| File name: | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe |
| Full analysis: | https://app.any.run/tasks/08ff1a14-665a-44eb-8e9c-df9dbc43c1fe |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2025, 05:15:14 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, 5 sections |
| MD5: | 128A8E676D8B3A5141C54790252EC620 |
| SHA1: | 25063DDC536BFA5F4F07F2A0613EF37ED6FA7458 |
| SHA256: | 49A431909850E4C2DF227A7F6A43B10F857FC144FCC374DC50B7E9D1802E662A |
| SSDEEP: | 1536:QPlbc9F8xi59F8xiG+3+U3aWf+0TRV0TRtjVABc9F8xi59F8xiG+3+U3aWf+0TR1:alOfSaofh |
MALICIOUS
ZOMBIE has been detected (YARA)
- 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe (PID: 4748)
SUSPICIOUS
Creates file in the systems drive root
- 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe (PID: 4748)
Executable content was dropped or overwritten
- 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe (PID: 4748)
The process creates files with name similar to system file names
- 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe (PID: 4748)
INFO
Creates files or folders in the user directory
- 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe (PID: 4748)
Checks supported languages
- 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe (PID: 4748)
Reads the software policy settings
- slui.exe (PID: 2292)
Checks proxy server information
- slui.exe (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.4) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.8) |
| .exe | | | DOS Executable Generic (18.8) |
| .vxd | | | VXD Driver (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit, No debug |
| PEType: | PE32 |
| LinkerVersion: | - |
| CodeSize: | - |
| InitializedDataSize: | - |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2130 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
135
Monitored processes
2
Malicious processes
1
Suspicious processes
0
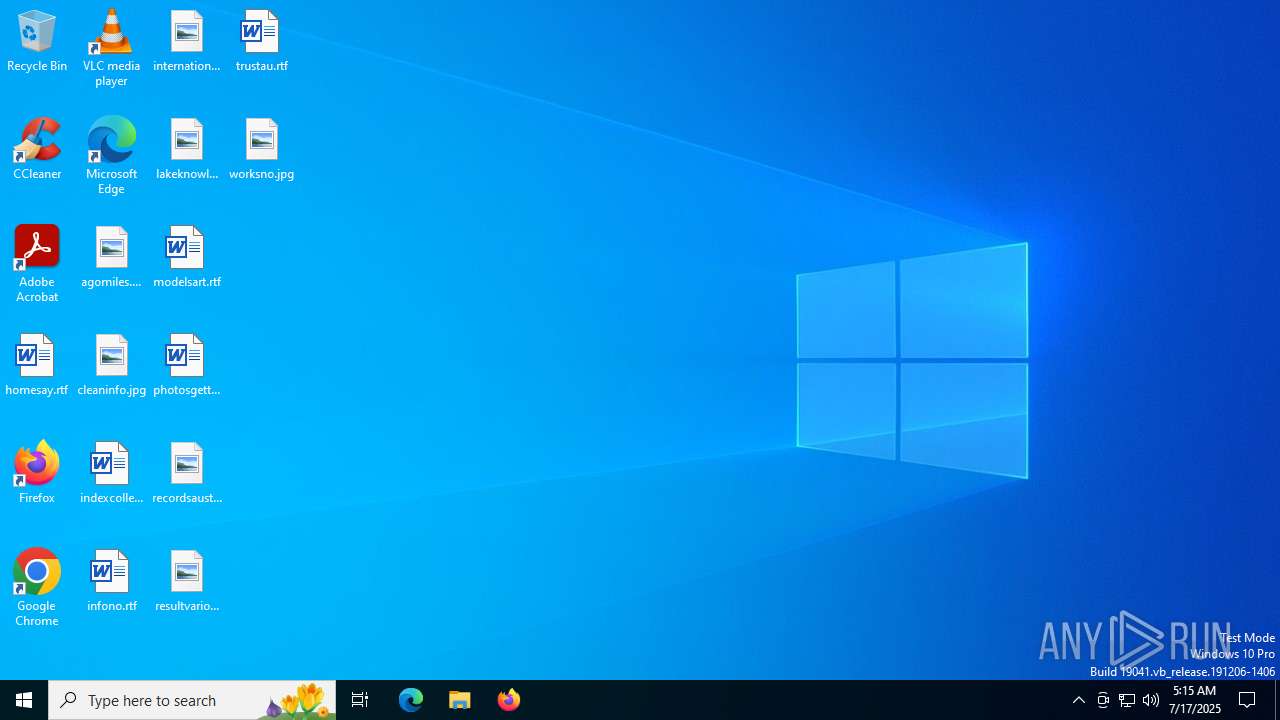
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2292 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4748 | "C:\Users\admin\Desktop\49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe" | C:\Users\admin\Desktop\49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
3 500
Read events
3 500
Write events
0
Delete events
0
Modification events
Executable files
1 811
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | — | ||
MD5:— | SHA256:— | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini.exe | executable | |
MD5:DBCA2BC629F88310EBFC3C216BC58C36 | SHA256:CF1CAB7FF44D9EBD91B8D0297F0DD2BA9BCE7B24B00DF6D66E8BBF89C67BEB03 | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\$Recycle.Bin\S-1-5-21-1693682860-607145093-2874071422-1001\desktop.ini.tmp | executable | |
MD5:DBCA2BC629F88310EBFC3C216BC58C36 | SHA256:CF1CAB7FF44D9EBD91B8D0297F0DD2BA9BCE7B24B00DF6D66E8BBF89C67BEB03 | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\bootmgr.tmp | executable | |
MD5:C4351B11C10C39DCFEA0AB4E759726D8 | SHA256:A902B82679A25D902ADD884C45A4CE010012409B1A7B0E2EC3000B52CC12FED1 | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat DC\Acrobat\1494870C-9912-C184-4CC9-B401-A53F4D8DE290.pdf.tmp | executable | |
MD5:4C21A723DD14ADD420314AB7A3F81B1E | SHA256:BA9EDA447FB1EACA4A1269BE8CC44A5A645D7638C48BCDBD177B2F1DB94AADEF | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe.tmp | executable | |
MD5:78DCE6CCEA006BE90147EEA56F971DC7 | SHA256:81BE3F23BDC72590D2A236BBE41C77717A2063BB719A94FC5BBBB8350FFD788F | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\bootTel.dat.tmp | executable | |
MD5:844B98372DFC2E4E692774069CFE10C2 | SHA256:E979FBDC3D52EC5E8CB0F85BD76883CE74EC4D7720208E444AA5C2E19A86B90D | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\BOOTNXT.tmp | executable | |
MD5:F67D6788D6AFD7D681912F8FB89E6397 | SHA256:164C1ADD5A581C49DE71BDFB8AB0BF92C8706742CD838020E9FE027A6062B0C4 | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat DC\Acrobat\AcroBroker.exe.tmp | executable | |
MD5:6DC3039C60247664EE70233270B24A0F | SHA256:1572124E30B39373745854BC12FEE5788A2F62B60F641E56570ADC61EB15F449 | |||
| 4748 | 49a431909850e4c2df227a7f6a43b10f857fc144fcc374dc50b7e9d1802e662a.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat DC\Acrobat\ACE.dll.tmp | executable | |
MD5:3AB2BDD7FCDCCCCB4624219CDE6A7BDC | SHA256:85EC229A3049A72A4194A59BFB7B2478C80FC6C4418B16D0DAAD07150BD4BF6D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
55
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
684 | RUXIMICS.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
684 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
4400 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
4400 | SIHClient.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
4400 | SIHClient.exe | GET | 200 | 2.16.241.14:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4400 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
684 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
684 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
684 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |