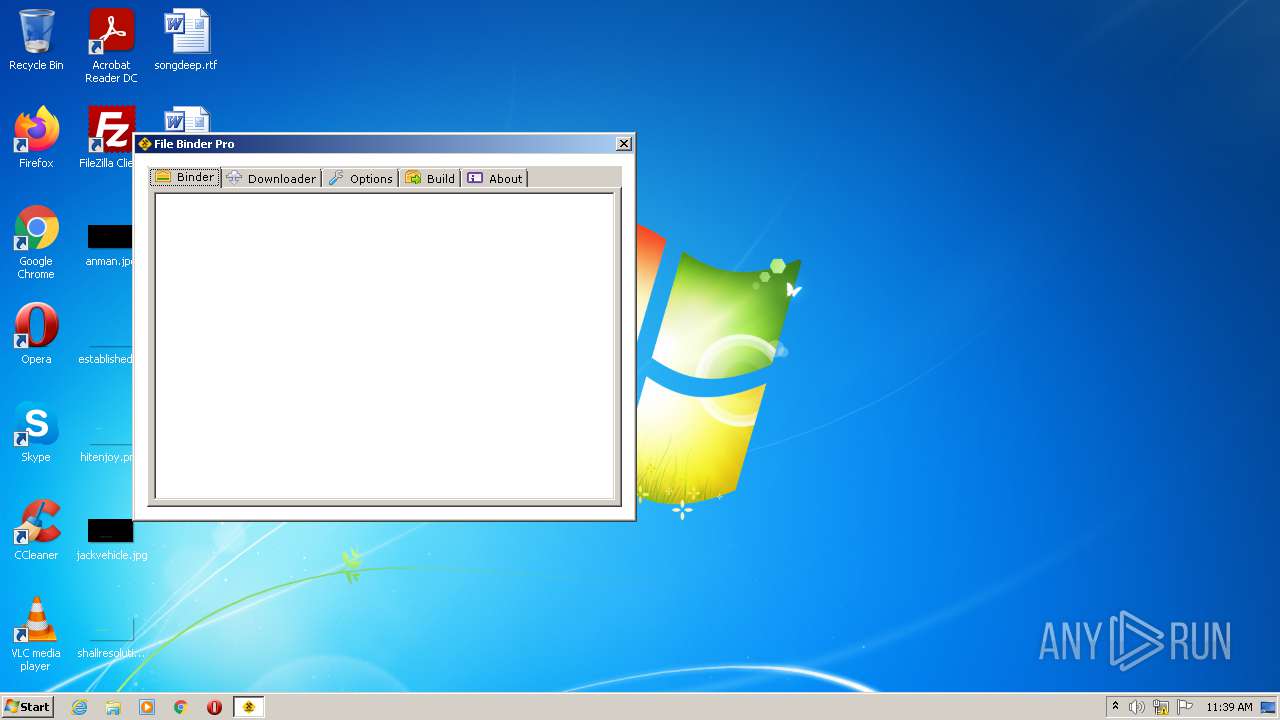
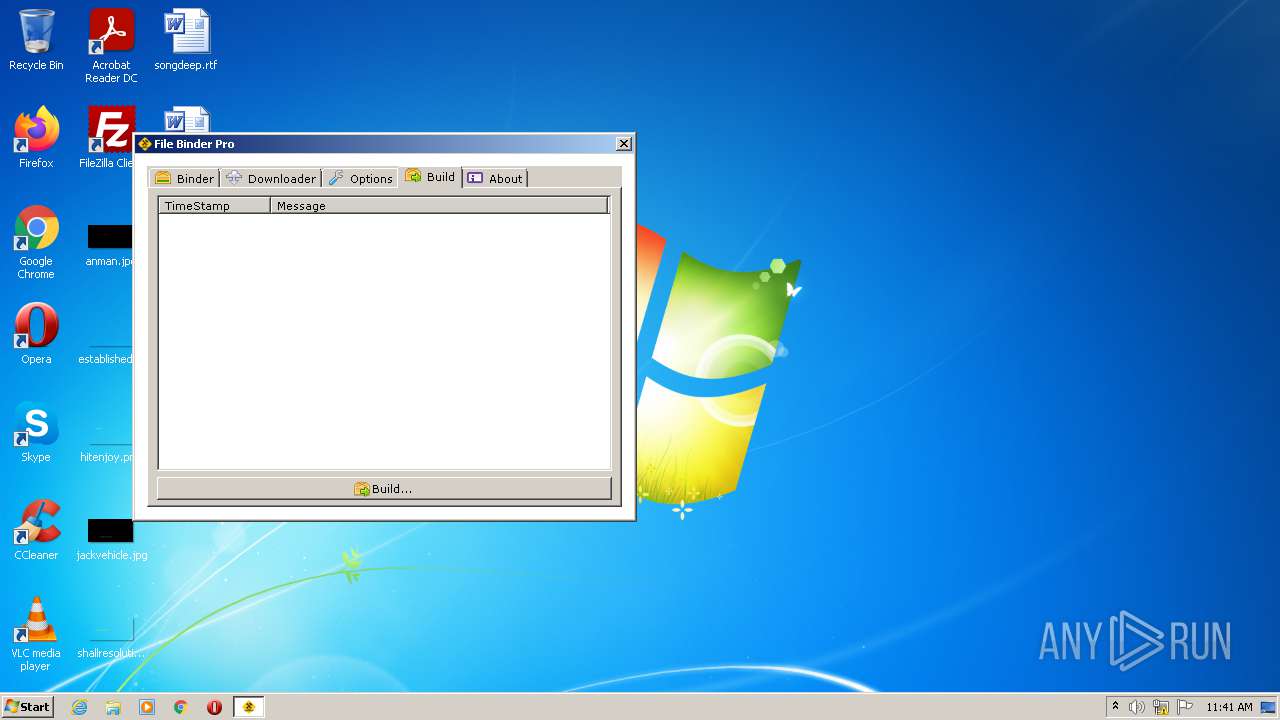
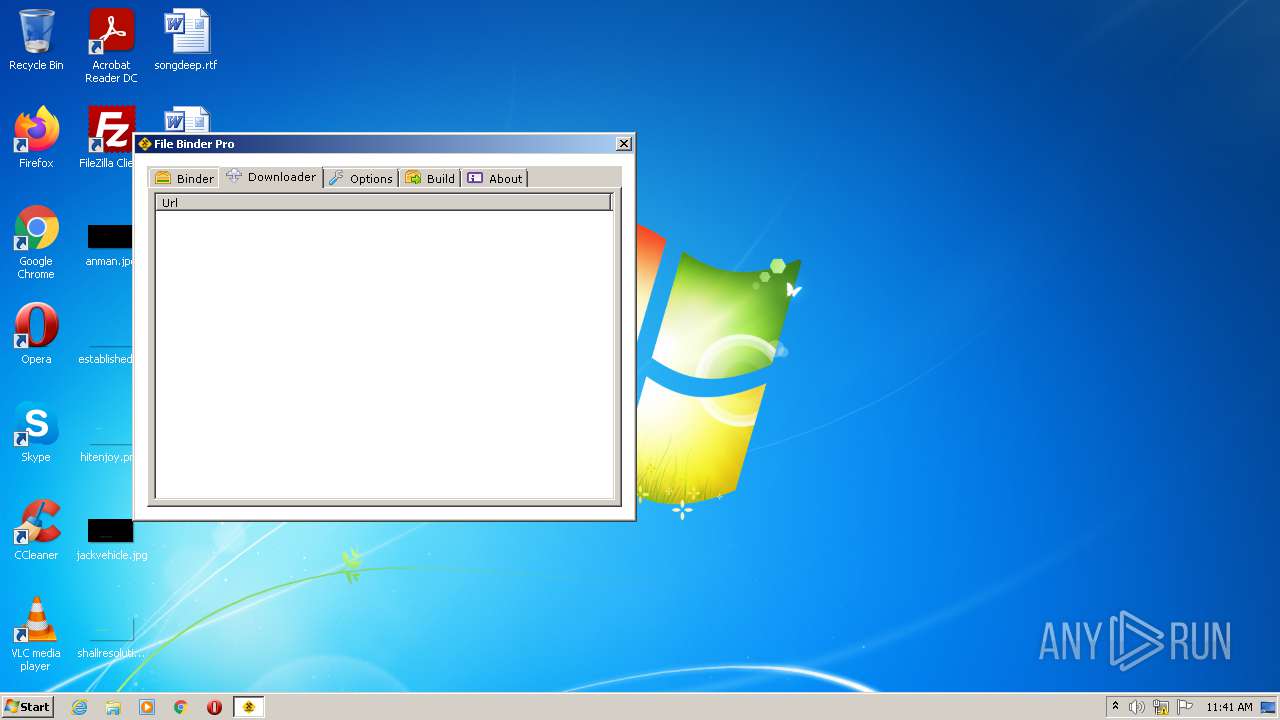
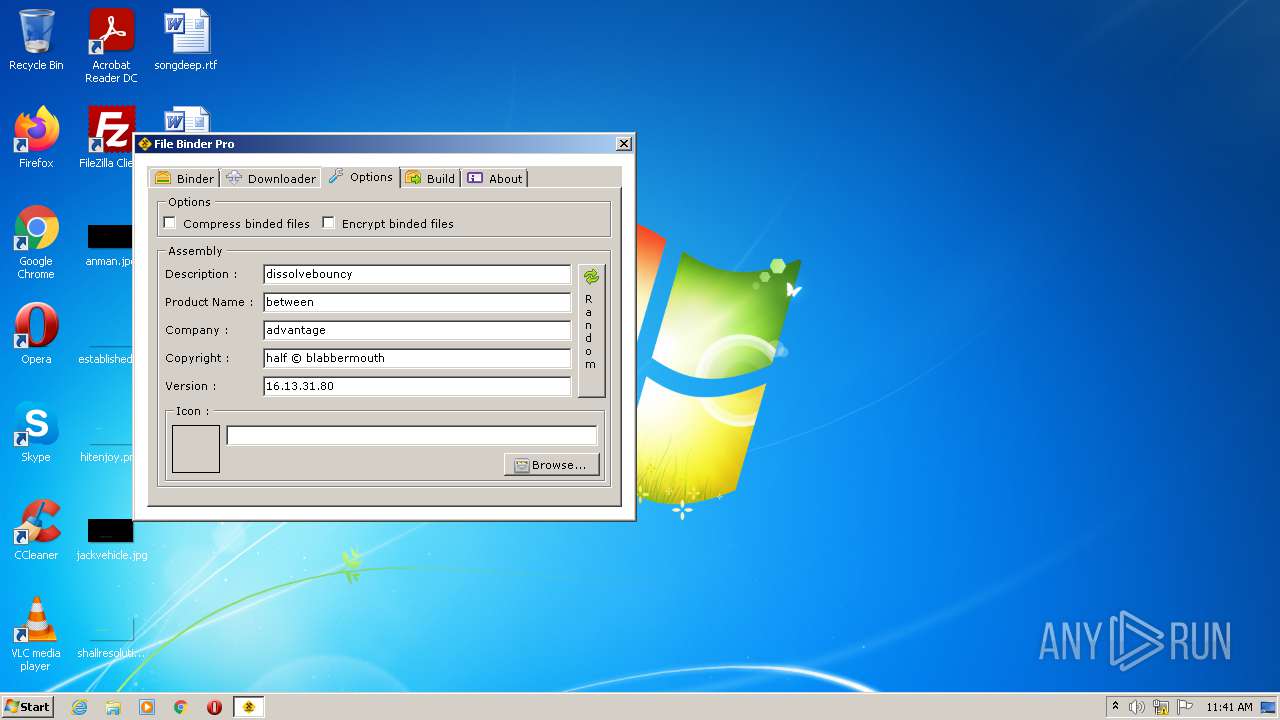
| File name: | File Binder Pro.exe |
| Full analysis: | https://app.any.run/tasks/2332fc55-6568-472c-a7a7-f8542ab7cb28 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2021, 10:39:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 467F775F26B2AE4D07BDF6E3A50E736A |
| SHA1: | 21FAA2087BA648BE91D96241A765C58DDDBB7D28 |
| SHA256: | 49505654D4204619F7672CFD2739B1712ADCA7D9D9EE55FEC94C39097C44A541 |
| SSDEEP: | 6144:CZlwTpbpF/Bhke/QyBhke/Q/Bhke/Qb6yeBnx/UkeL0:YW9bpFXPFPSPNBneP |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- File Binder Pro.exe (PID: 3984)
Checks supported languages
- File Binder Pro.exe (PID: 3984)
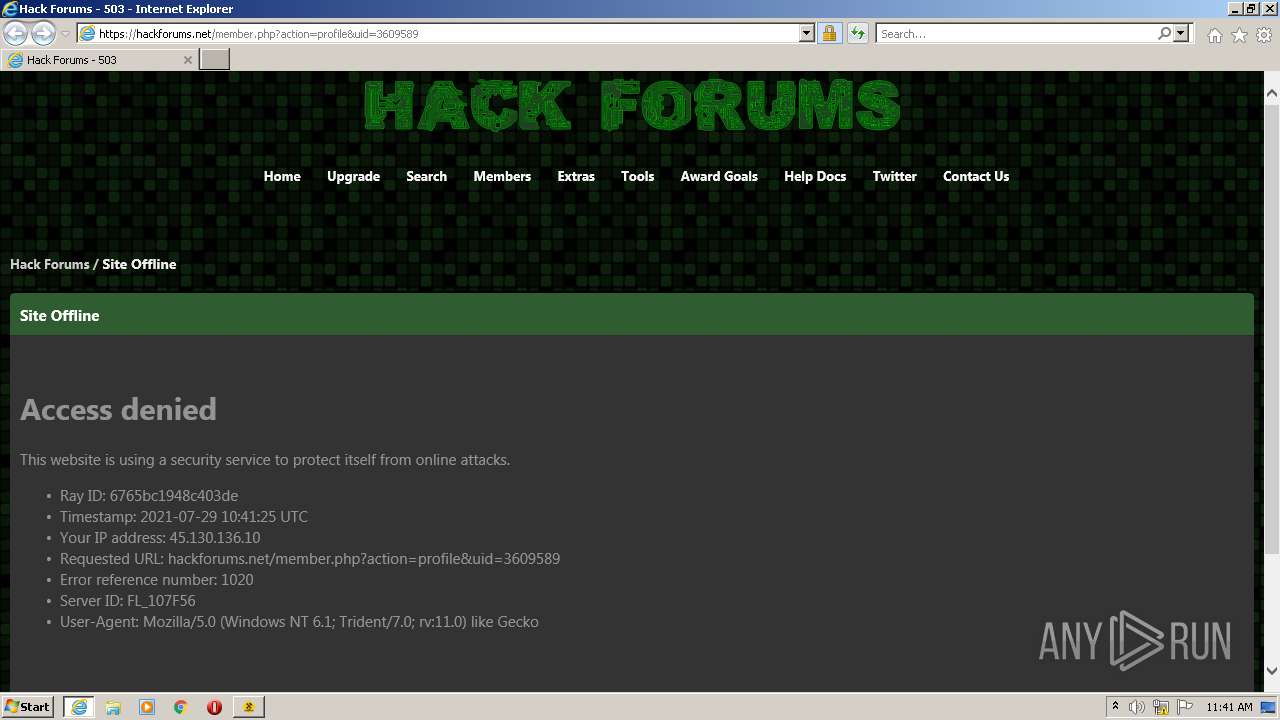
Starts Internet Explorer
- File Binder Pro.exe (PID: 3984)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2104)
INFO
Checks supported languages
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 2104)
Reads the computer name
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 2104)
Changes internet zones settings
- iexplore.exe (PID: 3748)
Application launched itself
- iexplore.exe (PID: 3748)
Checks Windows Trust Settings
- iexplore.exe (PID: 2104)
- iexplore.exe (PID: 3748)
Reads the date of Windows installation
- iexplore.exe (PID: 3748)
Reads settings of System Certificates
- iexplore.exe (PID: 3748)
- iexplore.exe (PID: 2104)
Reads internet explorer settings
- iexplore.exe (PID: 2104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
| ProductName: | File Binder Pro |
| OriginalFileName: | File Binder Pro.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © Rohan Patra 2020 |
| InternalName: | File Binder Pro.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | File Binder Pro |
| CompanyName: | Rohan Patra Inc. |
| Comments: | File Binder |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x119f82 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 315904 |
| CodeSize: | 1146880 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2020:03:23 00:11:53+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Mar-2020 23:11:53 |
| Debug artifacts: |
|
| Comments: | File Binder |
| CompanyName: | Rohan Patra Inc. |
| FileDescription: | File Binder Pro |
| FileVersion: | 1.0.0.0 |
| InternalName: | File Binder Pro.exe |
| LegalCopyright: | Copyright © Rohan Patra 2020 |
| LegalTrademarks: | - |
| OriginalFilename: | File Binder Pro.exe |
| ProductName: | File Binder Pro |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Mar-2020 23:11:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00117F88 | 0x00118000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 3.82071 |
.rsrc | 0x0011A000 | 0x0004CF58 | 0x0004D000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.01169 |
.reloc | 0x00168000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.96863 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.56106 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.12593 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.87885 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 2.57525 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.38142 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.16669 | 152104 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 7.97283 | 20794 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 3.07075 | 132 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2104 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3748 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3748 | "C:\Program Files\Internet Explorer\iexplore.exe" https://hackforums.net/member.php?action=profile&uid=3609589 | C:\Program Files\Internet Explorer\iexplore.exe | File Binder Pro.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3984 | "C:\Users\admin\AppData\Local\Temp\File Binder Pro.exe" | C:\Users\admin\AppData\Local\Temp\File Binder Pro.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Rohan Patra Inc. Integrity Level: MEDIUM Description: File Binder Pro Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
14 372
Read events
14 281
Write events
90
Delete events
1
Modification events
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30901350 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30901350 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3748) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
10
Text files
5
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2104 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3F1640BBEFF5A8BFA728433E1A528A27 | SHA256:6547E0044D5ACCE6A51B696298D74F247C9EB6DD210FFF881EB45642F80AC509 | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6E8EC962BA819BE3.TMP | gmc | |
MD5:20804ACE0377B963E5D70B17F26FCF85 | SHA256:93B799A12C494F174AEF2EE4A58F7A6BB58A186599A5A71054AEFD7F1DCD6AB8 | |||
| 2104 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:2B9057EA33DADB622ED43599D57BC266 | SHA256:1390AFB2E107EA17DA6EA337514A23F7F7EA0DC4595280B05F32C53482B4C428 | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB710268FA45DBB7D.TMP | gmc | |
MD5:1D3A94A94E2FFB370EE735F5F1B014DB | SHA256:0EFBFF82EABC65303BC99DBDF7C5F508EE3146592D5E5D4F4542BE21EA6CB49C | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:B49C46389448273AC2C516560D6D5874 | SHA256:C6A0003E37B8A3E597970F906B08AD5A315715927ECE8103DB02A5838CE9CF0B | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:54D4D2C127B18CD2645047BD0C39C6FA | SHA256:8499626DB150FFF07A2C65765DB297D682E4B6F2B623FE1407FC5C3F91724DC1 | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{84988548-F059-11EB-B7EE-12A9866C77DE}.dat | binary | |
MD5:3B7BE4C8126550D39DB46F3A2E9C7AC5 | SHA256:EFBABEAA44DD0053A82C7F3579F18CD367D0B903C3D5C59836F0B1C9F8191BD0 | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:96344AAEBA31219DF3D8D2D7DC4BC76C | SHA256:A25D1F5A34AE0E74C6C984412E7DF84FFEE51C3053D89B7D13B74F768EE4D8FC | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:F3AFB2199A1FFE71D930569027F4D5F9 | SHA256:49C81FC9765E0A0C52502C8EB5D704820E155785CBF4E163F83103F026BFF869 | |||
| 3748 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF6CFA445837637CE7.TMP | gmc | |
MD5:3D7C1074C67CF7EAD91926CC623B3F79 | SHA256:B148B0ED85F5FAFCC0B45C730C10BA8A7FF697F4C9396D7A3F5CA8971CE6C7DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
11
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | iexplore.exe | GET | 200 | 8.248.117.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b769f77acfc87c05 | US | compressed | 4.70 Kb | whitelisted |
2104 | iexplore.exe | GET | 200 | 8.248.117.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?8601adaada8d8c7d | US | compressed | 4.70 Kb | whitelisted |
2104 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3748 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | iexplore.exe | 104.23.132.78:443 | hackforums.net | Cloudflare Inc | US | unknown |
2104 | iexplore.exe | 8.248.117.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2104 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3748 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 72.21.81.200:443 | r20swj13mr.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3748 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hackforums.net |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |