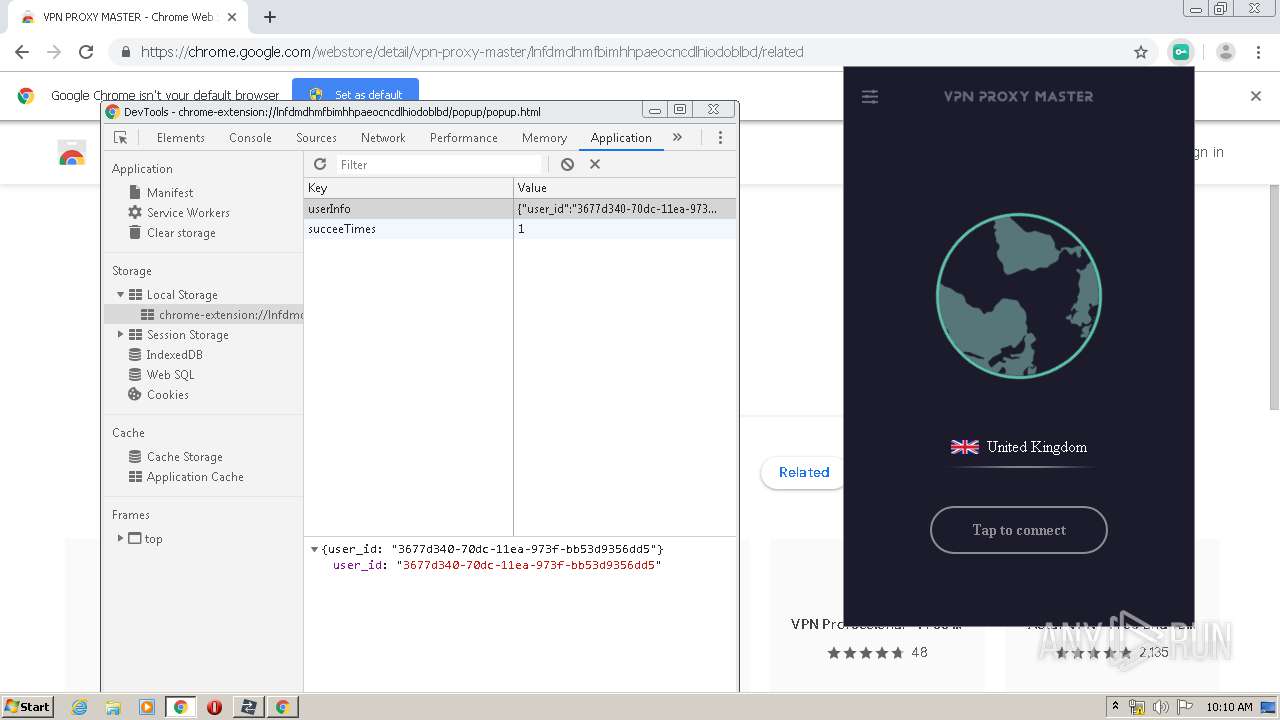
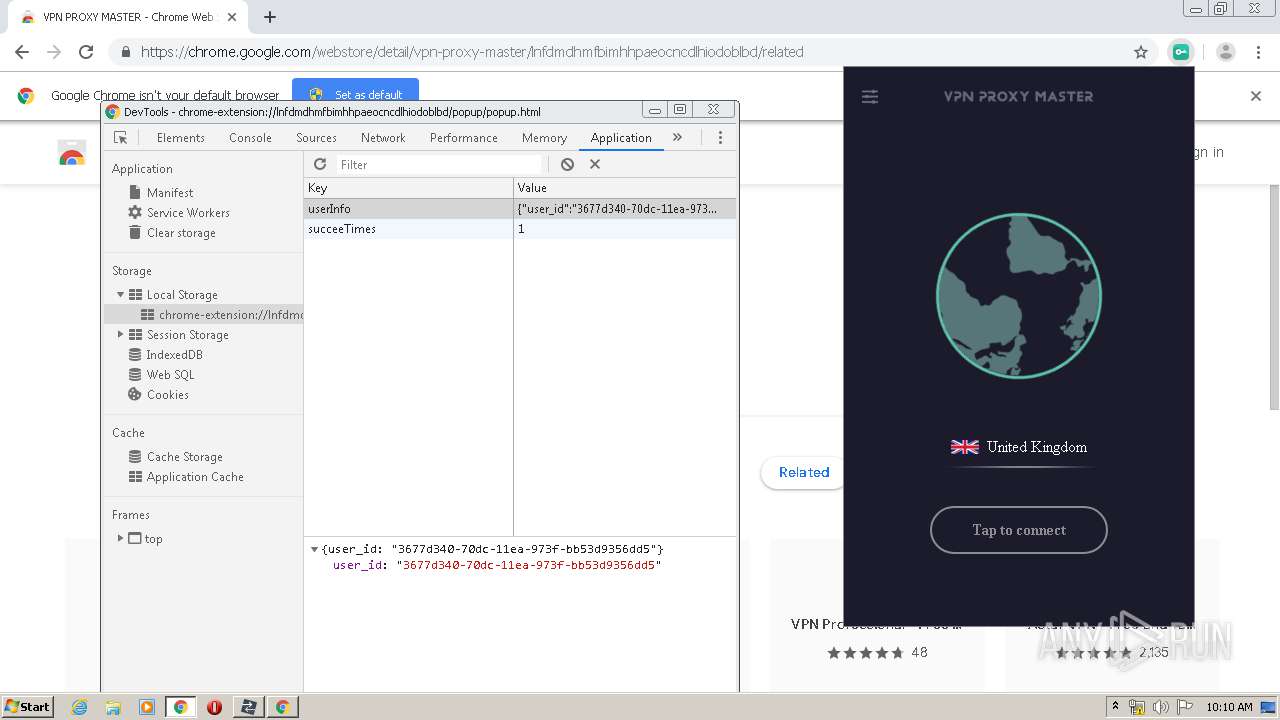
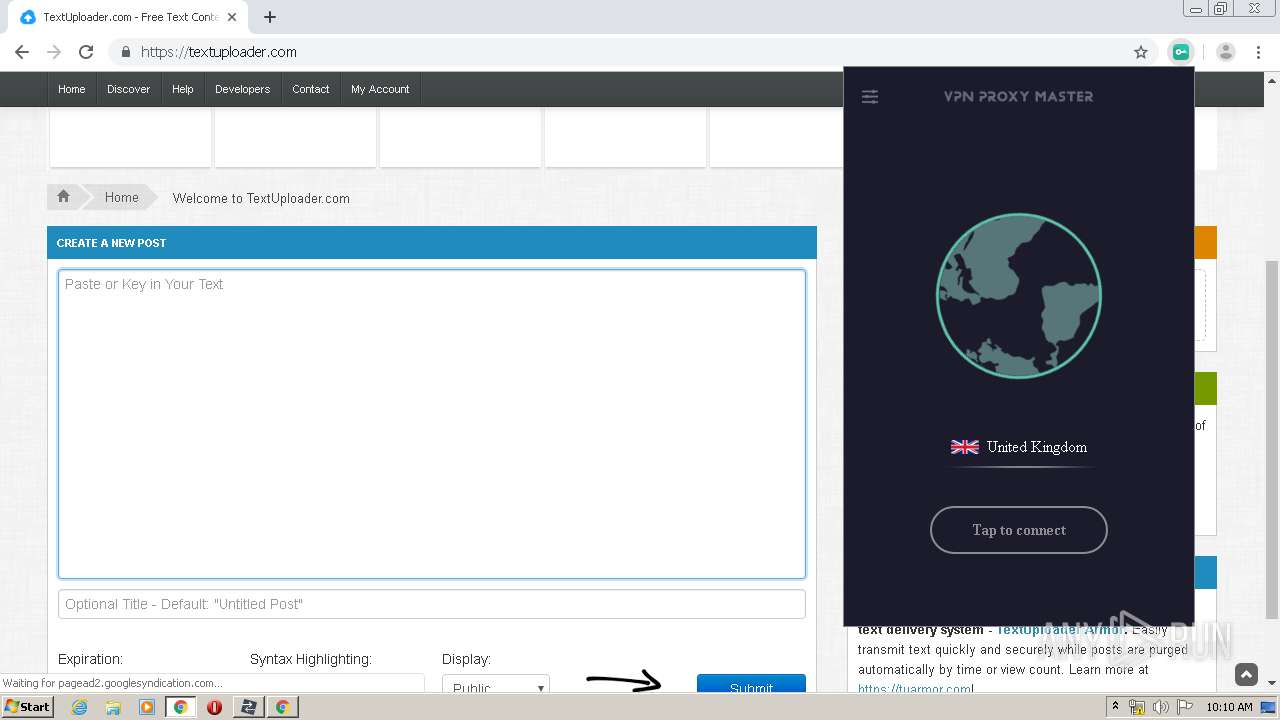
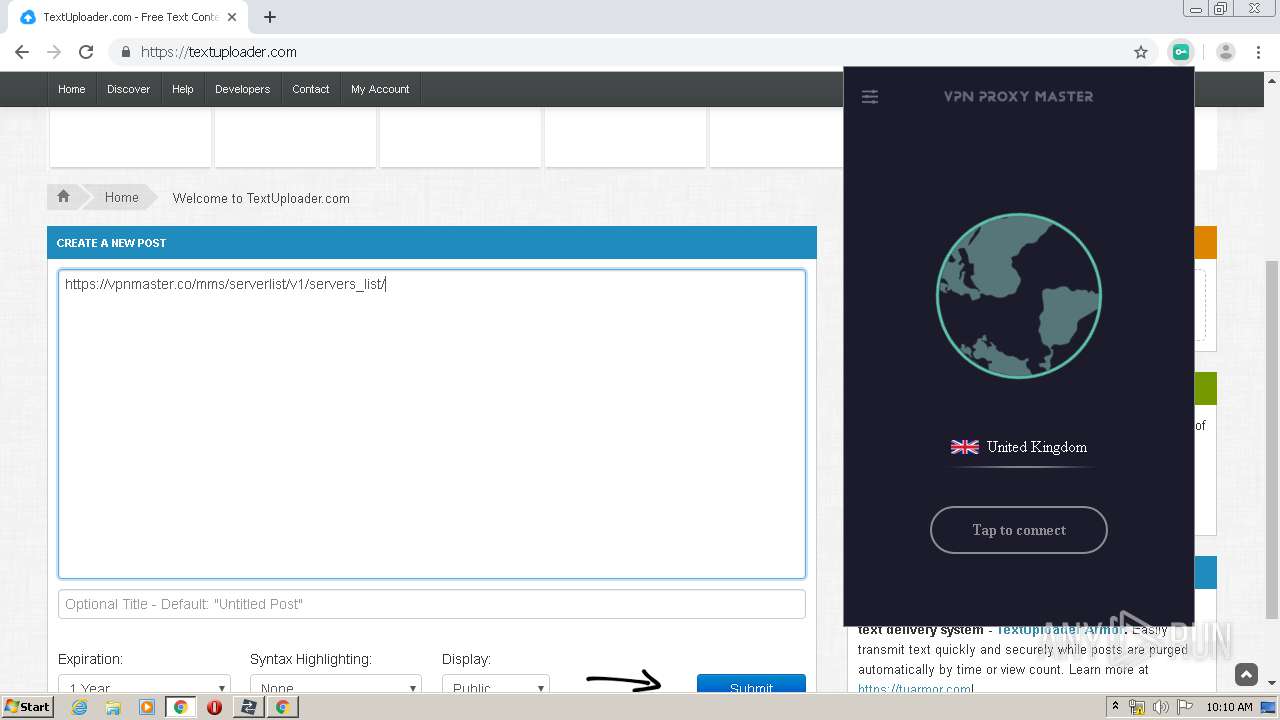
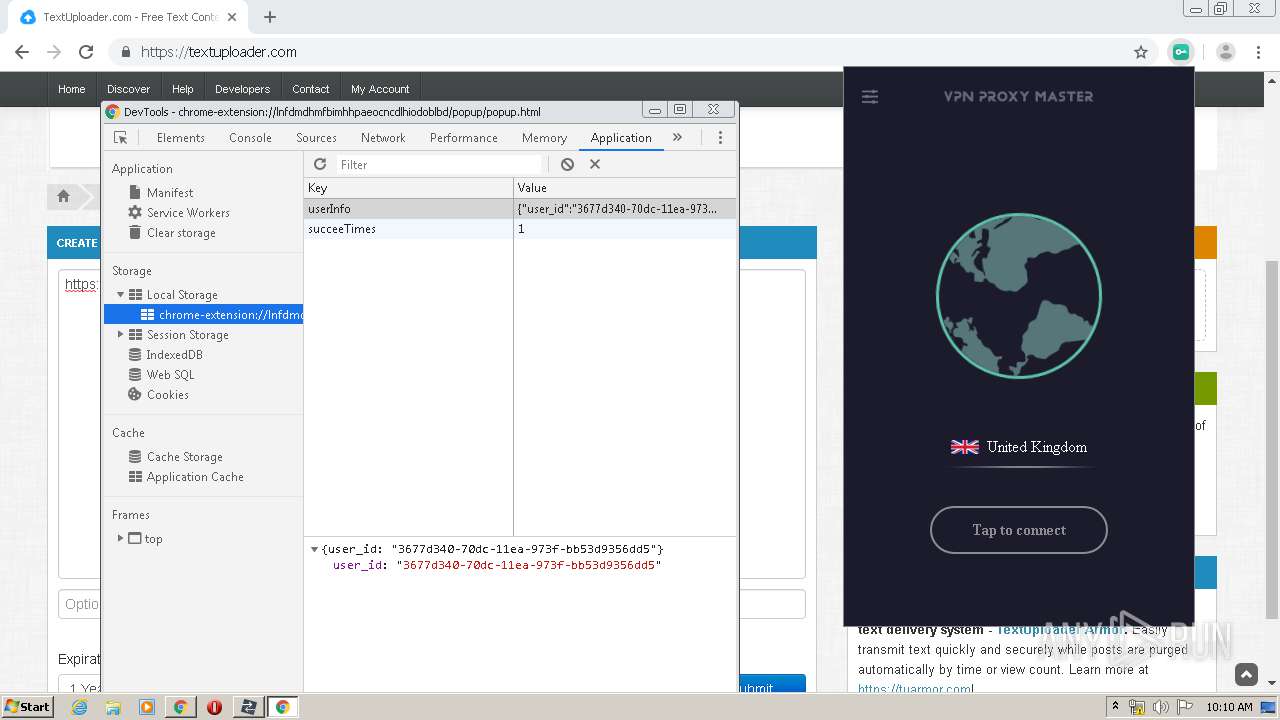
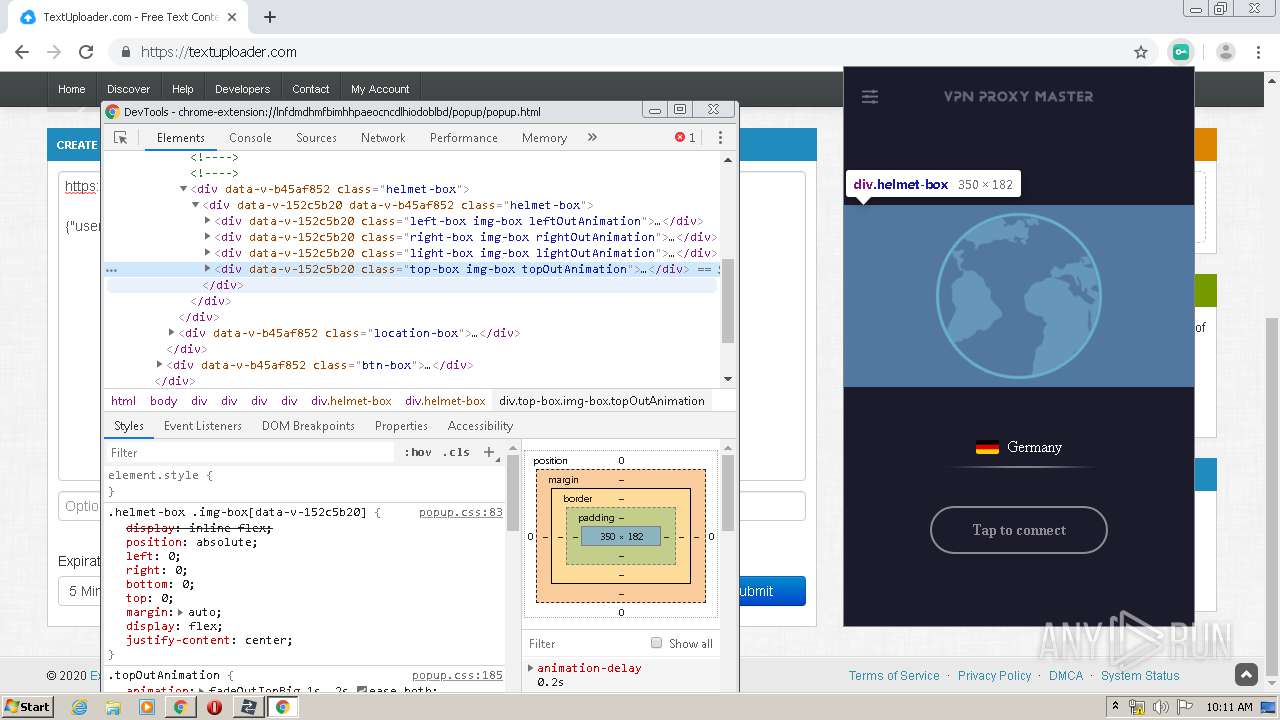
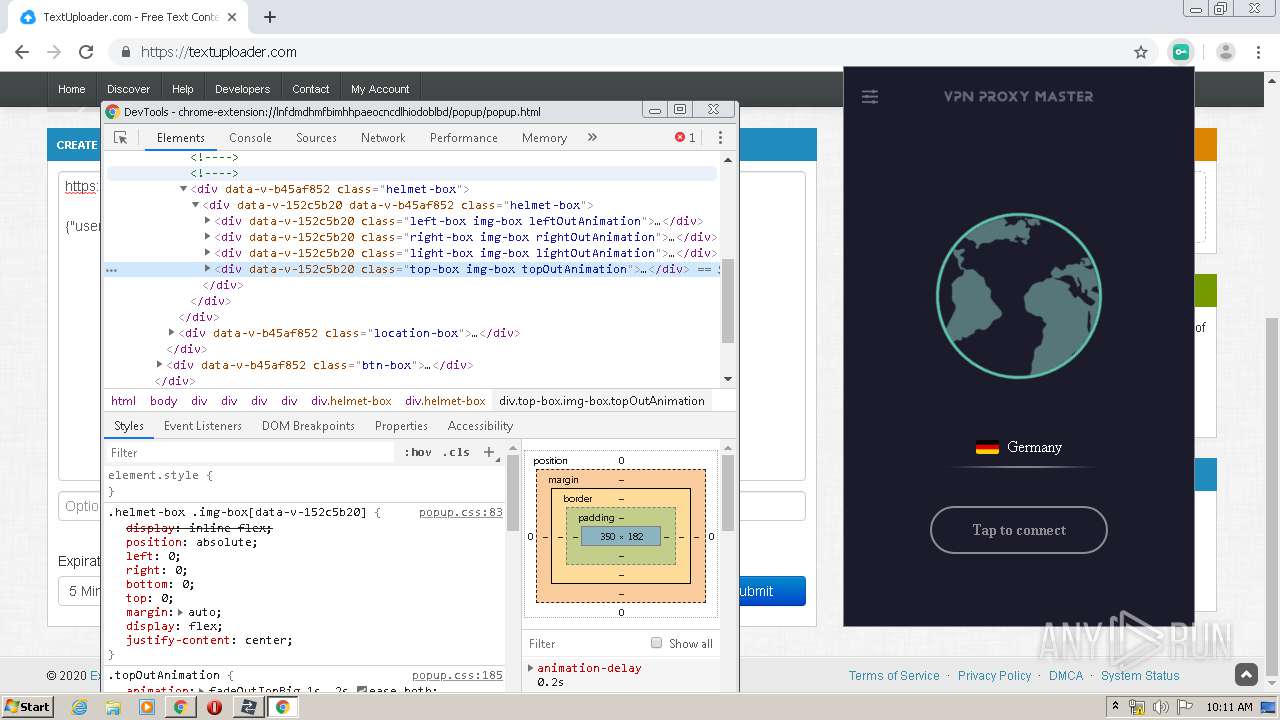
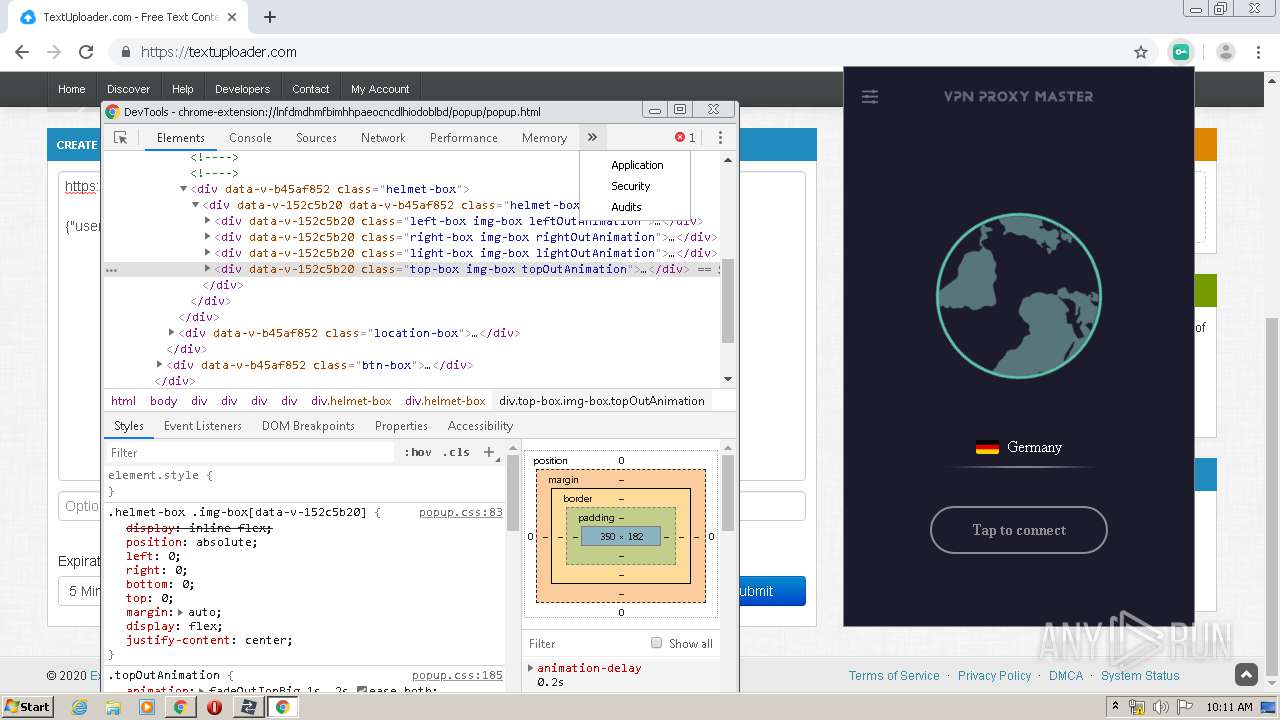
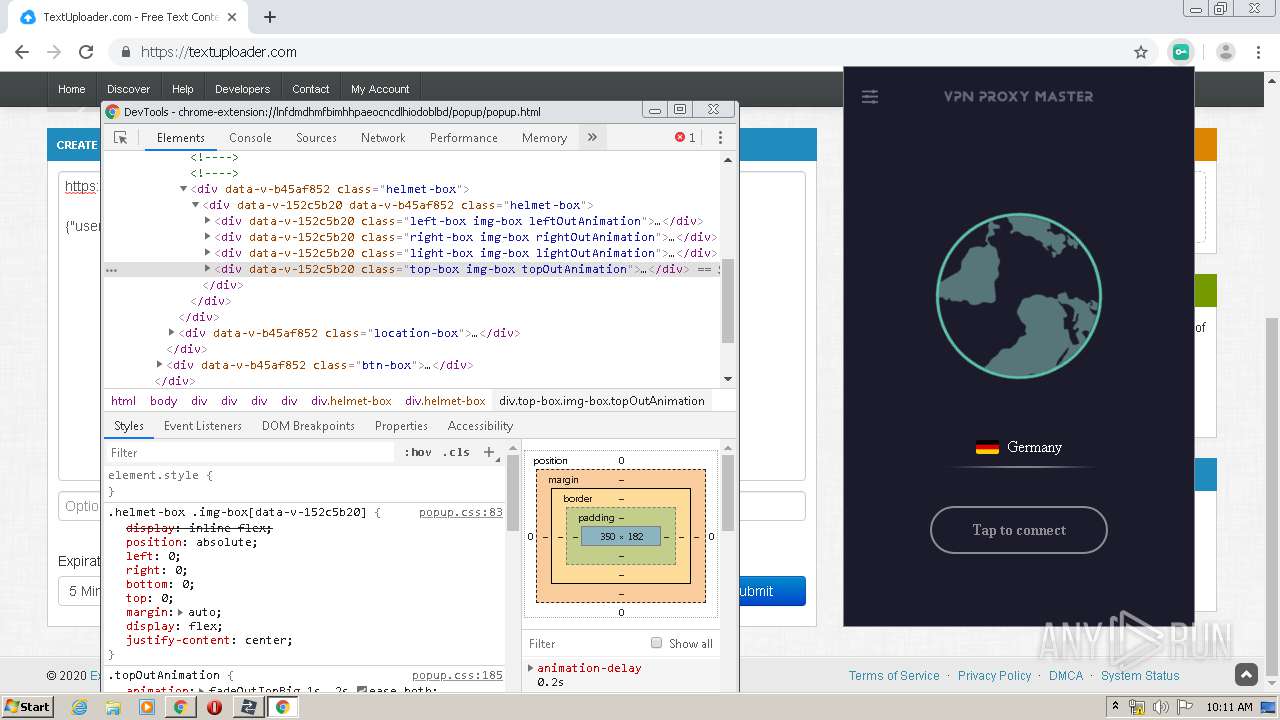
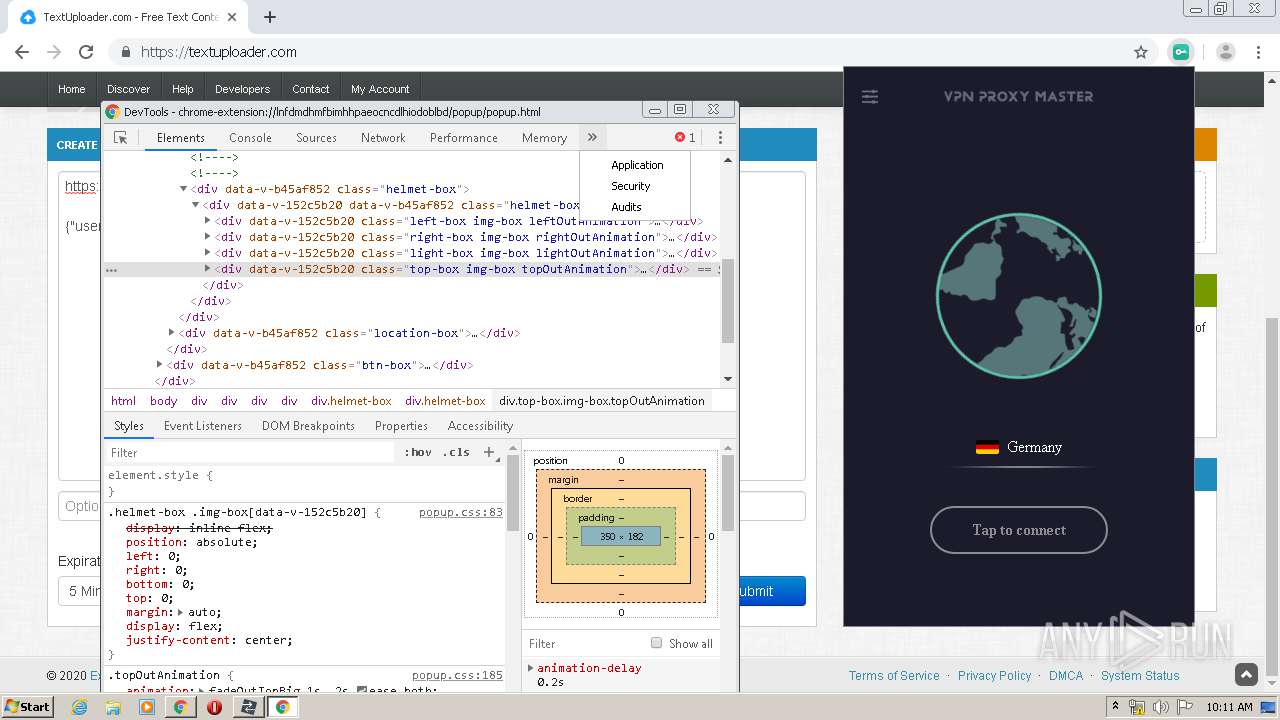
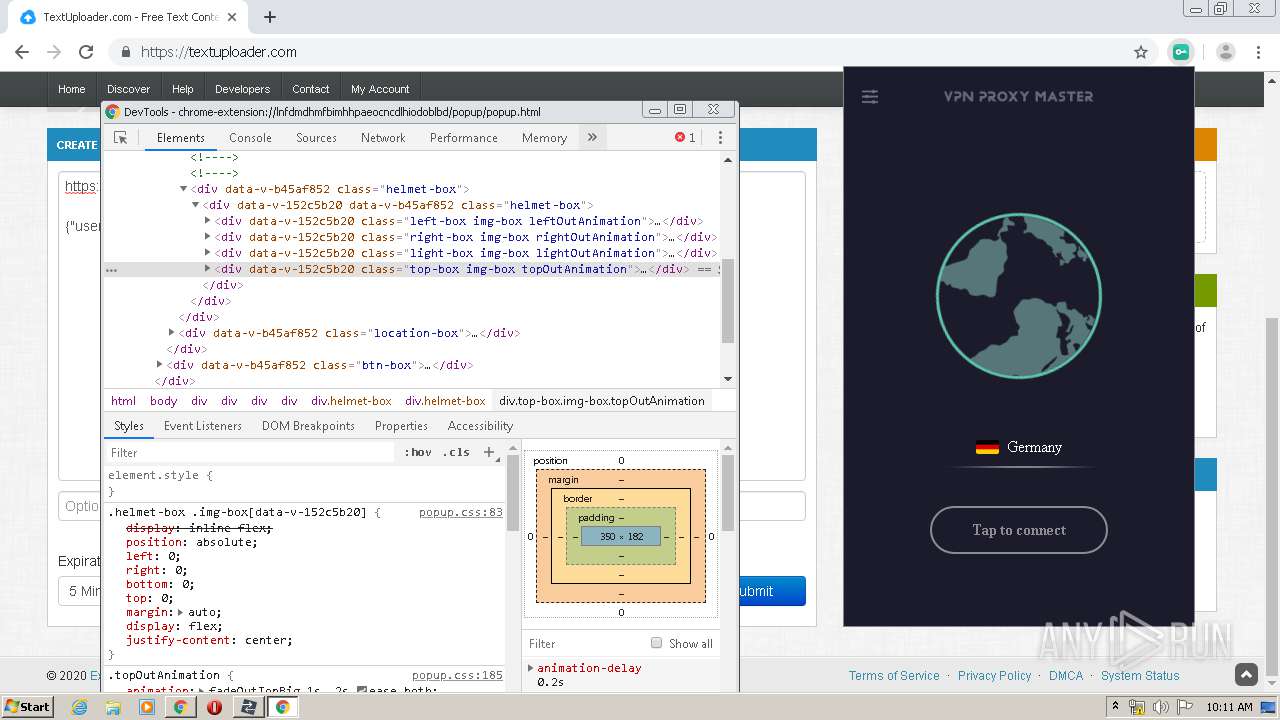
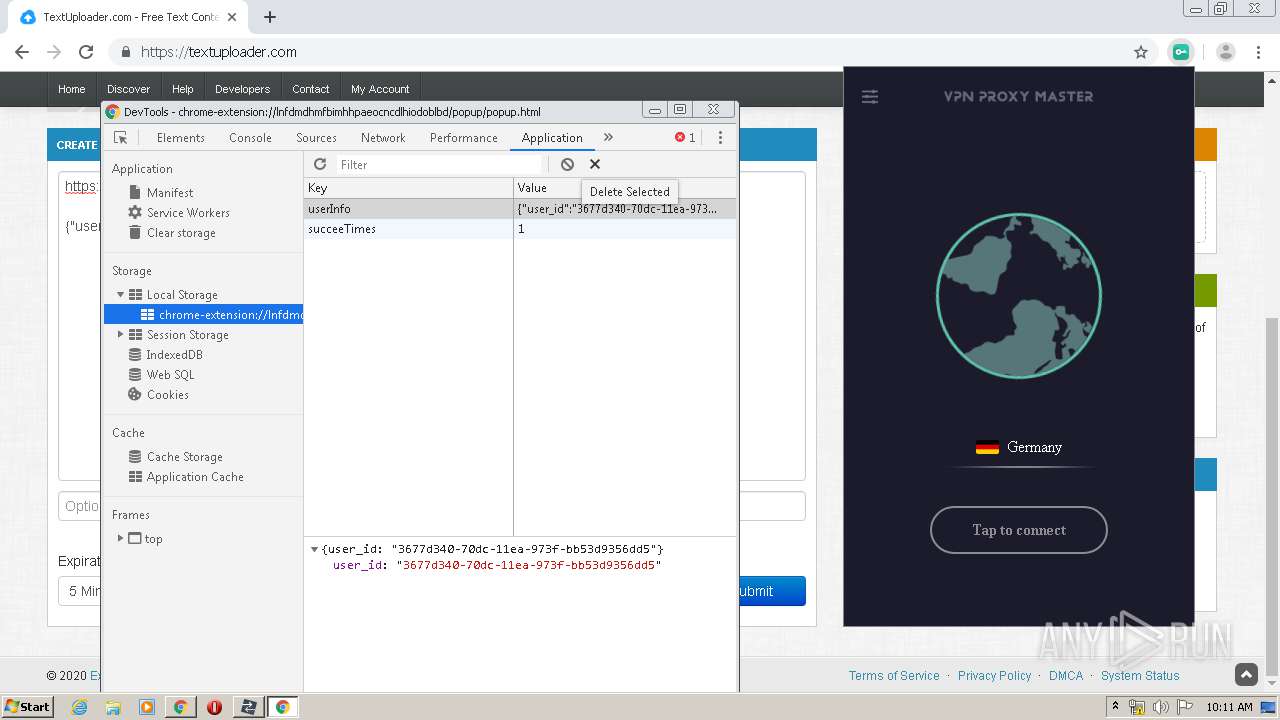
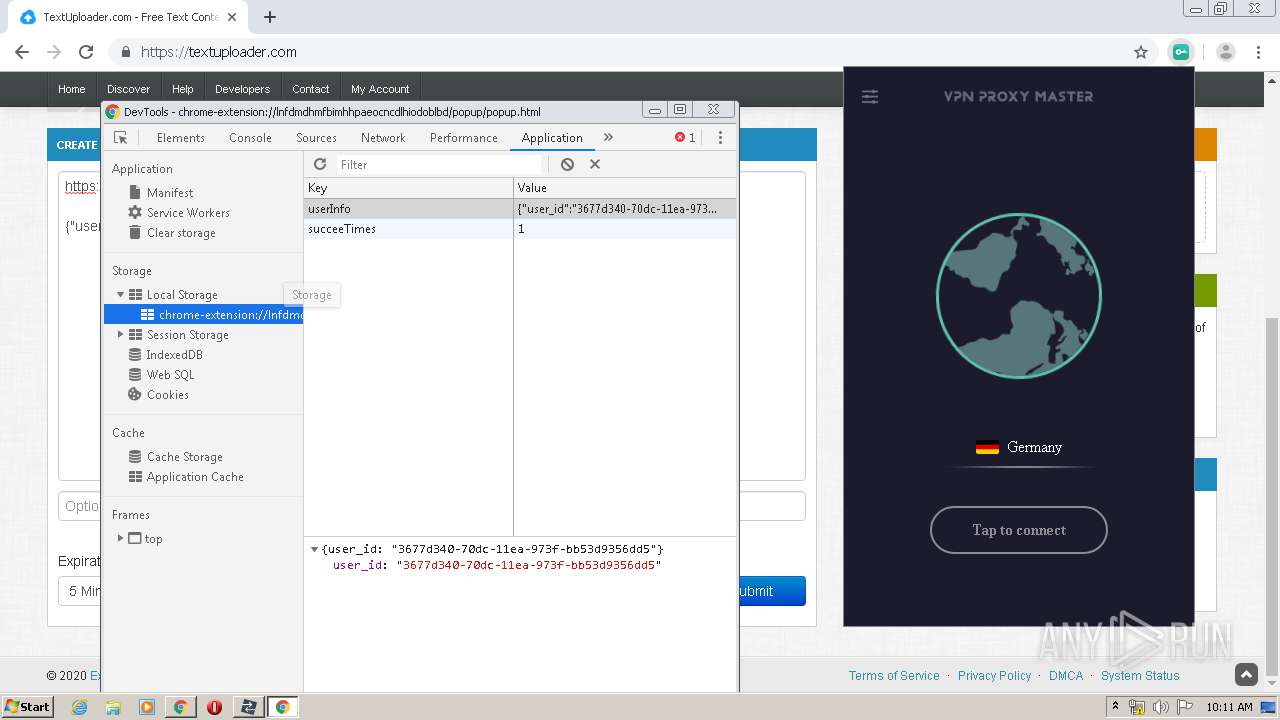
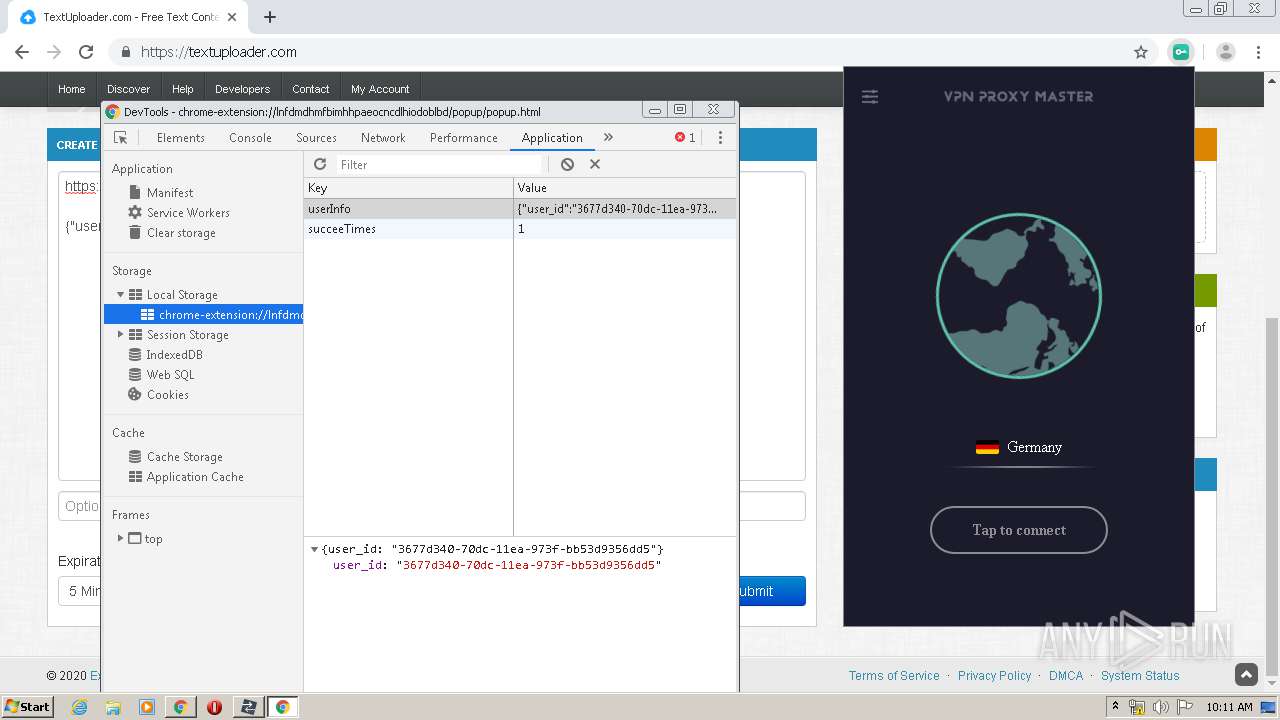
Modifies files in Chrome extension folder
- chrome.exe (PID: 3688)
Connects to server without host name
- chrome.exe (PID: 3260)
INFO
Application launched itself
- chrome.exe (PID: 2728)
- msiexec.exe (PID: 2668)
- chrome.exe (PID: 3688)
Reads the hosts file
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3688)
- chrome.exe (PID: 3260)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2072)
- MsiExec.exe (PID: 3356)
Reads settings of System Certificates
- chrome.exe (PID: 2728)
- HTTPDebuggerUI.exe (PID: 3240)
