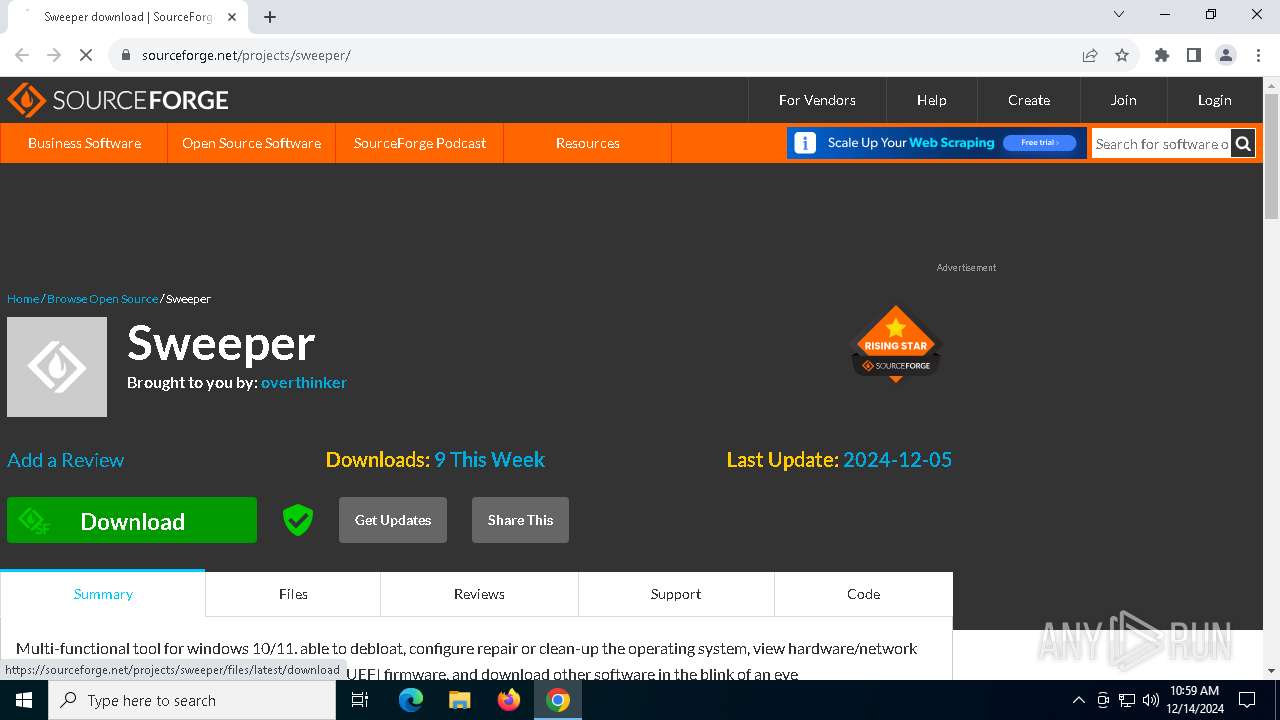
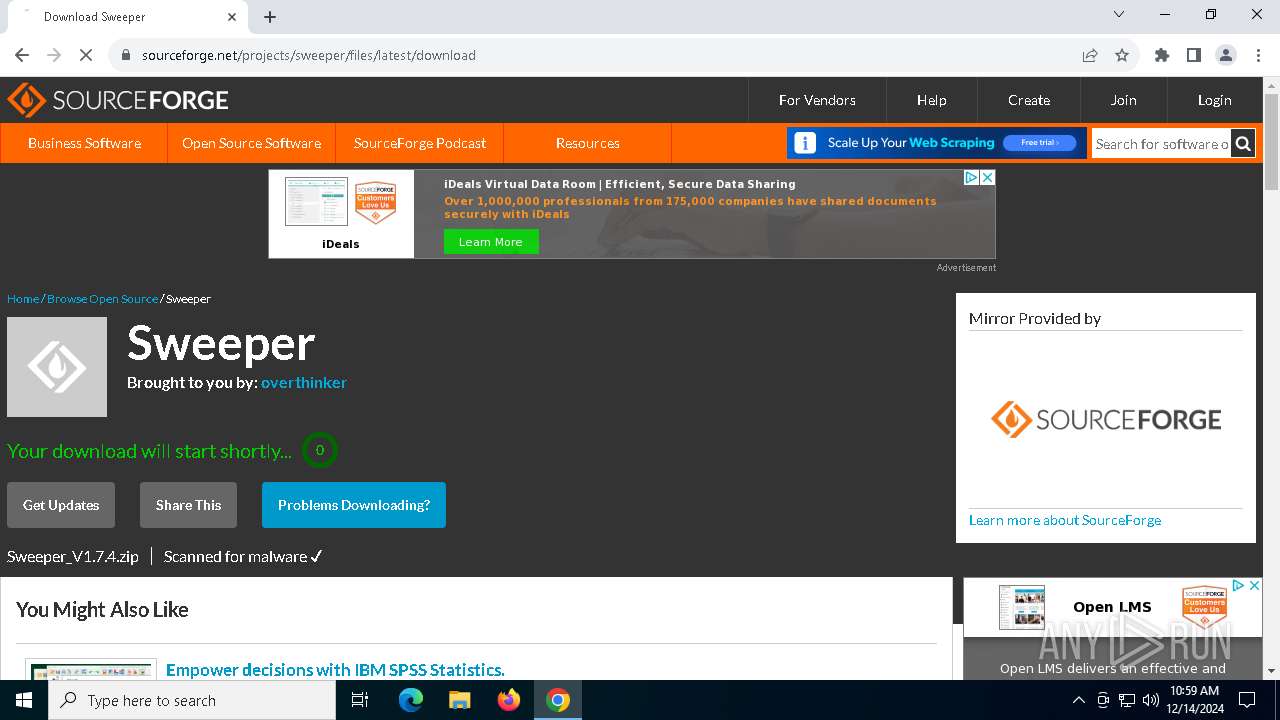
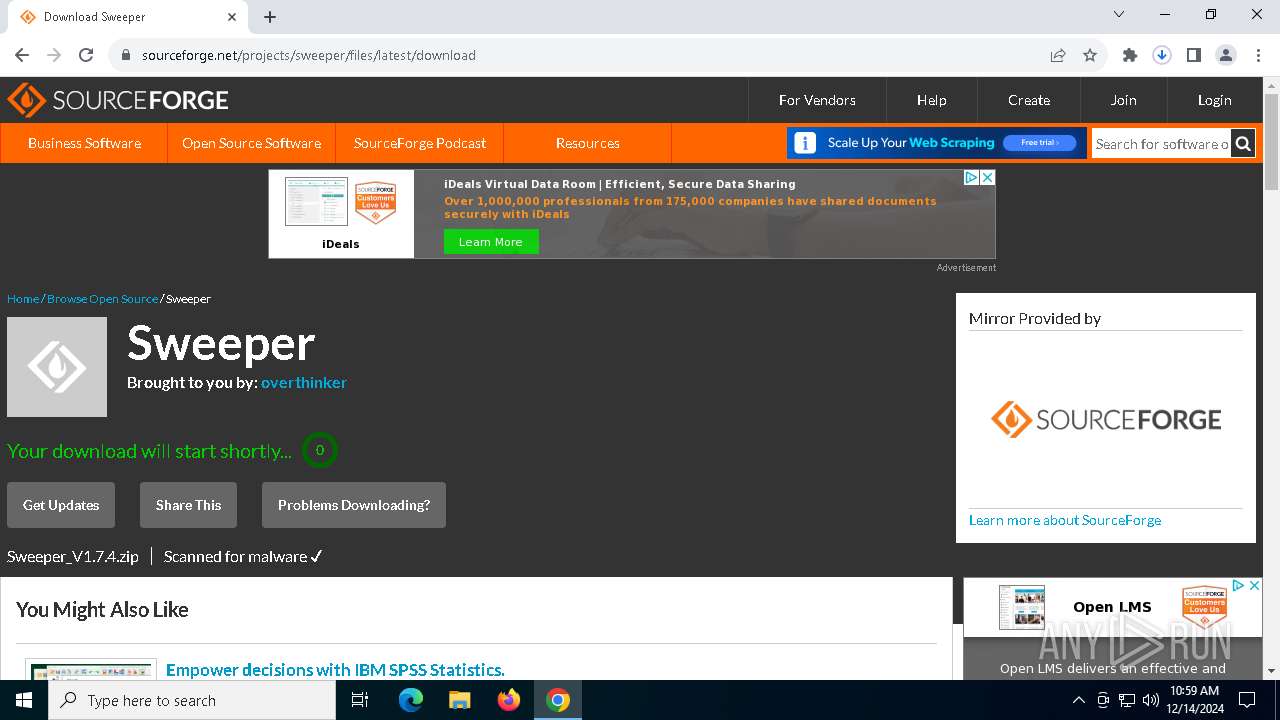
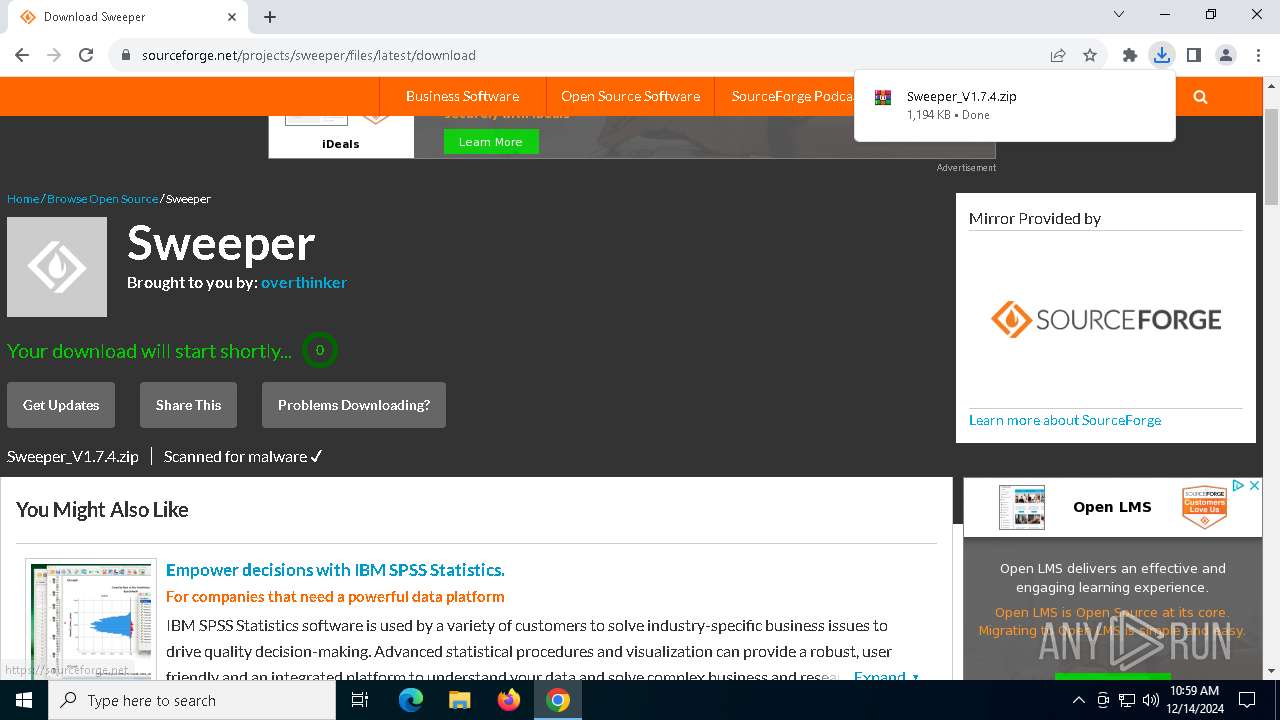
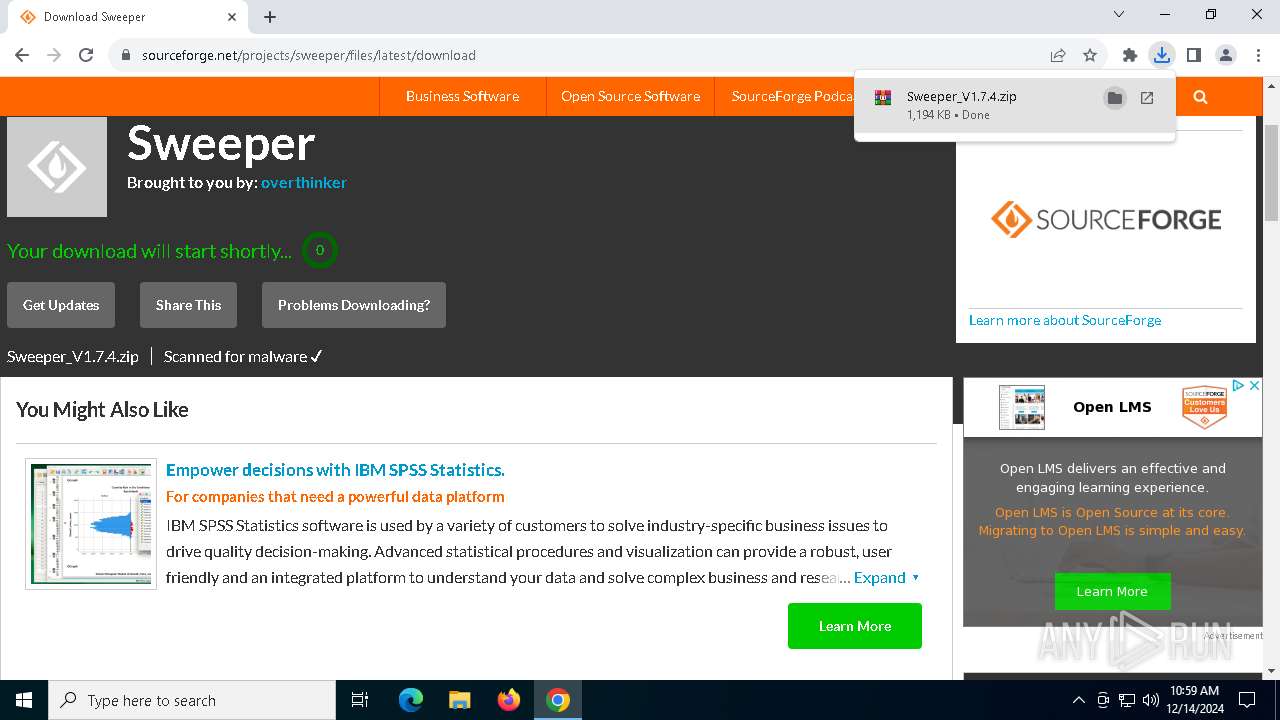
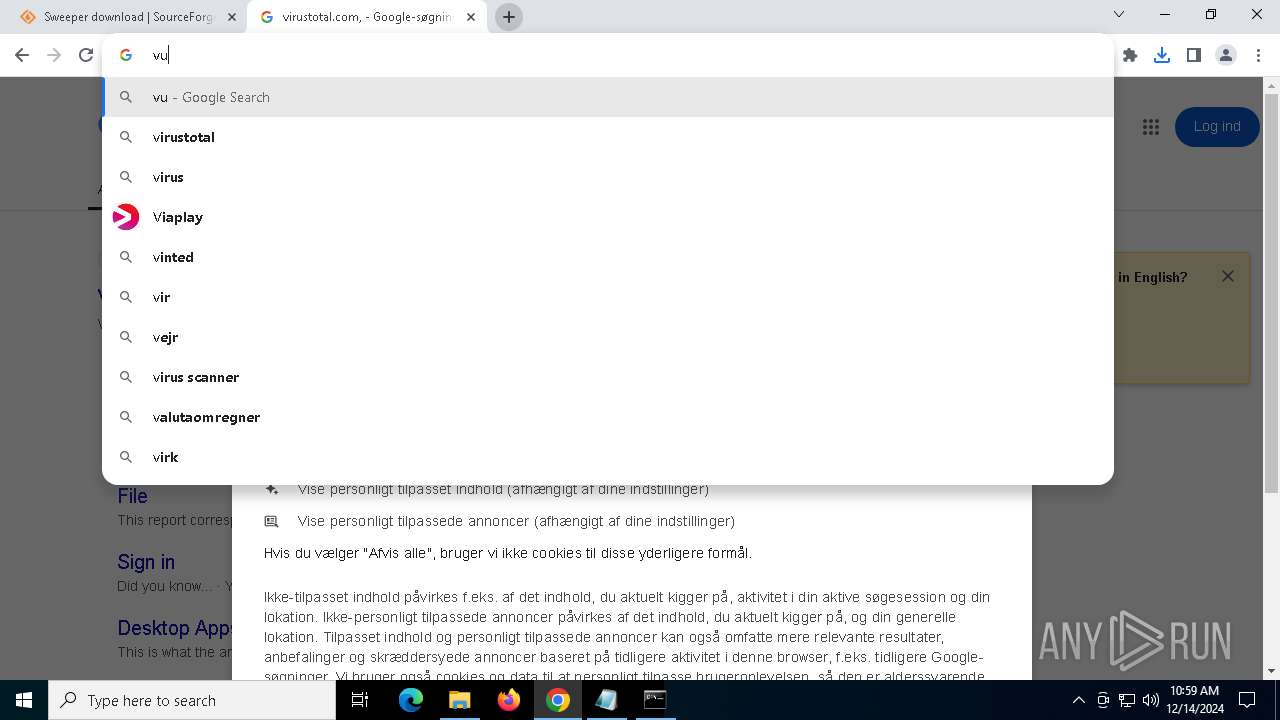
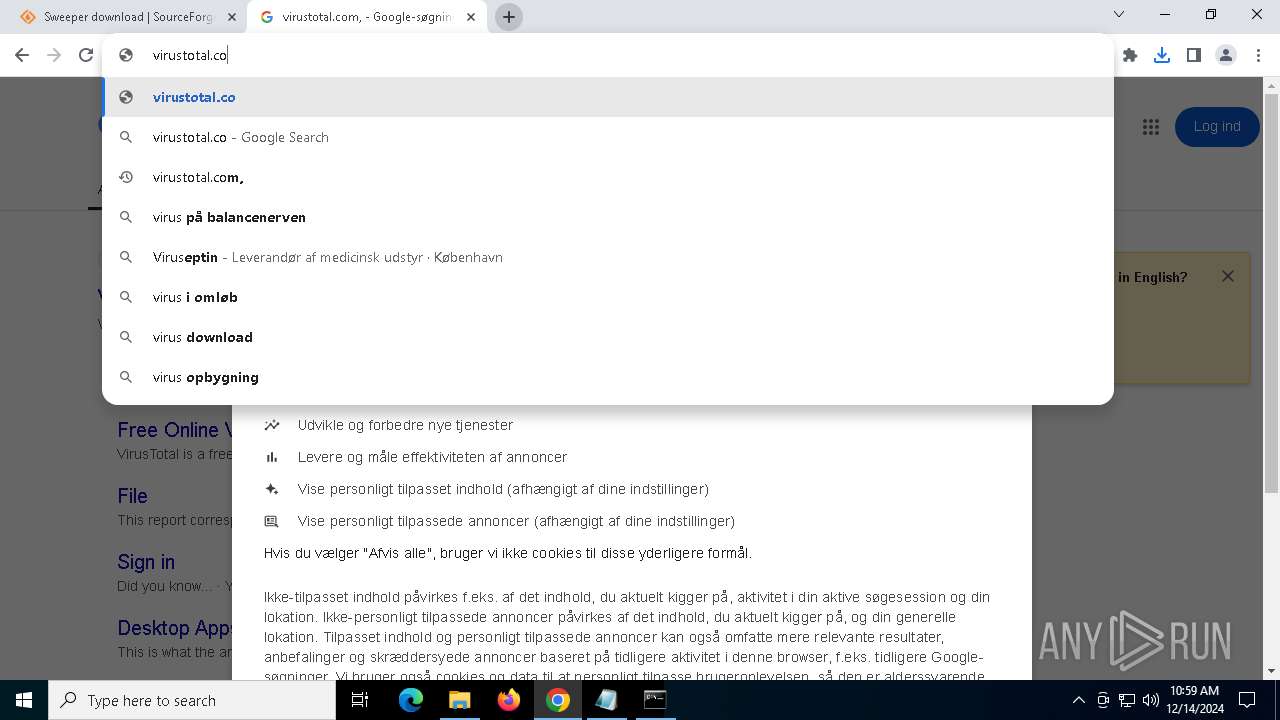
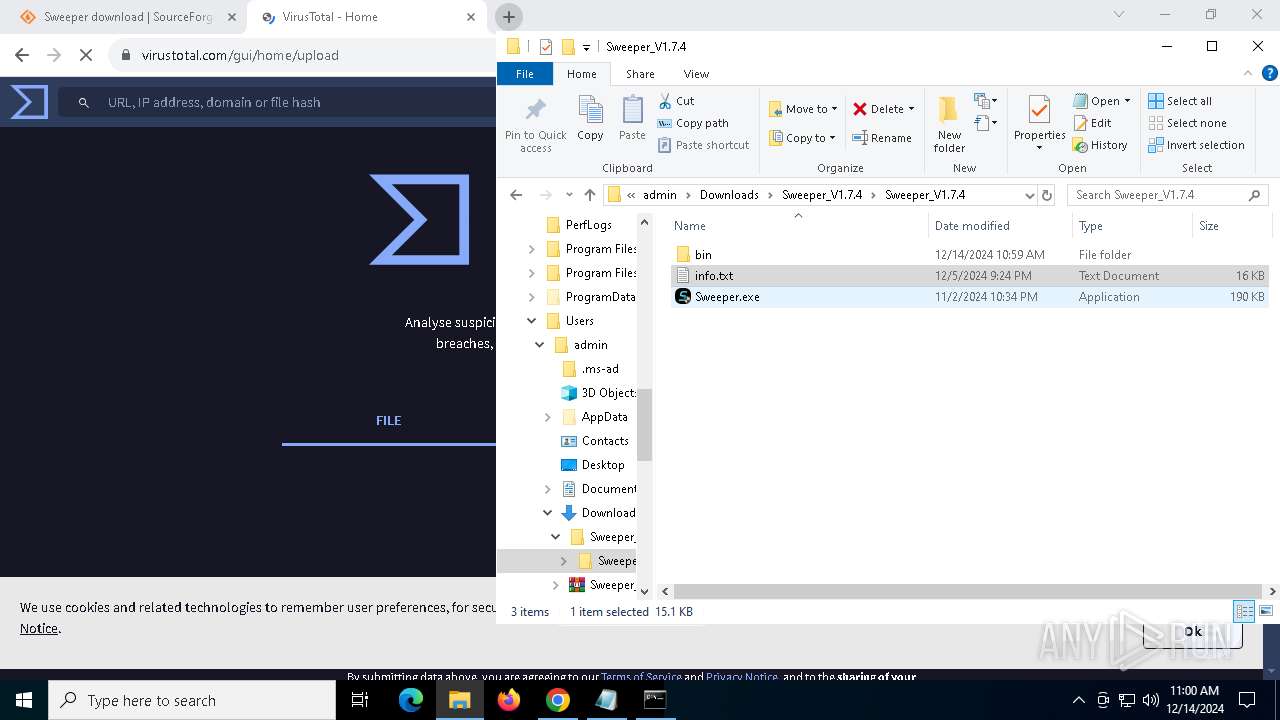
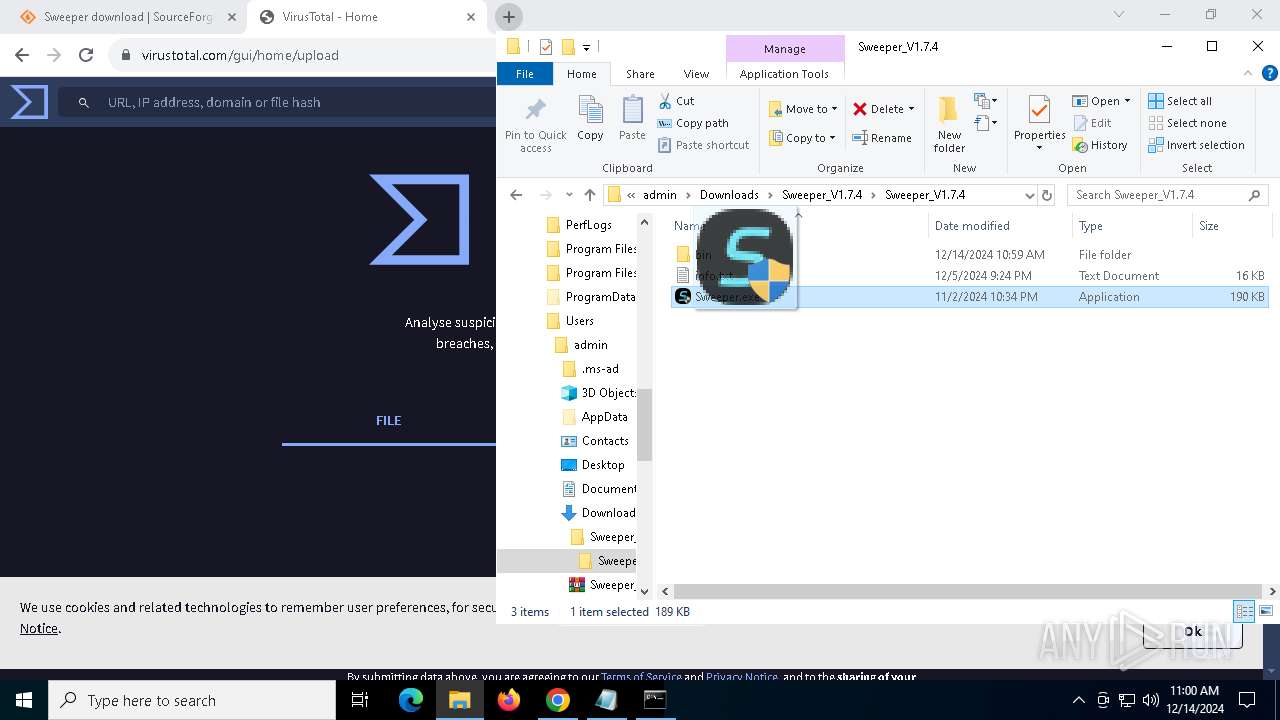
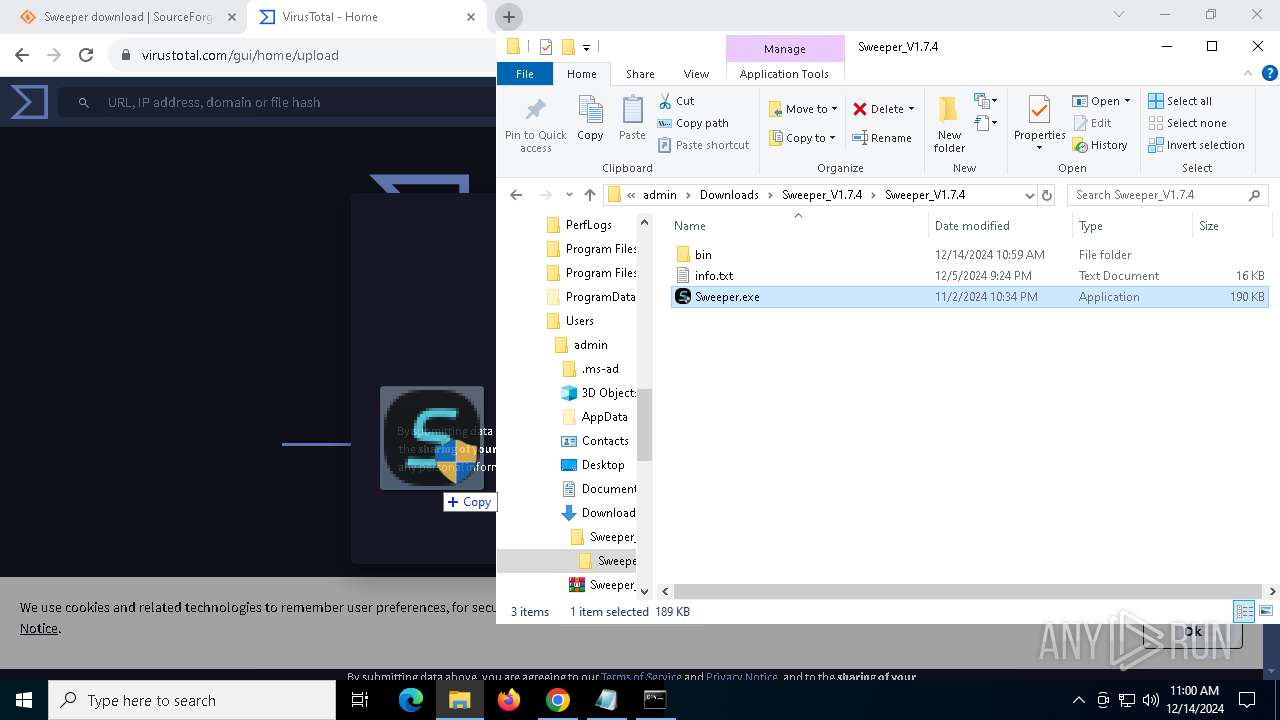
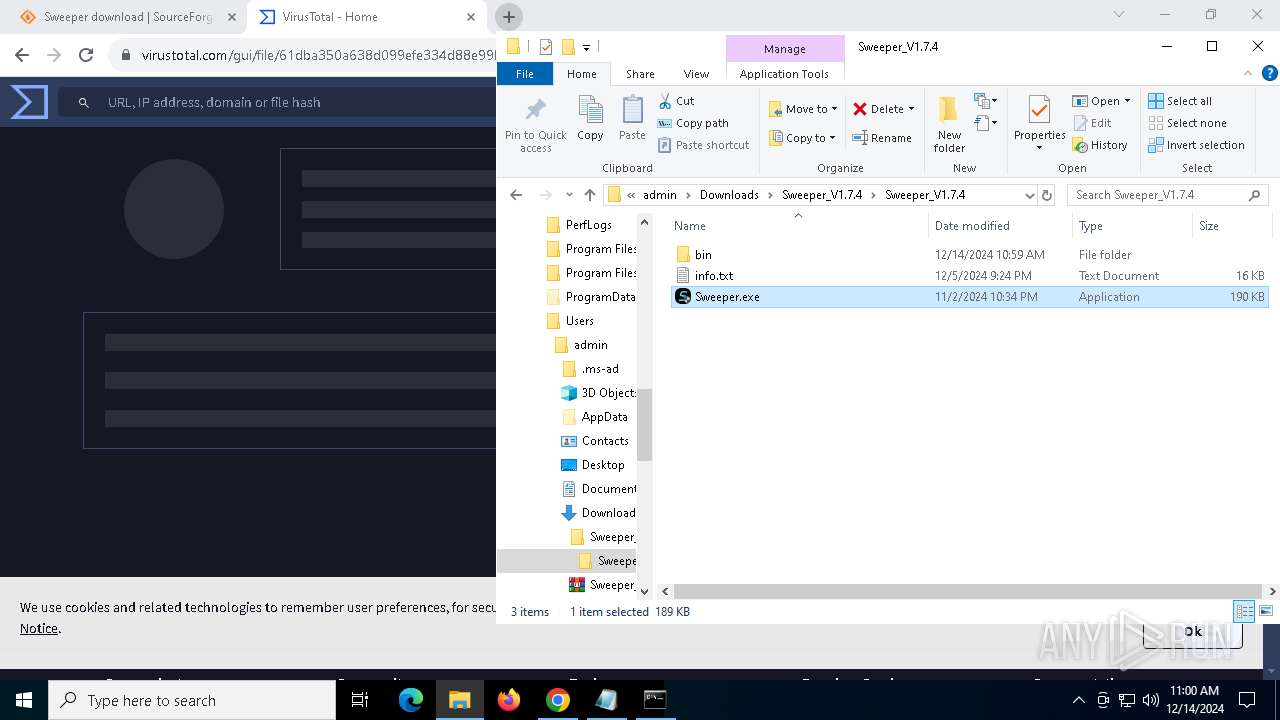
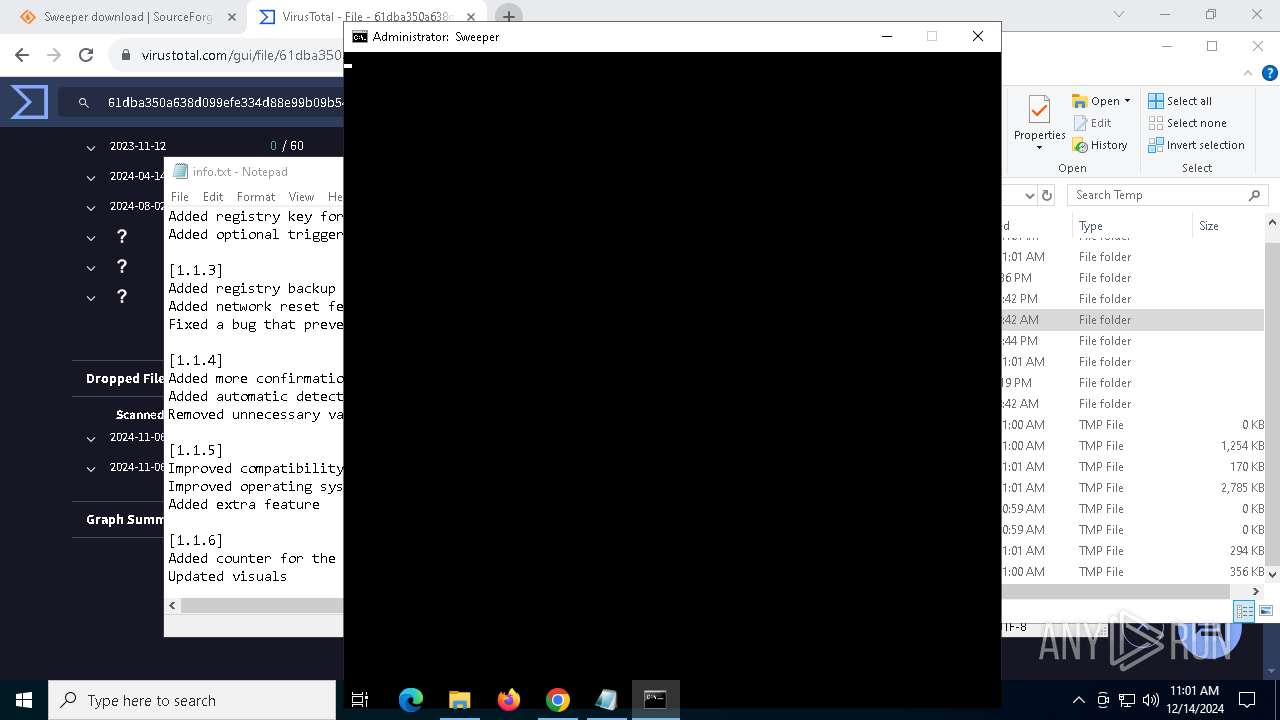
| URL: | https://sourceforge.net/projects/sweeper/ |
| Full analysis: | https://app.any.run/tasks/3720cccc-cdab-46c8-a3aa-7f65622aa7b8 |
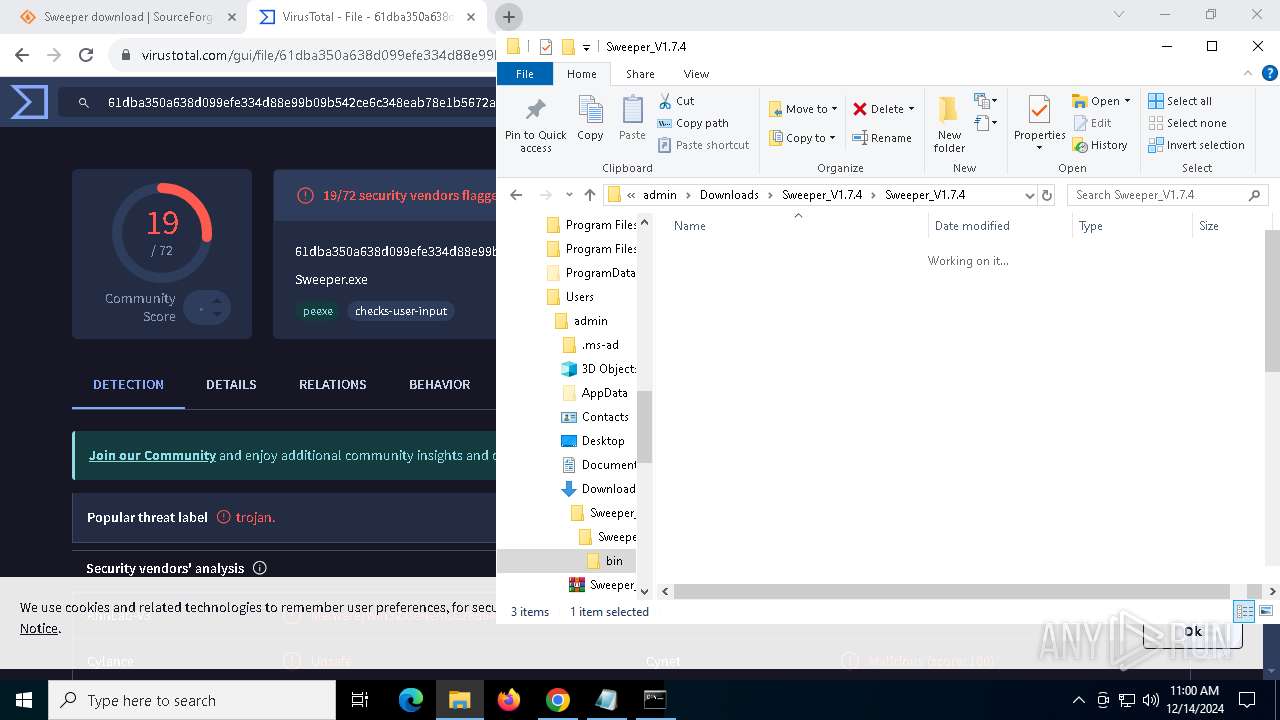
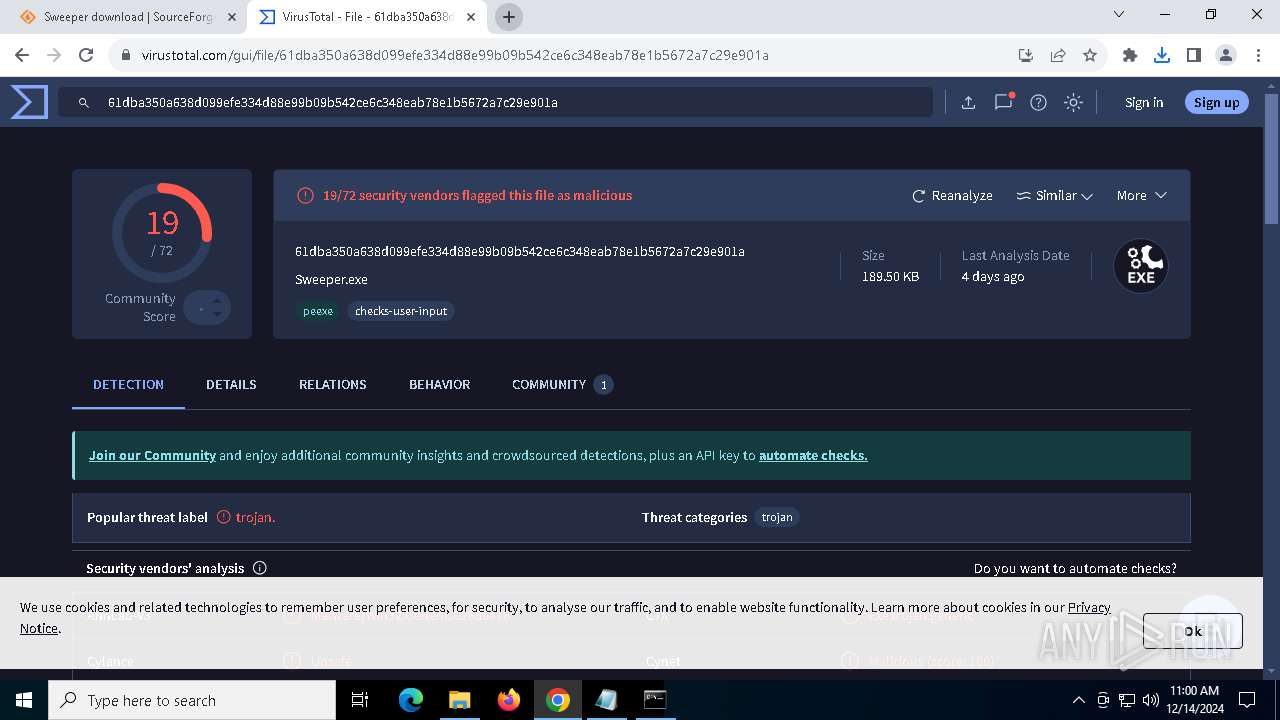
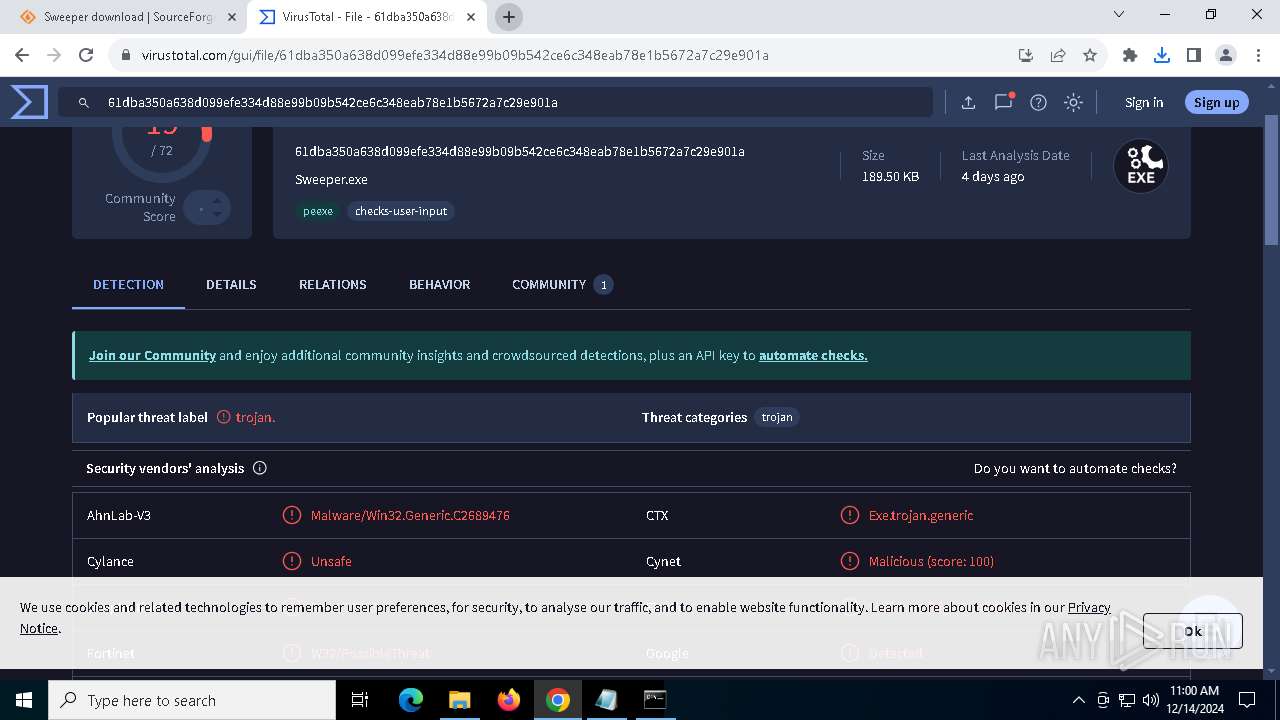
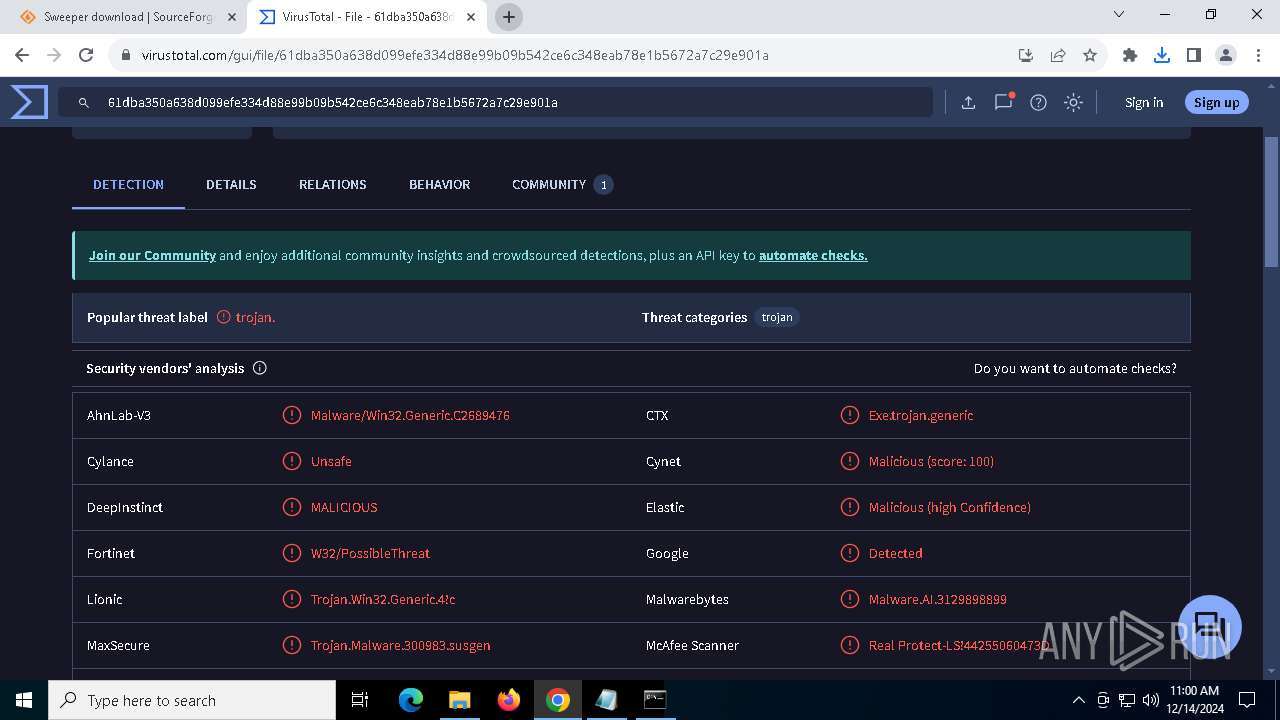
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 10:58:53 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0C26B62B88B49FD531D03C0706A24EDB |
| SHA1: | 60D862EC2D0E4F2CD04AA1727F0116A3C3AB7C6A |
| SHA256: | 496175246222CA6843D2CE3452CBAE1C613D35C3A96D03668AB5DB5CBA2B0BDA |
| SSDEEP: | 3:N8HCGSuLAuUtpqa:2iGnCtEa |
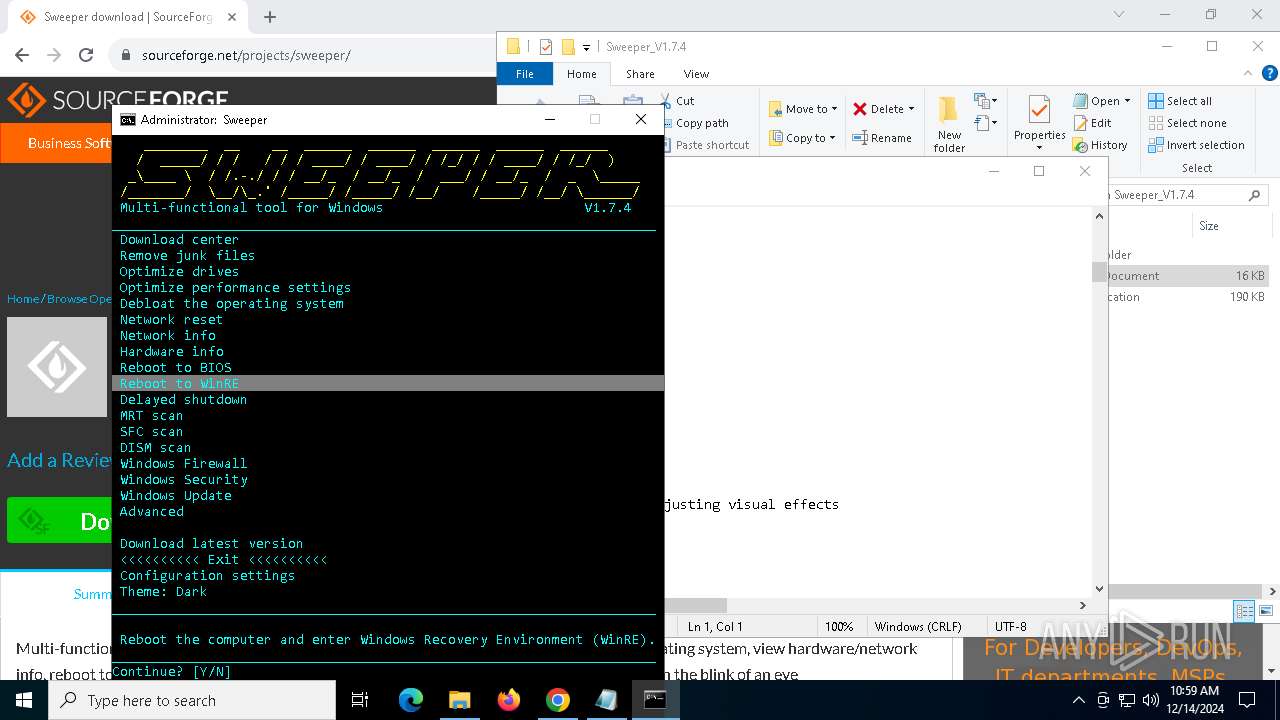
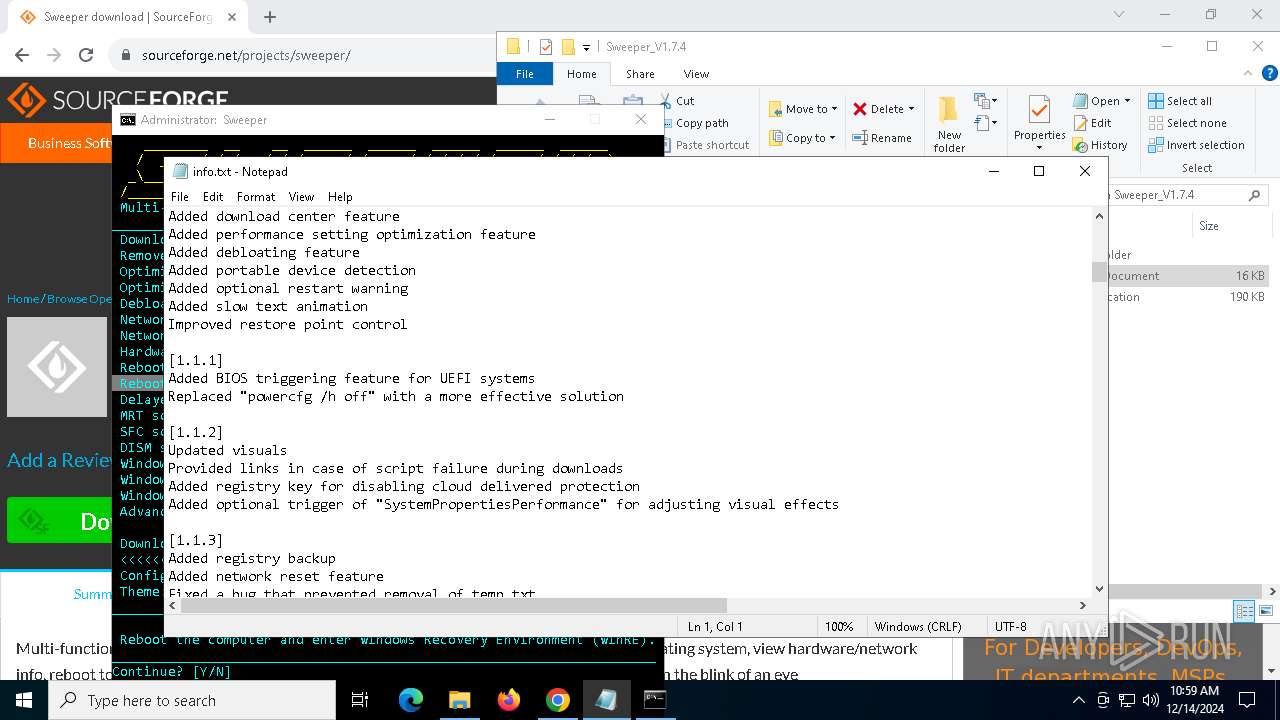
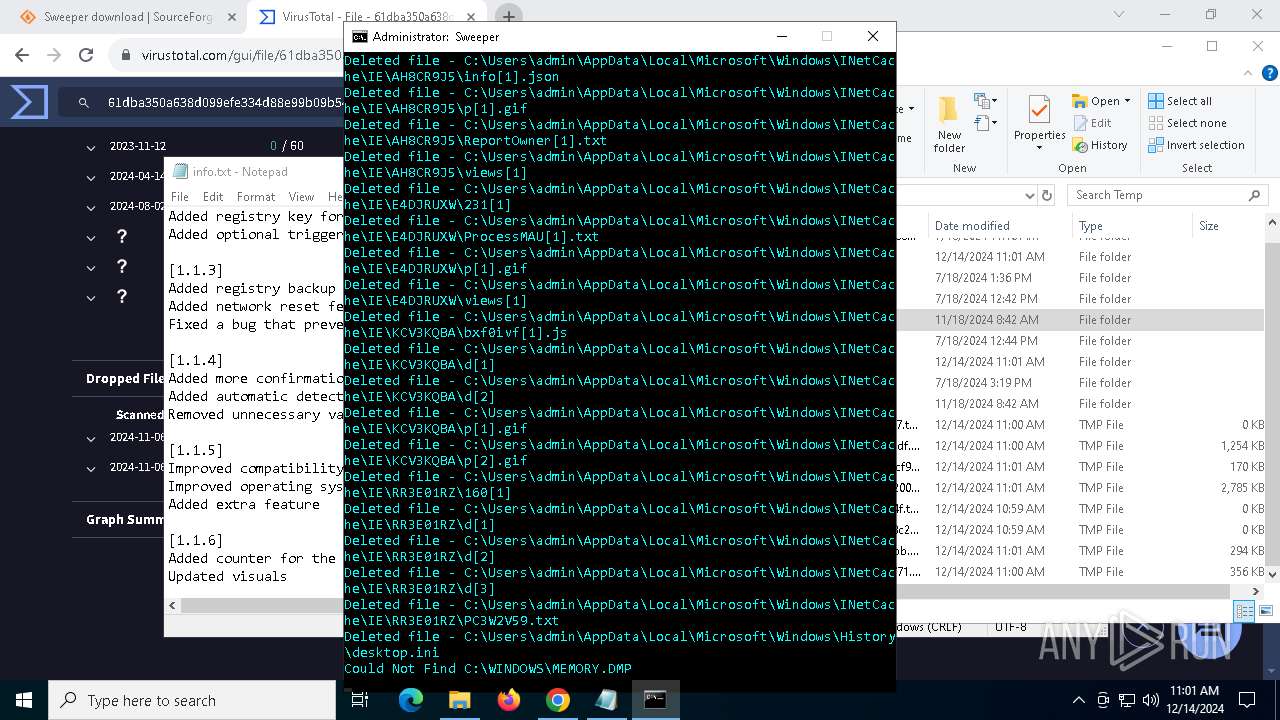
MALICIOUS
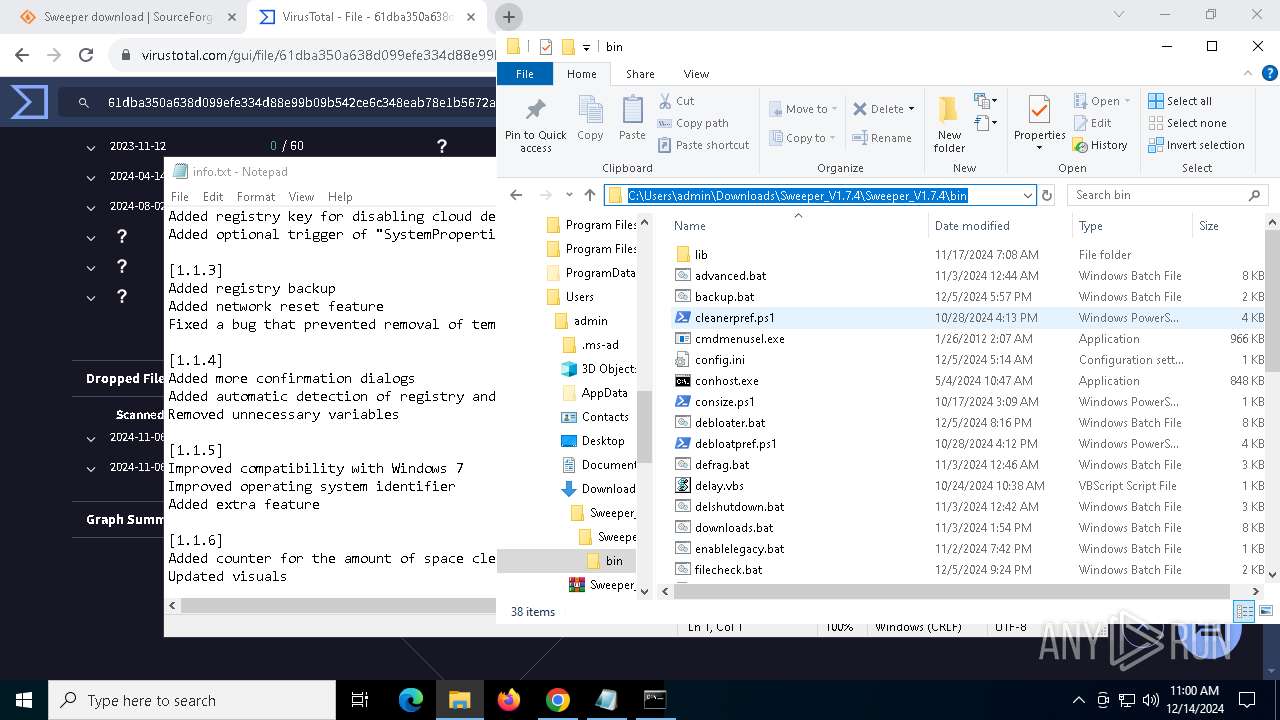
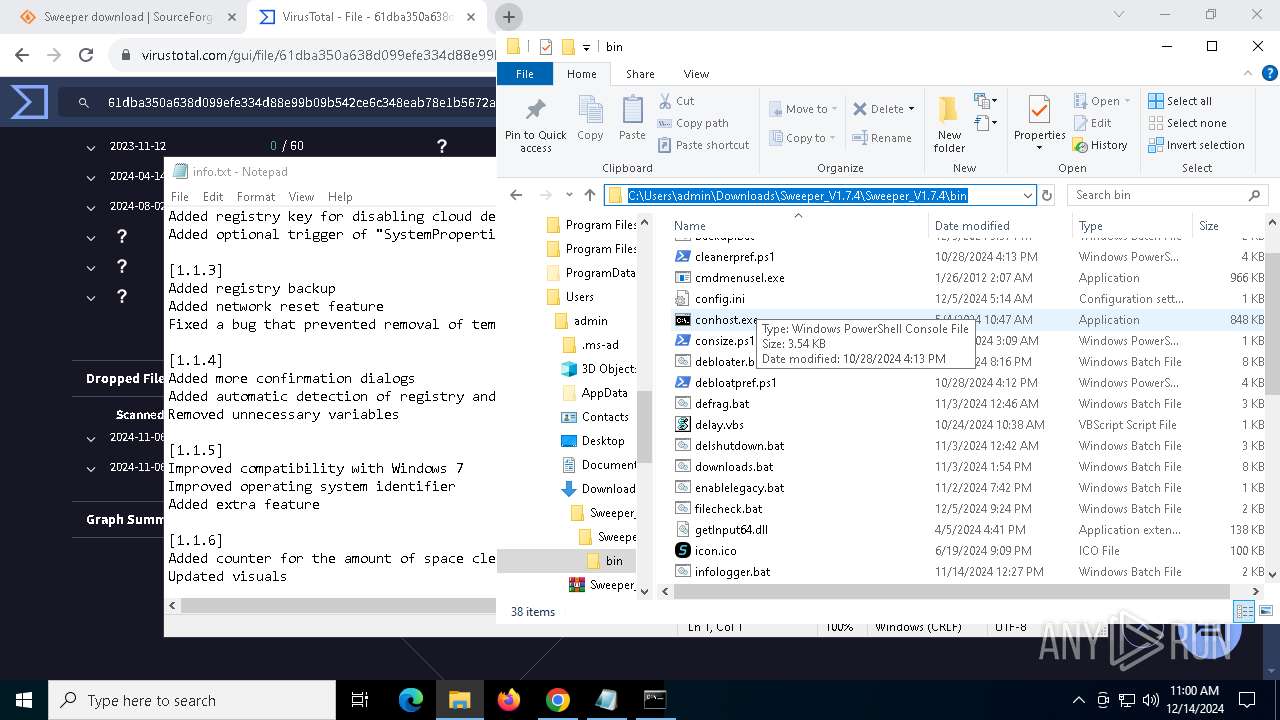
Execute application with conhost.exe as parent process
- cmd.exe (PID: 7756)
Uses sleep, probably for evasion detection (SCRIPT)
- cscript.exe (PID: 7844)
- cscript.exe (PID: 7928)
- cscript.exe (PID: 8016)
- cscript.exe (PID: 8084)
- cscript.exe (PID: 8120)
- cscript.exe (PID: 8052)
- cscript.exe (PID: 1944)
- cscript.exe (PID: 8160)
- cscript.exe (PID: 3608)
- cscript.exe (PID: 7196)
- cscript.exe (PID: 5556)
- cscript.exe (PID: 7504)
- cscript.exe (PID: 3296)
- cscript.exe (PID: 7392)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7572)
- cscript.exe (PID: 7632)
- cscript.exe (PID: 7536)
- cscript.exe (PID: 3560)
- cscript.exe (PID: 7624)
- cscript.exe (PID: 7664)
- cscript.exe (PID: 7744)
- cscript.exe (PID: 7944)
- cscript.exe (PID: 7968)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 7756)
Bypass execution policy to execute commands
- powershell.exe (PID: 7944)
- powershell.exe (PID: 6700)
- powershell.exe (PID: 7992)
- powershell.exe (PID: 4668)
- powershell.exe (PID: 3900)
- powershell.exe (PID: 1480)
- powershell.exe (PID: 7628)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 7268)
- powershell.exe (PID: 5192)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 7392)
- powershell.exe (PID: 8108)
SUSPICIOUS
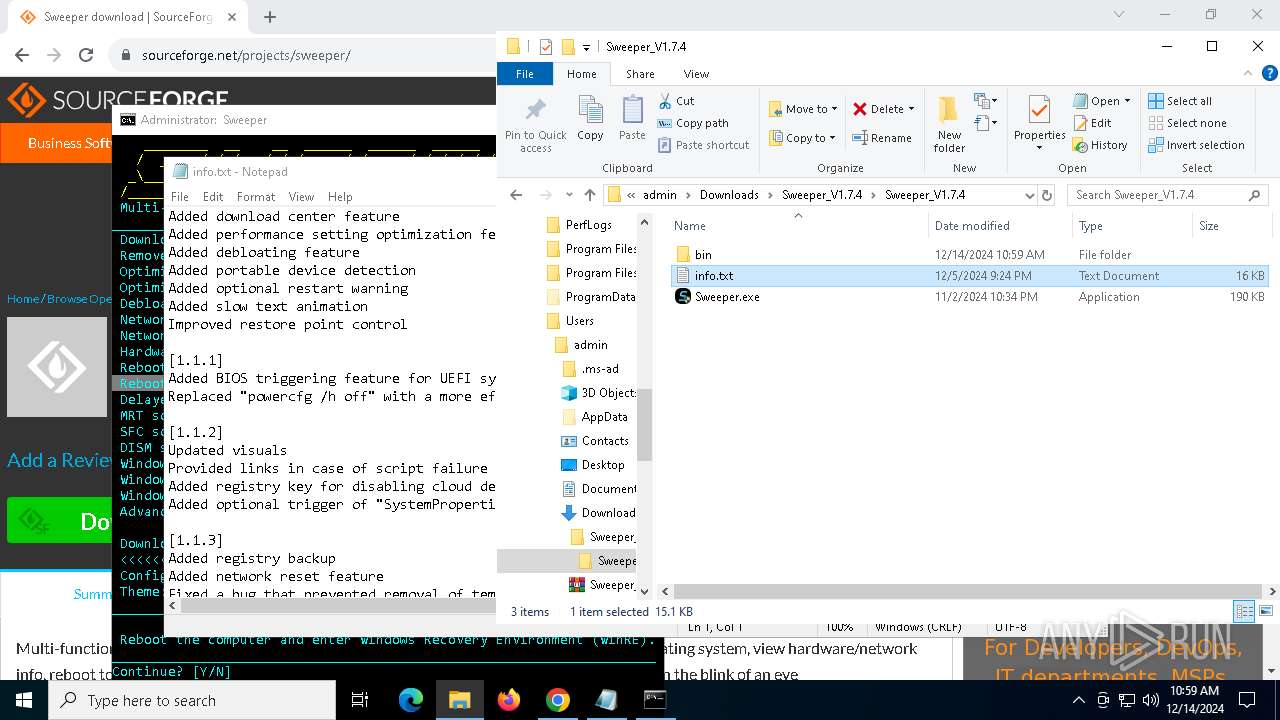
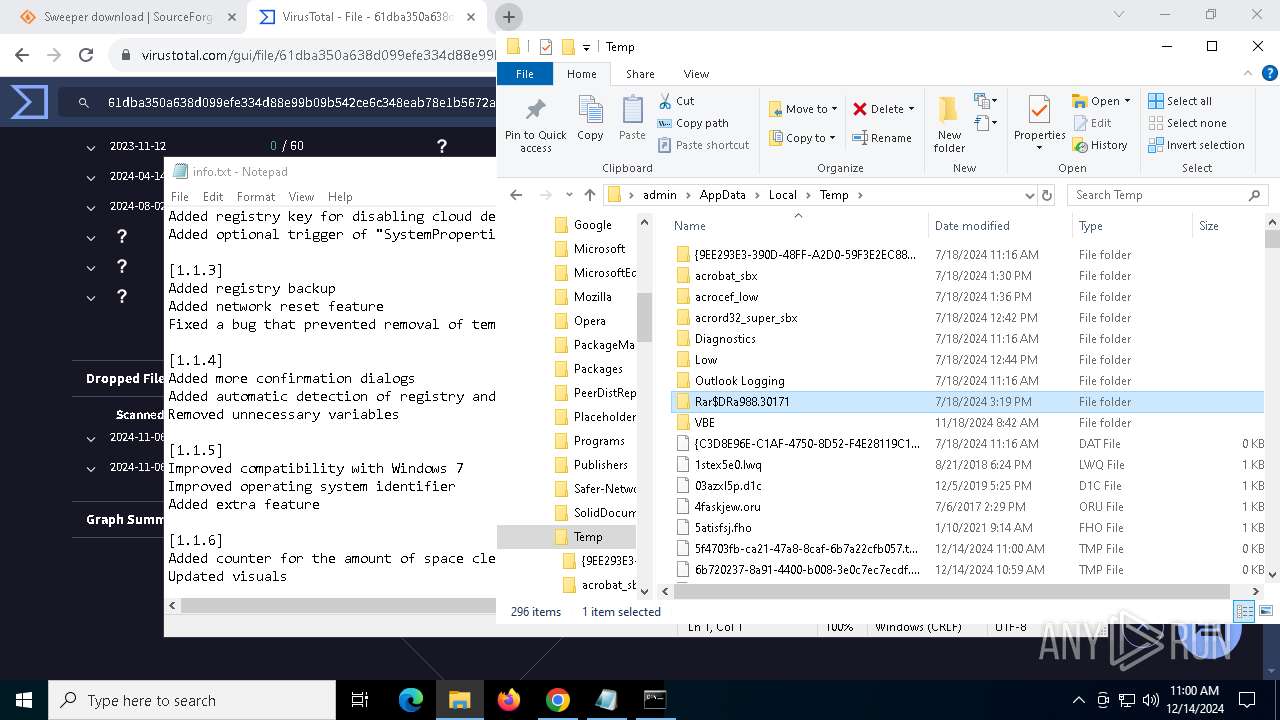
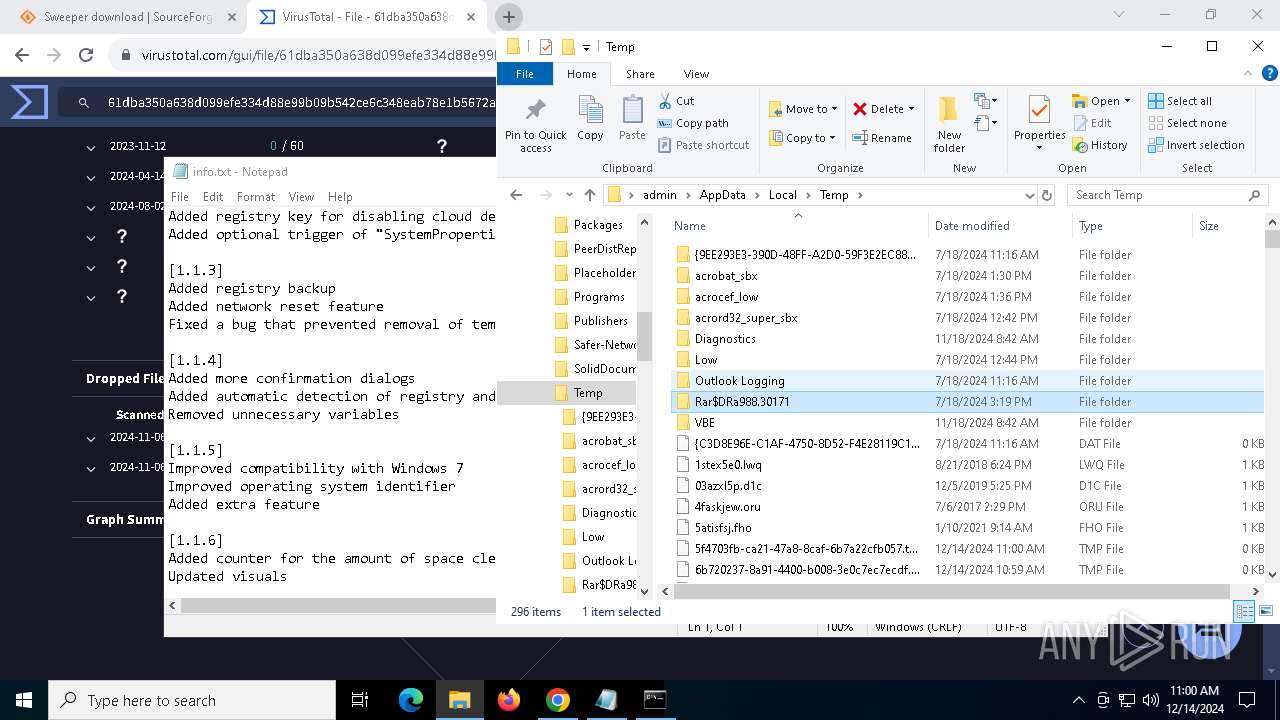
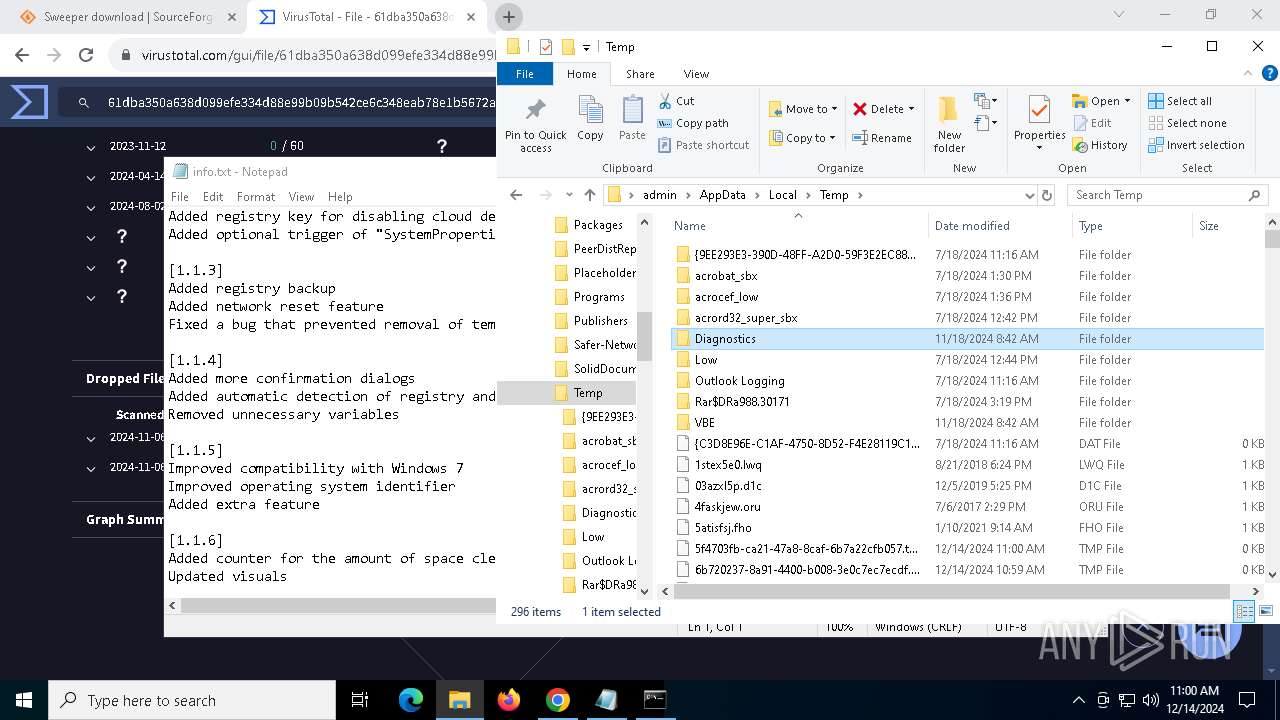
The process creates files with name similar to system file names
- WinRAR.exe (PID: 5920)
Starts CMD.EXE for commands execution
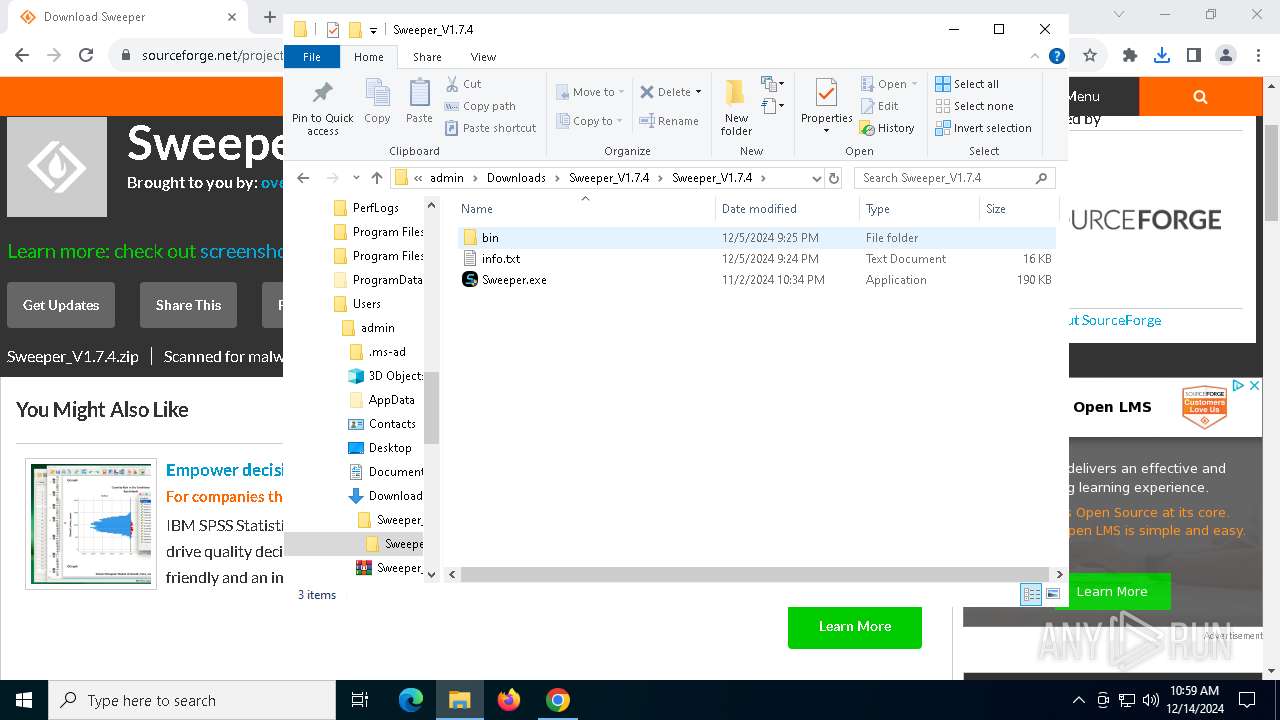
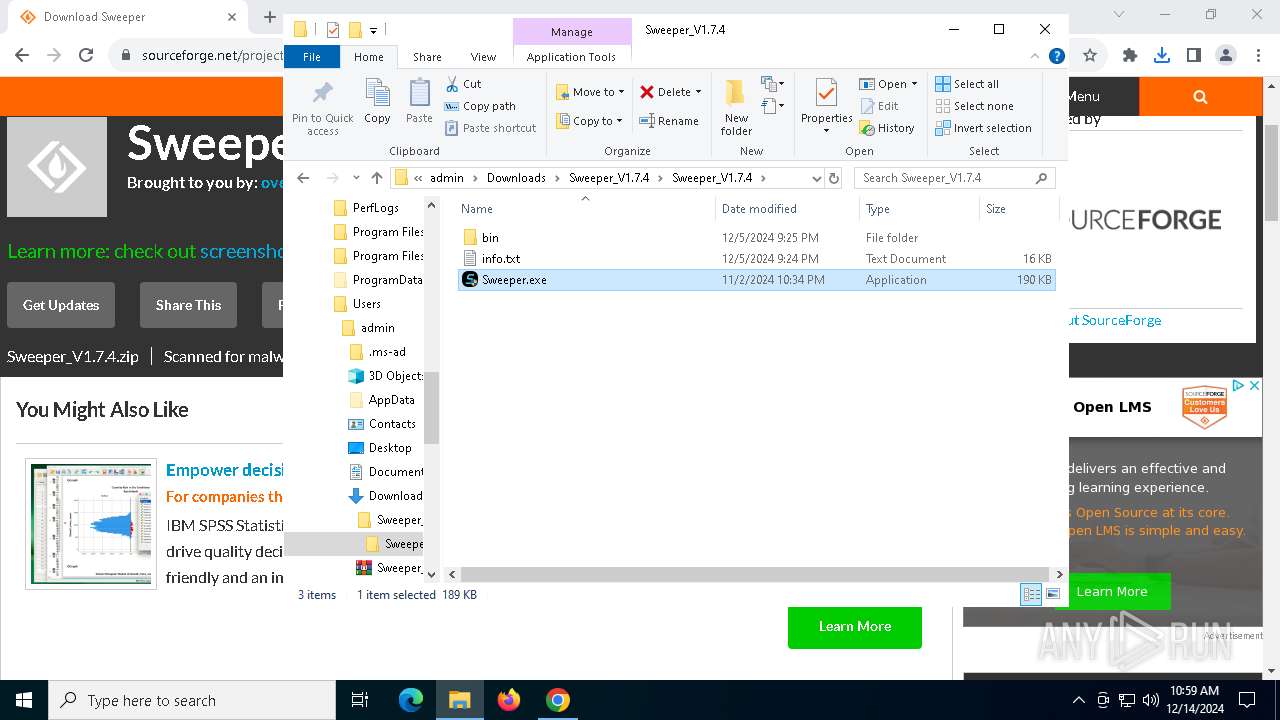
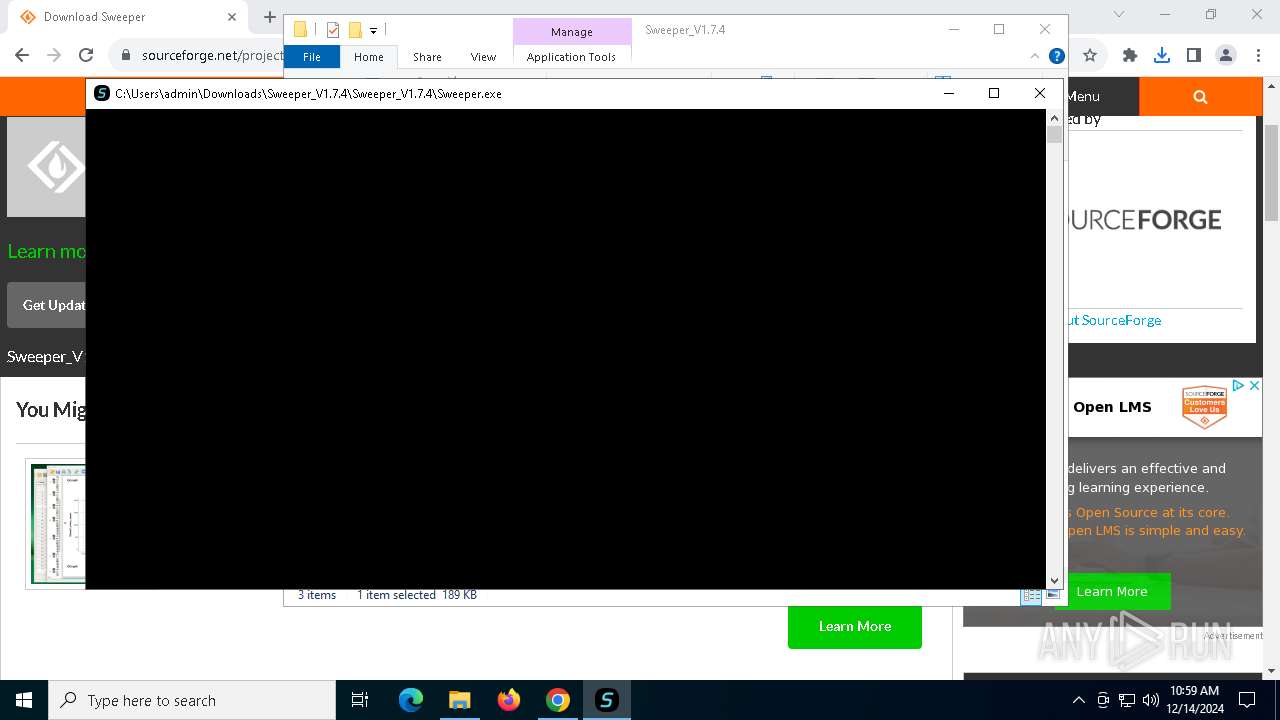
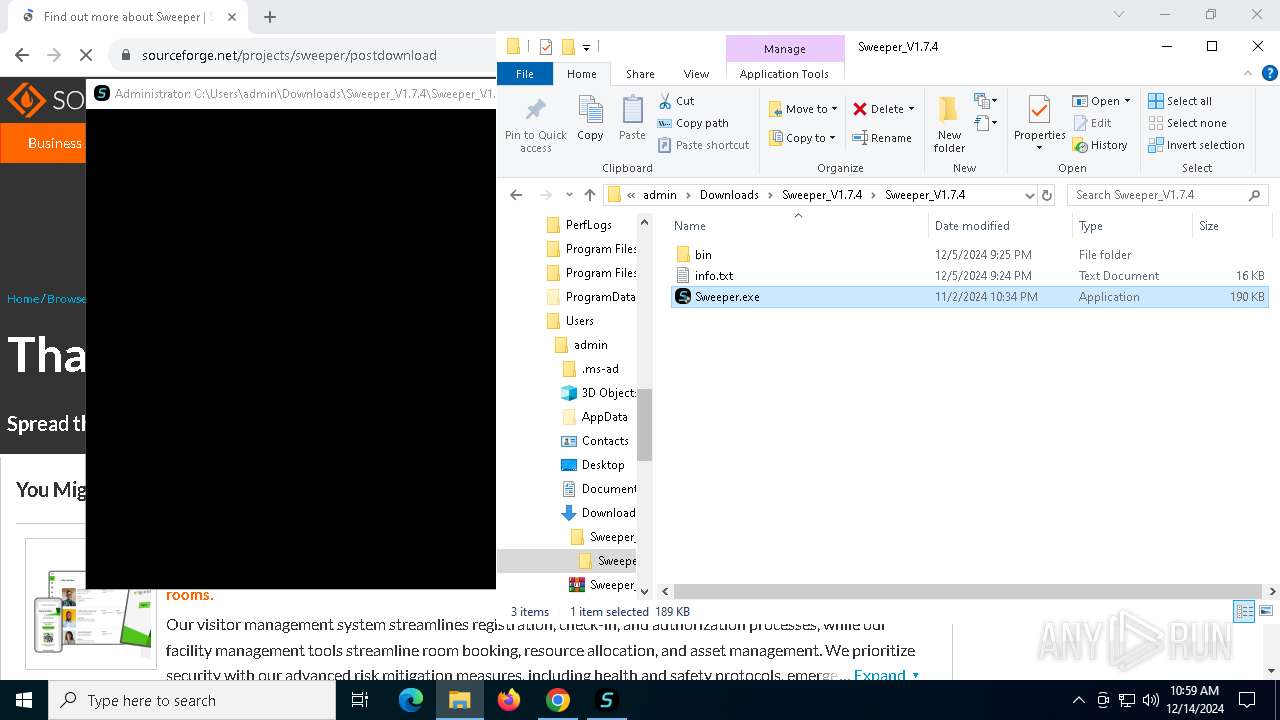
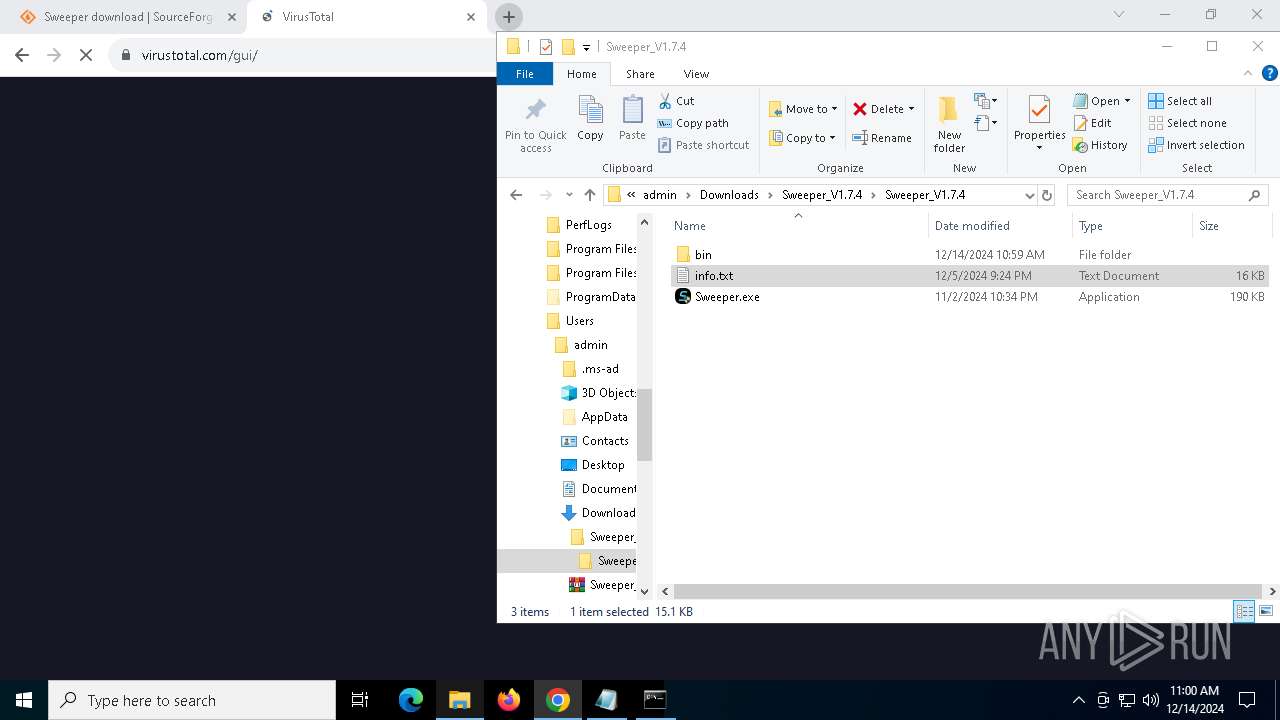
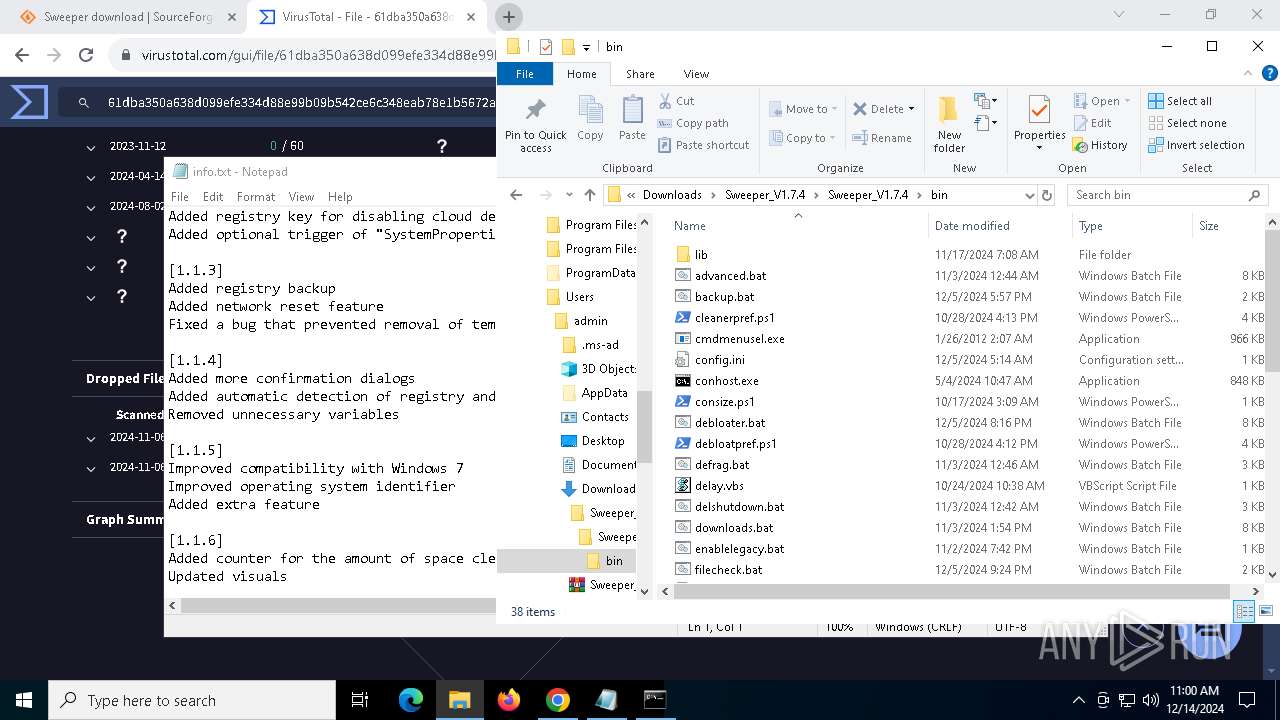
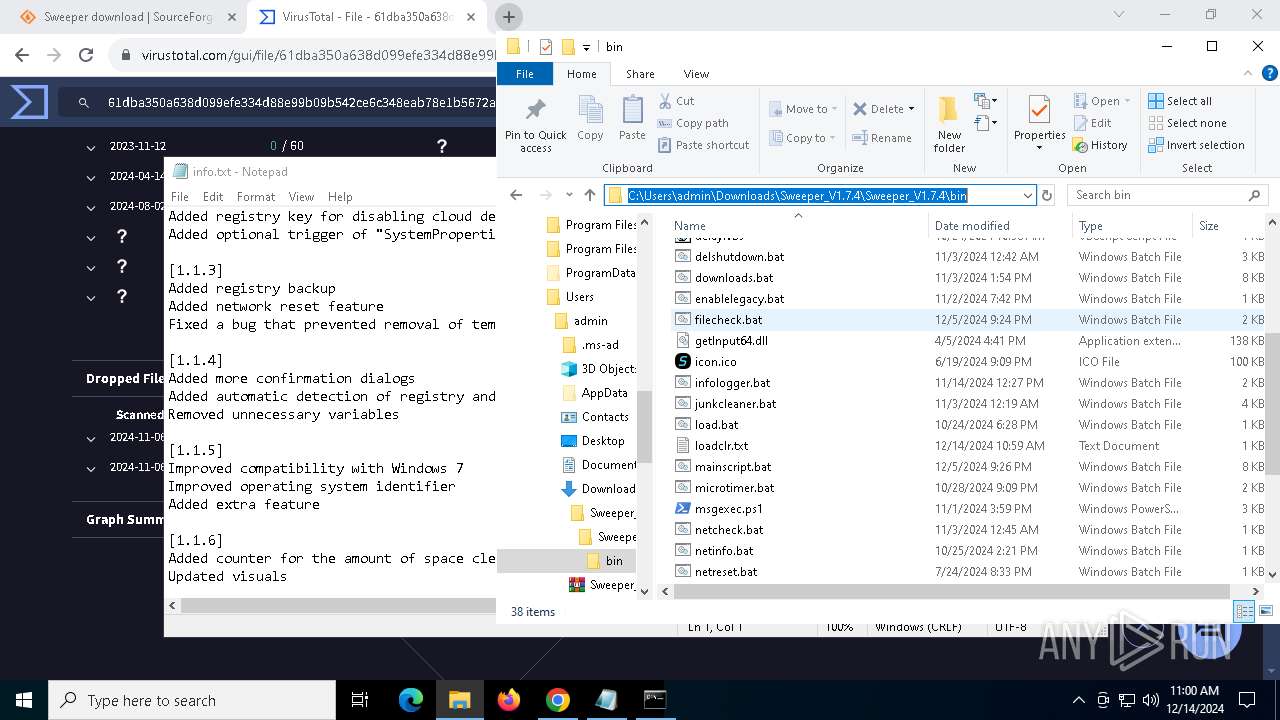
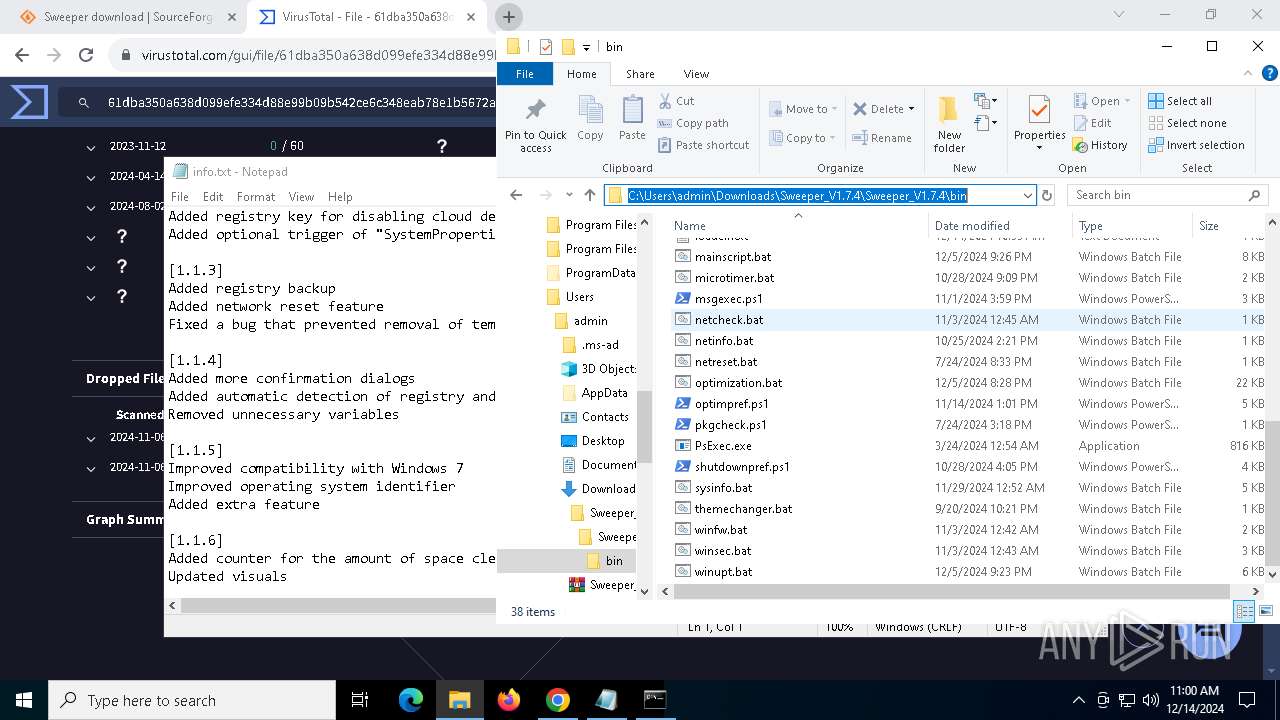
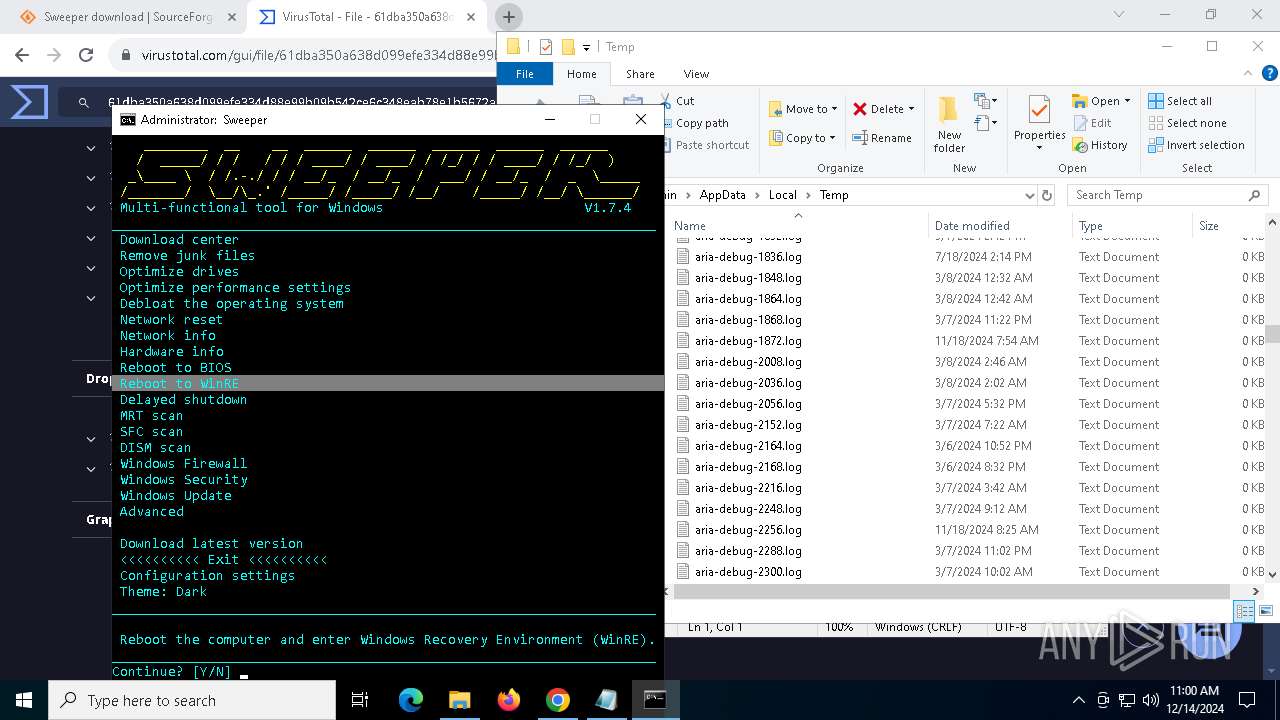
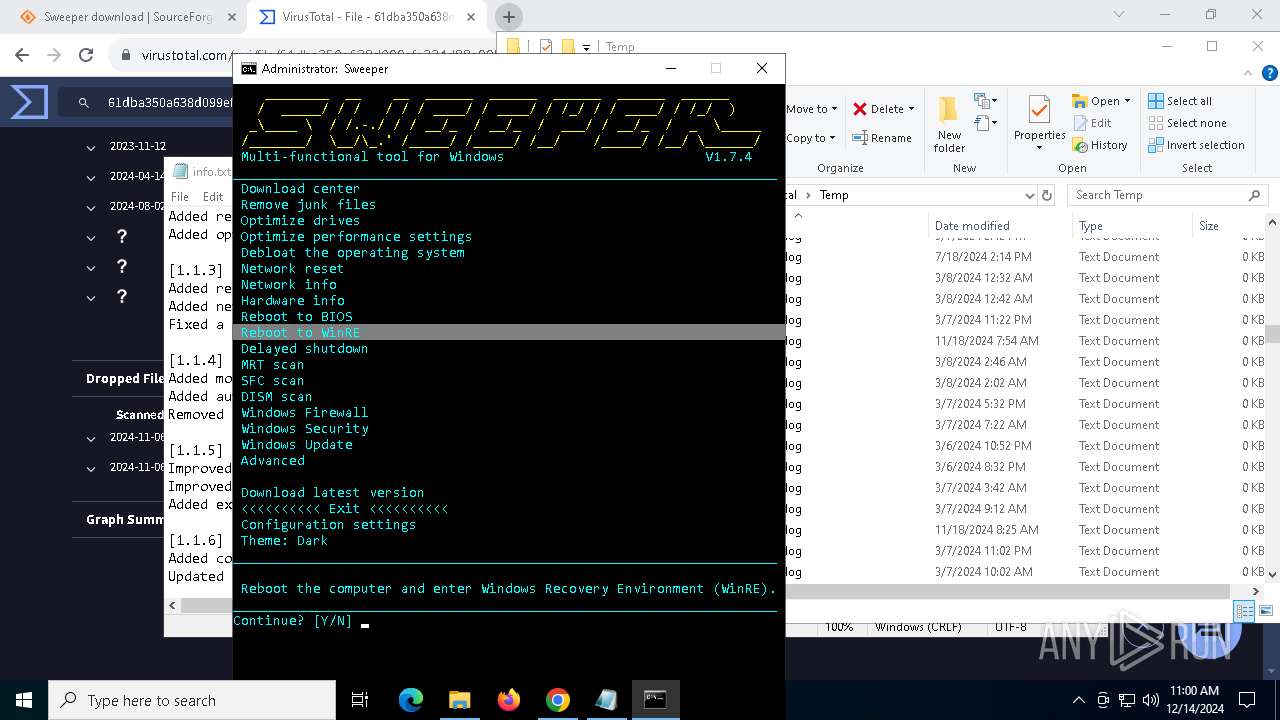
- Sweeper.exe (PID: 5076)
- cmd.exe (PID: 5652)
- cmd.exe (PID: 7756)
- conhost.exe (PID: 7720)
Process drops legitimate windows executable
- WinRAR.exe (PID: 5920)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7808)
- cmd.exe (PID: 6388)
- cmd.exe (PID: 7360)
- cmd.exe (PID: 7352)
- cmd.exe (PID: 7536)
- cmd.exe (PID: 7756)
- cmd.exe (PID: 6676)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 1572)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 1480)
- cmd.exe (PID: 3080)
- cmd.exe (PID: 7172)
- cmd.exe (PID: 432)
- cmd.exe (PID: 8052)
- cmd.exe (PID: 1216)
- cmd.exe (PID: 8140)
- cmd.exe (PID: 436)
Hides command output
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7808)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7808)
- cmd.exe (PID: 7756)
Executing commands from a ".bat" file
- Sweeper.exe (PID: 5076)
- conhost.exe (PID: 7720)
- cmd.exe (PID: 7756)
Application launched itself
- cmd.exe (PID: 5652)
- cmd.exe (PID: 7756)
The process executes VB scripts
- cmd.exe (PID: 7792)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 7756)
The executable file from the user directory is run by the CMD process
- cmdmenusel.exe (PID: 8068)
- cmdmenusel.exe (PID: 7360)
- cmdmenusel.exe (PID: 5300)
- cmdmenusel.exe (PID: 776)
- cmdmenusel.exe (PID: 3828)
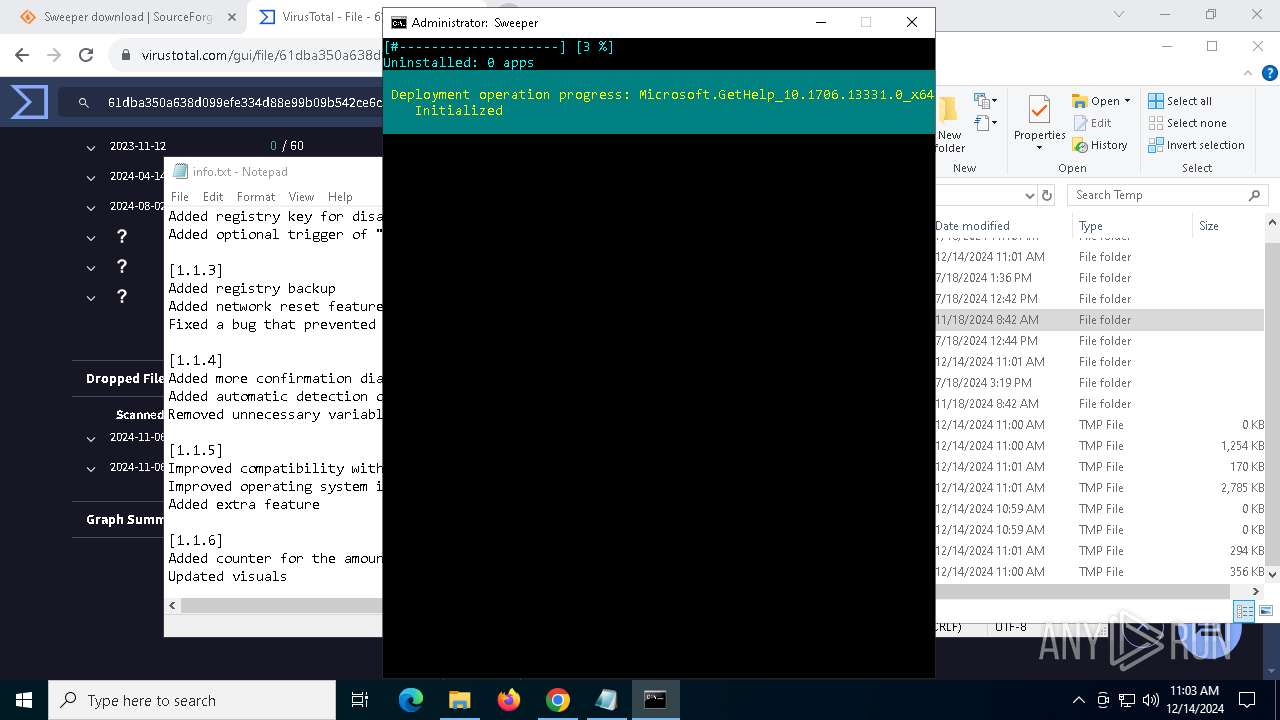
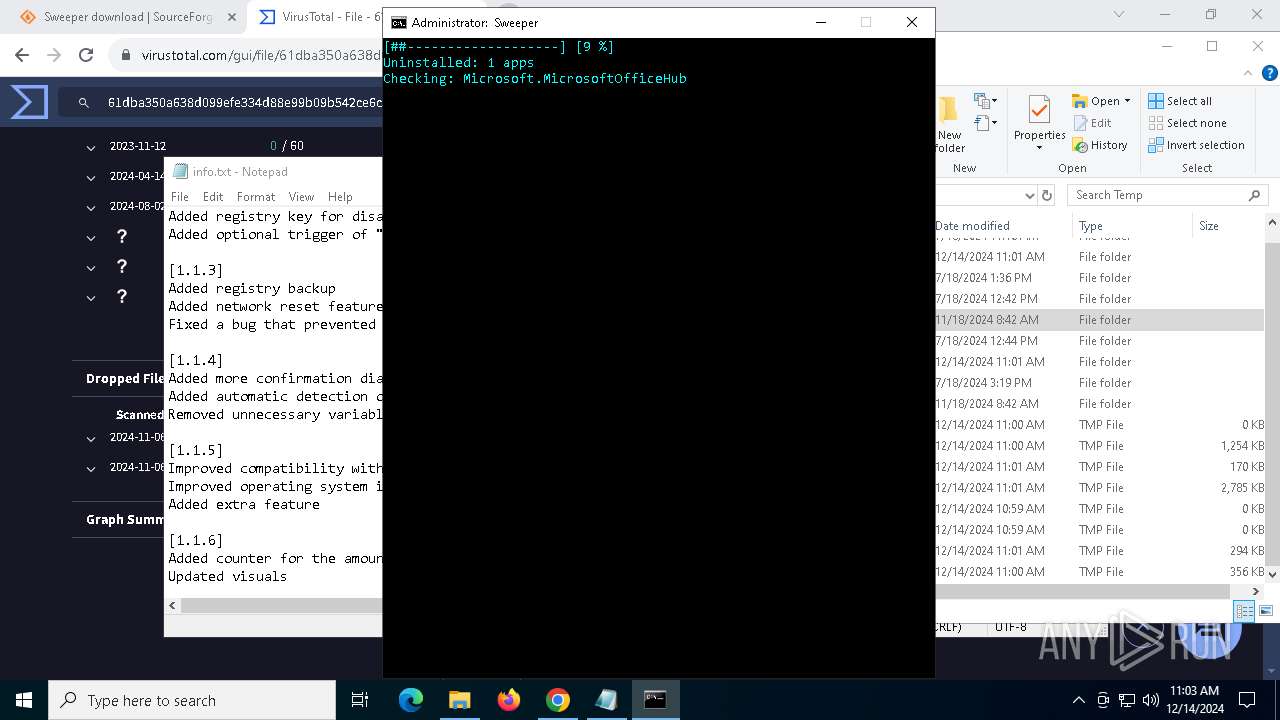
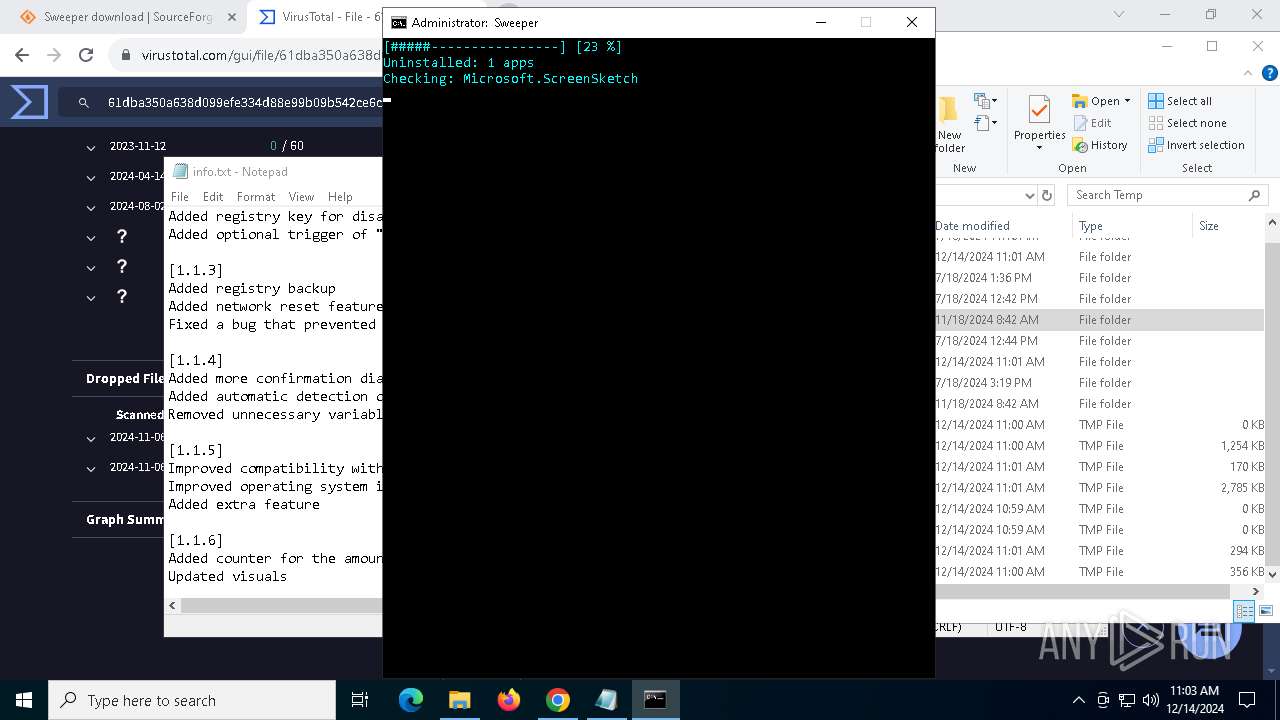
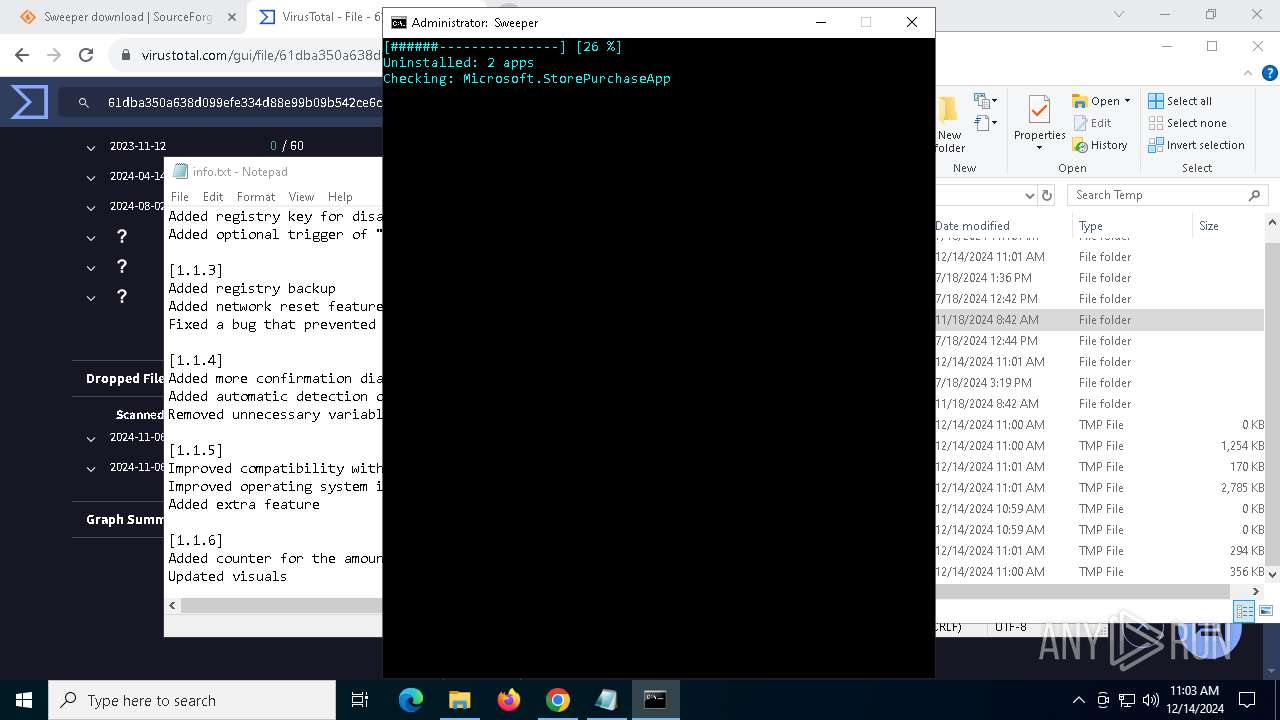
Probably fake Windows Update
- cmdmenusel.exe (PID: 8068)
- cmdmenusel.exe (PID: 7360)
- cmdmenusel.exe (PID: 5300)
- cmdmenusel.exe (PID: 776)
- cmdmenusel.exe (PID: 3828)
The process executes Powershell scripts
- cmd.exe (PID: 7756)
Uses WMIC.EXE to obtain local storage devices information
- cmd.exe (PID: 7008)
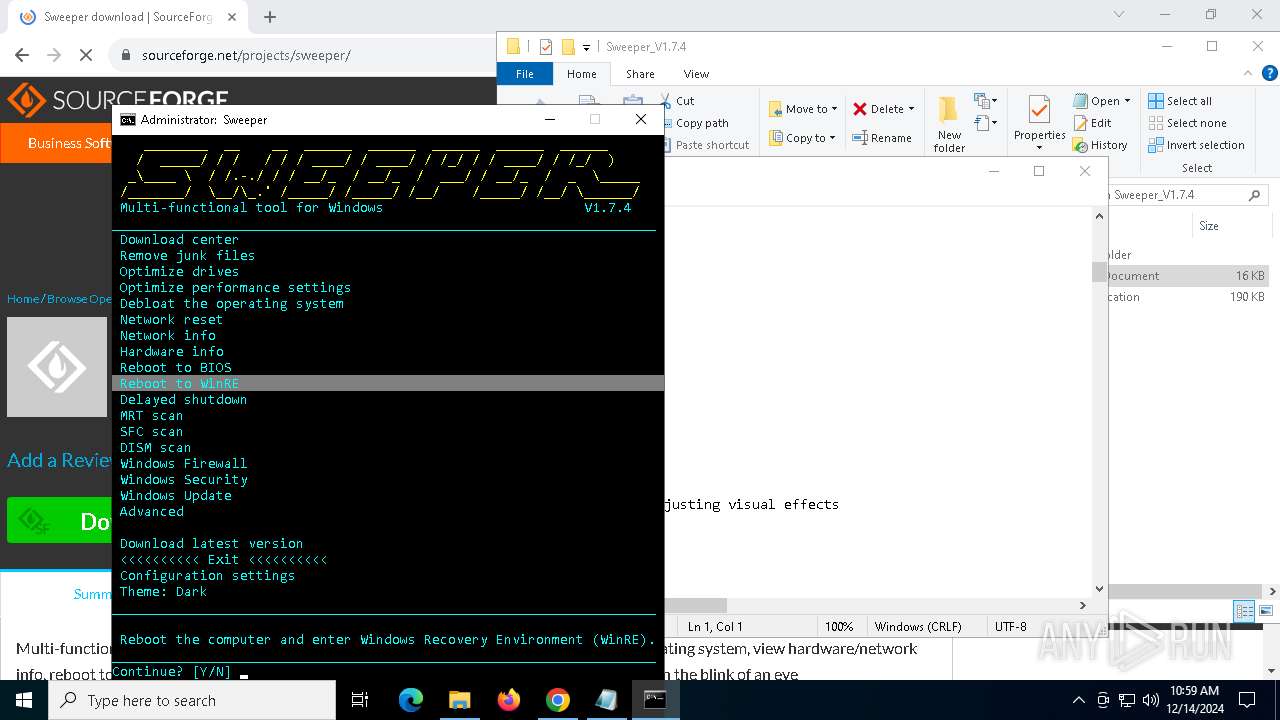
The system shut down or reboot
- cmd.exe (PID: 7756)
Reads Microsoft Outlook installation path
- reg.exe (PID: 5404)
Checks for the .NET to be installed
- reg.exe (PID: 5404)
Searches for installed software
- reg.exe (PID: 5404)
The process checks if it is being run in the virtual environment
- reg.exe (PID: 5404)
Executes as Windows Service
- VSSVC.exe (PID: 1380)
INFO
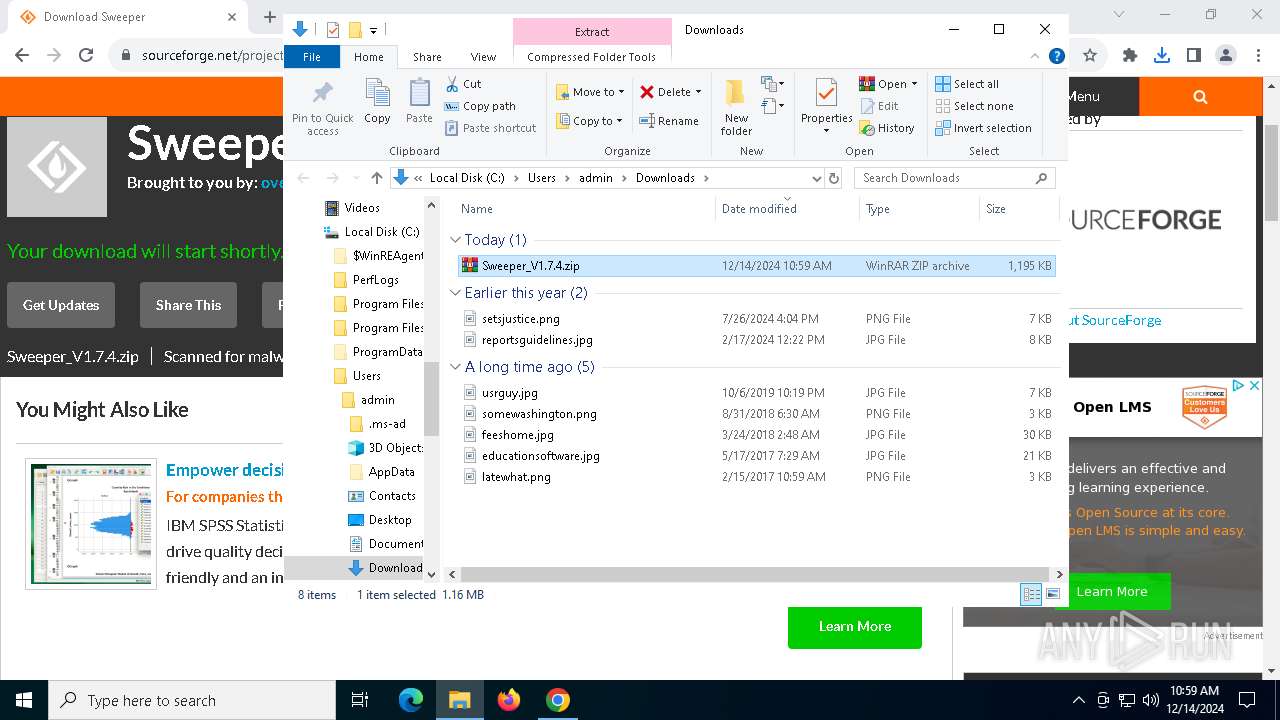
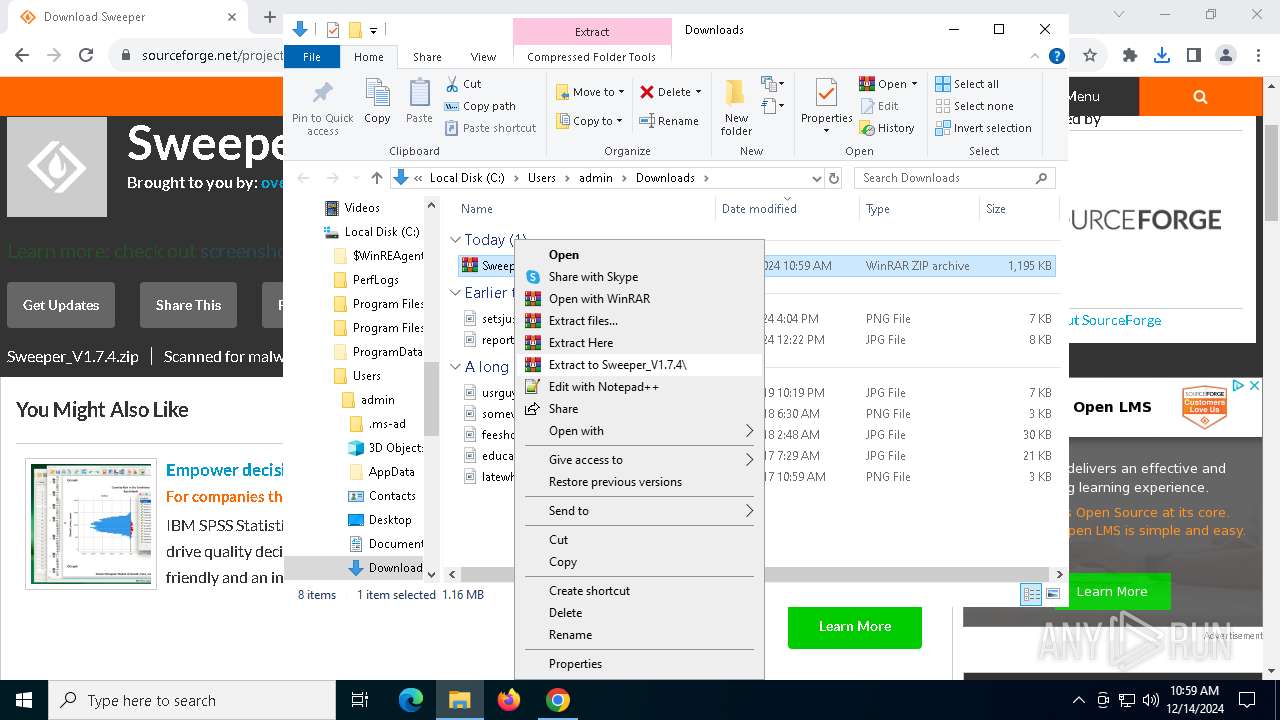
The process uses the downloaded file
- chrome.exe (PID: 3144)
- WinRAR.exe (PID: 5920)
Application launched itself
- chrome.exe (PID: 6428)
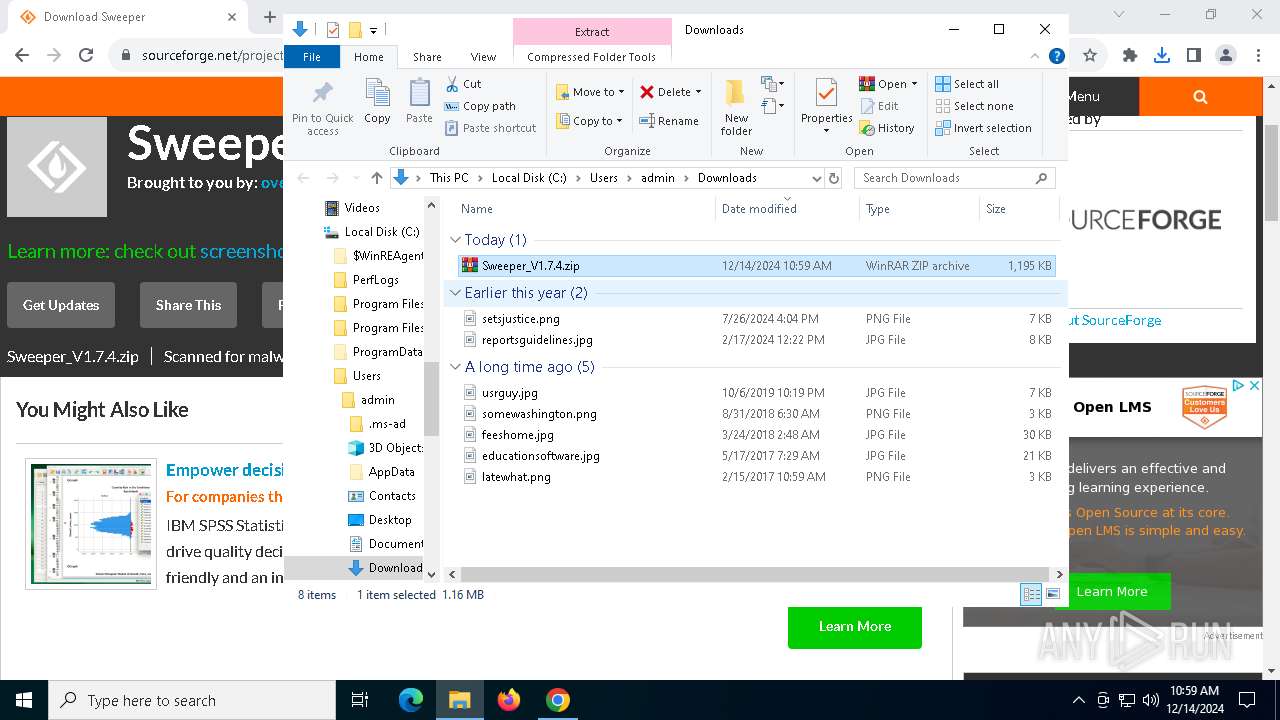
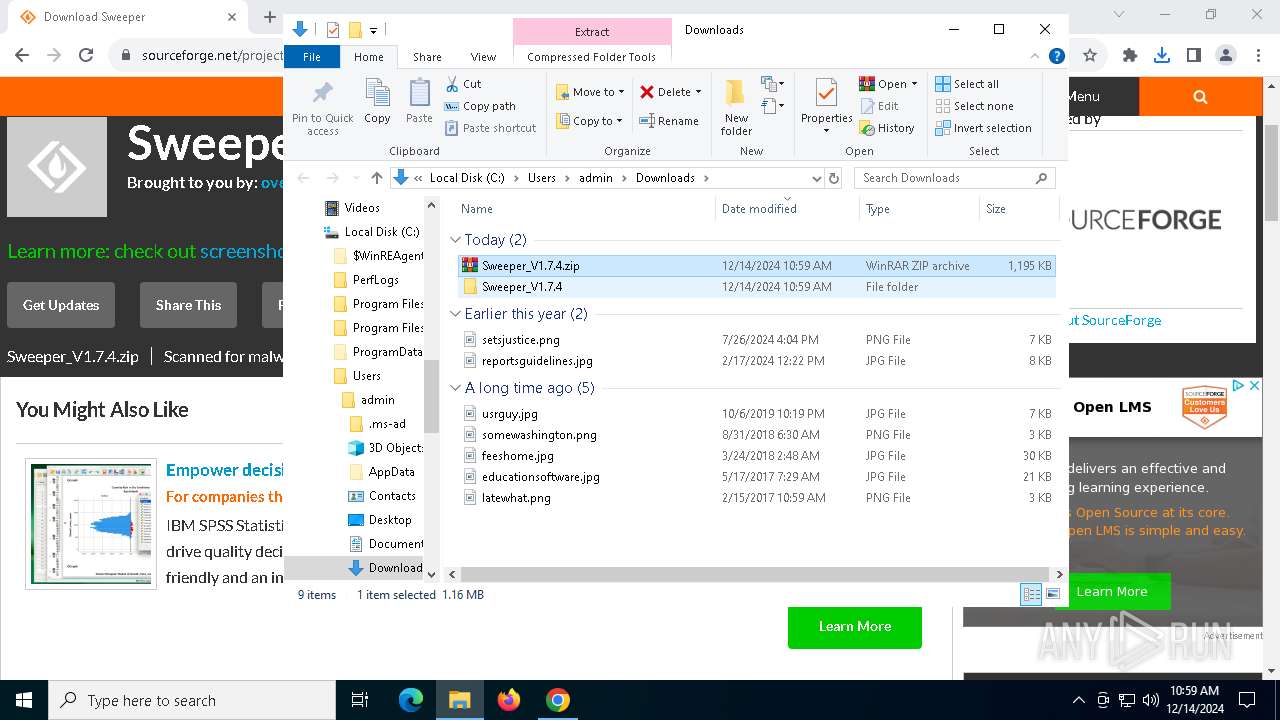
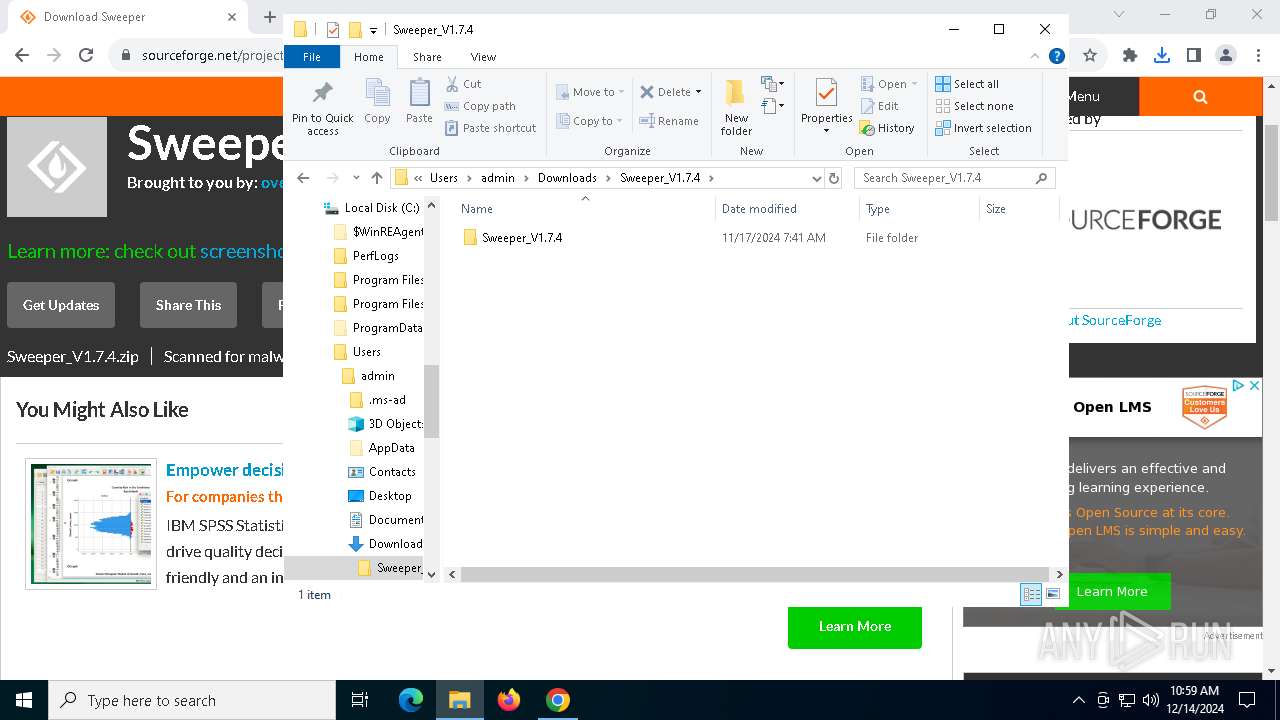
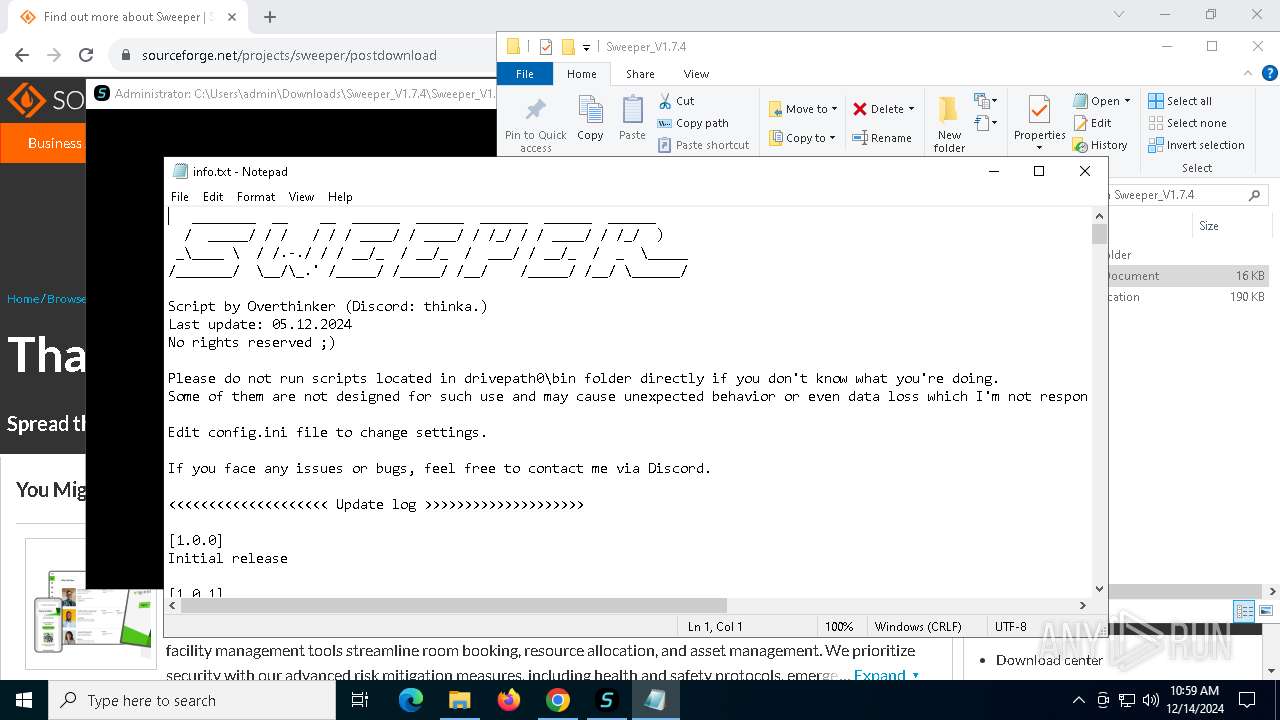
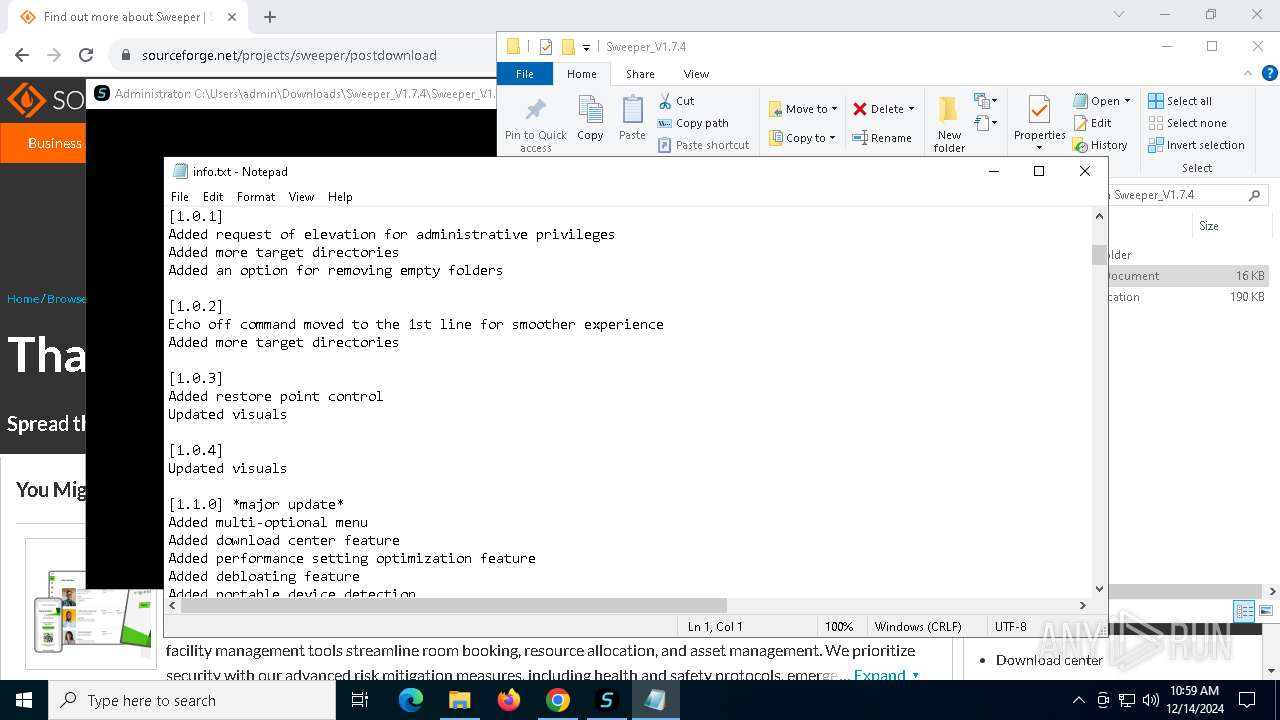
Manual execution by a user
- WinRAR.exe (PID: 5920)
- Sweeper.exe (PID: 4052)
- Sweeper.exe (PID: 5076)
- notepad.exe (PID: 7224)
Executable content was dropped or overwritten
- chrome.exe (PID: 4944)
- WinRAR.exe (PID: 5920)
- chrome.exe (PID: 7220)
- chrome.exe (PID: 3992)
Checks supported languages
- Sweeper.exe (PID: 5076)
- mode.com (PID: 7988)
- cmdmenusel.exe (PID: 8068)
- mode.com (PID: 6960)
- cmdmenusel.exe (PID: 7360)
- cmdmenusel.exe (PID: 5300)
- mode.com (PID: 3864)
- mode.com (PID: 7424)
- cmdmenusel.exe (PID: 776)
- mode.com (PID: 6964)
- cmdmenusel.exe (PID: 3828)
- mode.com (PID: 6404)
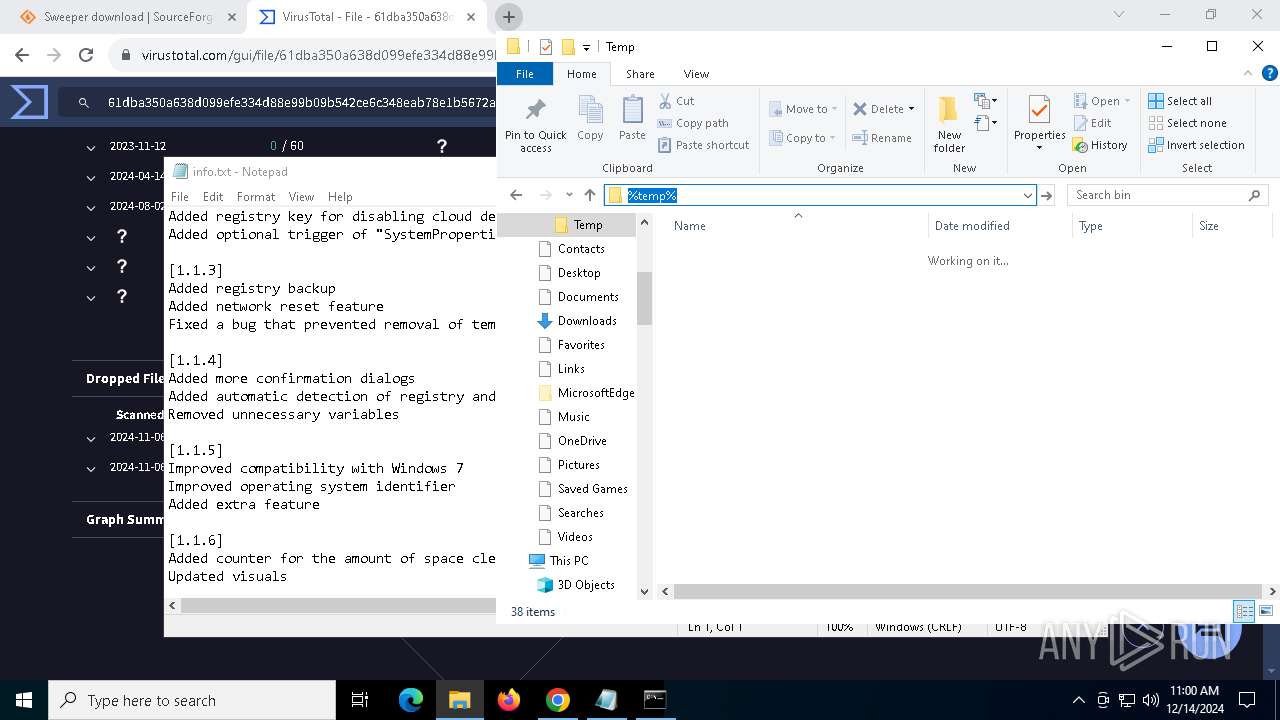
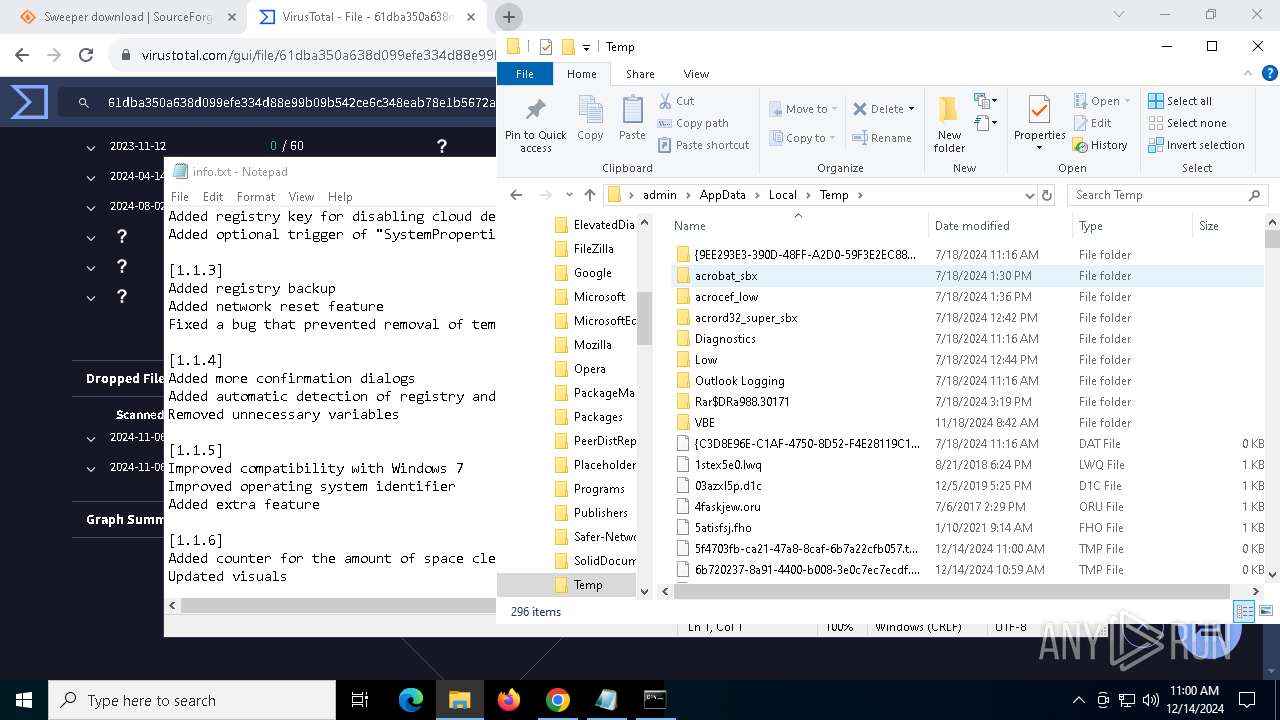
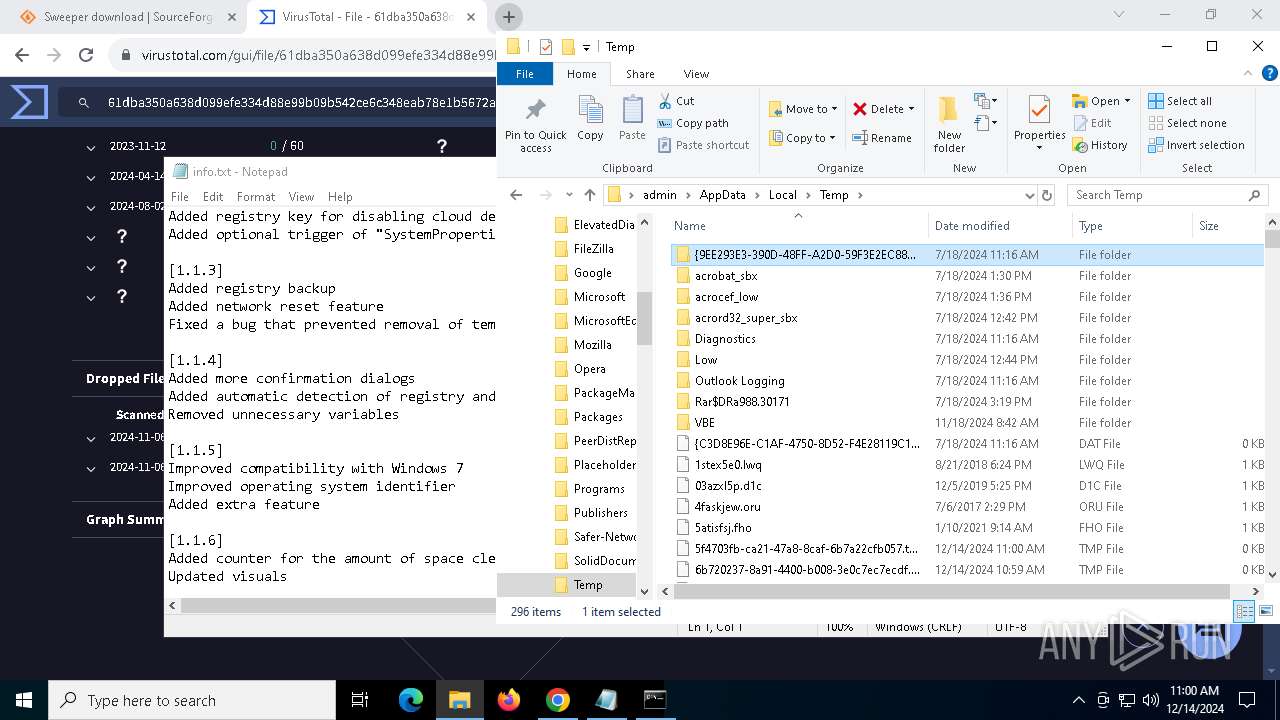
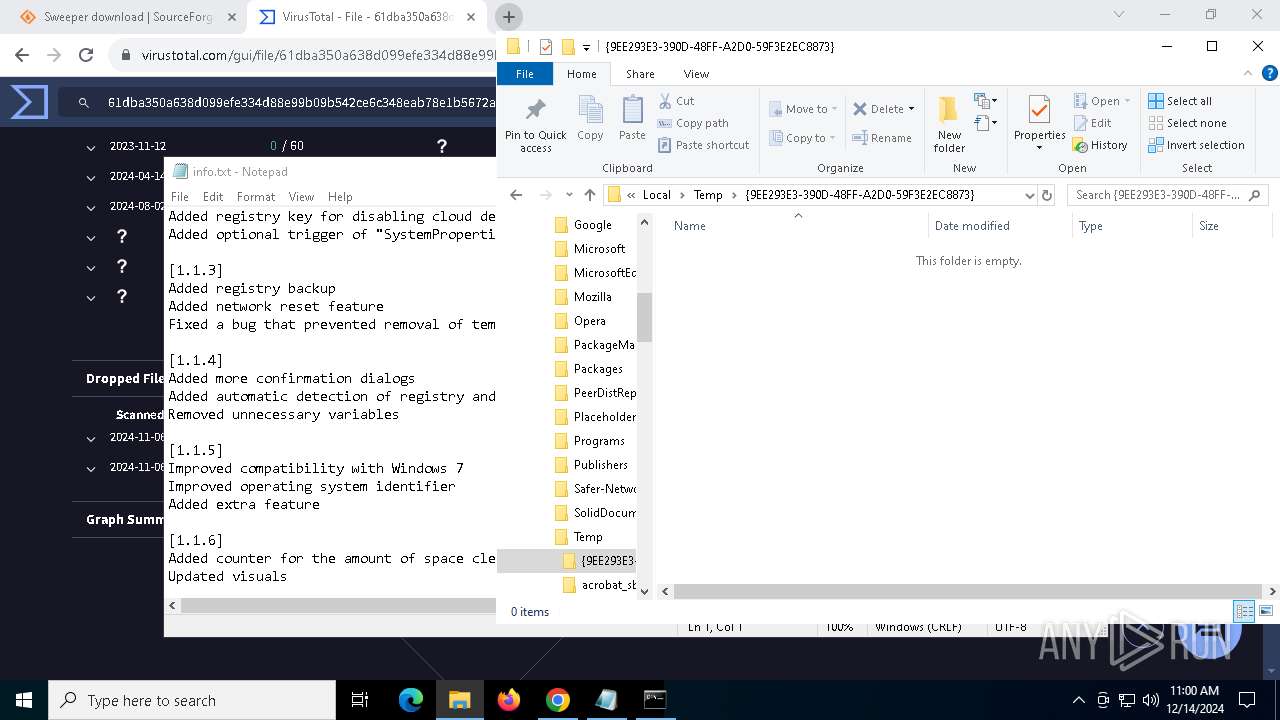
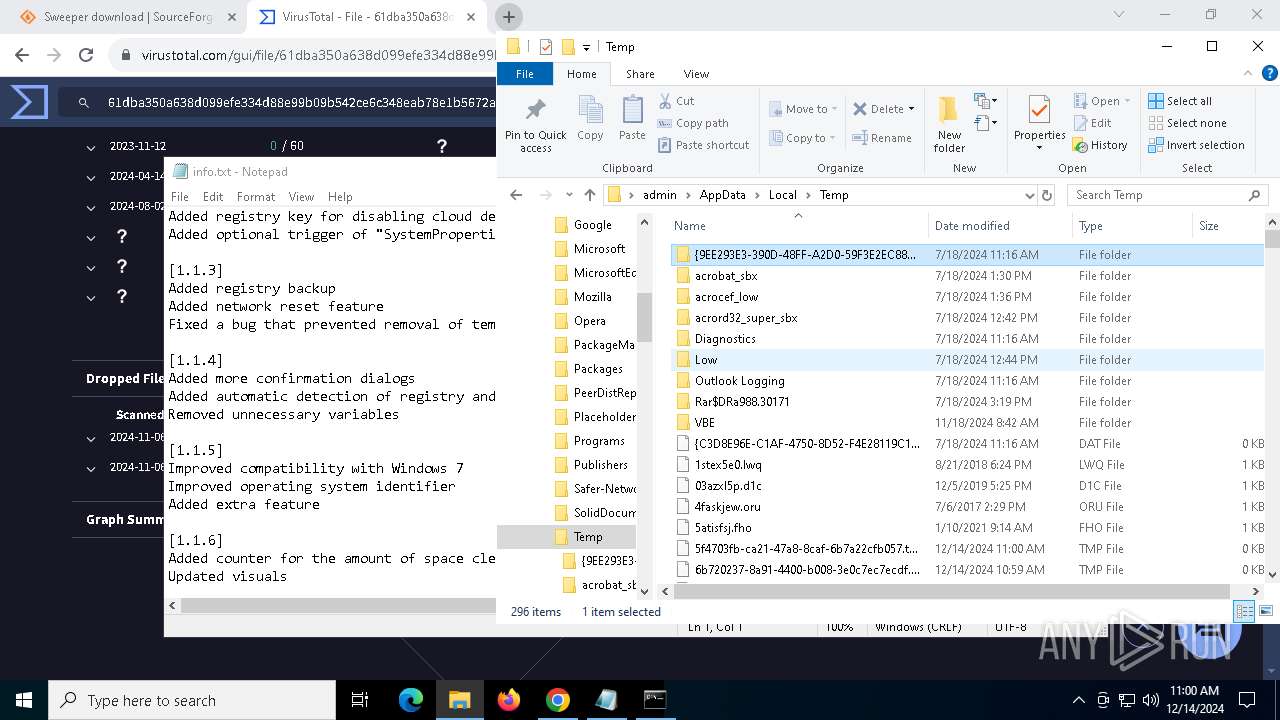
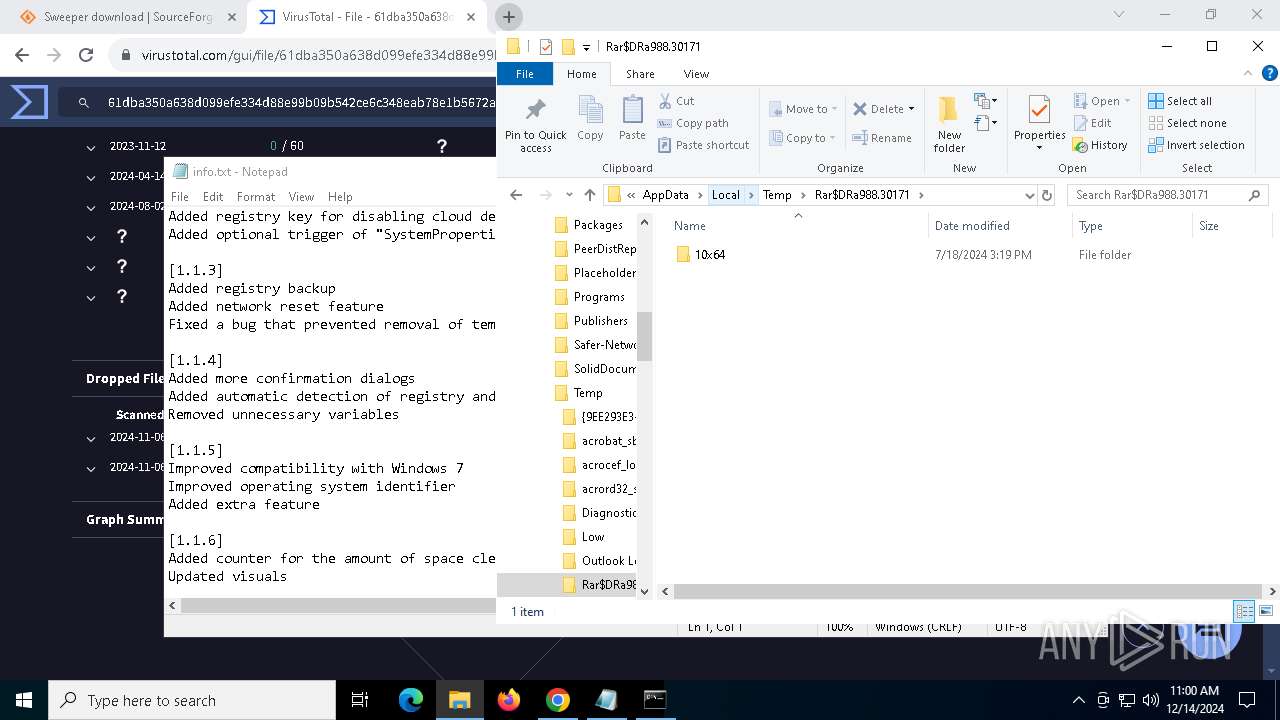
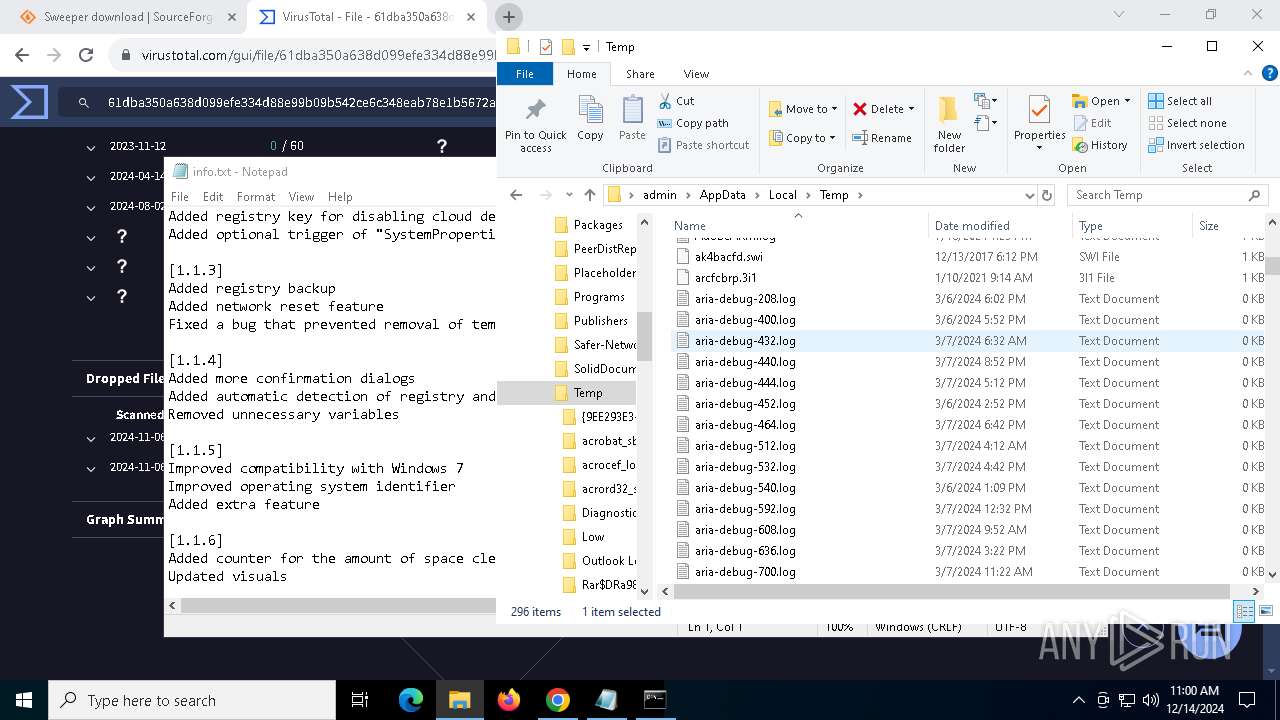
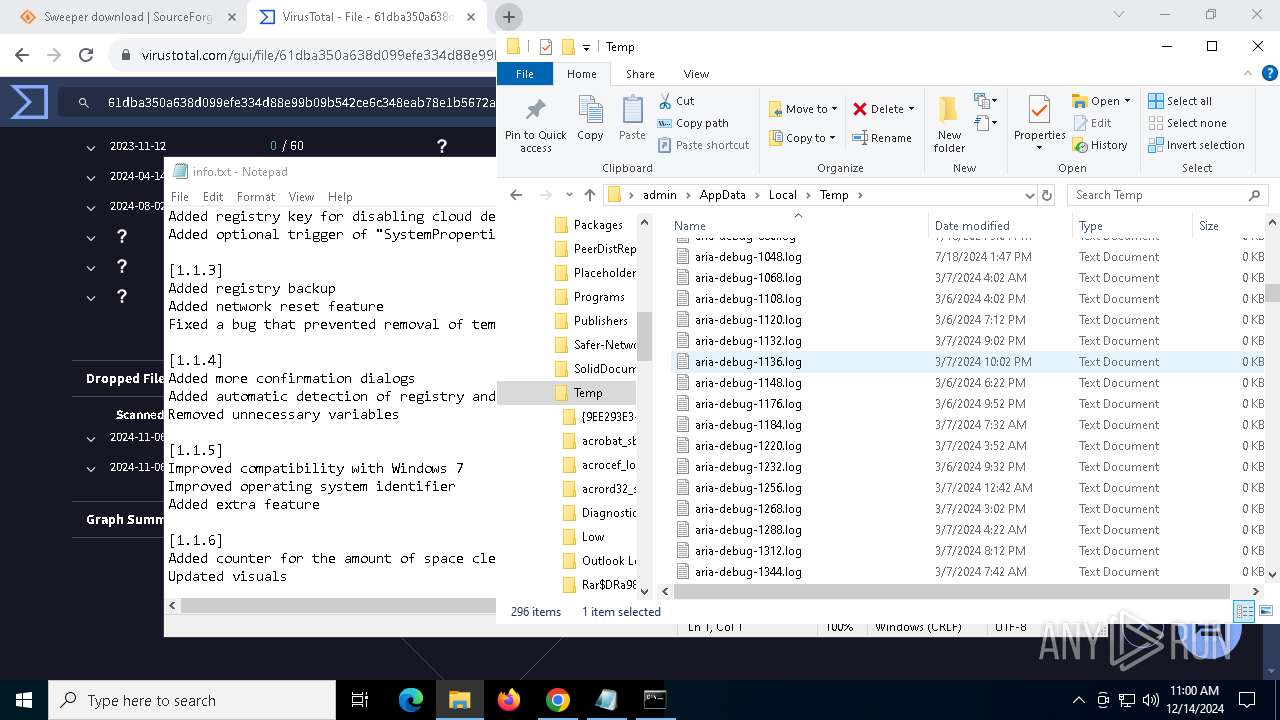
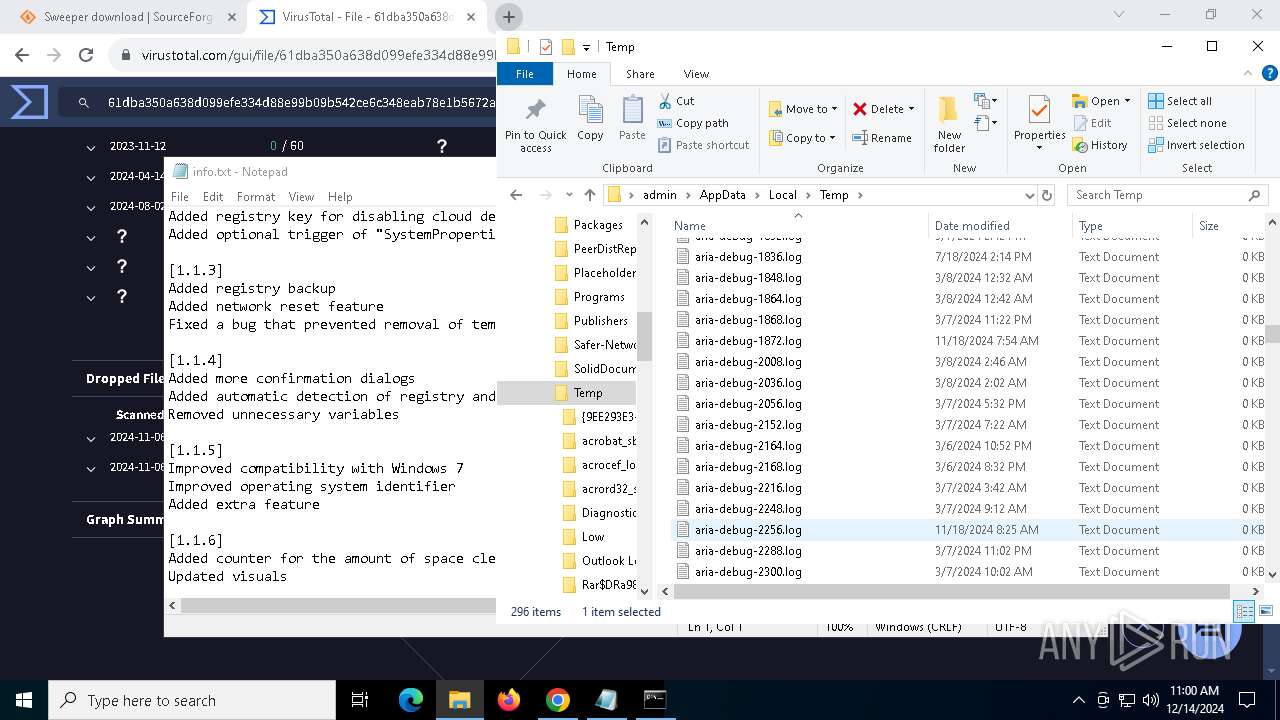
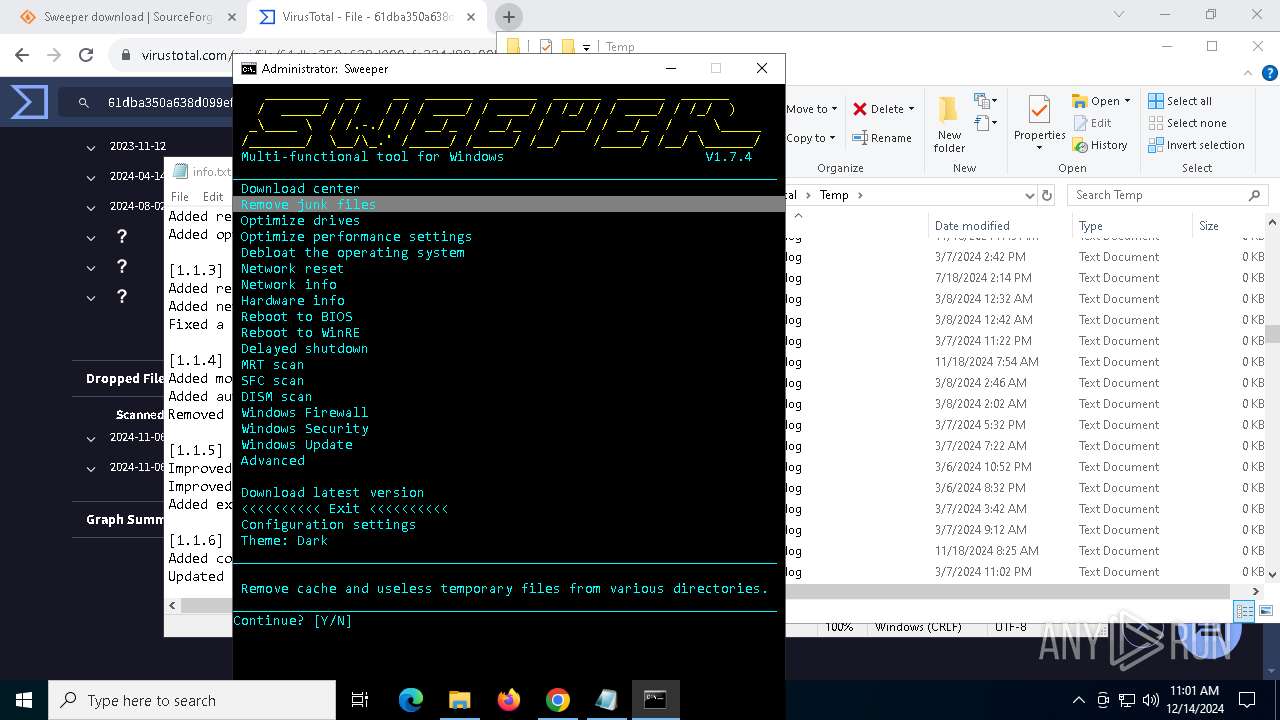
Create files in a temporary directory
- Sweeper.exe (PID: 5076)
- reg.exe (PID: 5404)
The sample compiled with english language support
- WinRAR.exe (PID: 5920)
- chrome.exe (PID: 7220)
- chrome.exe (PID: 3992)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7224)
- cscript.exe (PID: 7844)
- cscript.exe (PID: 7928)
- cscript.exe (PID: 7968)
- cscript.exe (PID: 8052)
- cscript.exe (PID: 8084)
- cscript.exe (PID: 8016)
- cscript.exe (PID: 8120)
- cscript.exe (PID: 8160)
- cscript.exe (PID: 3608)
- cscript.exe (PID: 1944)
- cscript.exe (PID: 7196)
- cscript.exe (PID: 5556)
- cscript.exe (PID: 3296)
- cscript.exe (PID: 7504)
- cscript.exe (PID: 7392)
- cscript.exe (PID: 7572)
- cscript.exe (PID: 7448)
- cscript.exe (PID: 7632)
- cscript.exe (PID: 7536)
- cscript.exe (PID: 7664)
- cscript.exe (PID: 3560)
- cscript.exe (PID: 7744)
- cscript.exe (PID: 7944)
- WMIC.exe (PID: 7824)
- cscript.exe (PID: 7624)
Starts MODE.COM to configure console settings
- mode.com (PID: 7988)
- mode.com (PID: 6960)
- mode.com (PID: 3864)
- mode.com (PID: 6404)
- mode.com (PID: 6964)
- mode.com (PID: 7424)
Gets data length (POWERSHELL)
- powershell.exe (PID: 3220)
- powershell.exe (PID: 6700)
Drops encrypted VBS script (Microsoft Script Encoder)
- cmd.exe (PID: 7756)
Reads Microsoft Office registry keys
- reg.exe (PID: 5404)
Reads the software policy settings
- reg.exe (PID: 5404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
315
Monitored processes
171
Malicious processes
6
Suspicious processes
24
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 432 | powershell -Command "(Get-WmiObject -Class Win32_LogicalDisk -Filter 'DeviceID=''C:''').FreeSpace" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | C:\WINDOWS\system32\cmd.exe /c powershell -command "Get-CimInstance -ClassName Win32_PhysicalMemory | Select-Object -ExpandProperty Speed" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 436 | C:\WINDOWS\system32\cmd.exe /c powershell -Command "(Get-WmiObject -Class Win32_LogicalDisk -Filter 'DeviceID=''C:''').FreeSpace" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 556 | powershell -command "[math]::Round(4294967296/1GB, 2)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 624 | powershell -command "Get-CimInstance -ClassName Win32_VideoController | Select-Object -ExpandProperty VideoModeDescription" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=5268 --field-trial-handle=1772,i,3518118210743745613,9519048337115081544,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
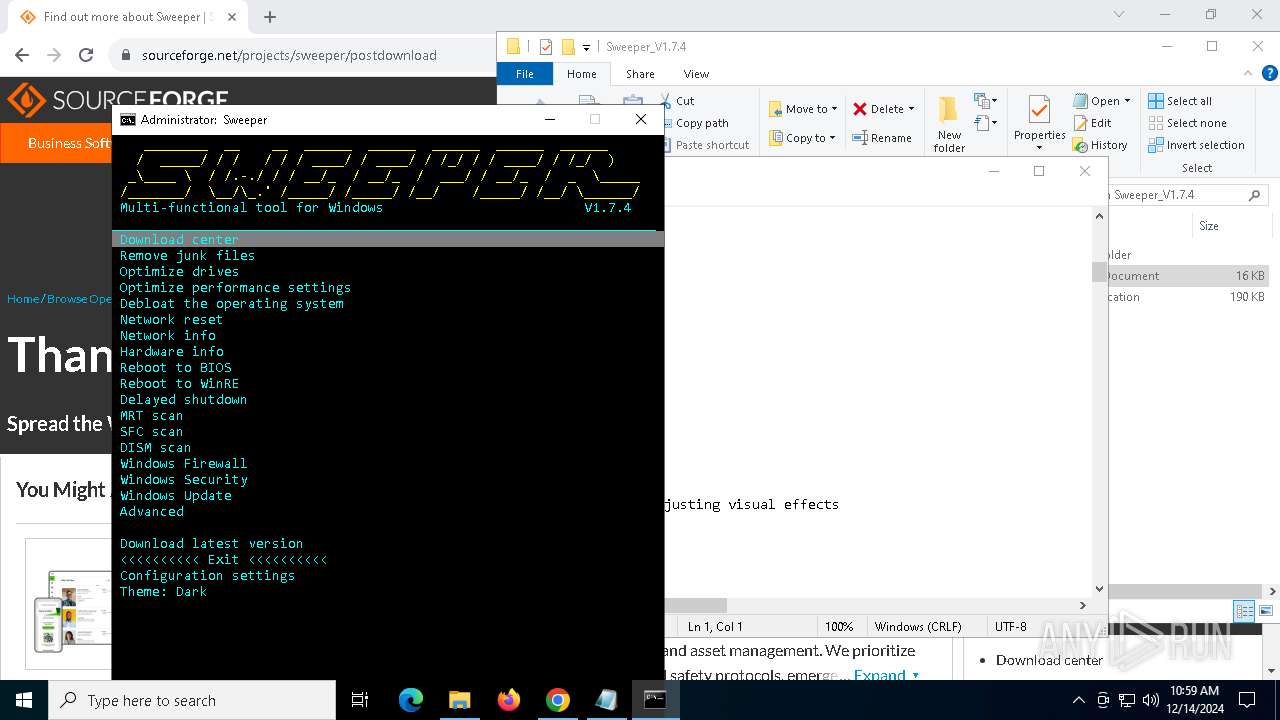
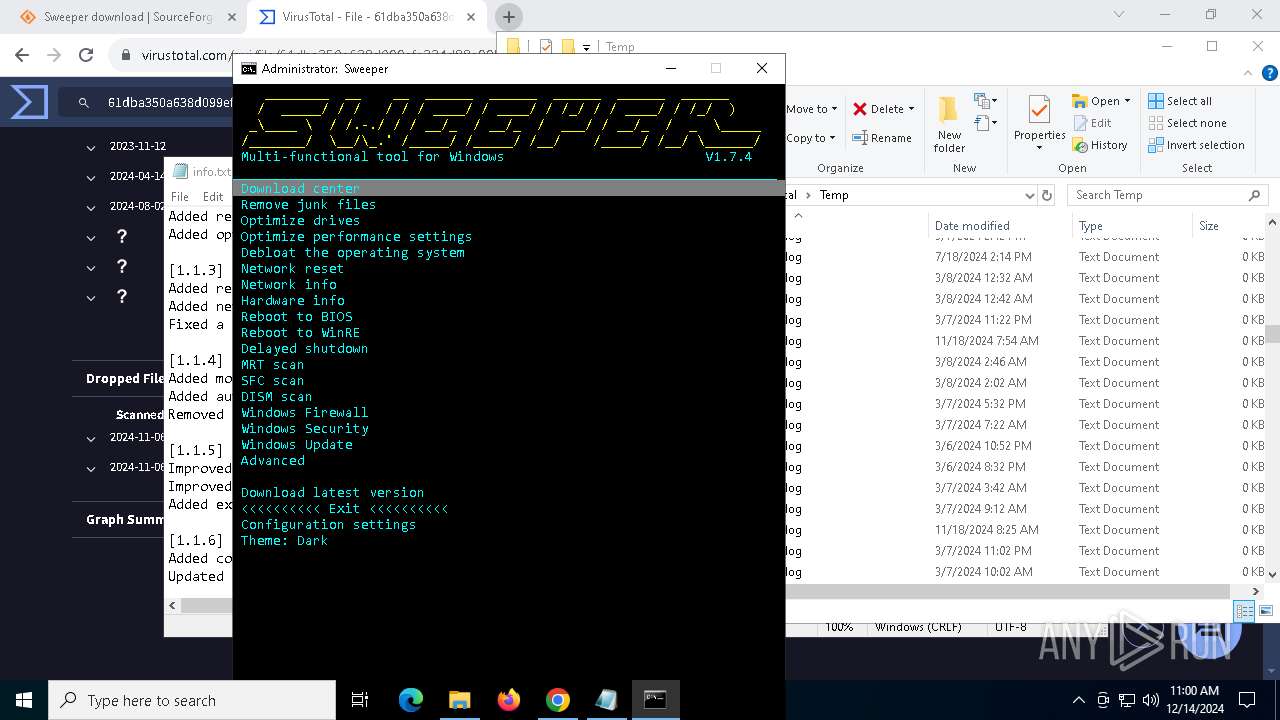
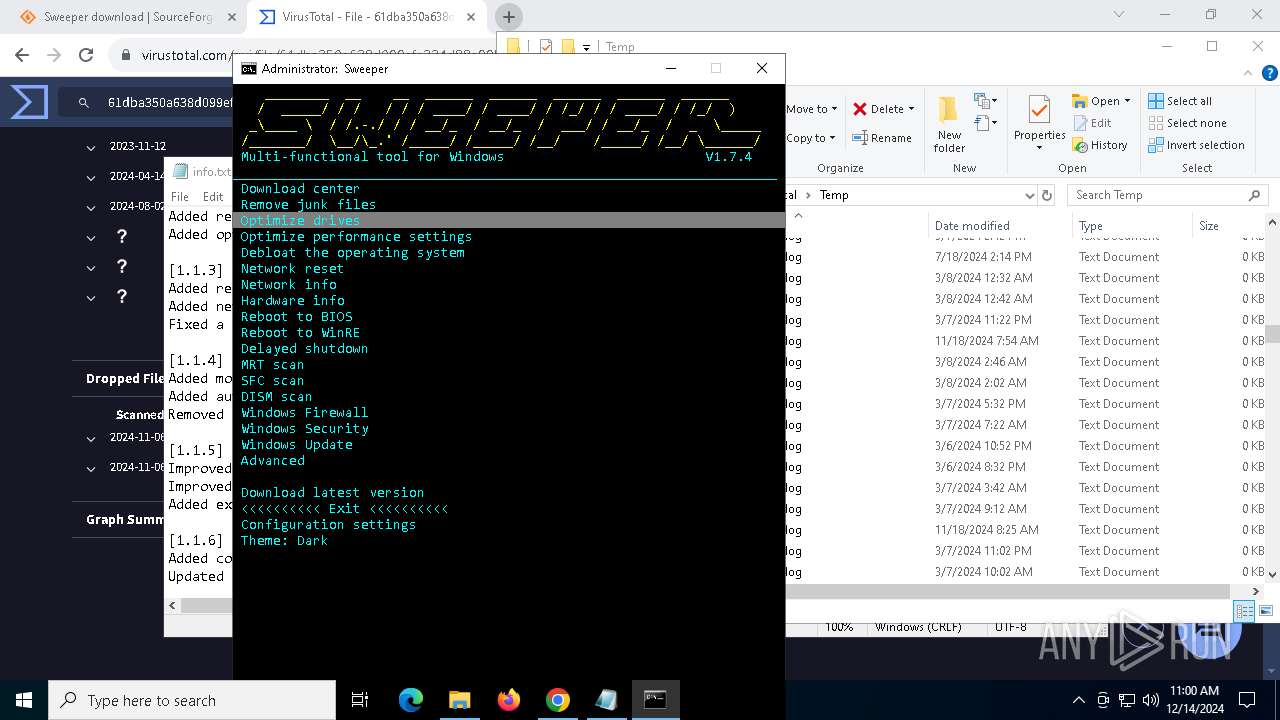
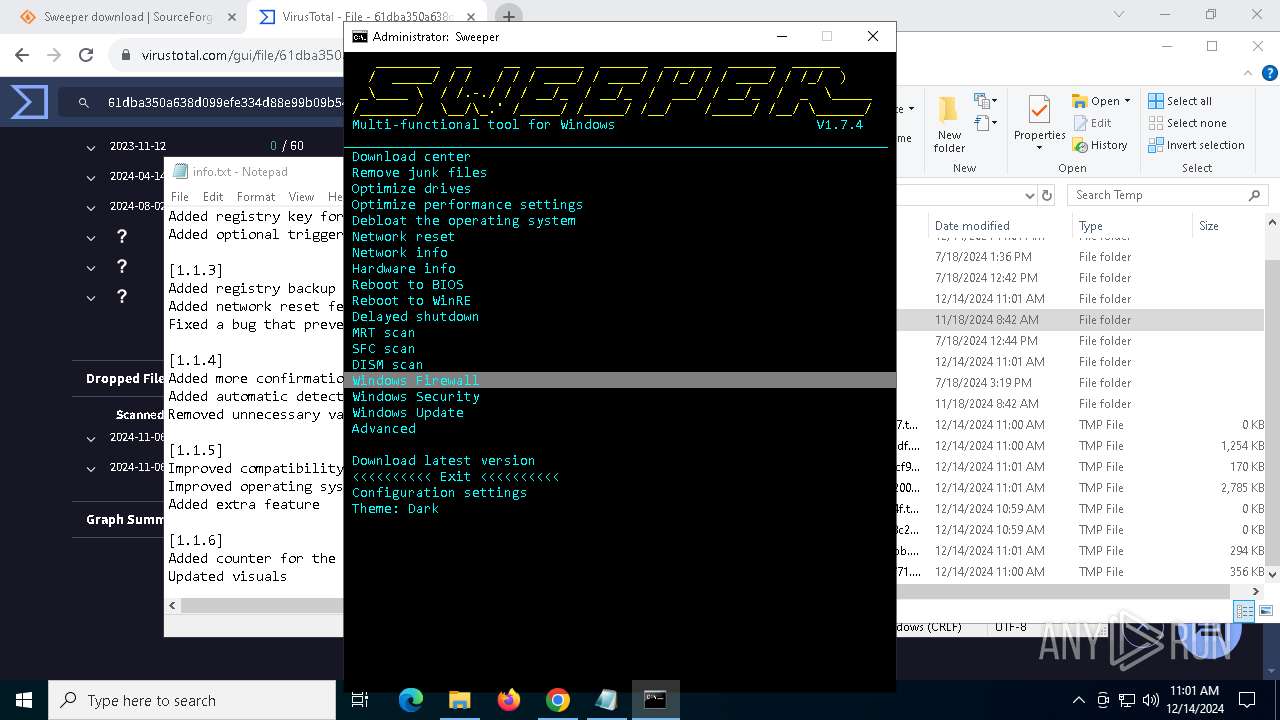
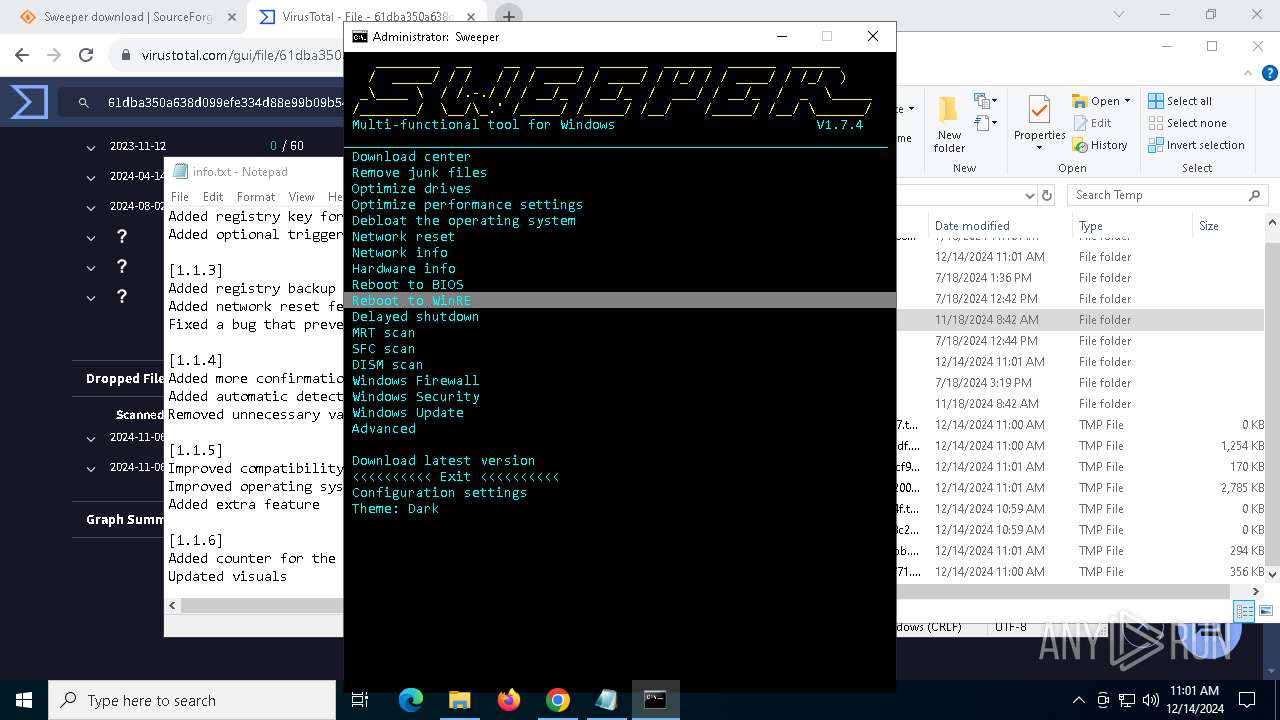
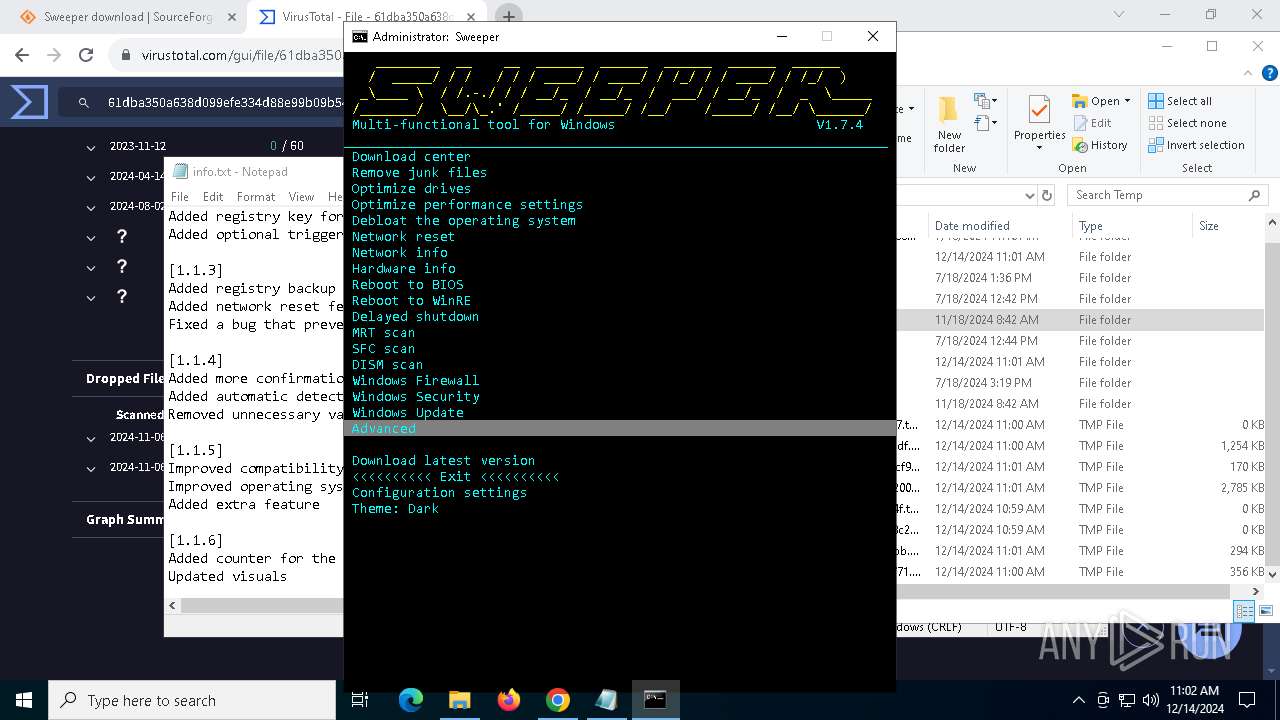
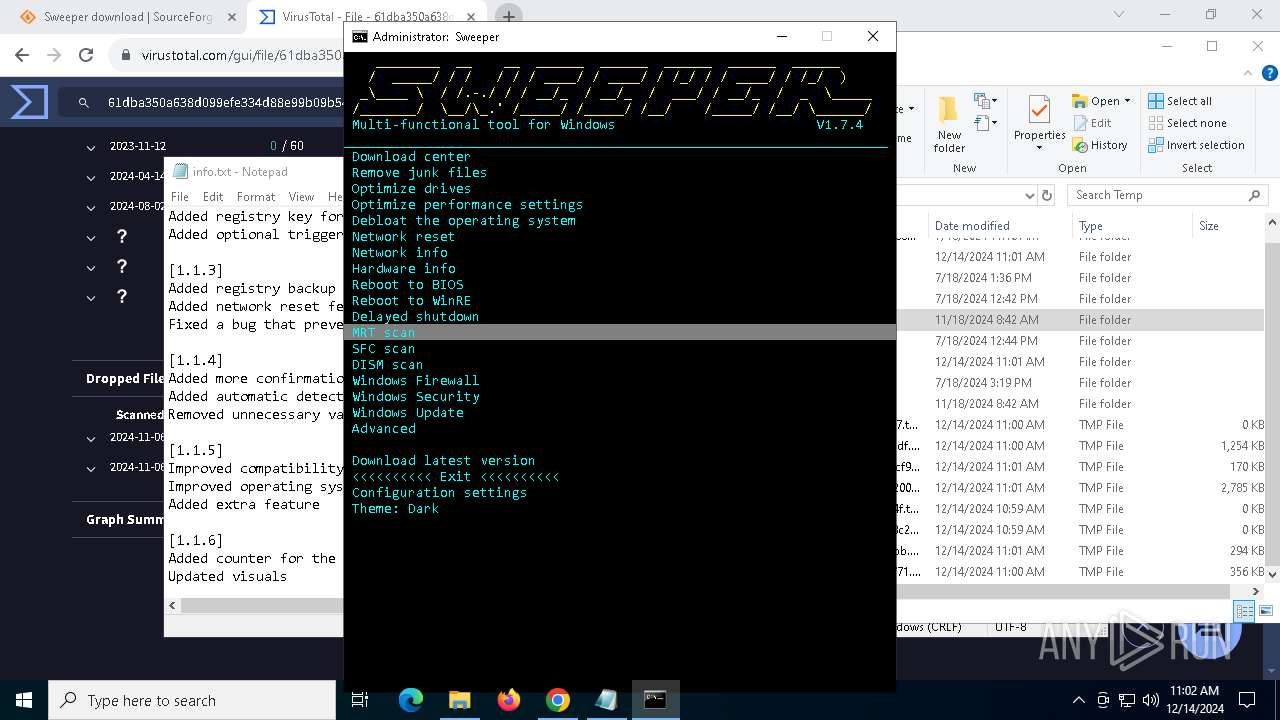
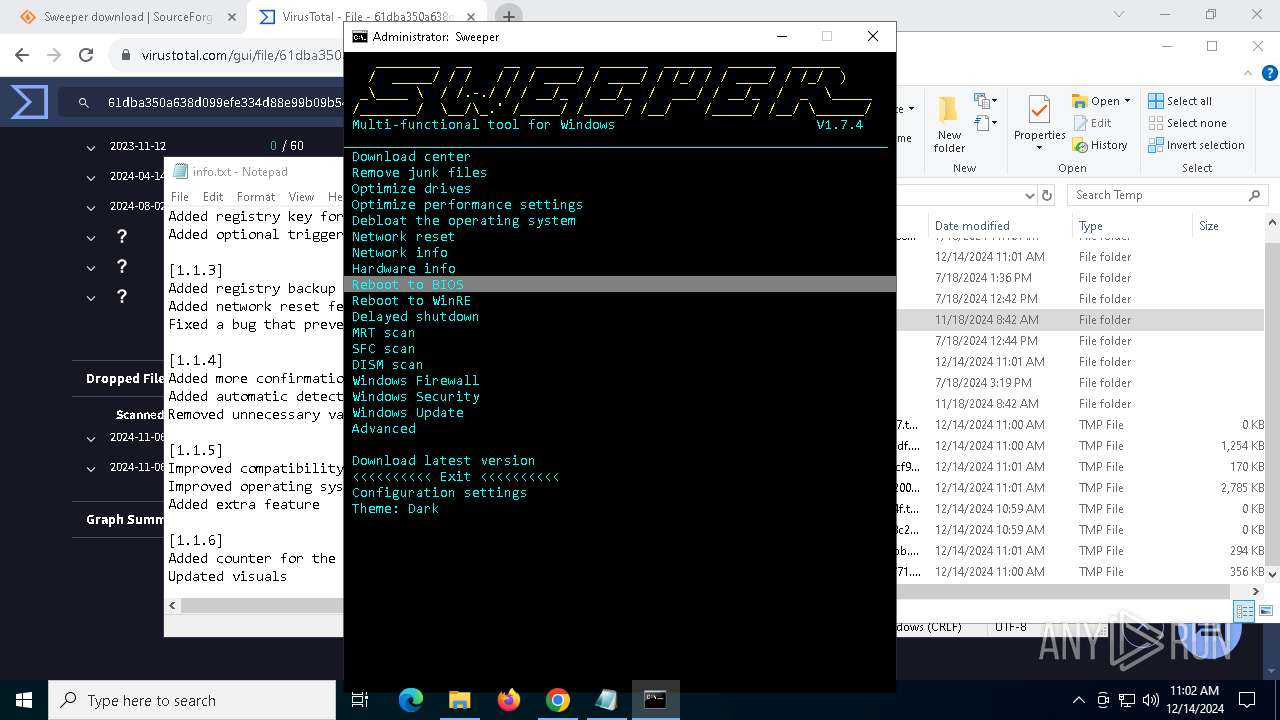
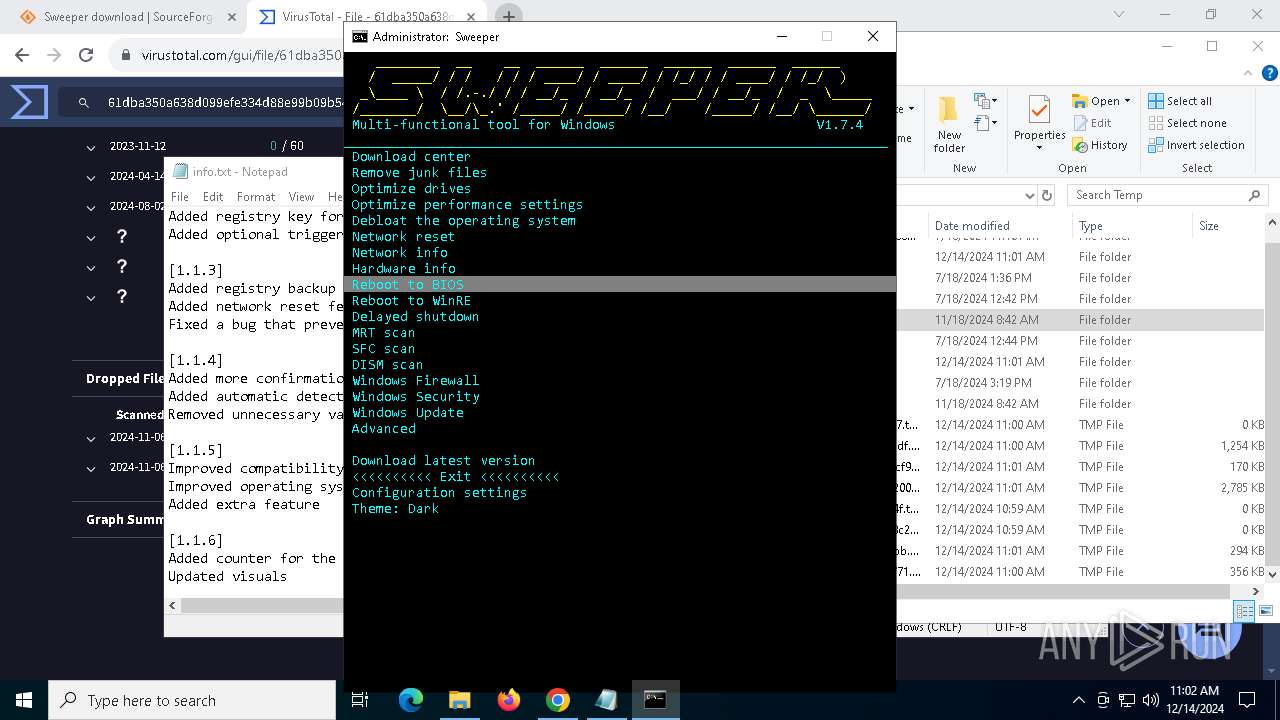
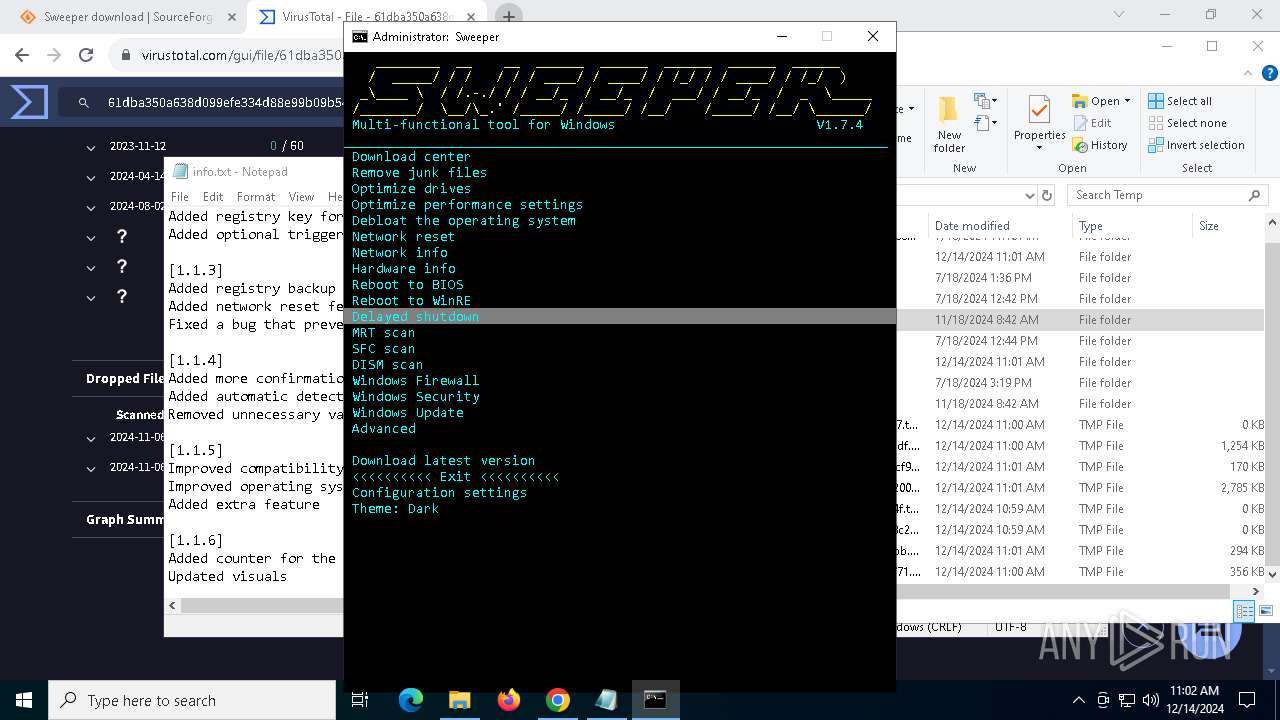
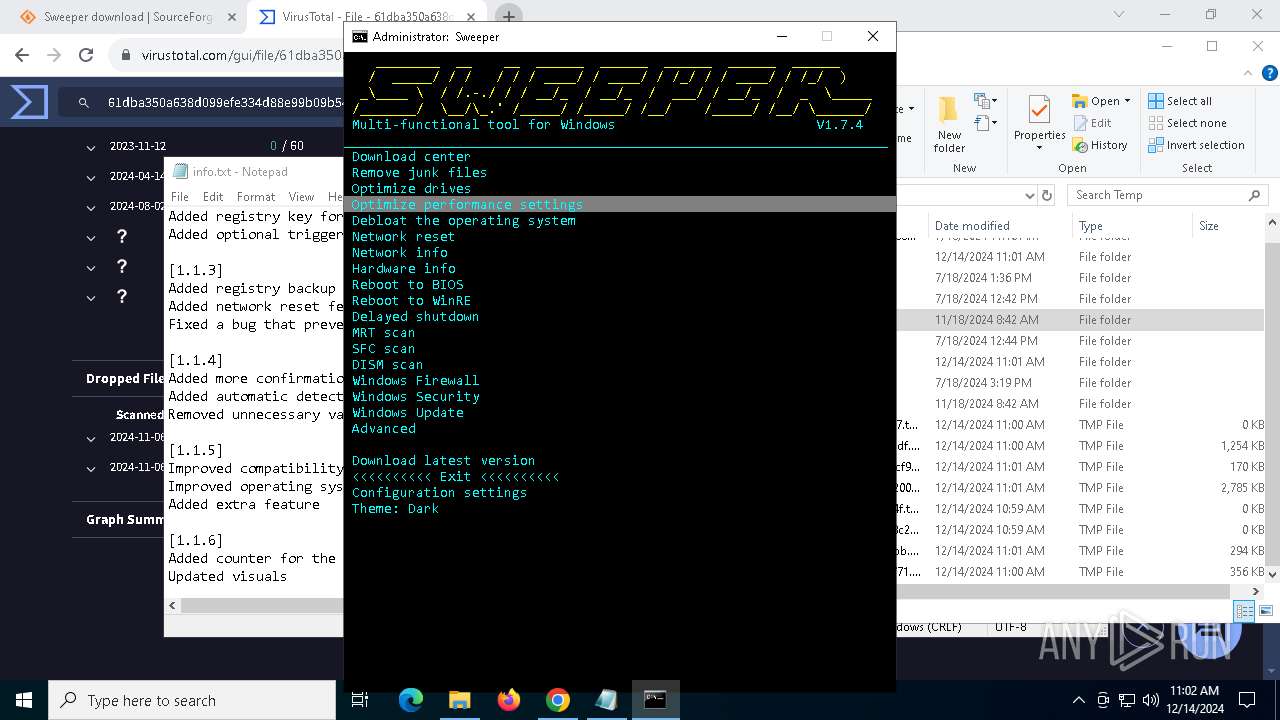
| 776 | cmdmenusel B8B0 " Download center" " Remove junk files" " Optimize drives" " Optimize performance settings" " Debloat the operating system" " Network reset" " Network info" " Hardware info" " Reboot to BIOS" " Reboot to WinRE" " Delayed shutdown" " MRT scan" " SFC scan" " DISM scan" " Windows Firewall" " Windows Security" " Windows Update" " Advanced" "" " Download latest version" " <<<<<<<<<< Exit <<<<<<<<<<" " Configuration settings" " Theme: Dark" | C:\Users\admin\Downloads\Sweeper_V1.7.4\Sweeper_V1.7.4\bin\cmdmenusel.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 9 Modules
| |||||||||||||||
| 1216 | C:\WINDOWS\system32\cmd.exe /c powershell -command "[math]::Round(4294967296/1GB, 2)" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | powershell "Get-WmiObject -Class Win32_Processor | Select-Object -ExpandProperty Name" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
589 633
Read events
589 564
Write events
44
Delete events
25
Modification events
| (PID) Process: | (6428) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6428) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6428) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6428) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6428) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000DE3F8537174EDB01 | |||
| (PID) Process: | (5920) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5920) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5920) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5920) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
12
Suspicious files
309
Text files
185
Unknown types
88
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13597d.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF13598d.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13598d.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13598d.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF13598d.TMP | — | |
MD5:— | SHA256:— | |||
| 6428 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
182
DNS requests
217
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2624 | svchost.exe | GET | 200 | 23.53.40.202:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2624 | svchost.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
848 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
848 | SIHClient.exe | GET | 200 | 23.215.121.133:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7496 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
7496 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2624 | svchost.exe | 23.53.40.202:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2624 | svchost.exe | 23.215.121.133:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.19.80.89:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6852 | chrome.exe | 104.18.12.149:443 | sourceforge.net | CLOUDFLARENET | — | whitelisted |
6428 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sourceforge.net |
| whitelisted |
accounts.google.com |
| whitelisted |
a.fsdn.com |
| whitelisted |
d.delivery.consentmanager.net |
| whitelisted |