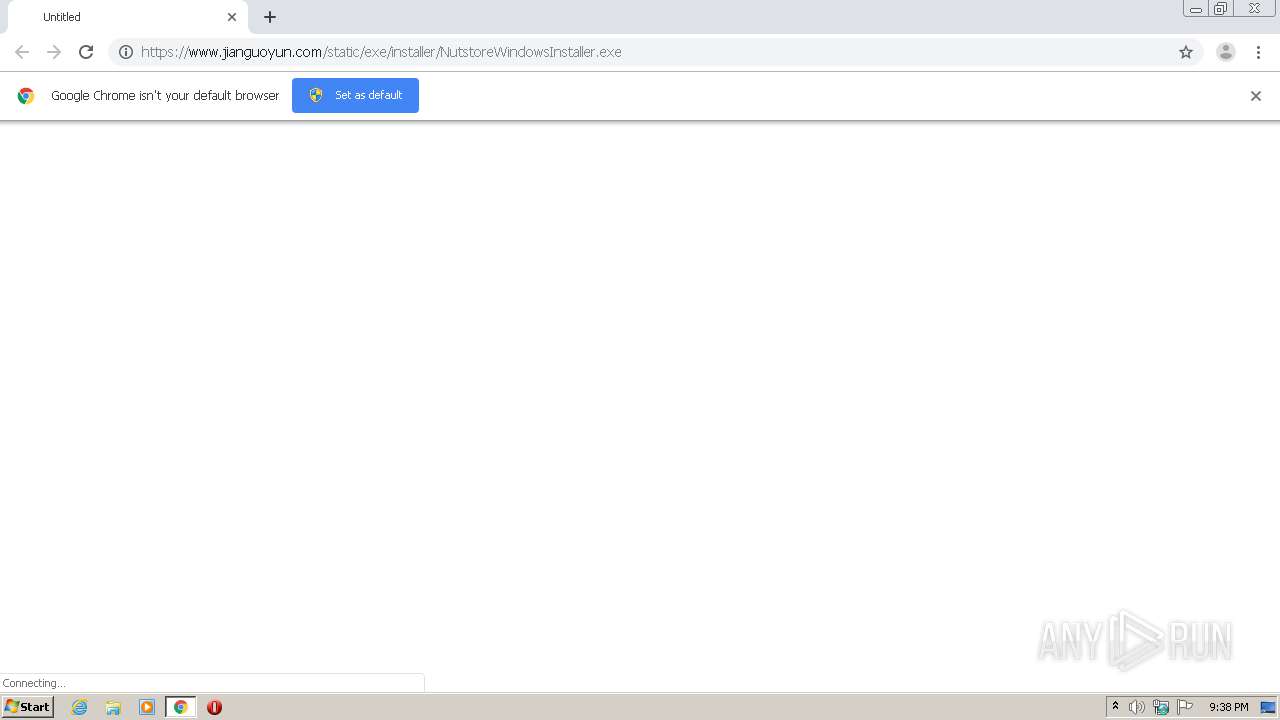
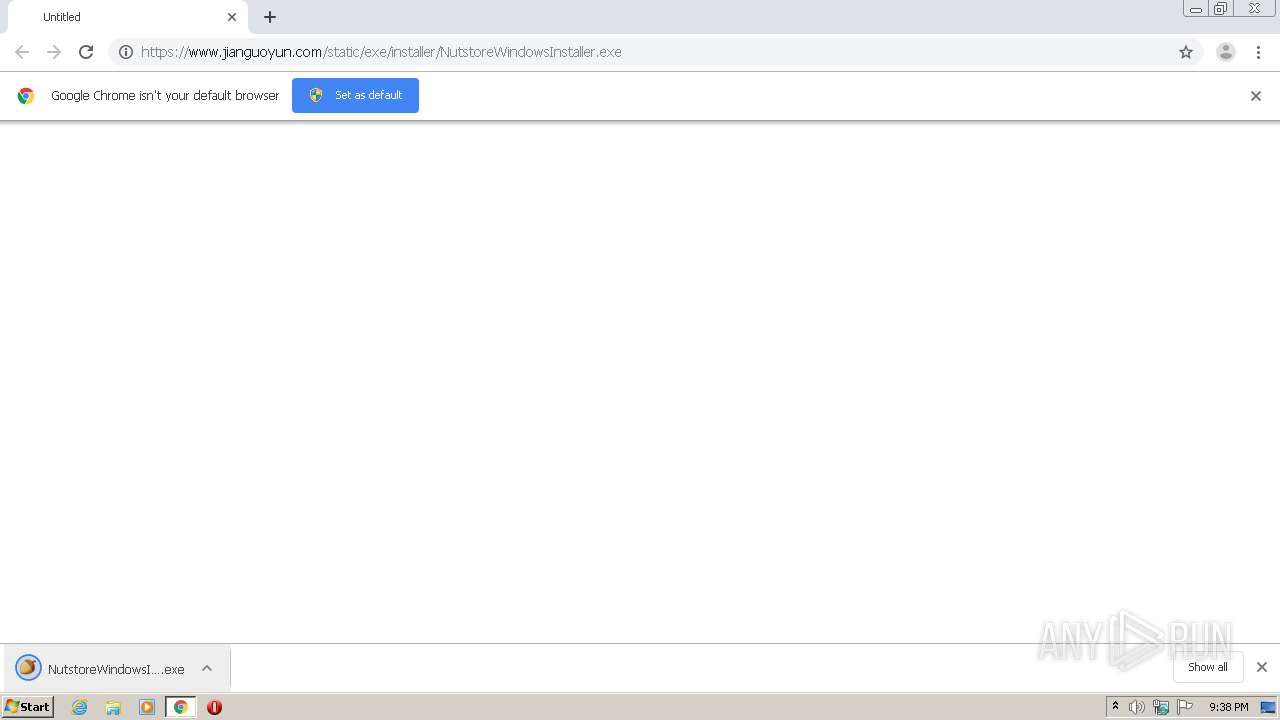
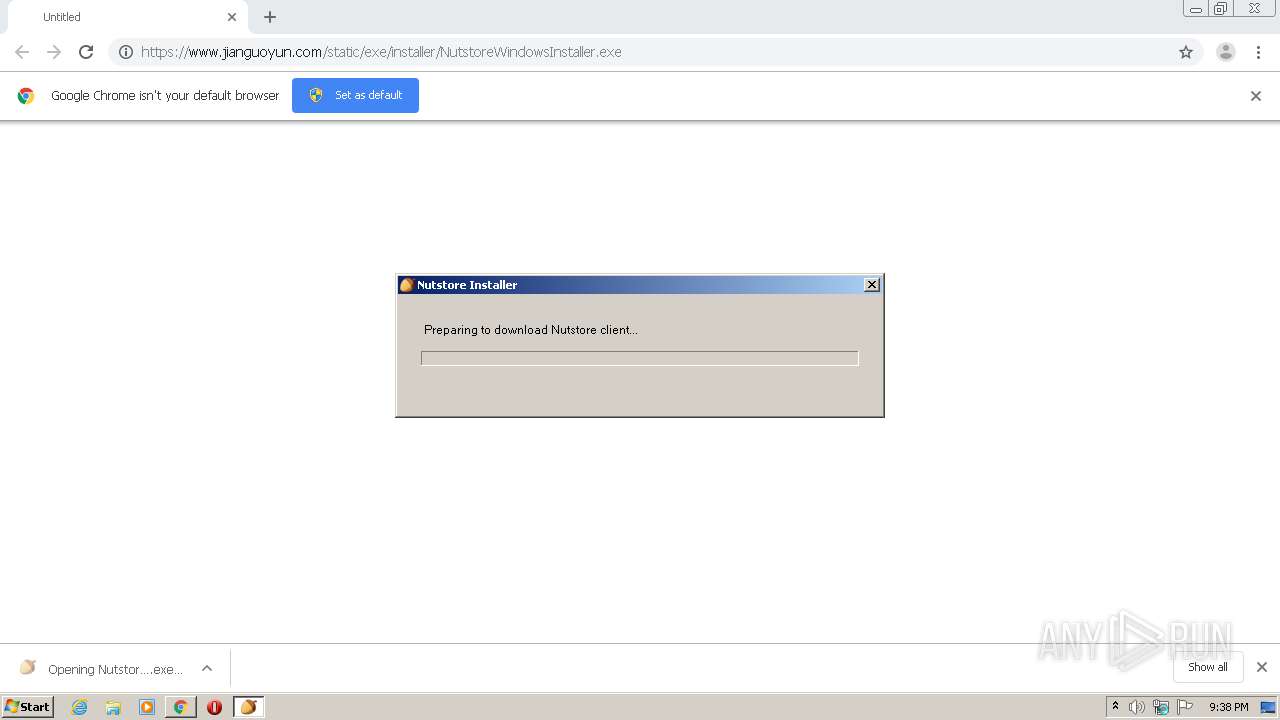
| URL: | https://www.jianguoyun.com/static/exe/installer/NutstoreWindowsInstaller.exe |
| Full analysis: | https://app.any.run/tasks/72205bbd-4787-456b-abcd-7223448c0730 |
| Verdict: | Malicious activity |
| Analysis date: | March 16, 2021, 21:38:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3EE7EE4B3675E6FE25C9639341B95F88 |
| SHA1: | 8E6D9C86F6C893F7F476A5A54971BB795B962F14 |
| SHA256: | 4960C8F84AC12FA3E64E7CC8925E5C9B9F850A621FA6D142C43E59FB97631B97 |
| SSDEEP: | 3:N8DSL0E2QKcUwRBGKYkOXKbsQosWigXLNn:2OL0E3K2RfOXisQo3TXLN |
MALICIOUS
Application was dropped or rewritten from another process
- NutstoreWindowsInstaller.exe (PID: 2248)
- NutstoreWindowsInstaller.exe (PID: 2692)
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
- MaintenanceService.exe (PID: 1276)
- NTFSWatcher.exe (PID: 2752)
- NTFSWatcher.exe (PID: 1760)
- NsExtInstaller.exe (PID: 2460)
- RegisterExtensionDotNet40.exe (PID: 3588)
- NutstoreClient.exe (PID: 1344)
- Nutstore.exe (PID: 1748)
- MaintenanceService.exe (PID: 2568)
- NutstoreWatchDog.exe (PID: 3604)
- PostUpdater.exe (PID: 2276)
Changes settings of System certificates
- NutstoreWindowsInstaller.exe (PID: 2692)
Loads dropped or rewritten executable
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
- rundll32.exe (PID: 2588)
- rundll32.exe (PID: 4012)
- RegisterExtensionDotNet40.exe (PID: 3588)
- NsExtInstaller.exe (PID: 2460)
- rundll32.exe (PID: 3680)
- NutstoreClient.exe (PID: 1344)
- explorer.exe (PID: 3448)
- svchost.exe (PID: 856)
- chrome.exe (PID: 3016)
Drops executable file immediately after starts
- rundll32.exe (PID: 2588)
- rundll32.exe (PID: 3680)
- rundll32.exe (PID: 1708)
Loads the Task Scheduler DLL interface
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
Loads the Task Scheduler COM API
- explorer.exe (PID: 3448)
SUSPICIOUS
Executable content was dropped or overwritten
- NutstoreWindowsInstaller.exe (PID: 2692)
- chrome.exe (PID: 3456)
- rundll32.exe (PID: 2588)
- rundll32.exe (PID: 4012)
- rundll32.exe (PID: 3680)
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
- rundll32.exe (PID: 1708)
Creates files in the user directory
- NutstoreWindowsInstaller.exe (PID: 2692)
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
- RegisterExtensionDotNet40.exe (PID: 3588)
- NutstoreClient.exe (PID: 1344)
- NutstoreWatchDog.exe (PID: 3604)
Adds / modifies Windows certificates
- NutstoreWindowsInstaller.exe (PID: 2692)
Drops a file that was compiled in debug mode
- NutstoreWindowsInstaller.exe (PID: 2692)
- rundll32.exe (PID: 2588)
- rundll32.exe (PID: 3680)
- rundll32.exe (PID: 4012)
- rundll32.exe (PID: 1708)
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
Starts Microsoft Installer
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
Reads Environment values
- MsiExec.exe (PID: 3436)
- MsiExec.exe (PID: 2108)
- NutstoreClient.exe (PID: 1344)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 2108)
Starts CMD.EXE for commands execution
- MsiExec.exe (PID: 2108)
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
- cmd.exe (PID: 560)
Drops a file with too old compile date
- tmpAC6D.tmp_NsInstaller.exe (PID: 2804)
Creates files in the program directory
- rundll32.exe (PID: 4012)
- MaintenanceService.exe (PID: 1276)
- NTFSWatcher.exe (PID: 2752)
- NsExtInstaller.exe (PID: 2460)
- NutstoreClient.exe (PID: 1344)
- MaintenanceService.exe (PID: 2568)
- RegisterExtensionDotNet40.exe (PID: 3588)
Executed as Windows Service
- NTFSWatcher.exe (PID: 1760)
- MaintenanceService.exe (PID: 2568)
Creates/Modifies COM task schedule object
- RegisterExtensionDotNet40.exe (PID: 3588)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 560)
Application launched itself
- cmd.exe (PID: 560)
Creates files in the Windows directory
- MaintenanceService.exe (PID: 2568)
INFO
Application launched itself
- chrome.exe (PID: 3456)
Reads the hosts file
- chrome.exe (PID: 3456)
- chrome.exe (PID: 3196)
Reads settings of System Certificates
- NutstoreWindowsInstaller.exe (PID: 2692)
- NutstoreClient.exe (PID: 1344)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2204)
- MsiExec.exe (PID: 3436)
- MsiExec.exe (PID: 2108)
Application was dropped or rewritten from another process
- MSIBCD.tmp (PID: 2352)
- MSI163D.tmp (PID: 1156)
Manual execution by user
- Nutstore.exe (PID: 1748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
40
Malicious processes
16
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | cmd /c ""C:\Users\admin\AppData\Local\Temp\EXE2D29.bat" " | C:\Windows\system32\cmd.exe | — | tmpAC6D.tmp_NsInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c23a9d0,0x6c23a9e0,0x6c23a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 856 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | C:\Windows\system32\cmd.exe /S /D /c" cls" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1156 | "C:\Windows\Installer\MSI163D.tmp" /DontWait "C:\Program Files\Nutstore\Nutstore.exe" | C:\Windows\Installer\MSI163D.tmp | msiexec.exe | ||||||||||||
User: admin Company: Caphyon LTD Integrity Level: HIGH Description: File that launches another file Exit code: 0 Version: 16.6.1.0 Modules
| |||||||||||||||
| 1260 | C:\Windows\System32\attrib.exe -r "C:\Users\admin\AppData\Local\Temp\EXE2D29.bat" | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1276 | "C:\ProgramData\Nutstore\service\MaintenanceService.exe" install | C:\ProgramData\Nutstore\service\MaintenanceService.exe | — | rundll32.exe | |||||||||||
User: SYSTEM Company: Shanghai Yicun Network Ltd. Integrity Level: SYSTEM Description: Nutstore Maintenance Service Exit code: 0 Version: 5.2.2.0 Modules
| |||||||||||||||
| 1344 | "C:\Program Files\Nutstore\bin-5.2.2\NutstoreClient.exe" | C:\Program Files\Nutstore\bin-5.2.2\NutstoreClient.exe | — | Nutstore.exe | |||||||||||
User: admin Company: Shanghai Yicun Network Ltd. Integrity Level: MEDIUM Description: Nutstore Client Exit code: 0 Version: 5.2.2 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,3734824550845268837,18398950890246003906,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10945981558264554875 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | rundll32.exe "C:\Windows\Installer\MSI534.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_918828 272 NutstoreCustomAction!NutstoreCustomAction.CustomActions.RunWithoutGUI | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 784
Read events
3 255
Write events
523
Delete events
6
Modification events
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | _ObjectId_ |
Value: F000000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services |
| Operation: | write | Name: | ObjectId |
Value: F000000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services |
| Operation: | write | Name: | ObjectLru |
Value: 0804000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | _ObjectLru_ |
Value: 0804000000000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | _FileId_ |
Value: 29C2000000000400 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | _Usn_ |
Value: 78EF0C0500000000 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class |
| Operation: | write | Name: | _UsnJournalId_ |
Value: CAF752A8FD3DD301 | |||
| (PID) Process: | (856) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\DeviceClasses |
| Operation: | write | Name: | F0 |
Value: F000000000000000 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3456) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
Executable files
201
Suspicious files
20
Text files
159
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60512567-D80.pma | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dc235bab-c97a-4032-8262-c57c0f0c8c93.tmp | — | |
MD5:— | SHA256:— | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 856 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:6534F5B88C7C04BDAF5C8EA10E166F82 | SHA256:4F771DBD2CAD230E51CDAFC9AEC8909916160651EC8176C5AA8E19F1EDD28685 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT~RFd901b.TMP | text | |
MD5:74D4DB05A4D3E7263E8AE314DEDD8DF1 | SHA256:67BF9950E818713E054268D40BED61A22D324385CE98E89DDF406A405B870802 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFd8f40.TMP | text | |
MD5:FB5B20517A0D1F7DAD485989565BEE5E | SHA256:99405F66EDBEB2306F4D0B4469DCADFF5293B5E1549C588CCFACEA439BB3B101 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFd8f40.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3456 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
10
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | MaintenanceService.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEC58h8wOk0pS%2FpT9HLfNNK8%3D | US | der | 727 b | whitelisted |
2568 | MaintenanceService.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSSdxXdG447ymkRNPVViULv3rkBzQQUKZFg%2F4pN%2Buv5pmq4z%2FnmS71JzhICEQDBe7OUevI91JYAncnk6qQP | US | der | 510 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3196 | chrome.exe | 35.244.242.96:443 | www.jianguoyun.com | — | US | unknown |
3196 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3196 | chrome.exe | 142.250.185.206:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
— | — | 35.244.242.96:443 | www.jianguoyun.com | — | US | unknown |
— | — | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
3196 | chrome.exe | 142.250.185.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.jianguoyun.com |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
Threats
Process | Message |
|---|---|
tmpAC6D.tmp_NsInstaller.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\tmpAC6D.tmp_NsInstaller.exe] CPU: __isa_available = 5
|
tmpAC6D.tmp_NsInstaller.exe | [AVX_CRT_Fix][\\?\C:\Users\admin\AppData\Roaming\NutstoreClient\install\decoder.dll] CPU: __isa_available = 5
|
tmpAC6D.tmp_NsInstaller.exe | [AVX_CRT_Fix][\\?\C:\Users\admin\AppData\Roaming\NutstoreClient\install\decoder.dll] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIE33D.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Users\admin\AppData\Local\Temp\MSIE3CB.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE6EC.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE76A.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE78A.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE7BA.tmp] CPU: __isa_available = 5
|
MsiExec.exe | [AVX_CRT_Fix][C:\Windows\Installer\MSIE7DA.tmp] CPU: __isa_available = 5
|