| File name: | Lockbit4.0.exe |
| Full analysis: | https://app.any.run/tasks/b22f64ef-20de-4535-9da4-435646423fee |
| Verdict: | Malicious activity |
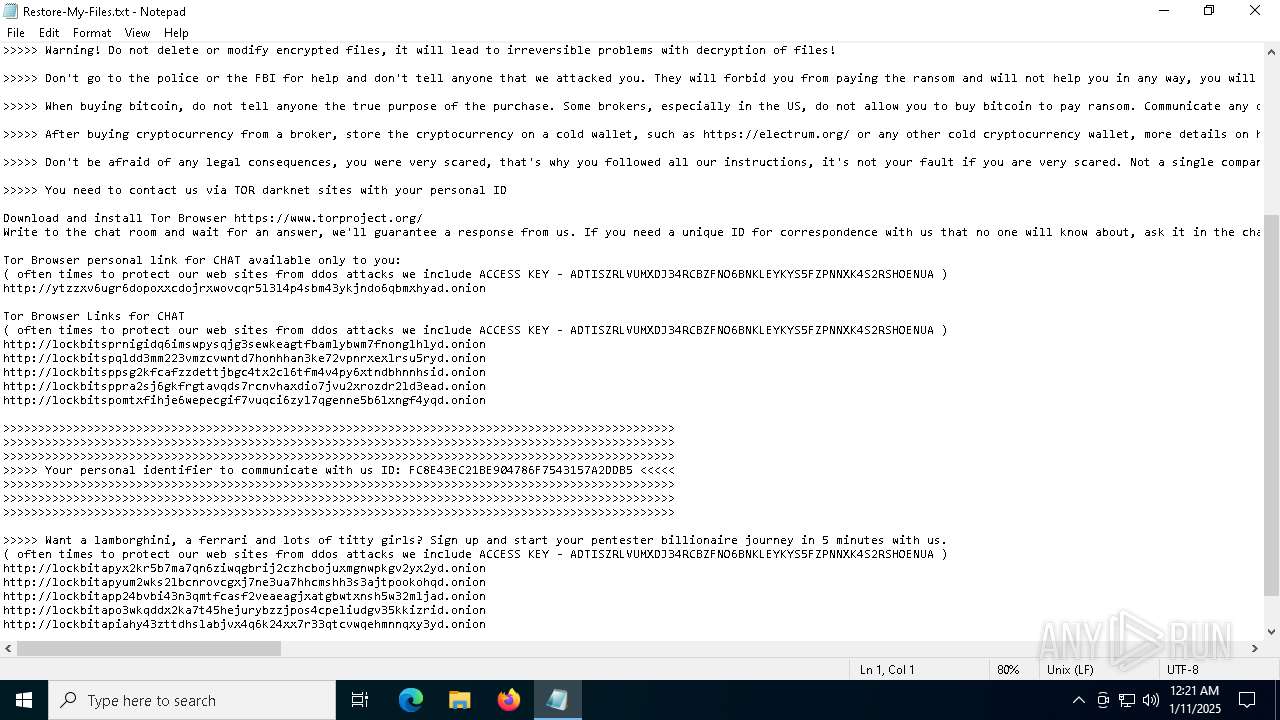
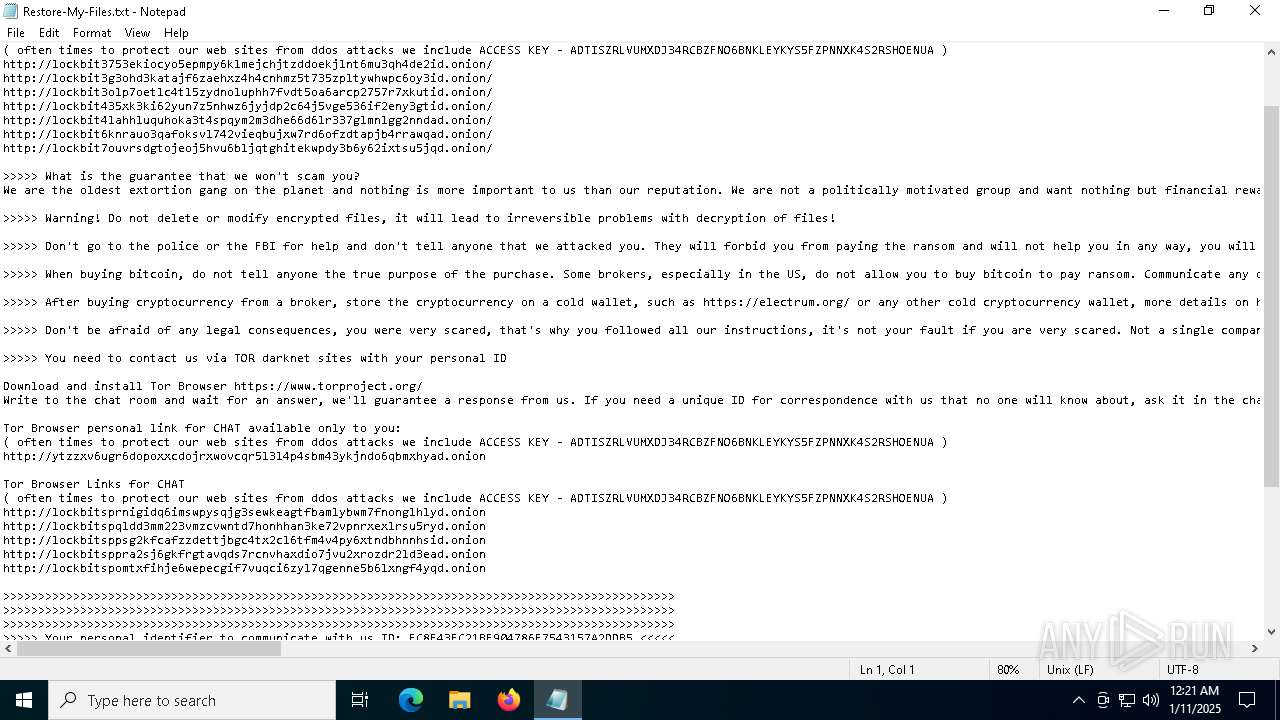
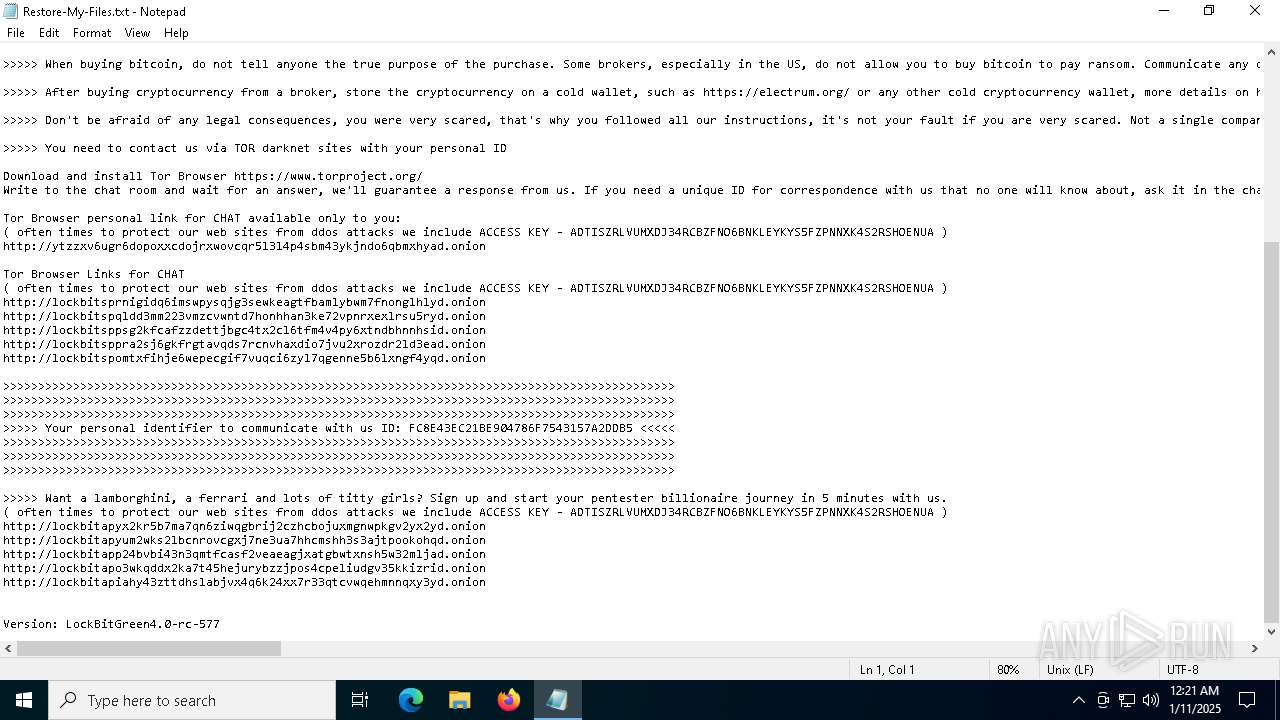
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | January 11, 2025, 00:20:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | C5CC3C5CEF6B382568A54F579B2965FF |
| SHA1: | E85B5BF2FD1EA0D5D71841F2CC8D46FC2055C22B |
| SHA256: | 48E2033A286775C3419BEA8702A717DE0B2AAF1E737EF0E6B3BF31EF6AE00EB5 |
| SSDEEP: | 1536:yuf4ADKKR9Anq2PMNGszIkL/n+mq/vylLa3/PgcoYv/sjEmM54kXQB:yuf4cKi9Aq2PMU5kL/n+tESgczEjRMc |
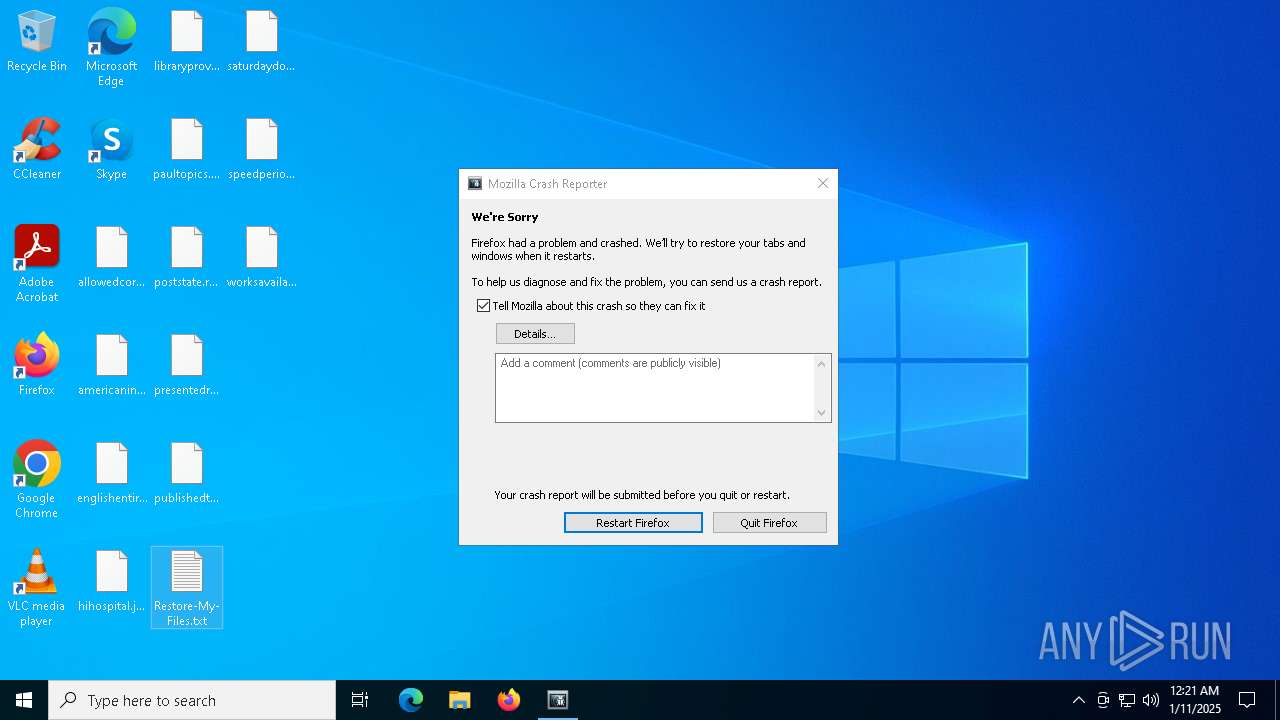
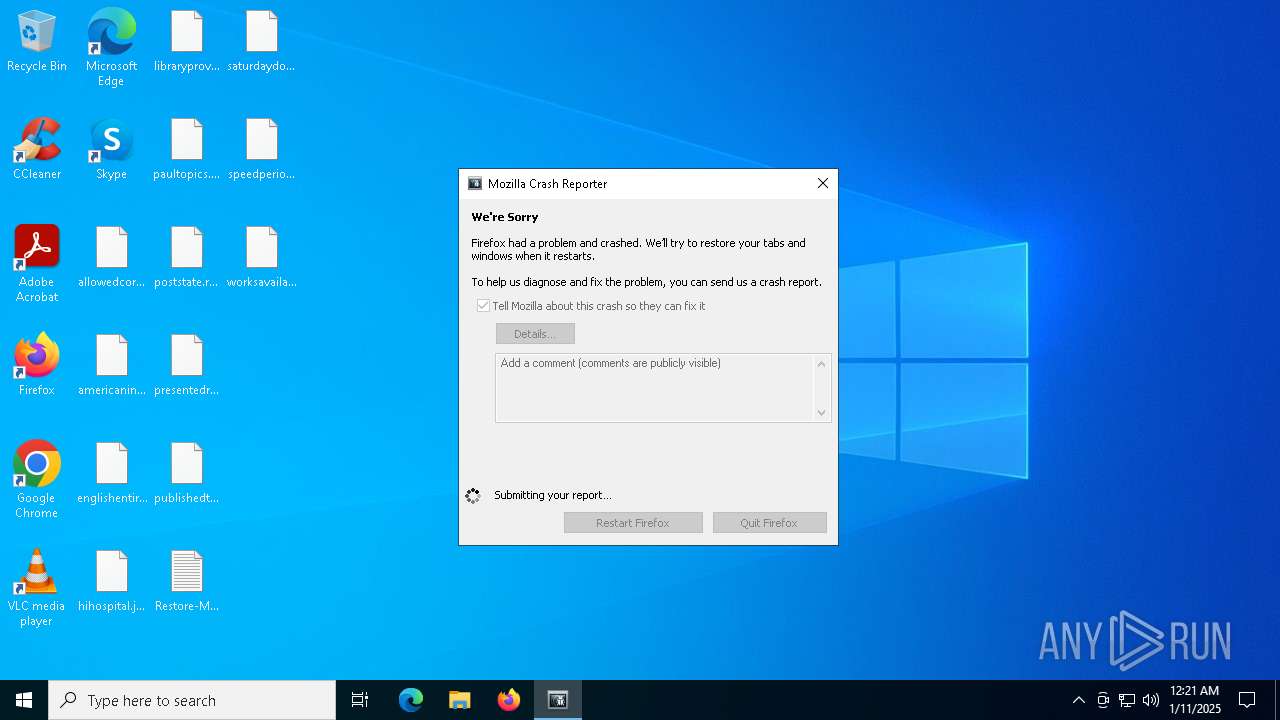
MALICIOUS
LOCKBIT has been found (auto)
- Lockbit4.0.exe (PID: 6340)
RANSOMWARE has been detected
- Lockbit4.0.exe (PID: 6340)
Steals credentials from Web Browsers
- Lockbit4.0.exe (PID: 6340)
Renames files like ransomware
- Lockbit4.0.exe (PID: 6340)
Actions looks like stealing of personal data
- Lockbit4.0.exe (PID: 6340)
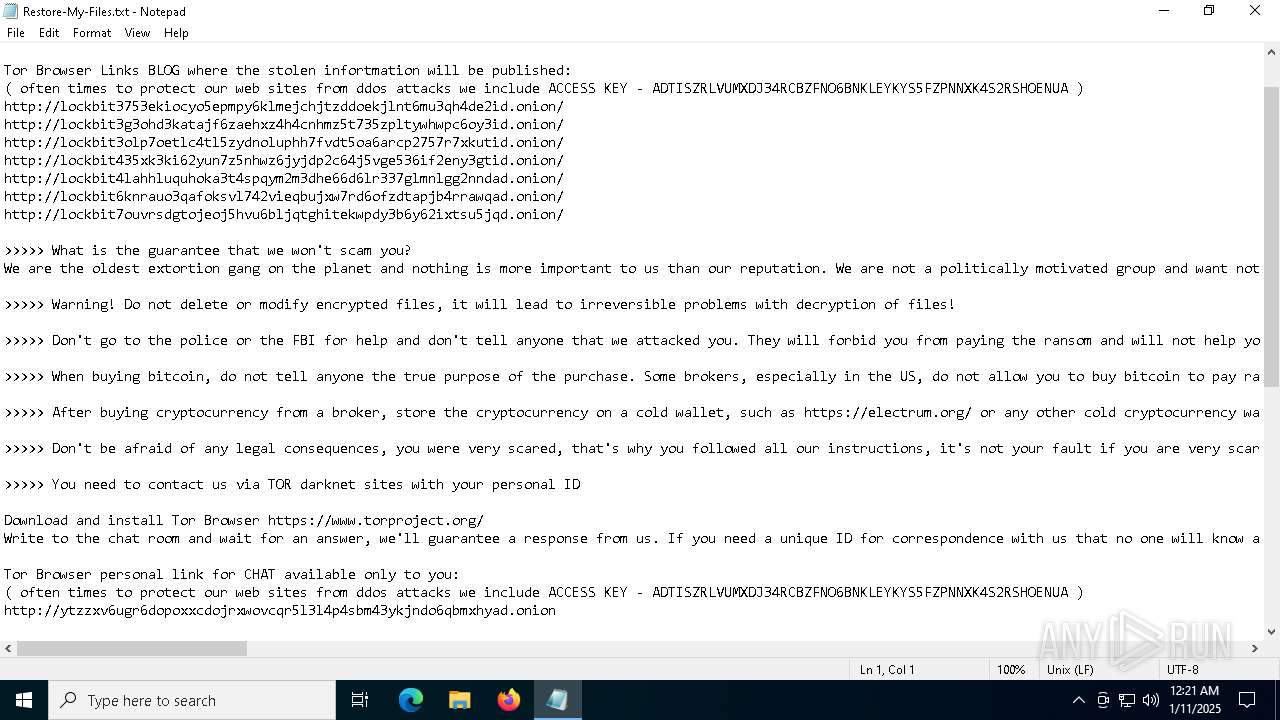
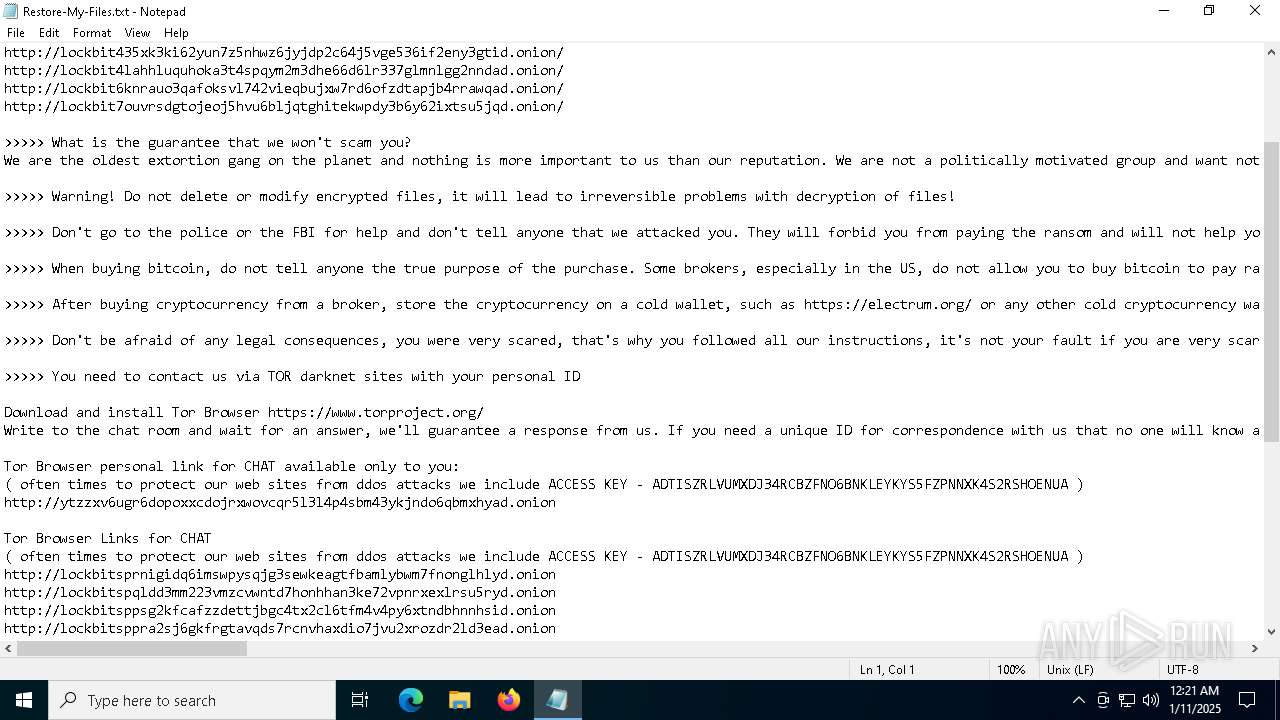
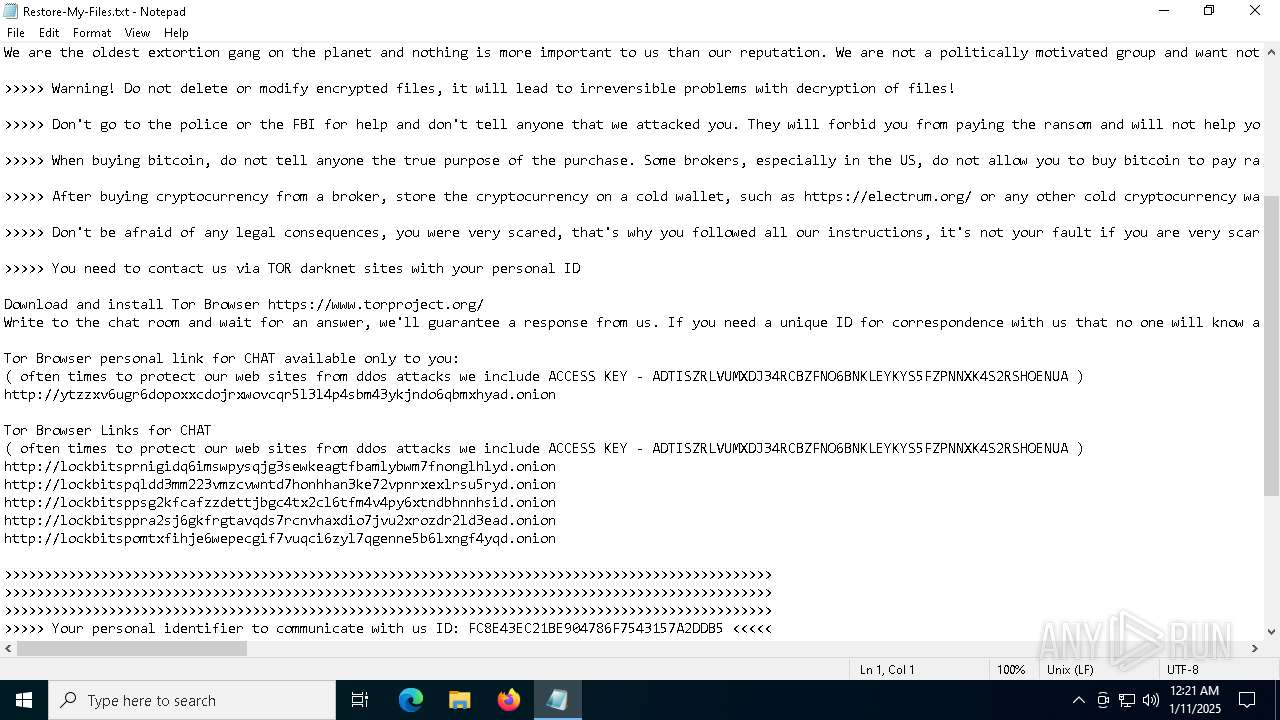
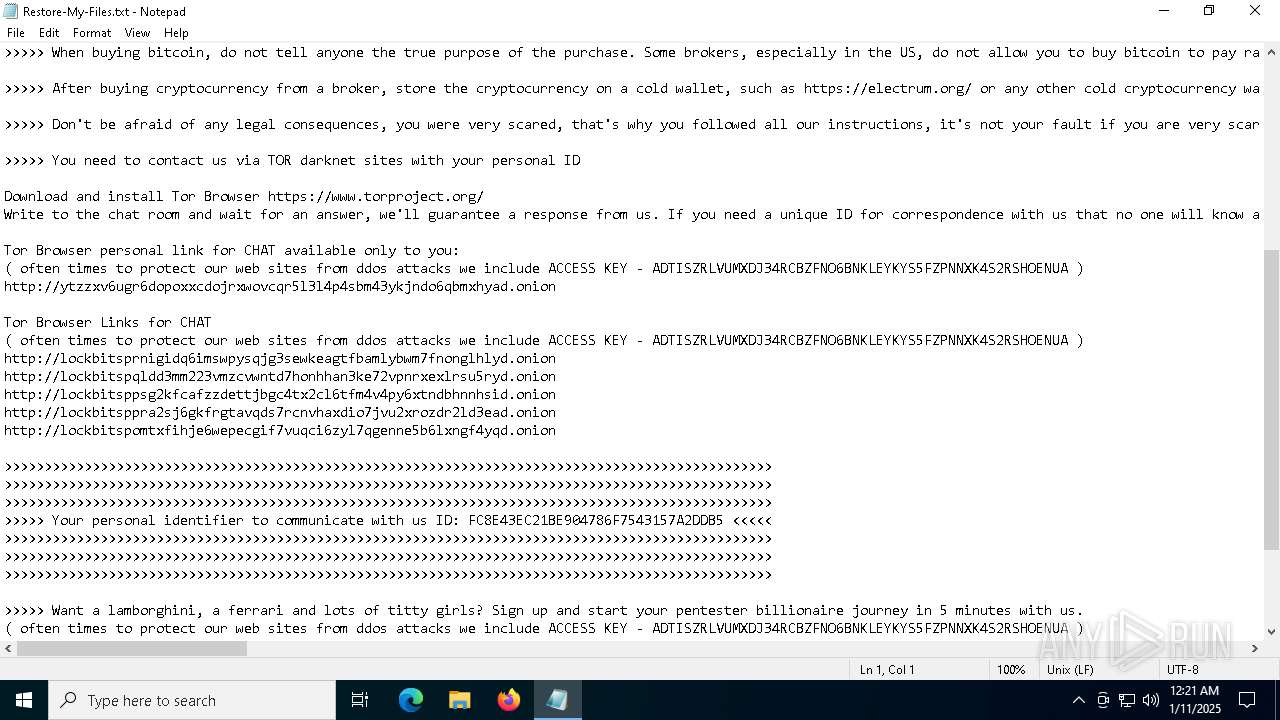
Drops known malicious image
- Lockbit4.0.exe (PID: 6340)
SUSPICIOUS
Creates file in the systems drive root
- Lockbit4.0.exe (PID: 6340)
Executable content was dropped or overwritten
- Lockbit4.0.exe (PID: 6340)
INFO
Creates files in the program directory
- Lockbit4.0.exe (PID: 6340)
Reads the computer name
- Lockbit4.0.exe (PID: 6340)
Creates files or folders in the user directory
- Lockbit4.0.exe (PID: 6340)
Checks supported languages
- Lockbit4.0.exe (PID: 6340)
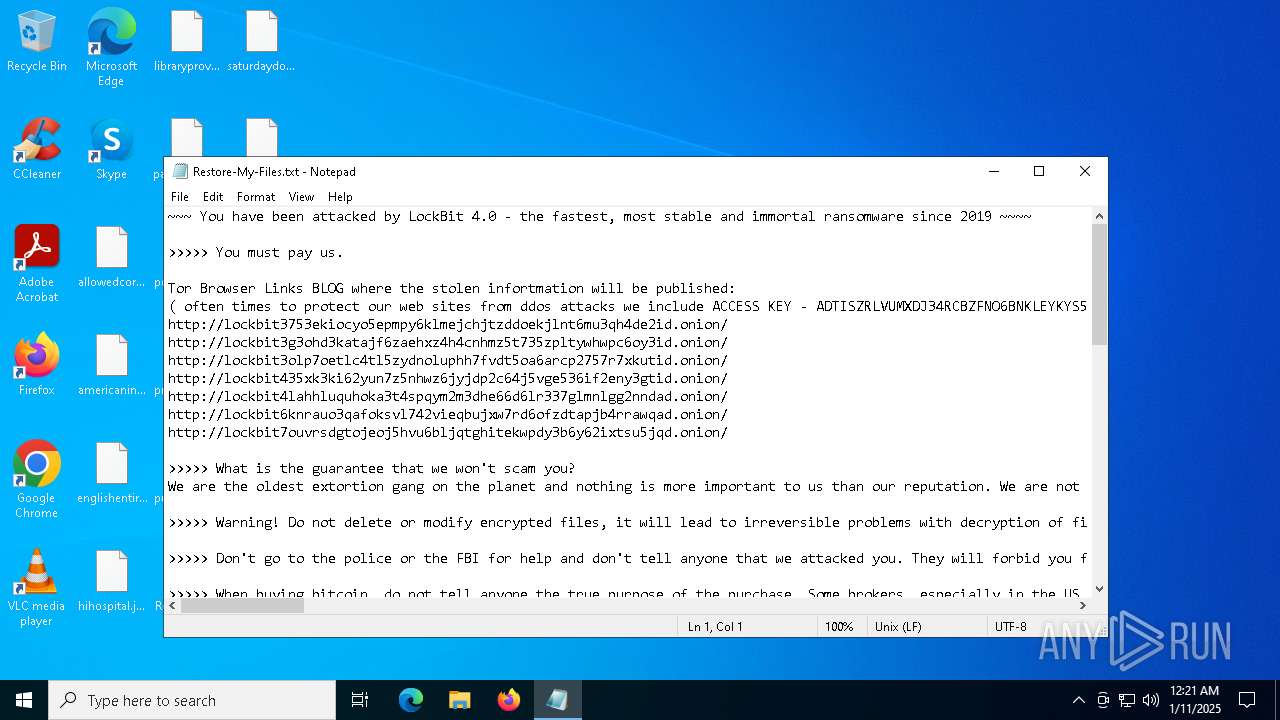
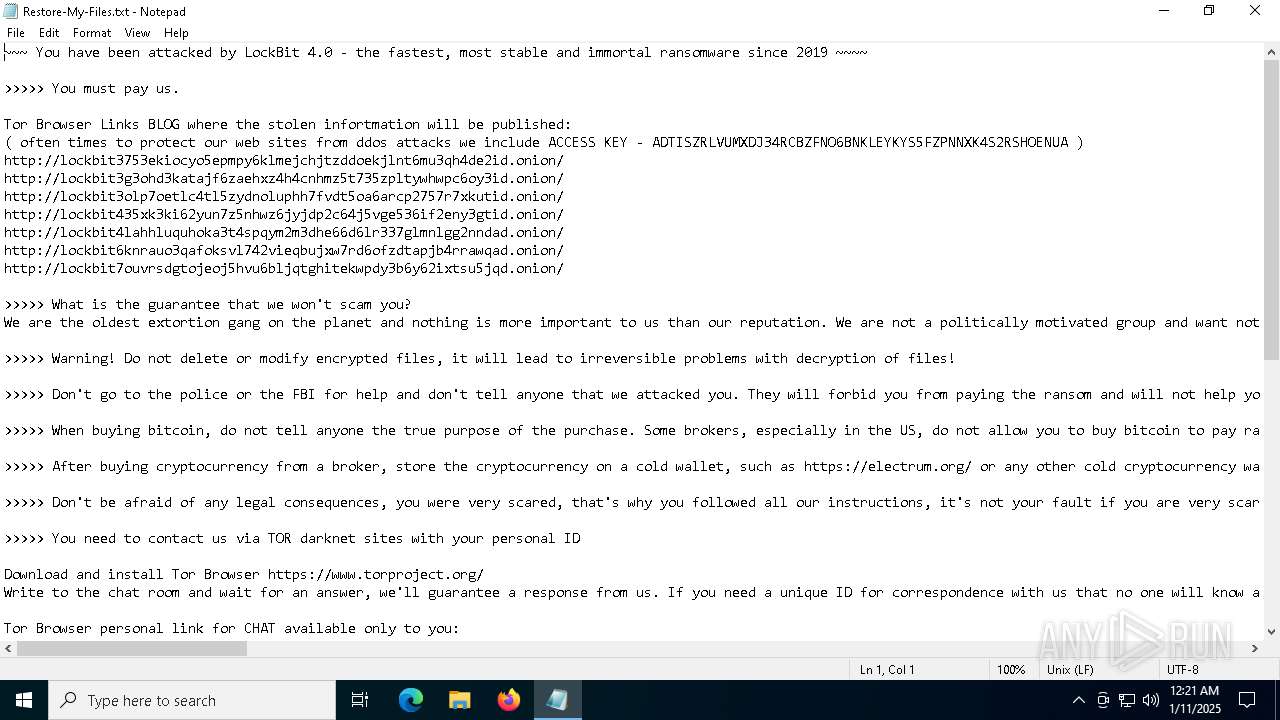
Manual execution by a user
- notepad.exe (PID: 2612)
Create files in a temporary directory
- Lockbit4.0.exe (PID: 6340)
Drops encrypted VBS script (Microsoft Script Encoder)
- Lockbit4.0.exe (PID: 6340)
The sample compiled with english language support
- Lockbit4.0.exe (PID: 6340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 61440 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 757760 |
| EntryPoint: | 0xc8a10 |
| OSVersion: | - |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
131
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2612 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\Restore-My-Files.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6340 | "C:\Users\admin\AppData\Local\Temp\Lockbit4.0.exe" | C:\Users\admin\AppData\Local\Temp\Lockbit4.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
Total events
501
Read events
501
Write events
0
Delete events
0
Modification events
Executable files
8
Suspicious files
614
Text files
2 130
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | Lockbit4.0.exe | — | ||
MD5:— | SHA256:— | |||
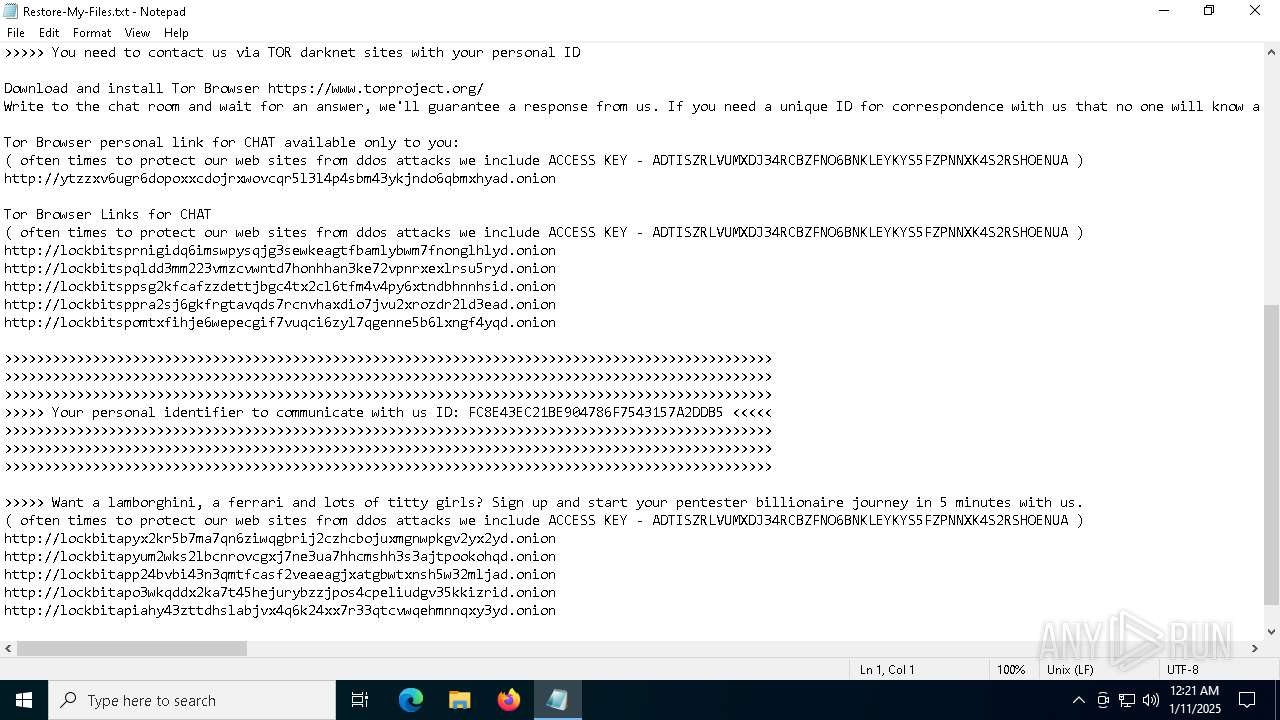
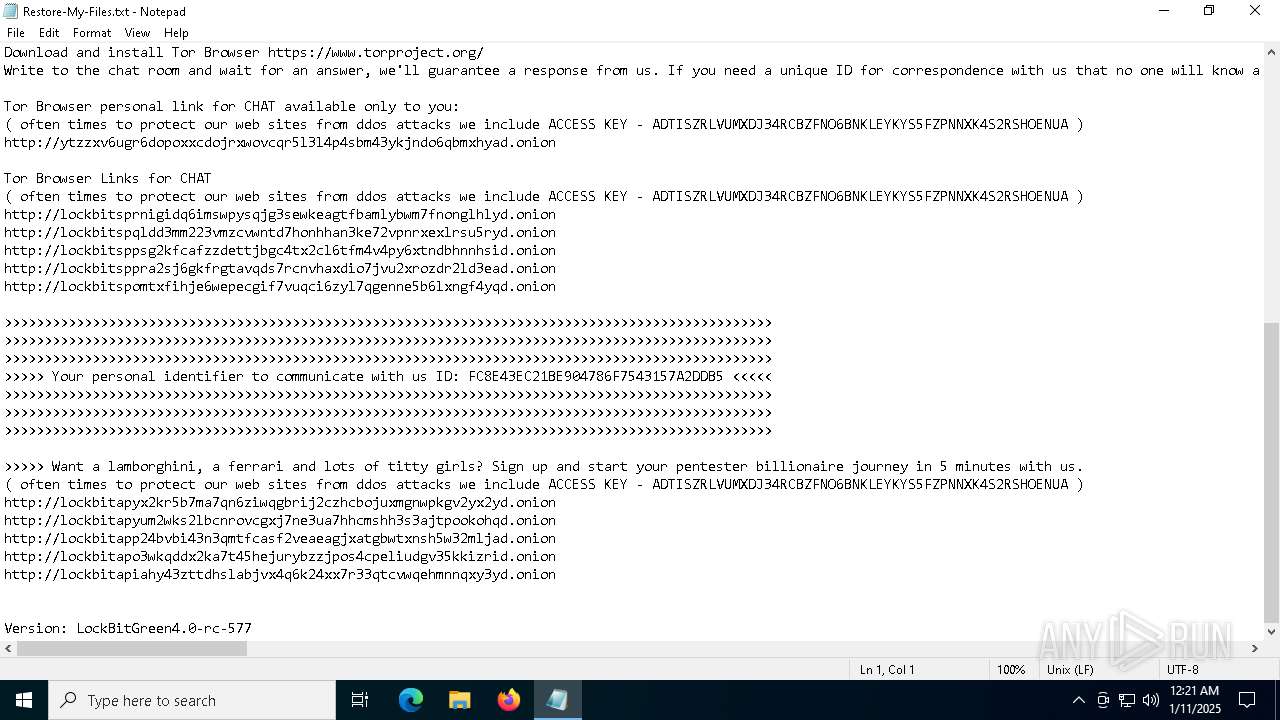
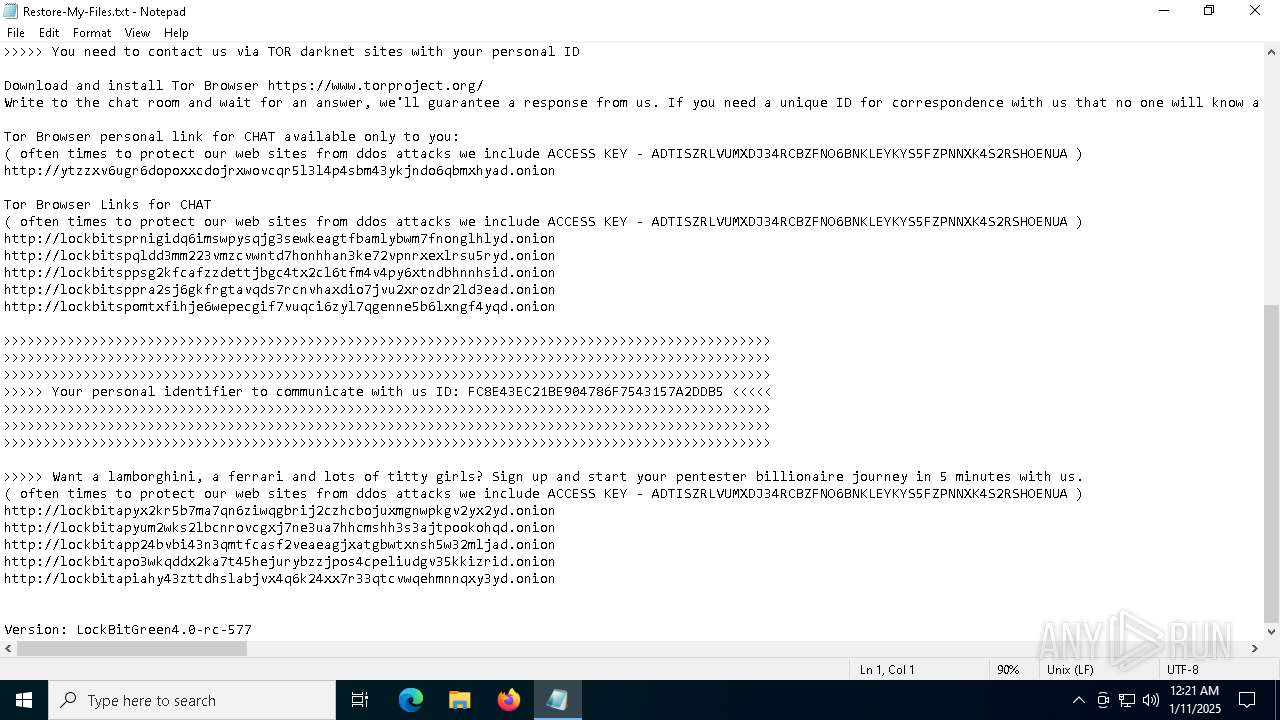
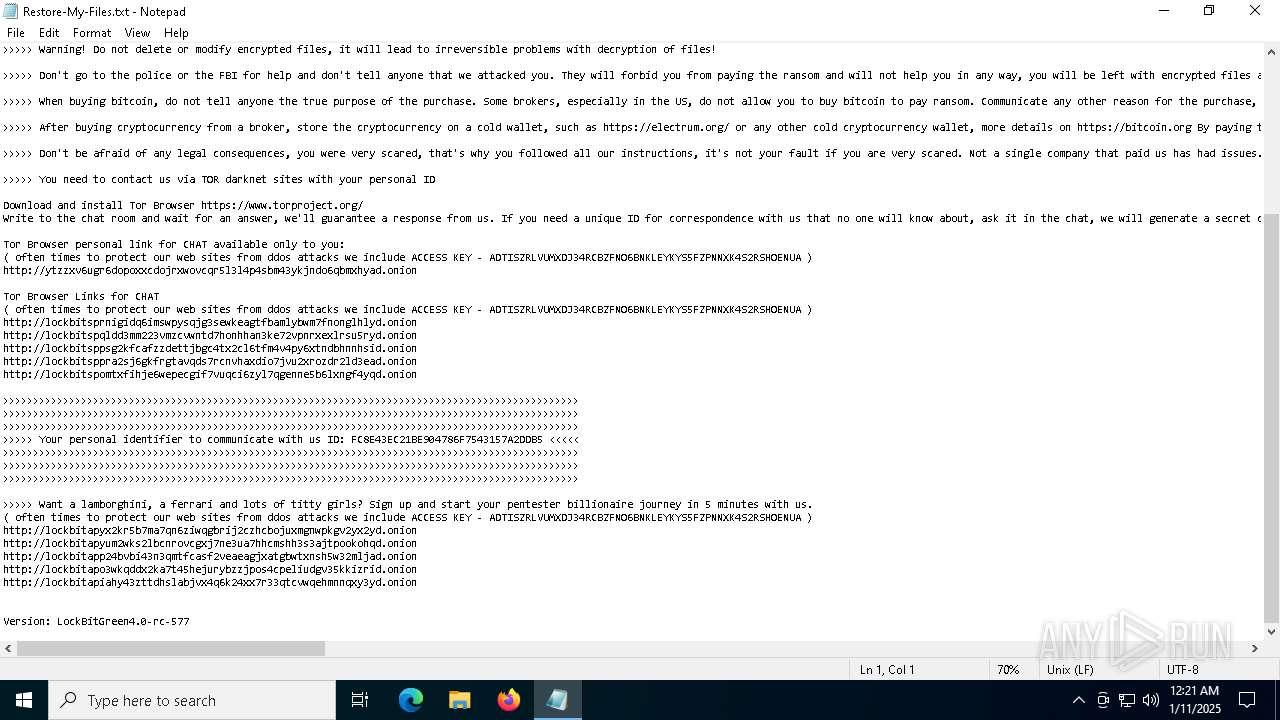
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Google\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\FileZilla FTP Client\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\CCleaner\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\CUAssistant\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\ProgramData\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\ProgramData\ntuser.pol.8153d113655b | binary | |
MD5:41E7A1F412418B73E9591F9124137457 | SHA256:47AAFBCE683791DE4E8A2398459AC4BC63533B2F628D001C3F646C7F6340D4A0 | |||
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
| 6340 | Lockbit4.0.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Restore-My-Files.txt | text | |
MD5:74A77BD81FA83B32B595EAFA20C978EC | SHA256:49CC31E84E5F3CF75DE5D5F58F62AC6C43D9DCA726DFC750593129B730A56616 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
41
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6860 | crashreporter.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
2744 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7052 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6860 | crashreporter.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAEXlo0%2BuXXOKrO9v4Lg2NI%3D | unknown | — | — | whitelisted |
7052 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.130:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3220 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crash-reports.mozilla.com |
| whitelisted |