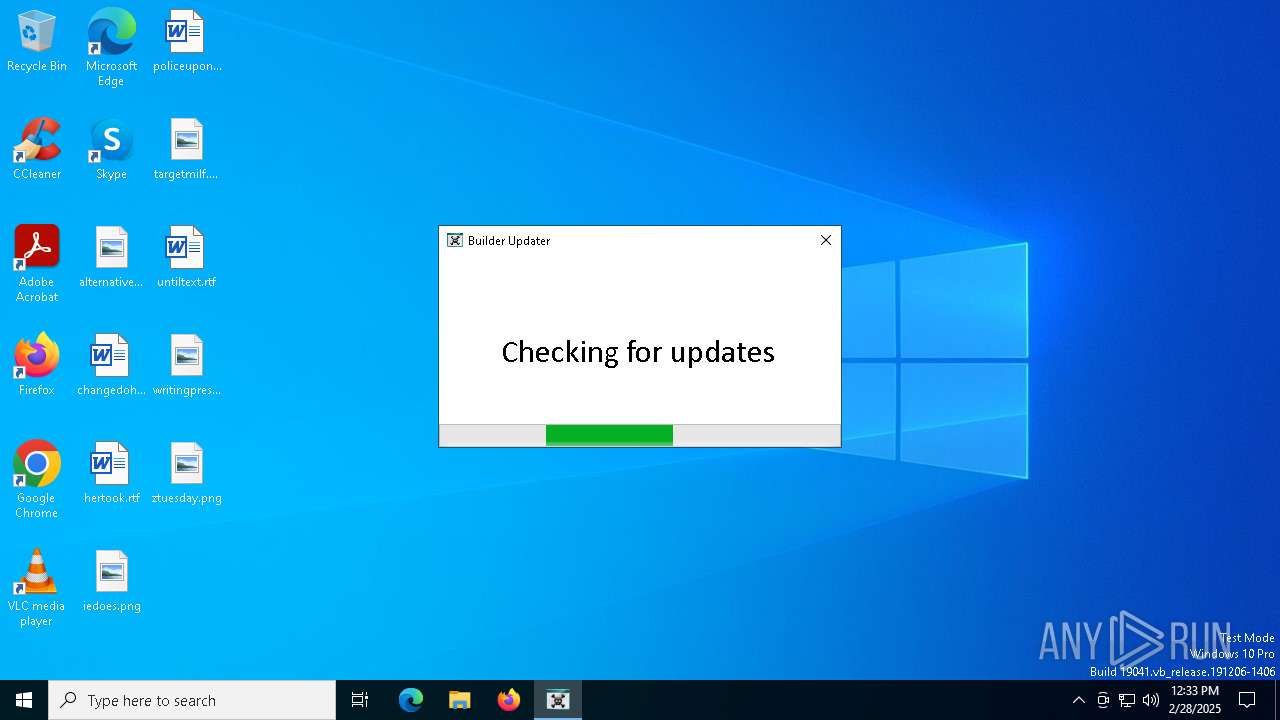
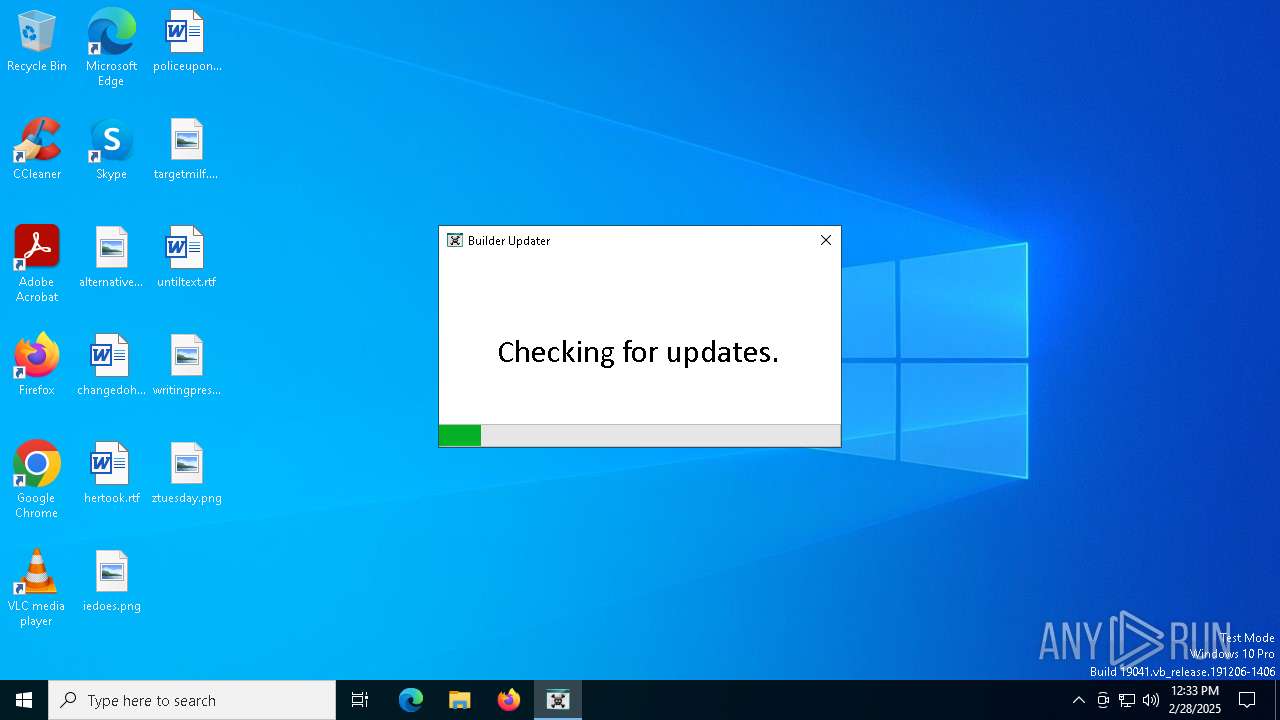
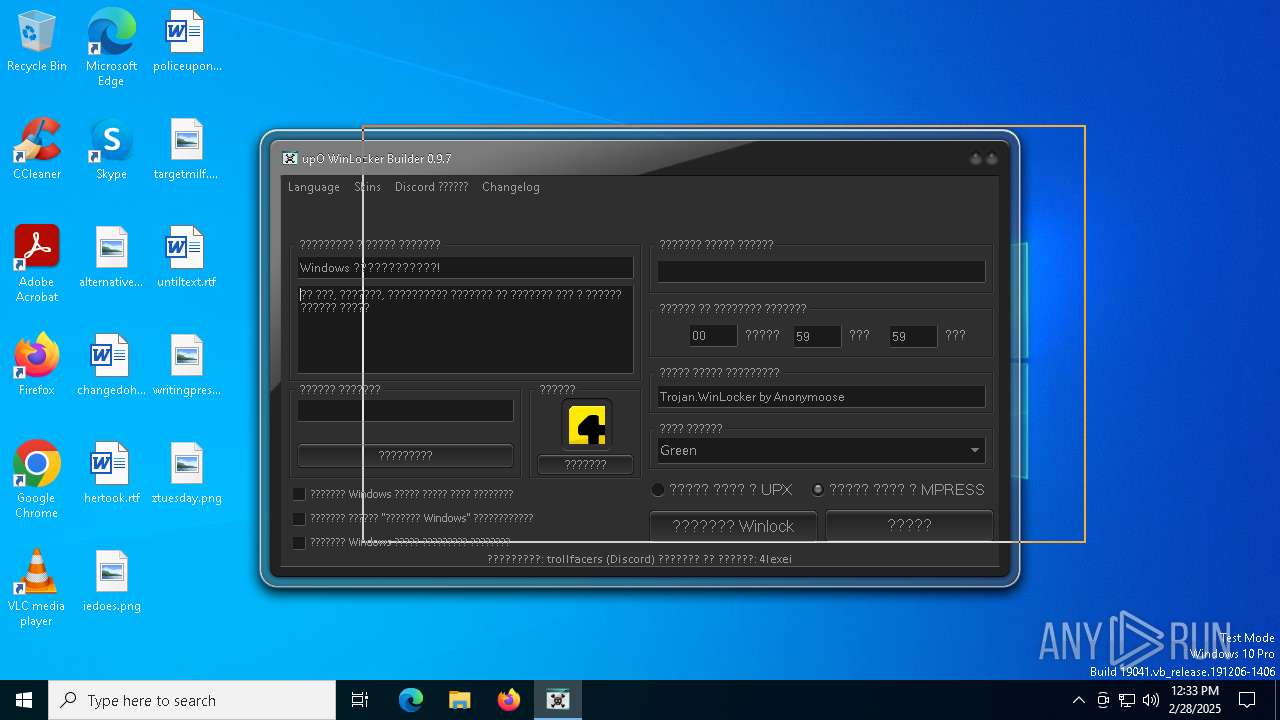
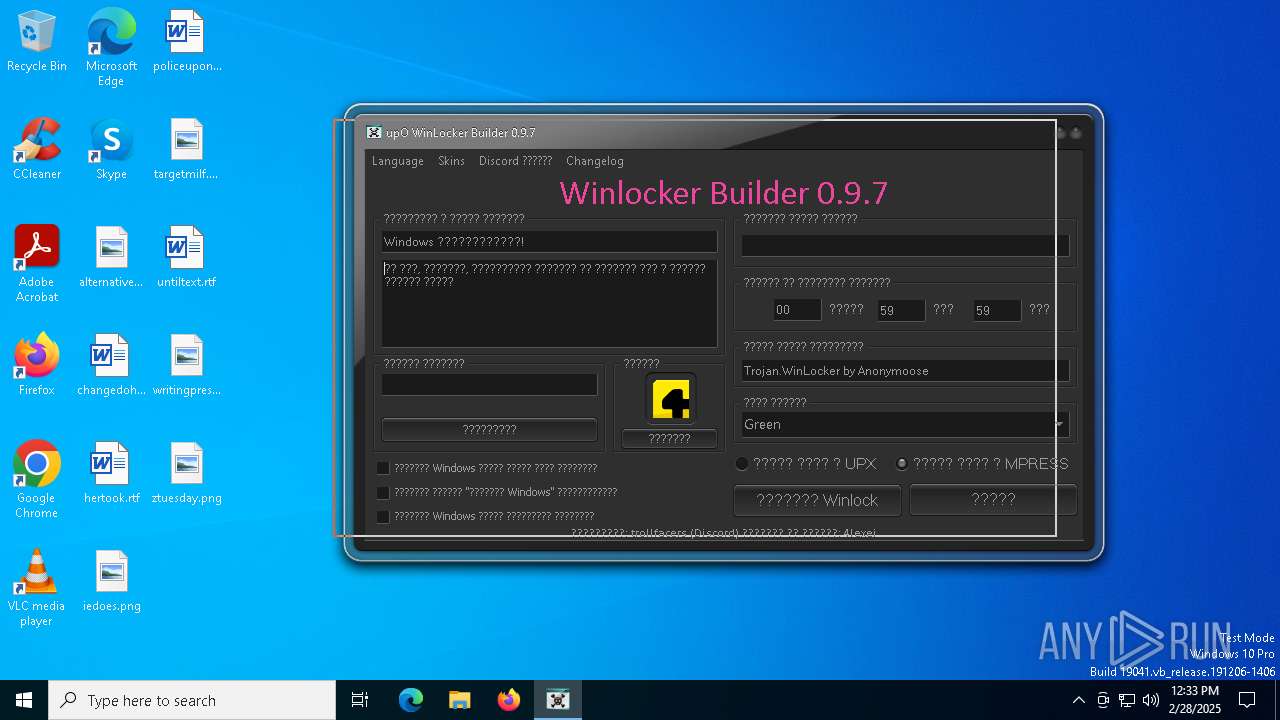
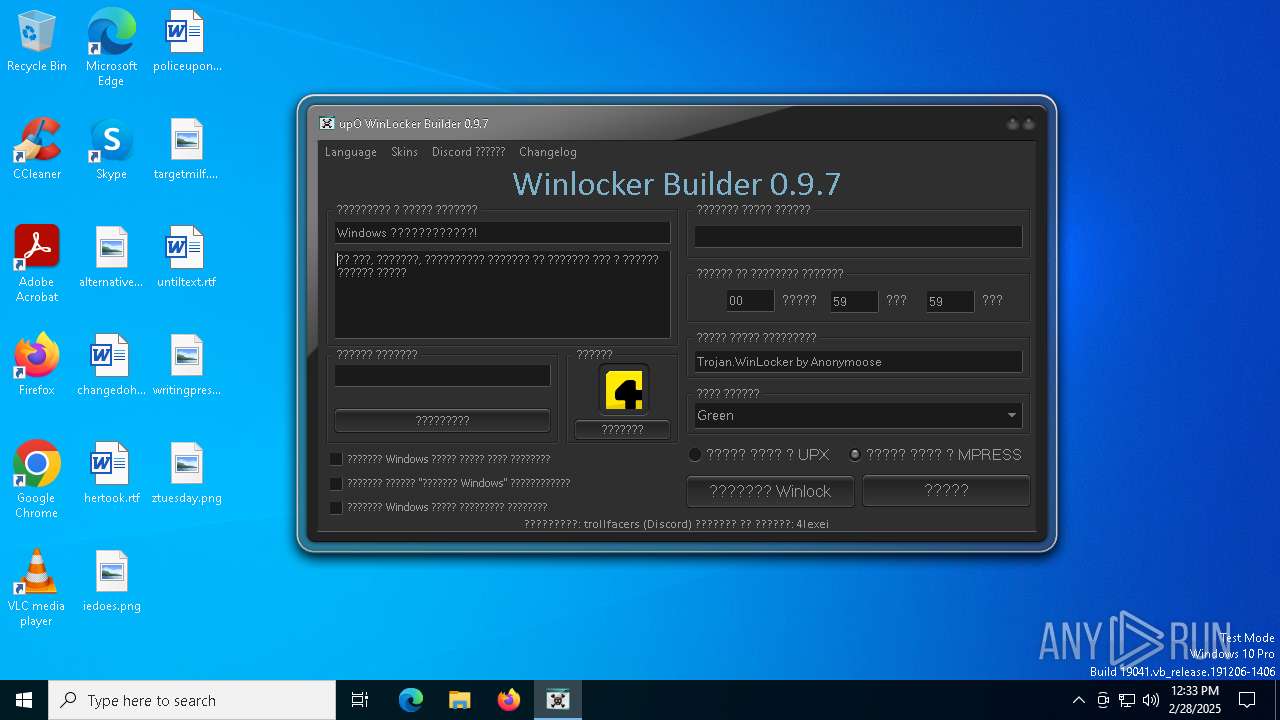
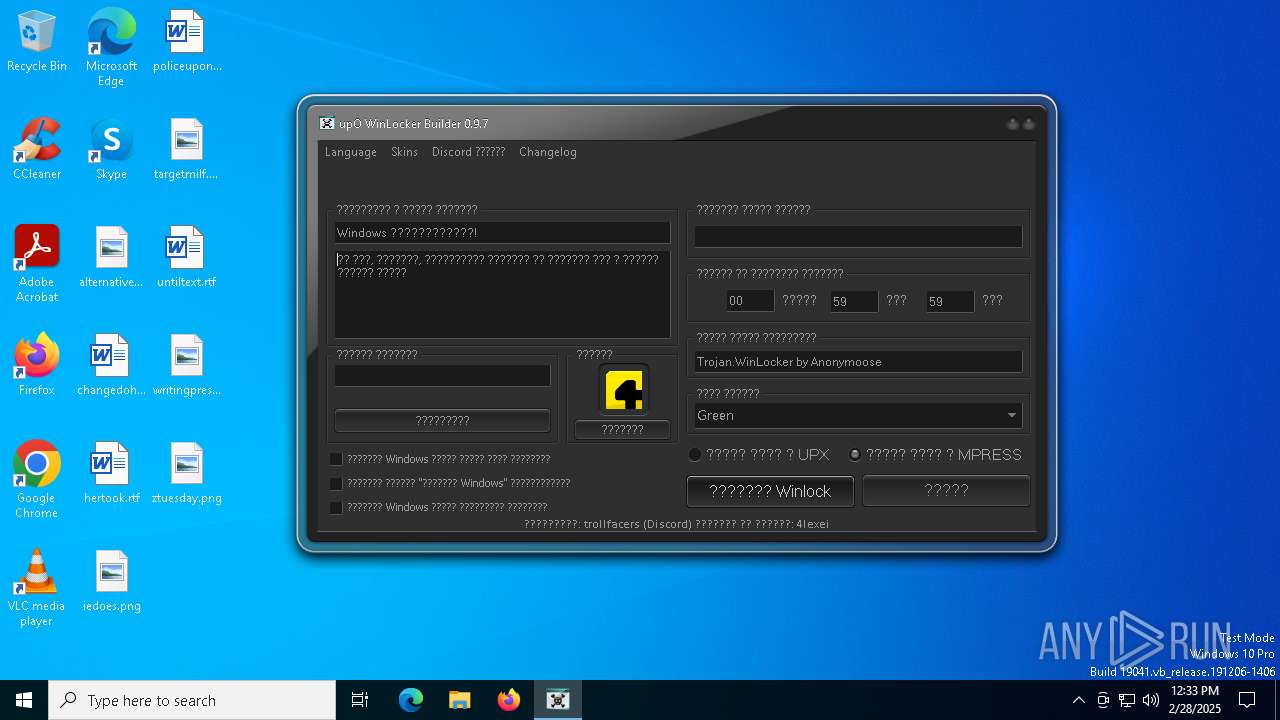
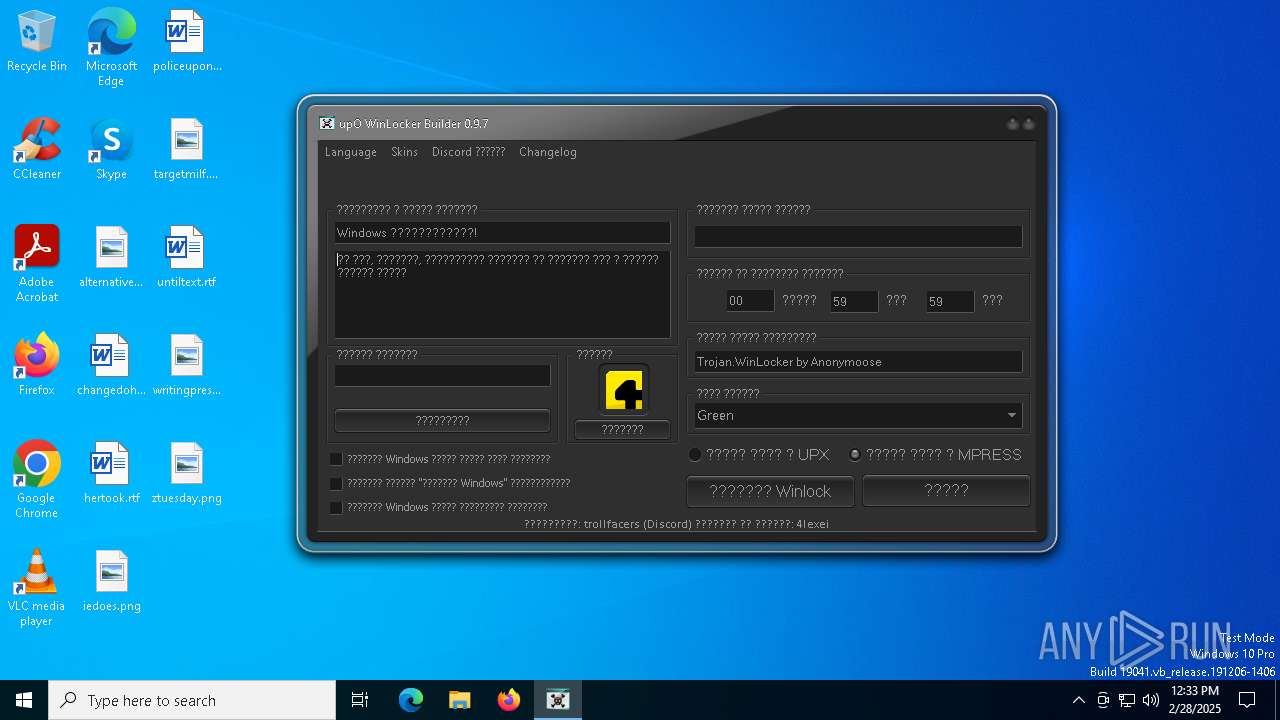
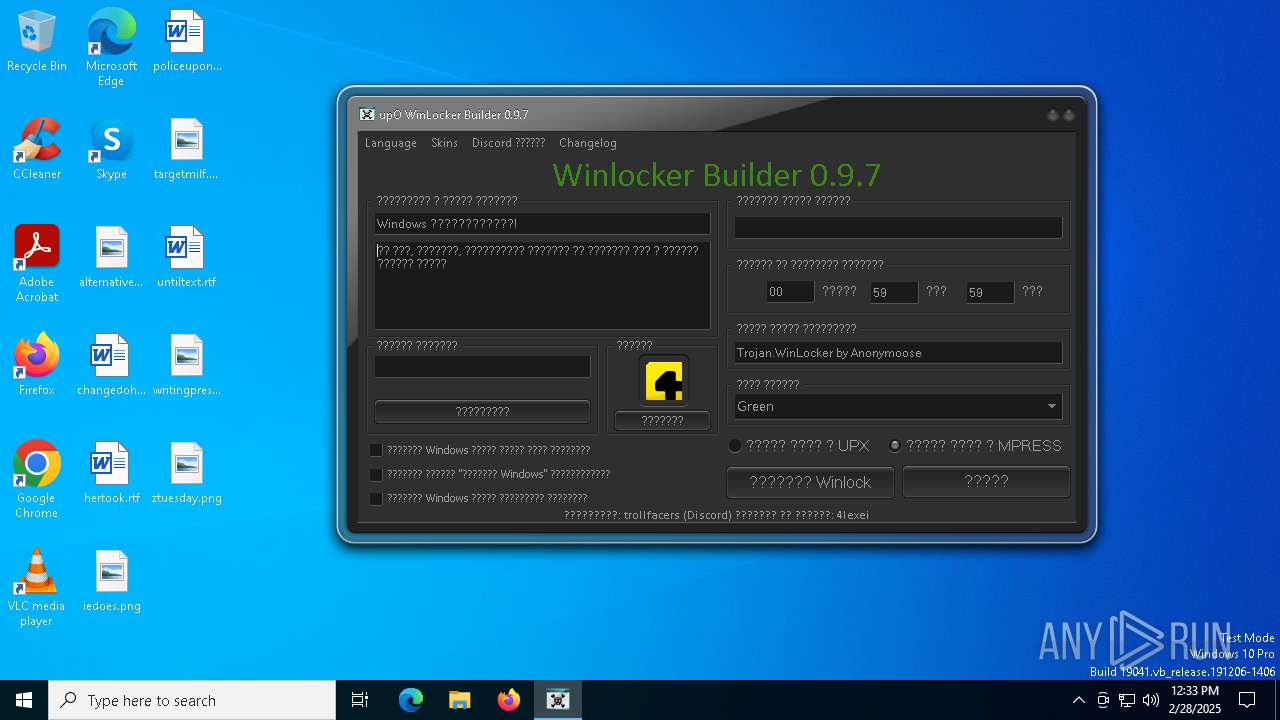
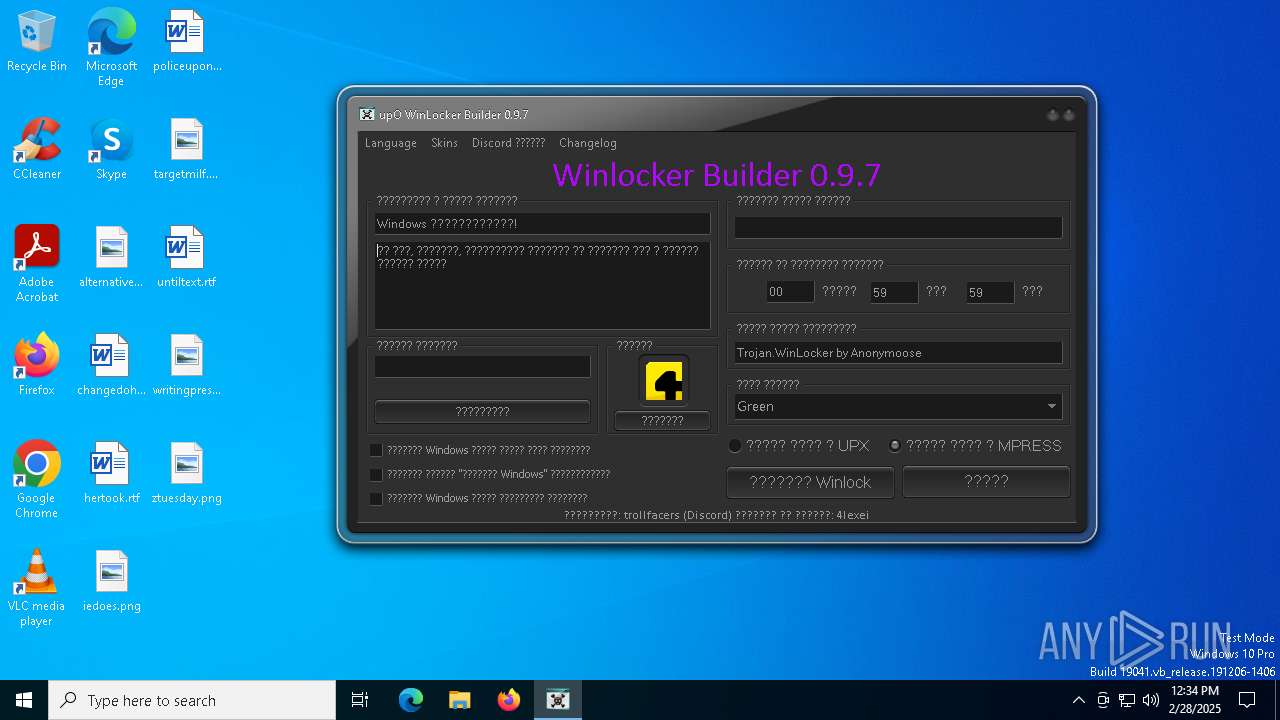
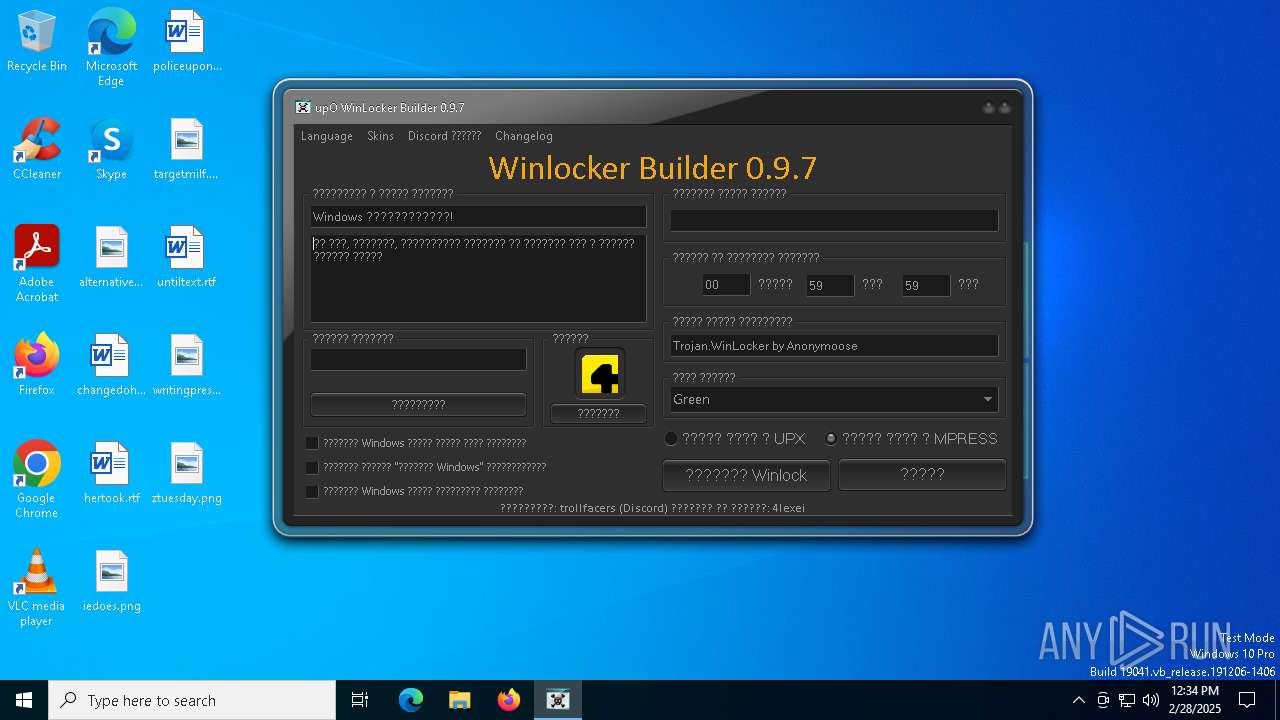
| File name: | upO Builder 0.9.7.exe |
| Full analysis: | https://app.any.run/tasks/5a7de8b4-37db-4fac-9ae4-a400fa7d29fd |
| Verdict: | Malicious activity |
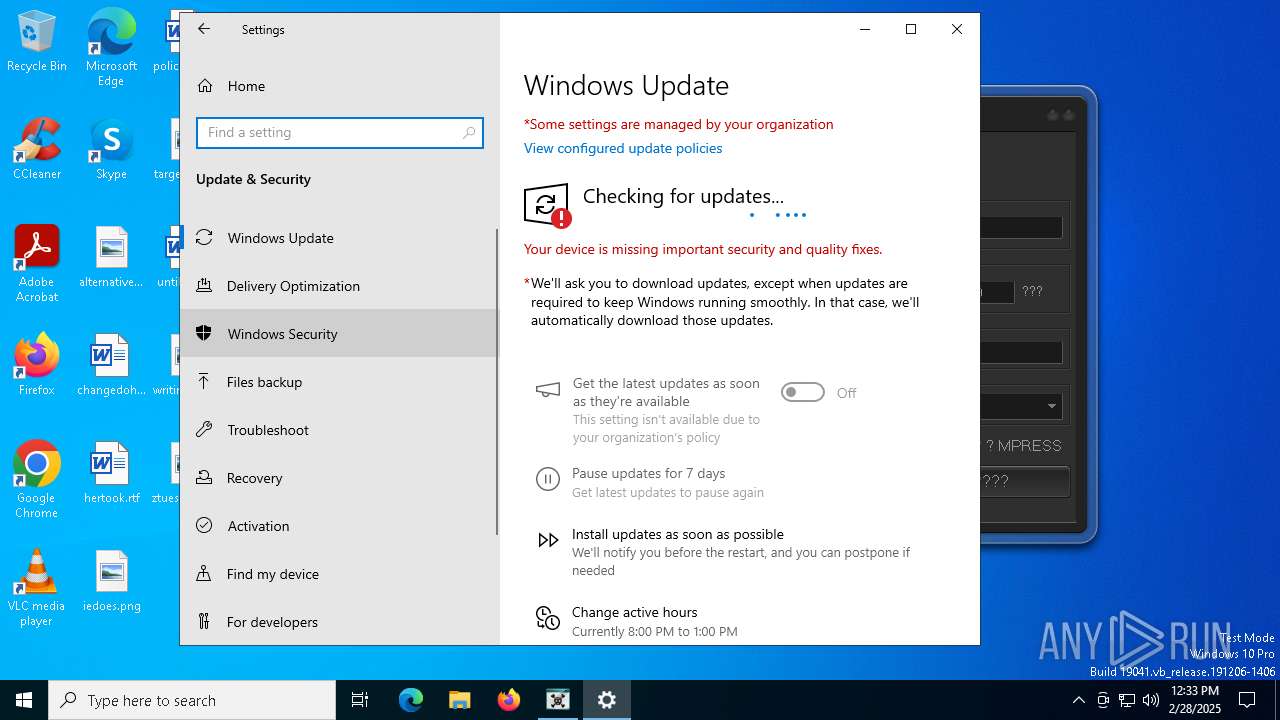
| Analysis date: | February 28, 2025, 12:33:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | A6B3B0EF9A6EE3C74315A2B8C573E5C8 |
| SHA1: | 80B75A960A383A824E48DD196416517E7E0525EC |
| SHA256: | 49E993C3C40C13C28E32C53E90DDE544665CF47FF43D418B7CBA94FDF37DB82D |
| SSDEEP: | 98304:+dzqzuHHrPnxMc4SdrIRTjM6h36MUwYLushXnhlCJydCp5foTW8UhJAhdeGOvRwj:rZfI |
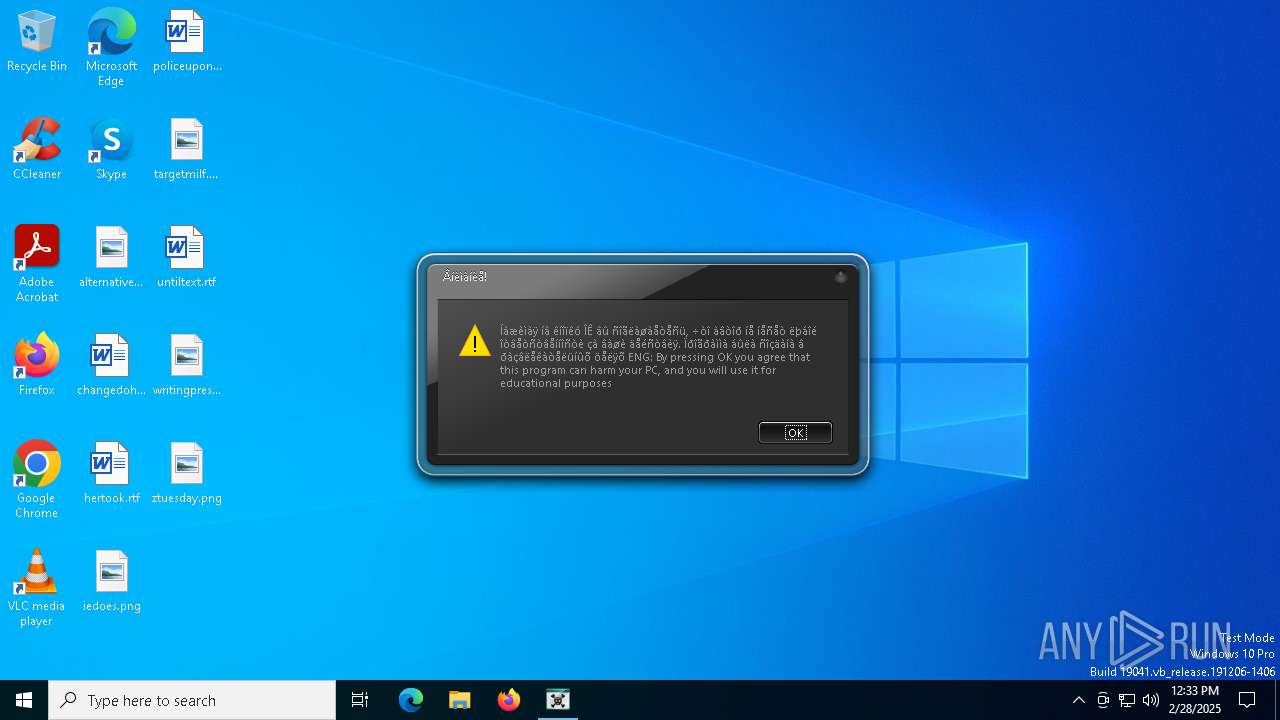
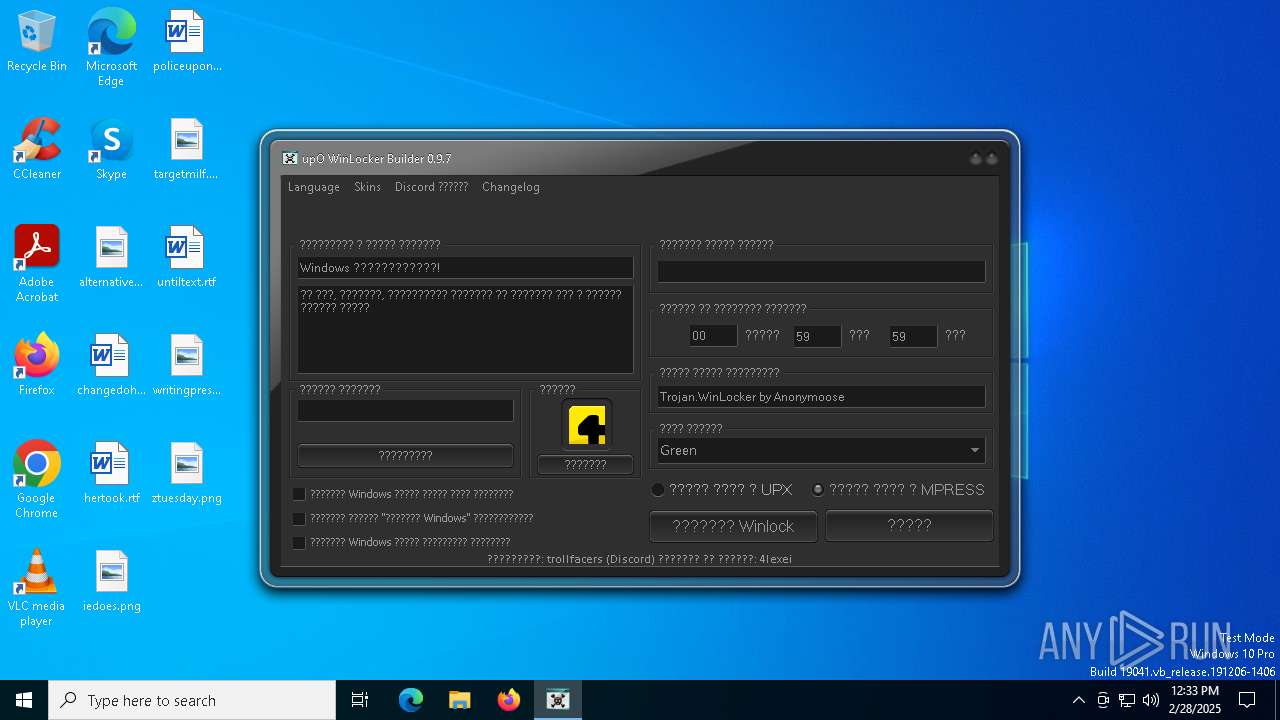
MALICIOUS
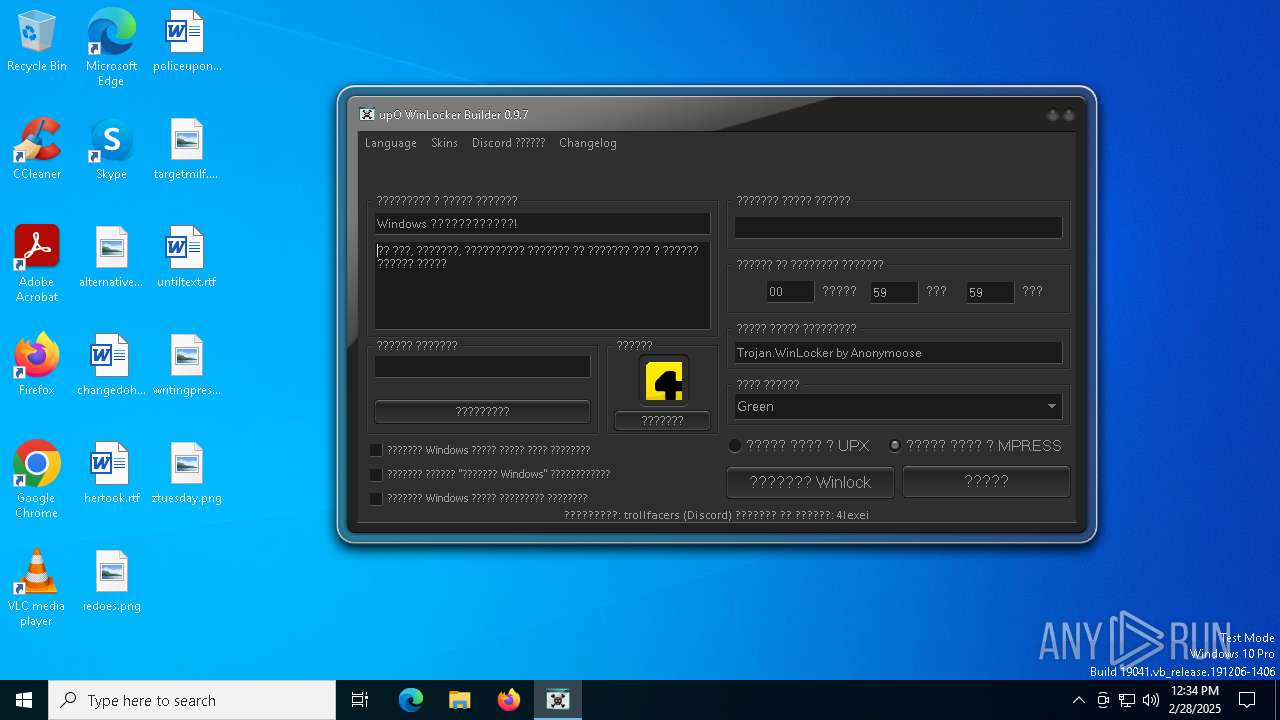
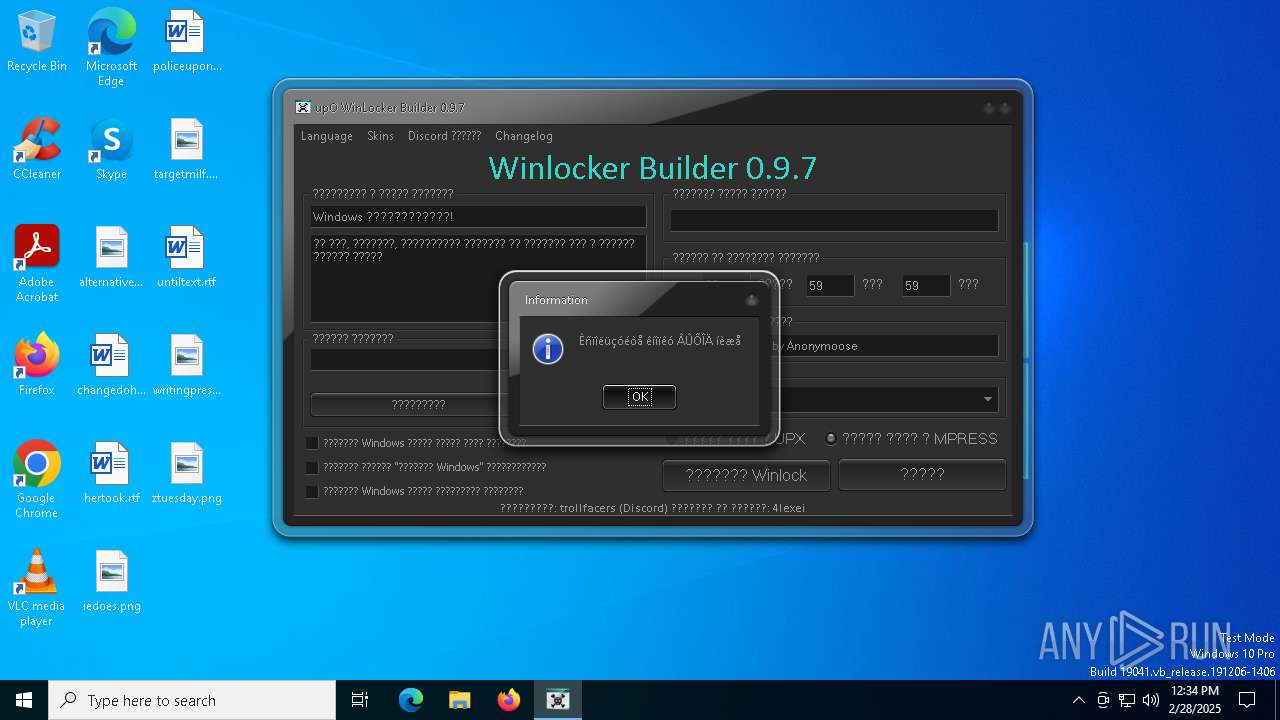
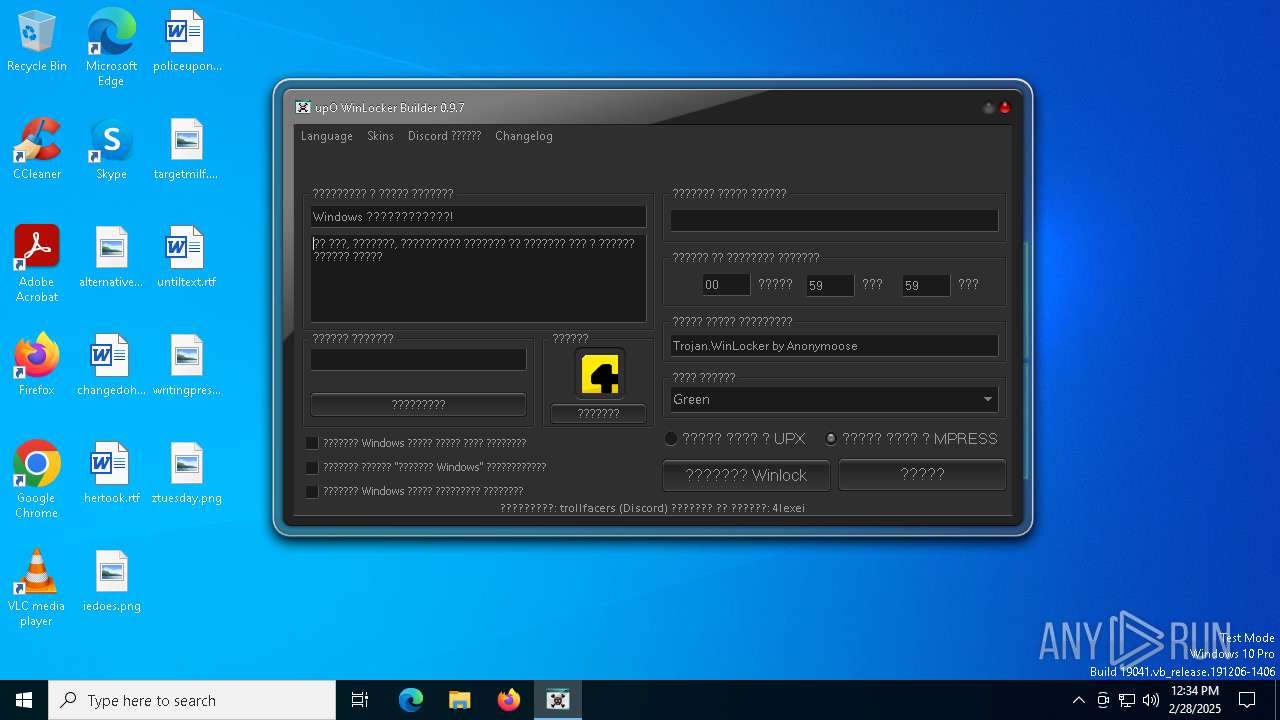
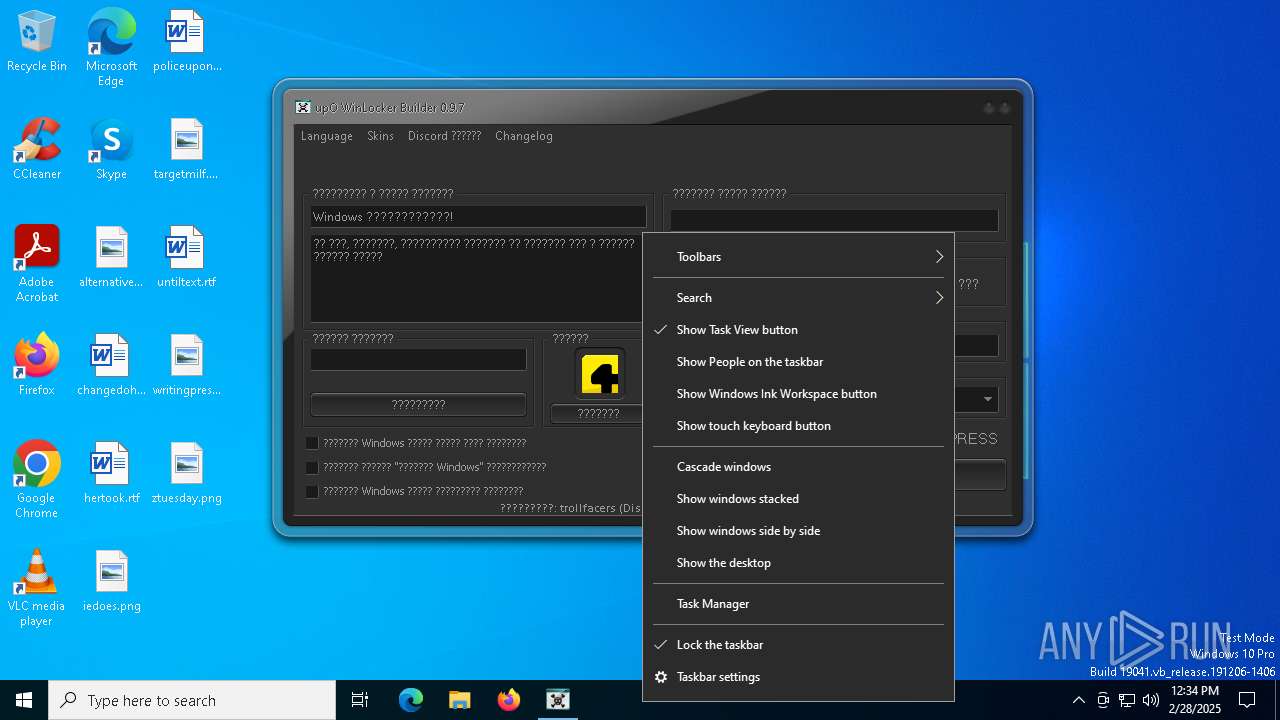
WINLOCKER has been detected (YARA)
- upO Builder.exe (PID: 7692)
SUSPICIOUS
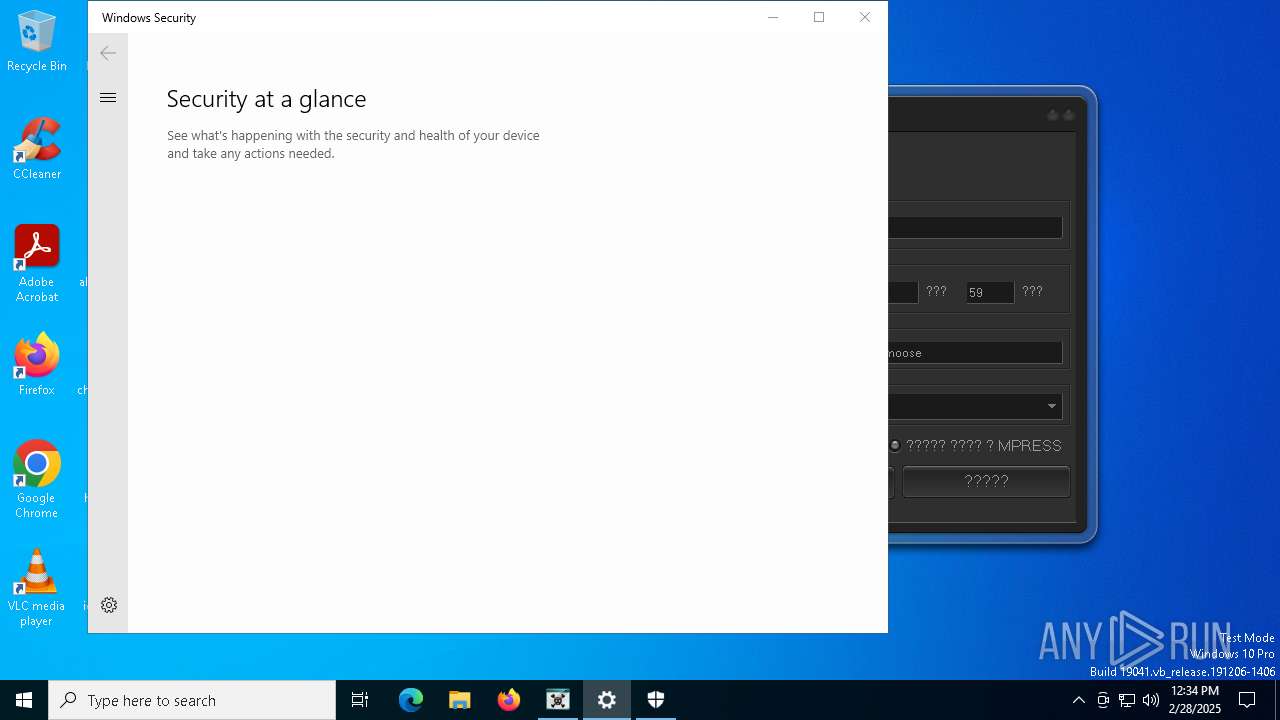
Reads security settings of Internet Explorer
- upO Builder 0.9.7.exe (PID: 7448)
- SecHealthUI.exe (PID: 6392)
There is functionality for VM detection VirtualBox (YARA)
- upO Builder.exe (PID: 7692)
There is functionality for VM detection VMWare (YARA)
- upO Builder.exe (PID: 7692)
Reads the date of Windows installation
- upO Builder 0.9.7.exe (PID: 7448)
There is functionality for taking screenshot (YARA)
- upO Builder.exe (PID: 7692)
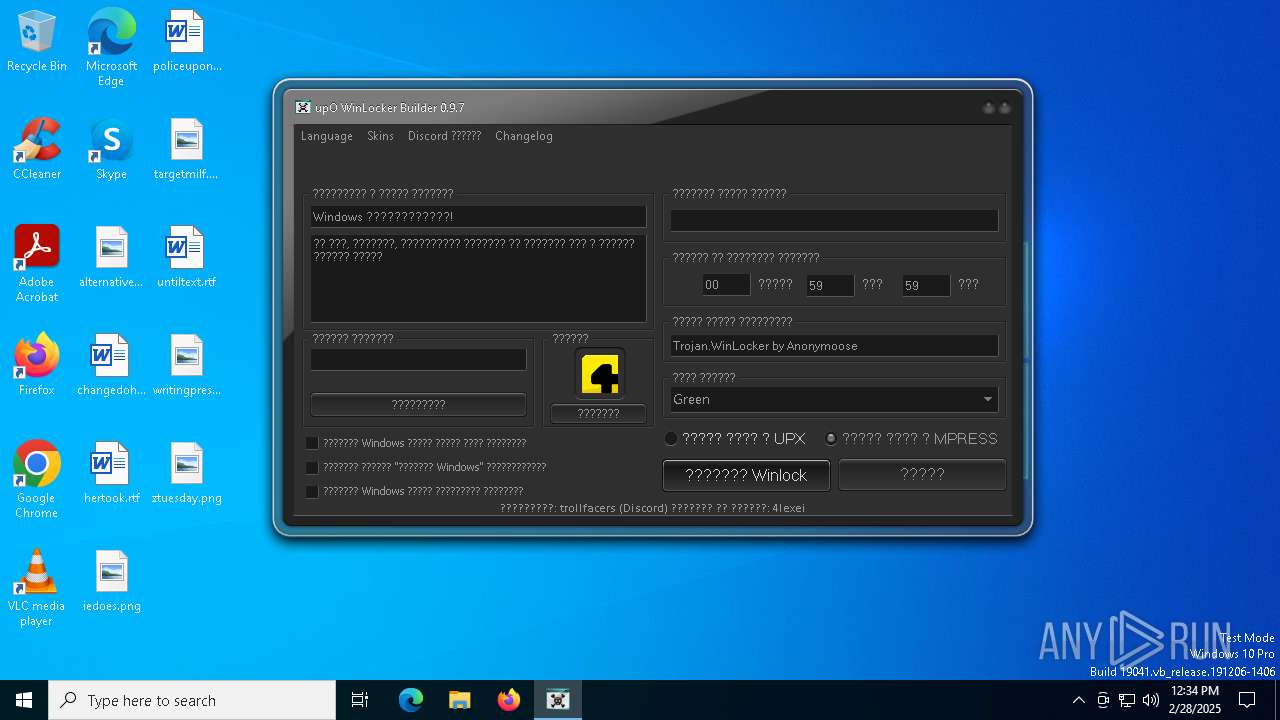
Executable content was dropped or overwritten
- upO Builder 0.9.7.exe (PID: 7448)
INFO
Reads the computer name
- upO Builder 0.9.7.exe (PID: 7448)
- upO Builder.exe (PID: 7692)
- SecHealthUI.exe (PID: 6392)
Checks proxy server information
- upO Builder 0.9.7.exe (PID: 7448)
Checks supported languages
- upO Builder 0.9.7.exe (PID: 7448)
- SecHealthUI.exe (PID: 6392)
- upO Builder.exe (PID: 7692)
Creates files or folders in the user directory
- upO Builder 0.9.7.exe (PID: 7448)
Disables trace logs
- upO Builder 0.9.7.exe (PID: 7448)
Process checks computer location settings
- upO Builder 0.9.7.exe (PID: 7448)
Mpress packer has been detected
- upO Builder.exe (PID: 7692)
Compiled with Borland Delphi (YARA)
- upO Builder.exe (PID: 7692)
Reads the software policy settings
- upO Builder 0.9.7.exe (PID: 7448)
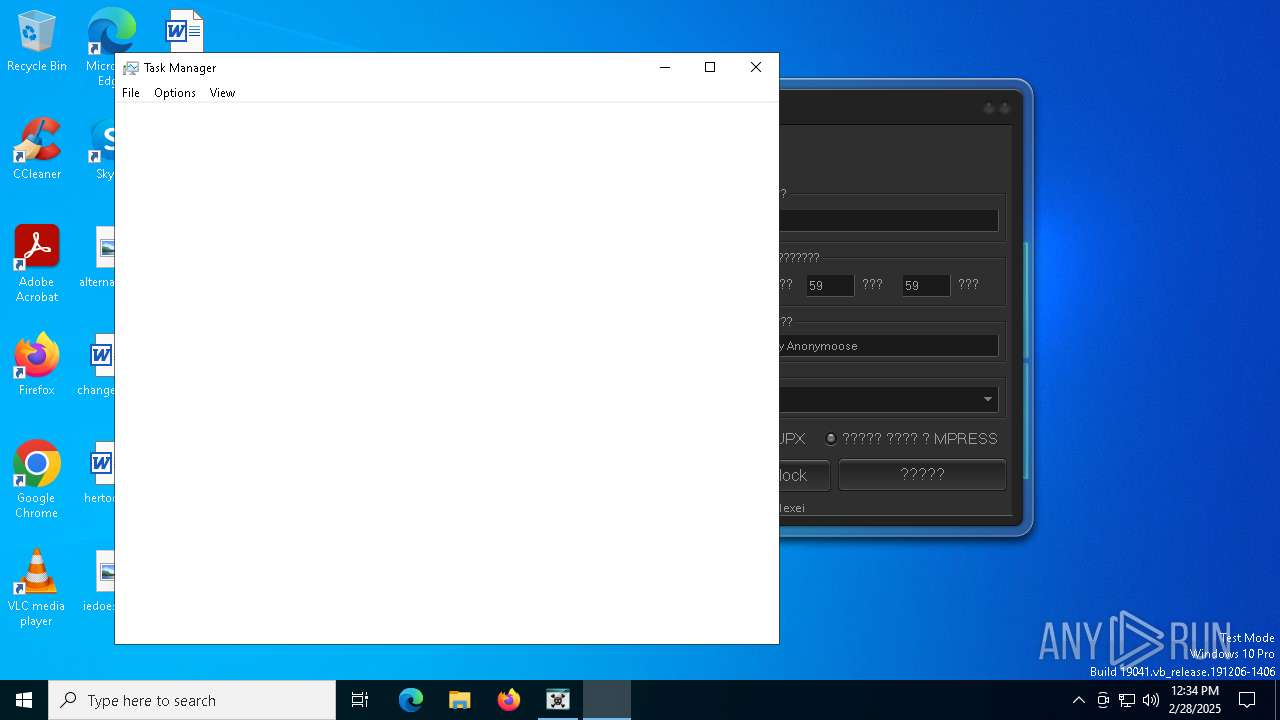
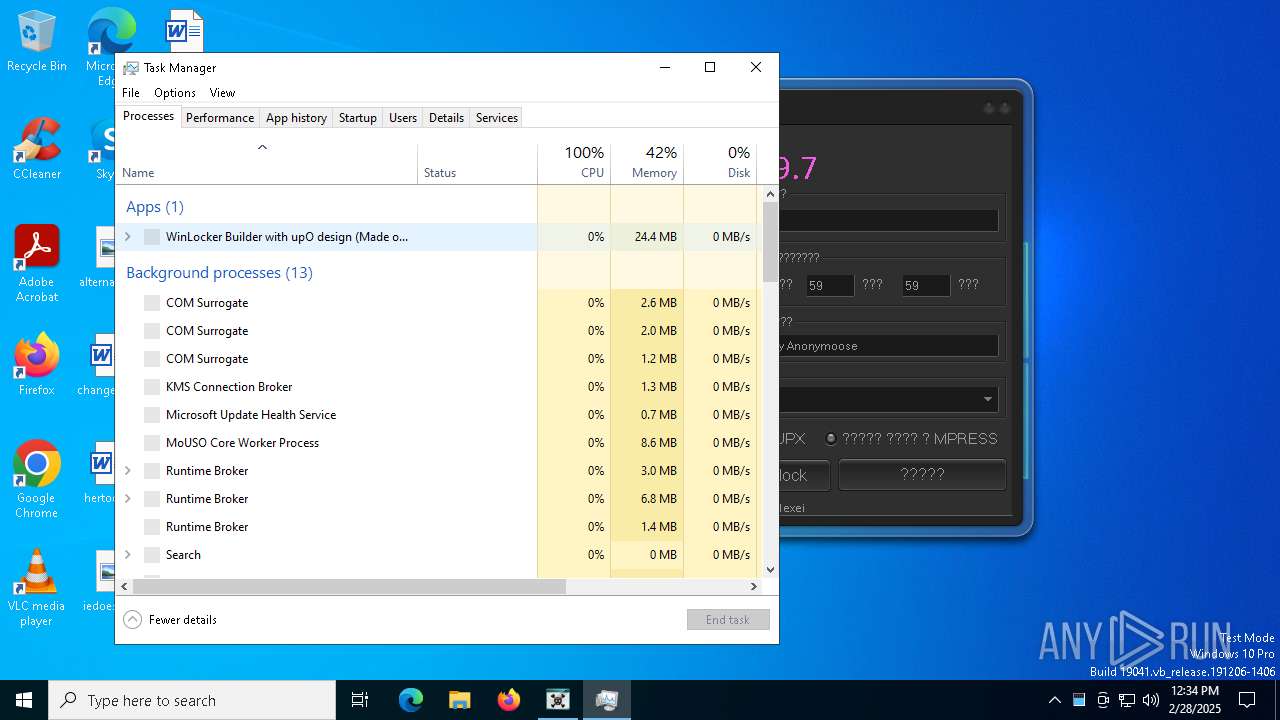
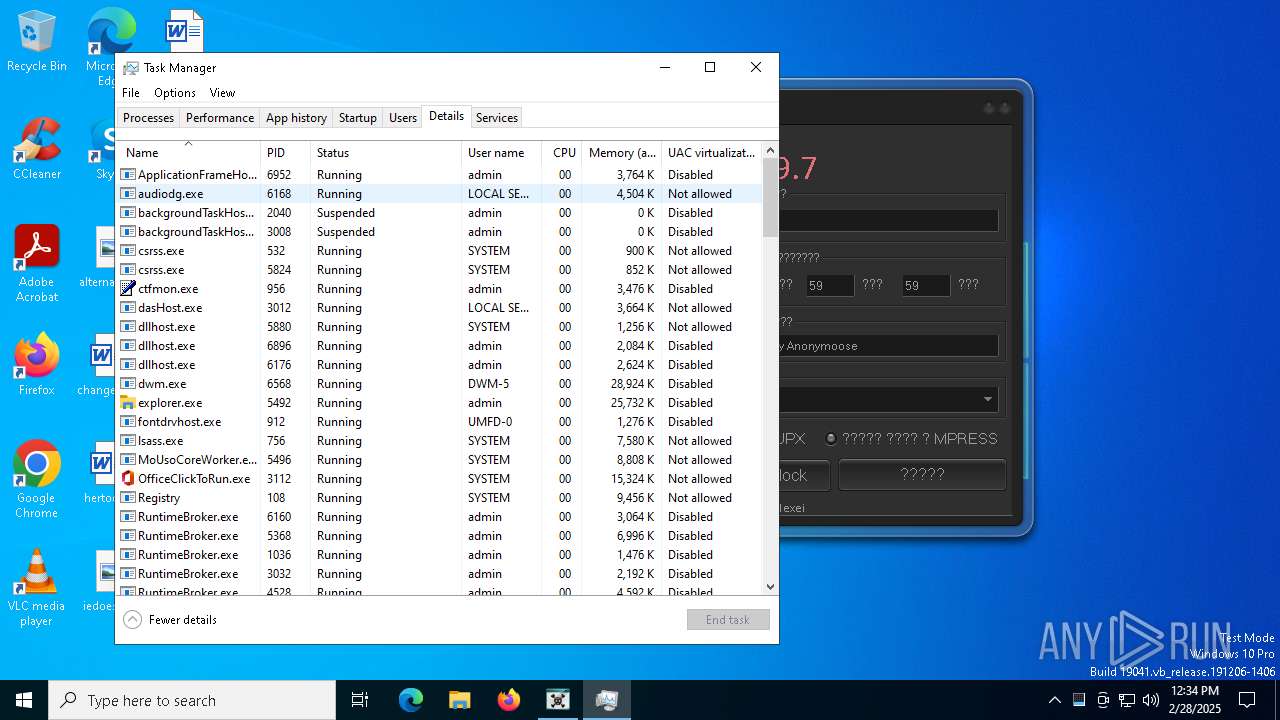
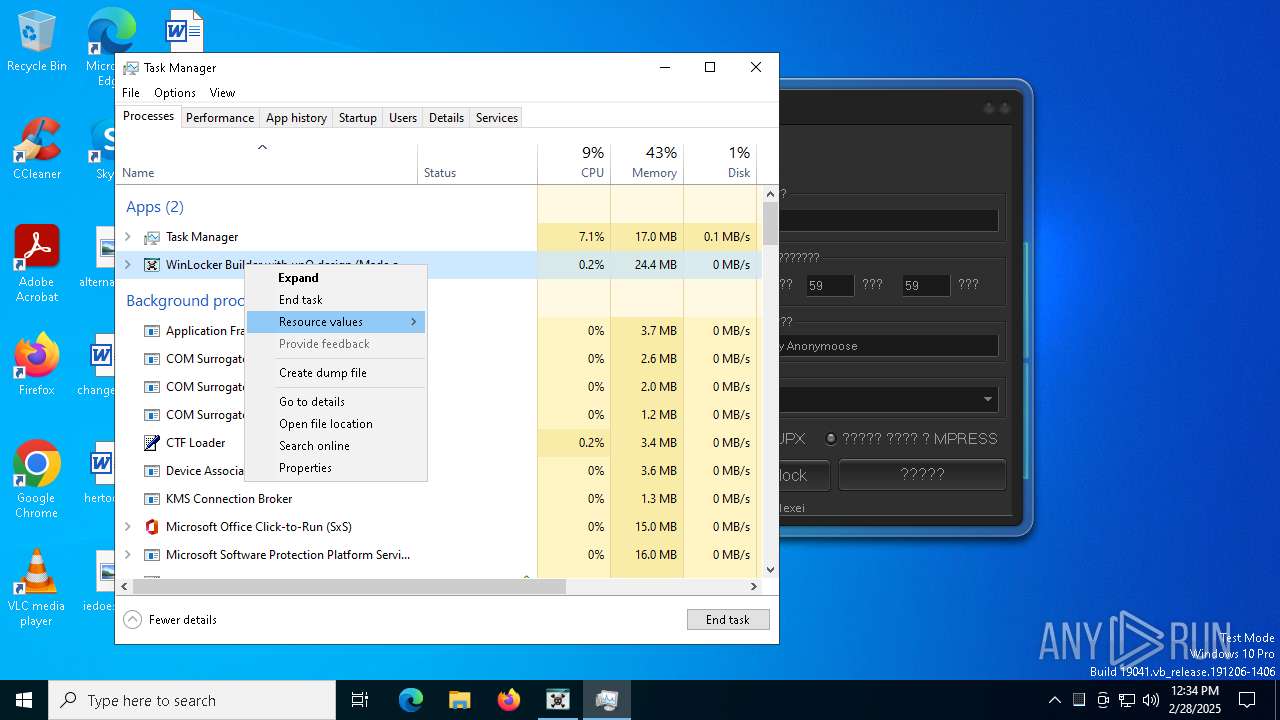
Manual execution by a user
- Taskmgr.exe (PID: 7896)
- Taskmgr.exe (PID: 8120)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 8120)
UPX packer has been detected
- upO Builder.exe (PID: 7692)
Reads the machine GUID from the registry
- upO Builder 0.9.7.exe (PID: 7448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:09 18:58:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.7.0 |
| ProductVersionNumber: | 0.9.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Updater |
| CompanyName: | sumhex |
| FileDescription: | Updater for upO Builder |
| FileVersion: | 0.9.7.0 |
| InternalName: | LockerBuilderUpdate.exe |
| LegalCopyright: | sumhex |
| LegalTrademarks: | - |
| OriginalFileName: | LockerBuilderUpdate.exe |
| ProductName: | Updater |
| ProductVersion: | 0.9.7.0 |
| AssemblyVersion: | 0.9.7.0 |
Total processes
153
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1272 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5056 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | "C:\WINDOWS\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe" -ServerName:SecHealthUI.AppXep4x2tbtjws1v9qqs0rmb3hxykvkpqtn.mca | C:\Windows\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender application Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7356 | "C:\Users\admin\AppData\Local\Temp\upO Builder 0.9.7.exe" | C:\Users\admin\AppData\Local\Temp\upO Builder 0.9.7.exe | — | explorer.exe | |||||||||||
User: admin Company: sumhex Integrity Level: MEDIUM Description: Updater for upO Builder Exit code: 3221226540 Version: 0.9.7.0 Modules
| |||||||||||||||
| 7448 | "C:\Users\admin\AppData\Local\Temp\upO Builder 0.9.7.exe" | C:\Users\admin\AppData\Local\Temp\upO Builder 0.9.7.exe | explorer.exe | ||||||||||||
User: admin Company: sumhex Integrity Level: HIGH Description: Updater for upO Builder Exit code: 0 Version: 0.9.7.0 Modules
| |||||||||||||||
| 7508 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7540 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7640 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
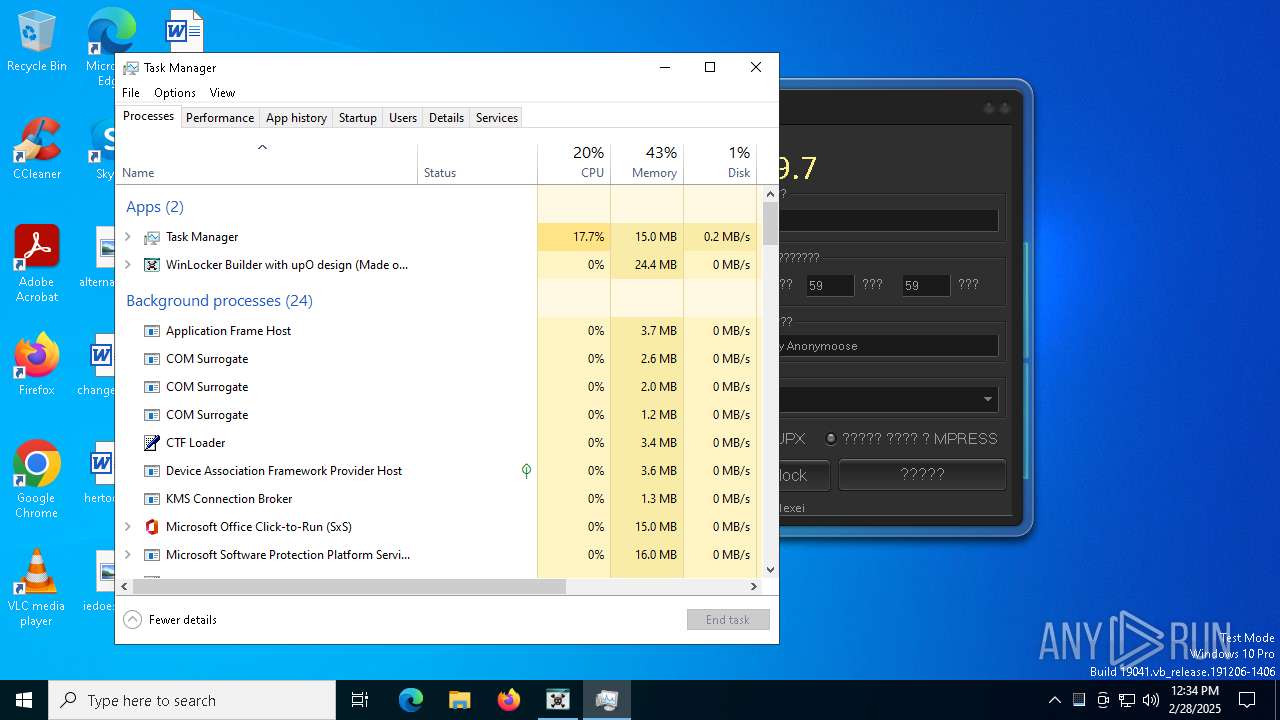
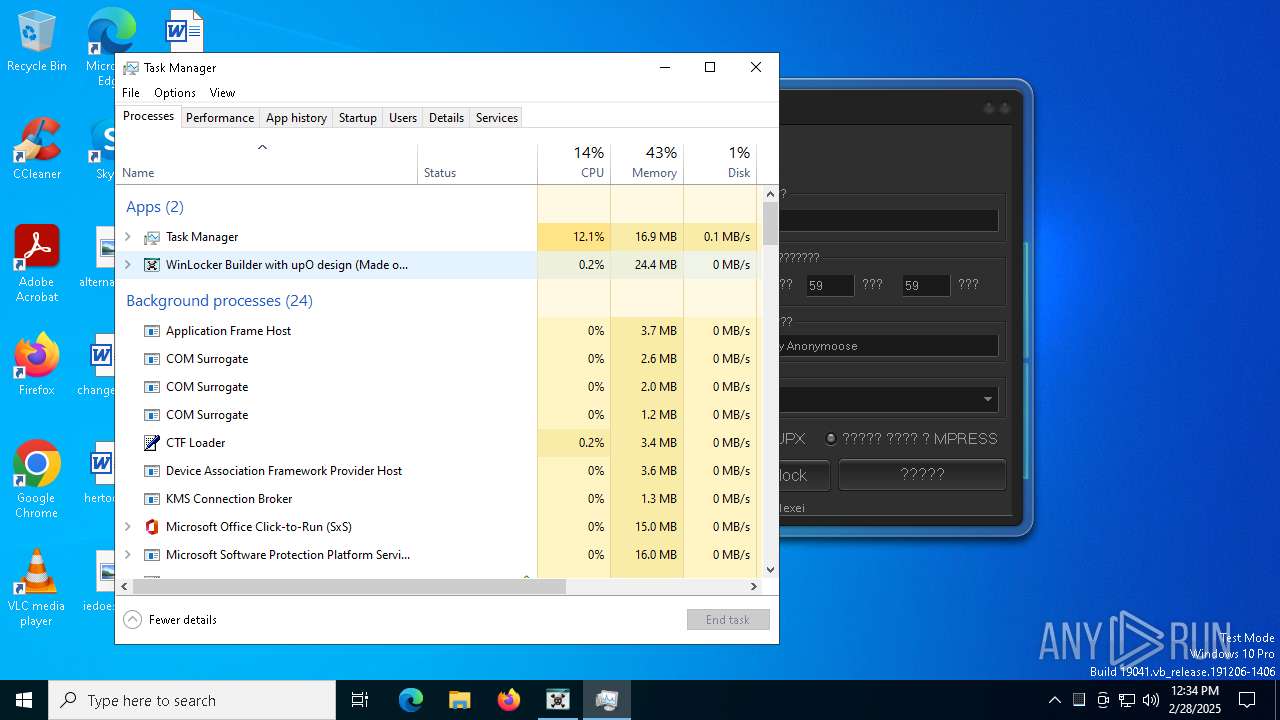
| 7692 | "C:\Users\admin\AppData\upO Builder.exe" | C:\Users\admin\AppData\upO Builder.exe | upO Builder 0.9.7.exe | ||||||||||||
User: admin Company: sumhex Integrity Level: HIGH Description: WinLocker Builder with upO design (Made on Delphi) Version: 1.0.0.0 Modules
| |||||||||||||||
| 7836 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 817
Read events
4 800
Write events
16
Delete events
1
Modification events
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7448) upO Builder 0.9.7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\upO Builder 0_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7448 | upO Builder 0.9.7.exe | C:\Users\admin\AppData\upO Builder.exe | executable | |
MD5:042B657C73AE1A47383D2BE31FA66B5E | SHA256:F6A4C7BFA61AEA65250174F3AB0C3D087F5082DC902B137DE686E42DA0952F2D | |||
| 8120 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
30
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8052 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8052 | SIHClient.exe | GET | 200 | 2.16.253.202:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4156 | SystemSettings.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7448 | upO Builder 0.9.7.exe | 185.199.111.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3008 | backgroundTaskHost.exe | 2.16.204.157:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
cxcs.microsoft.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |