| URL: | https://s.optnx.com/cimp.php?data=TVRZMU16QTJPVGsxTkh4aFlUUTBZalEwWldaaVltTXpPREUxTmpOa09XWTBabVEwTTJWbU5qRTNNdy0tfGh0dHBzOi8vZ28ueGx2aWlyZHIuY29tL3NtYXJ0cG9wL2QyZmZlNThiODQxZDEyOTc1YWUyOWE3ZjJhZjFkZDA0NmRiMjdlZmUyMzAwZDU0ODMzZGQ0NDRmNDkyY2UwMTIvP3NvdXJjZUlkPTQxNjY0OTZfMzQ1OTIzOV9QRVImbWVtYmVySWQ9b29kTmJOSFhYSE5aWkhQUlM0VzVIVVUxWFQwWE9wcXRycW1sbmRUWlZOSzUxVXRycHFiblhXdXBsZEs2VjBycWFIVVhVVjAxVE9vdW9ycHFyZEs2WjBycFhTdWxkTTZWMHJwblZUMjNXengxVFdUVlZVV1V1MTNvczJwcHIyejRwenJsdDMxM3JtdXMzbjFtbDRuNHNkVlBiZGJPN3Jzd2YuNF9zM09kSzZWMHJwWFN1bGRLNlYwcmcudy0mcDE9NDE2NjQ5NnxodHRwc3wxODEuNjYuMTc3LjIzNHxQRVJ8MTQ5fGhpdG9taS5sYXw1MTE1ODR8NjI4ODE3fDc5OTYzM3wzNDU5MjM5fDUwOHw0MTY2NDk2fDQ1ODY1MTAyfDQwfDk4fDB8MHw0M3w1Mjg5ODJ8OTZ8NzB8VVNEfFVTRHwxfDF8MjJ8fDF8UEVSfHwxNnw0fDF8fDUyODk4Mi41MTcxNTUzNzR8Y2UzN2Q0NDZkYWY0YTYwOGVjZTYxOTdlMmMxMGYyZjd8MXwwfGhpdG9taS5sYXwwfDMyODcwfDQ3NTEwfDB8MXwwfGV4Y2hhbmdlX2xpbmt8MHwwfDM5MzY0NTF8LTF8MHwzOTM2NDU2fHx8MXwxNDQwfHwwfDB8MHwwfDB8MHwxfDB8fDh8MXxNb3ppbGxhLzUuMCAoV2luZG93cyBOVCAxMC4wOyBXaW42NDsgeDY0KSBBcHBsZVdlYktpdC81MzcuMzYgKEtIVE1MLCBsaWtlIEdlY2tvKSBDaHJvbWUvMTAxLjAuNDk1MS42NCBTYWZhcmkvNTM3LjM2IEVkZy8xMDEuMC4xMjEwLjQ3fE9LfDI1MGRhYTU3MzVmODY4YjZiNjViY2I2ZGE3NTc0MzFm |
| Full analysis: | https://app.any.run/tasks/941c08ae-7e91-4a36-a502-6d21dba1faea |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 18:07:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 59BE3643915DAF5E3746EFB459964A4D |
| SHA1: | 84B1A8D83A7A1A38705295A7C2A586BD3002D395 |
| SHA256: | 497877D5B0089CA41AC1CE89605535902306FED825B4388BF80088B33D2C0DE0 |
| SSDEEP: | 24:2DReJ/BbqfoEfZNLL5dbudKABBb7XyFEkaC+Q809CQrjweI0PY:3bqfoEfzLgpBB/XxkbvtCQPO0PY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3340)
INFO
Checks supported languages
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2912)
Checks Windows Trust Settings
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2912)
Reads the computer name
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2912)
Reads settings of System Certificates
- iexplore.exe (PID: 3340)
- iexplore.exe (PID: 2912)
Creates files in the user directory
- iexplore.exe (PID: 3340)
Reads internet explorer settings
- iexplore.exe (PID: 3340)
Changes internet zones settings
- iexplore.exe (PID: 2912)
Application launched itself
- iexplore.exe (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2912 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://s.optnx.com/cimp.php?data=TVRZMU16QTJPVGsxTkh4aFlUUTBZalEwWldaaVltTXpPREUxTmpOa09XWTBabVEwTTJWbU5qRTNNdy0tfGh0dHBzOi8vZ28ueGx2aWlyZHIuY29tL3NtYXJ0cG9wL2QyZmZlNThiODQxZDEyOTc1YWUyOWE3ZjJhZjFkZDA0NmRiMjdlZmUyMzAwZDU0ODMzZGQ0NDRmNDkyY2UwMTIvP3NvdXJjZUlkPTQxNjY0OTZfMzQ1OTIzOV9QRVImbWVtYmVySWQ9b29kTmJOSFhYSE5aWkhQUlM0VzVIVVUxWFQwWE9wcXRycW1sbmRUWlZOSzUxVXRycHFiblhXdXBsZEs2VjBycWFIVVhVVjAxVE9vdW9ycHFyZEs2WjBycFhTdWxkTTZWMHJwblZUMjNXengxVFdUVlZVV1V1MTNvczJwcHIyejRwenJsdDMxM3JtdXMzbjFtbDRuNHNkVlBiZGJPN3Jzd2YuNF9zM09kSzZWMHJwWFN1bGRLNlYwcmcudy0mcDE9NDE2NjQ5NnxodHRwc3wxODEuNjYuMTc3LjIzNHxQRVJ8MTQ5fGhpdG9taS5sYXw1MTE1ODR8NjI4ODE3fDc5OTYzM3wzNDU5MjM5fDUwOHw0MTY2NDk2fDQ1ODY1MTAyfDQwfDk4fDB8MHw0M3w1Mjg5ODJ8OTZ8NzB8VVNEfFVTRHwxfDF8MjJ8fDF8UEVSfHwxNnw0fDF8fDUyODk4Mi41MTcxNTUzNzR8Y2UzN2Q0NDZkYWY0YTYwOGVjZTYxOTdlMmMxMGYyZjd8MXwwfGhpdG9taS5sYXwwfDMyODcwfDQ3NTEwfDB8MXwwfGV4Y2hhbmdlX2xpbmt8MHwwfDM5MzY0NTF8LTF8MHwzOTM2NDU2fHx8MXwxNDQwfHwwfDB8MHwwfDB8MHwxfDB8fDh8MXxNb3ppbGxhLzUuMCAoV2luZG93cyBOVCAxMC4wOyBXaW42NDsgeDY0KSBBcHBsZVdlYktpdC81MzcuMzYgKEtIVE1MLCBsaWtlIEdlY2tvKSBDaHJvbWUvMTAxLjAuNDk1MS42NCBTYWZhcmkvNTM3LjM2IEVkZy8xMDEuMC4xMjEwLjQ3fE9LfDI1MGRhYTU3MzVmODY4YjZiNjViY2I2ZGE3NTc0MzFm" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3340 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2912 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
12 678
Read events
12 562
Write events
116
Delete events
0
Modification events
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960756 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960756 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2912) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
11
Text files
27
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\cimp[1].htm | html | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WRRLUMTG.txt | text | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\P1LBFZ1G.txt | text | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0TOVLBPY.txt | text | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3340 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5W06L1BU.txt | text | |
MD5:— | SHA256:— | |||
| 2912 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
39
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2912 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 13.225.84.68:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
2912 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3340 | iexplore.exe | GET | 200 | 18.66.242.45:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3340 | iexplore.exe | GET | 200 | 18.66.242.155:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3340 | iexplore.exe | GET | 200 | 96.16.145.230:80 | http://x1.c.lencr.org/ | US | der | 717 b | whitelisted |
2912 | iexplore.exe | GET | 200 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9cb9948fc2784e09 | US | compressed | 4.70 Kb | whitelisted |
2912 | iexplore.exe | GET | 200 | 23.216.77.69:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?62193dec85ba3f97 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3340 | iexplore.exe | 95.211.229.245:443 | s.optnx.com | LeaseWeb Netherlands B.V. | NL | suspicious |
3340 | iexplore.exe | 95.211.229.248:443 | s.optnx.com | LeaseWeb Netherlands B.V. | NL | suspicious |
3340 | iexplore.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
3340 | iexplore.exe | 172.64.145.216:443 | go.xlviirdr.com | — | US | suspicious |
3340 | iexplore.exe | 104.16.62.52:443 | cdn.strpst.com | Cloudflare Inc | US | unknown |
— | — | 104.16.62.52:443 | cdn.strpst.com | Cloudflare Inc | US | unknown |
3340 | iexplore.exe | 13.225.84.68:80 | o.ss2.us | — | US | unknown |
3340 | iexplore.exe | 52.222.206.118:443 | cdn.amplitude.com | Amazon.com, Inc. | US | suspicious |
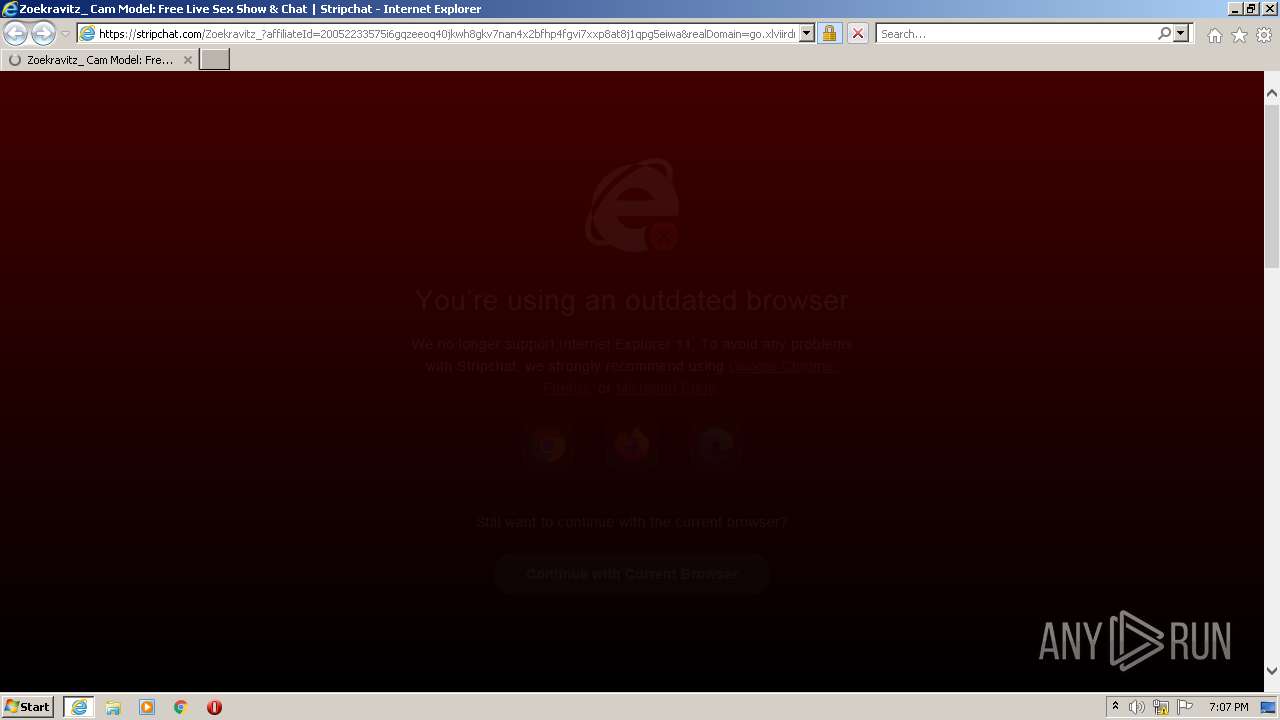
3340 | iexplore.exe | 104.19.183.41:443 | stripchat.com | Cloudflare Inc | US | unknown |
2912 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s.optnx.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
go.xlviirdr.com |
| suspicious |
stripchat.com |
| malicious |
cdn.strpst.com |
| malicious |
cdn.amplitude.com |
| whitelisted |