- HTTPDebuggerSvc.exe (PID: 3344)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3828)
Reads Internet Cache Settings
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3688)
Searches for installed software
- msiexec.exe (PID: 2668)
Creates files in the program directory
- msiexec.exe (PID: 2668)
Creates a software uninstall entry
- msiexec.exe (PID: 2668)
Manual execution by user
- chrome.exe (PID: 3688)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
119
Monitored processes
75
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,11451405413049679662,10144588660632284329,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17487081207851795304 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11451405413049679662,10144588660632284329,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16271717134487046093 --mojo-platform-channel-handle=3388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
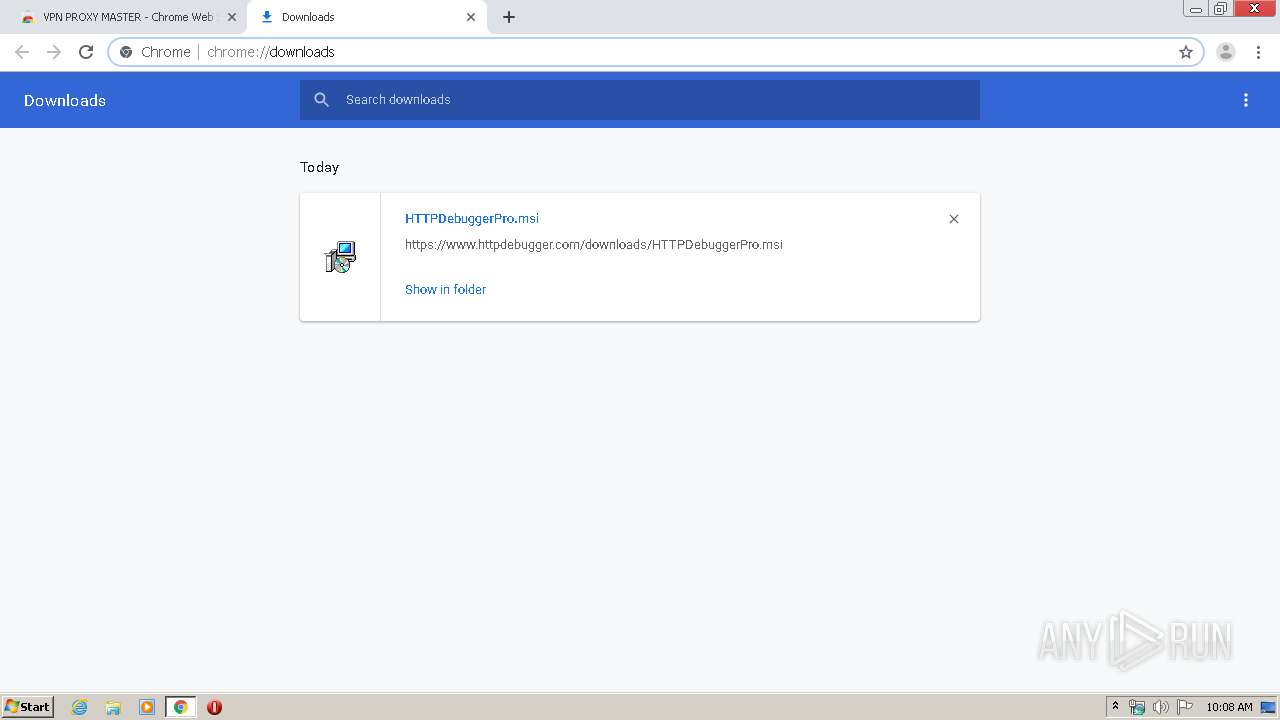
| 576 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\Downloads\HTTPDebuggerPro.msi" | C:\Windows\System32\msiexec.exe | chrome.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa8a9d0,0x6fa8a9e0,0x6fa8a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ebaa9d0,0x6ebaa9e0,0x6ebaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,11451405413049679662,10144588660632284329,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11399555585329207819 --mojo-platform-channel-handle=3368 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2052 | nss\certutil -A -t "TCu" -i "C:\ProgramData\HTTPDebuggerPro\Cert\SSL\HTTP DEBUGGER CA for DEBUG ONLY 2.cer" -n "HTTP DEBUGGER CA for DEBUG ONLY 2" -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\QLDYZ5~1.DEF"-f pwfile | C:\Program Files\HTTPDebuggerPro\nss\certutil.exe | — | HTTPDebuggerSvc.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 255 Modules
| |||||||||||||||
| 2072 | C:\Windows\system32\MsiExec.exe -Embedding CE81DE42F32254320E5785595B85DB96 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,11451405413049679662,10144588660632284329,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11300498712711085231 --mojo-platform-channel-handle=3444 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,18350942100763925543,16895672770203215882,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4421349305588361159 --mojo-platform-channel-handle=4100 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 539
Read events
1 864
Write events
648
Delete events
27
Modification events
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2976) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2728-13229863664681625 |
Value: 259 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
26
Suspicious files
157
Text files
457
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E7F21F1-AA8.pma | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c58f42c3-2f86-4452-83bb-944babb4bd53.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66d1a.TMP | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2728 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66f0e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
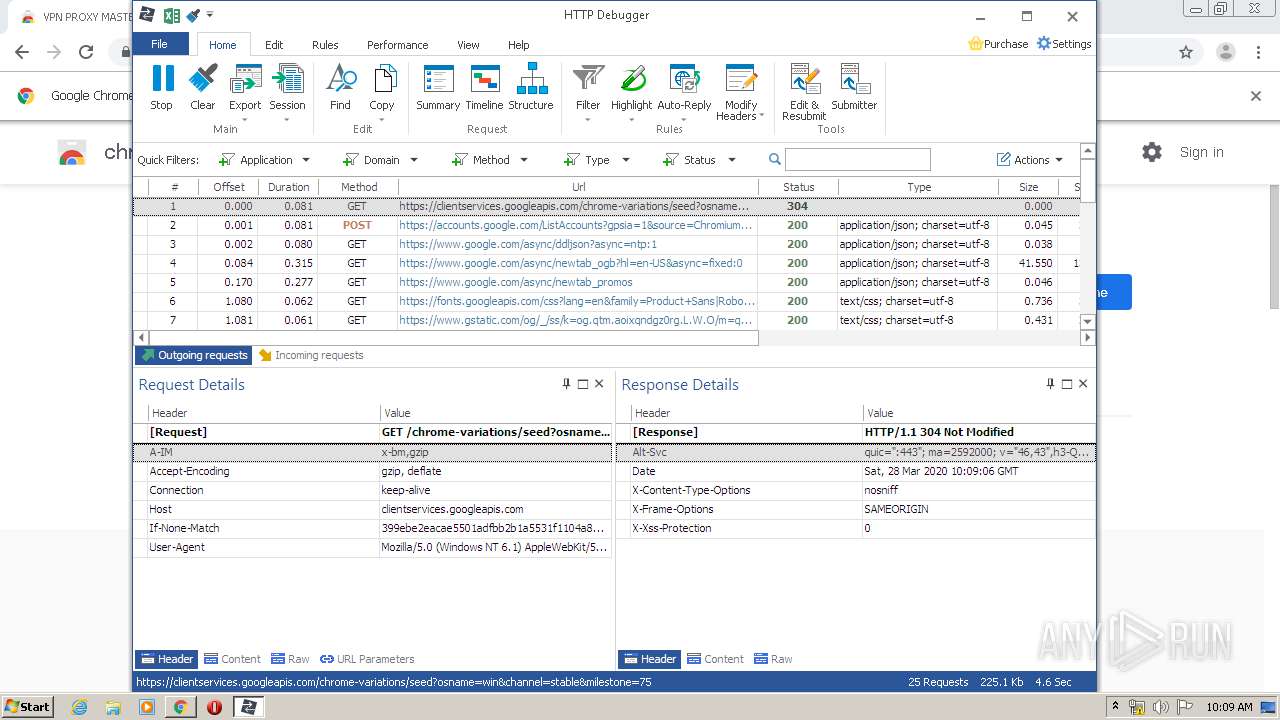
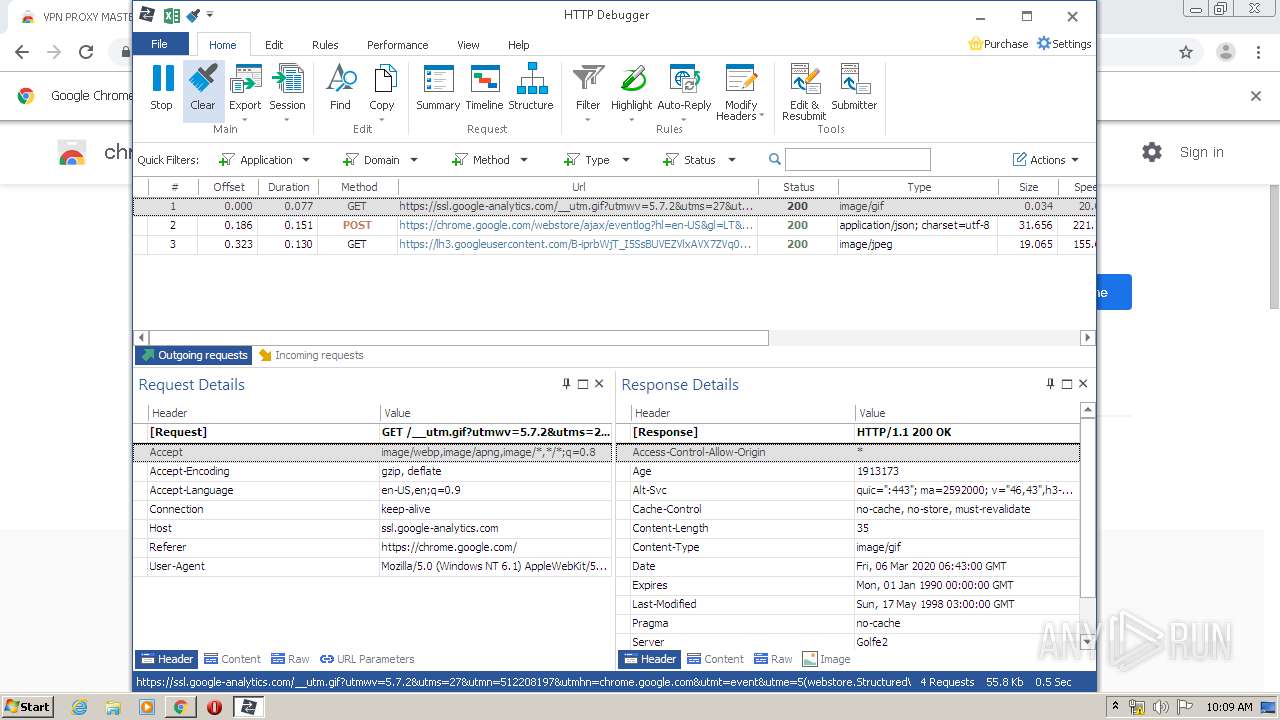
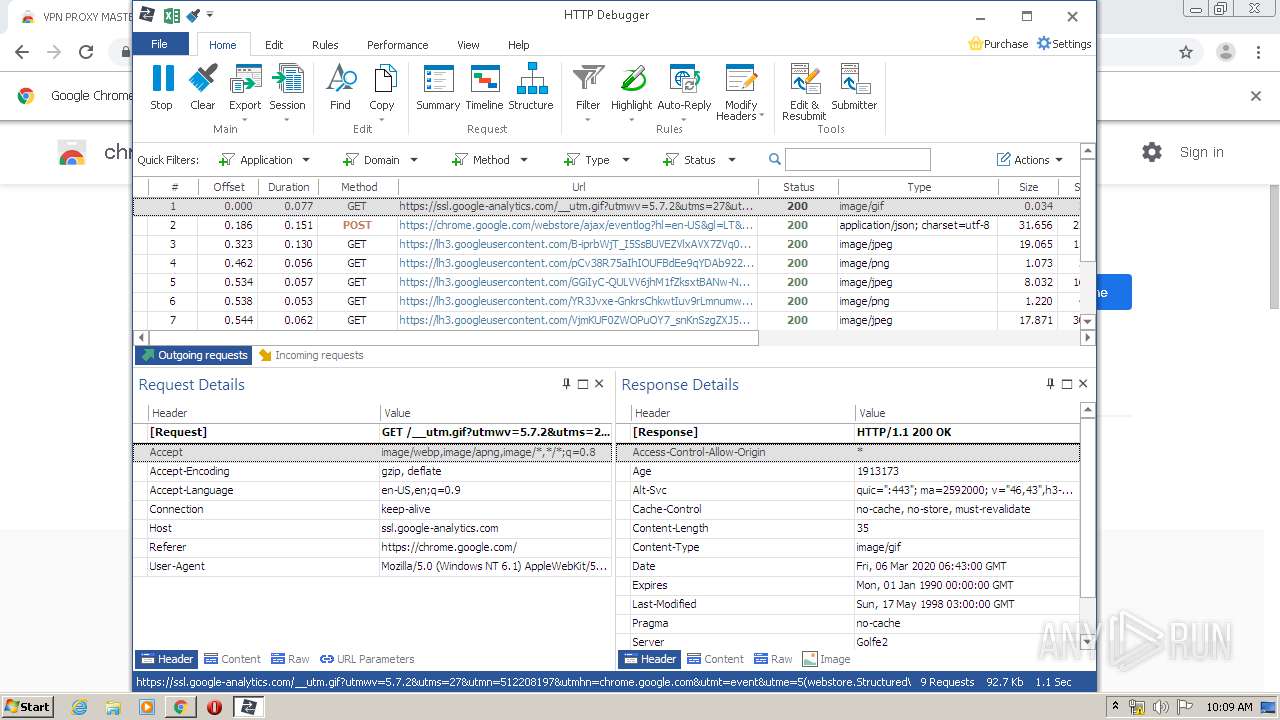
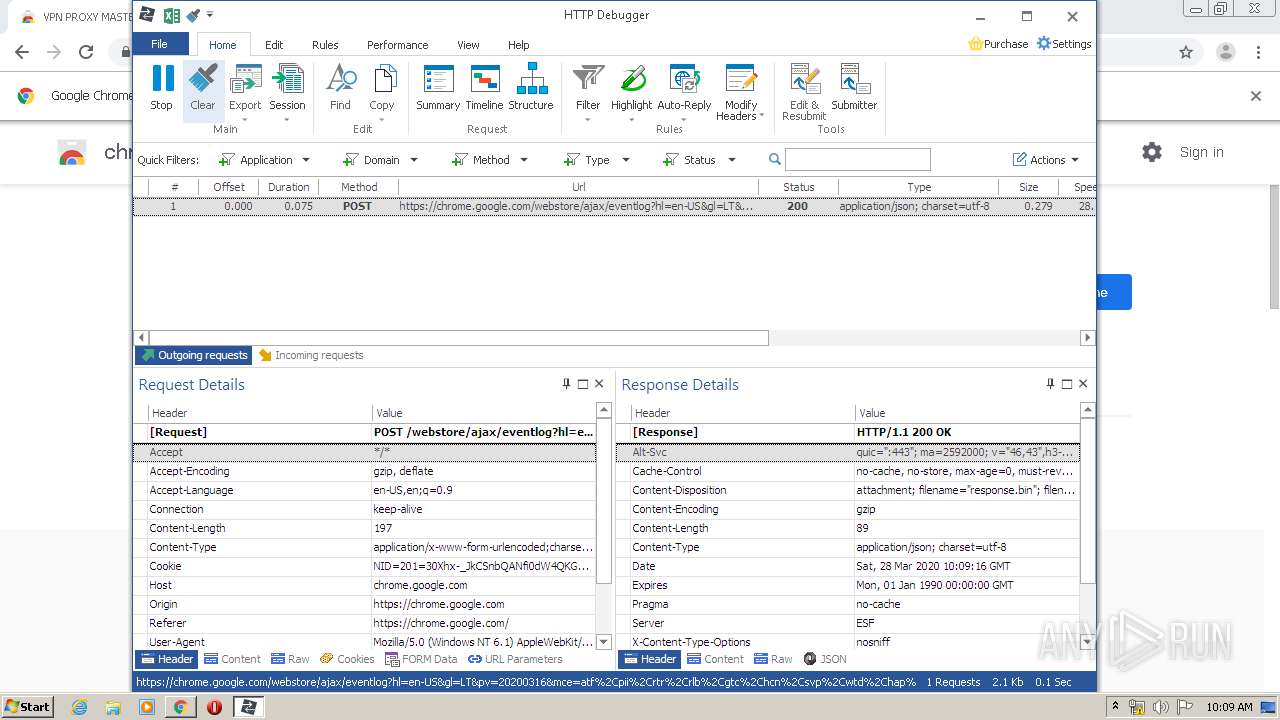
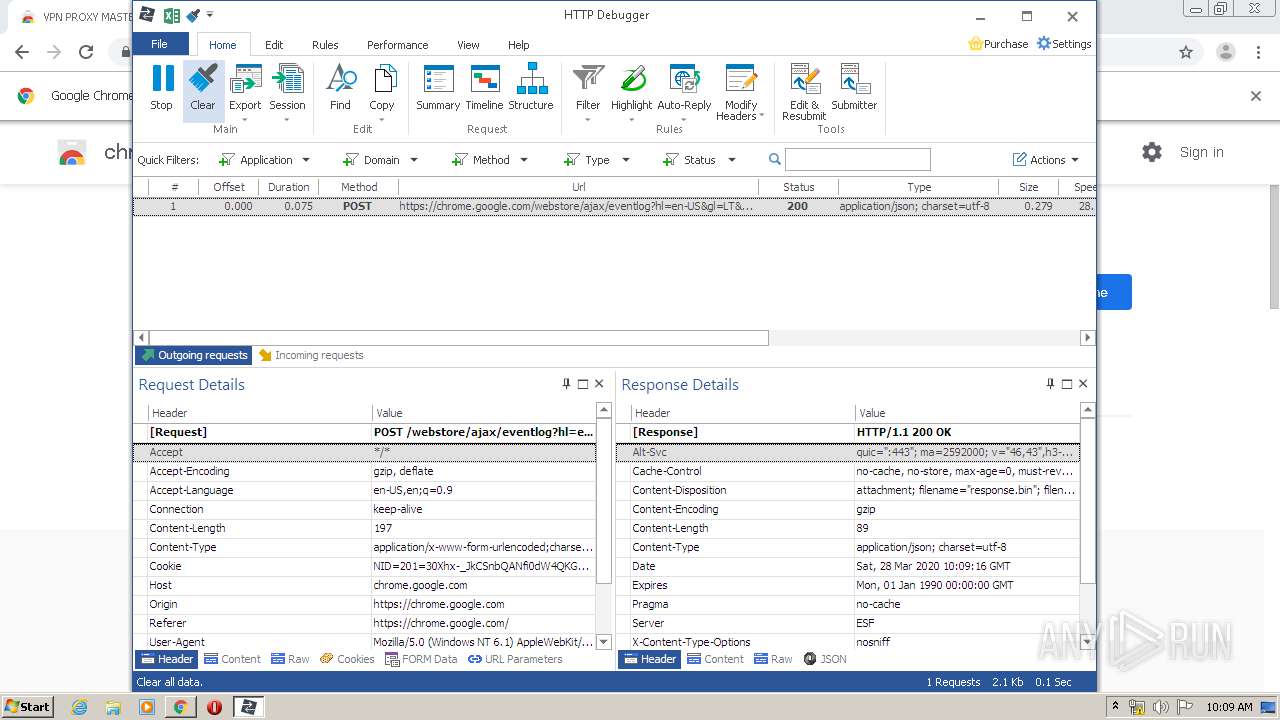
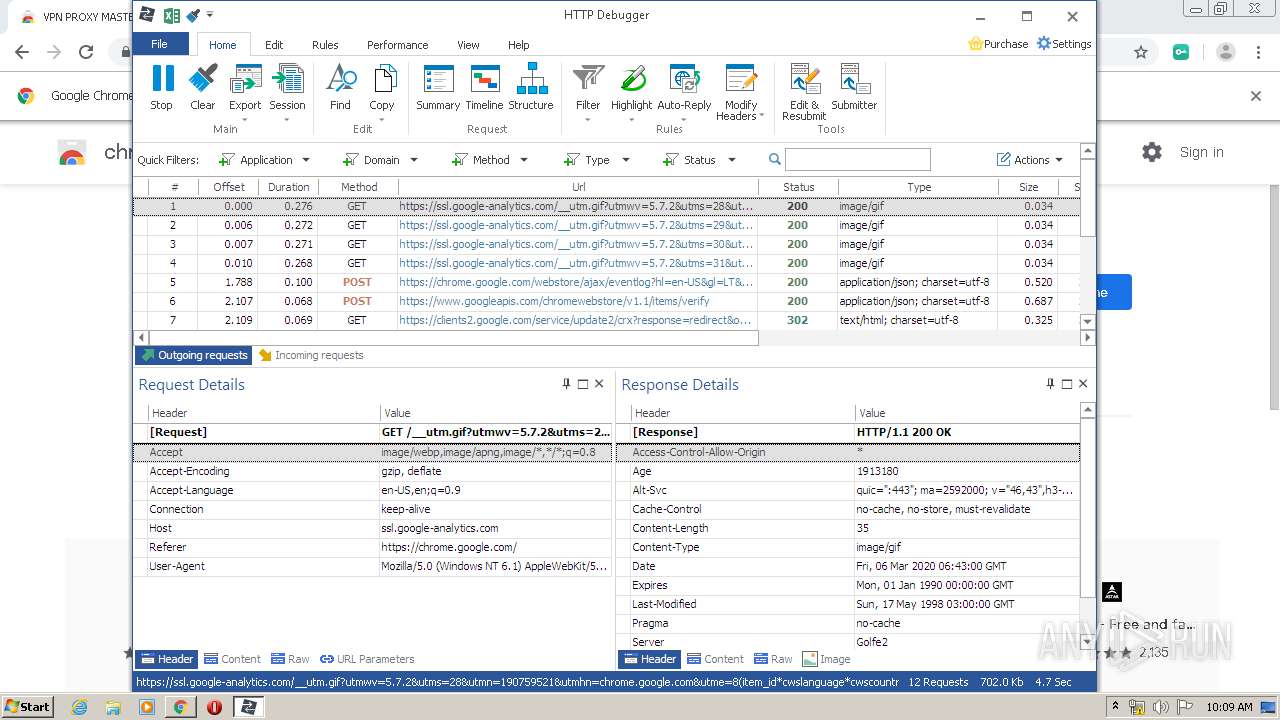
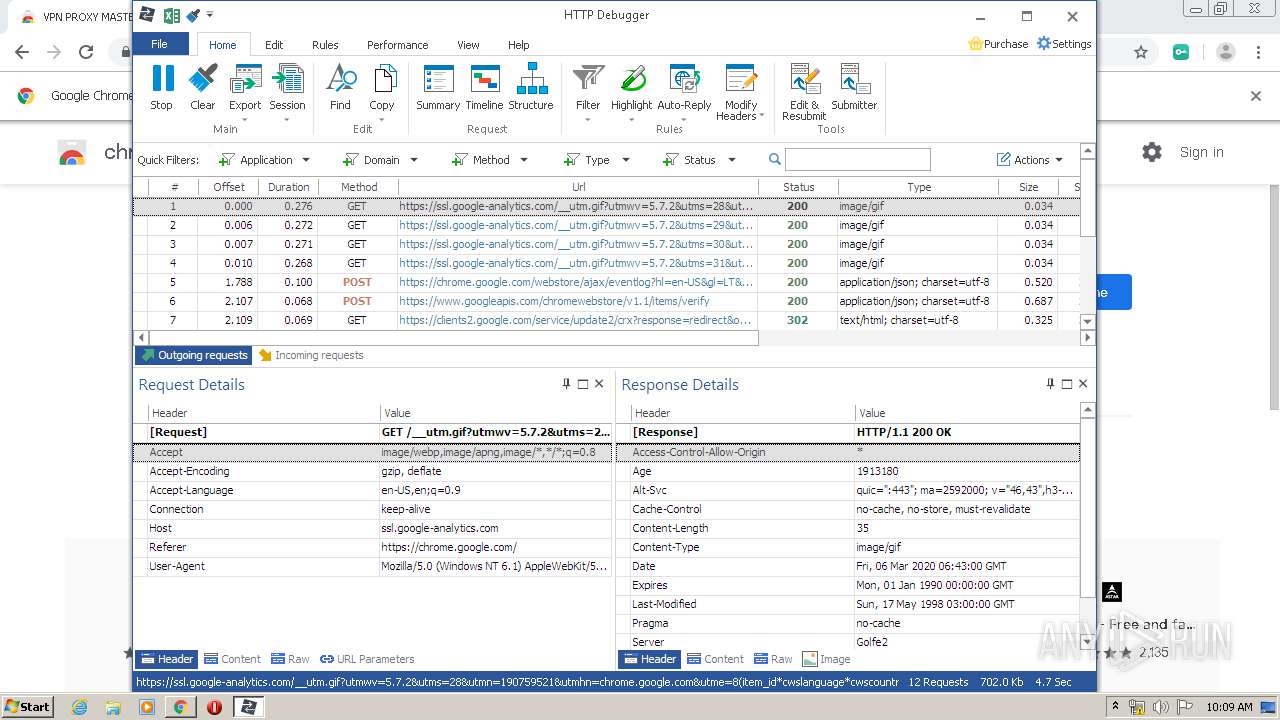
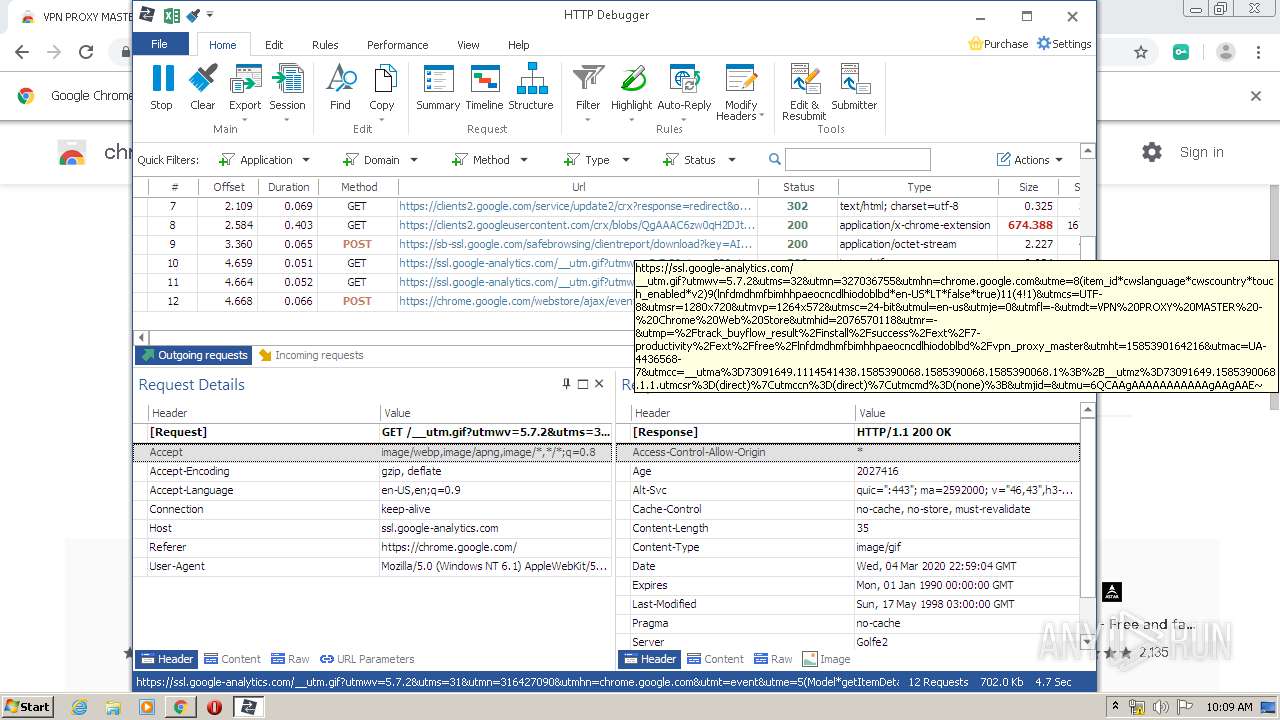
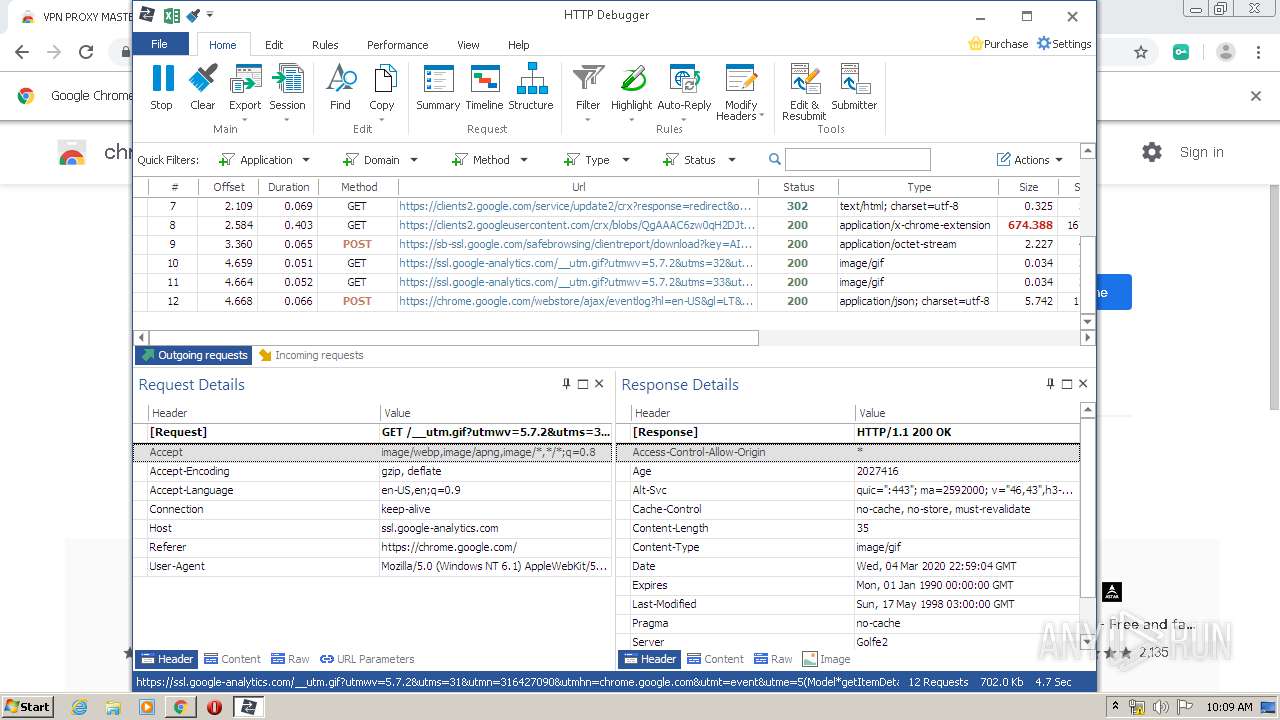
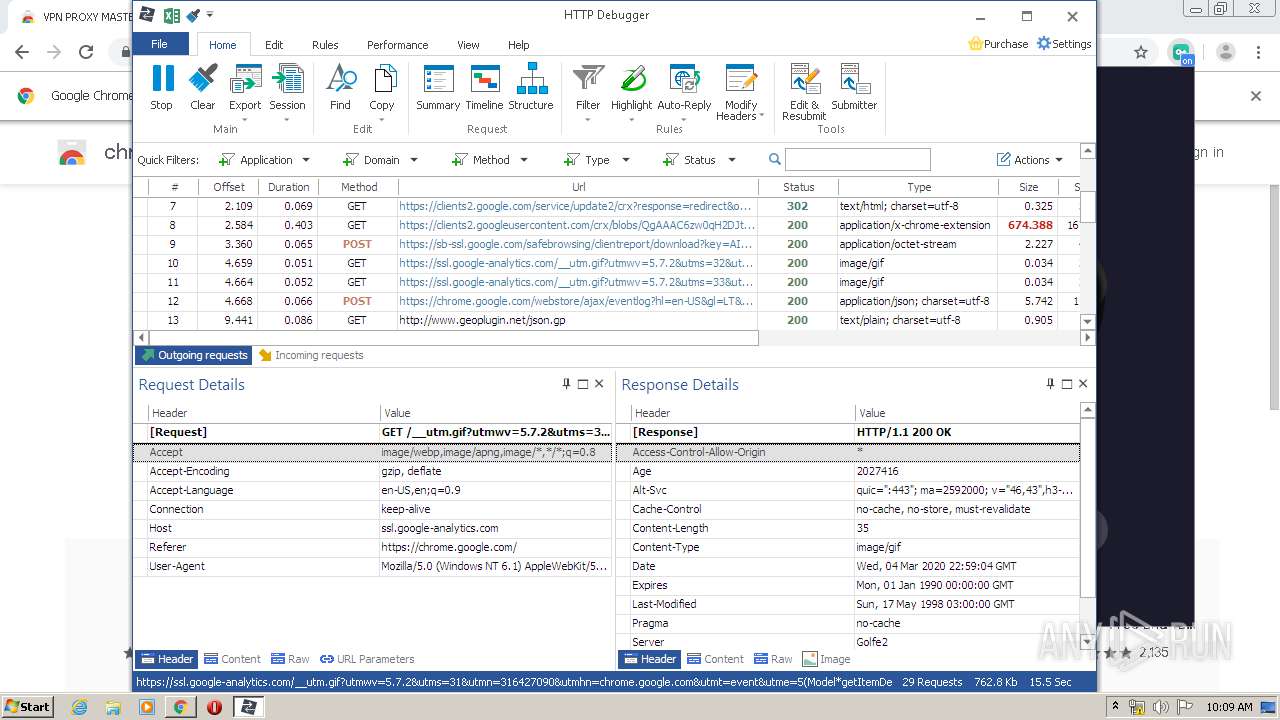
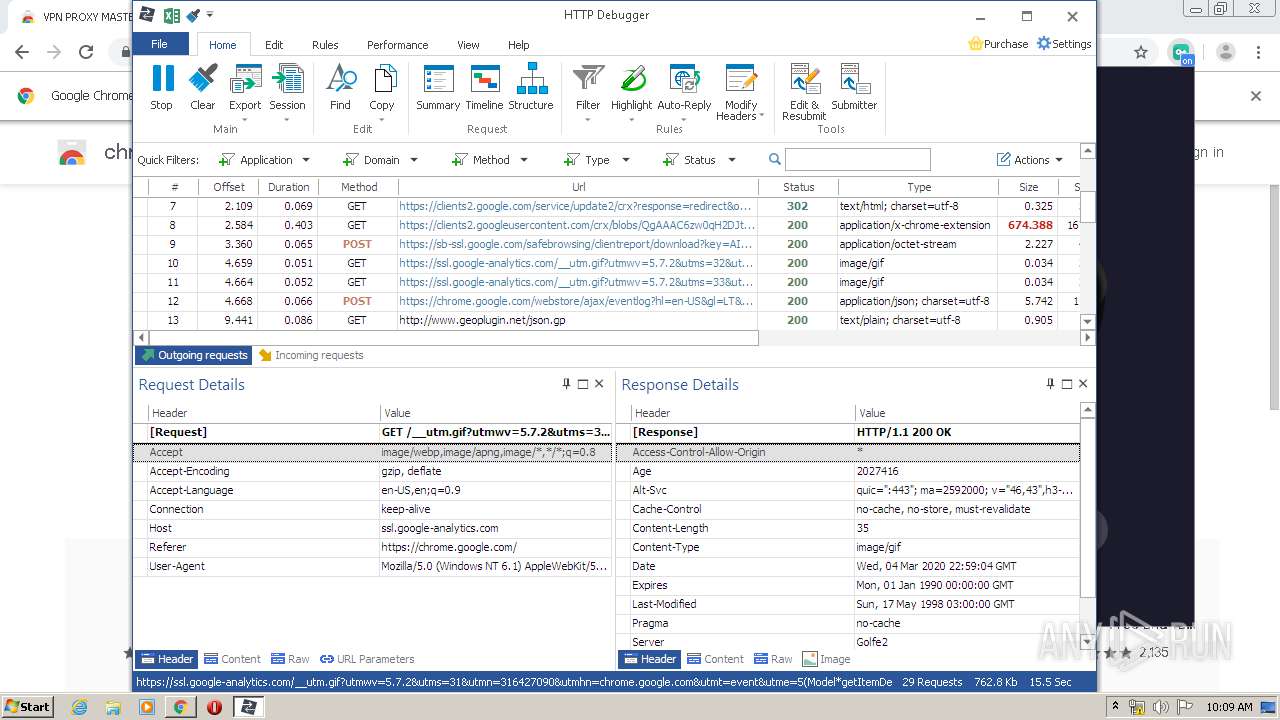
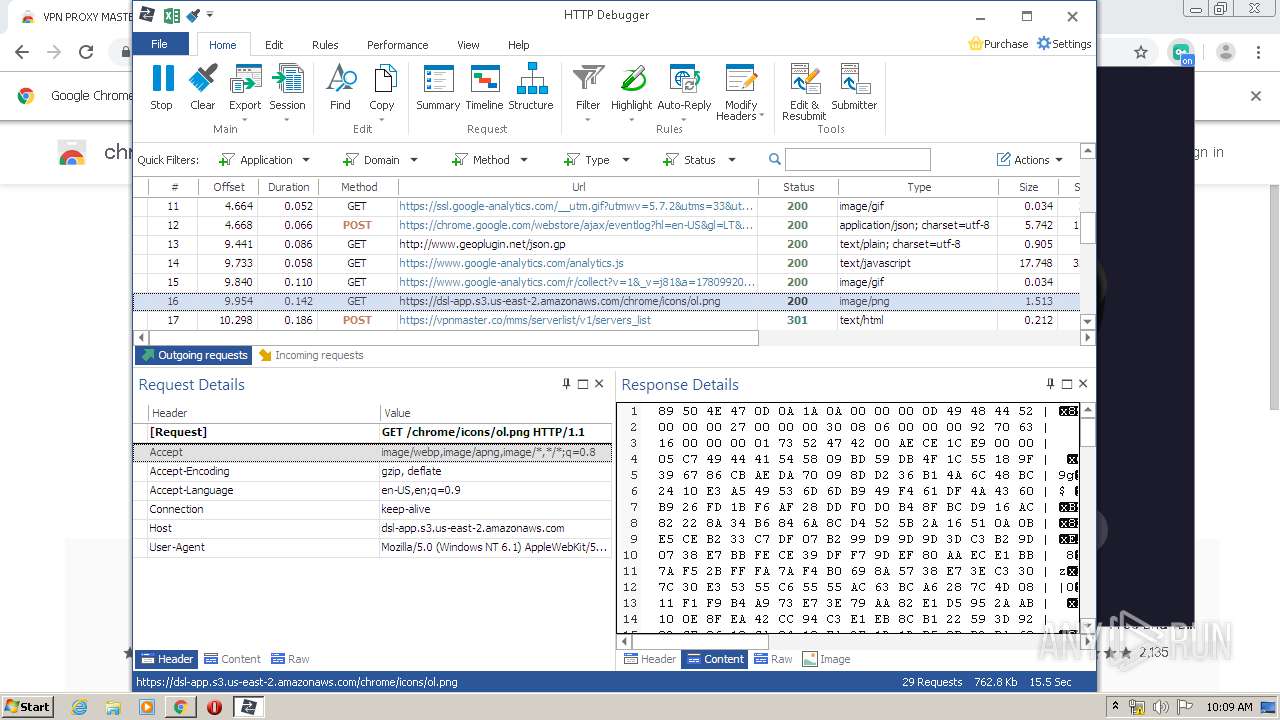
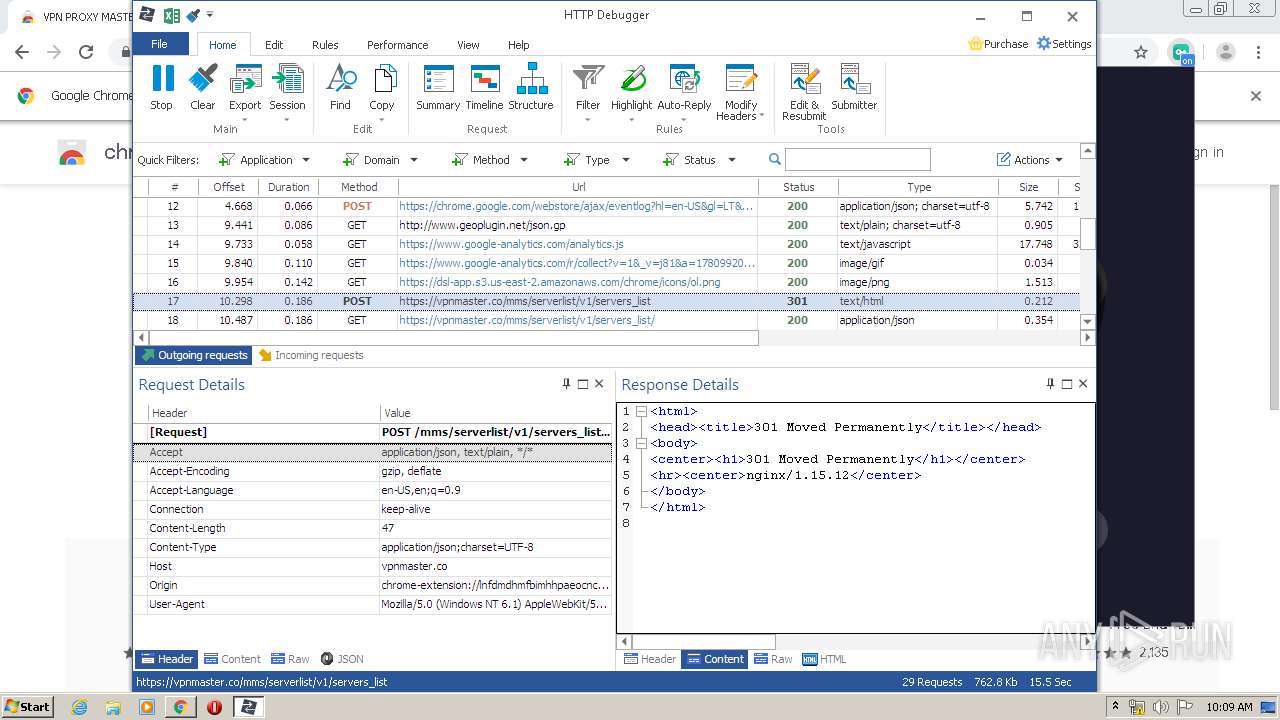
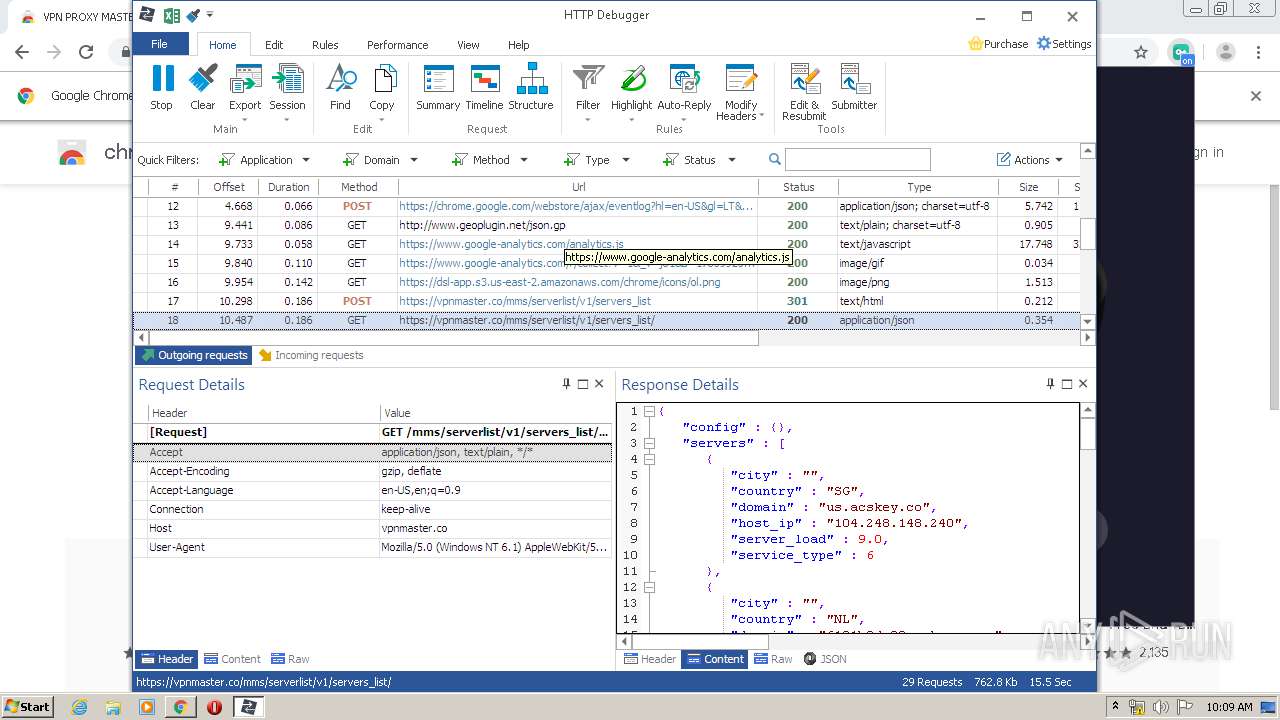
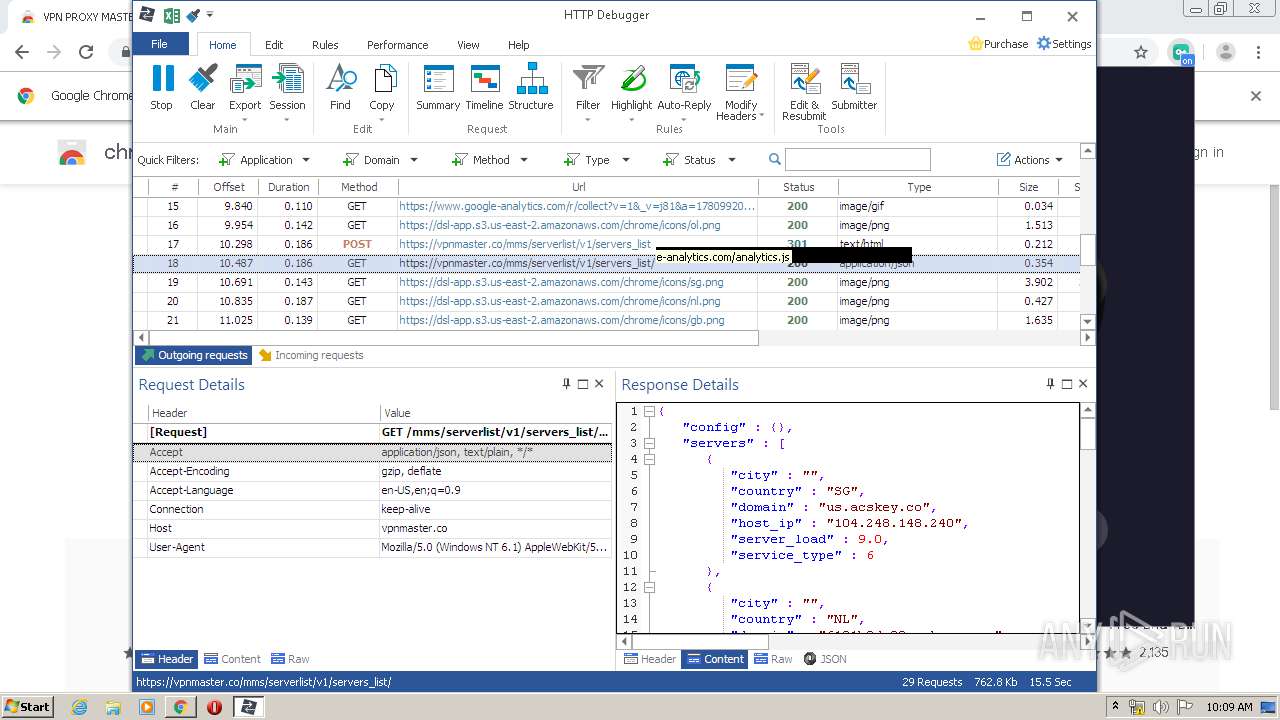
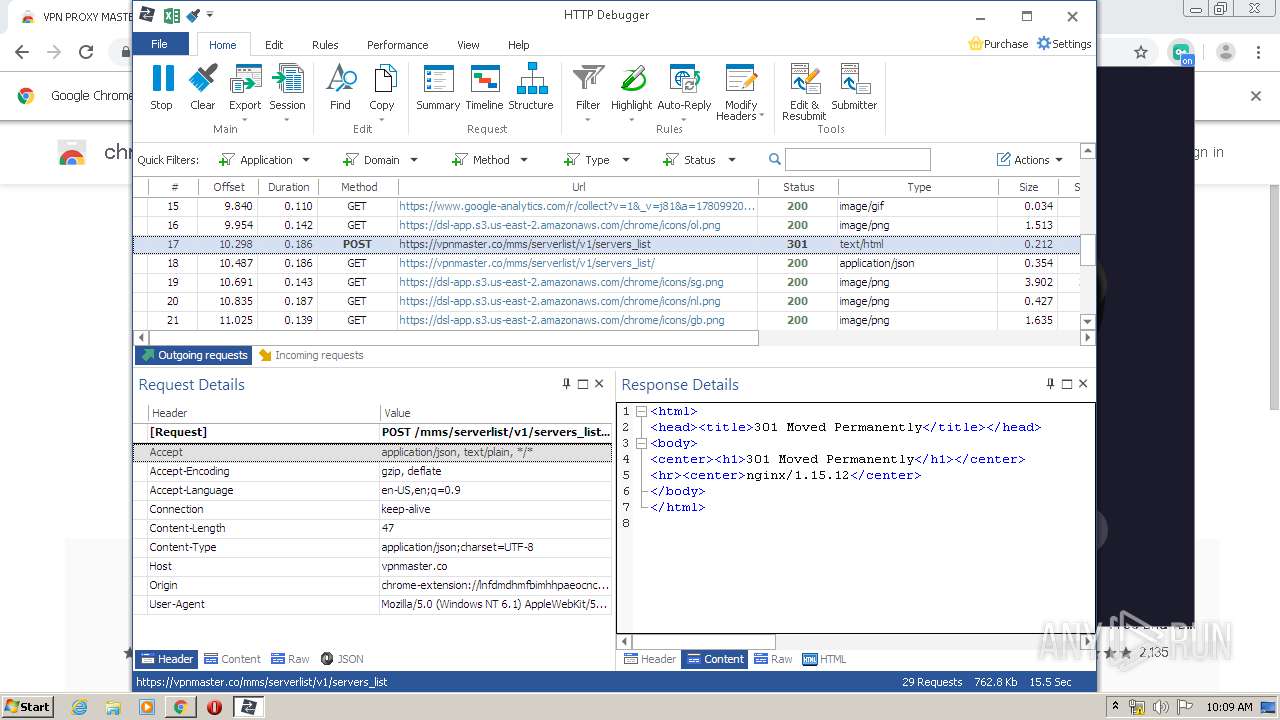
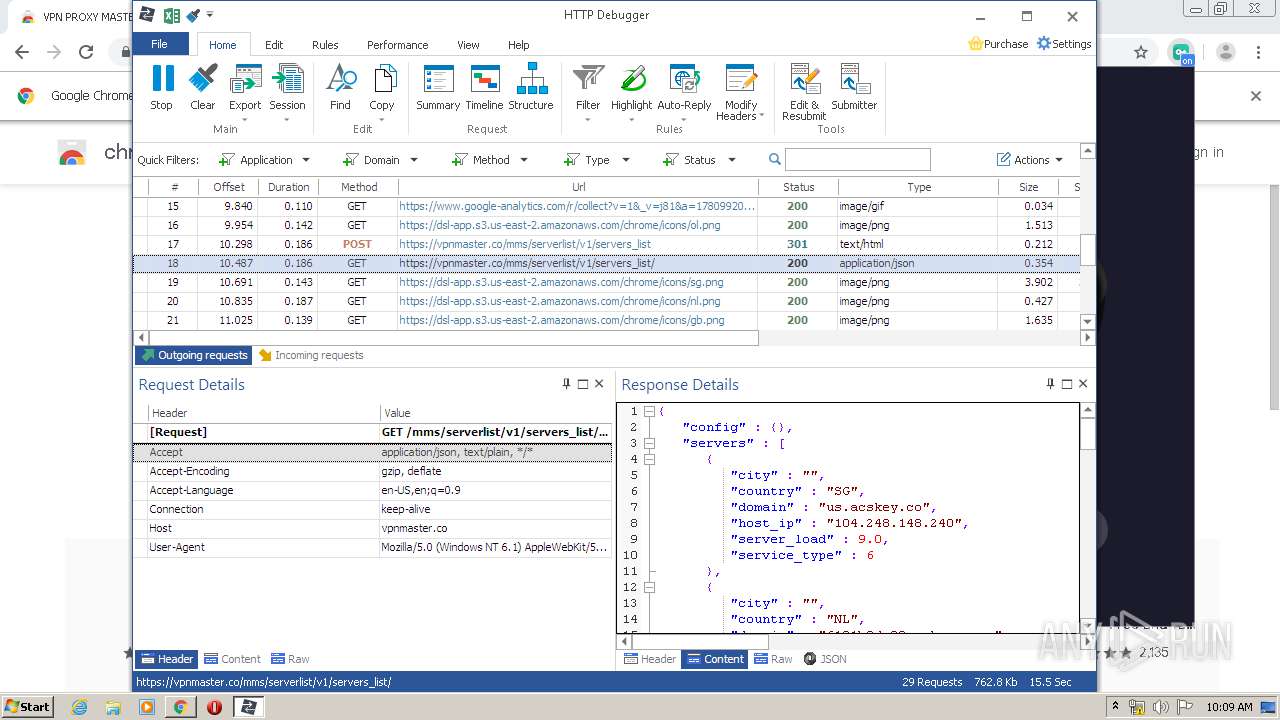
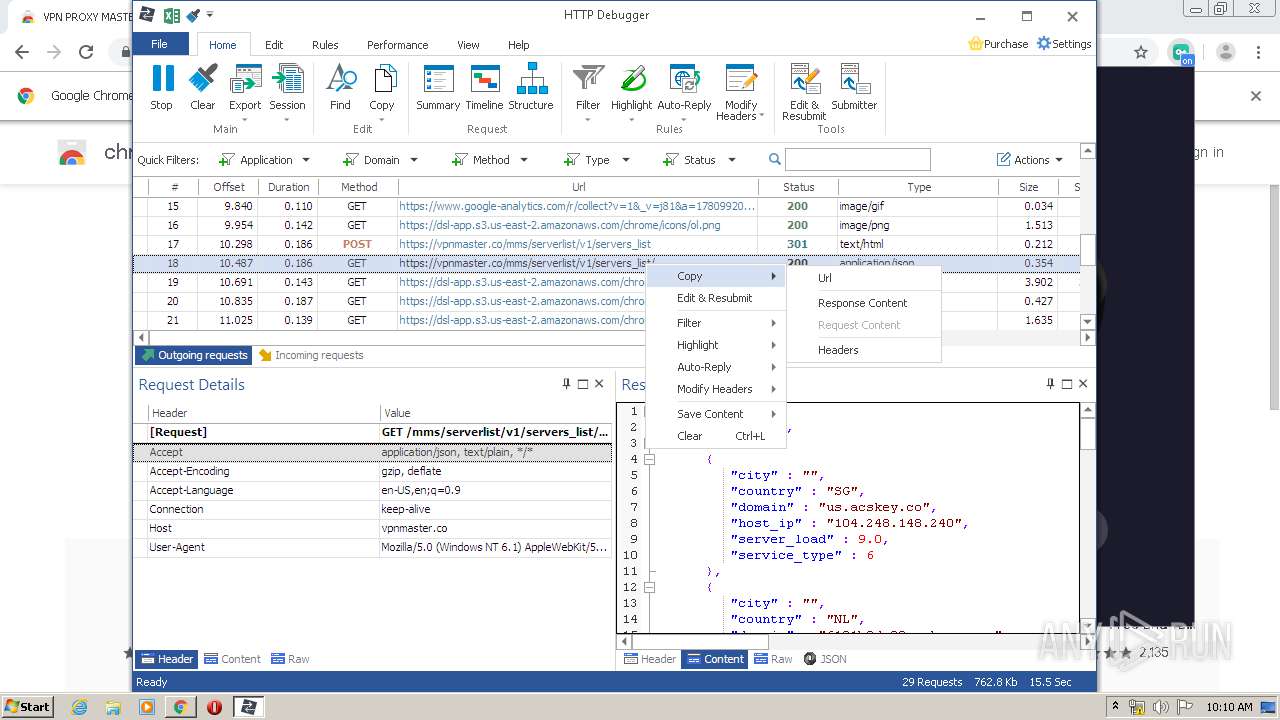
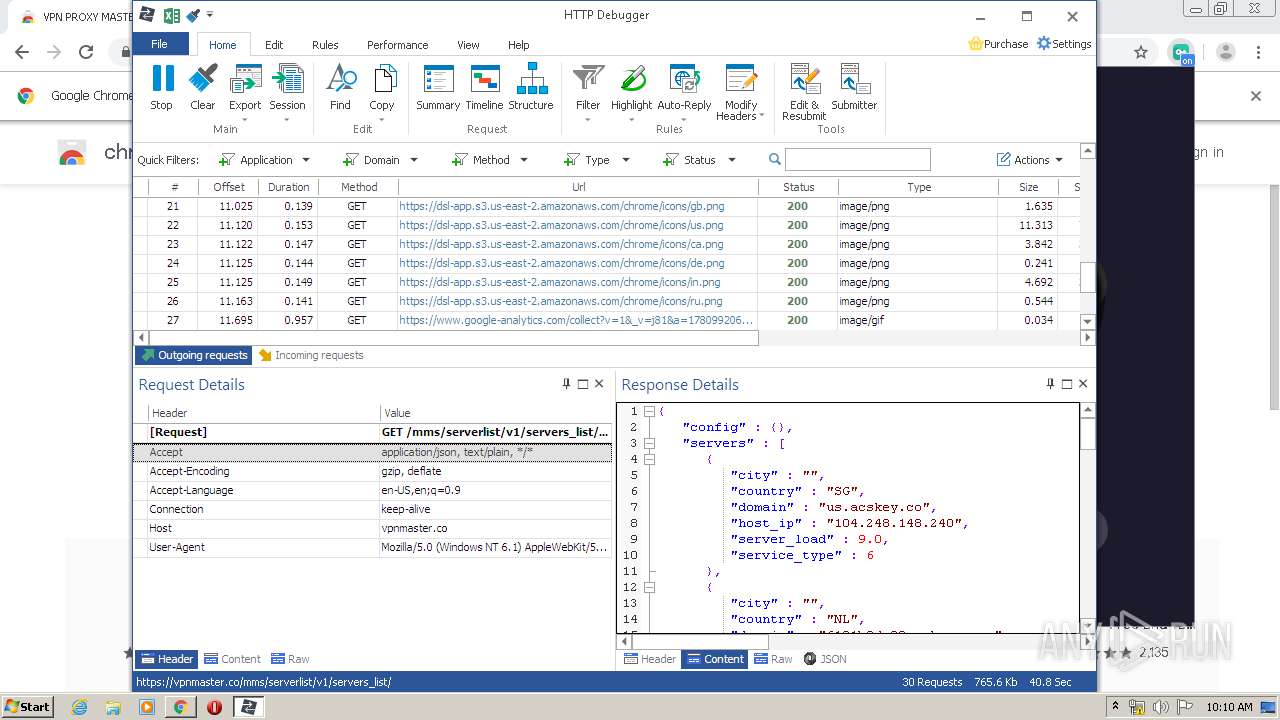
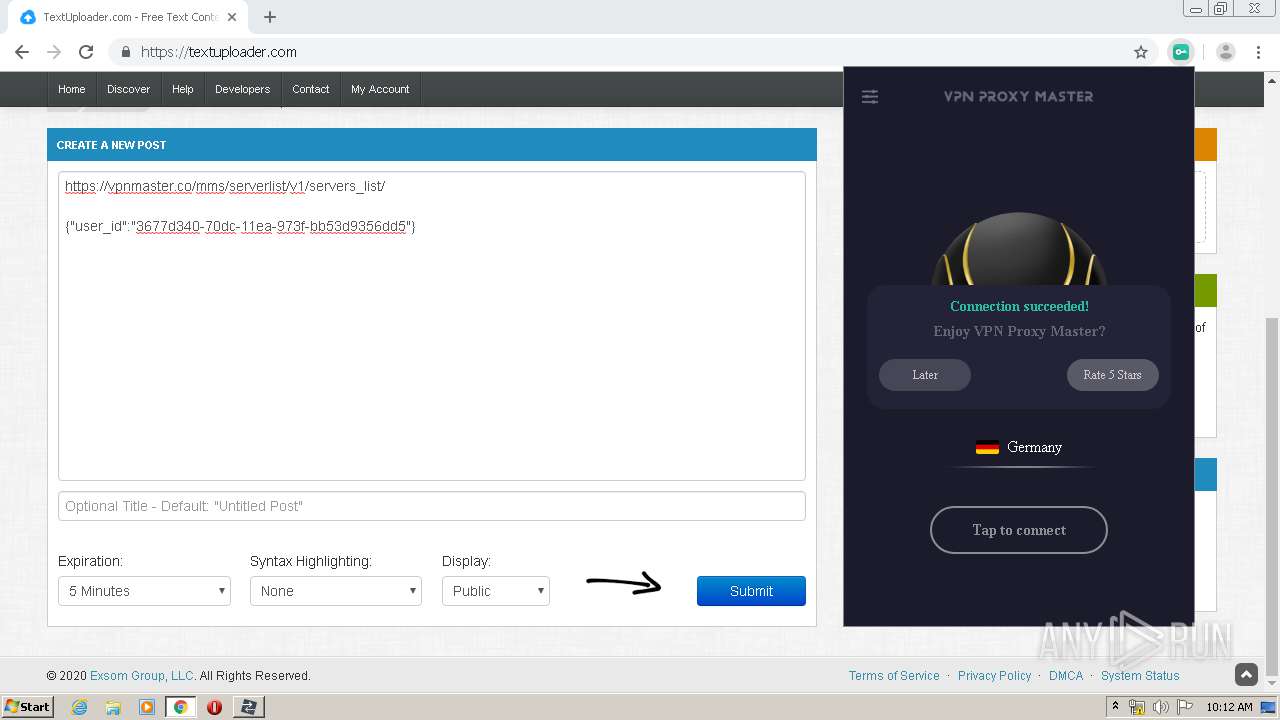
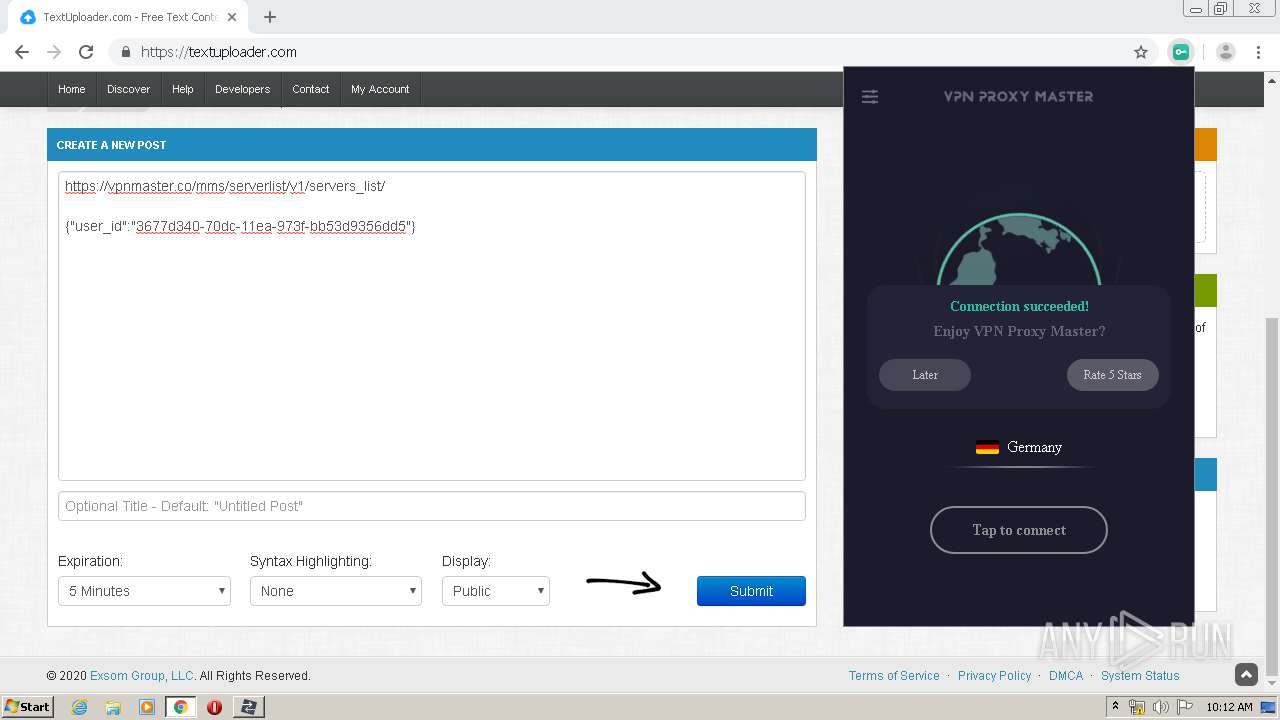
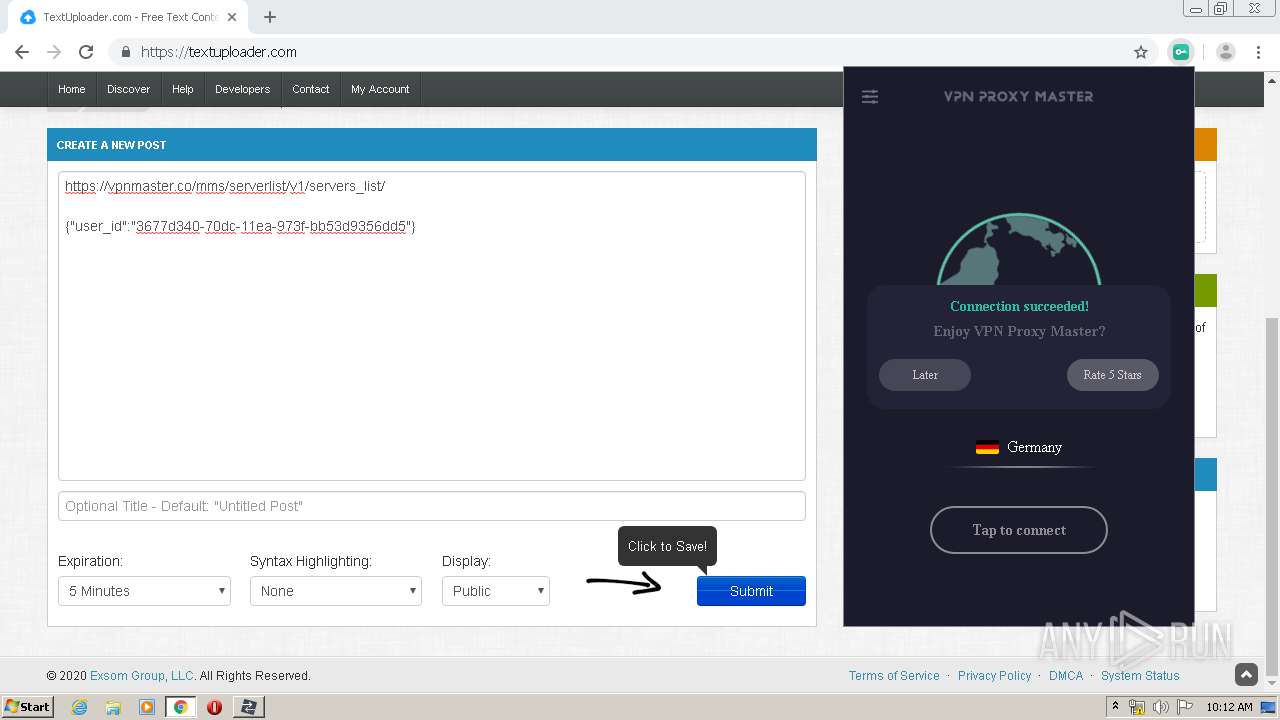
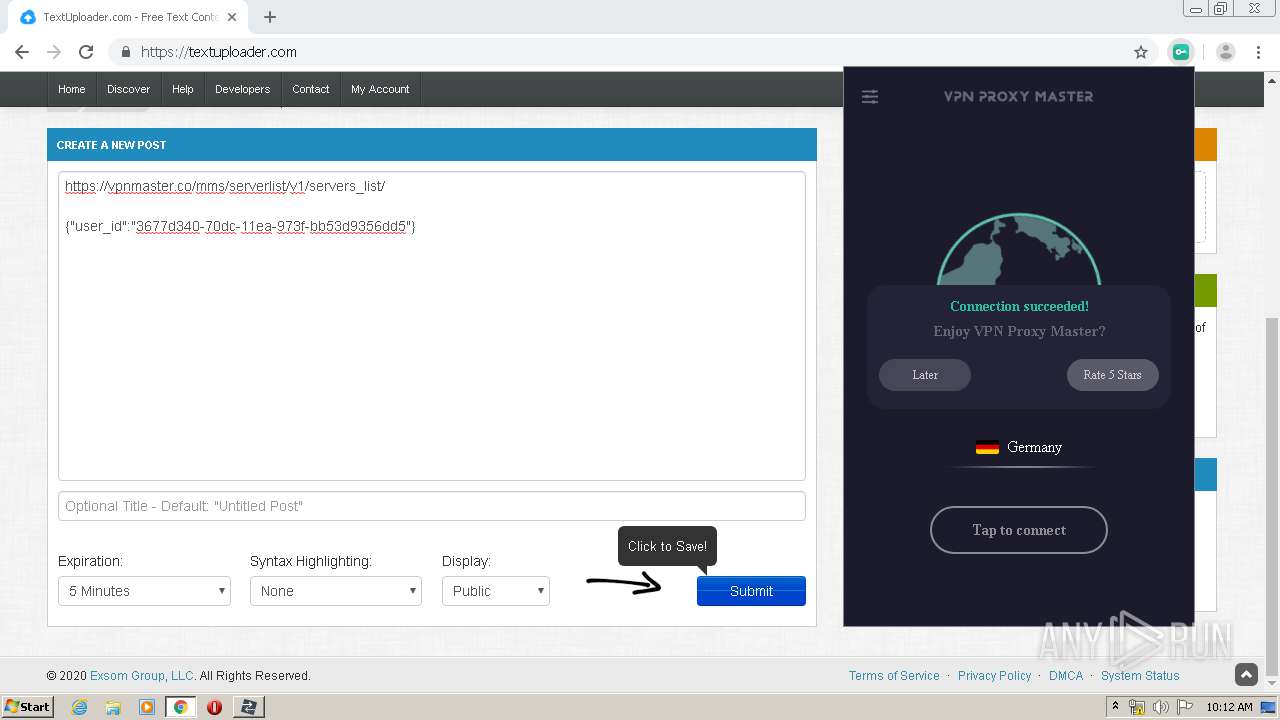
HTTP(S) requests
13
TCP/UDP connections
157
DNS requests
50
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
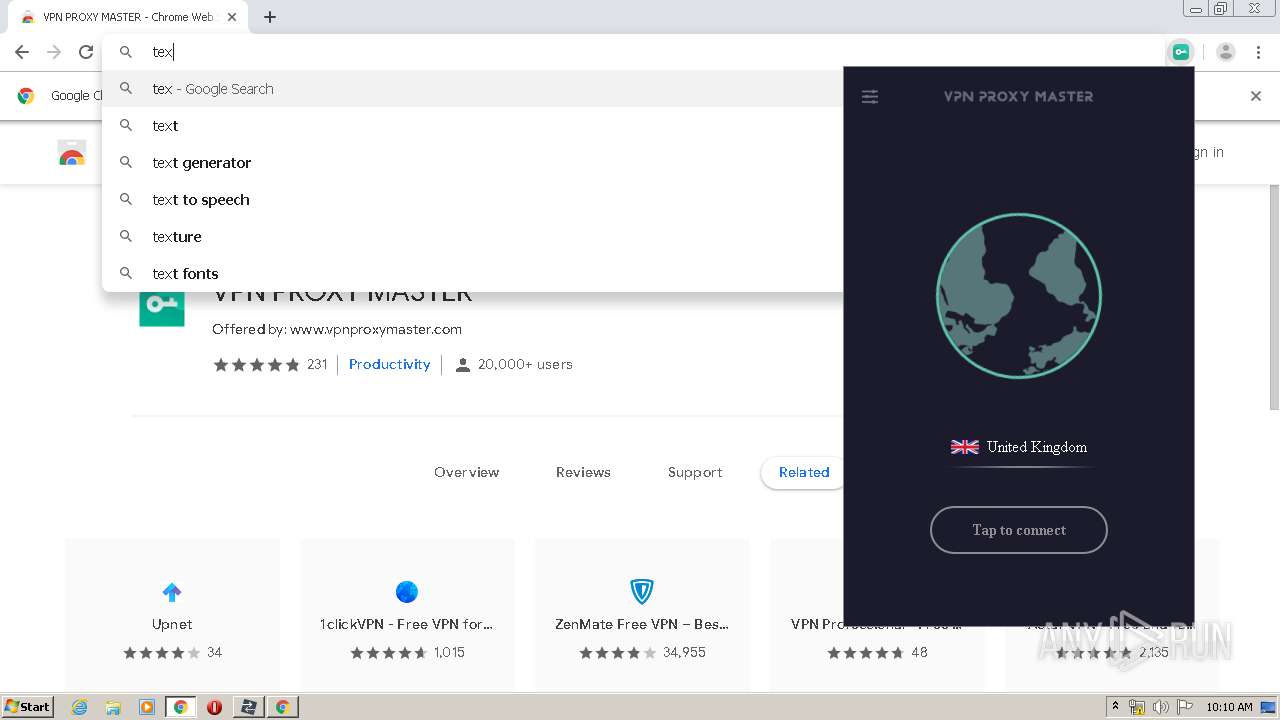
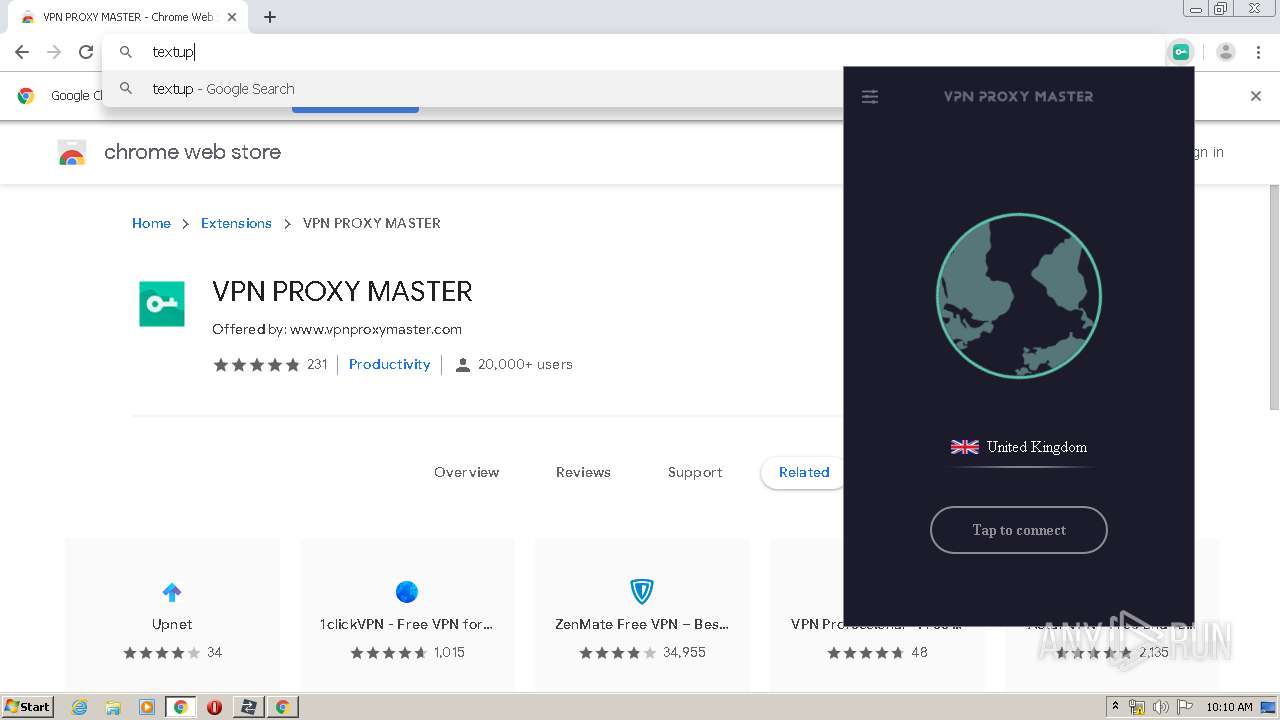
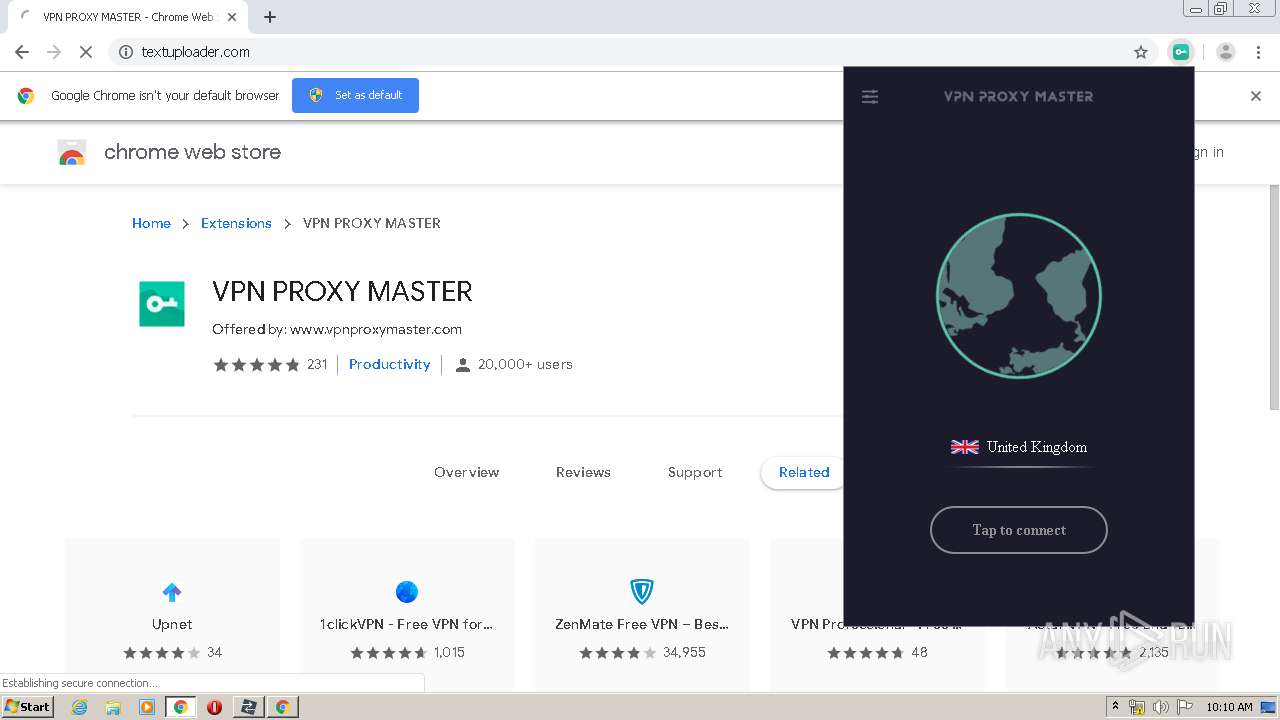
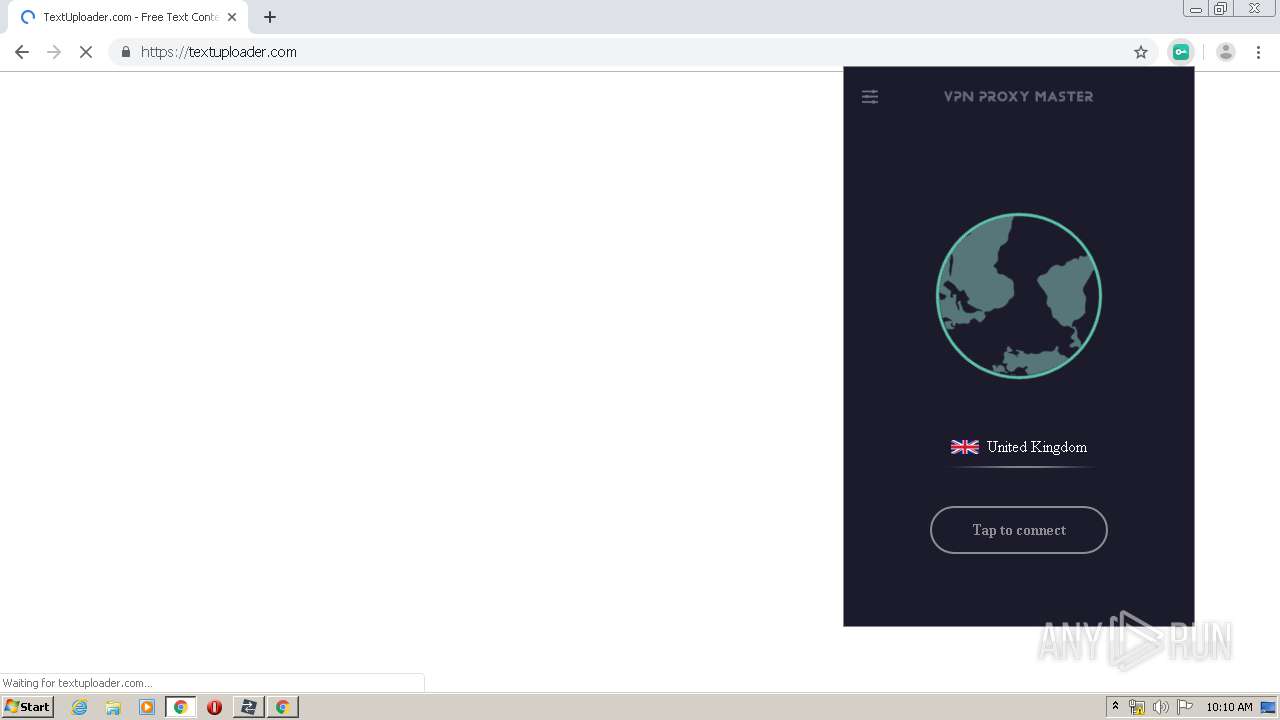
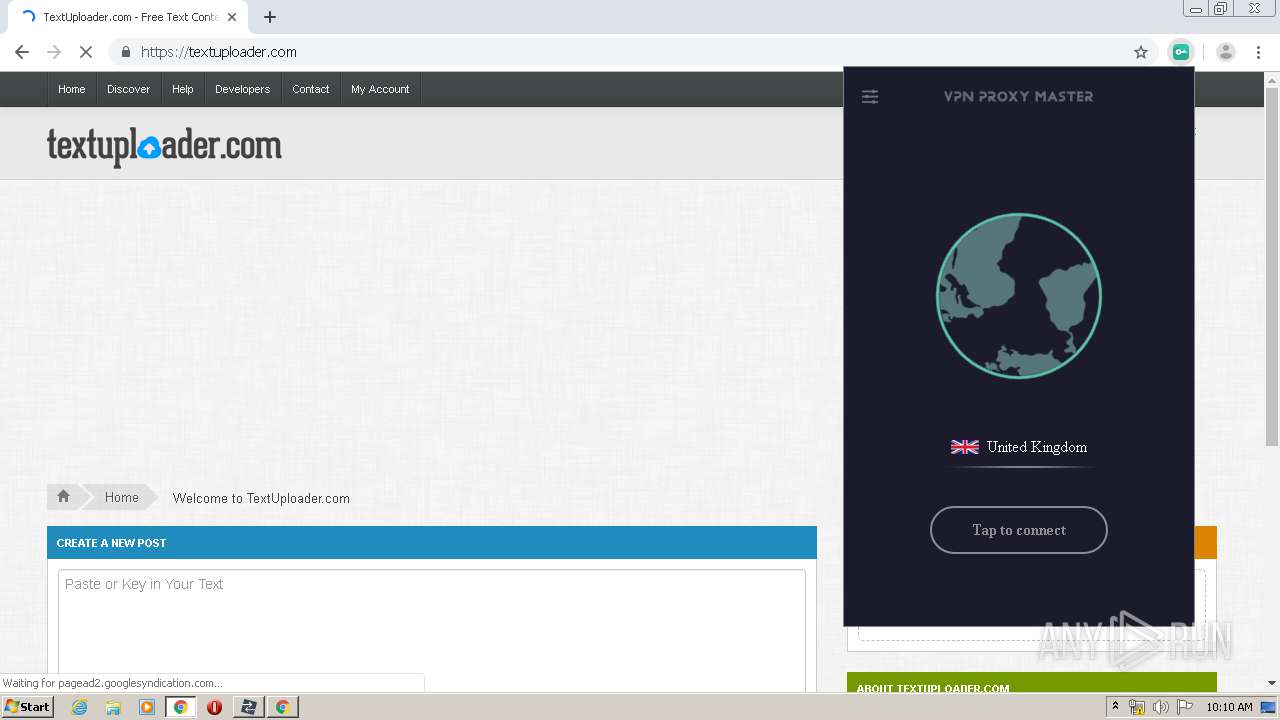
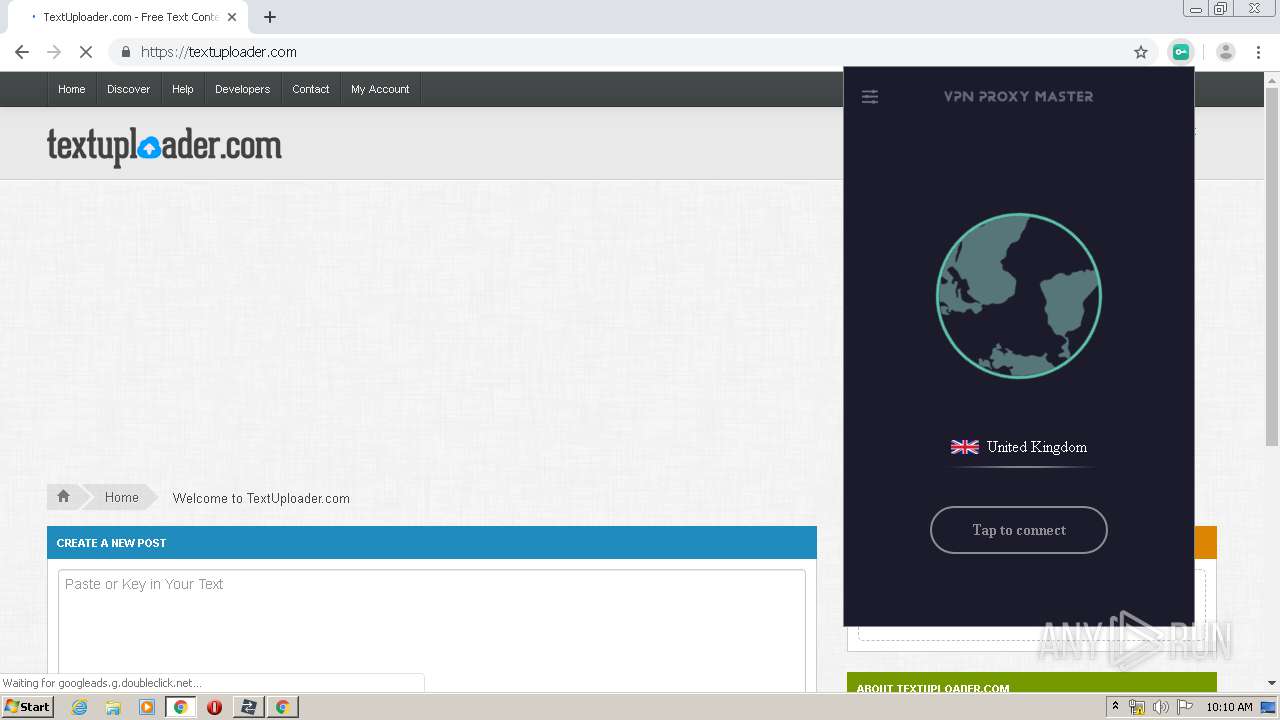
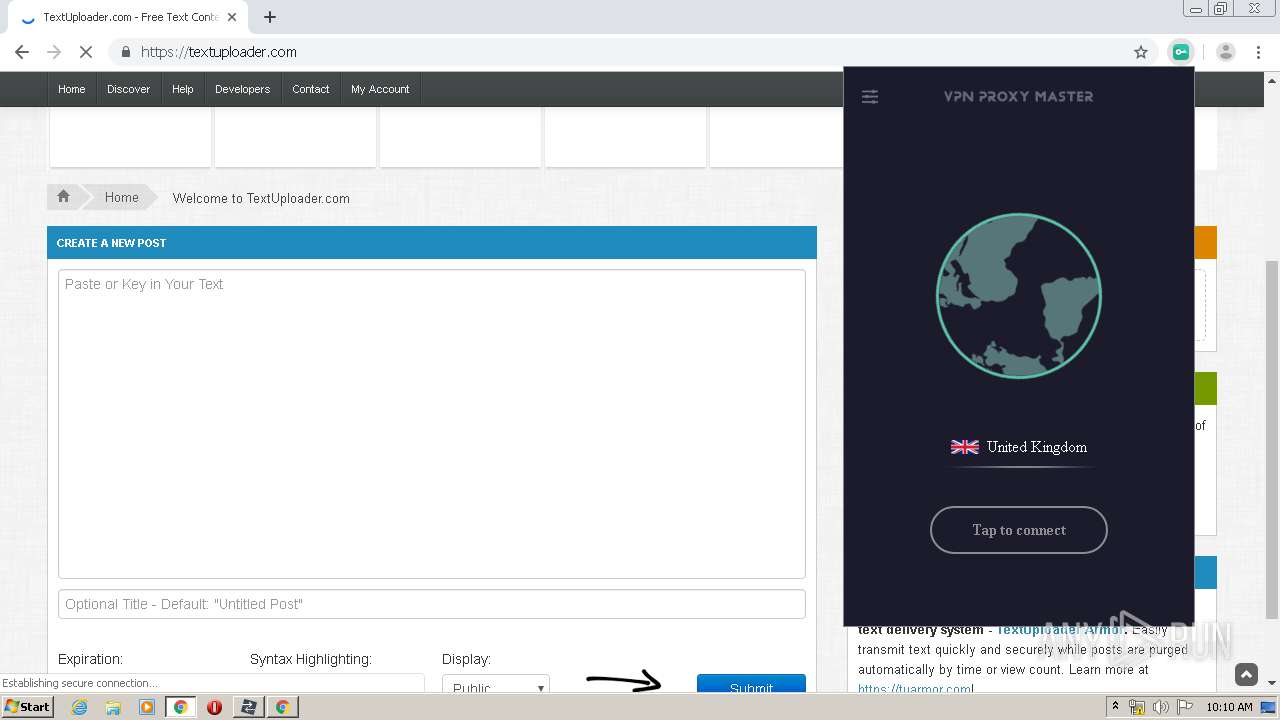
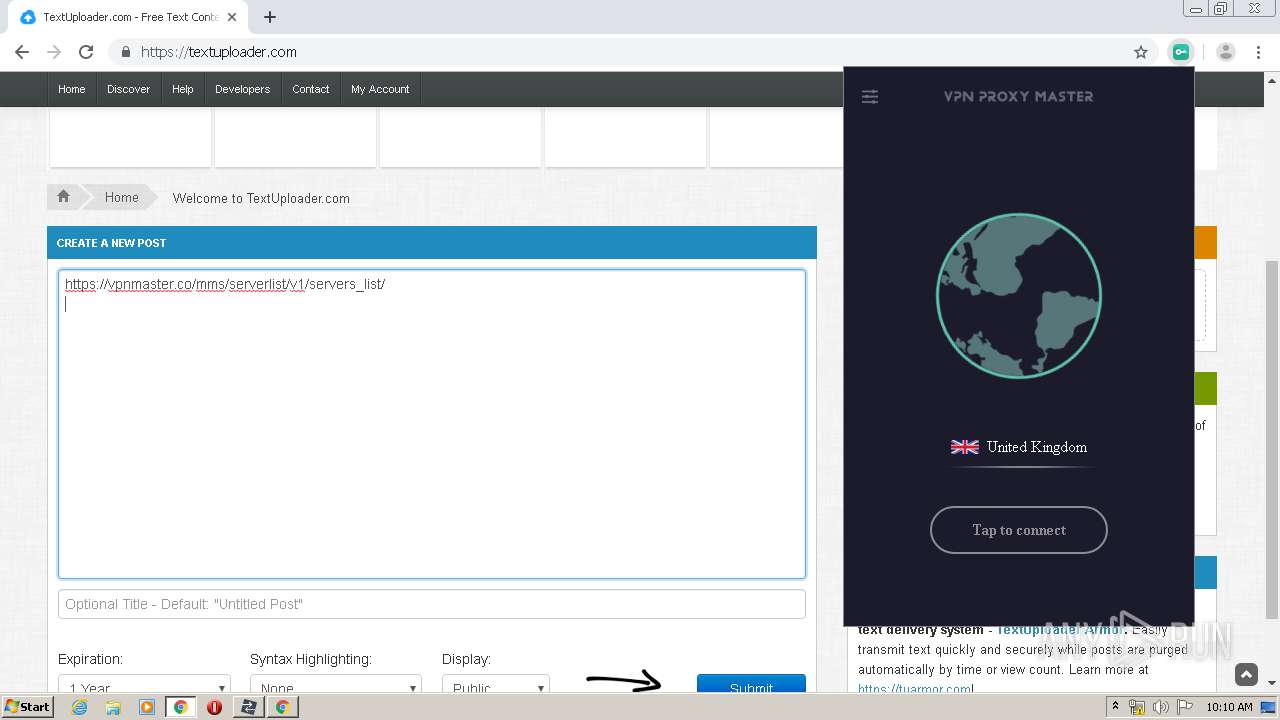
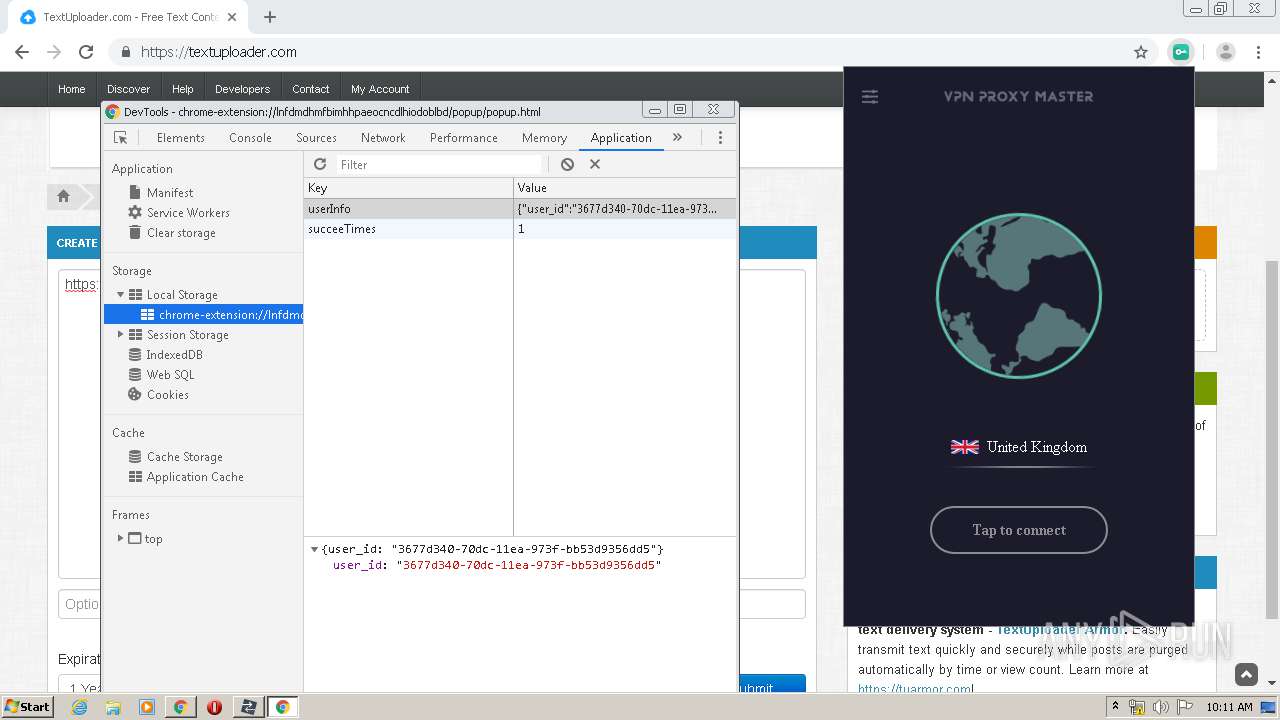
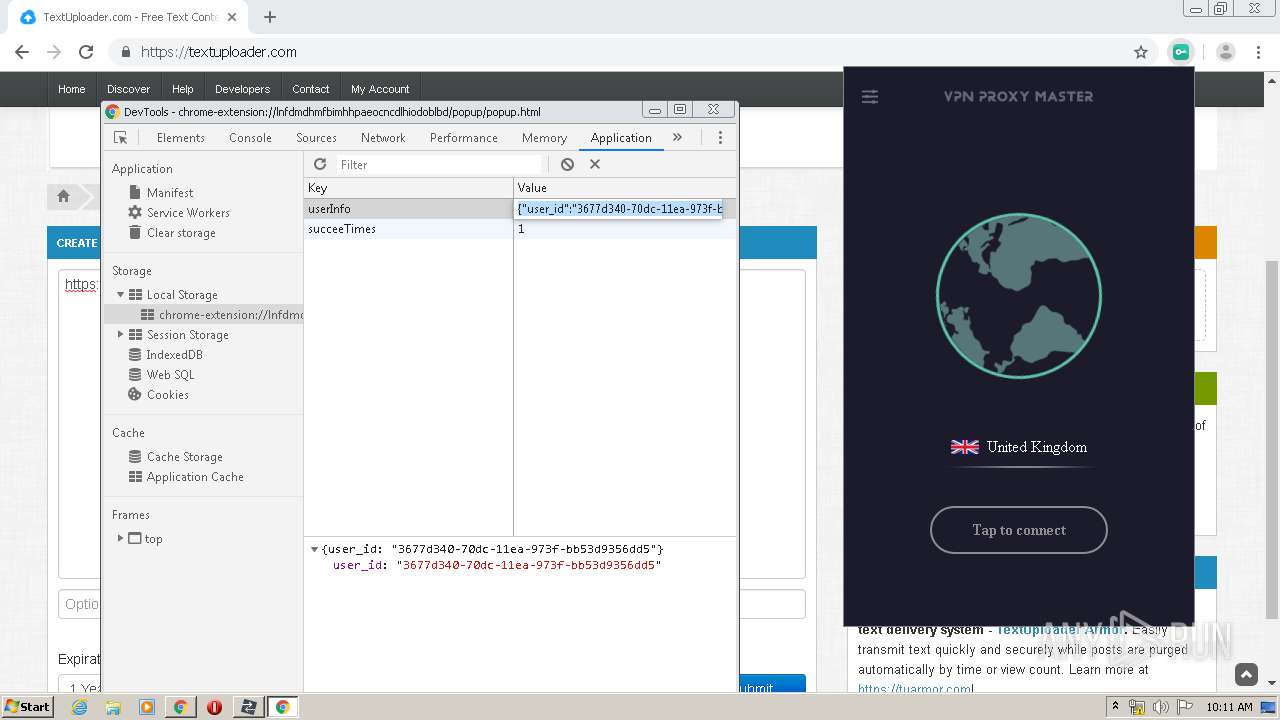
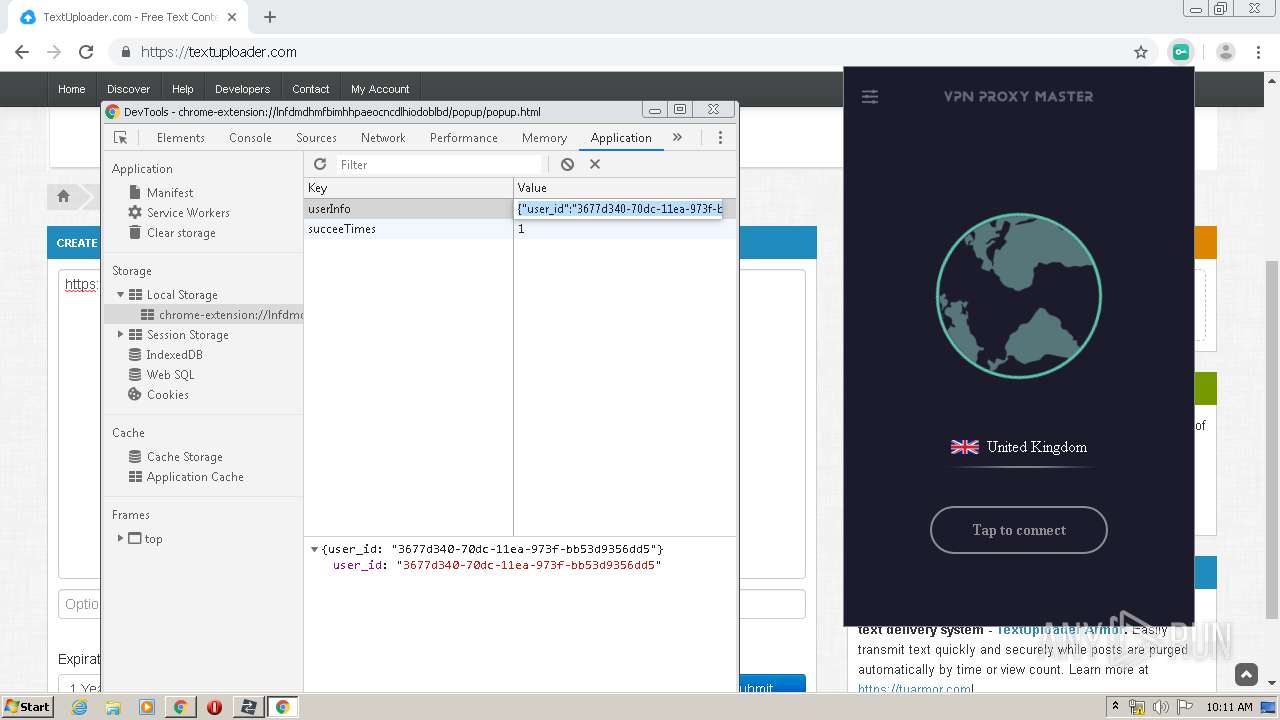
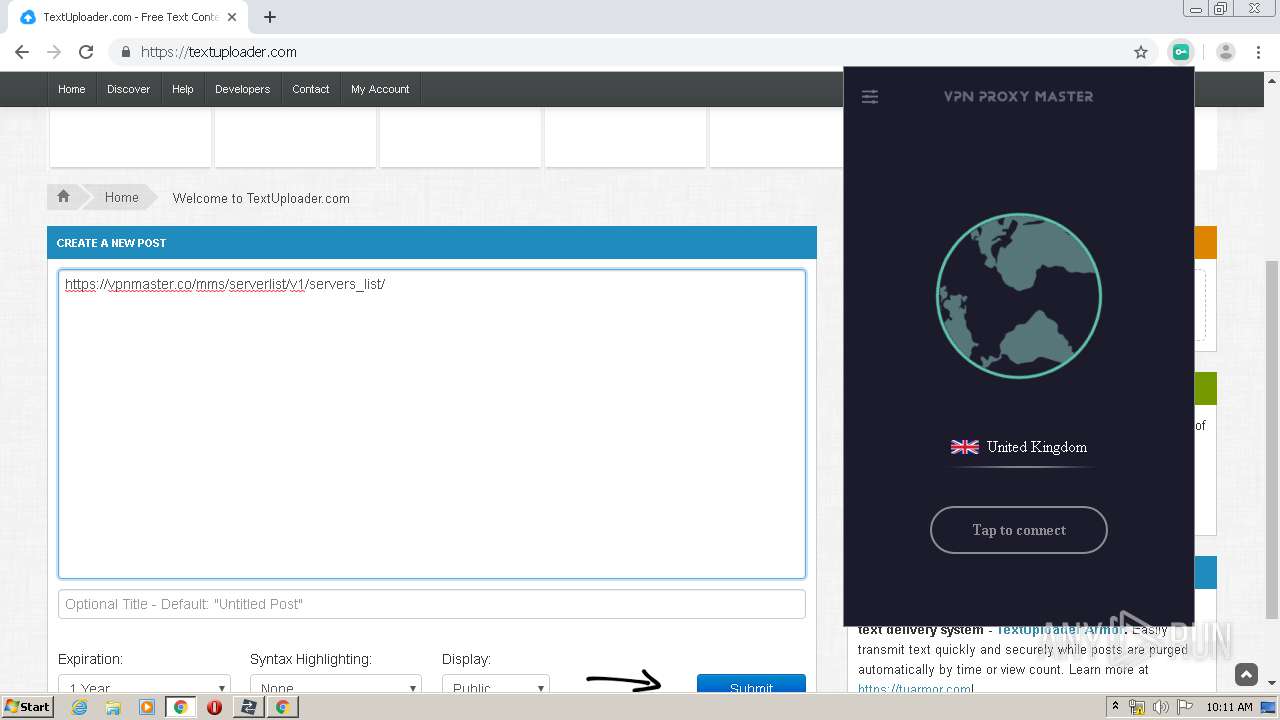
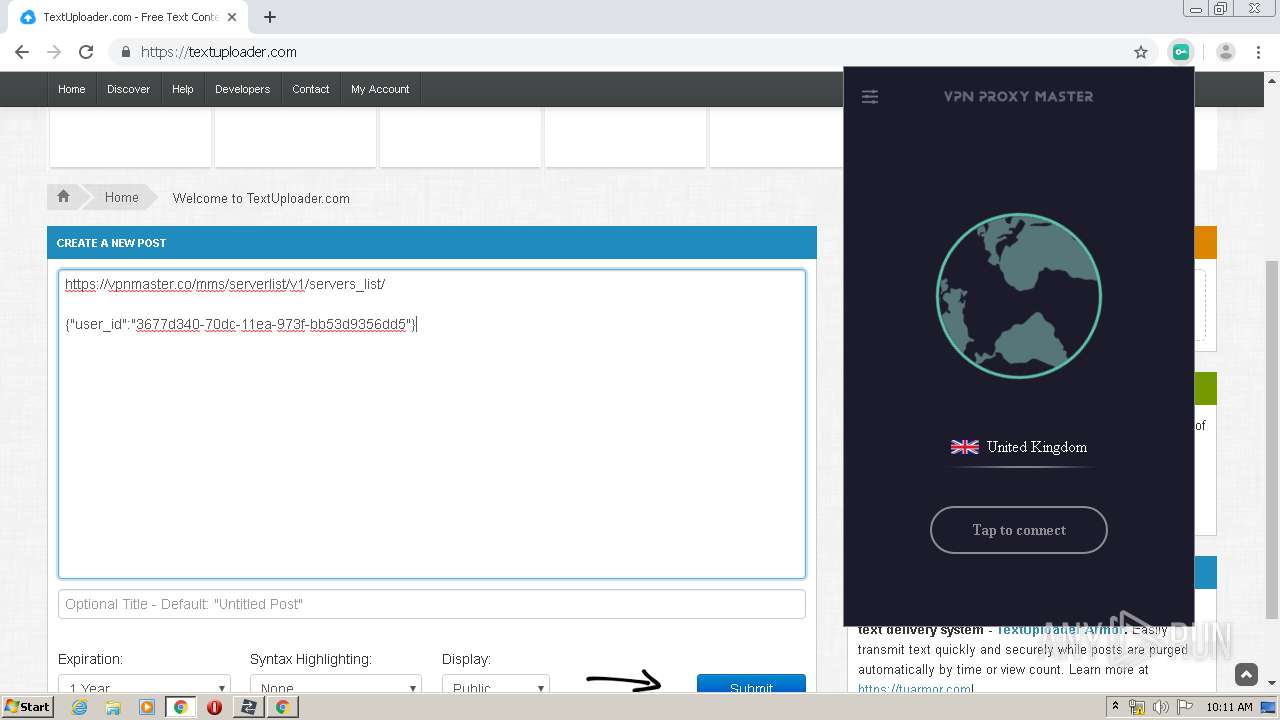
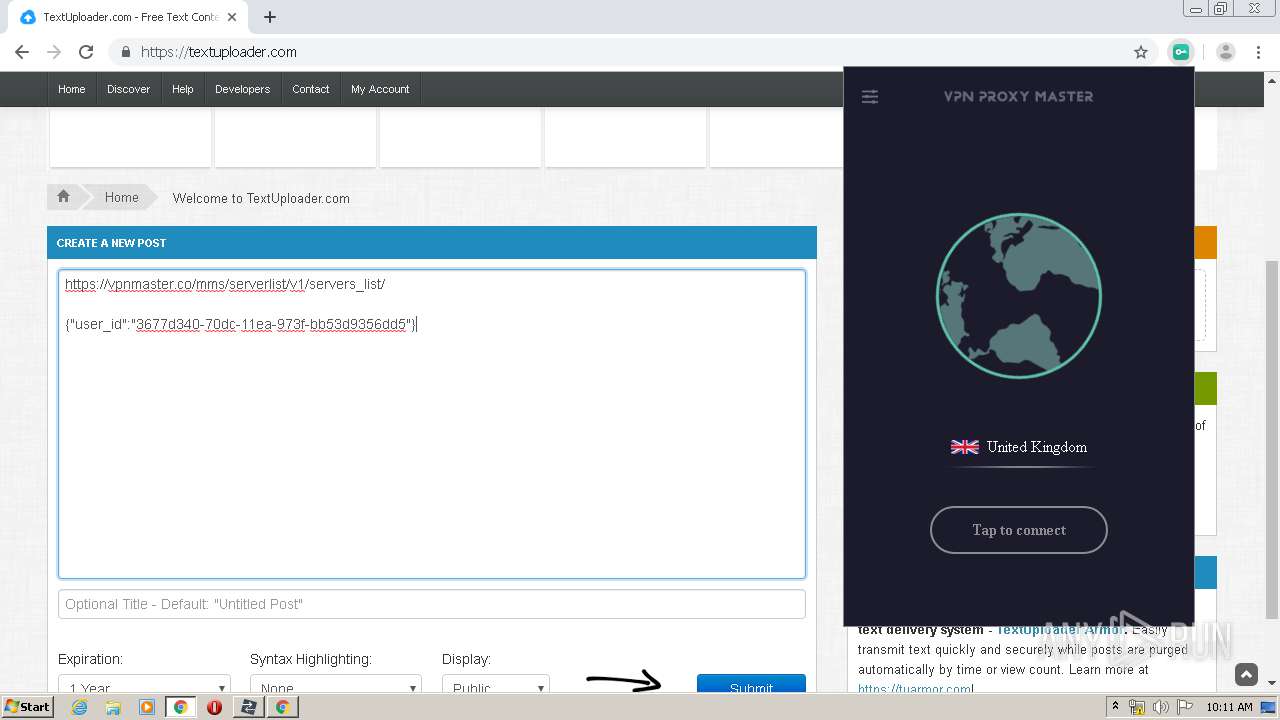
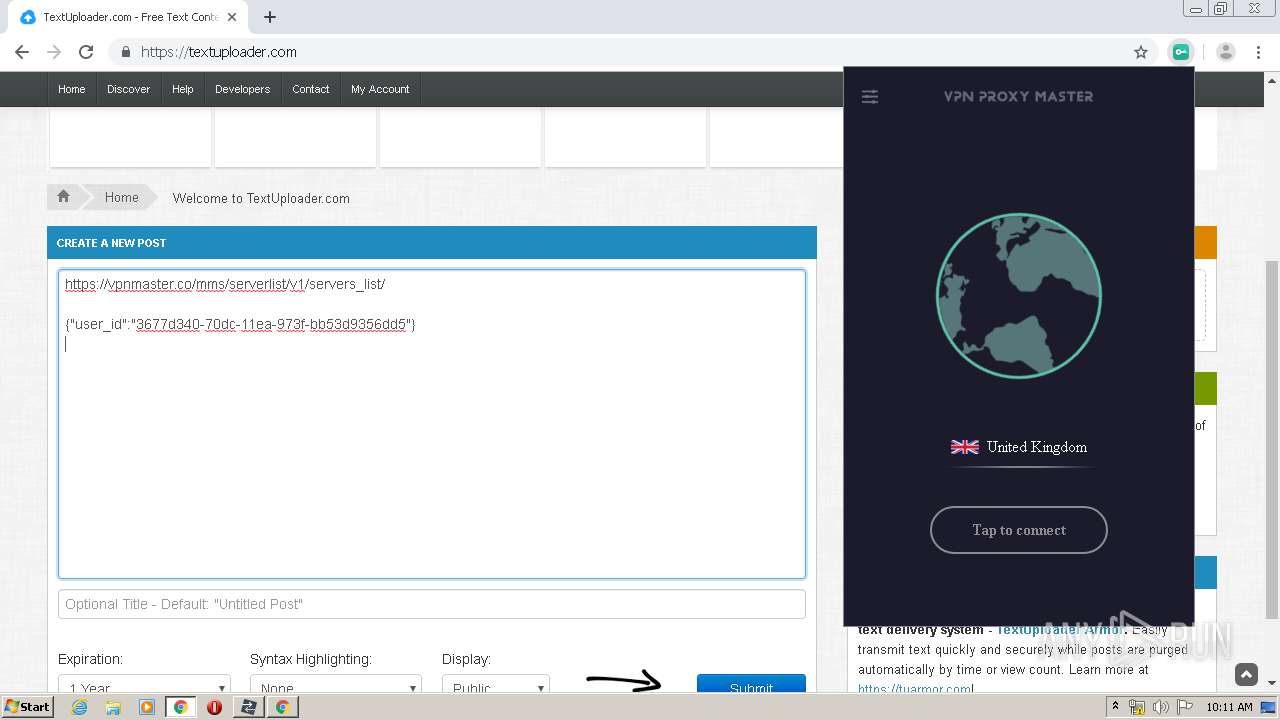
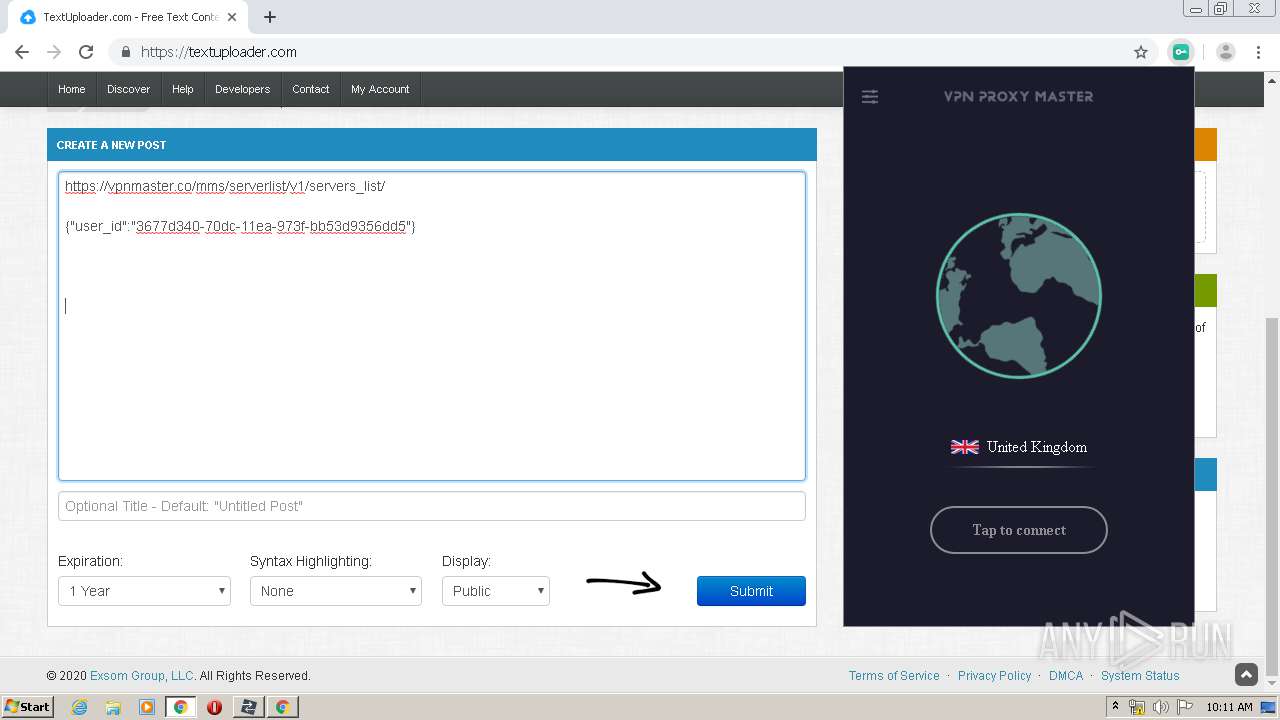
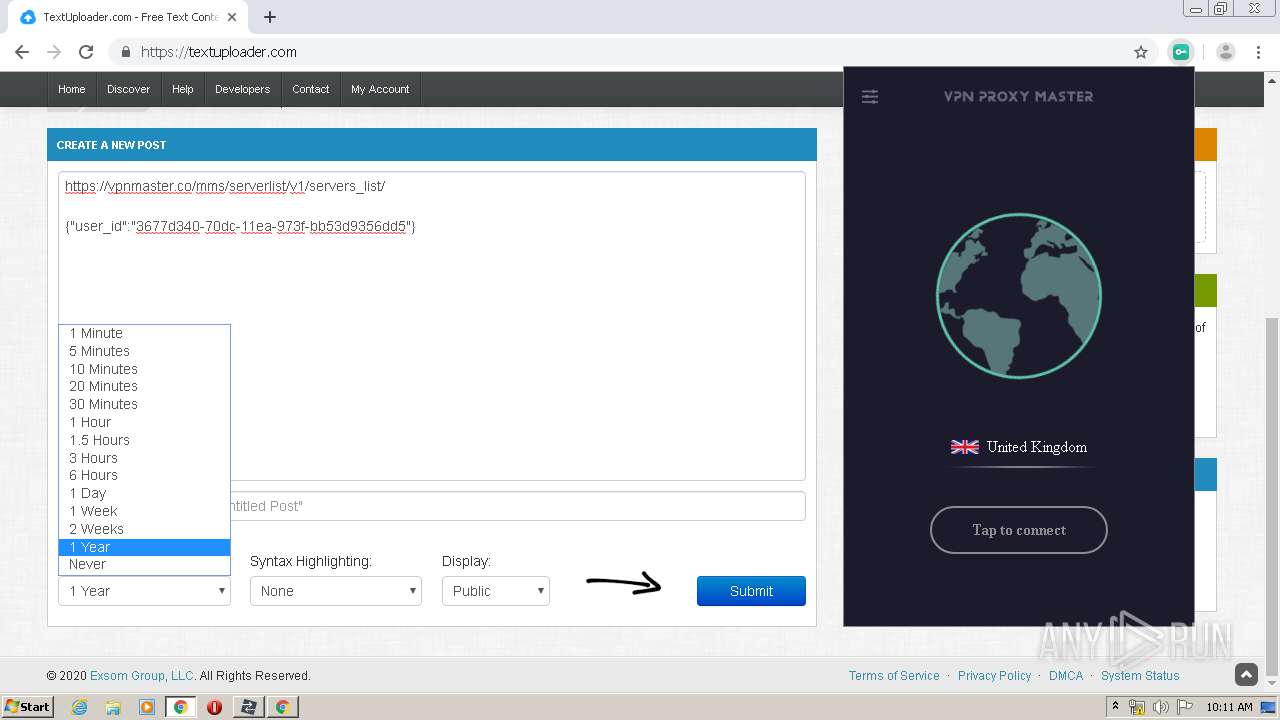
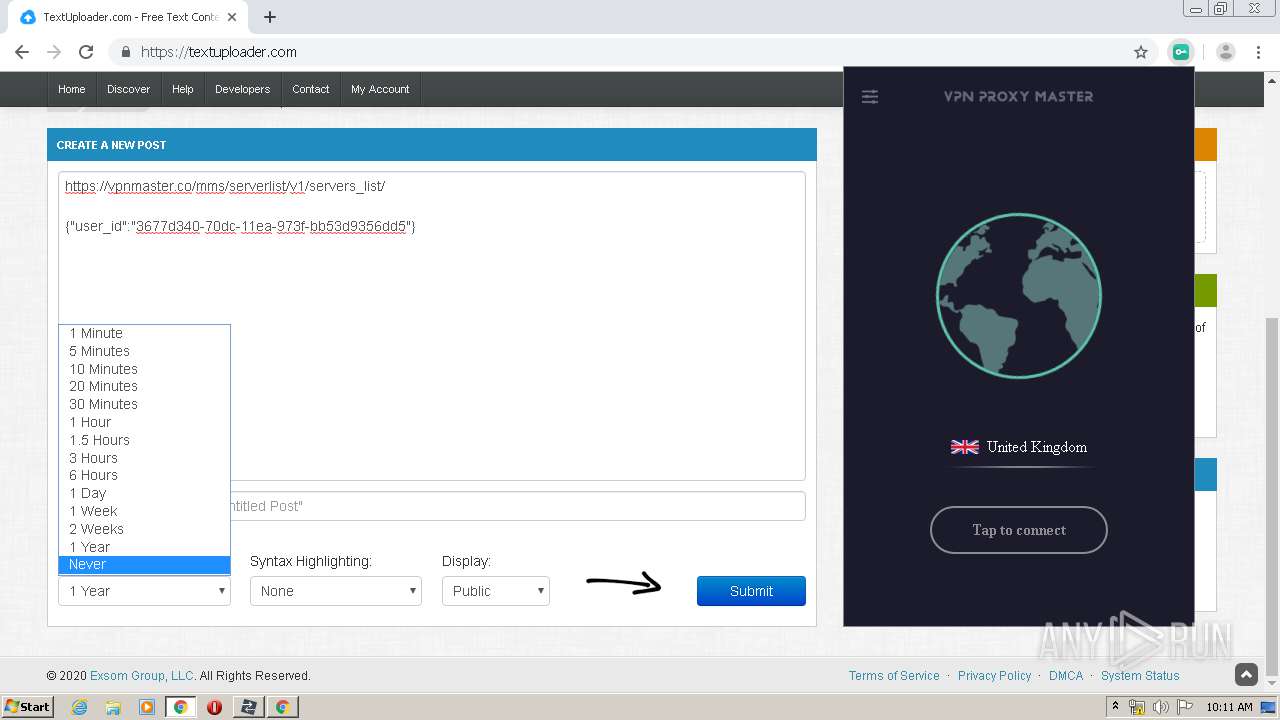
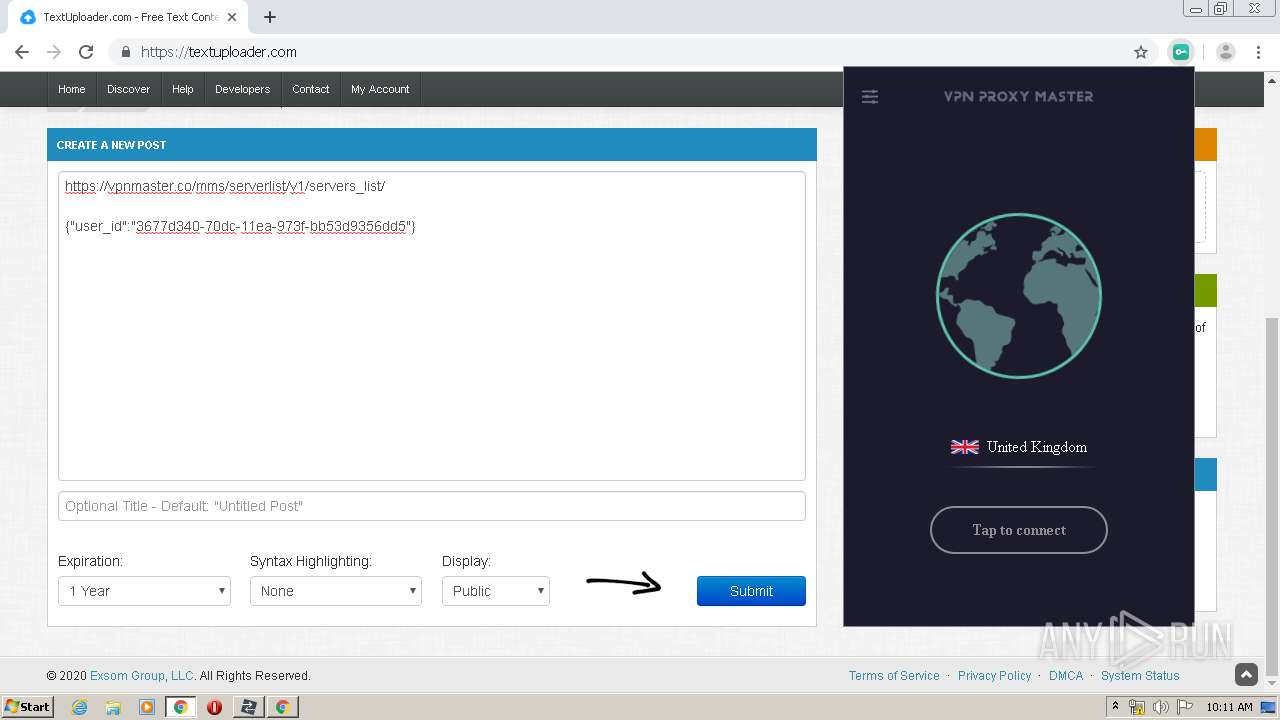
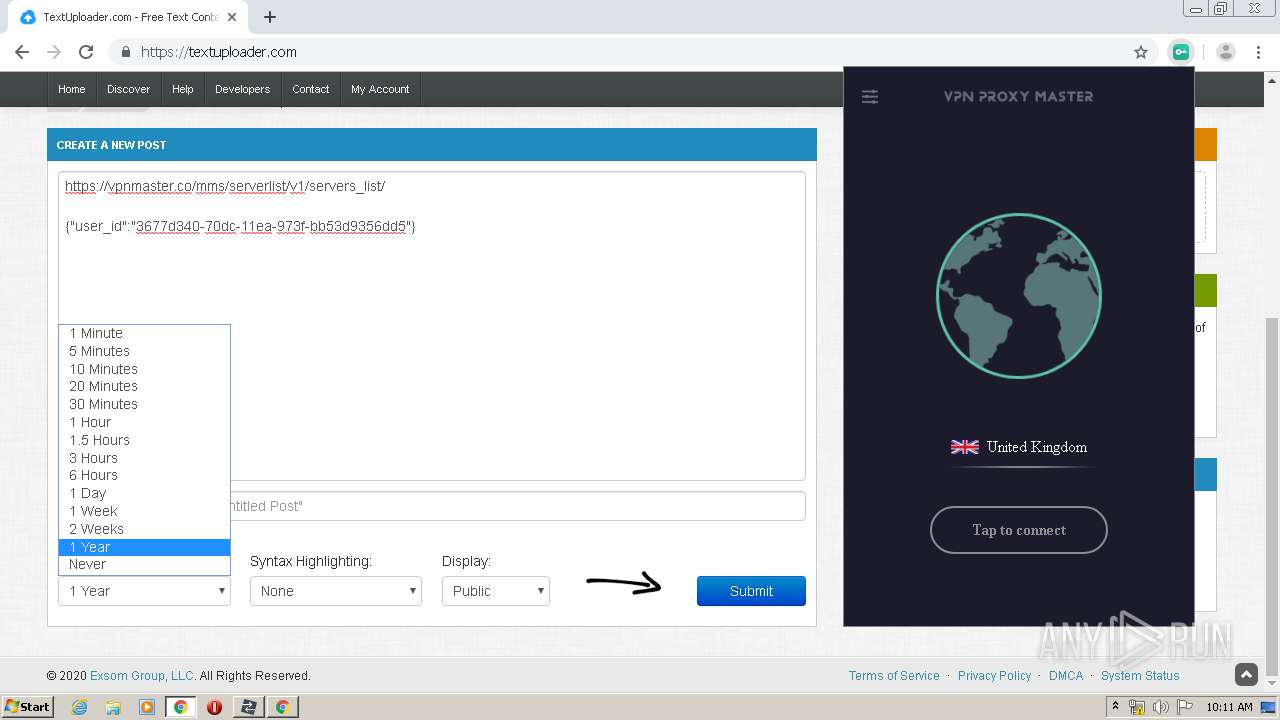
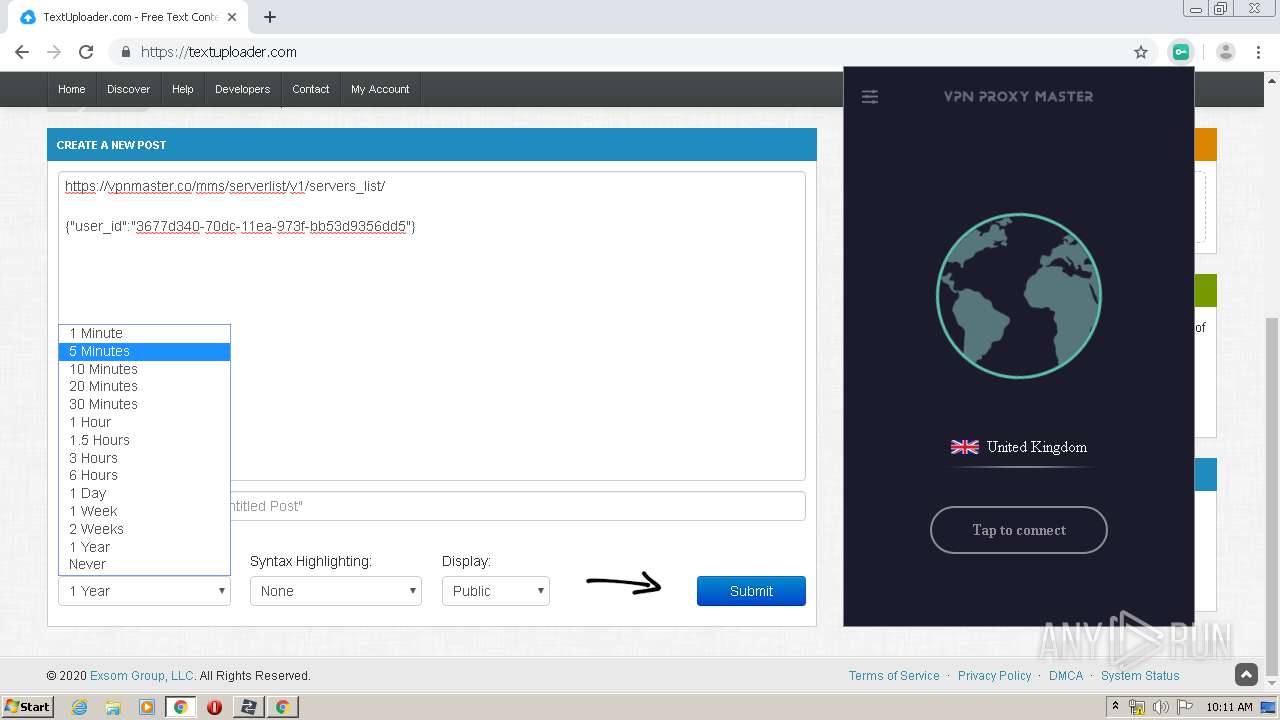
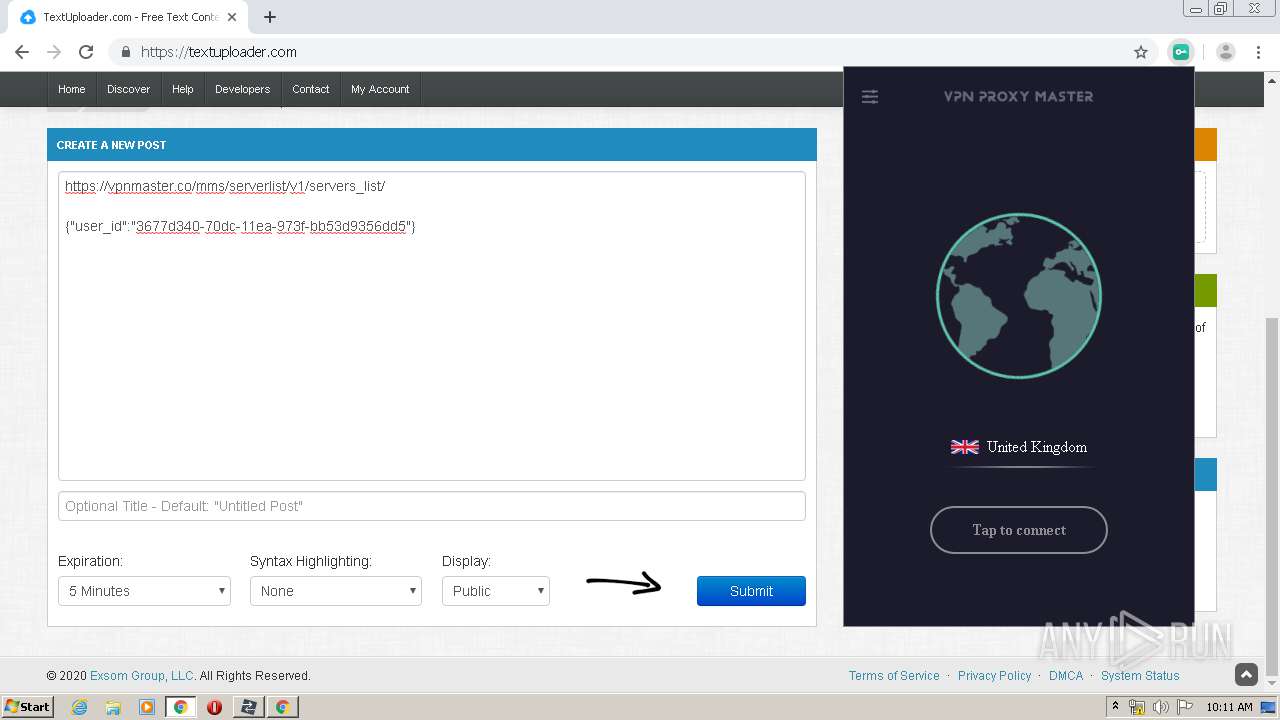
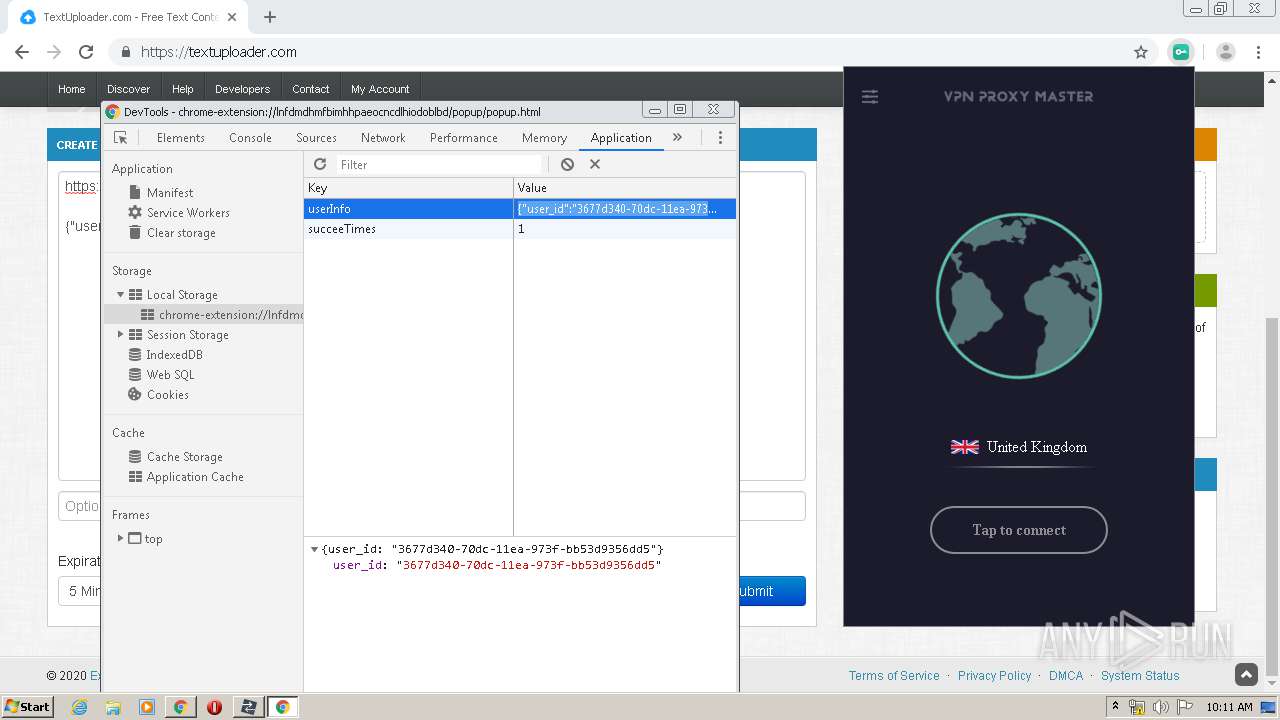
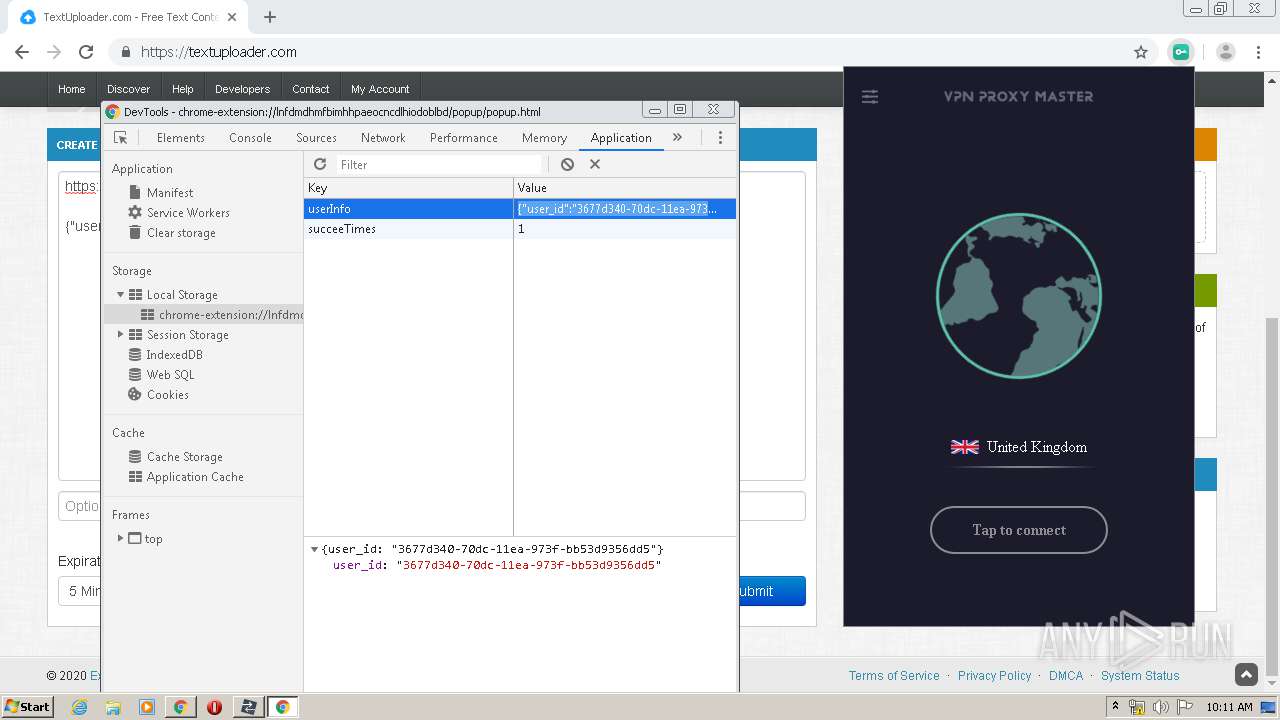
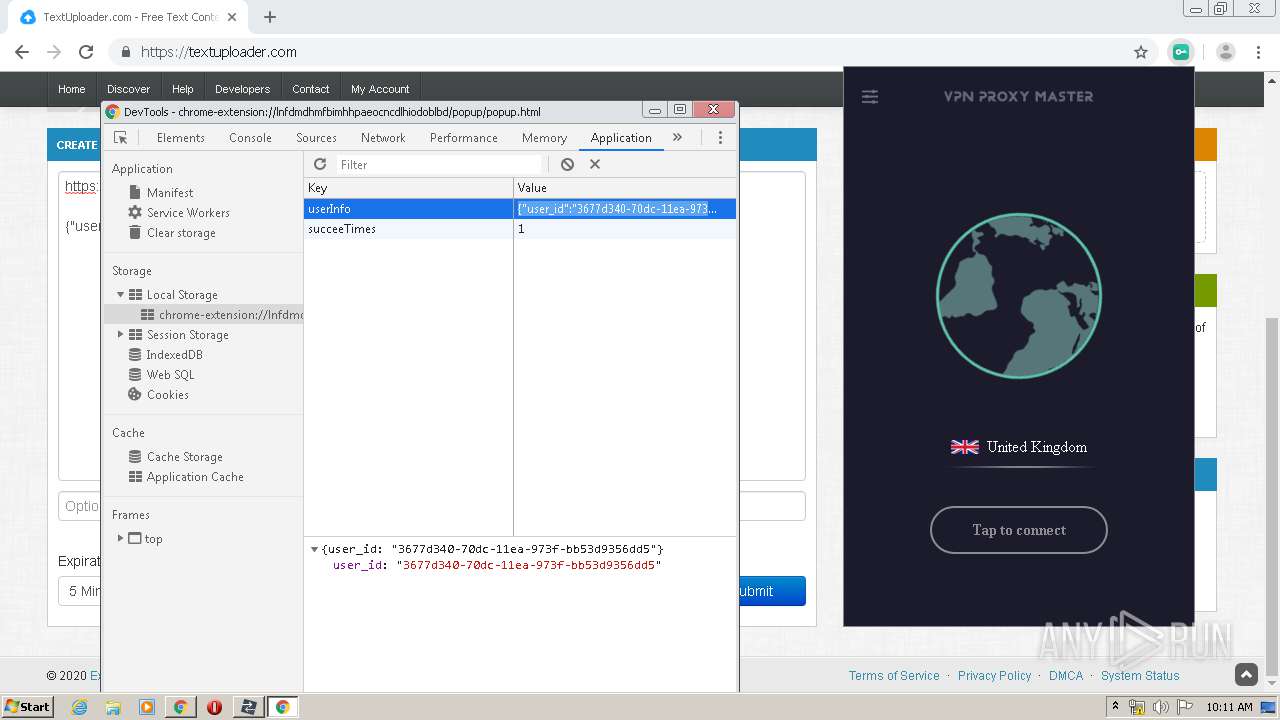
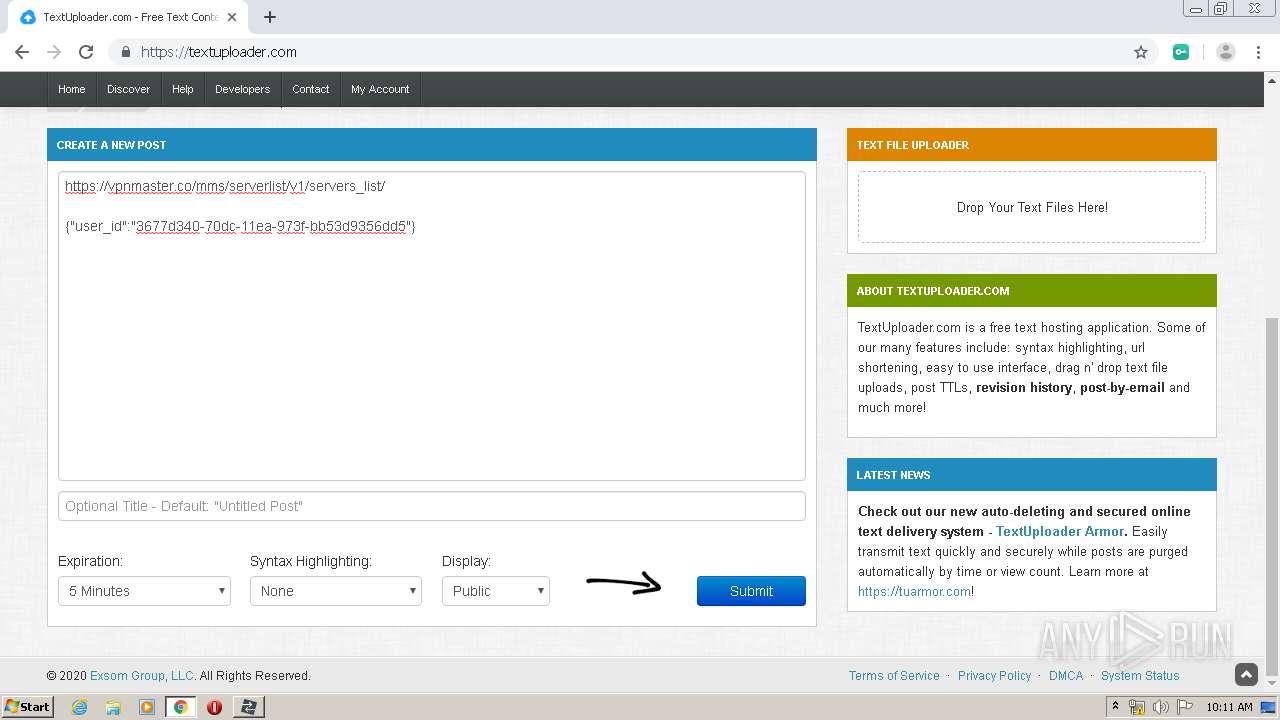
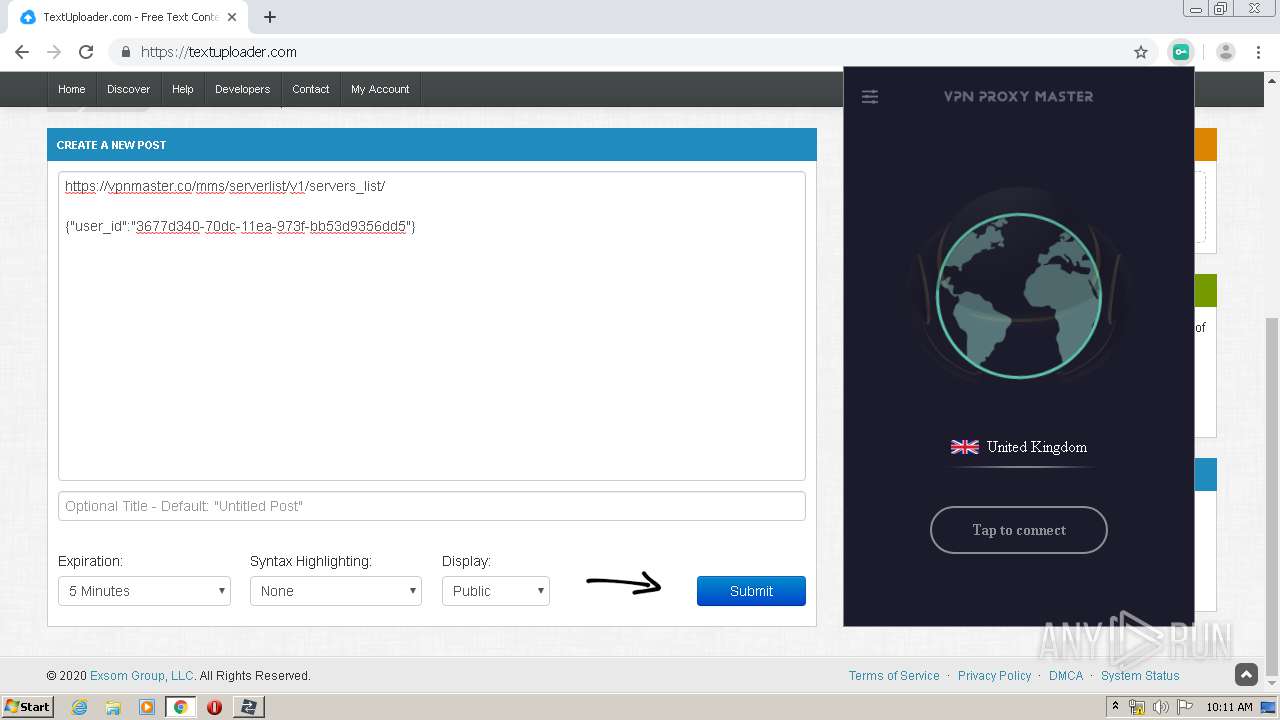
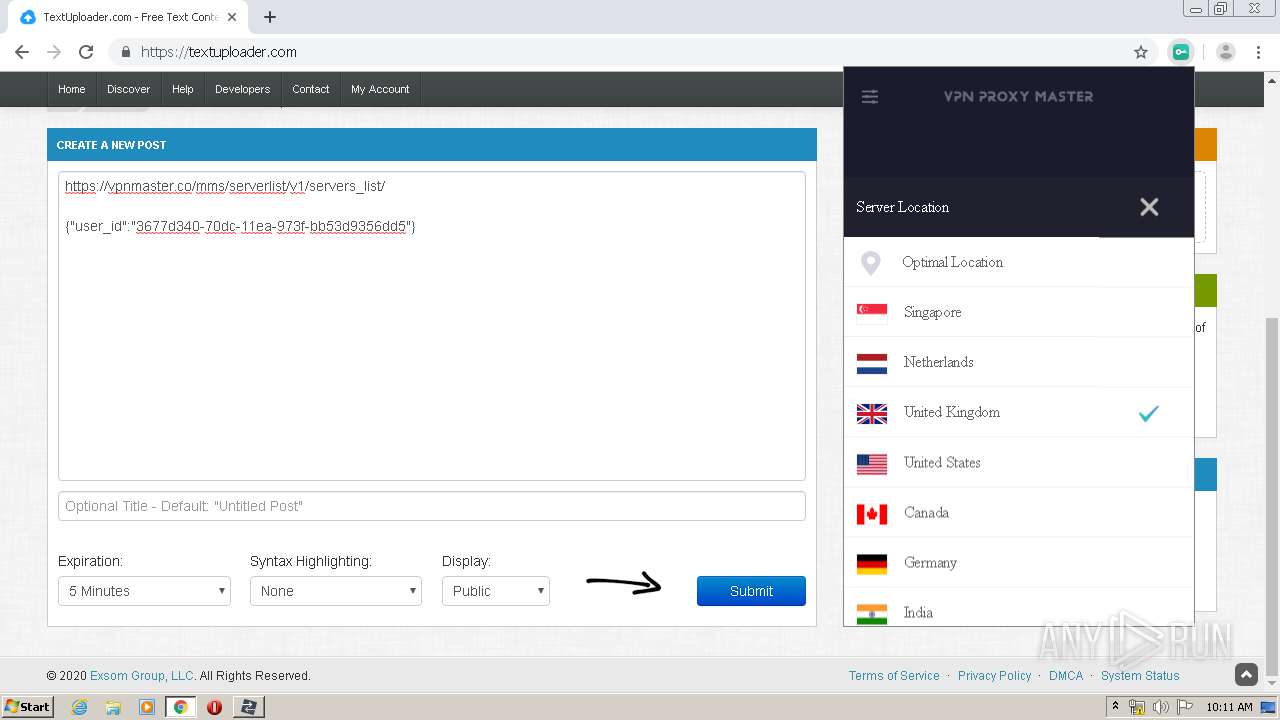
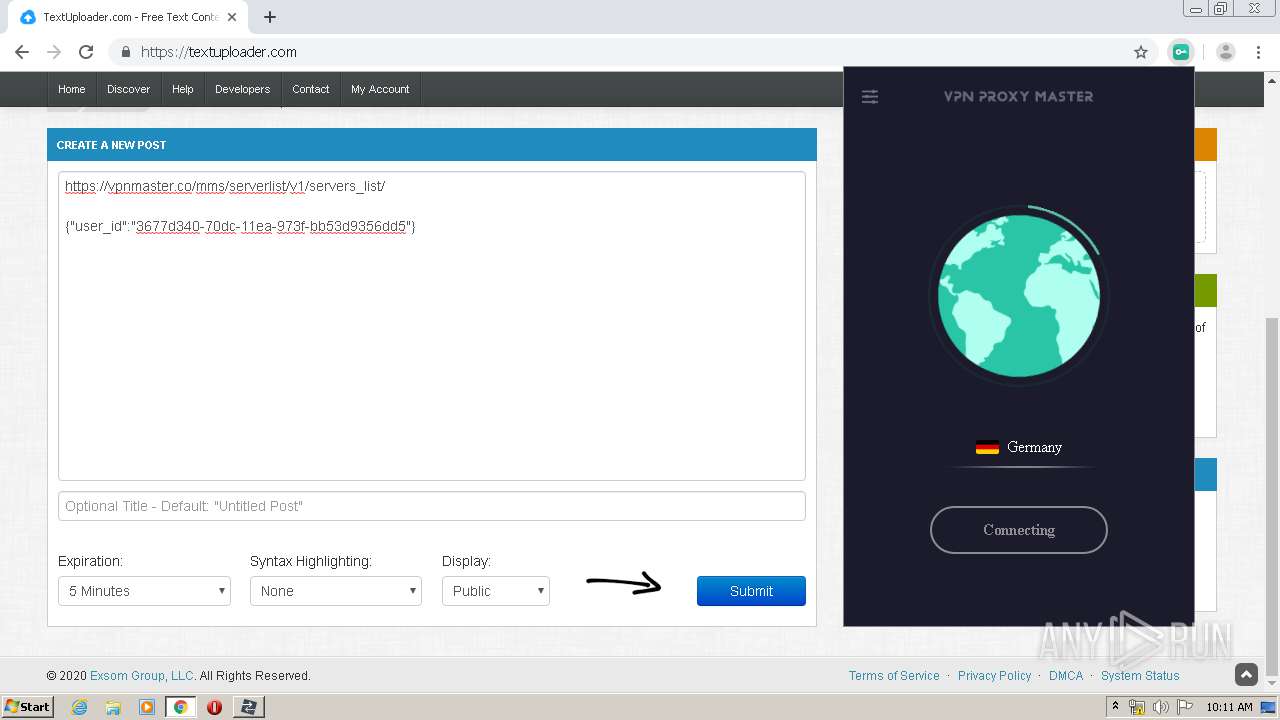
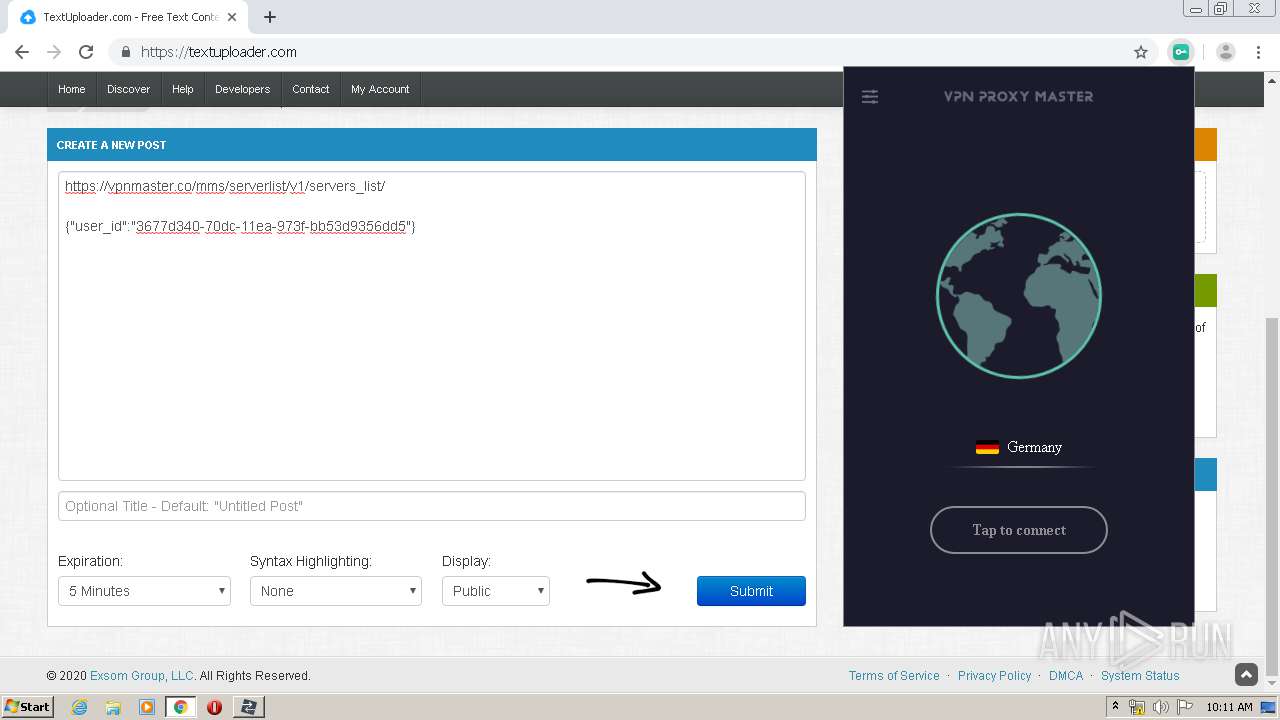
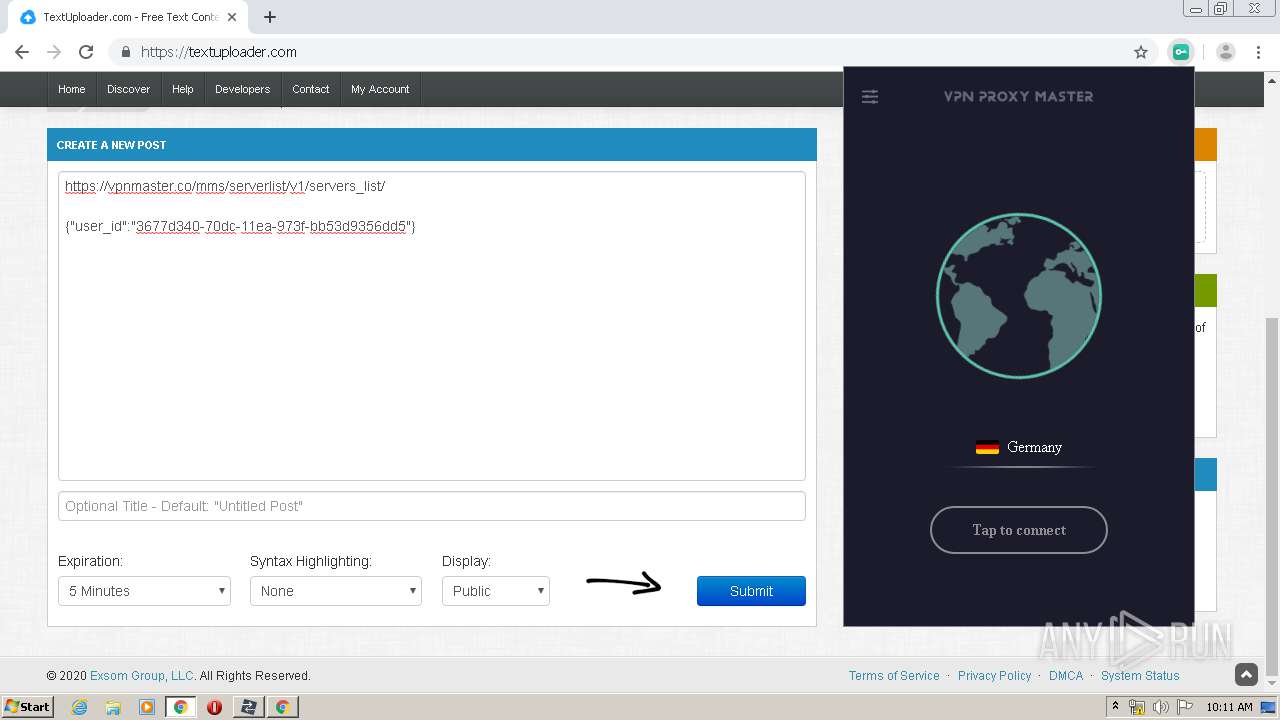
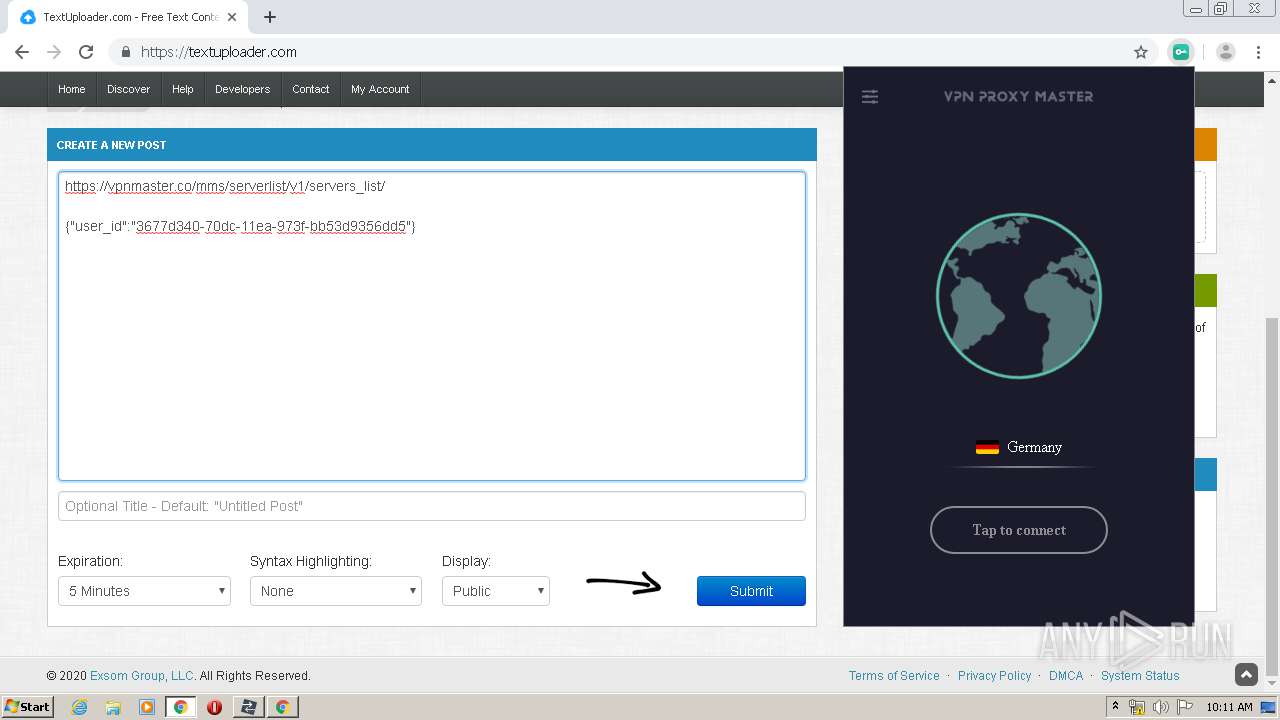
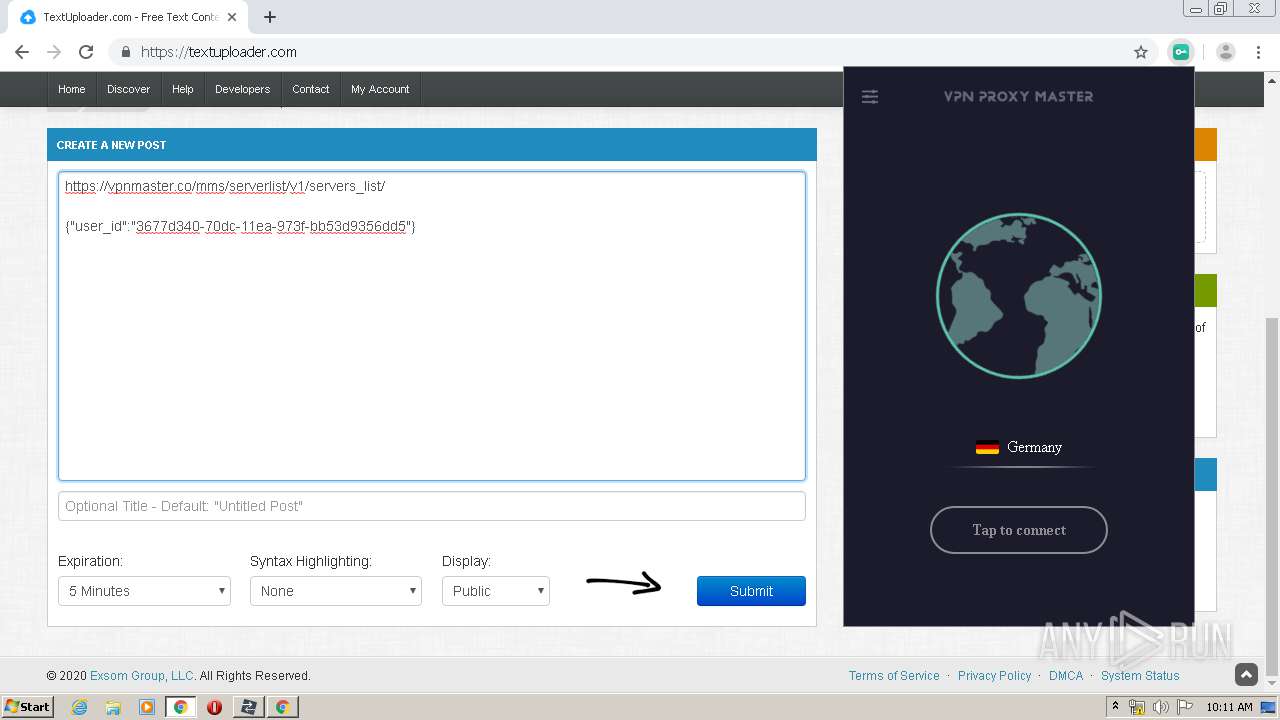
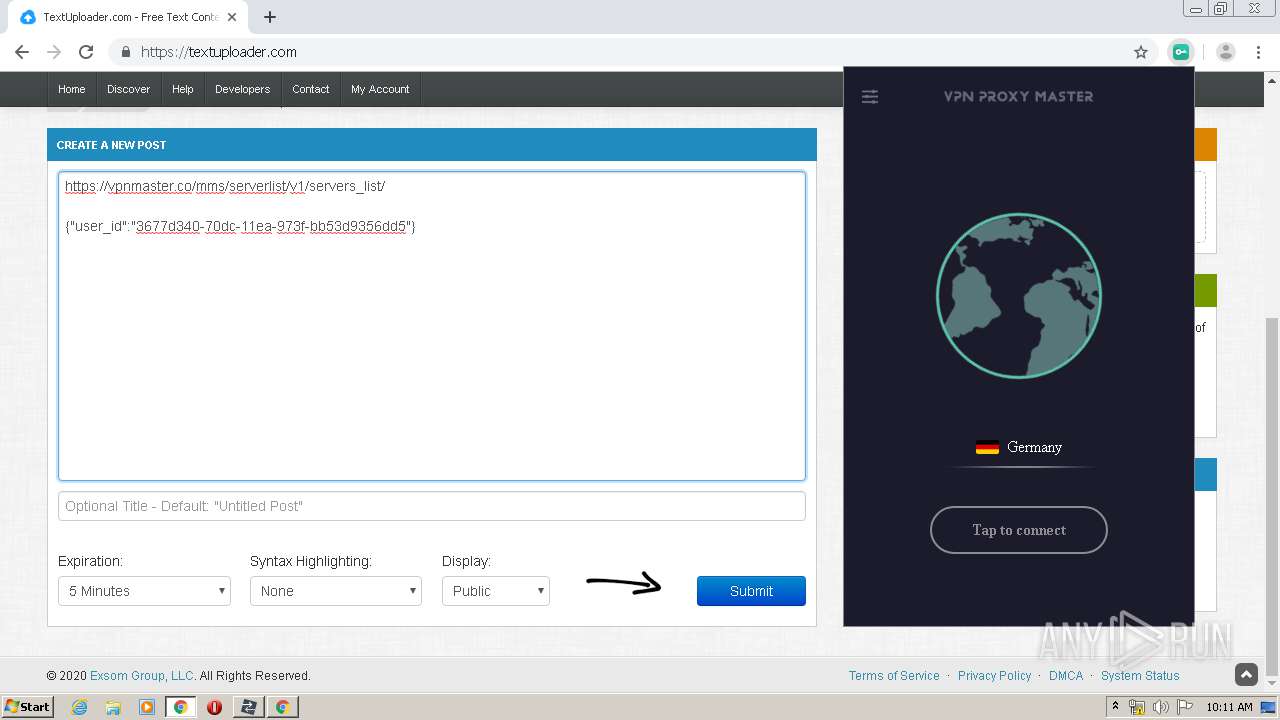
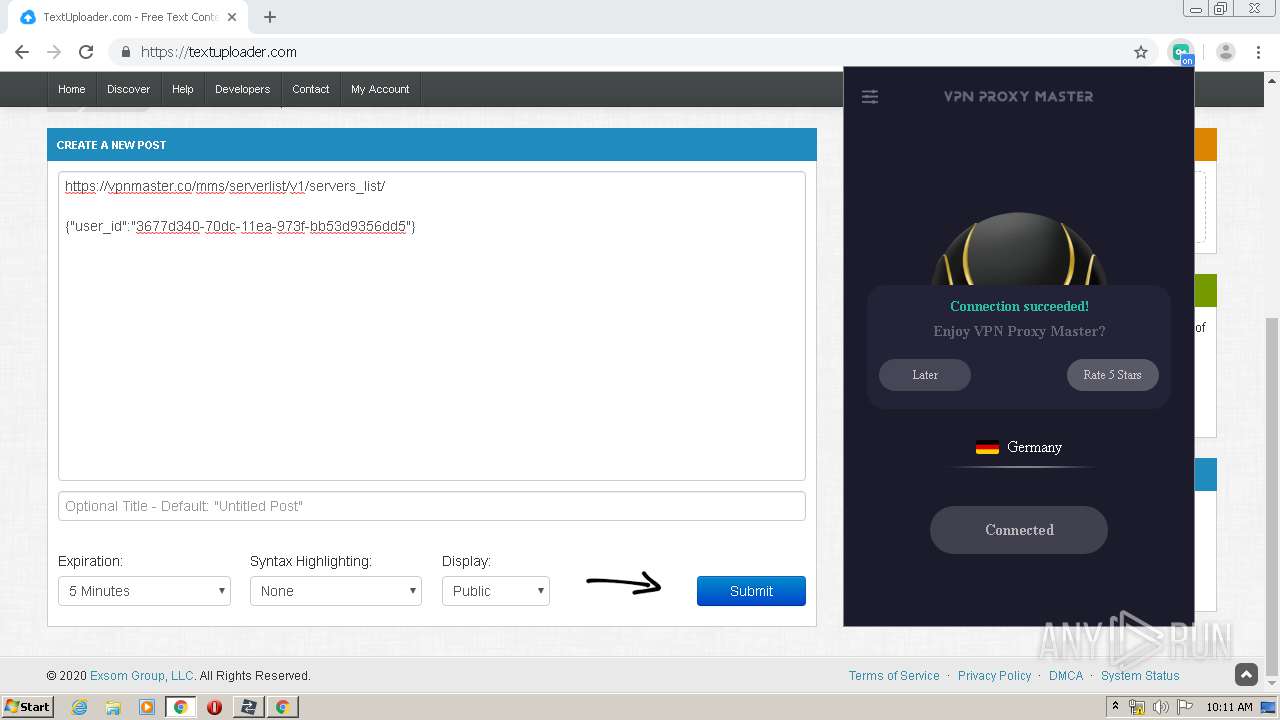
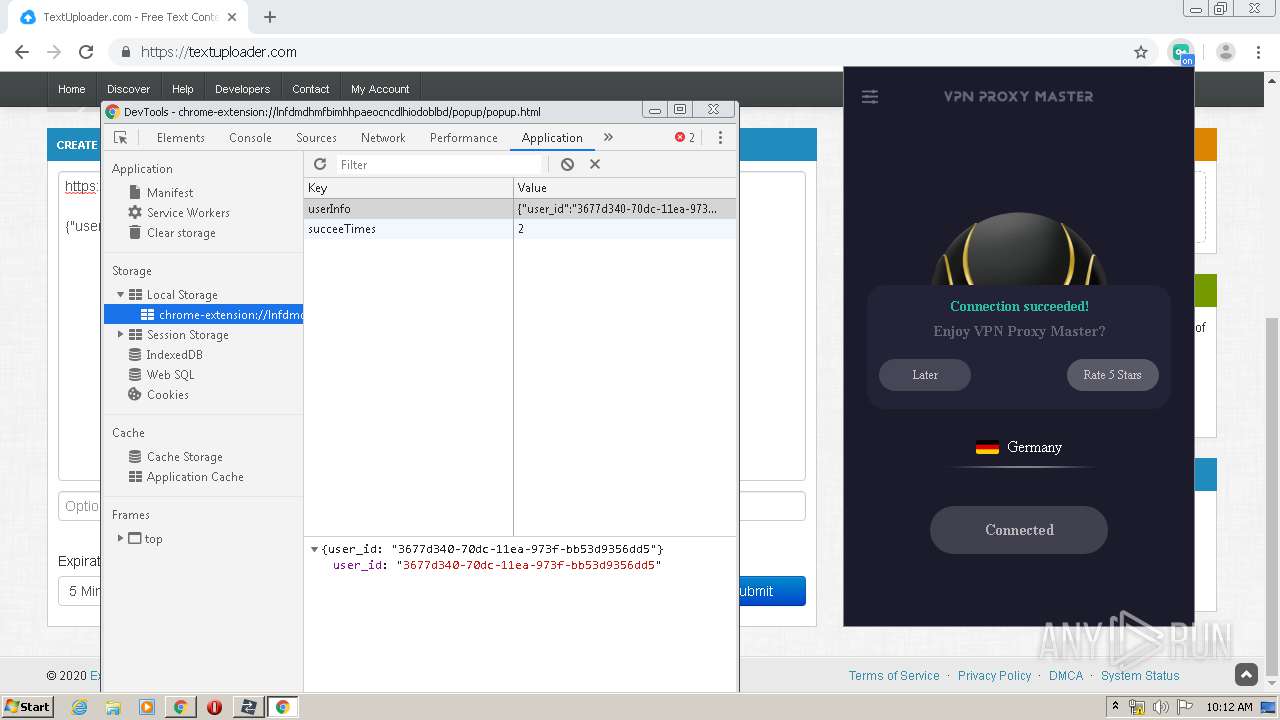
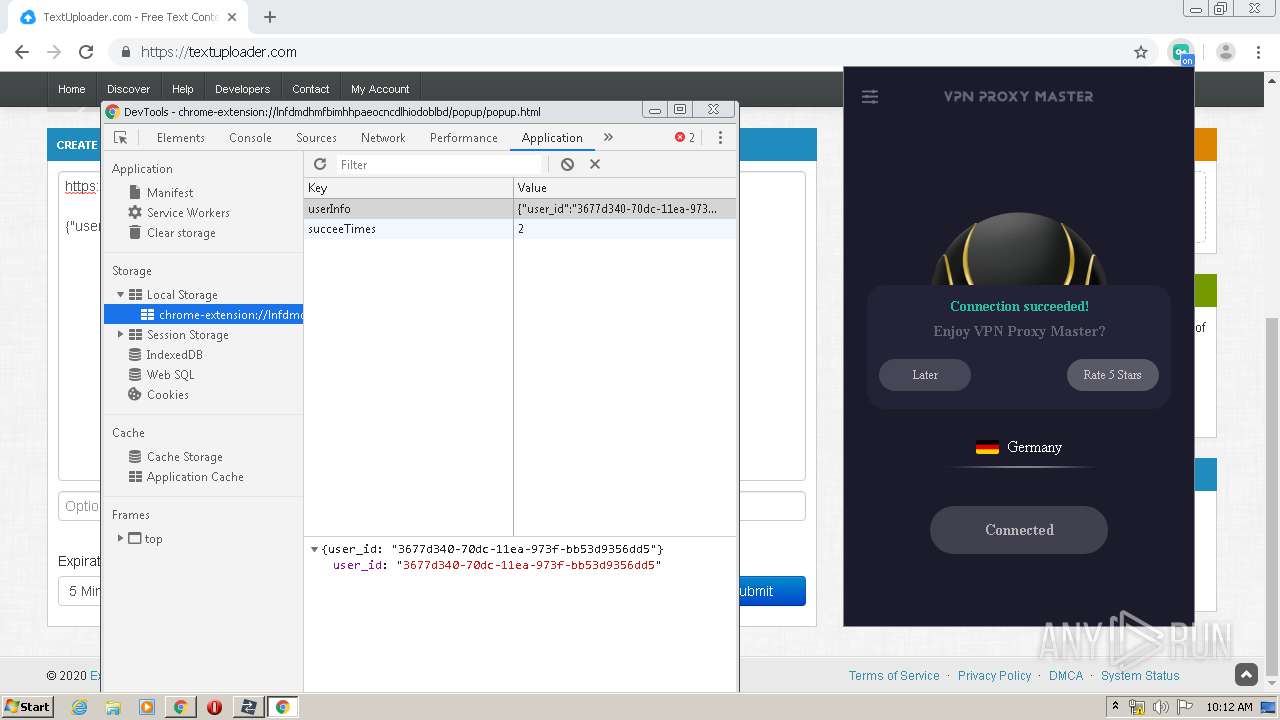
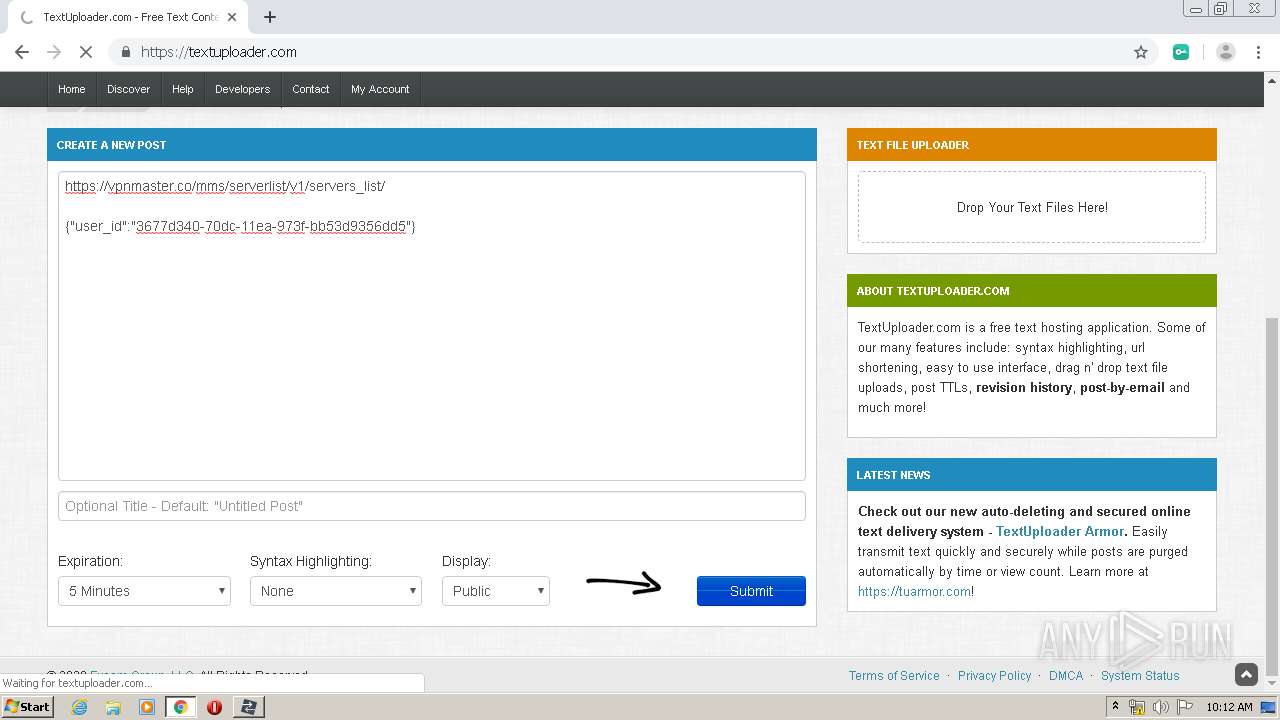
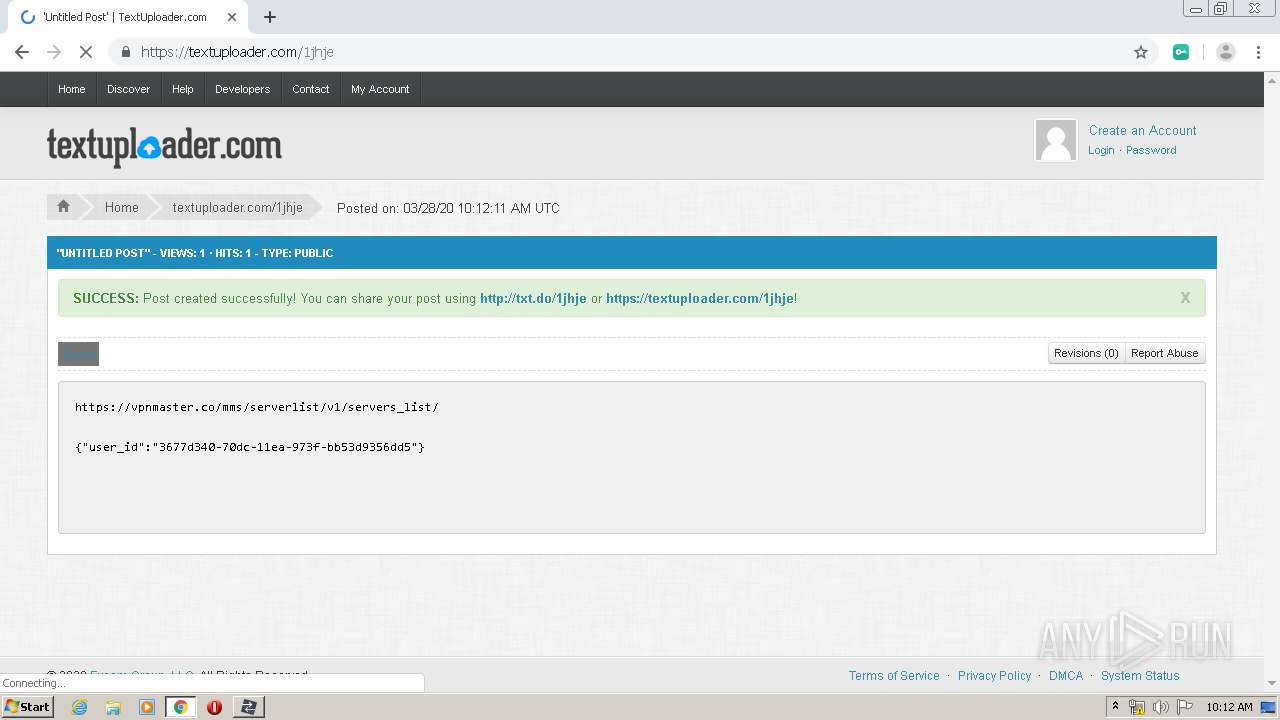
3260 | chrome.exe | GET | 302 | 104.26.9.236:80 | http://textuploader.com/ | US | — | — | suspicious |
3840 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 532 b | whitelisted |
3260 | chrome.exe | GET | 200 | 178.237.33.50:80 | http://www.geoplugin.net/json.gp | NL | html | 927 b | whitelisted |
3240 | HTTPDebuggerUI.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3260 | chrome.exe | GET | 200 | 178.237.33.50:80 | http://www.geoplugin.net/json.gp | NL | html | 927 b | whitelisted |
3260 | chrome.exe | GET | 200 | 178.237.33.50:80 | http://www.geoplugin.net/json.gp | NL | html | 927 b | whitelisted |
3840 | chrome.exe | GET | 200 | 87.245.216.147:80 | http://r8---sn-gxuo03g-3c2e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=85.206.166.82&mm=28&mn=sn-gxuo03g-3c2e&ms=nvh&mt=1585389971&mv=m&mvi=7&pl=23&shardbypass=yes | GB | crx | 293 Kb | whitelisted |
3840 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 527 b | whitelisted |
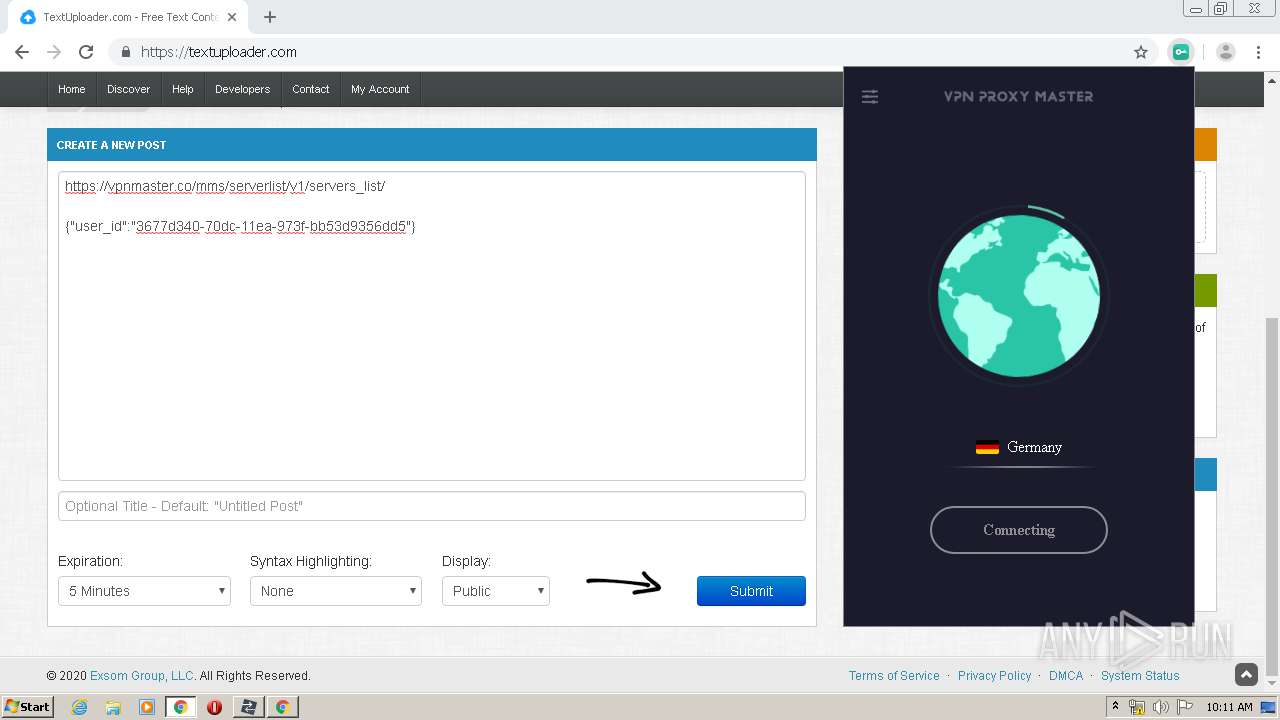
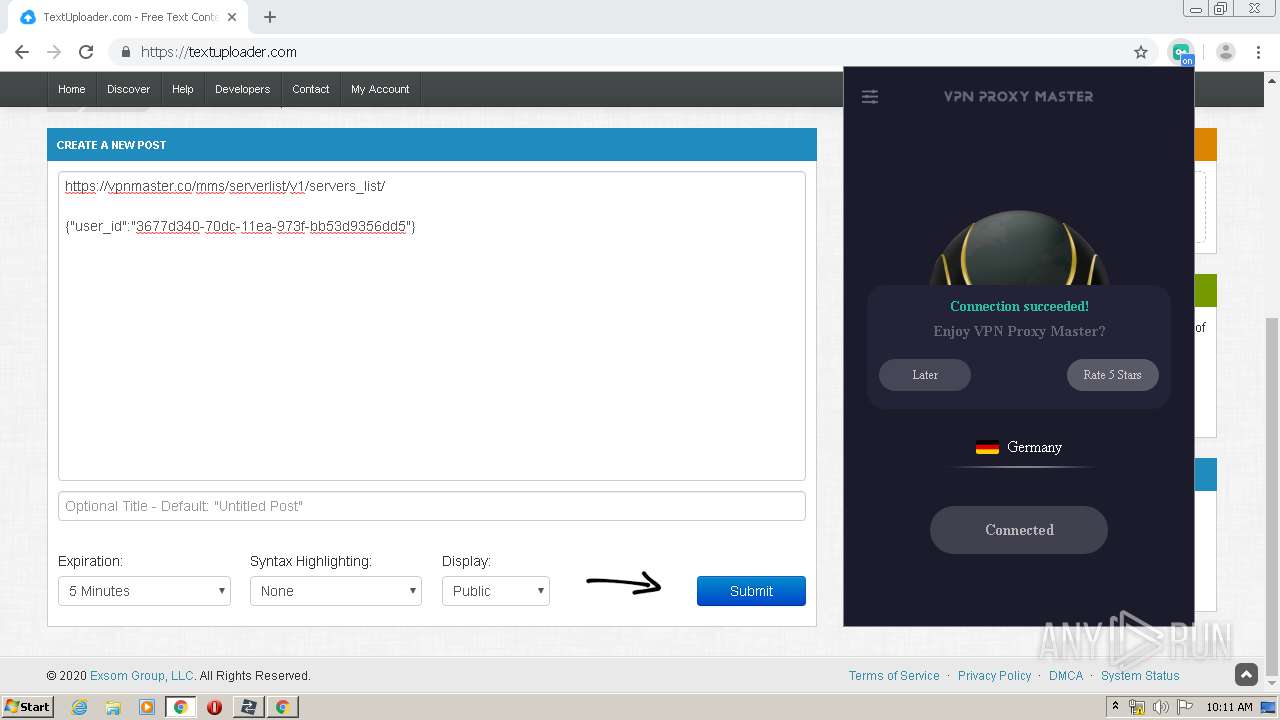
3260 | chrome.exe | POST | 200 | 165.22.34.185:80 | http://165.22.34.185/mms/report/v1/connection?time=0.20572030346013426 | US | text | 3 b | unknown |
3260 | chrome.exe | POST | 200 | 165.22.34.185:80 | http://165.22.34.185/mms/report/v1/connection?time=0.4770650374016916 | US | text | 3 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3840 | chrome.exe | 216.58.207.78:443 | chrome.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.210.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.18.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.205.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.16.129:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3840 | chrome.exe | 104.31.64.244:443 | www.httpdebugger.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chrome.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
3 ETPRO signatures available at the full report