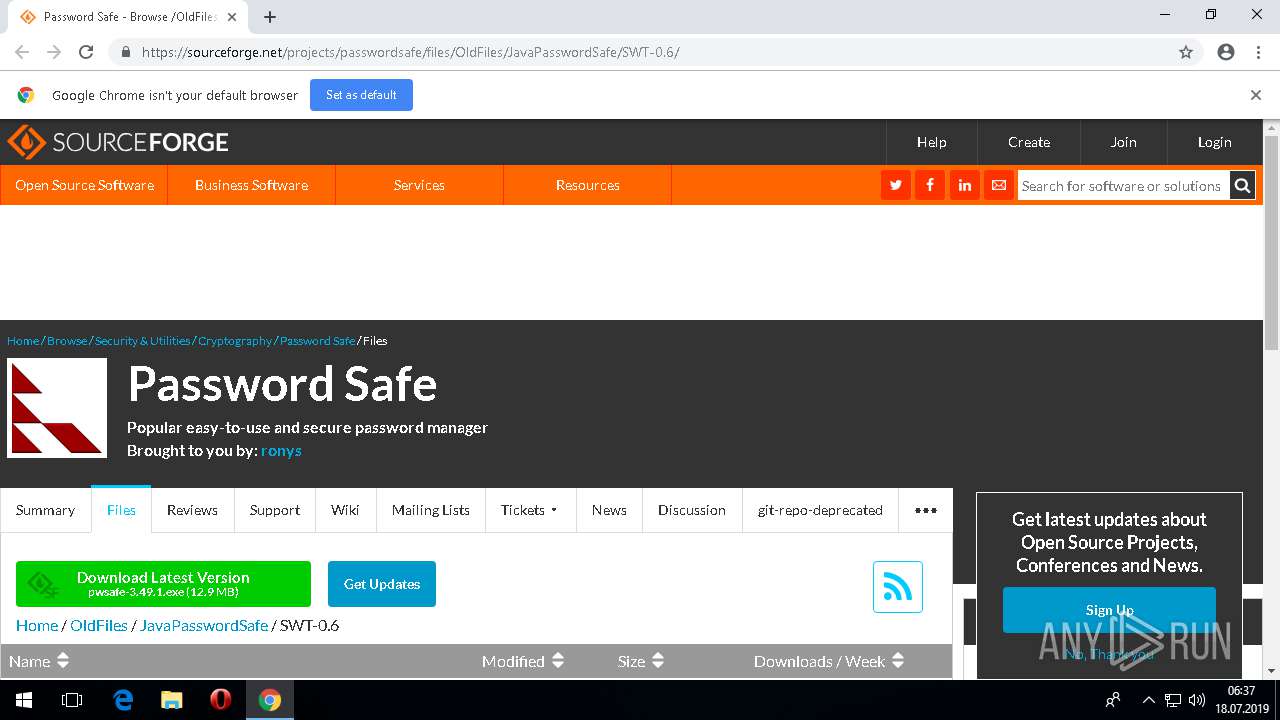
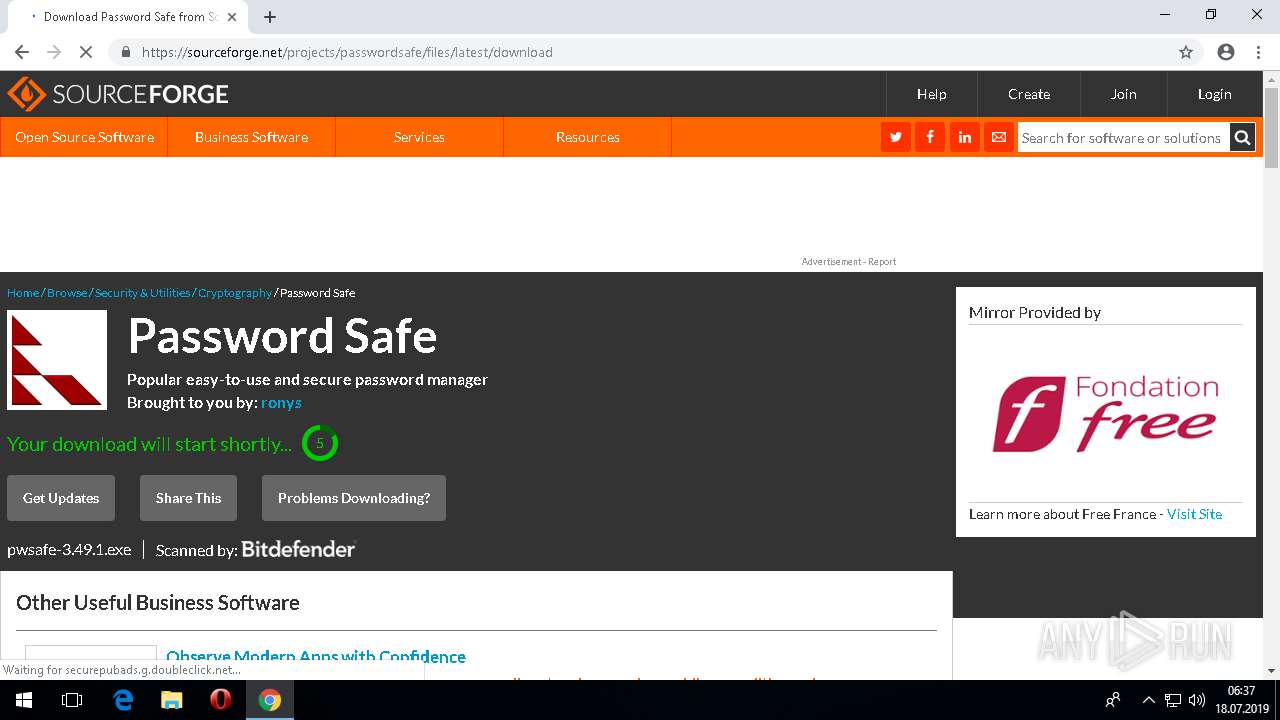
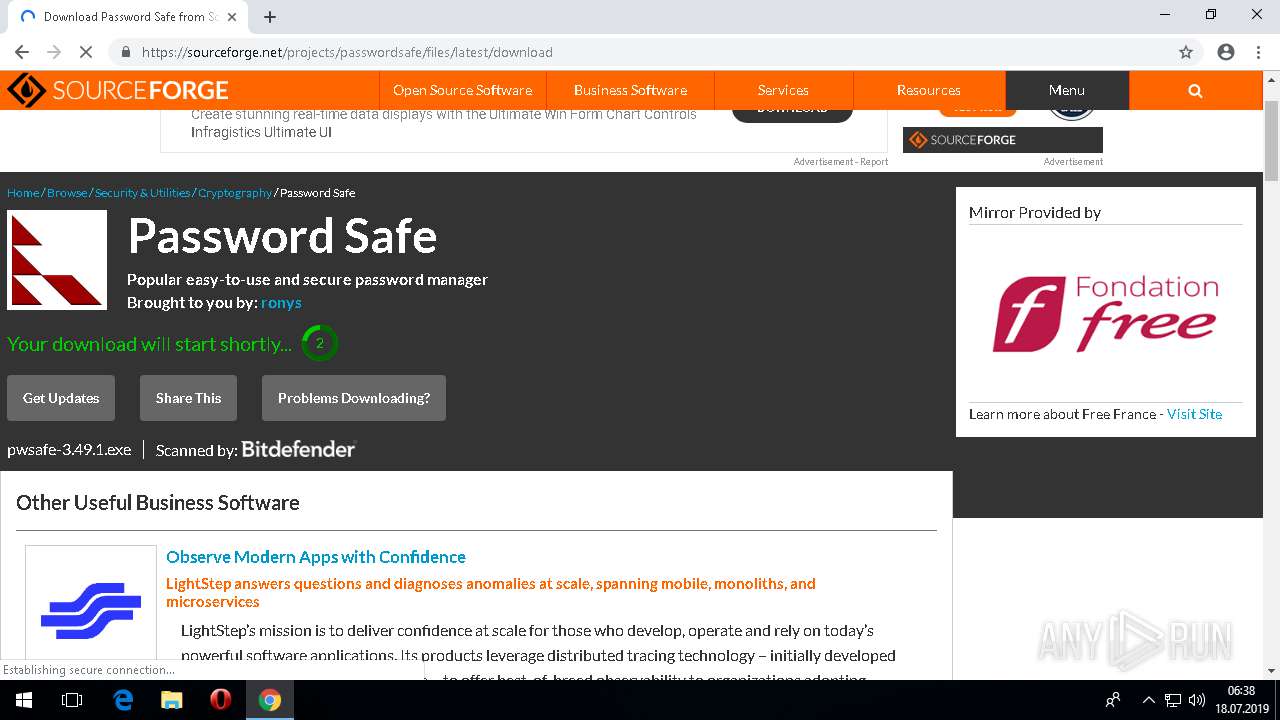
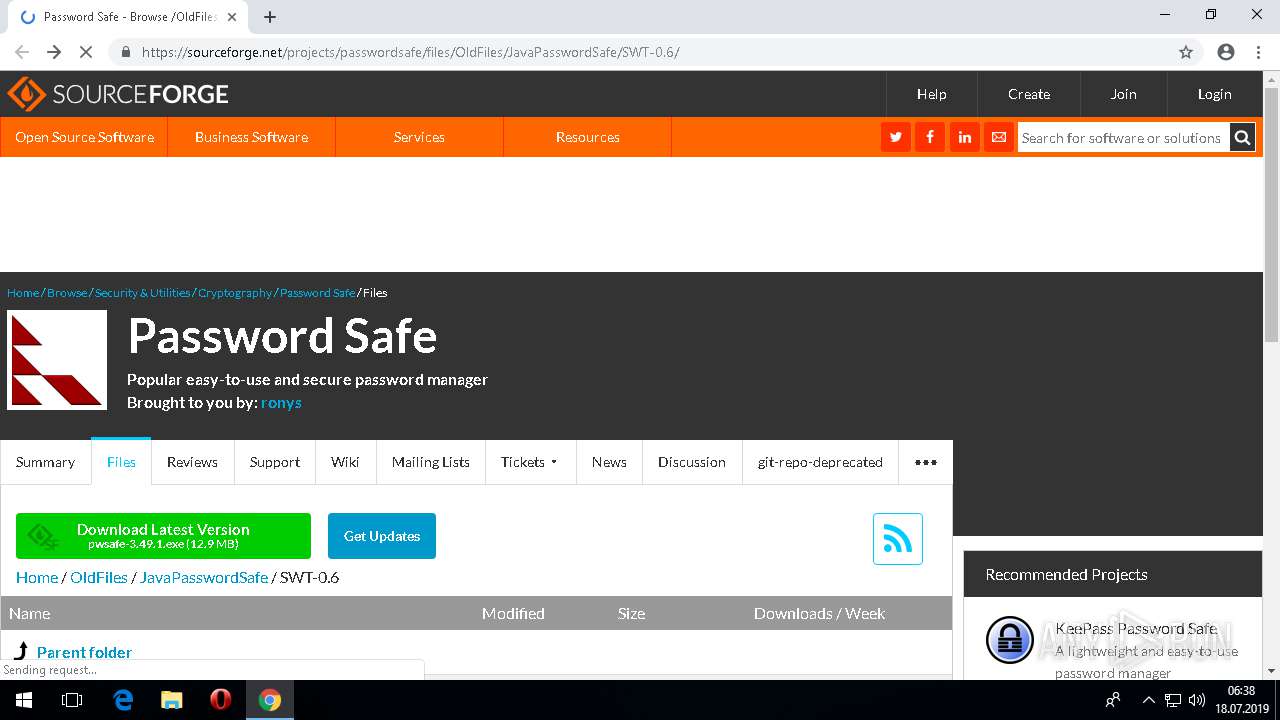
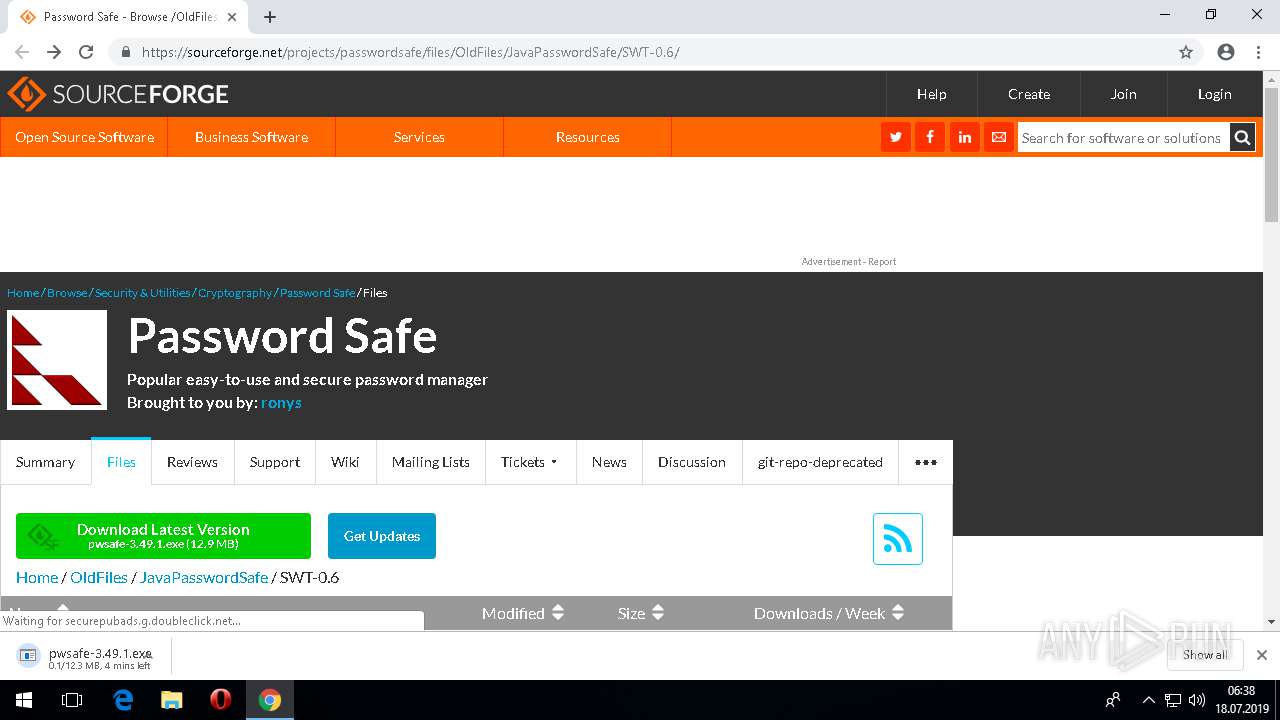
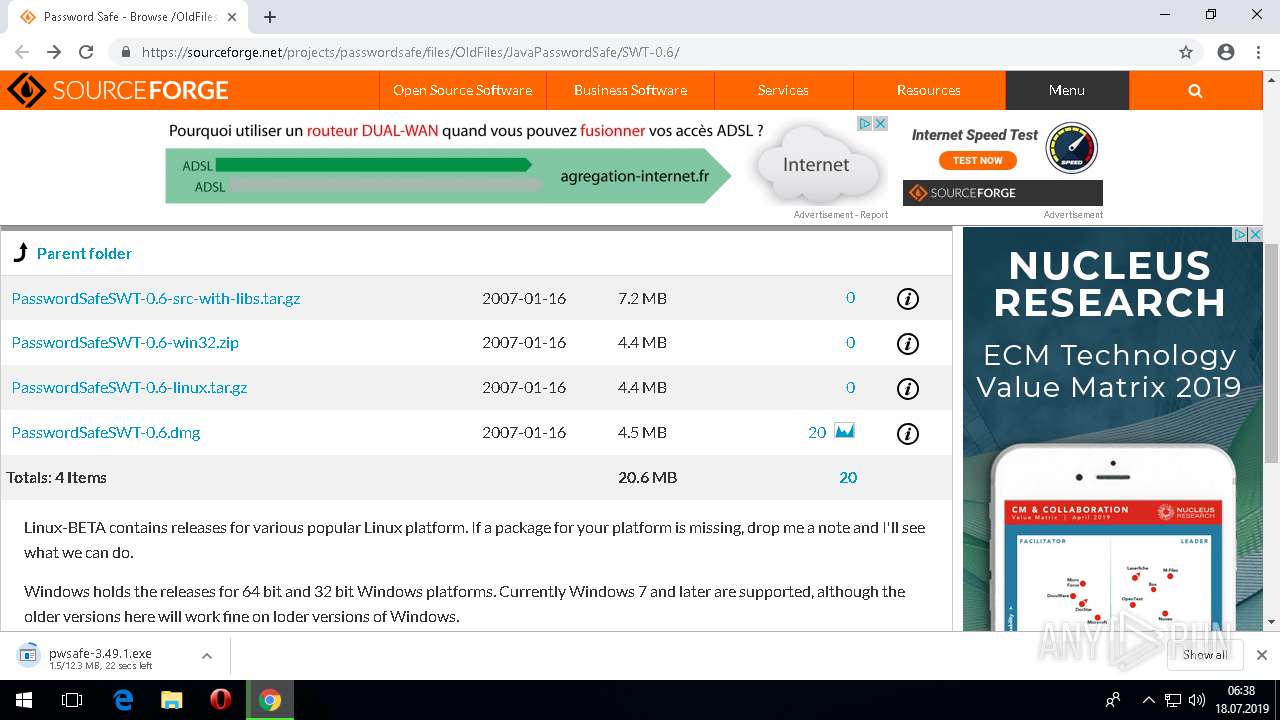
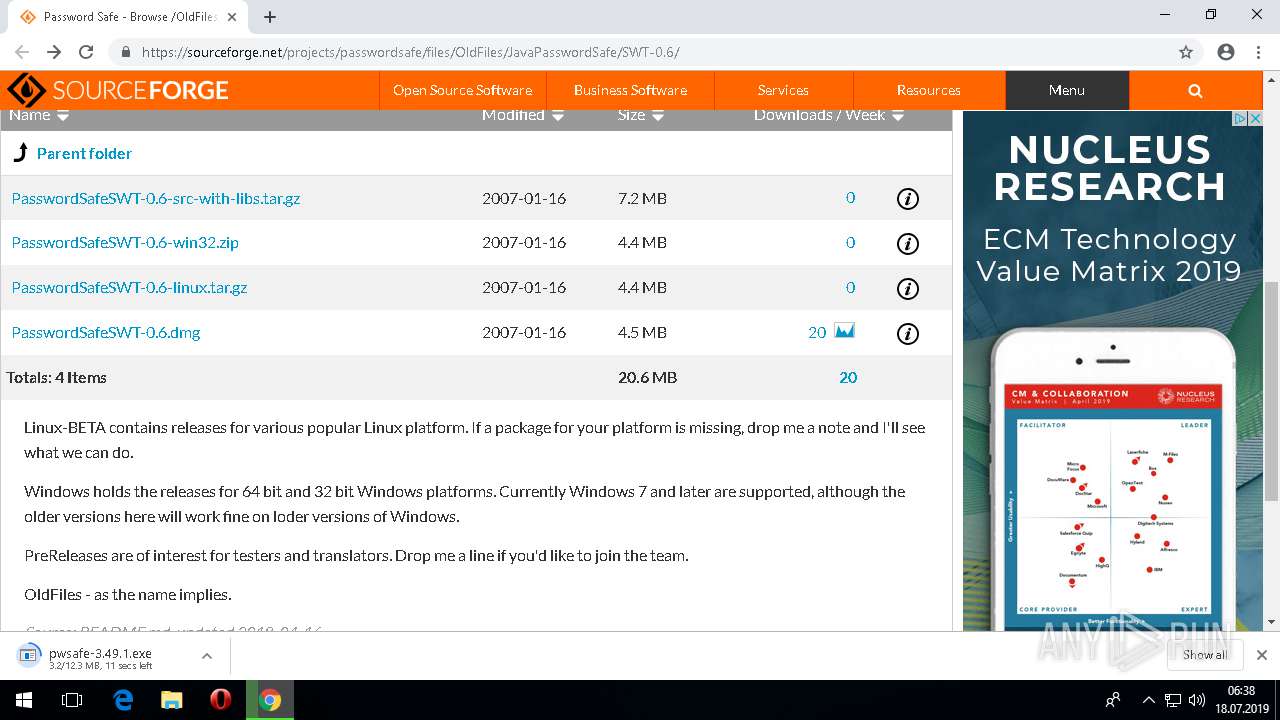
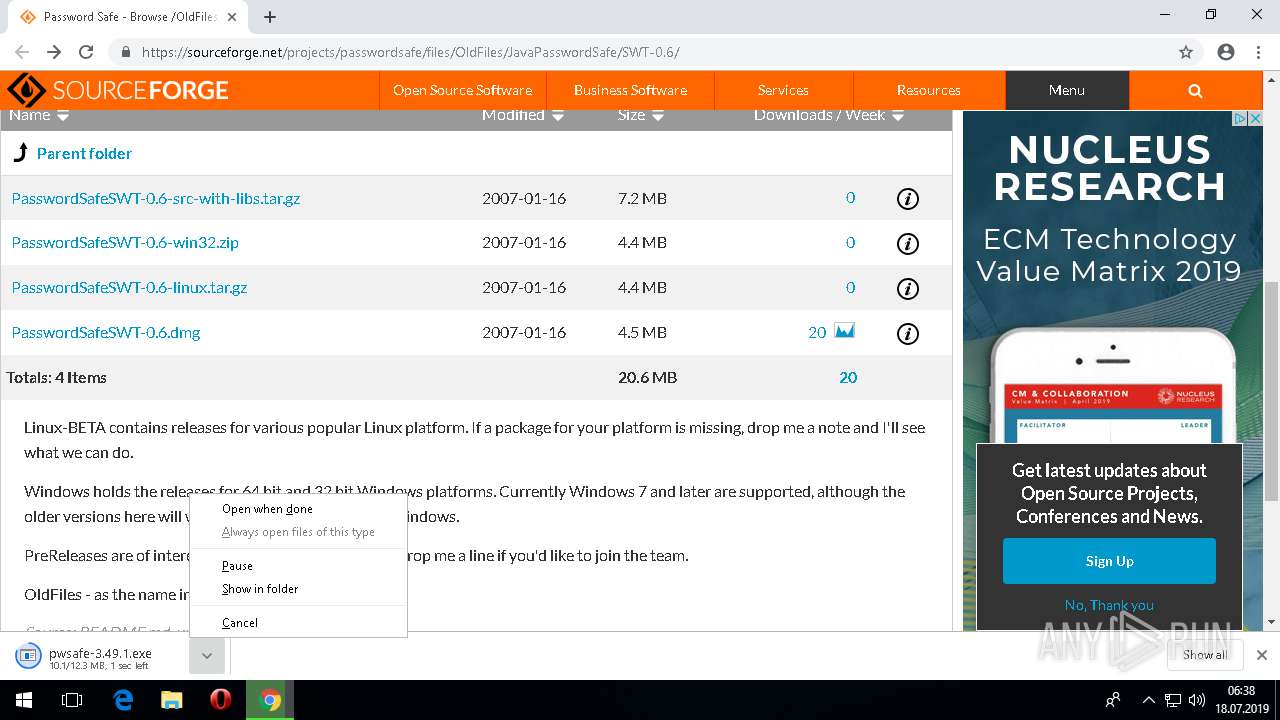
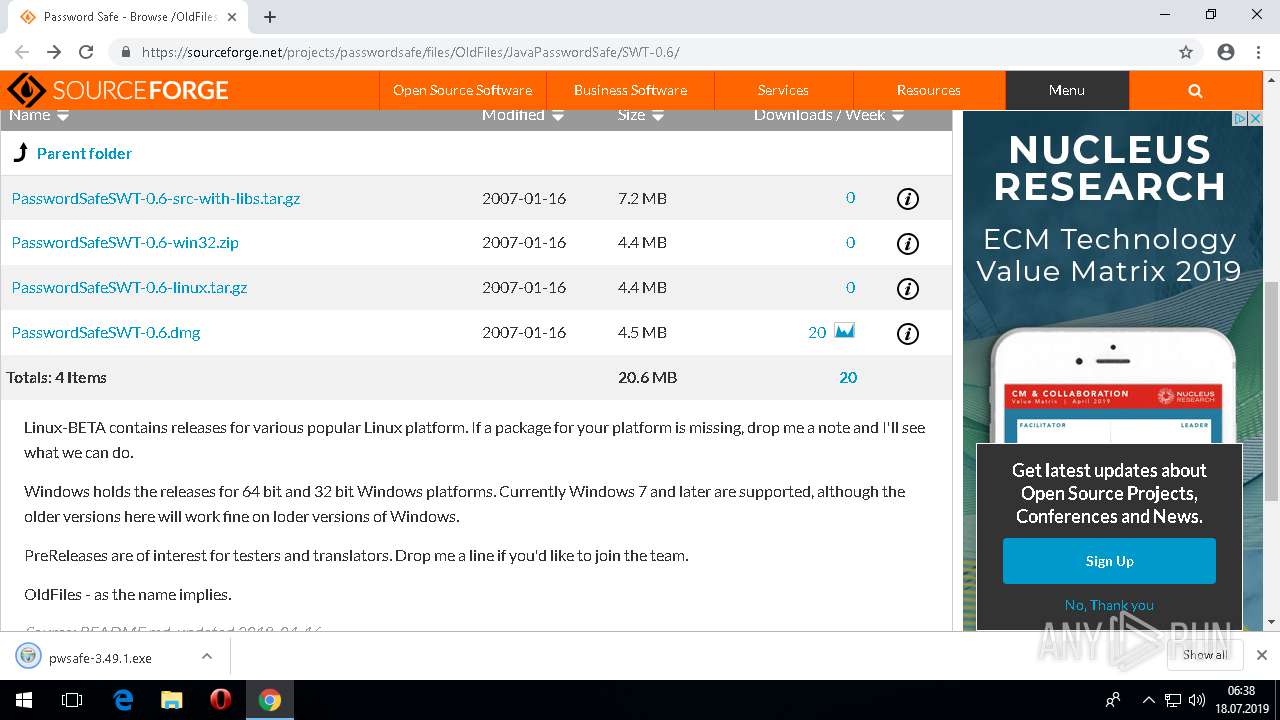
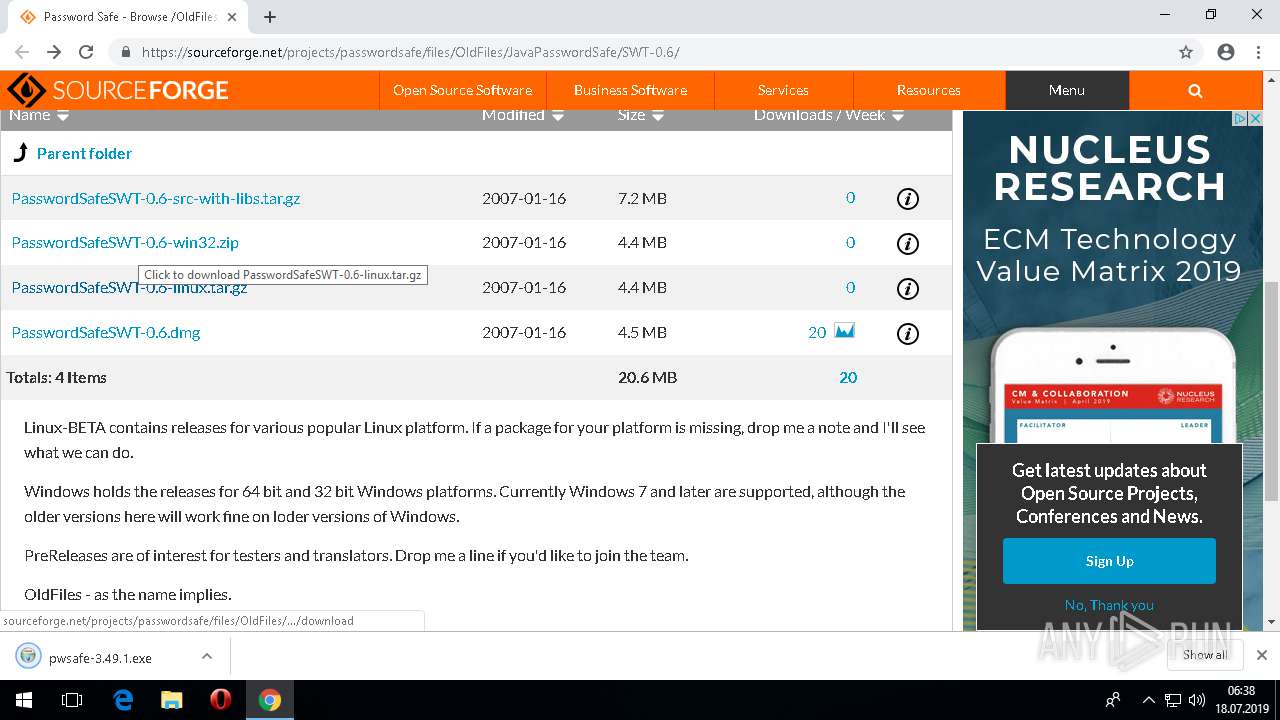
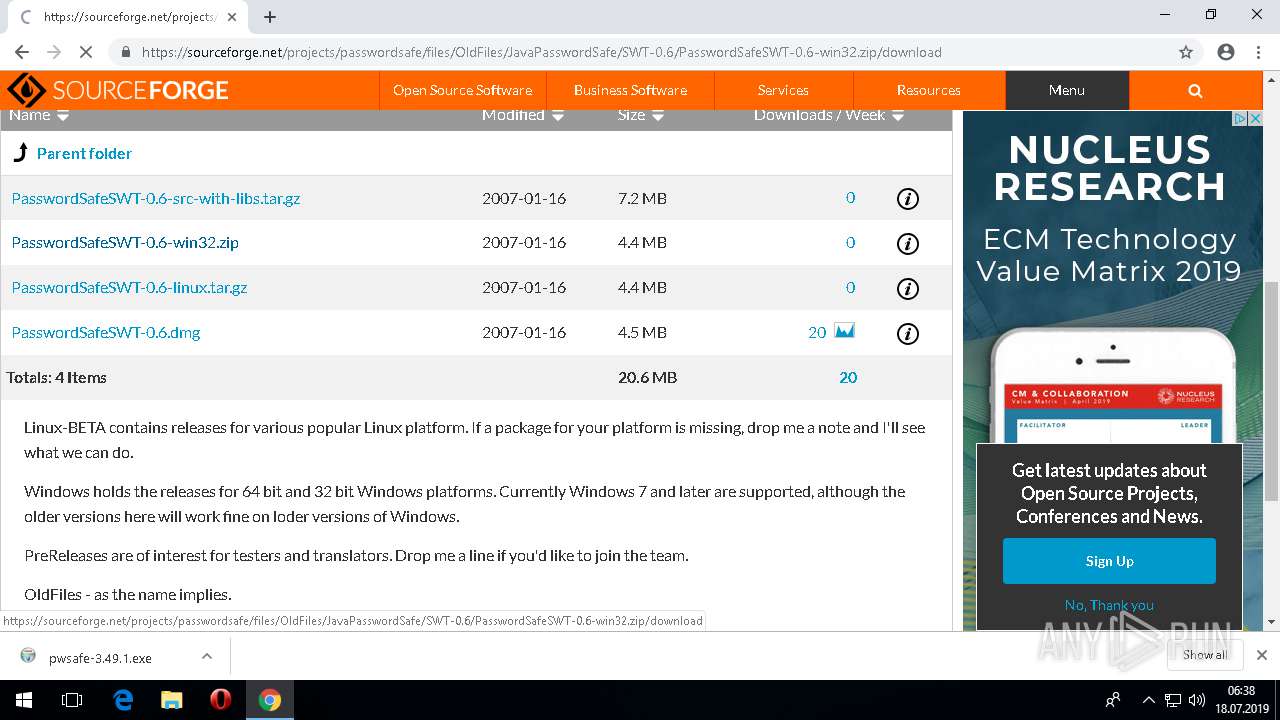
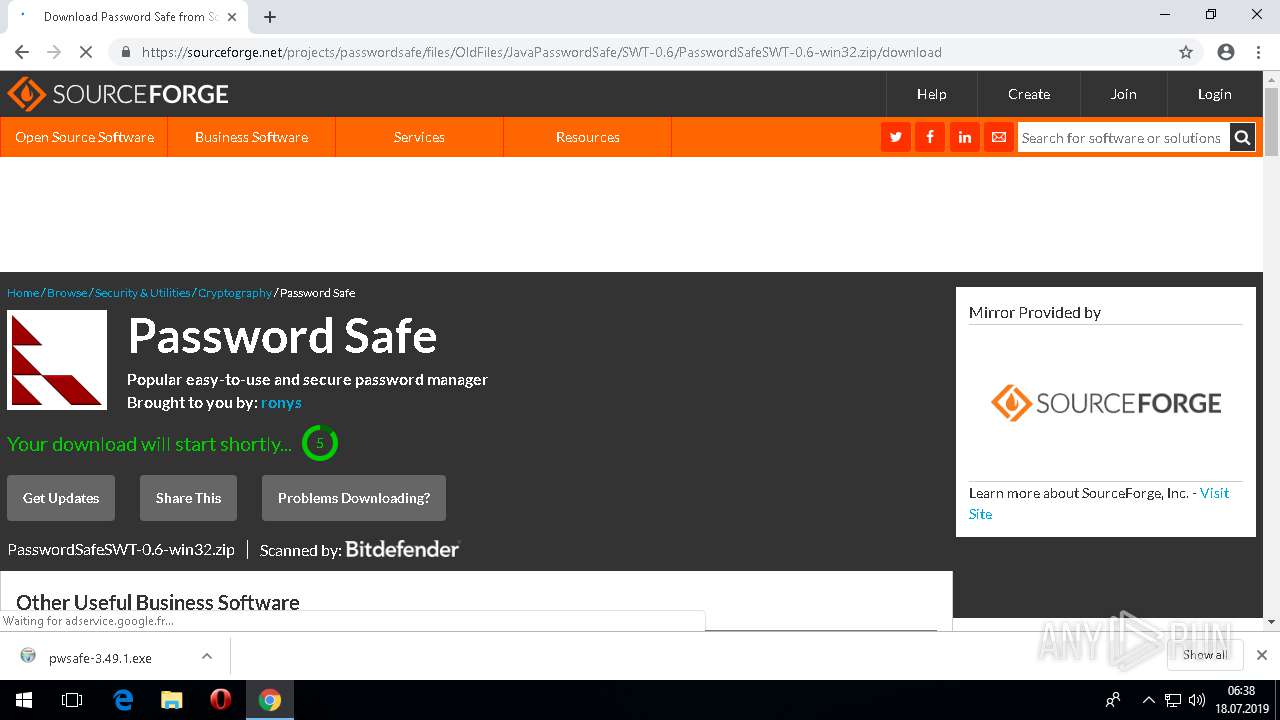
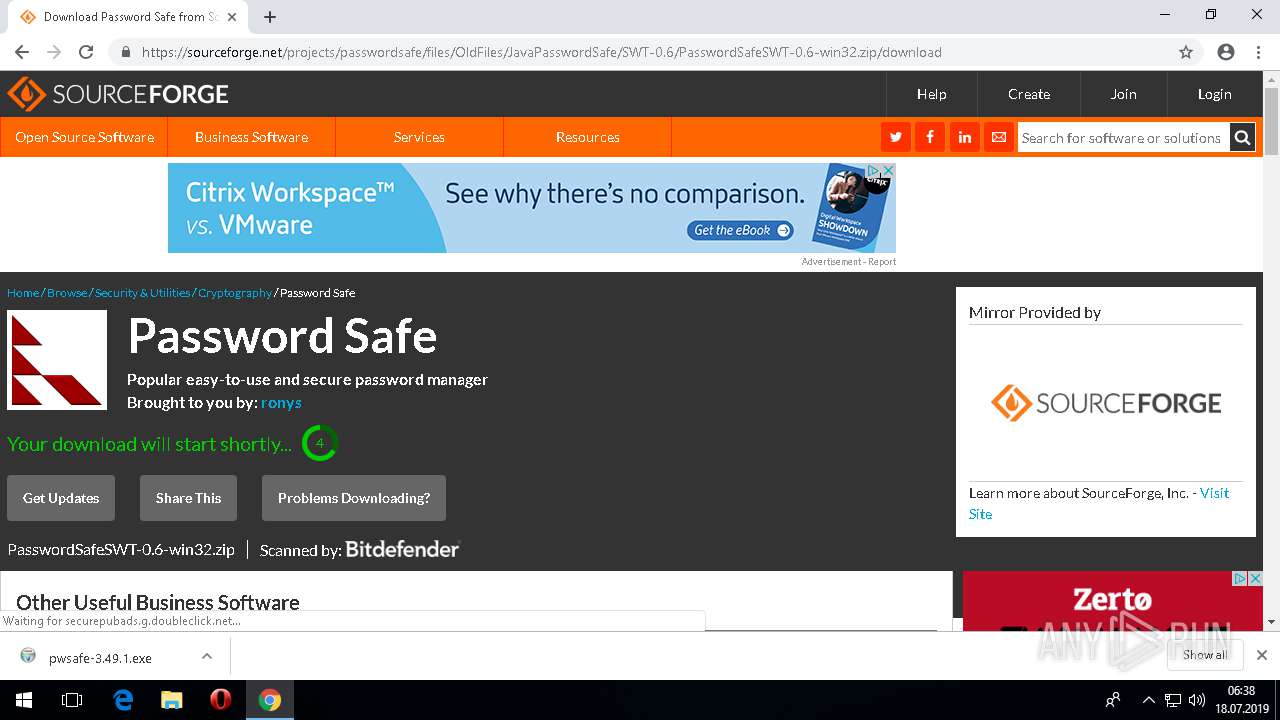
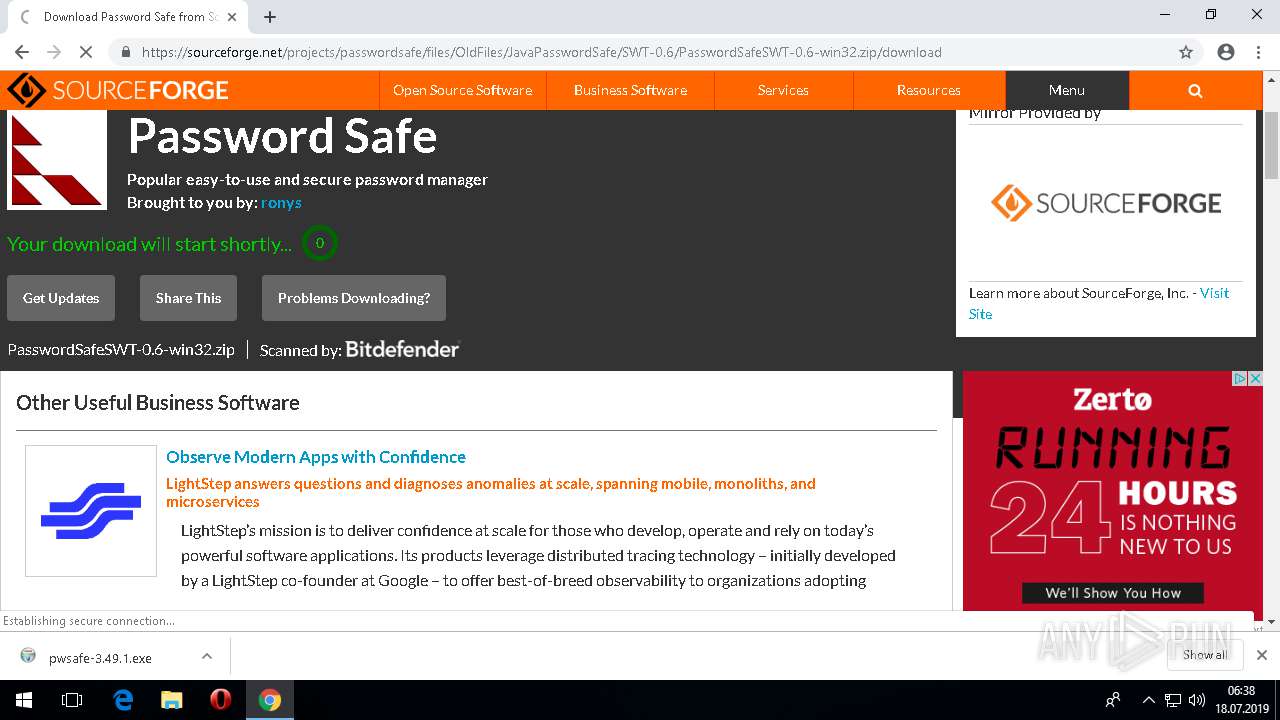
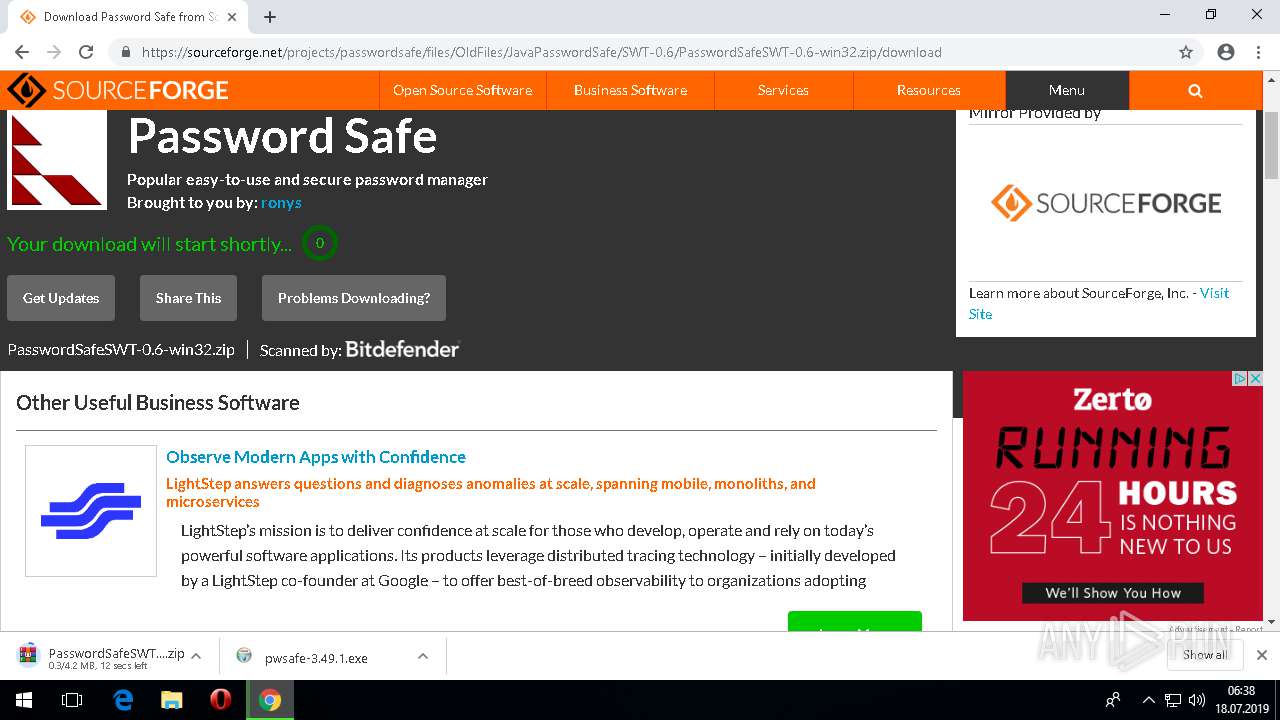
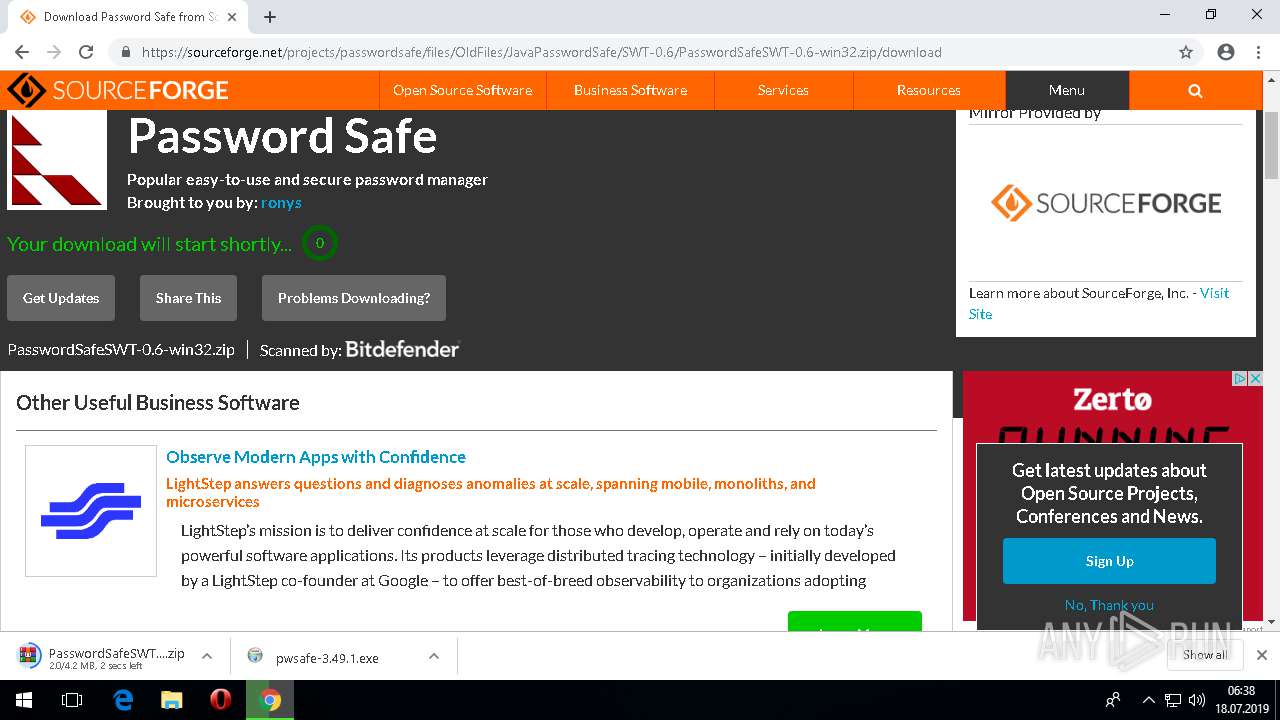
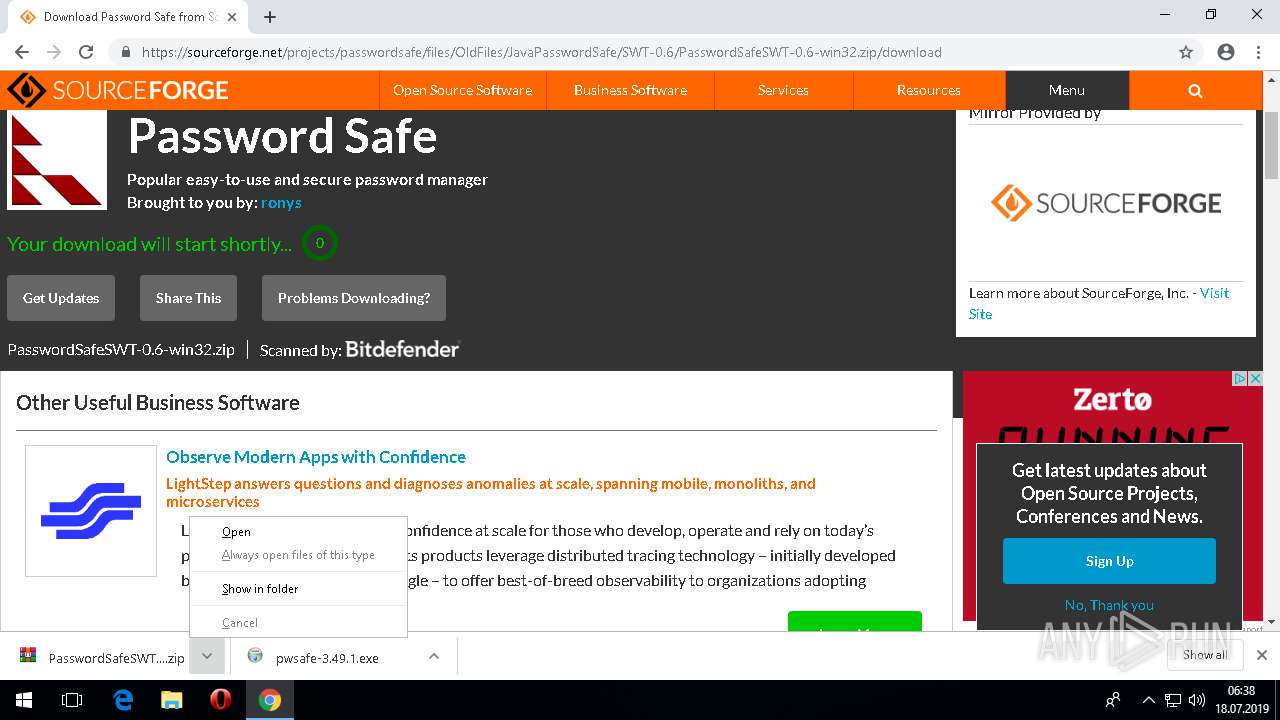
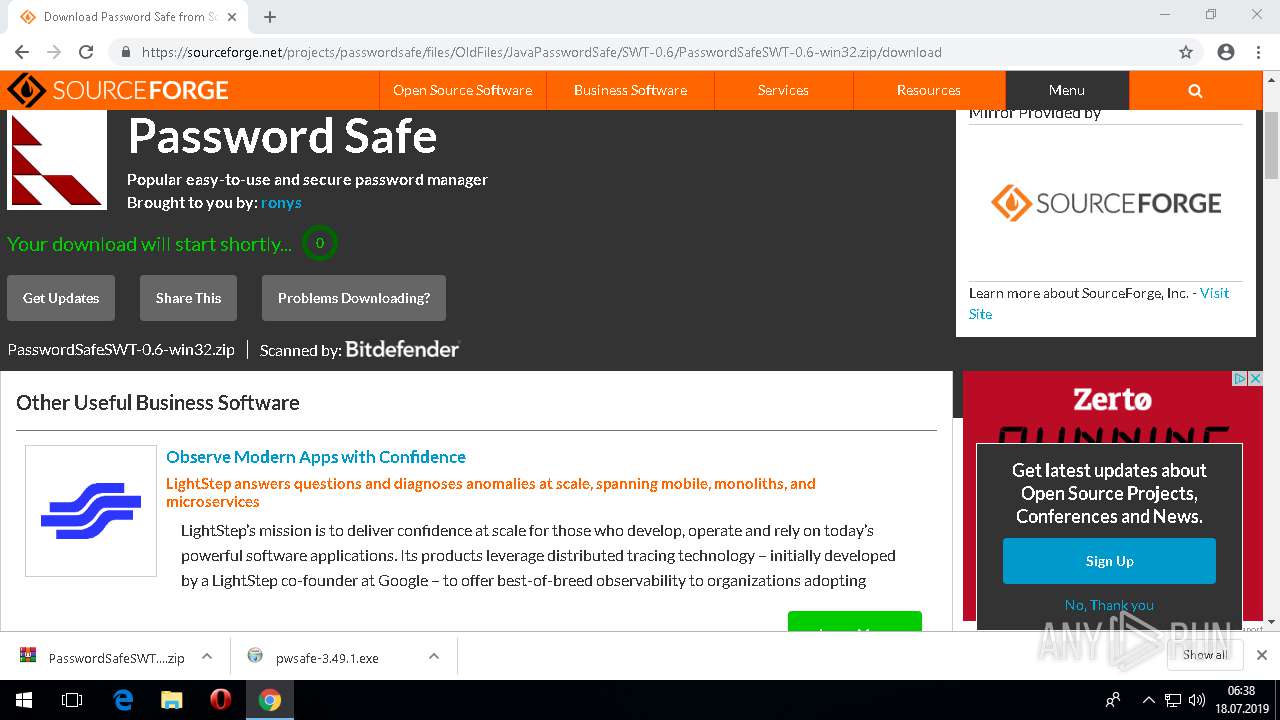
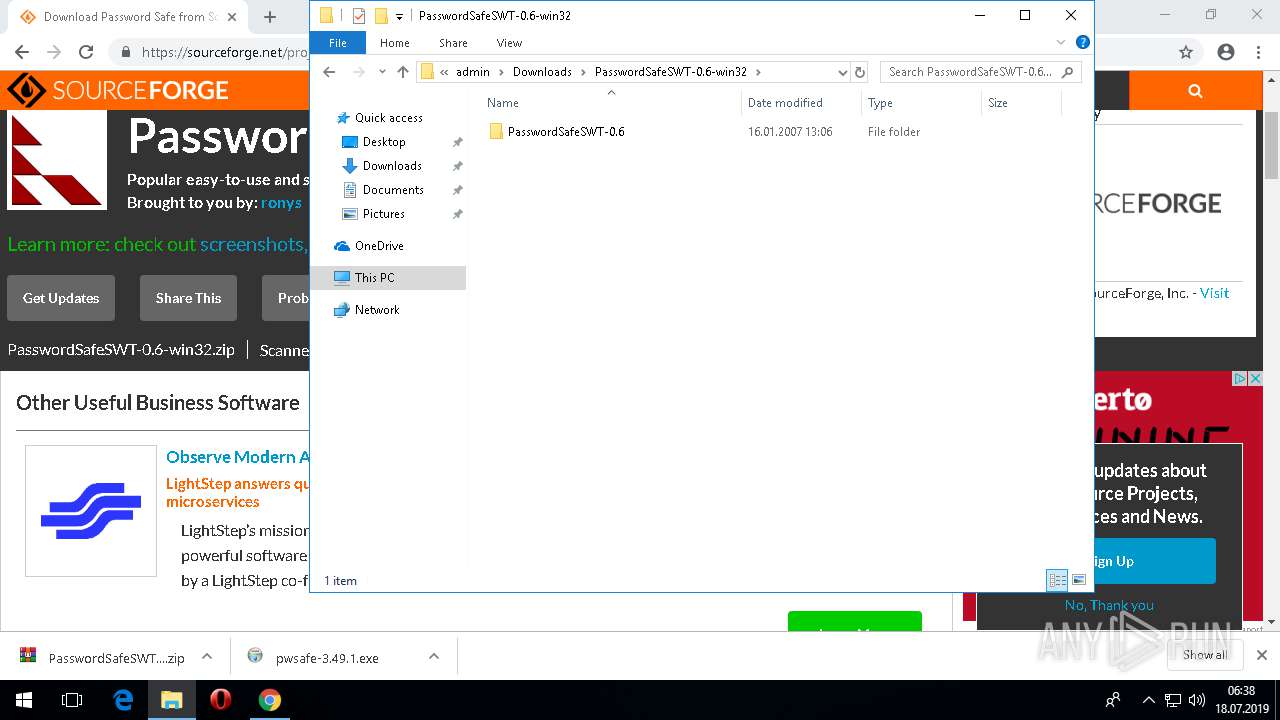
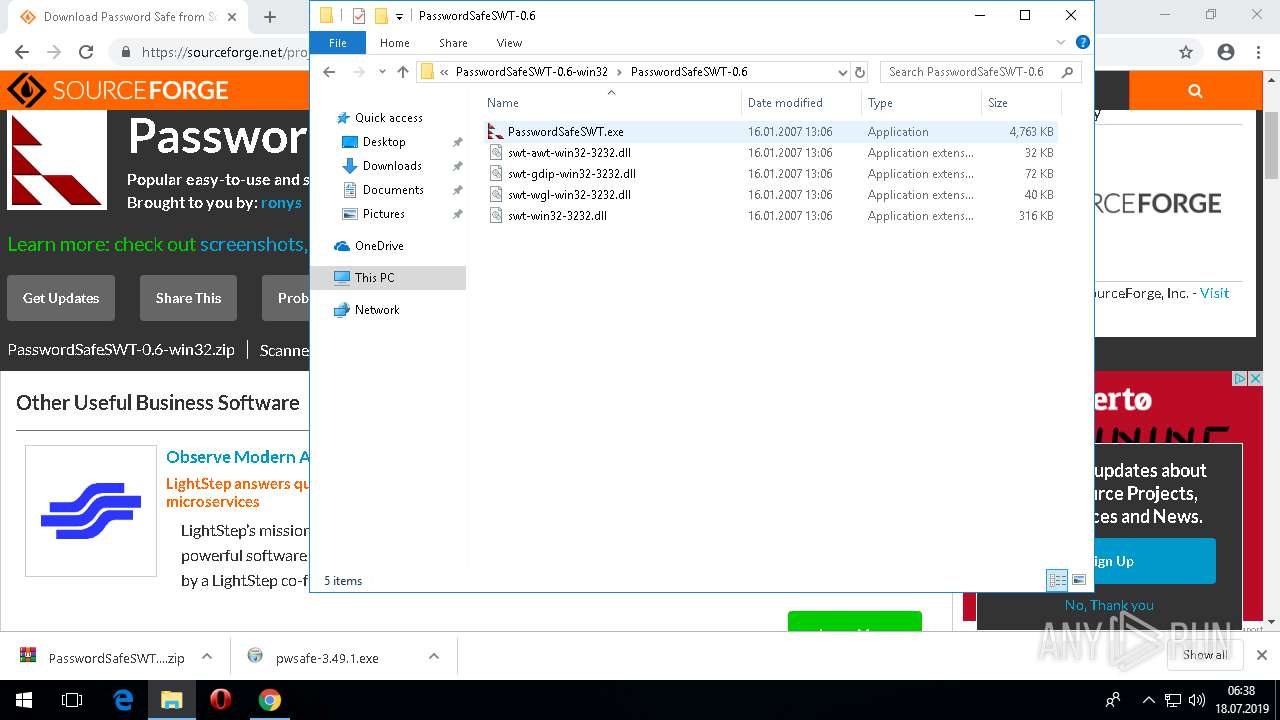
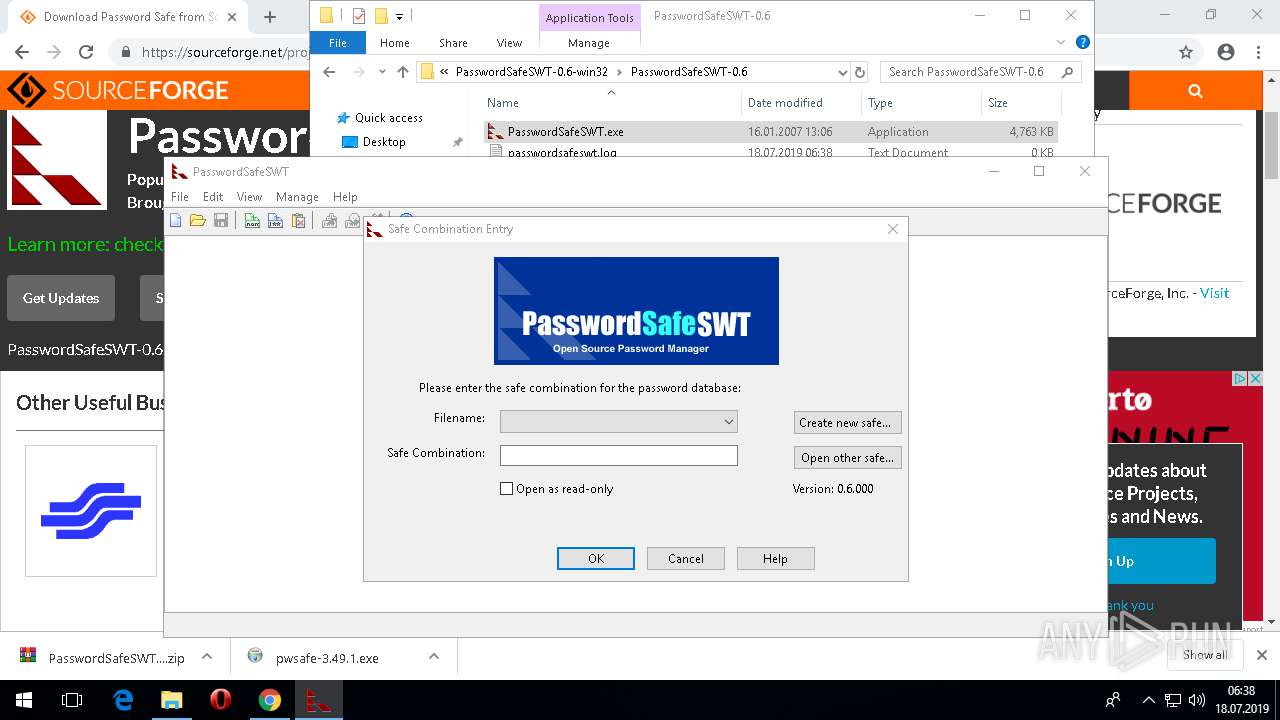
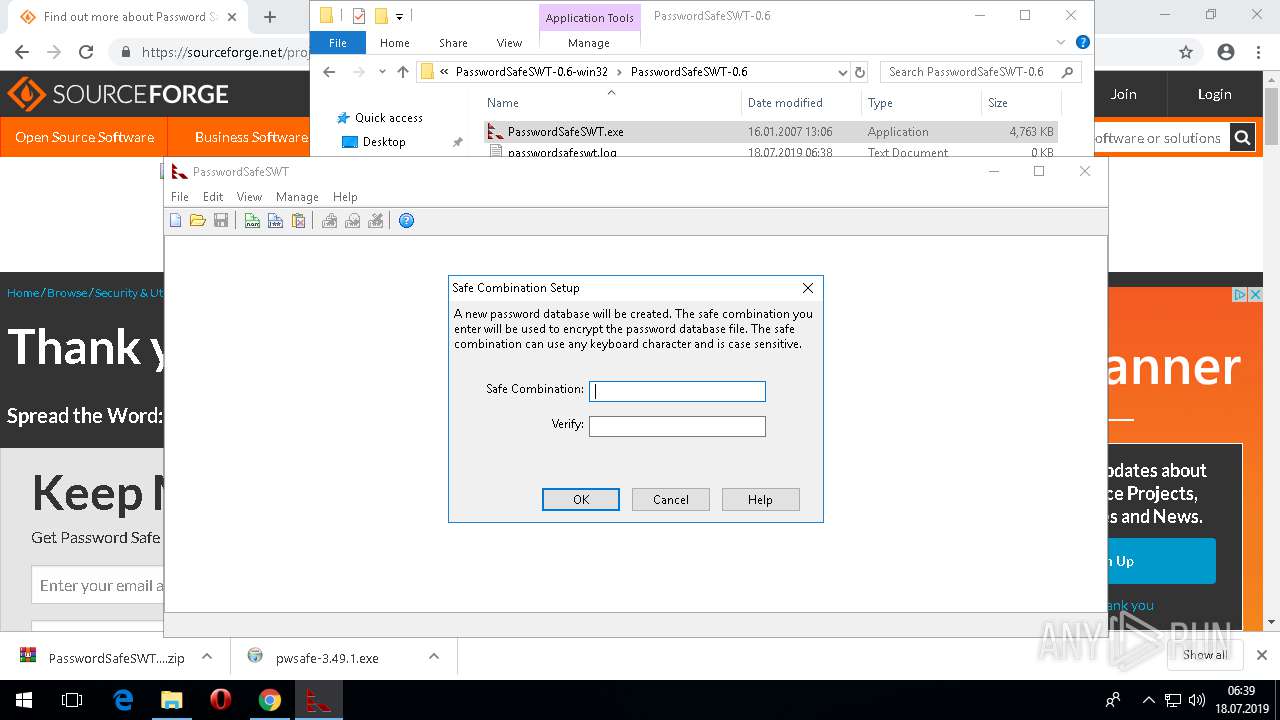
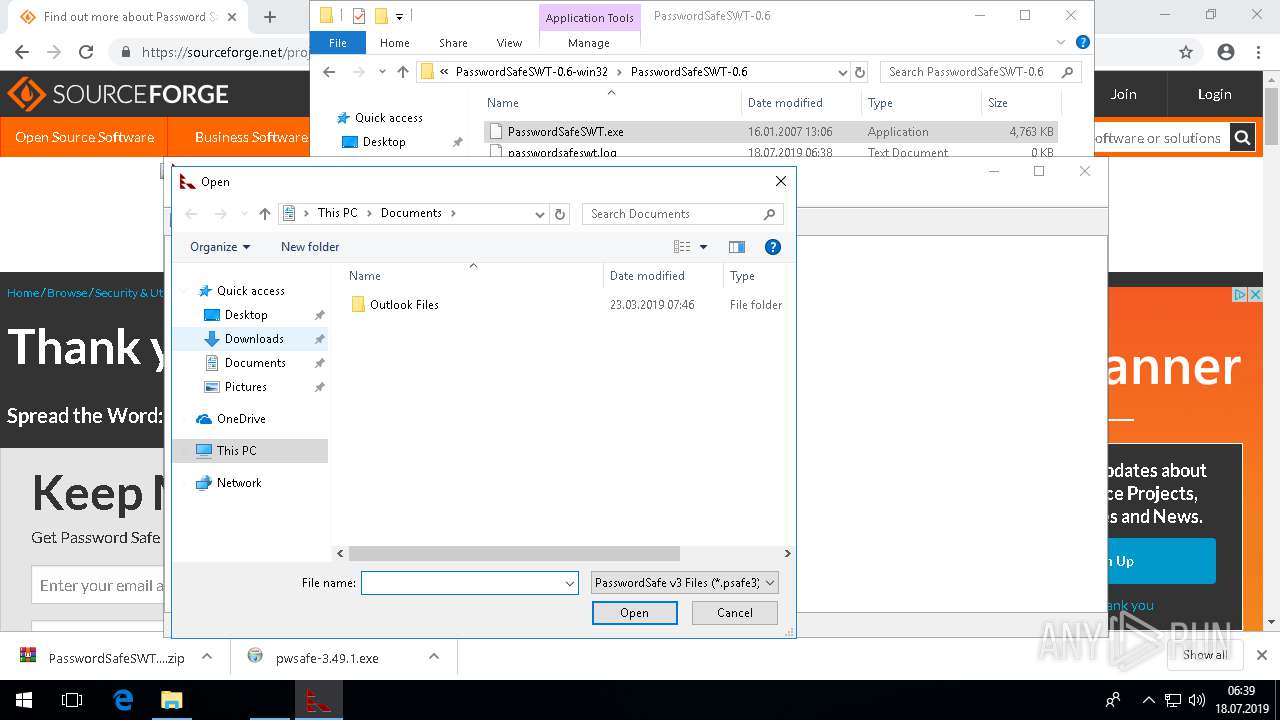
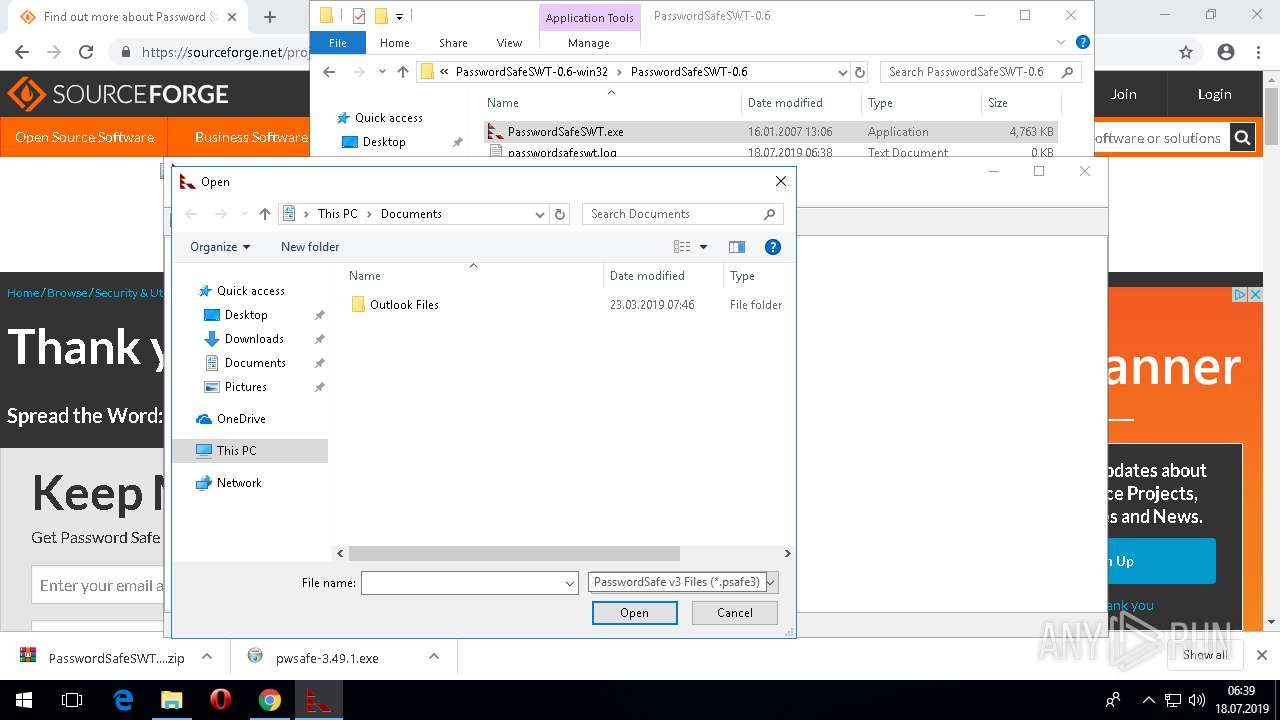
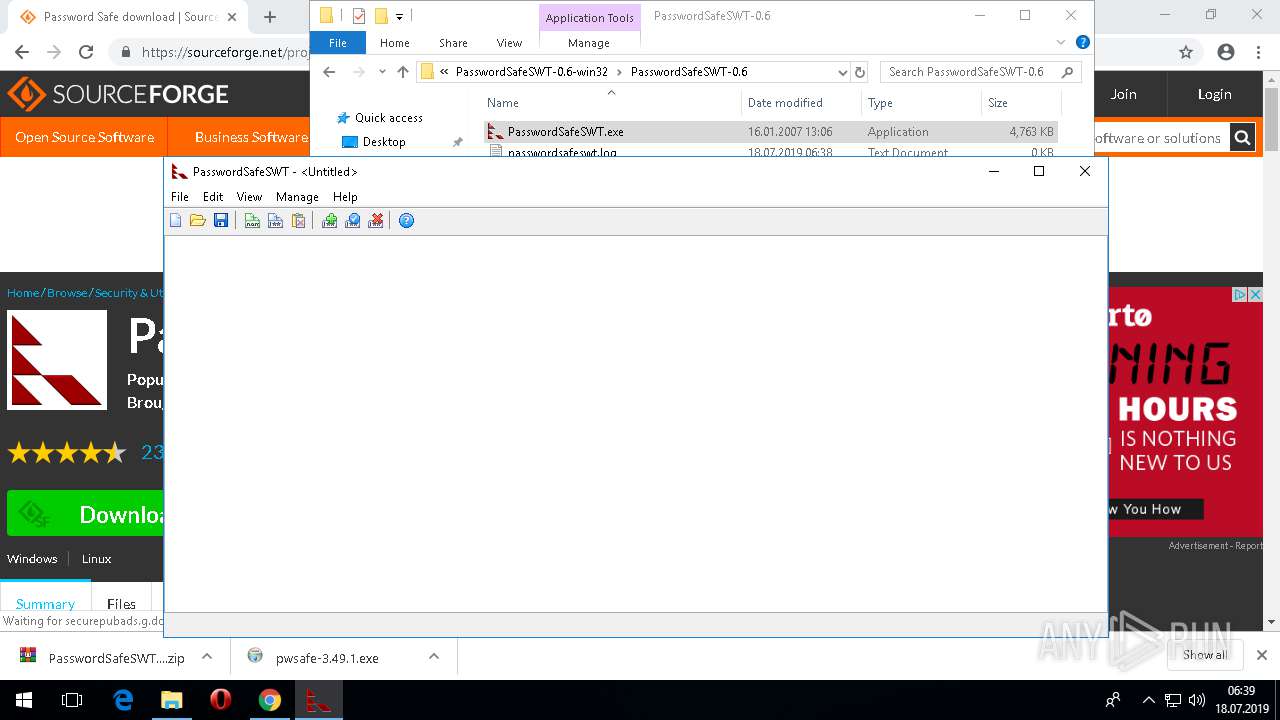
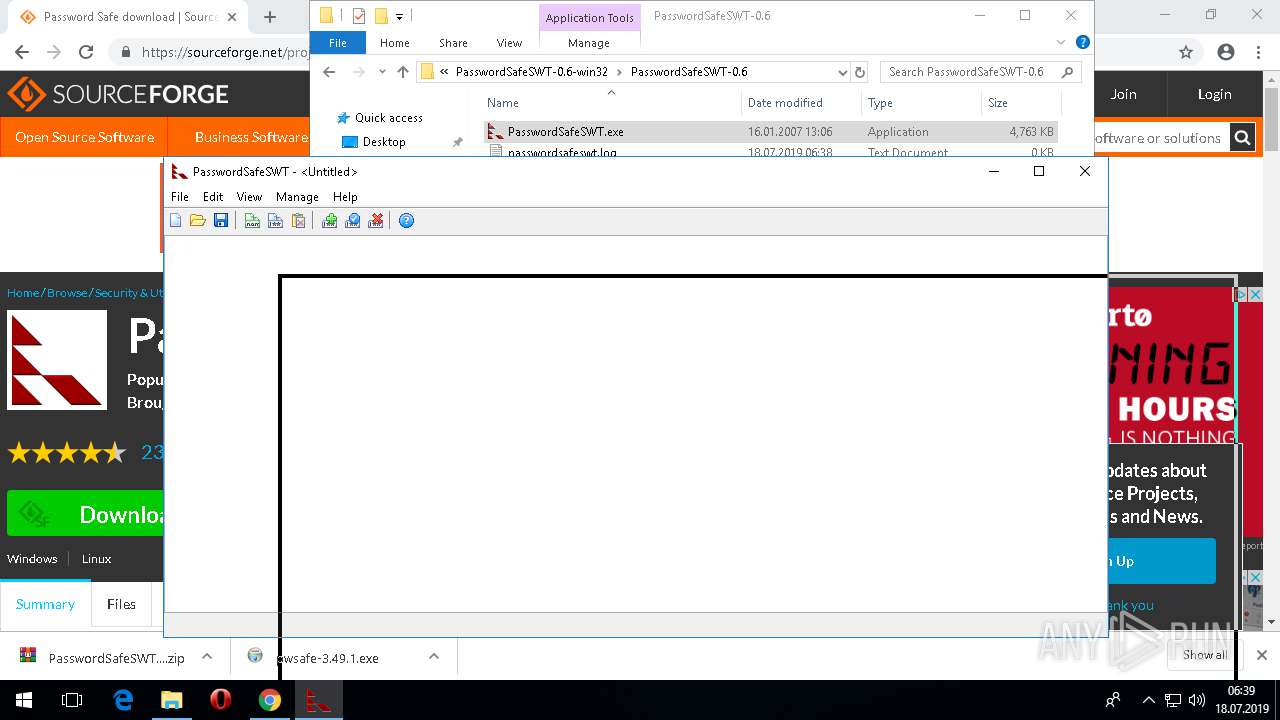
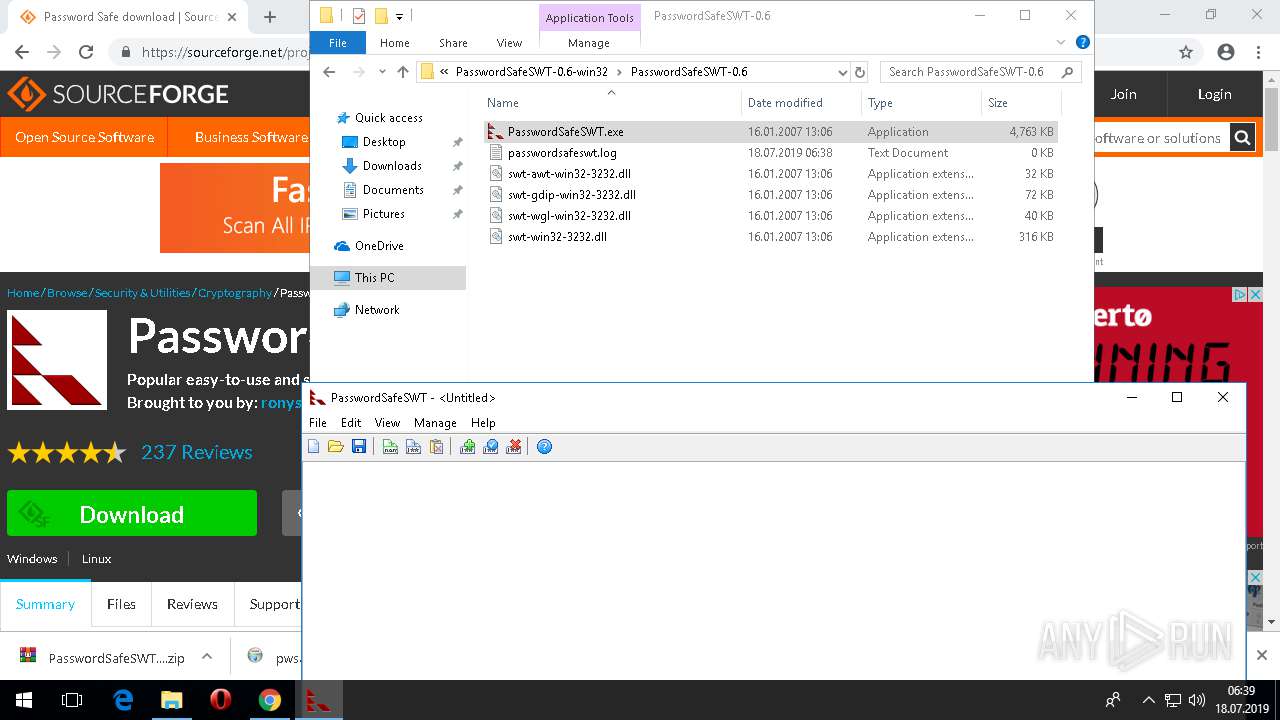
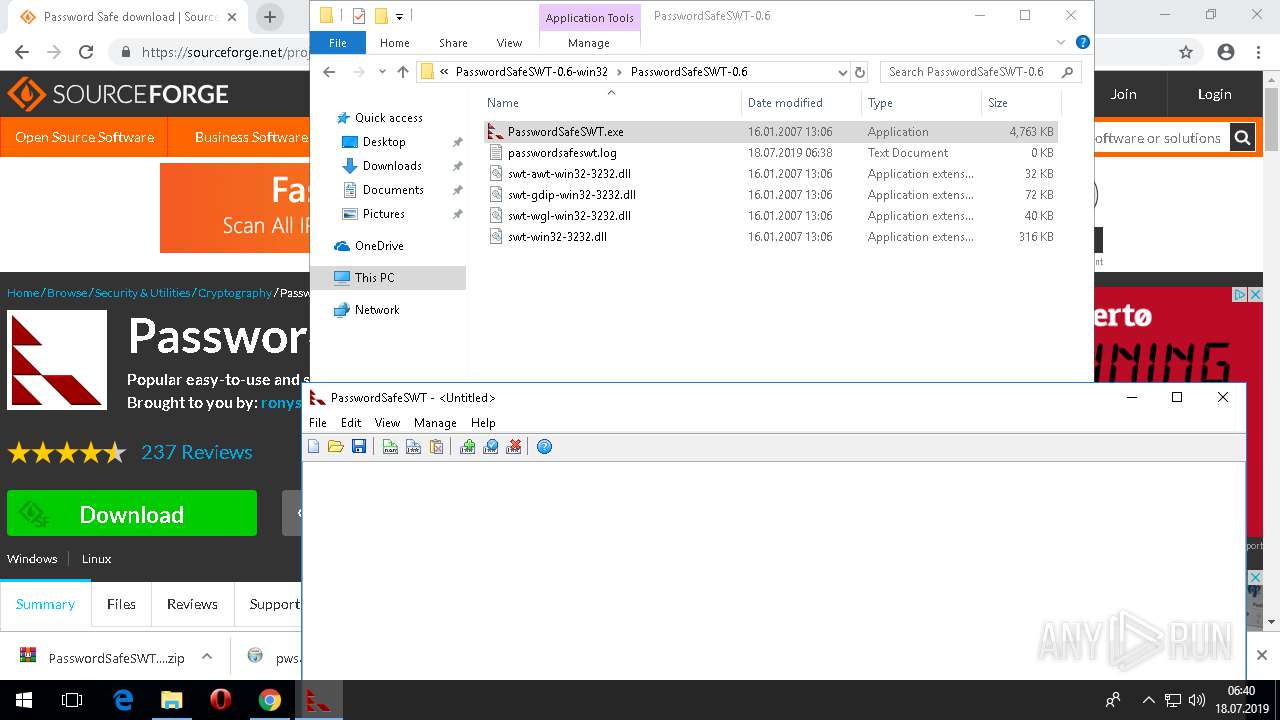
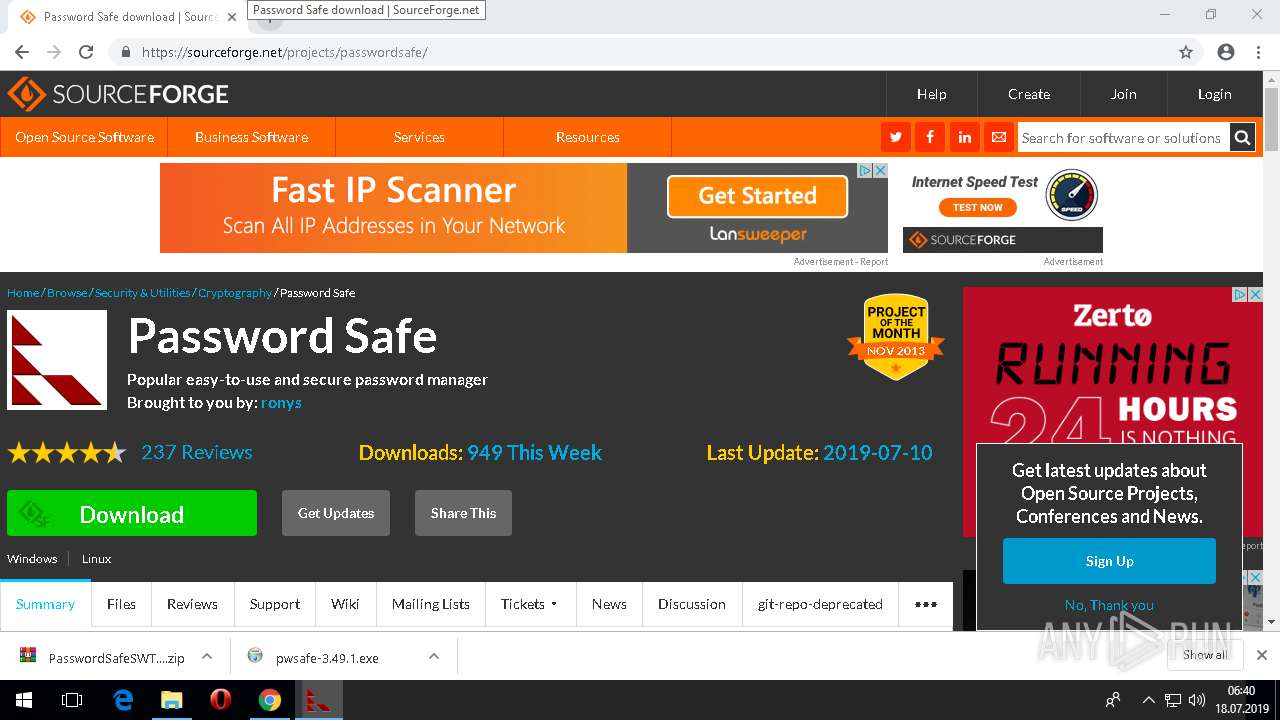
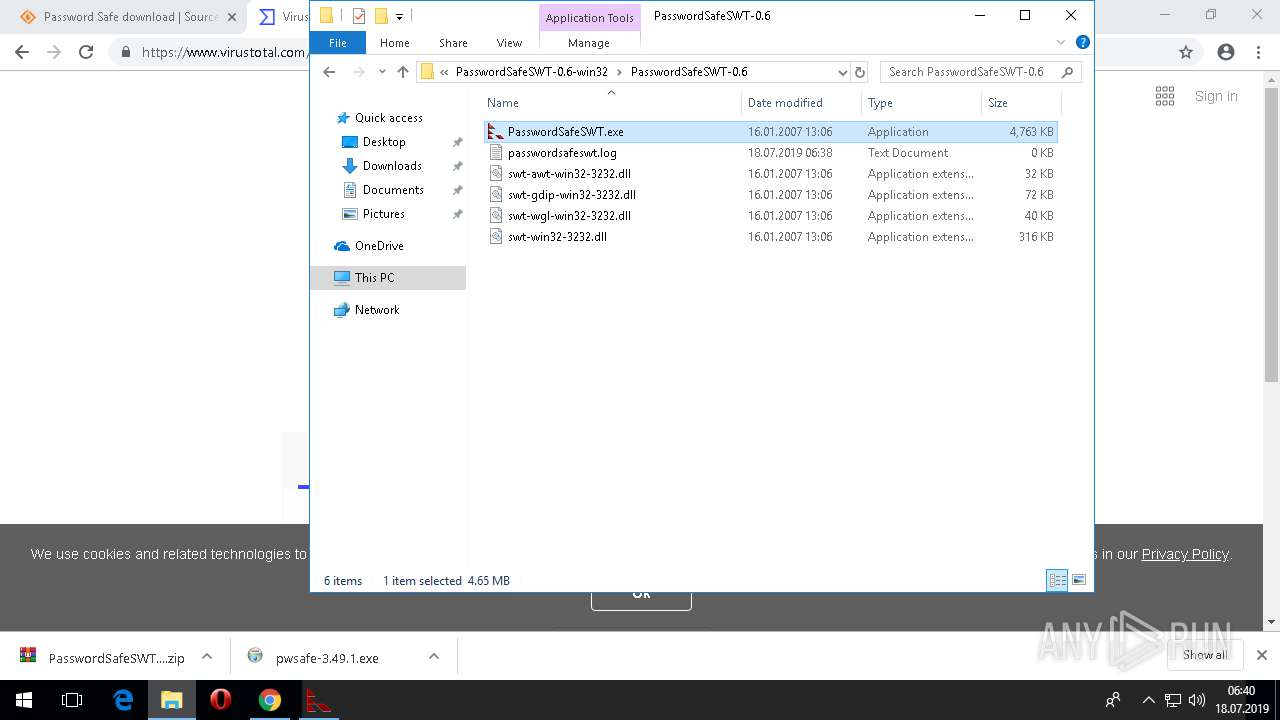
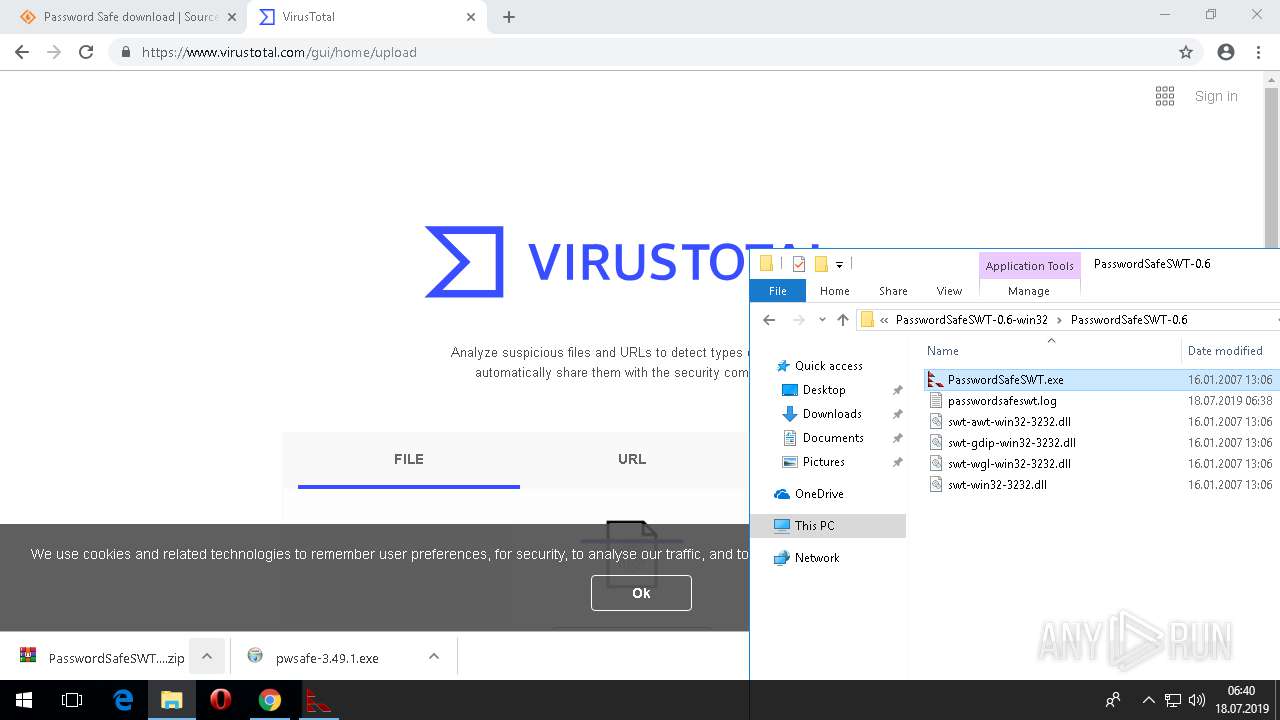
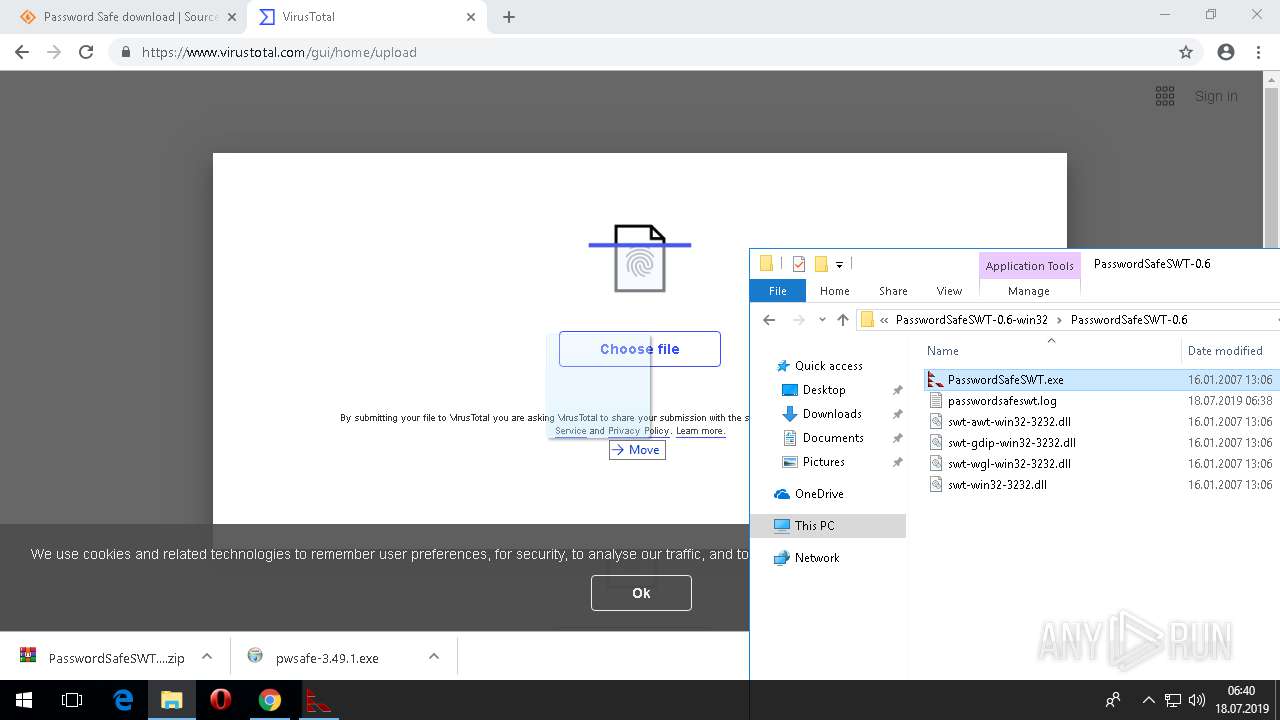
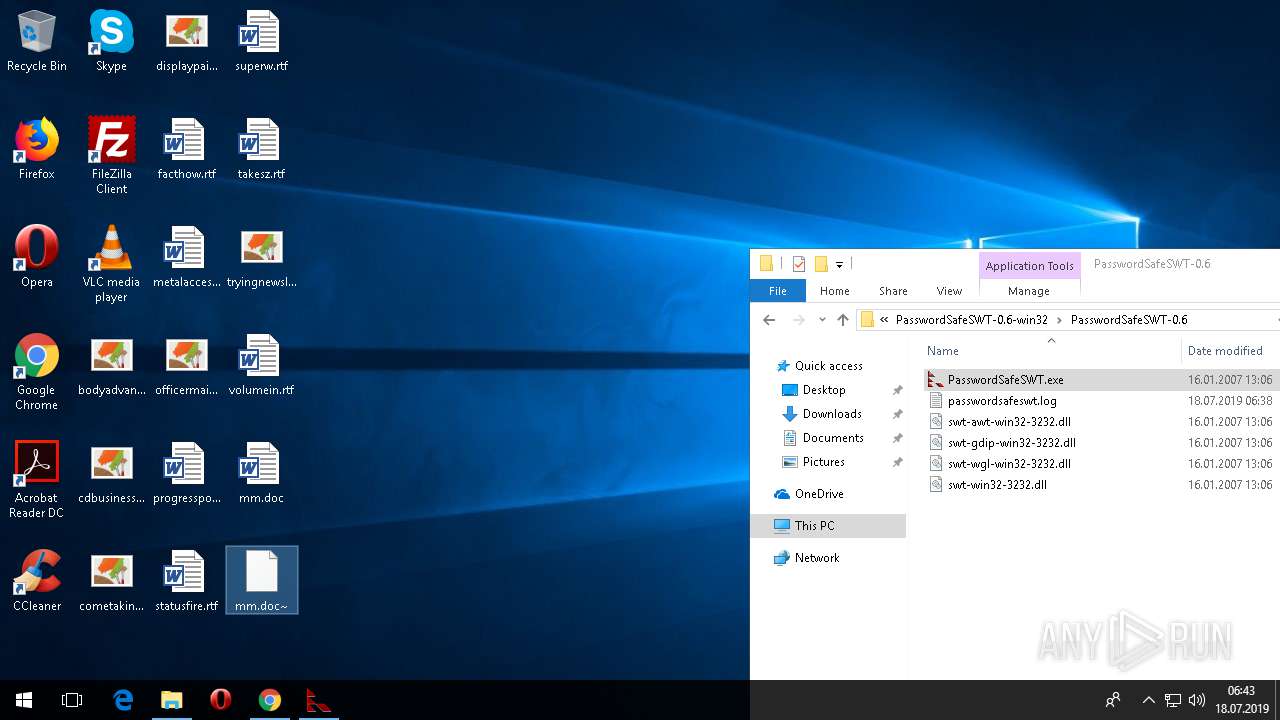
| URL: | https://sourceforge.net/projects/passwordsafe/files/OldFiles/JavaPasswordSafe/SWT-0.6/ |
| Full analysis: | https://app.any.run/tasks/bcc12f6d-814e-4f5d-b23c-0344b1d30af3 |
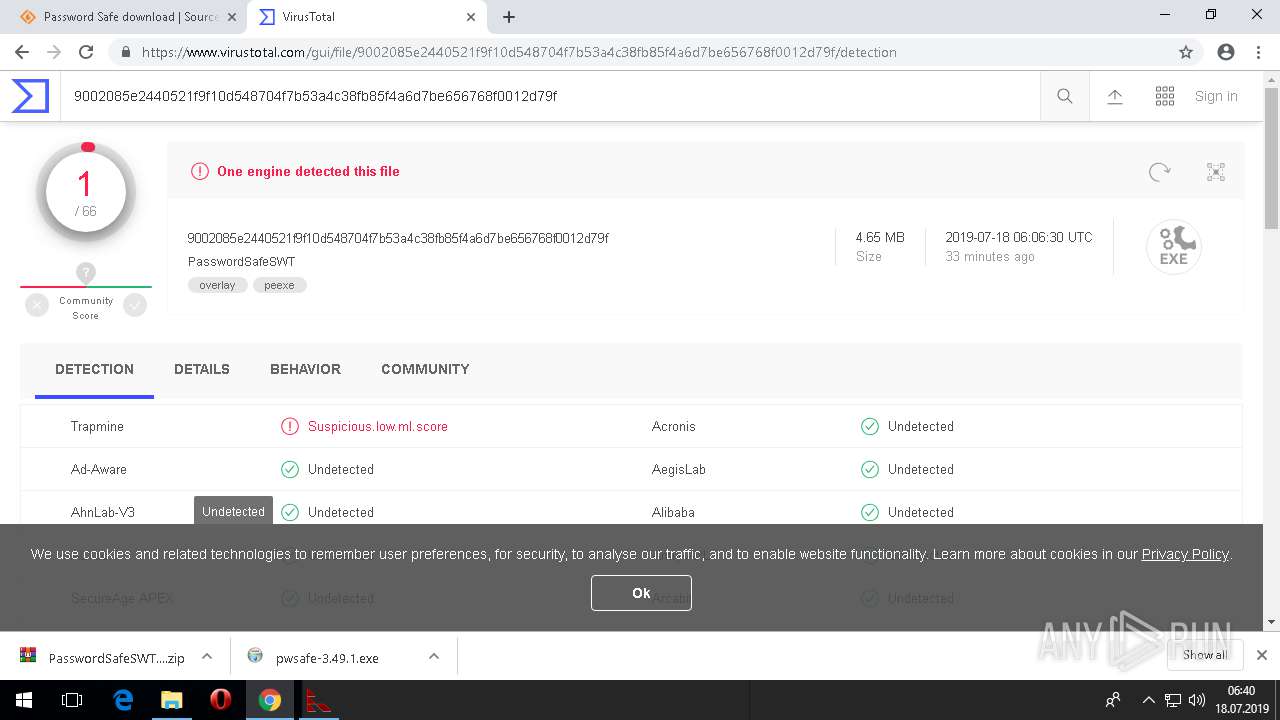
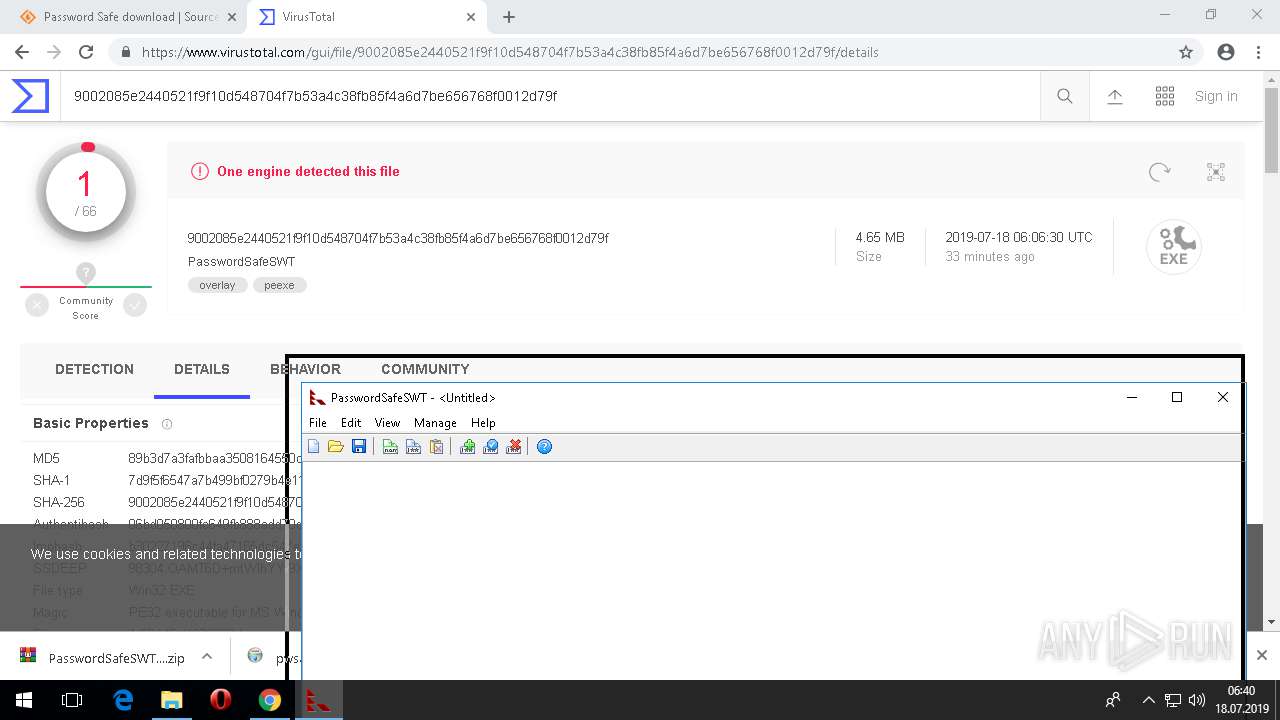
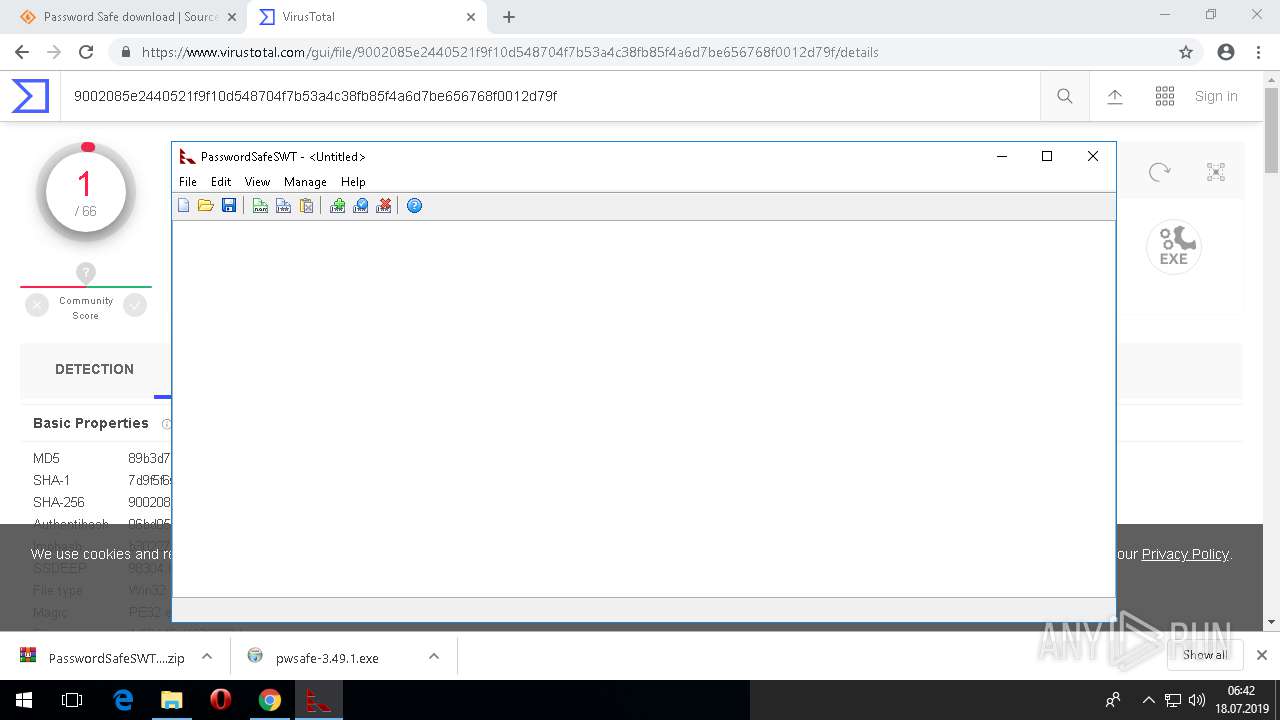
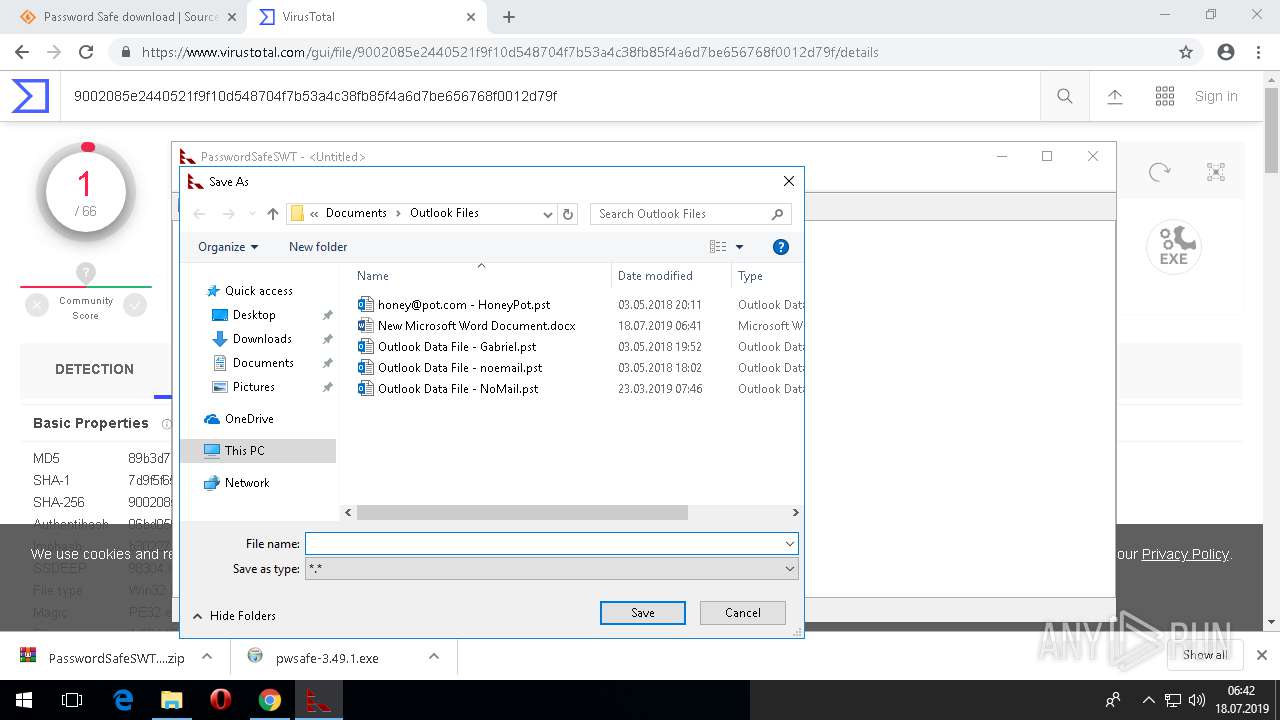
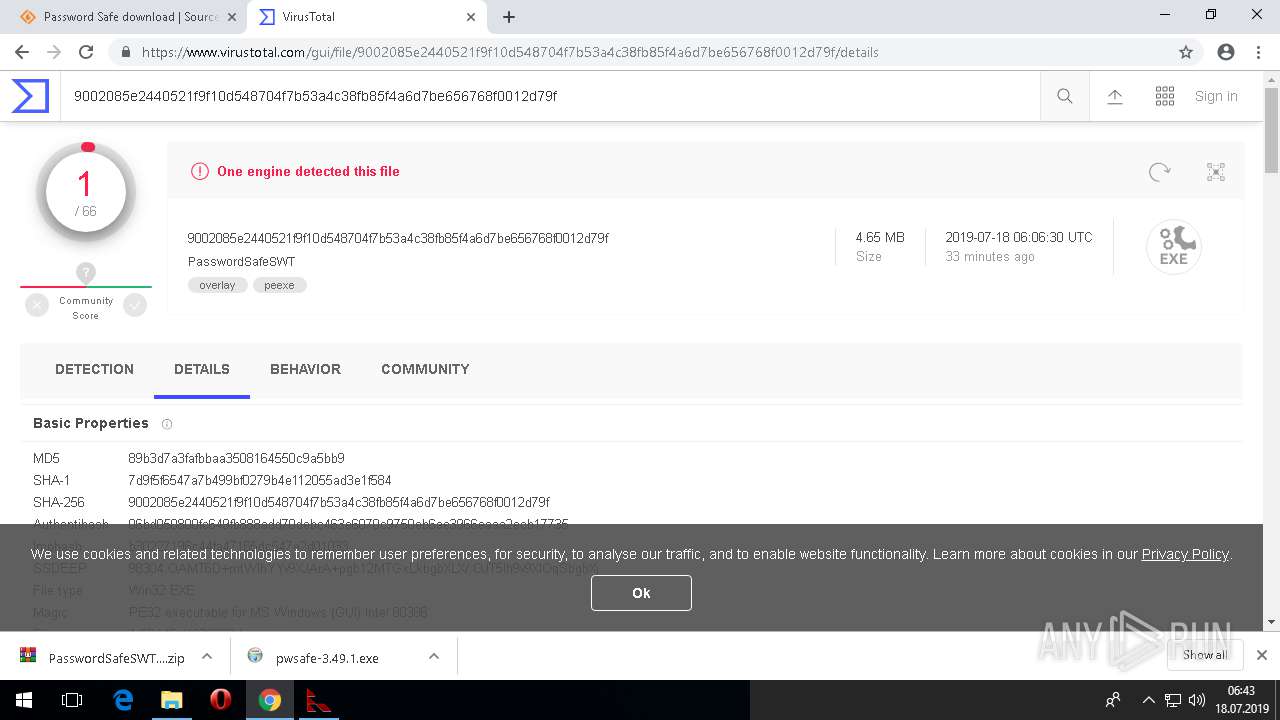
| Verdict: | Malicious activity |
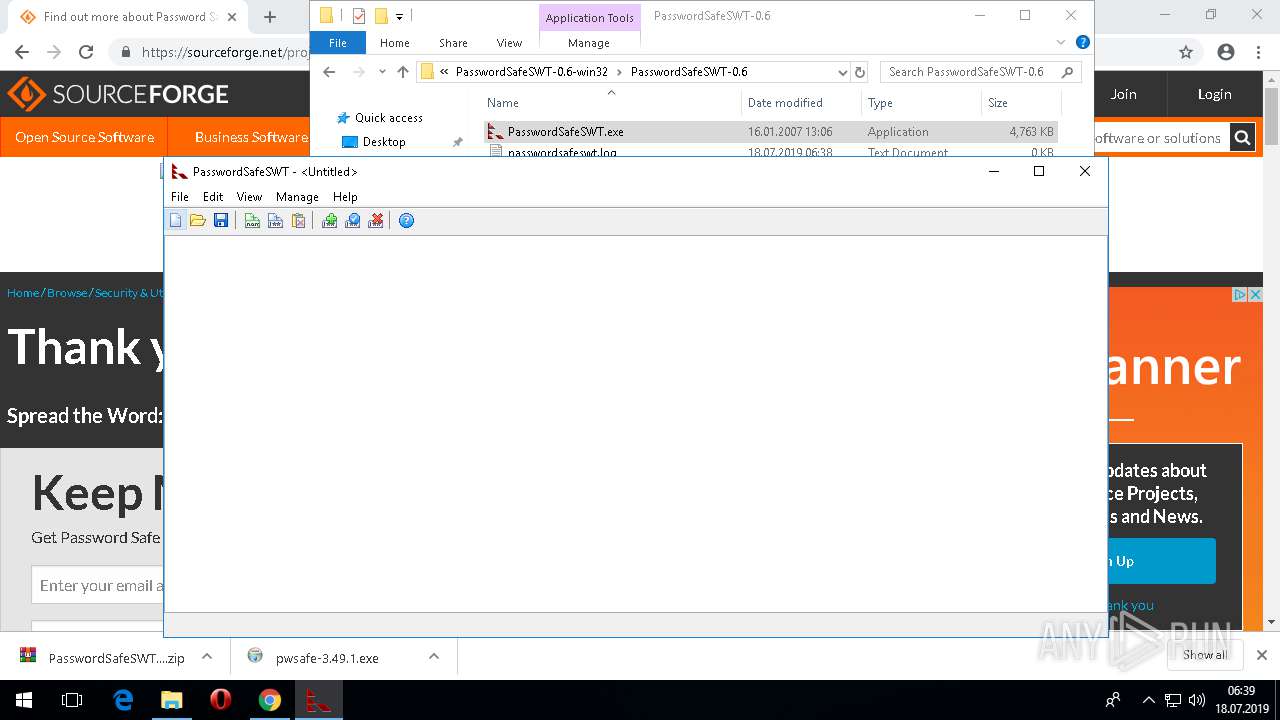
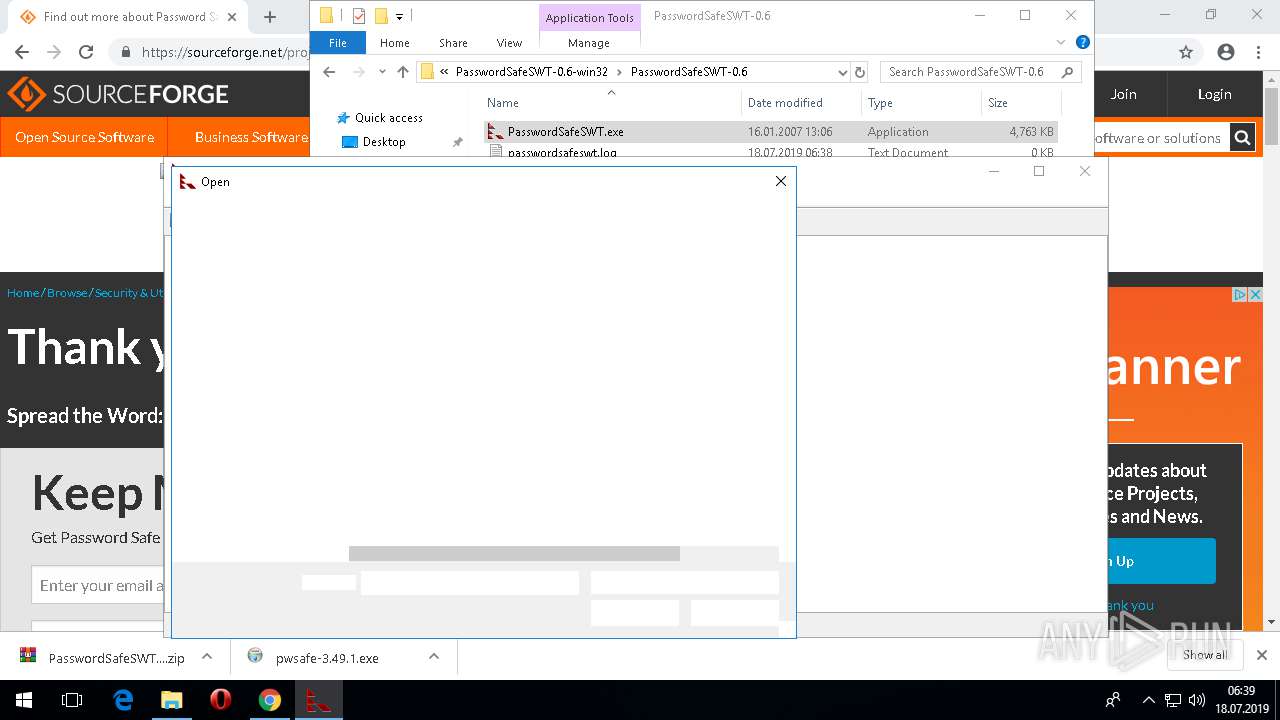
| Analysis date: | July 18, 2019, 06:37:17 |
| OS: | Windows 10 Professional (build: 16299, 32 bit) |
| Indicators: | |
| MD5: | 027213FB61B8822835E4A23D9D45A272 |
| SHA1: | 8EB07E8EA8744ADA3210BD1ADFA8AD34A0EBEC2F |
| SHA256: | 490BD9FA41FD35CD7E6CAAA1148EAD6F1D881A39E91895578374937D1808A6CE |
| SSDEEP: | 3:N8HCGSuLAuUt4XBDHzyVIm1EFjDAK2BLG:2iGnCt4XB+EF72BLG |
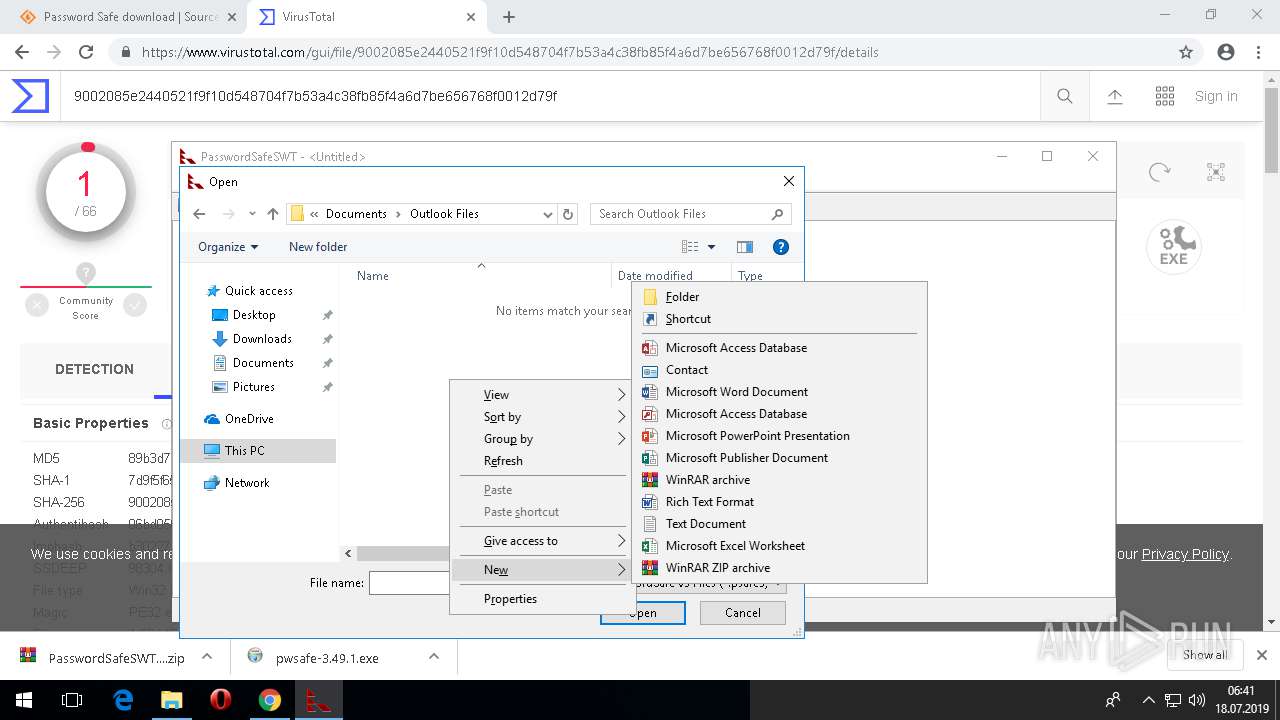
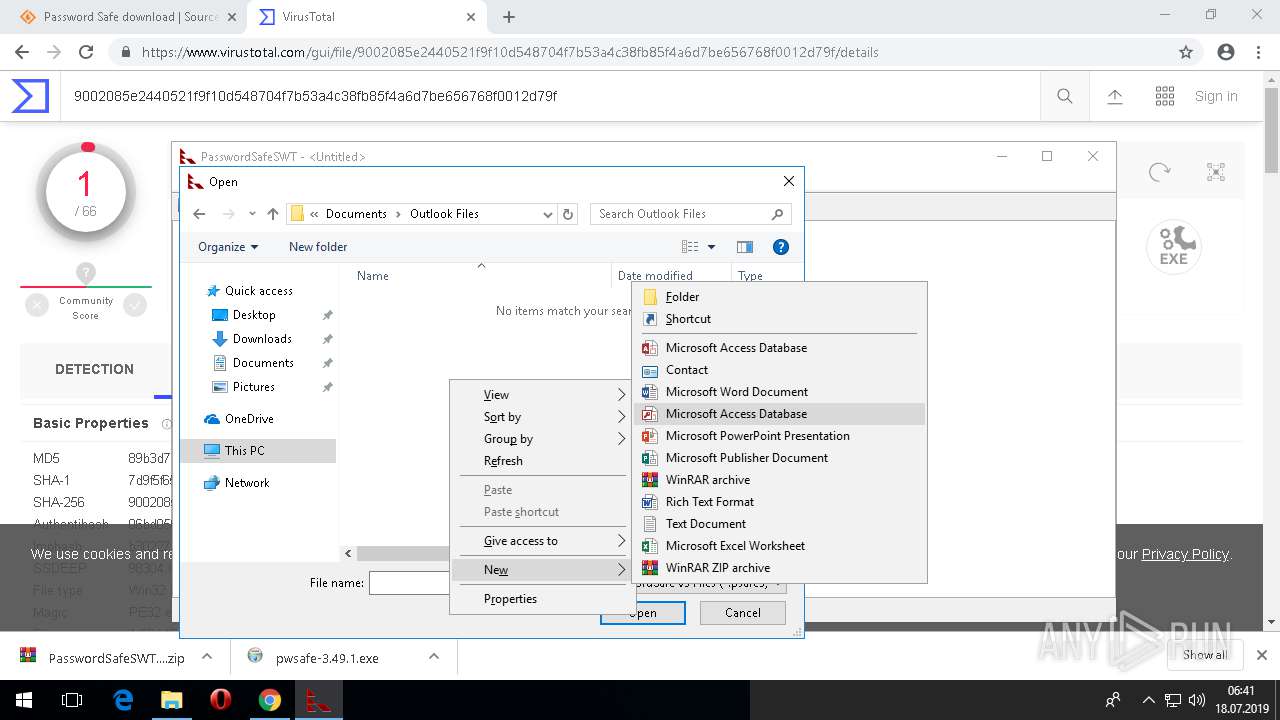
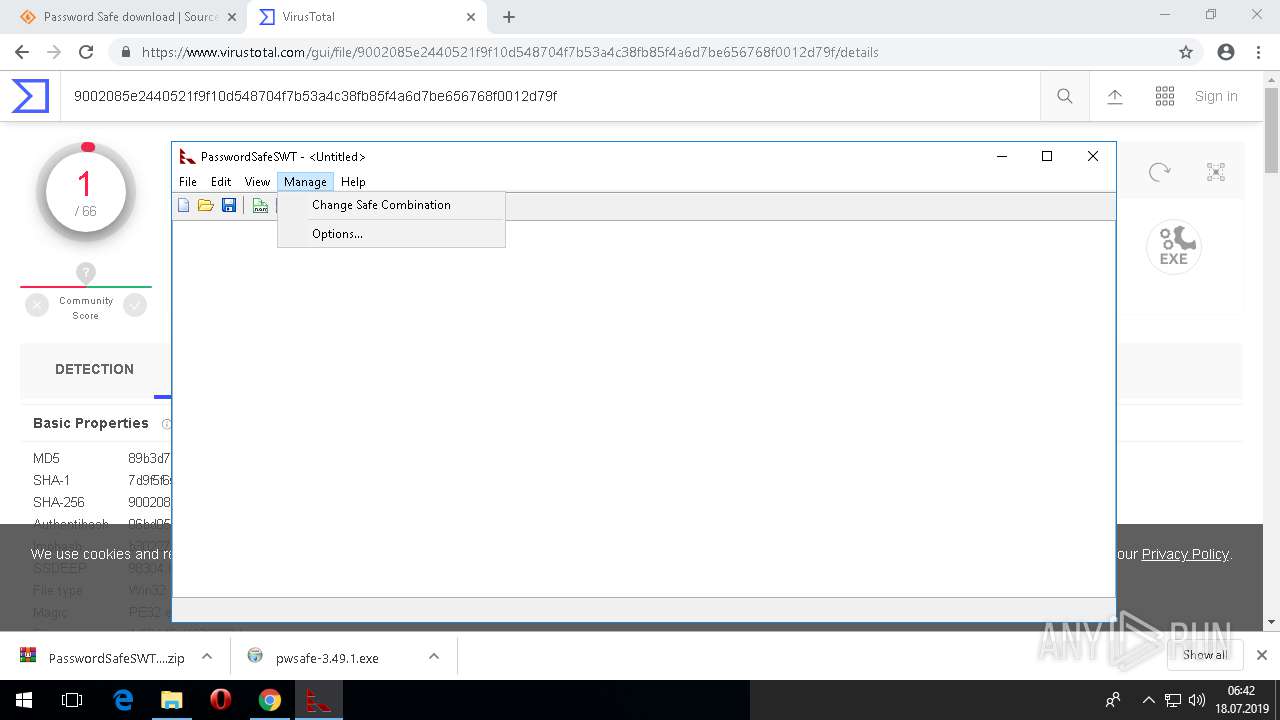
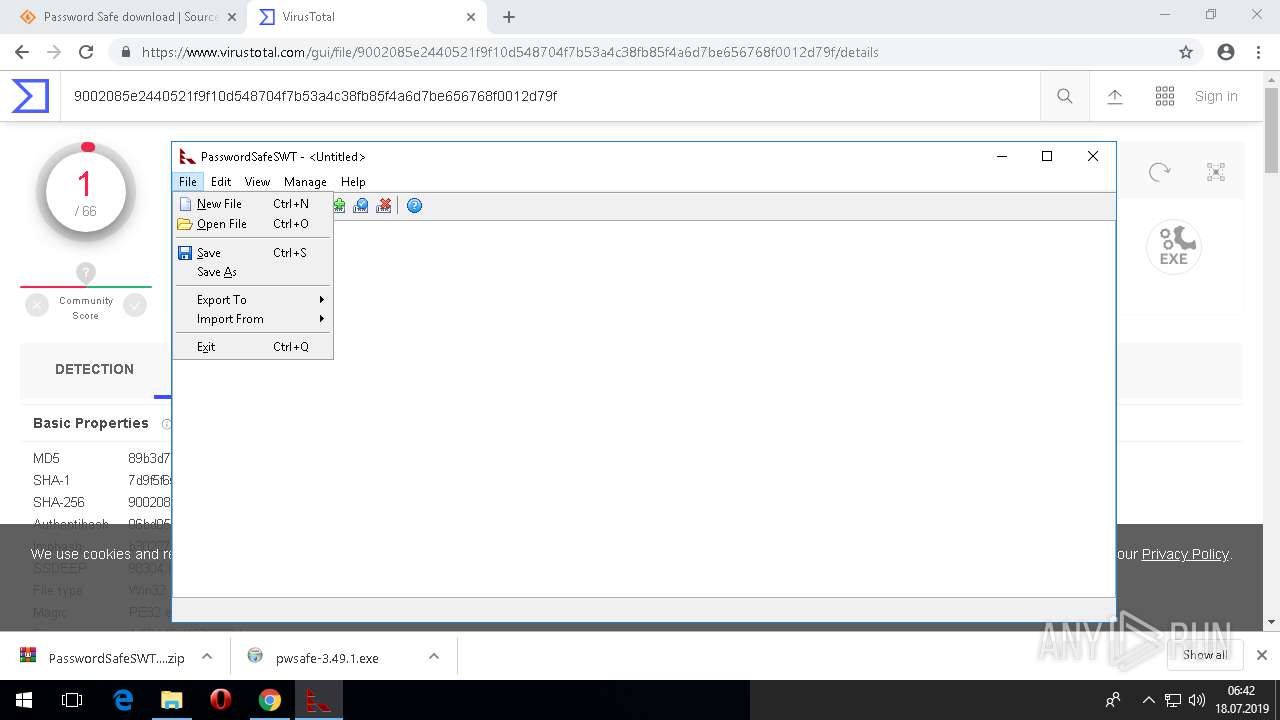
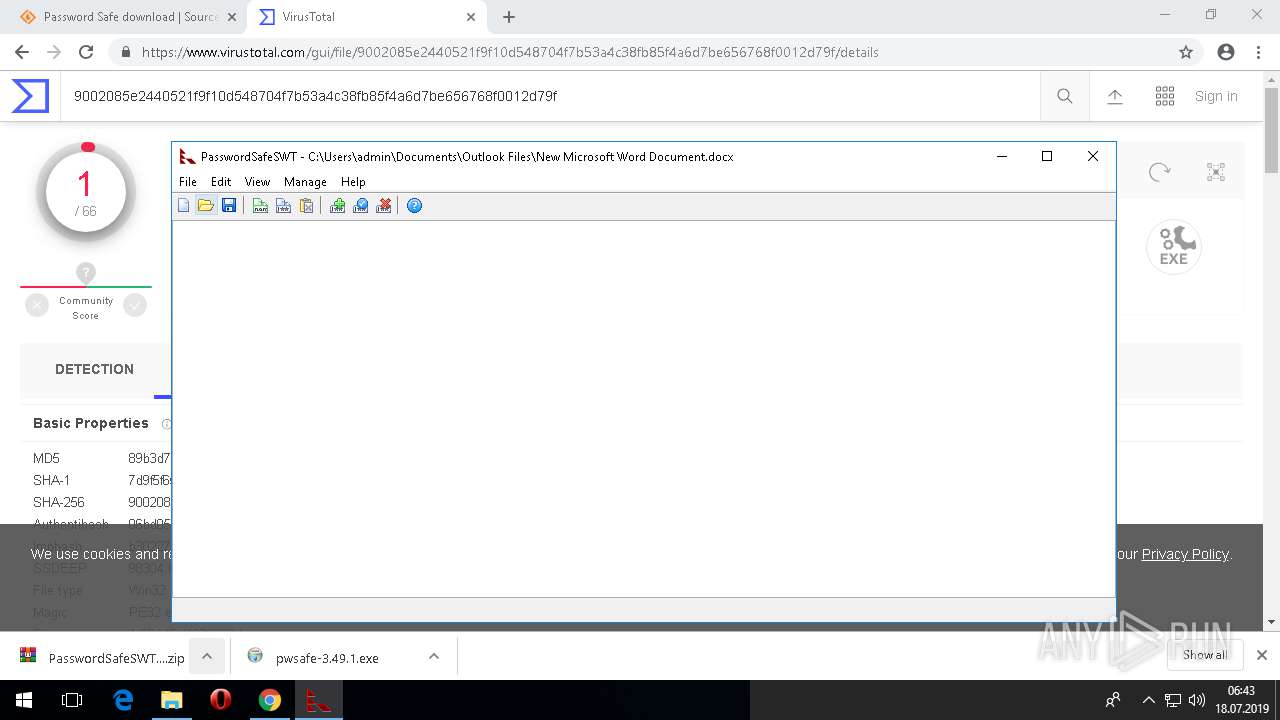
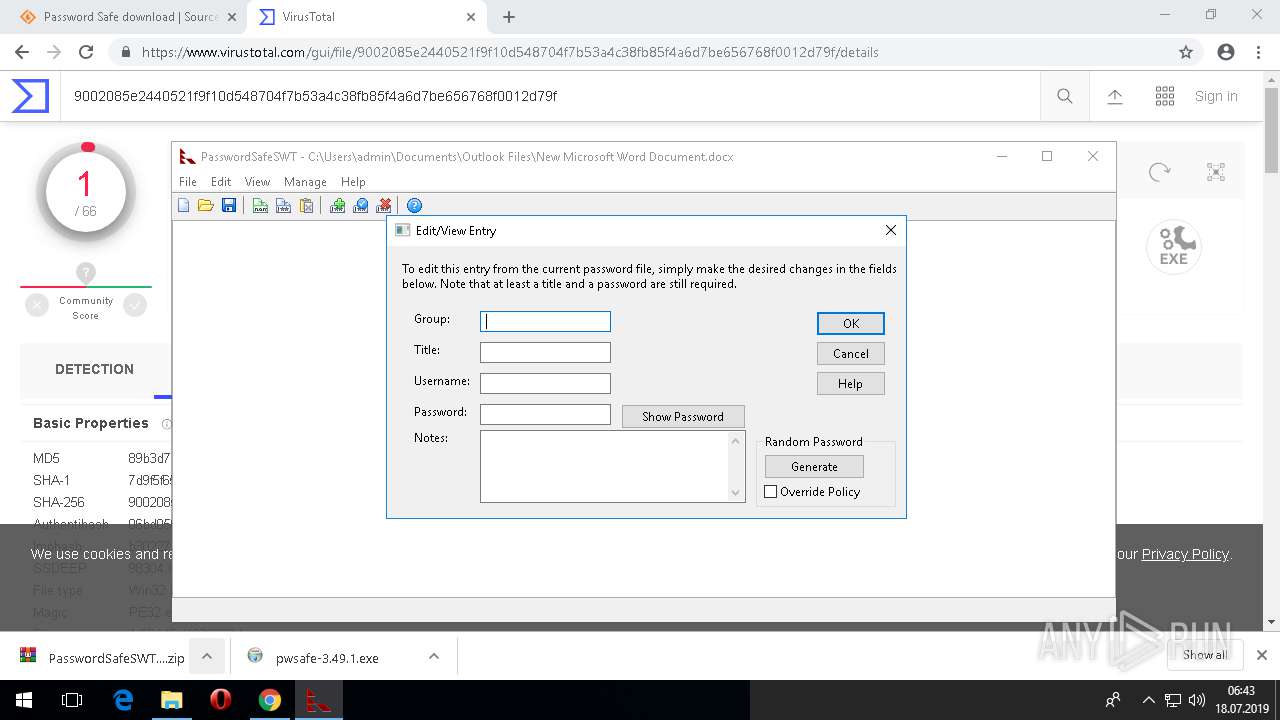
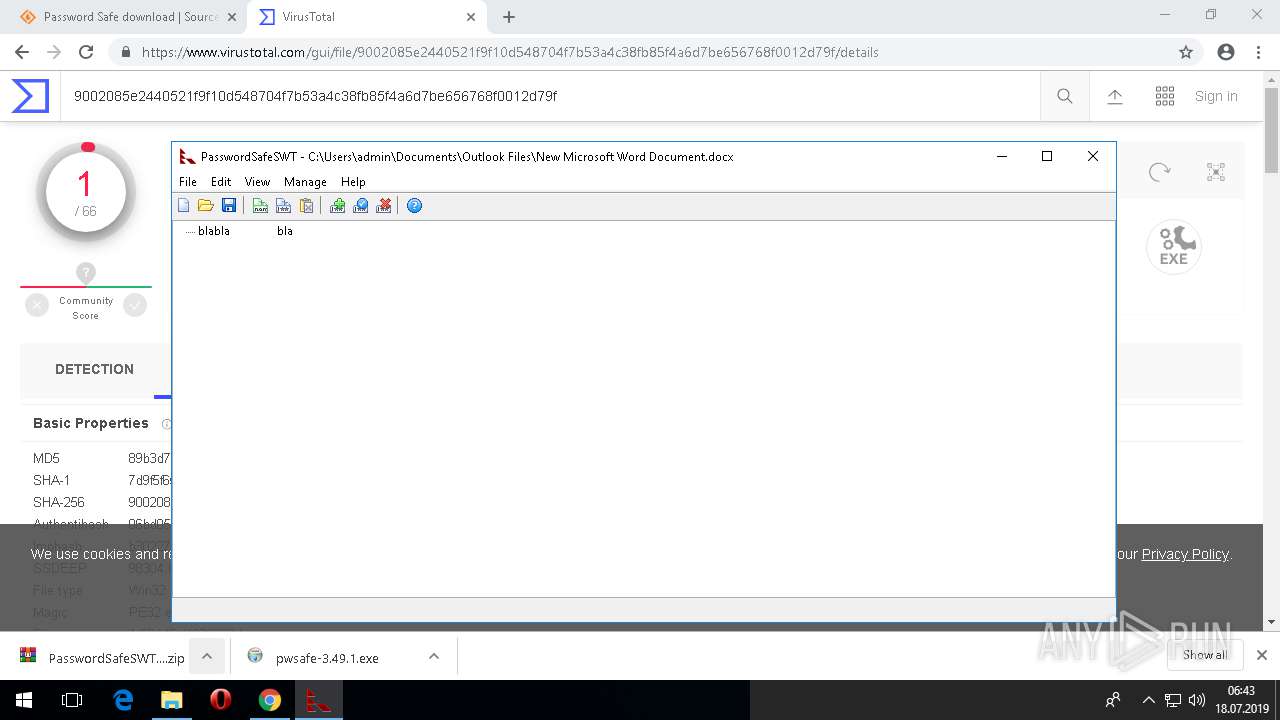
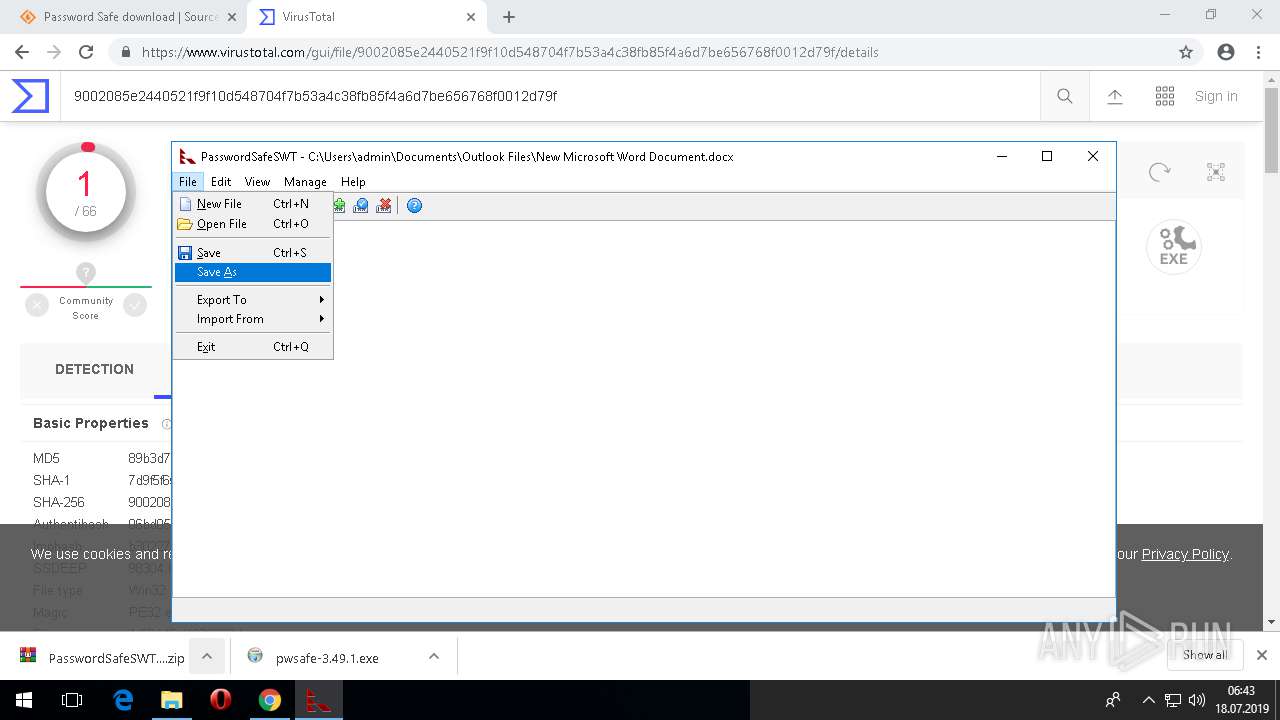
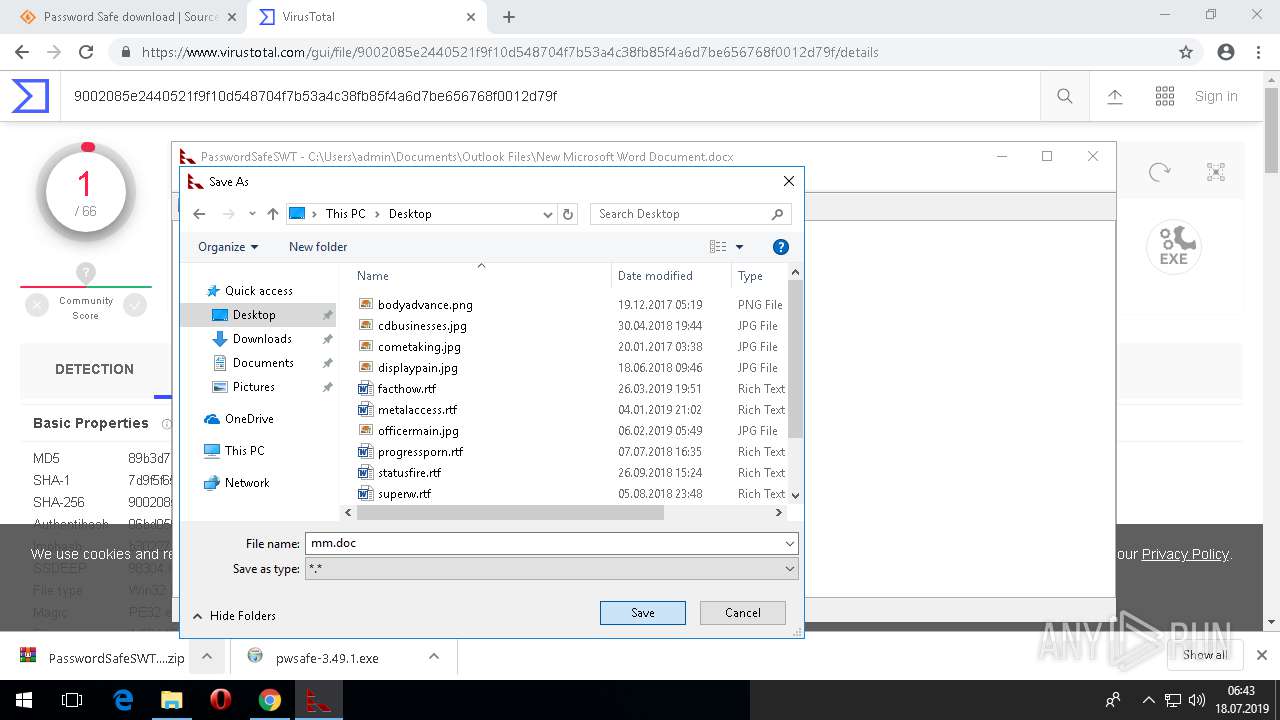
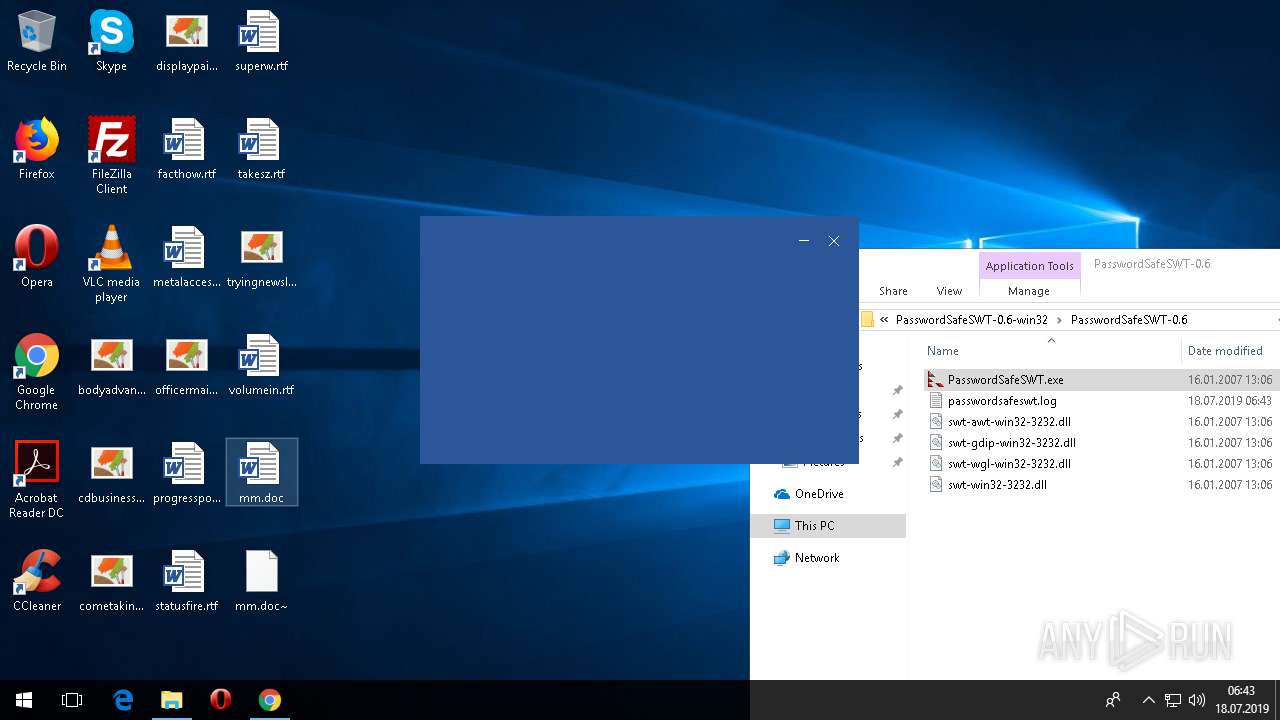
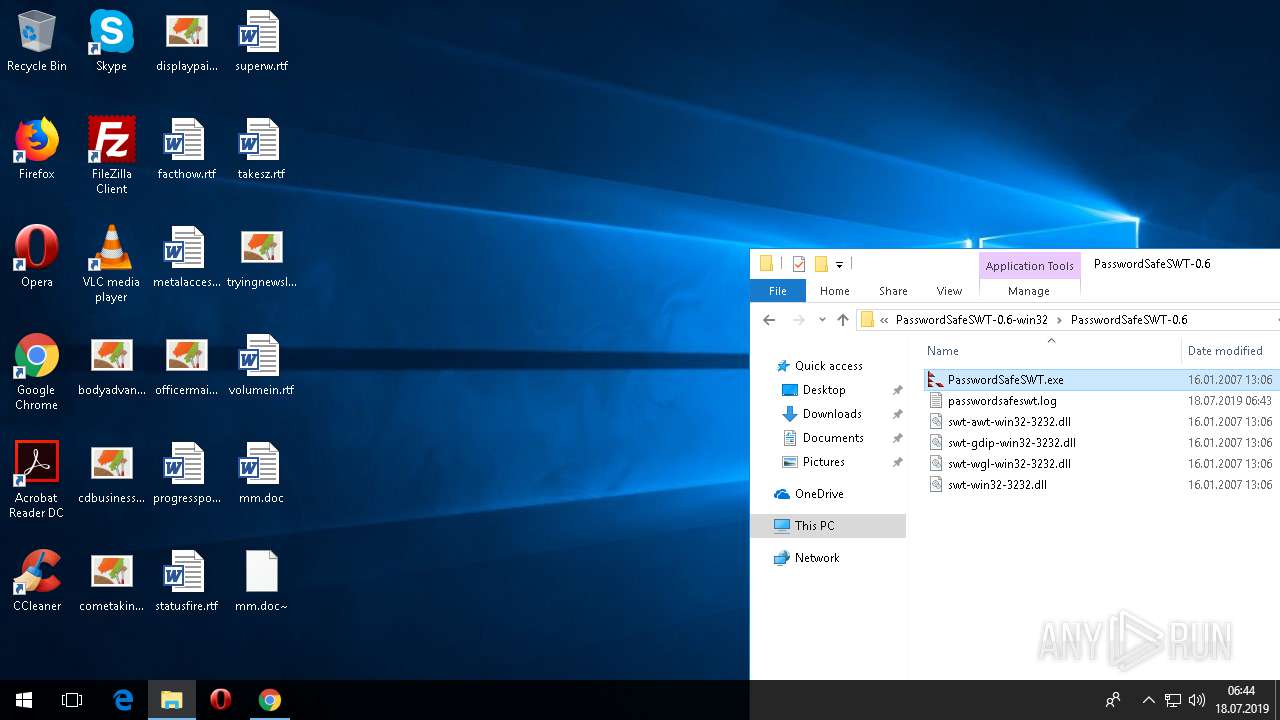
MALICIOUS
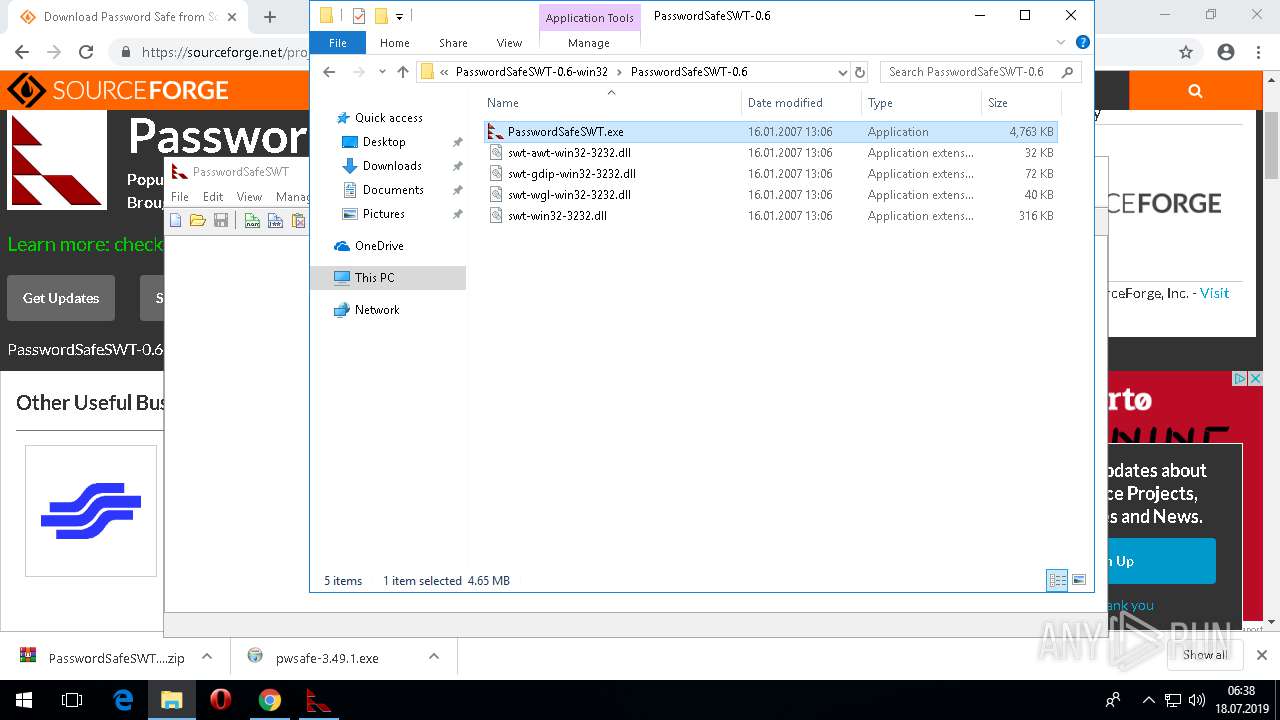
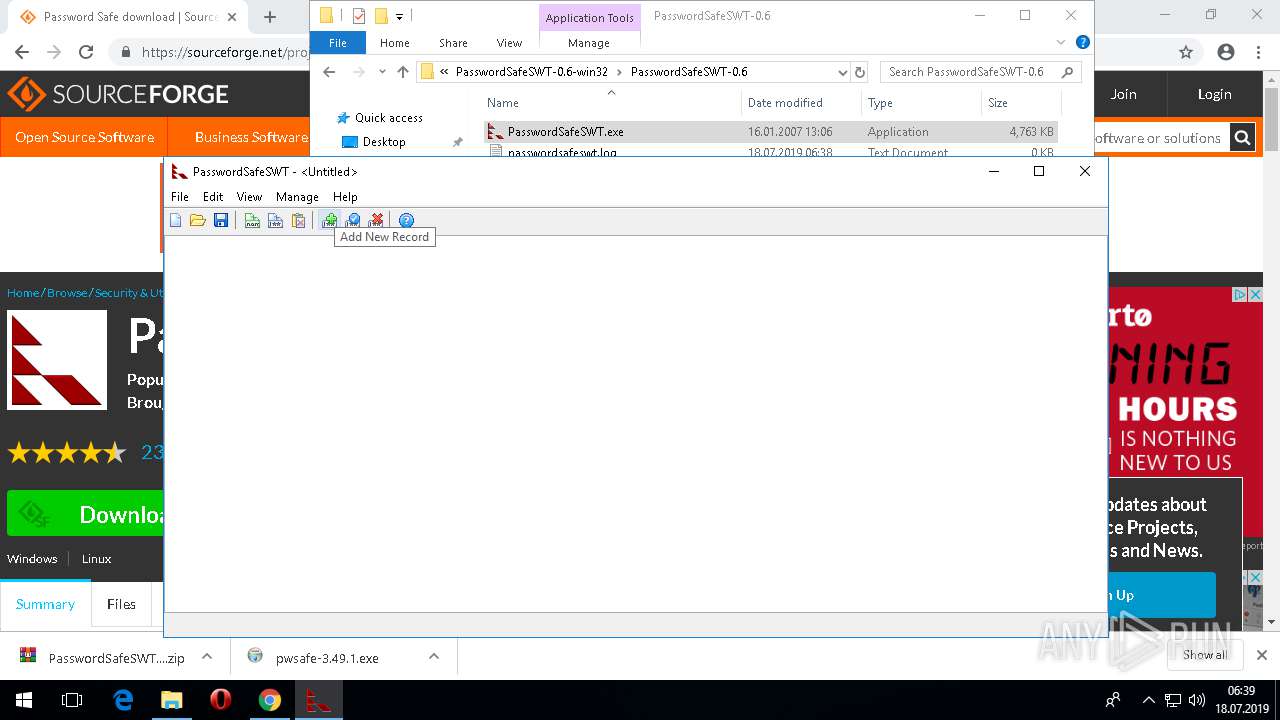
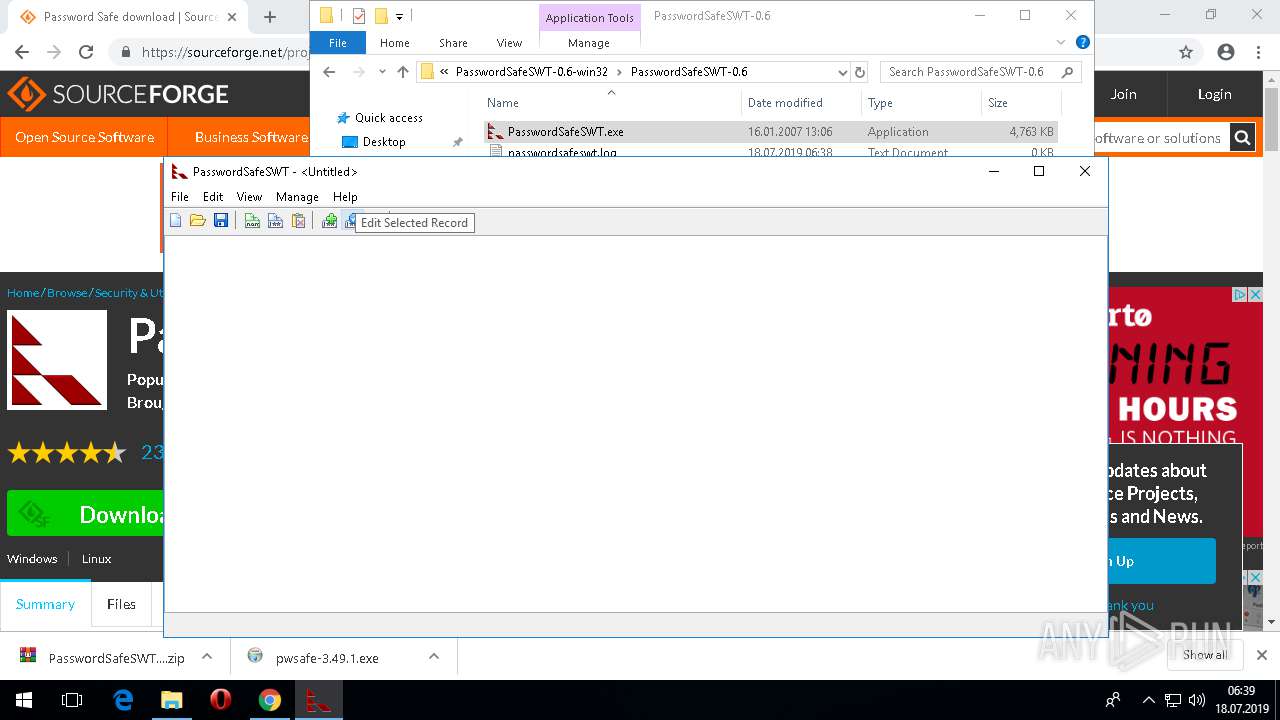
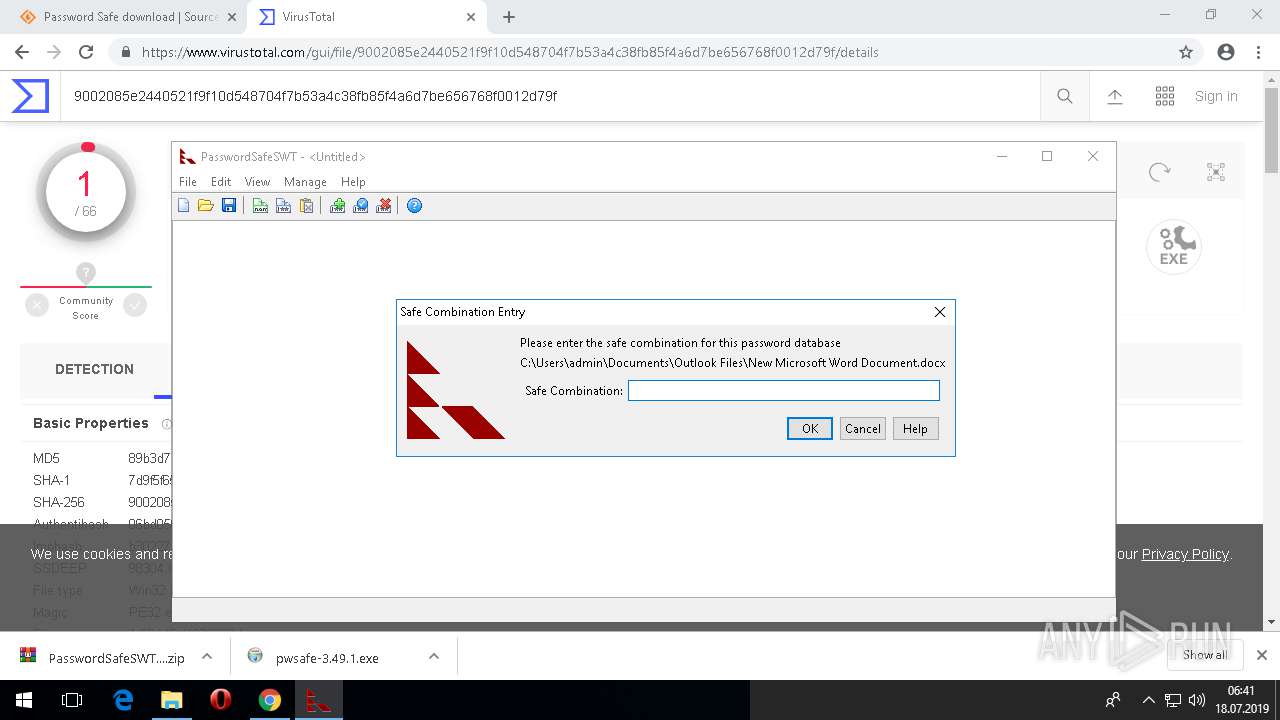
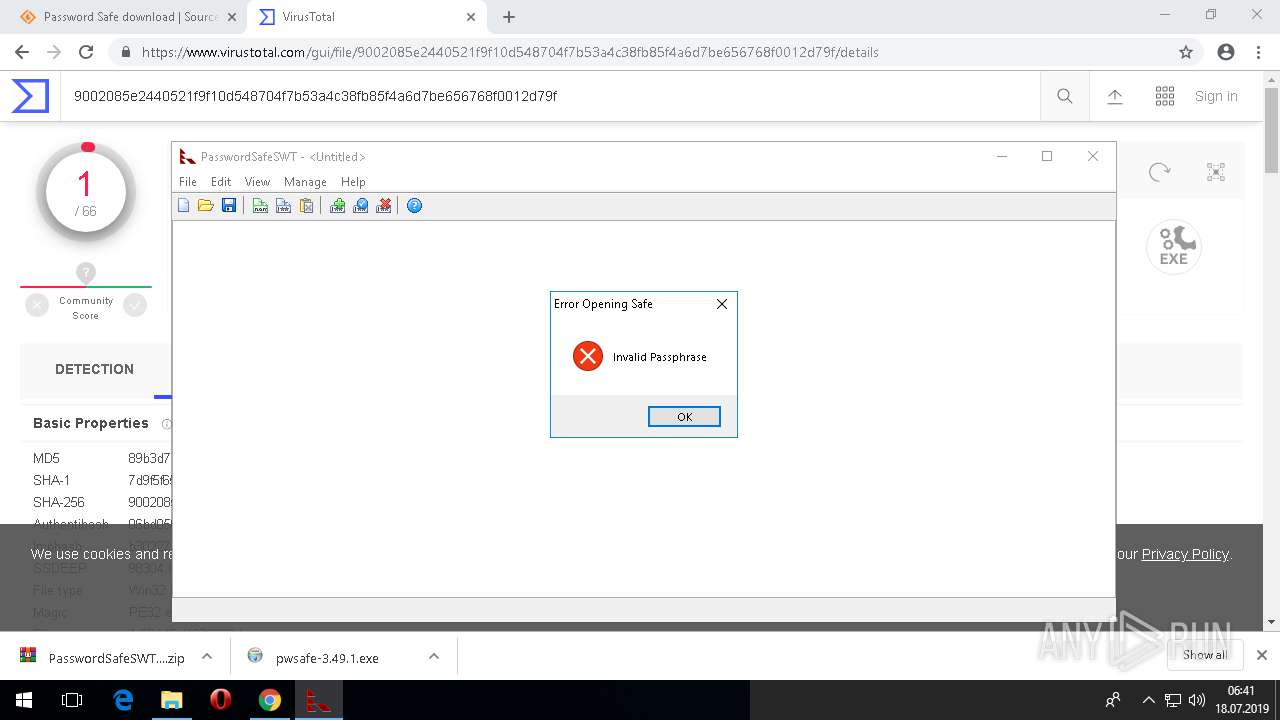
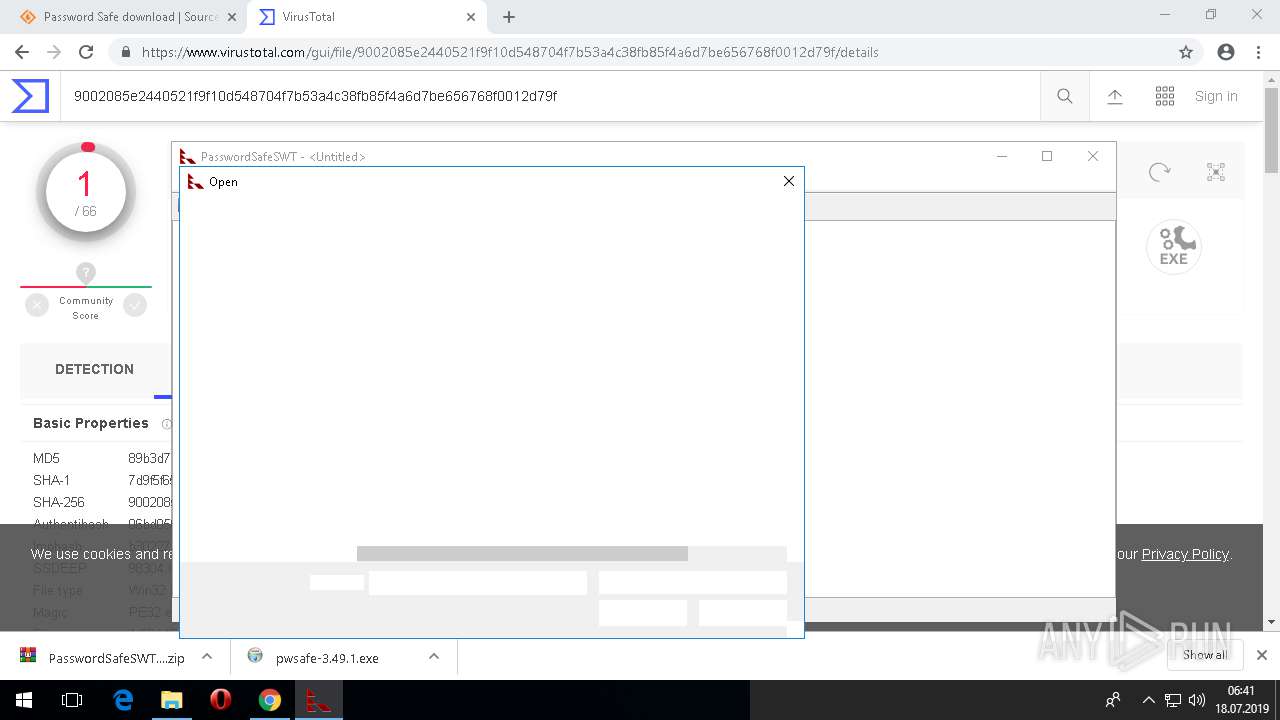
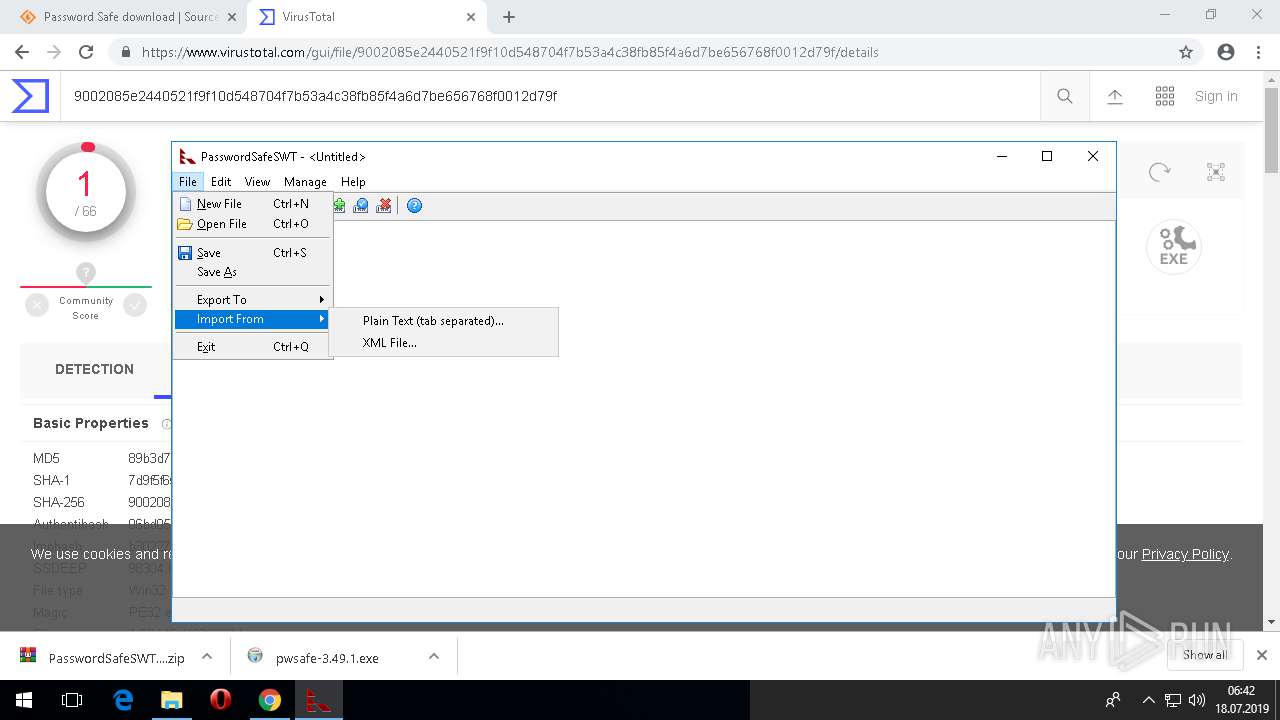
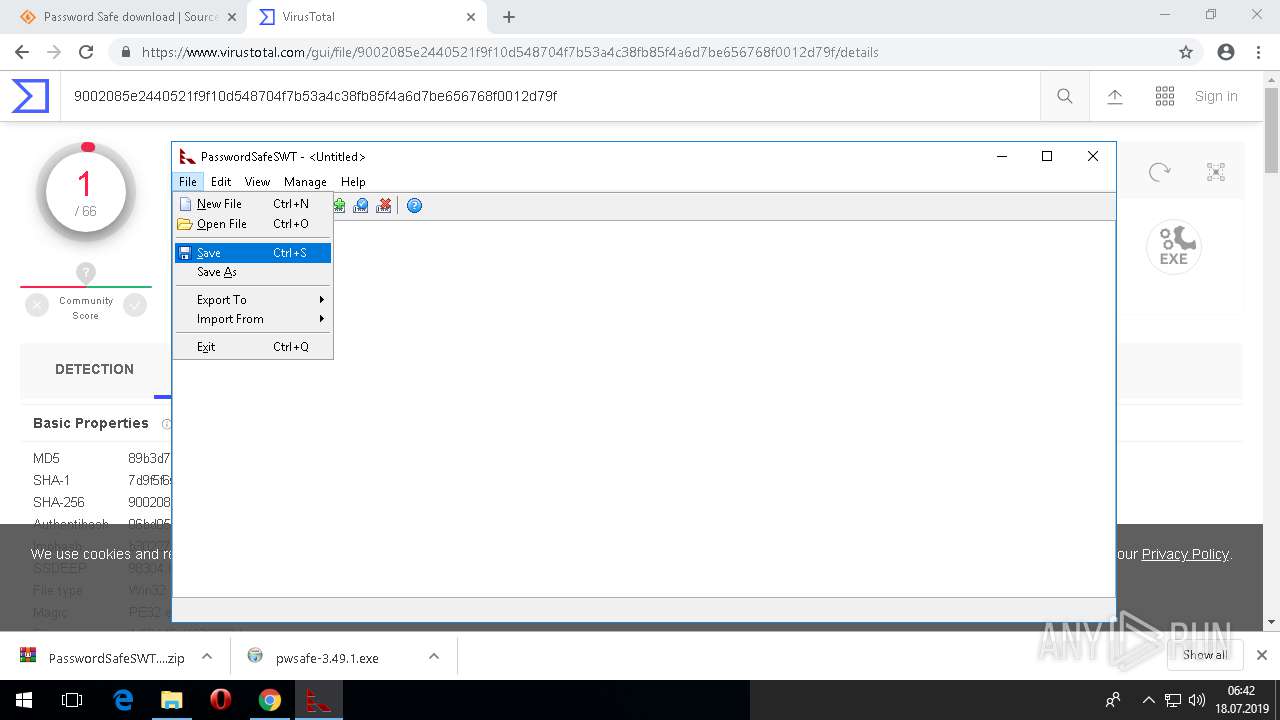
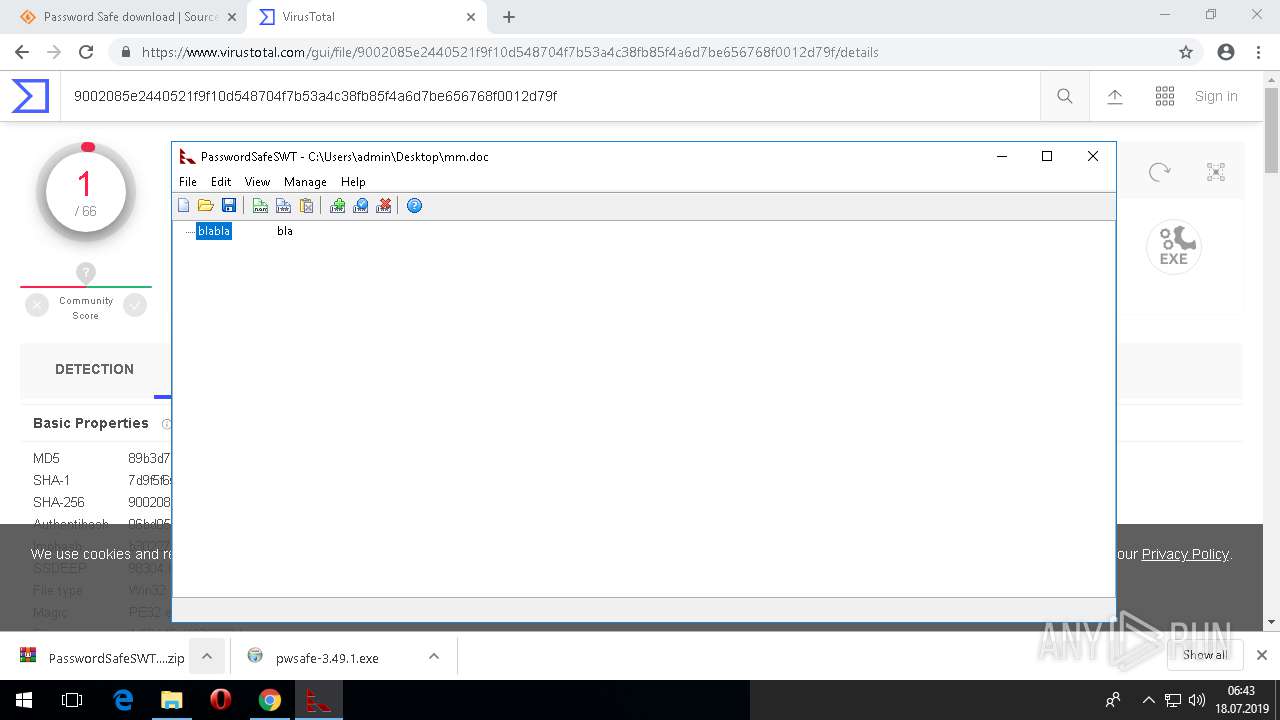
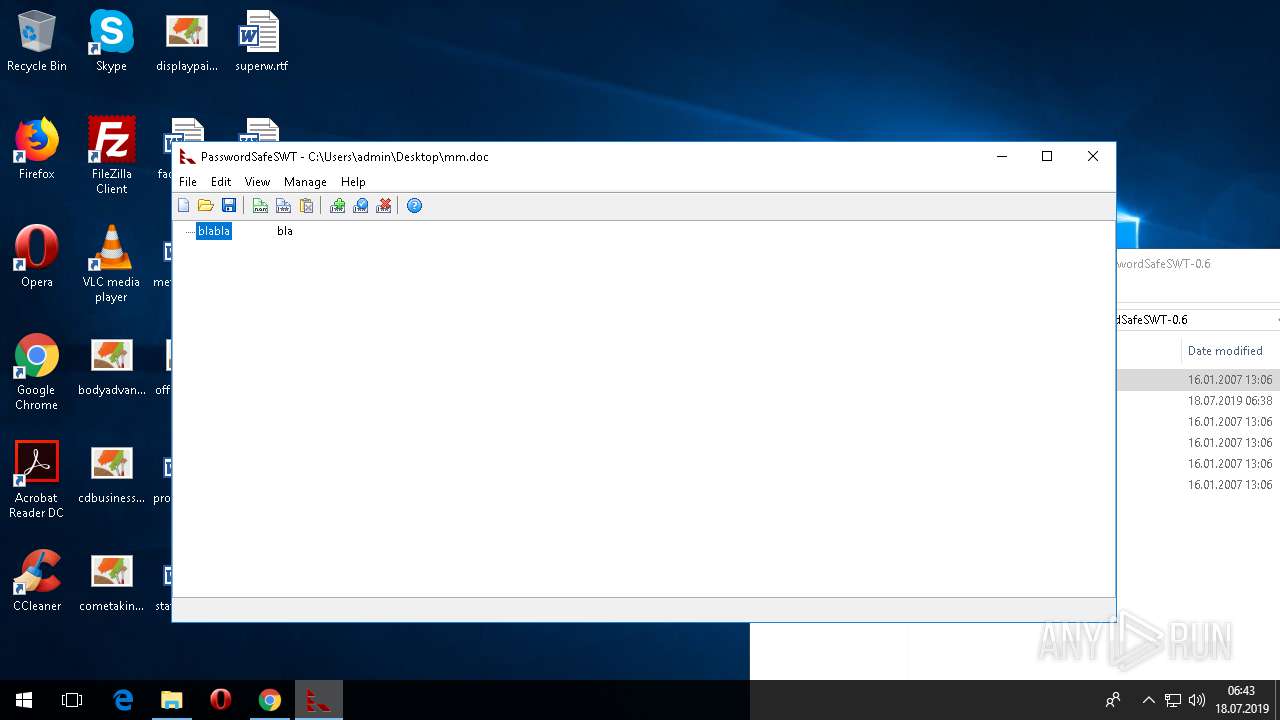
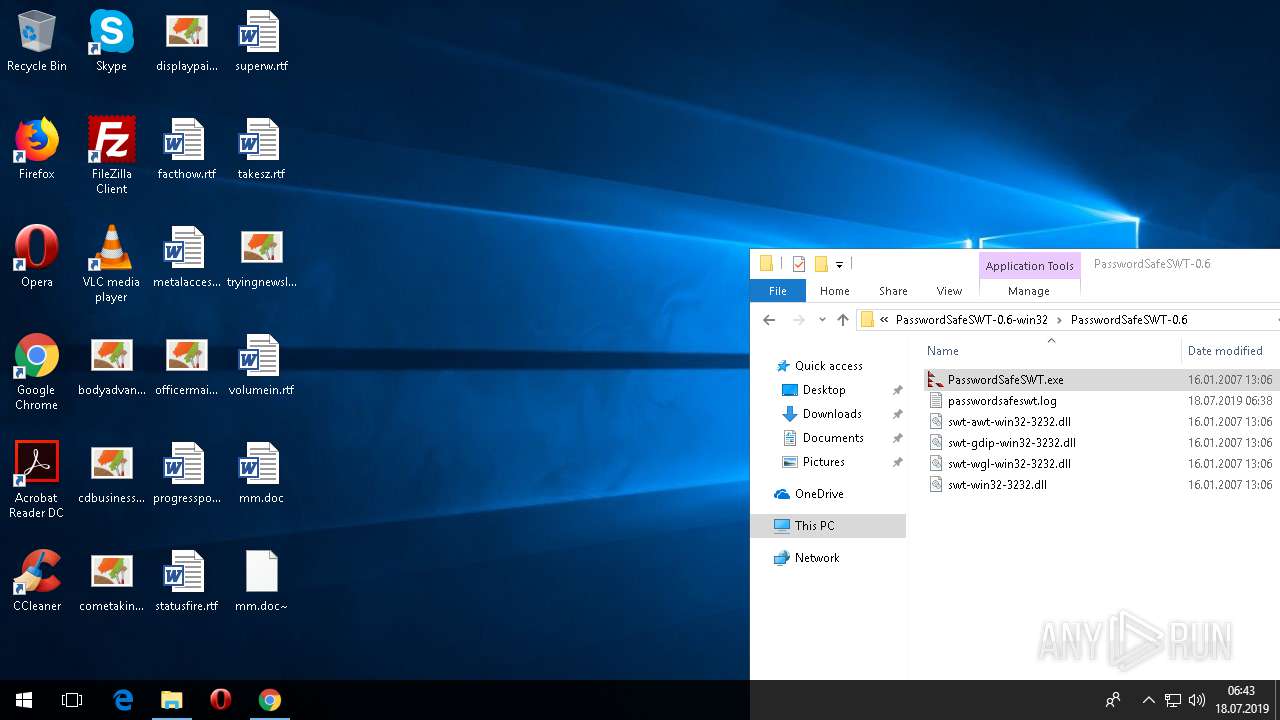
Application was dropped or rewritten from another process
- PasswordSafeSWT.exe (PID: 2348)
Loads dropped or rewritten executable
- PasswordSafeSWT.exe (PID: 2348)
Modifies files in Chrome extension folder
- PasswordSafeSWT.exe (PID: 2348)
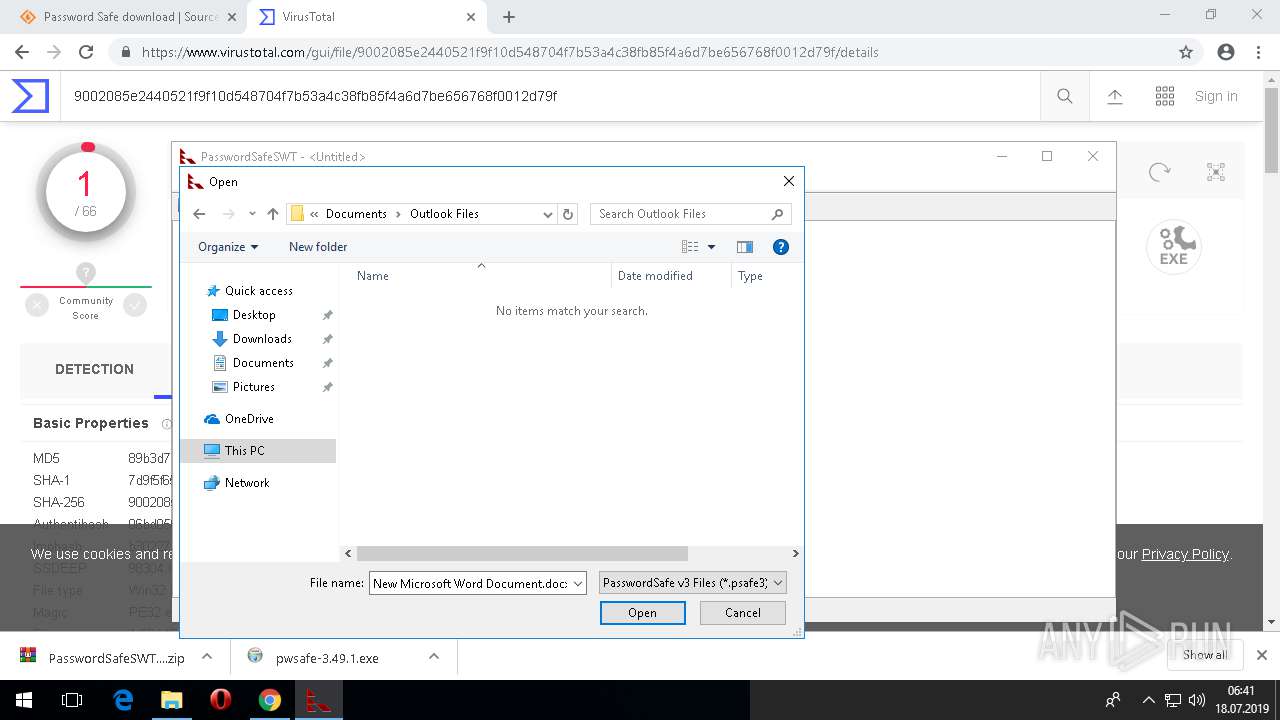
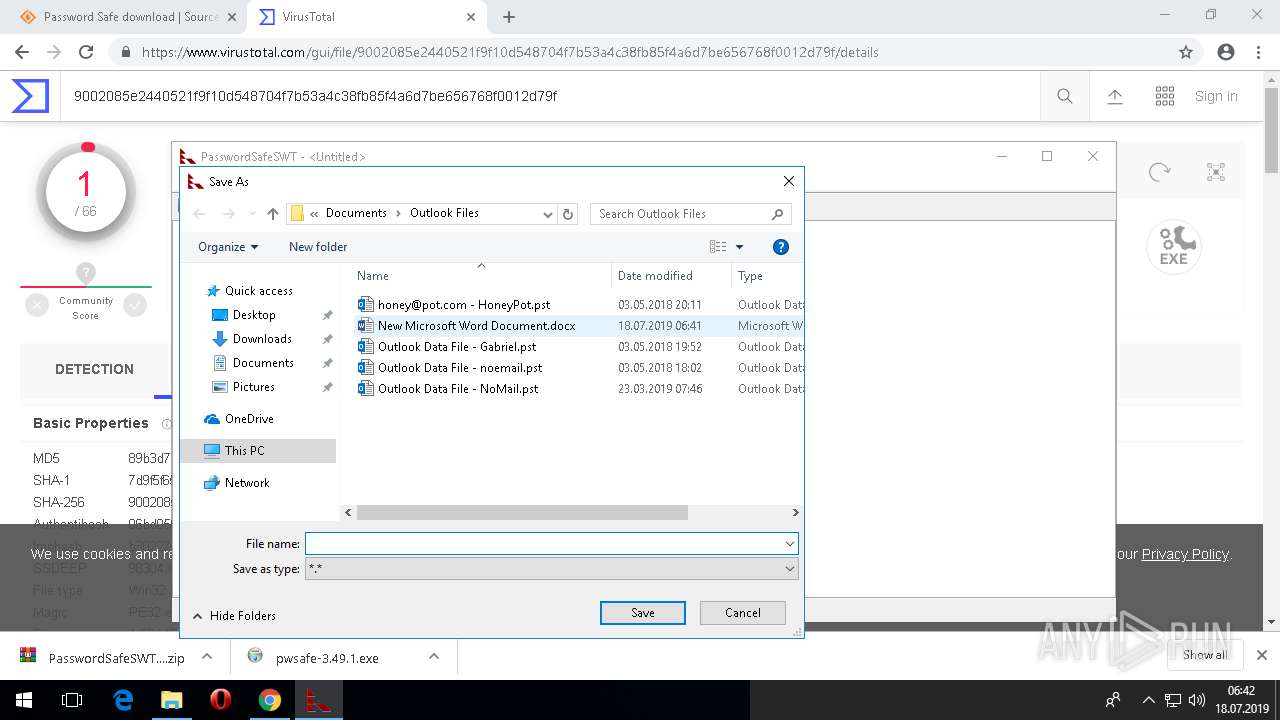
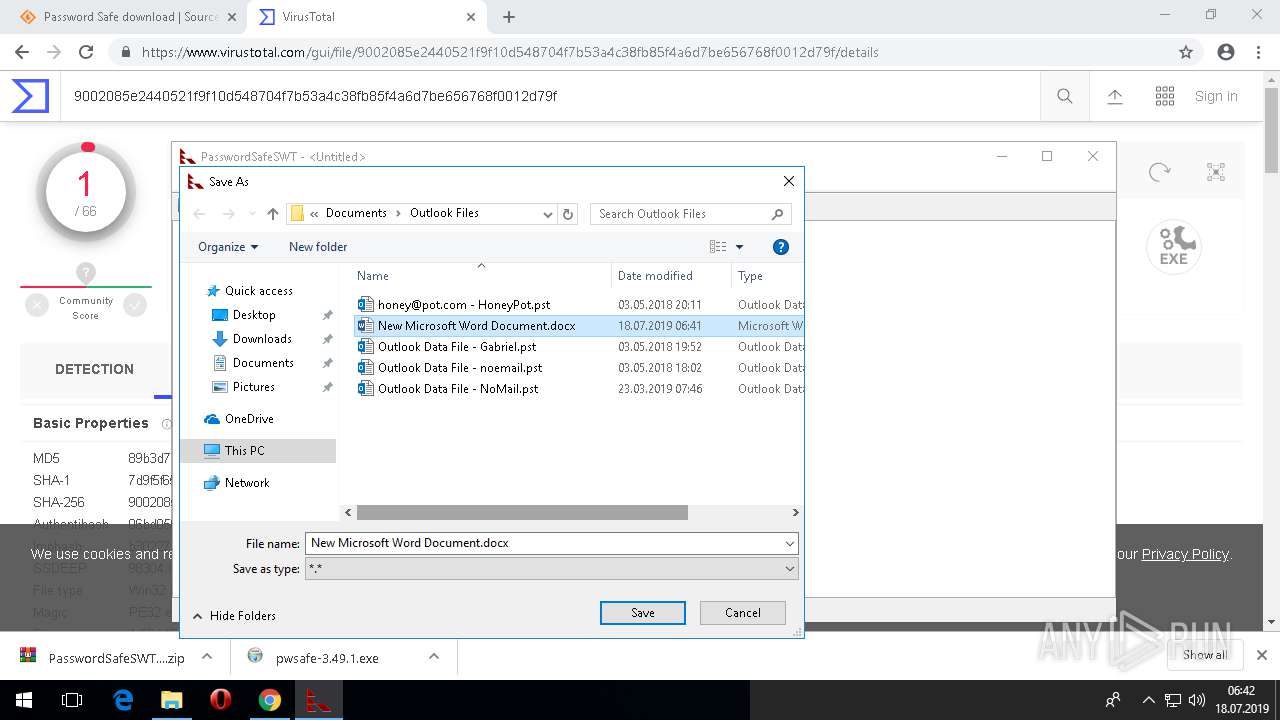
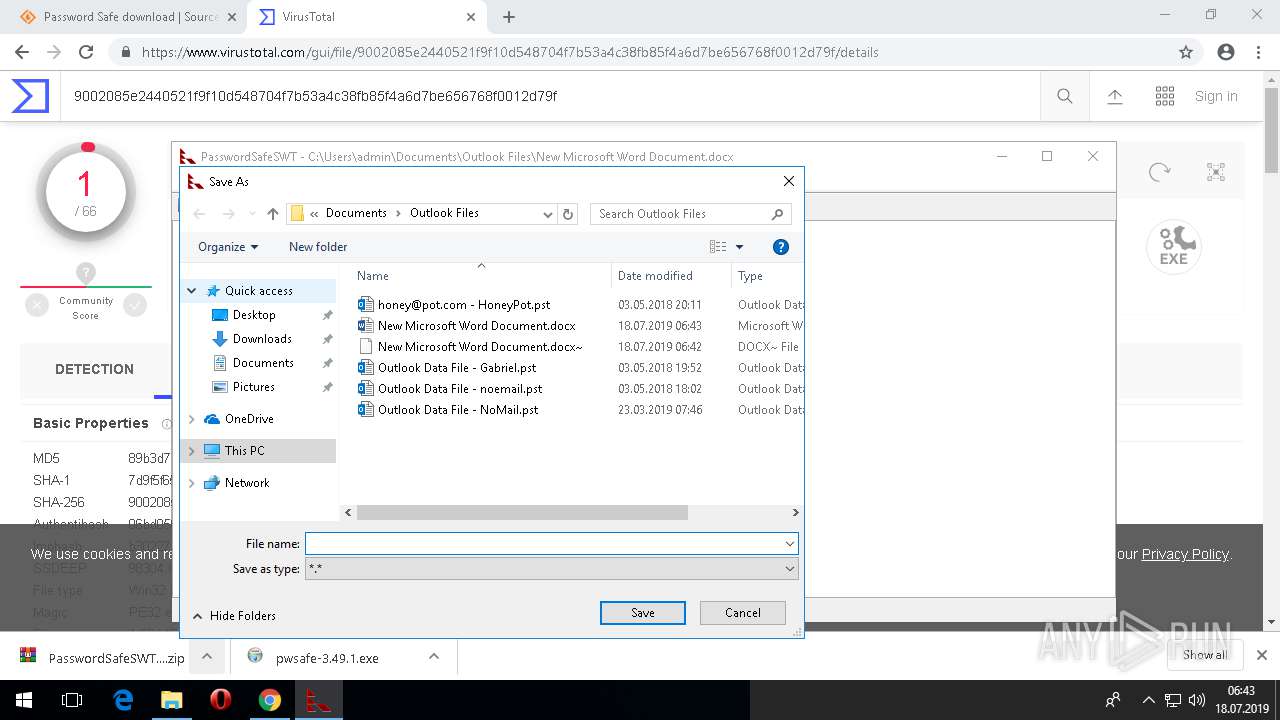
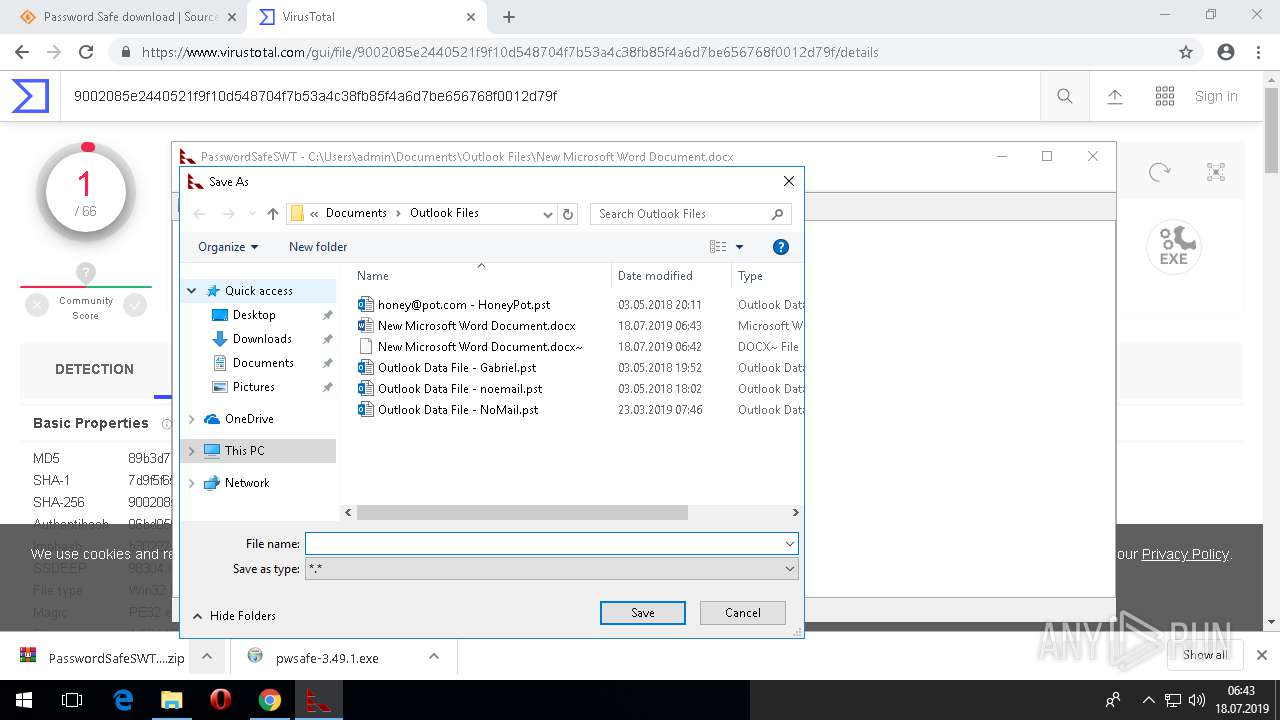
Scans artifacts that could help determine the target
- WINWORD.EXE (PID: 4716)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2460)
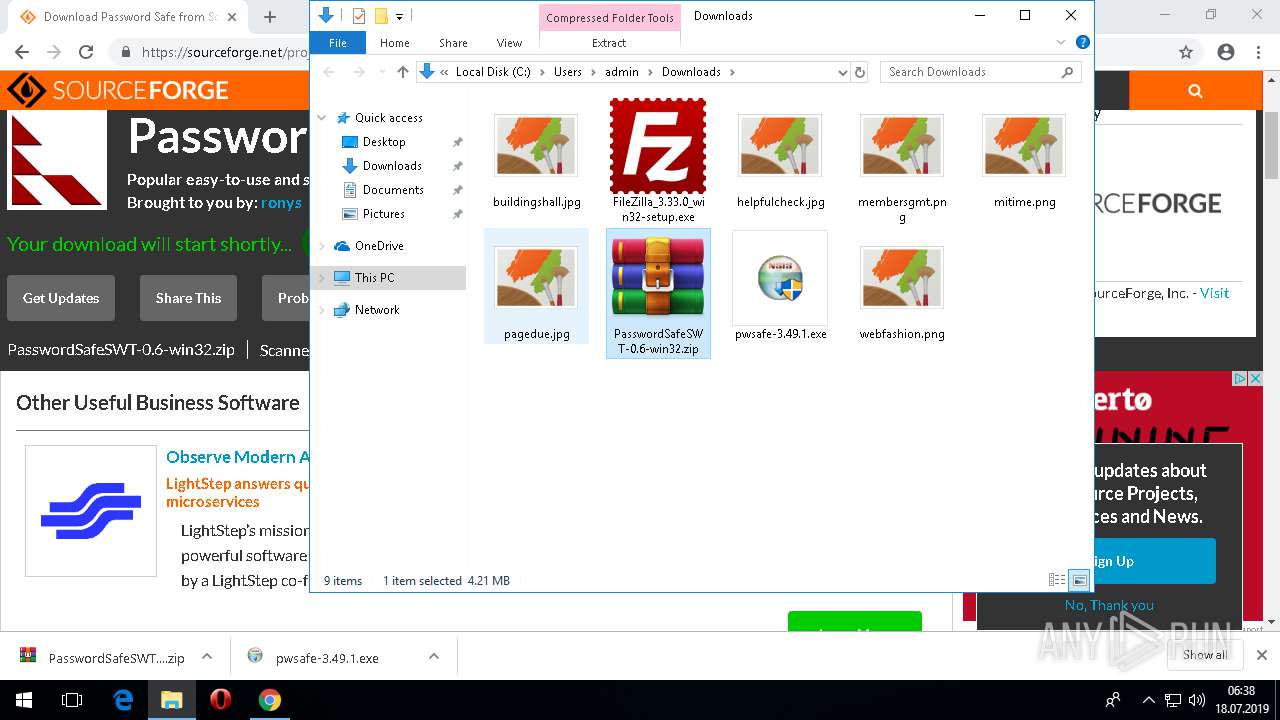
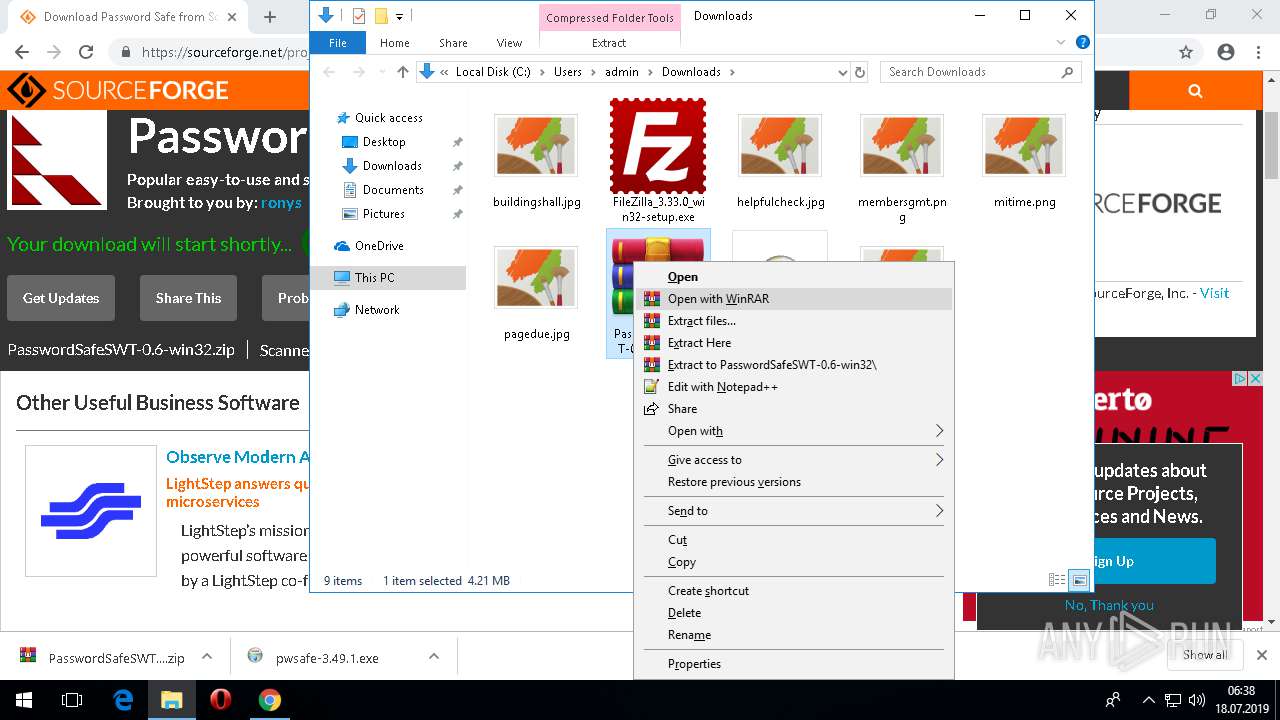
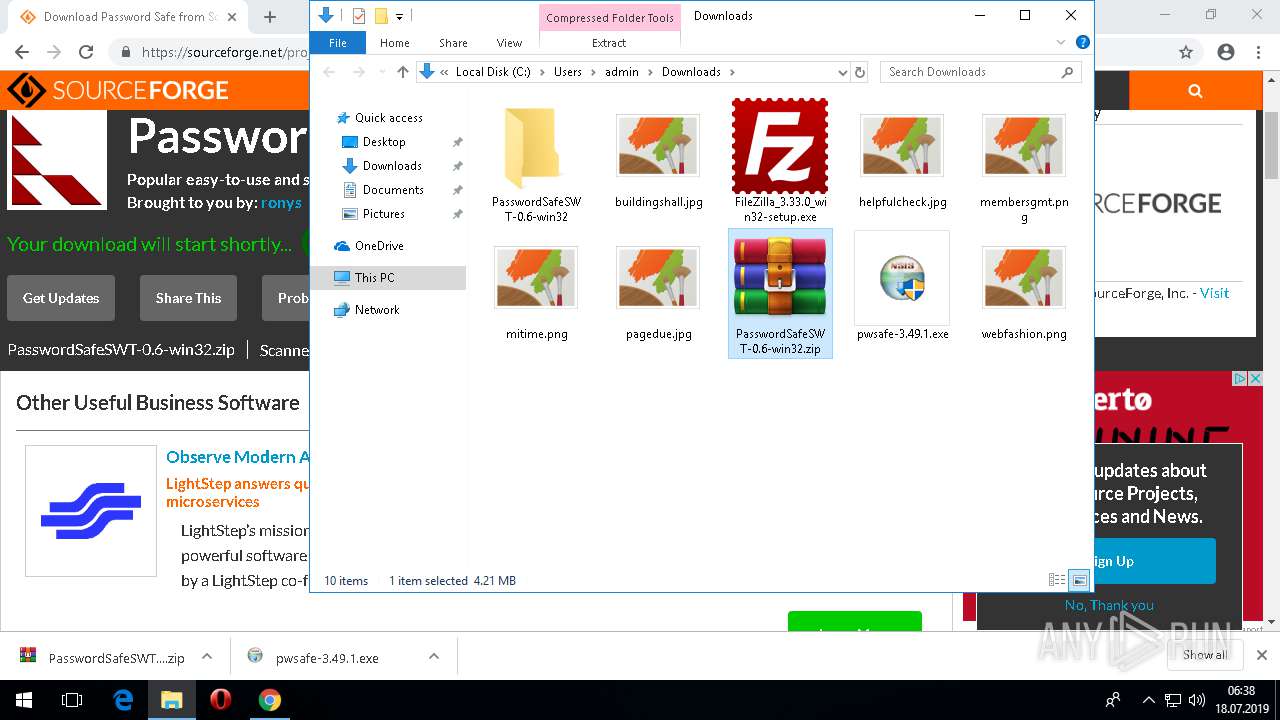
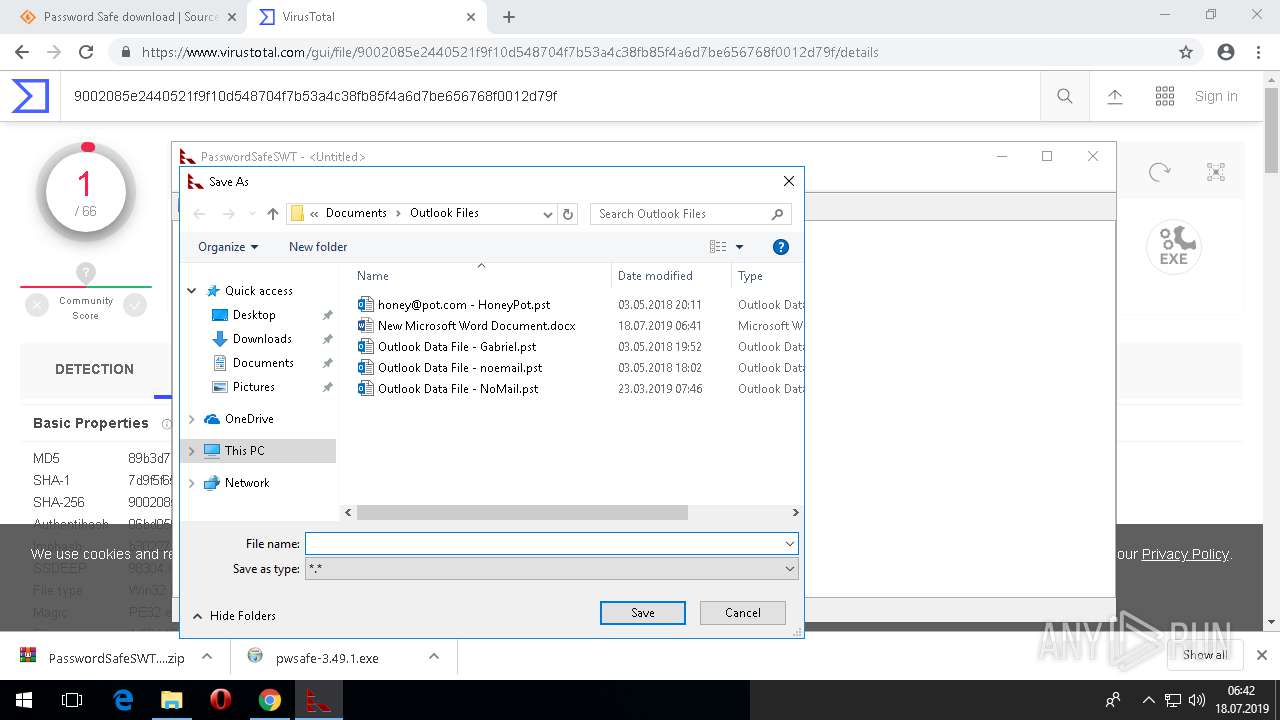
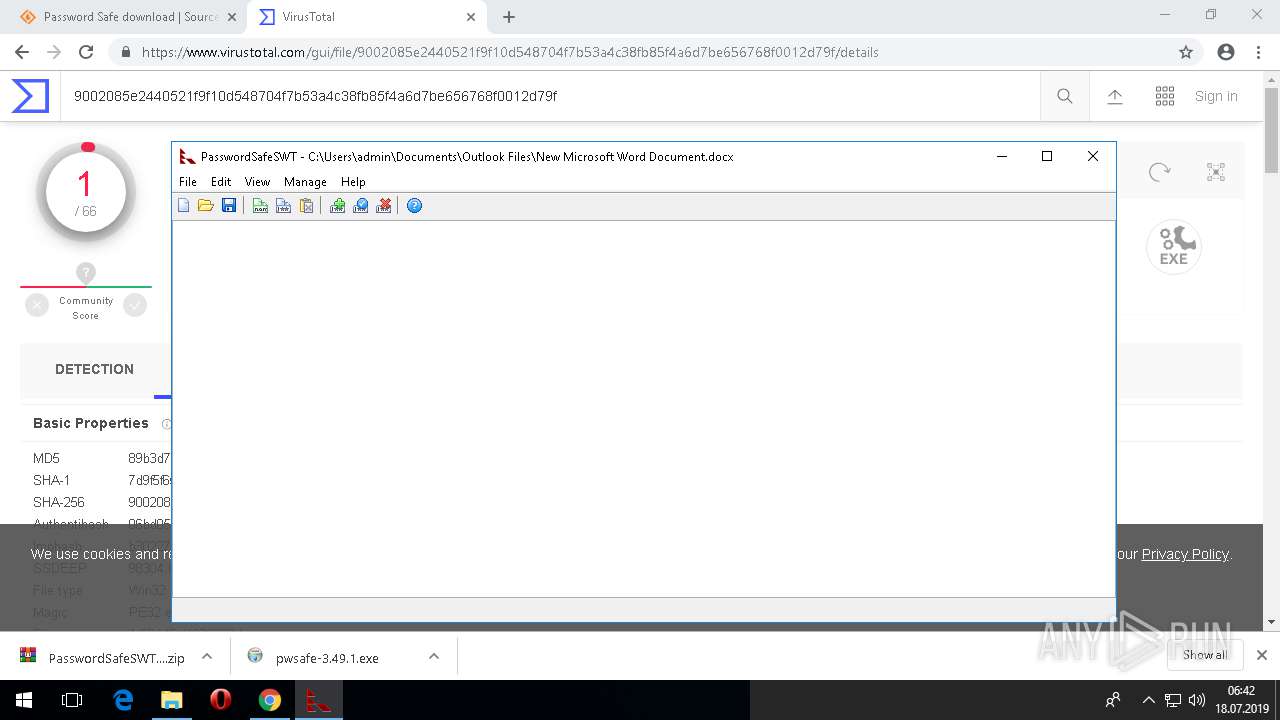
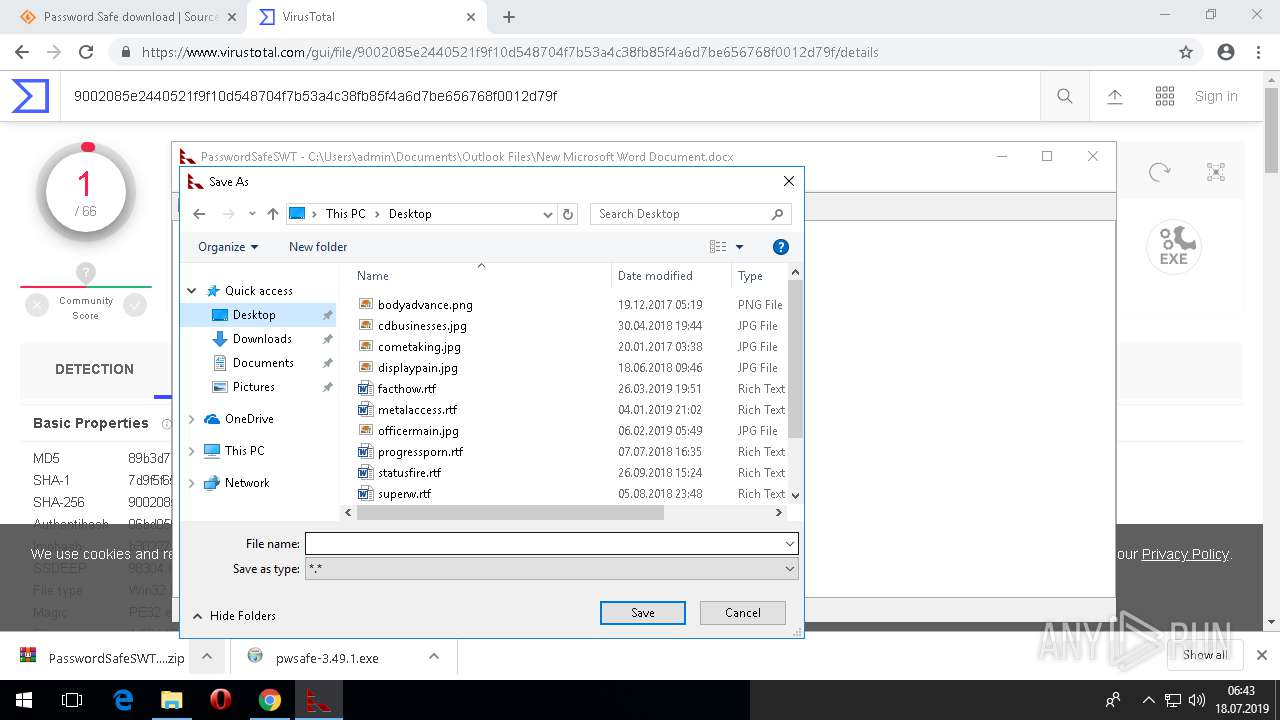
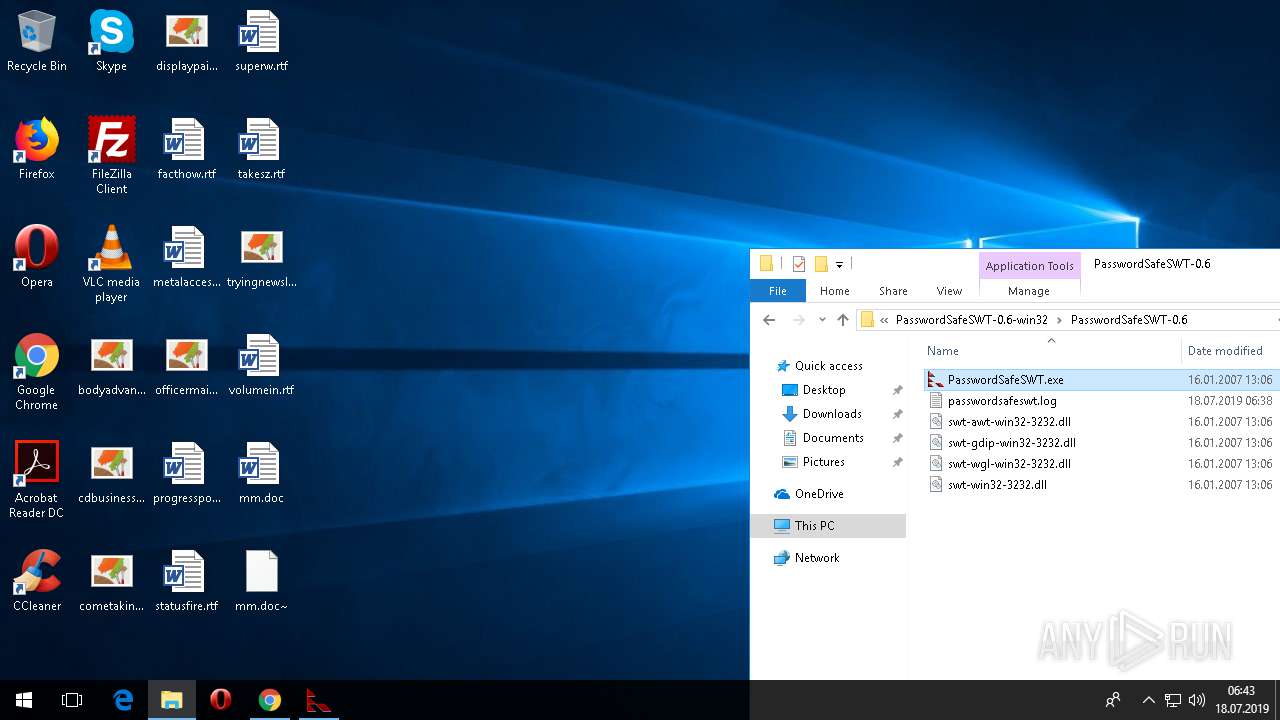
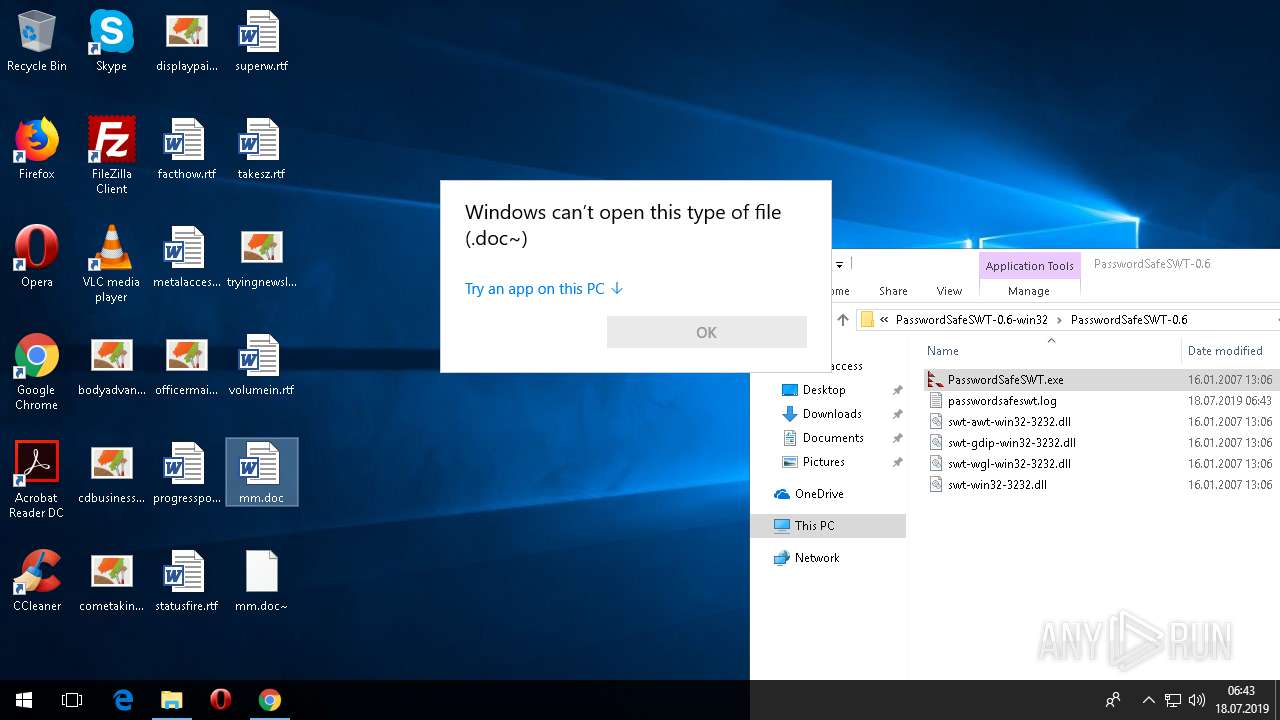
Creates files in the user directory
- WinRAR.exe (PID: 4076)
- PasswordSafeSWT.exe (PID: 2348)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4076)
- chrome.exe (PID: 2460)
Executed via COM
- rundll32.exe (PID: 5928)
- OpenWith.exe (PID: 2240)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2460)
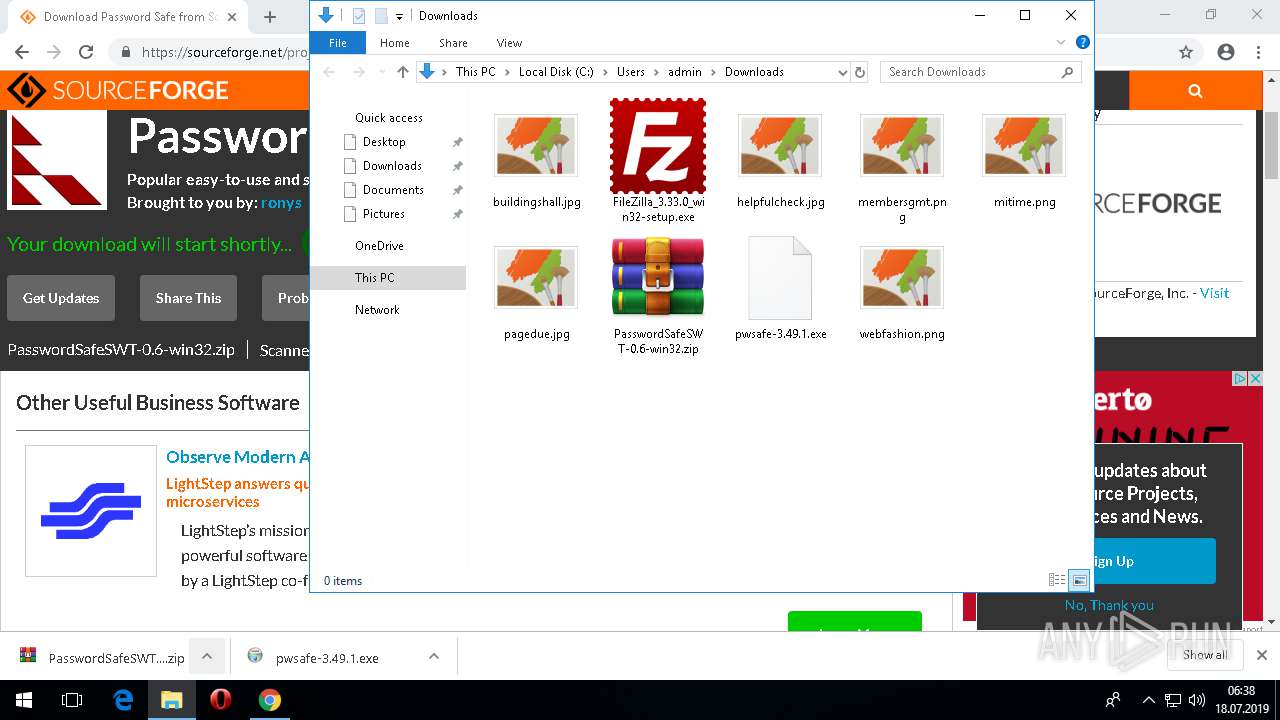
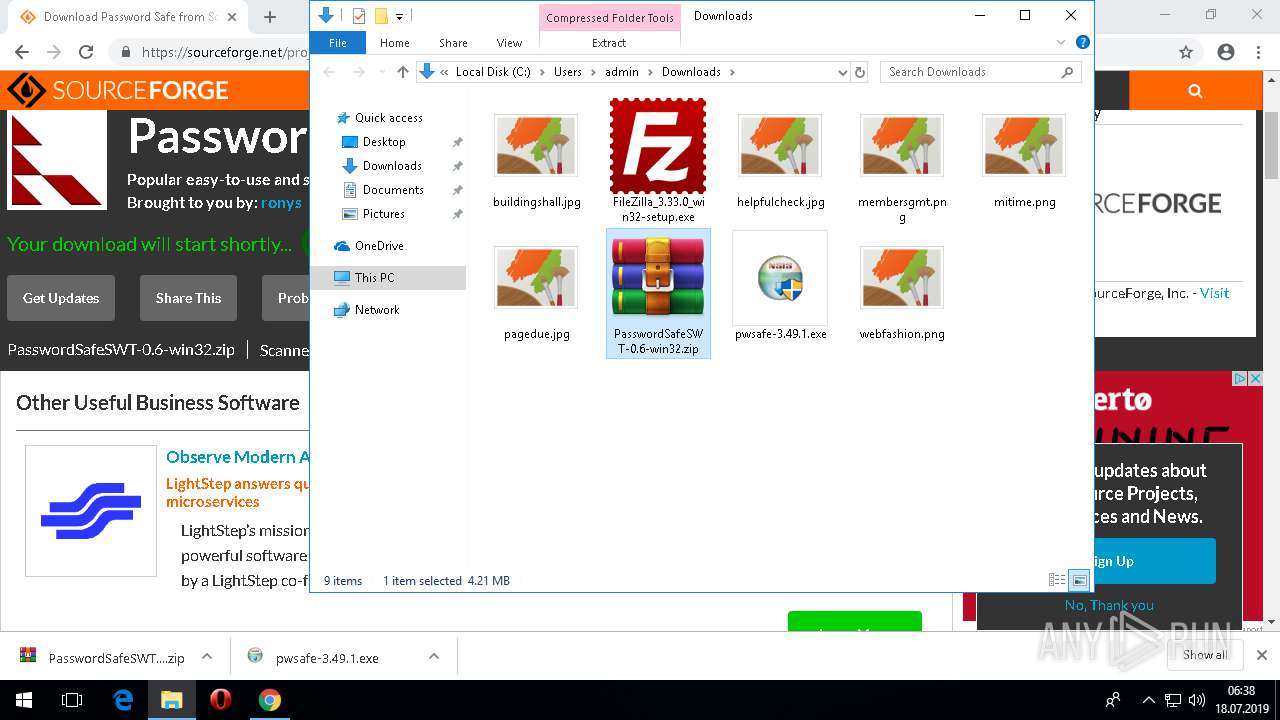
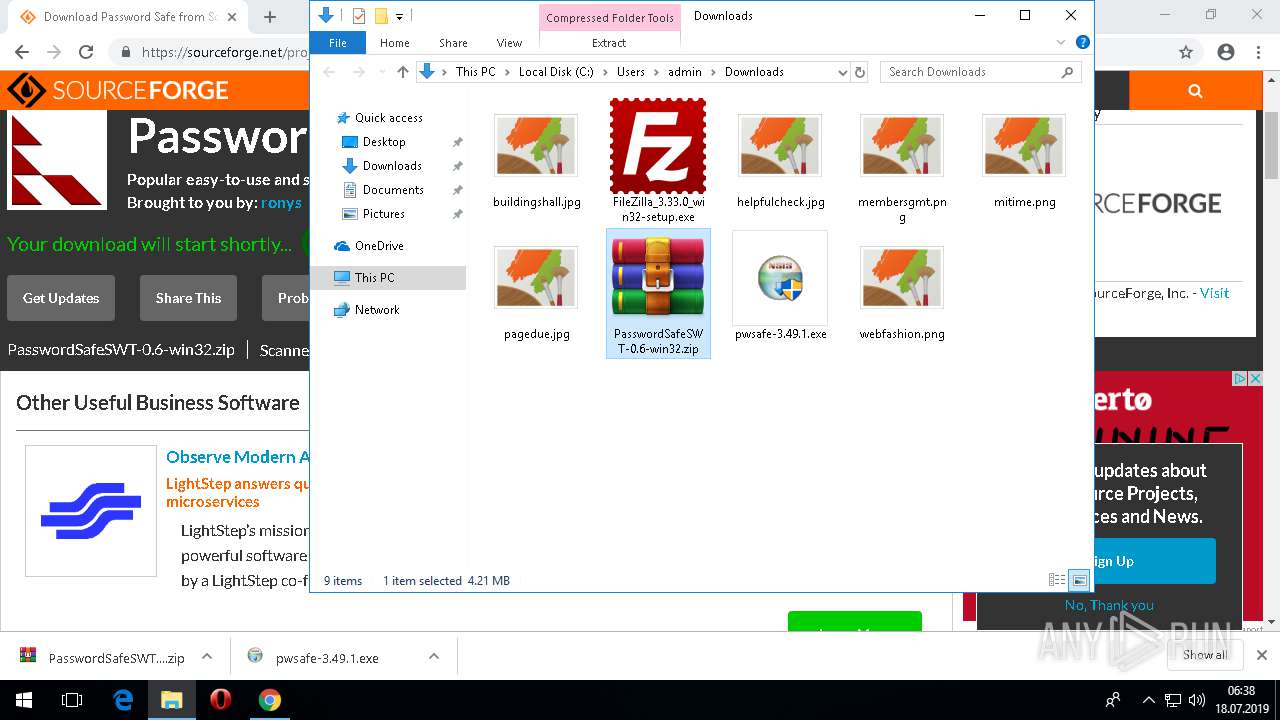
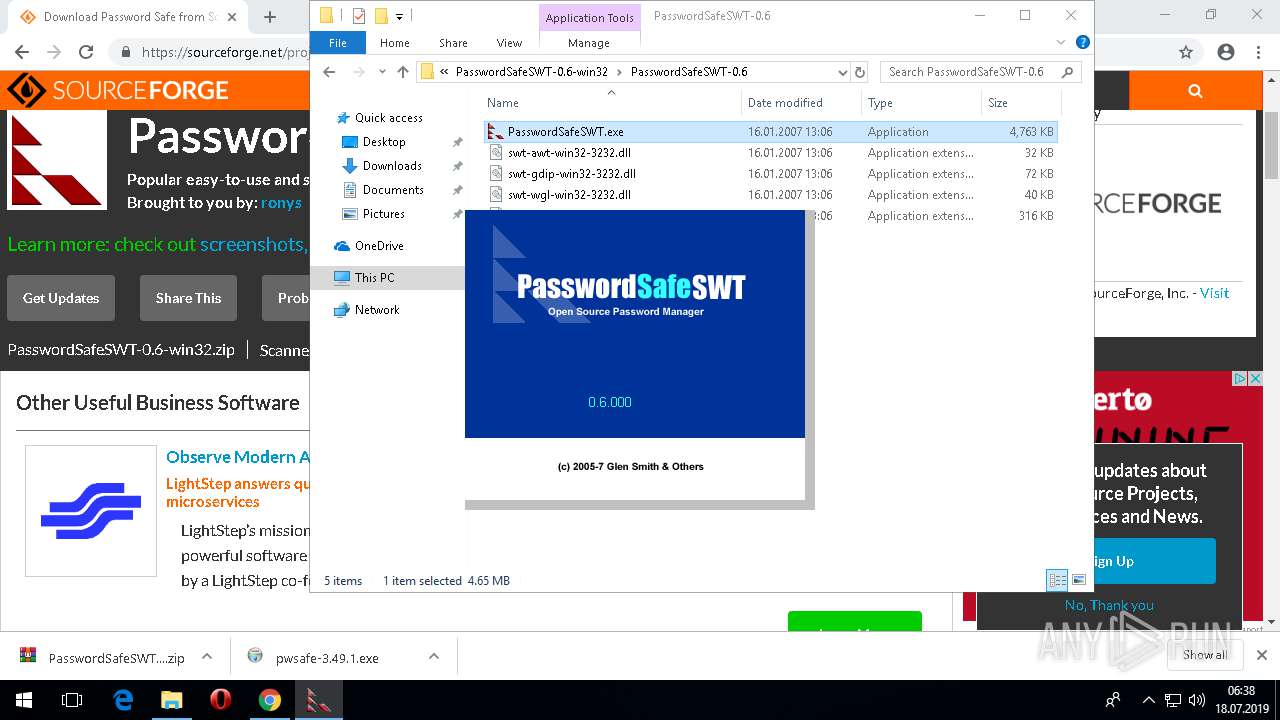
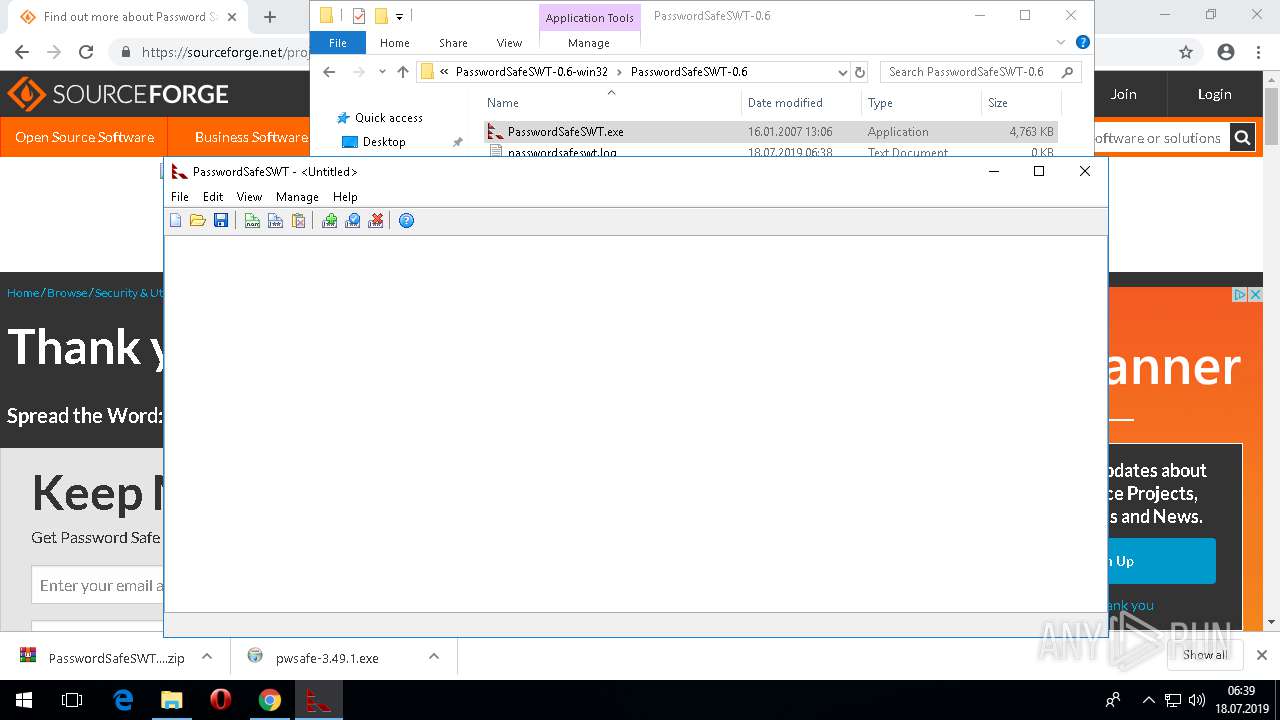
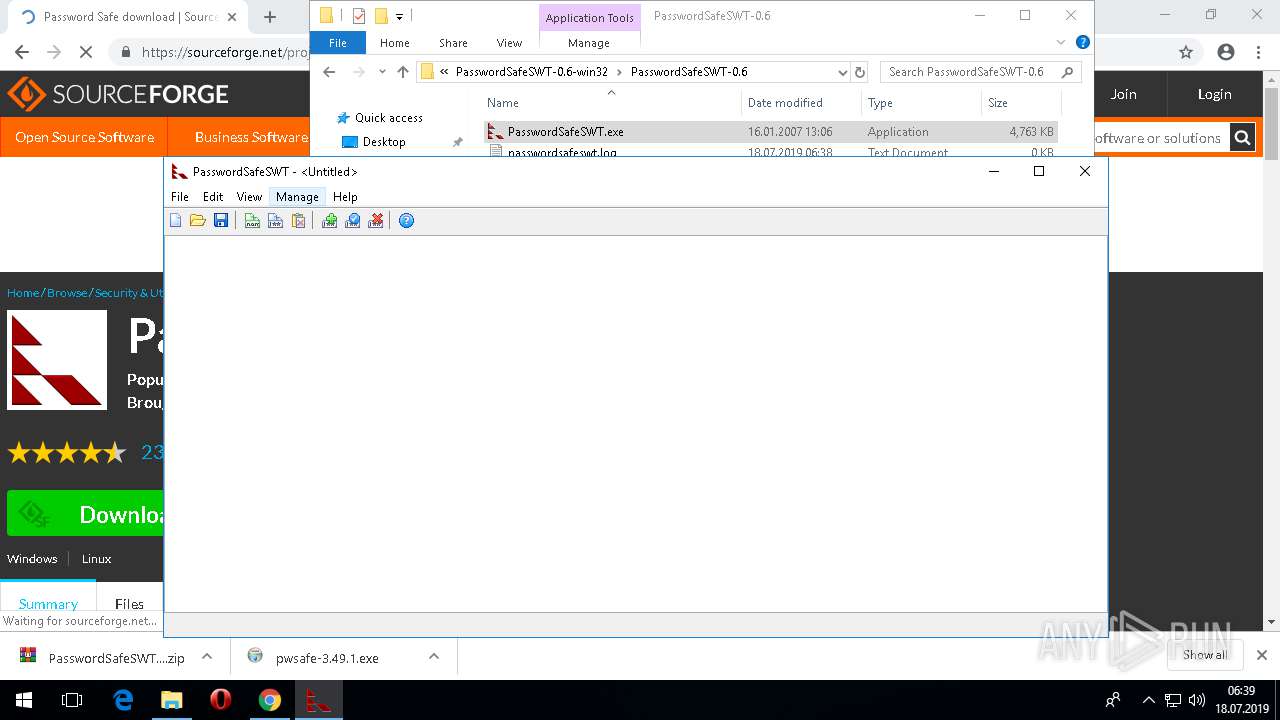
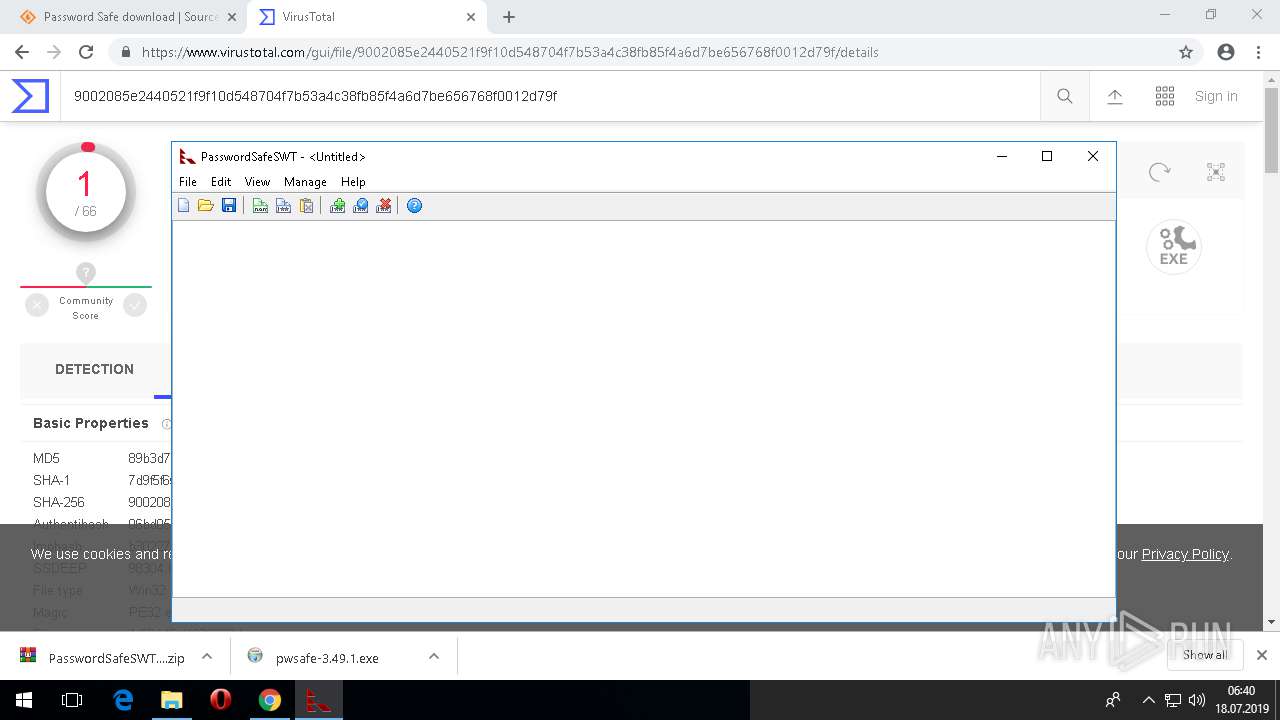
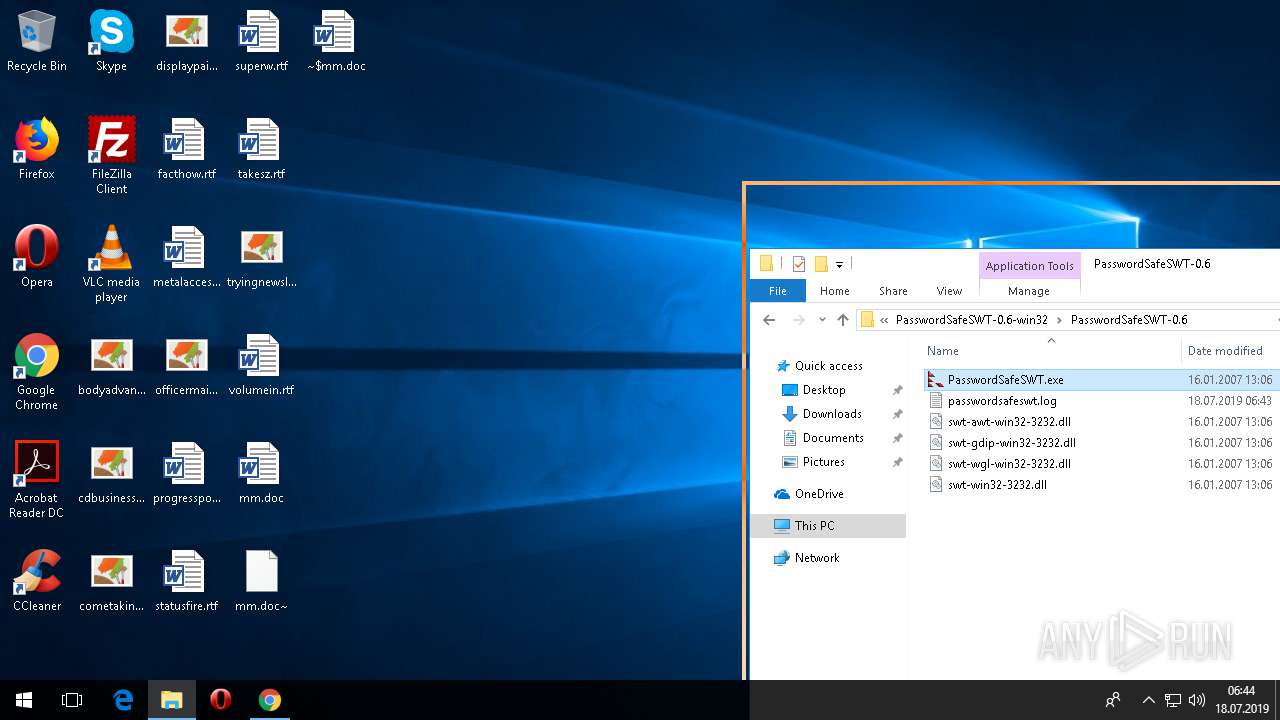
Manual execution by user
- WinRAR.exe (PID: 4076)
- PasswordSafeSWT.exe (PID: 2348)
- WINWORD.EXE (PID: 4716)
Searches for installed software
- chrome.exe (PID: 2460)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2460)
Reads the software policy settings
- chrome.exe (PID: 2460)
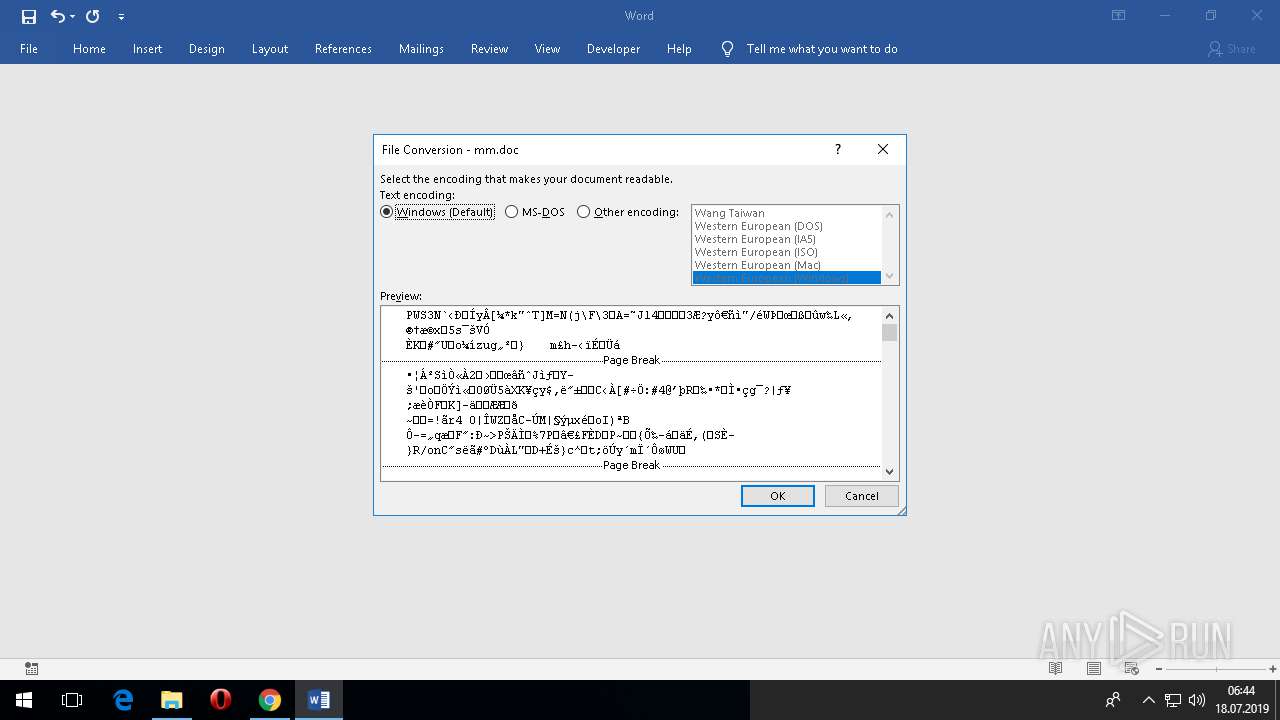
Creates files in the user directory
- WINWORD.EXE (PID: 4716)
Application launched itself
- chrome.exe (PID: 2460)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 4716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
107
Monitored processes
57
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --service-pipe-token=14871313312488731071 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14871313312488731071 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --disable-gpu-compositing --service-pipe-token=10013021398090514465 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10013021398090514465 --renderer-client-id=37 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2232212617923416695 --mojo-platform-channel-handle=5180 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --disable-gpu-compositing --service-pipe-token=2528359390118097778 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2528359390118097778 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=7820 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8731411751526375222 --mojo-platform-channel-handle=5824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --disable-gpu-compositing --service-pipe-token=10261105739975932364 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10261105739975932364 --renderer-client-id=30 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6999190017173698691 --mojo-platform-channel-handle=5048 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --disable-gpu-compositing --service-pipe-token=974266021012439682 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=974266021012439682 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18347650997841546565 --mojo-platform-channel-handle=6524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1516,6369184339147868885,5009110059485099934,131072 --disable-gpu-compositing --service-pipe-token=8694304029389253700 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8694304029389253700 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4504 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.86 Modules
| |||||||||||||||
Total events
8 706
Read events
7 678
Write events
978
Delete events
50
Modification events
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4012) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2460-13207905453765934 |
Value: 259 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 4076-13197800547538197 |
Value: 0 | |||
| (PID) Process: | (2460) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
11
Suspicious files
387
Text files
211
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0d54fc90-4045-4b79-8721-c0bbef606e99.tmp | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
174
DNS requests
141
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2460 | chrome.exe | GET | 302 | 216.239.34.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
— | — | HEAD | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx | US | — | — | whitelisted |
— | — | HEAD | 200 | 173.194.188.72:80 | http://r3---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1563432137&mv=m&mvi=2&pl=24&shardbypass=yes | US | — | — | whitelisted |
— | — | GET | 206 | 173.194.188.72:80 | http://r3---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1563432137&mv=m&mvi=2&pl=24&shardbypass=yes | US | binary | 10.0 Kb | whitelisted |
2460 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
— | — | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx | US | html | 515 b | whitelisted |
— | — | GET | 206 | 173.194.188.72:80 | http://r3---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1563432137&mv=m&mvi=2&pl=24&shardbypass=yes | US | binary | 21.6 Kb | whitelisted |
— | — | GET | 206 | 173.194.188.72:80 | http://r3---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1563432137&mv=m&mvi=2&pl=24&shardbypass=yes | US | binary | 4.25 Kb | whitelisted |
— | — | GET | 206 | 173.194.188.72:80 | http://r3---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1563432137&mv=m&mvi=2&pl=24&shardbypass=yes | US | binary | 44.9 Kb | whitelisted |
— | — | GET | 206 | 173.194.188.72:80 | http://r3---sn-4g5ednsl.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvN2MwQUFWdmlaX0VYMlk3YWlITHpVbV9MZw/0.57.44.2492_hnimpnehoodheedghdeeijklkeaacbdc.crx?cms_redirect=yes&mip=185.217.119.34&mm=28&mn=sn-4g5ednsl&ms=nvh&mt=1563432137&mv=m&mvi=2&pl=24&shardbypass=yes | US | binary | 91.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.90.23.242:443 | login.live.com | Microsoft Corporation | US | unknown |
2460 | chrome.exe | 216.105.38.13:443 | sourceforge.net | American Internet Services, LLC. | US | malicious |
2460 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2460 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
2460 | chrome.exe | 13.32.223.219:443 | privacy-api-gateway.quantcast.com | Amazon.com, Inc. | US | unknown |
2460 | chrome.exe | 13.32.223.176:443 | api.quantcast.mgr.consensu.org | Amazon.com, Inc. | US | unknown |
2460 | chrome.exe | 13.32.223.4:443 | audit.quantcast.mgr.consensu.org | Amazon.com, Inc. | US | suspicious |
2460 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
sourceforge.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| malicious |
a.fsdn.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
conhost.exe | InitSideBySide failed create an activation context. Error: 1814 |
WINWORD.EXE | 2019-07-18 06:44:13.645 T#5848 <E> [AriaSDK.PAL] PAL is already shutdown!
|