| URL: | http://aladel.net |
| Full analysis: | https://app.any.run/tasks/3c9ad048-0d6b-4958-855b-5ec97d1a95c4 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2020, 20:50:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5D624B9E26F5B105312EA3008472A35D |
| SHA1: | 7772C998D8641E20702AFA9D481F1ECCCBF3AD4A |
| SHA256: | 4916E0BC5B46495C4C3D5978383F28243EA2A1751A7A19D0B3C709CA645F4681 |
| SSDEEP: | 3:N1KfLJLL0:CFs |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 4052)
- iexplore.exe (PID: 4092)
Reads settings of System Certificates
- iexplore.exe (PID: 4092)
Changes internet zones settings
- iexplore.exe (PID: 4092)
Application launched itself
- iexplore.exe (PID: 4092)
Changes settings of System certificates
- iexplore.exe (PID: 4092)
Reads internet explorer settings
- iexplore.exe (PID: 4052)
Creates files in the user directory
- iexplore.exe (PID: 4052)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4092 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4092 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://aladel.net" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
381
Read events
274
Write events
106
Delete events
1
Modification events
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3922131160 | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30837665 | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4092) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
24
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VSBYT7PN.txt | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\2FSDNA5W.txt | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\qsml[1].htm | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ISGGYHFQ.htm | html | |
MD5:6E762FFCAF485095DE241F467679C9B7 | SHA256:CB0CB01A78697BEA7A9F46602E63030DBBB69A36949B1157CCD8786A643112BA | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\88I3F1Z1.txt | text | |
MD5:17F0937960A616B4C39760047C00DE62 | SHA256:93E83C963570CAC2EFF319ACAFAF962197BBFA4B189B8EC3C52B5CF7768C5A63 | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\qsml[1].xml | xml | |
MD5:ED7FFABD2361581D0A9FD47E64AE6CC8 | SHA256:1C81681552AF540A40CD66A98FE50540A1E96F0A0391987FBC72FA1F4B811827 | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PW2LB7HF.txt | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\7FCGJN07.txt | — | |
MD5:— | SHA256:— | |||
| 4052 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\KOE22OPT.txt | text | |
MD5:3E6EC4763BA18FCEEFEEFC508BC46A41 | SHA256:5054CE6480318DF6529A8702742FA615F9C084293F696C718D641EB22DD6297E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
44
DNS requests
14
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
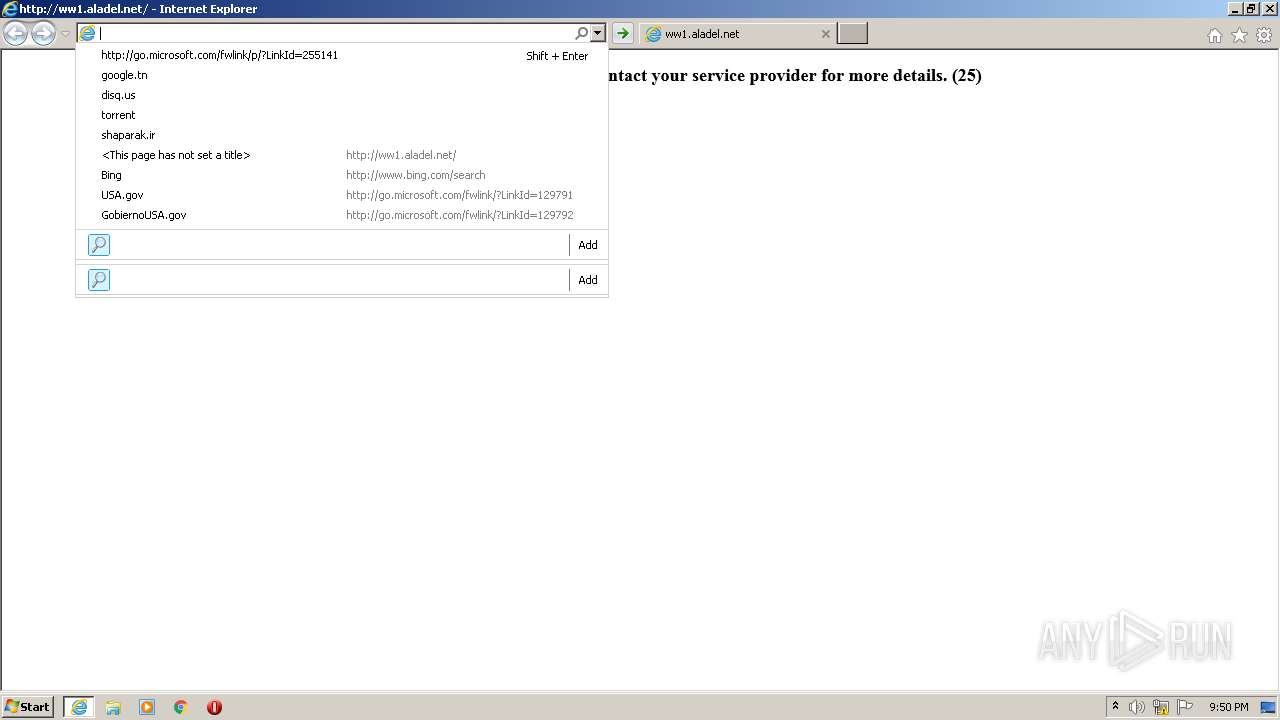
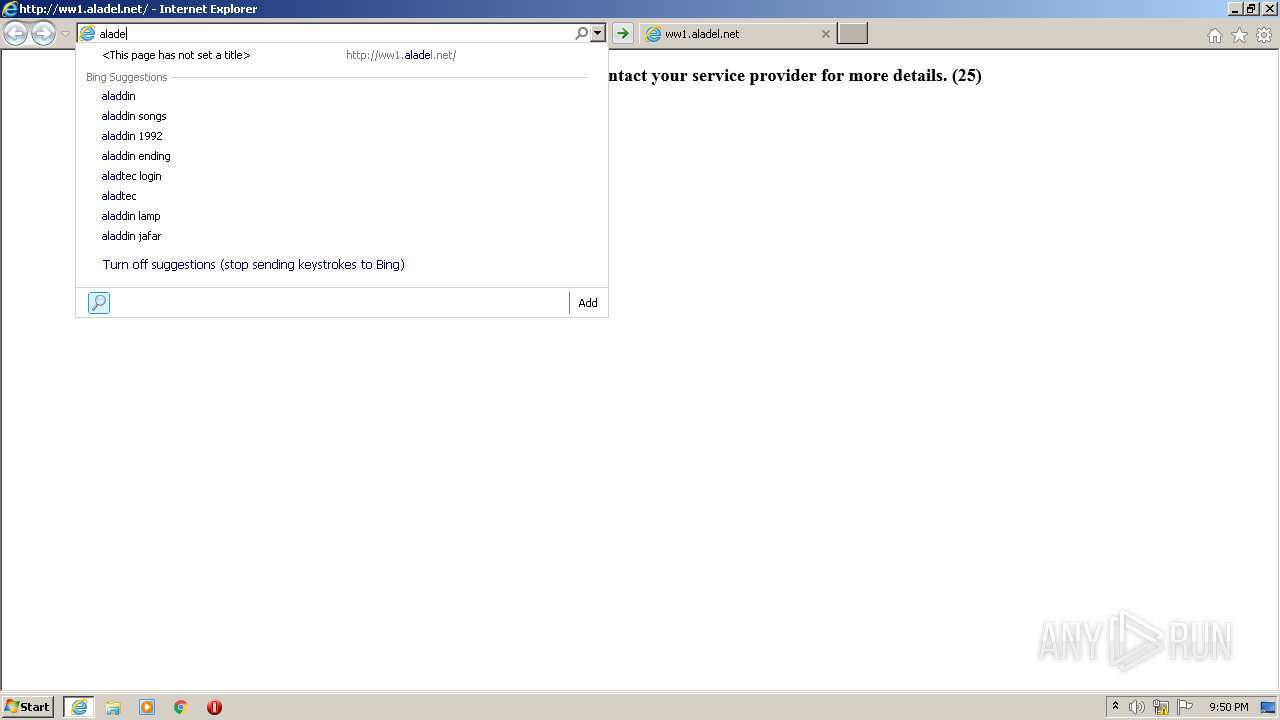
4052 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fww1.aladel.n&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 175 b | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fww1.aladel&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fww1.al&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fww1.alad&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fww1.&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fw&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2F&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=http%3A%2F%2Fww1&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
4052 | iexplore.exe | GET | — | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=htt&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4052 | iexplore.exe | 207.244.67.214:80 | aladel.net | Leaseweb USA, Inc. | US | malicious |
4052 | iexplore.exe | 13.107.5.80:80 | api.bing.com | Microsoft Corporation | US | whitelisted |
4052 | iexplore.exe | 208.91.196.145:80 | ww1.aladel.net | Confluence Networks Inc | VG | malicious |
— | — | 207.244.67.214:80 | aladel.net | Leaseweb USA, Inc. | US | malicious |
4092 | iexplore.exe | 208.91.196.145:80 | ww1.aladel.net | Confluence Networks Inc | VG | malicious |
— | — | 173.192.101.24:80 | infopicked.com | SoftLayer Technologies Inc. | US | suspicious |
4052 | iexplore.exe | 188.225.75.54:80 | cryptomoneyinsiders.work | TimeWeb Ltd. | RU | suspicious |
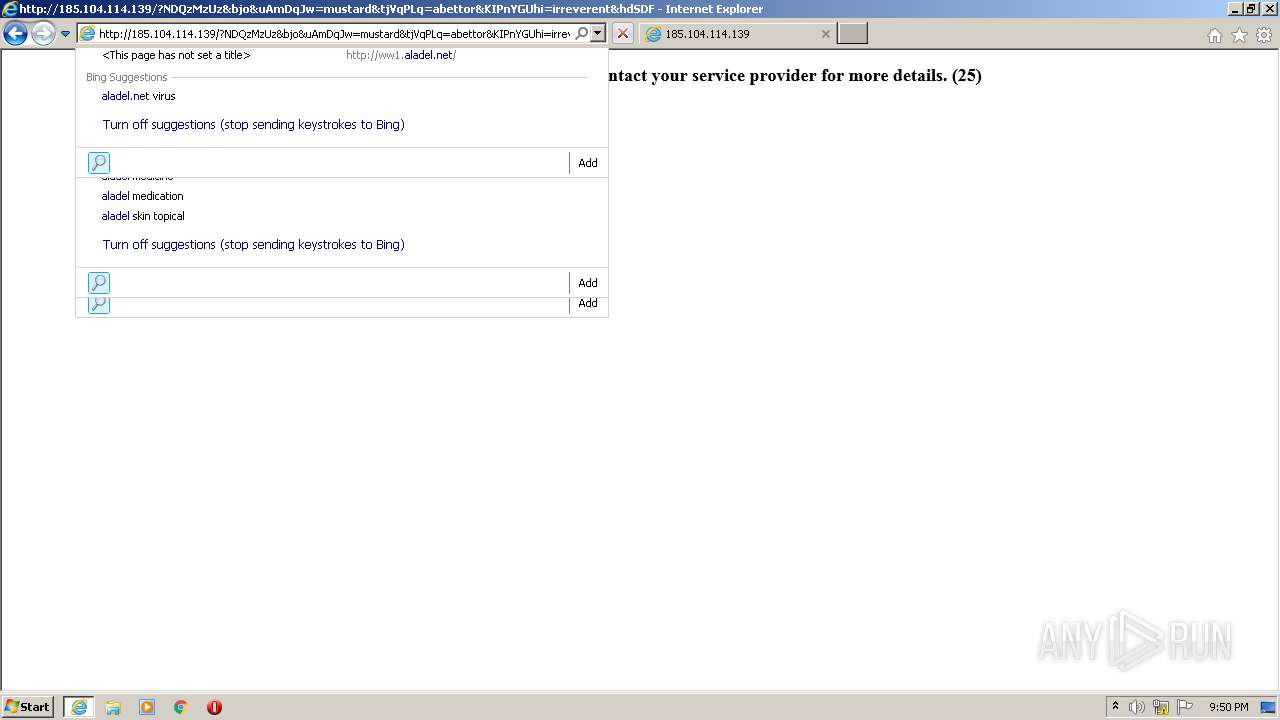
4092 | iexplore.exe | 185.104.114.139:80 | — | Tikhonova Vera Pavlovna PE | RU | malicious |
4052 | iexplore.exe | 185.104.114.139:80 | — | Tikhonova Vera Pavlovna PE | RU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
aladel.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ww1.aladel.net |
| malicious |
infopicked.com |
| whitelisted |
p185689.infopicked.com |
| whitelisted |
cryptomoneyinsiders.work |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .work TLD |
4052 | iexplore.exe | Potentially Bad Traffic | ET INFO HTTP Request to Suspicious *.work Domain |
4052 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
4052 | iexplore.exe | A Network Trojan was detected | MALWARE [PTsecurity] RIG-EK Landing Page |
1 ETPRO signatures available at the full report