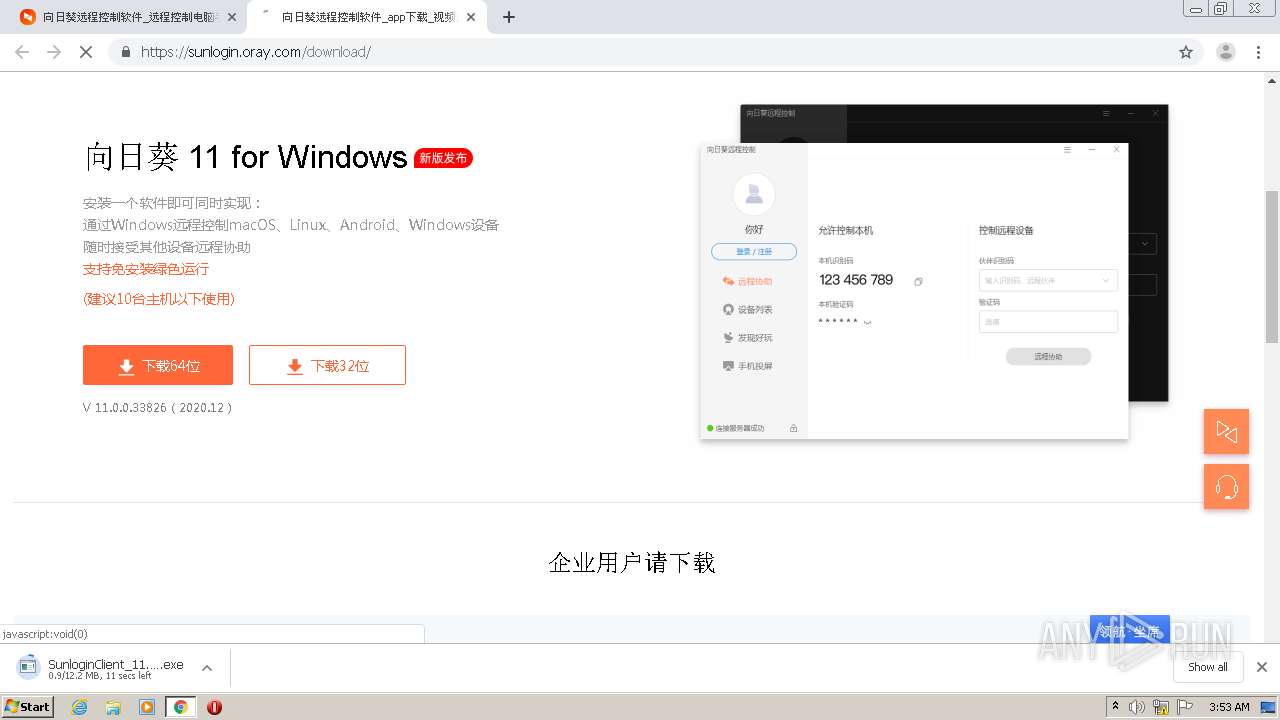
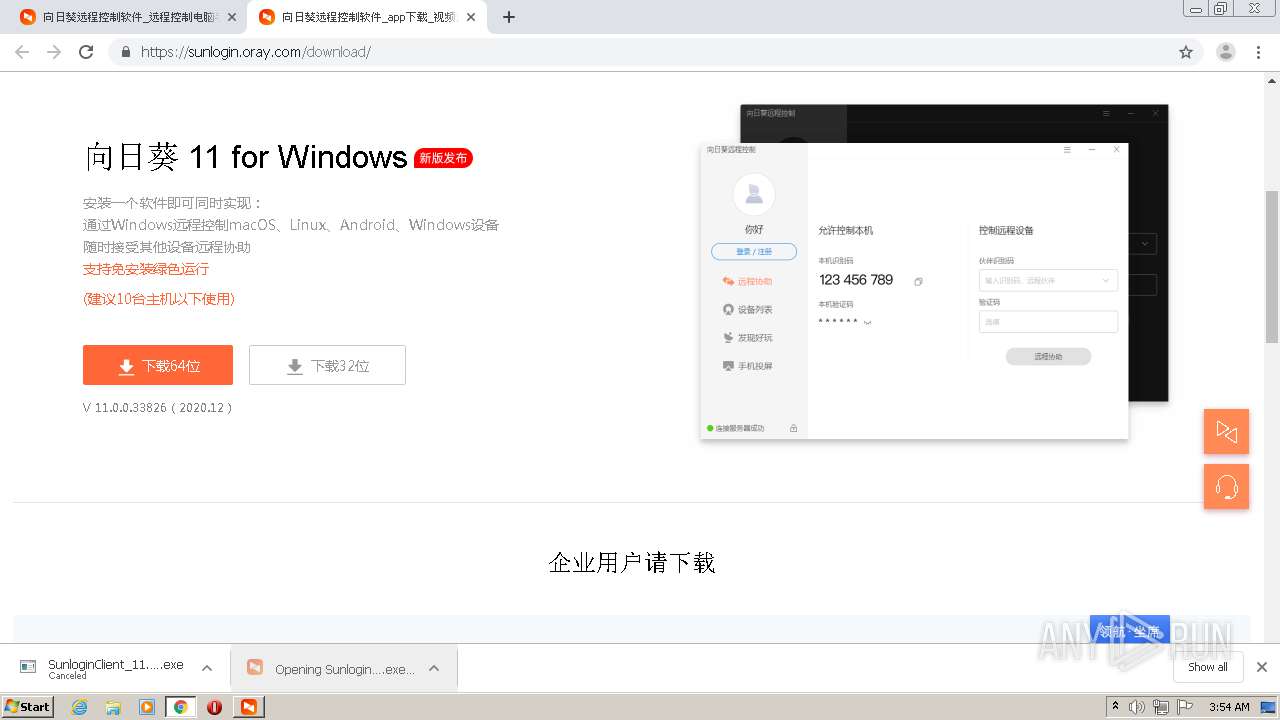
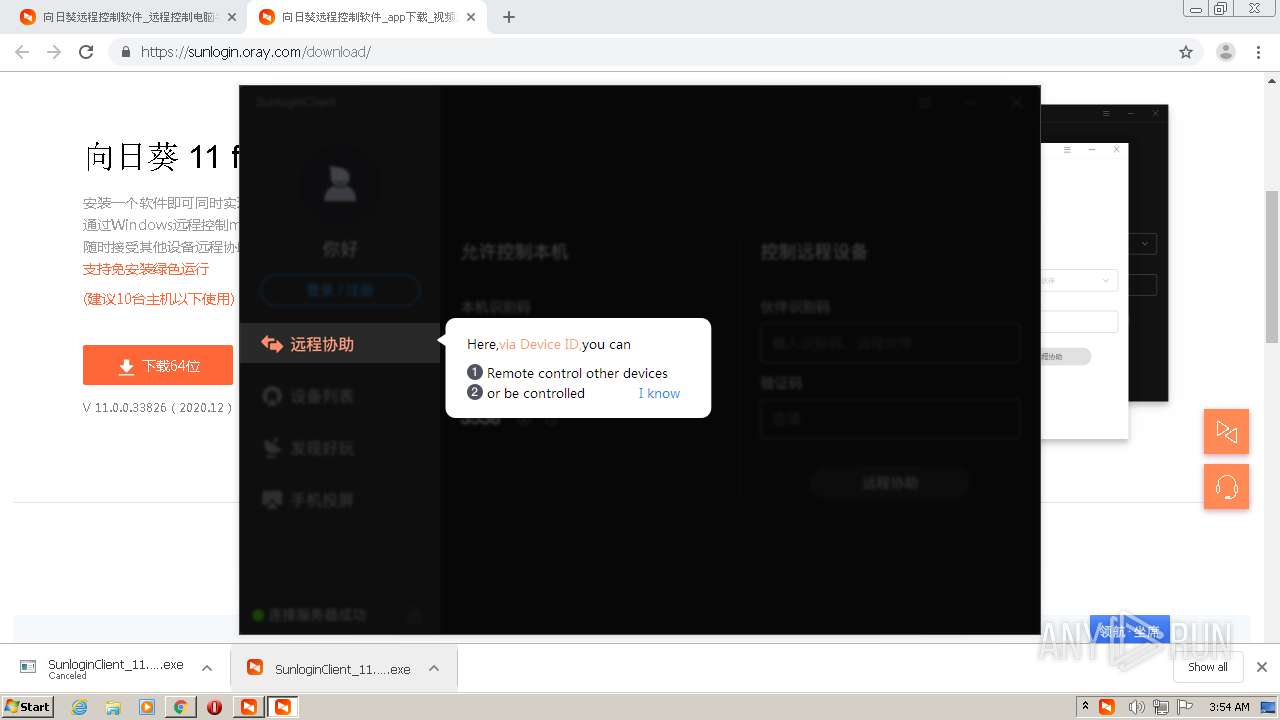
| URL: | https://sunlogin.oray.com/ |
| Full analysis: | https://app.any.run/tasks/e5f27be4-1146-4e62-a14c-4b19e733cce8 |
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2020, 03:52:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8B12B7A9ADF7DB3533A2C7CD80BBE39E |
| SHA1: | 4E36D0656716007EAD2E6E68E6F888D8A44332B2 |
| SHA256: | 49690E1C1DC21237778BA4DB3EDC19D02898FF6059036B9682C5AA926529FD8F |
| SSDEEP: | 3:N8d9KMEcLGGn:2qmLGG |
MALICIOUS
Application was dropped or rewritten from another process
- SunloginClient_11.0.0.33826.exe (PID: 1588)
- SunloginClient_11.0.0.33826.exe (PID: 788)
- SunloginClient.exe (PID: 3092)
- devcon.exe (PID: 3472)
- SunloginClient.exe (PID: 3084)
- SunloginClient.exe (PID: 3980)
- SunloginClient.exe (PID: 3280)
- SunloginClient_11.0.0.33826.exe (PID: 1716)
- sunloginclient.exe (PID: 3104)
Changes the autorun value in the registry
- SunloginClient_11.0.0.33826.exe (PID: 788)
- SunloginClient.exe (PID: 3084)
Changes settings of System certificates
- devcon.exe (PID: 3472)
Drops executable file immediately after starts
- SunloginClient.exe (PID: 3084)
- DrvInst.exe (PID: 3528)
SUSPICIOUS
Drops a file with a compile date too recent
- chrome.exe (PID: 2560)
- SunloginClient_11.0.0.33826.exe (PID: 788)
- SunloginClient.exe (PID: 3084)
- DrvInst.exe (PID: 1312)
- DrvInst.exe (PID: 3528)
- devcon.exe (PID: 3472)
Application launched itself
- SunloginClient_11.0.0.33826.exe (PID: 1588)
- cmd.exe (PID: 1144)
- SunloginClient.exe (PID: 3084)
Cleans NTFS data-stream (Zone Identifier)
- SunloginClient_11.0.0.33826.exe (PID: 1588)
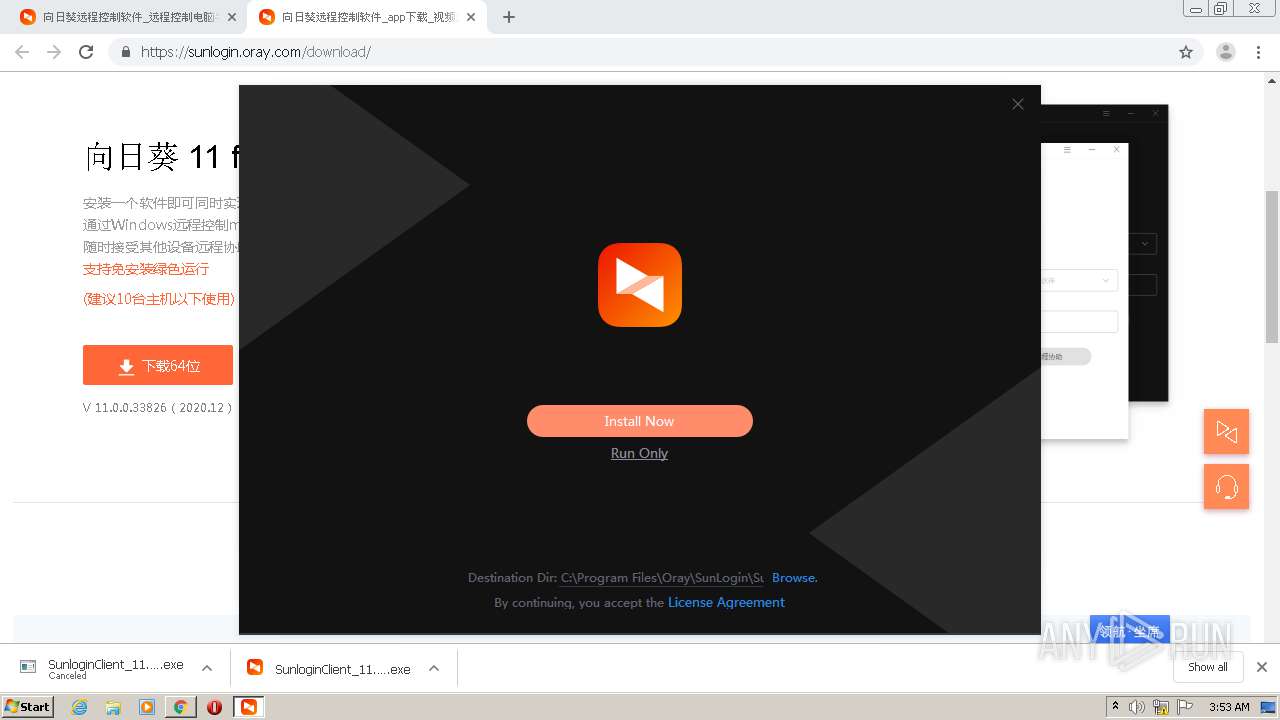
Creates a directory in Program Files
- SunloginClient_11.0.0.33826.exe (PID: 788)
- SunloginClient.exe (PID: 3084)
Executable content was dropped or overwritten
- chrome.exe (PID: 2560)
- SunloginClient_11.0.0.33826.exe (PID: 788)
- devcon.exe (PID: 3472)
- SunloginClient.exe (PID: 3084)
- DrvInst.exe (PID: 3528)
Creates files in the program directory
- SunloginClient_11.0.0.33826.exe (PID: 788)
- SunloginClient.exe (PID: 3084)
- SunloginClient.exe (PID: 3980)
- sunloginclient.exe (PID: 3104)
Drops a file with too old compile date
- SunloginClient_11.0.0.33826.exe (PID: 788)
Drops a file that was compiled in debug mode
- SunloginClient_11.0.0.33826.exe (PID: 788)
- devcon.exe (PID: 3472)
- DrvInst.exe (PID: 3528)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 1144)
- SunloginClient_11.0.0.33826.exe (PID: 788)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2396)
- cmd.exe (PID: 2216)
- cmd.exe (PID: 3120)
- cmd.exe (PID: 2056)
- cmd.exe (PID: 3500)
- cmd.exe (PID: 1796)
- cmd.exe (PID: 3684)
Starts itself from another location
- SunloginClient_11.0.0.33826.exe (PID: 788)
- SunloginClient_11.0.0.33826.exe (PID: 1716)
Executed as Windows Service
- SunloginClient.exe (PID: 3084)
Executed via COM
- DrvInst.exe (PID: 1312)
- DrvInst.exe (PID: 3528)
Creates a software uninstall entry
- SunloginClient_11.0.0.33826.exe (PID: 788)
Adds / modifies Windows certificates
- devcon.exe (PID: 3472)
Removes files from Windows directory
- DrvInst.exe (PID: 1312)
- DrvInst.exe (PID: 3528)
Creates files in the Windows directory
- DrvInst.exe (PID: 1312)
- DrvInst.exe (PID: 3528)
Creates files in the driver directory
- DrvInst.exe (PID: 1312)
- DrvInst.exe (PID: 3528)
INFO
Application launched itself
- chrome.exe (PID: 2560)
Reads the hosts file
- chrome.exe (PID: 2560)
- chrome.exe (PID: 1952)
Reads settings of System Certificates
- DrvInst.exe (PID: 1312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
38
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
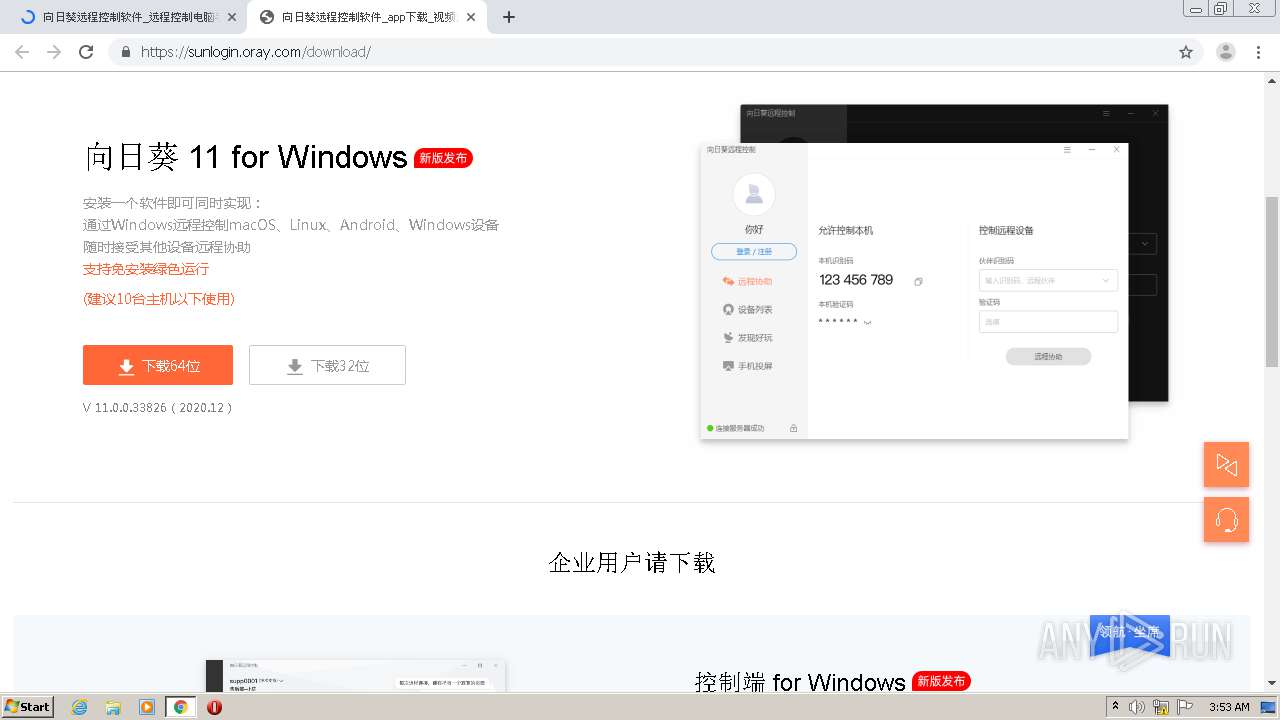
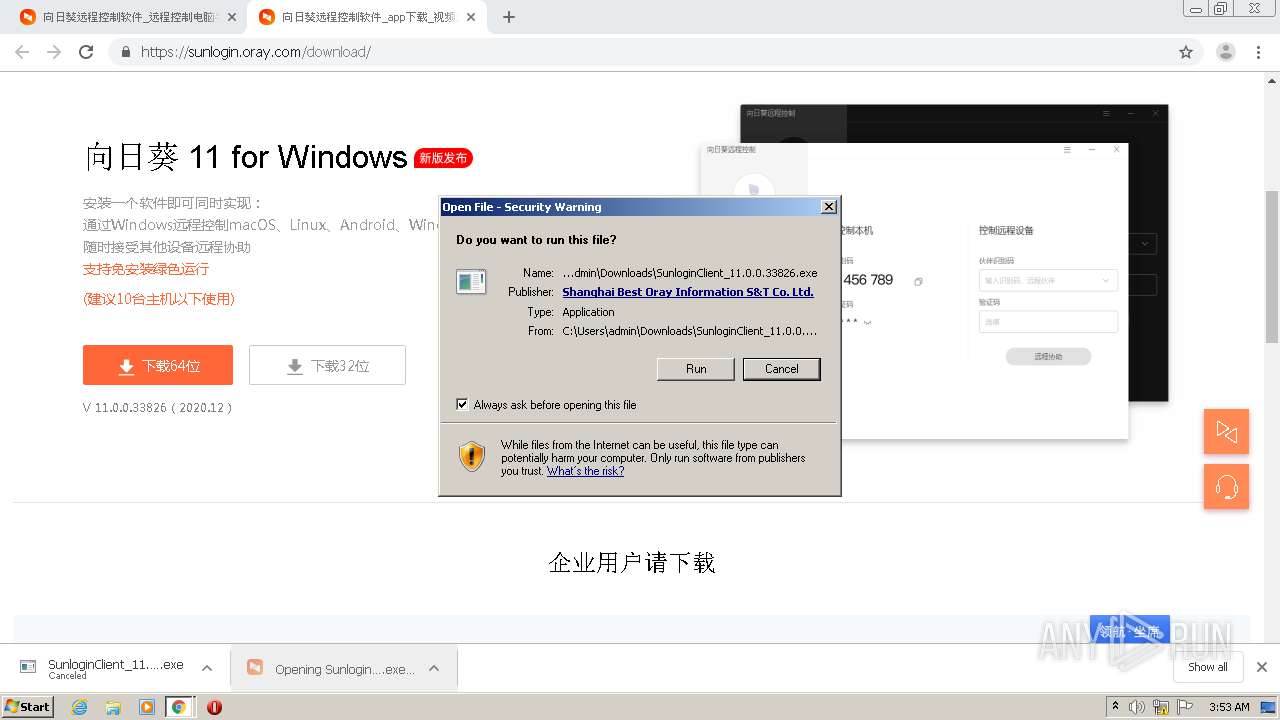
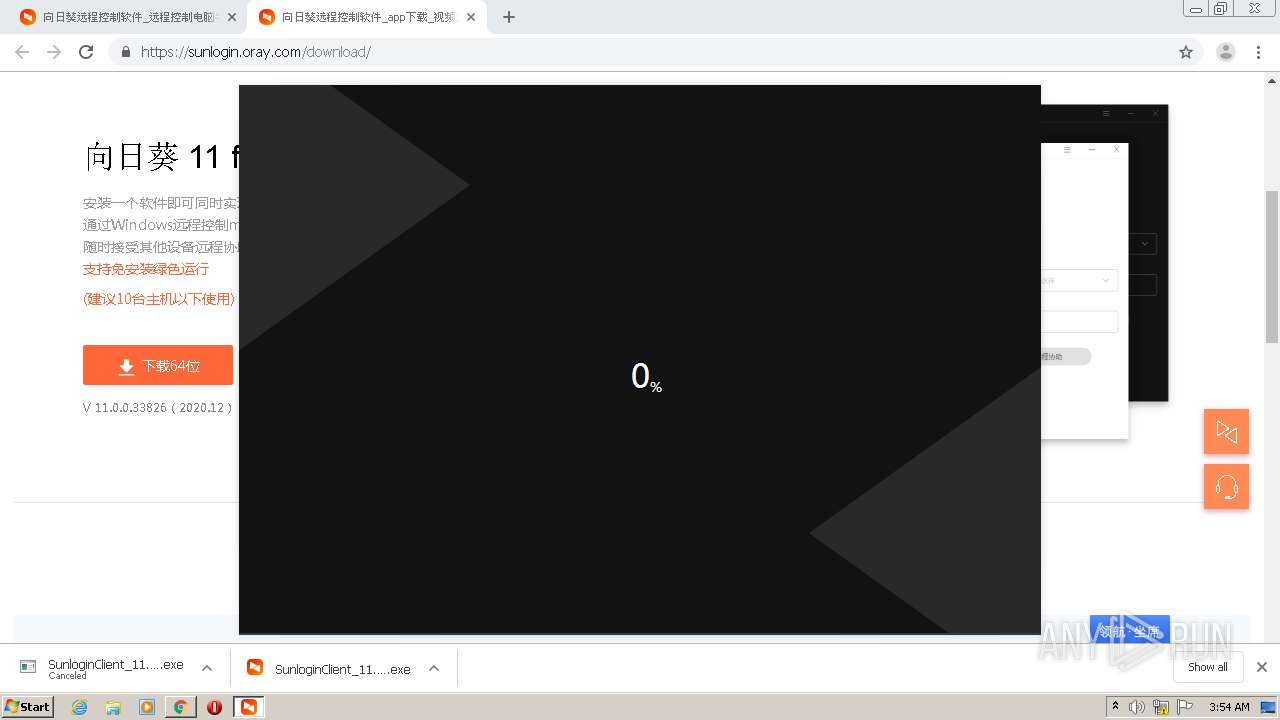
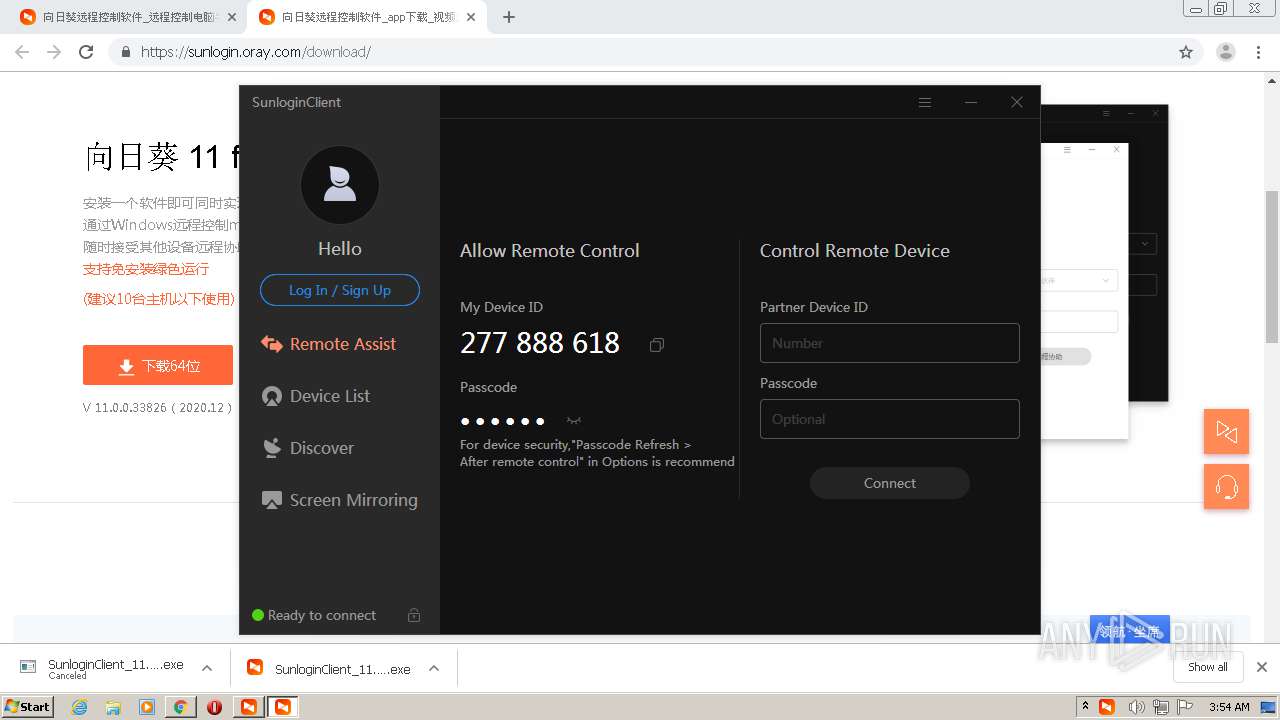
| 788 | "C:\Users\admin\Downloads\SunloginClient_11.0.0.33826.exe" --mod=install --admin=1 | C:\Users\admin\Downloads\SunloginClient_11.0.0.33826.exe | SunloginClient_11.0.0.33826.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: HIGH Description: SunloginClient Exit code: 0 Version: 11.0.0.33826 Modules
| |||||||||||||||
| 856 | netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=public | C:\Windows\system32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2540 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | cmd /c install.bat SunloginClient | C:\Windows\system32\cmd.exe | — | SunloginClient_11.0.0.33826.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1312 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{33db60b3-df5d-0c85-cfb5-6e59d67ccb05}\oraymir.inf" "0" "6e6179ed3" "000003D8" "WinSta0\Default" "000004D4" "208" "c:\program files\oray\sunlogin\sunloginclient\driver\mirror" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
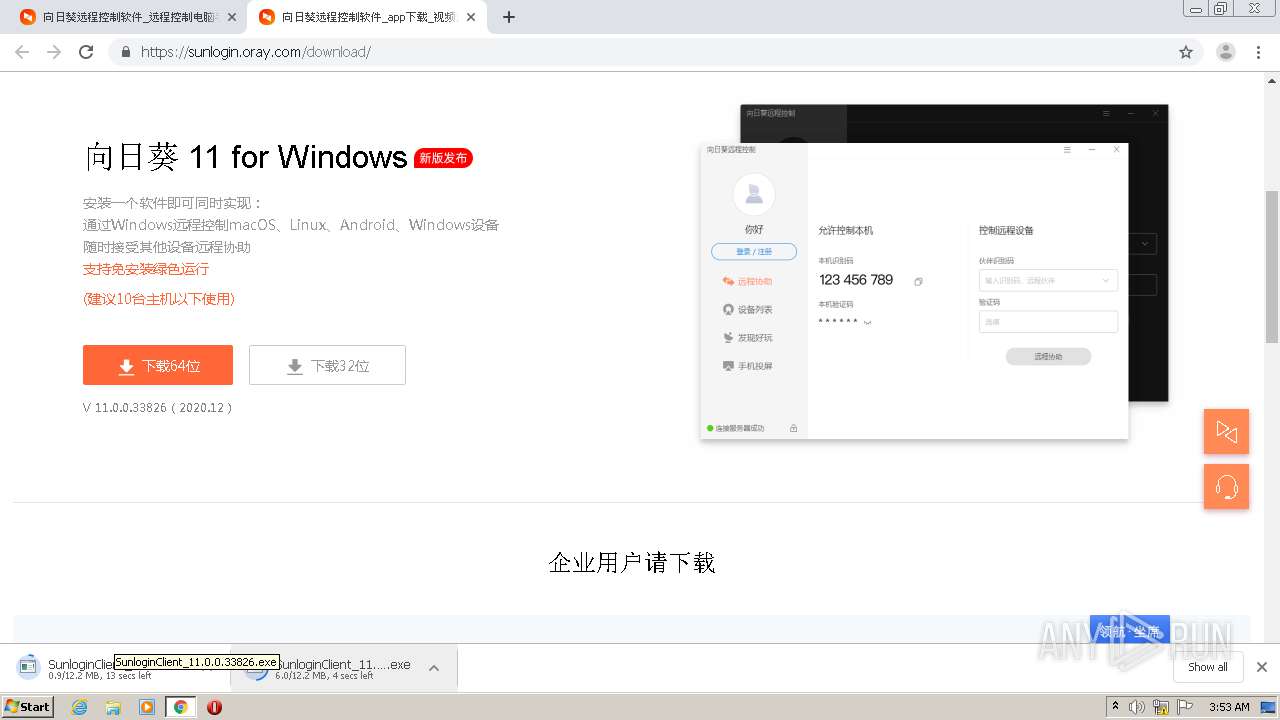
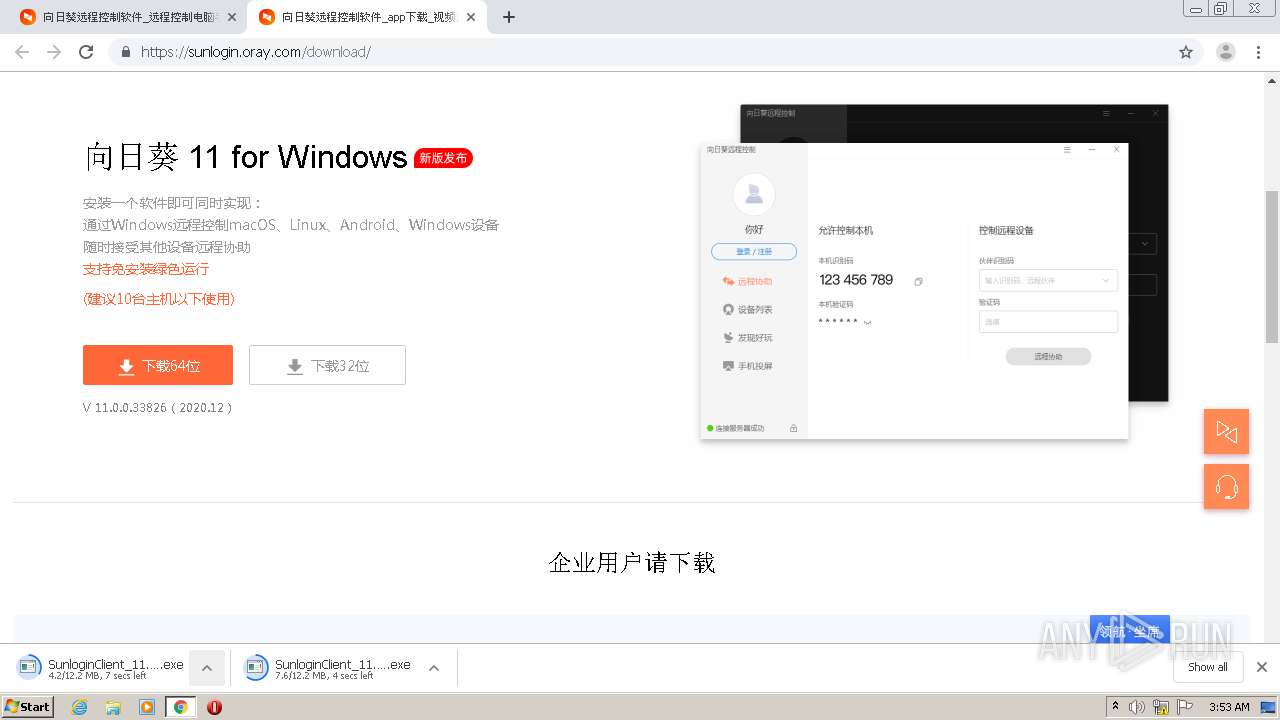
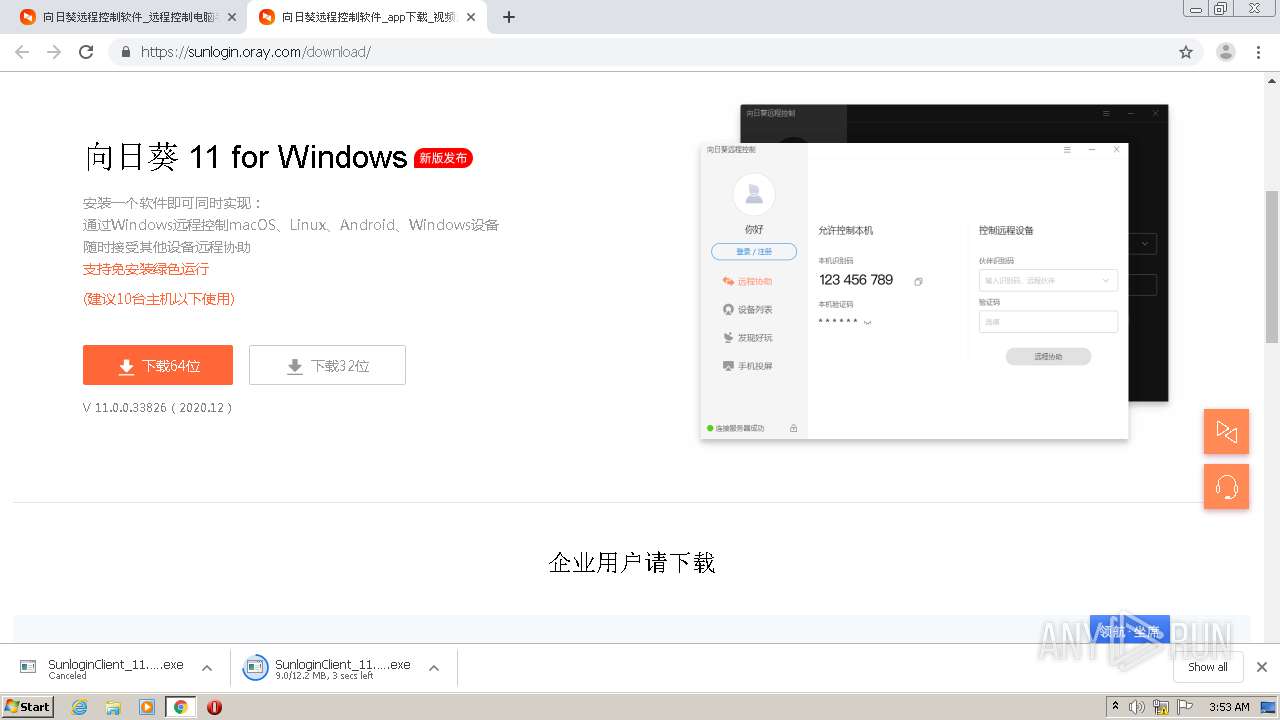
| 1588 | "C:\Users\admin\Downloads\SunloginClient_11.0.0.33826.exe" | C:\Users\admin\Downloads\SunloginClient_11.0.0.33826.exe | chrome.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: MEDIUM Description: SunloginClient Exit code: 1 Version: 11.0.0.33826 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,5254729506309061426,3696805421618380405,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4711754189590573925 --mojo-platform-channel-handle=1048 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1716 | "C:\Users\admin\Downloads\SunloginClient_11.0.0.33826.exe" | C:\Users\admin\Downloads\SunloginClient_11.0.0.33826.exe | chrome.exe | ||||||||||||
User: admin Company: Shanghai Best Oray Information Technology Co., Ltd. Integrity Level: MEDIUM Description: SunloginClient Exit code: 1 Version: 11.0.0.33826 Modules
| |||||||||||||||
| 1796 | cmd /c netsh advfirewall firewall add rule name="SunloginClient" dir=in action=allow program="C:\Program Files\Oray\SunLogin\SunloginClient\SunloginClient.exe" protocol=udp enable=yes profile=private | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,5254729506309061426,3696805421618380405,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3477977809047151801 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 083
Read events
1 627
Write events
451
Delete events
5
Modification events
| (PID) Process: | (1012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2560-13253601172915750 |
Value: 259 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
33
Suspicious files
71
Text files
211
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FE95695-A00.pma | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0429e3ee-50fb-43b3-8185-086d6ef3423a.tmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1541a6.TMP | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15438a.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
68
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3084 | SunloginClient.exe | GET | 200 | 47.246.43.225:80 | http://download.oray.com/plugins/node-1.0.1.7z | US | compressed | 5.78 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
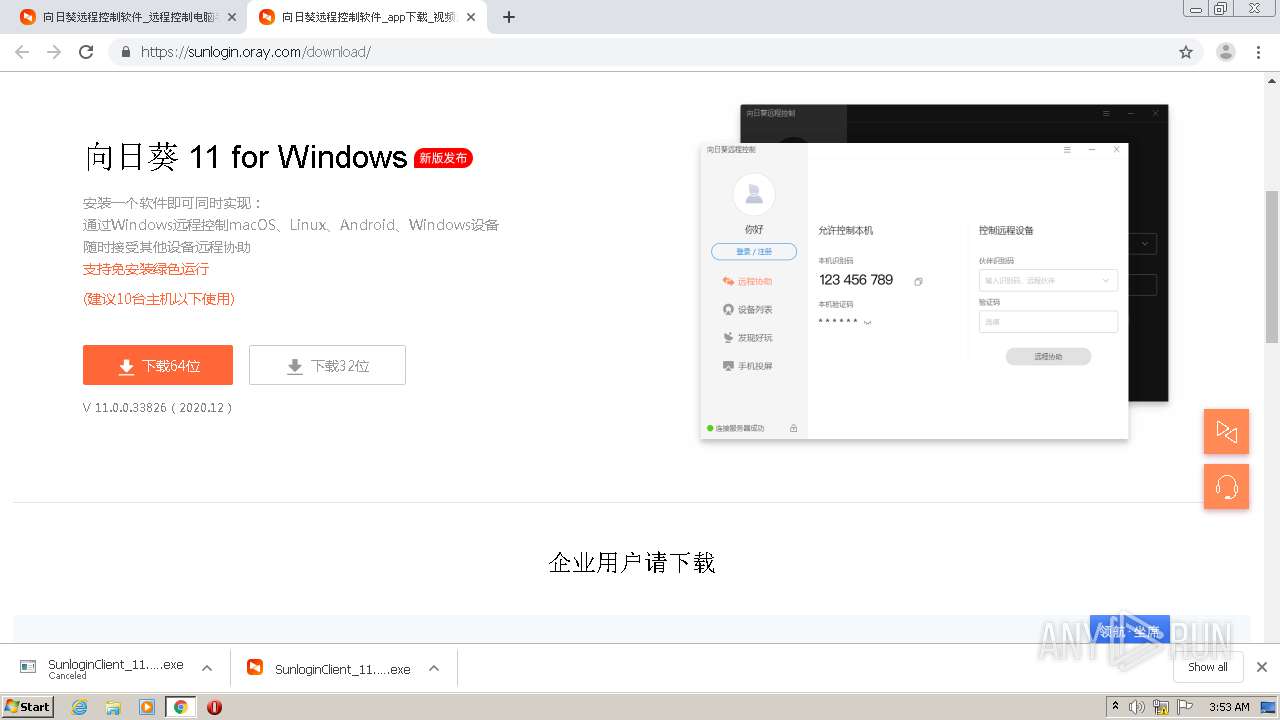
788 | SunloginClient_11.0.0.33826.exe | 116.62.101.24:443 | sl-tk.oray.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
1952 | chrome.exe | 47.110.217.173:443 | sunlogin.oray.com | — | CN | unknown |
1952 | chrome.exe | 163.181.56.212:443 | res.orayimg.com | — | US | suspicious |
1952 | chrome.exe | 108.177.8.84:443 | accounts.google.com | Google Inc. | US | unknown |
1952 | chrome.exe | 47.246.43.224:443 | res.orayimg.com | — | US | malicious |
1952 | chrome.exe | 101.37.127.85:443 | webchat.7moor.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
1952 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1952 | chrome.exe | 110.242.68.204:443 | fxgate.baidu.com | CHINA UNICOM China169 Backbone | CN | unknown |
1952 | chrome.exe | 103.235.46.191:443 | hm.baidu.com | Beijing Baidu Netcom Science and Technology Co., Ltd. | HK | suspicious |
1952 | chrome.exe | 121.196.50.151:443 | client-api.oray.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sunlogin.oray.com |
| suspicious |
accounts.google.com |
| shared |
res.orayimg.com |
| malicious |
webchat.7moor.com |
| unknown |
cdn.orayimg.com |
| malicious |
static.orayimg.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
hm.baidu.com |
| whitelisted |
fxgate.baidu.com |
| unknown |
fclog.baidu.com |
| unknown |
Threats
Process | Message |
|---|---|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:44.509 - Info - SetDPIAwareness isn't support.
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:45.533 - Info - SetDPIAwareness isn't support.
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:48.470 - Info - [http call3] new call id:1, url:https://sl-tk.oray.com/track
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:48.471 - Info - [http call3] id:1 create new connection : https://sl-tk.oray.com:443
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:48.670 - Info - attempt to connect server sl-tk.oray.com:443(116.62.101.24:443)
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:49.336 = Debug = ! This certificate has no flags
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:49.336 = Debug = ! This certificate has no flags
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:49.336 = Debug = ! This certificate has no flags
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:49.601 = Debug = POST /track HTTP/1.1
User-Agent: SensorsAnalytics CPP SDK 0.3
Accept: */*
Host: sl-tk.oray.com
Content-Length: 409
data_list=H4sIAAAAAAACCm1QwUrEMBD9l%2BCxXZI2pO3ebKvfIIiUmg4a3DYhjQuy7FHYPe3JL9izHrwqCPZbVv0Mpy1aBAlk5r28eZOZ8xWpVOtUI12hKjInPD3OM55nPg8z6vOYpX5CT6mfiuQkF1ywPBLEI7CExqE8WyhM8JY3yC7UJZmvyNEQiTQGuR4UNbhr3dtLXcEPuQTbKt0gS2chWXvEWG3AOgXt%2Fy5%2FCzxSSjfCw9P2a39fjOHjcX943X1uN6iQw%2FeKpqwBZd2ue%2B423cP7W%2FdyNr2a8gp%2BTSZ66sbYjOIJwzjoZ7dQawfDthDdtmDHHCdwqm%2FEBE1YEIkg5hFF8s70%2Fs6WuKT1xTfiII0%2BcwEAAA%3D%3D&gzip=1
|
SunloginClient_11.0.0.33826.exe | 2020-12-28 03:53:49.863 - Info - [http call3] id:1, url:https://sl-tk.oray.com/track, status code:200
|