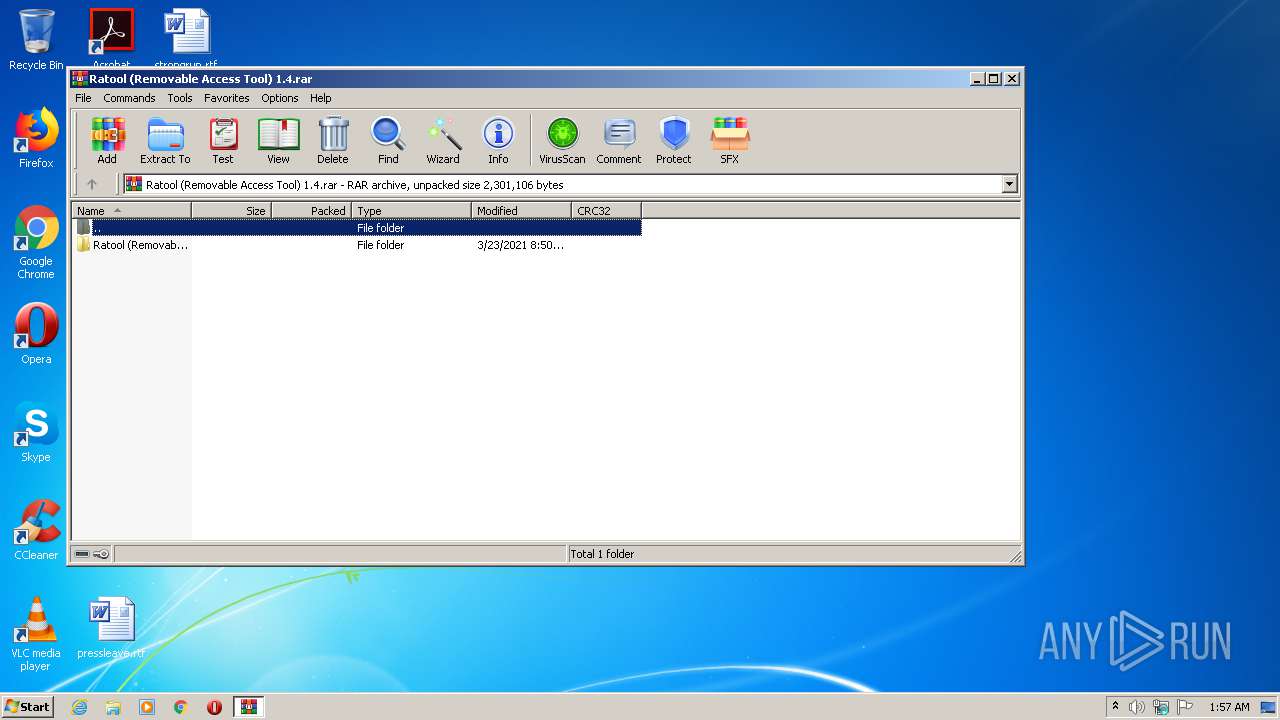
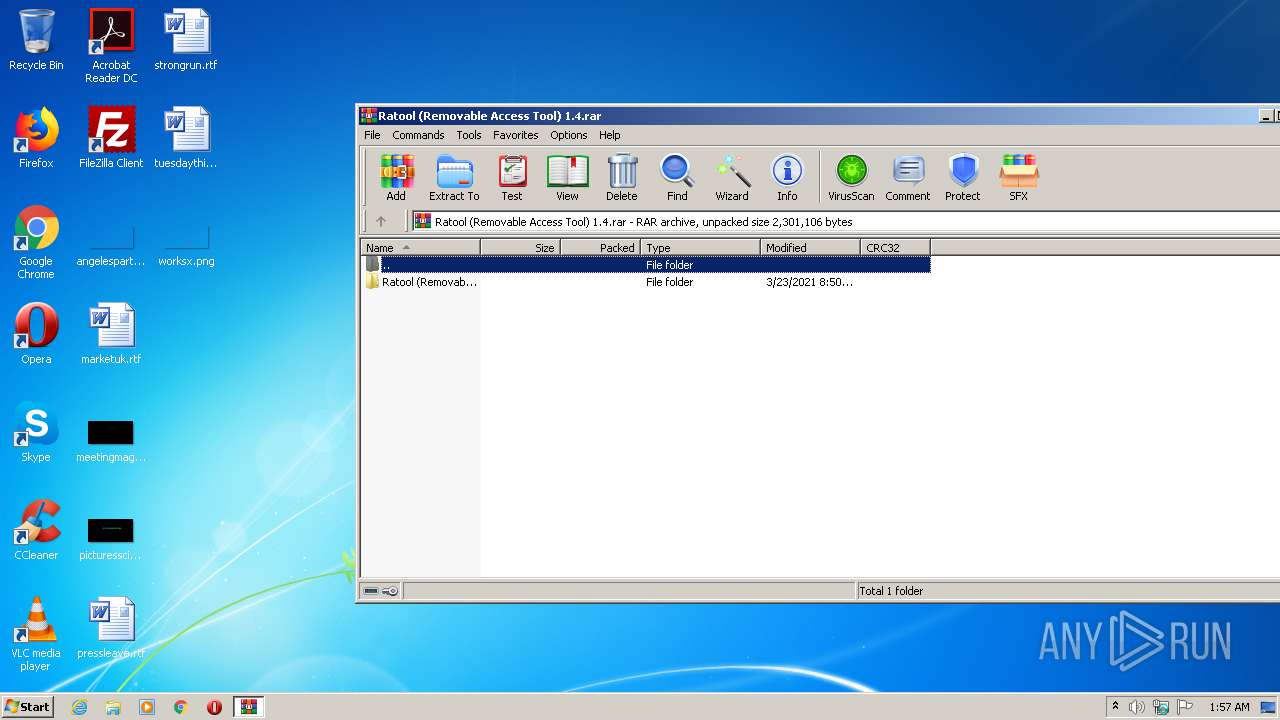
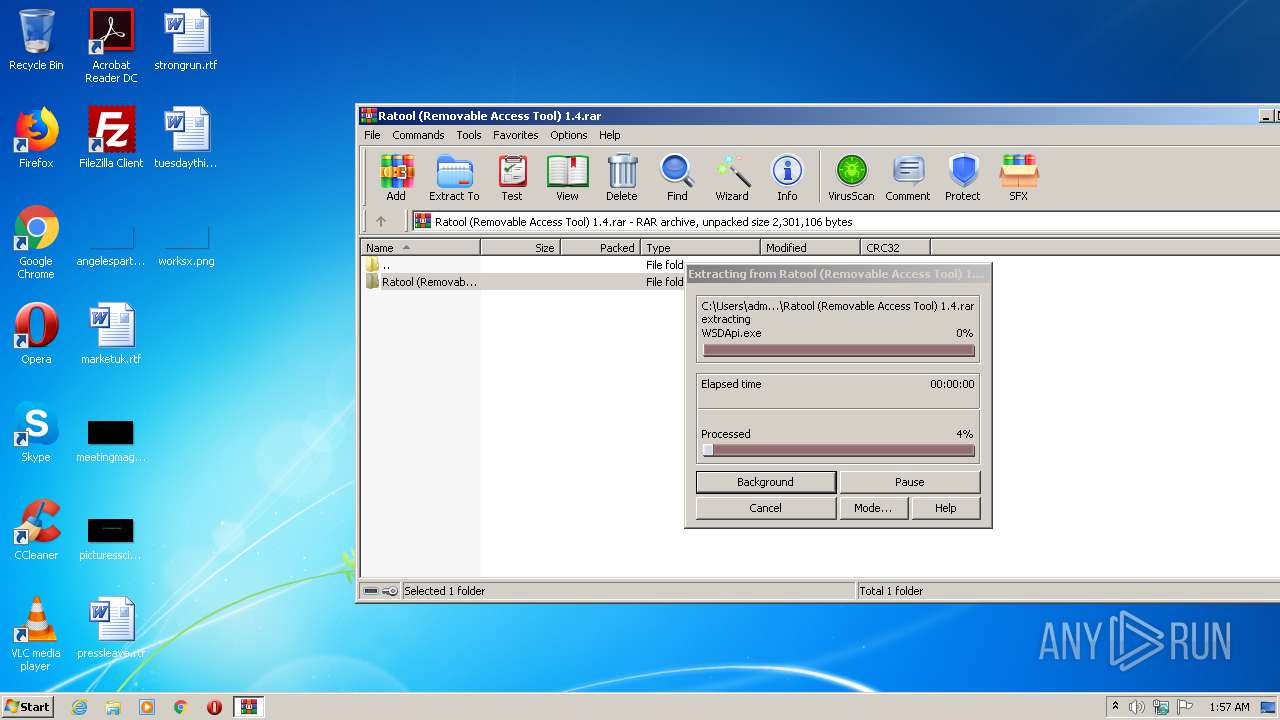
| File name: | Ratool (Removable Access Tool) 1.4.rar |
| Full analysis: | https://app.any.run/tasks/08768f70-46e8-4fd5-937c-e68378d2825b |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2021, 00:57:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 55010C24AE8B82B4370EE0E9F82D77A5 |
| SHA1: | 7B809418DAE71012717C5B23E2B49EE635295264 |
| SHA256: | 4991CC5BBE2CF817711F166F86C3C91592EBEDCAD86E6E65E012E304DB51DDB9 |
| SSDEEP: | 24576:f4XHiwSH2RLuYiqNoZ0BDqstVWgpgevNAebofR81EN:wXHih+utODfVWFeviekG1EN |
MALICIOUS
Writes to a start menu file
- Launcher.exe (PID: 608)
Changes the autorun value in the registry
- Launcher.exe (PID: 608)
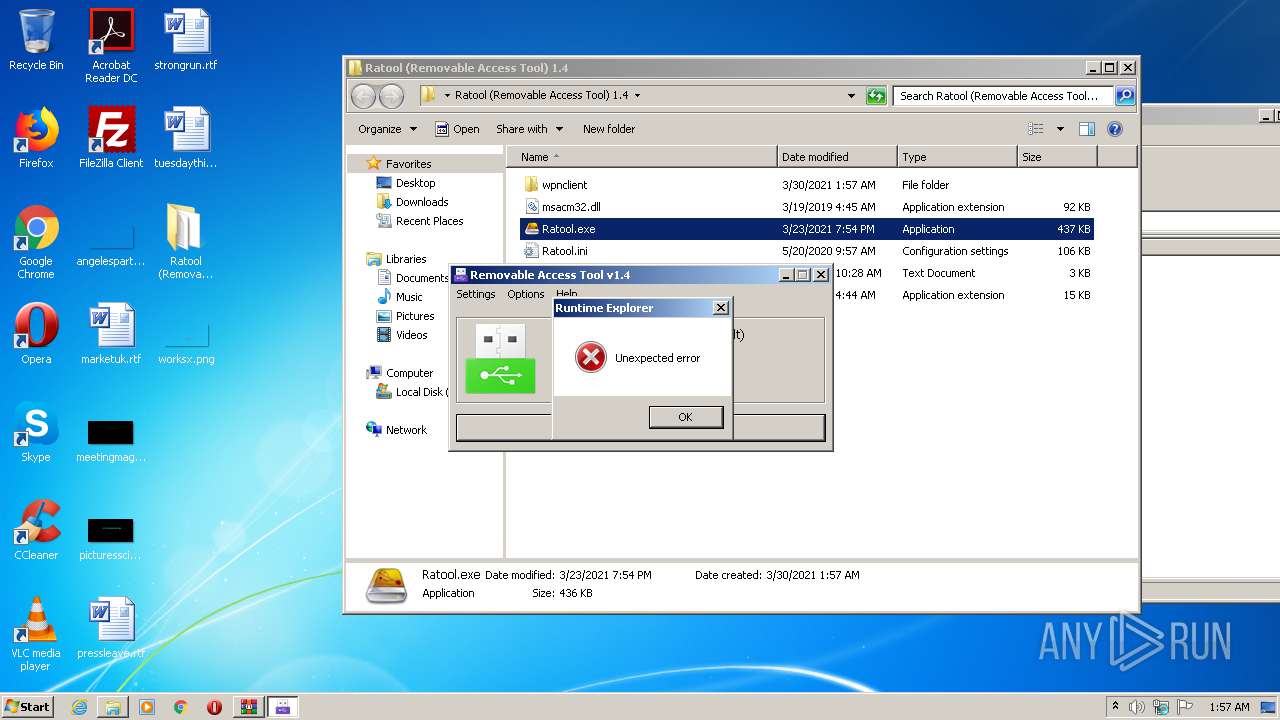
Application was dropped or rewritten from another process
- Windows Services.exe (PID: 3456)
- Runtime Explorer.exe (PID: 748)
- Secure System Shell.exe (PID: 2200)
- Runtime Explorer.exe (PID: 1404)
- Runtime Explorer.exe (PID: 3376)
- Runtime Explorer.exe (PID: 2444)
- Runtime Explorer.exe (PID: 4092)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2684)
- Launcher.exe (PID: 608)
Drops a file with a compile date too recent
- Launcher.exe (PID: 608)
- DrvInst.exe (PID: 2584)
Executable content was dropped or overwritten
- Launcher.exe (PID: 608)
Executes PowerShell scripts
- Launcher.exe (PID: 608)
Creates files in the Windows directory
- Launcher.exe (PID: 608)
- WSDApi.exe (PID: 1324)
Creates or modifies windows services
- WSDApi.exe (PID: 1324)
Executed via COM
- DrvInst.exe (PID: 2584)
- rundll32.exe (PID: 592)
- DrvInst.exe (PID: 3392)
- rundll32.exe (PID: 1940)
INFO
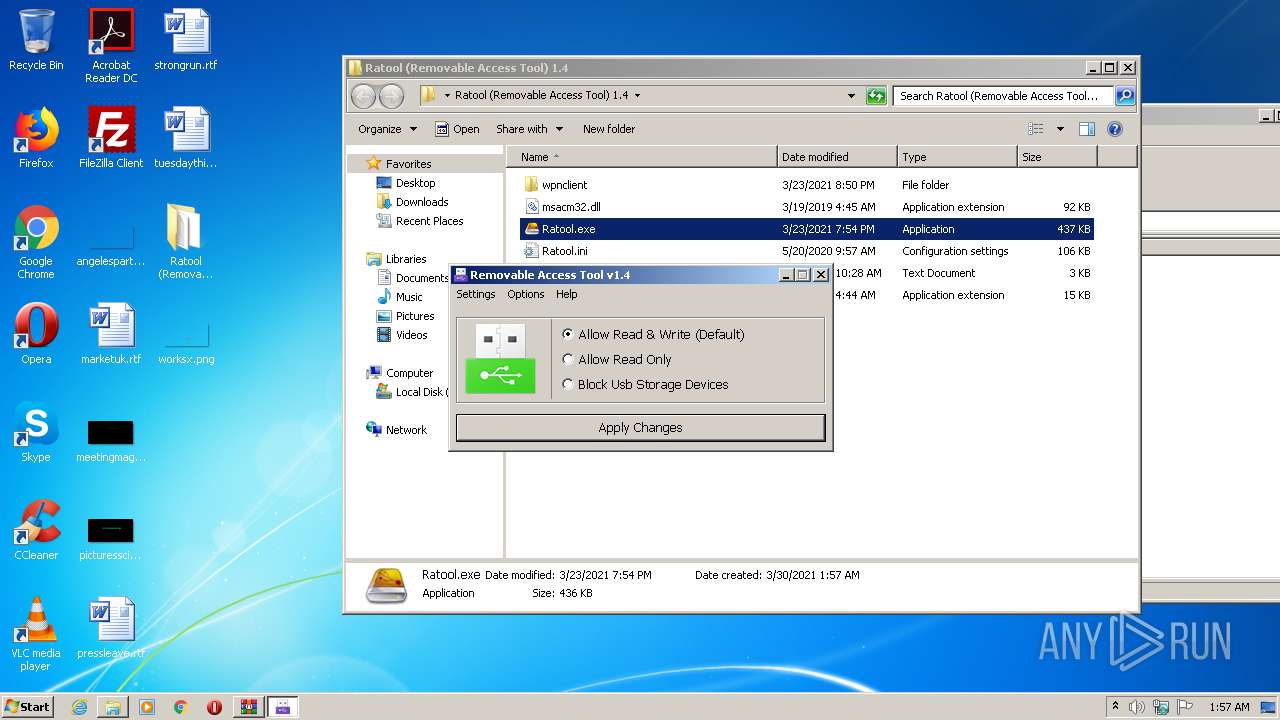
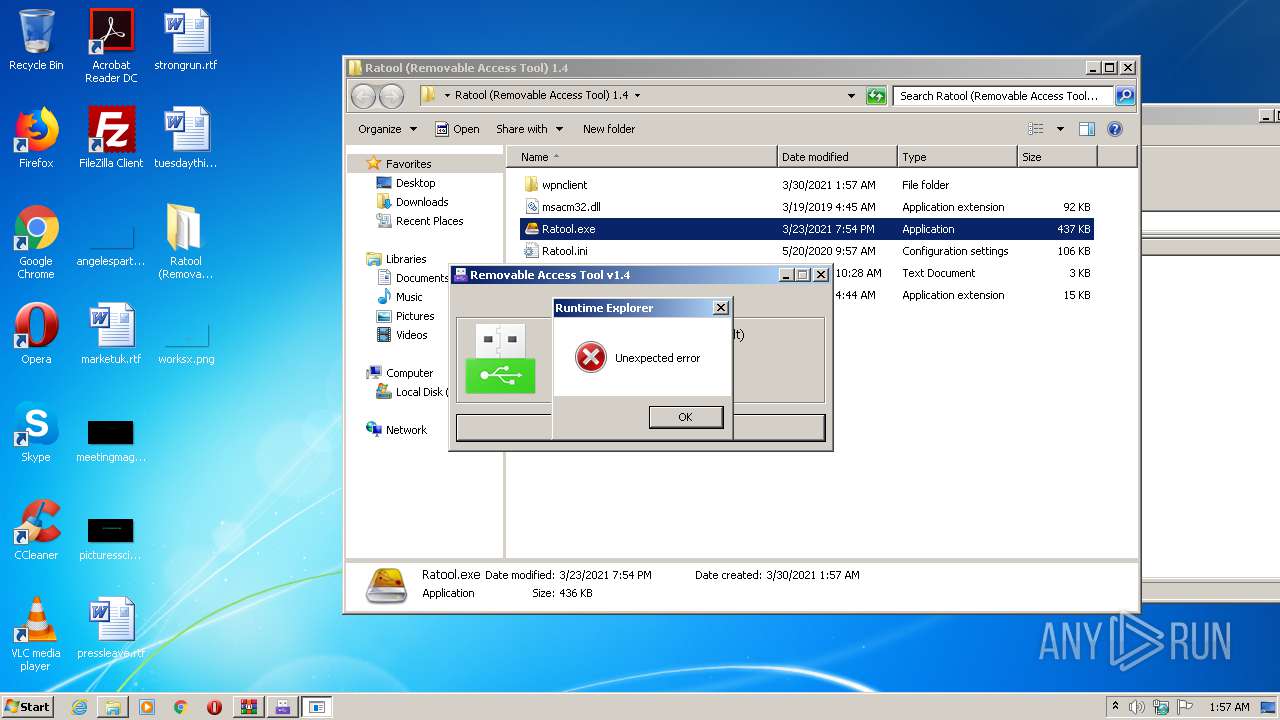
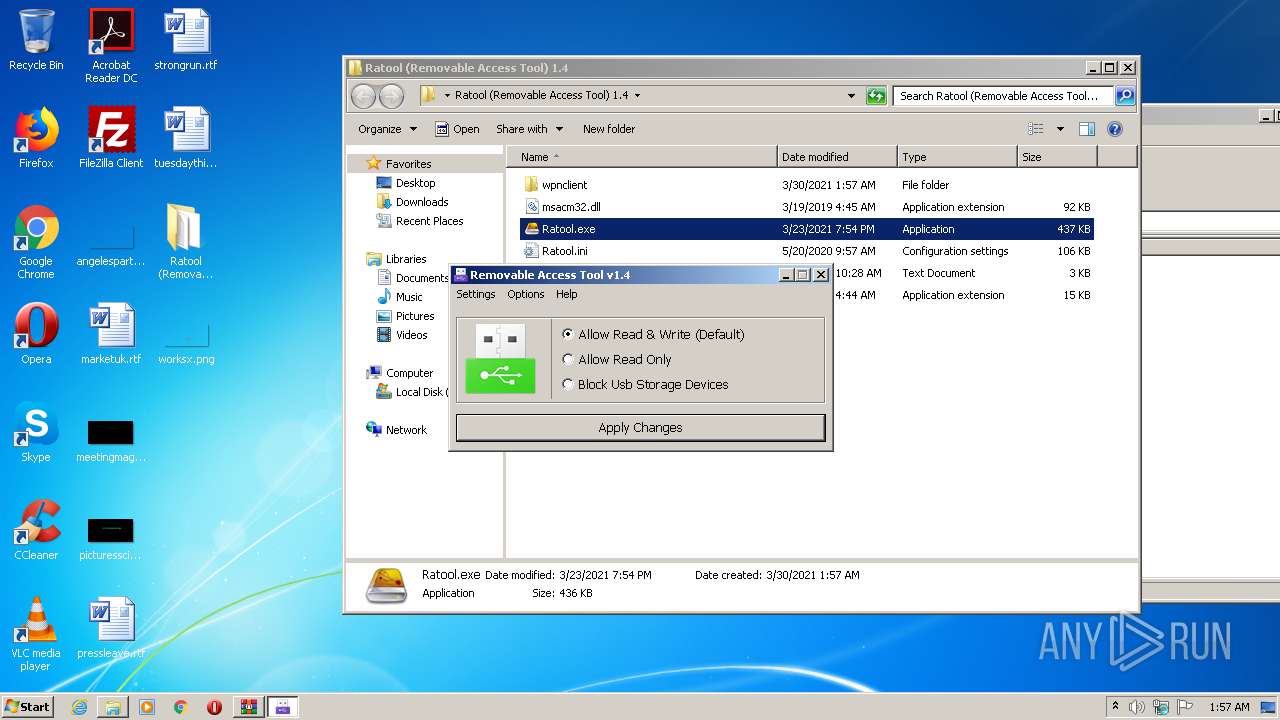
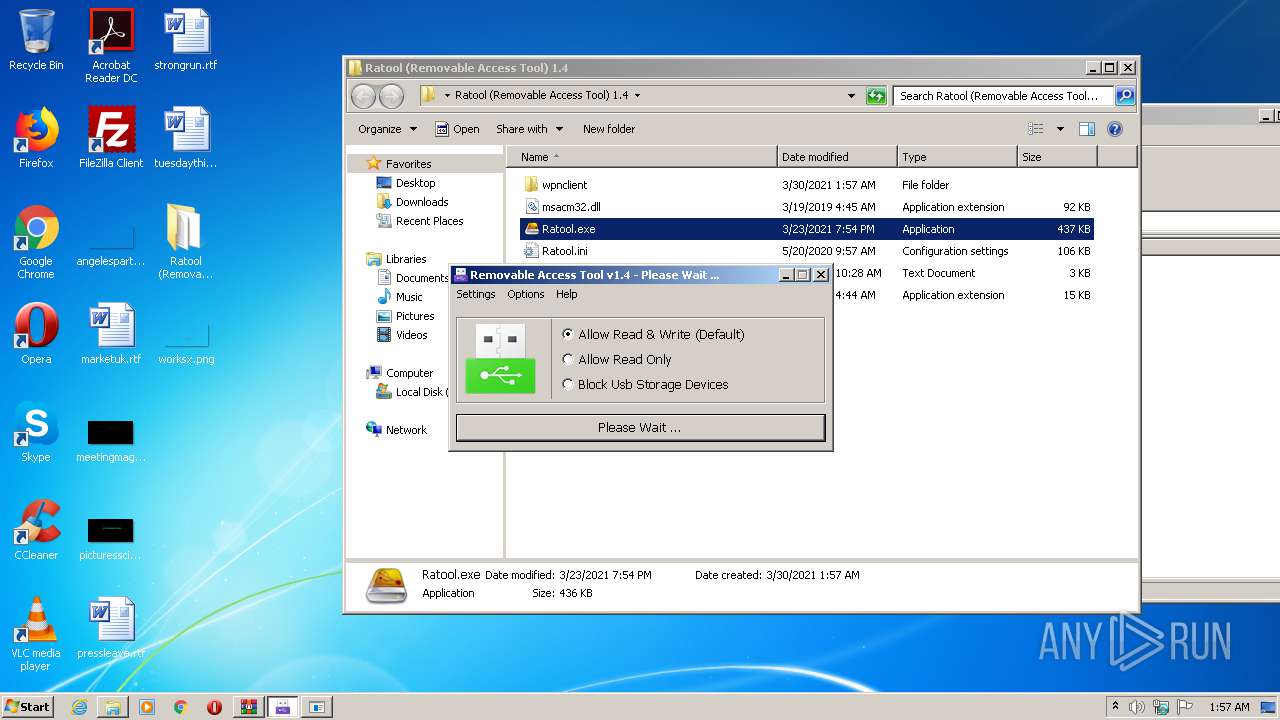
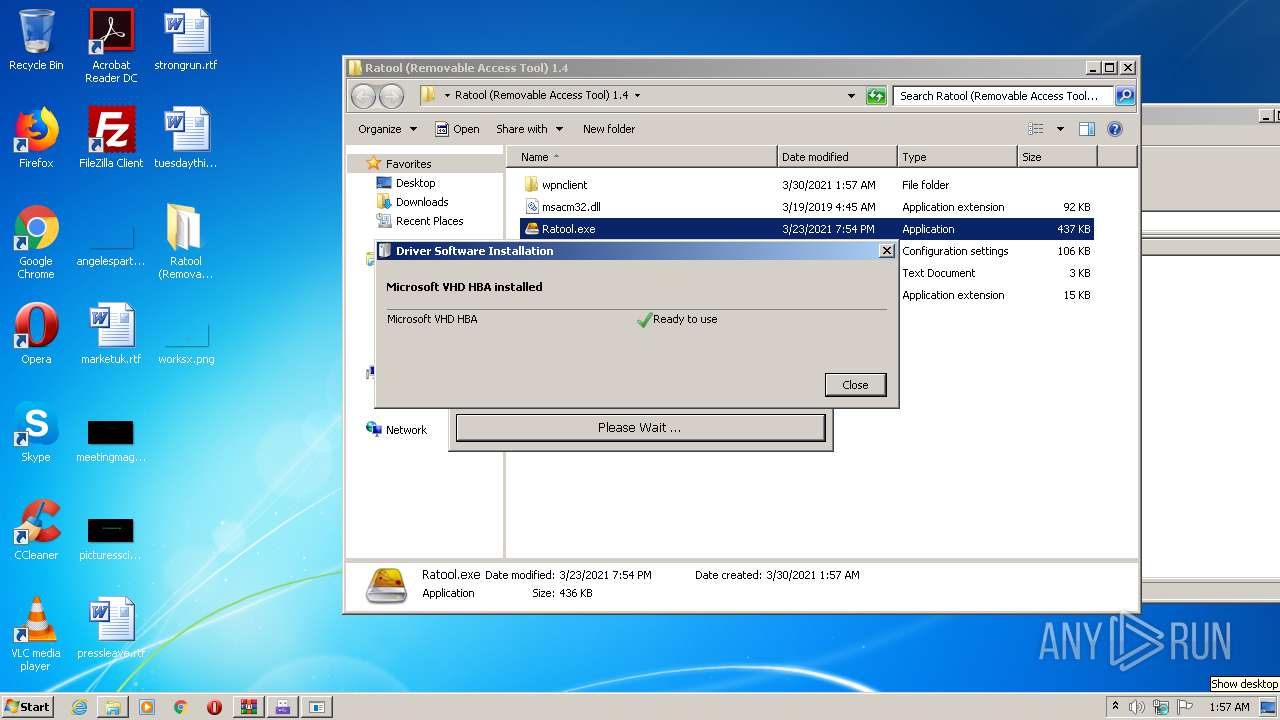
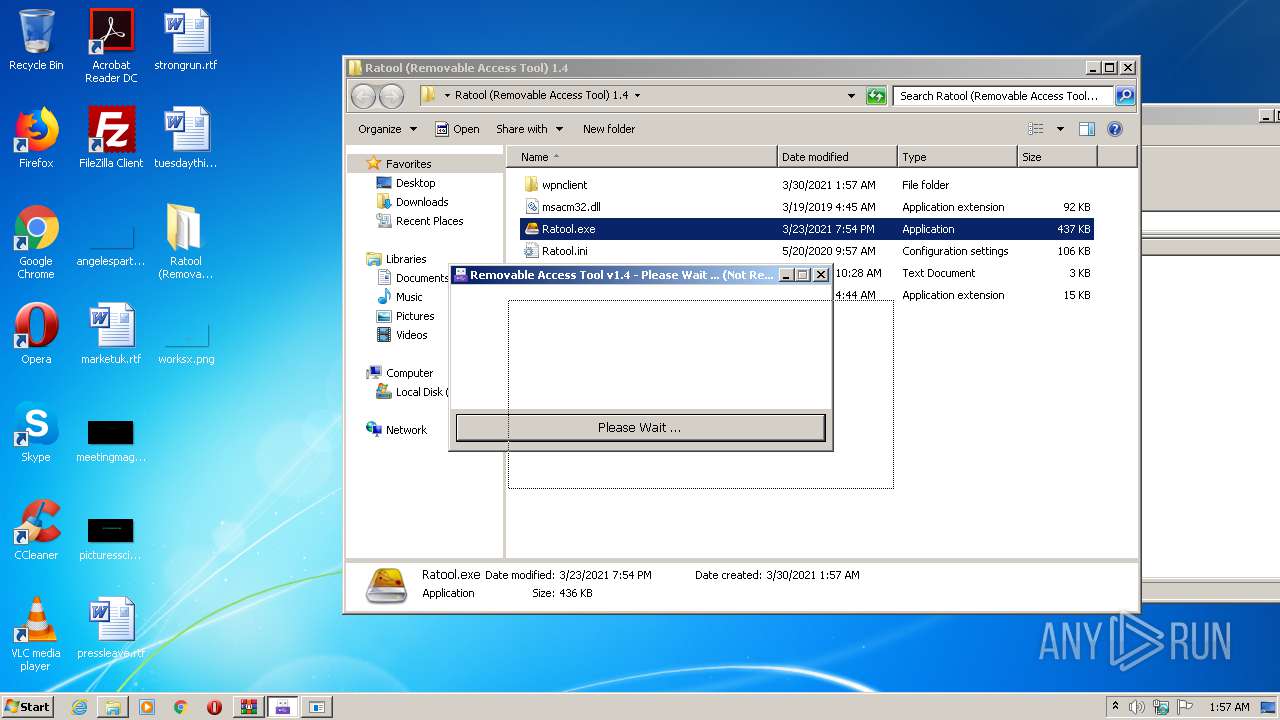
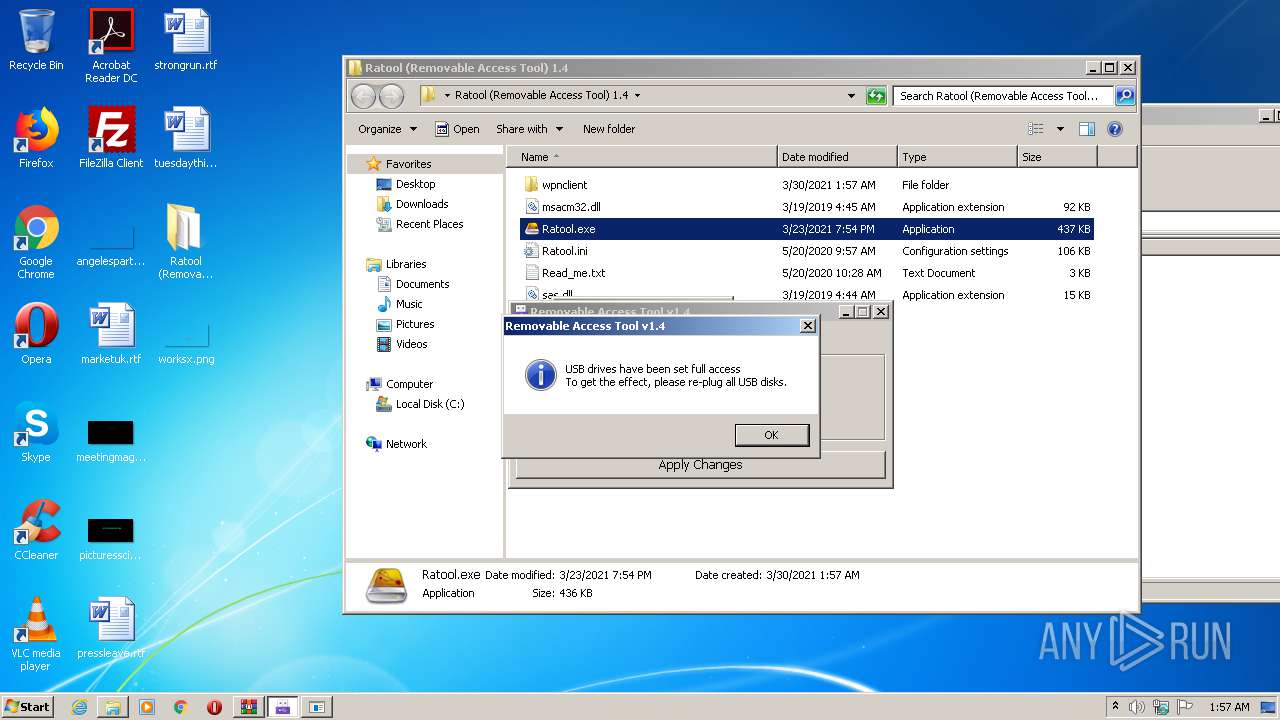
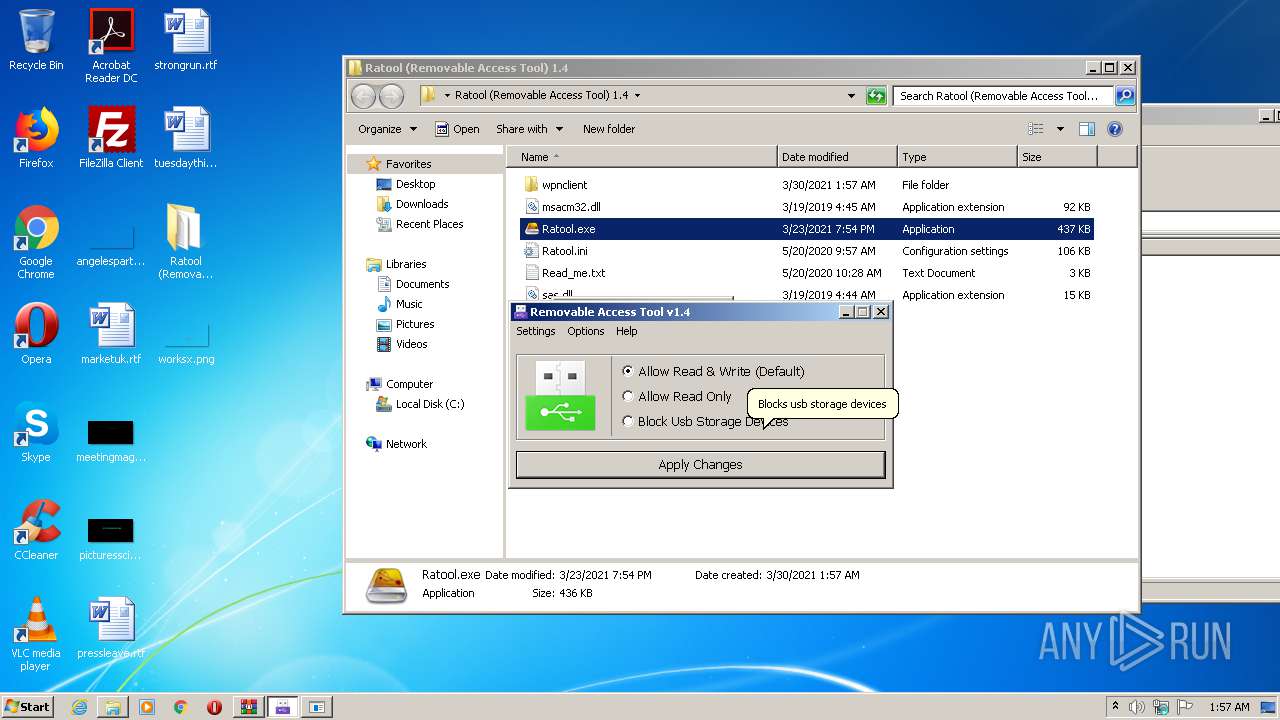
Manual execution by user
- Ratool.exe (PID: 952)
Dropped object may contain Bitcoin addresses
- Launcher.exe (PID: 608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
62
Monitored processes
17
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | rundll32.exe C:\Windows\system32\newdev.dll,pDiDeviceInstallNotification \\.\pipe\PNP_Device_Install_Pipe_1.{05433966-5e97-4286-9265-9f6455373b2b} "(null)" | C:\Windows\system32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 608 | "C:\Users\admin\Desktop\Ratool (Removable Access Tool) 1.4\wpnclient\Launcher.exe" | C:\Users\admin\Desktop\Ratool (Removable Access Tool) 1.4\wpnclient\Launcher.exe | Ratool.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 748 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Control Service Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
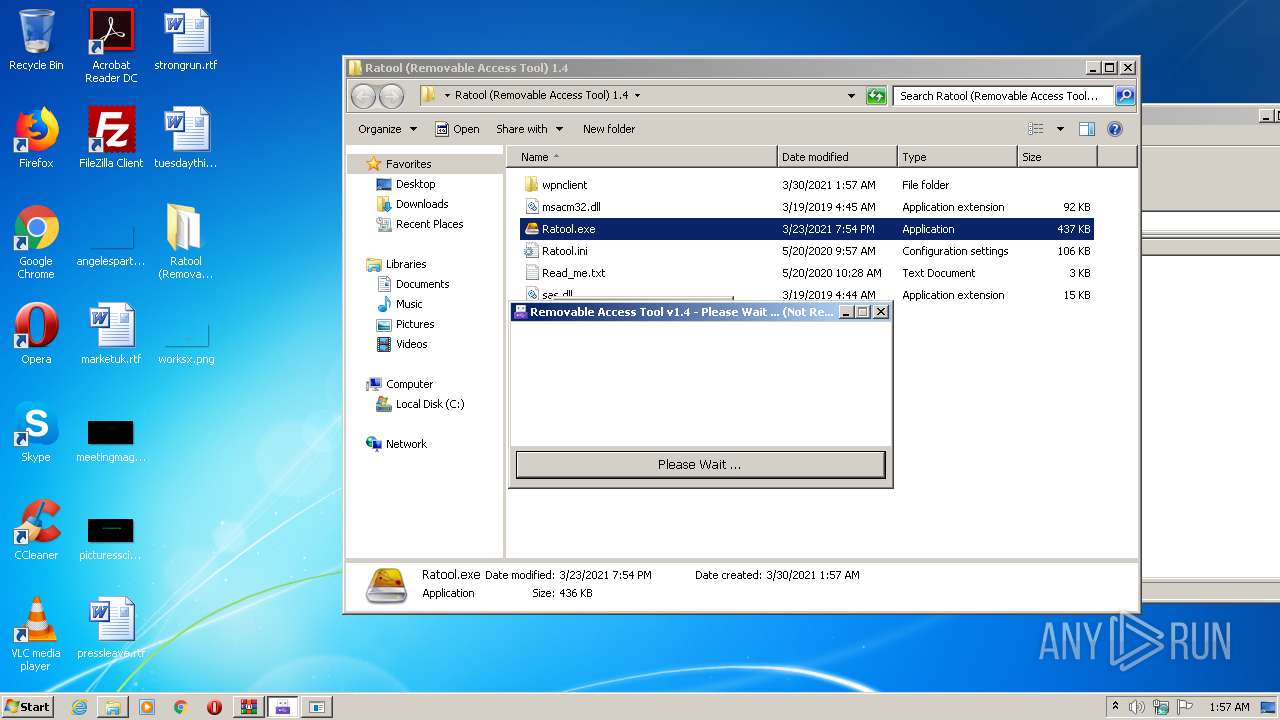
| 952 | "C:\Users\admin\Desktop\Ratool (Removable Access Tool) 1.4\Ratool.exe" | C:\Users\admin\Desktop\Ratool (Removable Access Tool) 1.4\Ratool.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Launcher Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1324 | "C:\Users\admin\Desktop\Ratool (Removable Access Tool) 1.4\wpnclient\WSDApi.exe" | C:\Users\admin\Desktop\Ratool (Removable Access Tool) 1.4\wpnclient\WSDApi.exe | Ratool.exe | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: Removable Access Tool Exit code: 0 Version: 1.4.0.0 Modules
| |||||||||||||||
| 1404 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Control Service Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 1664 | "C:\Windows\System32\dinotify.exe" pnpui.dll,SimplifiedDINotification | C:\Windows\System32\dinotify.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Device Installation Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1940 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2200 | "C:\Windows\IMF\Secure System Shell.exe" | C:\Windows\IMF\Secure System Shell.exe | — | Windows Services.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Secure System Shell Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2444 | "C:\Windows\IMF\Runtime Explorer.exe" | C:\Windows\IMF\Runtime Explorer.exe | — | Windows Services.exe | |||||||||||
User: admin Company: Control Service Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
1 110
Read events
990
Write events
120
Delete events
0
Modification events
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Ratool (Removable Access Tool) 1.4.rar | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3200) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (952) Ratool.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
13
Text files
78
Unknown types
4
Dropped files
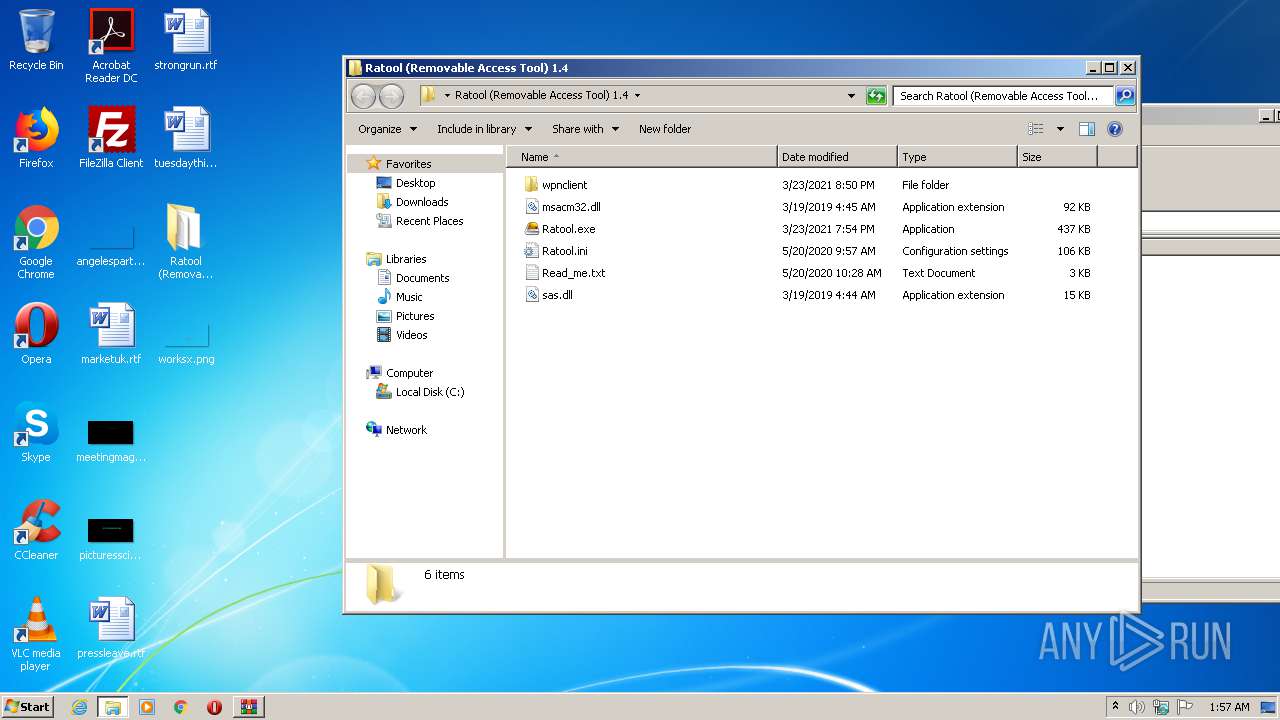
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\msacm32.dll | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\Ratool.exe | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\Ratool.ini | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\Read_me.txt | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\sas.dll | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\wpnclient\Ionic.Zip.dll | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\wpnclient\Launcher.exe | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\wpnclient\LICENCE.dat | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\wpnclient\msacm32.dll | — | |
MD5:— | SHA256:— | |||
| 3200 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3200.17152\Ratool (Removable Access Tool) 1.4\wpnclient\Ratool.ini | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report