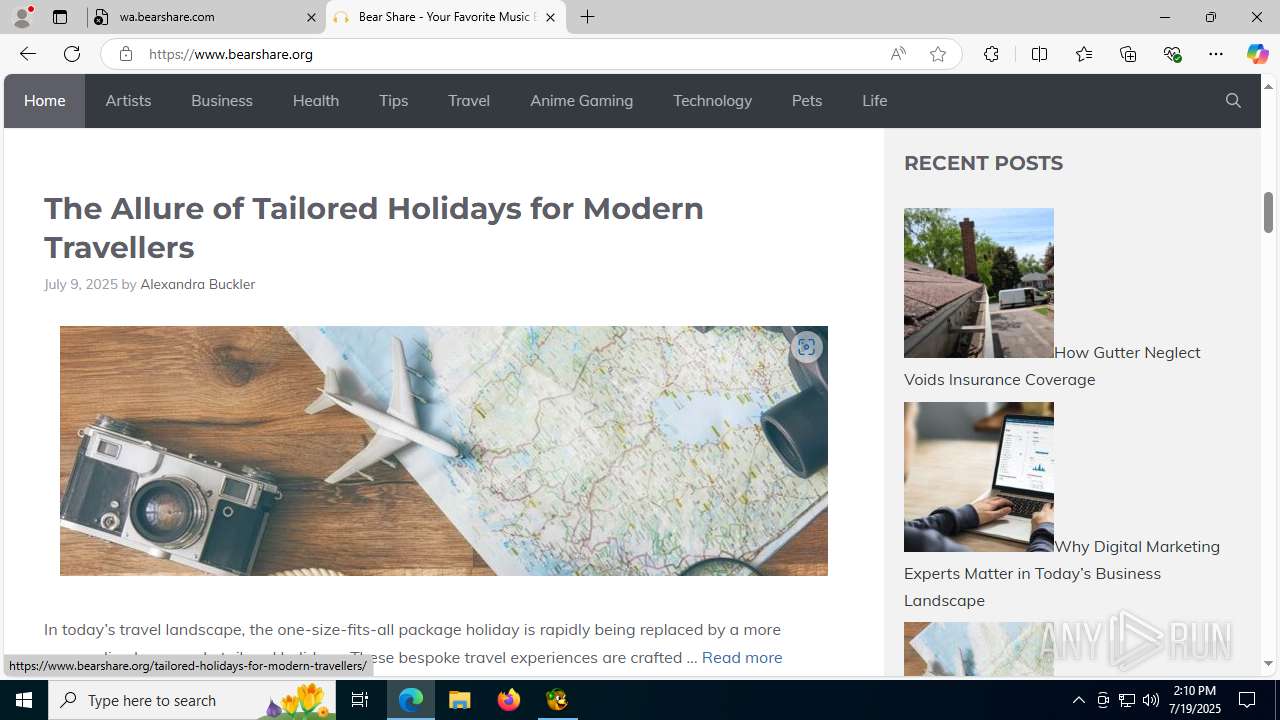
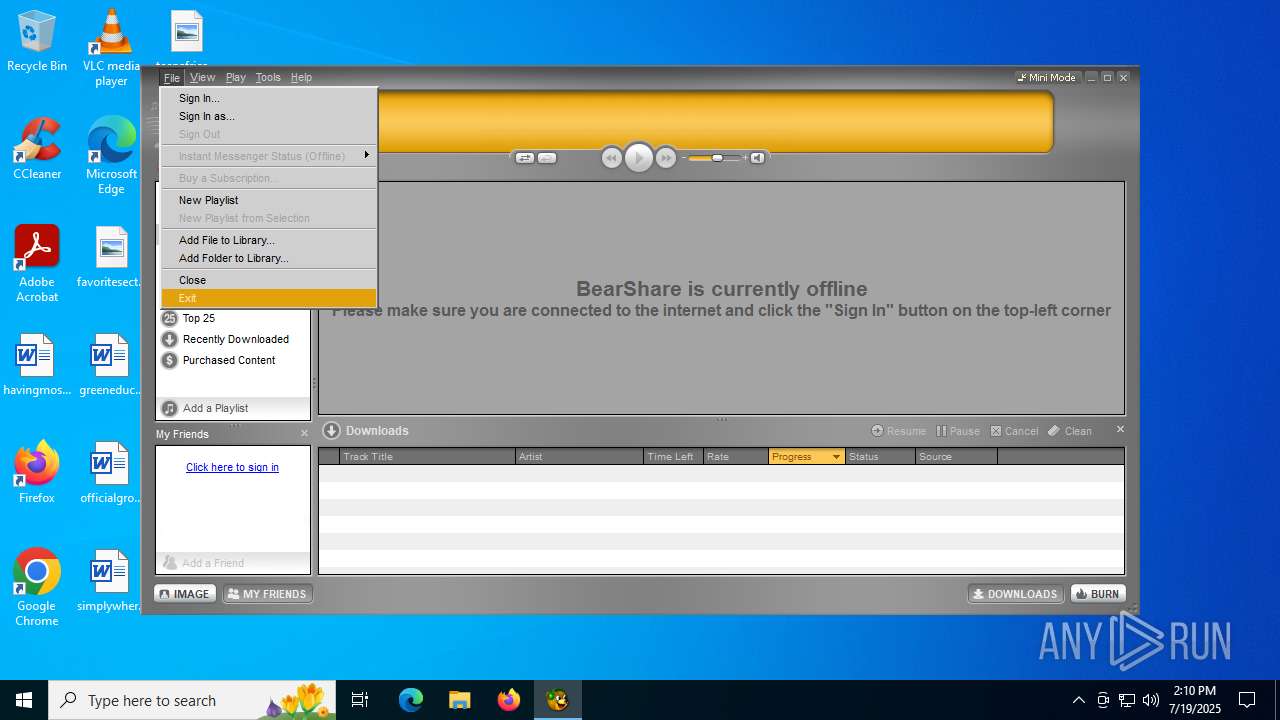
| File name: | BearShareV6.exe |
| Full analysis: | https://app.any.run/tasks/d1cd2e45-cc54-46ba-b488-5e83c8e70304 |
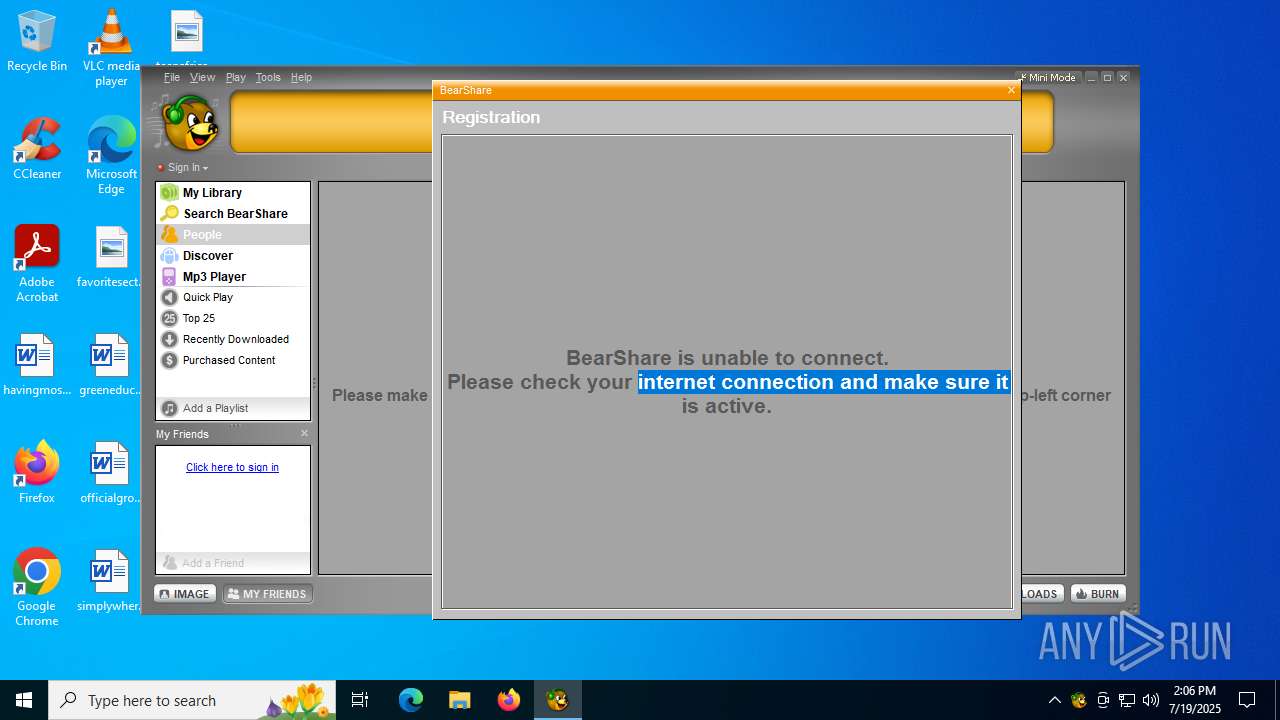
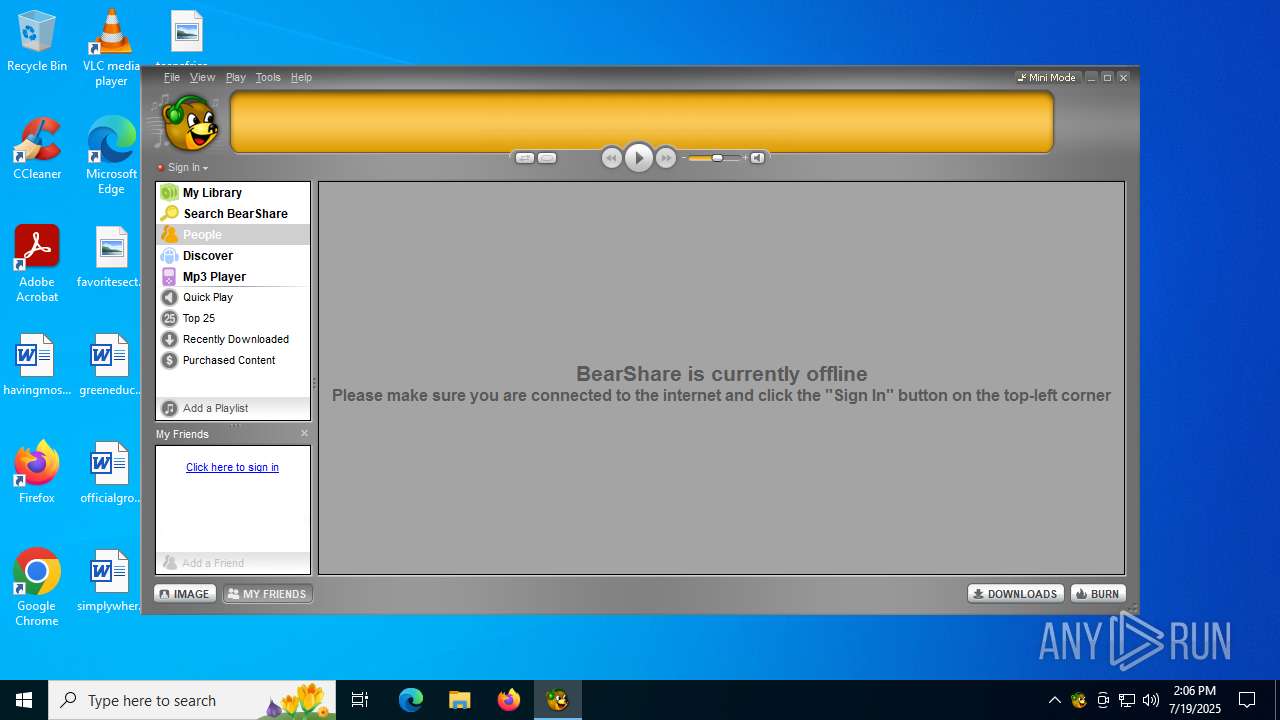
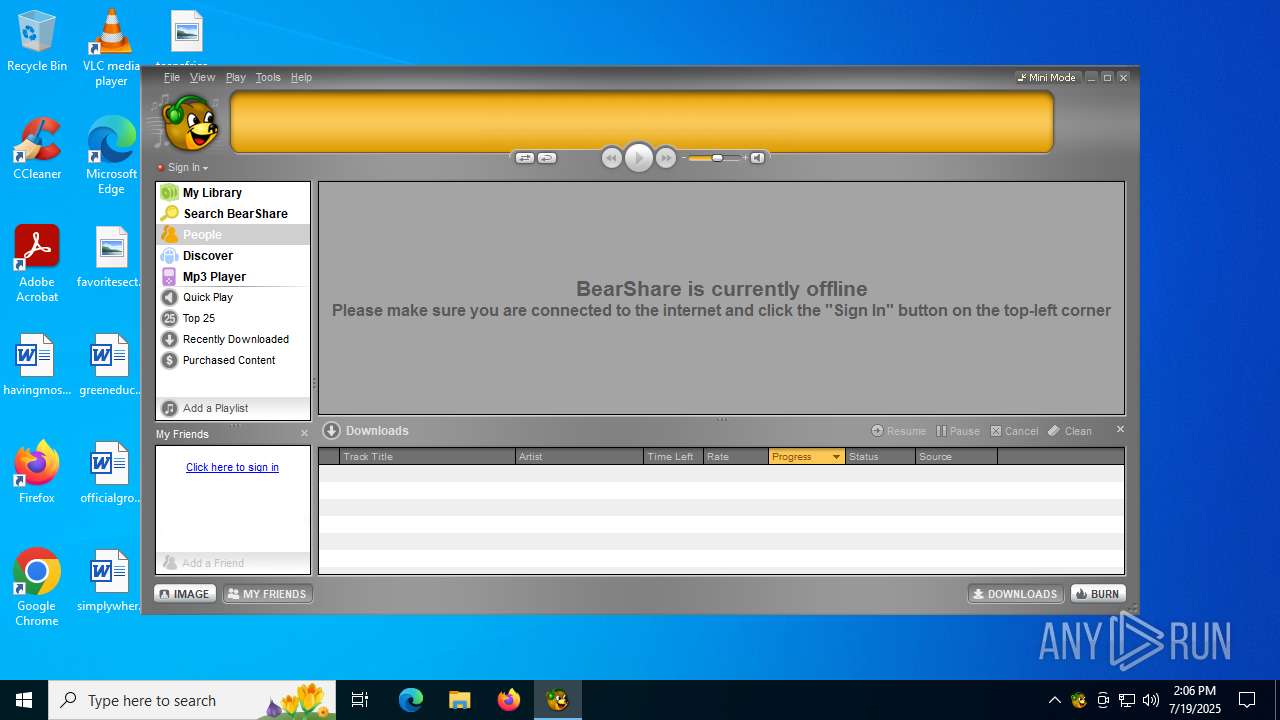
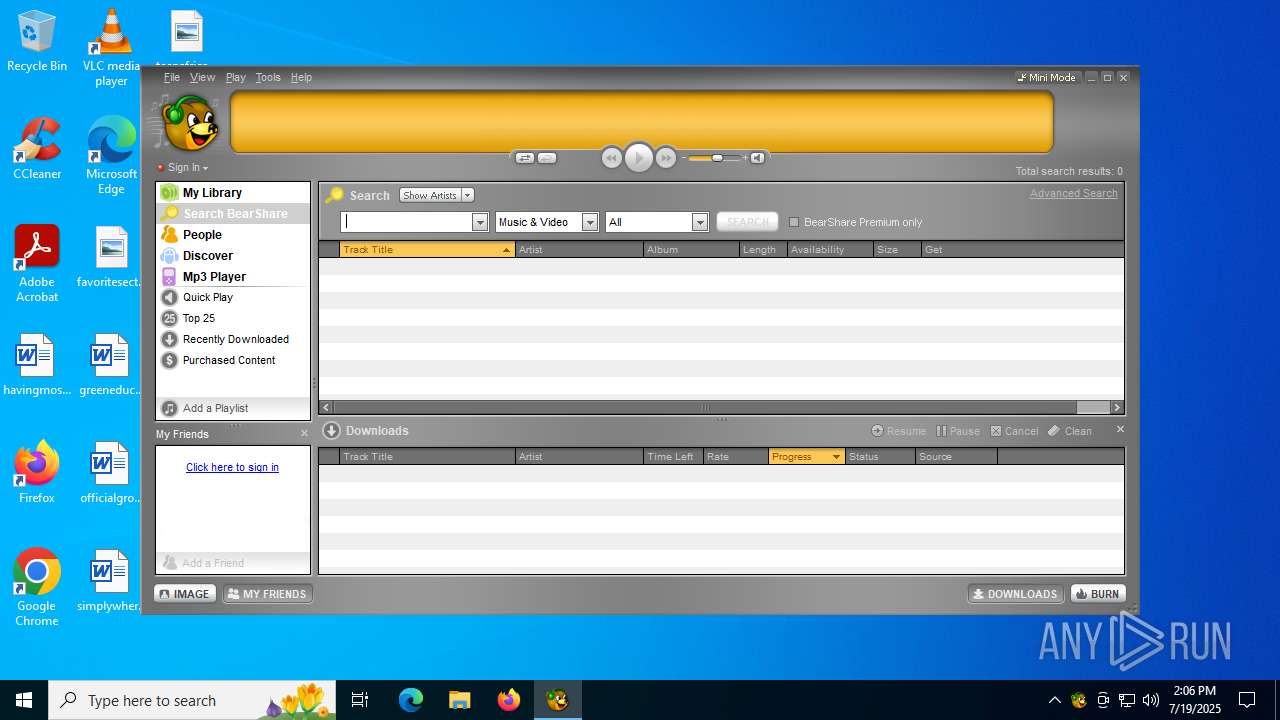
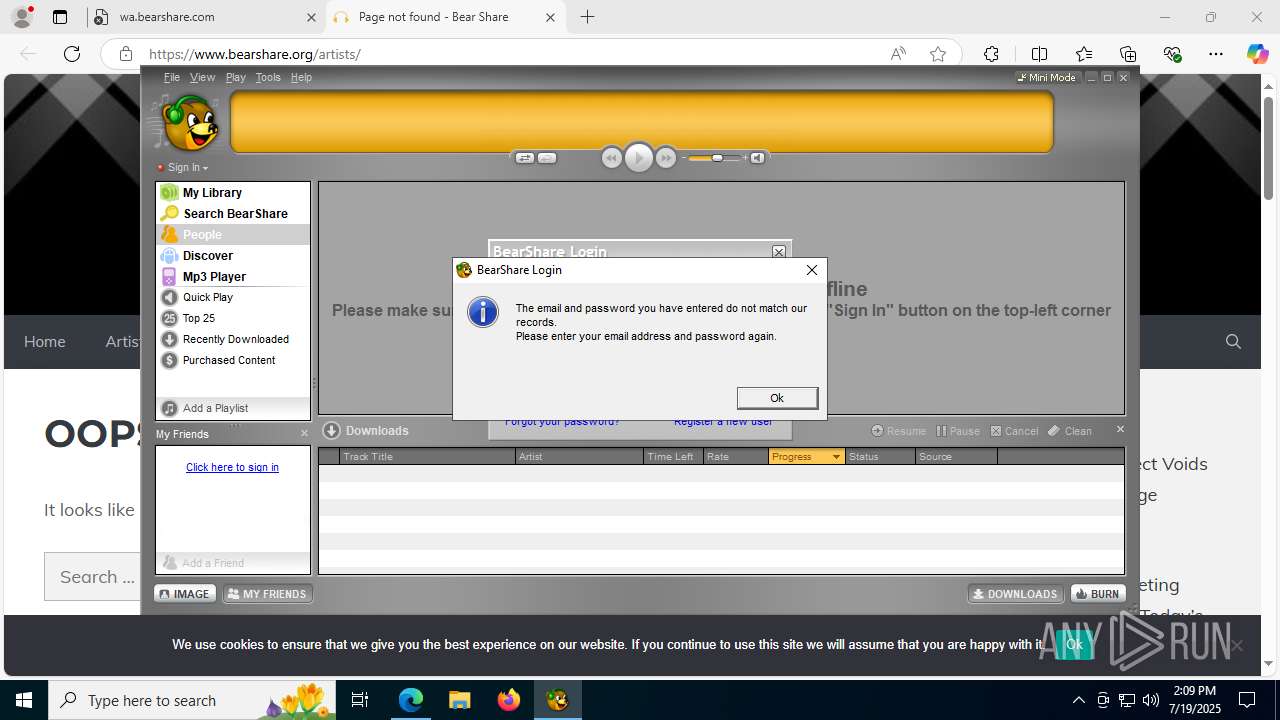
| Verdict: | Malicious activity |
| Analysis date: | July 19, 2025, 14:05:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 4 sections |
| MD5: | 93163FE3C7B948F401142A0EB733203B |
| SHA1: | 3BE3F52C347F3EBA9EA877CCC125B1F882C2C6CB |
| SHA256: | 49DA6B95FD58CCDBC728E786E88C8530CE61E74B977ABE176858F4F555385575 |
| SSDEEP: | 98304:jVJtekPcvJVyN2lc09CTjYSpKeHDSNnPdn1umcyvsVvOrqWeoMQKN62Rqtbkqfv1:k7QDTgD3mpVVO |
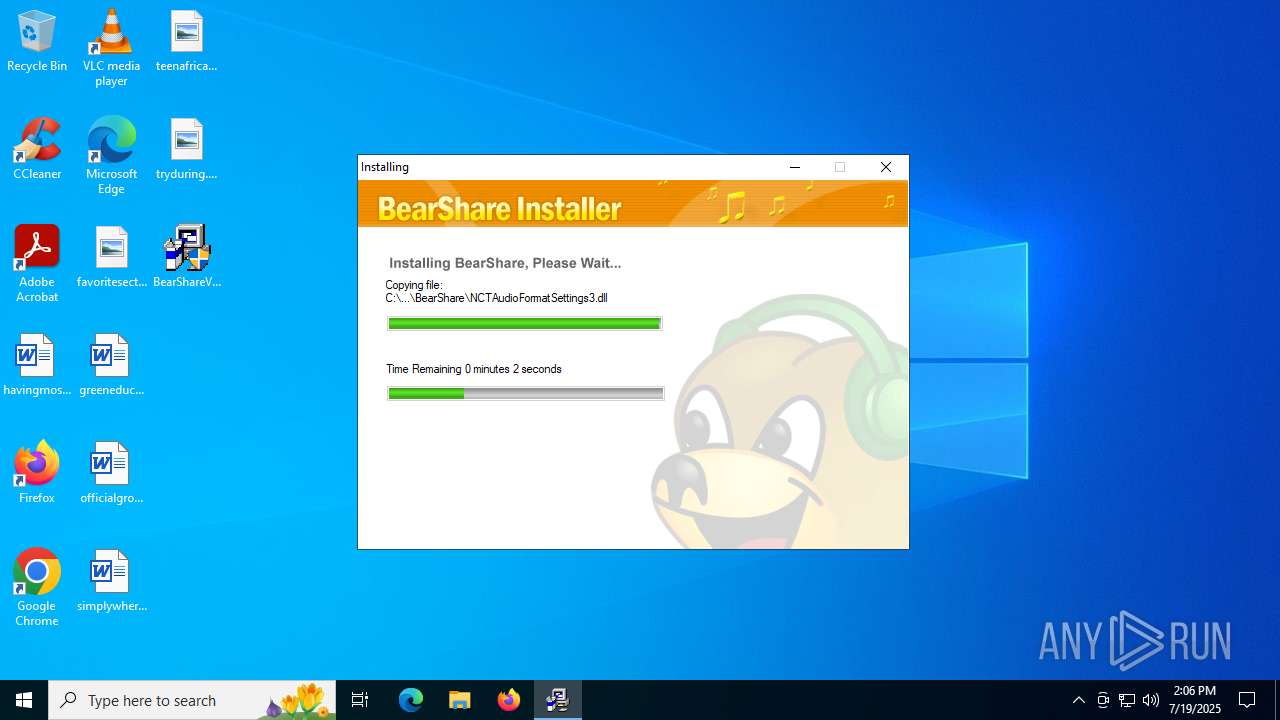
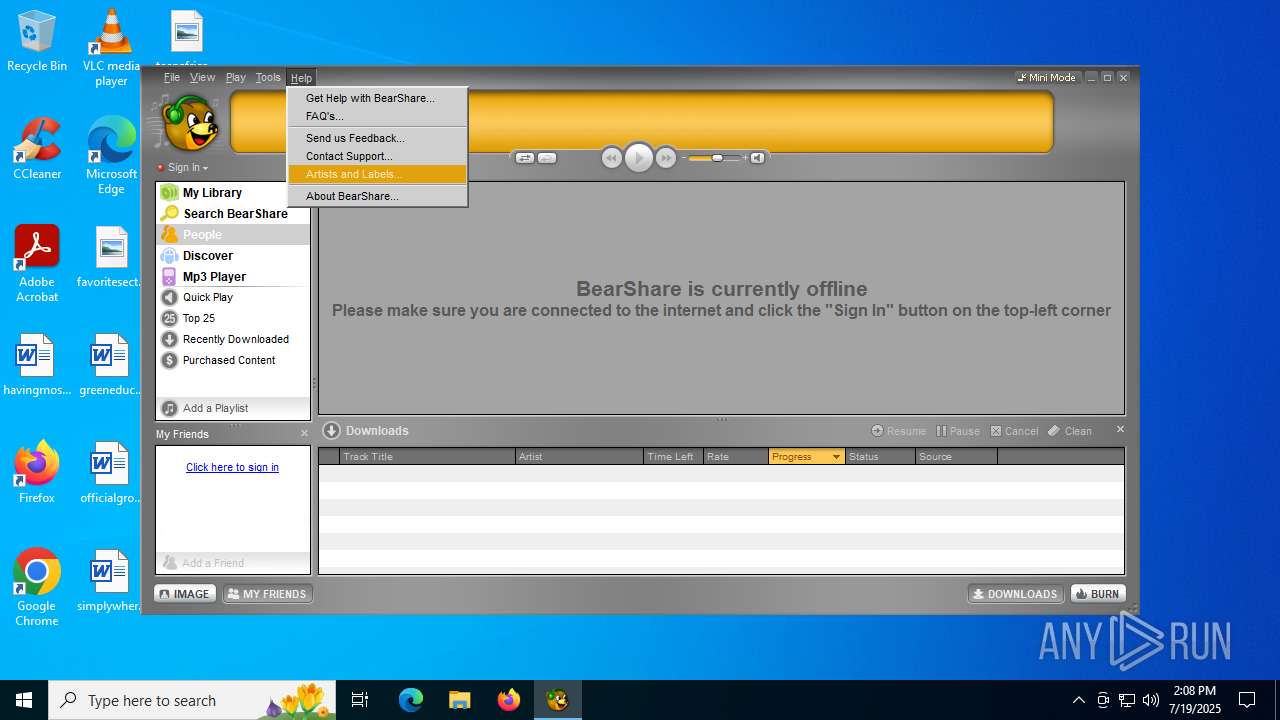
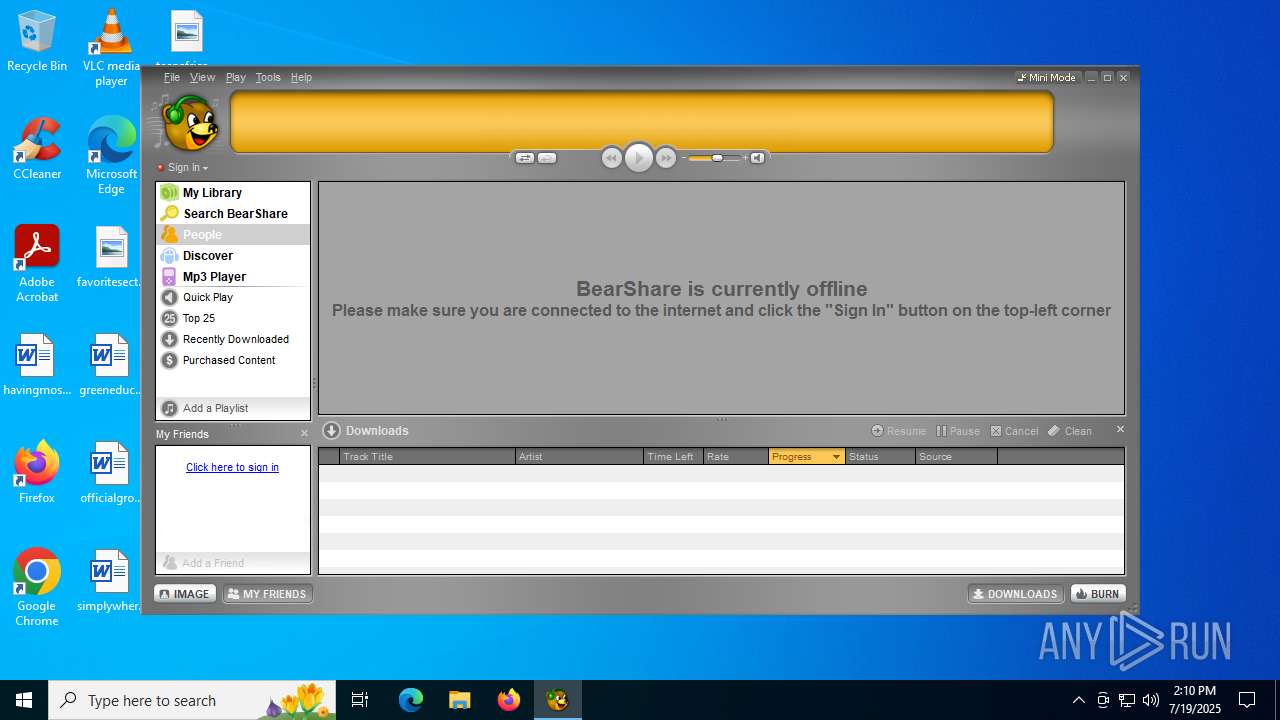
MALICIOUS
Executing a file with an untrusted certificate
- BearShareV6.exe (PID: 1668)
- BearShareV6.exe (PID: 6376)
- BearShare.exe (PID: 2144)
- MediaBar.exe (PID: 4224)
Registers / Runs the DLL via REGSVR32.EXE
- MediaBar.exe (PID: 4224)
SUSPICIOUS
Starts application with an unusual extension
- BearShareV6.exe (PID: 6376)
- GLBC7FE.tmp (PID: 6620)
Executable content was dropped or overwritten
- BearShareV6.exe (PID: 6376)
- GLBC7FE.tmp (PID: 6620)
- MediaBar.exe (PID: 4224)
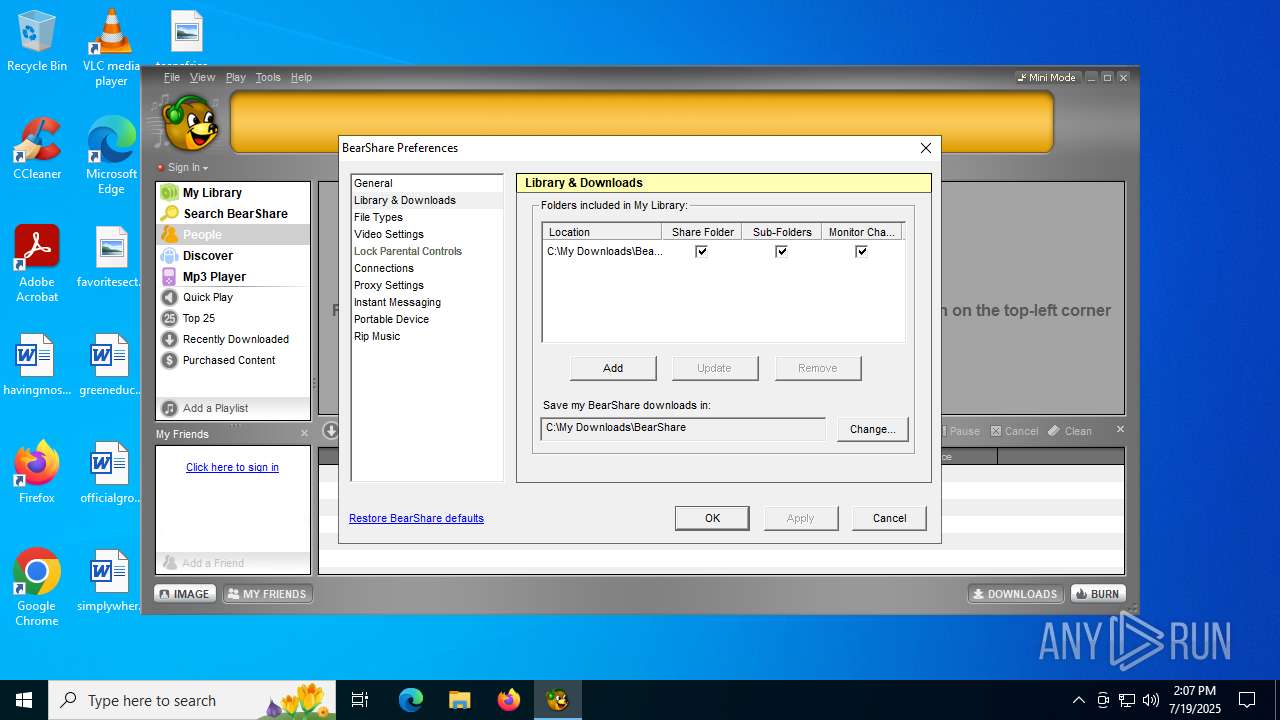
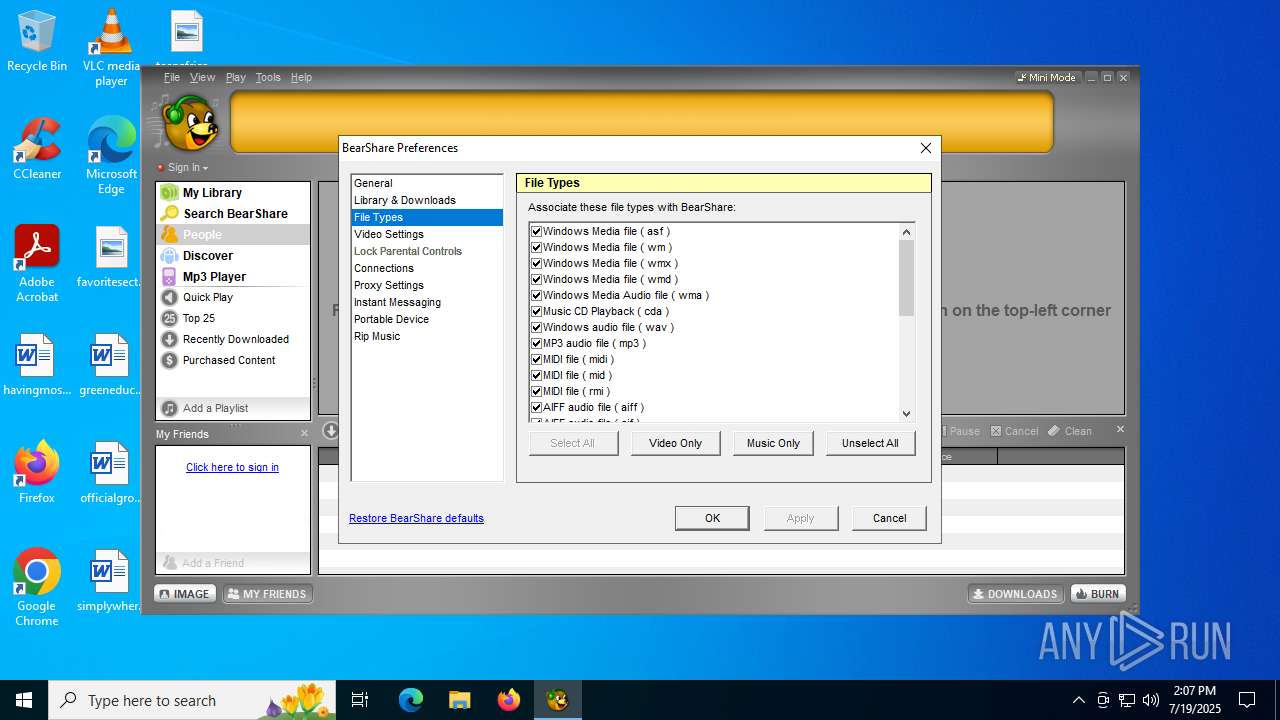
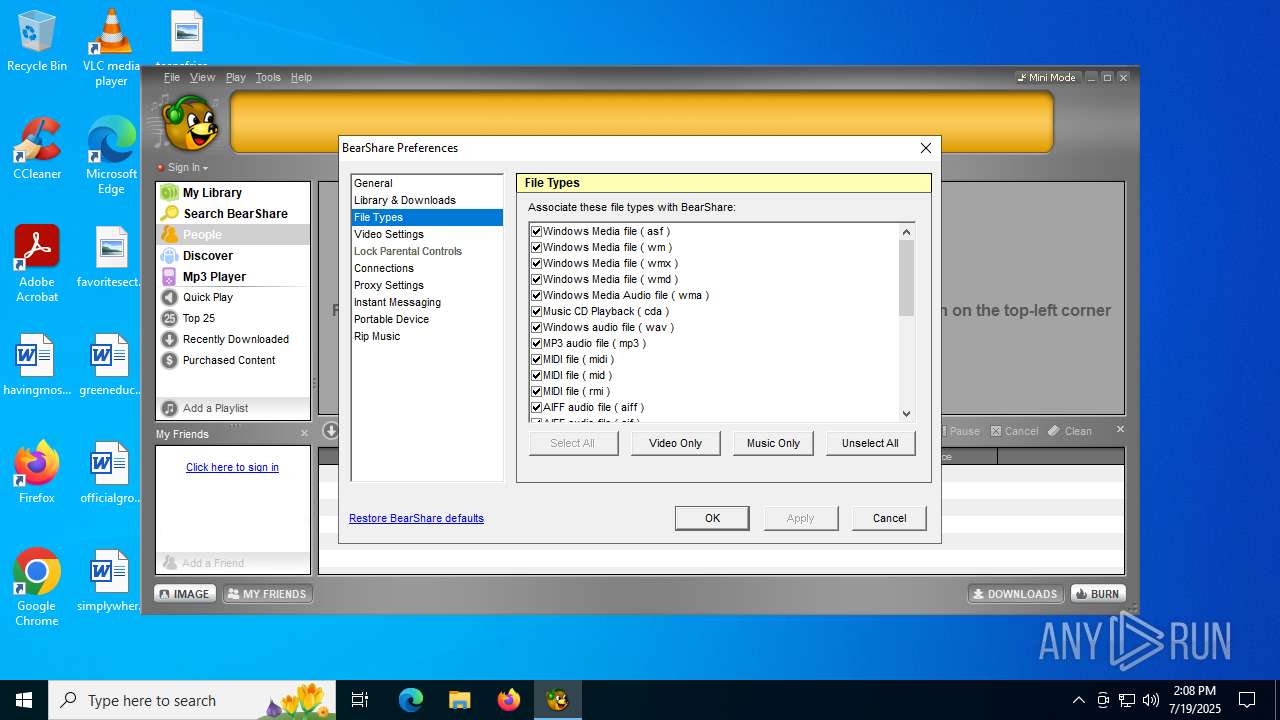
Changes default file association
- GLBC7FE.tmp (PID: 6620)
Creates/Modifies COM task schedule object
- GLJC87C.tmp (PID: 3656)
- GLJC87C.tmp (PID: 620)
- GLJC87C.tmp (PID: 3572)
- GLJC87C.tmp (PID: 6668)
- GLJC87C.tmp (PID: 2728)
- GLJC87C.tmp (PID: 1828)
- GLJC87C.tmp (PID: 1352)
- GLJC87C.tmp (PID: 4264)
- GLJC87C.tmp (PID: 2628)
- GLJC87C.tmp (PID: 1180)
- GLJC87C.tmp (PID: 6344)
- GLJC87C.tmp (PID: 4412)
- regsvr32.exe (PID: 320)
There is functionality for taking screenshot (YARA)
- BearShareV6.exe (PID: 6376)
- GLBC7FE.tmp (PID: 6620)
- BearShare.exe (PID: 2144)
Searches for installed software
- GLBC7FE.tmp (PID: 6620)
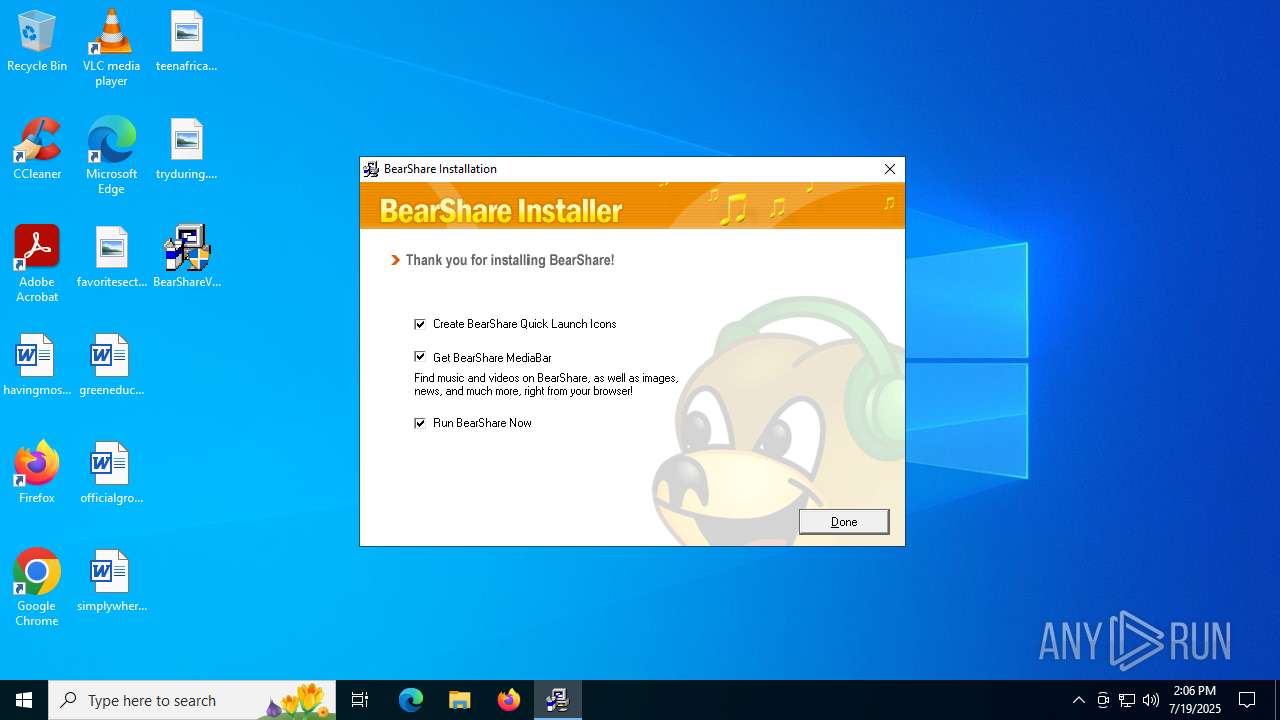
Creates a software uninstall entry
- GLBC7FE.tmp (PID: 6620)
- MediaBar.exe (PID: 4224)
- regsvr32.exe (PID: 320)
Process drops legitimate windows executable
- GLBC7FE.tmp (PID: 6620)
The process drops C-runtime libraries
- GLBC7FE.tmp (PID: 6620)
Reads security settings of Internet Explorer
- GLBC7FE.tmp (PID: 6620)
- BearShare.exe (PID: 2144)
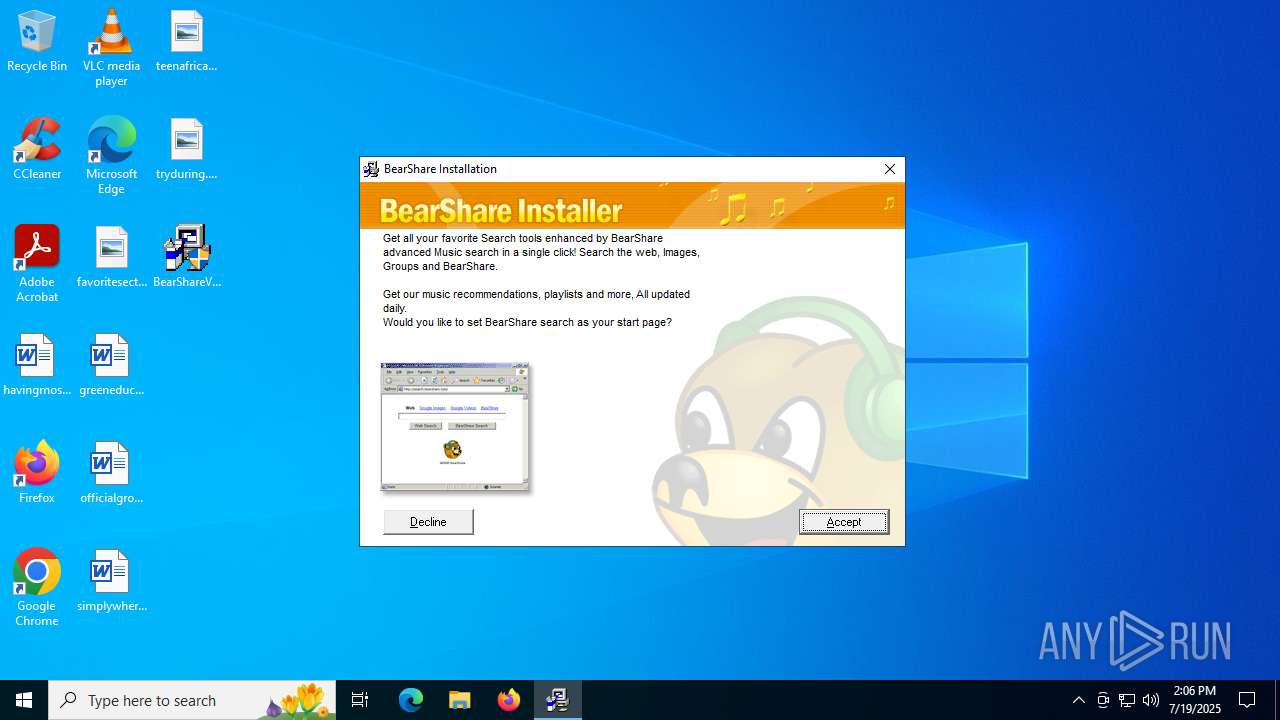
Changes the Home page of Internet Explorer
- GLBC7FE.tmp (PID: 6620)
Changes the title of the Internet Explorer window
- GLBC7FE.tmp (PID: 6620)
Reads Microsoft Outlook installation path
- BearShare.exe (PID: 2144)
Reads Internet Explorer settings
- BearShare.exe (PID: 2144)
INFO
The sample compiled with english language support
- BearShareV6.exe (PID: 6376)
- GLBC7FE.tmp (PID: 6620)
- MediaBar.exe (PID: 4224)
Create files in a temporary directory
- BearShareV6.exe (PID: 6376)
- GLBC7FE.tmp (PID: 6620)
- MediaBar.exe (PID: 4224)
Checks supported languages
- GLBC7FE.tmp (PID: 6620)
- BearShareV6.exe (PID: 6376)
- GLJC87C.tmp (PID: 620)
- GLJC87C.tmp (PID: 3572)
- GLJC87C.tmp (PID: 1352)
- GLJC87C.tmp (PID: 2728)
- GLJC87C.tmp (PID: 4412)
- GLJC87C.tmp (PID: 6668)
- GLJC87C.tmp (PID: 1828)
- GLJC87C.tmp (PID: 3656)
- GLJC87C.tmp (PID: 4264)
- GLJC87C.tmp (PID: 1180)
- GLJC87C.tmp (PID: 6344)
- GLJC87C.tmp (PID: 1132)
- GLJC87C.tmp (PID: 2628)
- MediaBar.exe (PID: 4224)
- Launcher.exe (PID: 3932)
- BearShare.exe (PID: 2144)
- identity_helper.exe (PID: 4788)
- identity_helper.exe (PID: 4892)
Reads the computer name
- GLBC7FE.tmp (PID: 6620)
- GLJC87C.tmp (PID: 620)
- GLJC87C.tmp (PID: 1352)
- GLJC87C.tmp (PID: 3572)
- GLJC87C.tmp (PID: 2728)
- GLJC87C.tmp (PID: 6668)
- GLJC87C.tmp (PID: 1828)
- GLJC87C.tmp (PID: 3656)
- GLJC87C.tmp (PID: 4264)
- GLJC87C.tmp (PID: 2628)
- GLJC87C.tmp (PID: 1180)
- GLJC87C.tmp (PID: 6344)
- GLJC87C.tmp (PID: 4412)
- BearShare.exe (PID: 2144)
- Launcher.exe (PID: 3932)
- identity_helper.exe (PID: 4788)
- identity_helper.exe (PID: 4892)
Creates files in the program directory
- GLBC7FE.tmp (PID: 6620)
- GLJC87C.tmp (PID: 1180)
- MediaBar.exe (PID: 4224)
- regsvr32.exe (PID: 320)
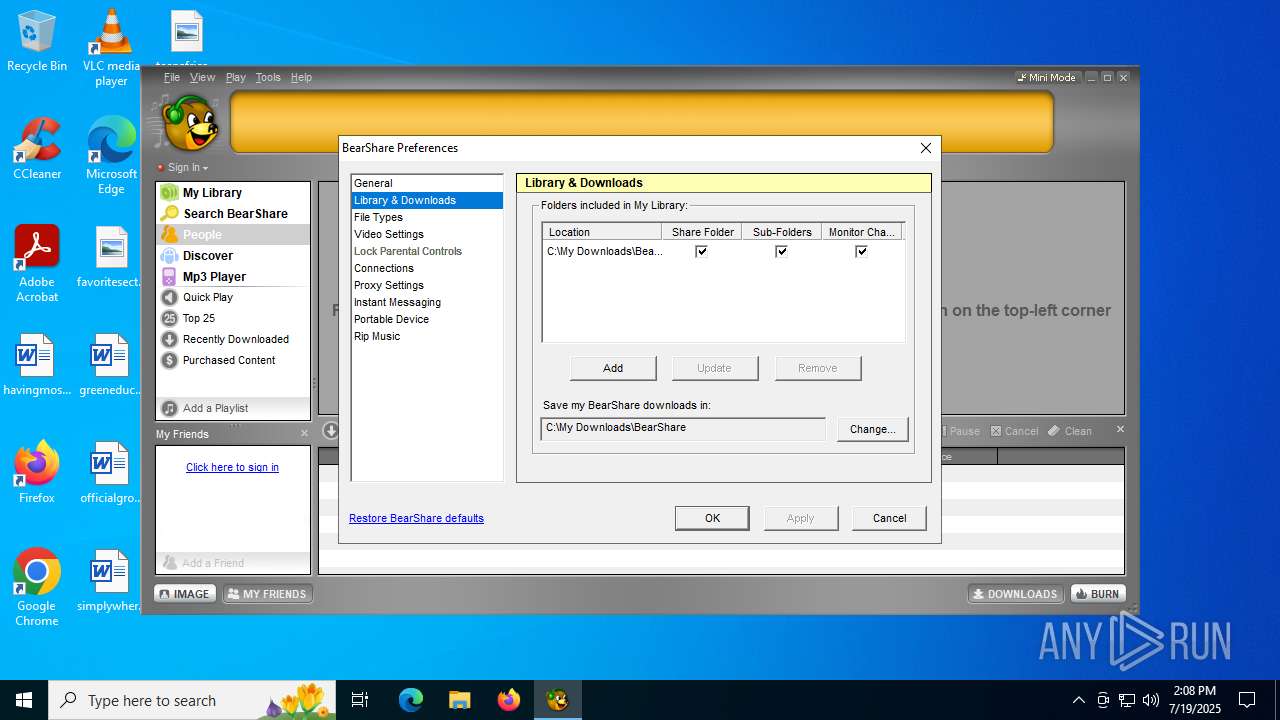
Creates files or folders in the user directory
- GLBC7FE.tmp (PID: 6620)
- BearShare.exe (PID: 2144)
Process checks computer location settings
- GLBC7FE.tmp (PID: 6620)
- BearShare.exe (PID: 2144)
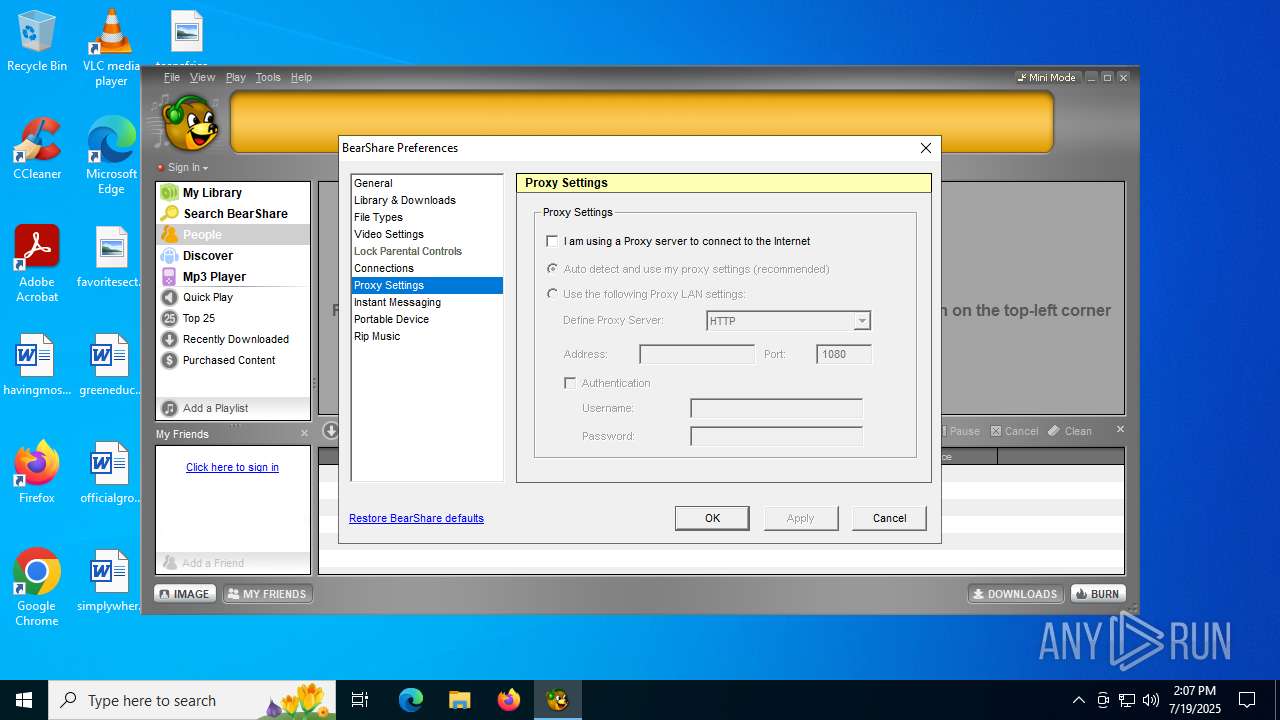
Checks proxy server information
- GLBC7FE.tmp (PID: 6620)
- BearShare.exe (PID: 2144)
- slui.exe (PID: 3688)
Reads the machine GUID from the registry
- BearShare.exe (PID: 2144)
Reads the software policy settings
- slui.exe (PID: 3688)
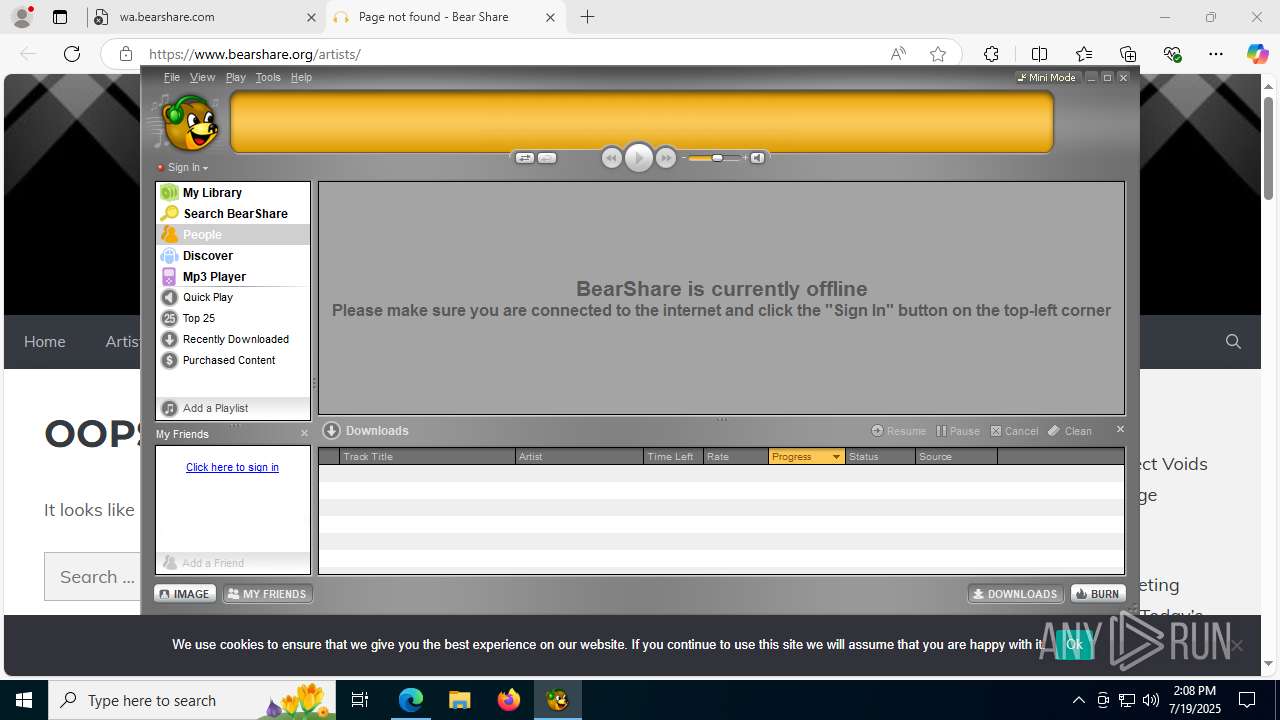
Manual execution by a user
- msedge.exe (PID: 1380)
Application launched itself
- msedge.exe (PID: 6524)
- msedge.exe (PID: 4476)
- msedge.exe (PID: 1380)
- msedge.exe (PID: 1864)
- msedge.exe (PID: 5080)
Reads Environment values
- identity_helper.exe (PID: 4788)
- identity_helper.exe (PID: 4892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Wise Installer executable (91.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (5.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.2) |
| .exe | | | Win32 Executable (generic) (0.8) |
| .exe | | | Generic Win/DOS Executable (0.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:04:08 20:24:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 512 |
| InitializedDataSize: | 8882688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.0.0 |
| ProductVersionNumber: | 7.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows 16-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
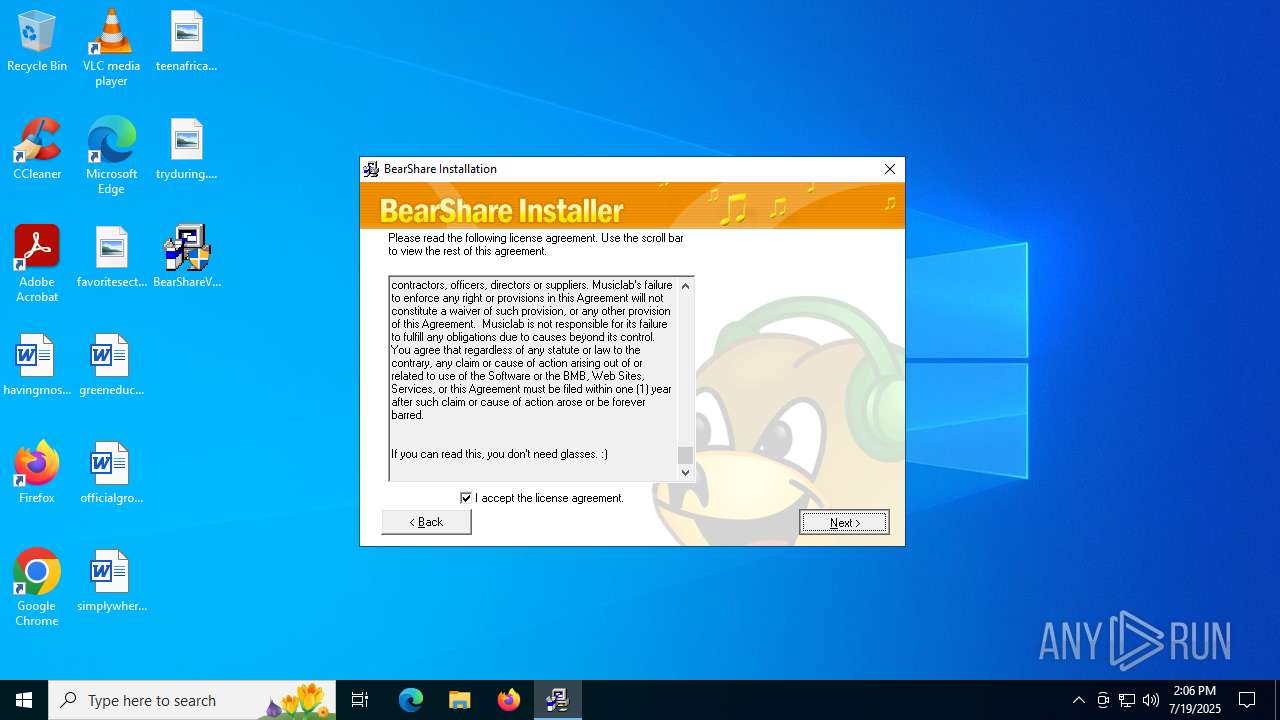
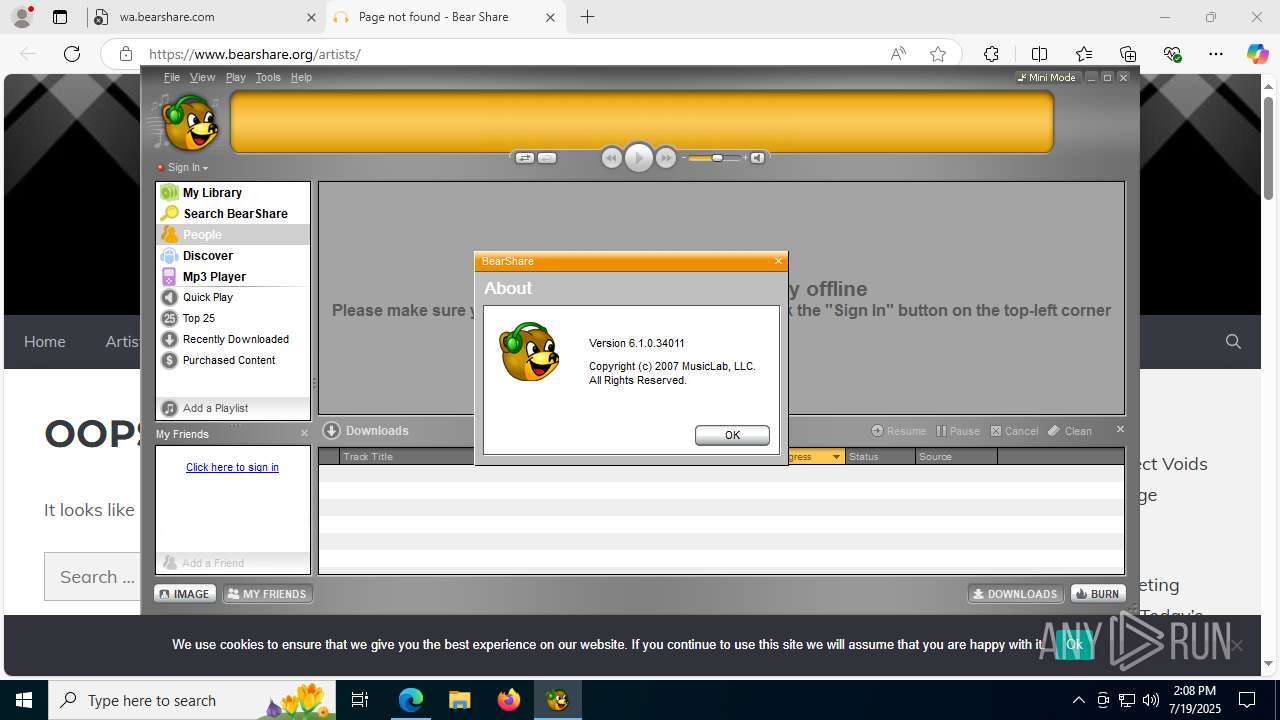
| CompanyName: | MusicLab, LLC |
| FileDescription: | BearShare |
| FileVersion: | 7 |
| LegalCopyright: | MusicLab, LLC |
Total processes
224
Monitored processes
72
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | C:\WINDOWS\system32\regsvr32 /s "C:\Program Files (x86)\BearShare applications\BearShare MediaBar\MediaBar.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | MediaBar.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --from-ie-to-edge=8 --edge-skip-compat-layer-relaunch -- http://www.bearshare.com/artists/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --always-read-main-dll --field-trial-handle=5656,i,9357581473848226466,5872778426202686129,262144 --variations-seed-version --mojo-platform-channel-handle=4004 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 620 | "C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp" C:\Program Files (x86)\BearShare Applications\BearShare\IMWebControl.dll | C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp | — | GLBC7FE.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6376,i,9357581473848226466,5872778426202686129,262144 --variations-seed-version --mojo-platform-channel-handle=6412 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=25 --always-read-main-dll --field-trial-handle=6908,i,9357581473848226466,5872778426202686129,262144 --variations-seed-version --mojo-platform-channel-handle=6896 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4820,i,5294932035583917393,11177601771898966213,262144 --variations-seed-version --mojo-platform-channel-handle=4652 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp" C:\Program Files (x86)\BearShare Applications\BearShare\Shw32.dll | C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp | — | GLBC7FE.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp" C:\Program Files (x86)\BearShare Applications\BearShare\WMHelper.dll | C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp | GLBC7FE.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffc4556f208,0x7ffc4556f214,0x7ffc4556f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
15 853
Read events
15 013
Write events
834
Delete events
6
Modification events
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\BearShare |
| Operation: | write | Name: | DisplayName |
Value: BearShare | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\BearShare |
| Operation: | write | Name: | UninstallString |
Value: C:\PROGRA~2\BEARSH~1\BEARSH~1\UNWISE.EXE C:\PROGRA~2\BEARSH~1\BEARSH~1\INSTALL.LOG | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .mid |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .rmi |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .aiff |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .aif |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .aifc |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .au |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .mp2 |
Value: BearShare.file | |||
| (PID) Process: | (6620) GLBC7FE.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\BearShare\Capabilities\FileAssociations |
| Operation: | write | Name: | .mpv2 |
Value: BearShare.file | |||
Executable files
77
Suspicious files
381
Text files
252
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\~GLH0003.TMP | text | |
MD5:C1C94DC0D007D2088C4D2947F1246267 | SHA256:27547DCC5A7408E546E62EA033473EE83641C841F4CFCC8FB028FDA43FFF3AAD | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLJC87C.tmp | executable | |
MD5:6F608D264503796BEBD7CD66B687BE92 | SHA256:49833D2820AFB1D7409DFBD916480F2CDF5787D2E2D94166725BEB9064922D5D | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\~GLH0001.TMP | text | |
MD5:C1C94DC0D007D2088C4D2947F1246267 | SHA256:27547DCC5A7408E546E62EA033473EE83641C841F4CFCC8FB028FDA43FFF3AAD | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLMCC95.tmp | executable | |
MD5:484CB68472473A1A84FF07996BB8C1F6 | SHA256:15BB390AF019D92E1D02771B02335FA360DB1BB34BCF4F0C72705027428F4FF1 | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLKCA81.tmp | executable | |
MD5:CDF4448B491701C3CE033FCC75542F4A | SHA256:4389853F4898DA22D28FDF47B5EE9046C1A4242497C61C4FF91A6DEE0FB66261 | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLFE9D5.tmp | text | |
MD5:C1C94DC0D007D2088C4D2947F1246267 | SHA256:27547DCC5A7408E546E62EA033473EE83641C841F4CFCC8FB028FDA43FFF3AAD | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\~GLH0000.TMP | executable | |
MD5:3B2E23D259394C701050486E642D14FA | SHA256:166D7156142F3EE09FA69EB617DD22E4FD248AA80A1AC08767DB6AD99A2705C1 | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLFD449.tmp | executable | |
MD5:3B2E23D259394C701050486E642D14FA | SHA256:166D7156142F3EE09FA69EB617DD22E4FD248AA80A1AC08767DB6AD99A2705C1 | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLFE9F6.tmp | text | |
MD5:AEA4EB92B33D97EC6BDF4D13D98074EC | SHA256:600EF90949D7149D04E21FF4A2BD7238B41D06E1243F67F285C80CEBAEBDA3DD | |||
| 6620 | GLBC7FE.tmp | C:\Users\admin\AppData\Local\Temp\GLFEA06.tmp | text | |
MD5:C1C94DC0D007D2088C4D2947F1246267 | SHA256:27547DCC5A7408E546E62EA033473EE83641C841F4CFCC8FB028FDA43FFF3AAD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
89
DNS requests
121
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3948 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4724 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1936 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:6LdyYBFV26RsjeRSBKPbE5WWbFIpJv1Luo1frLTJa7E&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1236 | svchost.exe | HEAD | 200 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753146081&P2=404&P3=2&P4=HtlOES6zqd5UHWVs38e8ilJDFGp7yHij3gD3u0yhrrUR4h1i0q%2b%2fEQNxQh3cTOp8cOBQAIYOrxsFX%2bU1D148JQ%3d%3d | unknown | — | — | whitelisted |
6352 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 104.76.201.34:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1236 | svchost.exe | GET | 206 | 23.48.23.43:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1753146081&P2=404&P3=2&P4=HtlOES6zqd5UHWVs38e8ilJDFGp7yHij3gD3u0yhrrUR4h1i0q%2b%2fEQNxQh3cTOp8cOBQAIYOrxsFX%2bU1D148JQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4944 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3948 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3948 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
wa.bearshare.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1936 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1936 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
Process | Message |
|---|---|
GLJC87C.tmp | HKCR
{
NoRemove AppID
{
'{AD71F65D-CD13-4837-A2DC-E4D90020E7D4}' = s 'NCTAudioCDGrabber2'
'NCTAudioCDGrabber2.DLL'
{
val AppID = s '{AD71F65D-CD13-4837-A2DC-E4D90020E7D4}'
}
}
}
|
GLJC87C.tmp | |
GLJC87C.tmp | HKCR
{
NCTAudioCDGrabber2.AudioCDGrabber2.1 = s 'AudioCDGrabber2 Class'
{
CLSID = s '{5EB0259D-AB79-4ae6-A6E6-24FFE21C3DA4}'
}
NCTAudioCDGrabber2.AudioCDGrabber2 = s 'AudioCDGrabber2 Class'
{
CLSID = s '{5EB0259D-AB79-4ae6-A6E6-24FFE21C3DA4}'
CurVer = s 'NCTAudioCDGrabber2.AudioCDGrabber2.1'
}
NoRemove CLSID
{
ForceRemove {5EB0259D-AB79-4ae6-A6E6-24FFE21C3DA4} = s 'AudioCDGrabber2 Class'
{
ProgID = s 'NCTAudioCDGrabber2.AudioCDGrabber2.1'
VersionIndependentProgID = s 'NCTAudioCDGrabber2.AudioCDGrabber2'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files (x86)\BearShare Applications\BearShare\NCTAudioCDGrabber2.dll'
{
val ThreadingModel = s 'Apartment'
}
val AppID = s '{AD71F65D-CD13-4837-A2DC-E4D90020E7D4}'
'TypeLib' = s '{81CA8FCD-1420-4A07-B47D-B30F3DDA79E1}'
}
}
}
|
GLJC87C.tmp | |
GLJC87C.tmp | HKCR
{
NCTAudioCDGrabber2.FreeDBInformation2.1 = s 'FreeDBInformation2 Class'
{
CLSID = s '{CADAF6BE-BF50-4669-8BFD-C27BD4E6181B}'
}
NCTAudioCDGrabber2.FreeDBInformation2 = s 'FreeDBInformation2 Class'
{
CLSID = s '{CADAF6BE-BF50-4669-8BFD-C27BD4E6181B}'
CurVer = s 'NCTAudioCDGrabber2.FreeDBInformation2.1'
}
NoRemove CLSID
{
ForceRemove {CADAF6BE-BF50-4669-8BFD-C27BD4E6181B} = s 'FreeDBInformation2 Class'
{
ProgID = s 'NCTAudioCDGrabber2.FreeDBInformation2.1'
VersionIndependentProgID = s 'NCTAudioCDGrabber2.FreeDBInformation2'
ForceRemove 'Programmable'
InprocServer32 = s 'C:\Program Files (x86)\BearShare Applications\BearShare\NCTAudioCDGrabber2.dll'
{
val ThreadingModel = s 'Apartment'
}
val AppID = s '{AD71F65D-CD13-4837-A2DC-E4D90020E7D4}'
'TypeLib' = s '{81CA8FCD-1420-4A07-B47D-B30F3DDA79E1}'
}
}
}
|
GLJC87C.tmp | |
GLJC87C.tmp | WMHelper, Sat Jul 19 14:06:05 2025, *** Log opened for build 4.0.0.160 of MusicNet Client SDK (iMesh release build) ***
|
GLJC87C.tmp | WMHelper, Sat Jul 19 14:06:05 2025, Log Level: 1, Max Size: 268435456 bytes
|