| File name: | samplePutty (1) - Copy.doc |
| Full analysis: | https://app.any.run/tasks/d2fe847e-382f-4b69-8de6-0e2aba4371f9 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 16:29:22 |
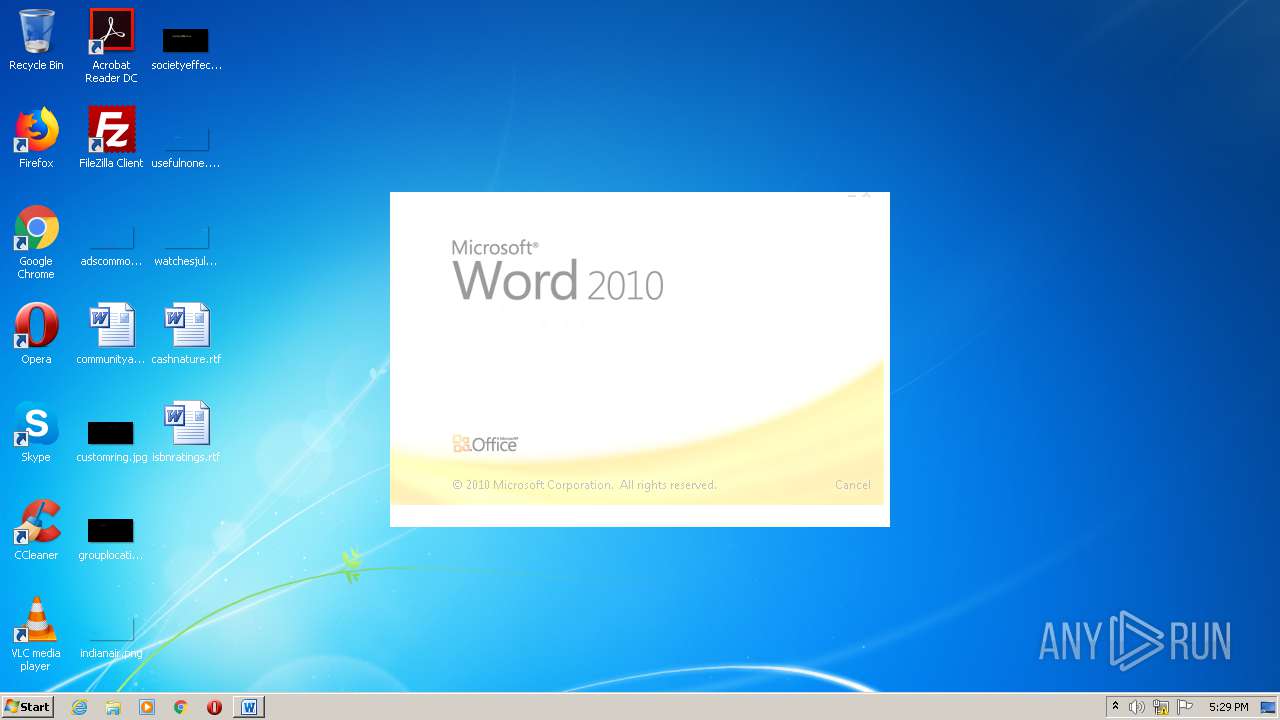
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: Jules Leblerc, Template: Normal.dotm, Last Saved By: Julian Incognito, Revision Number: 16, Name of Creating Application: Microsoft Office Word, Total Editing Time: 30:00, Create Time/Date: Sat Aug 8 16:14:00 2020, Last Saved Time/Date: Sat Aug 8 16:55:00 2020, Number of Pages: 1, Number of Words: 1, Number of Characters: 7, Security: 0 |
| MD5: | 4BB297608996A583D82D6C46817E9B88 |
| SHA1: | 0580B8FDFDF663AF4DCCBA15119FC4916E214778 |
| SHA256: | 494E2CF3AAA100A76E29831E7667643426F029E52873CA19B8F7CBAE318C9EB5 |
| SSDEEP: | 384:ZU1iSX3mSBqEIU/tAmQqzaT3lxbbN37jNgomluHasiD4zxUapIIVpLPZWWMNVdK0:ZuqzqQqz6Nrj160LPZWBn1fC |
MALICIOUS
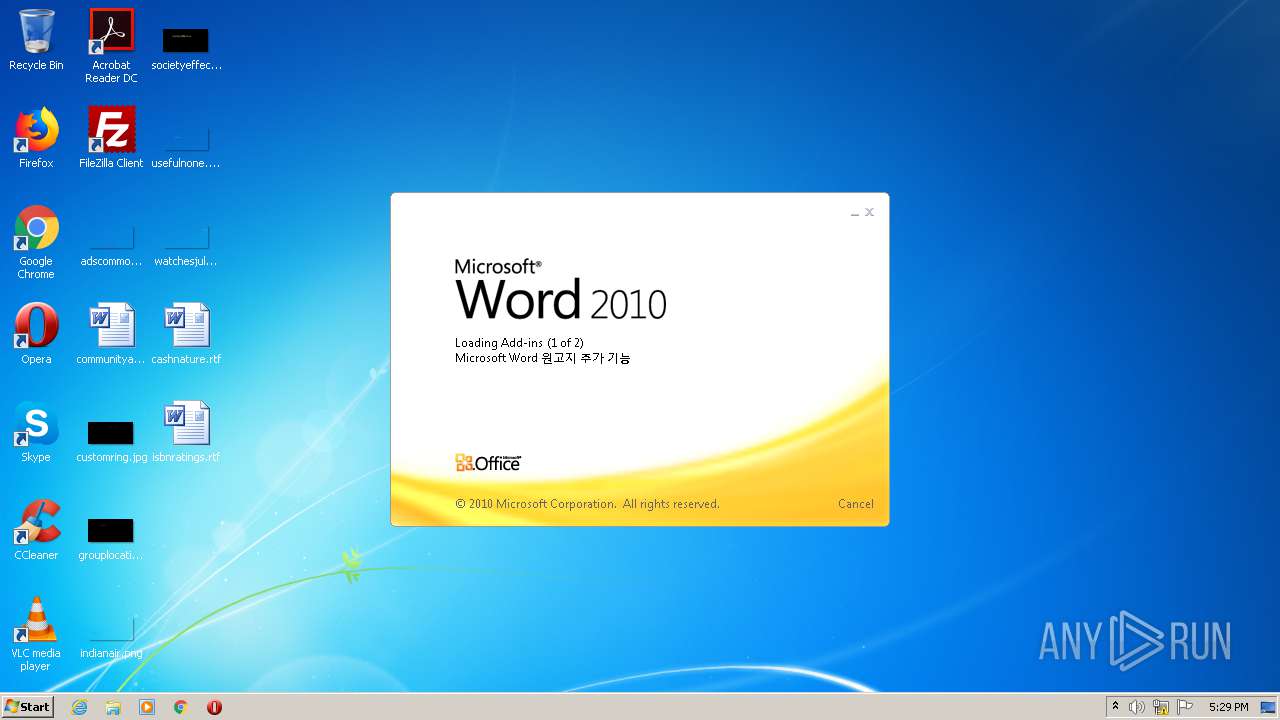
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 296)
SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- WINWORD.EXE (PID: 296)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Document Microsoft Word 97-2003 |
| Title: | - |
| Subject: | - |
| Author: | Jules Leblerc |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Julian Incognito |
| RevisionNumber: | 16 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 30.0 minutes |
| CreateDate: | 2020:08:08 15:14:00 |
| ModifyDate: | 2020:08:08 15:55:00 |
| Pages: | 1 |
| Words: | 1 |
| Characters: | 7 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 7 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
Total processes
43
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
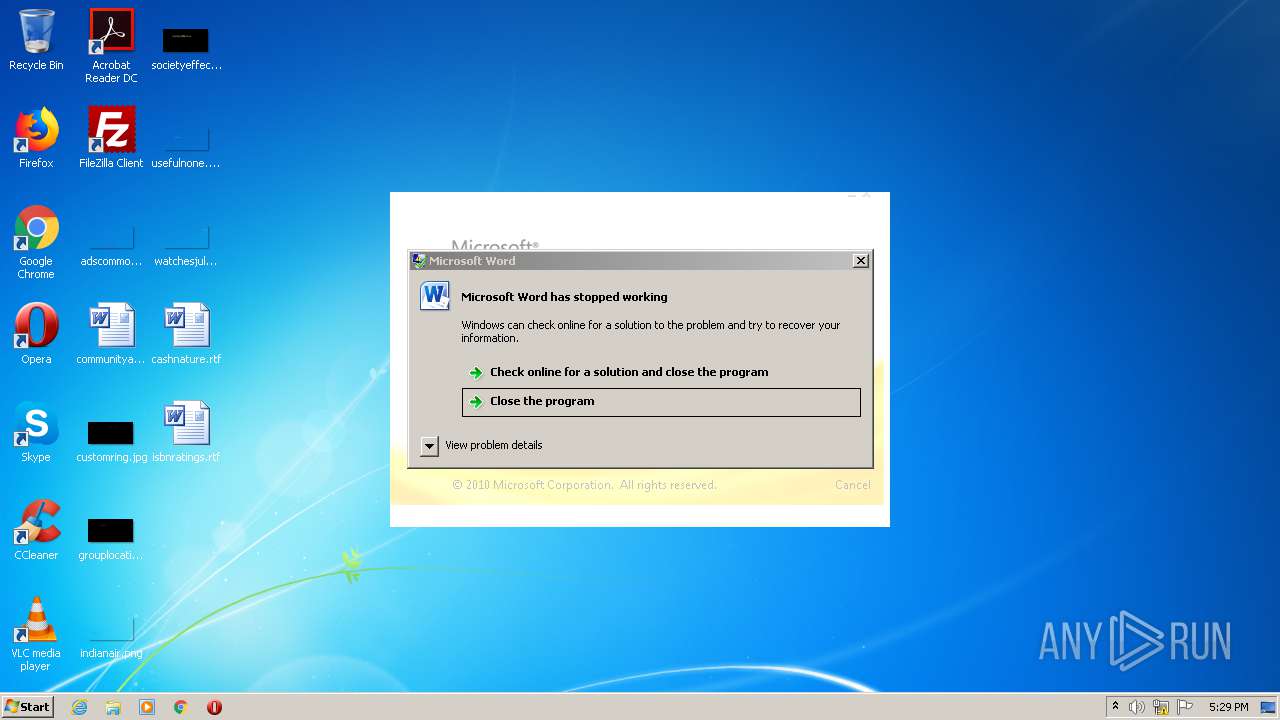
| 296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\samplePutty (1) - Copy.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1780 | C:\Windows\system32\dwwin.exe -x -s 1288 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1288 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
Total events
588
Read events
524
Write events
50
Delete events
14
Modification events
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a78 |
Value: 6137380028010000010000000000000000000000 | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (296) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7BC1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{E282E026-F603-45C7-8482-7052791FA1D9}.tmp | — | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD8F51C1A8656CD97.TMP | — | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$mplePutty (1) - Copy.doc | pgc | |
MD5:— | SHA256:— | |||
| 1780 | dwwin.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_WINWORD.EXE_52b4af3b9f20a1e29894183f62cf08553c9517_06e1adbe\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\1410250.cvr | sqm | |
MD5:— | SHA256:— | |||
| 296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{DC5FB976-EBC2-41C1-B9E9-1F09086307B3}.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report