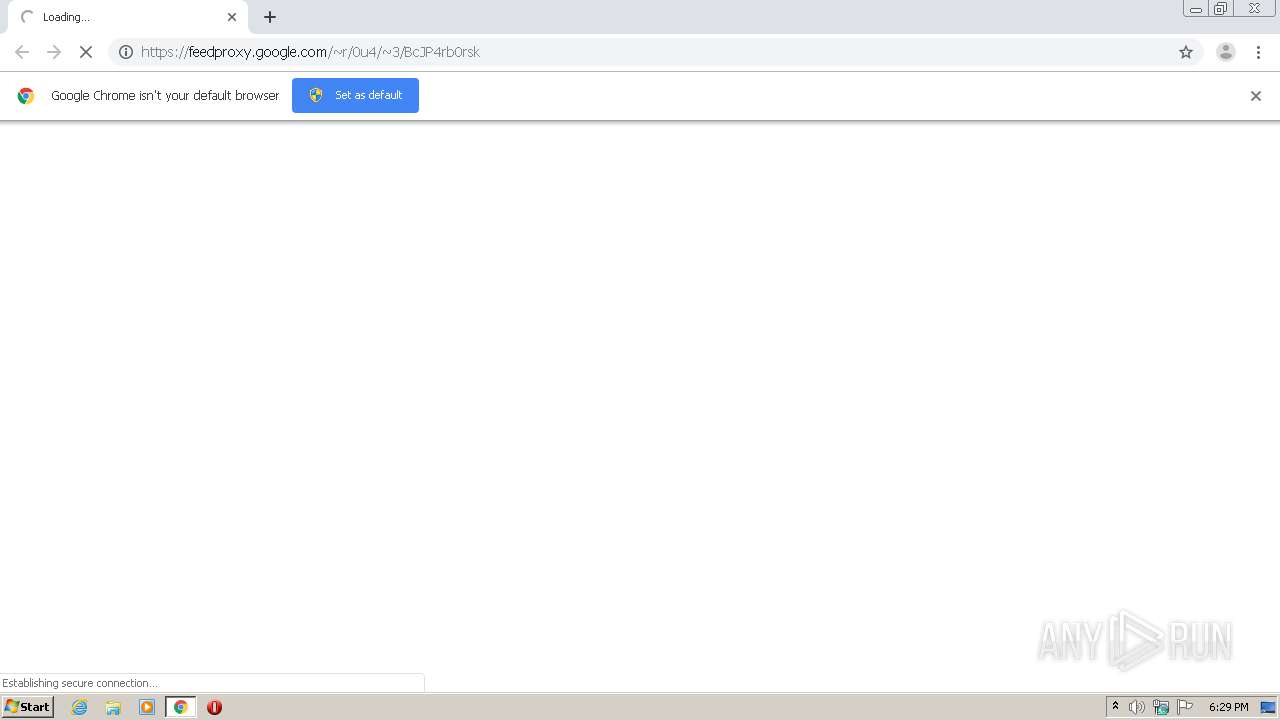
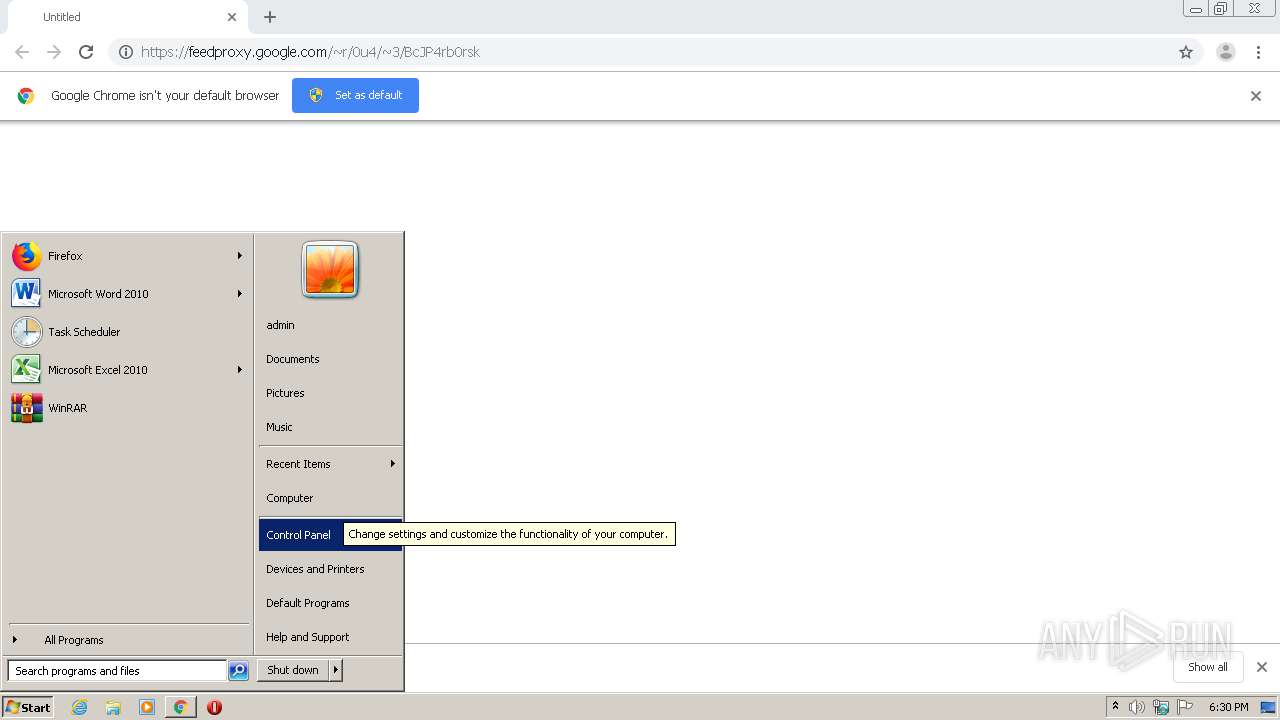
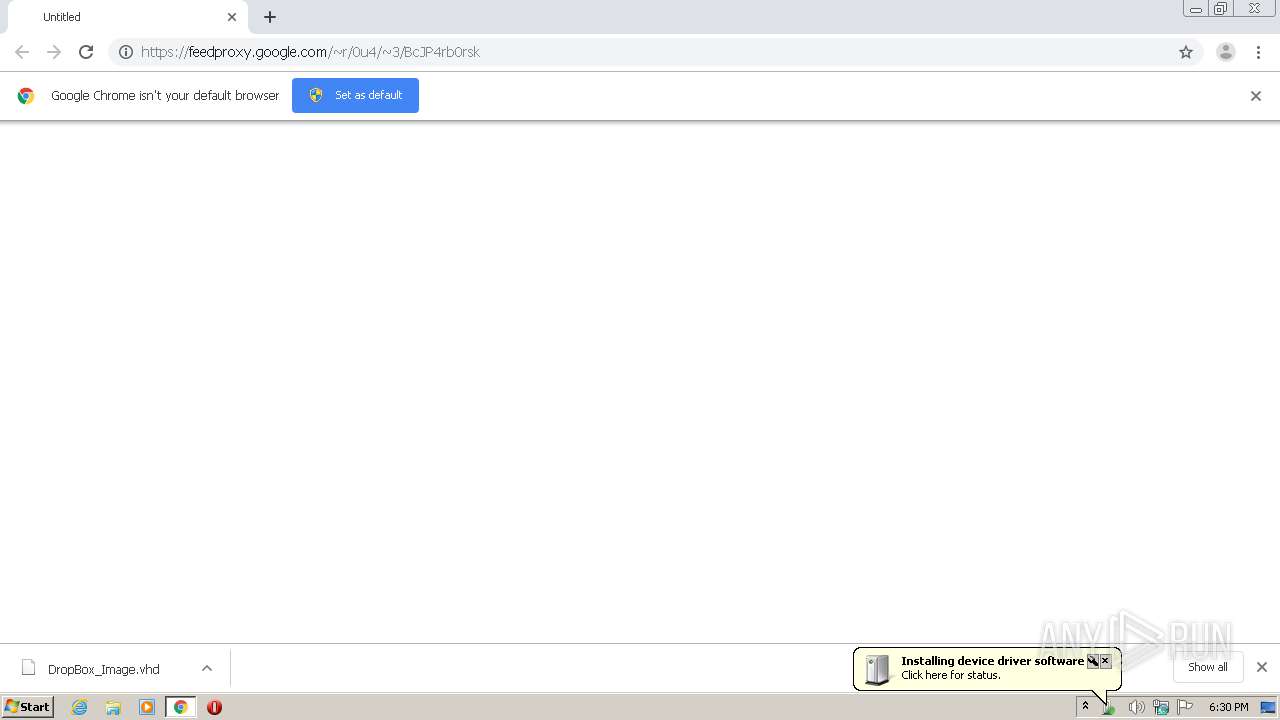
| URL: | https://feedproxy.google.com/~r/0u4/~3/BcJP4rb0rsk |
| Full analysis: | https://app.any.run/tasks/e80c61c5-a90e-40d7-b675-16ea14af584a |
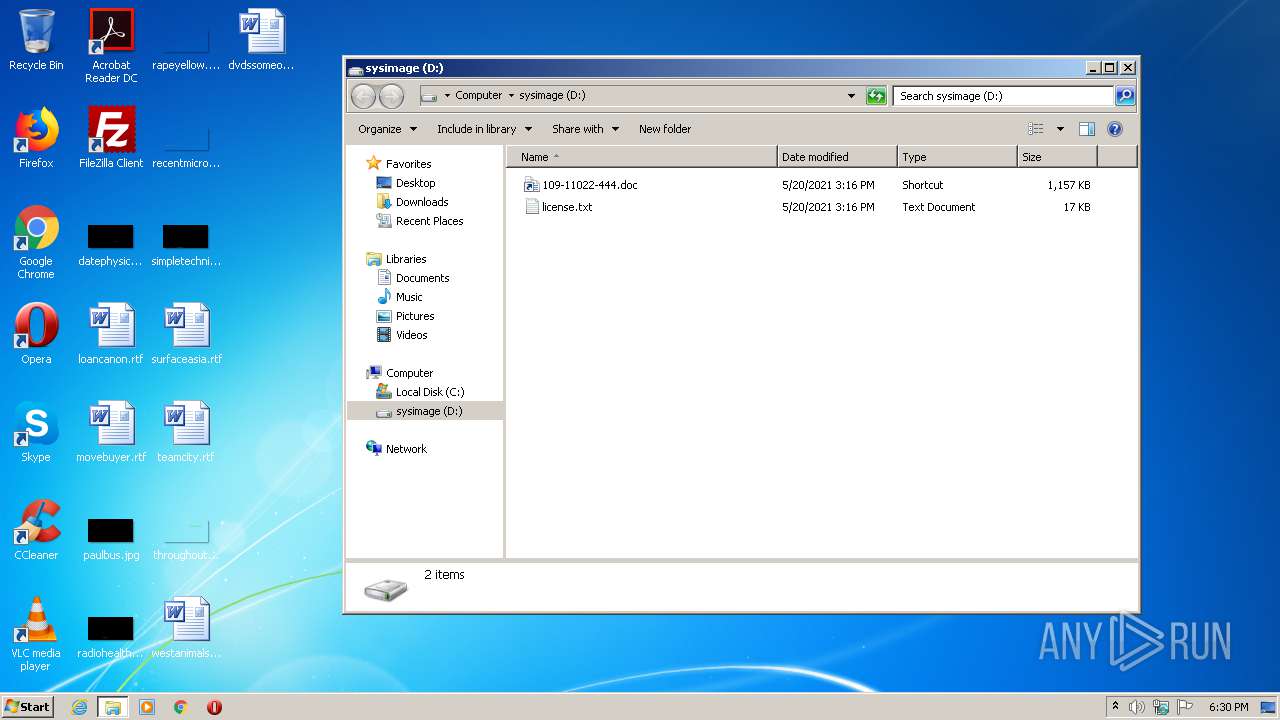
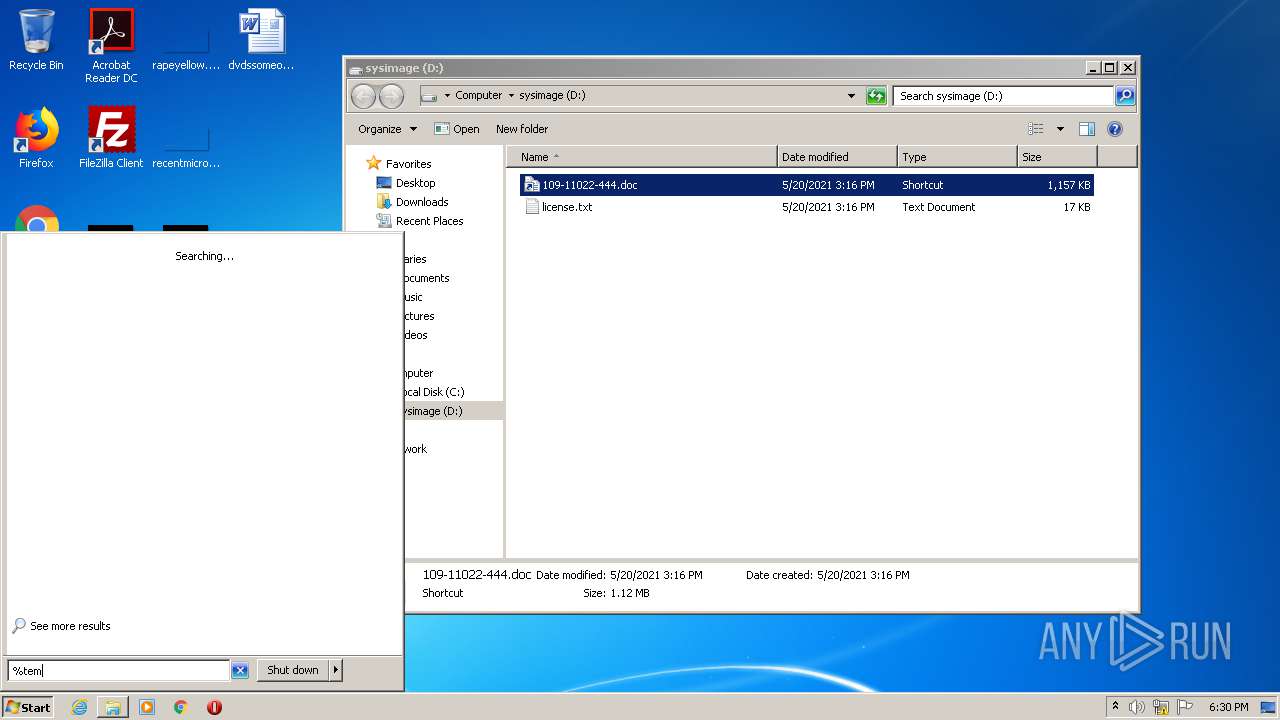
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2021, 17:29:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 803AD9EB2A83F4EA499A30D96FF1C91E |
| SHA1: | 27AF251710ADBD923DF1633B0EC3D37B0AA5656A |
| SHA256: | 48F8099D1DE4049792925D976F69D1E9262F9DAEAD4371039B1FF9F1EF2ED80B |
| SSDEEP: | 3:N8NAcLI9eEAN41x1XWO:27ck6CO |
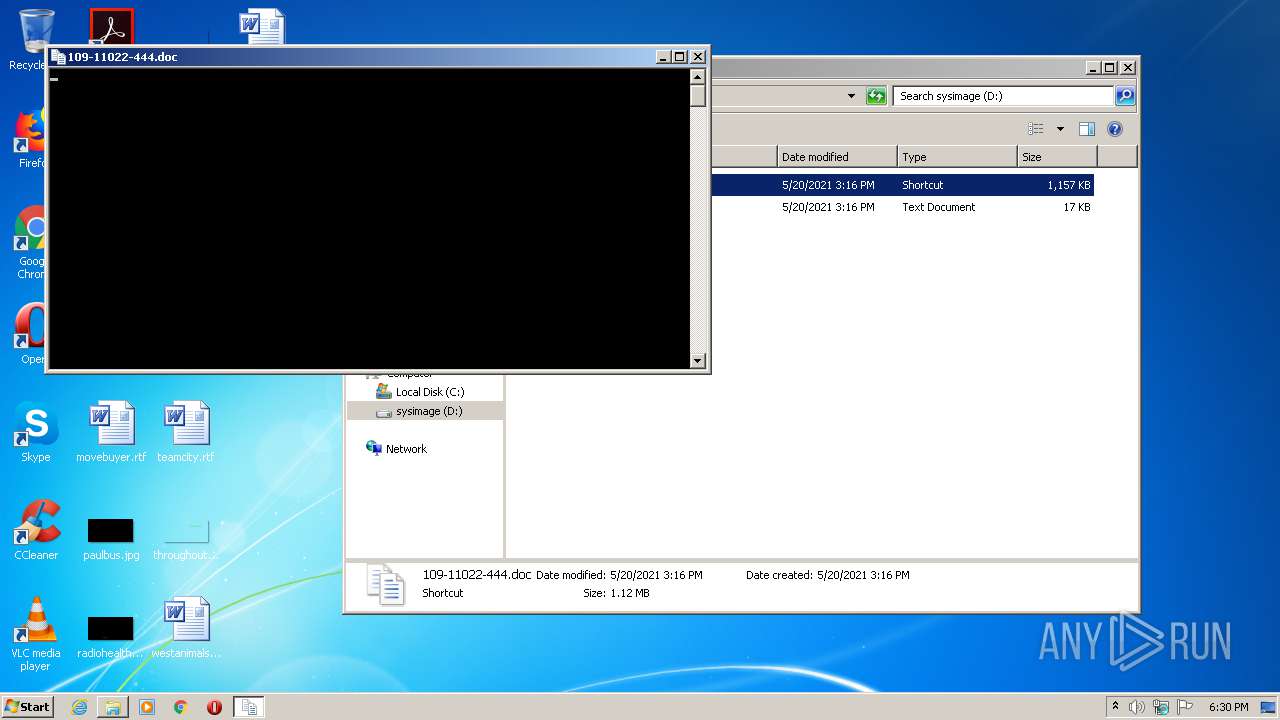
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 292)
SUSPICIOUS
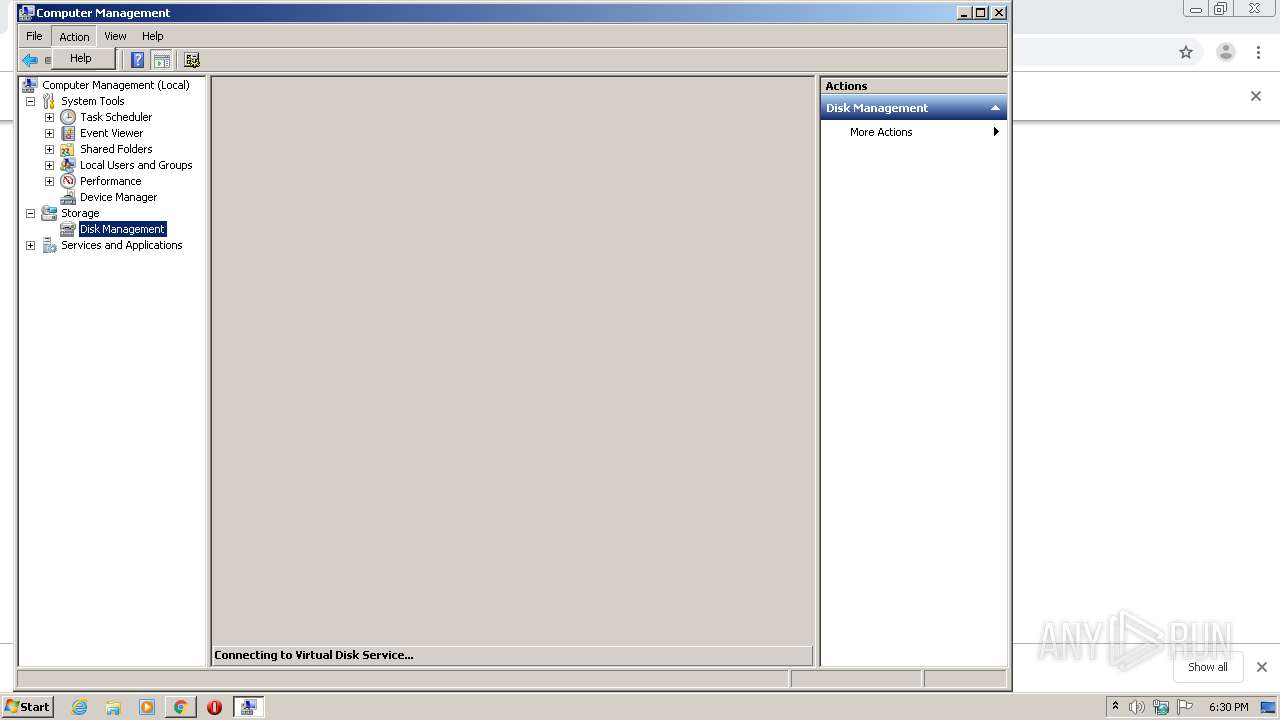
Executed via COM
- vdsldr.exe (PID: 1096)
- rundll32.exe (PID: 3384)
- DrvInst.exe (PID: 3856)
- DrvInst.exe (PID: 1492)
- DrvInst.exe (PID: 2316)
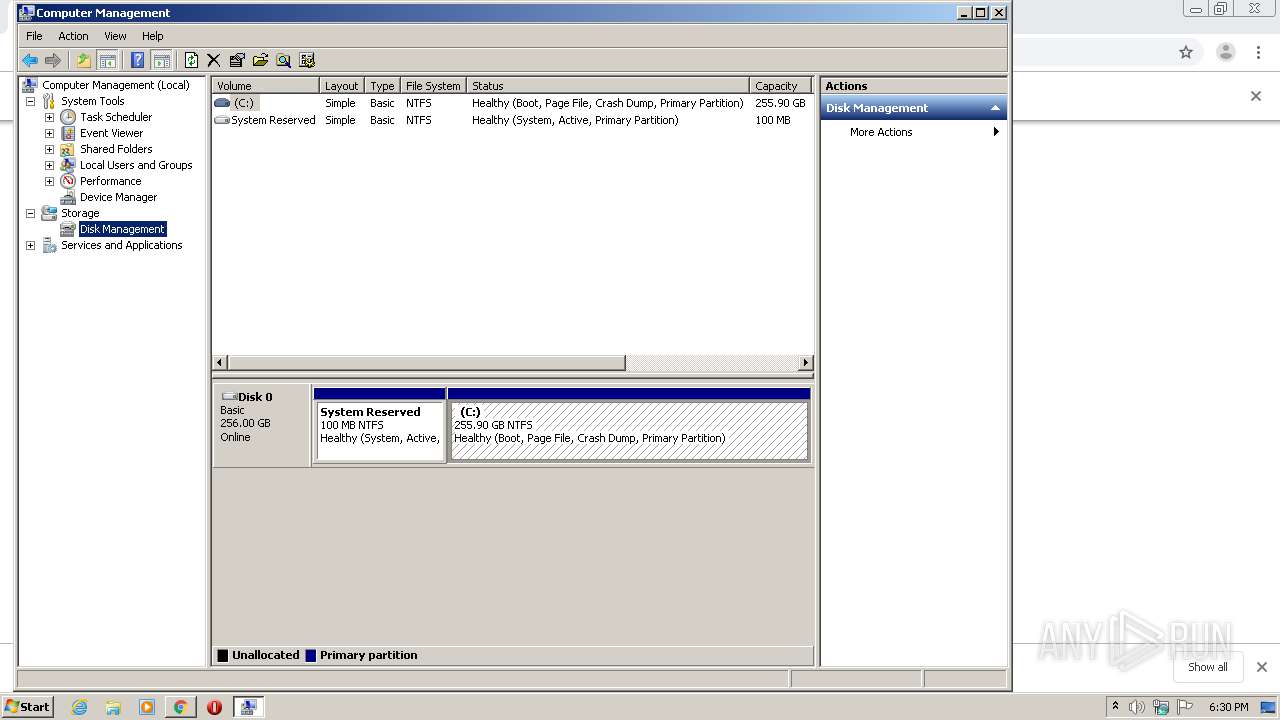
Executed as Windows Service
- vds.exe (PID: 2376)
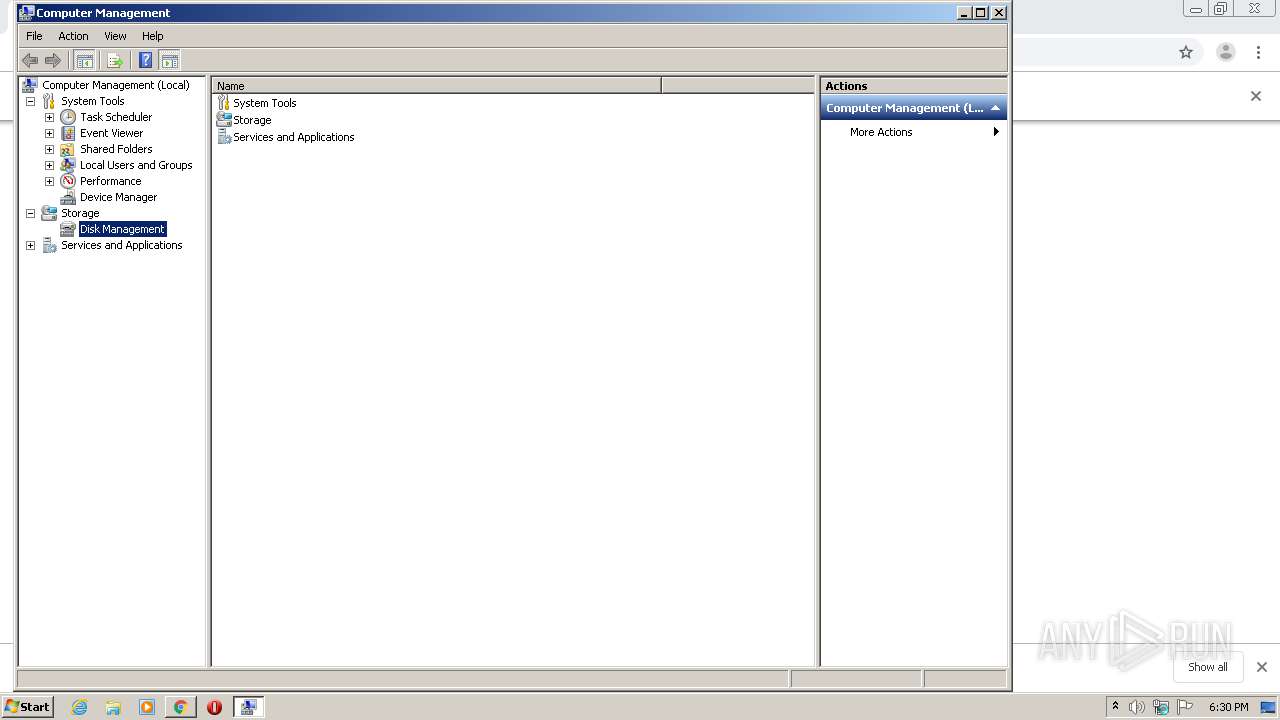
Low-level read access rights to disk partition
- vds.exe (PID: 2376)
- explorer.exe (PID: 292)
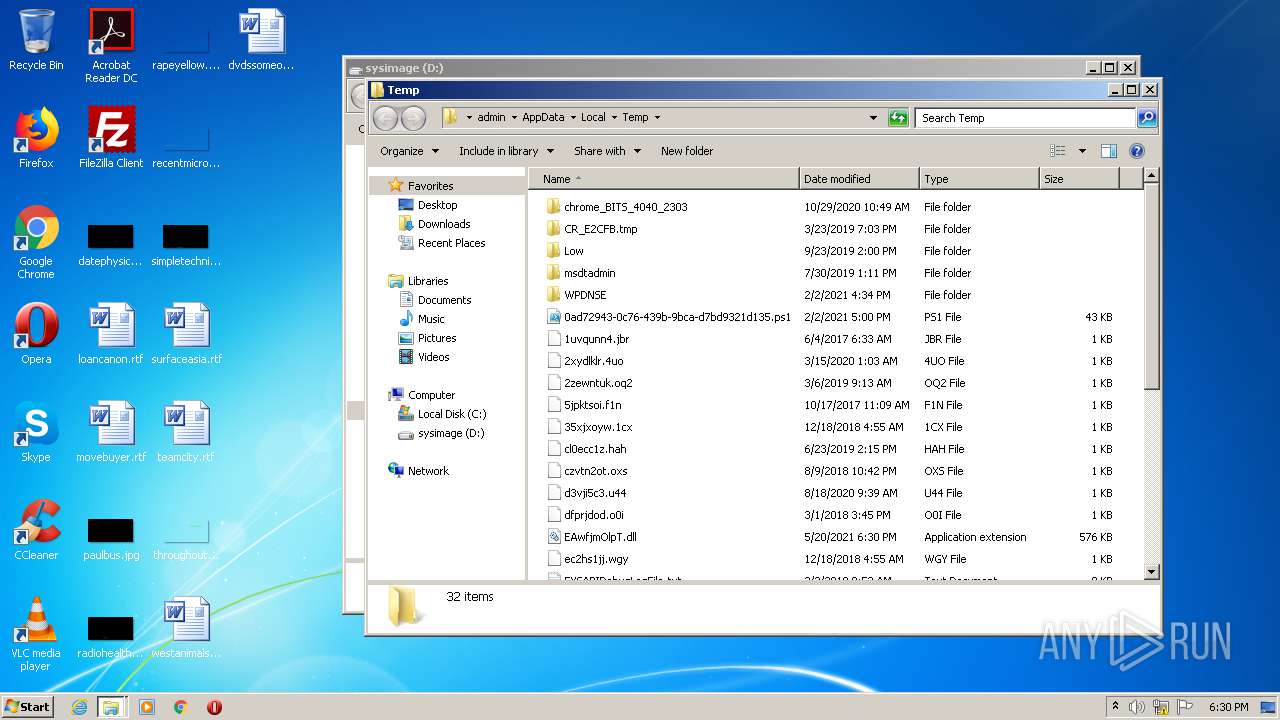
Creates files in the user directory
- explorer.exe (PID: 292)
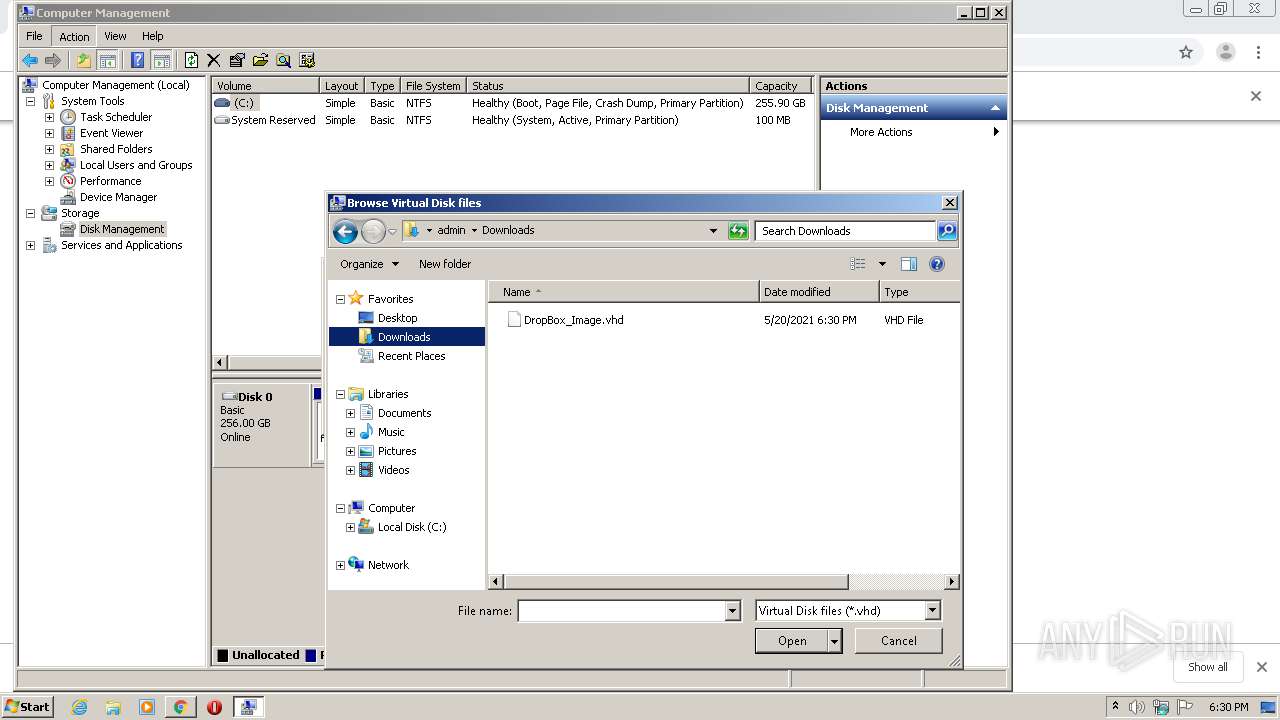
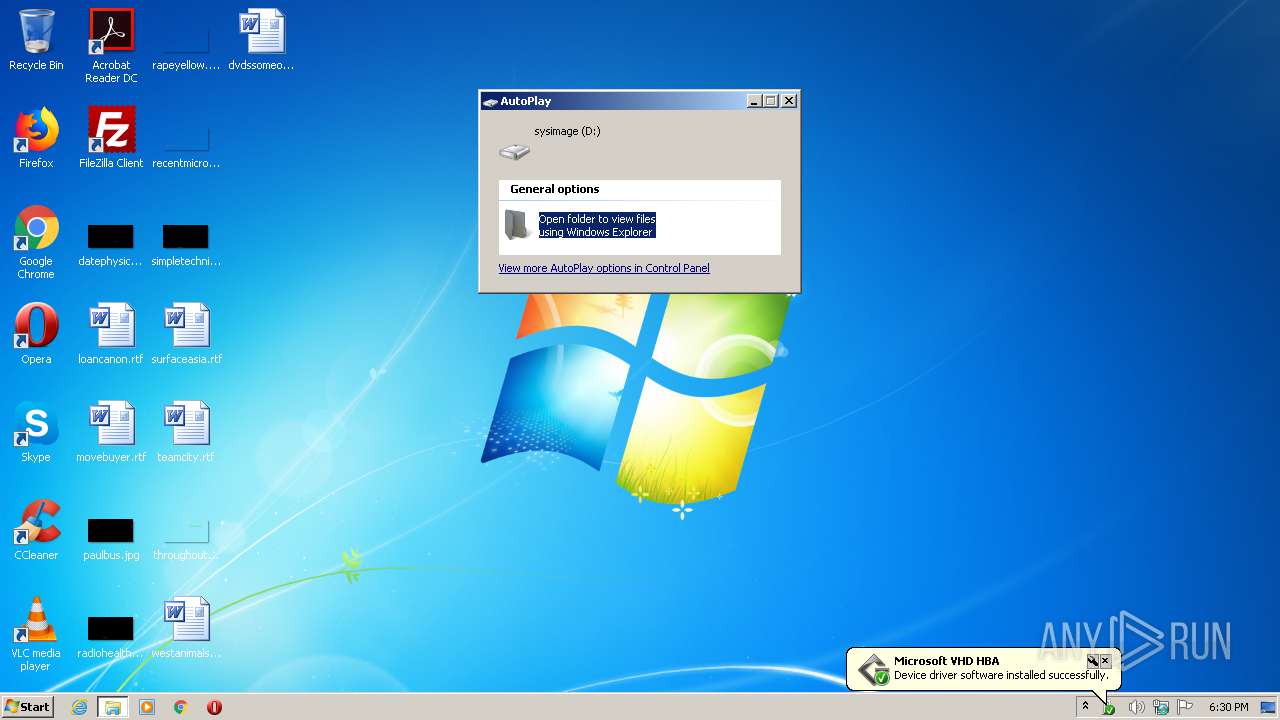
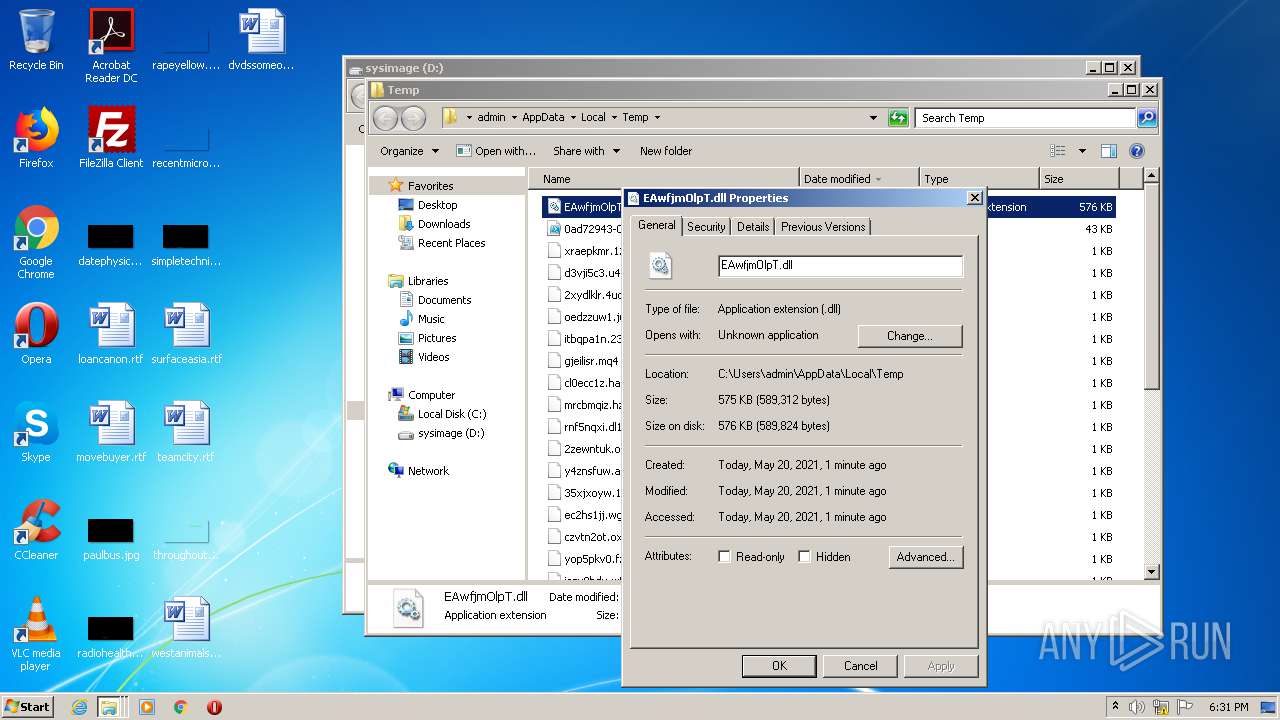
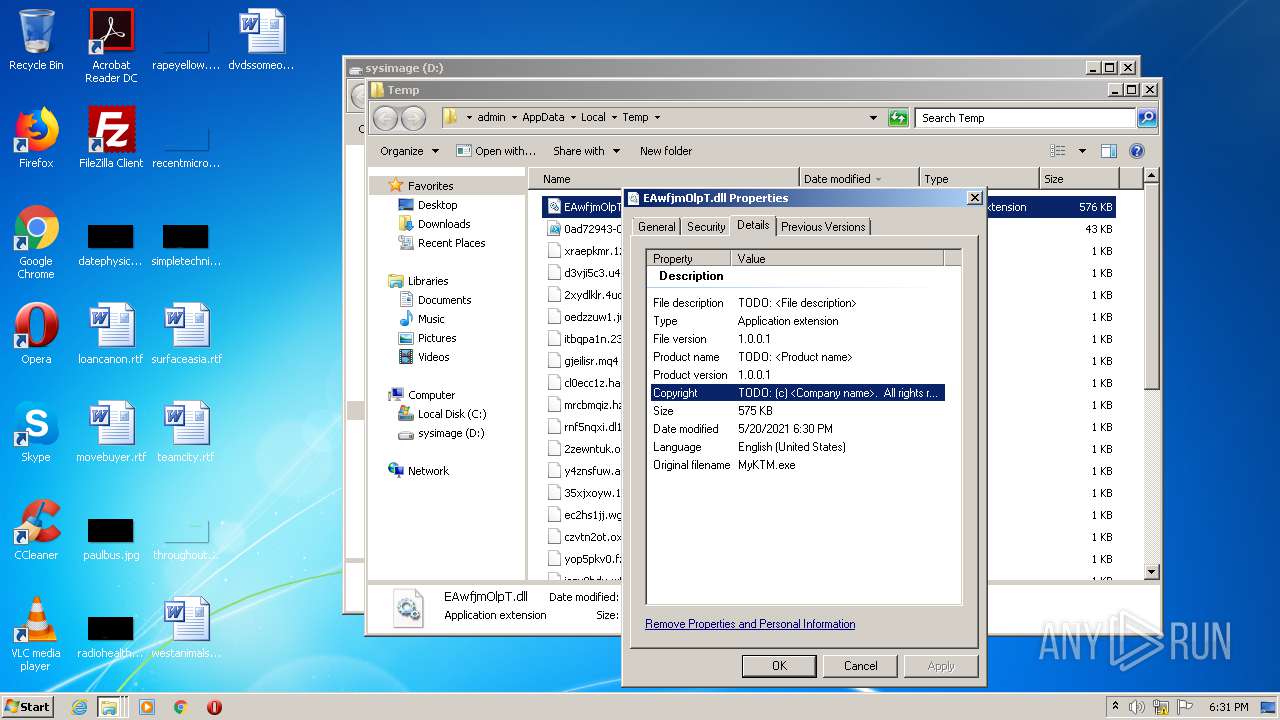
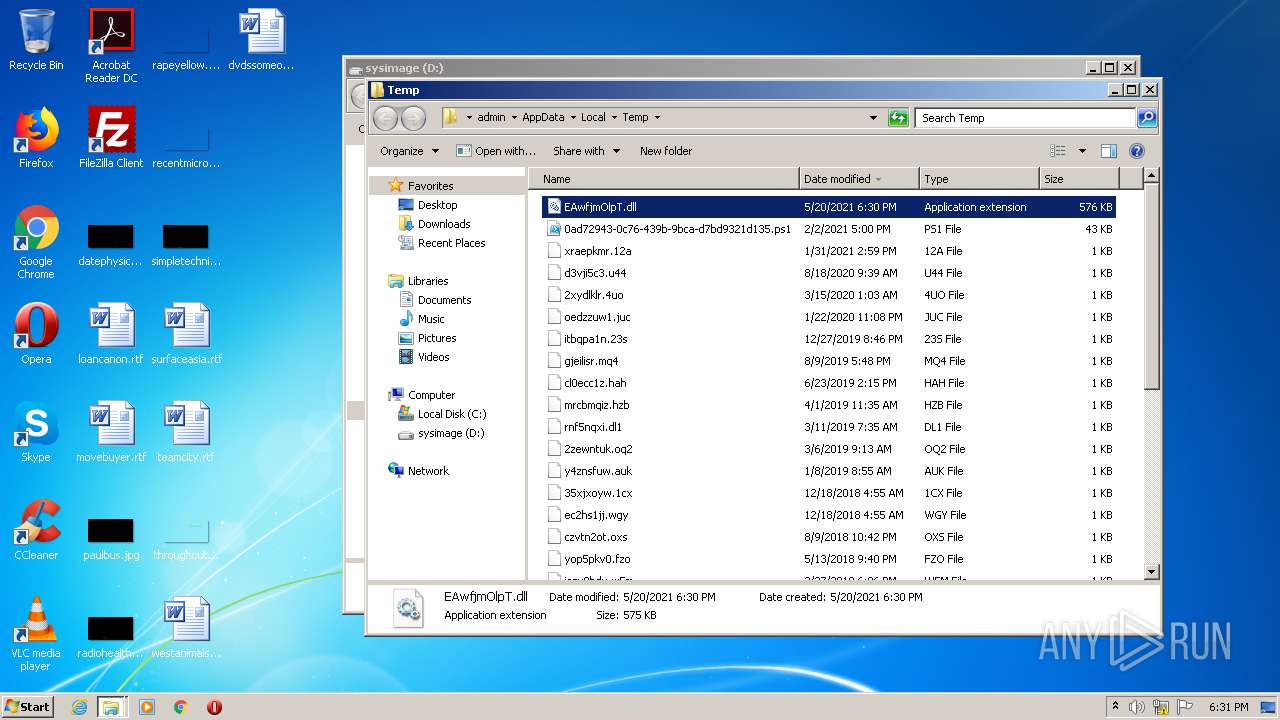
Drops a file with a compile date too recent
- DrvInst.exe (PID: 3856)
- WScript.exe (PID: 2496)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 292)
Executes scripts
- cmd.exe (PID: 2928)
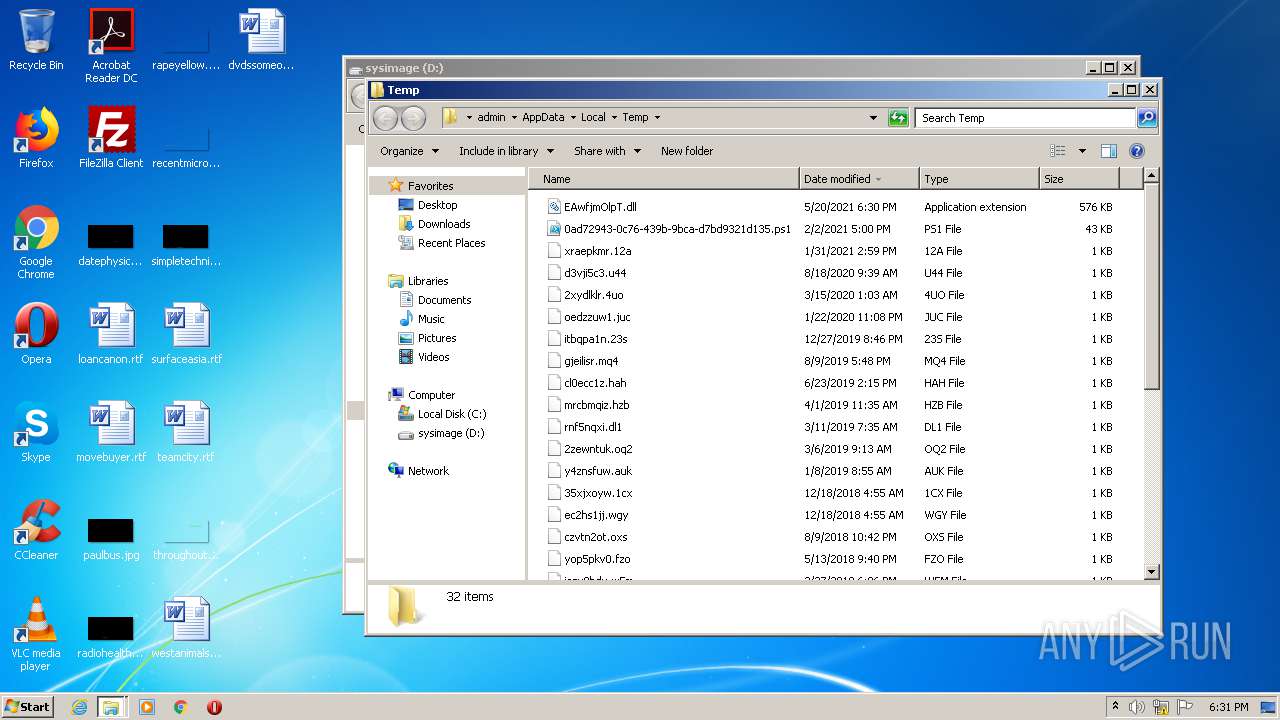
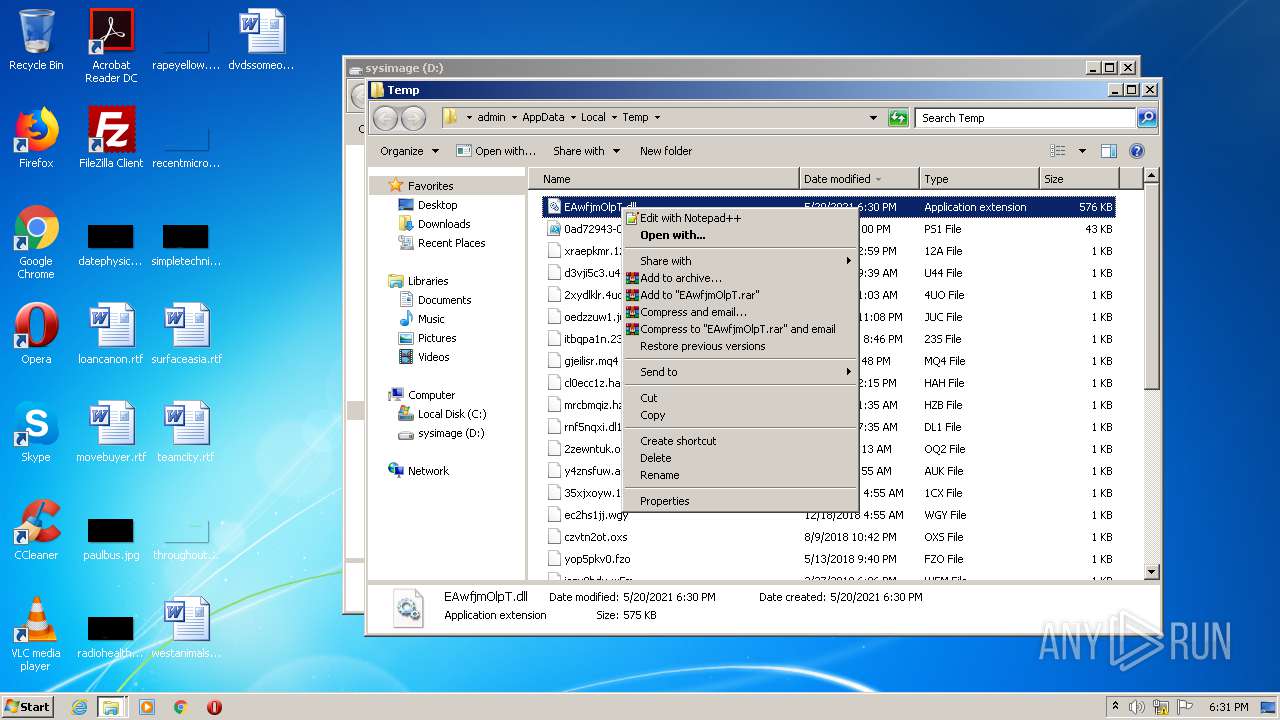
Uses RUNDLL32.EXE to load library
- WScript.exe (PID: 2496)
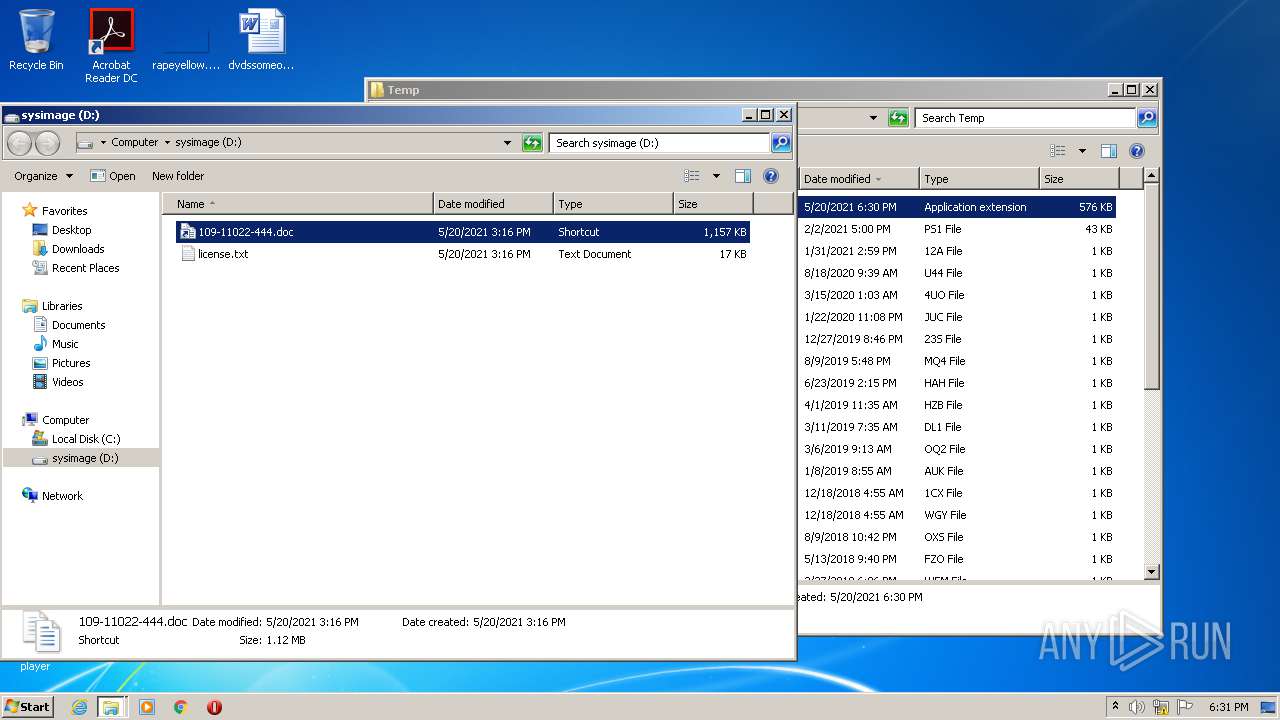
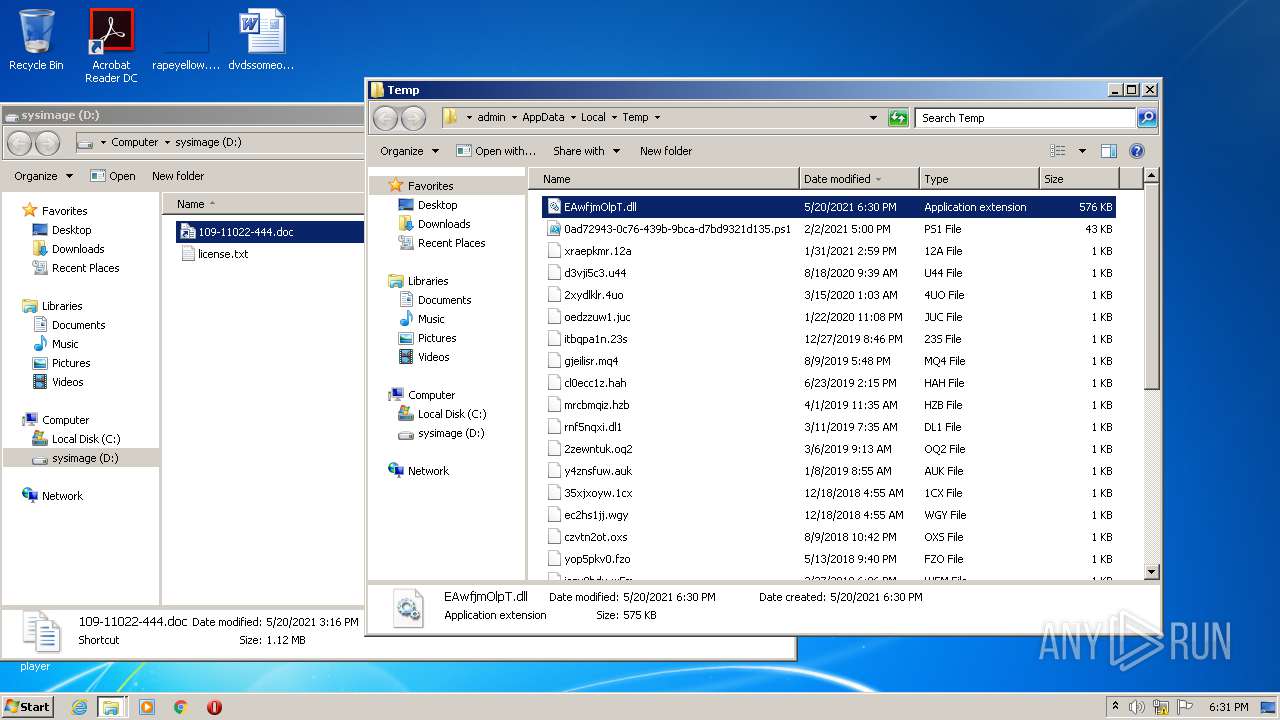
Executable content was dropped or overwritten
- WScript.exe (PID: 2496)
Drops a file that was compiled in debug mode
- WScript.exe (PID: 2496)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1644)
INFO
Reads the hosts file
- chrome.exe (PID: 2804)
- chrome.exe (PID: 3972)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 1000)
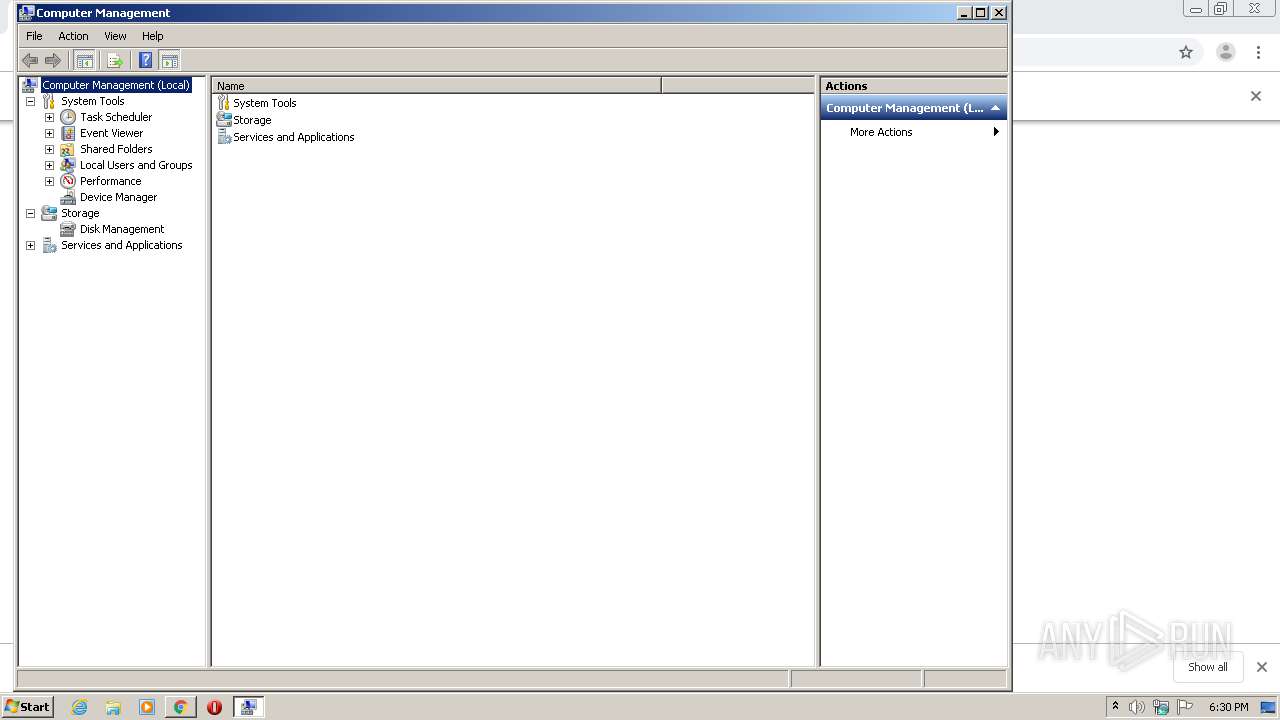
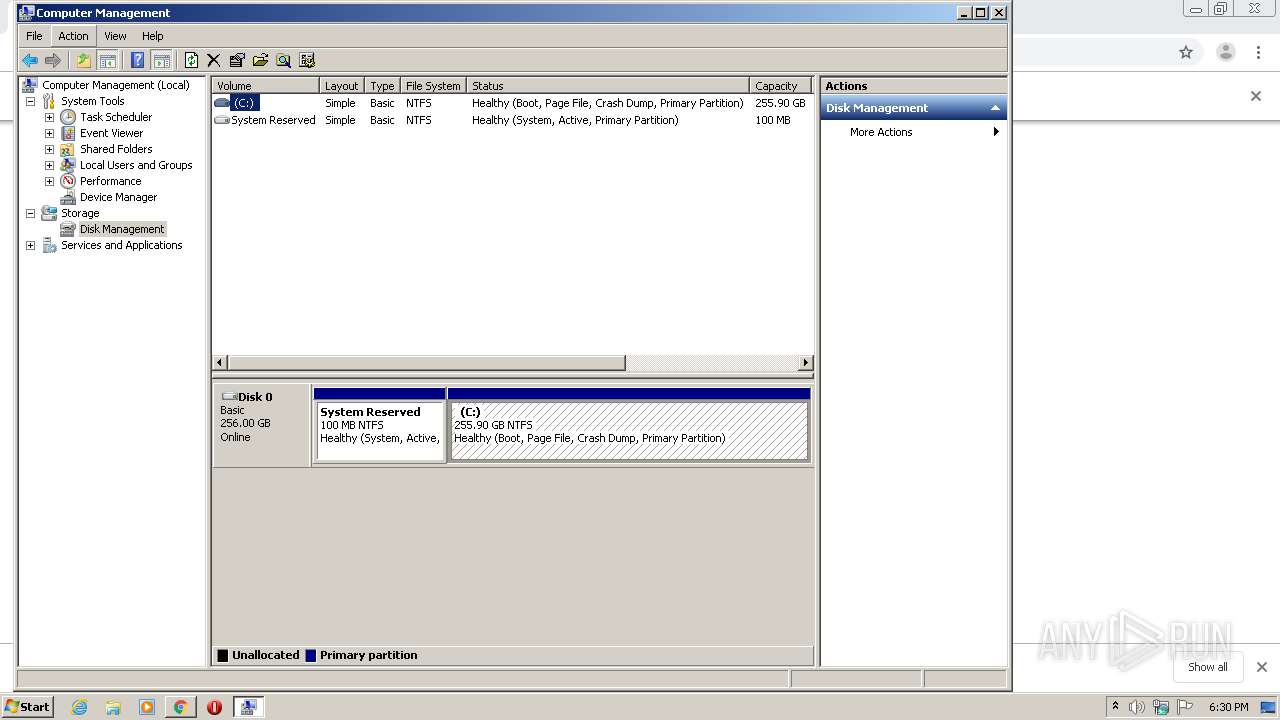
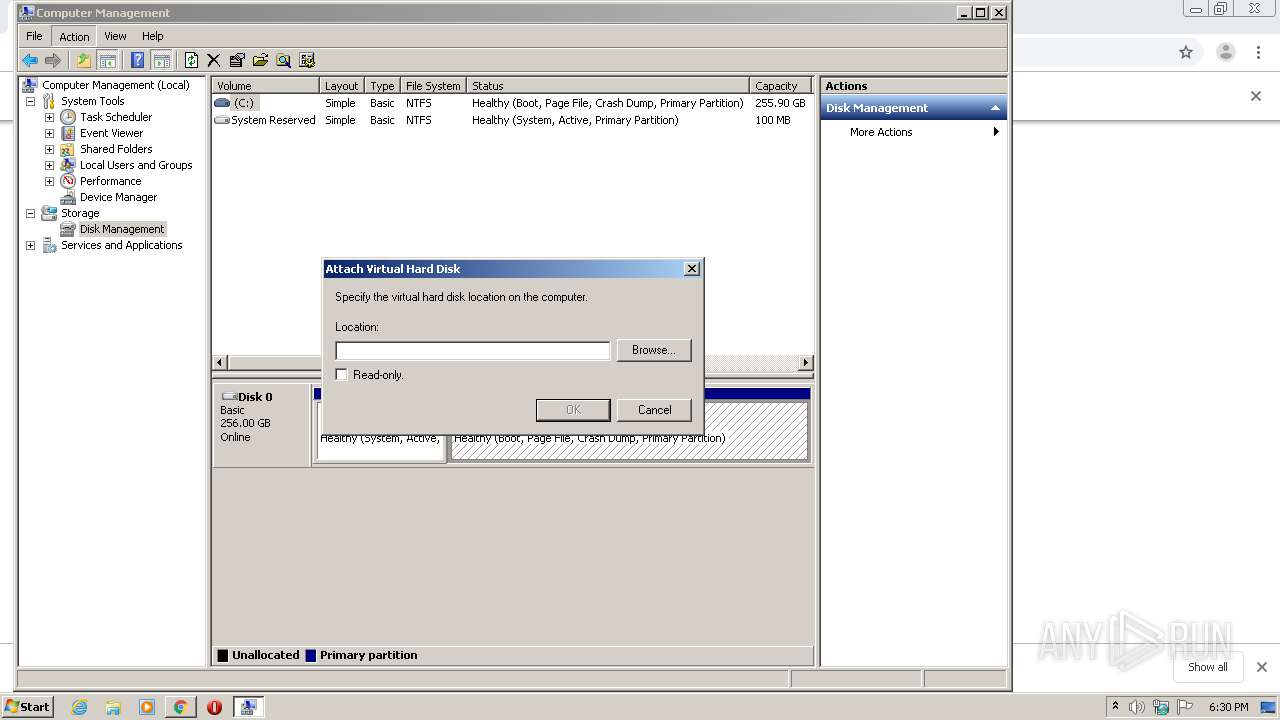
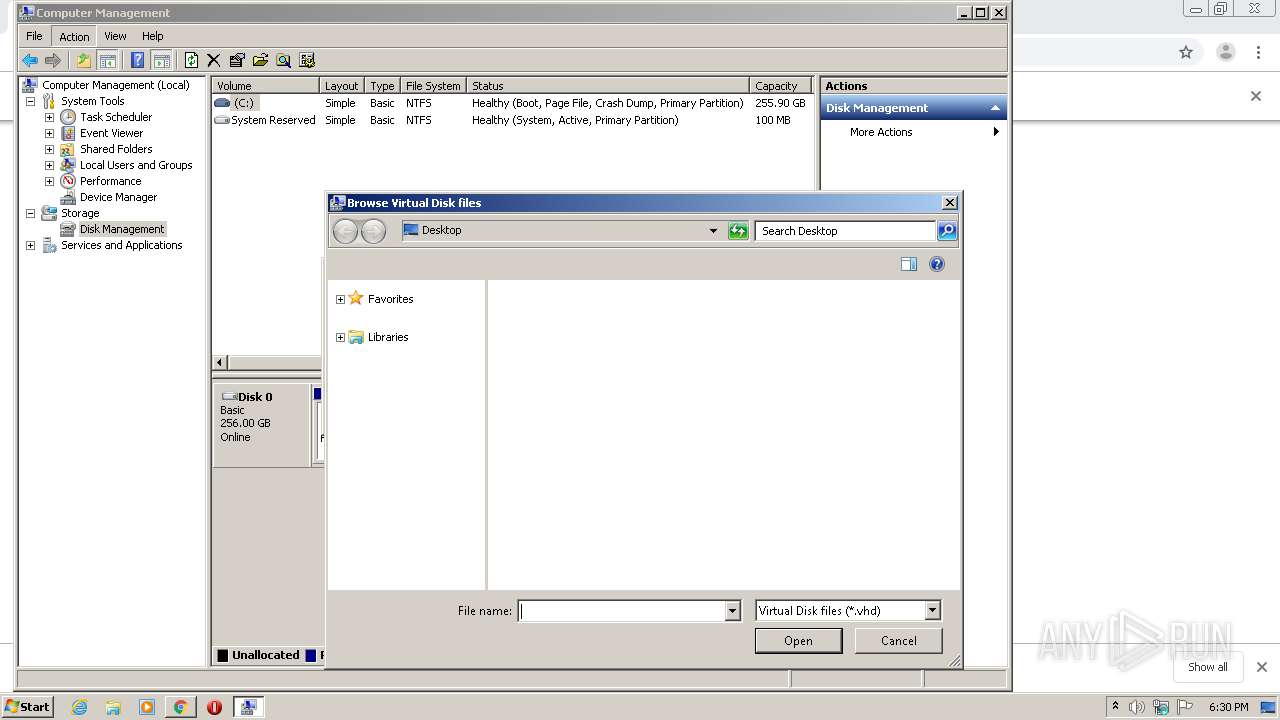
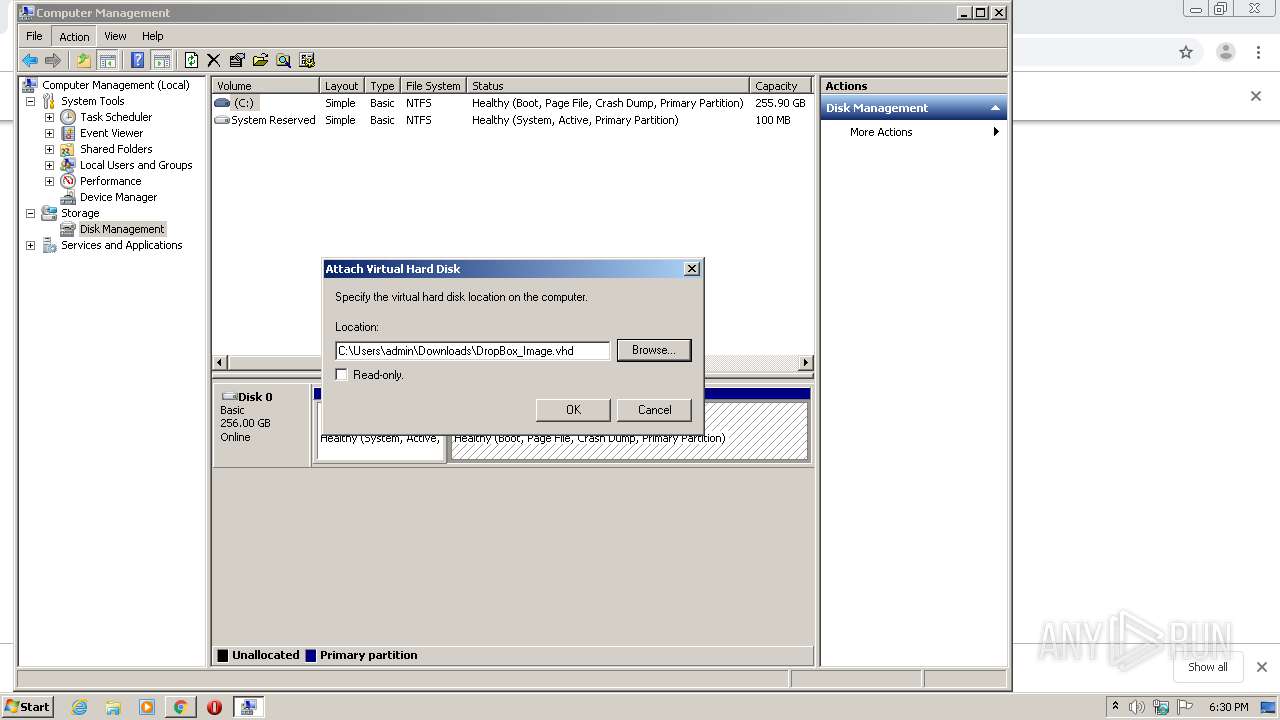
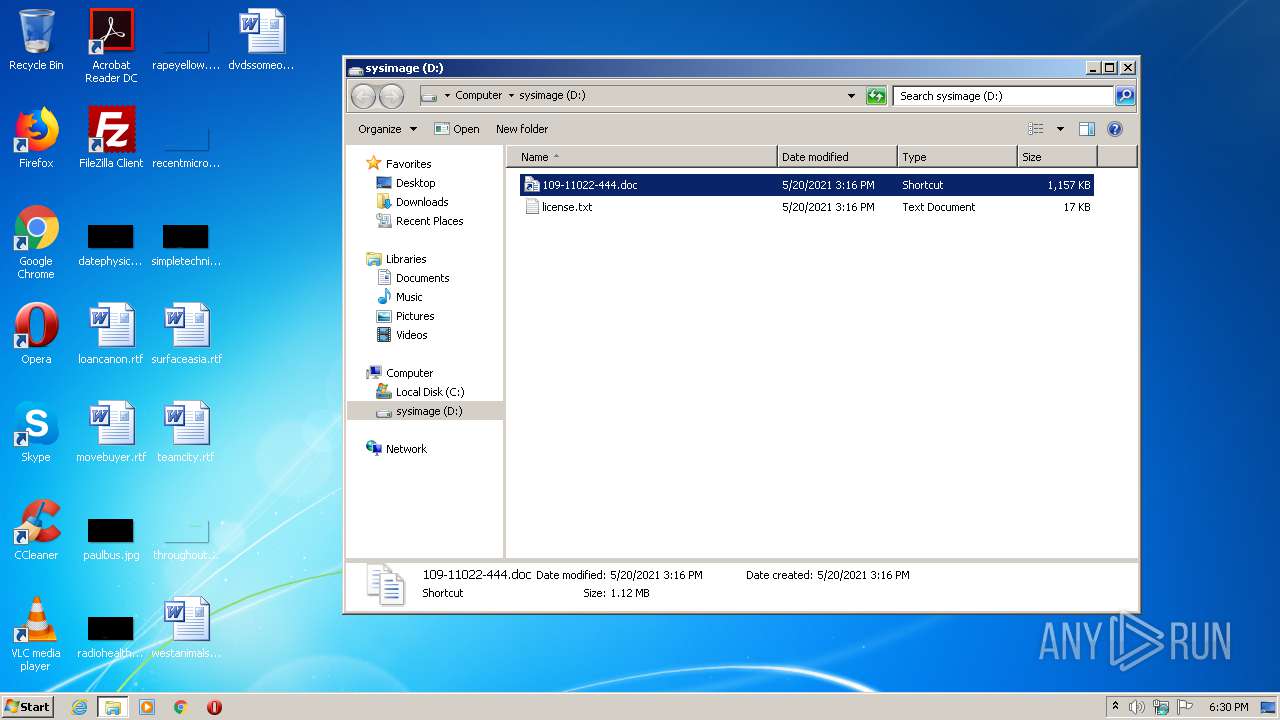
Manual execution by user
- CompMgmtLauncher.exe (PID: 3048)
- CompMgmtLauncher.exe (PID: 3672)
- cmd.exe (PID: 2928)
- verclsid.exe (PID: 1940)
Application launched itself
- chrome.exe (PID: 3972)
- chrome.exe (PID: 1644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
62
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,15020991101520602278,2565580116971330177,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5283786272004029417 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2408 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 572 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,553342330447591291,5080578291867338786,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3042042667765978536 --mojo-platform-channel-handle=4696 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
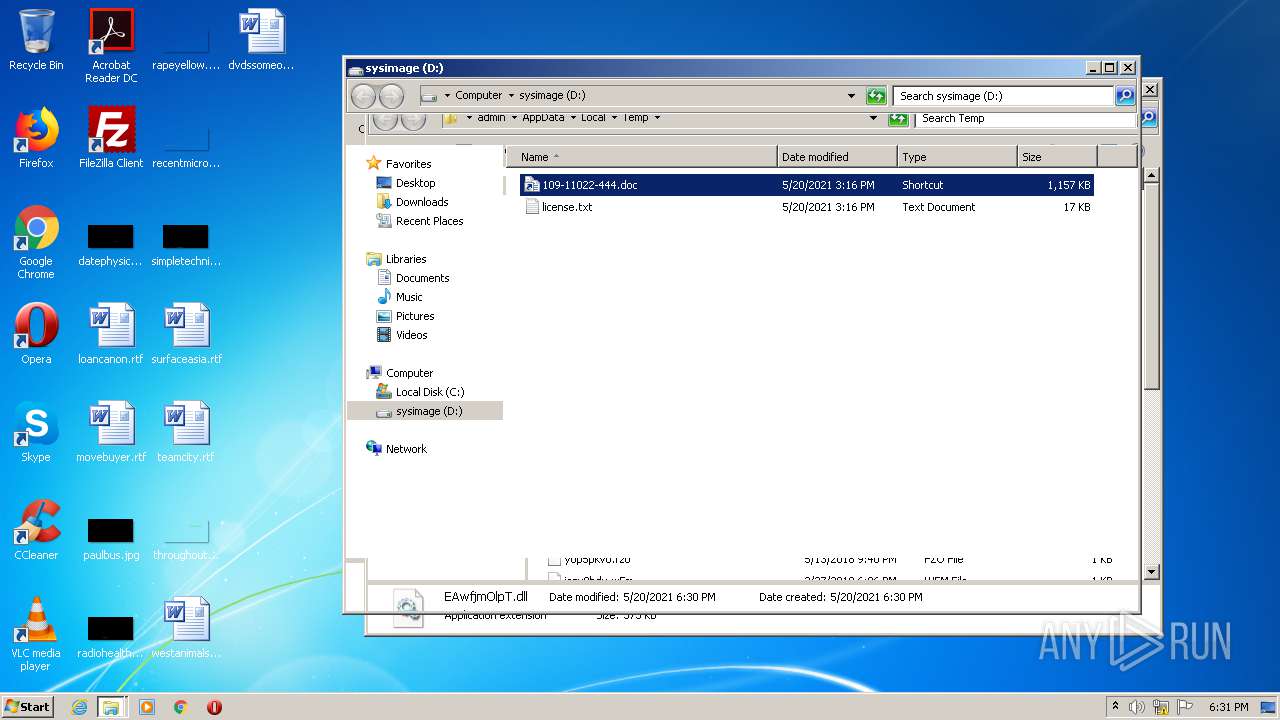
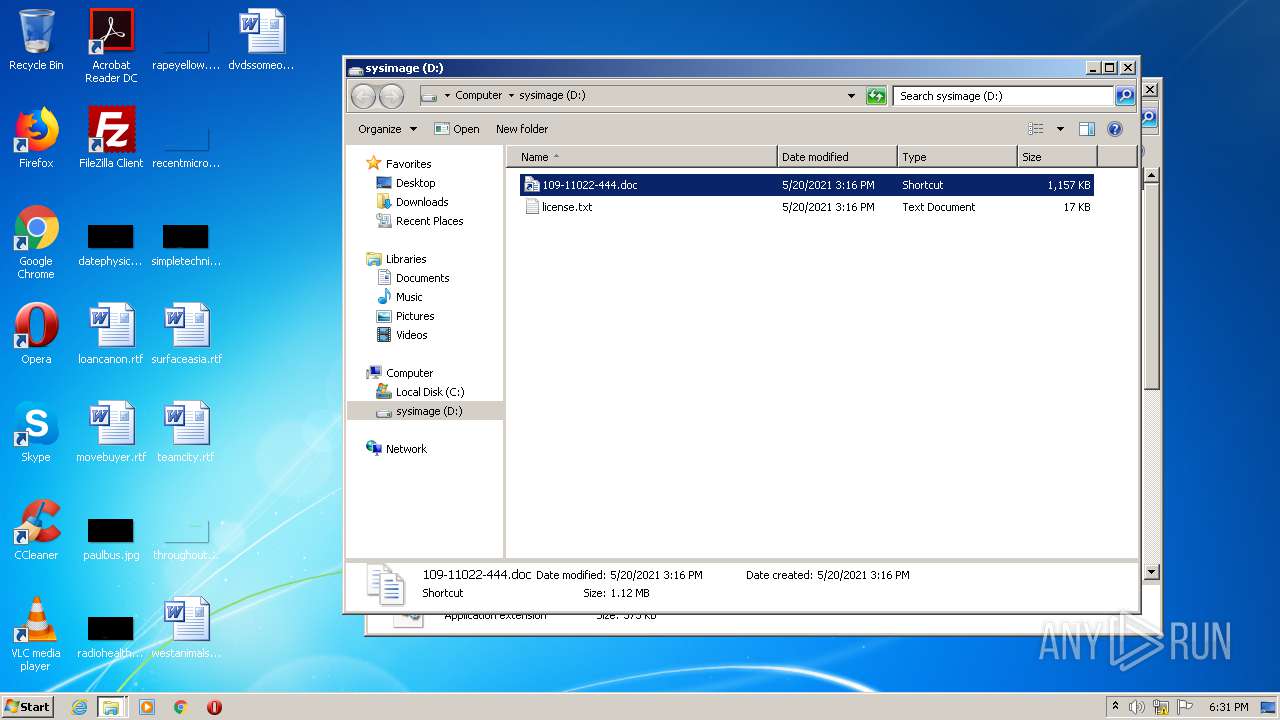
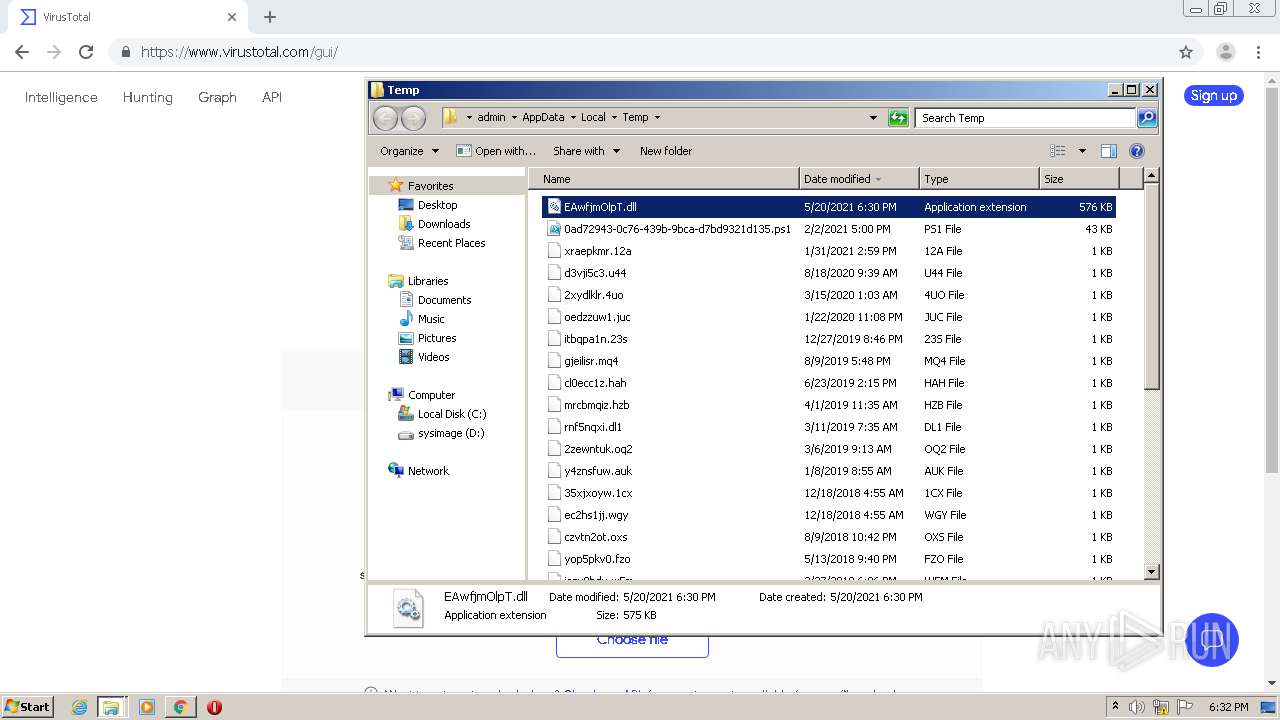
| 616 | C:\Windows\SYSTEM32\rundll32.exe C:\Users\admin\AppData\Local\Temp\EAwfjmOlpT.dll, StartW | C:\Windows\SYSTEM32\rundll32.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2880 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,553342330447591291,5080578291867338786,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=308422267989443913 --mojo-platform-channel-handle=1512 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | C:\Windows\System32\vdsldr.exe -Embedding | C:\Windows\System32\vdsldr.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Virtual Disk Service Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,553342330447591291,5080578291867338786,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8011264415132296031 --mojo-platform-channel-handle=4332 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | DrvInst.exe "1" "200" "SCSI\Disk&Ven_Msft&Prod_Virtual_Disk\2&1f4adffe&0&000001" "" "" "69911eaf3" "00000000" "00000568" "00000548" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,553342330447591291,5080578291867338786,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6092461065377013721 --mojo-platform-channel-handle=4156 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 875
Read events
2 855
Write events
1 006
Delete events
14
Modification events
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB01000000D3774223686C7D41BA10F94A8A6CF0AE0000000002000000000010660000000100002000000006E9146C2FECF0ED50441BEE3D457DD417A11F9C688DD2D0B3FBAF35B39D69B8000000000E800000000200002000000038F9A6F0961870BD0501E30544B84D3C919AEA0F48567C4385F564DD7FA0B112300000003908178BAE9B3FCD8621714311F11A5843E1B56AF84463F4FAEFB8C0BA25BFE5648A1D7B80C7B063795F0E11EB559677400000009B1D37270401FDB7F5061F653271A94A16621D2B3DBDBD83704807FEF0C033BE7FB82724FF1B8EAF4EC66E8EBF8662442B93DE856AE807F0745B5FFF8CC0754D | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3972-13266005390636250 |
Value: 259 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3972) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
Executable files
1
Suspicious files
68
Text files
434
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60A69C8F-F84.pma | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3cc783e6-20a2-431e-82e1-d92ce8439589.tmp | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18391c.TMP | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18392c.TMP | text | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF183b3f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
36
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
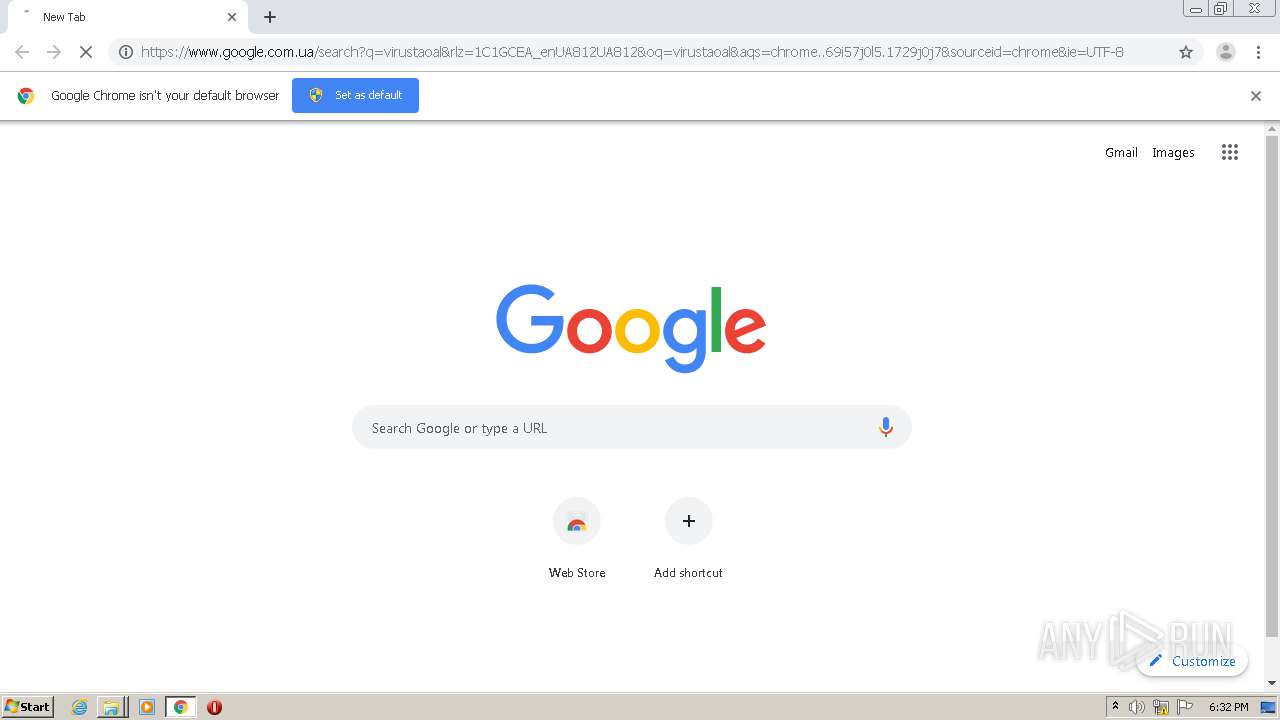
1000 | chrome.exe | GET | 302 | 216.239.38.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
1000 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | chrome.exe | 142.250.185.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2804 | chrome.exe | 172.217.18.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2804 | chrome.exe | 142.250.186.78:443 | feedproxy.google.com | Google Inc. | US | whitelisted |
2804 | chrome.exe | 142.250.181.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2804 | chrome.exe | 47.242.134.95:443 | ccmun.org | — | US | unknown |
1000 | chrome.exe | 142.250.181.237:443 | accounts.google.com | Google Inc. | US | suspicious |
1000 | chrome.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1000 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1000 | chrome.exe | 142.250.185.206:443 | apis.google.com | Google Inc. | US | whitelisted |
1000 | chrome.exe | 142.250.186.78:443 | feedproxy.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
feedproxy.google.com |
| whitelisted |
accounts.google.com |
| shared |
ccmun.org |
| unknown |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |