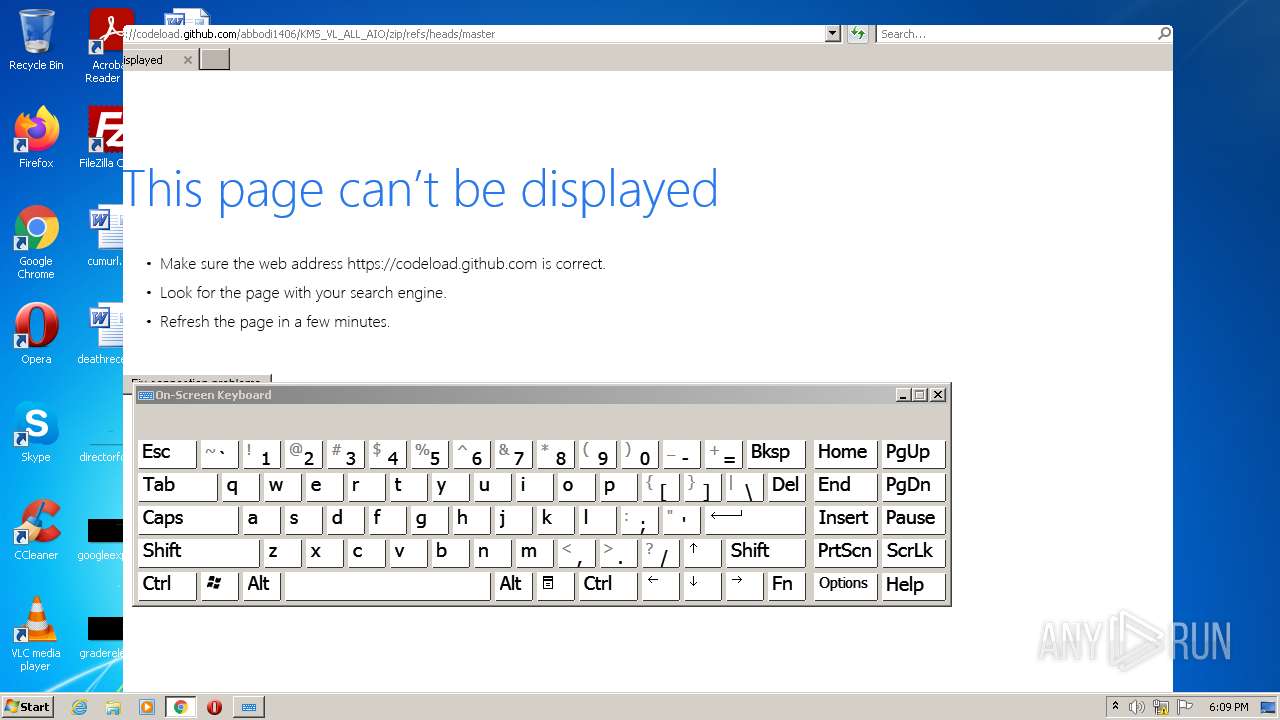
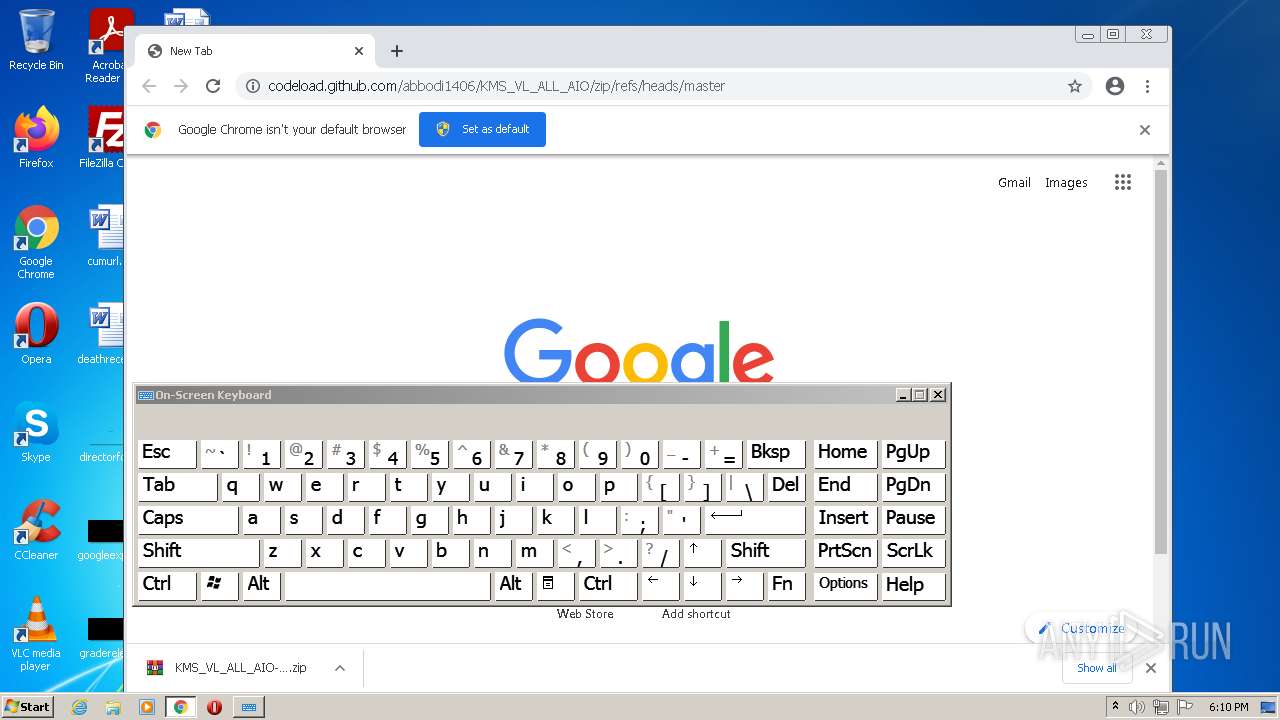
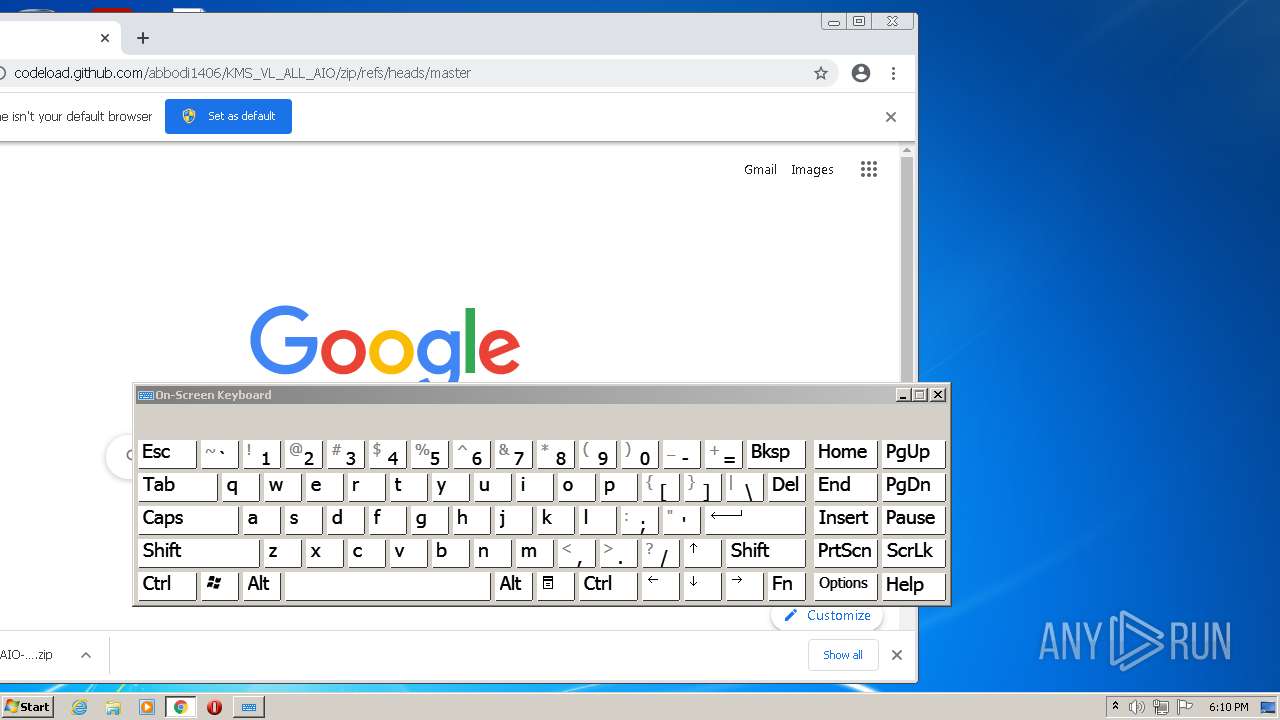
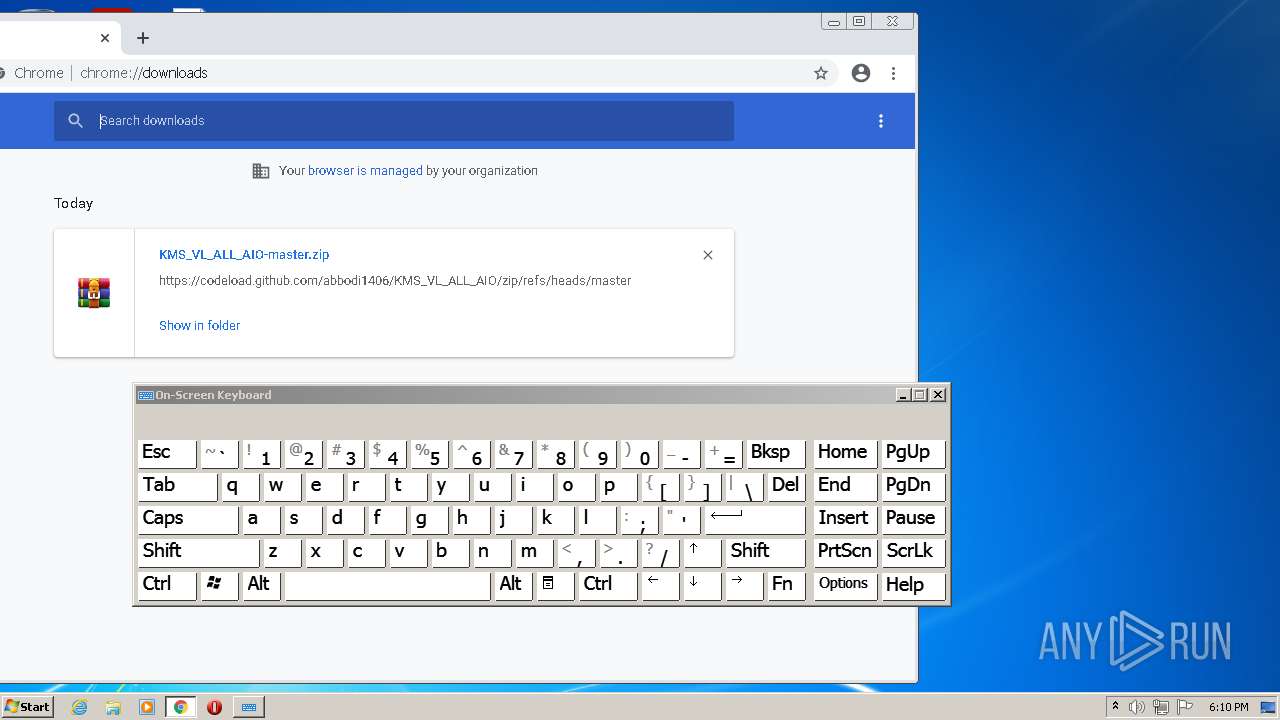
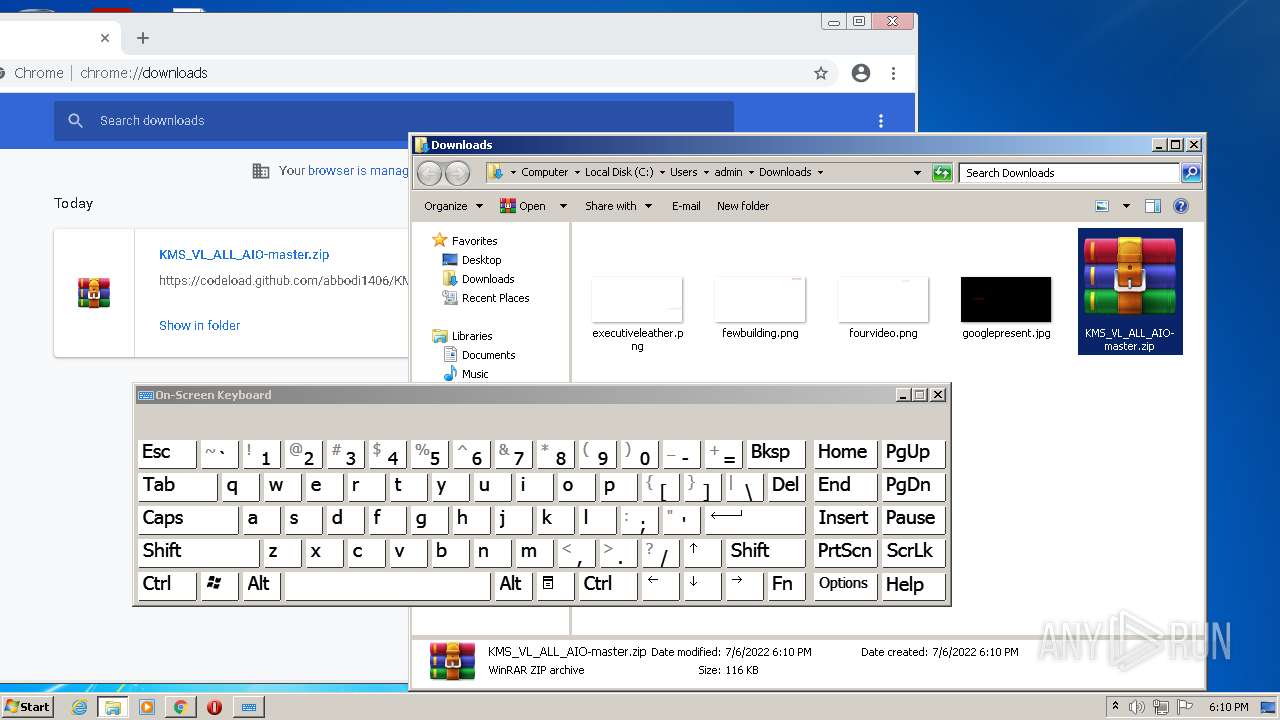
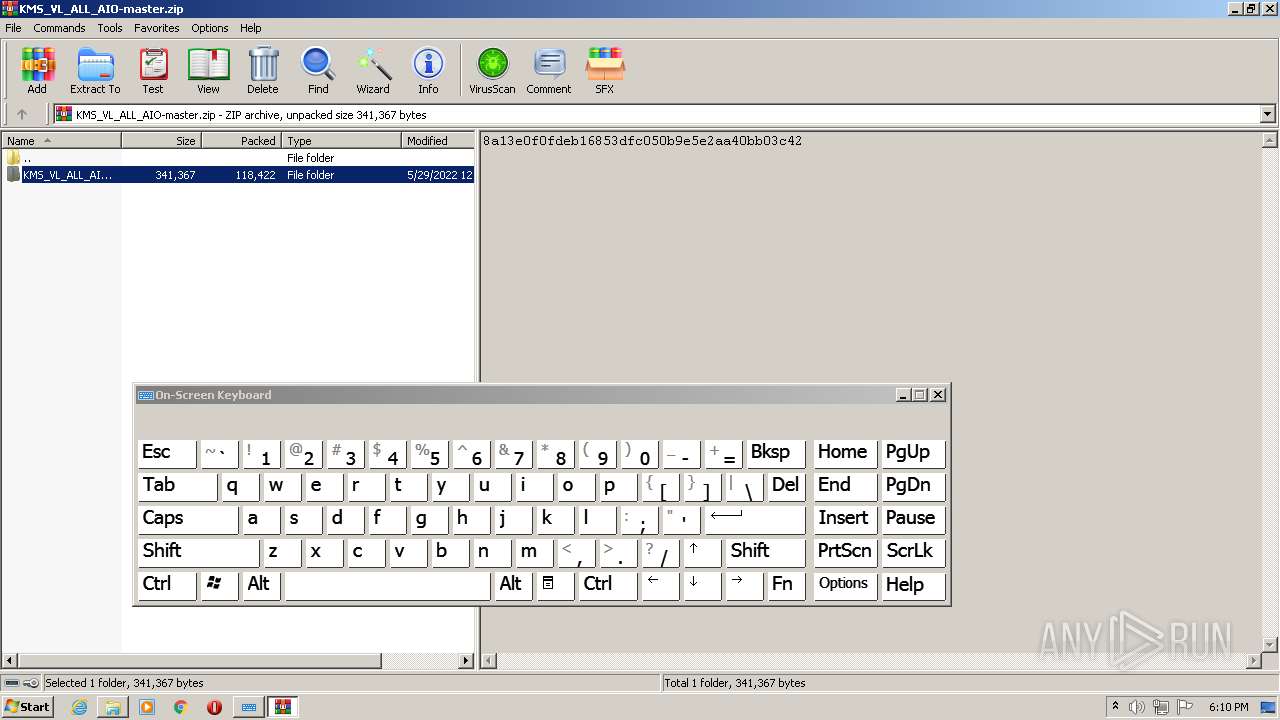
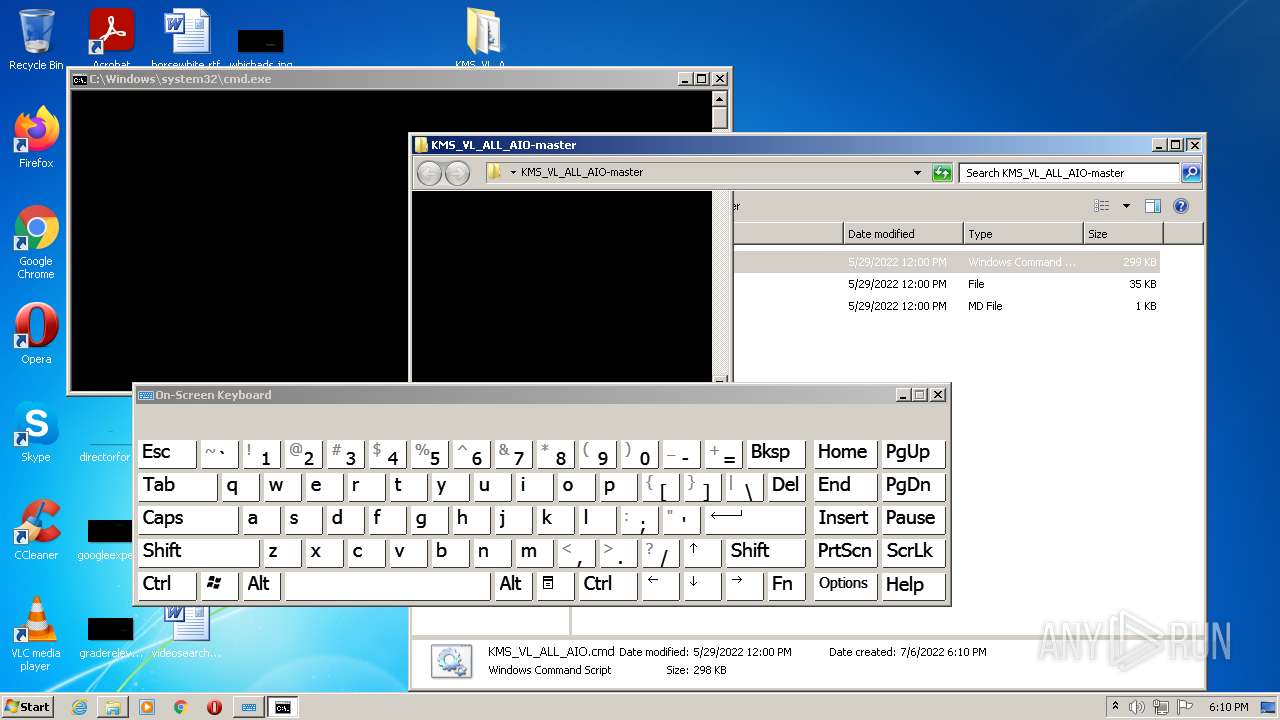
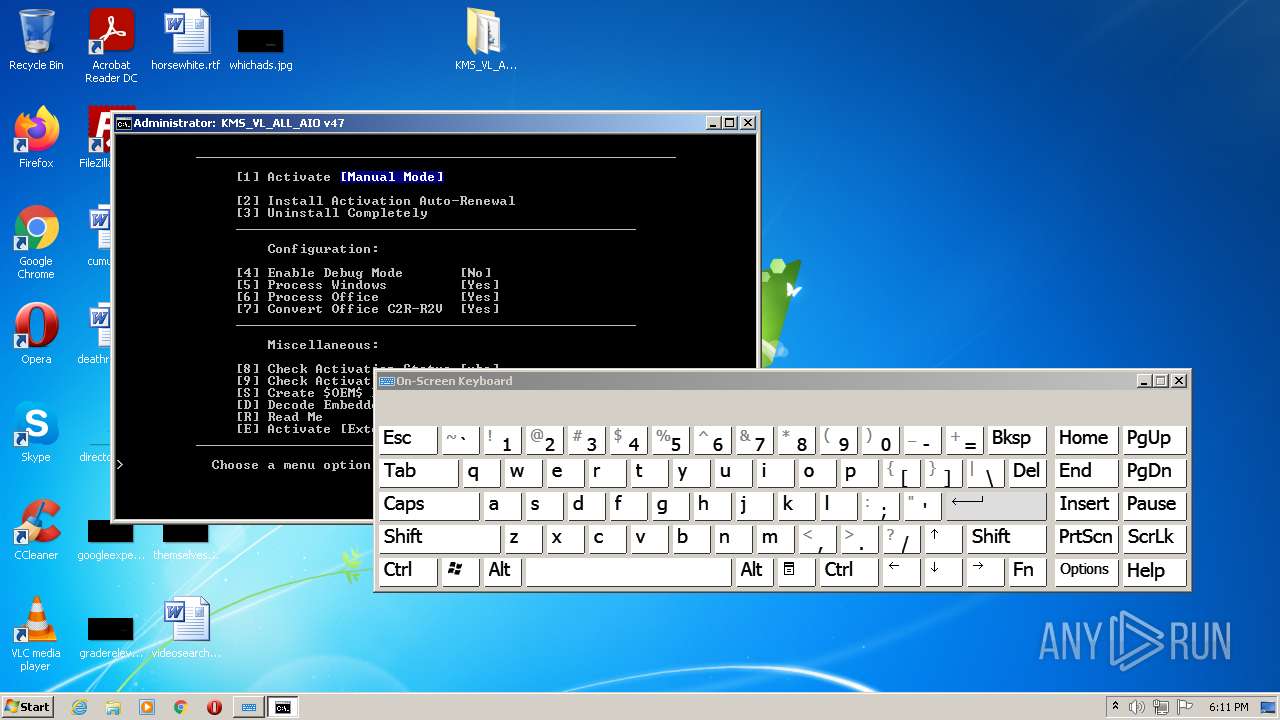
| URL: | https://github.com/abbodi1406/KMS_VL_ALL_AIO/archive/refs/heads/master.zip |
| Full analysis: | https://app.any.run/tasks/eff2c4d8-acb4-4f31-892b-91816f5ffae9 |
| Verdict: | Malicious activity |
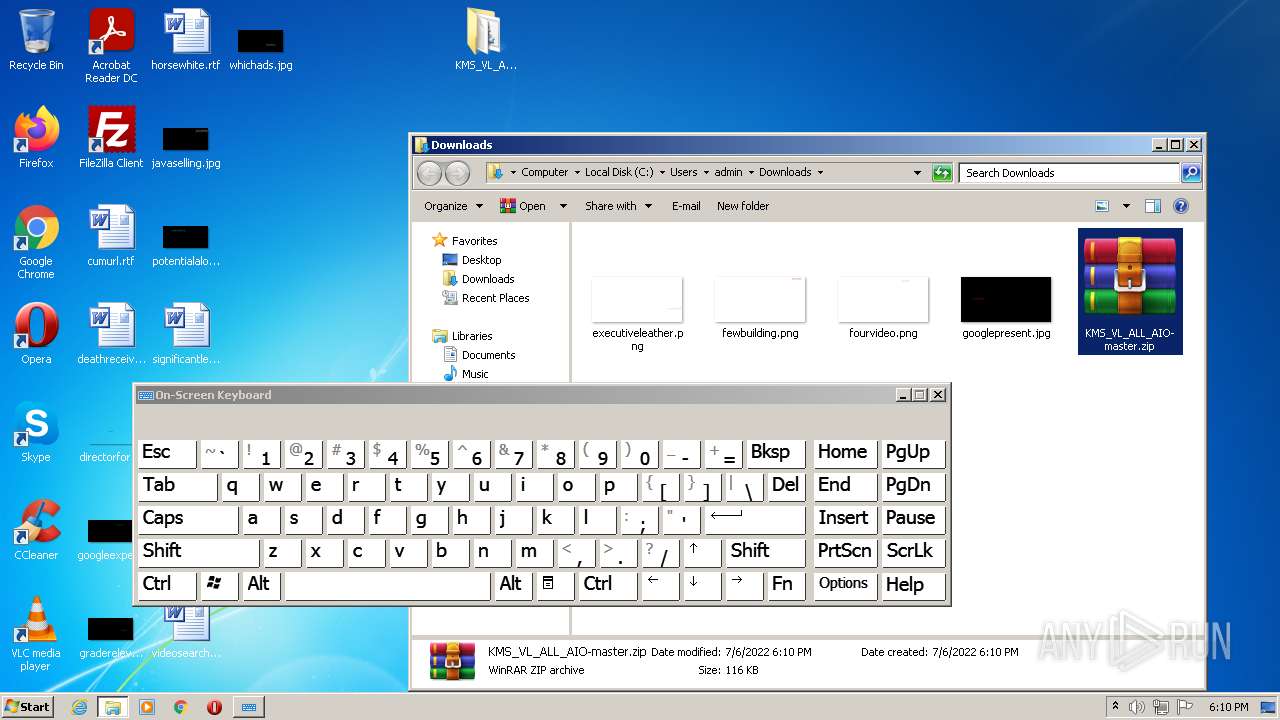
| Analysis date: | July 06, 2022, 17:08:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EFC9F6DFFC1DADF8A924C1EB1705F499 |
| SHA1: | B48D48FE0E37044FBE122F7D2F40AE7FB03D93B5 |
| SHA256: | 4A0DD0E4CA2A7A09CE8853082A574019058B935DDC8A9869270C9038F2395C73 |
| SSDEEP: | 3:N8tEd0nHIVGnPsqfXT4RSL6o:2uiogsqL4UL6o |
MALICIOUS
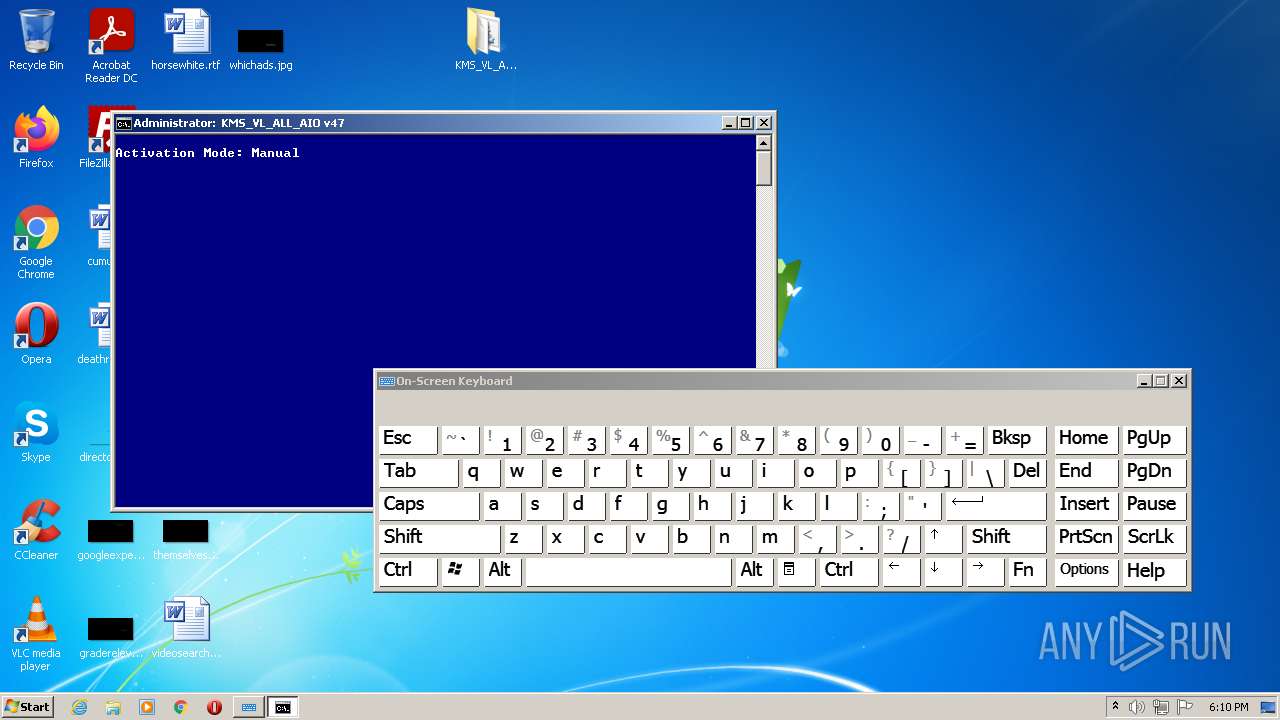
Executes PowerShell scripts
- cmd.exe (PID: 736)
- cmd.exe (PID: 3420)
Drops executable file immediately after starts
- csc.exe (PID: 2564)
- powershell.exe (PID: 2784)
Starts Visual C# compiler
- powershell.exe (PID: 2784)
Loads dropped or rewritten executable
- sppsvc.exe (PID: 2232)
- OSPPSVC.EXE (PID: 4060)
Loads the Task Scheduler COM API
- sppsvc.exe (PID: 2232)
- OSPPSVC.EXE (PID: 4060)
Starts NET.EXE for service management
- cmd.exe (PID: 3420)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3476)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3296)
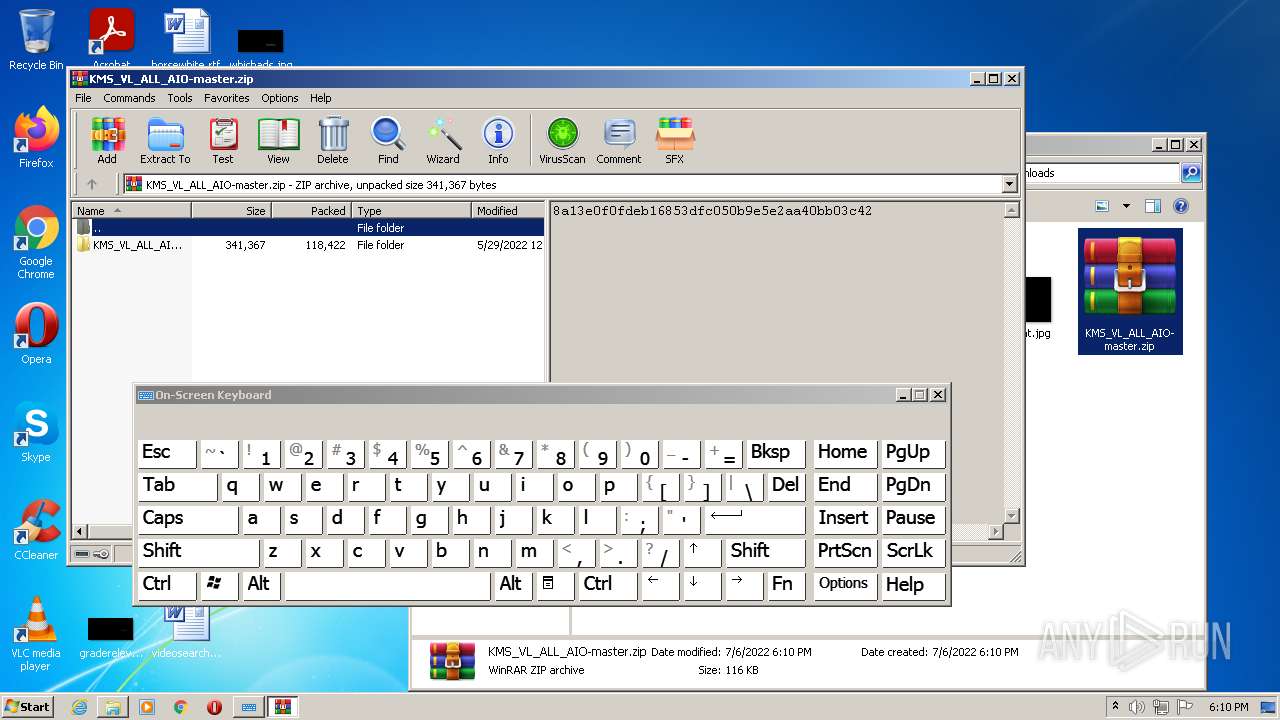
Reads the computer name
- WinRAR.exe (PID: 2084)
- WMIC.exe (PID: 2756)
- powershell.exe (PID: 2504)
- cscript.exe (PID: 3564)
- WMIC.exe (PID: 2040)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 3528)
- powershell.exe (PID: 2784)
- WMIC.exe (PID: 1528)
- WMIC.exe (PID: 1152)
- WMIC.exe (PID: 1680)
- WMIC.exe (PID: 3052)
- WMIC.exe (PID: 3520)
- WMIC.exe (PID: 2180)
- WMIC.exe (PID: 1780)
- WMIC.exe (PID: 3016)
- WMIC.exe (PID: 2112)
- OSPPSVC.EXE (PID: 4060)
- WMIC.exe (PID: 3356)
- WMIC.exe (PID: 1972)
Checks supported languages
- WinRAR.exe (PID: 2084)
- cmd.exe (PID: 736)
- WMIC.exe (PID: 2756)
- cscript.exe (PID: 3564)
- powershell.exe (PID: 2504)
- cmd.exe (PID: 3420)
- WMIC.exe (PID: 2040)
- powershell.exe (PID: 3100)
- cmd.exe (PID: 1592)
- cmd.exe (PID: 280)
- cmd.exe (PID: 2488)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 3808)
- mode.com (PID: 2756)
- powershell.exe (PID: 3528)
- powershell.exe (PID: 2784)
- cvtres.exe (PID: 1604)
- csc.exe (PID: 2564)
- cmd.exe (PID: 1252)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 3736)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 2920)
- cmd.exe (PID: 1808)
- WMIC.exe (PID: 1528)
- cmd.exe (PID: 1280)
- WMIC.exe (PID: 1152)
- WMIC.exe (PID: 1680)
- WMIC.exe (PID: 3052)
- WMIC.exe (PID: 3016)
- WMIC.exe (PID: 3520)
- cmd.exe (PID: 3164)
- WMIC.exe (PID: 2180)
- WMIC.exe (PID: 1780)
- OSPPSVC.EXE (PID: 4060)
- WMIC.exe (PID: 2112)
- WMIC.exe (PID: 3356)
- WMIC.exe (PID: 1972)
- mode.com (PID: 3712)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 736)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 1592)
- cmd.exe (PID: 1252)
- cmd.exe (PID: 1872)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 1780)
- cmd.exe (PID: 2920)
- cmd.exe (PID: 3736)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 736)
- cmd.exe (PID: 3420)
- cmd.exe (PID: 1808)
- cmd.exe (PID: 1280)
