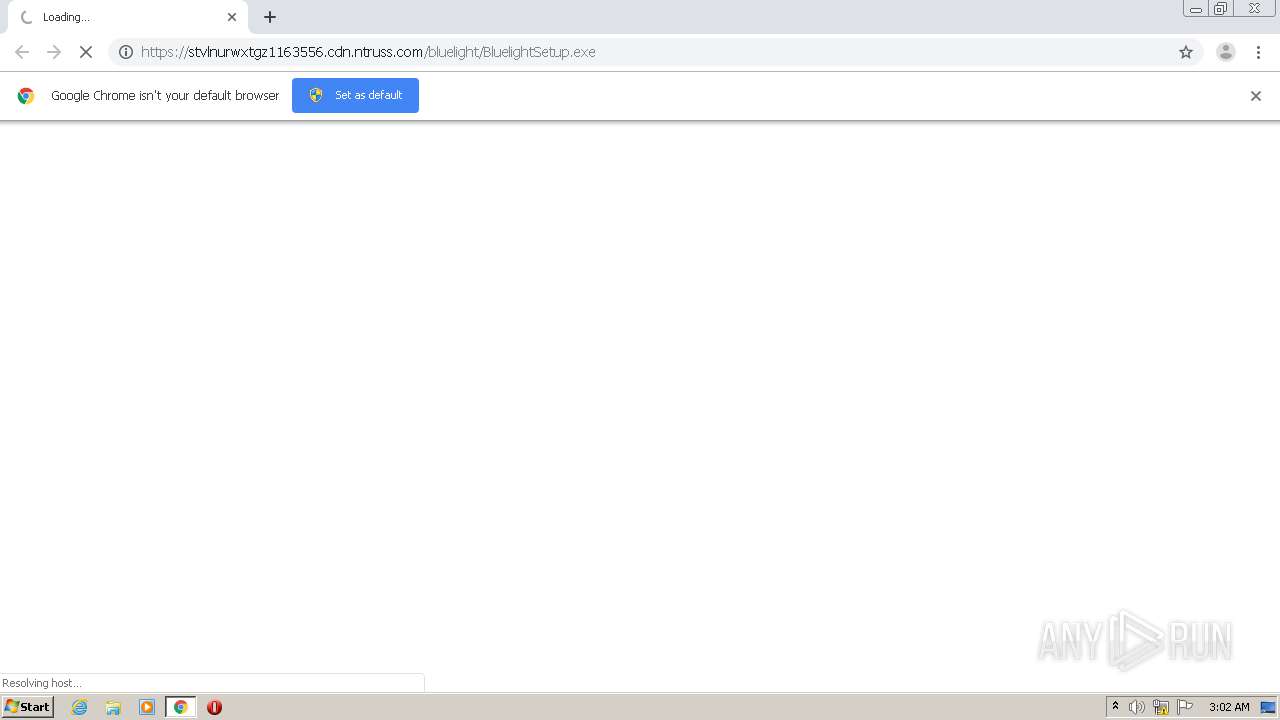
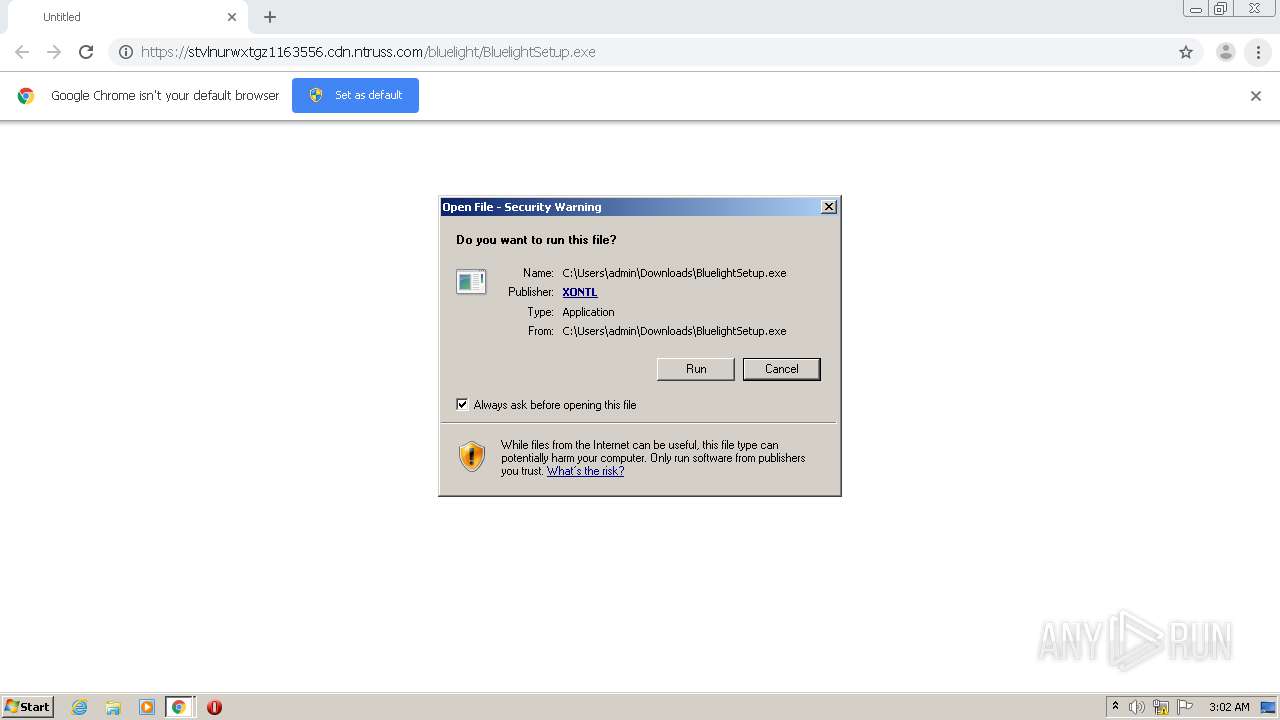
| URL: | https://stvlnurwxtgz1163556.cdn.ntruss.com/bluelight/BluelightSetup.exe |
| Full analysis: | https://app.any.run/tasks/2b69b44b-525a-4e75-a76d-38a6c0d3631c |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 03:02:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 53FE18EDA7C7EC5B37F14D264B0C3415 |
| SHA1: | 030AADFB052AA5AE2B8F7FF566D9B475A1FAFAA2 |
| SHA256: | 4950329132483F3FB7F3F69FD87F582ECCA8981B3E1AF2229D34D0ADF0E9EEFA |
| SSDEEP: | 3:N8cu8C39Ll6Z3hMORiJDNRnRAkA:2cud39Ll77vA |
MALICIOUS
Application was dropped or rewritten from another process
- nsA2F2.tmp (PID: 1972)
- nsC761.tmp (PID: 3288)
- BluelightSetup.exe (PID: 3492)
- nsC7CF.tmp (PID: 2984)
- BluelightSetup.exe (PID: 2128)
- nsCDEB.tmp (PID: 2620)
- nsD176.tmp (PID: 2548)
- chtaskmanager.exe (PID: 3592)
- Bluelight.exe (PID: 1964)
- Bluelight.exe (PID: 3444)
Loads dropped or rewritten executable
- BluelightSetup.exe (PID: 2128)
- BluelightSetup.exe (PID: 3492)
- Bluelight.exe (PID: 1964)
Drops executable file immediately after starts
- BluelightSetup.exe (PID: 3492)
Loads the Task Scheduler COM API
- chtaskmanager.exe (PID: 3592)
Changes settings of System certificates
- Bluelight.exe (PID: 1964)
SUSPICIOUS
Starts application with an unusual extension
- BluelightSetup.exe (PID: 2128)
- BluelightSetup.exe (PID: 3492)
Executable content was dropped or overwritten
- chrome.exe (PID: 2564)
- BluelightSetup.exe (PID: 2128)
- BluelightSetup.exe (PID: 3492)
Drops a file that was compiled in debug mode
- BluelightSetup.exe (PID: 3492)
Uses TASKKILL.EXE to kill process
- nsC7CF.tmp (PID: 2984)
- nsCDEB.tmp (PID: 2620)
Executes scripts
- nsA2F2.tmp (PID: 1972)
Drops a file with too old compile date
- BluelightSetup.exe (PID: 3492)
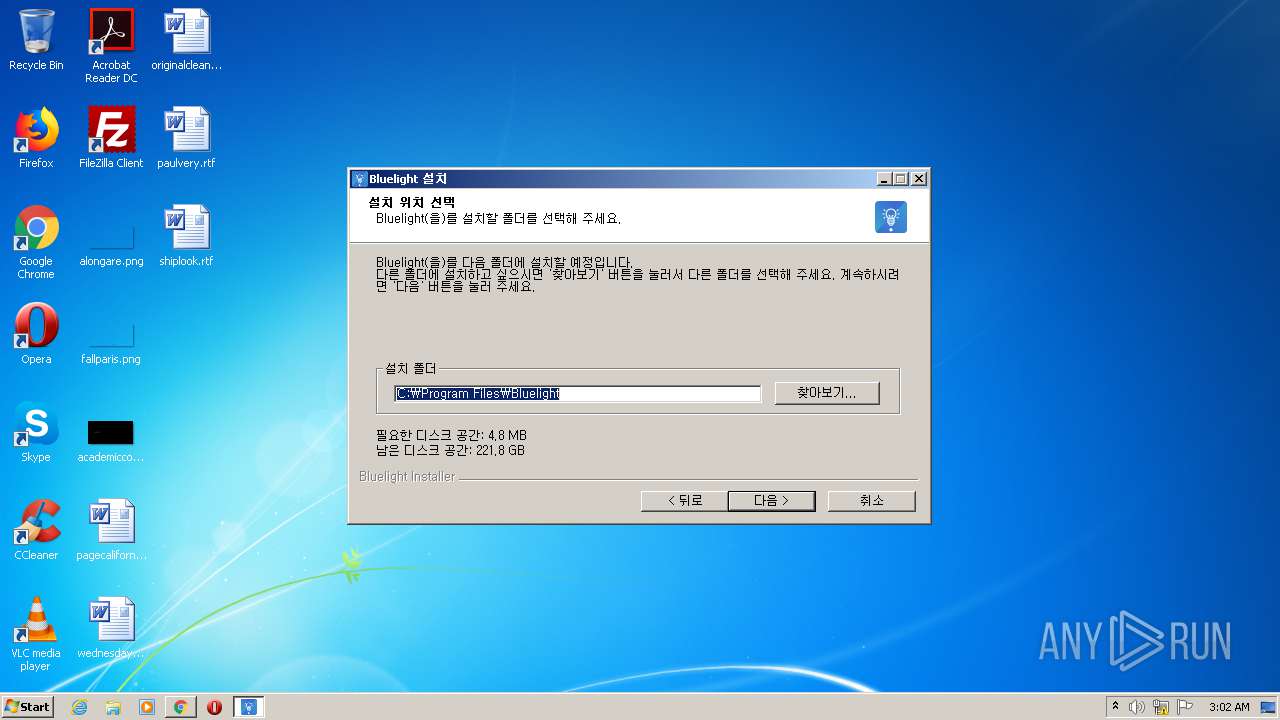
Creates files in the program directory
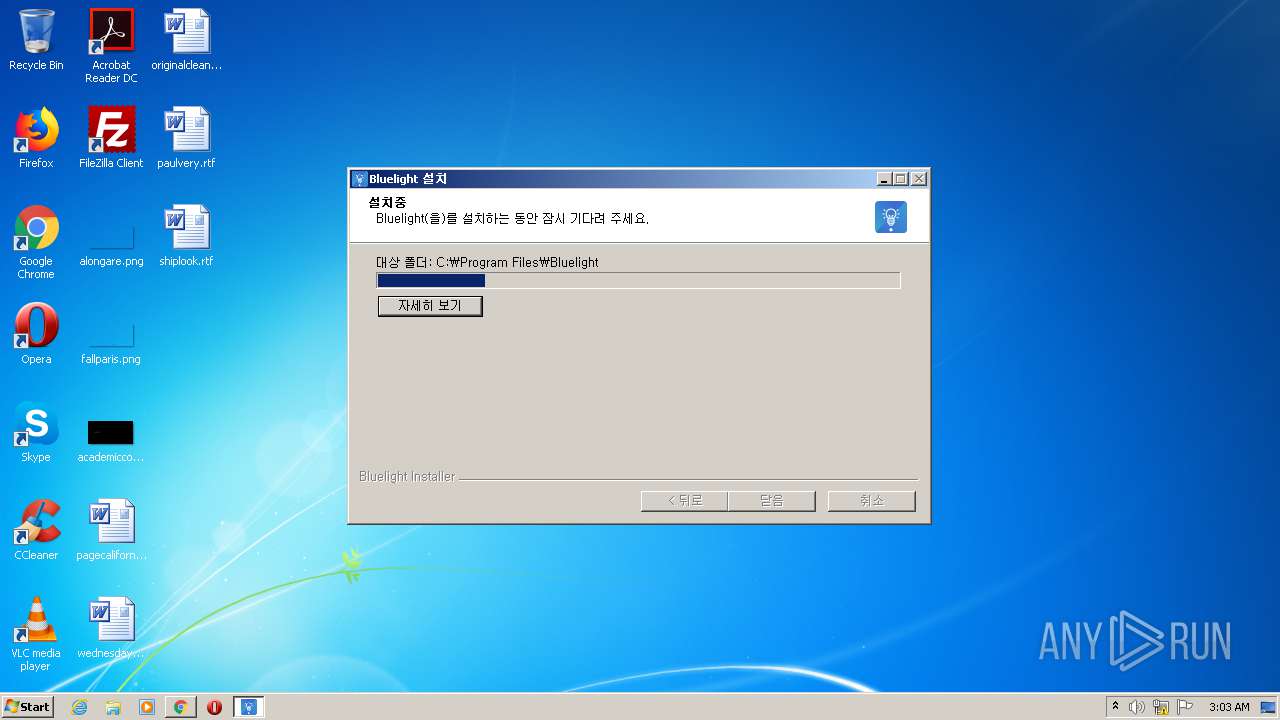
- BluelightSetup.exe (PID: 3492)
Creates a directory in Program Files
- BluelightSetup.exe (PID: 3492)
Creates a software uninstall entry
- BluelightSetup.exe (PID: 3492)
Creates files in the user directory
- BluelightSetup.exe (PID: 3492)
Reads Environment values
- Bluelight.exe (PID: 1964)
Adds / modifies Windows certificates
- Bluelight.exe (PID: 1964)
Reads internet explorer settings
- Bluelight.exe (PID: 1964)
Changes IE settings (feature browser emulation)
- Bluelight.exe (PID: 1964)
INFO
Reads the hosts file
- chrome.exe (PID: 380)
- chrome.exe (PID: 2564)
Application launched itself
- chrome.exe (PID: 2564)
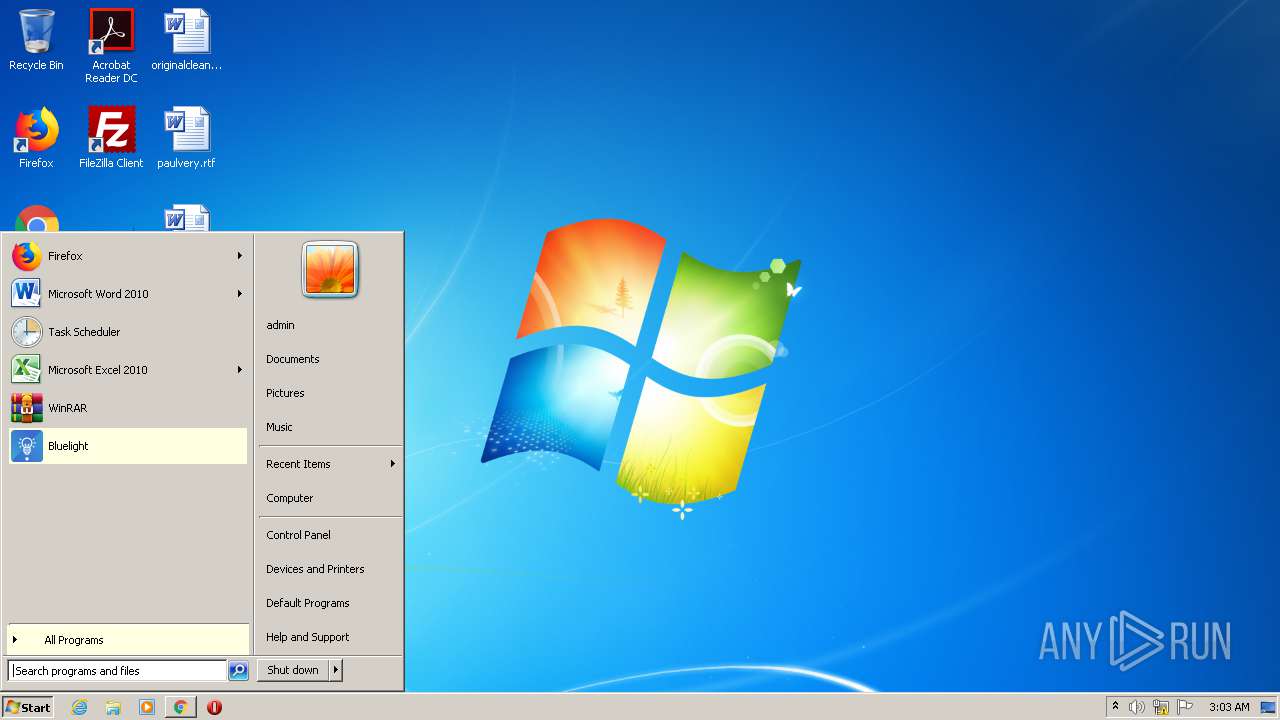
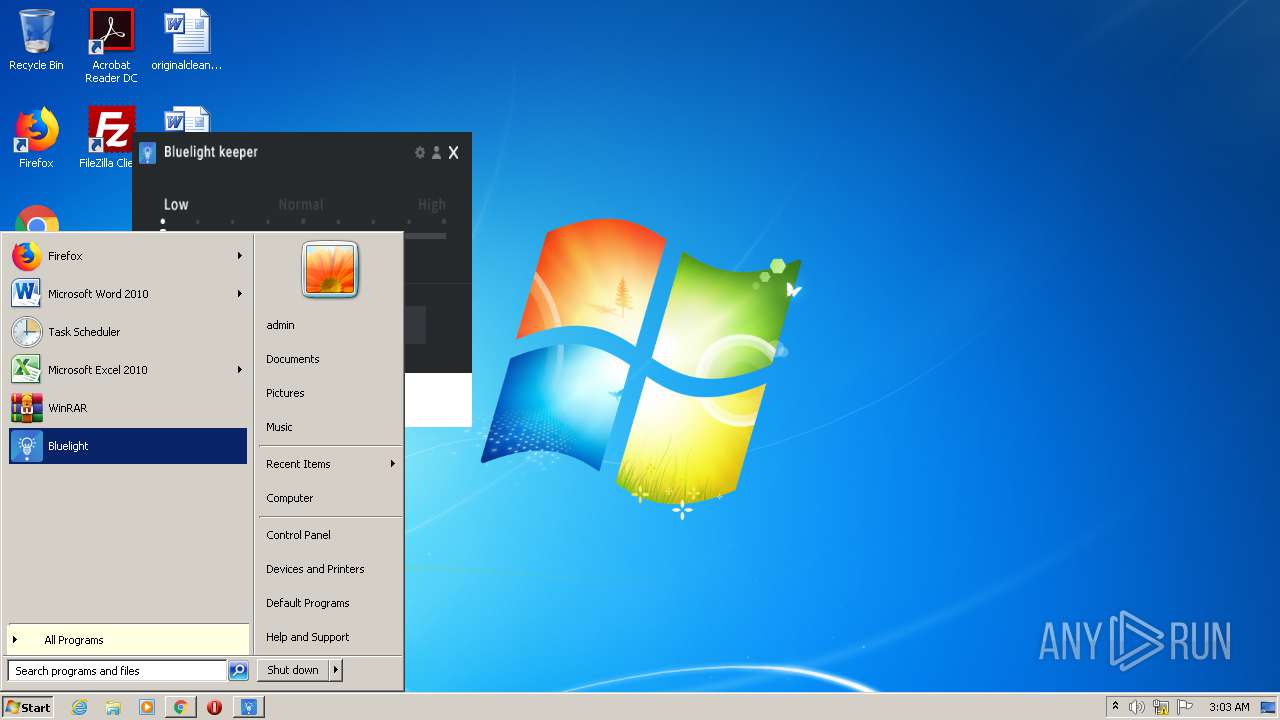
Manual execution by user
- Bluelight.exe (PID: 3444)
Reads settings of System Certificates
- Bluelight.exe (PID: 1964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
67
Monitored processes
23
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,4302535587188076086,7979628363982899736,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17862551872500899293 --mojo-platform-channel-handle=1548 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,4302535587188076086,7979628363982899736,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12246351972103105344 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 800 | taskkill /F /T /im Bluelight.exe | C:\Windows\system32\taskkill.exe | — | nsCDEB.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,4302535587188076086,7979628363982899736,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=18016528212519549122 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2644 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
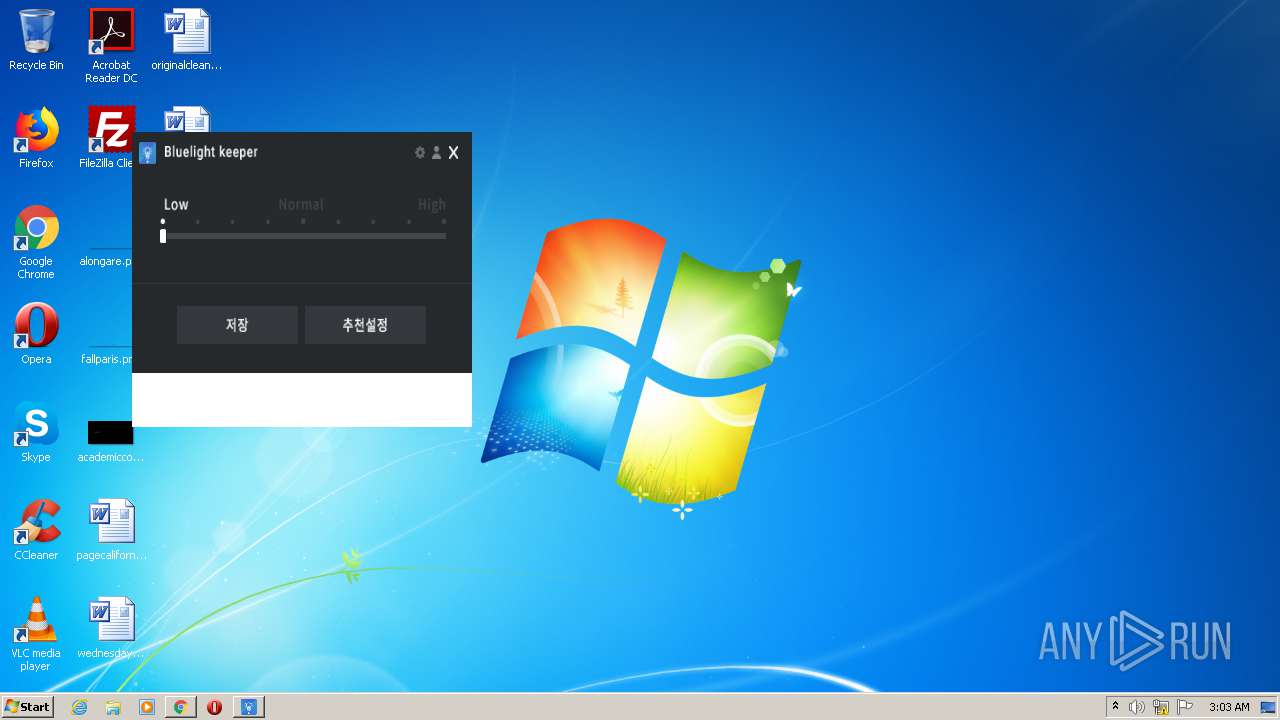
| 1964 | "C:\Program Files\Bluelight\Bluelight.exe" | C:\Program Files\Bluelight\Bluelight.exe | BluelightSetup.exe | ||||||||||||
User: admin Company: XONTL Integrity Level: HIGH Description: Blulight Exit code: 0 Version: 1.1.8.0 Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Temp\nstA2E0.tmp\nsA2F2.tmp" C:\Windows\system32\CScript.exe C:\Users\admin\AppData\Local\Temp\nsjA2F1.tmp.vbs "C:\Users\admin\Downloads\BluelightSetup.exe" | C:\Users\admin\AppData\Local\Temp\nstA2E0.tmp\nsA2F2.tmp | — | BluelightSetup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\Downloads\BluelightSetup.exe" | C:\Users\admin\Downloads\BluelightSetup.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,4302535587188076086,7979628363982899736,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13716473697354337451 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,4302535587188076086,7979628363982899736,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13270891677018597563 --mojo-platform-channel-handle=4048 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 346
Read events
2 228
Write events
115
Delete events
3
Modification events
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1168) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2564-13251178958316875 |
Value: 259 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
35
Suspicious files
14
Text files
84
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC460CF-A04.pma | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dafd882a-9c67-4ca0-9db7-1a27c2a96c5f.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF1271ae.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF127085.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1270a4.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1272f6.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1964 | Bluelight.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
1964 | Bluelight.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
1964 | Bluelight.exe | GET | 200 | 23.55.163.71:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | US | der | 1.37 Kb | whitelisted |
1964 | Bluelight.exe | GET | 200 | 23.55.163.48:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgTsdjbS%2BP6QBI0%2FZN0l%2B3AxQg%3D%3D | US | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1964 | Bluelight.exe | 183.111.25.18:443 | stvlnurwxtgz1163556.cdn.ntruss.com | Korea Telecom | KR | unknown |
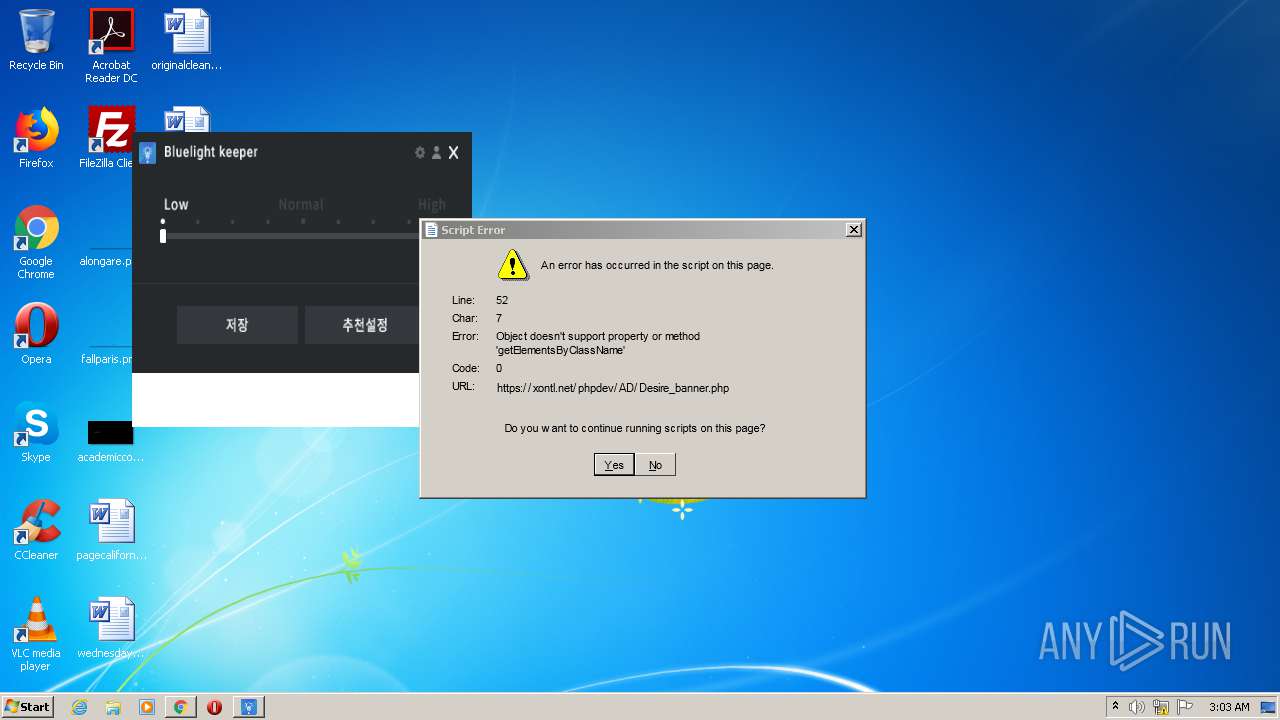
1964 | Bluelight.exe | 101.101.167.113:443 | xontl.net | — | KR | unknown |
380 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1964 | Bluelight.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
— | — | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
1964 | Bluelight.exe | 23.55.163.71:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | suspicious |
380 | chrome.exe | 172.217.12.205:443 | accounts.google.com | Google Inc. | US | suspicious |
380 | chrome.exe | 172.217.12.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
380 | chrome.exe | 101.79.246.131:443 | stvlnurwxtgz1163556.cdn.ntruss.com | purplestones | KR | unknown |
1964 | Bluelight.exe | 23.55.163.48:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stvlnurwxtgz1163556.cdn.ntruss.com |
| unknown |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
xontl.net |
| unknown |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
code.jquery.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |