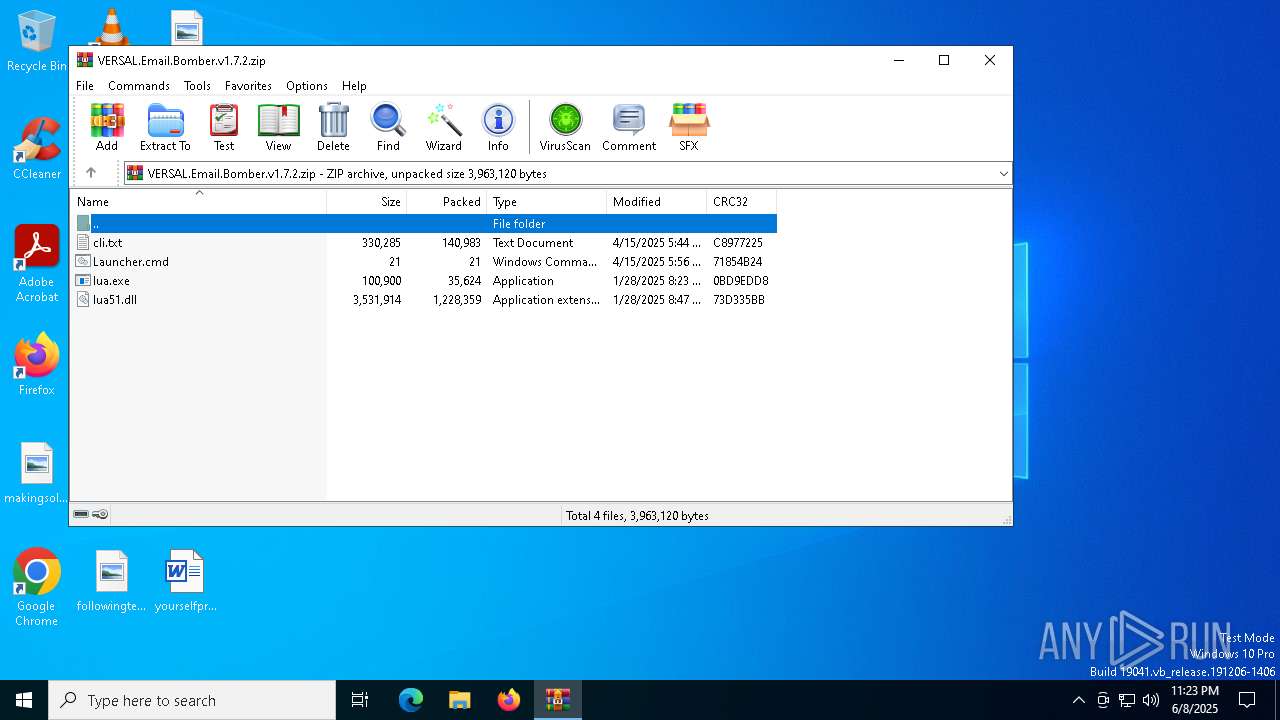
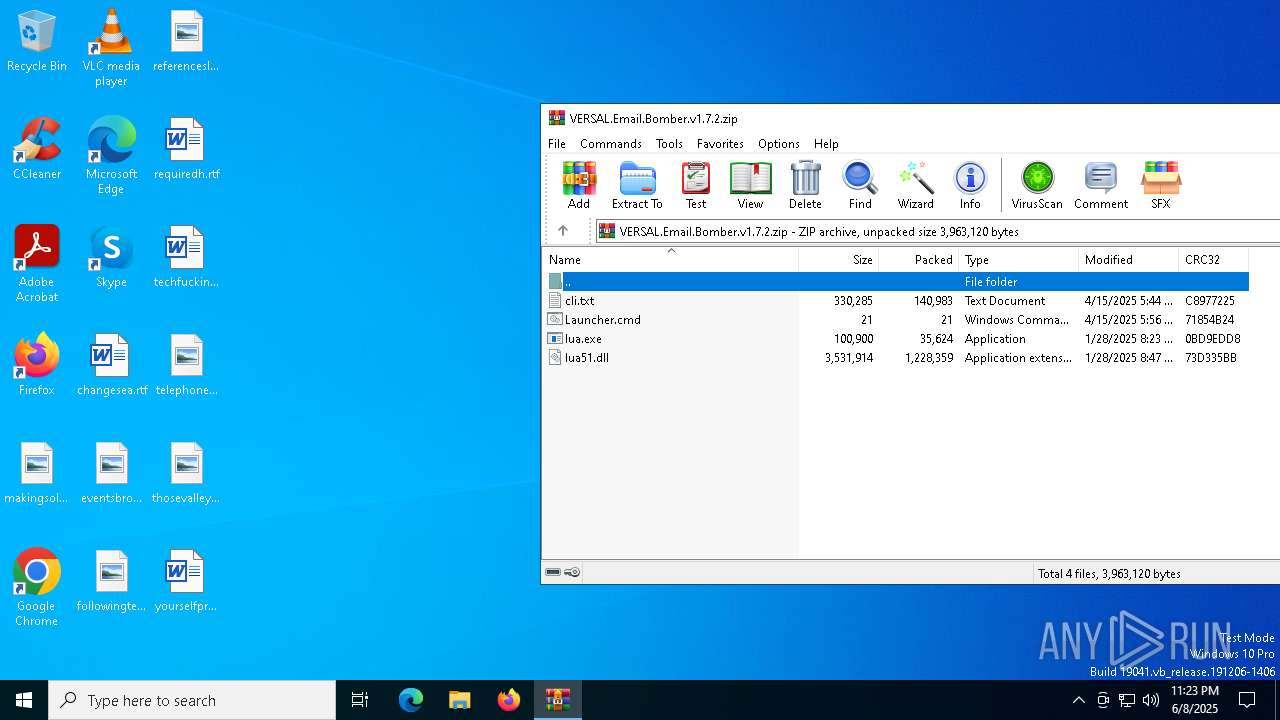
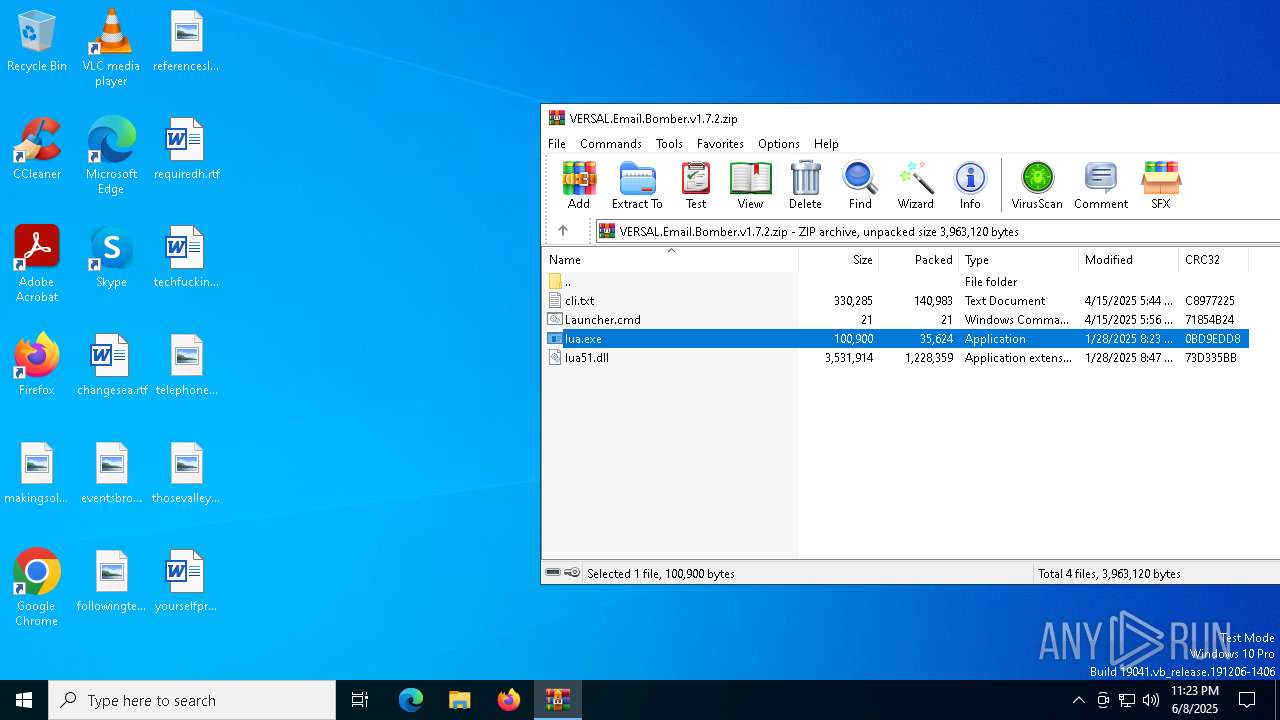
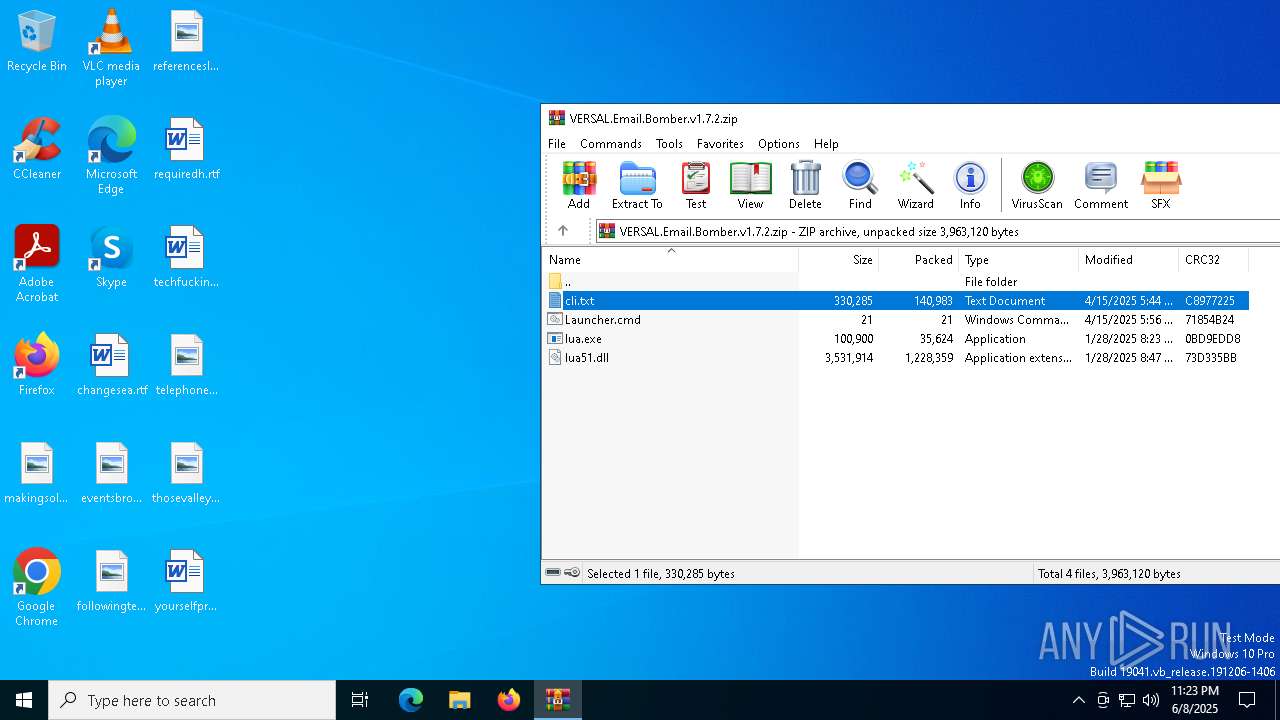
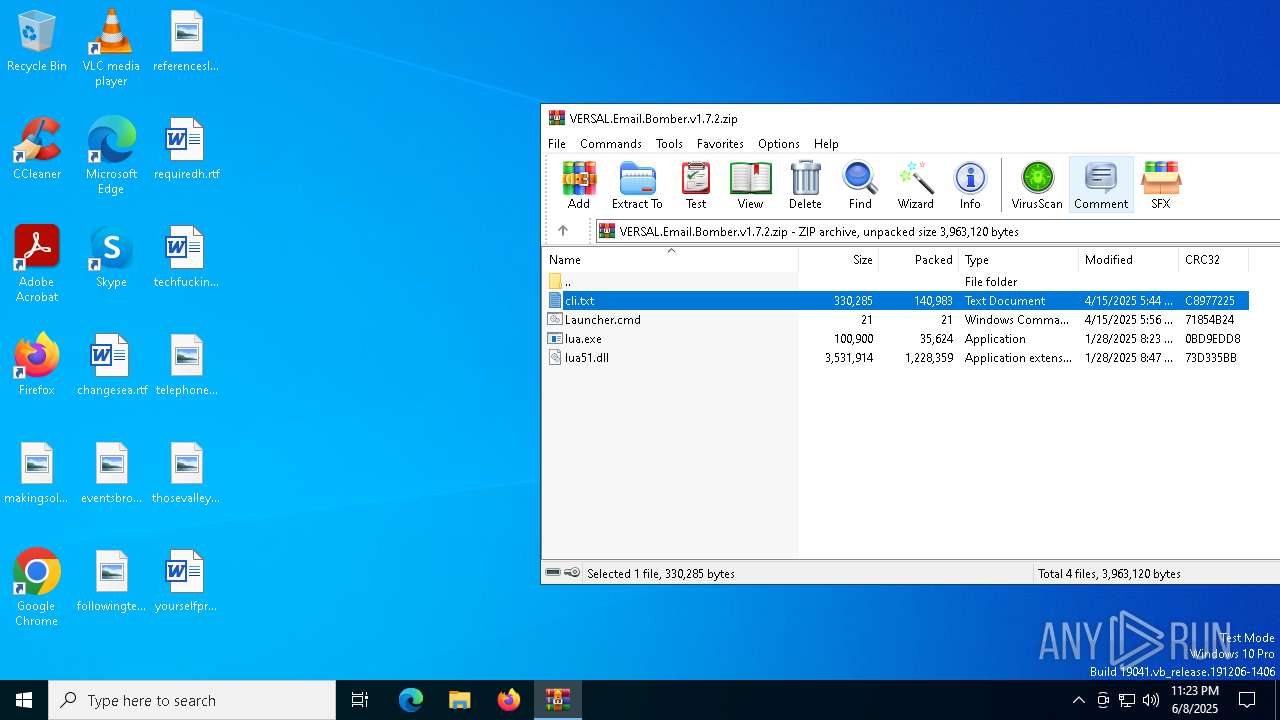
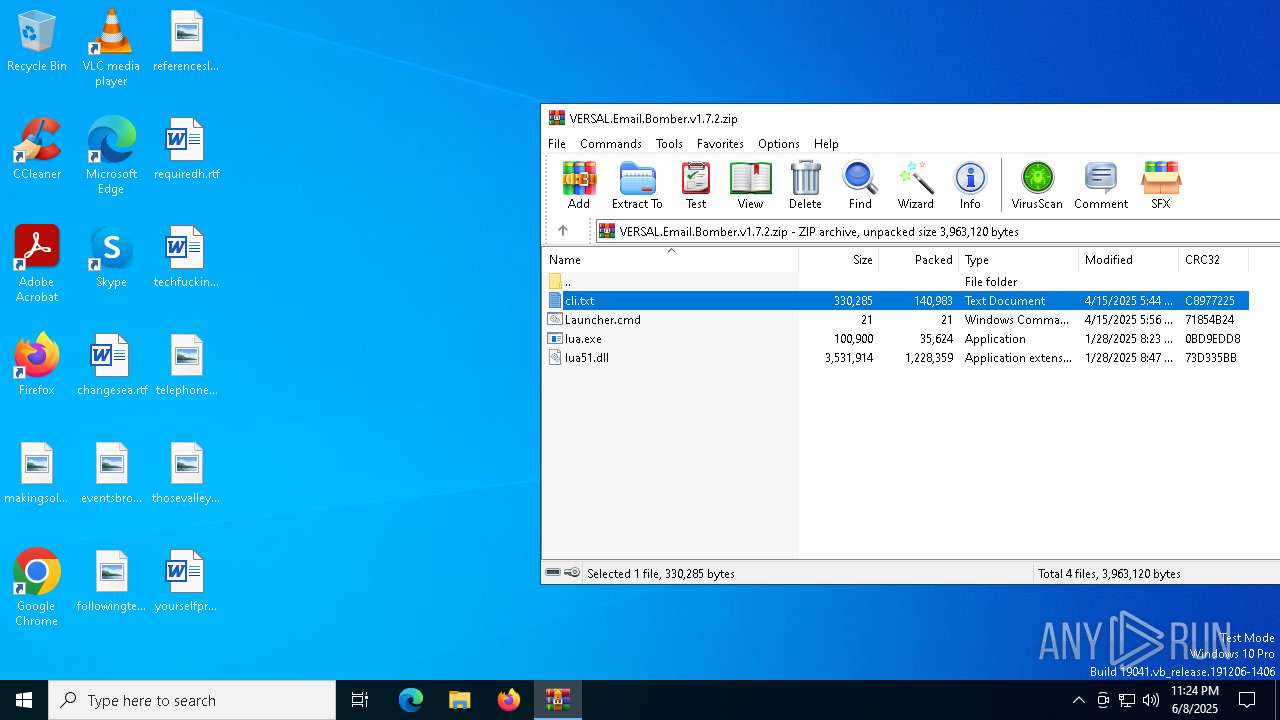
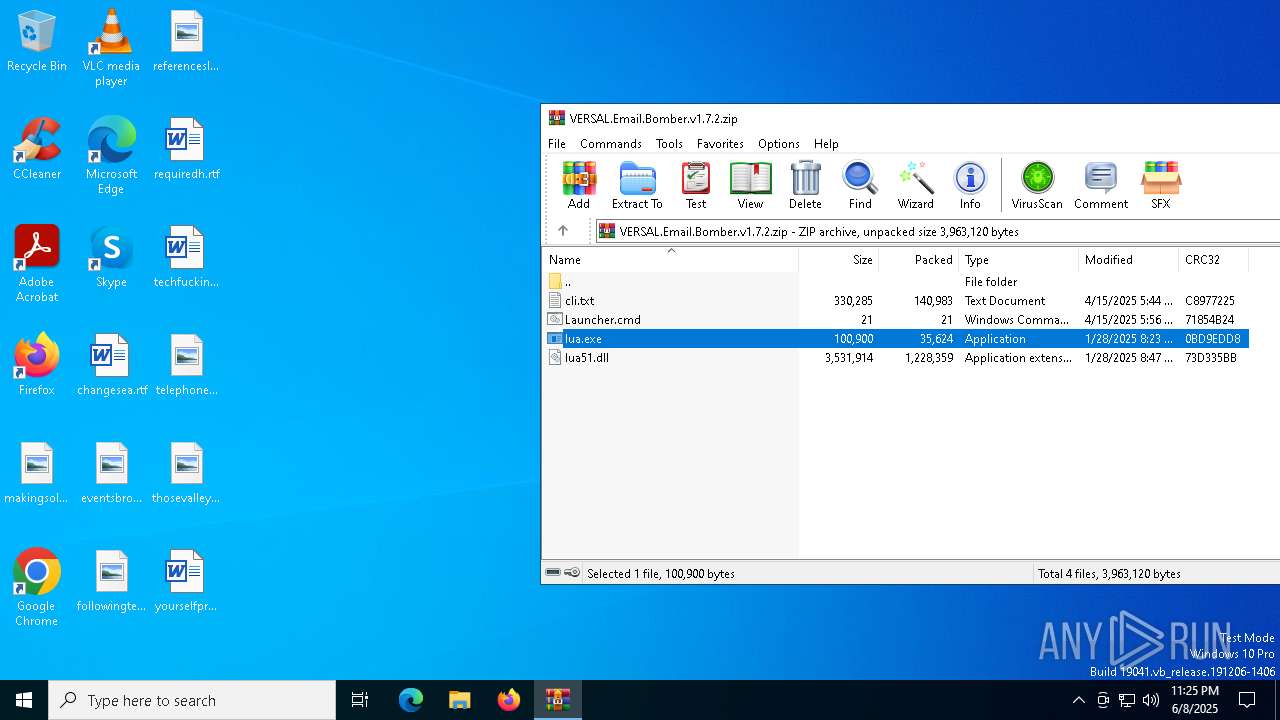
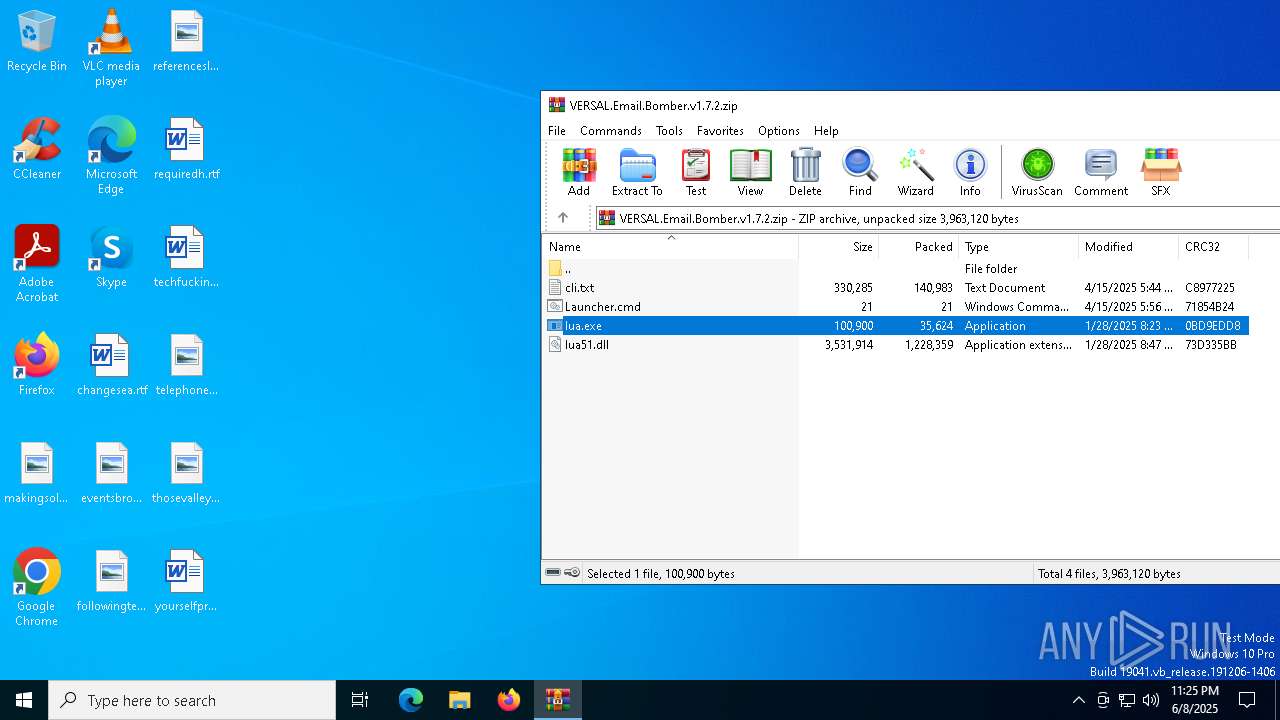
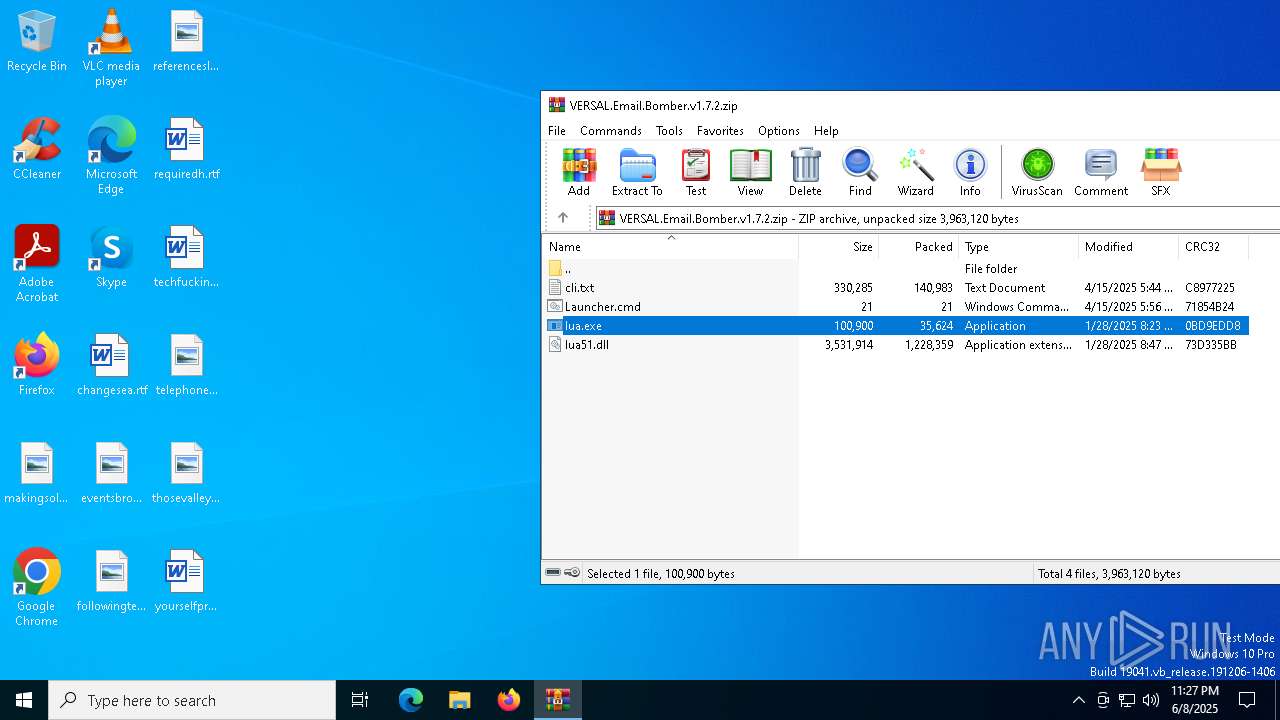
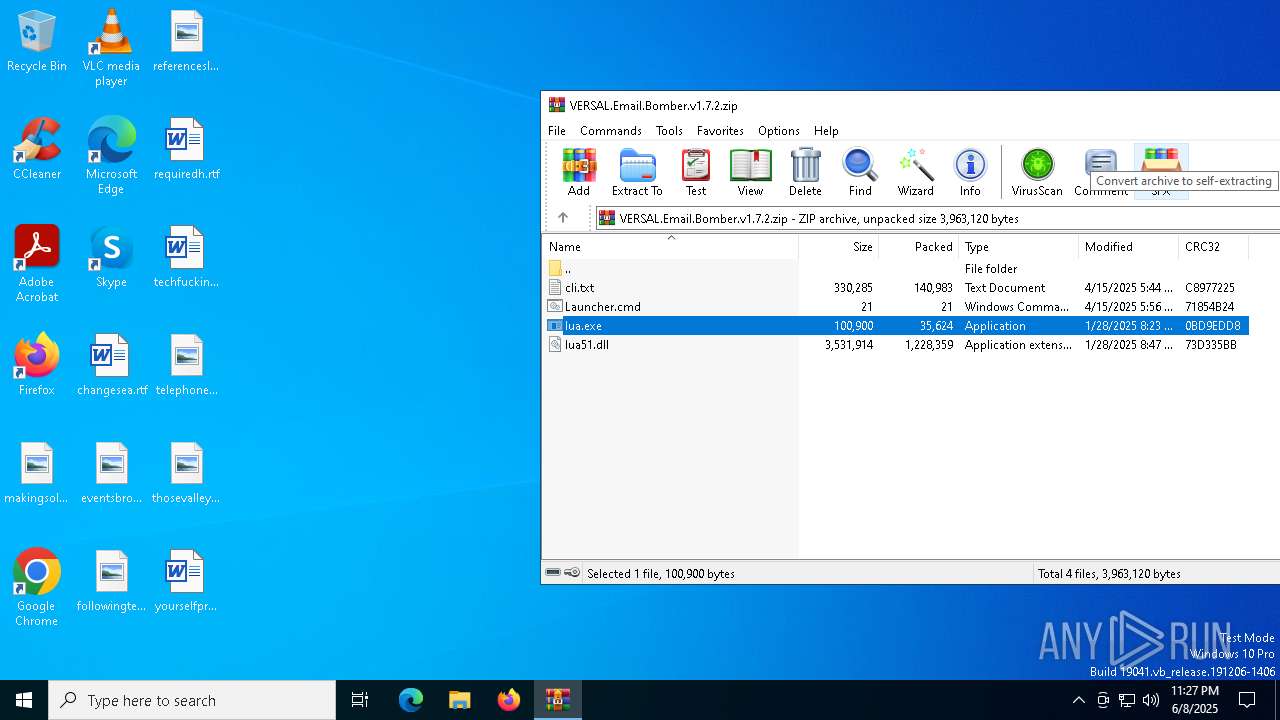
| File name: | VERSAL.Email.Bomber.v1.7.2.zip |
| Full analysis: | https://app.any.run/tasks/67dee1d0-6d73-4446-98f0-a77c46fa4bf4 |
| Verdict: | Malicious activity |
| Analysis date: | June 08, 2025, 23:23:12 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 5E0D088E420FA20C70824A56CFAD505B |
| SHA1: | C8AF6ED1CC82636B6DC68A7907A401367F168FFA |
| SHA256: | 49DA59C2CDC31E3D4BB5C4E09149842B417402CF542515E89AA7F24D0C4BFBFF |
| SSDEEP: | 49152:vDPQb9yGZrne9qKA8hYOjGSOFWaHhmKjrZOFwkHfIfPEwPea2MDyCyzGhJGYl6F0:vDPQb9yGp23YmGSOFWagUrZK5gfciOGx |
MALICIOUS
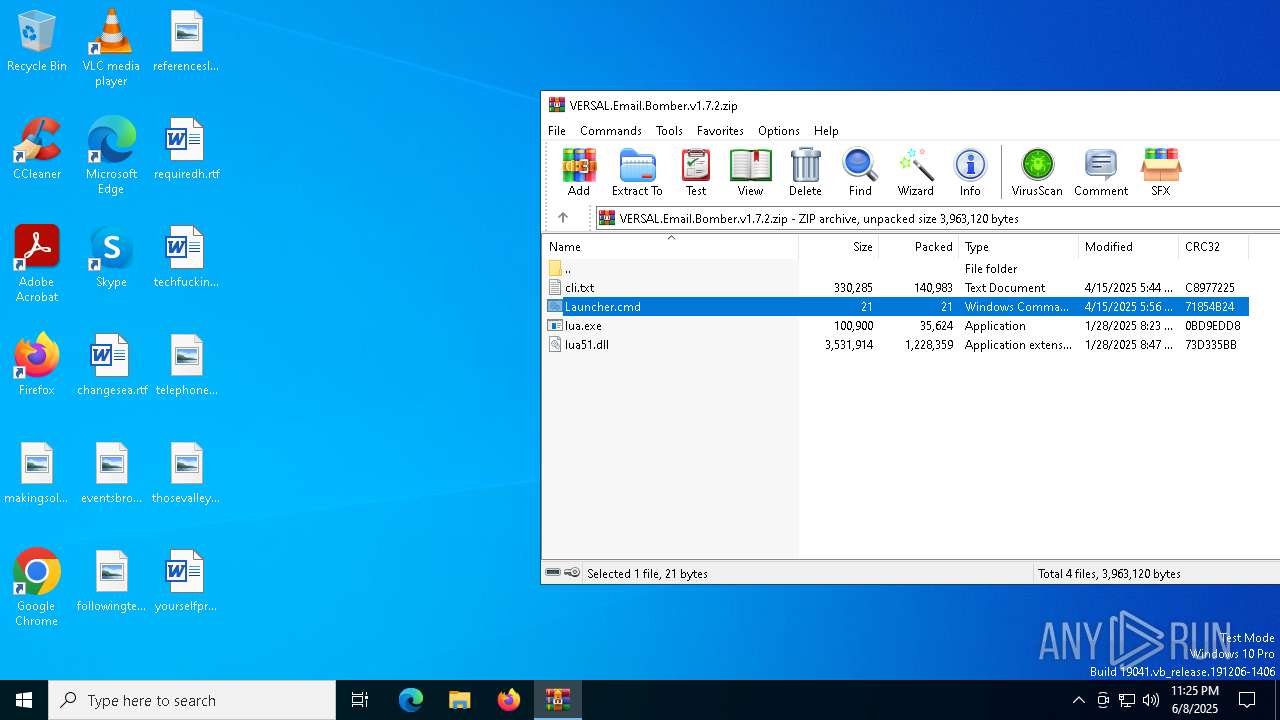
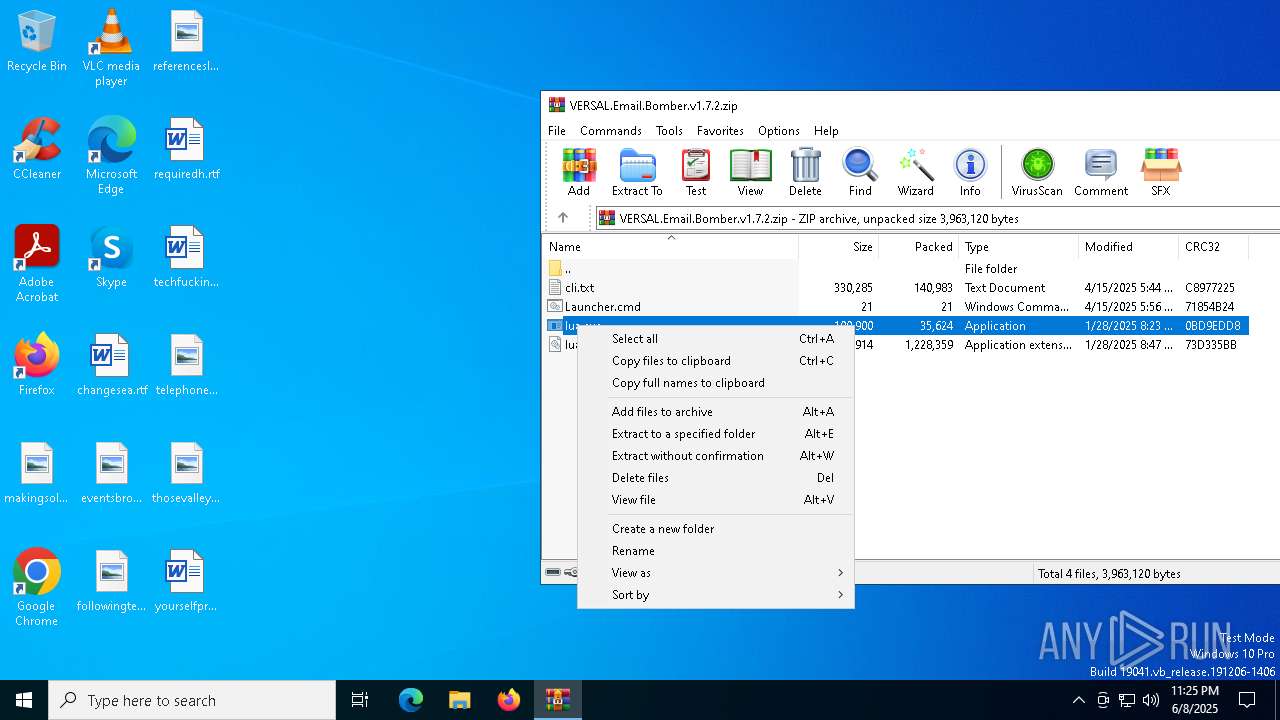
Generic archive extractor
- WinRAR.exe (PID: 4400)
GENERIC has been found (auto)
- WinRAR.exe (PID: 4400)
SUSPICIOUS
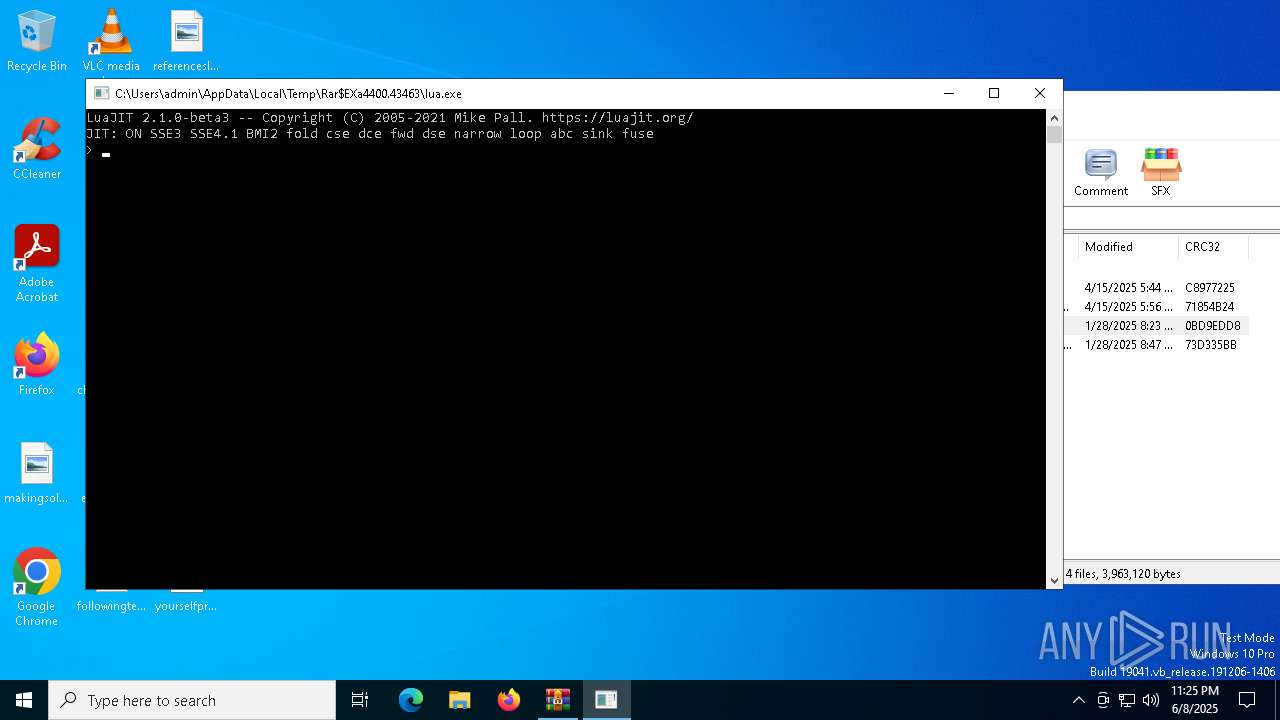
Executing commands from ".cmd" file
- WinRAR.exe (PID: 4400)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4400)
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 4400)
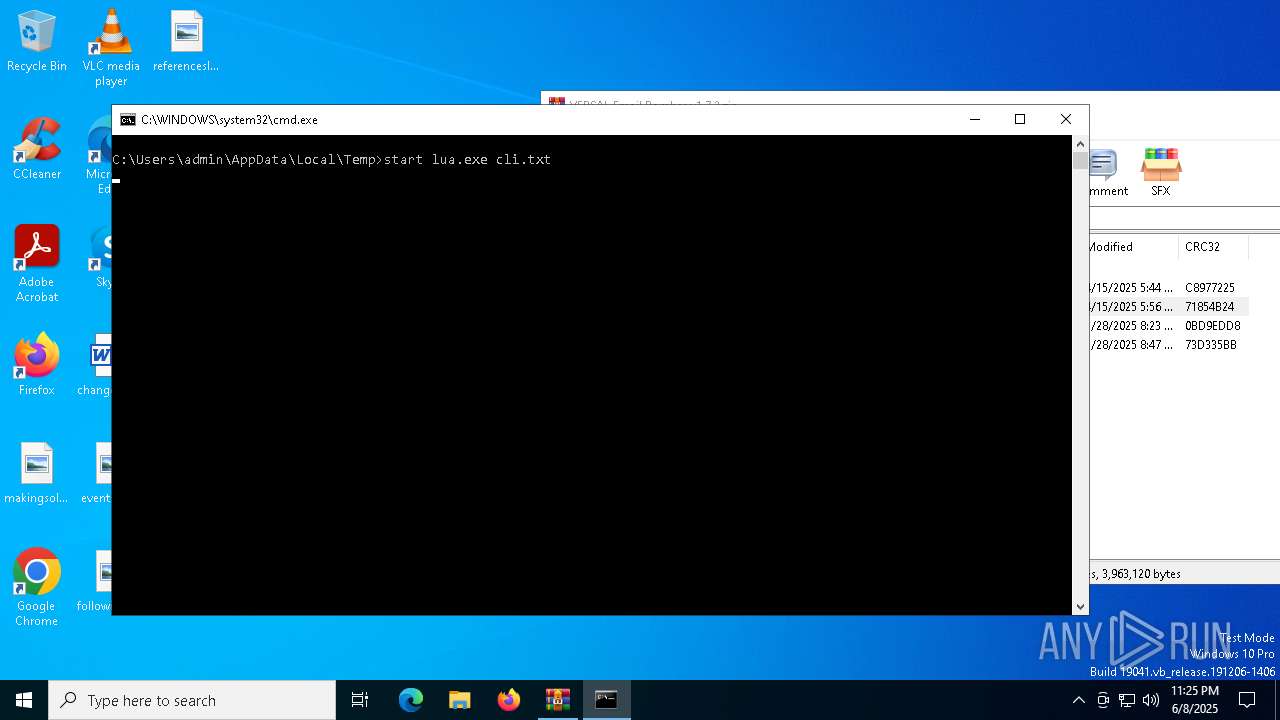
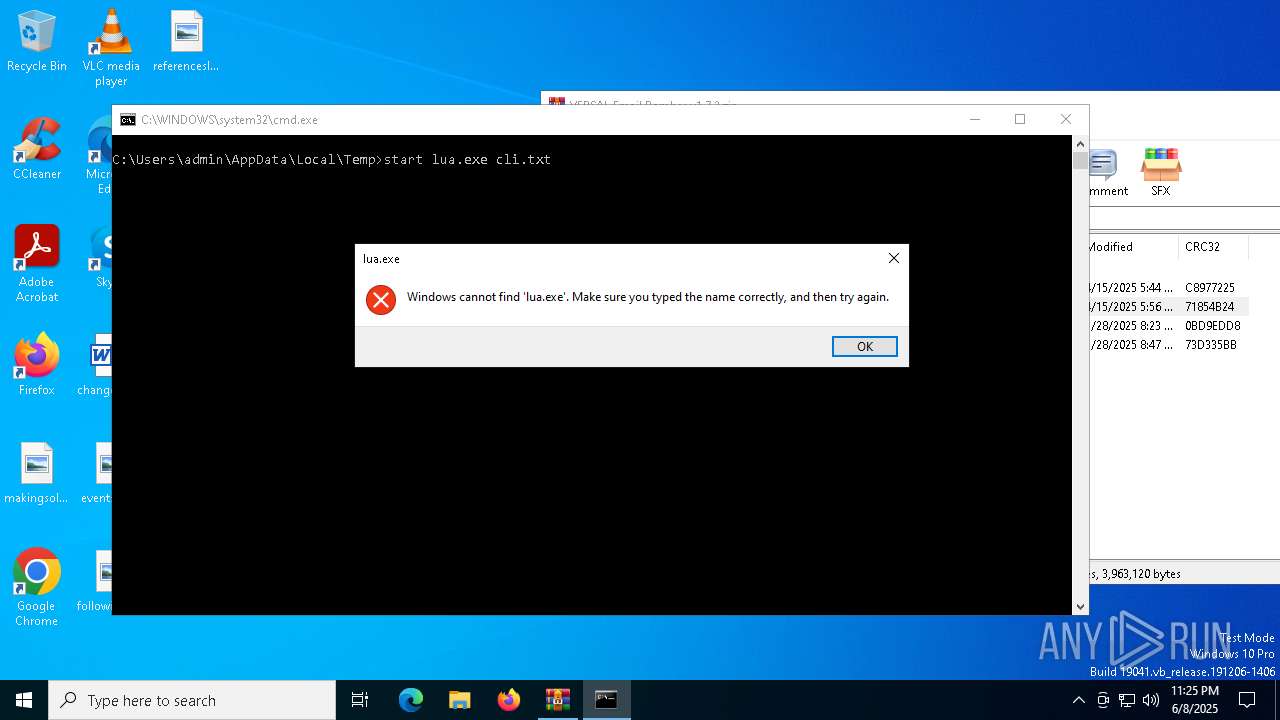
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 4400)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4400)
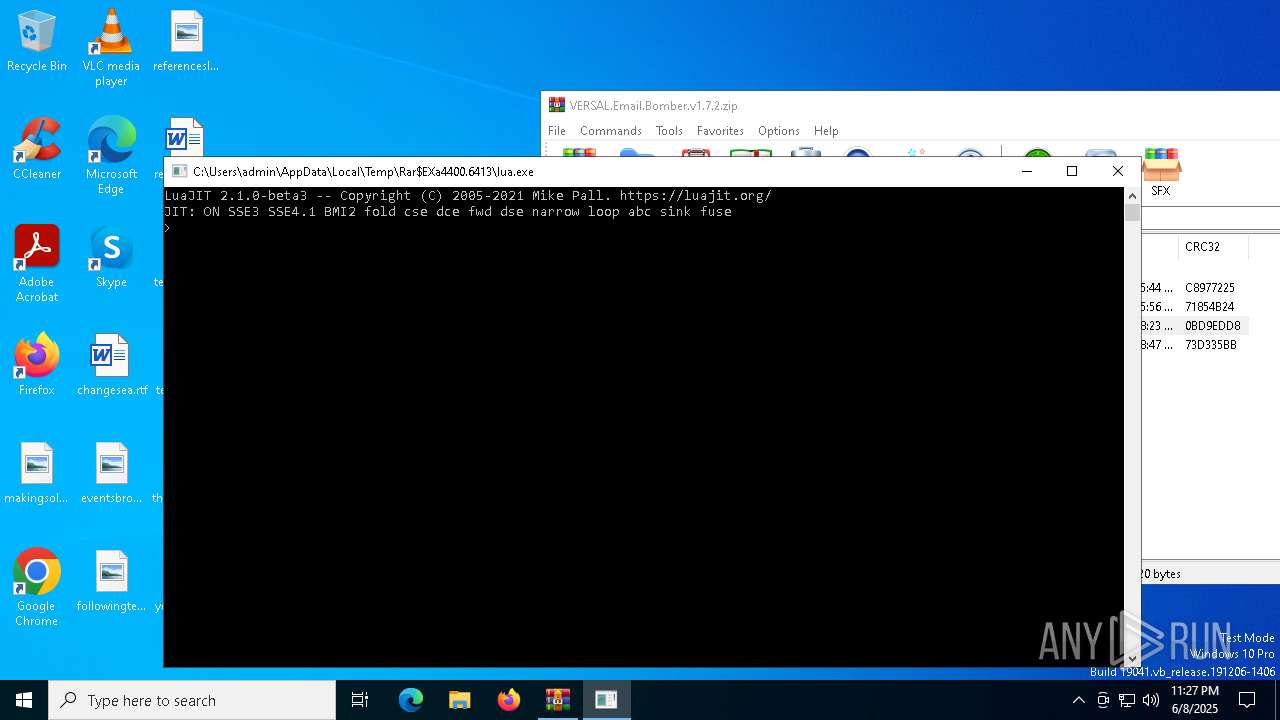
Checks supported languages
- lua.exe (PID: 3032)
- lua.exe (PID: 7336)
- lua.exe (PID: 7288)
- lua.exe (PID: 5116)
- lua.exe (PID: 7612)
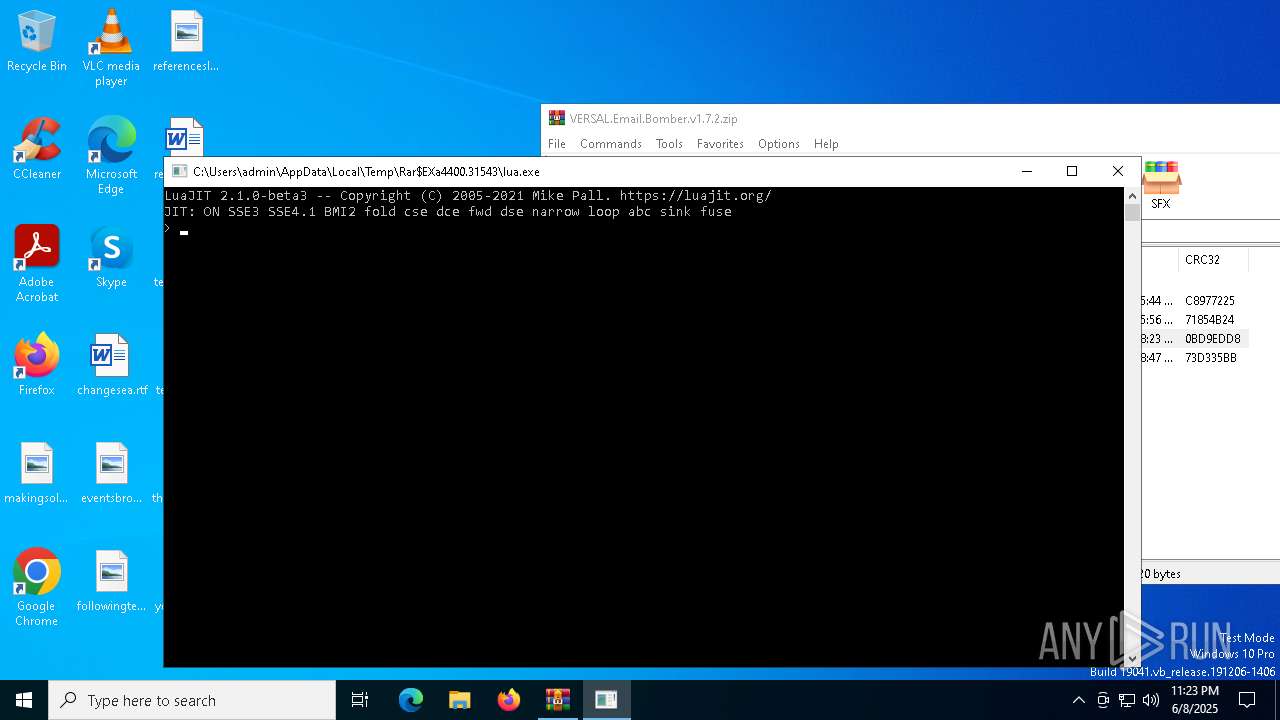
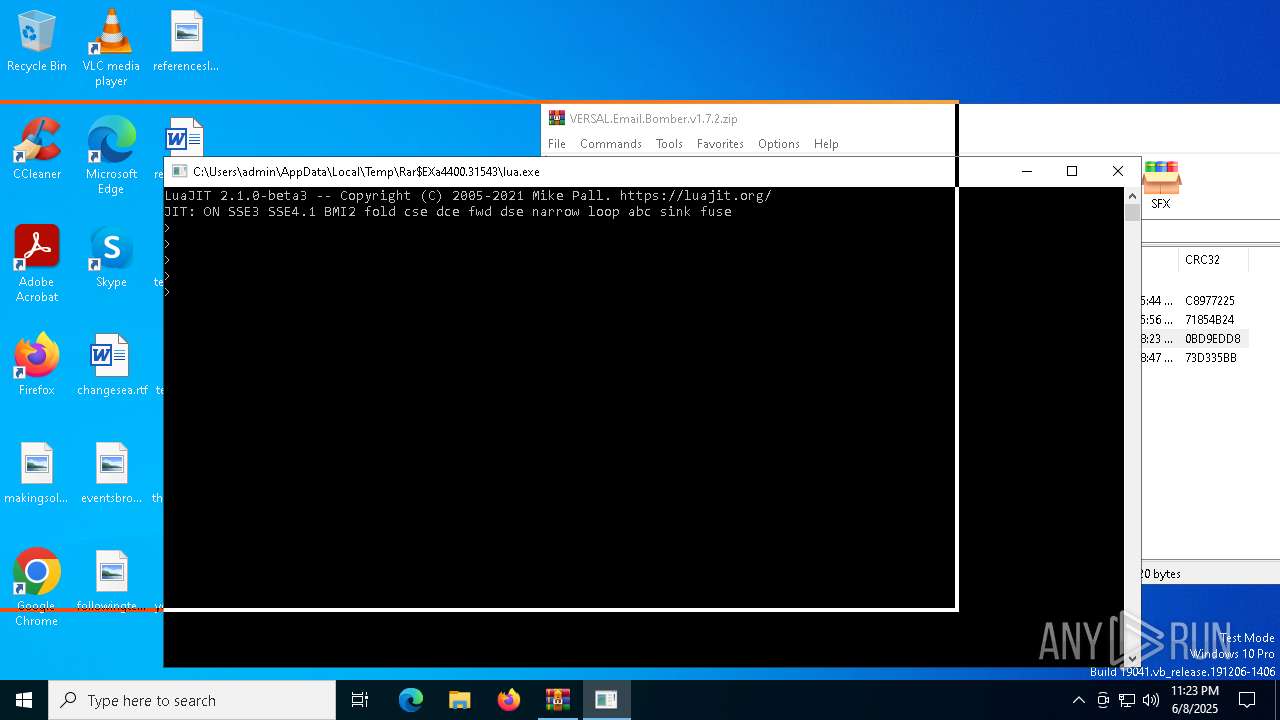
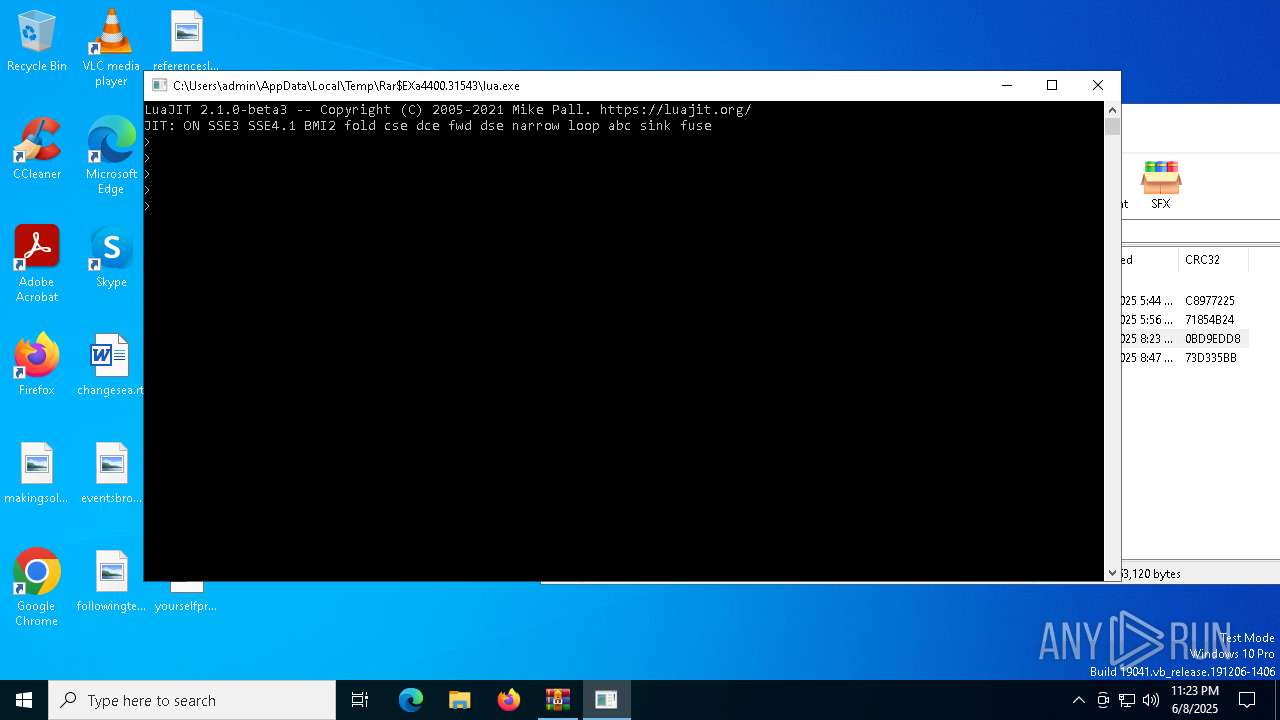
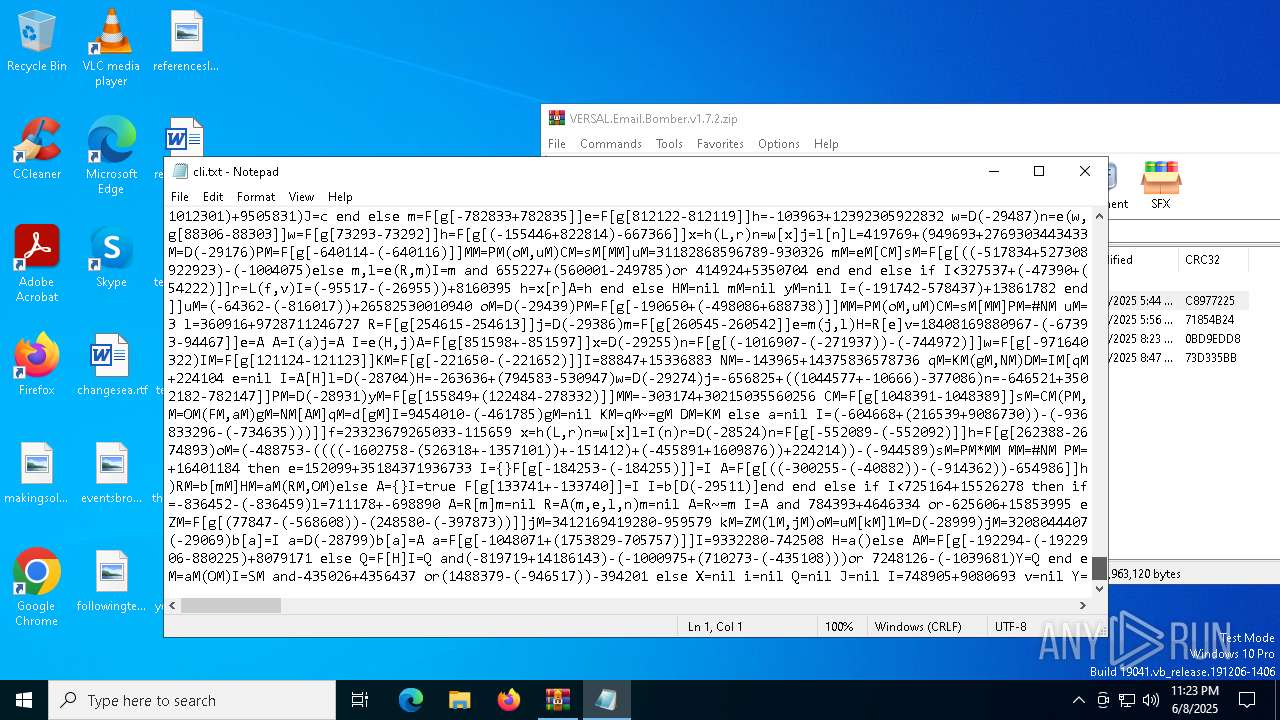
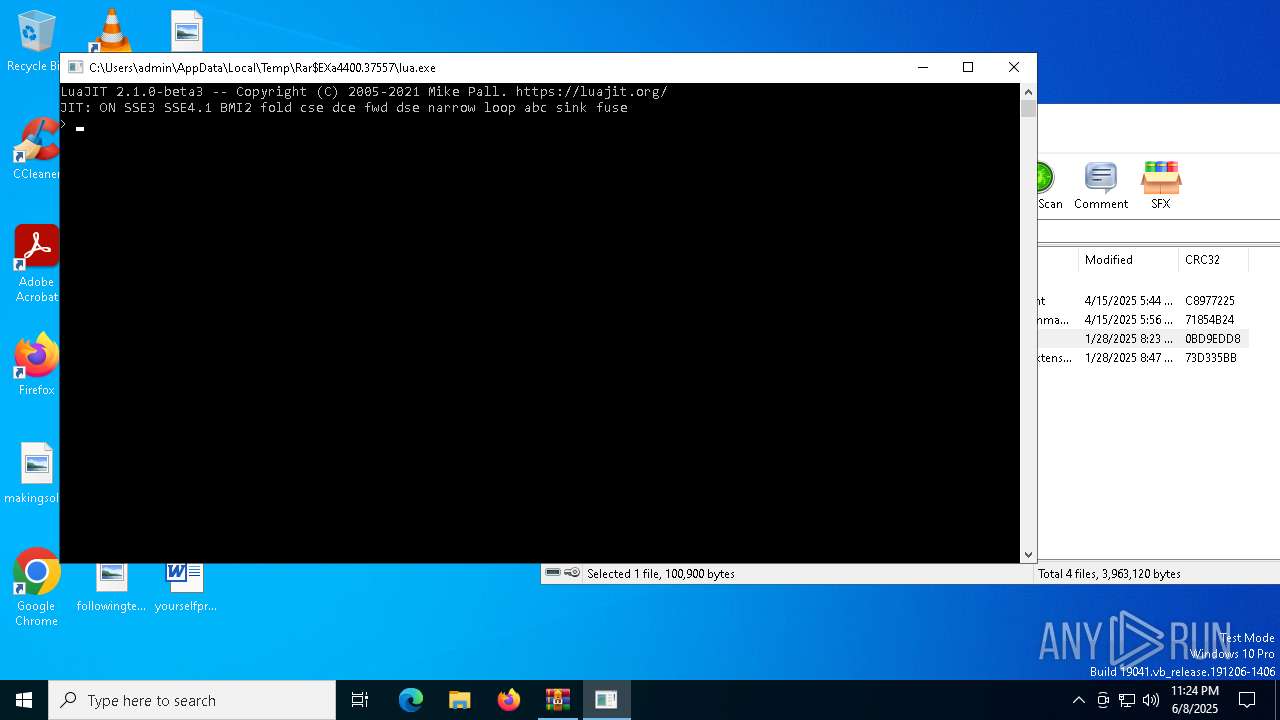
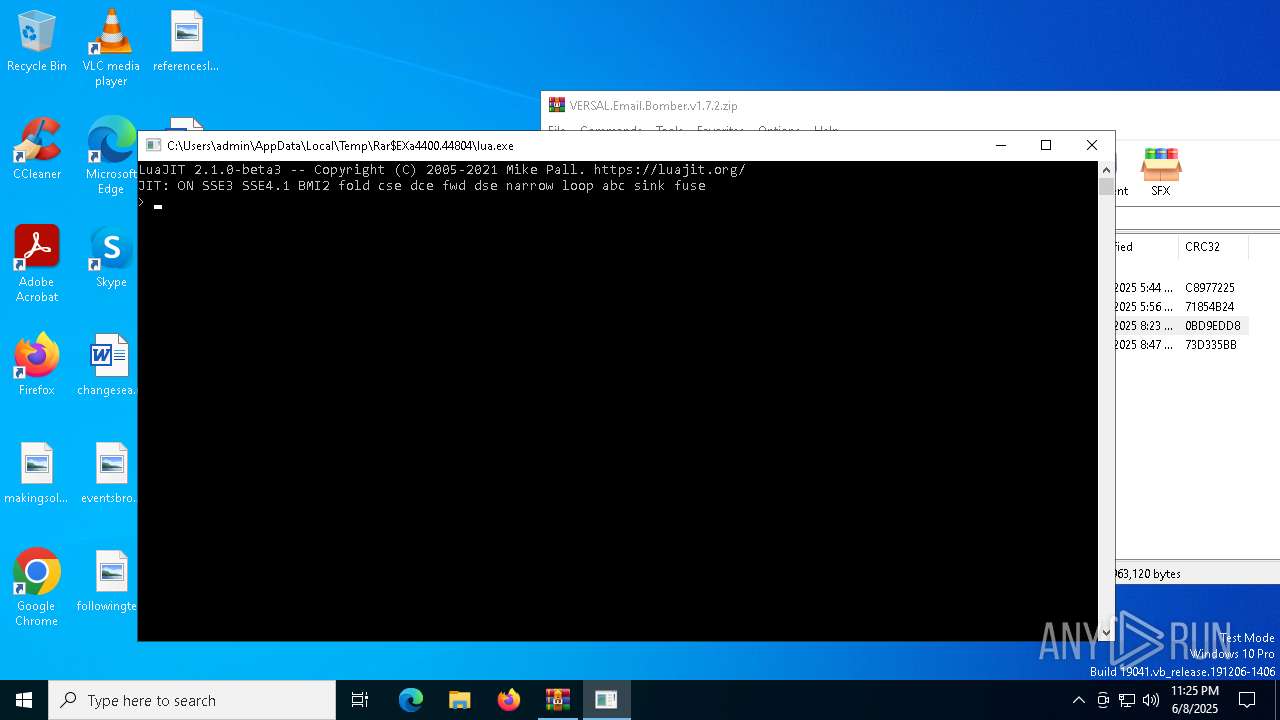
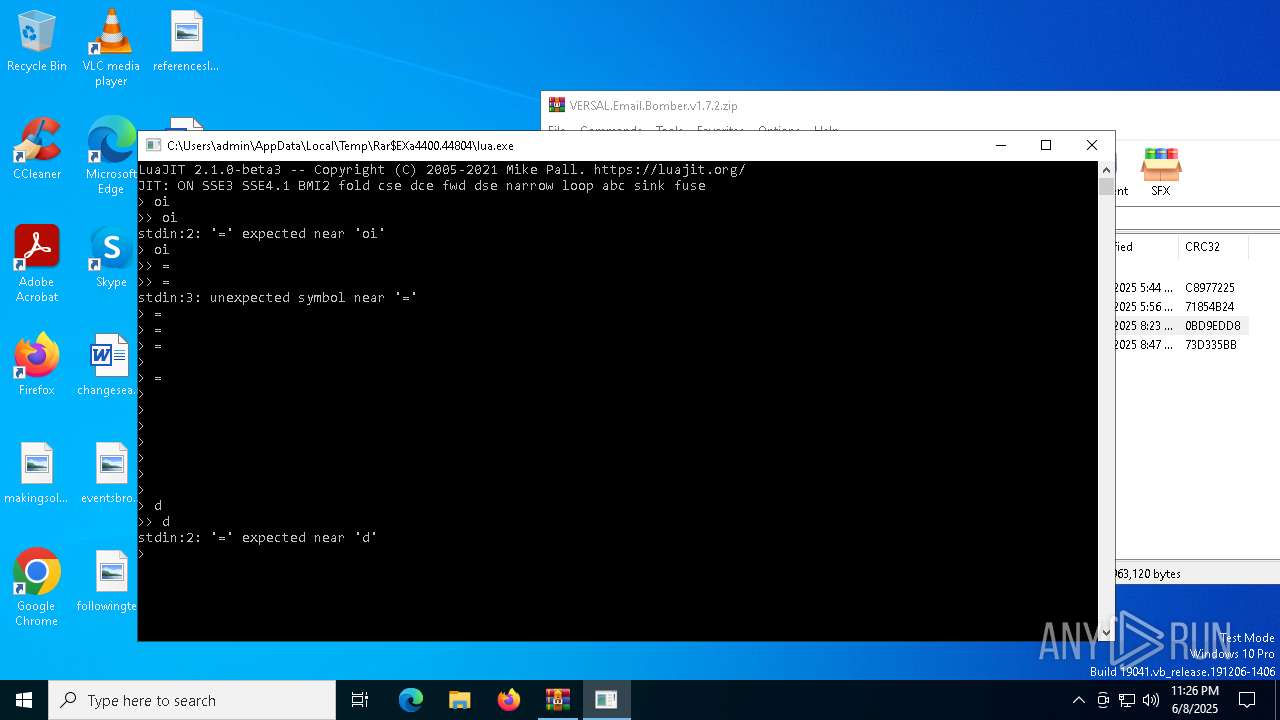
The process uses Lua
- lua.exe (PID: 7336)
- lua.exe (PID: 7288)
- lua.exe (PID: 7612)
- lua.exe (PID: 3032)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 4400)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5452)
Reads the software policy settings
- slui.exe (PID: 6240)
- slui.exe (PID: 8032)
Checks proxy server information
- slui.exe (PID: 8032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
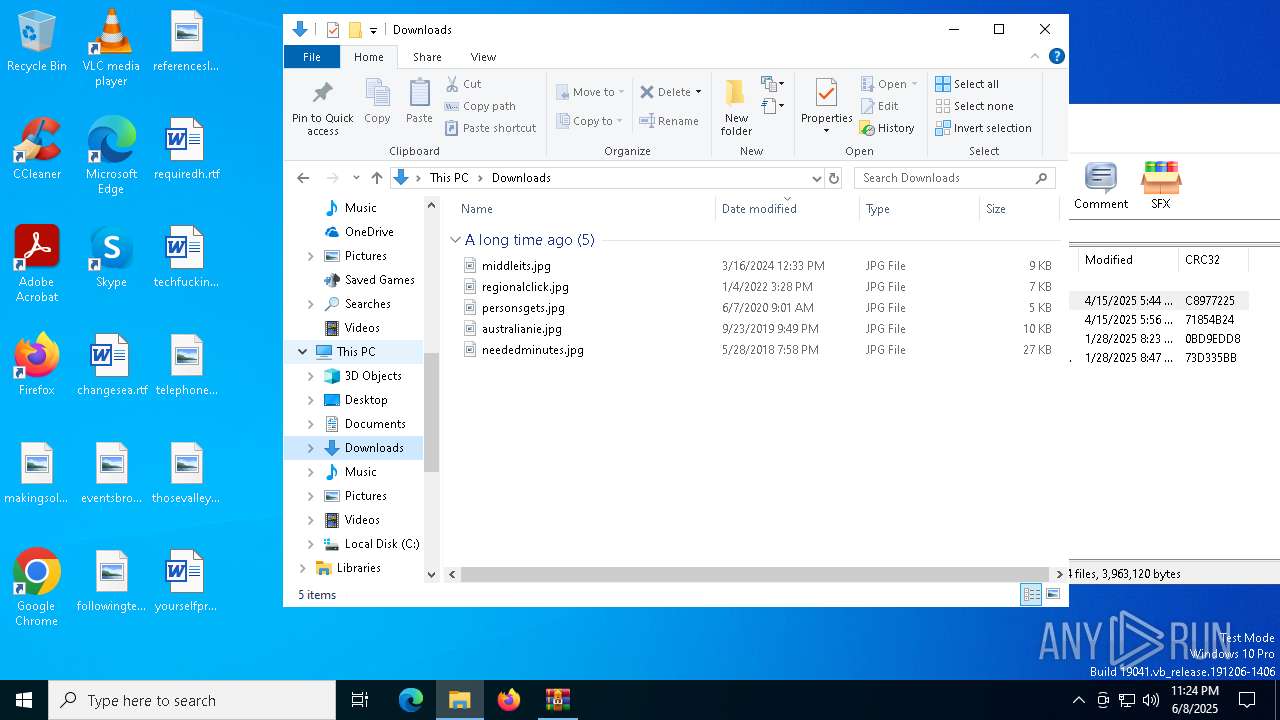
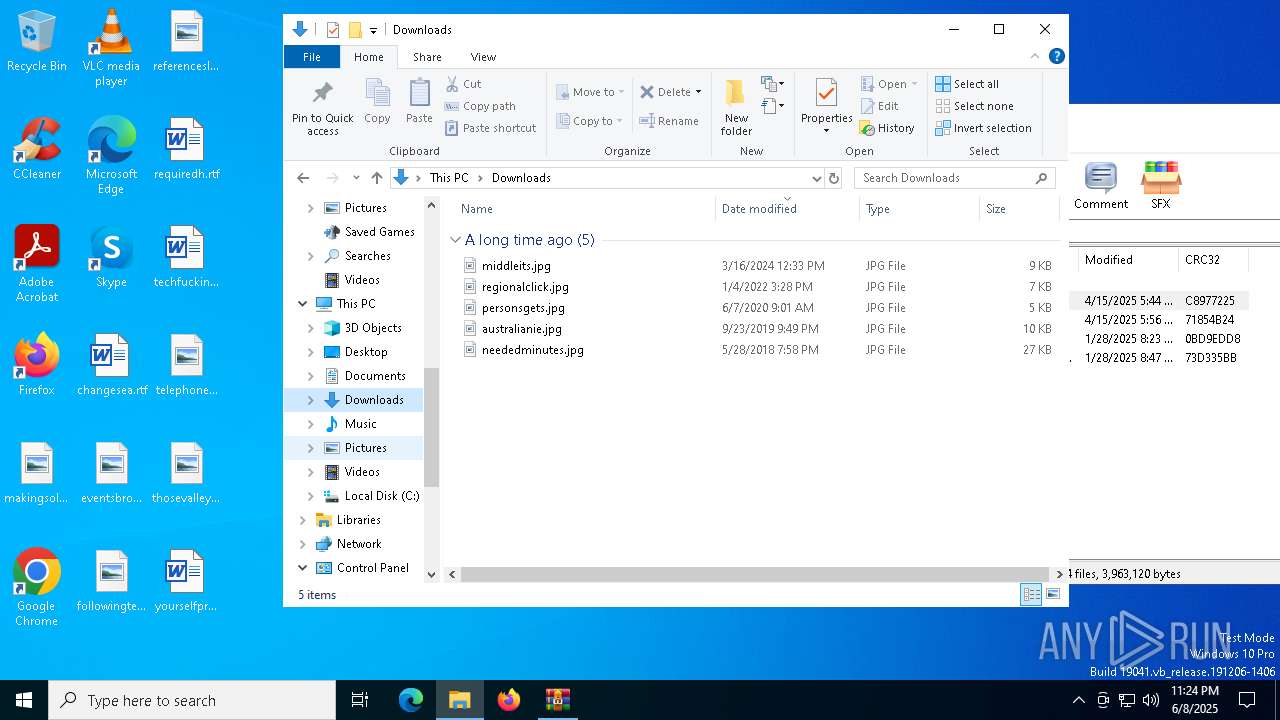
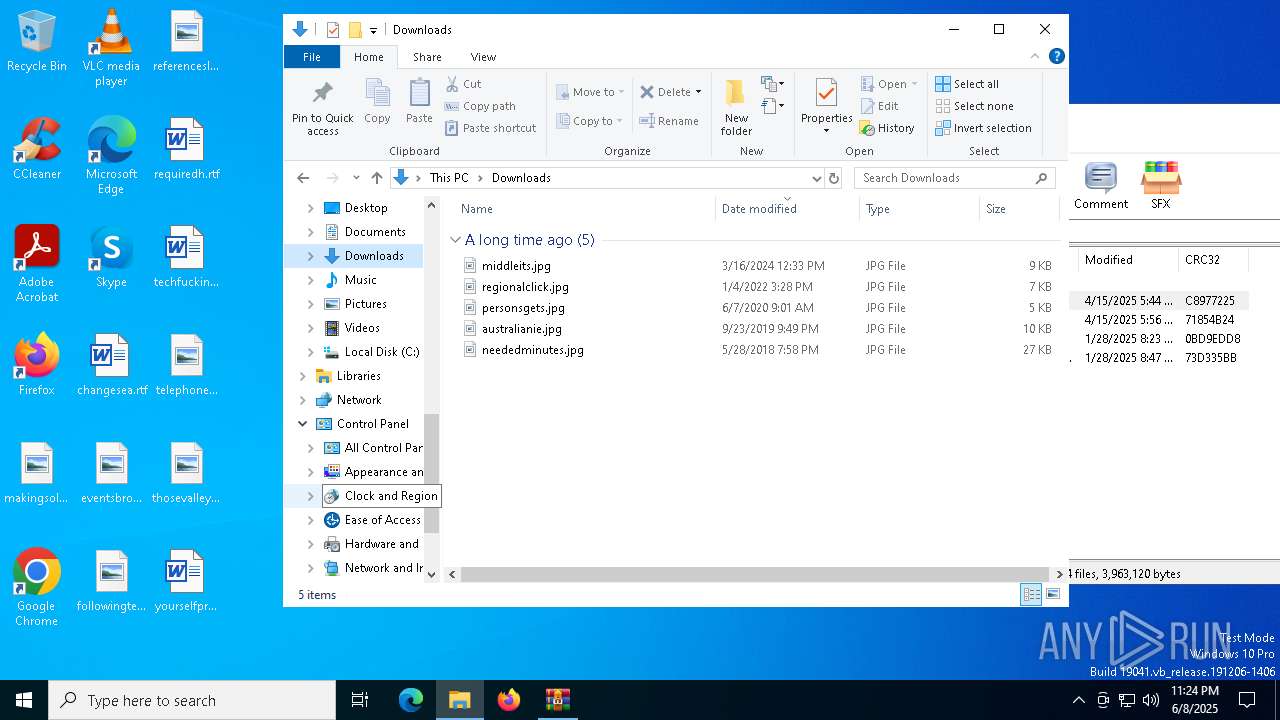
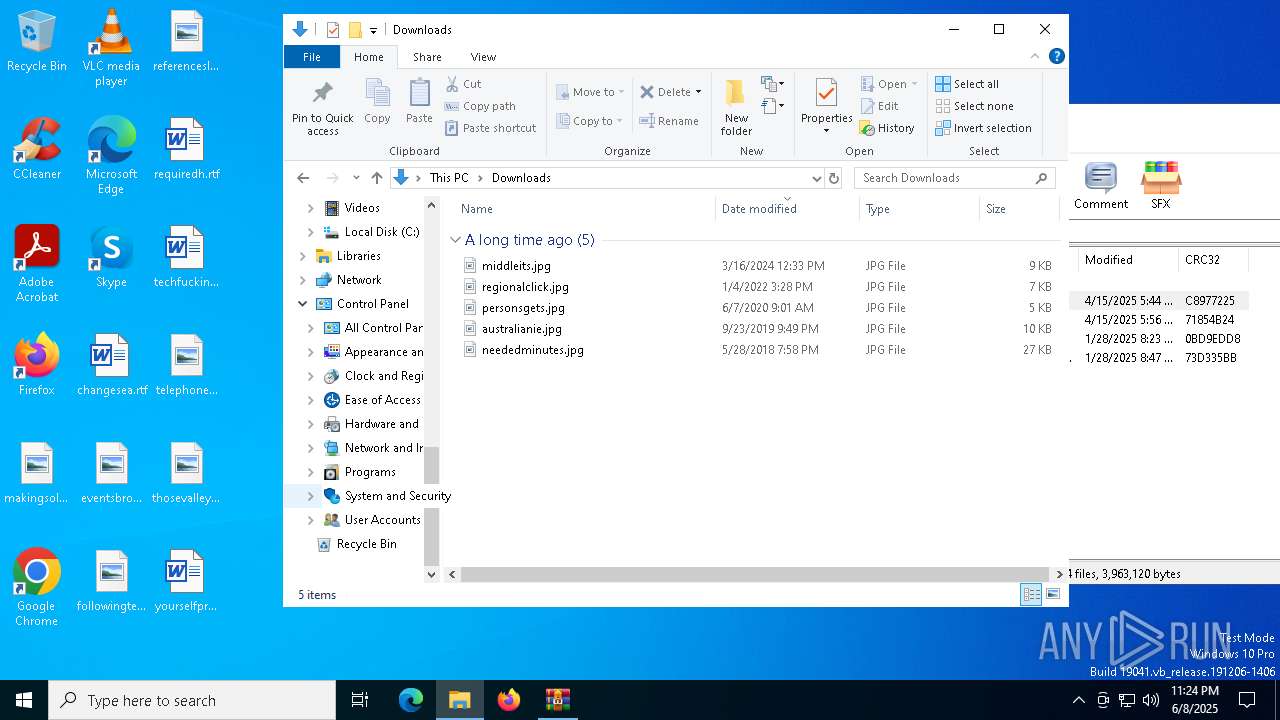
| ZipModifyDate: | 2025:04:15 10:44:44 |
| ZipCRC: | 0xc8977225 |
| ZipCompressedSize: | 140983 |
| ZipUncompressedSize: | 330285 |
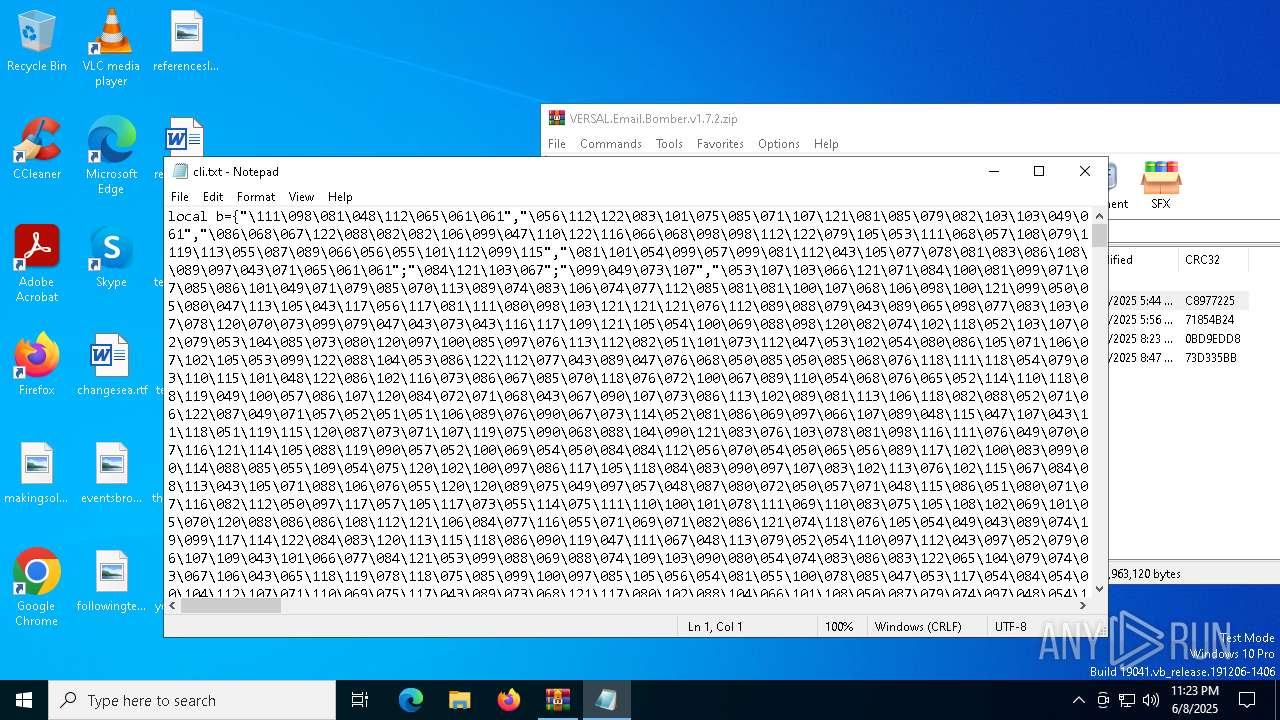
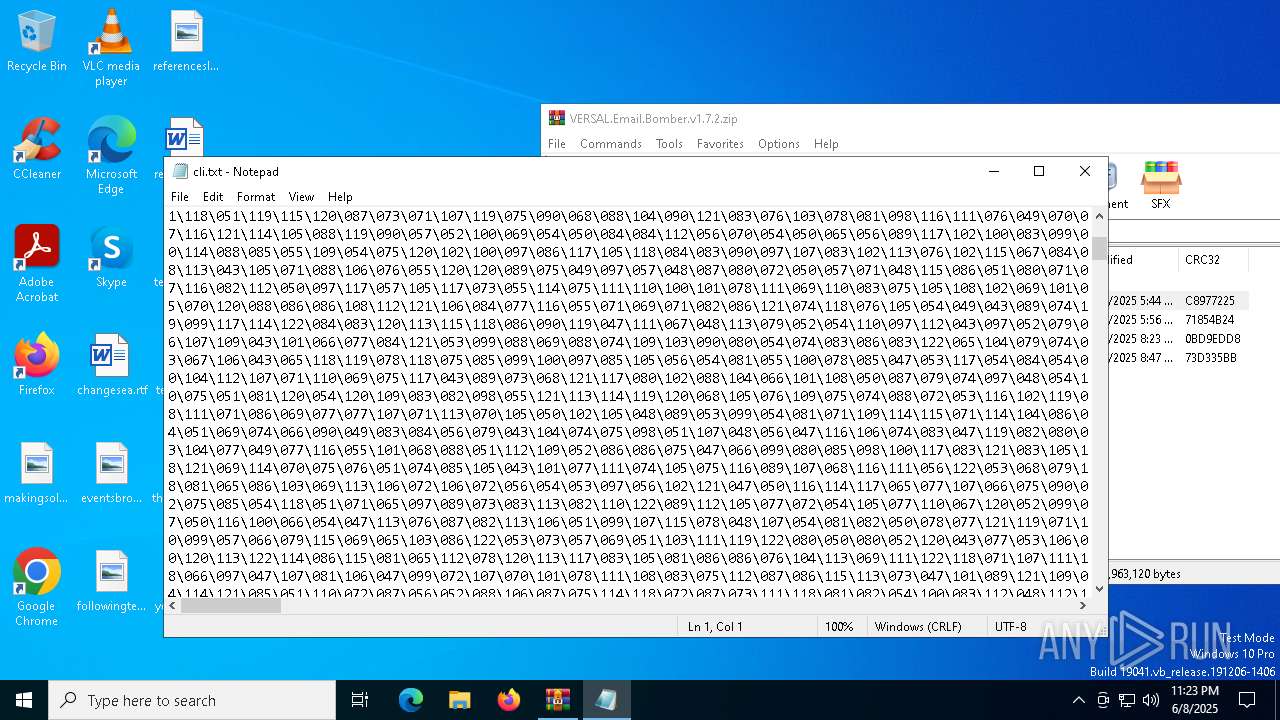
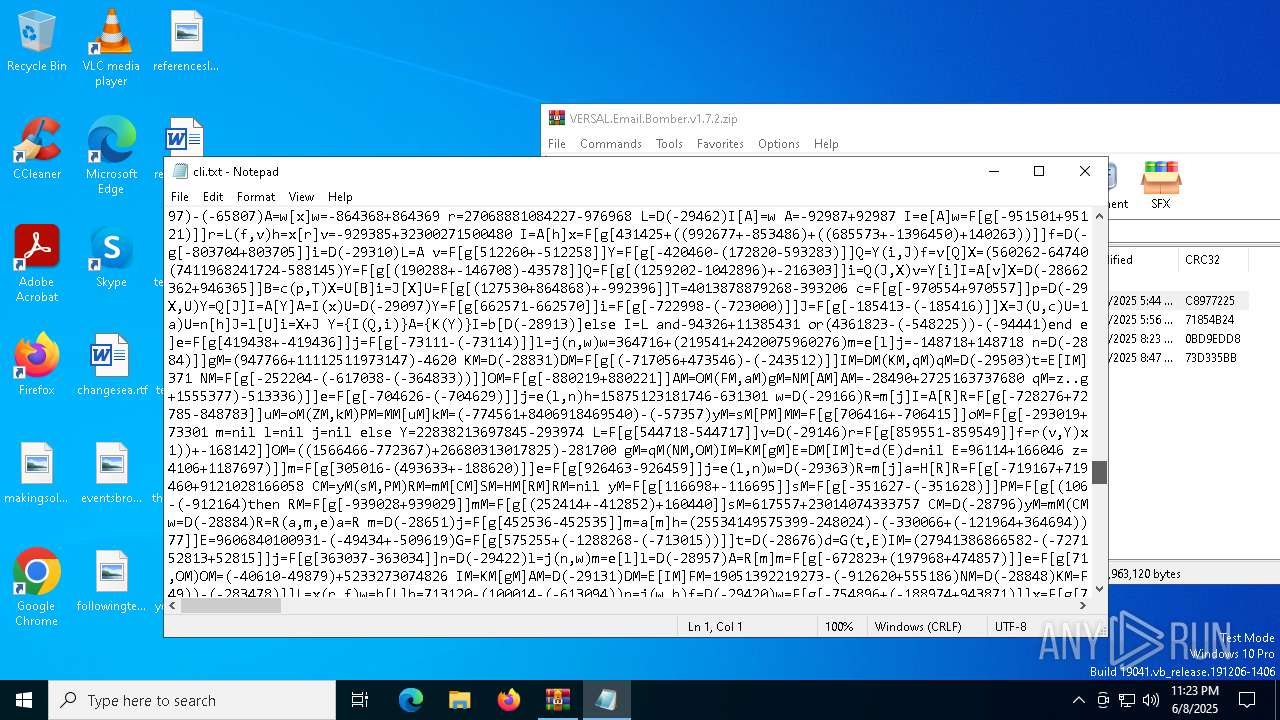
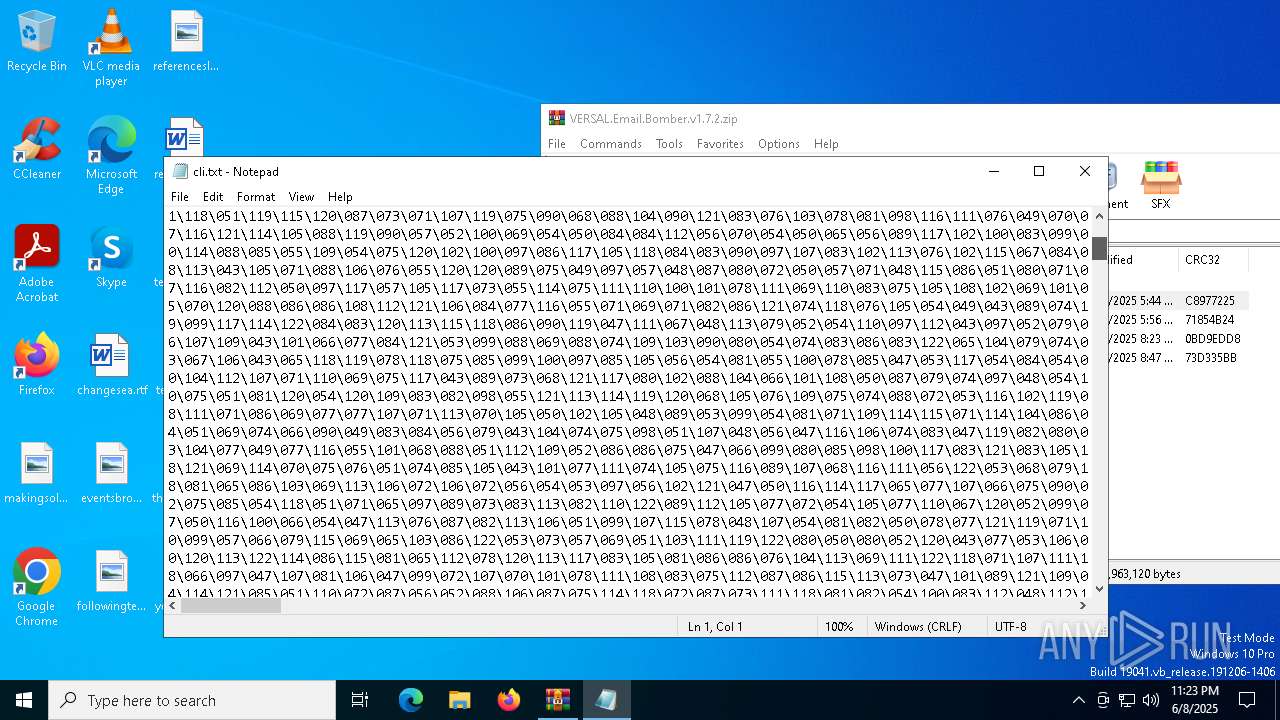
| ZipFileName: | cli.txt |
Total processes
145
Monitored processes
18
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2104 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.6413\lua.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.6413\lua.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 4400 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\VERSAL.Email.Bomber.v1.7.2.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5116 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.43463\lua.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.43463\lua.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
| 5452 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa4400.33381\cli.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5596 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa4400.43993\Launcher.cmd" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5736 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | lua.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 816
Read events
7 804
Write events
12
Delete events
0
Modification events
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\VERSAL.Email.Bomber.v1.7.2.zip | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4400) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
10
Suspicious files
0
Text files
12
Unknown types
0
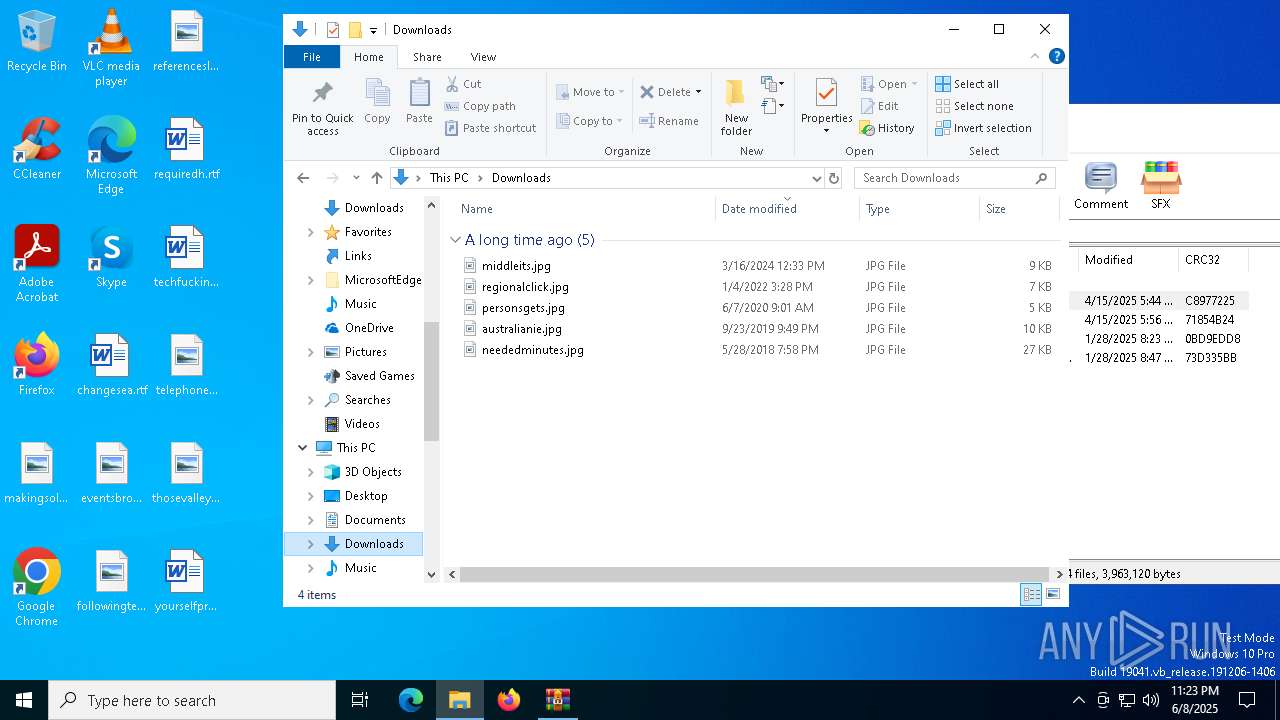
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.37557\cli.txt | text | |
MD5:4D744F3E77A4CB86A676DA9C0A28B186 | SHA256:277A0AA3FB3762438F5BD1F9F35A58979430622BC6234E95A4383667A8402952 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa4400.33381\cli.txt | text | |
MD5:4D744F3E77A4CB86A676DA9C0A28B186 | SHA256:277A0AA3FB3762438F5BD1F9F35A58979430622BC6234E95A4383667A8402952 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.43463\cli.txt | text | |
MD5:4D744F3E77A4CB86A676DA9C0A28B186 | SHA256:277A0AA3FB3762438F5BD1F9F35A58979430622BC6234E95A4383667A8402952 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.31543\lua51.dll | executable | |
MD5:4EBD617A3AD9A9619172BD14A902A400 | SHA256:C7A657AF5455812FB215A8888B7E3FD8FA1BA27672A3ED9021EB6004EFF271AC | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.43463\Launcher.cmd | text | |
MD5:E66816F9880811713867E9AF8176D26A | SHA256:0B2DD257C50ED37C239E248987132EBC75138D09D01B3BE5D360953C190EE5D6 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.37557\lua.exe | executable | |
MD5:00F60EE3FF2DEE681B5D7D442009B2C2 | SHA256:5343326FB0B4F79C32276F08FFCC36BD88CDE23AA19962BD1E8D8B80F5D33953 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.43463\lua51.dll | executable | |
MD5:4EBD617A3AD9A9619172BD14A902A400 | SHA256:C7A657AF5455812FB215A8888B7E3FD8FA1BA27672A3ED9021EB6004EFF271AC | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.31543\cli.txt | text | |
MD5:4D744F3E77A4CB86A676DA9C0A28B186 | SHA256:277A0AA3FB3762438F5BD1F9F35A58979430622BC6234E95A4383667A8402952 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.44804\lua.exe | executable | |
MD5:00F60EE3FF2DEE681B5D7D442009B2C2 | SHA256:5343326FB0B4F79C32276F08FFCC36BD88CDE23AA19962BD1E8D8B80F5D33953 | |||
| 4400 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4400.31543\lua.exe | executable | |
MD5:00F60EE3FF2DEE681B5D7D442009B2C2 | SHA256:5343326FB0B4F79C32276F08FFCC36BD88CDE23AA19962BD1E8D8B80F5D33953 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
29
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
872 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
872 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6544 | svchost.exe | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |