| URL: | ibomma.com |
| Full analysis: | https://app.any.run/tasks/5281e7cb-5020-4722-9e3c-1503e2d4c38a |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2024, 07:18:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7CCD69F2CA6E4EB0F8C2E069655219F3 |
| SHA1: | 4AD3151DE5D4C1482F85265922F286041C5DACBD |
| SHA256: | 49D79244F963741D76A156B0C65E8E53BE5B57DF94153FC3CCD8A6D310D150A9 |
| SSDEEP: | 3:GKkGT:GKPT |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- msdt.exe (PID: 1844)
Reads settings of System Certificates
- msdt.exe (PID: 1844)
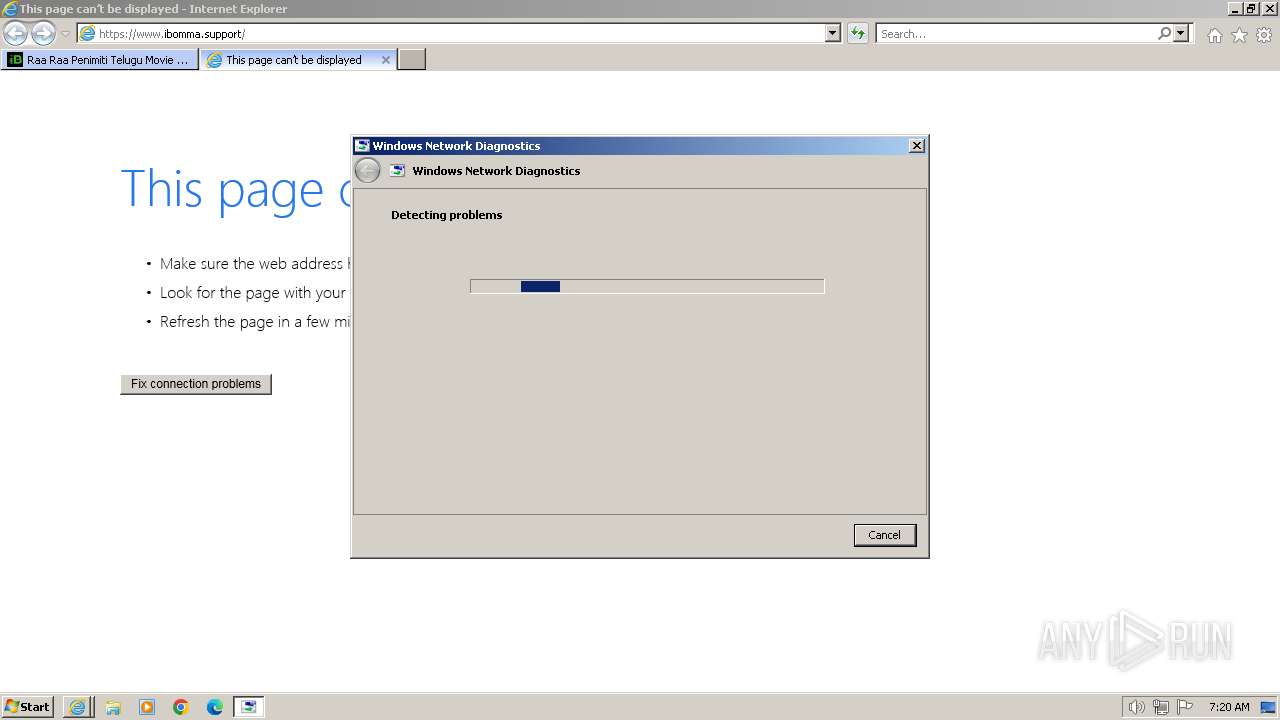
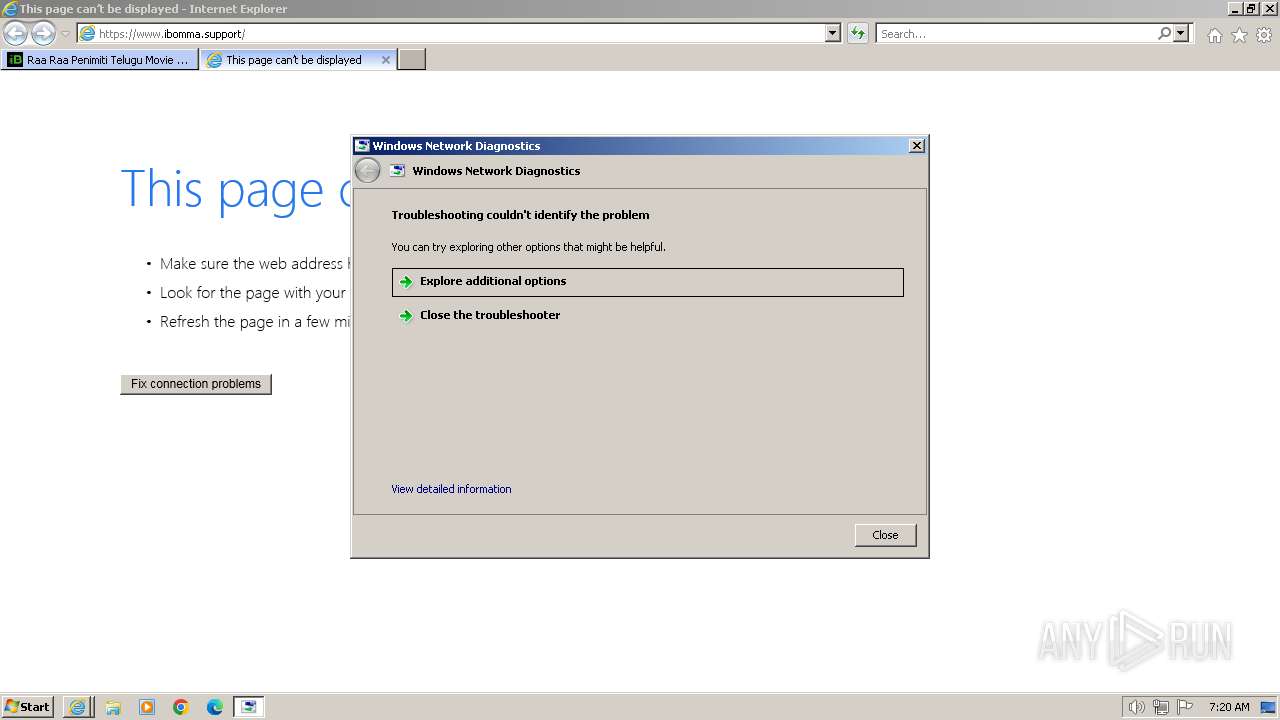
Process uses IPCONFIG to discover network configuration
- sdiagnhost.exe (PID: 2804)
Reads the Internet Settings
- sdiagnhost.exe (PID: 2804)
Uses ROUTE.EXE to obtain the routing table information
- sdiagnhost.exe (PID: 2804)
INFO
Application launched itself
- iexplore.exe (PID: 3668)
Reads security settings of Internet Explorer
- msdt.exe (PID: 1844)
- sdiagnhost.exe (PID: 2804)
Reads the software policy settings
- msdt.exe (PID: 1844)
Drops the executable file immediately after the start
- msdt.exe (PID: 1844)
Create files in a temporary directory
- msdt.exe (PID: 1844)
- makecab.exe (PID: 3444)
- sdiagnhost.exe (PID: 2804)
Creates files or folders in the user directory
- msdt.exe (PID: 1844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
8
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1844 | -modal 1114548 -skip TRUE -path C:\Windows\diagnostics\system\networking -af C:\Users\admin\AppData\Local\Temp\NDF7E9D.tmp -ep NetworkDiagnosticsWeb | C:\Windows\System32\msdt.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Diagnostics Troubleshooting Wizard Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2040 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\System32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2172 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\System32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2804 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3668 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3444 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\System32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Internet Explorer\iexplore.exe" "ibomma.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3776 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3668 CREDAT:3609887 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
32 487
Read events
32 233
Write events
215
Delete events
39
Modification events
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31090618 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31090618 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
52
Text files
92
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\logo[1].svg | image | |
MD5:2DEF442B0E2D75C069457F159288A36D | SHA256:CB7E016F81E91531A4F3801CF97C265ABD829332484D55622FE3D5390925BC2E | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3C8F137F12129D0F41D9235D01046749 | SHA256:E8FC1E95AE146B6A67918353D41EB09060BF2C86252AE4490B7E496216833BB8 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\responsive[1].css | text | |
MD5:15CF5365788B721F4ABF11D15C7B9163 | SHA256:12109F36B27E94E45EC62EE949A50BCF7A8784886BEAA5DA215509B76C052D6A | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\android-icon-192x192[1].png | image | |
MD5:81A8A16948B280080501C068411B5FD5 | SHA256:6EC3849B544BB08DFEEF5469D95C58EC6AB3054EBDB961BF0FF90F4627EBD928 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:5D6A57DC537C0E6E965DCD67581142B2 | SHA256:2A8D3F00B77E963A4DFEC1523E0BC49FB3EA96D8AB38F954035AD9DA65D3DCC0 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\UHVs7jR_RN63PG8SIAriEAOEpWw[1].js | text | |
MD5:B8F9744EBBD2D112699F26F24A3FFFFC | SHA256:9A27DE13F20512D7300C6B286CC11B85CC9740CF610306019D401FAFEC9B0667 | |||
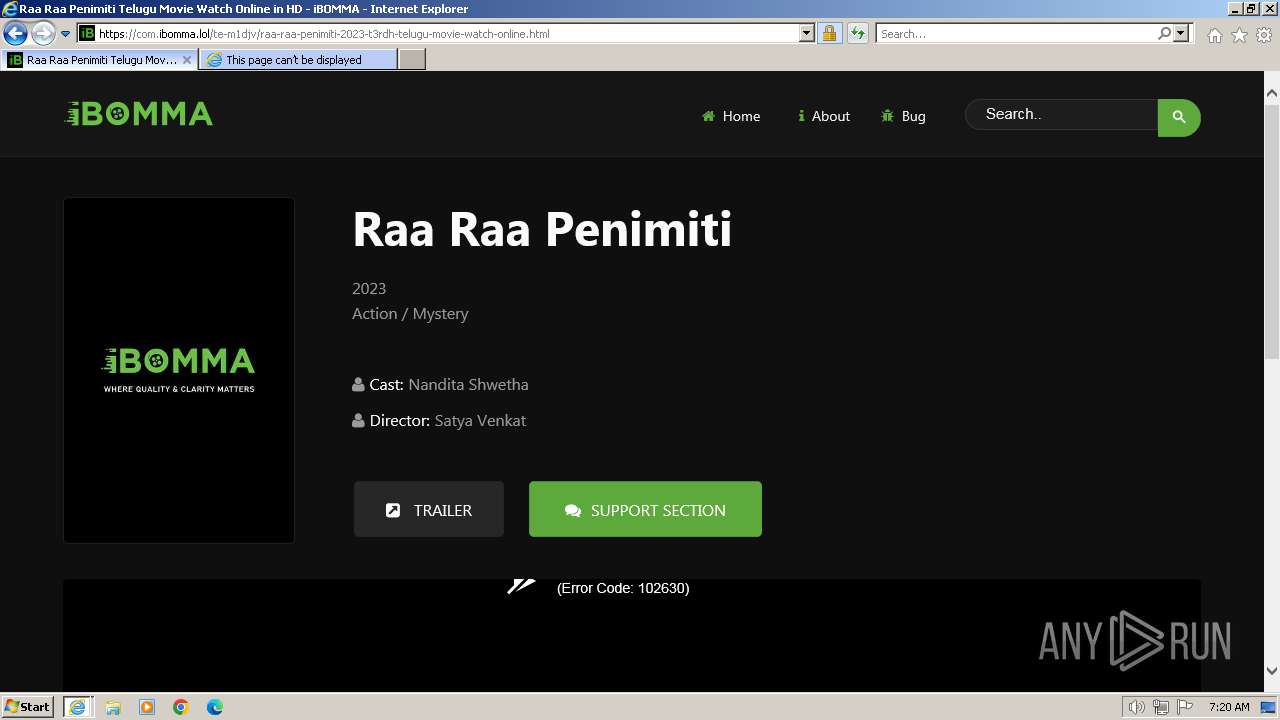
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\telugu-movies[1].htm | html | |
MD5:8B39641FA4384EAED83374F7764AD4D0 | SHA256:BF17BC28D6C1C11CD199FCB6B59E9F5172797E9D360DDD8DE9E6A868FB2BE331 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\imagestore\f7ruq93\imagestore.dat | binary | |
MD5:BC94C6E1E34B5BD3ADA49C6C8B7A2B7C | SHA256:091D04BF53CA3C173D7F569969A5E4A221F251EFFFBE2C5B376A181A11EF9F12 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:D4406E9626B2B3F701BF31C6CB74D048 | SHA256:1AE3E1561FE90721141829B39AC9D24065C01B8CFADE5FBAD5D23DCB00DA8452 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:80E56464F06C608115109ACB9FE492C4 | SHA256:93E29D9D7C8ED234E87C9659FC960CB47E2D200AA2E84A425B1B5B3E59CADC6C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
63
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 302 | 188.114.97.3:80 | http://ibomma.com/ | NL | — | — | unknown |
3348 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8a21c6ad756e8dd9 | GB | — | — | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | binary | 1.47 Kb | unknown |
3668 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9ff441305e057d43 | GB | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEH6HwqMlsnS7%2BryQ1sUoZV4%3D | US | binary | 1.40 Kb | unknown |
3348 | iexplore.exe | GET | 301 | 188.114.97.3:80 | http://com.ibomma.lol/telugu-movies/ | NL | — | — | unknown |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGHsycmQas7CCZXEOfu%2B%2Bqs%3D | US | binary | 471 b | unknown |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDDidhelLJLaQnsKqlsZYpa | US | binary | 472 b | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3ff405f9fd660c92 | GB | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3348 | iexplore.exe | 188.114.97.3:80 | ibomma.com | CLOUDFLARENET | NL | unknown |
3348 | iexplore.exe | 188.114.96.3:443 | ibomma.com | CLOUDFLARENET | NL | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3348 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3348 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3668 | iexplore.exe | 188.114.96.3:443 | ibomma.com | CLOUDFLARENET | NL | unknown |
3668 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3668 | iexplore.exe | 184.86.251.19:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ibomma.com |
| unknown |
url9wzcllmpz6wx0_njzxse--vets5cvds.ibomma.support |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
akamai-aws-s3--ib-com-bucket.lokicdn.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
com.ibomma.lol |
| unknown |
cdnjs.cloudflare.com |
| whitelisted |