- cmd.exe (PID: 3164)
Executes scripts
- cmd.exe (PID: 736)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 3564)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 3564)
- cmd.exe (PID: 3420)
Application launched itself
- cmd.exe (PID: 3420)
Starts SC.EXE for service management
- cmd.exe (PID: 3420)
Creates files in the Windows directory
- cmd.exe (PID: 3420)
- powershell.exe (PID: 2784)
- csc.exe (PID: 2564)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 3420)
Removes files from Windows directory
- powershell.exe (PID: 2784)
- csc.exe (PID: 2564)
- cmd.exe (PID: 3420)
Executable content was dropped or overwritten
- csc.exe (PID: 2564)
- powershell.exe (PID: 2784)
Drops a file with a compile date too recent
- csc.exe (PID: 2564)
- powershell.exe (PID: 2784)
Reads Environment values
- reg.exe (PID: 3380)
INFO
Application launched itself
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 3296)
Checks supported languages
- iexplore.exe (PID: 3476)
- osk.exe (PID: 3516)
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 1320)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 3088)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 1504)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 1604)
- chrome.exe (PID: 336)
- chrome.exe (PID: 2444)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 4012)
- reg.exe (PID: 3168)
- find.exe (PID: 2688)
- chrome.exe (PID: 3308)
- find.exe (PID: 1320)
- rundll32.exe (PID: 2140)
- reg.exe (PID: 2564)
- find.exe (PID: 3756)
- find.exe (PID: 2536)
- reg.exe (PID: 3108)
- reg.exe (PID: 188)
- reg.exe (PID: 1468)
- reg.exe (PID: 2724)
- find.exe (PID: 2320)
- reg.exe (PID: 844)
- find.exe (PID: 1228)
- find.exe (PID: 3596)
- find.exe (PID: 2088)
- sc.exe (PID: 2572)
- choice.exe (PID: 3160)
- findstr.exe (PID: 892)
- findstr.exe (PID: 2836)
- find.exe (PID: 1804)
- sc.exe (PID: 3544)
- find.exe (PID: 2220)
- sc.exe (PID: 1880)
- find.exe (PID: 2760)
- sc.exe (PID: 3852)
- find.exe (PID: 3084)
- sc.exe (PID: 3456)
- reg.exe (PID: 3208)
- reg.exe (PID: 2908)
- reg.exe (PID: 3160)
- reg.exe (PID: 4044)
- reg.exe (PID: 3508)
- reg.exe (PID: 3620)
- reg.exe (PID: 3548)
- reg.exe (PID: 2728)
- reg.exe (PID: 2380)
- reg.exe (PID: 1388)
- reg.exe (PID: 3156)
- reg.exe (PID: 3324)
- reg.exe (PID: 3564)
- reg.exe (PID: 3048)
- reg.exe (PID: 3028)
- reg.exe (PID: 3380)
- reg.exe (PID: 3284)
- reg.exe (PID: 1968)
- reg.exe (PID: 3932)
- reg.exe (PID: 1584)
- reg.exe (PID: 1936)
- reg.exe (PID: 3944)
- reg.exe (PID: 2272)
- reg.exe (PID: 3432)
- reg.exe (PID: 3560)
- reg.exe (PID: 1844)
- reg.exe (PID: 3544)
- findstr.exe (PID: 3984)
- sppsvc.exe (PID: 2232)
- reg.exe (PID: 1408)
- reg.exe (PID: 3136)
- reg.exe (PID: 3896)
- reg.exe (PID: 1640)
- reg.exe (PID: 3348)
- findstr.exe (PID: 2364)
- findstr.exe (PID: 1396)
- findstr.exe (PID: 1360)
- findstr.exe (PID: 2280)
- reg.exe (PID: 3196)
- reg.exe (PID: 3848)
- reg.exe (PID: 4076)
- reg.exe (PID: 2712)
- reg.exe (PID: 3300)
- reg.exe (PID: 932)
- reg.exe (PID: 2076)
- reg.exe (PID: 564)
- reg.exe (PID: 3104)
- net.exe (PID: 3488)
- net1.exe (PID: 3752)
- reg.exe (PID: 2544)
- reg.exe (PID: 1872)
- find.exe (PID: 1192)
- find.exe (PID: 2852)
- find.exe (PID: 3028)
- find.exe (PID: 2288)
- find.exe (PID: 3792)
- find.exe (PID: 3384)
- find.exe (PID: 2532)
- find.exe (PID: 2968)
- findstr.exe (PID: 1372)
- sc.exe (PID: 2700)
- sc.exe (PID: 3356)
- find.exe (PID: 1600)
- find.exe (PID: 1980)
- find.exe (PID: 1592)
- find.exe (PID: 2132)
- find.exe (PID: 1932)
- sc.exe (PID: 3728)
- sc.exe (PID: 2240)
- find.exe (PID: 1452)
- sc.exe (PID: 3468)
- net1.exe (PID: 3760)
- find.exe (PID: 1872)
- net.exe (PID: 2276)
- sc.exe (PID: 3456)
- find.exe (PID: 1640)
- reg.exe (PID: 2936)
- find.exe (PID: 1364)
- net.exe (PID: 2804)
- net1.exe (PID: 3984)
- reg.exe (PID: 2356)
- reg.exe (PID: 3844)
- reg.exe (PID: 3192)
- reg.exe (PID: 3380)
- reg.exe (PID: 3112)
- reg.exe (PID: 3564)
- reg.exe (PID: 2704)
- reg.exe (PID: 1448)
- reg.exe (PID: 3068)
- reg.exe (PID: 1864)
- reg.exe (PID: 3944)
- reg.exe (PID: 3168)
- reg.exe (PID: 3860)
- reg.exe (PID: 3252)
- sc.exe (PID: 3276)
- reg.exe (PID: 3288)
- reg.exe (PID: 2680)
- reg.exe (PID: 3600)
- findstr.exe (PID: 4040)
- findstr.exe (PID: 3516)
- choice.exe (PID: 3276)
Reads the computer name
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 3296)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 4012)
- sc.exe (PID: 2572)
- sc.exe (PID: 3544)
- sc.exe (PID: 1880)
- sc.exe (PID: 3852)
- sc.exe (PID: 3456)
- sppsvc.exe (PID: 2232)
- net1.exe (PID: 3752)
- sc.exe (PID: 3728)
- sc.exe (PID: 2700)
- sc.exe (PID: 2240)
- sc.exe (PID: 3468)
- net1.exe (PID: 3760)
- sc.exe (PID: 3456)
- sc.exe (PID: 3356)
- net1.exe (PID: 3984)
- sc.exe (PID: 3276)
Changes internet zones settings
- iexplore.exe (PID: 2976)
Checks Windows Trust Settings
- iexplore.exe (PID: 2976)
- iexplore.exe (PID: 3476)
- powershell.exe (PID: 2504)
- cscript.exe (PID: 3564)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 3528)
- powershell.exe (PID: 2784)
Reads internet explorer settings
- iexplore.exe (PID: 3476)
Reads settings of System Certificates
- iexplore.exe (PID: 3476)
- iexplore.exe (PID: 2976)
- chrome.exe (PID: 4004)
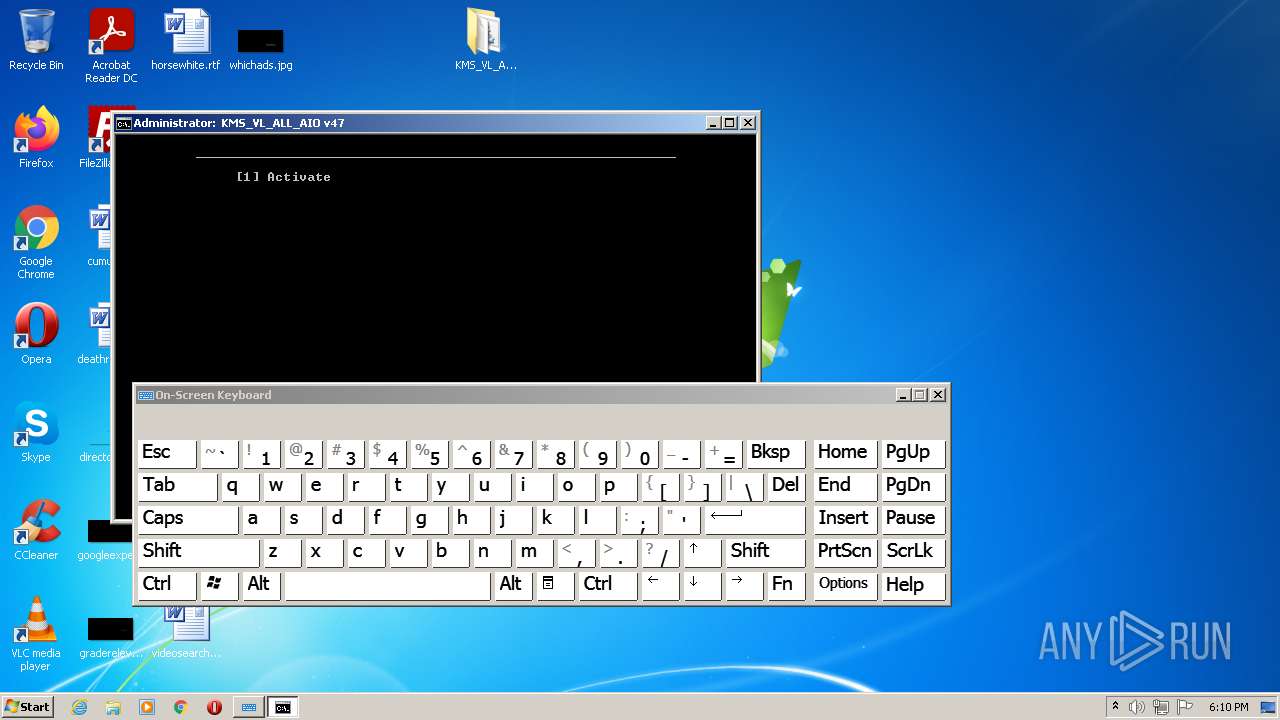
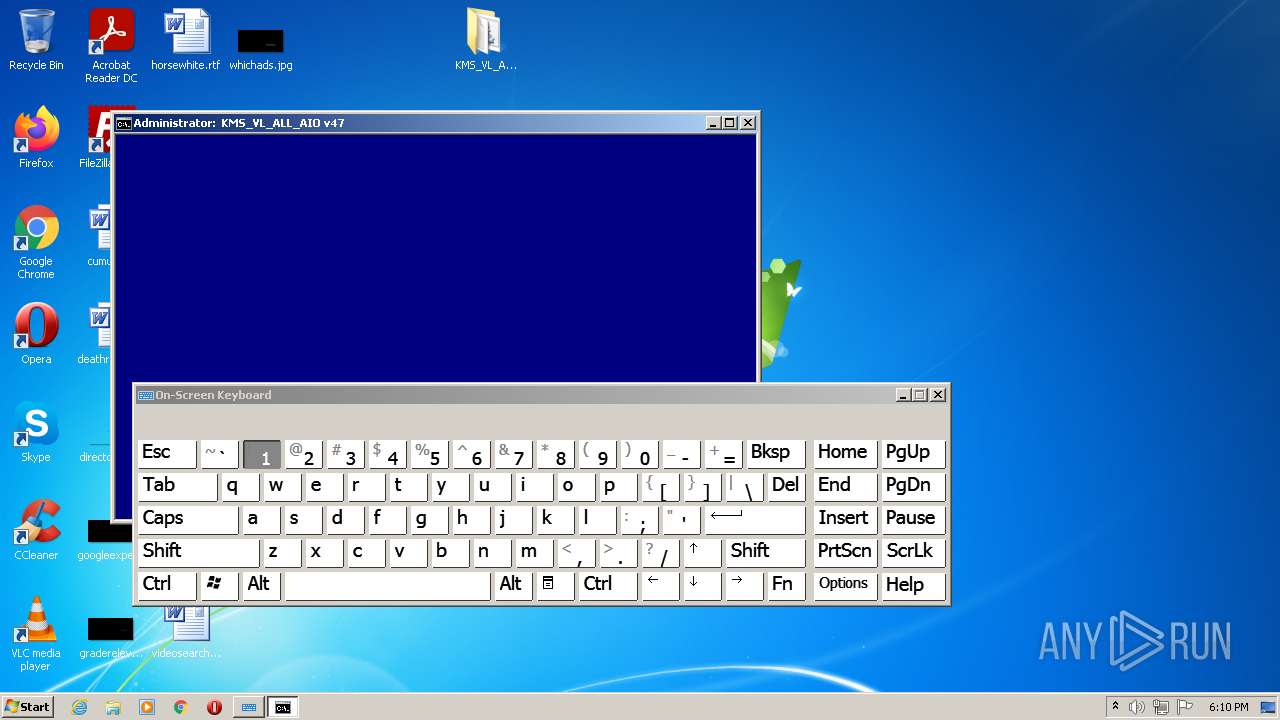
Manual execution by user
- osk.exe (PID: 1012)
- chrome.exe (PID: 3296)
- osk.exe (PID: 3516)
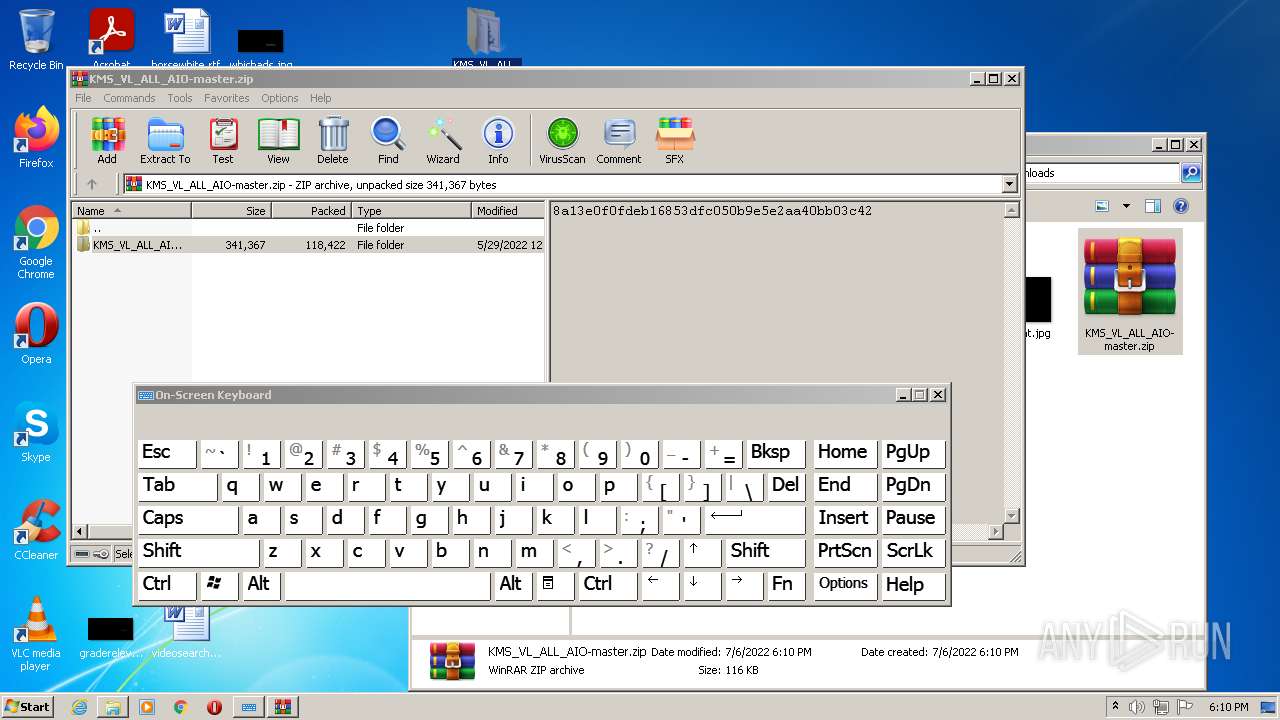
- WinRAR.exe (PID: 2084)
- cmd.exe (PID: 736)
Reads the hosts file
- chrome.exe (PID: 3296)
- chrome.exe (PID: 4004)
Creates files in the user directory
- iexplore.exe (PID: 2976)
Reads the date of Windows installation
- iexplore.exe (PID: 2976)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2976)
- sppsvc.exe (PID: 2232)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2976)
Changes settings of System certificates
- iexplore.exe (PID: 2976)
Reads Microsoft Office registry keys
- reg.exe (PID: 3944)
- OSPPSVC.EXE (PID: 4060)
- reg.exe (PID: 3600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
246
Monitored processes
193
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | reg query HKU\S-1-5-19 | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 280 | C:\Windows\system32\cmd.exe /c ver | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,18336649952708441122,8779826525561439910,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3200 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 564 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v DisableKeyManagementServiceHostCaching | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
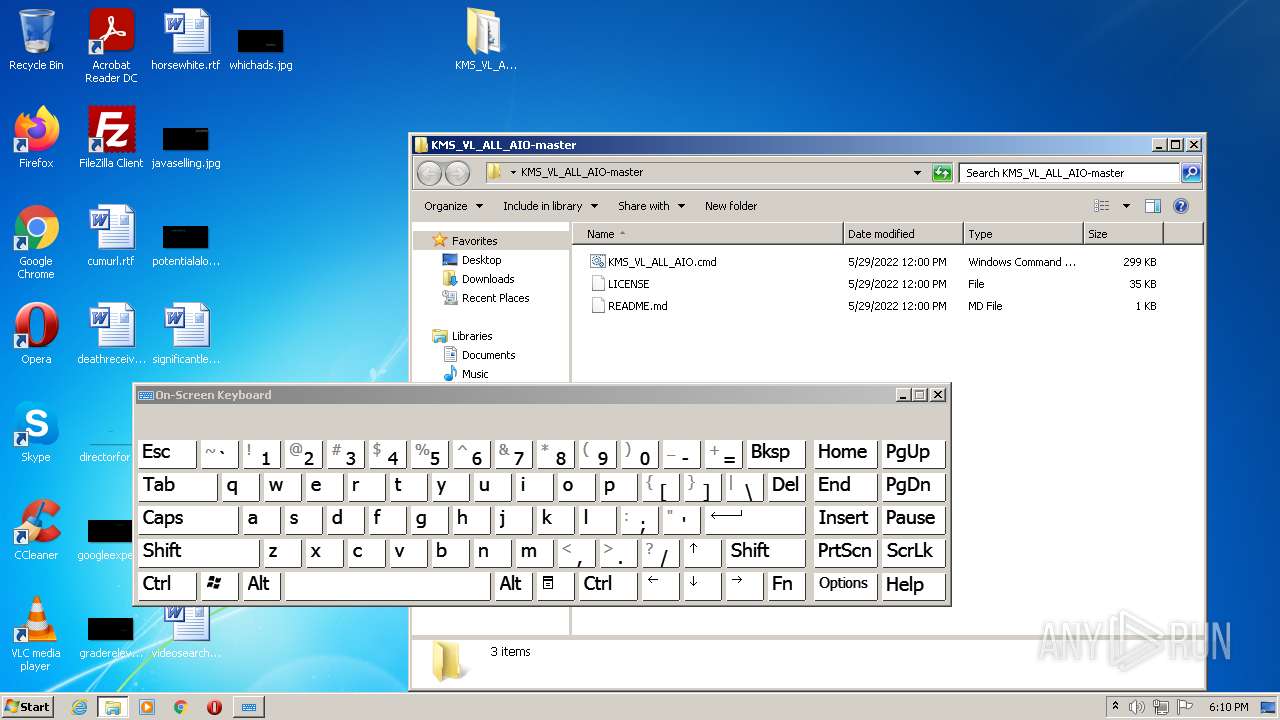
| 736 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\KMS_VL_ALL_AIO-master\KMS_VL_ALL_AIO.cmd" " | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 844 | reg query "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 892 | findstr /a:07 /f:`.txt "." | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 932 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v KeyManagementServicePort | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Windows\system32\osk.exe" | C:\Windows\system32\osk.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Accessibility On-Screen Keyboard Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | C:\Windows\system32\cmd.exe /c "reg query HKLM\SOFTWARE\Microsoft\Office\15.0\Common\InstallRoot /v Path" 2>nul | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
35 920
Read events
35 616
Write events
291
Delete events
13
Modification events
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 217968912 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30970203 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 517971412 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30970203 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
164
Text files
146
Unknown types
24
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3296 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62C5C1D7-CE0.pma | — | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | der | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | binary | |
MD5:— | SHA256:— | |||
| 3476 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 2976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
55
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAUYmlTr6MfpA%2BCrDZJVRd4%3D | US | der | 314 b | whitelisted |
2976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
4004 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 591 b | whitelisted |
2976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3476 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
2976 | iexplore.exe | GET | 200 | 8.252.42.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?828d55acd2f71243 | US | compressed | 4.70 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 8.252.42.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?445c0246080af403 | US | compressed | 4.70 Kb | whitelisted |
4004 | chrome.exe | GET | 200 | 74.125.100.103:80 | http://r2---sn-5hnekn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=157.97.122.3&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1657127075&mv=m&mvi=2&pl=24&rmhost=r5---sn-5hnekn7z.gvt1.com&shardbypass=sd&smhost=r5---sn-5hneknes.gvt1.com | US | crx | 242 Kb | whitelisted |
2976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3476 | iexplore.exe | GET | 200 | 8.252.74.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?22d680452c1be668 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3476 | iexplore.exe | 8.252.42.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2976 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2976 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2976 | iexplore.exe | 8.252.42.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3476 | iexplore.exe | 8.252.74.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3476 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4004 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2976 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 140.82.121.9:443 | codeload.github.com | — | US | suspicious |
4004 | chrome.exe | 142.250.184.196:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
codeload.github.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |