| File name: | Gandcrab5.0.3.exe |
| Full analysis: | https://app.any.run/tasks/cb8c34bb-7a41-49ce-8a21-ecee14c7cc98 |
| Verdict: | Malicious activity |
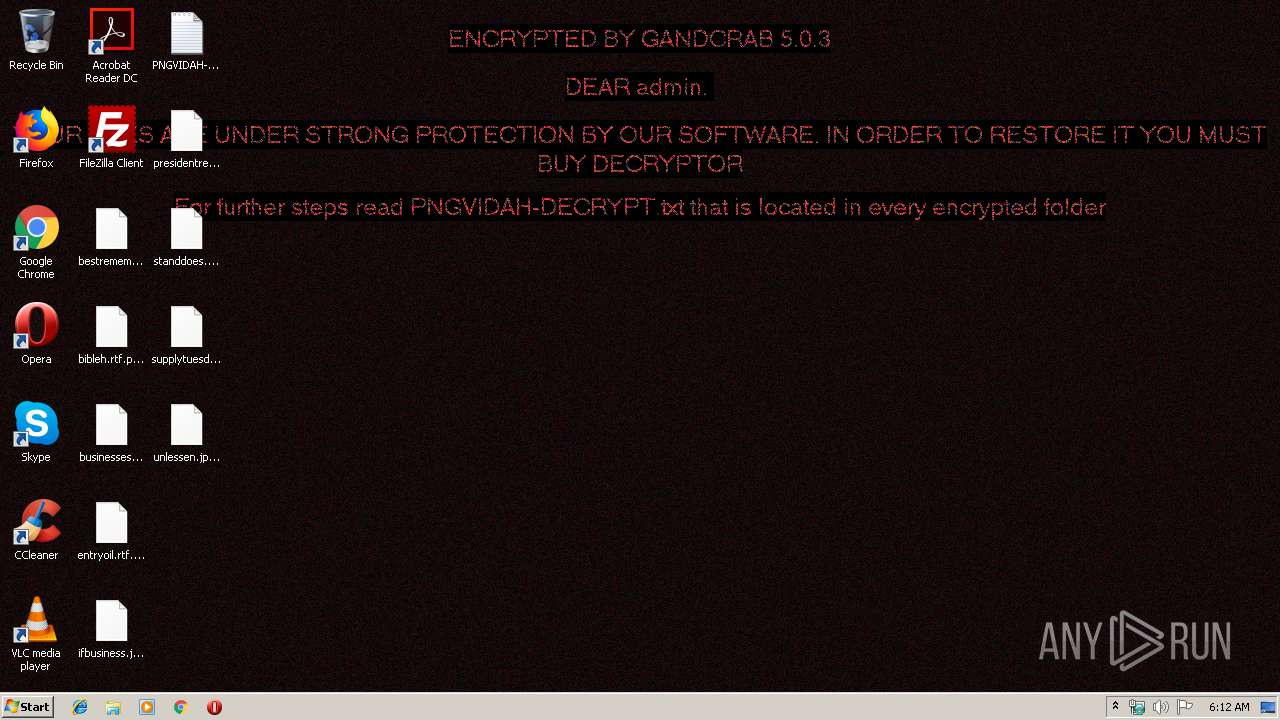
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
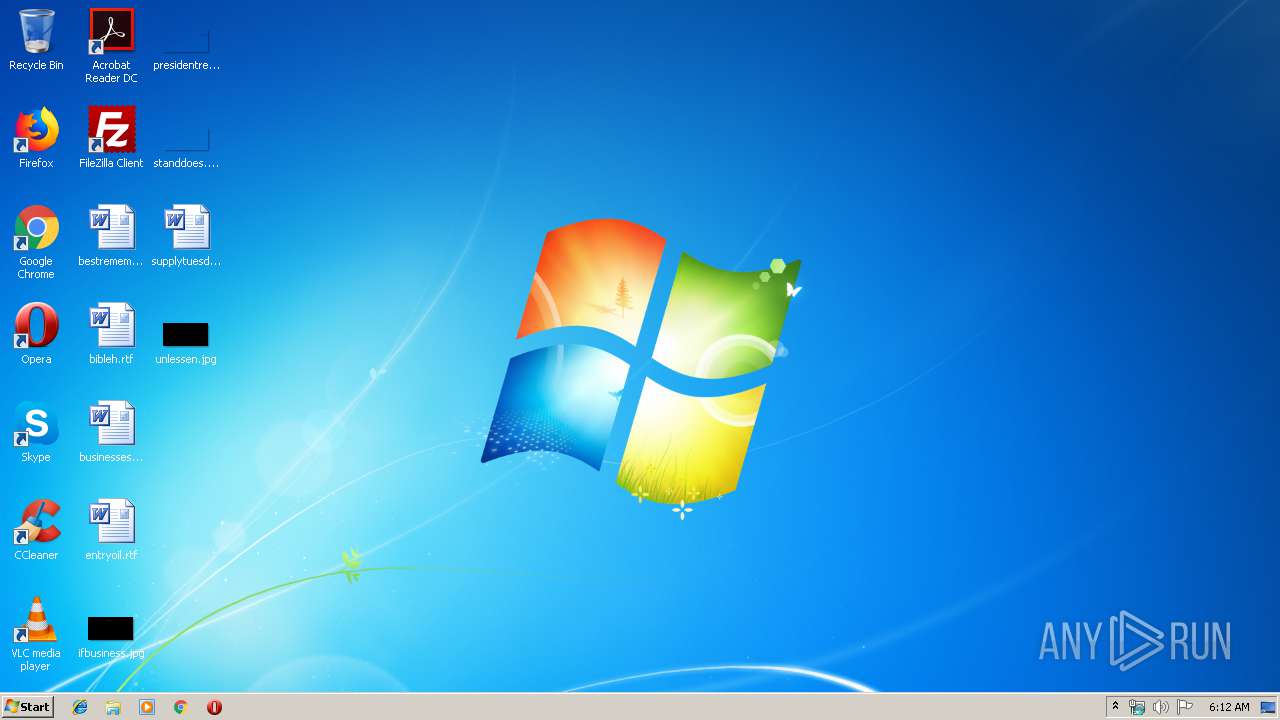
| Analysis date: | January 18, 2020, 06:12:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 95557A29DE4B70A25CE62A03472BE684 |
| SHA1: | 5BAABF2869278E60D4C4F236B832BFFDDD6CF969 |
| SHA256: | 49B769536224F160B6087DC866EDF6445531C6136AB76B9D5079CE622B043200 |
| SSDEEP: | 6144:/UGV83D35bJrqV2L/E0tA+j16kUef5Nj1mB9WjEw0tzMV:qvmVe9h1qEtkBzw0tQ |
MALICIOUS
GandCrab keys found
- wermgr.exe (PID: 1552)
Actions looks like stealing of personal data
- wermgr.exe (PID: 1552)
Deletes shadow copies
- wermgr.exe (PID: 1552)
Writes file to Word startup folder
- wermgr.exe (PID: 1552)
Renames files like Ransomware
- wermgr.exe (PID: 1552)
GANDCRAB detected
- wermgr.exe (PID: 1552)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- wermgr.exe (PID: 1552)
Creates files like Ransomware instruction
- wermgr.exe (PID: 1552)
Creates files in the user directory
- wermgr.exe (PID: 1552)
INFO
Dropped object may contain Bitcoin addresses
- wermgr.exe (PID: 1552)
Dropped object may contain TOR URL's
- wermgr.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:12:06 12:34:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 12288 |
| InitializedDataSize: | 417792 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x377e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.0.800 |
| ProductVersionNumber: | 4.2.0.800 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | www.sopcast.com |
| CompanyName: | www.sopcast.com |
| FileDescription: | SopCast Main Application |
| FileVersion: | 4.2.0.800 |
| InternalName: | SopCast.exe |
| LegalCopyright: | Copyright (C) 2004 - 2013, SopCast.com. All rights reserved. |
| OriginalFileName: | SopCast.exe |
| ProductName: | SopCast |
| ProductVersion: | 4.2.0.800 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Dec-2016 11:34:00 |
| Detected languages: |
|
| Comments: | www.sopcast.com |
| CompanyName: | www.sopcast.com |
| FileDescription: | SopCast Main Application |
| FileVersion: | 4.2.0.800 |
| InternalName: | SopCast.exe |
| LegalCopyright: | Copyright (C) 2004 - 2013, SopCast.com. All rights reserved. |
| OriginalFilename: | SopCast.exe |
| ProductName: | SopCast |
| ProductVersion: | 4.2.0.800 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Dec-2016 11:34:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00002D3A | 0x00003000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.82269 |
.rdata | 0x00004000 | 0x00001988 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.21012 |
.data | 0x00006000 | 0x000147BC | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.31754 |
.rsrc | 0x0001B000 | 0x00031D4C | 0x00032000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.4756 |
.xml | 0x0004D000 | 0x0001CE90 | 0x0001D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.01172 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.44549 | 868 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.46398 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.6789 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.67062 | 21640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.60127 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.78842 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.22584 | 84 | UNKNOWN | English - United States | RT_STRING |
8 | 5.07979 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.12251 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
100 | 3.46376 | 974 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
MFC42.DLL |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1484 | "C:\Users\admin\AppData\Local\Temp\Gandcrab5.0.3.exe" | C:\Users\admin\AppData\Local\Temp\Gandcrab5.0.3.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sopcast.com Integrity Level: MEDIUM Description: SopCast Main Application Exit code: 0 Version: 4.2.0.800 Modules
| |||||||||||||||
| 1552 | "C:\Windows\System32\wermgr.exe" | C:\Windows\System32\wermgr.exe | Gandcrab5.0.3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3372 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | wermgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
126
Read events
90
Write events
36
Delete events
0
Modification events
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_CURRENT_USER\Software\ex_data\data |
| Operation: | write | Name: | ext |
Value: 2E0070006E006700760069006400610068000000 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | public |
Value: 0602000000A40000525341310008000001000100F37F990AB7D0E27D23EDD837690884F69D81D56300D2B59B11881ECD7CDD5029C277FD7486A9B28E67C6E58E2824DADDF2251E8038DF43018D241D5B7923C33E6EE6BF2B7C474EBA8323E0208AFBAC47D10494E8CC4B755E7F701484491644433D3F781B8749F2D2698A7BCFC2B20570327381DA6E0439DFE30F04994386BD79D56696FC75EF6F96FE3DFC8C5ECFC818D73DA6C58D0E775FCE8B6DA9CA2AD3339A1E1F4BDAF573722DEDD6AA60CD2A53ED33050B551544EFC79E6802BE06B702D34FE89ECC26EF0E462CF1FC19572C34E01116B6004879F7EE530217F367299EFE1CE13BC6AF97DFD05C17CBE5ECF7335845AA59D30B181EDF69EDA63E2F55B0 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_CURRENT_USER\Software\keys_data\data |
| Operation: | write | Name: | private |
Value: 94040000B8ADF8453866C068AF1E910307DBDBAA4089732999DFA59DDC63E7E6ACCACC7F30EEB4A4A8D11BADE4C1226043FFEAC4C63728FB8AD89BBE8164EE5F0C62B6E6646B7E63E8E4205C0FBF0E8E25D1D30A999356B89B8724BC680D2F0CBB18C83C572E90AB512C3BB49B21BC0718C6FE5A1F32D03C22B528AB4A135D6EA309F0EE49BA29BAFEDA9D37A353E6A2A3F7272DB36B190F2100507F2EEEB39FC62C68A6F685C67DE4021B4E2C0B3157177B72F83D6DBB2204792D5B9469C95120EEE7F1F22C2E841D976D6C0C524D6B950434BA2D40927C99B37B27D1834A356B09BA57CB3D367D9E9FCC56B802C5A615E28CF948D655345059EEC0A6F1062E79CBFA78AD7490417CD5120166182200C421498704A0D8B5A882452088962CF70B2A144DFB3827F43EFABEBEA75171969F70E3F4DCAFFFFE80397AE812338D024F01A12E94E5BBCC3087416CA03ACF94C0B46906E52C89836F90AC3AA62D8060CAFB7B16AF8E818668B915C1275611AF588E4E64DF78D4DD41811CCC40AE59C6A45BA4E9A382BD65458F76AAB7D19D23501ADD6233A83E0F4F90E67E46A2F45F69767D54EAA2EB8841D414F35ACE1F44F9AB4F7AE7D4C313F74C0A759B86DDB6A2D6807C6206BF4865FE25CFFA012CF65FE80E42B1A4B158DFB8A54D4FFB32E540D86171580F26E1C0426B9A0C1E2BAFEB38B205873993980214B2FD99118505786EE20FCD8C61ACA92212A061F5A86B74D4B2E9A40740E124E88D5CD60ABE26E9F21B6D203593C543C909EC5BE1DAFFED62C448F0556ECEA571B17F0A36C3A758ED171B5D5B67E780BE5E694BAA55132F53FA11D04FBE06E1A91830CA2D0AB3CF9ED0FA03B58667DBA39E116067C5EA94DE51AC774B9DD8448CBACC70EC33D0C62CD196B951C2284B5DAEB9E2759337A0E43D83EC696E79B8AFDCA12D51AB899706DDFE9D8FB49477F07C332B75AD313FFE386939628D68D7622603144BE671B47372C7E39325B8A32950EECCAD103E4AB634CB2DA93C17A2BA0150DF3E644BC51D380414408D43E84C0CFA5E9594D641AF7D7D00A9825D72705F70BC12724E67DBF95BB479B3E6B5640F65249B2365F8C376BDDF75B4A8BAAEDFB8FA5AD3297CBB2A772772F4CC0FE1DA20002B2ADF0FD7D4A7D9B55ECB0EB6A18B694AA5B2AB92C1FF409646CCD32CDF9F95D196E71E94949BF578FFB9A1EDEB30323ED892E10C0F06B788791F652678B8AF962A4605A4BBCB64BD1C485CF5C393560DB1D3BCDC1DD167991CAB6947A11A9E311E2A398B23E71CDFD12FA455CE97AAA75A7FDAAF20A6C09560F5A6830105B615EB197603831696EA158CC7A535F93BEE6319ECEDB045552265E943D09B9BB8F02873C8F36B4673B585F7F1D1061C596BEB8DF5BDDF066A7A113279C0211800A54084BF049FB0C279C406B75DFCB5343F9A7E5D3D9DC16255085E87BC764BED51A2FA2182F0D6D532E35F08E09C2ADE2425DC82A776AD6FF17442E4B33DA9E0BAF6A8A2AA2E523BBDD7F29BDDB1D4B608DCAD544AA7396829D17E09442FF3D63CDA9A86CE4C65378F22B44E362A826826F14EAFDCF58BD3556A08B7B4D3E593ED7DC487FA2A757098862FFFAEC9C3412A4A5200859C4C7D01D4FBE11E47AA3D4C143DCCD218F40E7124CDF8F9E84EBFB5536C766CFE657D818CFC2A8ECAF837AE4B87ECB25E4B3381ACEB9450116B1871E7F26442ED1E3E3A7DC69EF2089E160B5AF624F748FACD16C0EED3983B32BCF7C52CAD1A0B7DED1F8A8A0CB0AD1E6D65F22EB3E88CBB934AC2DEB5AEDF2CCD1897FE169299C7F9E492EC0426EA04FBBFAF17D9CA1C2209F80D598508F7076433F5768A798D438EBFB429ACC43AD8983C051B6202A9AC79B61B531F2BE2F401589F7A50A42910676EB03259C2D77853CB81A11646834D736502F44AEBB2E3C88930690FE71599755FC0164680E5A2D55E6D9C2B37DEC93D08973519484544ABAF8EF8A484E80D34F7F29FDEF87B8C5A20532D42F6BD8FA01EDCCCCD04A37D8B05CDD21BFD4FABF0AFE7D10CEDAF71C36ECC6FBC50A6B79172A29EDCC346F01DE71C0527789EF62D19F5C188C7D88B64F62FEEB0E0CDD78E447297C960A4FD3ACCEDF515937C547FADD479BFF56EE36666AB4C9E05F53E8F249C3EB8664A25F6E5867BCF5CA904C972D22C9E62DCE528C4C9D16929865E13D4BB3C0354E2A98D75619CA10E0C34D5EB46F2069070B2D8A09919F4394E3544DEB0F70FEEEC375392A55A2C9D4B93400ED9F3E31103F81195A0D46FE9E3C283384223B93D18E89DB75F1D1C47CB6229810EC4758D57403795DCA47000ADEB8AA0E49A11D2FBACD9FA6AC50A92C6015ABBF600B9FF79DDE0351D8E15B4577D164D1A92 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wermgr_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wermgr_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wermgr_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wermgr_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1552) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wermgr_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
0
Suspicious files
303
Text files
213
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1484 | Gandcrab5.0.3.exe | C:\Users\admin\AppData\Local\Temp\Liebert.bmp | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobSettings | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\addressbook.acrodata | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\0FDED5CEB68C302B1CDB2BDDD9D0000E76539CB0.crl | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\Security\CRLCache\CE338828149963DCEA4CD26BB86F0363B4CA0BA5.crl | — | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\PNGVIDAH-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\.oracle_jre_usage\PNGVIDAH-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 1552 | wermgr.exe | C:\Users\admin\PNGVIDAH-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
77
DNS requests
37
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1552 | wermgr.exe | GET | 301 | 62.210.218.151:80 | http://www.arbezie.com/news/assets/rudaimkaka.bmp | FR | html | 178 b | suspicious |
1552 | wermgr.exe | GET | 200 | 8.248.129.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
1552 | wermgr.exe | GET | 200 | 8.248.129.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1552 | wermgr.exe | 18.207.88.16:443 | www.hardrockhoteldavos.com | — | US | malicious |
1552 | wermgr.exe | 83.166.138.7:443 | www.whitepod.com | Infomaniak Network SA | CH | malicious |
1552 | wermgr.exe | 195.201.72.6:443 | www.2mmotorsport.biz | Awanti Ltd. | RU | malicious |
— | — | 195.201.72.6:443 | www.2mmotorsport.biz | Awanti Ltd. | RU | malicious |
1552 | wermgr.exe | 217.26.53.161:443 | www.haargenau.biz | Hostpoint AG | CH | malicious |
1552 | wermgr.exe | 74.220.199.8:443 | www.bizziniinfissi.com | Unified Layer | US | malicious |
1552 | wermgr.exe | 8.248.129.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
1552 | wermgr.exe | 94.126.20.68:443 | www.holzbock.biz | METANET AG | CH | suspicious |
1552 | wermgr.exe | 136.243.162.140:443 | www.seitensprungzimmer24.com | Hetzner Online GmbH | DE | suspicious |
1552 | wermgr.exe | 62.210.218.151:80 | www.arbezie.com | Online S.a.s. | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.2mmotorsport.biz |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.download.windowsupdate.com |
| whitelisted |
www.holzbock.biz |
| unknown |
www.schreiner-freiamt.ch |
| suspicious |
www.fliptray.biz |
| malicious |
www.pizcam.com |
| unknown |
www.swisswellness.com |
| whitelisted |
www.hotelweisshorn.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1552 | wermgr.exe | Potential Corporate Privacy Violation | ET POLICY Self Signed SSL Certificate (SomeOrganizationalUnit) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1552 | wermgr.exe | Generic Protocol Command Decode | SURICATA Applayer Mismatch protocol both directions |
1552 | wermgr.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |
1552 | wermgr.exe | Misc activity | ET POLICY Signed TLS Certificate with md5WithRSAEncryption |