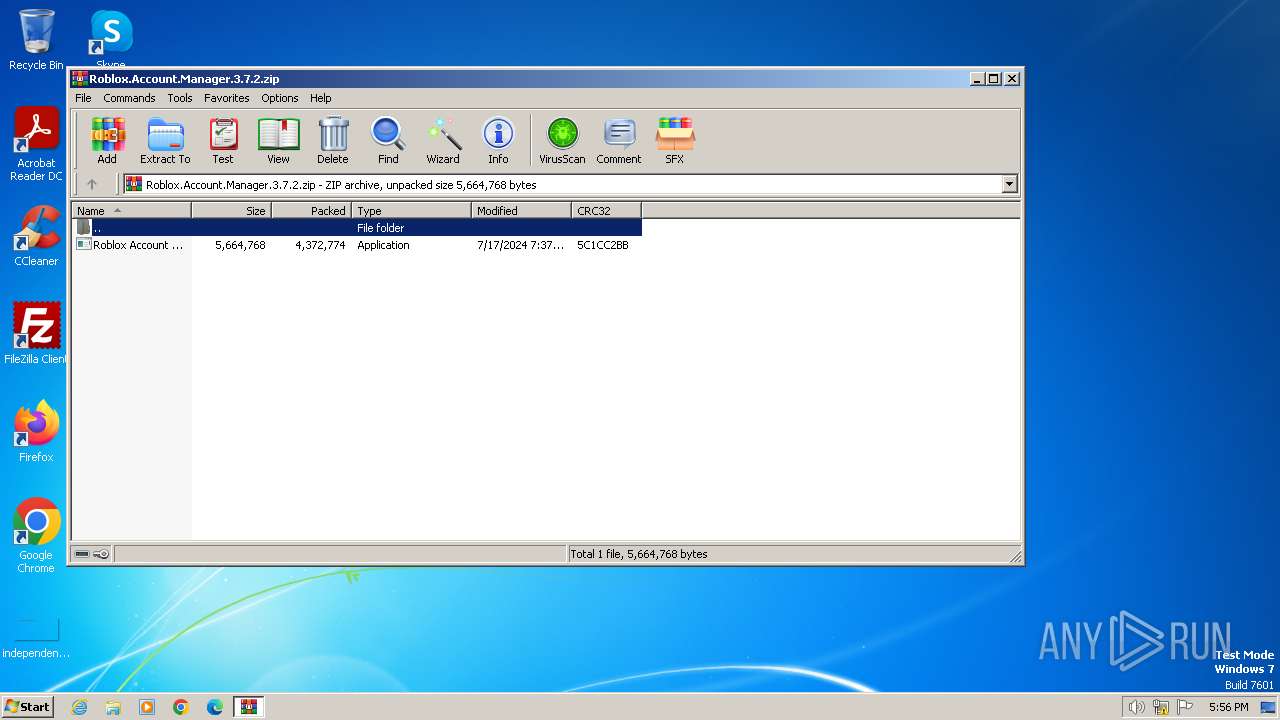
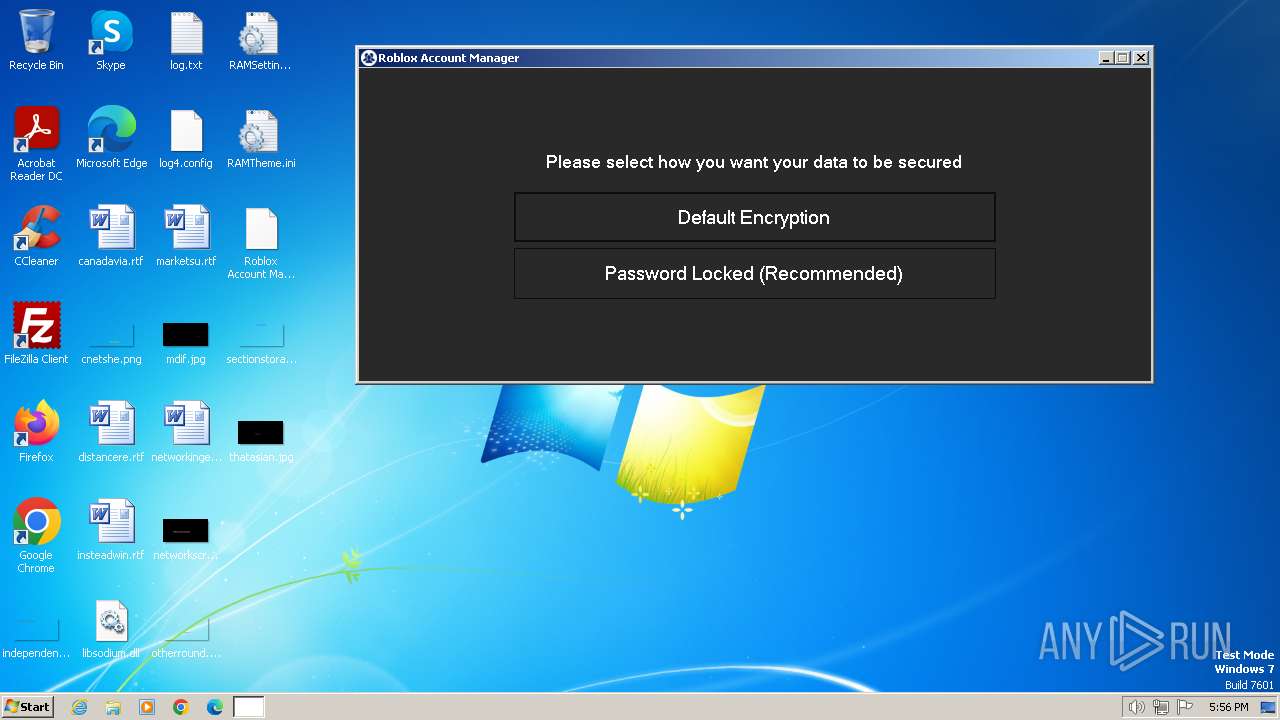
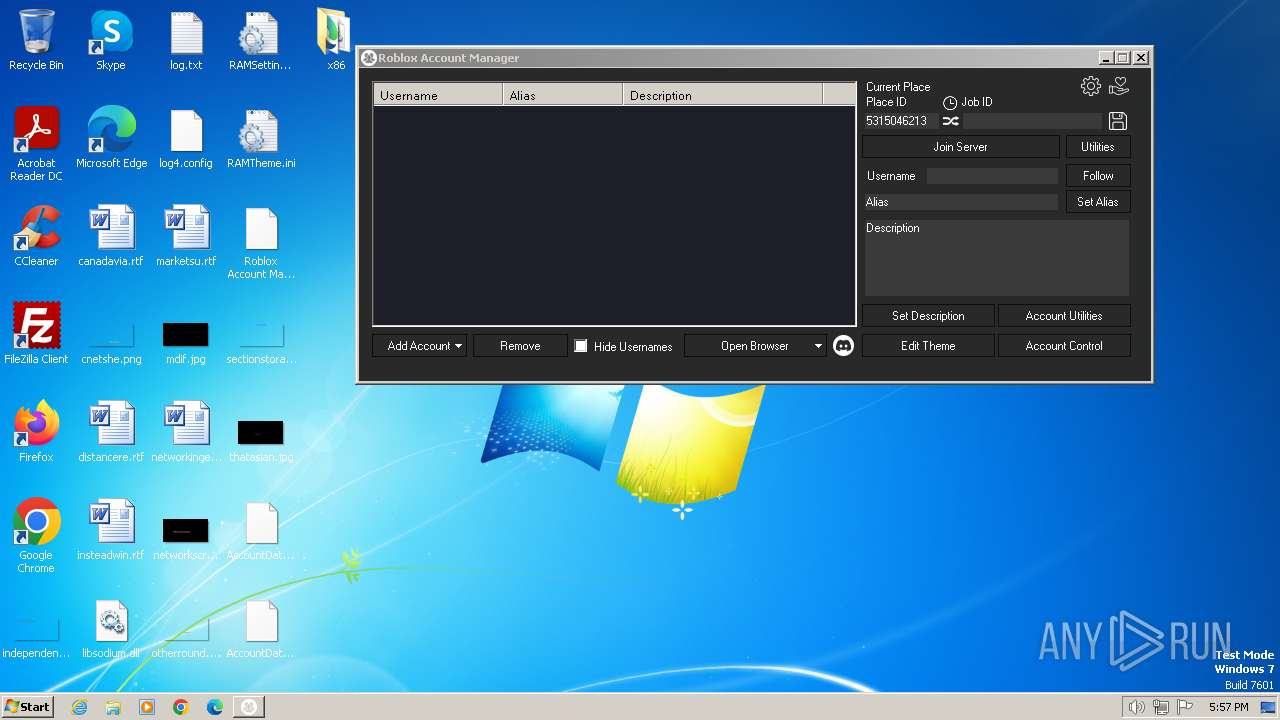
| File name: | Roblox.Account.Manager.3.7.2.zip |
| Full analysis: | https://app.any.run/tasks/8647c514-b688-48b5-84bb-efaa6d8c36e1 |
| Verdict: | Malicious activity |
| Analysis date: | November 18, 2024, 17:56:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D58B79CB3D3635BA963427362F75D075 |
| SHA1: | 0E33EEFF9B625FCEB2D2D0195E6F32523D57DB79 |
| SHA256: | 49B2C015DA0851A2ED43820799A7BCDA08E1BC5F315E107598F87F4B1BD36DAC |
| SSDEEP: | 98304:lEQBRQV3BdUKmD4I3UV5AaONlAUntE4vA0j1Yfyb/plXAWyz7N9j/SfH1e7zWIQ7:XcGtpl |
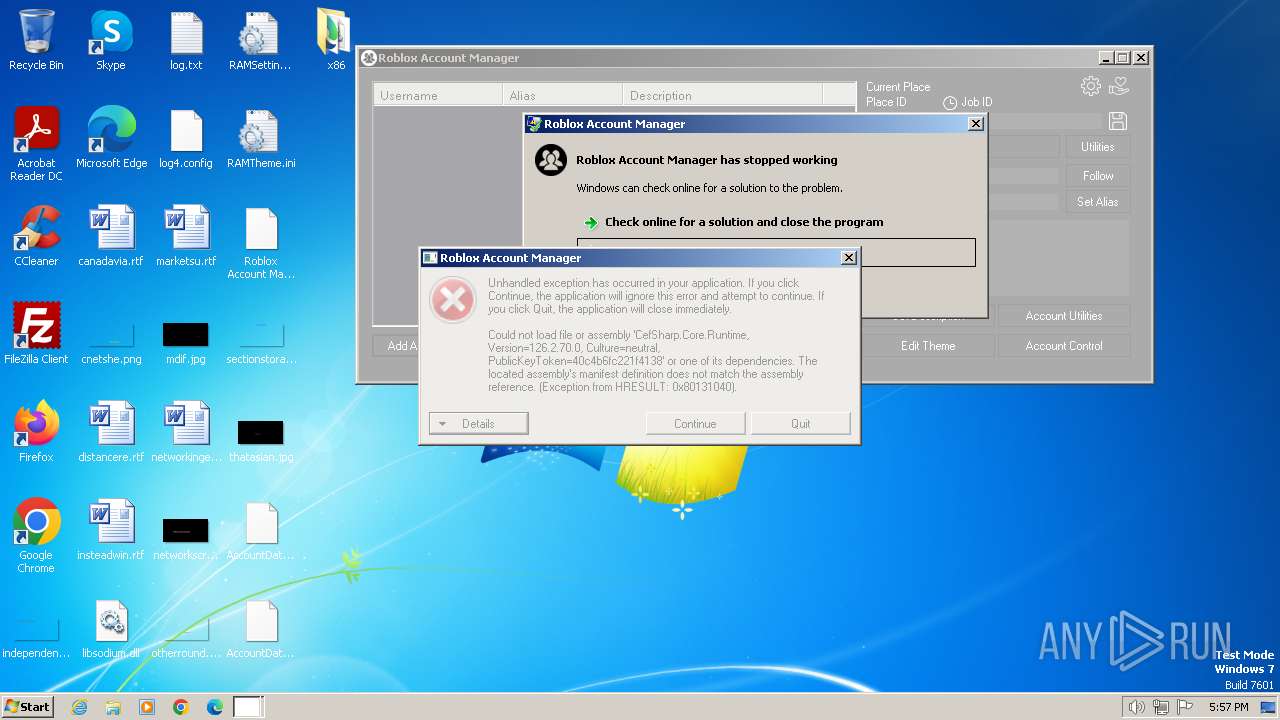
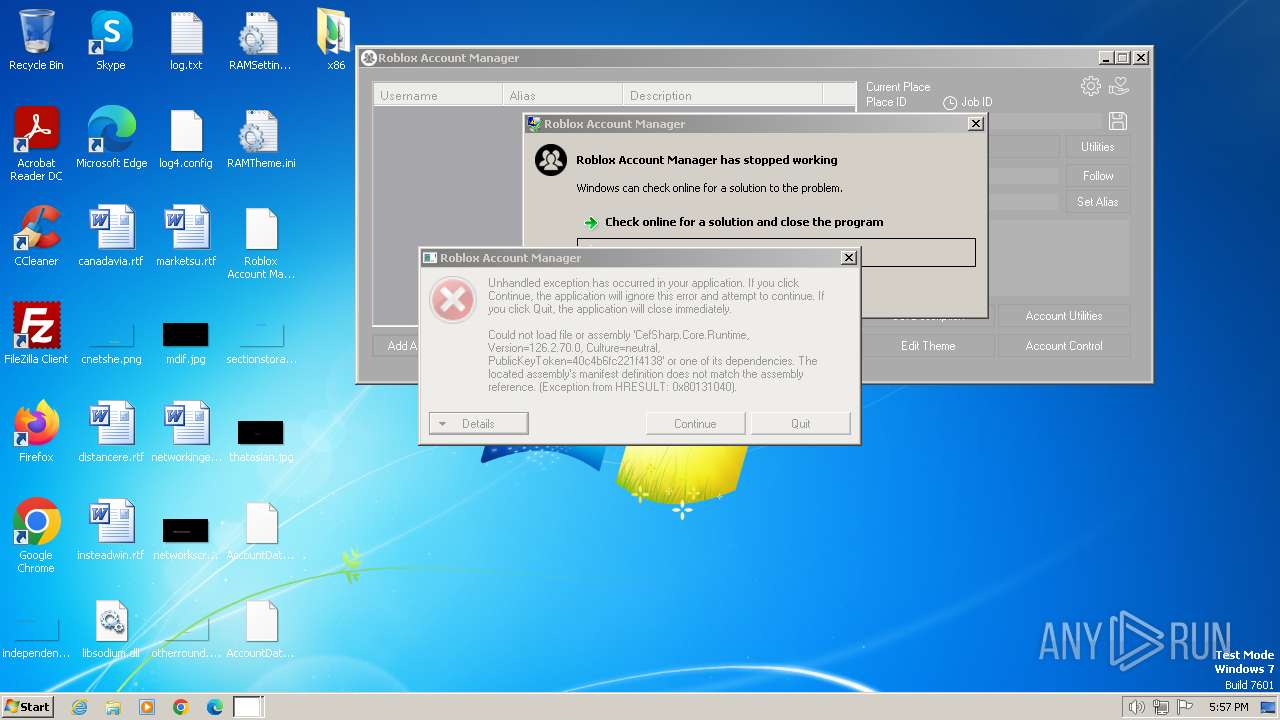
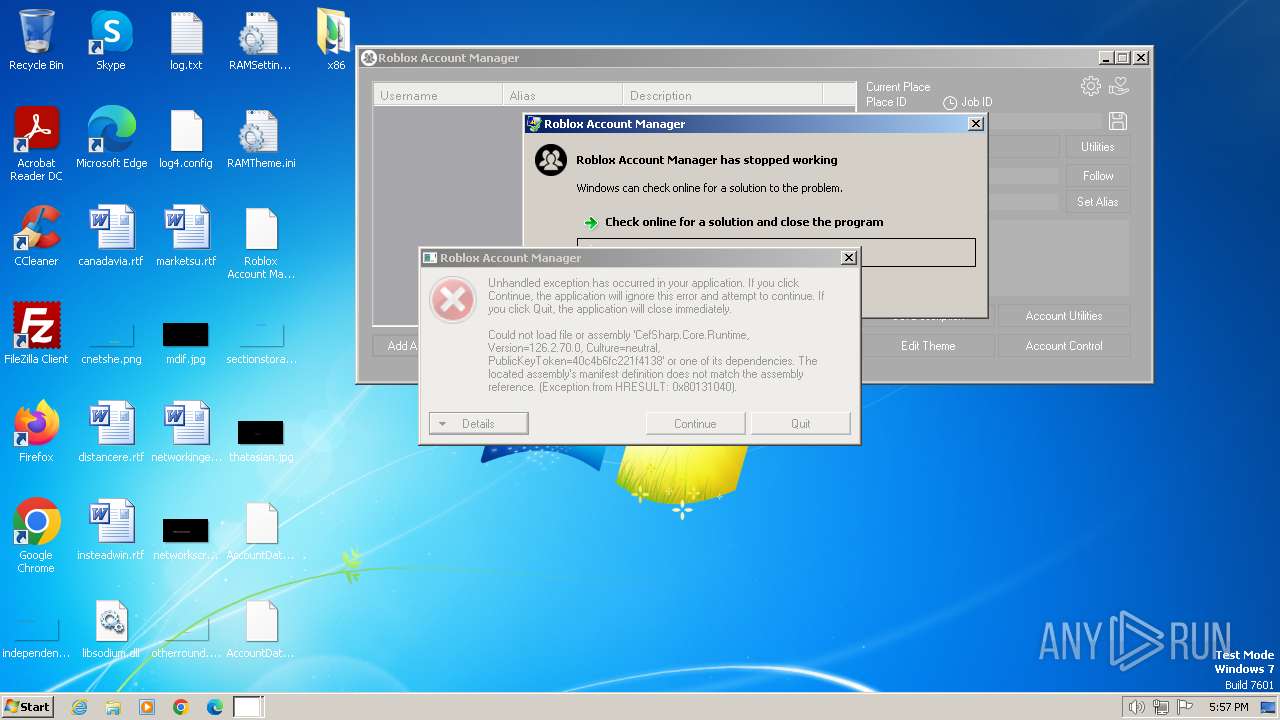
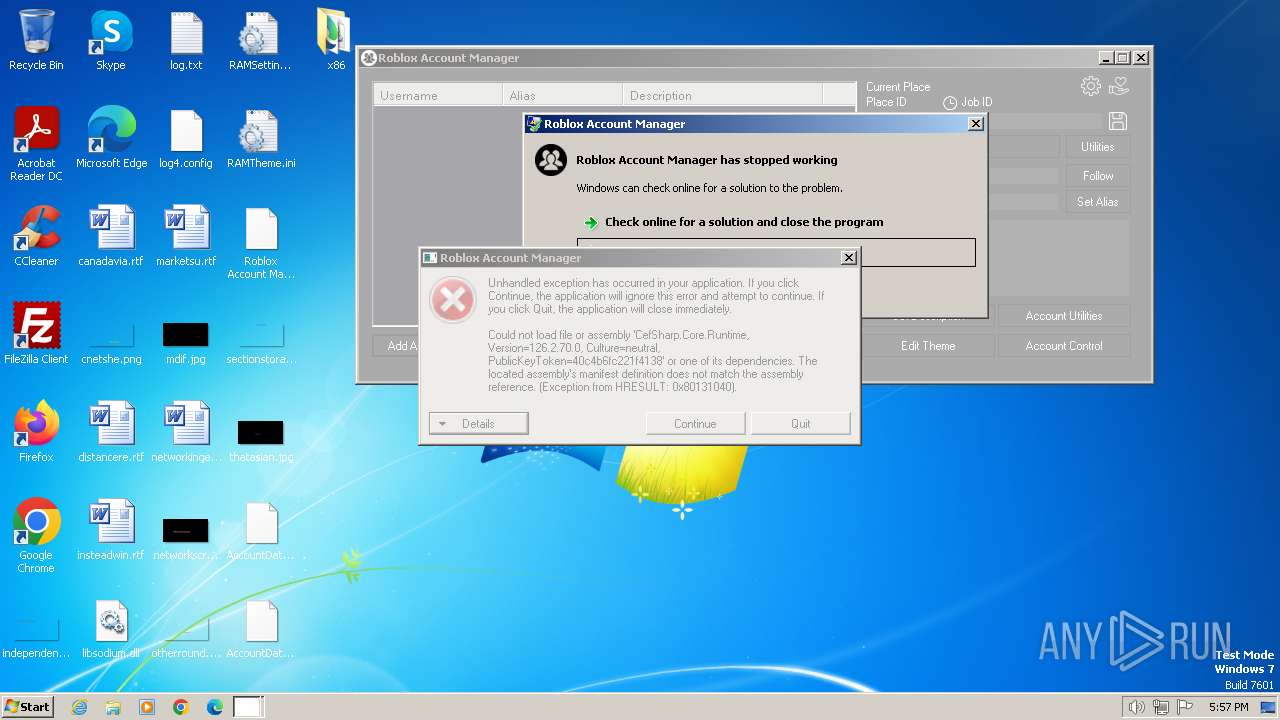
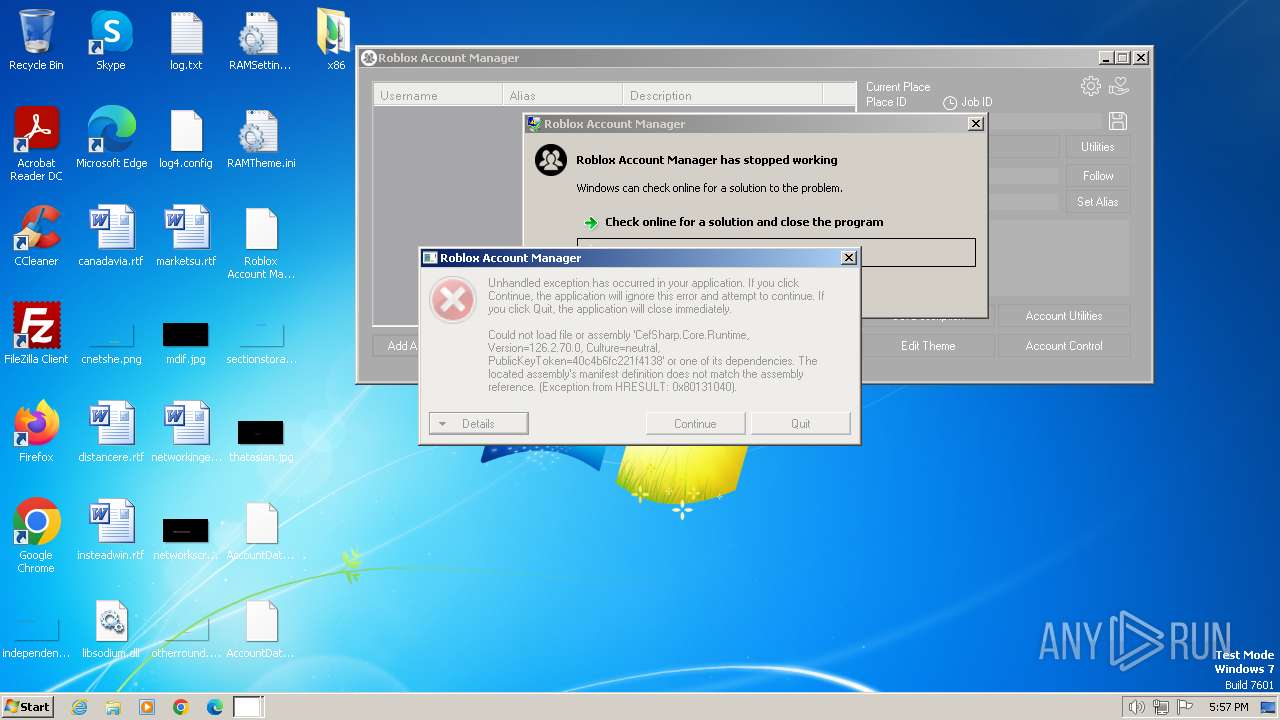
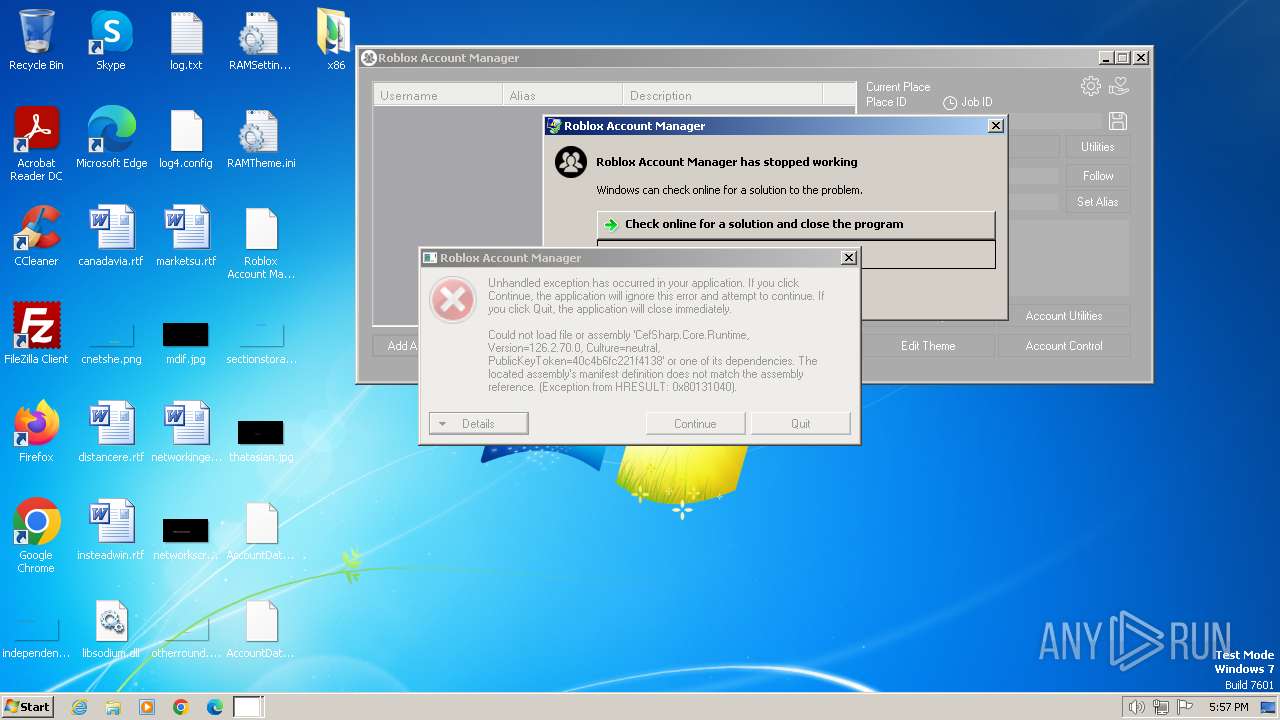
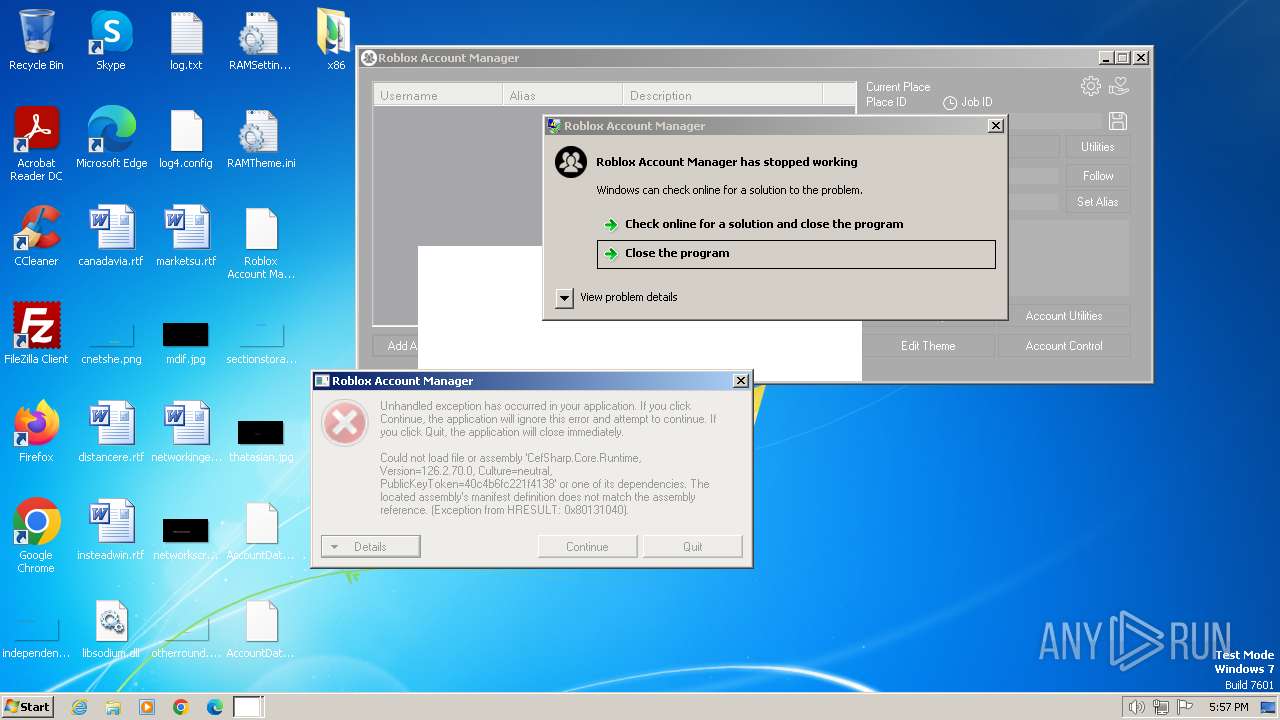
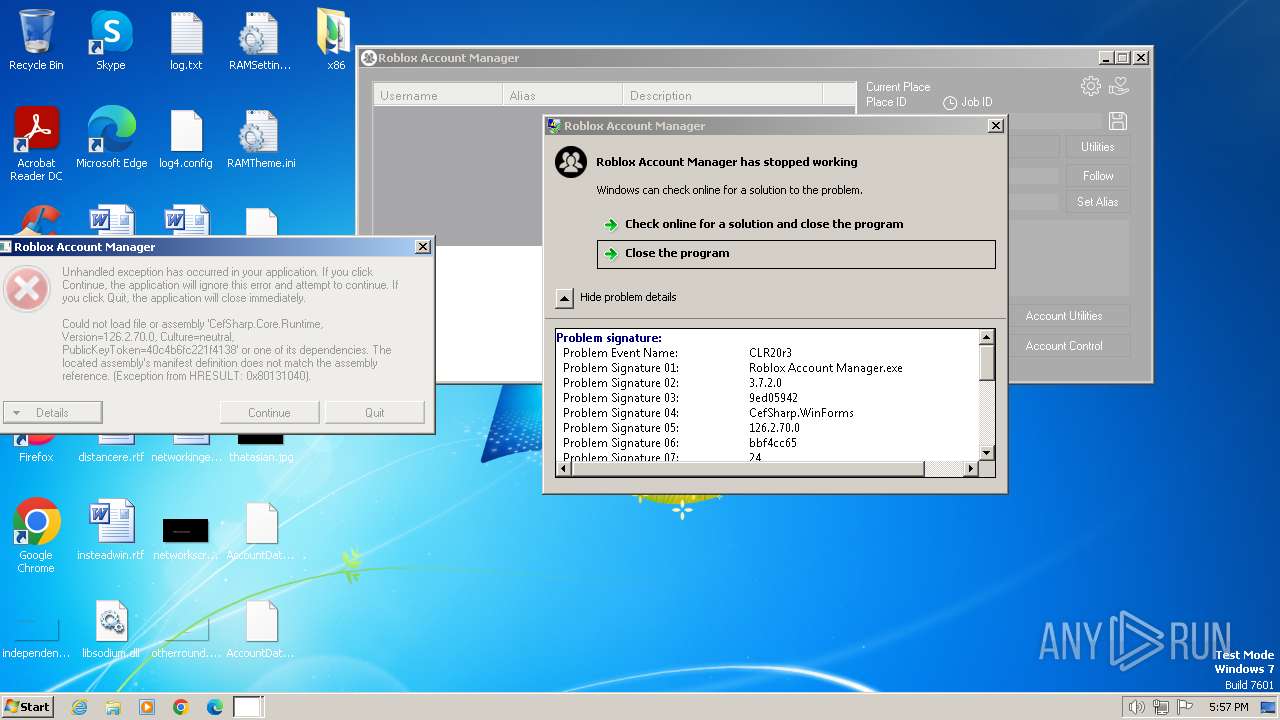
MALICIOUS
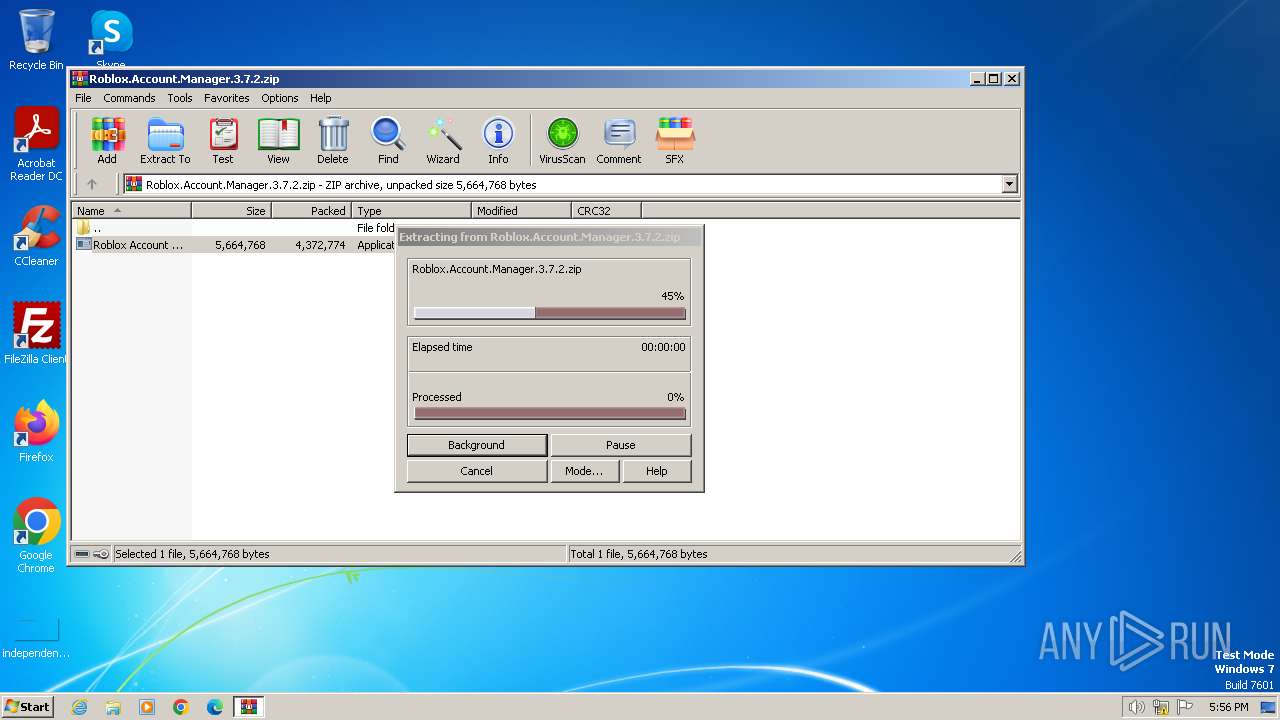
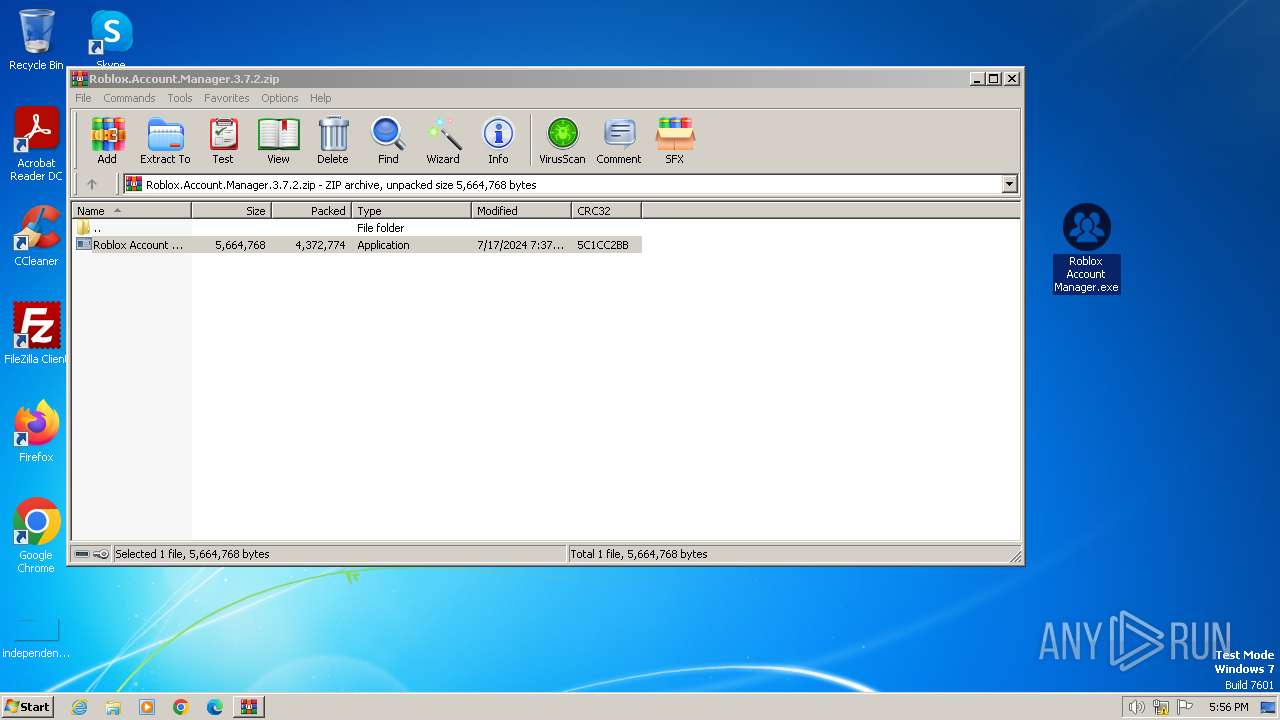
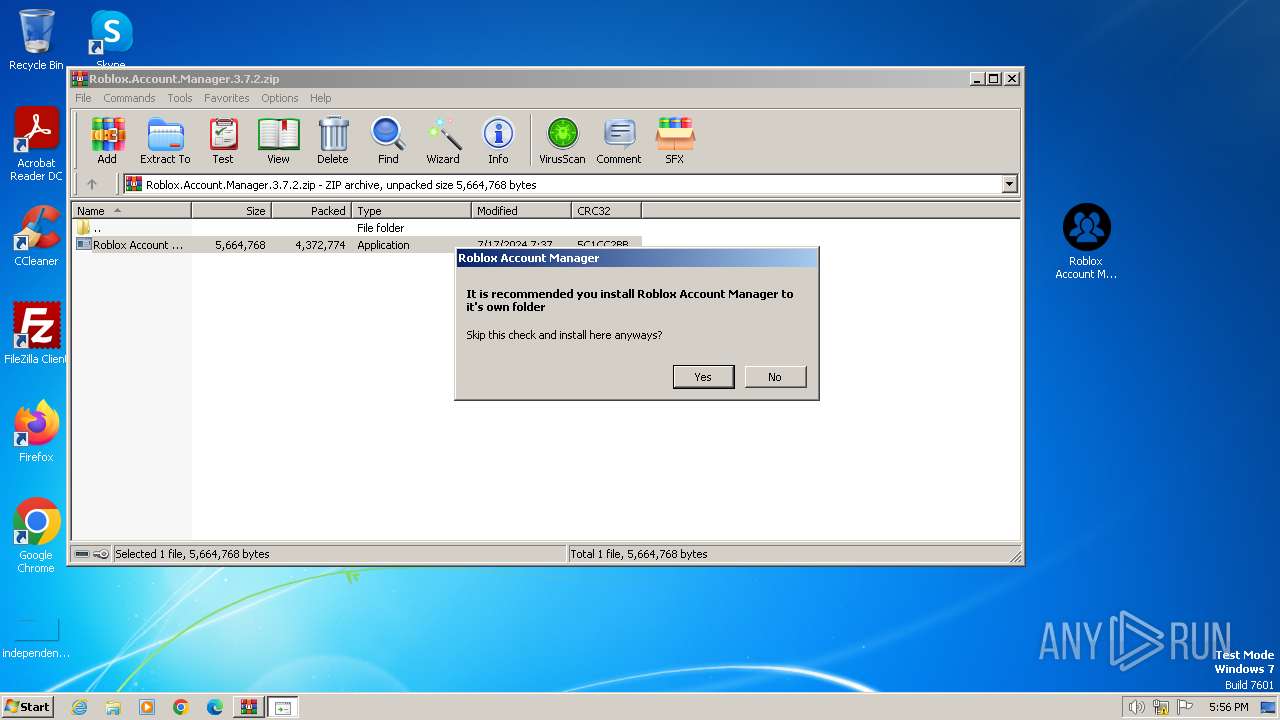
Generic archive extractor
- WinRAR.exe (PID: 1652)
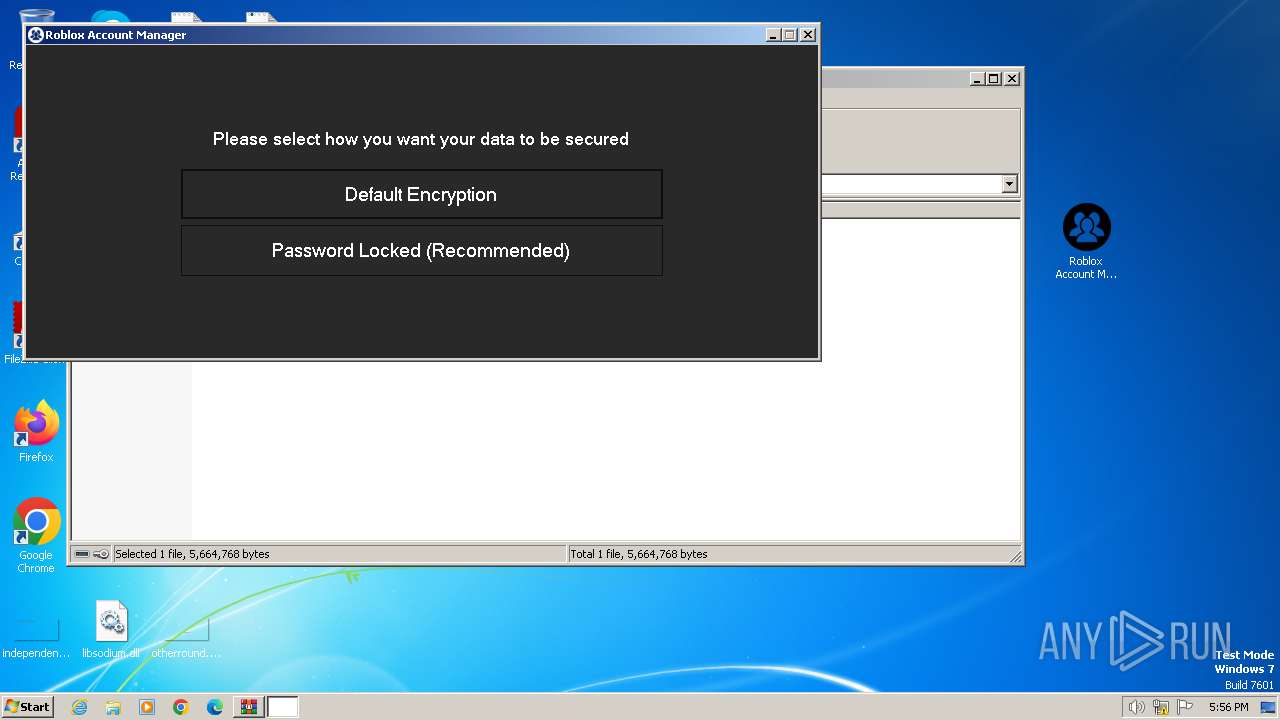
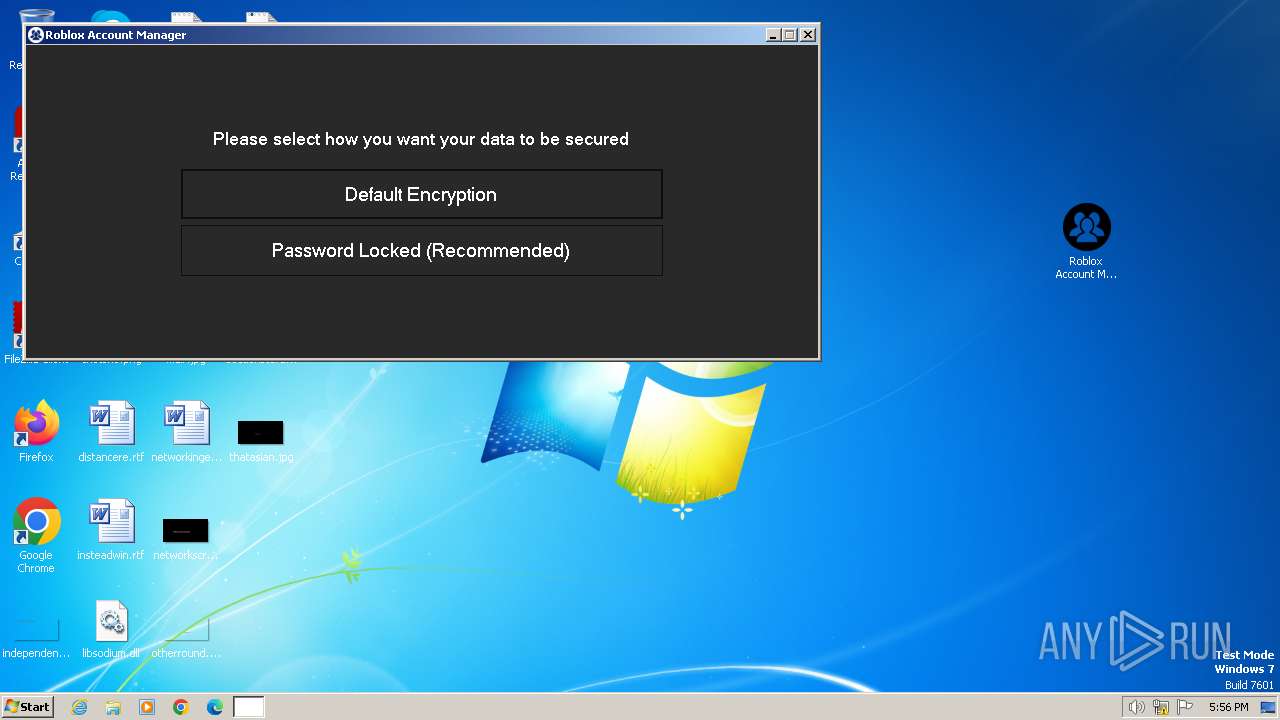
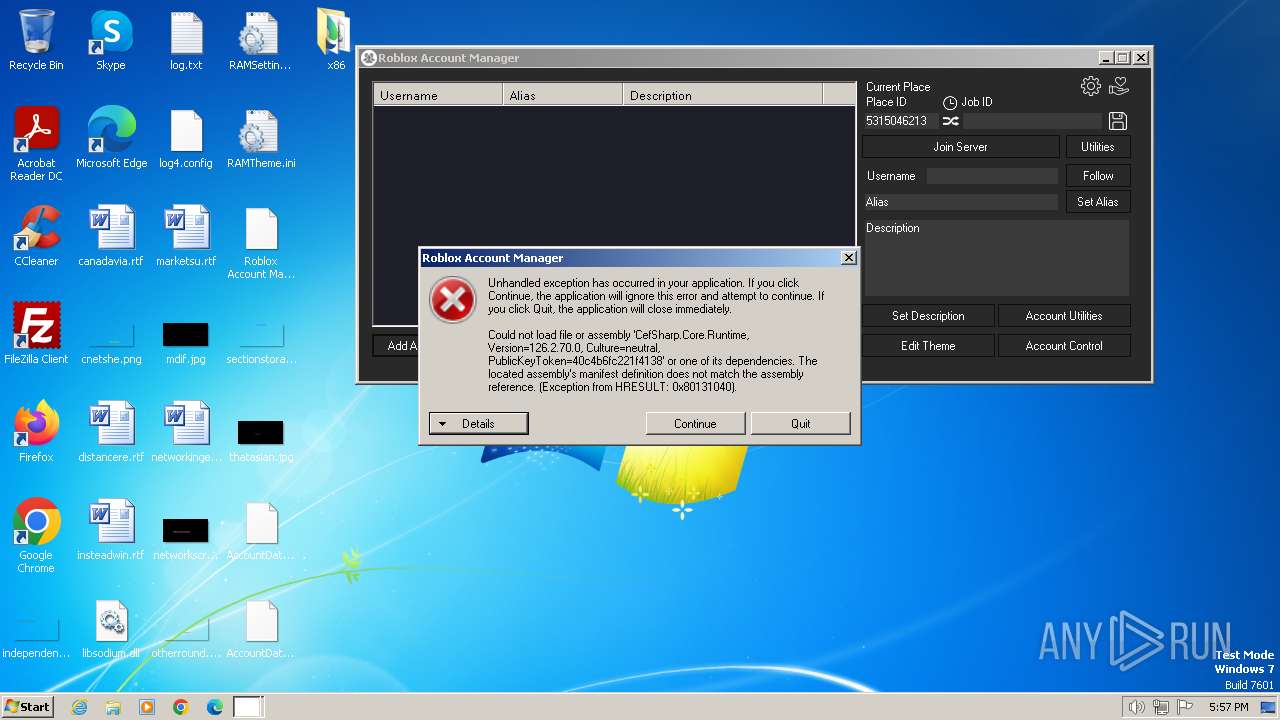
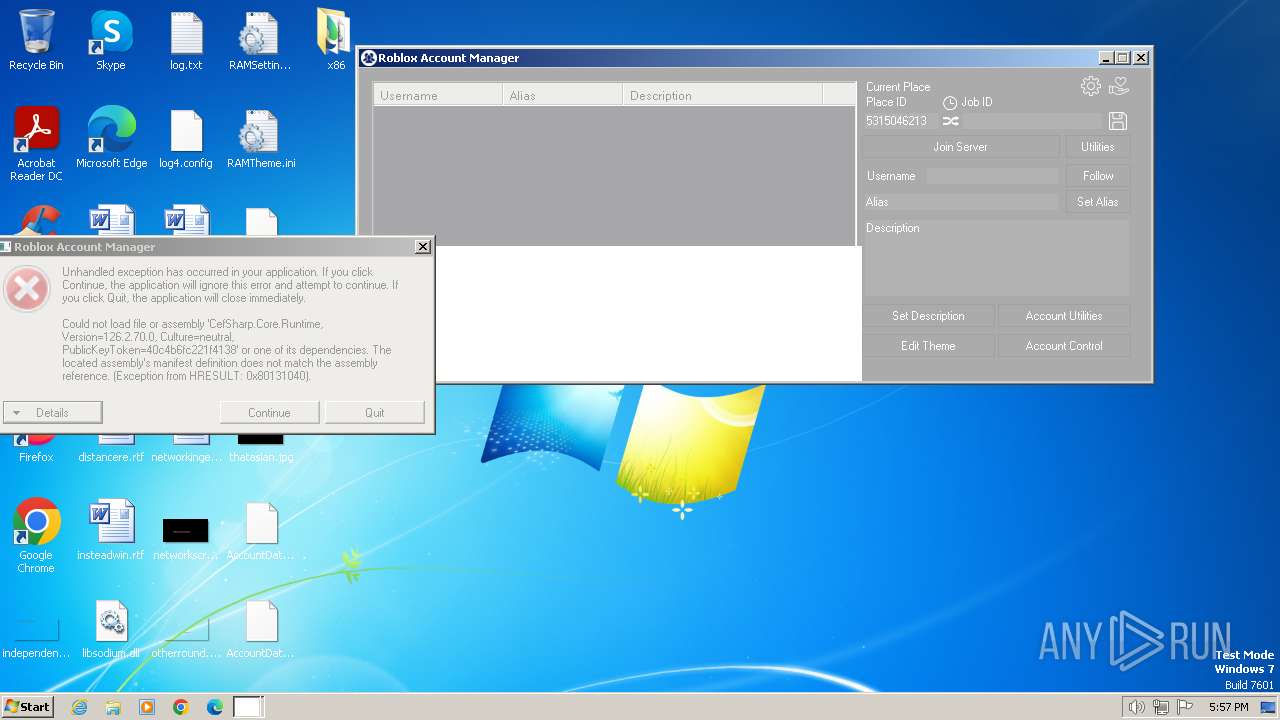
SUSPICIOUS
Application launched itself
- Roblox Account Manager.exe (PID: 1876)
Reads the Internet Settings
- Roblox Account Manager.exe (PID: 1876)
- Roblox Account Manager.exe (PID: 2220)
Reads security settings of Internet Explorer
- Roblox Account Manager.exe (PID: 1876)
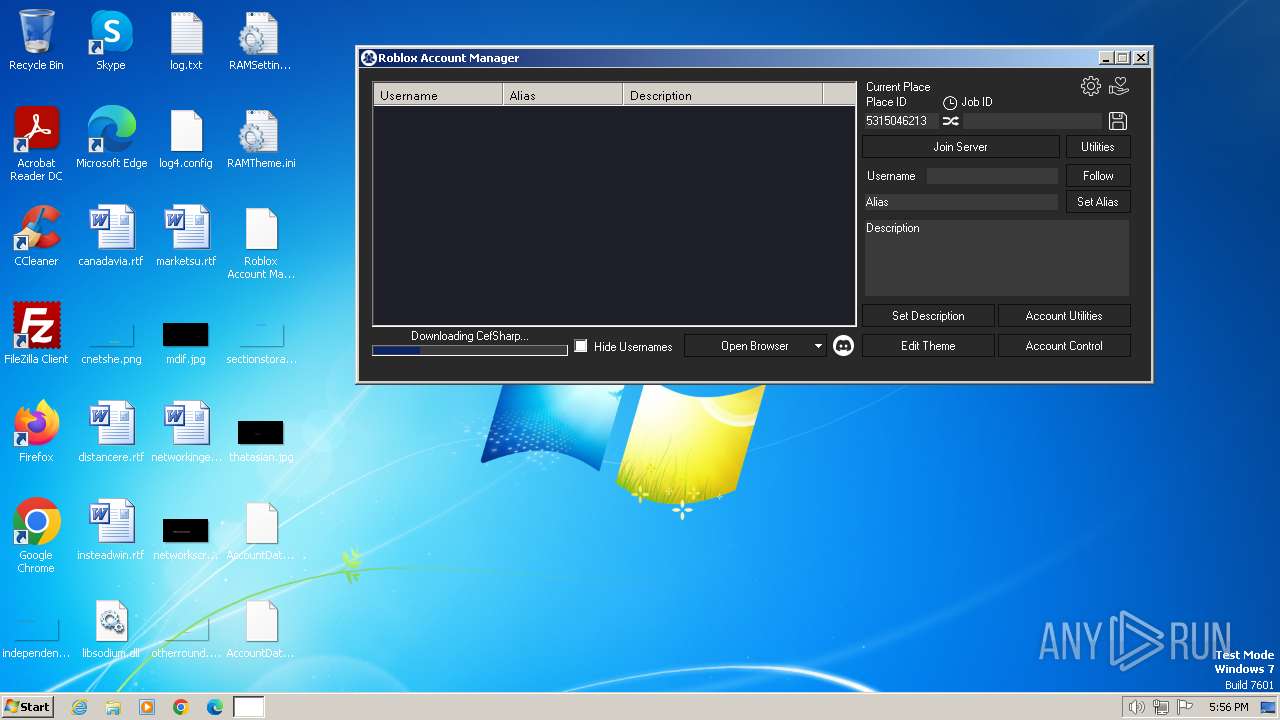
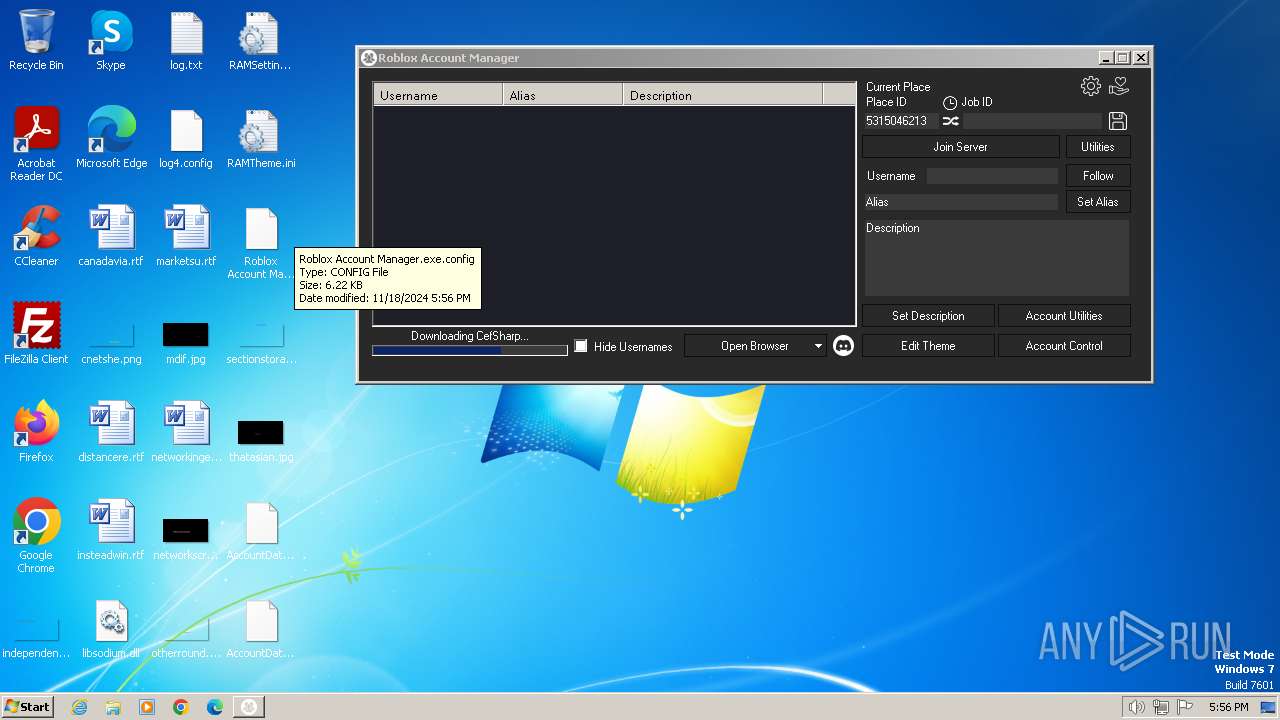
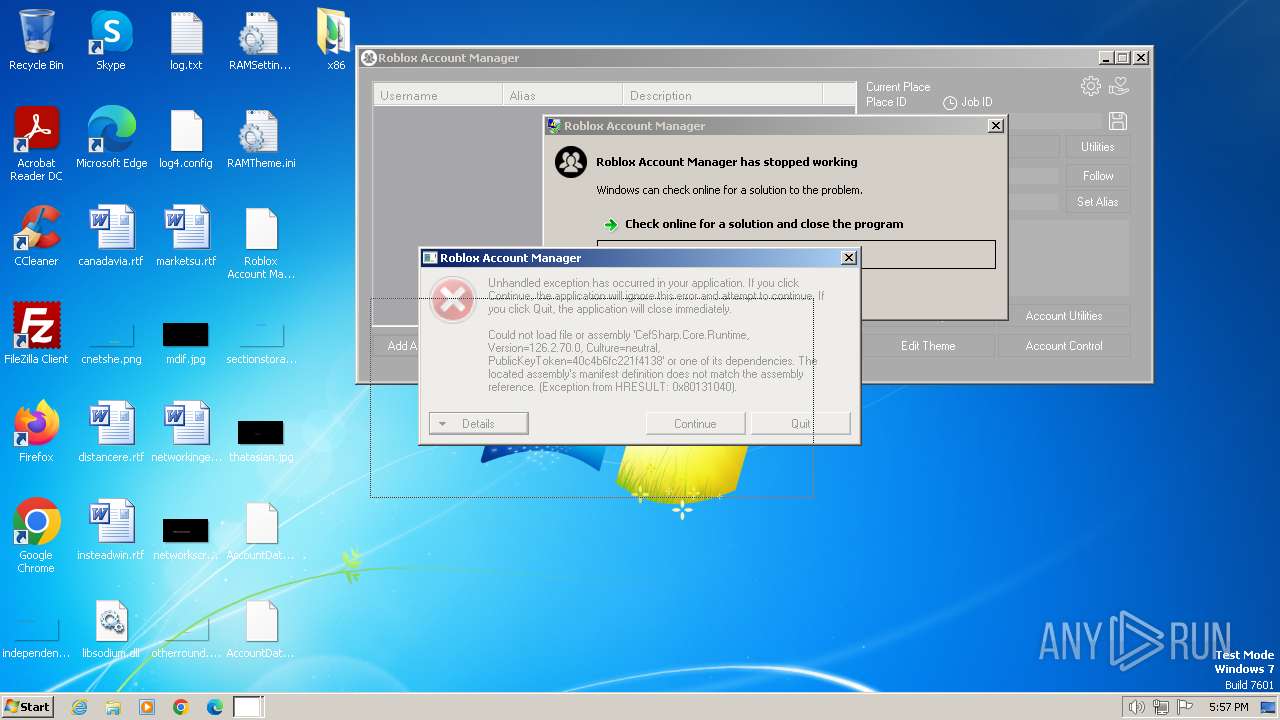
Executable content was dropped or overwritten
- Roblox Account Manager.exe (PID: 2220)
Reads settings of System Certificates
- Roblox Account Manager.exe (PID: 2220)
Process drops legitimate windows executable
- Roblox Account Manager.exe (PID: 2220)
INFO
The process uses the downloaded file
- WinRAR.exe (PID: 1652)
- Roblox Account Manager.exe (PID: 1876)
Creates files in the program directory
- Roblox Account Manager.exe (PID: 1876)
- Roblox Account Manager.exe (PID: 2220)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1652)
Checks supported languages
- Roblox Account Manager.exe (PID: 1876)
- Roblox Account Manager.exe (PID: 2220)
Reads the computer name
- Roblox Account Manager.exe (PID: 1876)
- Roblox Account Manager.exe (PID: 2220)
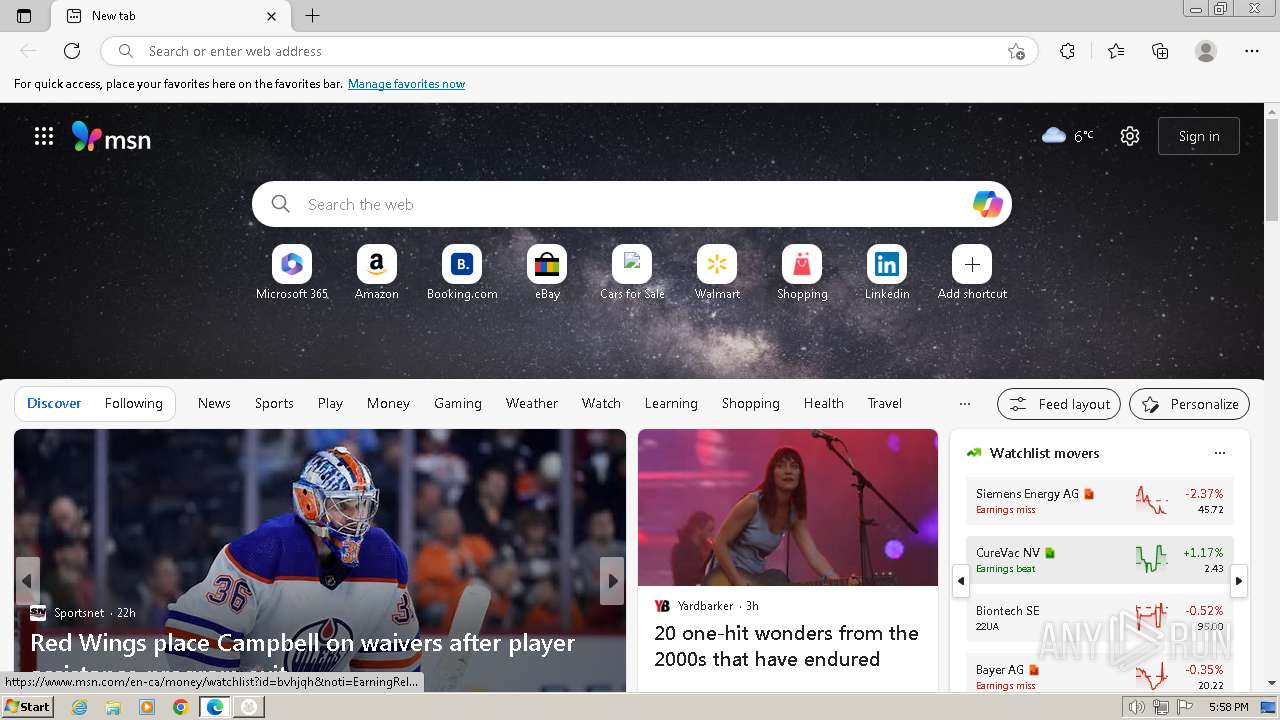
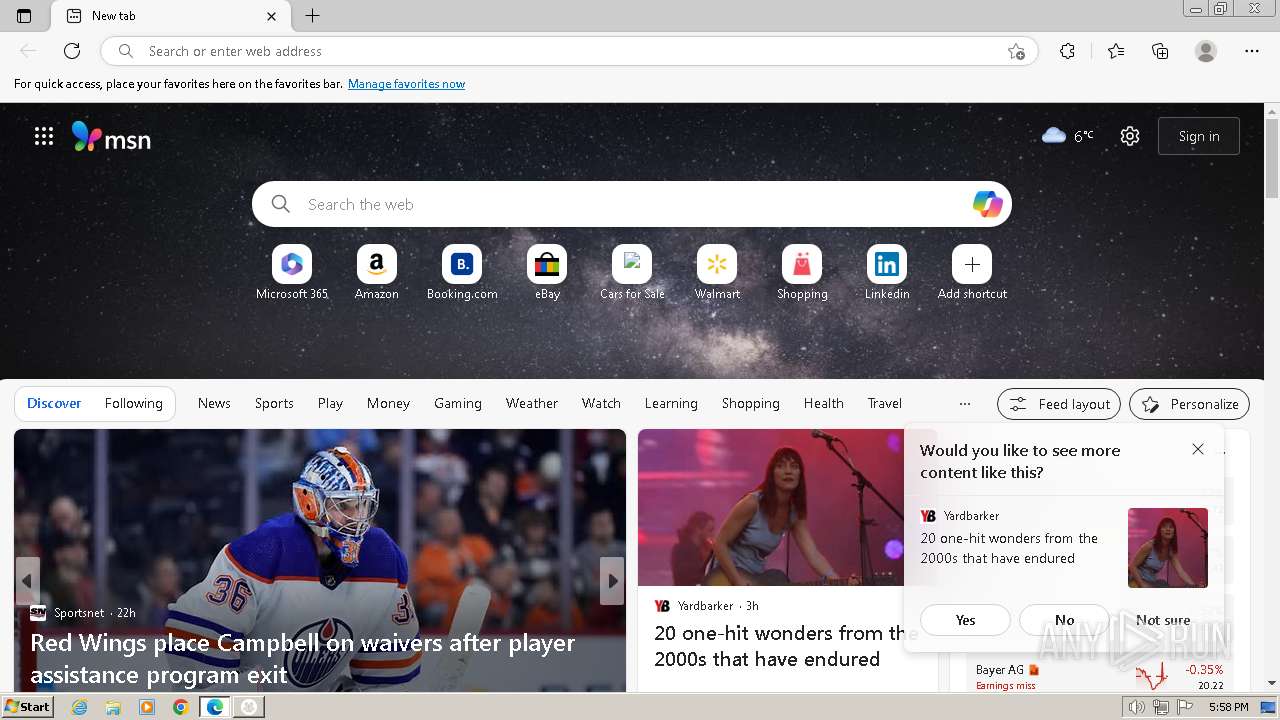
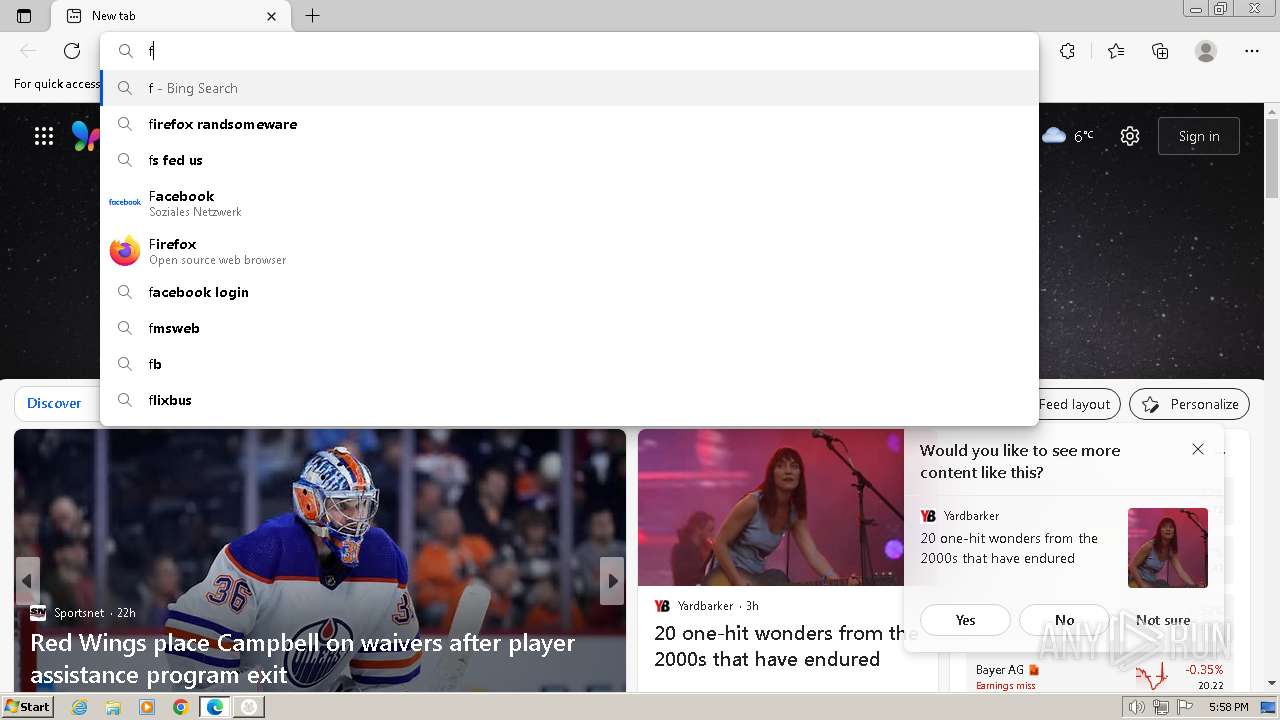
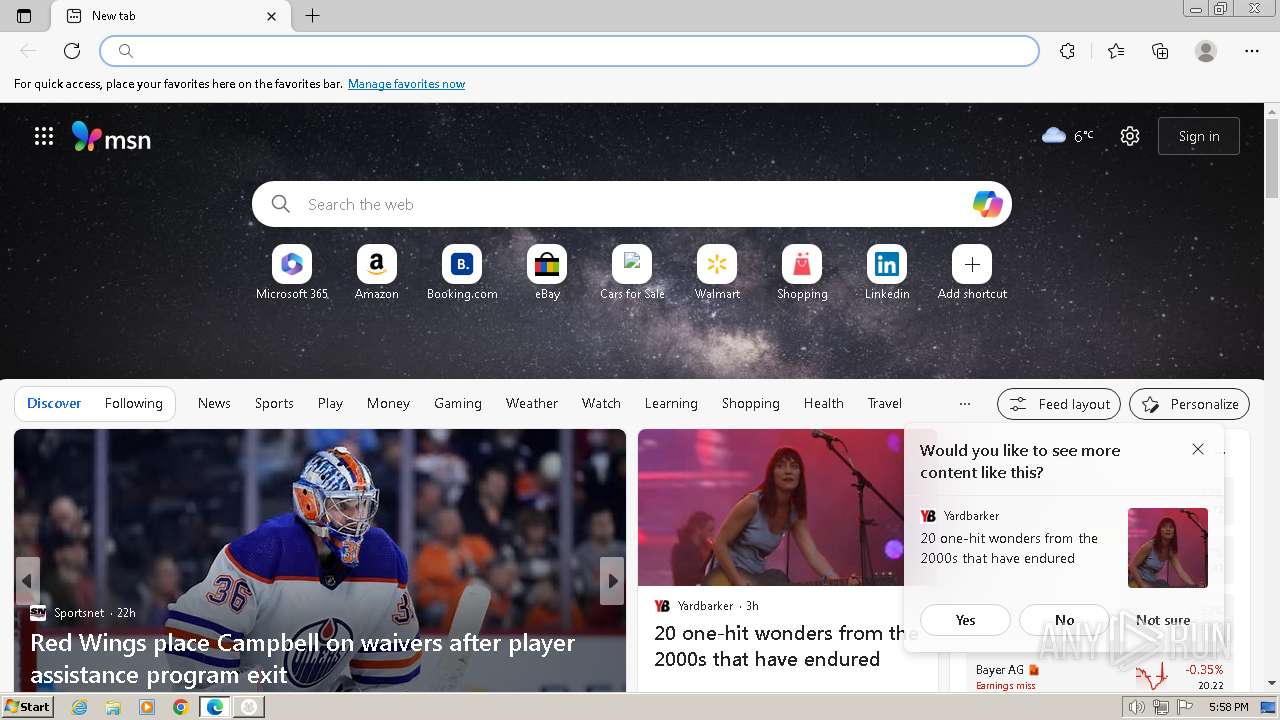
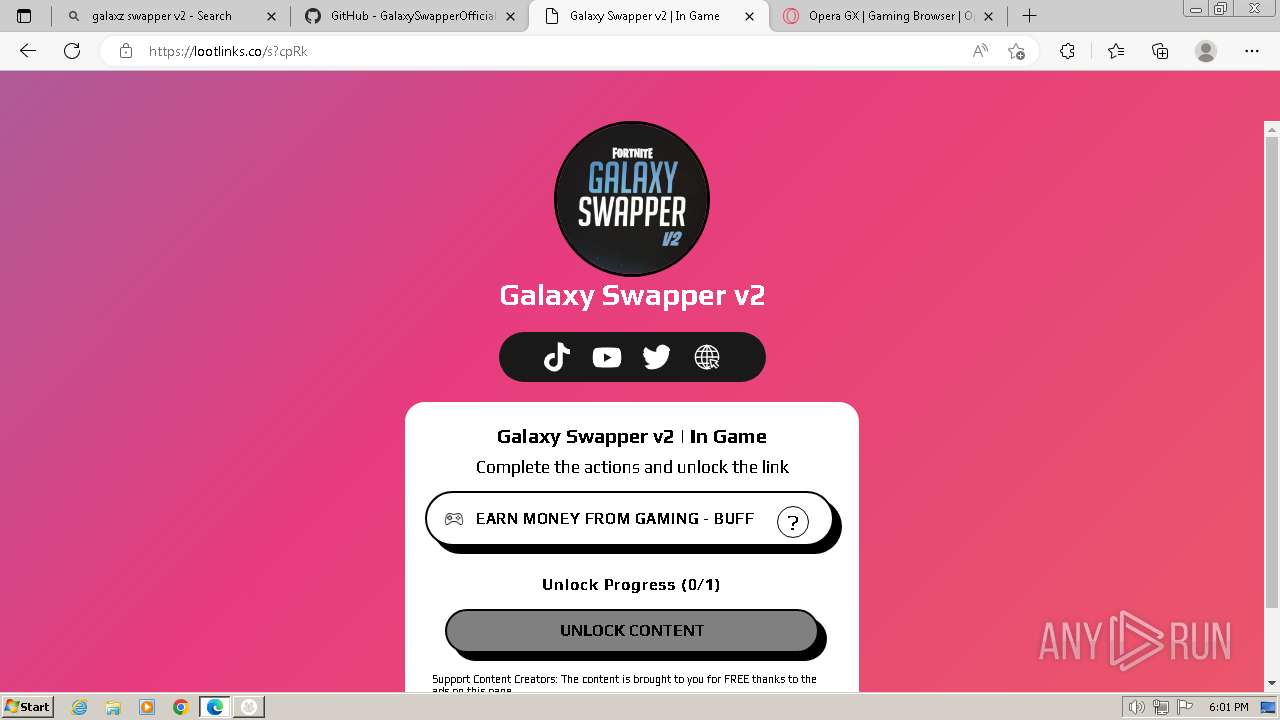
Manual execution by a user
- Roblox Account Manager.exe (PID: 1876)
- chrome.exe (PID: 3504)
- msedge.exe (PID: 1132)
- Roblox Account Manager.exe (PID: 3792)
- wmpnscfg.exe (PID: 2724)
Reads the machine GUID from the registry
- Roblox Account Manager.exe (PID: 1876)
- Roblox Account Manager.exe (PID: 2220)
Reads Environment values
- Roblox Account Manager.exe (PID: 2220)
Disables trace logs
- Roblox Account Manager.exe (PID: 2220)
Application launched itself
- chrome.exe (PID: 3504)
- msedge.exe (PID: 1132)
Reads the software policy settings
- Roblox Account Manager.exe (PID: 2220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:07:17 19:37:00 |
| ZipCRC: | 0x5c1cc2bb |
| ZipCompressedSize: | 4372774 |
| ZipUncompressedSize: | 5664768 |
| ZipFileName: | Roblox Account Manager.exe |
Total processes
106
Monitored processes
63
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4056 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 648 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3556 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 656 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3616 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 724 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --mojo-platform-channel-handle=1532 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 840 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --mojo-platform-channel-handle=4932 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 1132 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1388 --field-trial-handle=1216,i,8666545231918563569,9050832739092860758,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1128 --field-trial-handle=1216,i,8666545231918563569,9050832739092860758,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --mojo-platform-channel-handle=4392 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 | |||||||||||||||
| 1420 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=44 --mojo-platform-channel-handle=4448 --field-trial-handle=1396,i,4739491070571016044,15986124529288927490,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 | |||||||||||||||
Total events
22 346
Read events
22 227
Write events
112
Delete events
7
Modification events
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Roblox.Account.Manager.3.7.2.zip | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
24
Suspicious files
939
Text files
155
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF235f7b.TMP | — | |
MD5:— | SHA256:— | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2220 | Roblox Account Manager.exe | C:\Users\admin\Desktop\RAMSettings.ini | ini | |
MD5:2770C51BDC8469129A258AC8C2DA4693 | SHA256:593050CBC8F30C794FD710328FAD3A51156B5648A43F2EC686A6F55F0177DABC | |||
| 1876 | Roblox Account Manager.exe | C:\Users\admin\Desktop\log4.config | xml | |
MD5:E4659AC08AF3582A23F38BF6C562F841 | SHA256:E4B10630D9EC2AF508DE31752FBBC6816C7426C40A3E57F0A085CE7F42C77BD5 | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF236094.TMP | text | |
MD5:98CC34E7F20FD8F55568DB9B3D3B507E | SHA256:8D3D74EC41FF0CCE1F26B23F66E5981B7F59C40AB0DBB468B3A3E5E63C80F3C7 | |||
| 2220 | Roblox Account Manager.exe | C:\Users\admin\Desktop\libsodium.dll | executable | |
MD5:4F6426E3626D5D46FB19C13043CB84DE | SHA256:7A960129F6D3F8D44B4C6BE27F587C29AA8BAFB9C4D3C85BB84A5F5D8FA6E2BA | |||
| 1876 | Roblox Account Manager.exe | C:\Users\admin\Desktop\RAMTheme.ini | text | |
MD5:F18FA783F4D27E35E54E54417334BFB4 | SHA256:563EB35FD613F4298CD4DCEFF67652A13BA516A6244D9407C5709323C4CA4BB1 | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3504 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
173
DNS requests
226
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
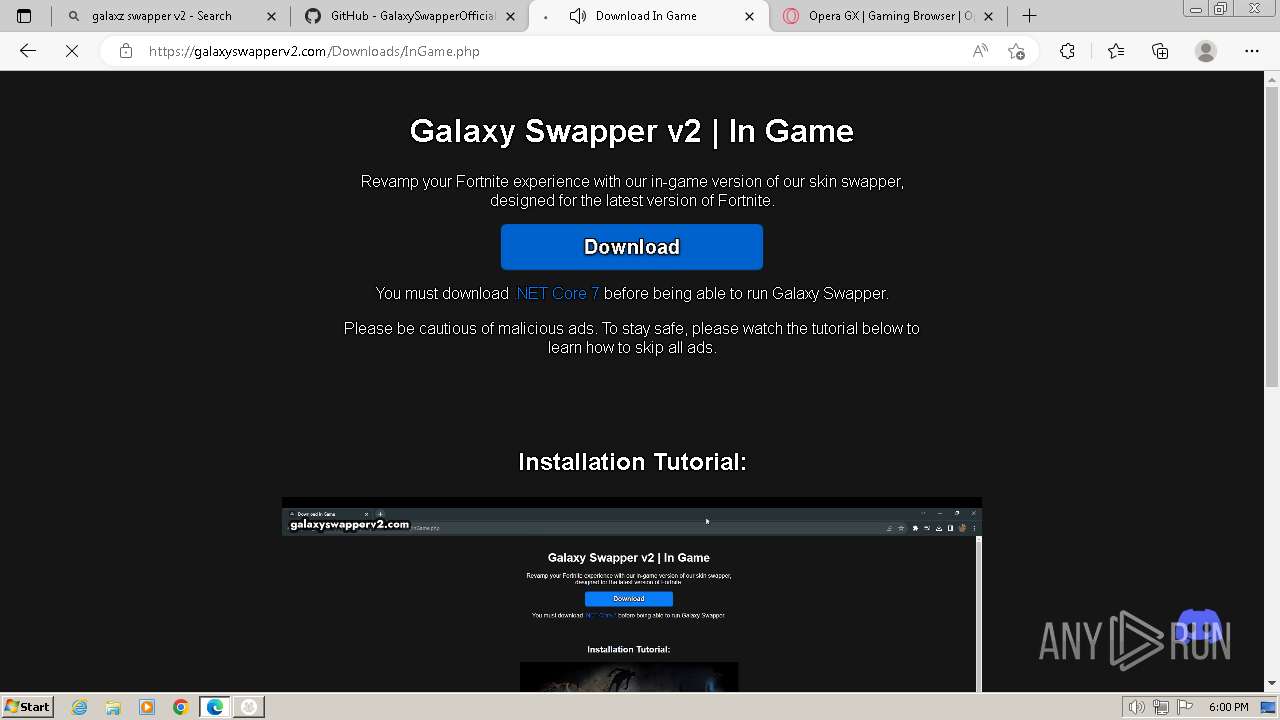
— | — | GET | 302 | 172.234.192.109:80 | http://impactedgestar.com/ | unknown | — | — | unknown |
— | — | GET | 200 | 64.190.63.136:80 | http://ww1.impactedgestar.com/?usid=101&utid=971596f11024232f709fc61ec374c6dc | unknown | — | — | whitelisted |
— | — | GET | 200 | 64.190.63.136:80 | http://ww1.impactedgestar.com/search/tsc.php?ses=ogc59_wrF2rJXja4Lklq-DNJB_LOzaWhH9SImoUbuKg4wdVIXbgYSs95jk7yQG7uyJAoqEACHwVhX9C9tqxm-drUNYXLj7bNIw-XCll03zHLbI3oVXx3FyuJOaE541WWVQEcnB4WecfvW8ThlXwWb7MbyZ5CVzDcbJL6Xsl7rhdq24NLuG249zWqId05T8trDKiwhiyplICmX1VT7-f8AD4B328OC0c_McCwmeSvMeNOzwXN86A3wrcVvkYHyS37fvicexMwywad9WjwU7iwhLgGXAkiCycmNnynemBqnFVt2r-4FsNuZV1Ci4Pym3eNfOYk6bsTo82ESKHoG149EAVpo0dS66evepPDj3XvOOqyxv4hr4pT7iwUz0h9pLC&cv=2 | unknown | — | — | whitelisted |
— | — | GET | 441 | 64.190.63.136:80 | http://ww1.impactedgestar.com/img.sedoparking.com/images/js_preloader.gif | unknown | — | — | whitelisted |
— | — | GET | 302 | 64.190.63.136:80 | http://ww1.impactedgestar.com/search/redirect.php?f=http%3A%2F%2Fxml.sedodna.com%2Fclick%3Fi%3DwlmglNYkJ5s_0&v=ZGVlNjhlOGZkOTBlMzZiYzZhOGM2NTBjN2FkYTBlM2UJMQl3dzEuaW1wYWN0ZWRnZXN0YXIuY29tNjczYjgwNmQzOWVkMDcuNjY5NjkxNjYJd3cxLmltcGFjdGVkZ2VzdGFyLmNvbTY3M2I4MDZkMzlmMWIxLjY4MDI4MjY1CTE3MzE5NTI3NTEJYWRfNjNfMA%3D%3D&l=ogcuXf1-pKI8sLreEkuwkPukb46GFvH4i3Yw0CnKBRpe1sEL-mSTNiIWzR_K6Om-aObjAwwBUZaYRUIbZnL2snlKz0u0HNjtVxpdok_ZOBADekgYtDC3hhvppWij1WCOw_N88niYVaF62DcofZPGJq-mgqLaTIoPn94nbIxGTmGz9W4Ivj2lUnYXUdzVpdhf8GOLJIMrrjvI3wBTFK-PrA-wTClrA-g14Bgp3RFkAAe7EHpm4EA5CFtEkMLc7Sy9KgUifjx8IUXGLU69p2PnZjQiN3tersbbOyP84hpvDmlo6y3WJ3Yhr_-a5-WPPe1M5j7W8L7O1hKSwDB_gOERFR-2BcGVNjjdbRIEd3do-L4mYgrSukk6oMZLXvxAHNYYysB9Af6j8VCnAAKDTQDwbtPlKILiQQDjI8pSVe4P_z5H2JTMOnOngwskyz7k4AvElCM1EQaPWWZXhrtdO8wq86jdQwirjvxRobLTS1evD9E9wbEldU7lb8d9vx7qQ33f7vU1EV60qVWW-n6w9akAzsym-zzdjAbpf_6sbdPtZqtSKEWNnkxs3mZpbJAp9x1xWQRSOMUsEVYiFPMyQCKvSi9jYAqIu76IFhmu_ToHm6Lfk0aRjDb45lZuEXLreSXFYdZ4UCPnqaoVV9pBwIJl3RhhbsVNB1Af58VFXg2VbJXYeAPRSneDZ2jsvQRIKz8YbOJDyFp0ji78_oHtGkISw | unknown | — | — | whitelisted |
— | — | GET | 441 | 64.190.63.136:80 | http://ww1.impactedgestar.com/img.sedoparking.com/images/js_preloader.gif | unknown | — | — | whitelisted |
— | — | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/logos/sedo_logo.png | unknown | — | — | whitelisted |
— | — | GET | 302 | 64.190.63.136:80 | http://ww1.impactedgestar.com/search/tcerider.php?f=http%3A%2F%2Fxml.sedodna.com%2Fclick%3Fi%3DwlmglNYkJ5s_0&v=ZGVlNjhlOGZkOTBlMzZiYzZhOGM2NTBjN2FkYTBlM2UJMQl3dzEuaW1wYWN0ZWRnZXN0YXIuY29tNjczYjgwNmQzOWVkMDcuNjY5NjkxNjYJd3cxLmltcGFjdGVkZ2VzdGFyLmNvbTY3M2I4MDZkMzlmMWIxLjY4MDI4MjY1CTE3MzE5NTI3NTEJYWRfNjNfMA%3D%3D&l=ogcuXf1-pKI8sLreEkuwkPukb46GFvH4i3Yw0CnKBRpe1sEL-mSTNiIWzR_K6Om-aObjAwwBUZaYRUIbZnL2snlKz0u0HNjtVxpdok_ZOBADekgYtDC3hhvppWij1WCOw_N88niYVaF62DcofZPGJq-mgqLaTIoPn94nbIxGTmGz9W4Ivj2lUnYXUdzVpdhf8GOLJIMrrjvI3wBTFK-PrA-wTClrA-g14Bgp3RFkAAe7EHpm4EA5CFtEkMLc7Sy9KgUifjx8IUXGLU69p2PnZjQiN3tersbbOyP84hpvDmlo6y3WJ3Yhr_-a5-WPPe1M5j7W8L7O1hKSwDB_gOERFR-2BcGVNjjdbRIEd3do-L4mYgrSukk6oMZLXvxAHNYYysB9Af6j8VCnAAKDTQDwbtPlKILiQQDjI8pSVe4P_z5H2JTMOnOngwskyz7k4AvElCM1EQaPWWZXhrtdO8wq86jdQwirjvxRobLTS1evD9E9wbEldU7lb8d9vx7qQ33f7vU1EV60qVWW-n6w9akAzsym-zzdjAbpf_6sbdPtZqtSKEWNnkxs3mZpbJAp9x1xWQRSOMUsEVYiFPMyQCKvSi9jYAqIu76IFhmu_ToHm6Lfk0aRjDb45lZuEXLreSXFYdZ4UCPnqaoVV9pBwIJl3RhhbsVNB1Af58VFXg2VbJXYeAPRSneDZ2jsvQRIKz8YbOJDyFp0ji78_oHtGkISw | unknown | — | — | whitelisted |
— | — | GET | 302 | 173.239.53.32:80 | http://xml.sedodna.com/click?i=wlmglNYkJ5s_0 | unknown | — | — | whitelisted |
— | — | GET | 200 | 178.162.151.164:80 | http://q3.quotes.com/cf7a9ff8-a5d6-11ef-9297-f50b3ea4ae7b | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2220 | Roblox Account Manager.exe | 2.20.158.181:443 | aka.ms | AKAMAI-AS | IT | whitelisted |
2220 | Roblox Account Manager.exe | 140.82.121.5:443 | api.github.com | GITHUB | US | whitelisted |
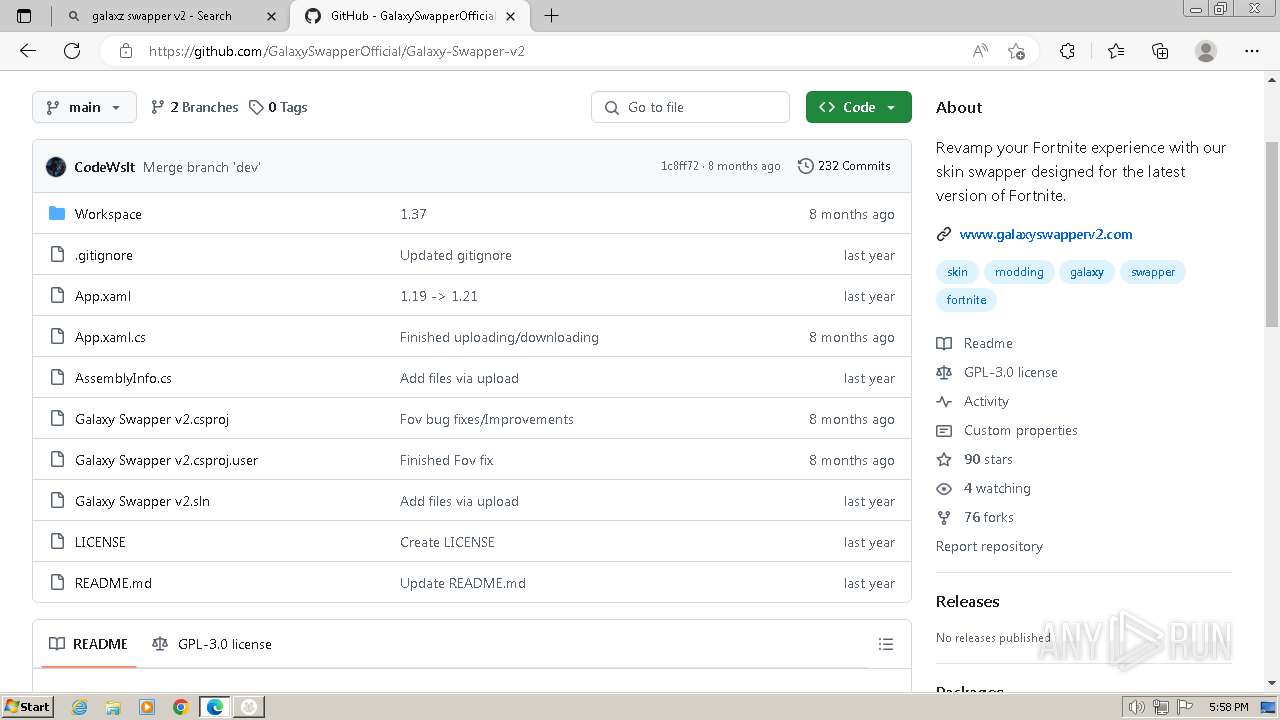
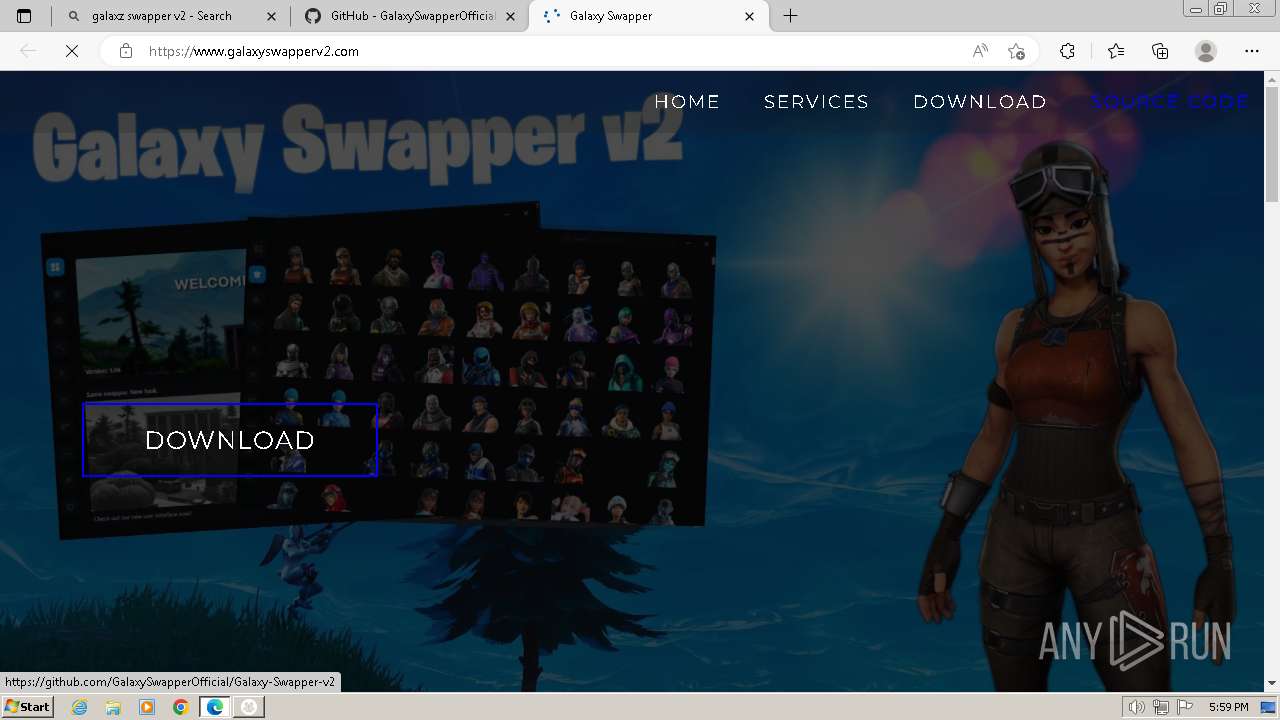
2220 | Roblox Account Manager.exe | 140.82.121.4:443 | github.com | GITHUB | US | shared |
2220 | Roblox Account Manager.exe | 128.116.44.3:443 | clientsettings.roblox.com | ROBLOX-PRODUCTION | US | whitelisted |
2220 | Roblox Account Manager.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
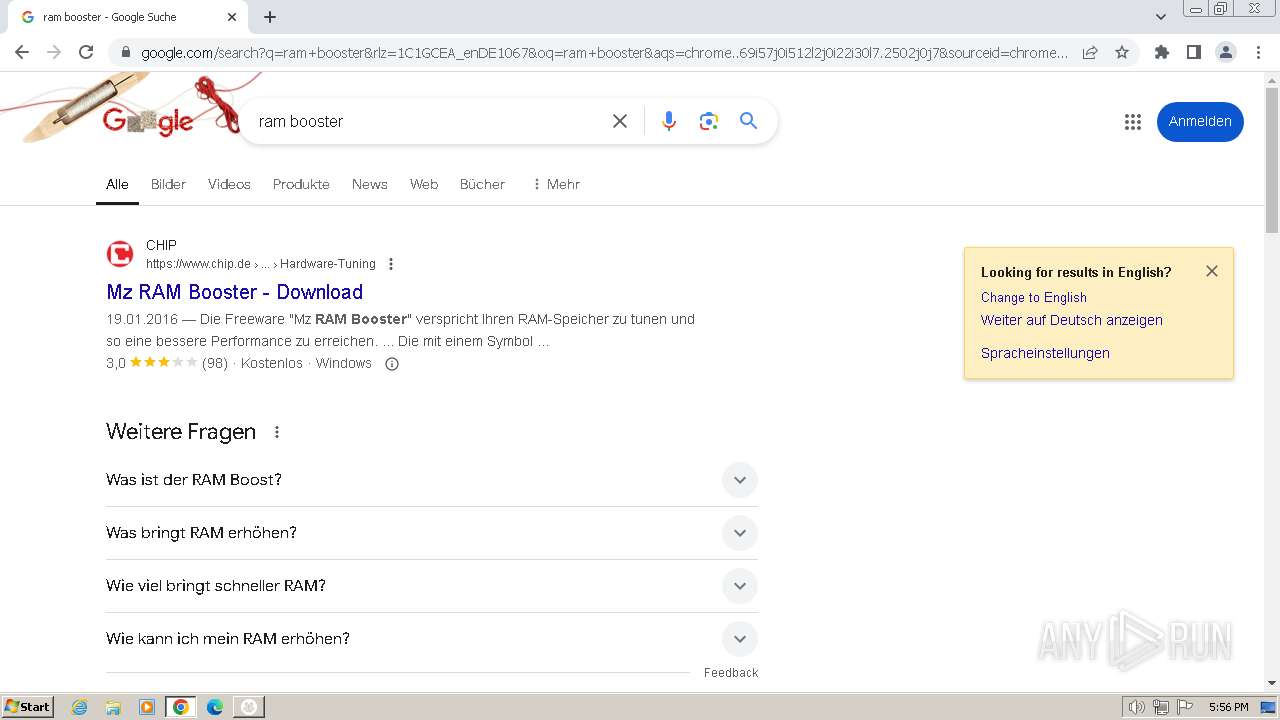
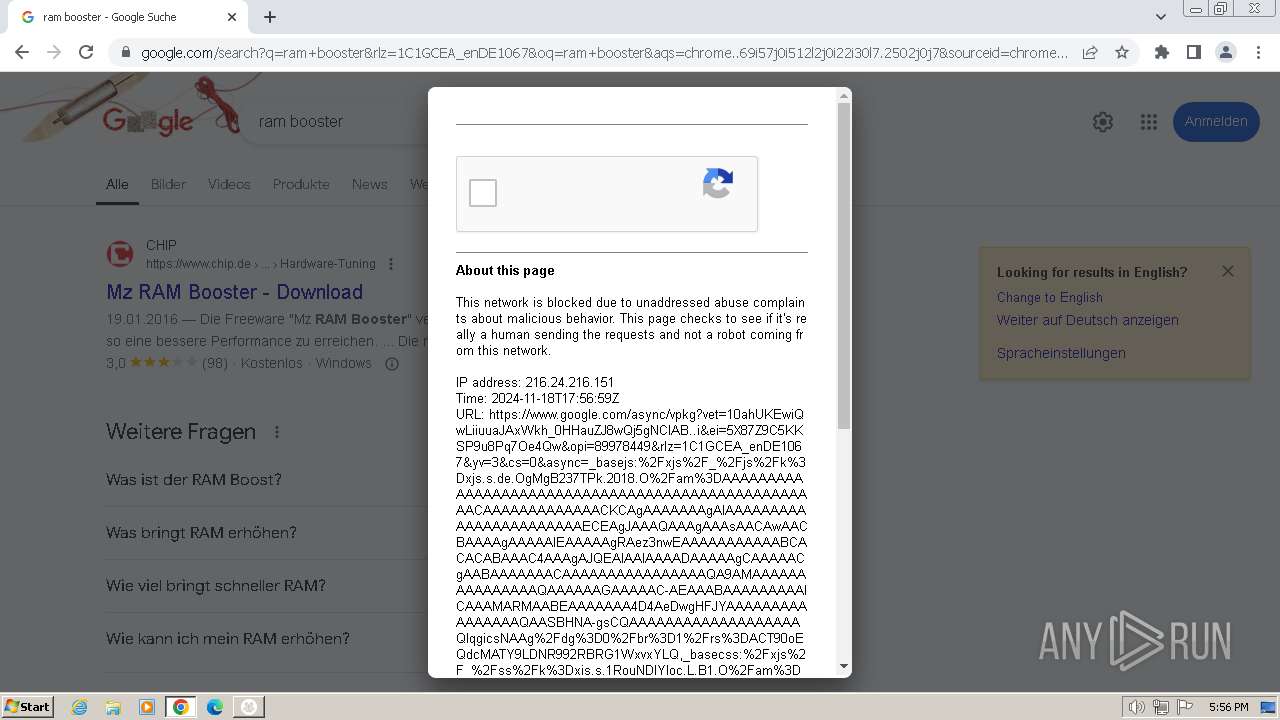
google.com |
| whitelisted |
aka.ms |
| whitelisted |
api.github.com |
| whitelisted |
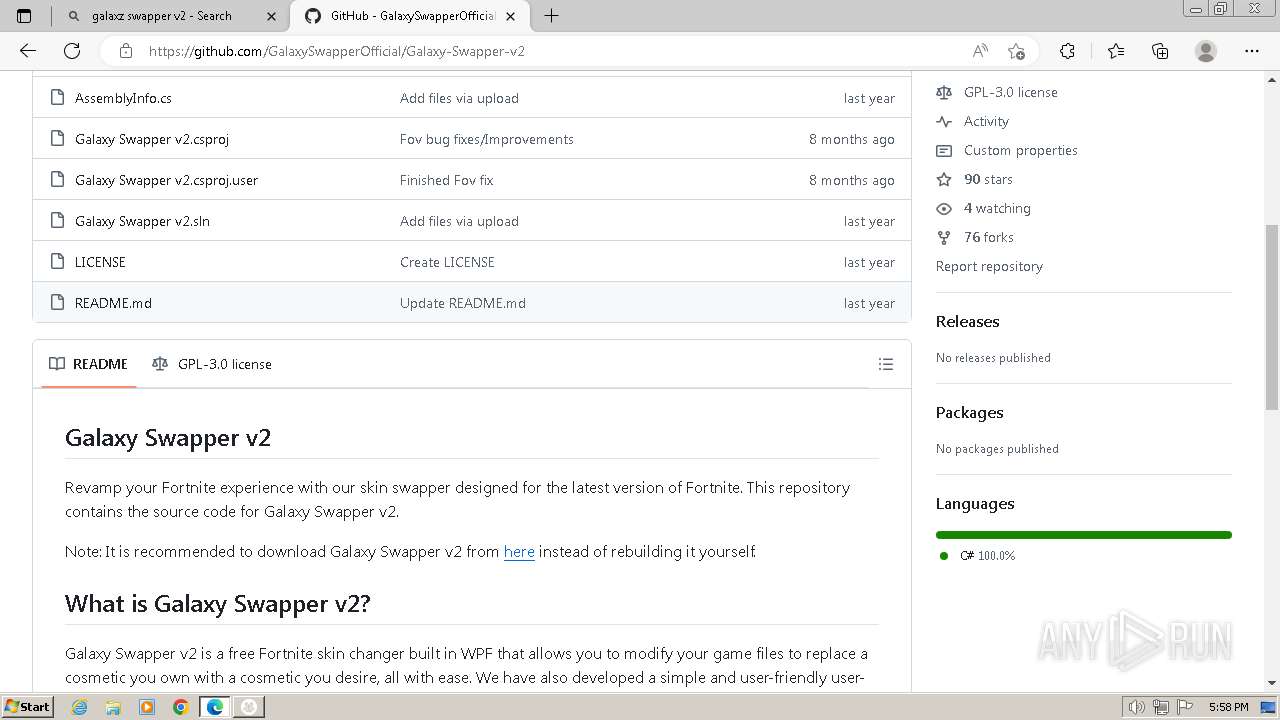
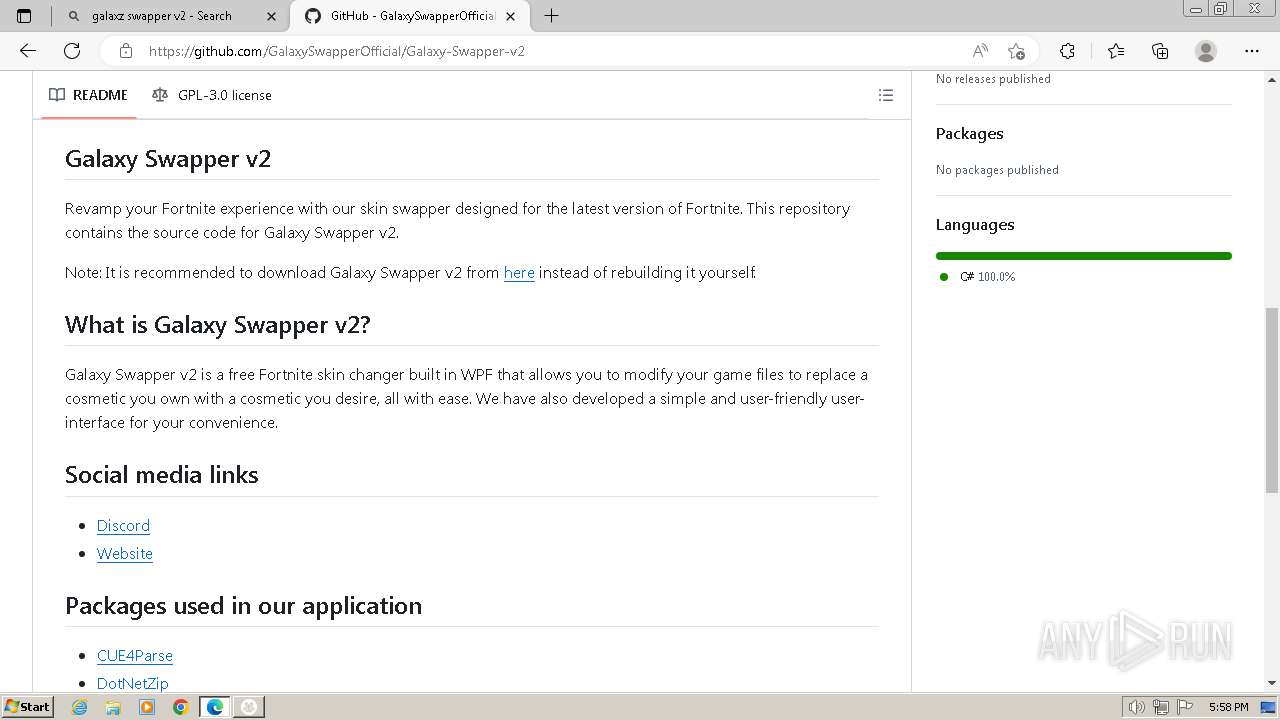
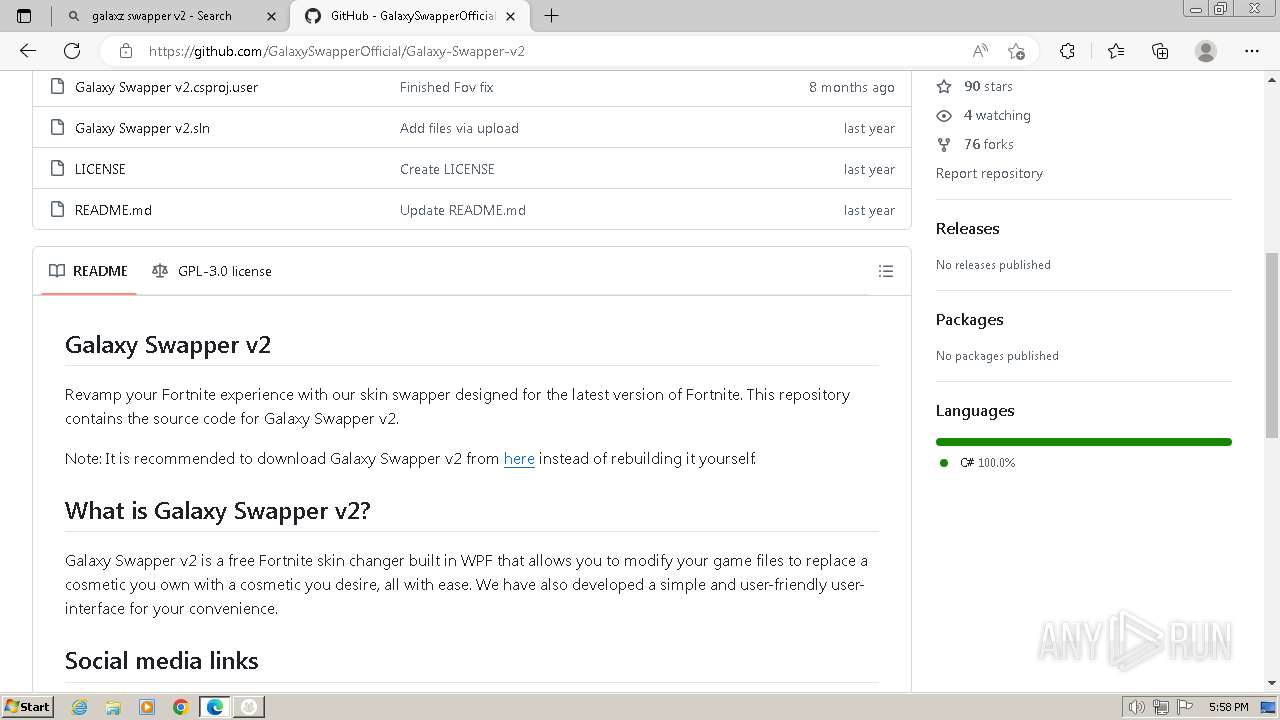
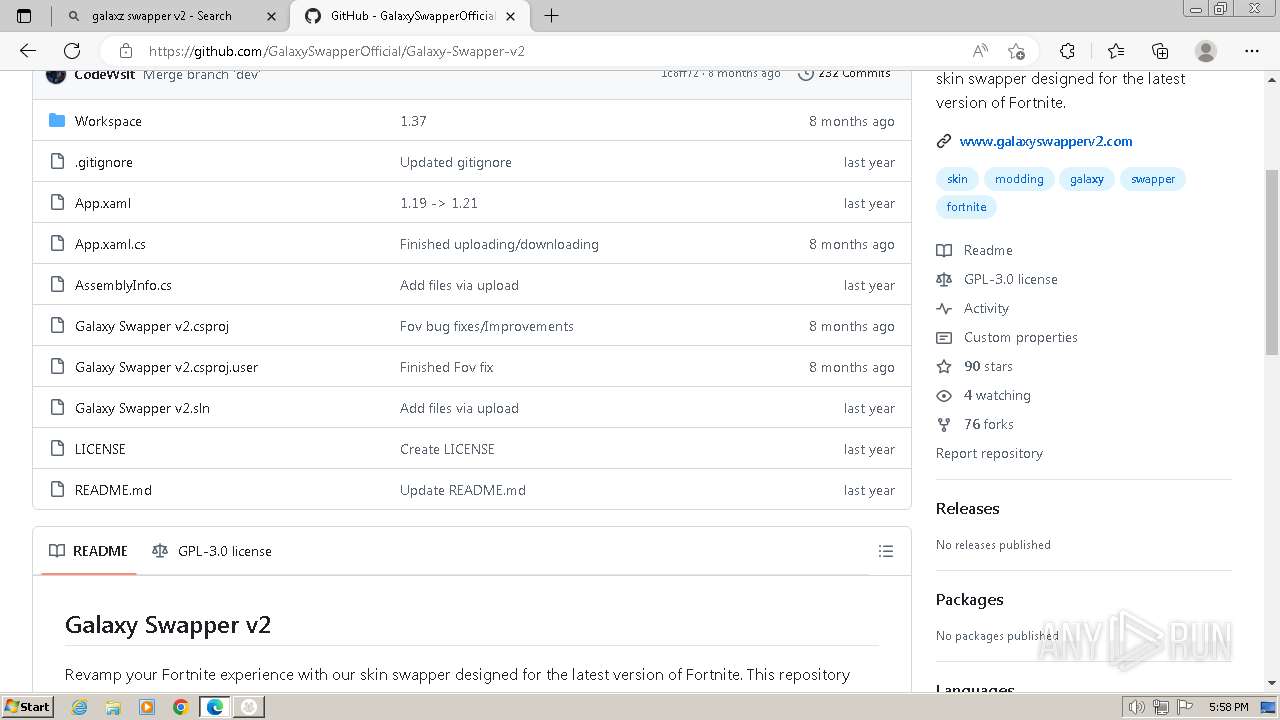
github.com |
| shared |
clientsettings.roblox.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
objects.githubusercontent.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
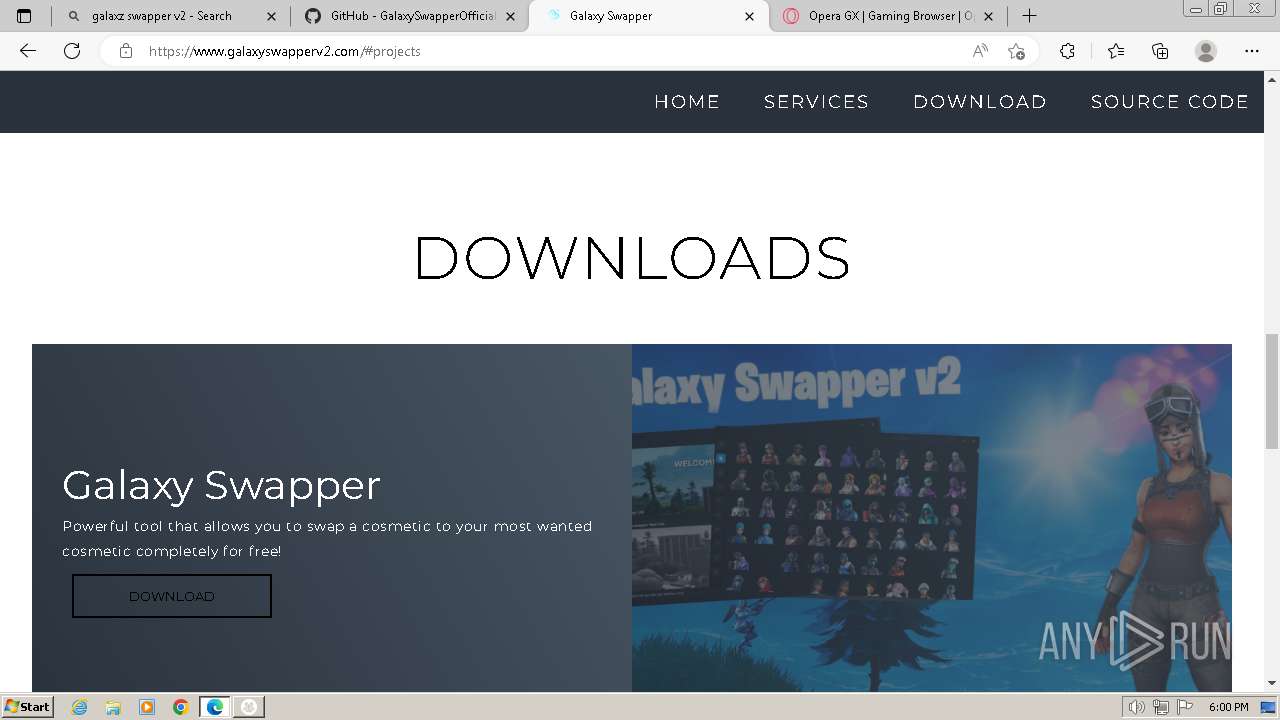
1060 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
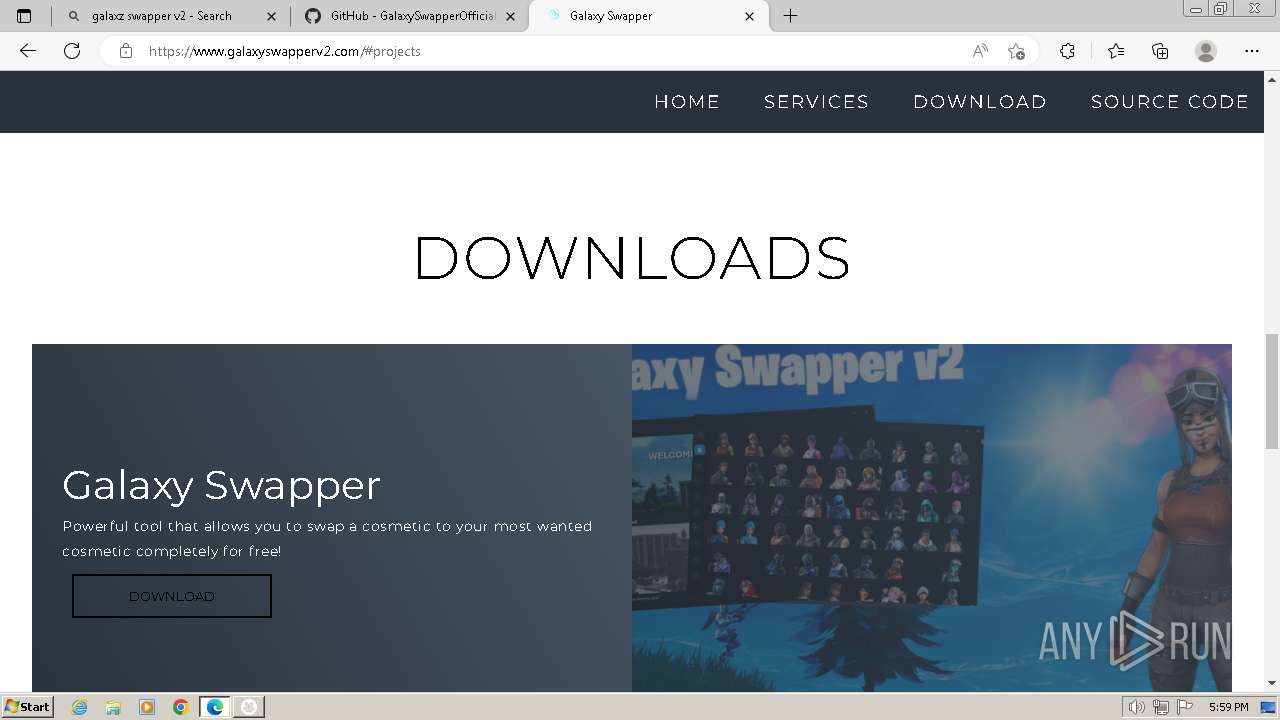
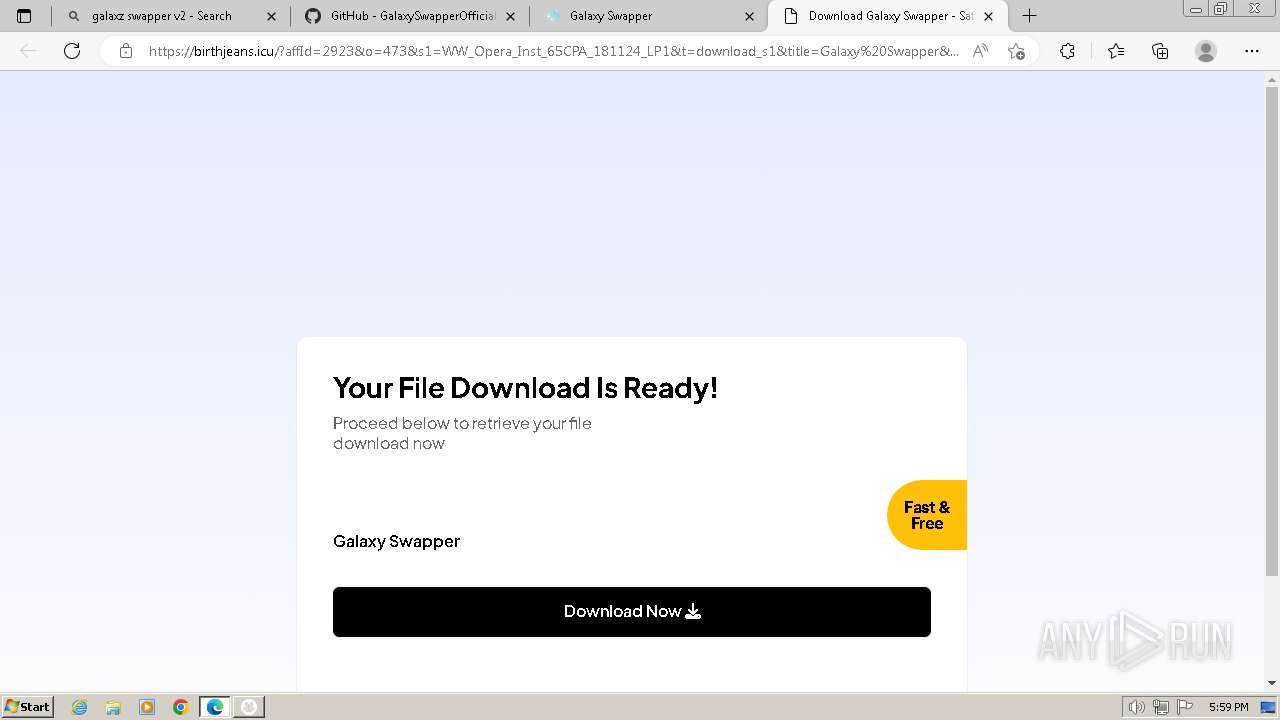
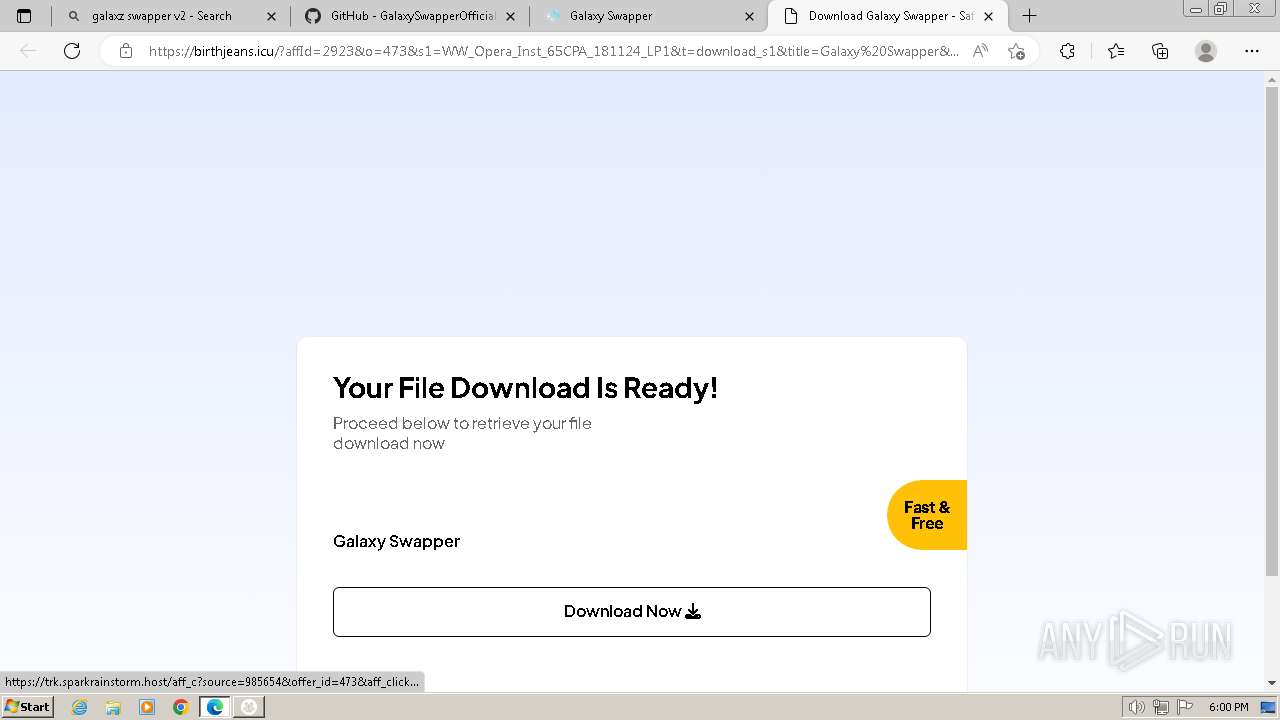
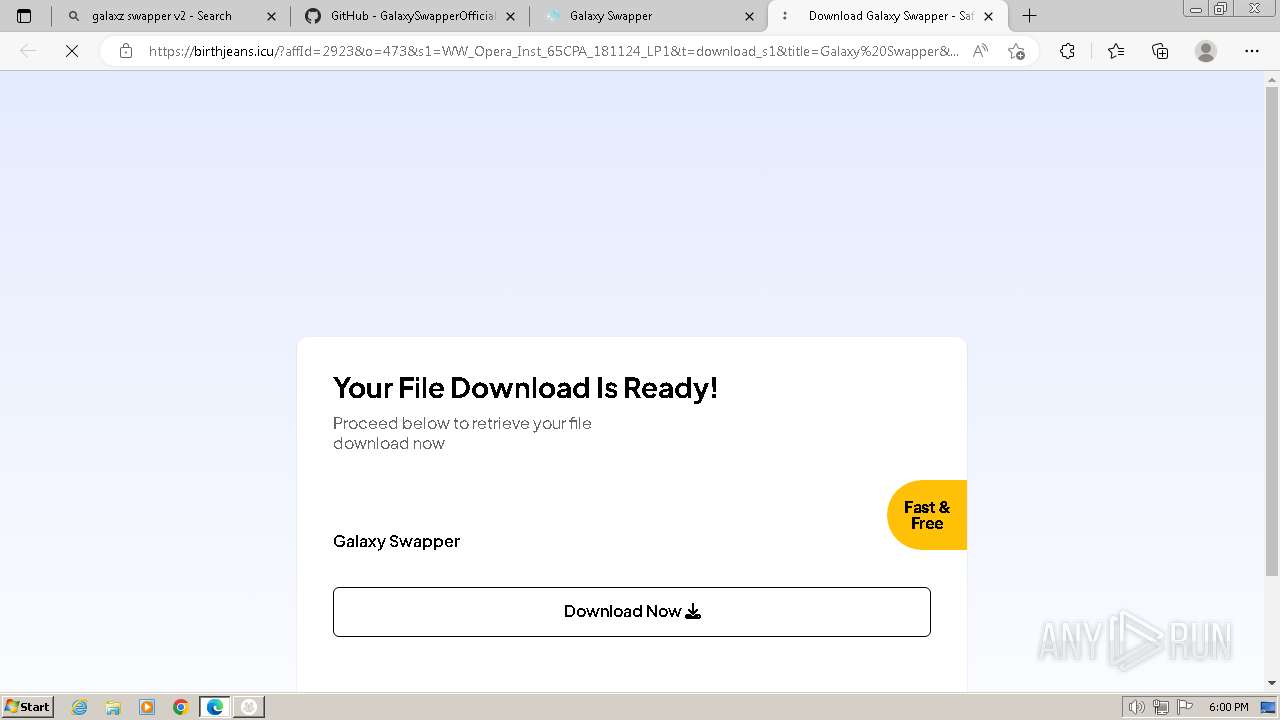
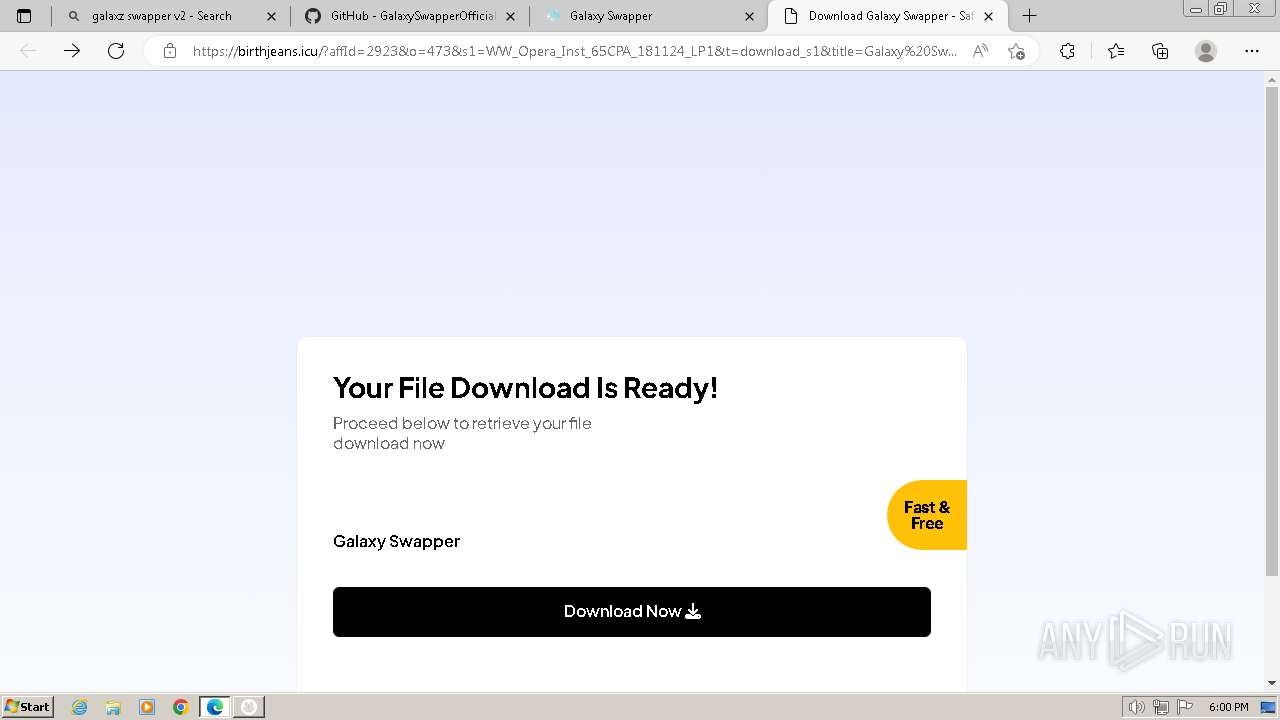
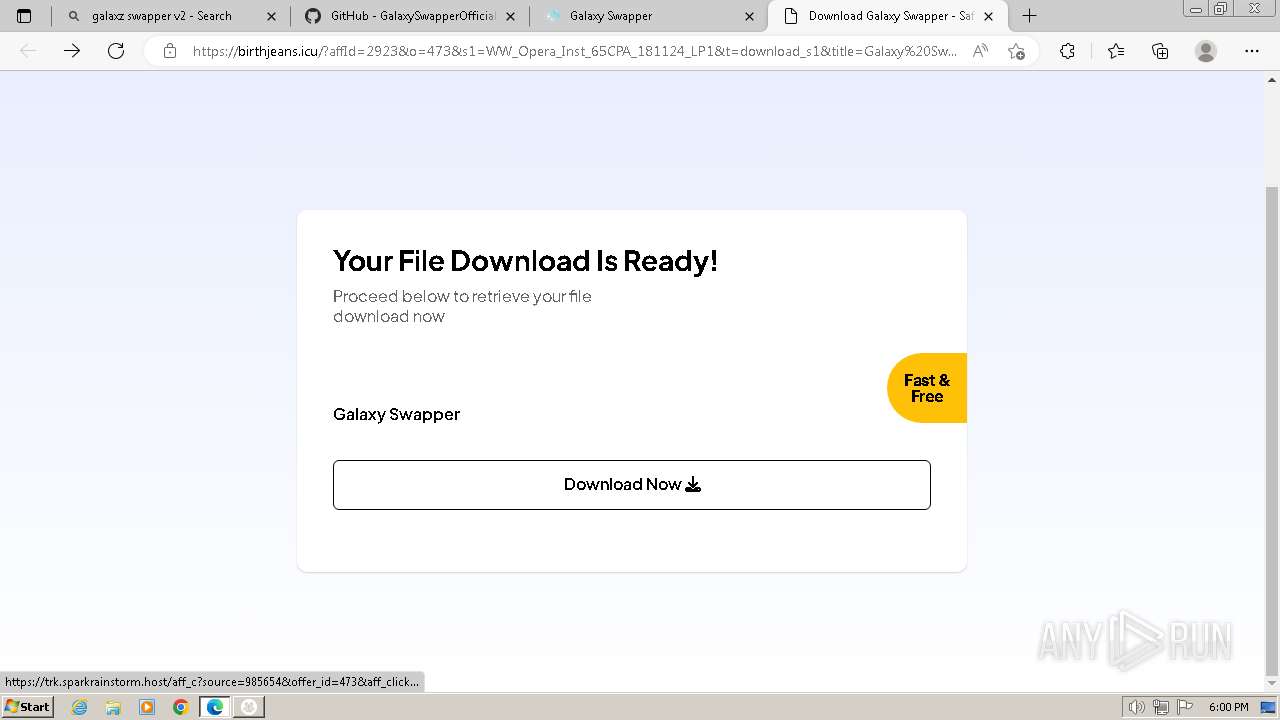
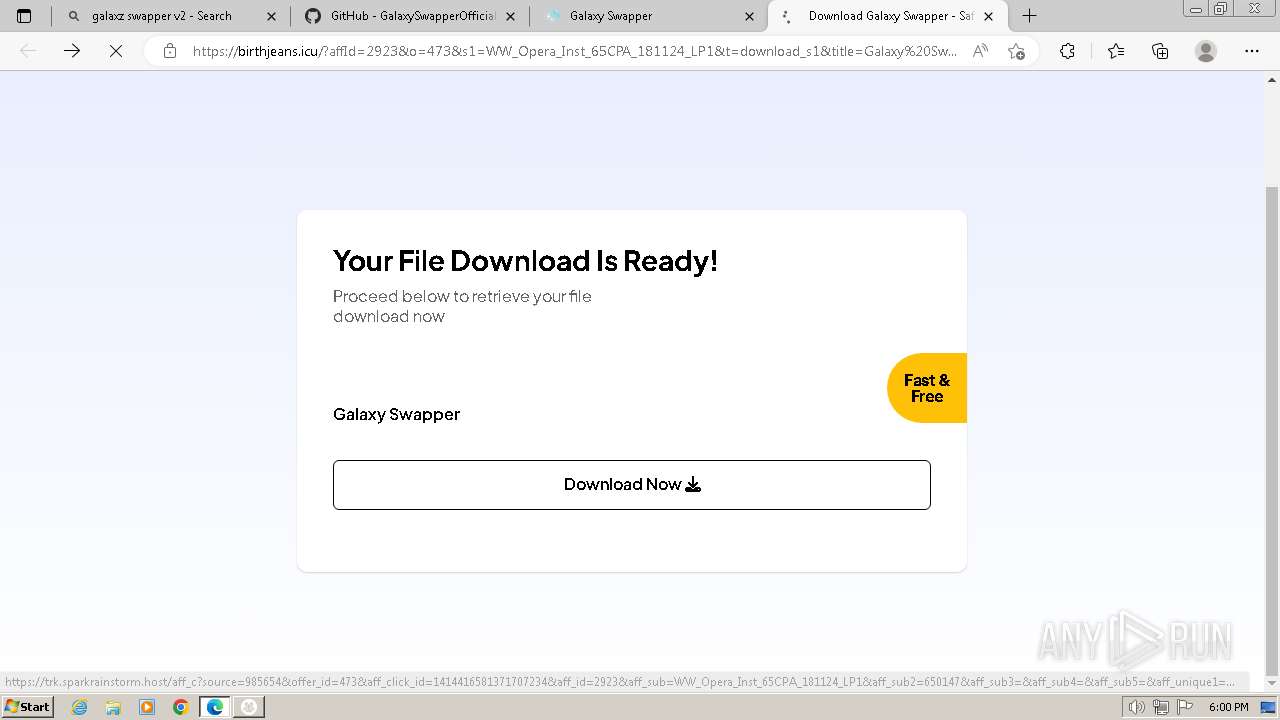
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
— | — | Potentially Bad Traffic | ET INFO Suspicious Domain (*.icu) in TLS SNI |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |