| File name: | privatadocs.exe |
| Full analysis: | https://app.any.run/tasks/50398584-609d-42e7-8e45-39b03b0a0c07 |
| Verdict: | Malicious activity |
| Analysis date: | May 19, 2025, 17:01:00 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | A6B3B0EF9A6EE3C74315A2B8C573E5C8 |
| SHA1: | 80B75A960A383A824E48DD196416517E7E0525EC |
| SHA256: | 49E993C3C40C13C28E32C53E90DDE544665CF47FF43D418B7CBA94FDF37DB82D |
| SSDEEP: | 98304:+dzqzuHHrPnxMc4SdrIRTjM6h36MUwYLushXnhlCJydCp5foTW8UhJAhdeGOvRwj:rZfI |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- privatadocs.exe (PID: 6124)
Reads settings of System Certificates
- privatadocs.exe (PID: 6124)
There is functionality for taking screenshot (YARA)
- privatadocs.exe (PID: 6124)
INFO
Disables trace logs
- privatadocs.exe (PID: 6124)
Reads Environment values
- privatadocs.exe (PID: 6124)
Reads the machine GUID from the registry
- privatadocs.exe (PID: 6124)
Checks proxy server information
- privatadocs.exe (PID: 6124)
.NET Reactor protector has been detected
- privatadocs.exe (PID: 6124)
Reads the software policy settings
- privatadocs.exe (PID: 6124)
UPX packer has been detected
- privatadocs.exe (PID: 6124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:12:09 18:58:13+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 4096 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2e5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.7.0 |
| ProductVersionNumber: | 0.9.7.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
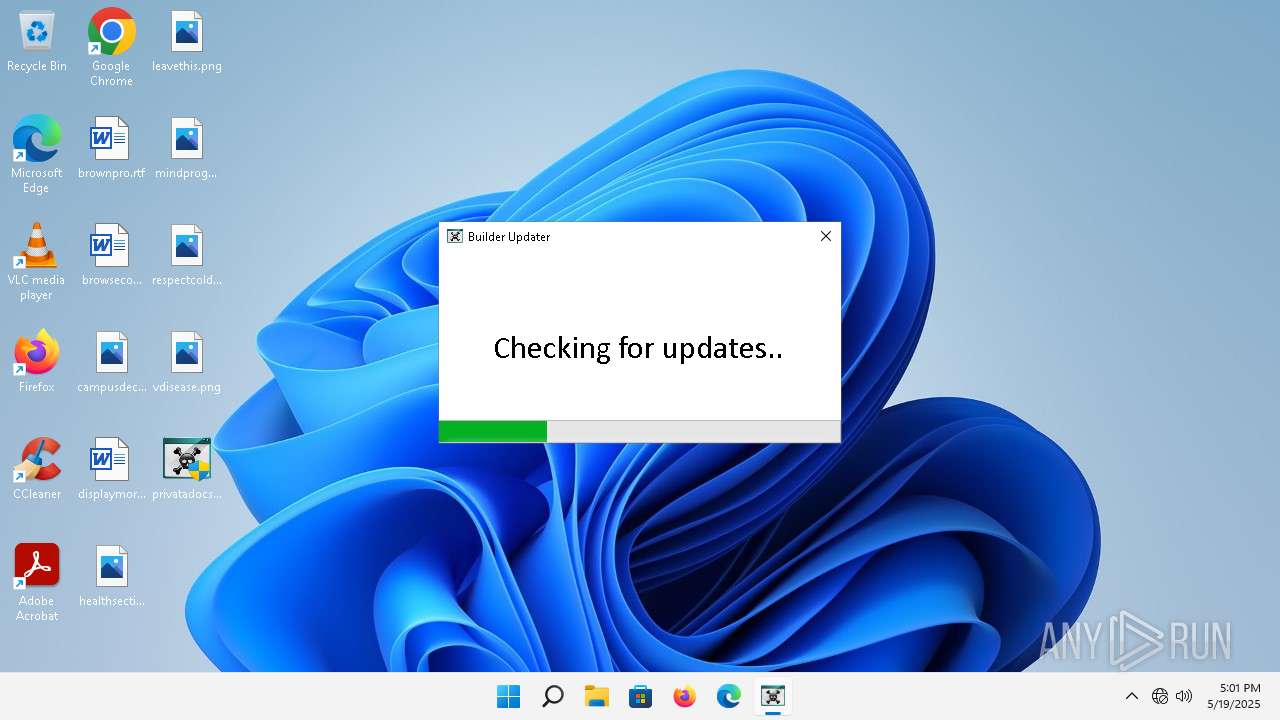
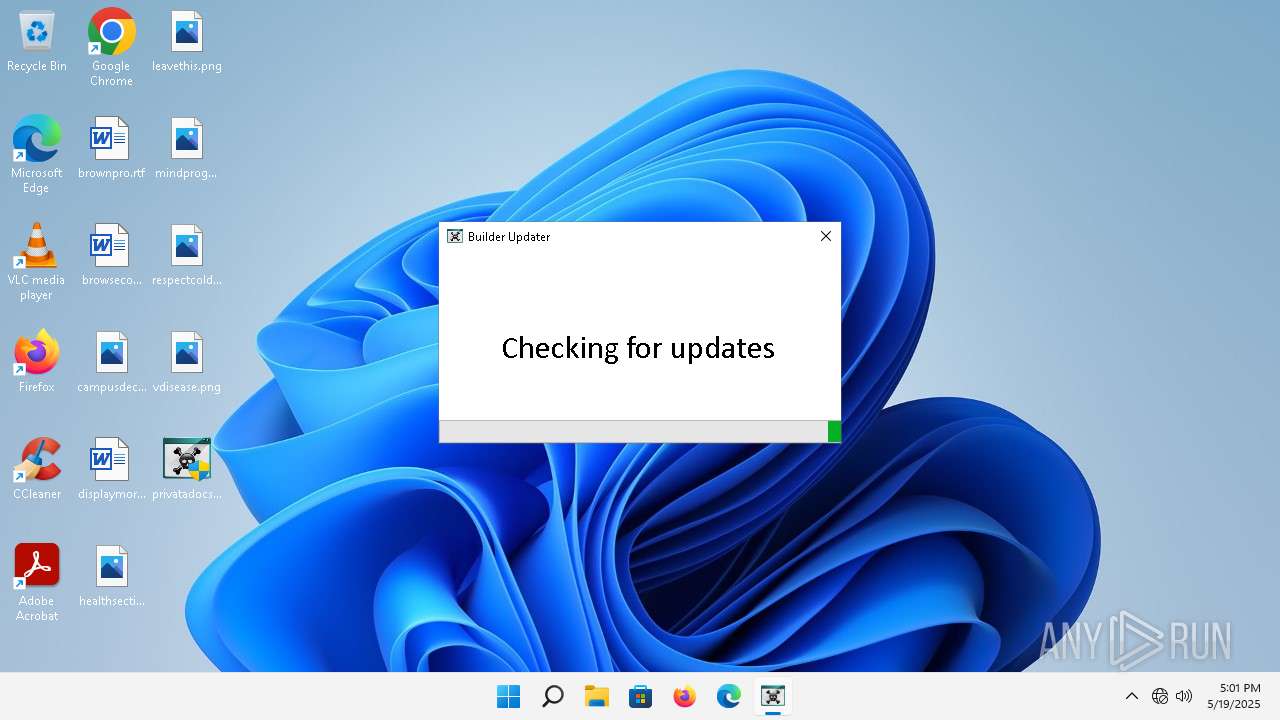
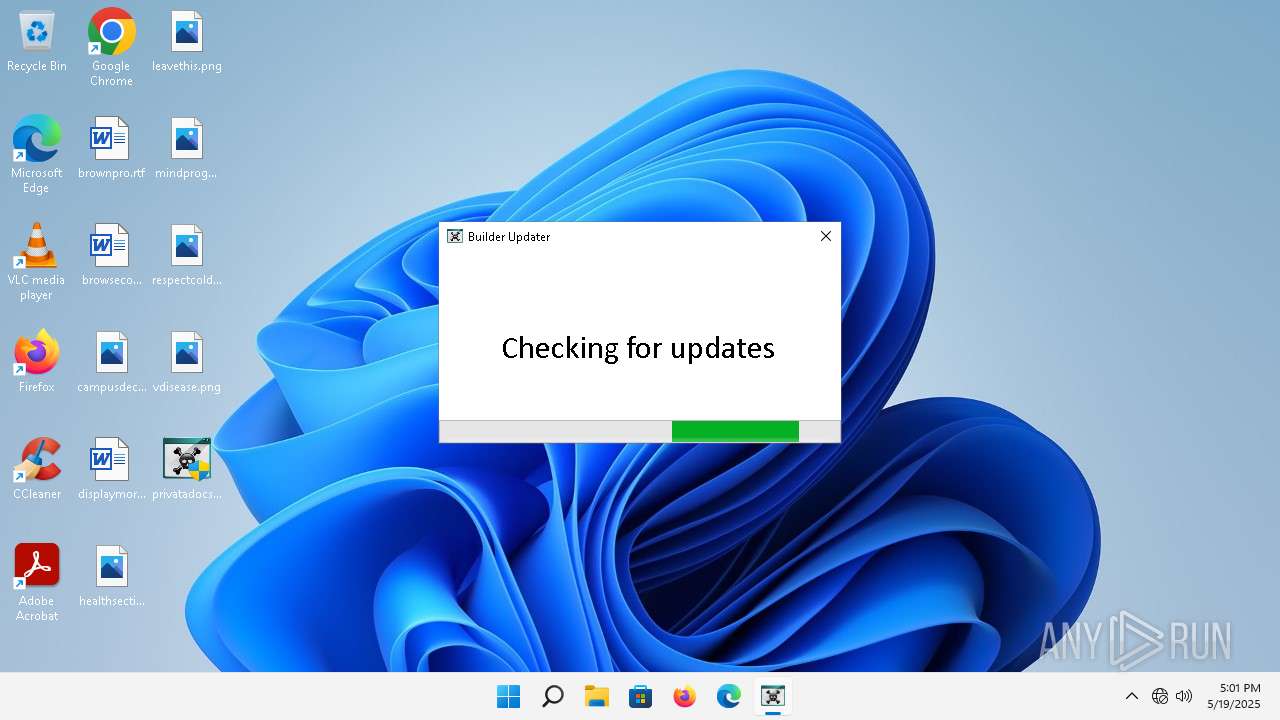
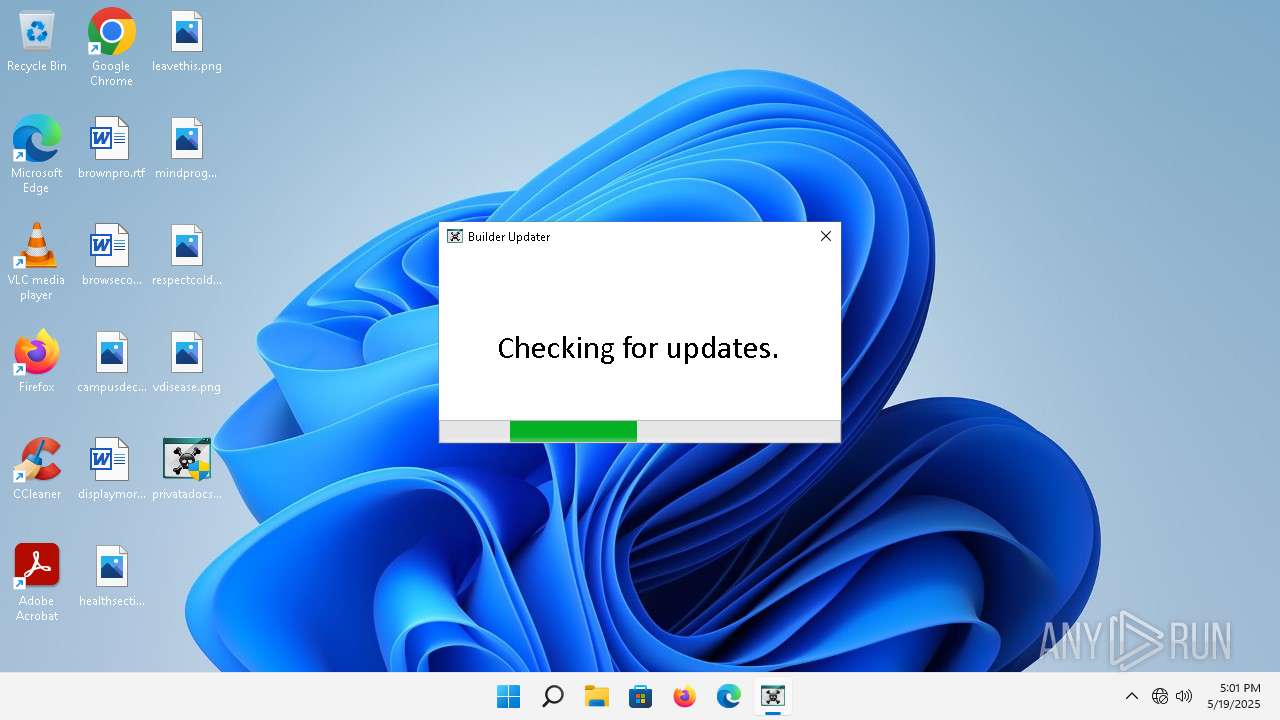
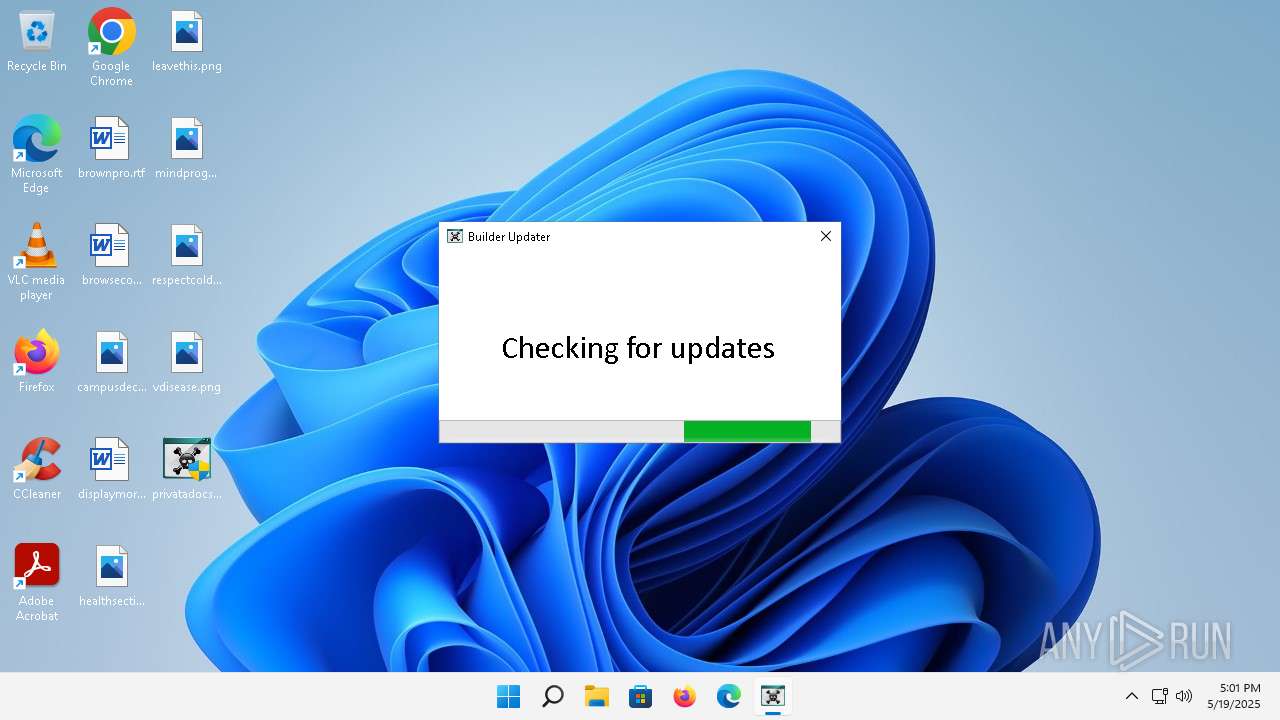
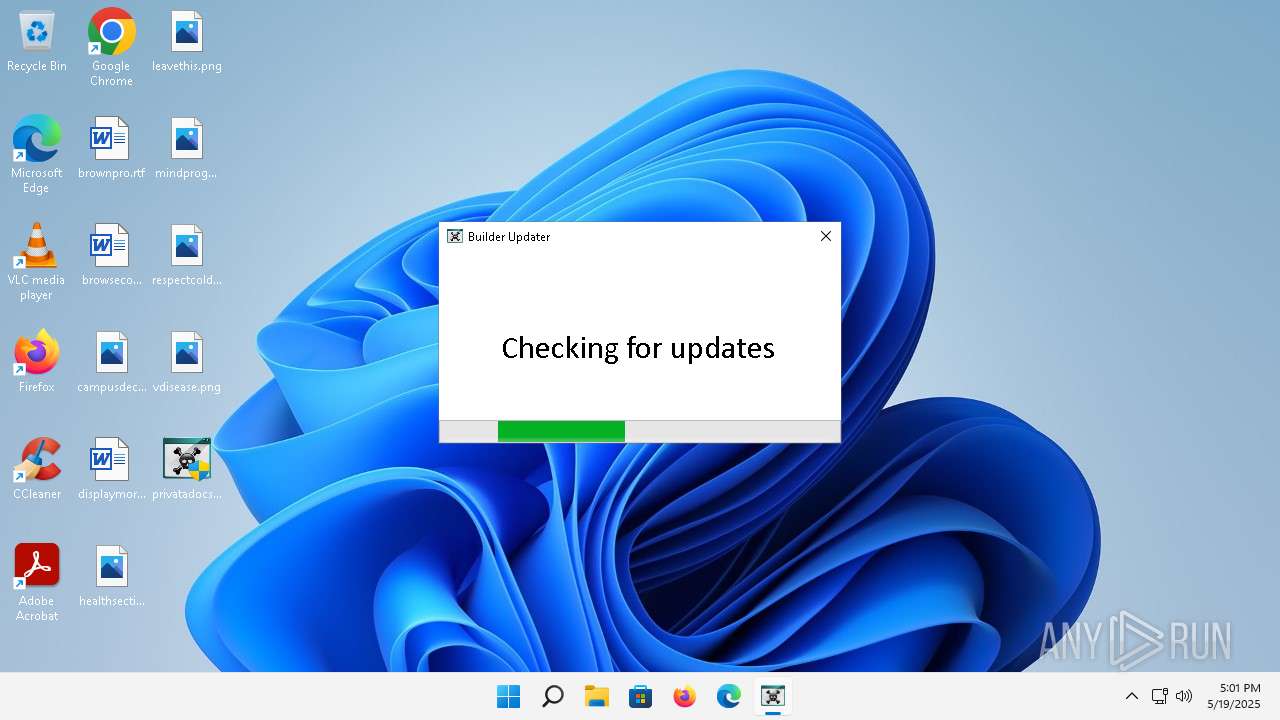
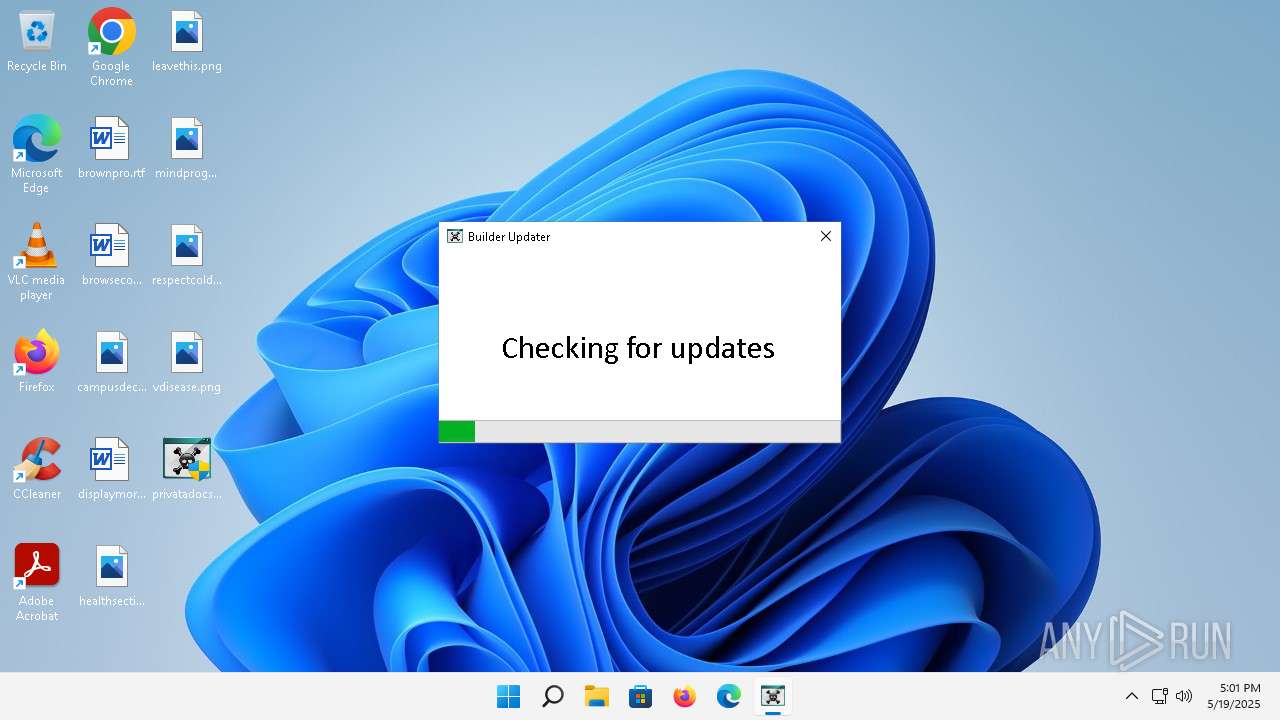
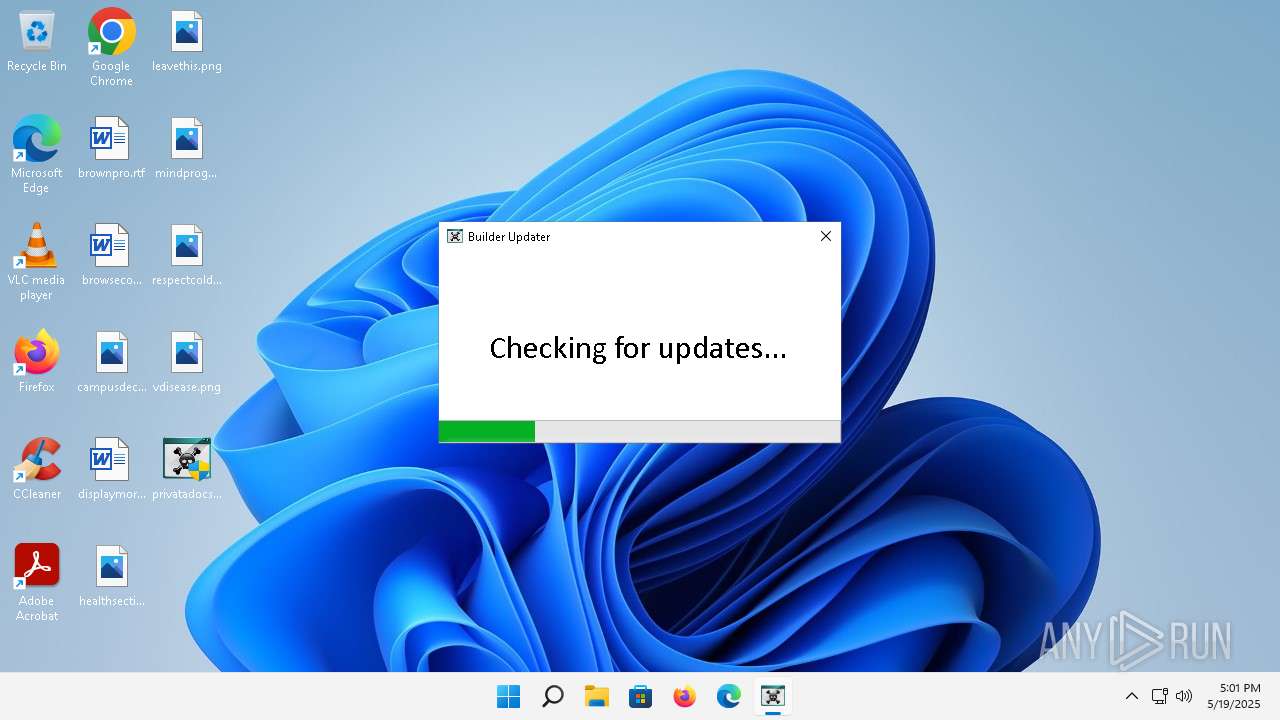
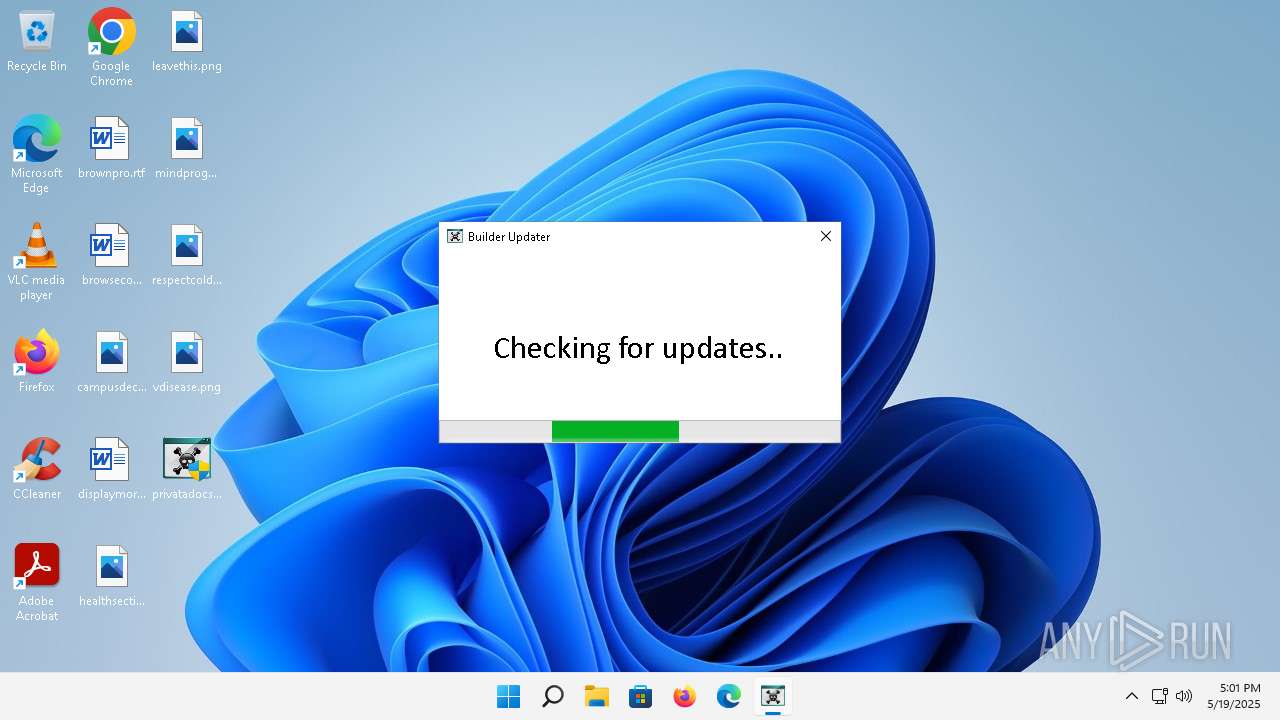
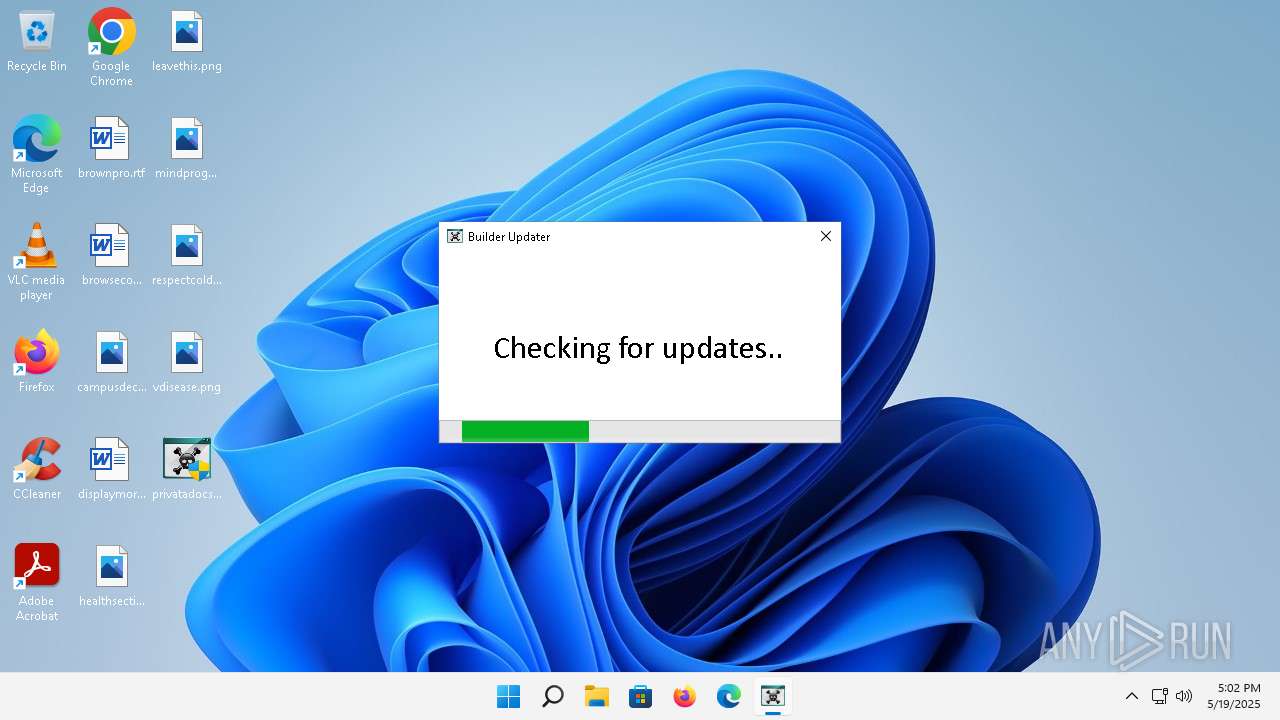
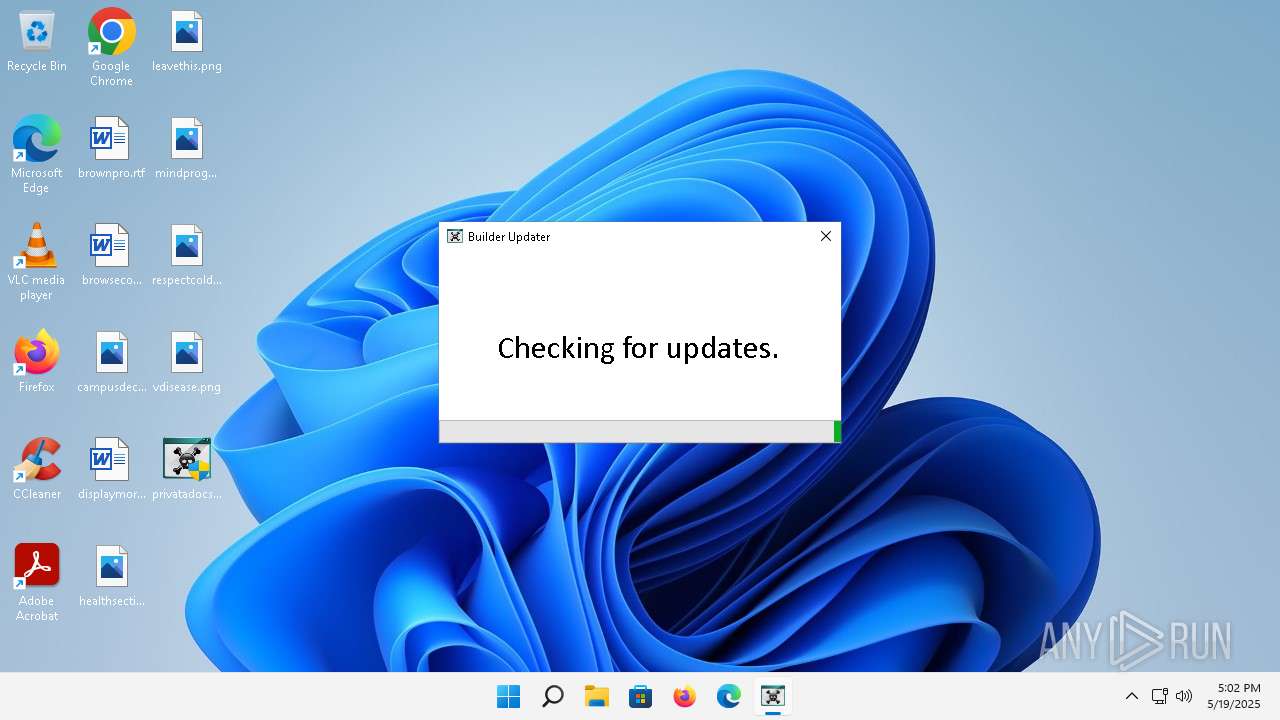
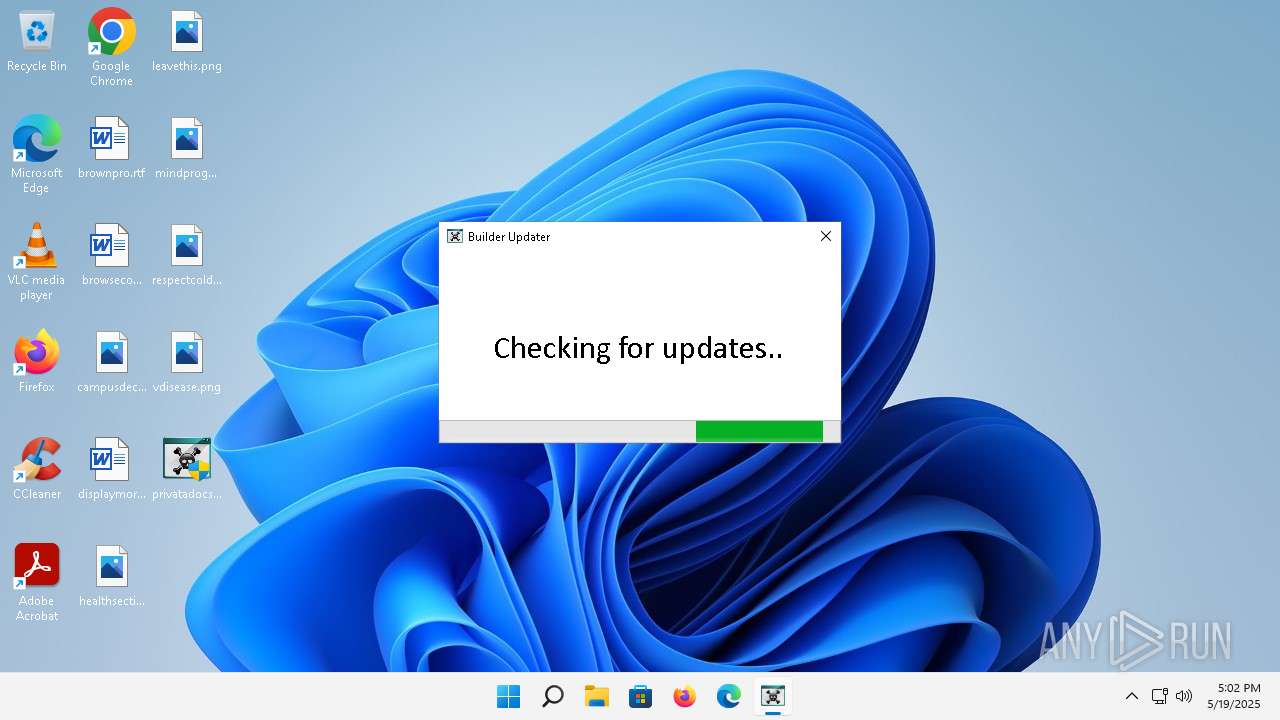
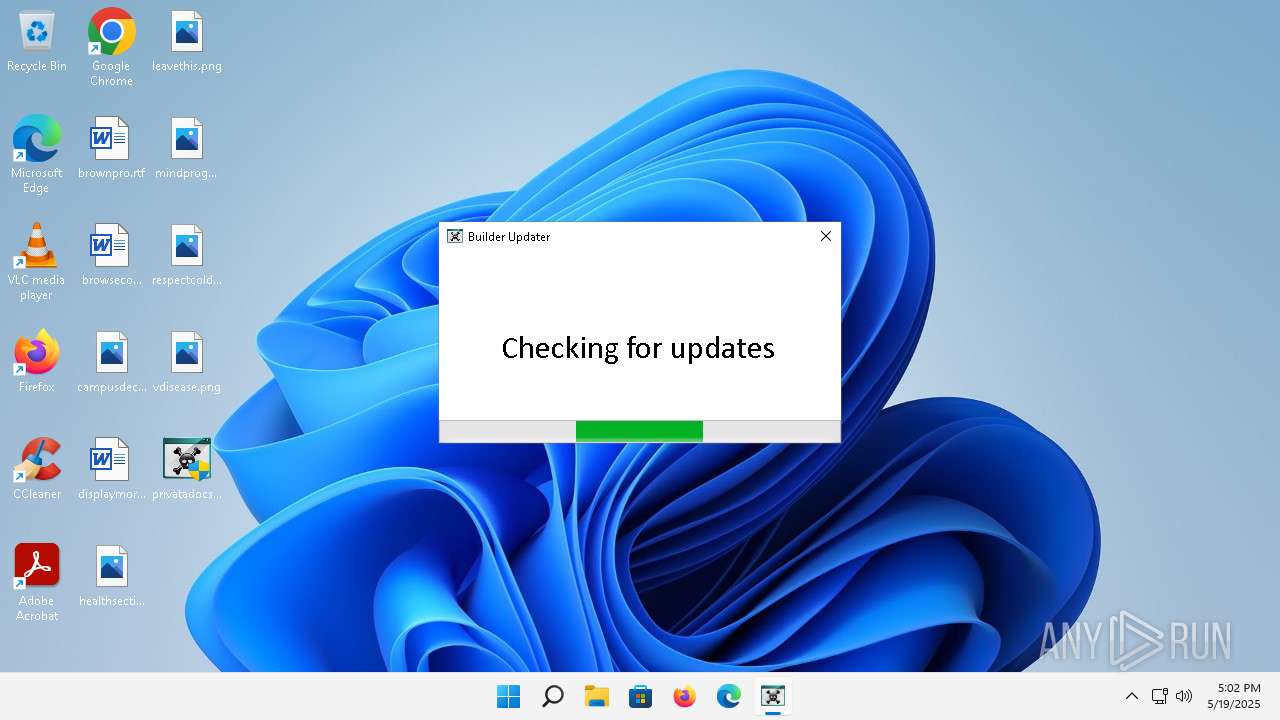
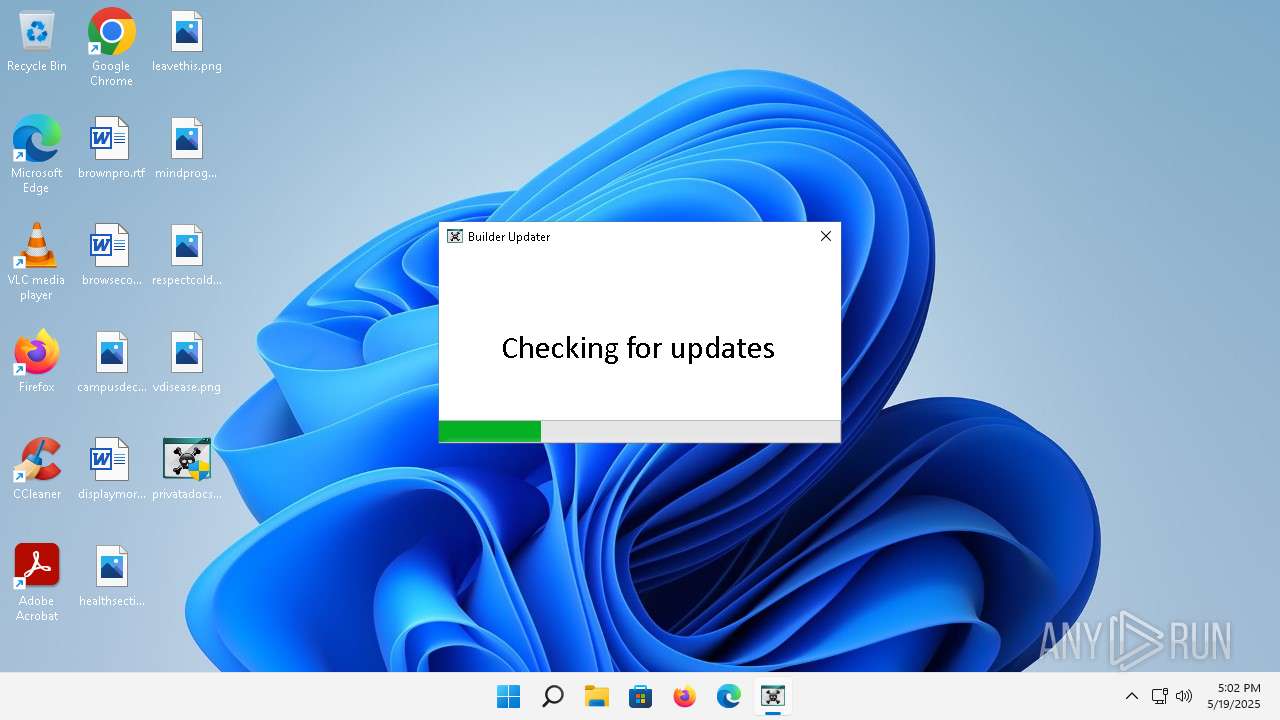
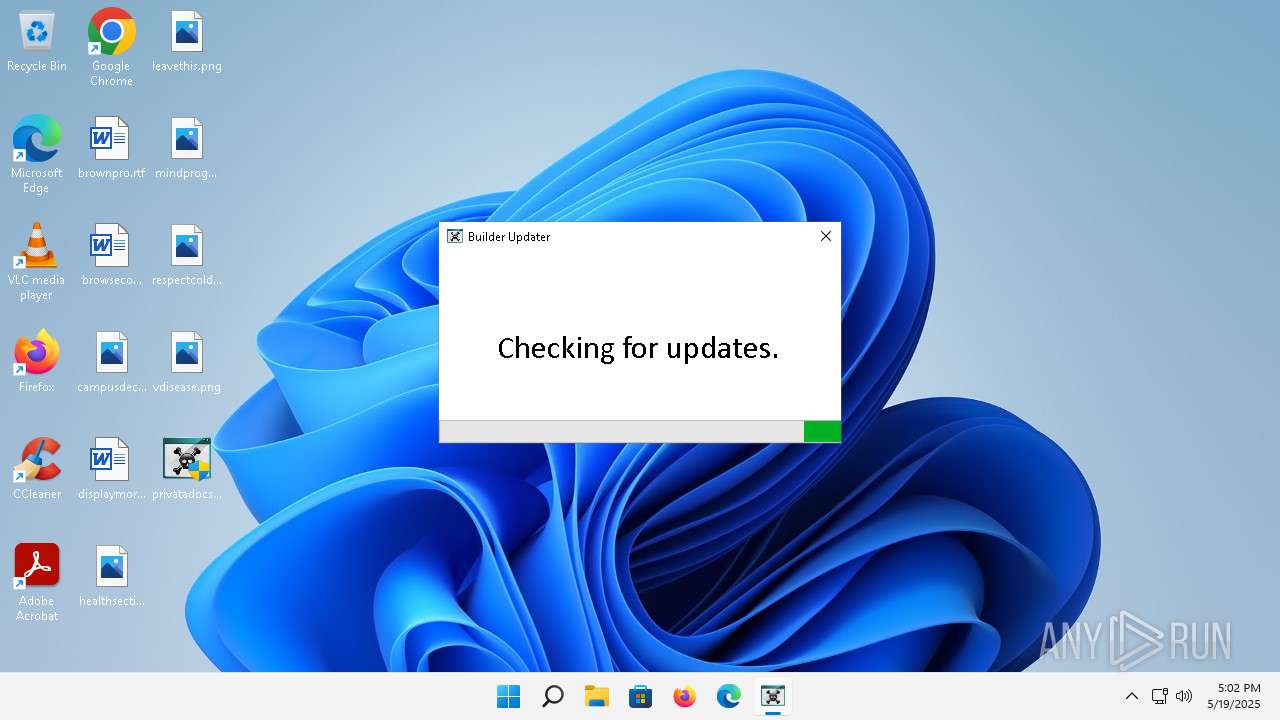
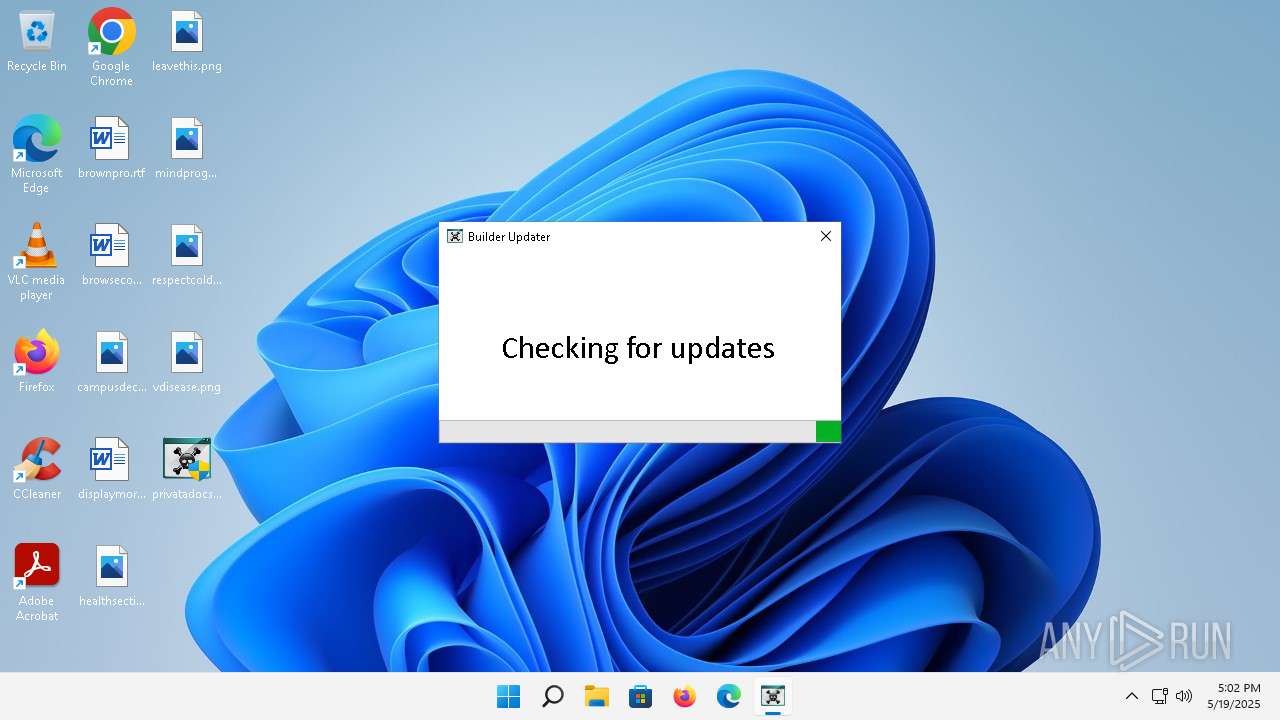
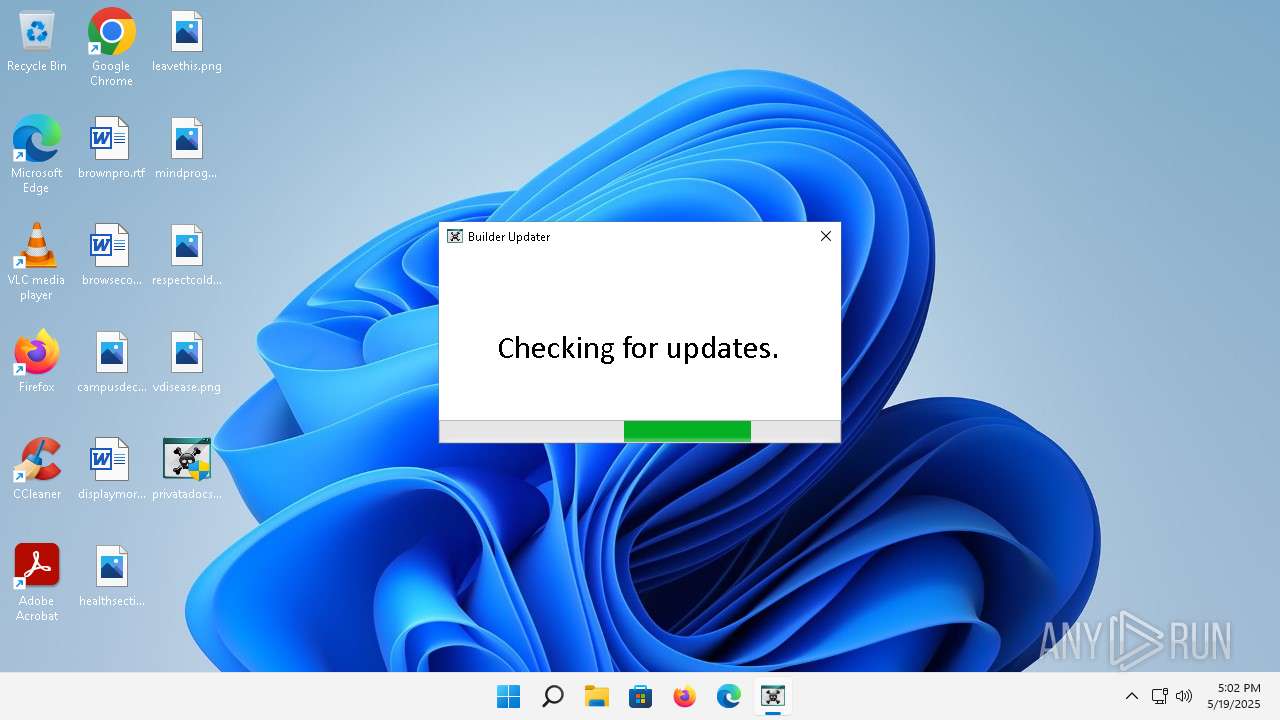
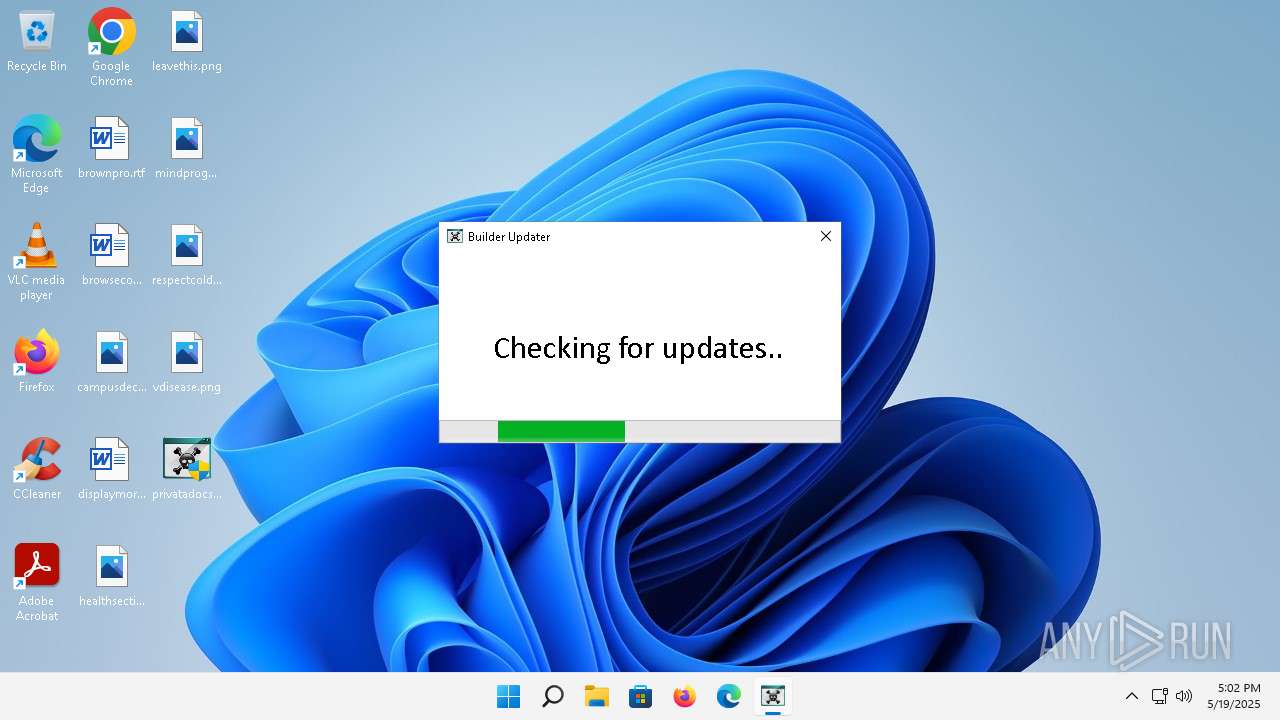
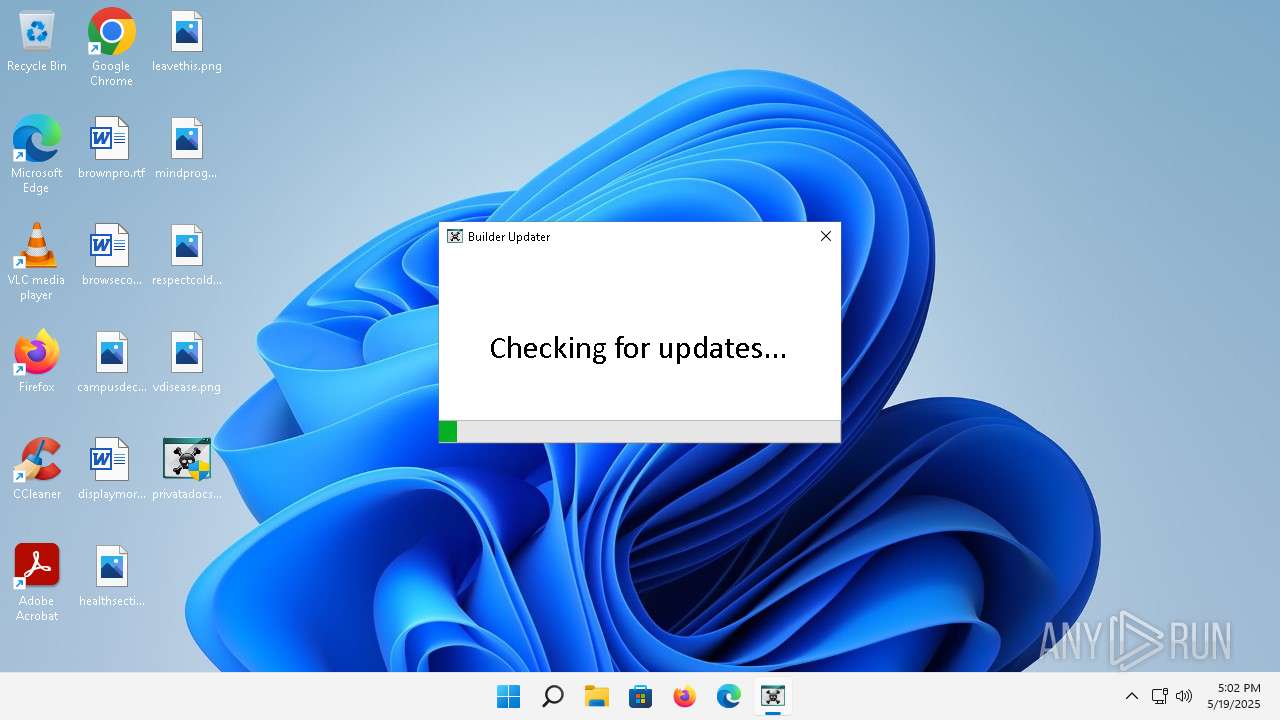
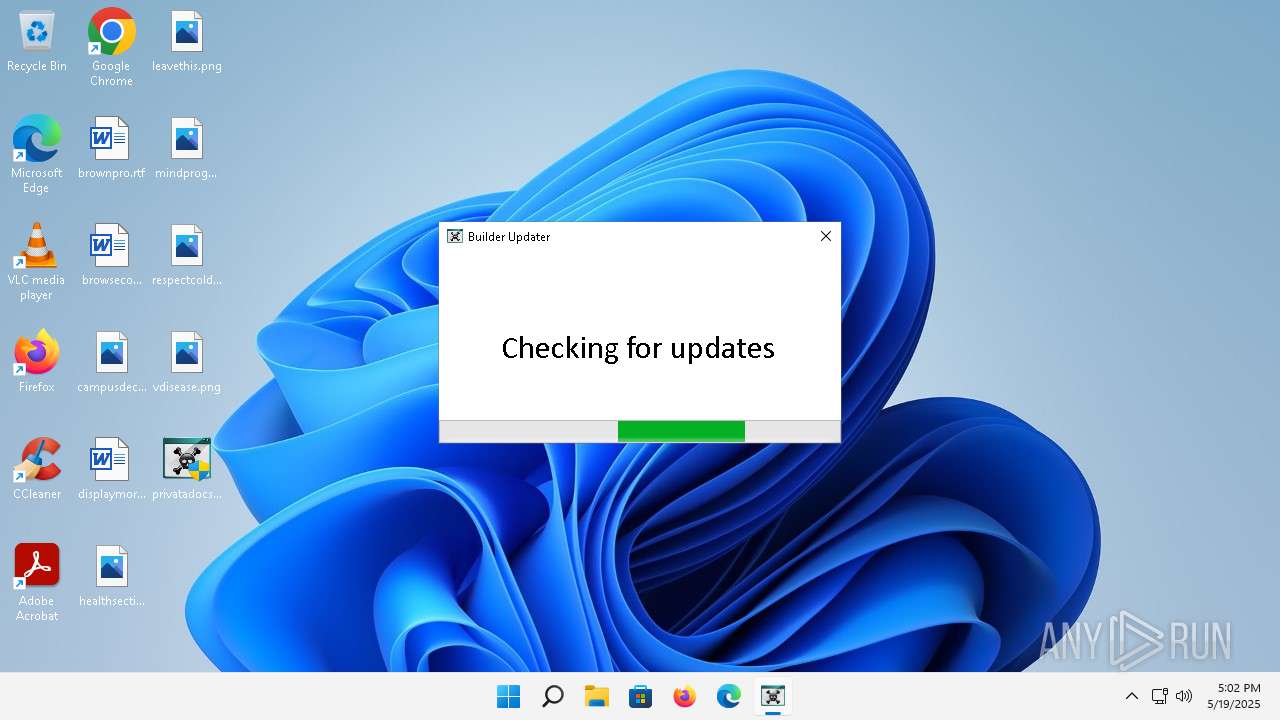
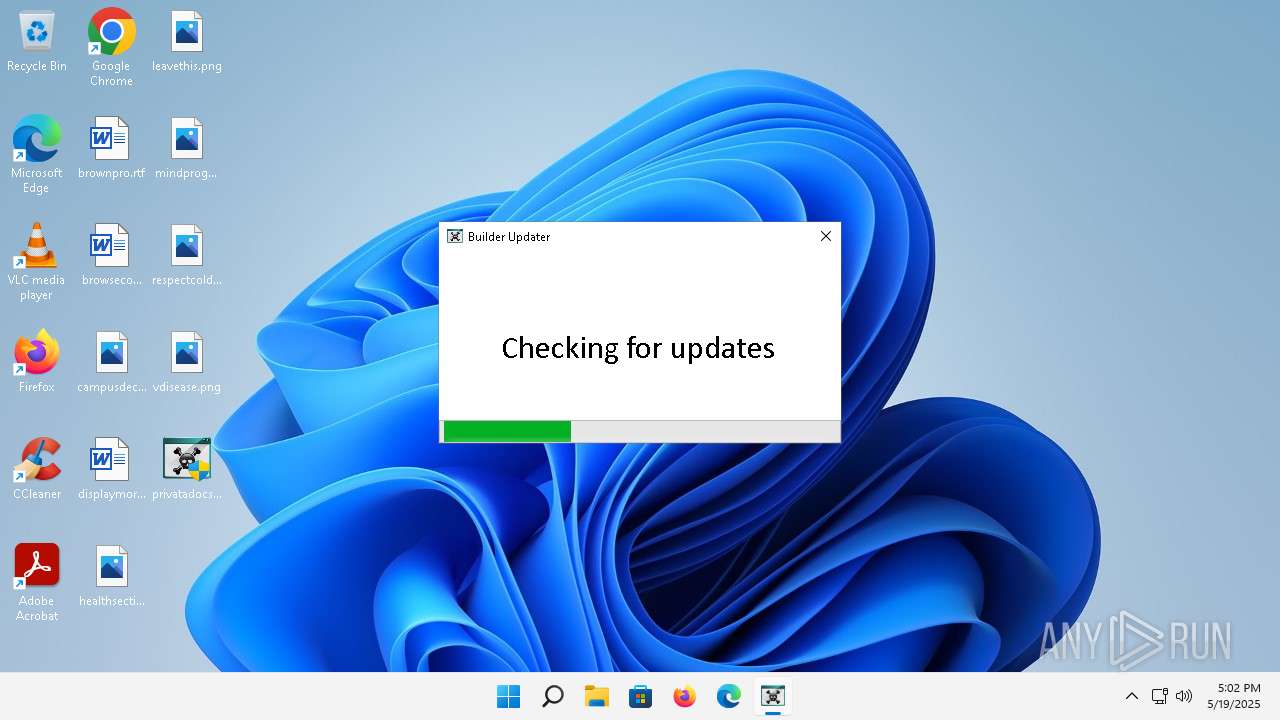
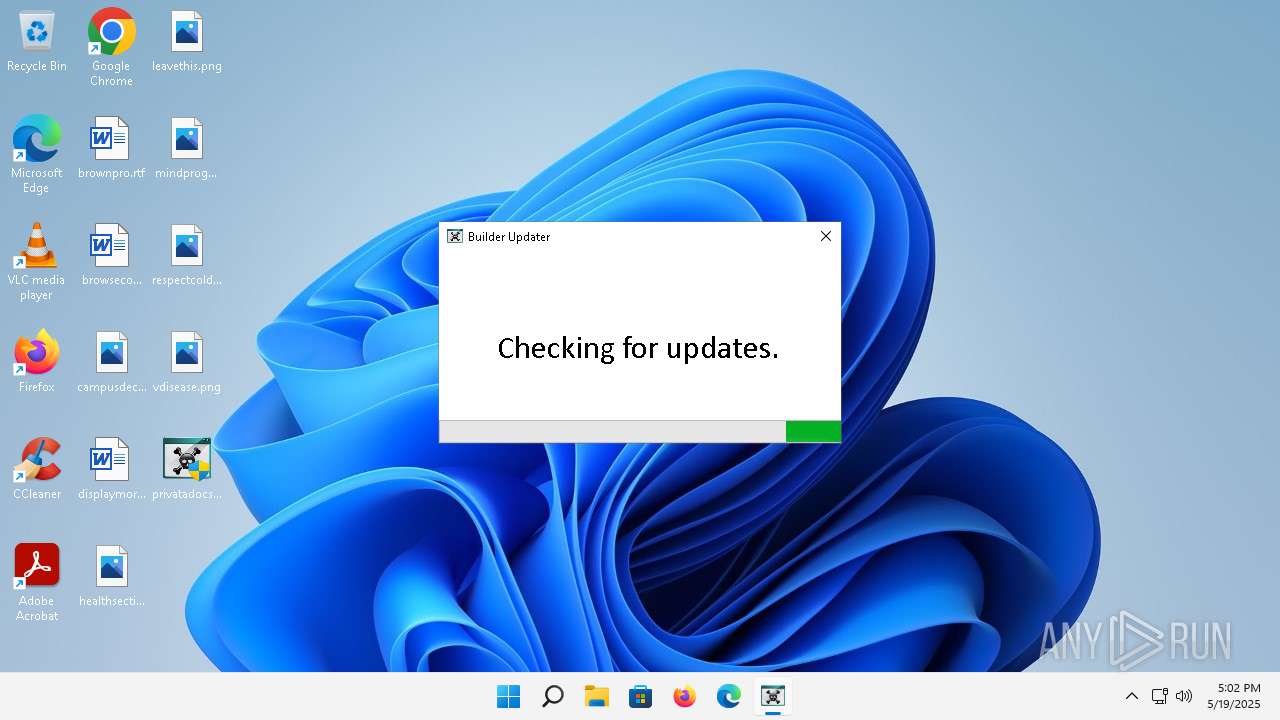
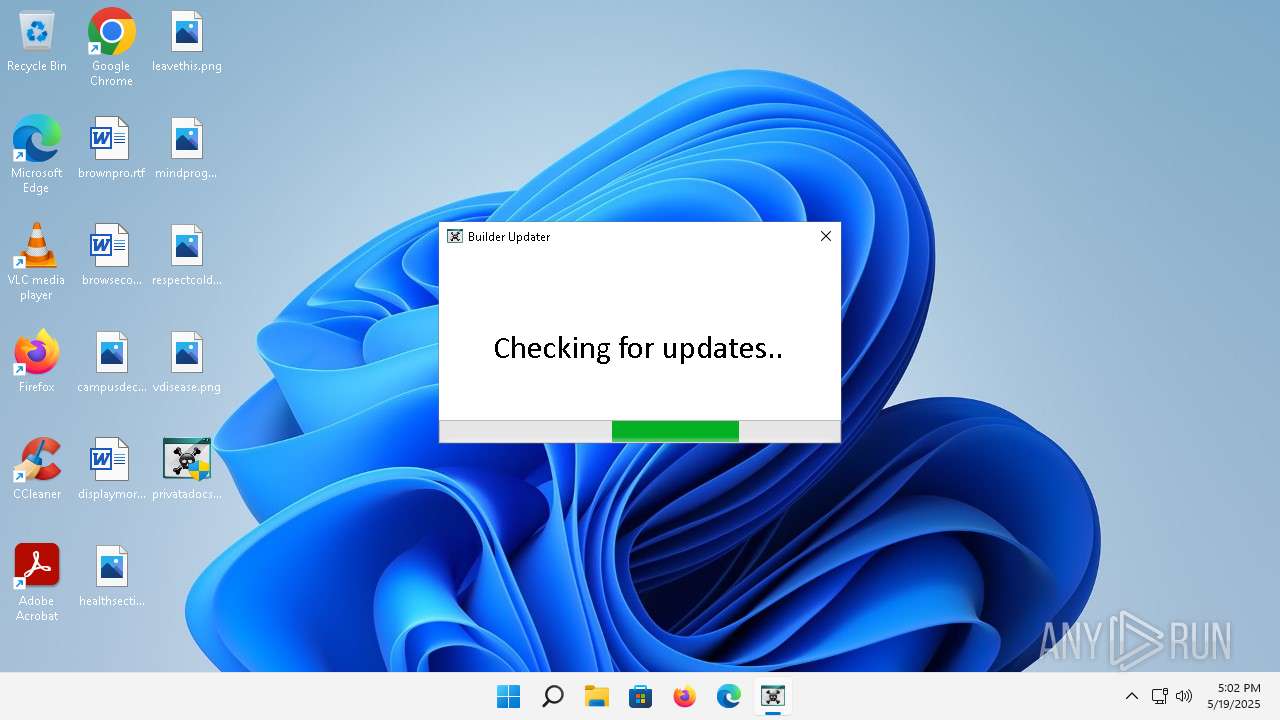
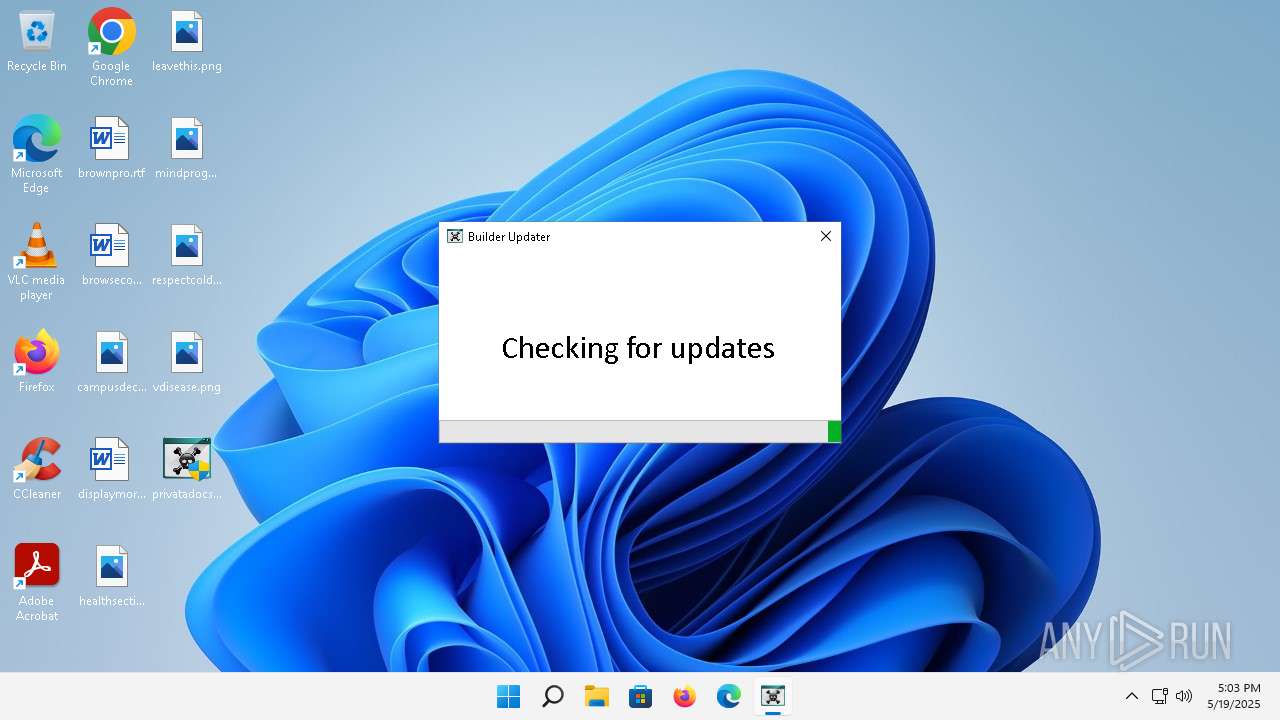
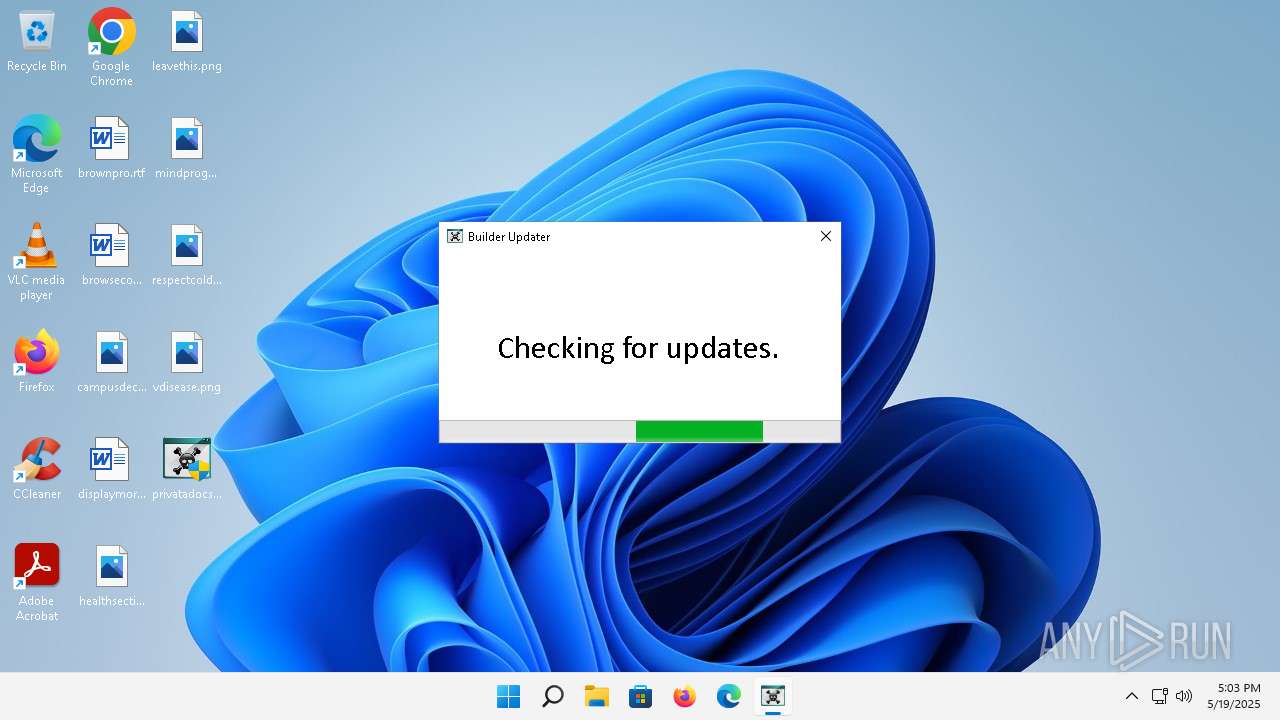
| Comments: | Updater |
| CompanyName: | sumhex |
| FileDescription: | Updater for upO Builder |
| FileVersion: | 0.9.7.0 |
| InternalName: | LockerBuilderUpdate.exe |
| LegalCopyright: | sumhex |
| LegalTrademarks: | - |
| OriginalFileName: | LockerBuilderUpdate.exe |
| ProductName: | Updater |
| ProductVersion: | 0.9.7.0 |
| AssemblyVersion: | 0.9.7.0 |
Total processes
102
Monitored processes
2
Malicious processes
0
Suspicious processes
1
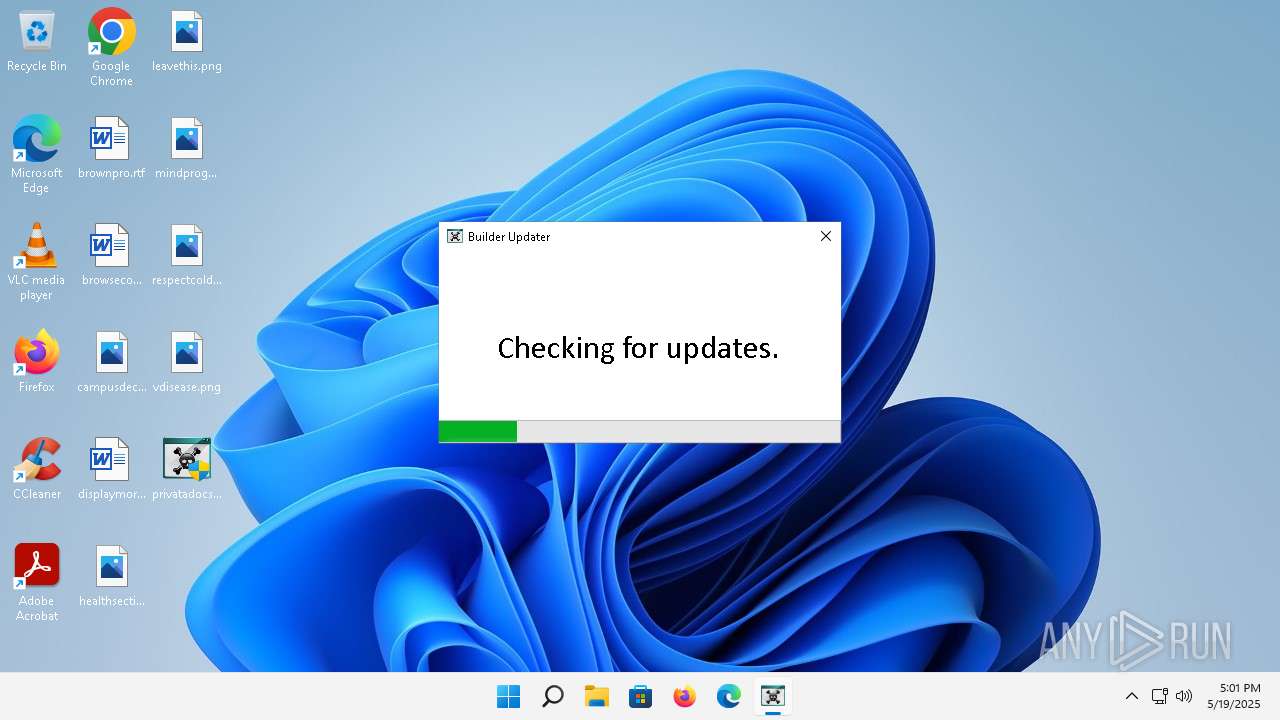
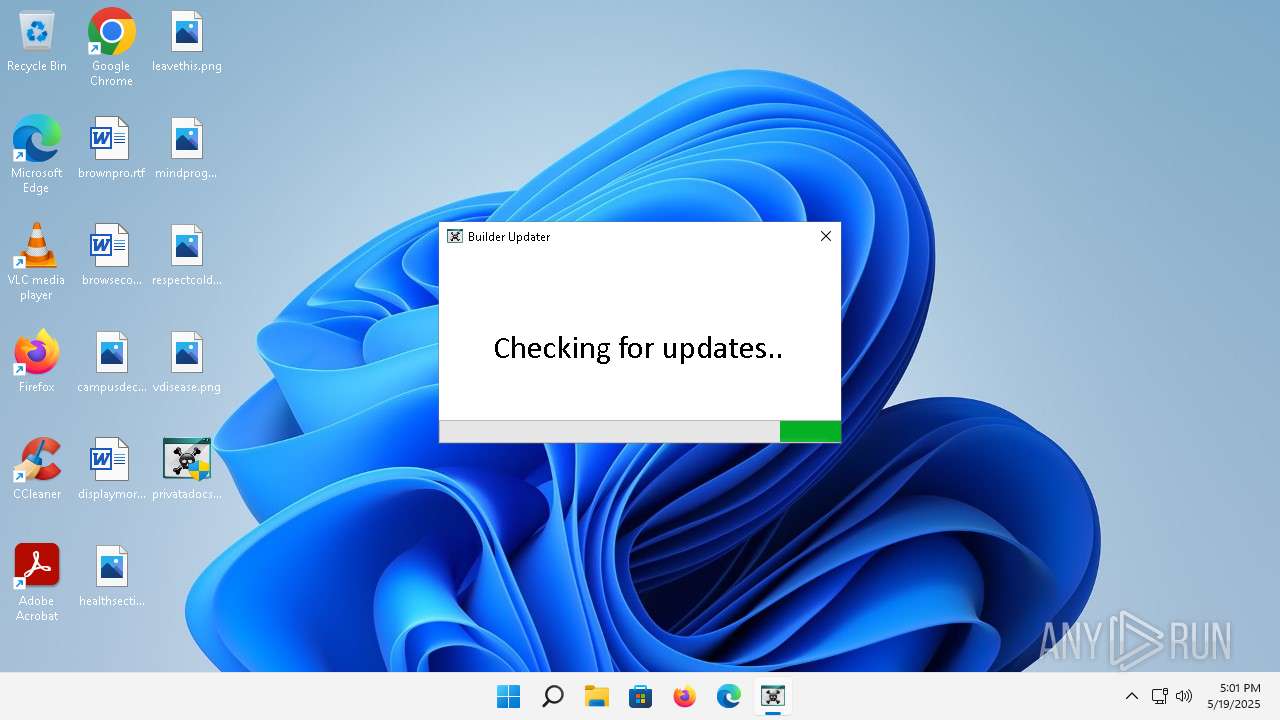
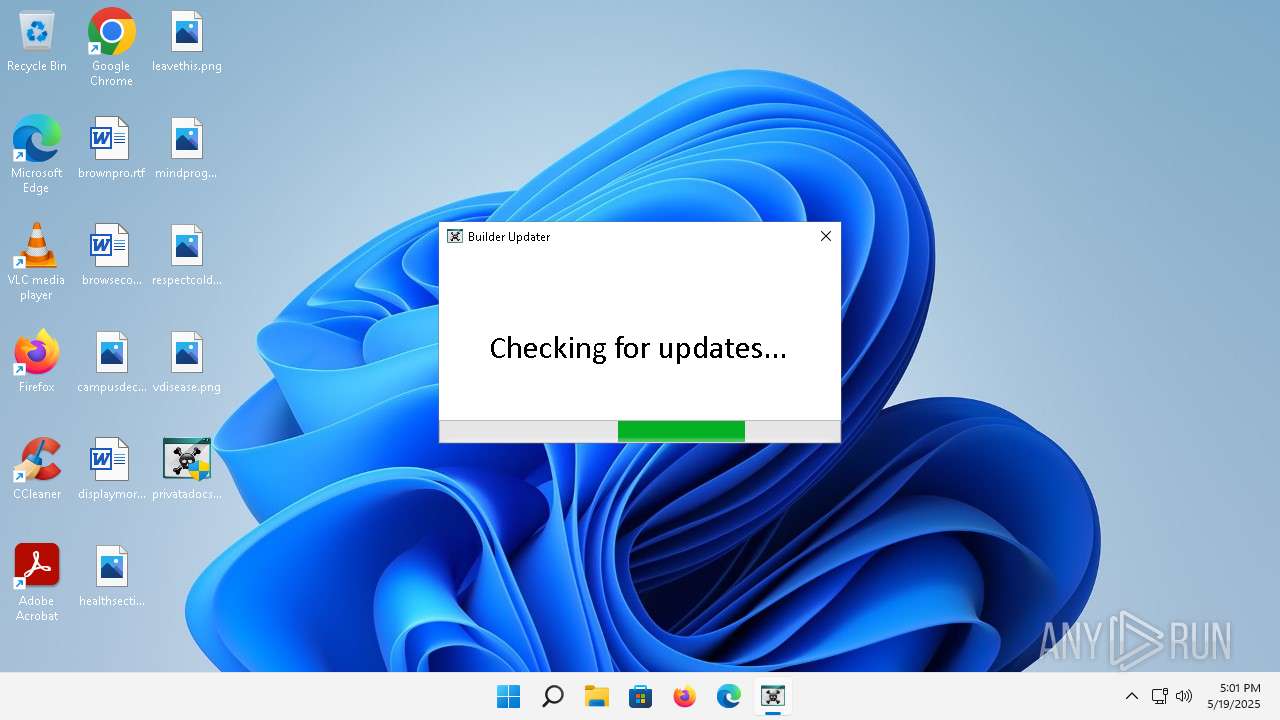
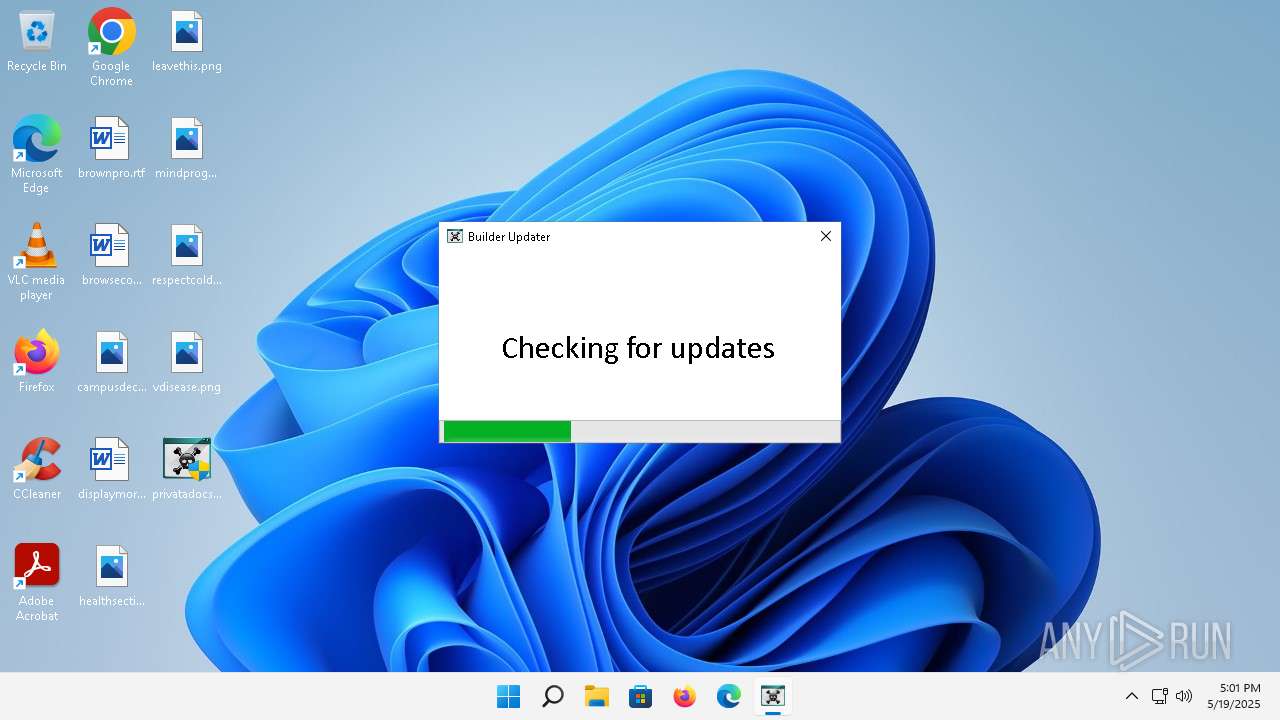
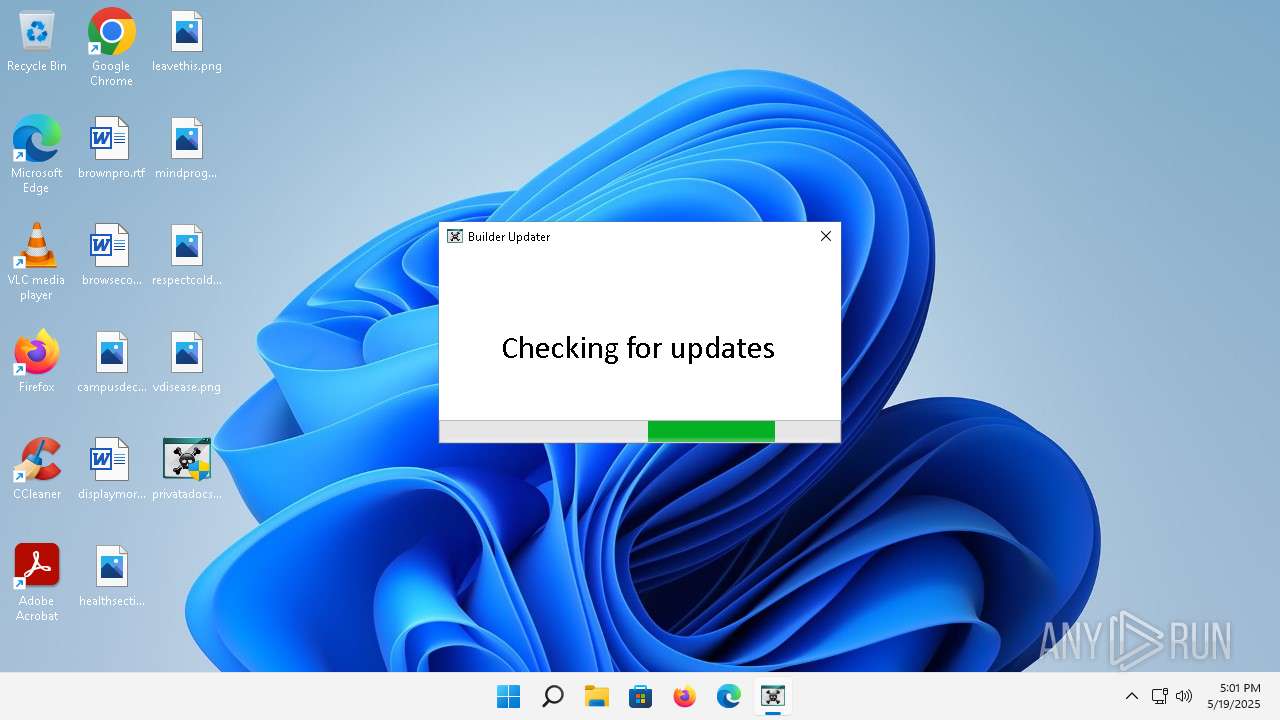
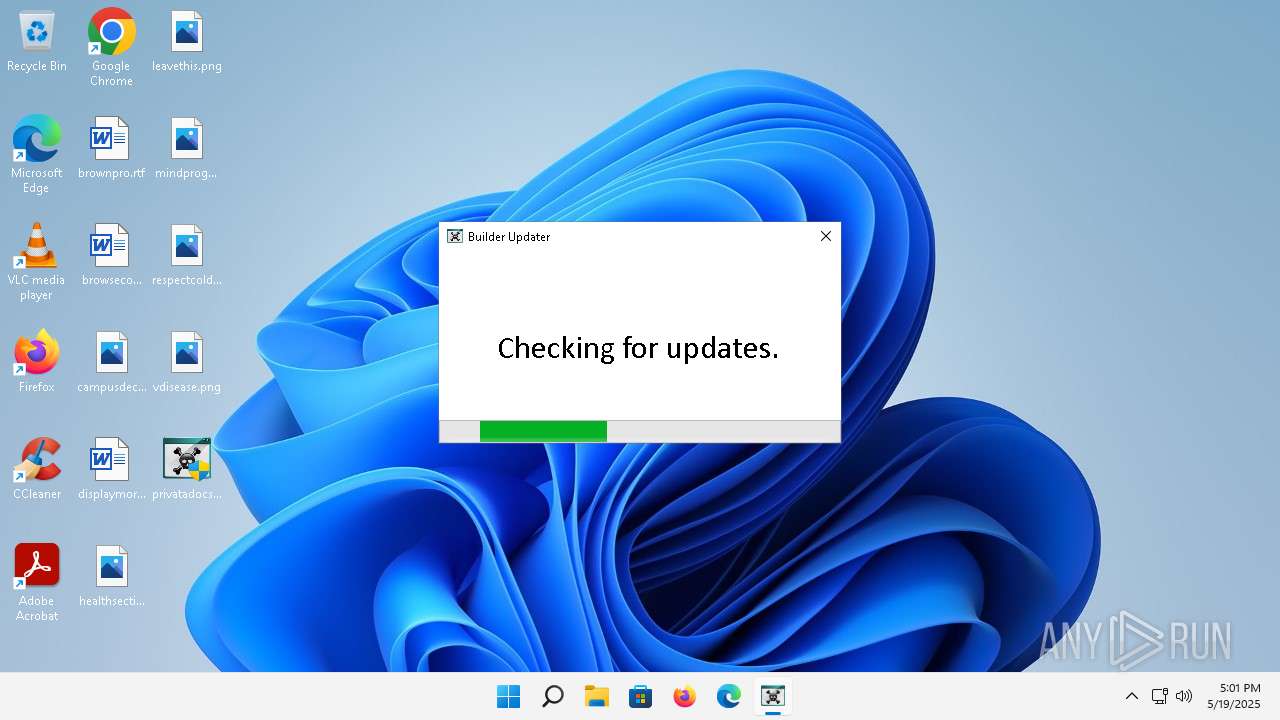
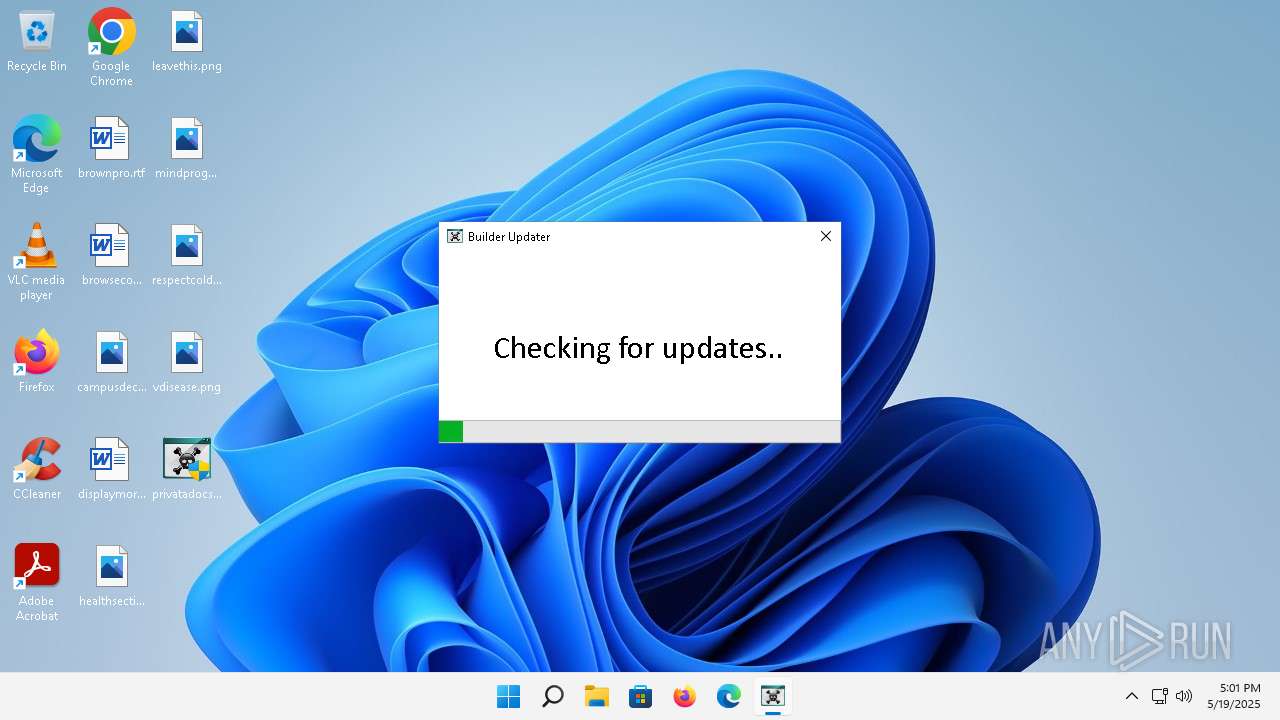
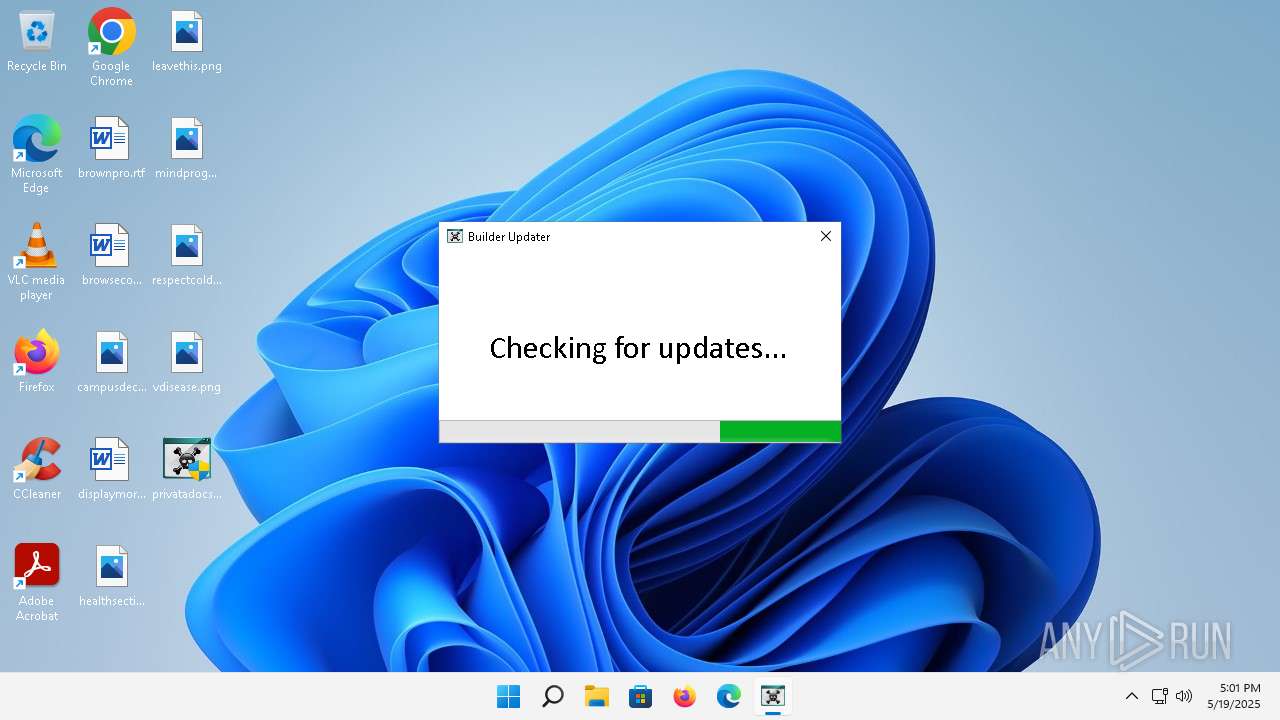
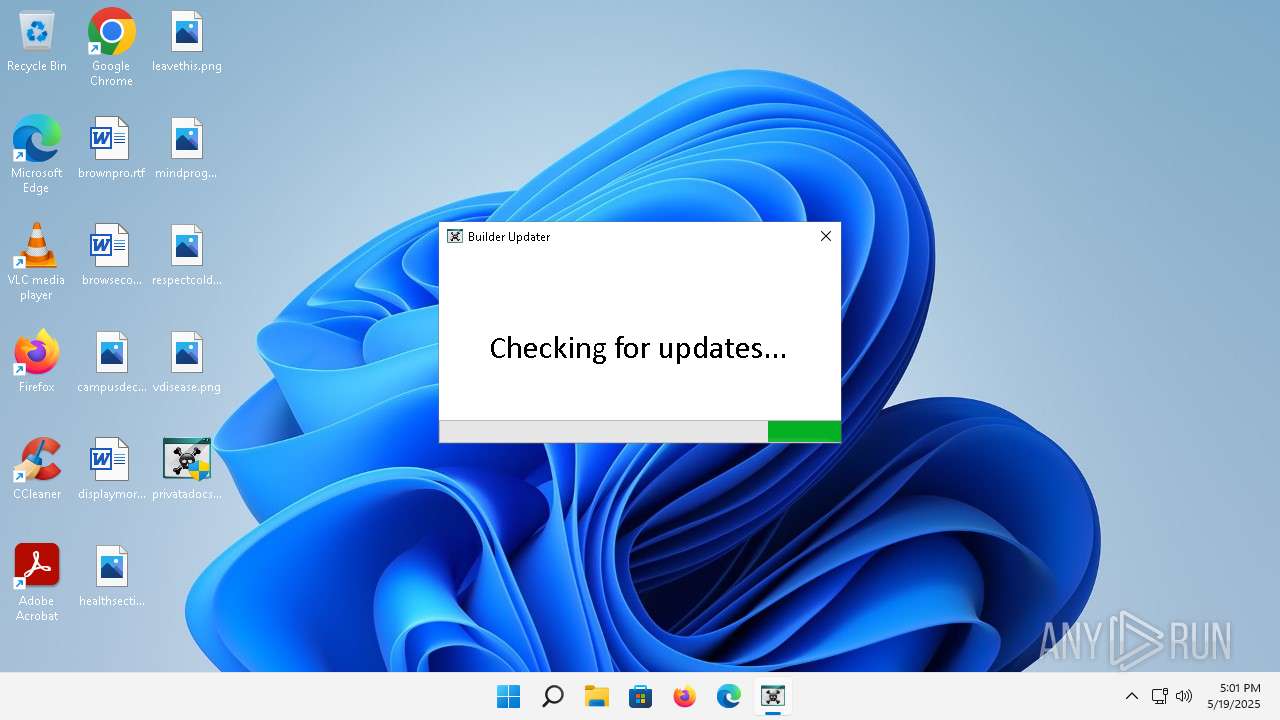
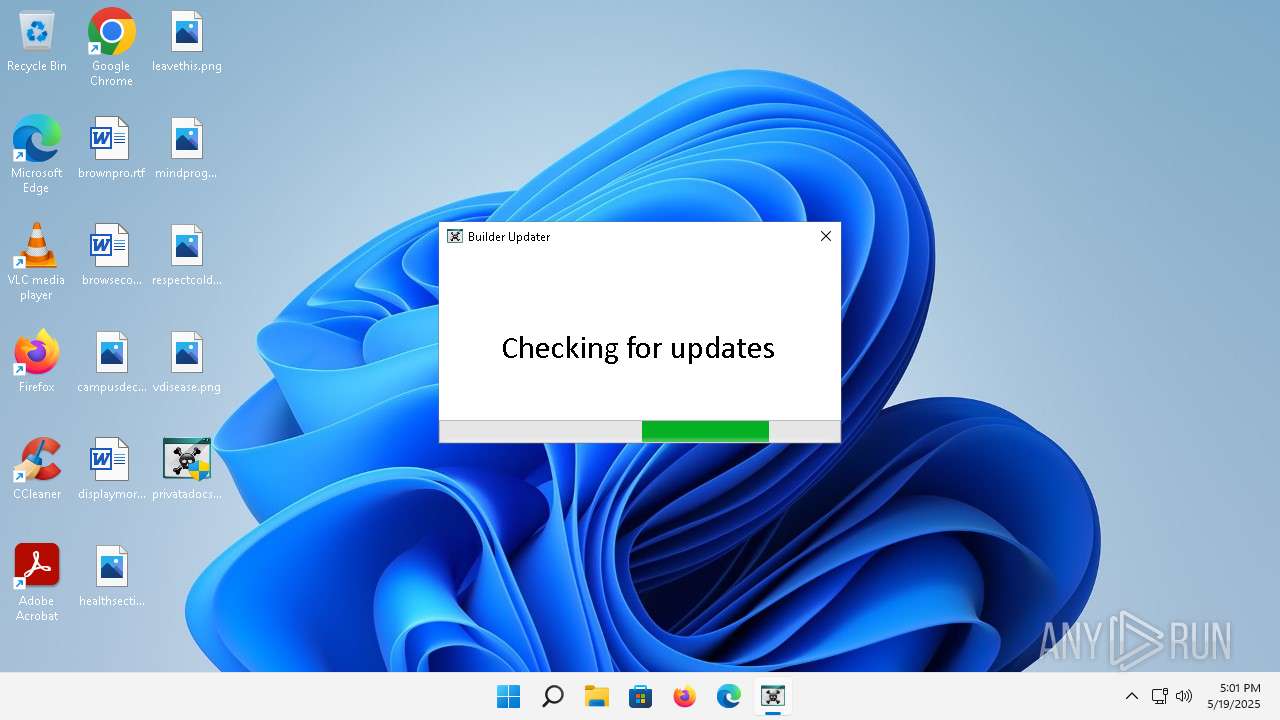
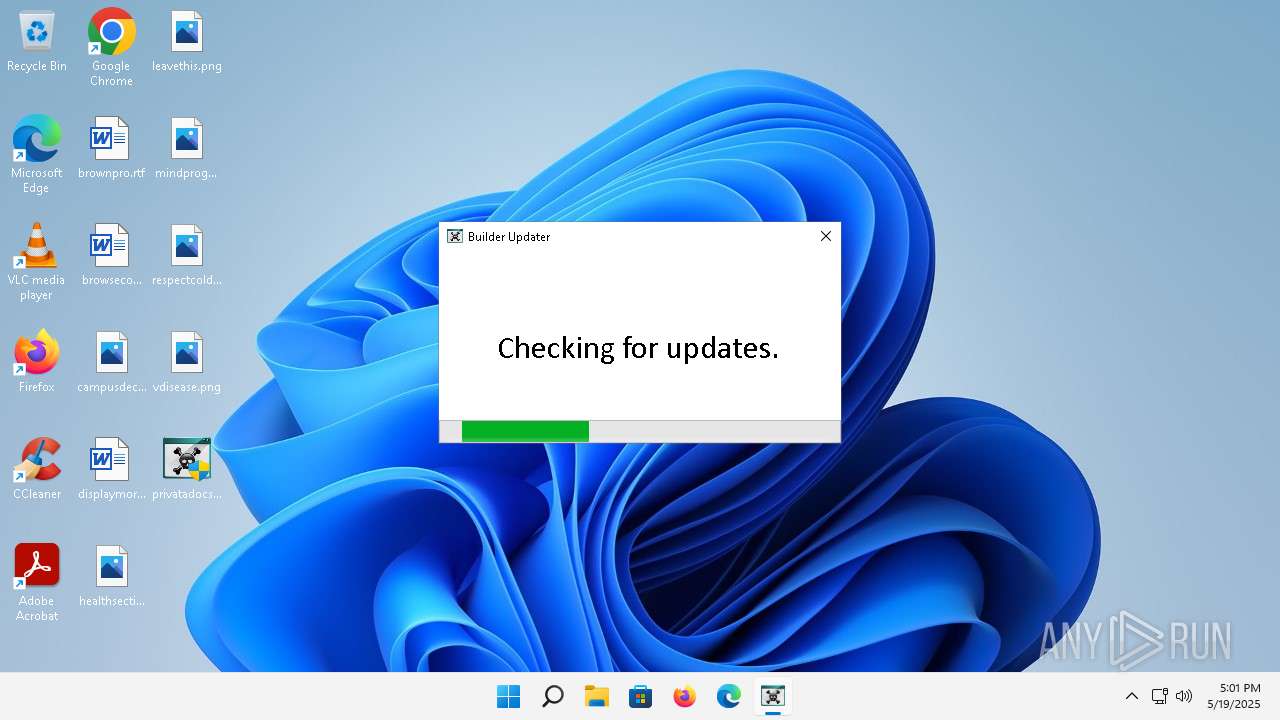
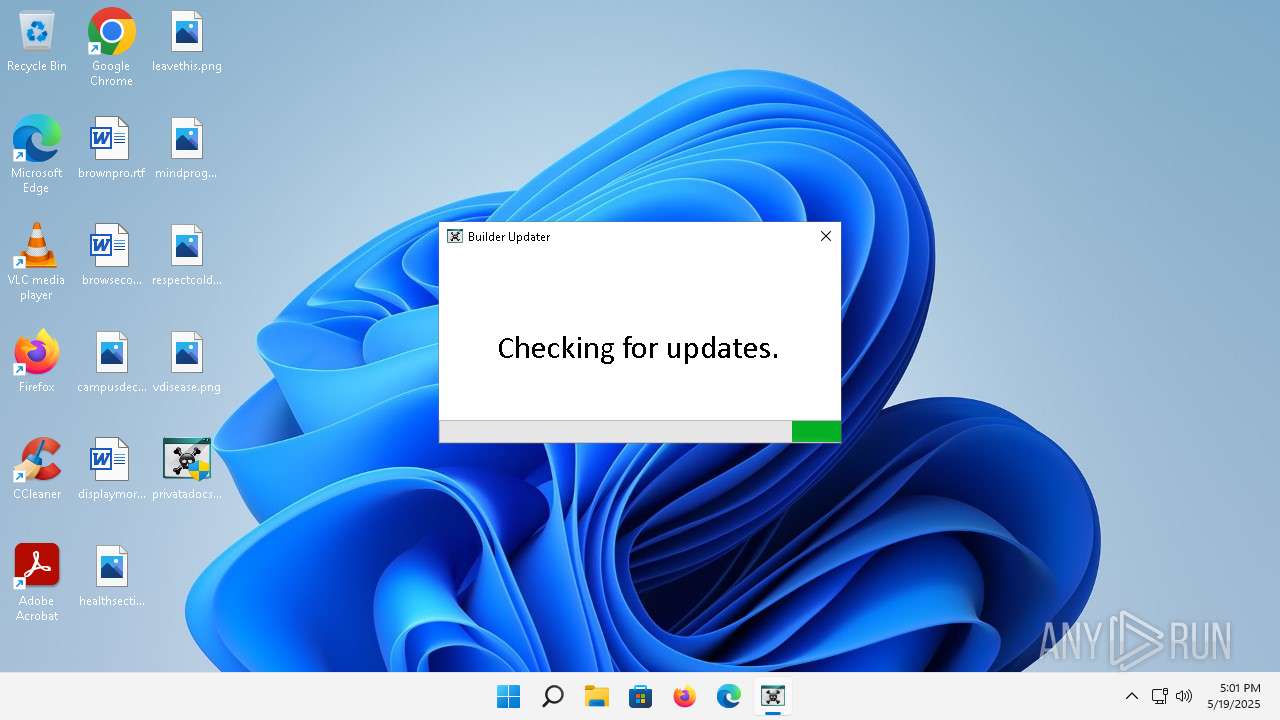
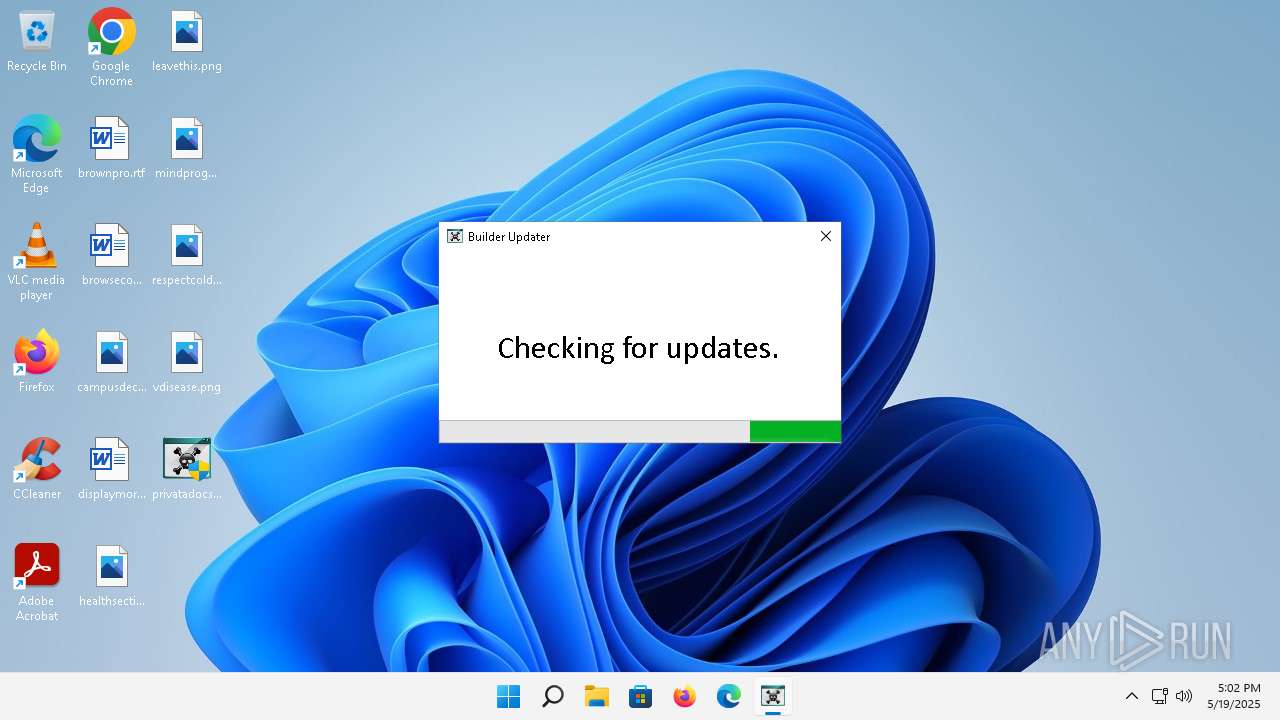
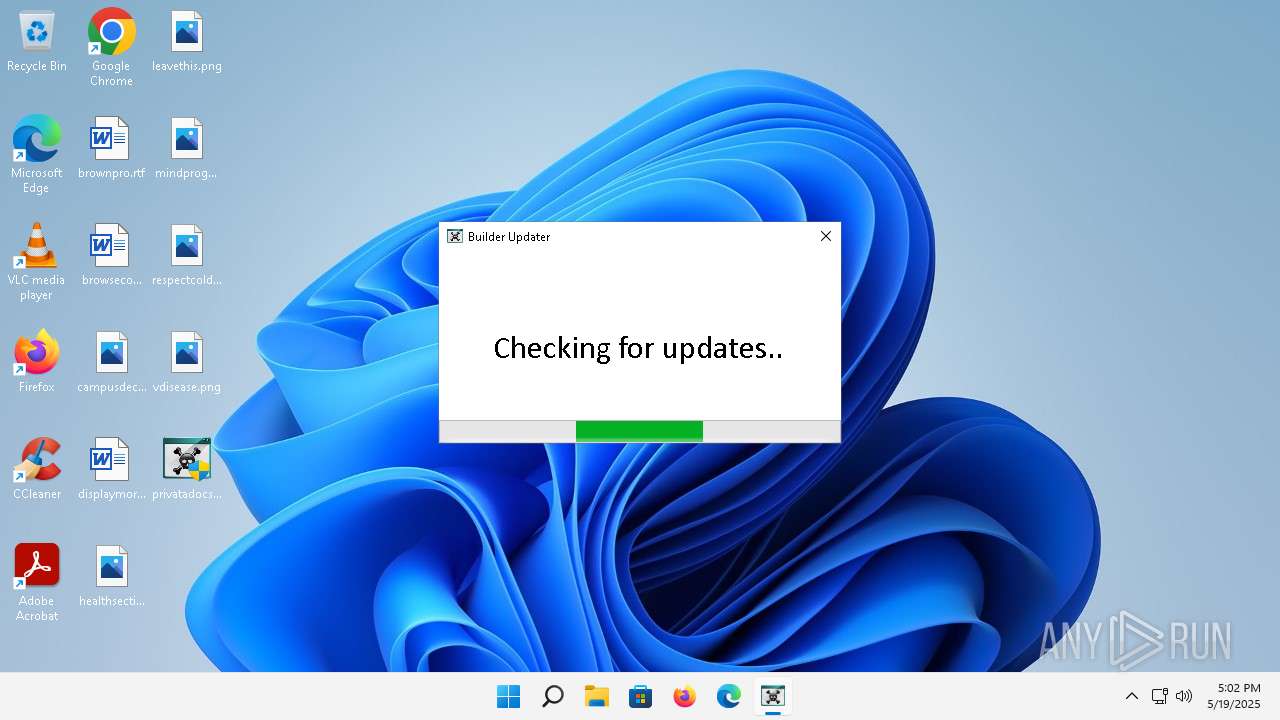
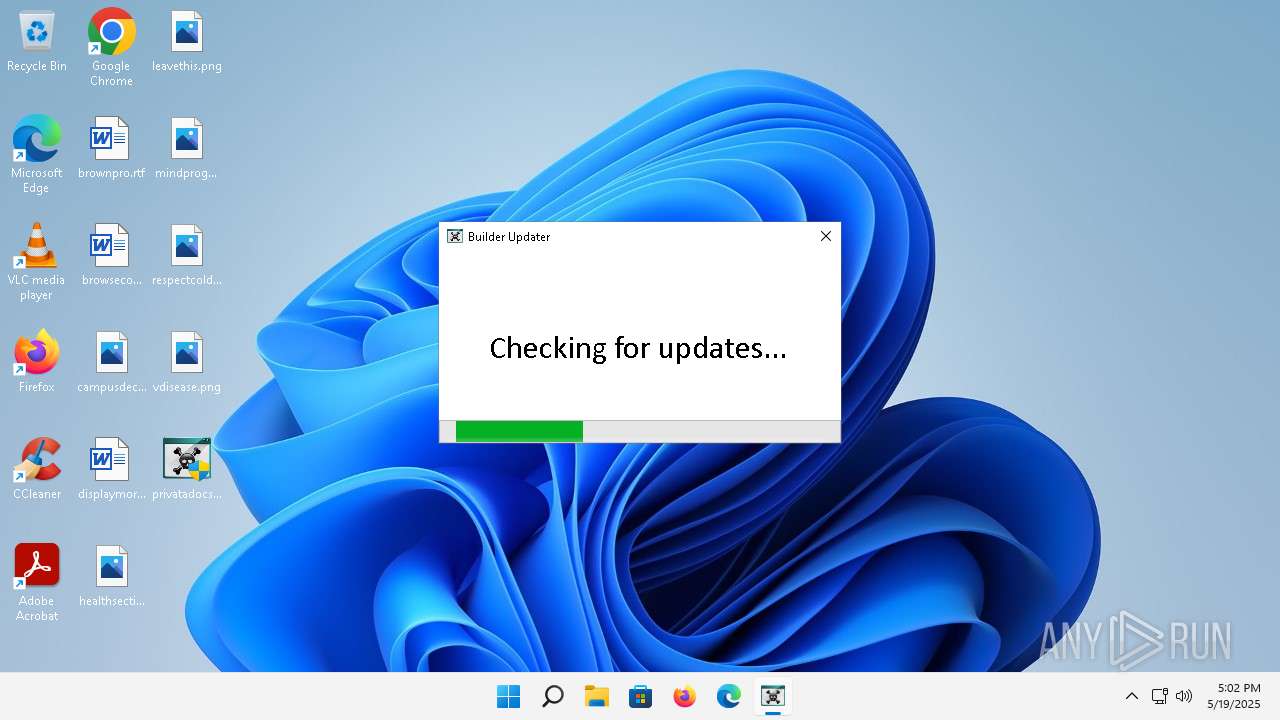
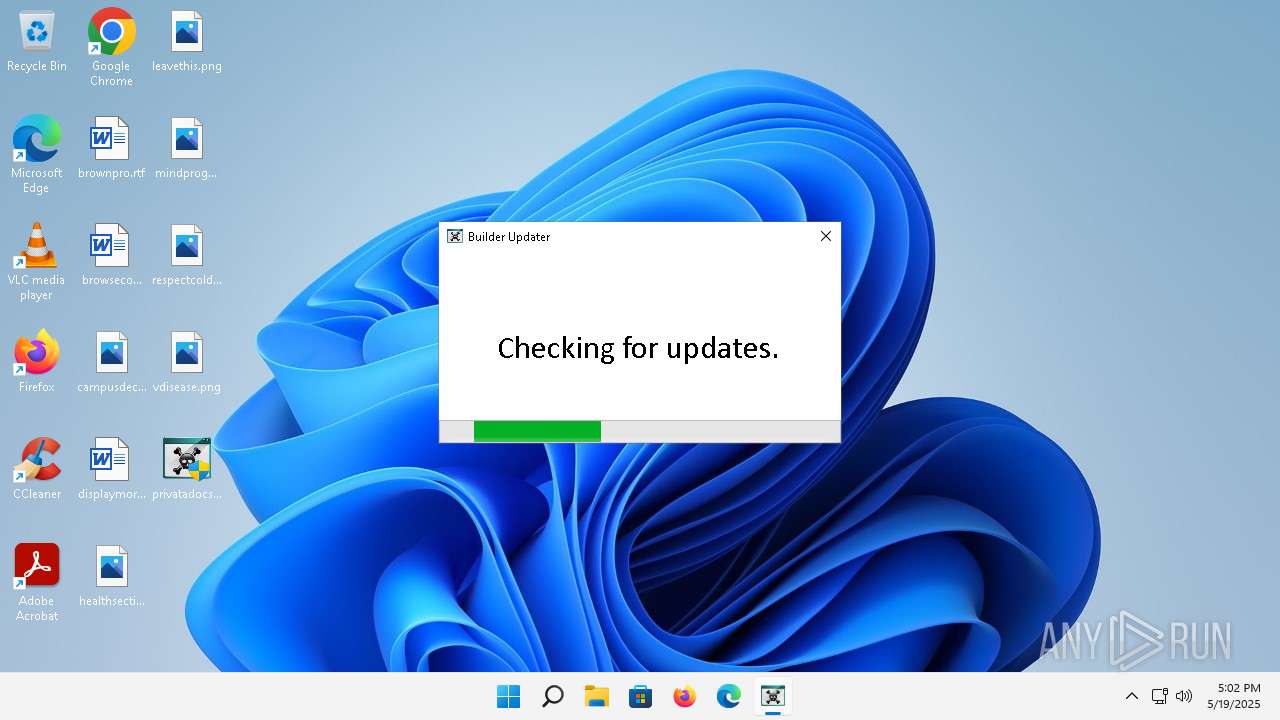
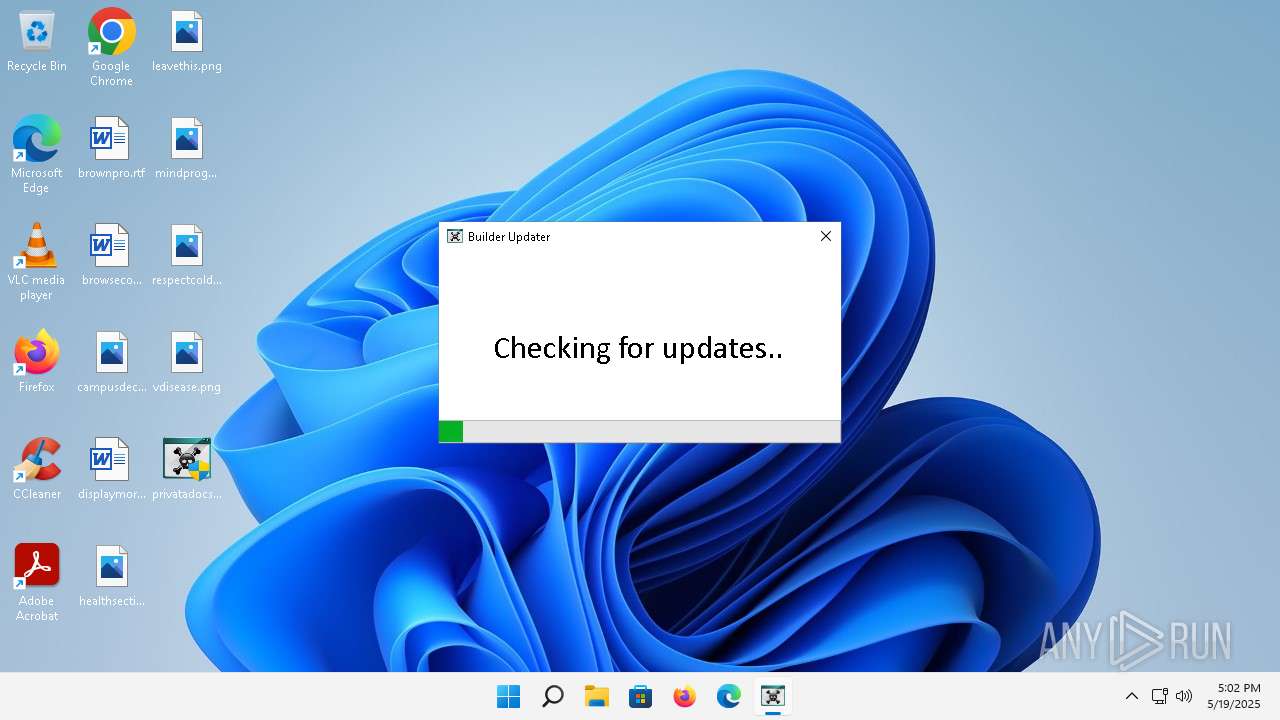
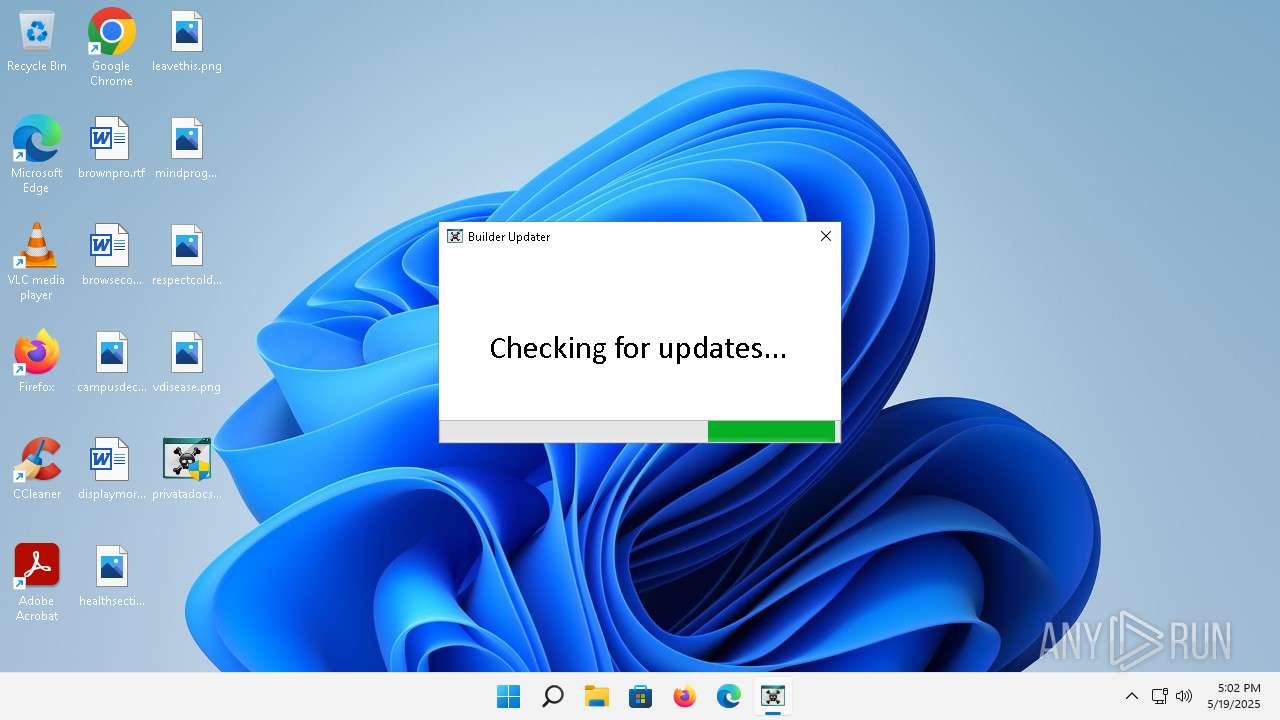
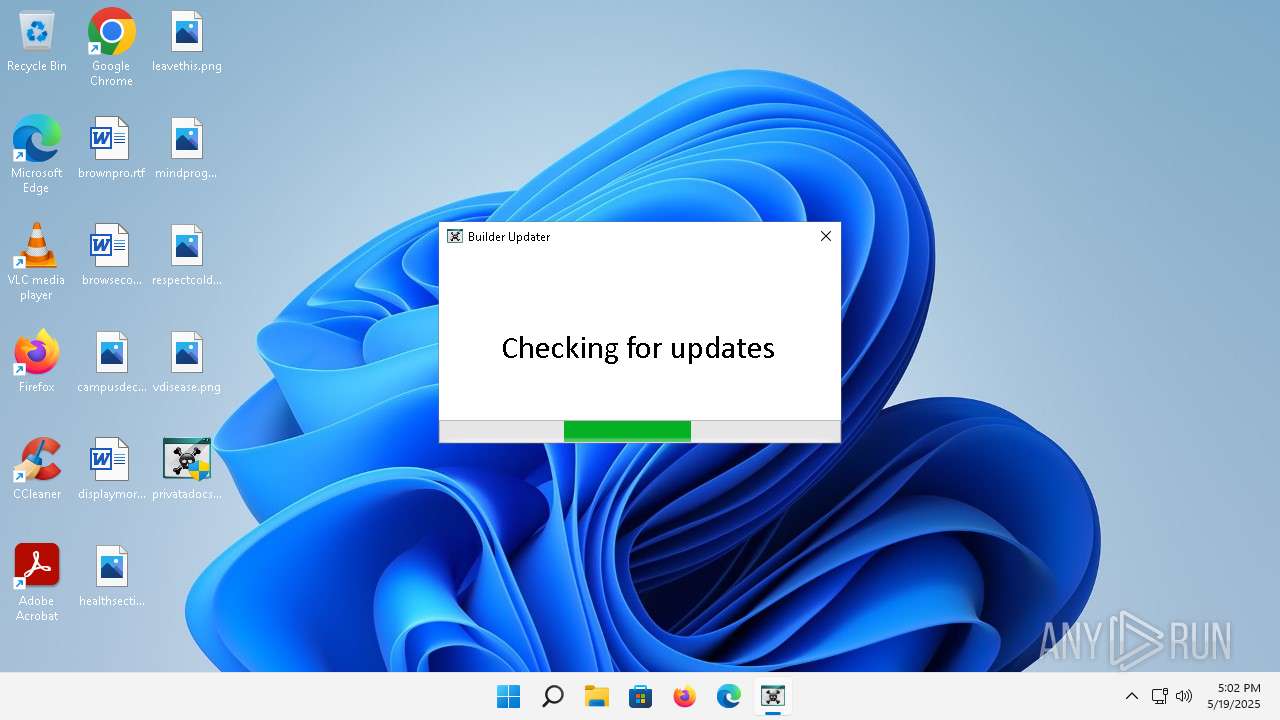
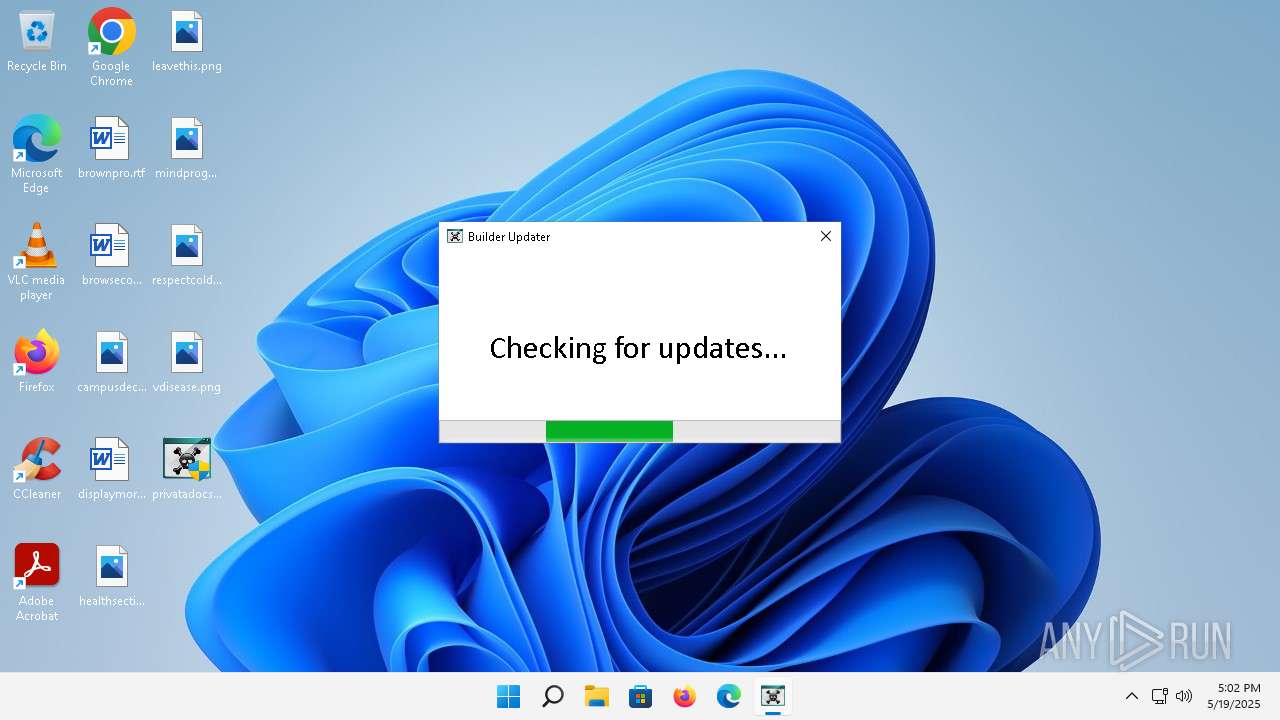
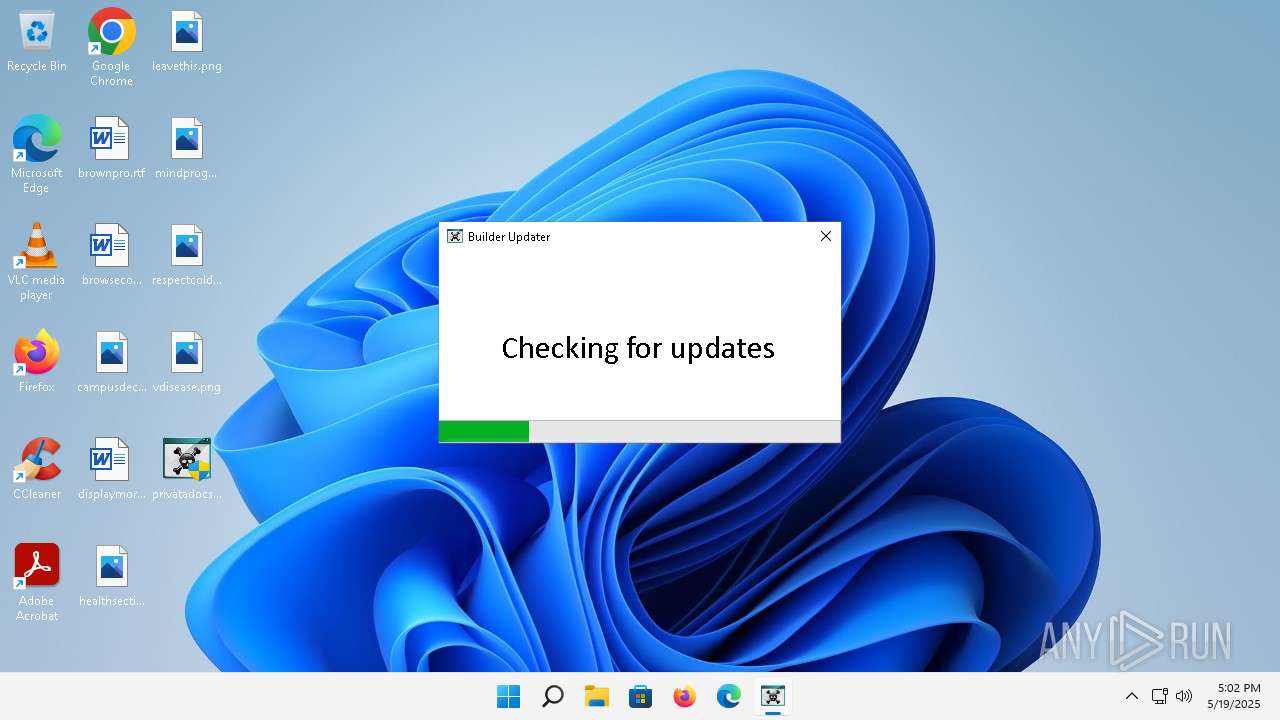
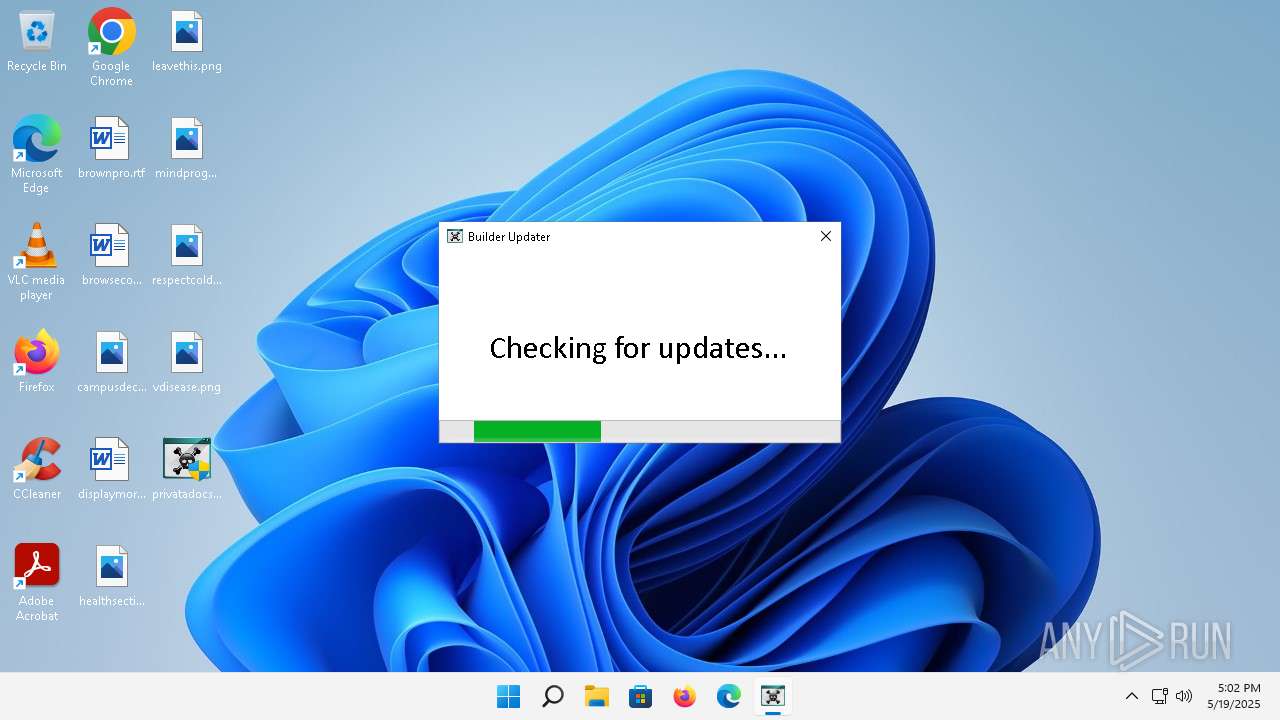
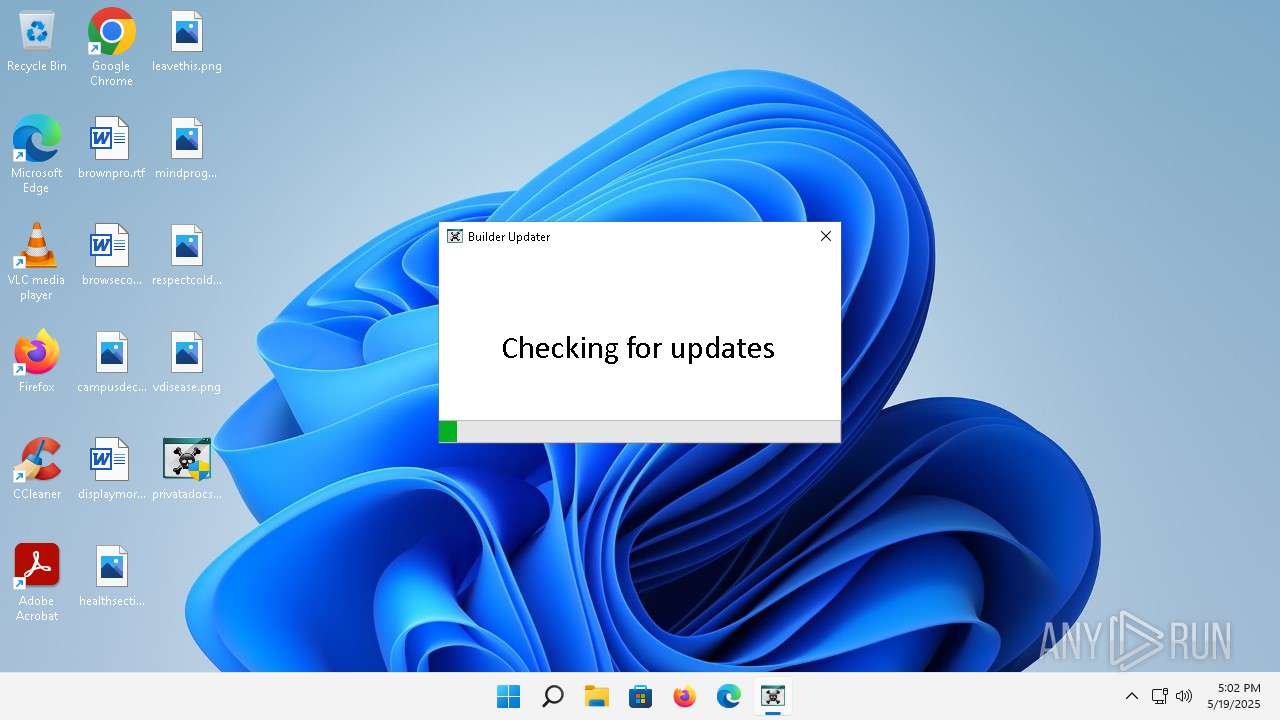
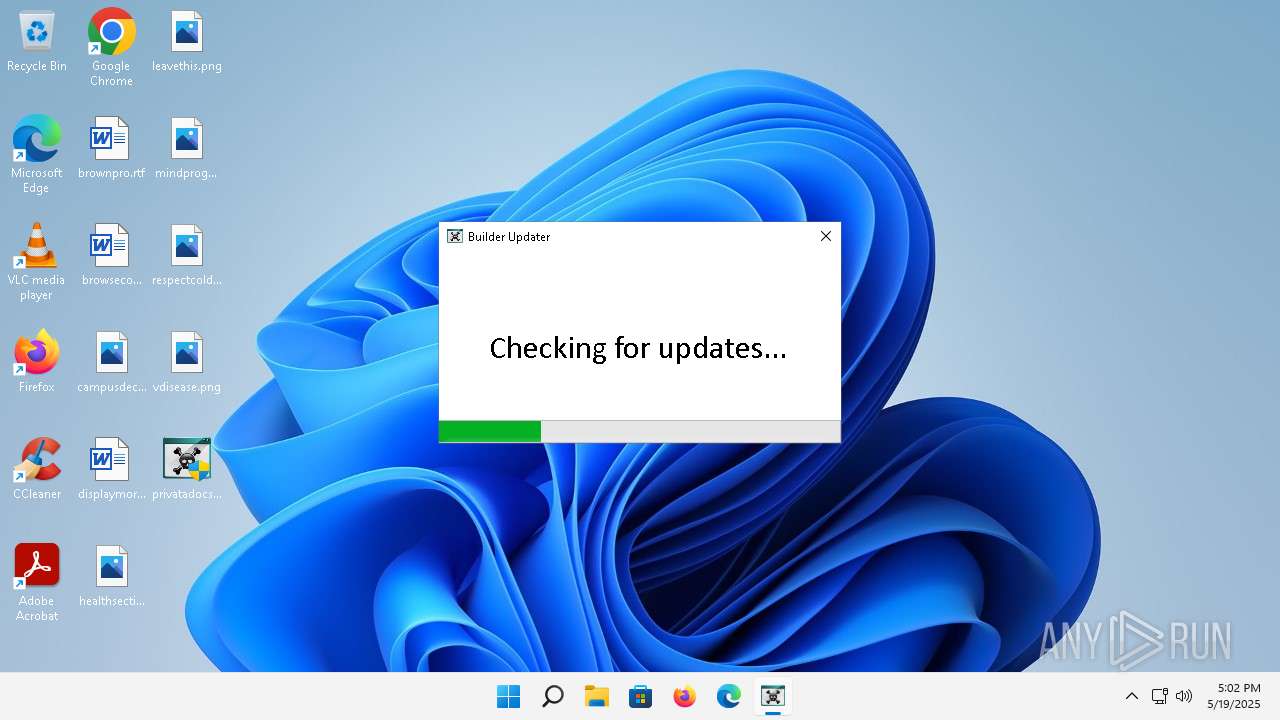
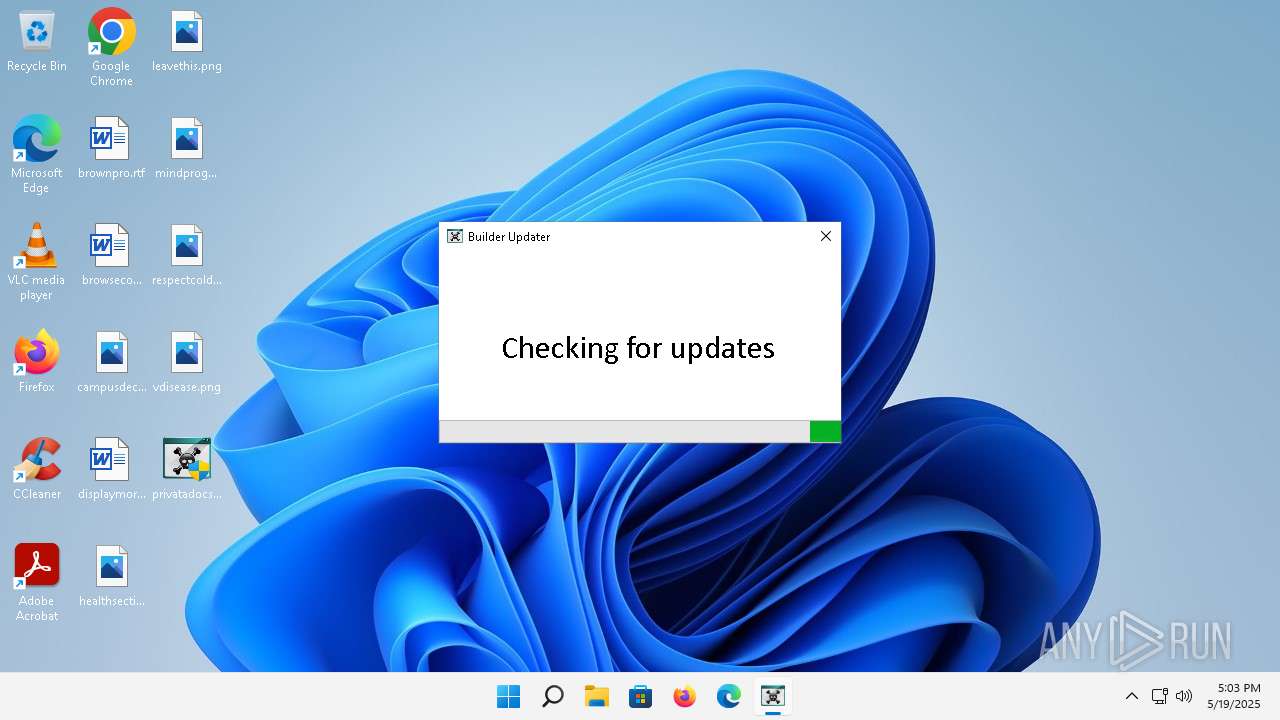
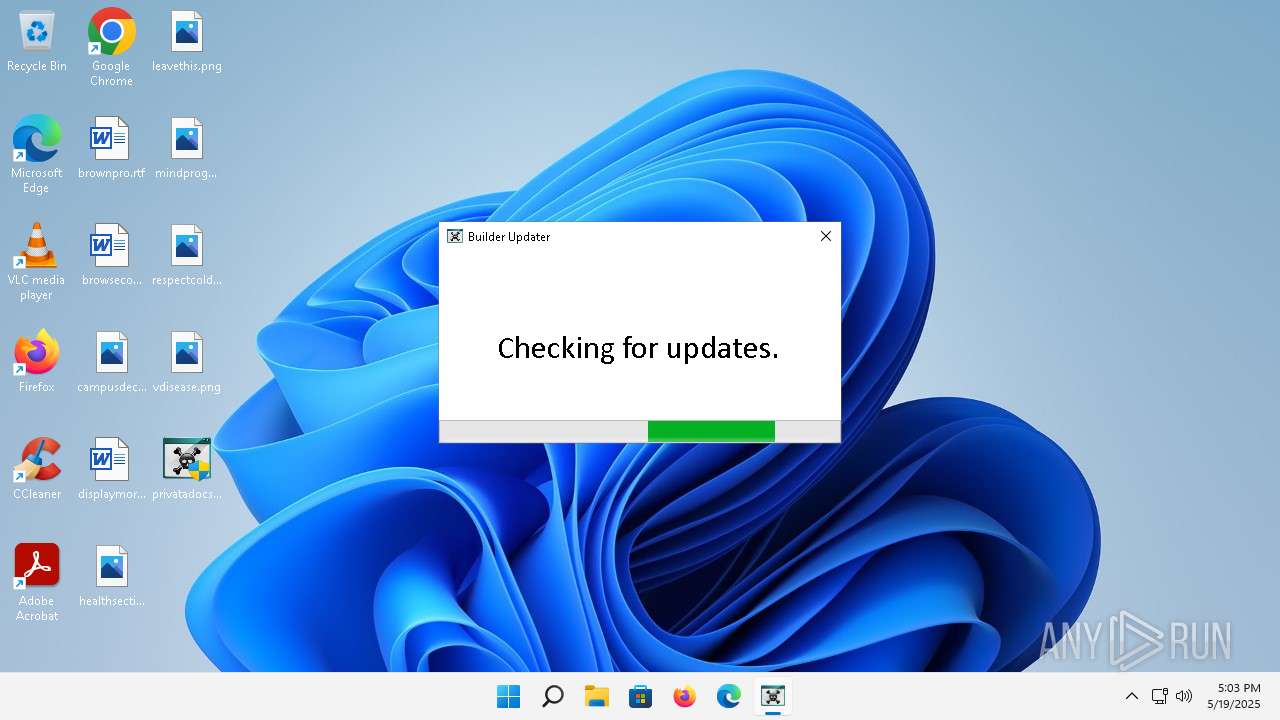
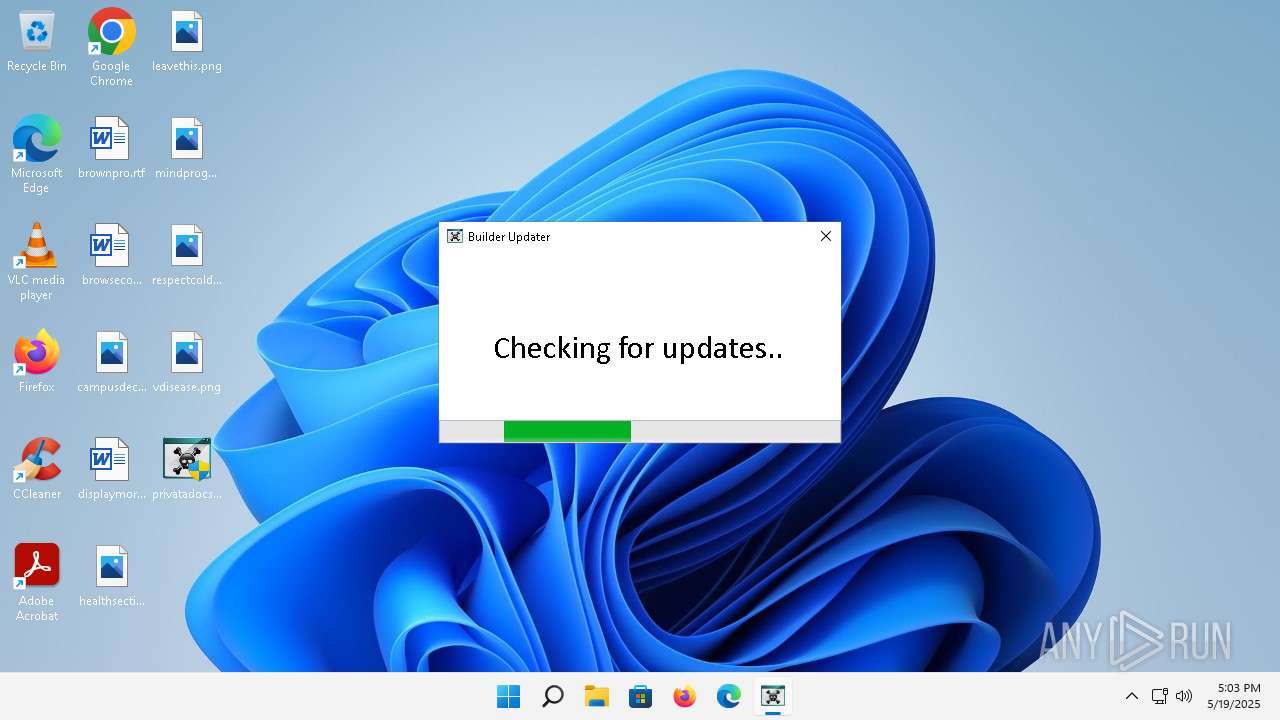
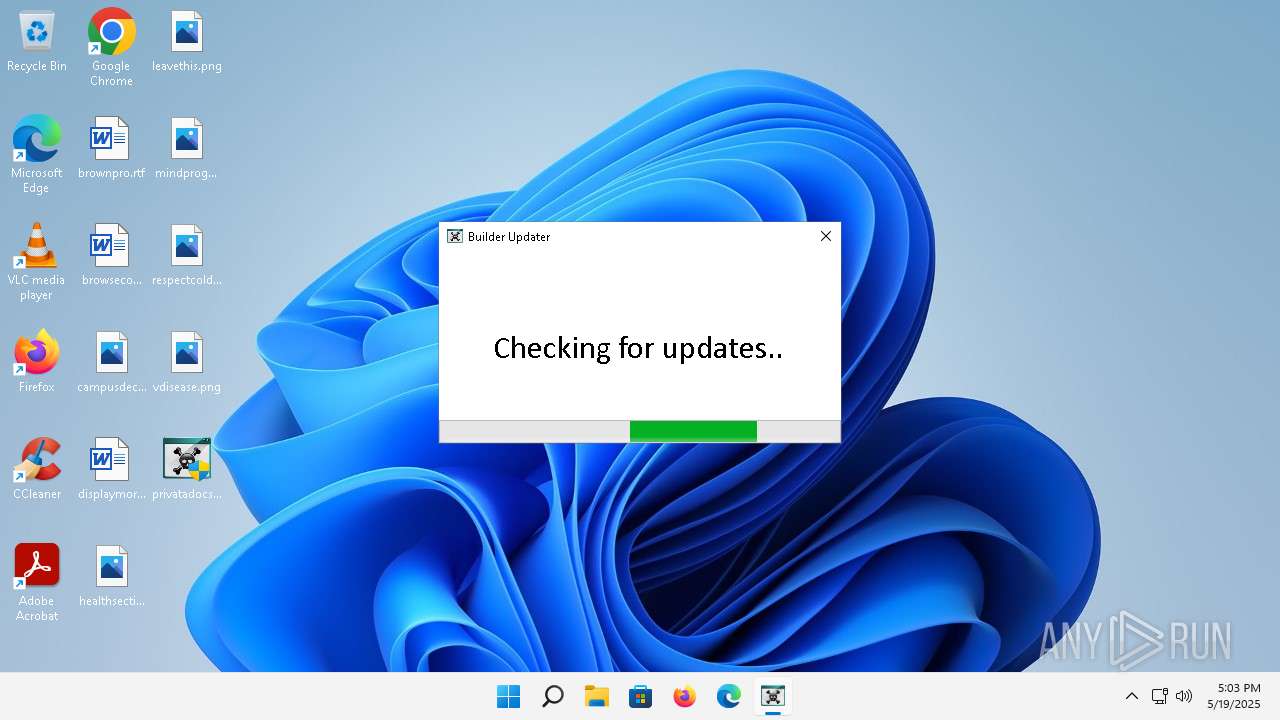
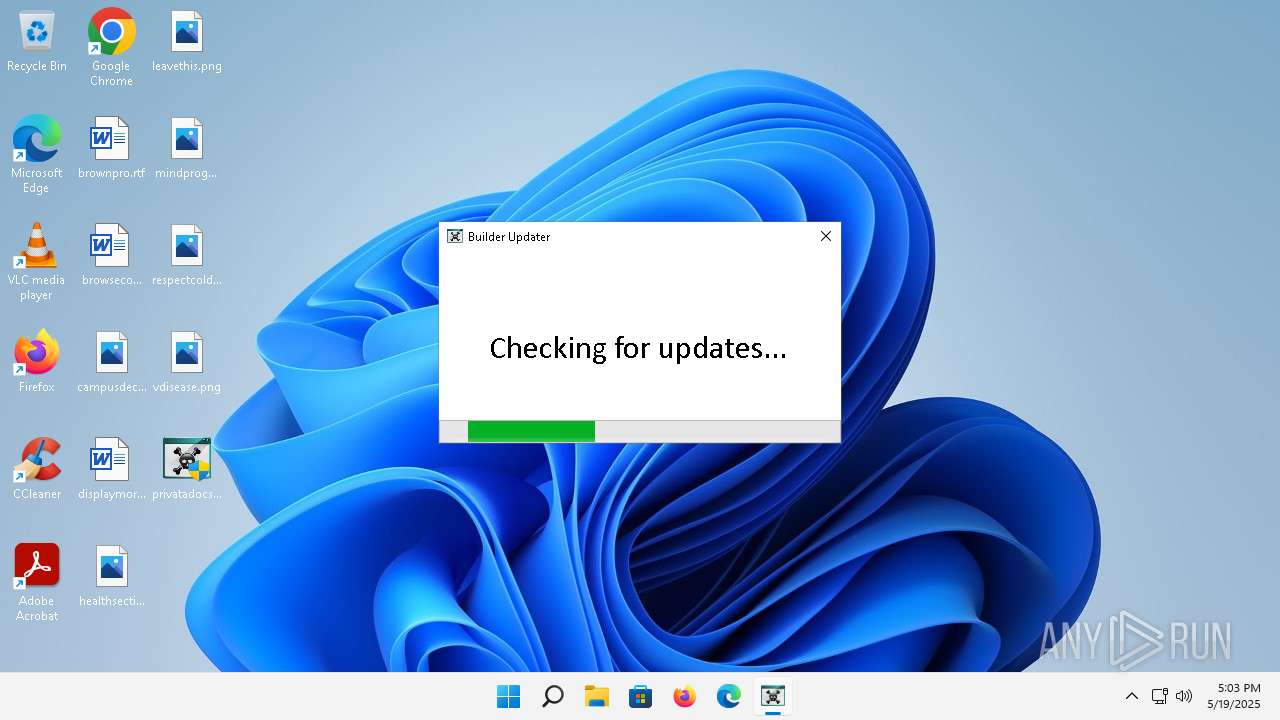
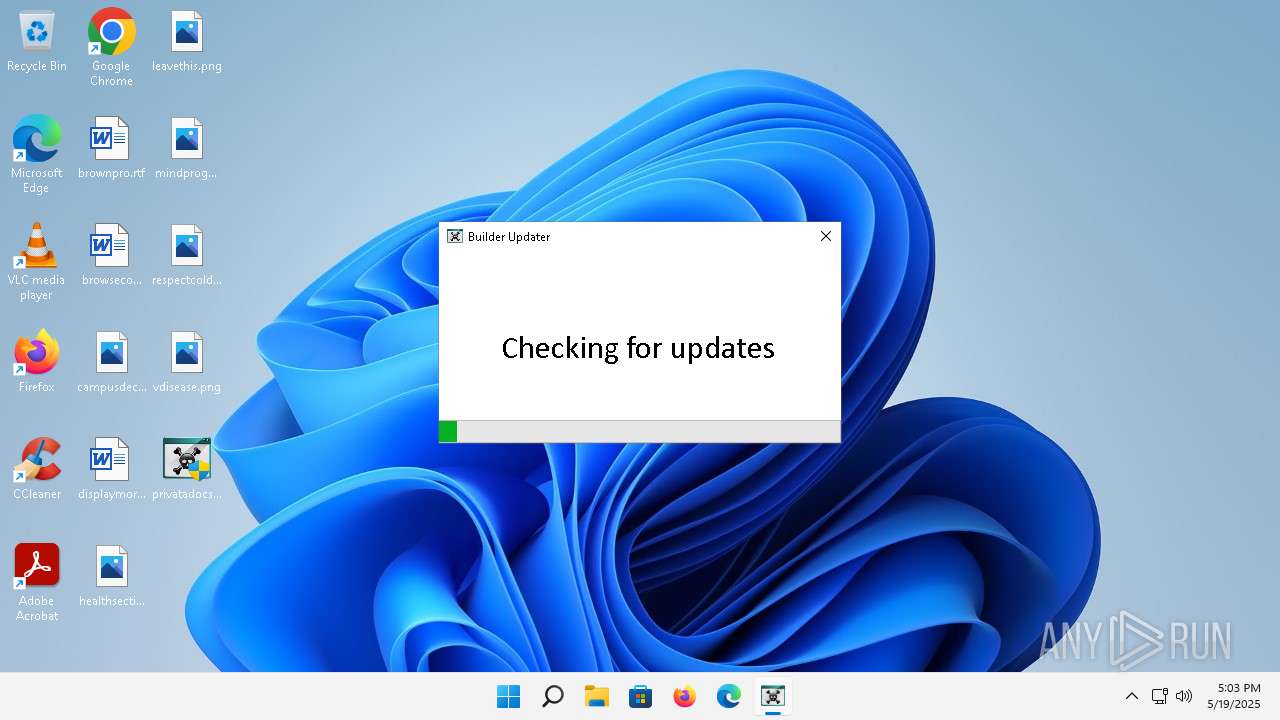
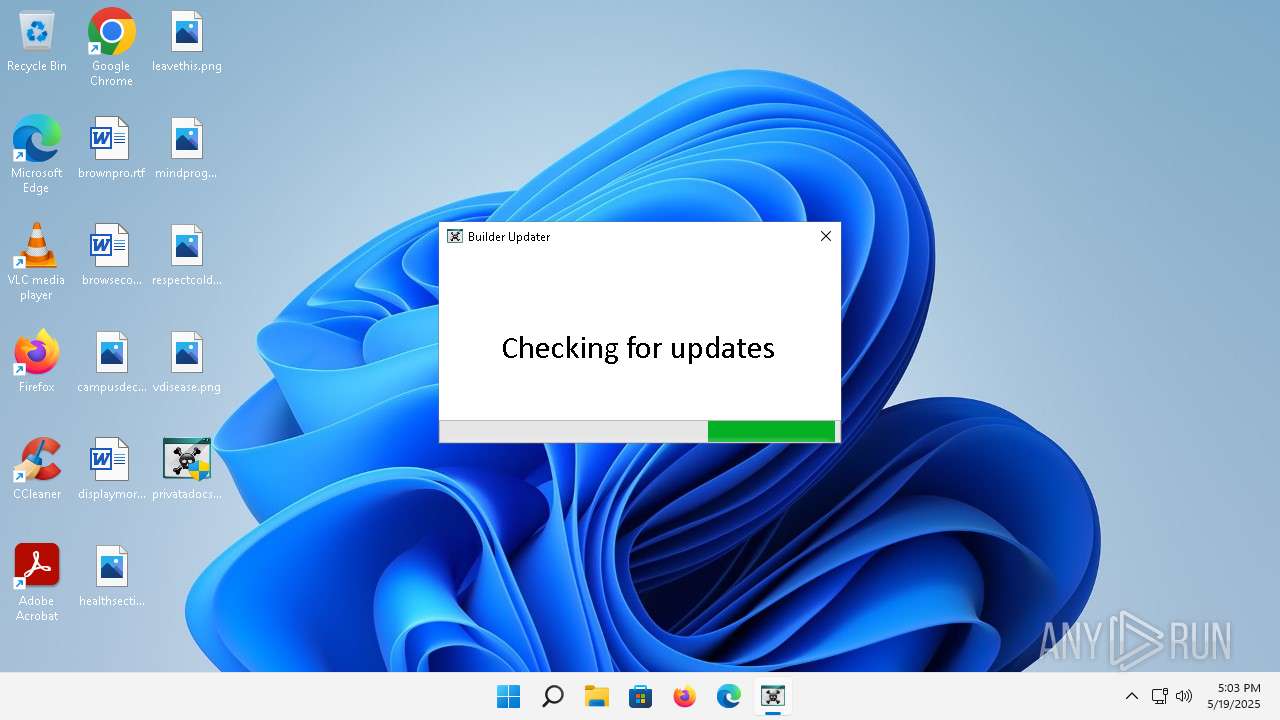
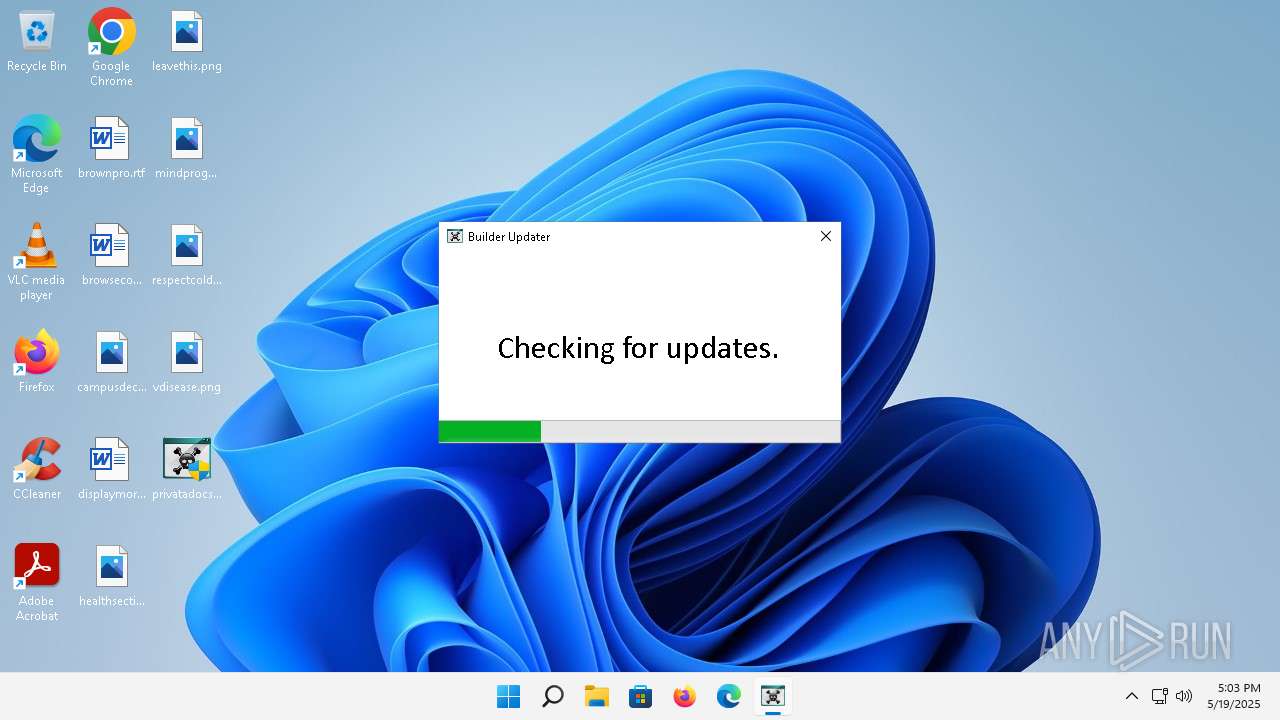
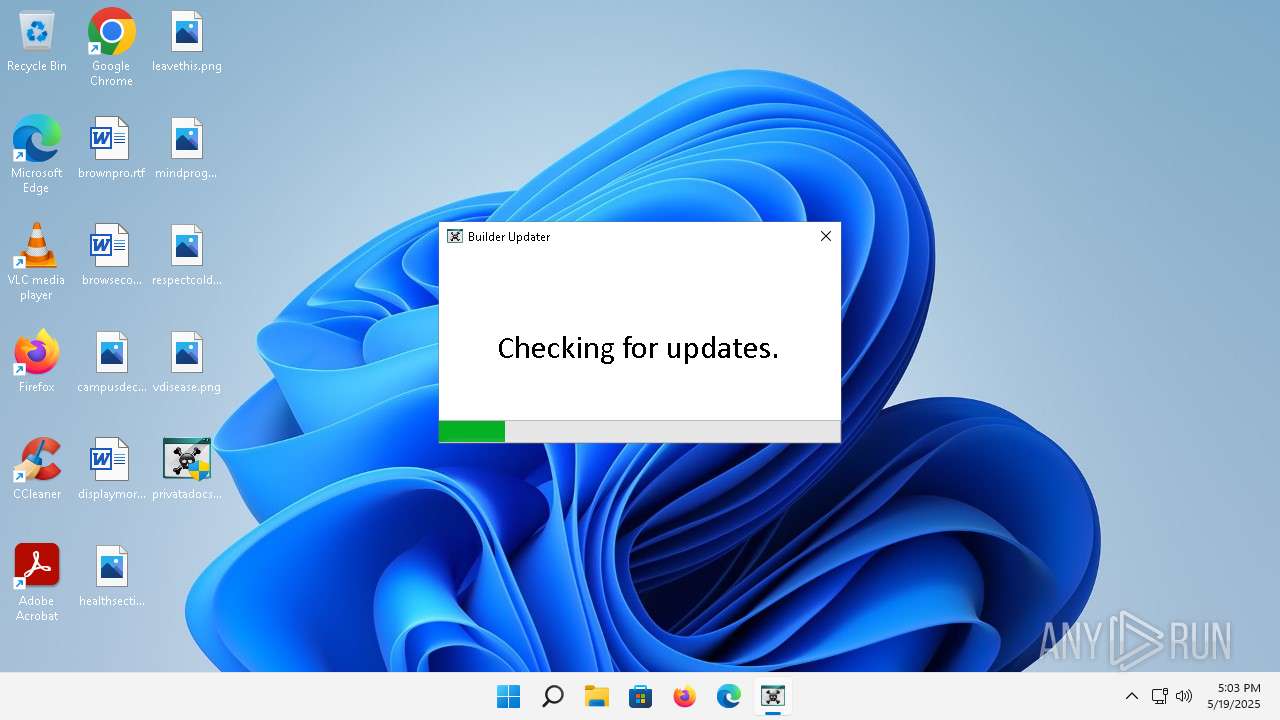
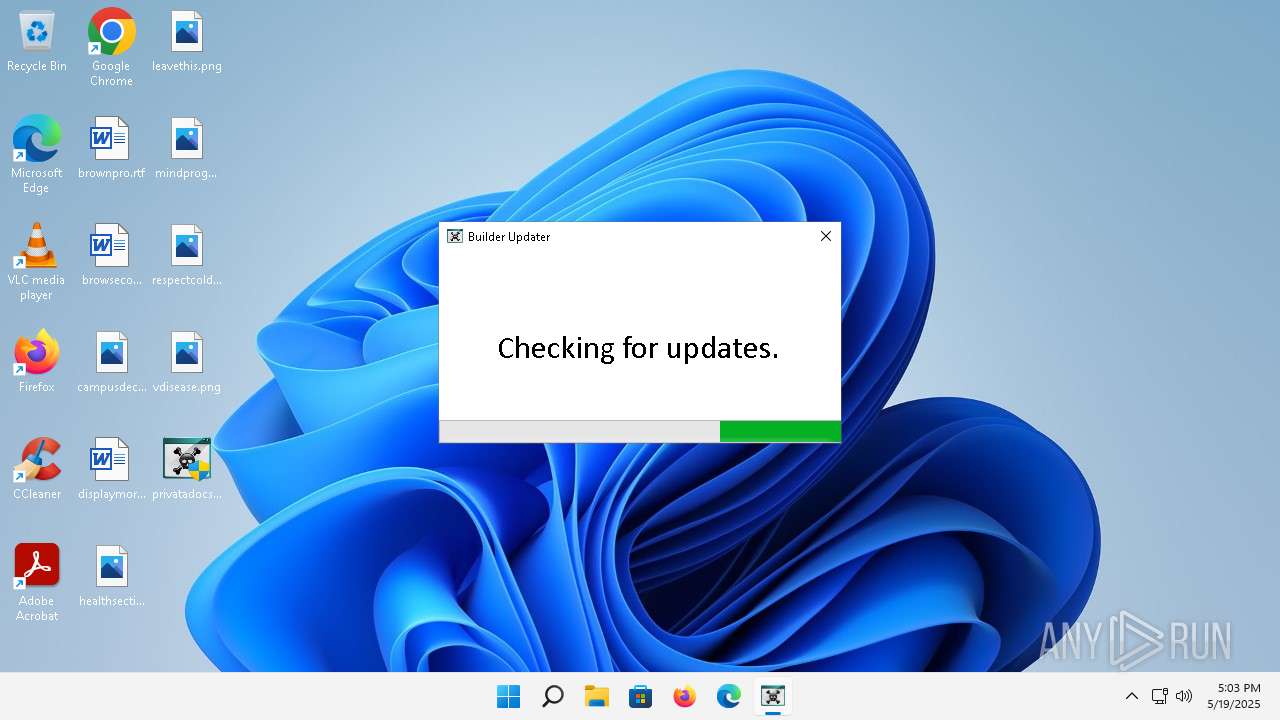
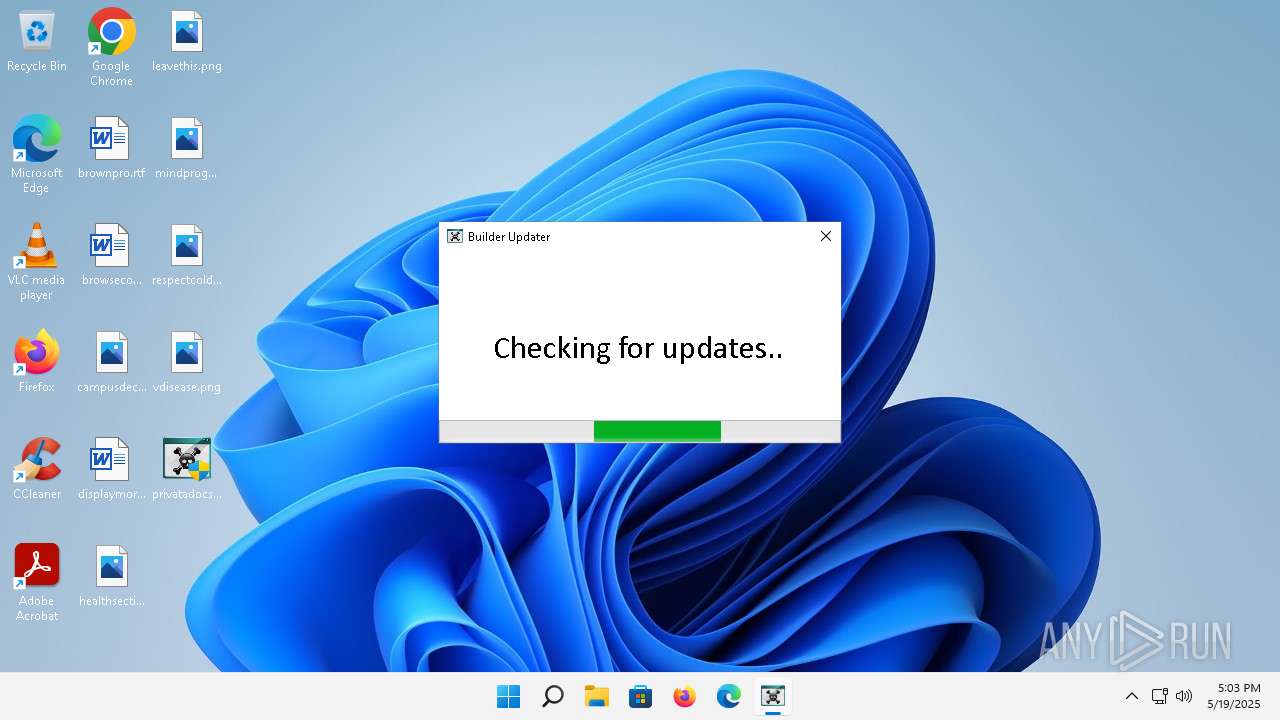
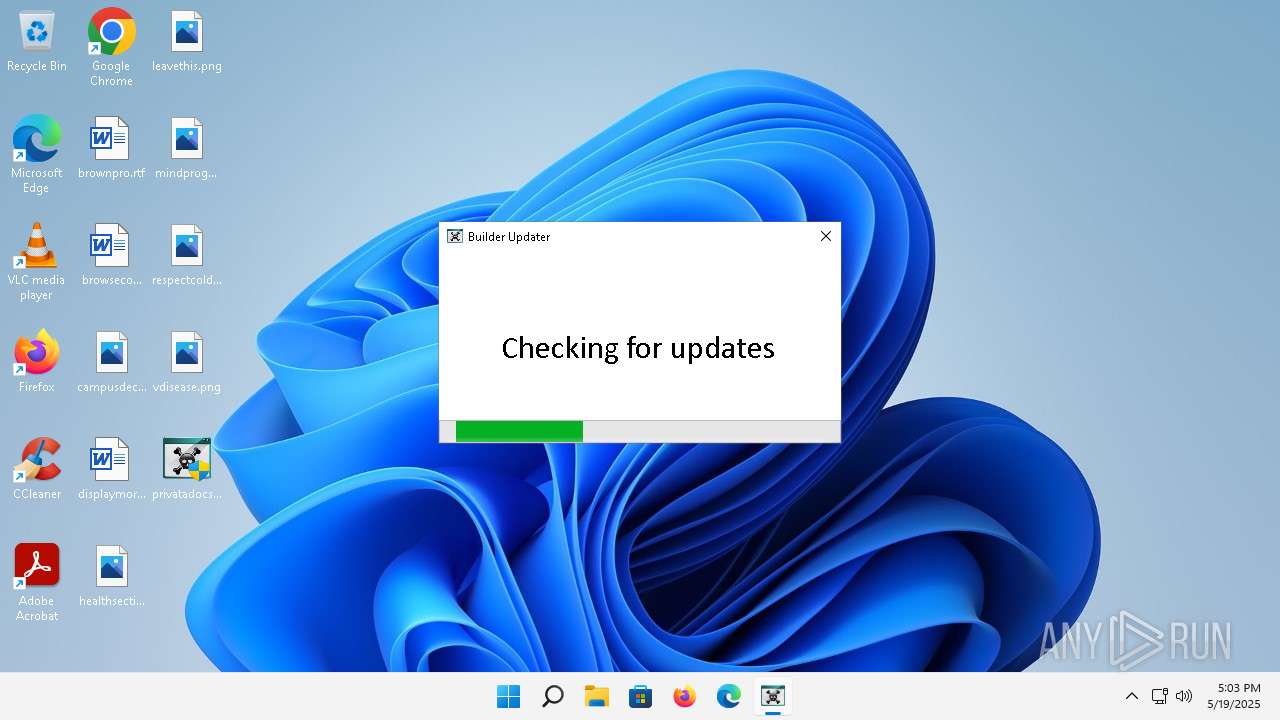
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5740 | "C:\Users\admin\Desktop\privatadocs.exe" | C:\Users\admin\Desktop\privatadocs.exe | — | explorer.exe | |||||||||||
User: admin Company: sumhex Integrity Level: MEDIUM Description: Updater for upO Builder Exit code: 3221226540 Version: 0.9.7.0 Modules
| |||||||||||||||
| 6124 | "C:\Users\admin\Desktop\privatadocs.exe" | C:\Users\admin\Desktop\privatadocs.exe | explorer.exe | ||||||||||||
User: admin Company: sumhex Integrity Level: HIGH Description: Updater for upO Builder Version: 0.9.7.0 Modules
| |||||||||||||||
Total events
3 404
Read events
3 390
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6124) privatadocs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\privatadocs_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
11
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.50.131.202:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?dfa57398ee8fc3fc | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 88.221.110.216:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 23.50.131.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?e8295883656f7dad | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 23.50.131.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?6fdd1136c0f80710 | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 23.50.131.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?ef64459d07e8a2ca | unknown | — | — | whitelisted |
2768 | svchost.exe | GET | 200 | 23.50.131.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?064b5ebb11c8d78a | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 88.221.110.216:80 | — | Akamai International B.V. | DE | unknown |
900 | smartscreen.exe | 20.82.9.214:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.50.131.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
6124 | privatadocs.exe | 185.199.108.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
3204 | svchost.exe | 23.197.142.186:443 | fs.microsoft.com | Akamai International B.V. | US | whitelisted |
4576 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2776 | svchost.exe | 20.50.201.201:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2768 | svchost.exe | 23.50.131.208:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Generic Protocol Command Decode | SURICATA HTTP Request unrecognized authorization method |
1664 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |