| File name: | sample_105.zip |
| Full analysis: | https://app.any.run/tasks/cba36864-081c-4375-a81f-6805fca53cf4 |
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 10:45:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 96C625E75BA5B78244FFE7CC5DB5E780 |
| SHA1: | E3FB2208CECA0337F37D0CAFFBA808B3A99D5174 |
| SHA256: | 49DB364AAE7BF313F4BCCDE1365164D1AD2DDF70AC9C98BFCACB14572D27FD57 |
| SSDEEP: | 12288:1GY57KVpISRpQ5W4kEAaa8KHh+l5MjLYIuYgpLxTqo7:kYc16BA/5UK8IPgplTqy |
MALICIOUS
Application was dropped or rewritten from another process
- sample_105.exe (PID: 3216)
Changes settings of System certificates
- sample_105.exe (PID: 3216)
Changes the autorun value in the registry
- sample_105.exe (PID: 3216)
SUSPICIOUS
Reads internet explorer settings
- sample_105.exe (PID: 3216)
Adds / modifies Windows certificates
- sample_105.exe (PID: 3216)
INFO
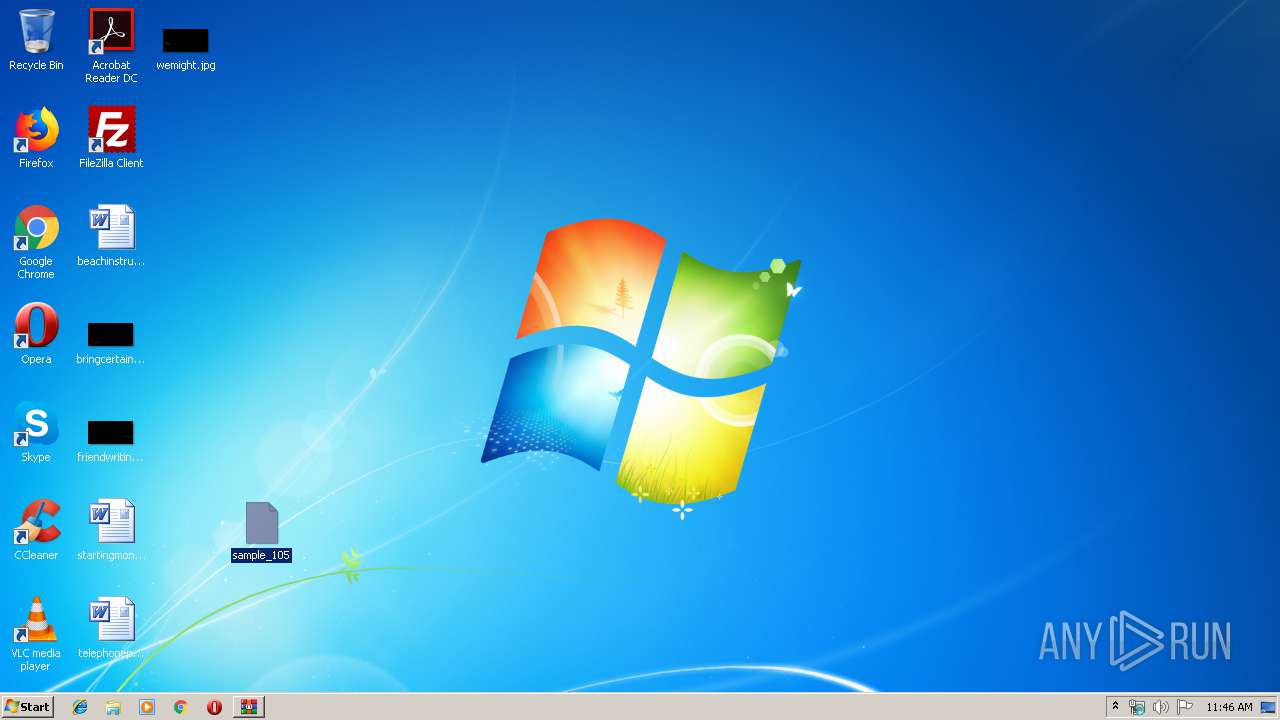
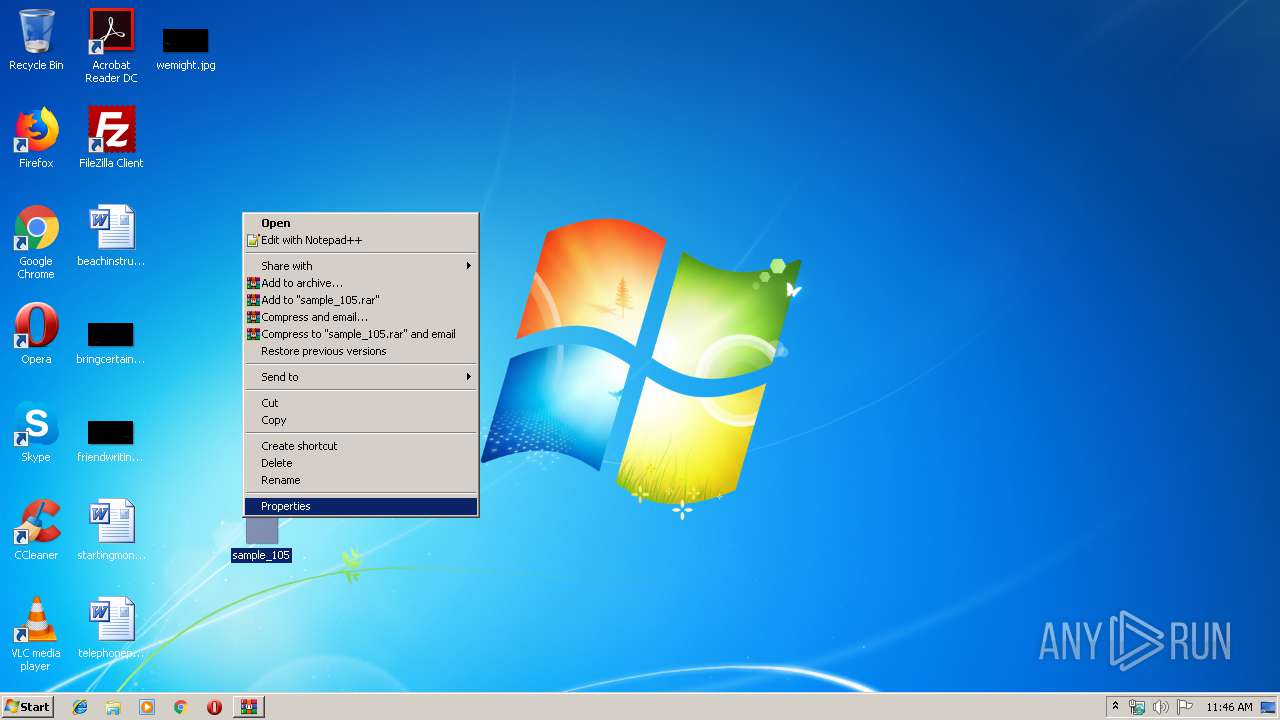
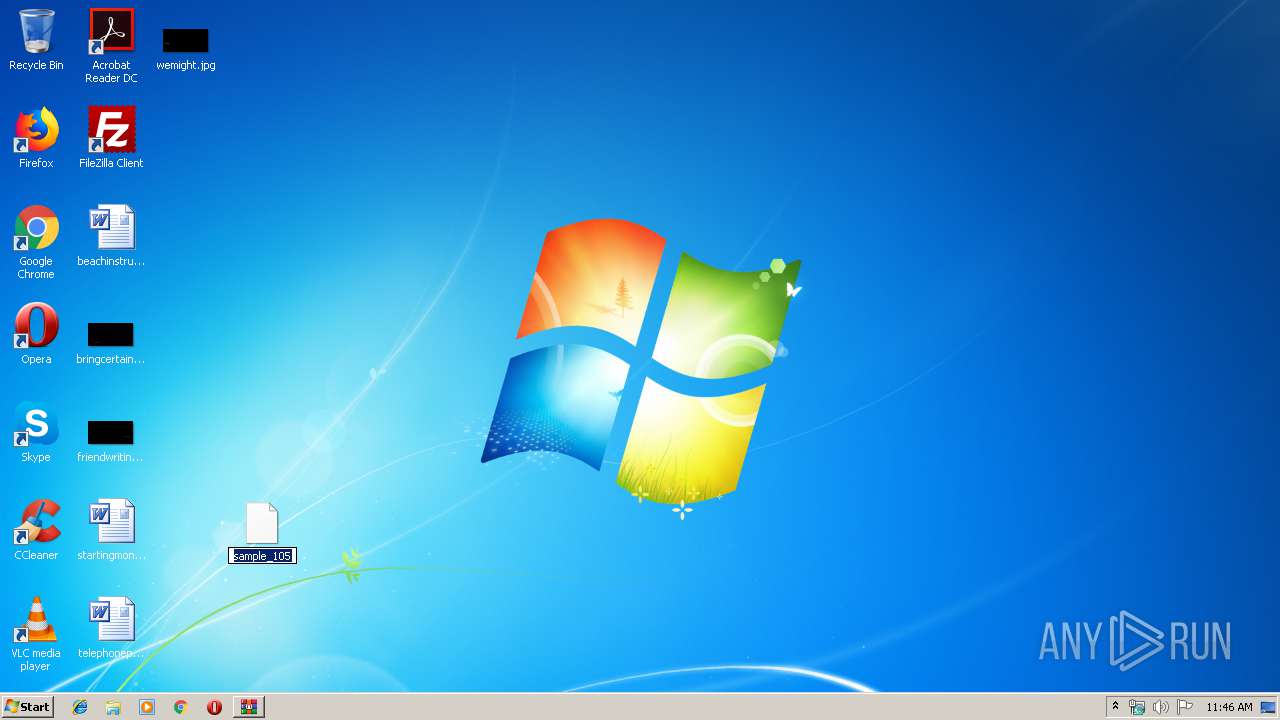
Manual execution by user
- sample_105.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 20:40:26 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_105/ |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
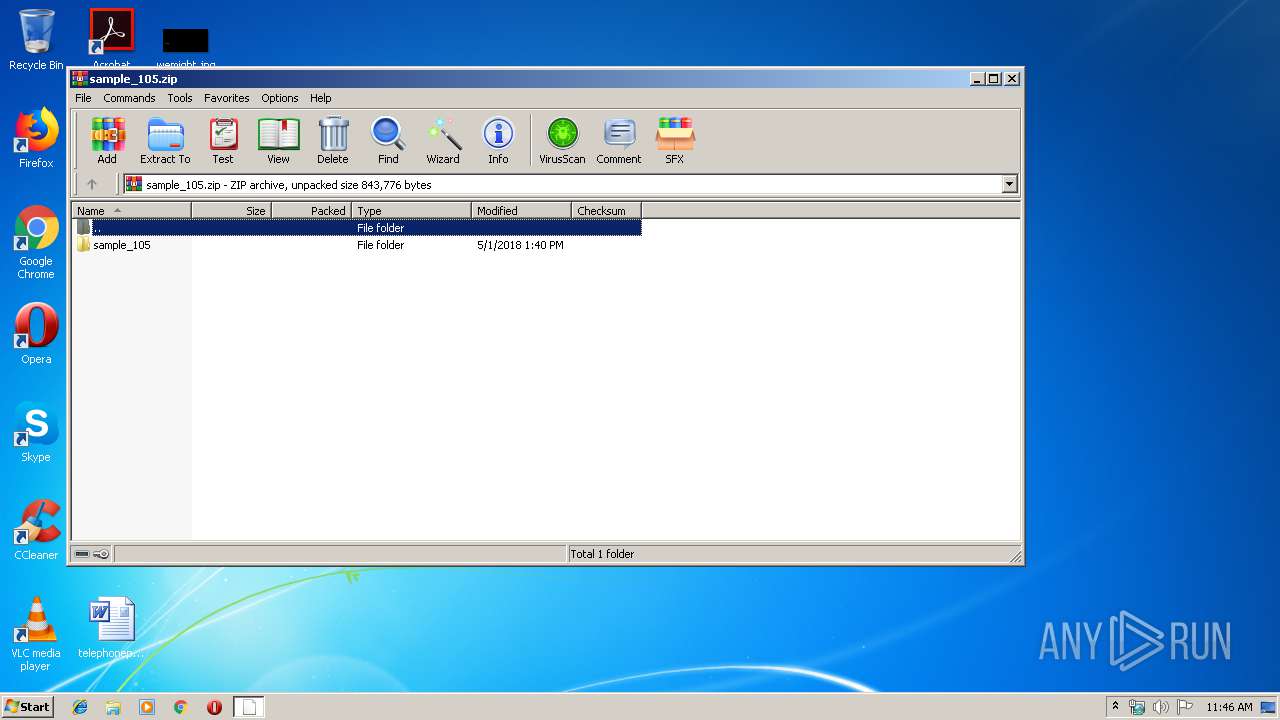
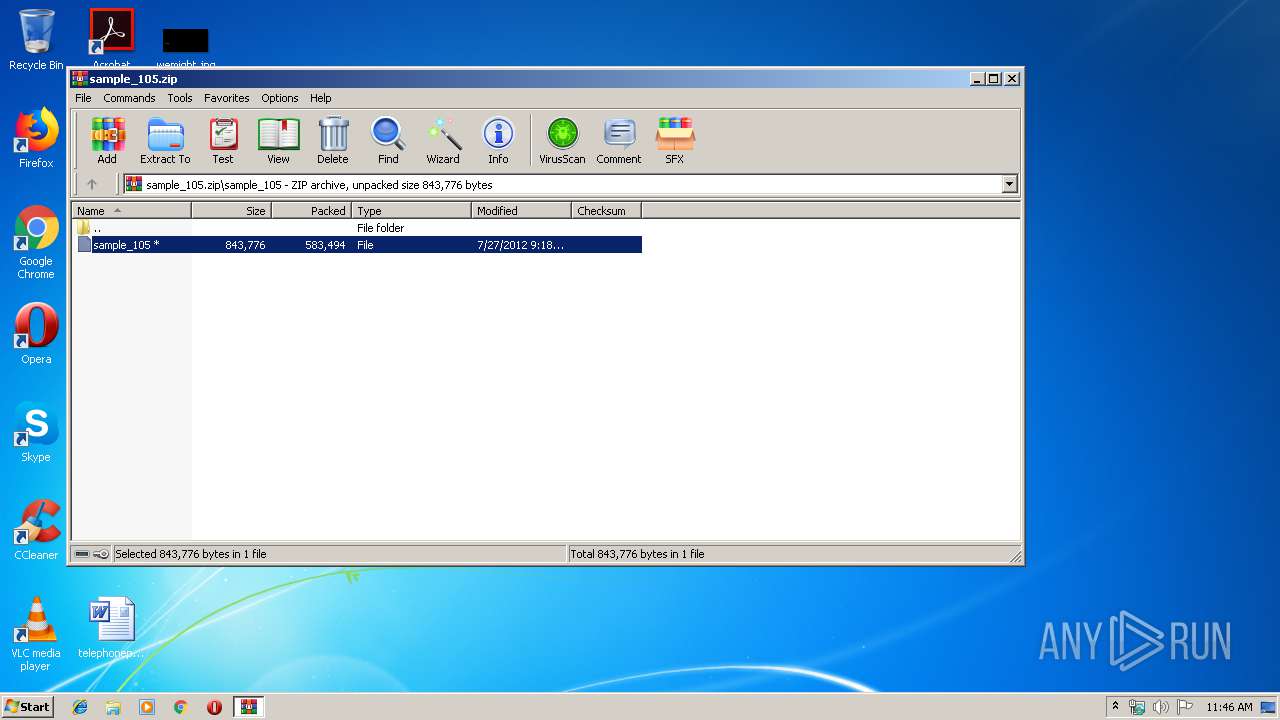
| 2952 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_105.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3216 | "C:\Users\admin\Desktop\sample_105.exe" | C:\Users\admin\Desktop\sample_105.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
1 017
Read events
971
Write events
44
Delete events
2
Modification events
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_105.zip | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
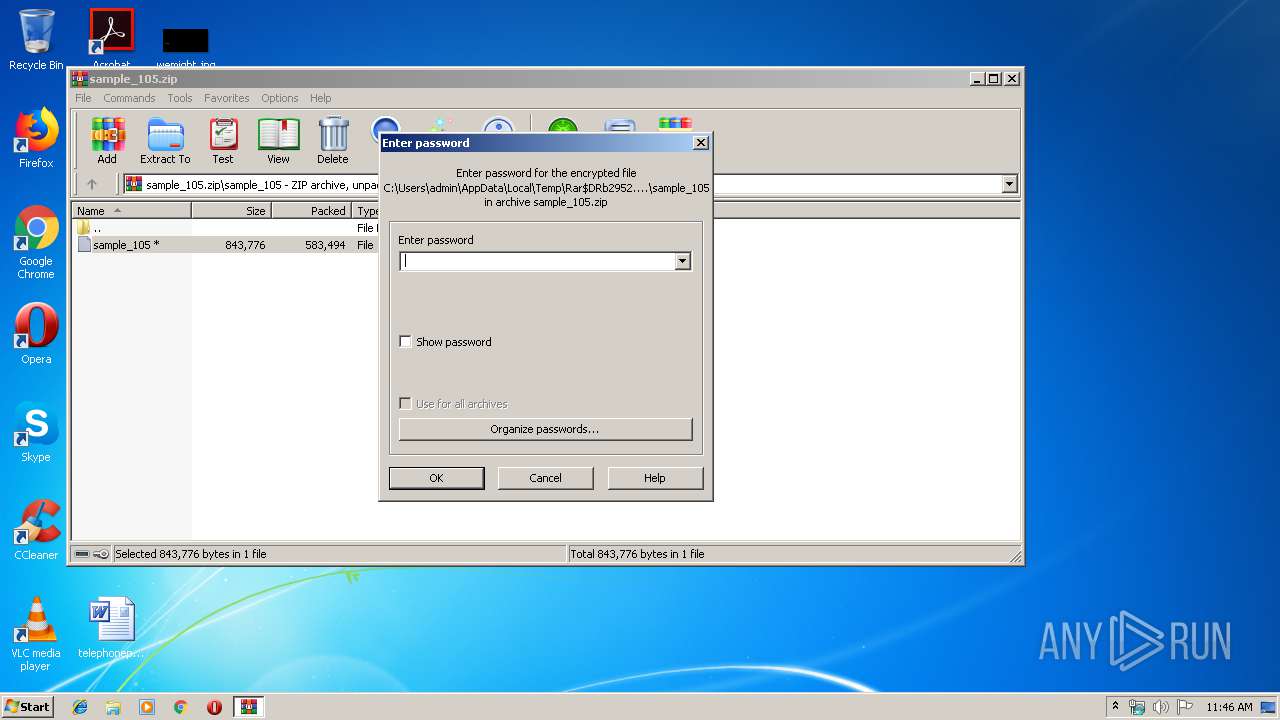
| (PID) Process: | (2952) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3216) sample_105.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2952.38751\sample_105\sample_105 | — | |
MD5:— | SHA256:— | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ErrorPageTemplate[1] | — | |
MD5:— | SHA256:— | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\errorPageStrings[1] | — | |
MD5:— | SHA256:— | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\httpErrorPagesScripts[1] | — | |
MD5:— | SHA256:— | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\dnserrordiagoff_webOC[1] | html | |
MD5:— | SHA256:— | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\navcancl[1] | html | |
MD5:4BCFE9F8DB04948CDDB5E31FE6A7F984 | SHA256:BEE0439FCF31DE76D6E2D7FD377A24A34AC8763D5BF4114DA5E1663009E24228 | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ErrorPageTemplate[2] | text | |
MD5:F4FE1CB77E758E1BA56B8A8EC20417C5 | SHA256:8D018639281B33DA8EB3CE0B21D11E1D414E59024C3689F92BE8904EB5779B5F | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\bullet[1] | image | |
MD5:0C4C086DD852704E8EEB8FF83E3B73D1 | SHA256:1CB3B6EA56C5B5DECF5E1D487AD51DBB2F62E6A6C78F23C1C81FDA1B64F8DB16 | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\background_gradient[1] | image | |
MD5:20F0110ED5E4E0D5384A496E4880139B | SHA256:1471693BE91E53C2640FE7BAEECBC624530B088444222D93F2815DFCE1865D5B | |||
| 3216 | sample_105.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\info_48[1] | image | |
MD5:49E0EF03E74704089A60C437085DB89E | SHA256:CAA140523BA00994536B33618654E379216261BABAAE726164A0F74157BB11FF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3216 | sample_105.exe | GET | 301 | 162.125.66.6:80 | http://dl.dropbox.com/u/61023552/MSSTDFMT.DLL.jpg | DE | html | 162 b | shared |
3216 | sample_105.exe | GET | 301 | 162.125.66.6:80 | http://dl.dropbox.com/u/61023552/MSCOMCTL.OCX.jpg | DE | html | 162 b | shared |
3216 | sample_105.exe | GET | 301 | 162.125.66.6:80 | http://dl.dropbox.com/u/61023552/MSCOMCTL.oca.jpg | DE | html | 162 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3216 | sample_105.exe | 162.125.66.6:80 | dl.dropbox.com | Dropbox, Inc. | DE | shared |
3216 | sample_105.exe | 162.125.66.6:443 | dl.dropbox.com | Dropbox, Inc. | DE | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kalagata.no-ip.biz |
| unknown |
dl.dropbox.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a Suspicious no-ip Domain |
3 ETPRO signatures available at the full report