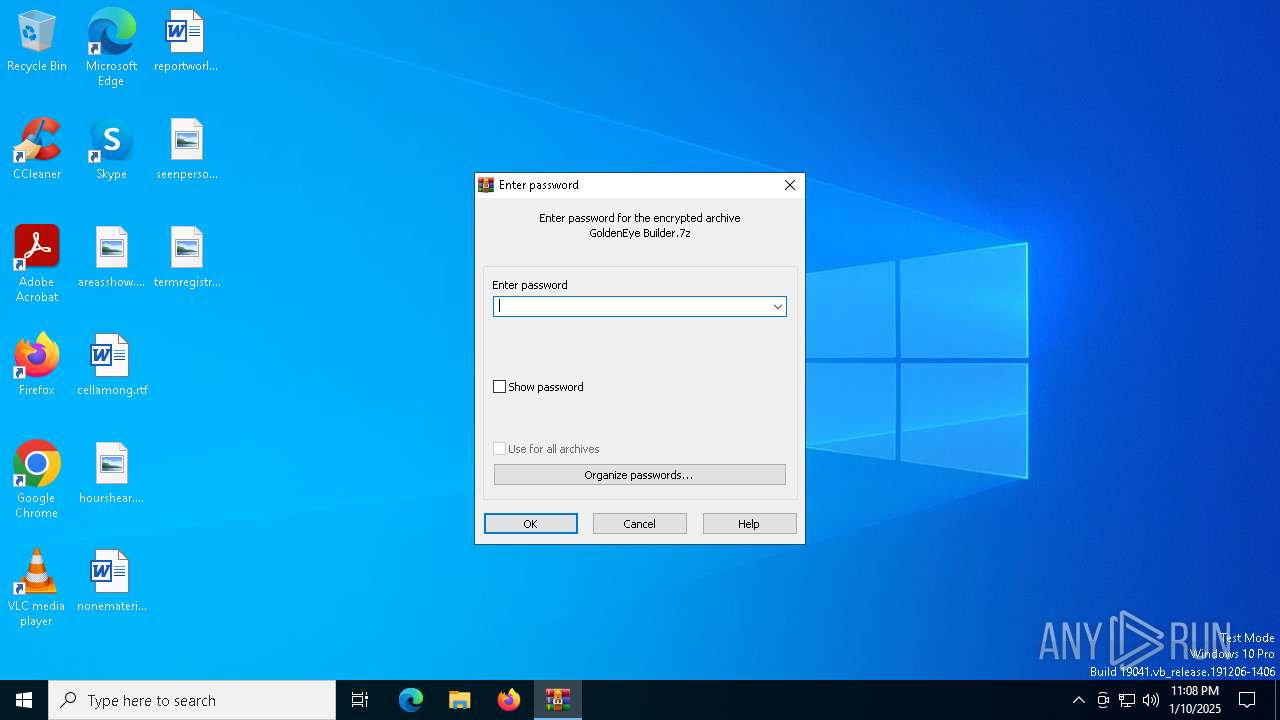
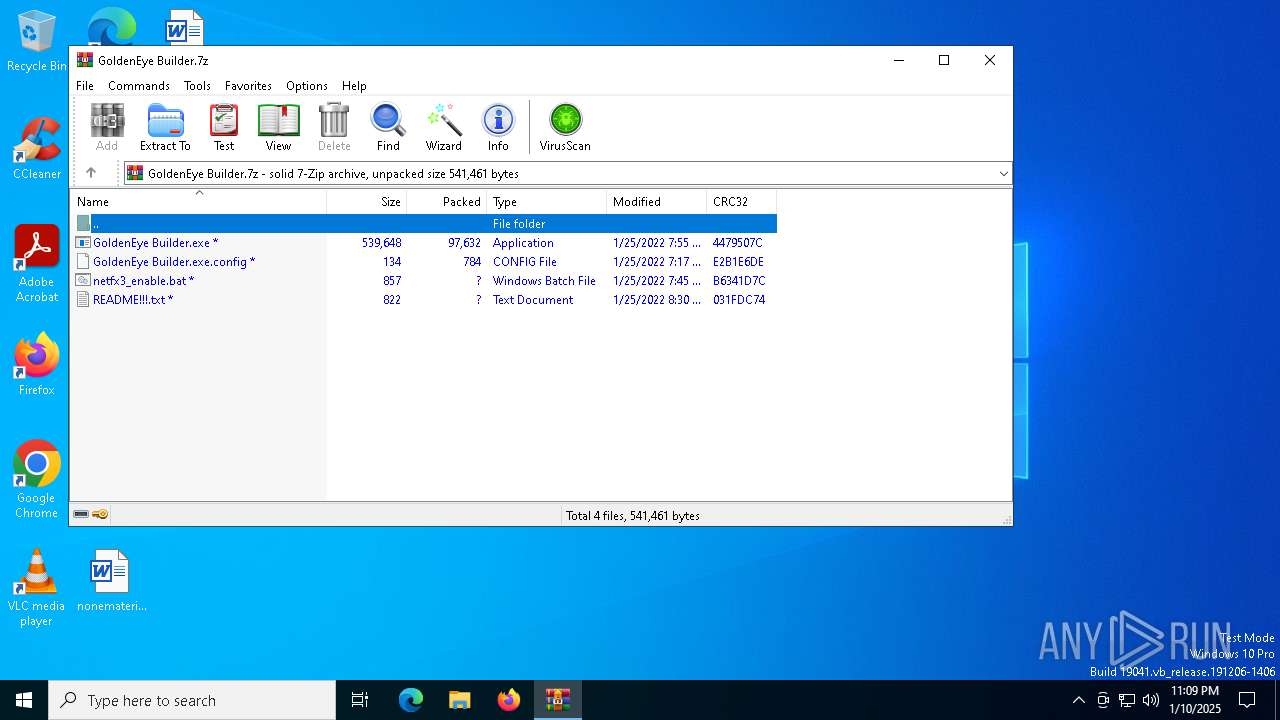
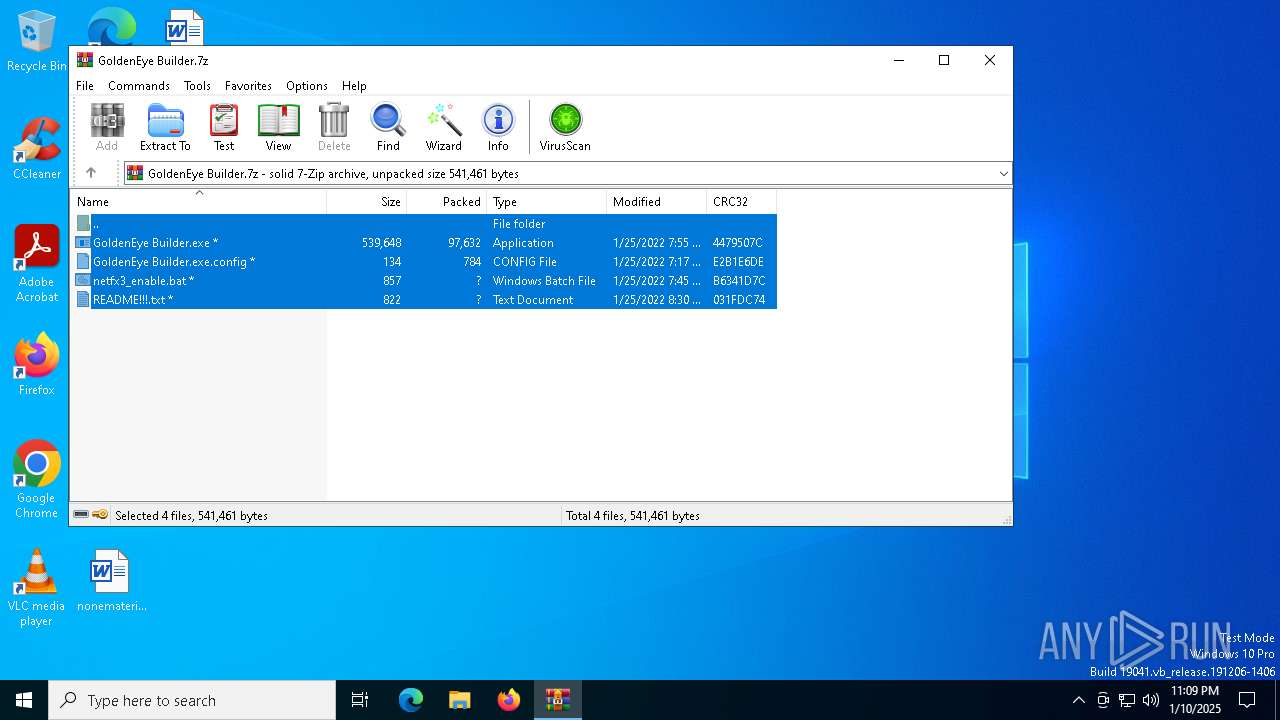
| File name: | GoldenEye Builder.7z |
| Full analysis: | https://app.any.run/tasks/aa9f29b3-79ed-4ac5-8fc6-c1b41748c497 |
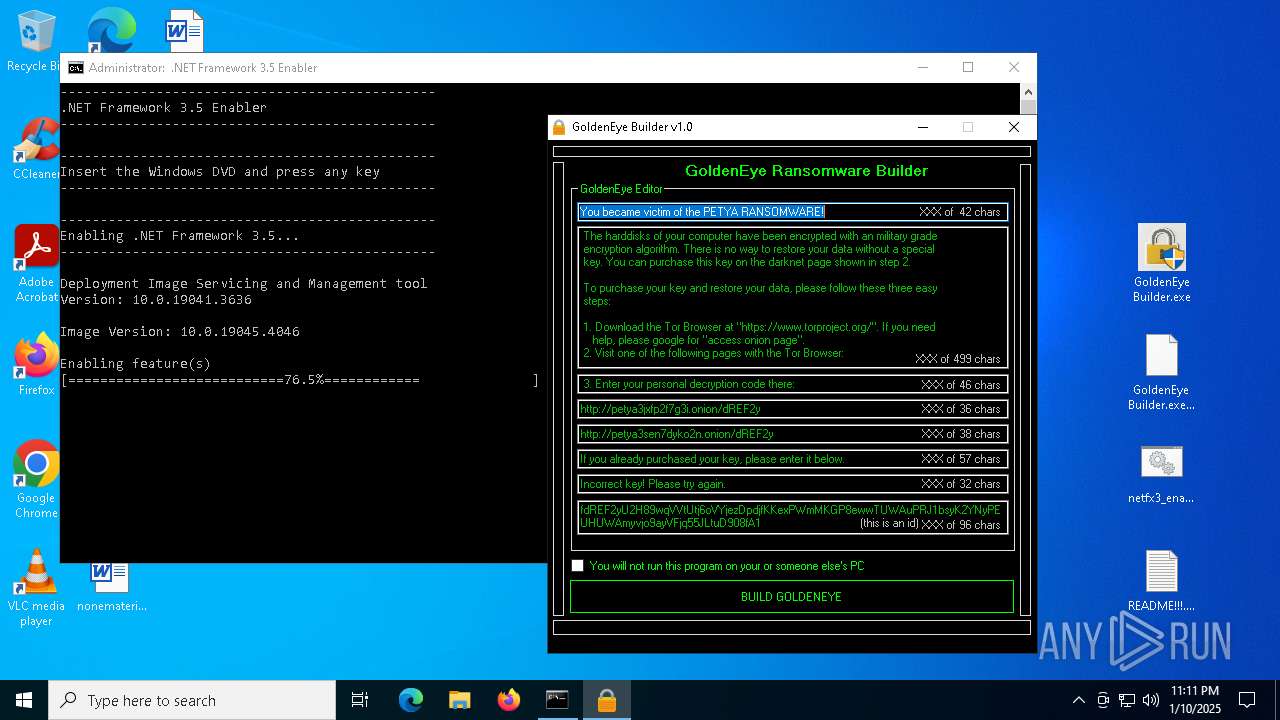
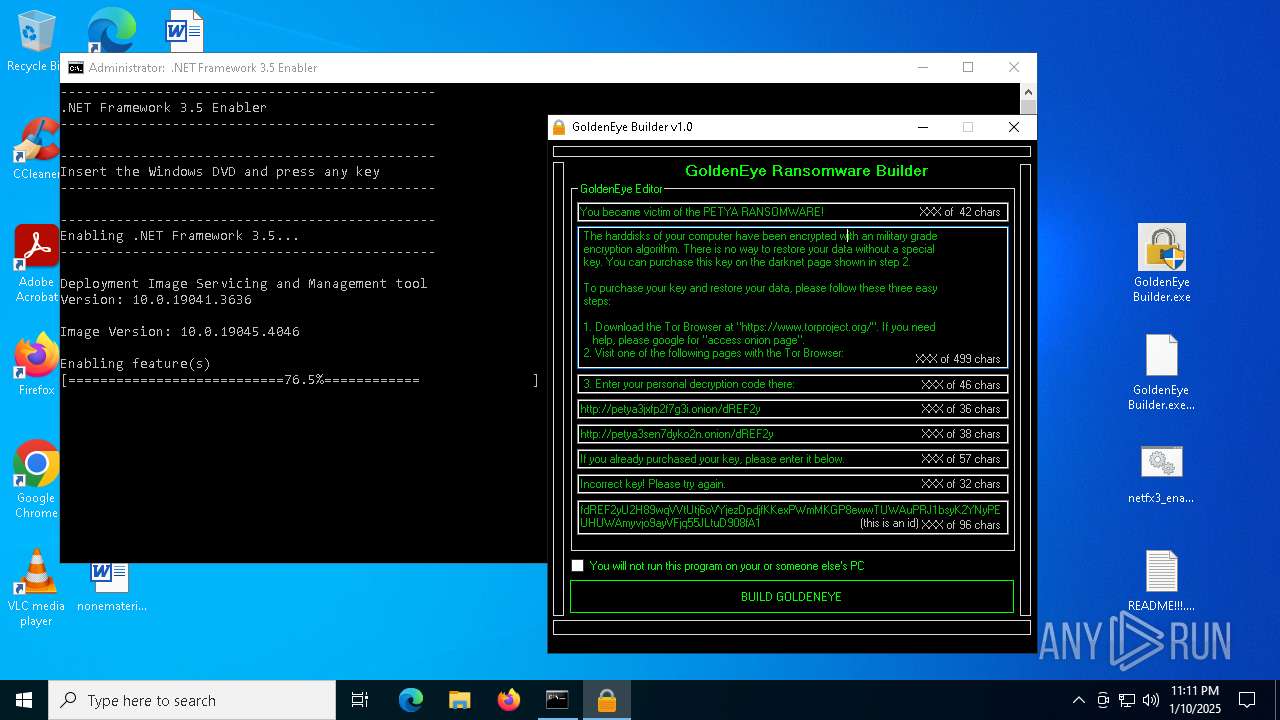
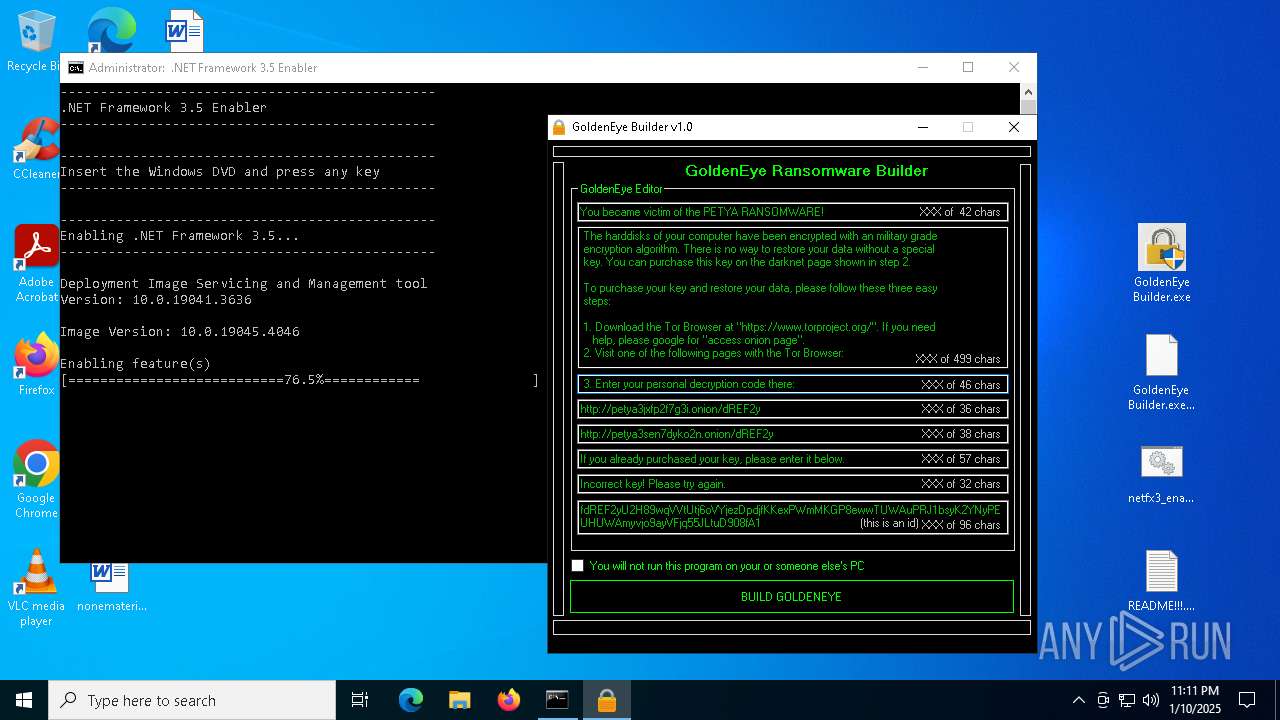
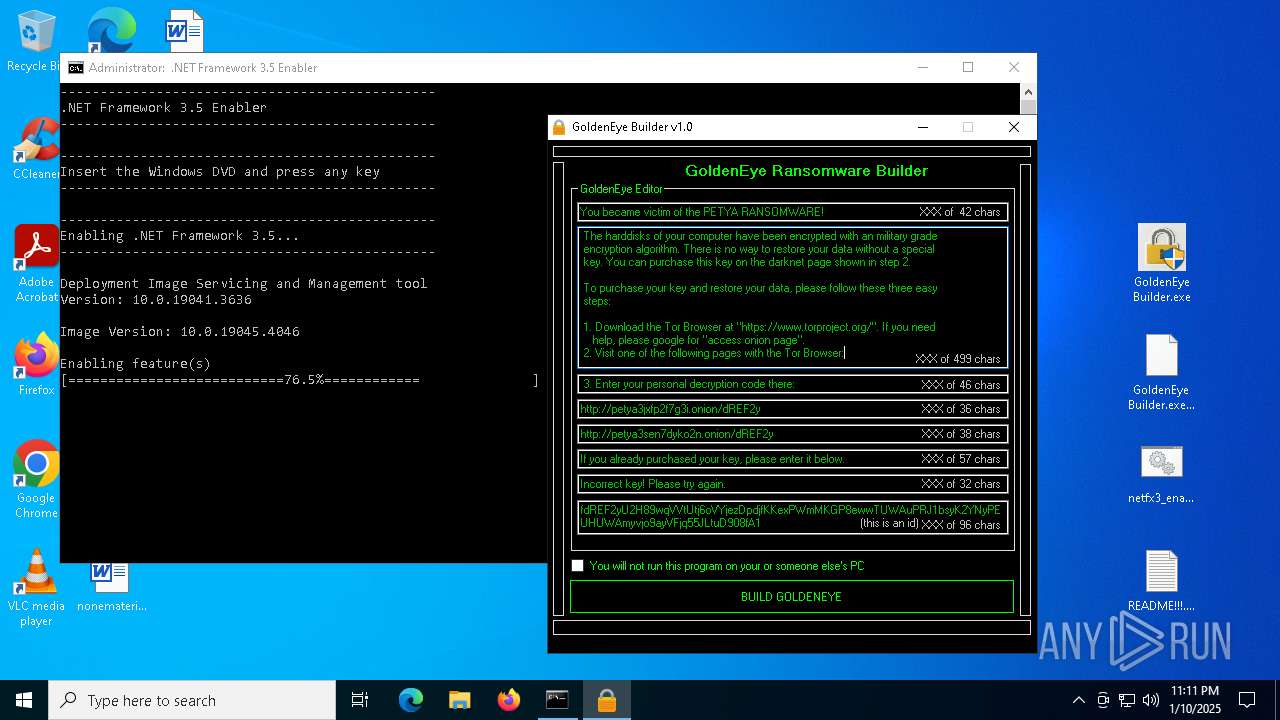
| Verdict: | Malicious activity |
| Analysis date: | January 10, 2025, 23:08:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 4D01DBC86DF141A6E694C059648ACE39 |
| SHA1: | 68A6349C2104CB6E0D042CD1CBA7C6BB0F35B9FF |
| SHA256: | 48DE9BAFD54FED92B7D23E3F59EAEF1071BB0B3DC23B3F59C9547E8967BE3CED |
| SSDEEP: | 3072:m54ojSZlaWnMu8QQKQ7zzs60w+Ctas/WtsAn:m2o2LLTrrQ7zzs60dCtaztN |
MALICIOUS
No malicious indicators.SUSPICIOUS
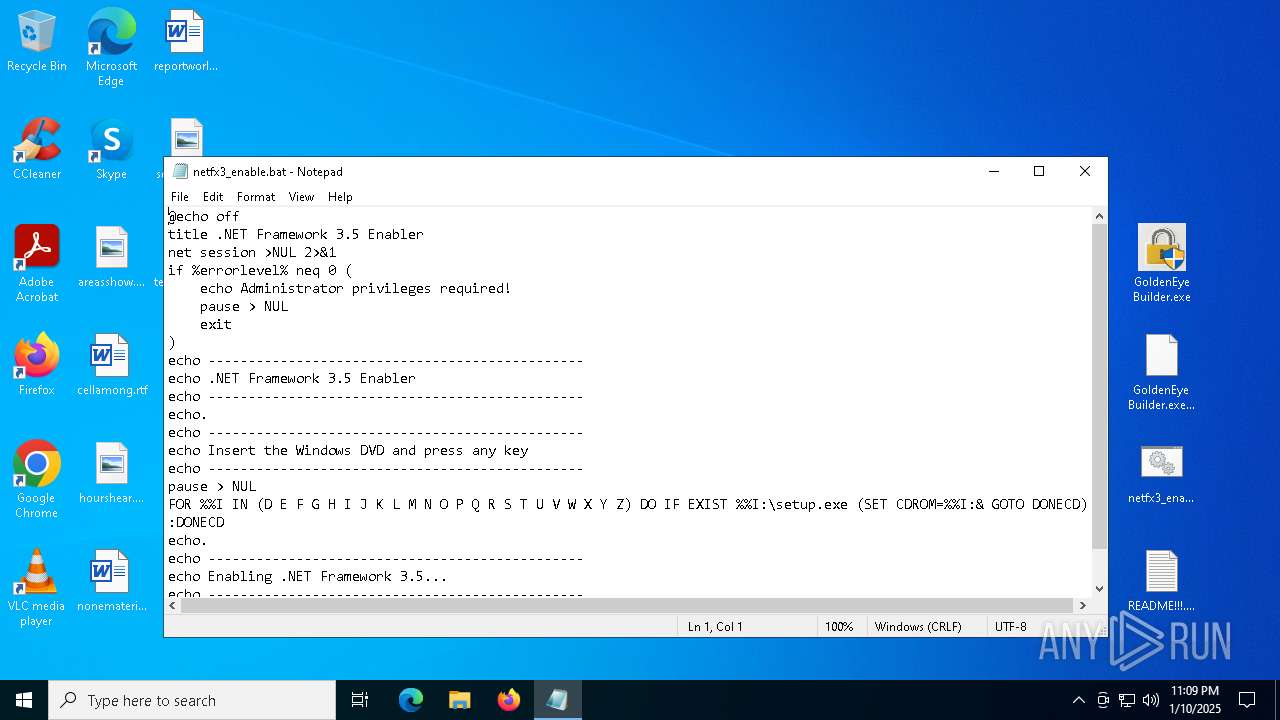
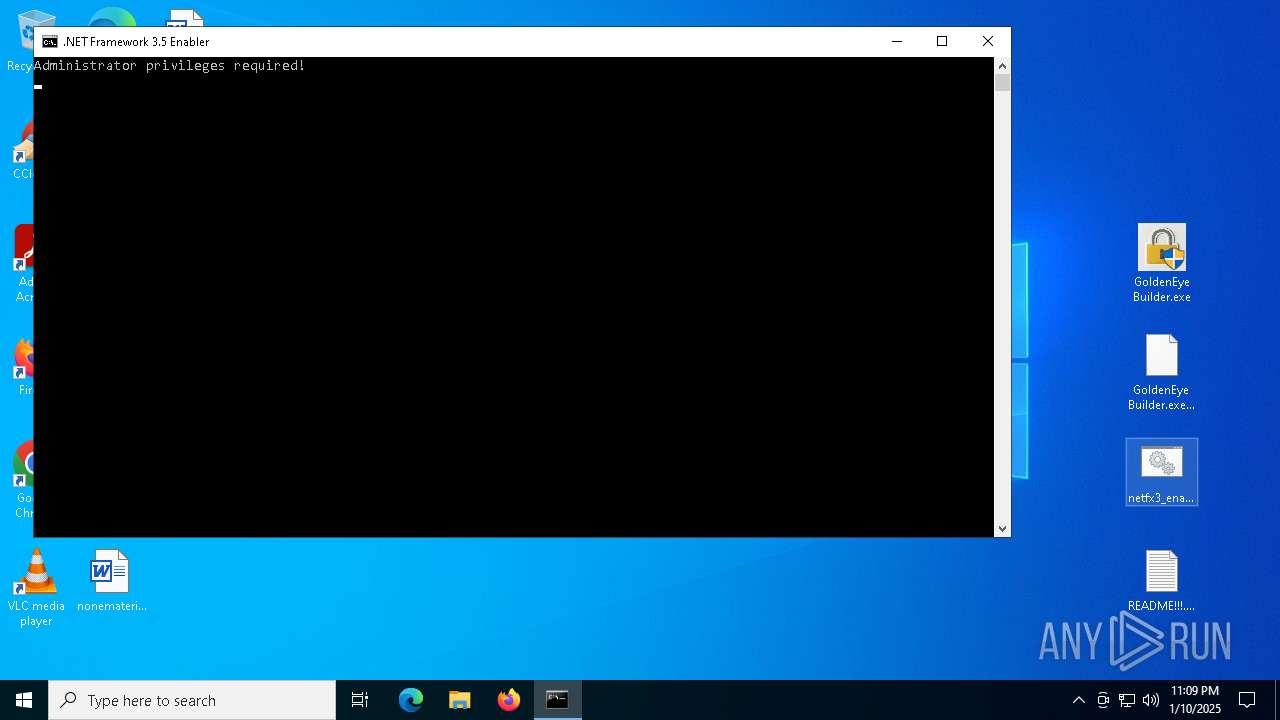
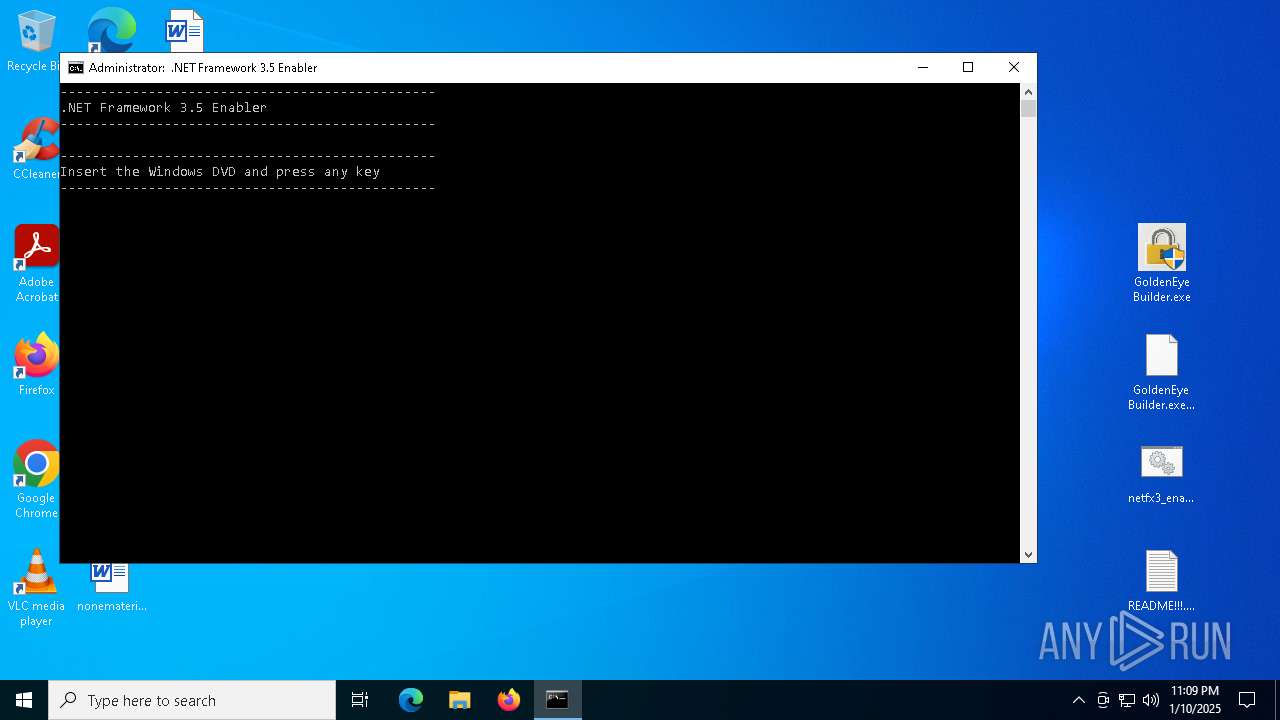
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 3620)
- net.exe (PID: 5788)
- net.exe (PID: 4132)
- cmd.exe (PID: 6092)
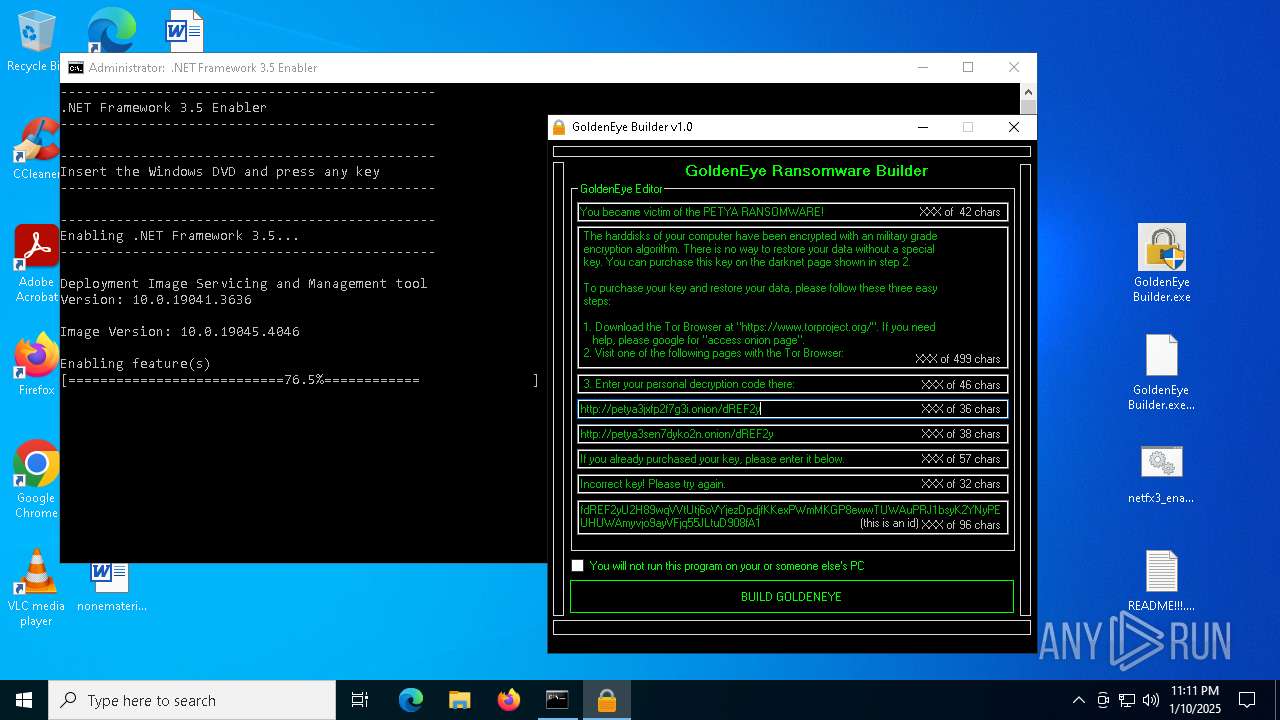
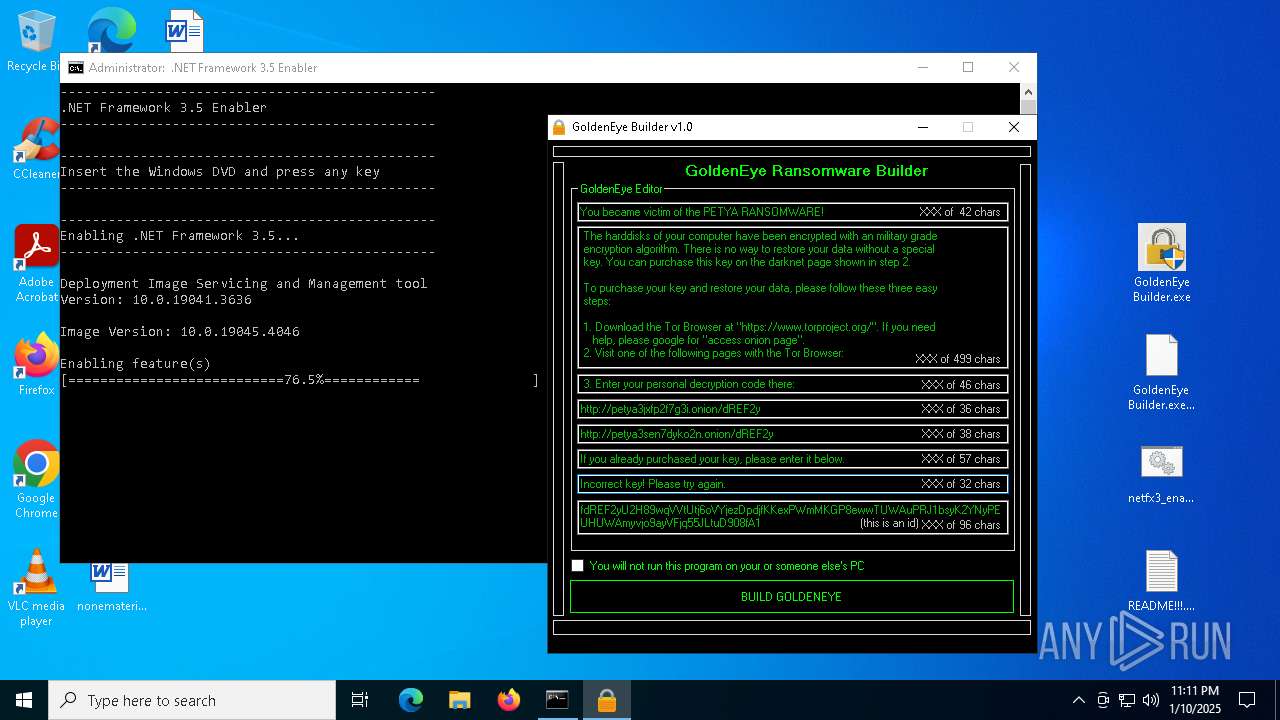
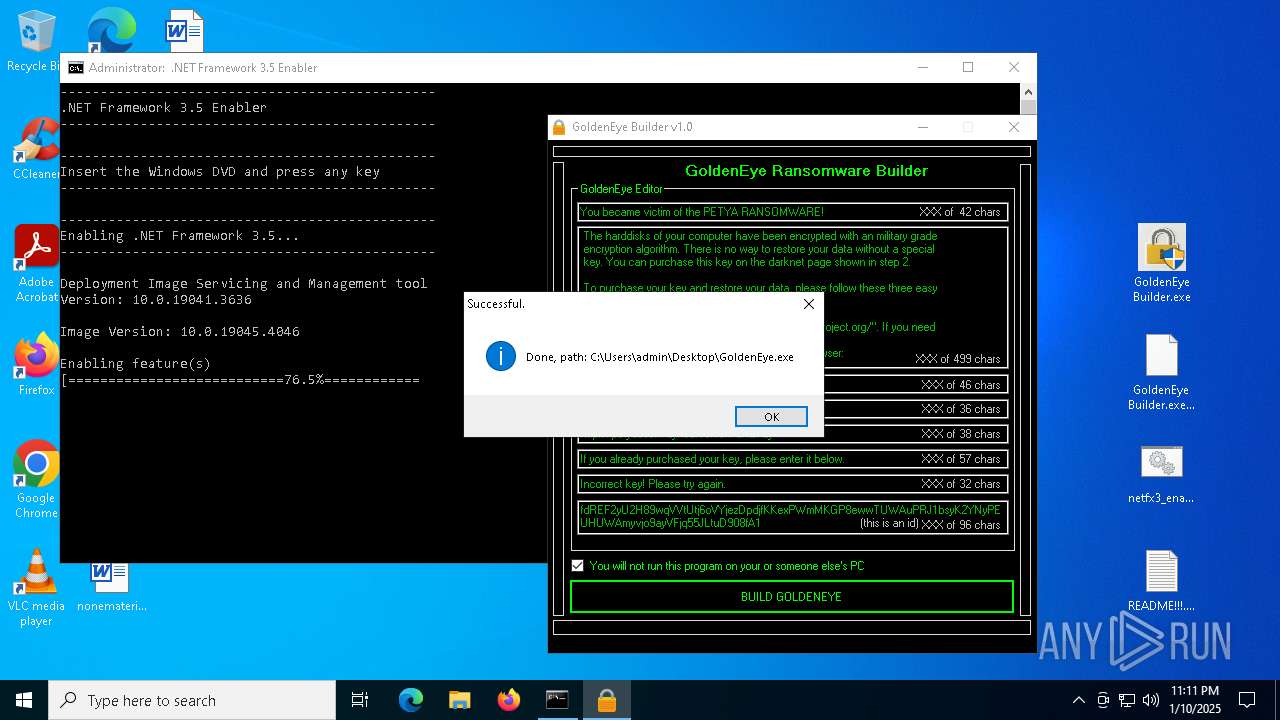
Executable content was dropped or overwritten
- Dism.exe (PID: 3060)
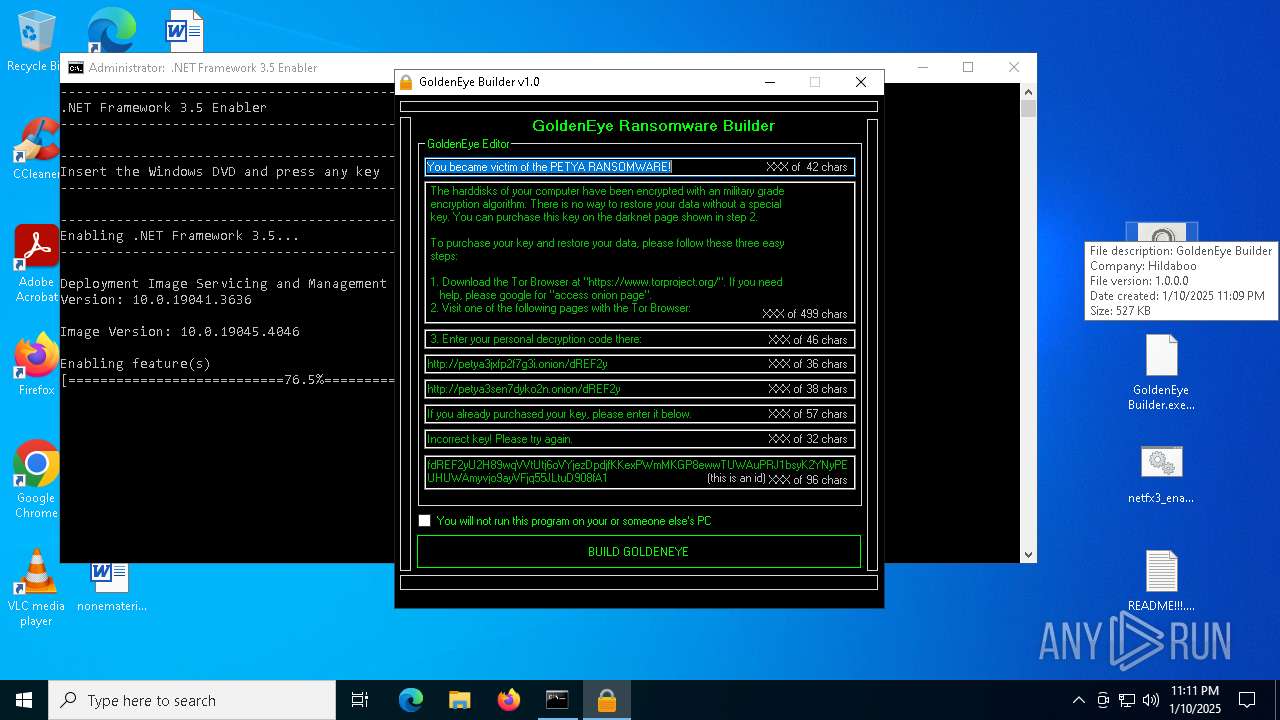
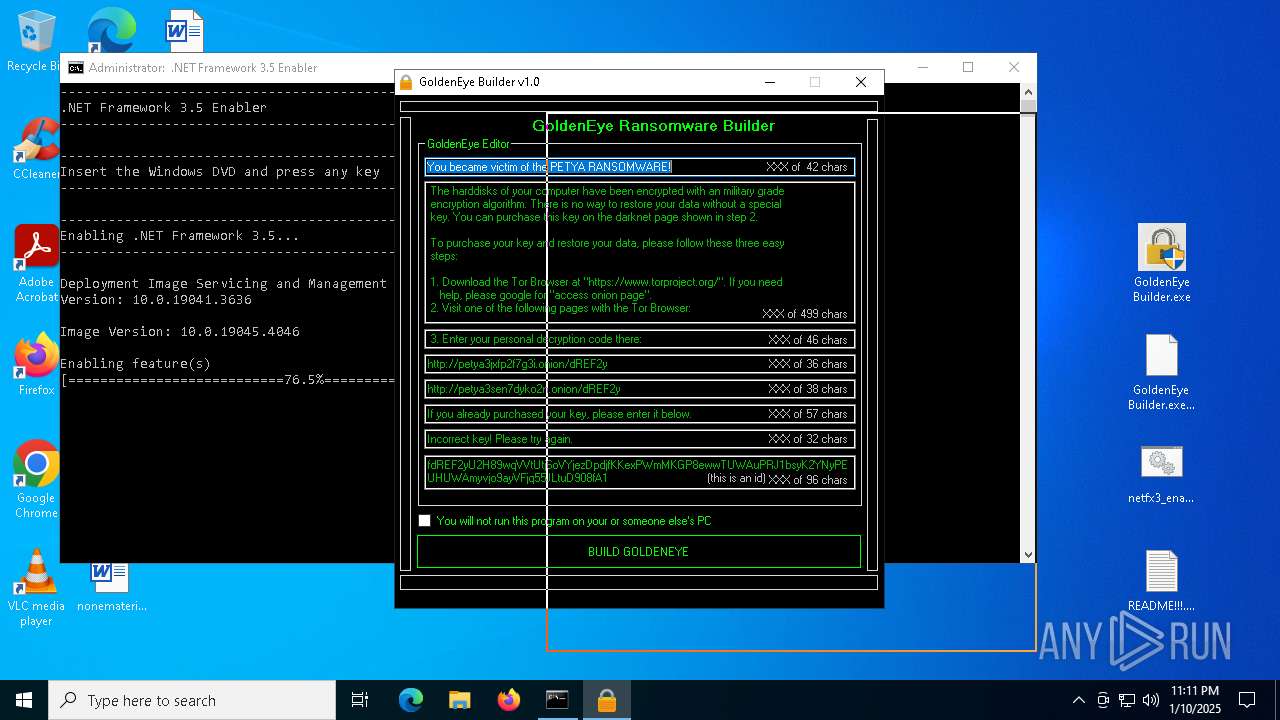
- GoldenEye Builder.exe (PID: 7100)
The process creates files with name similar to system file names
- Dism.exe (PID: 3060)
Searches for installed software
- TiWorker.exe (PID: 2408)
Executes as Windows Service
- VSSVC.exe (PID: 6404)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 4672)
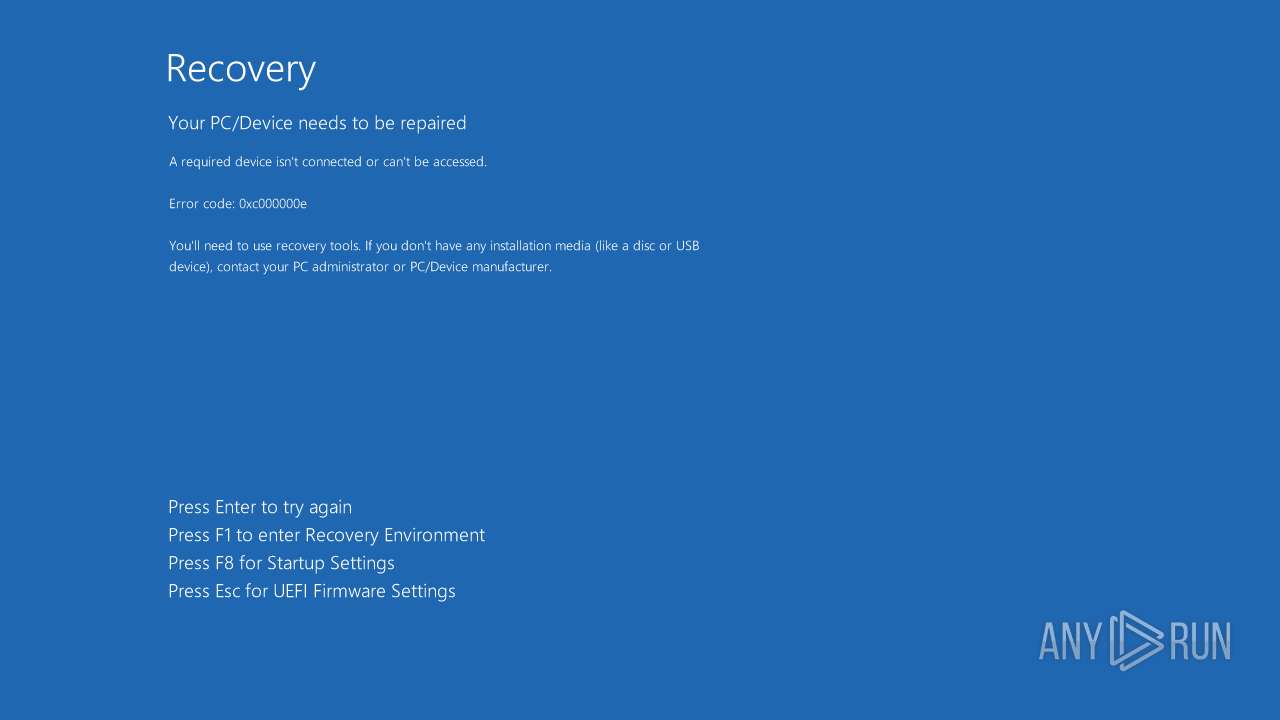
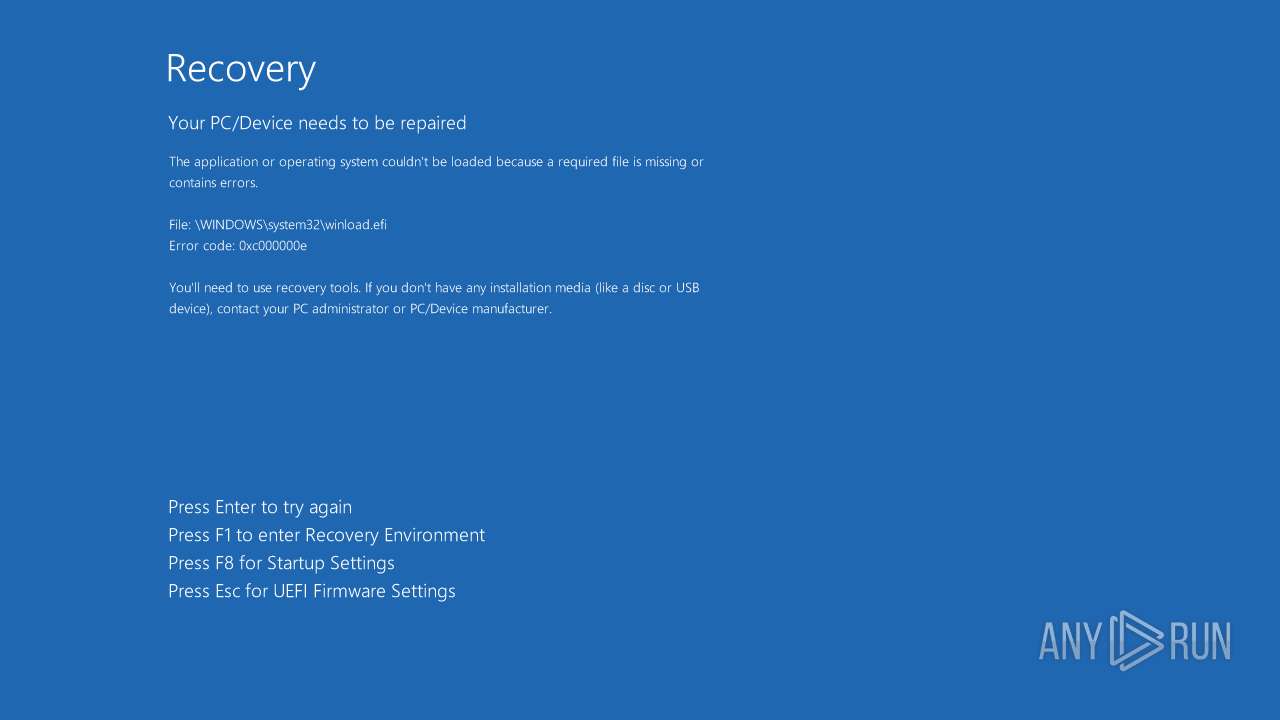
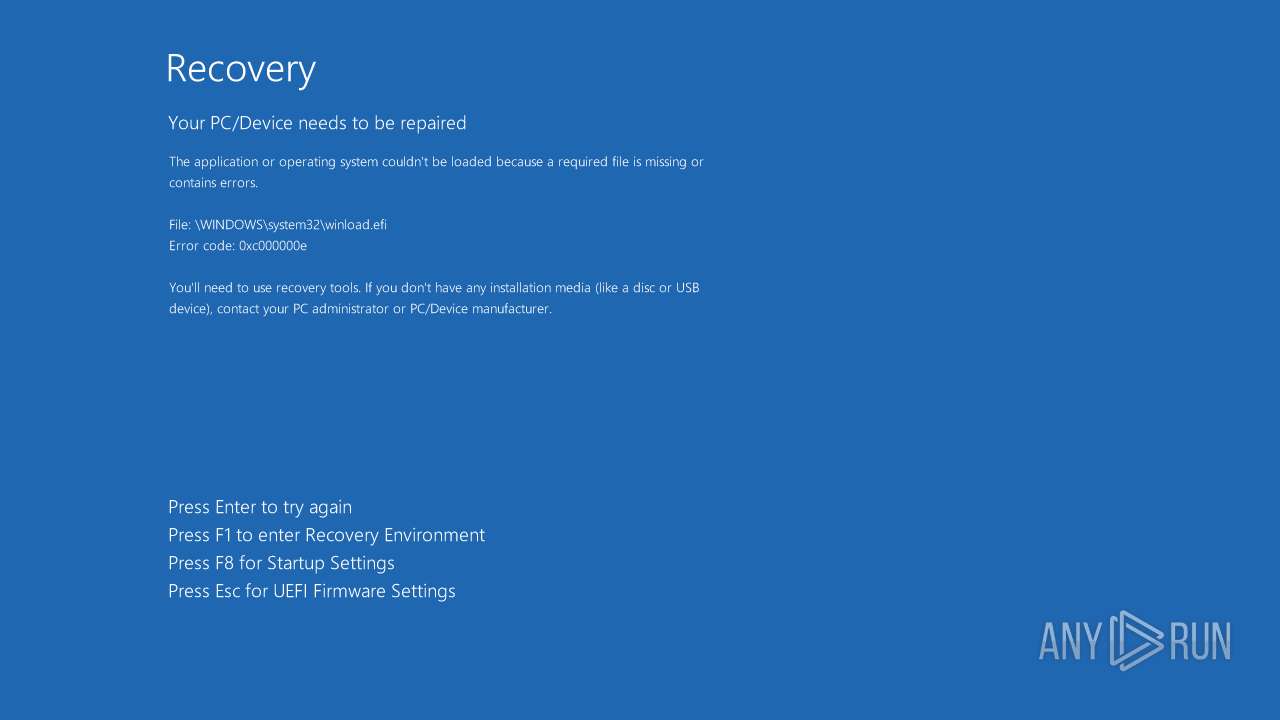
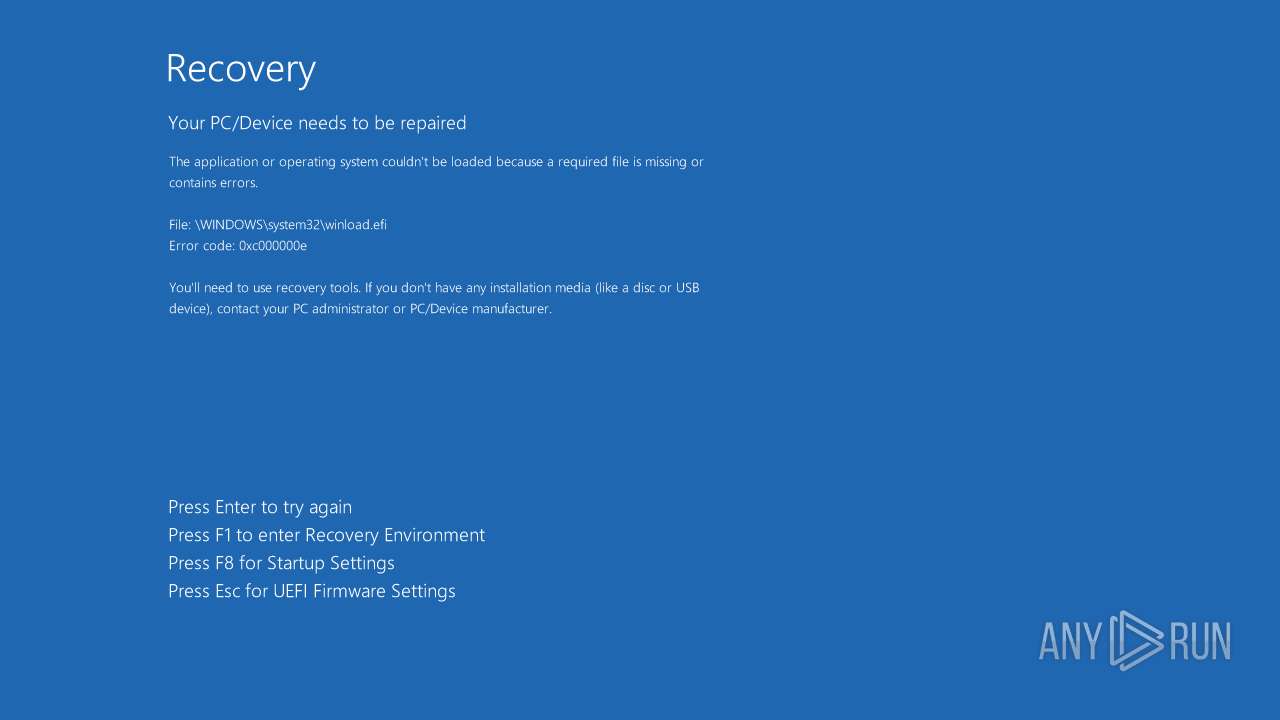
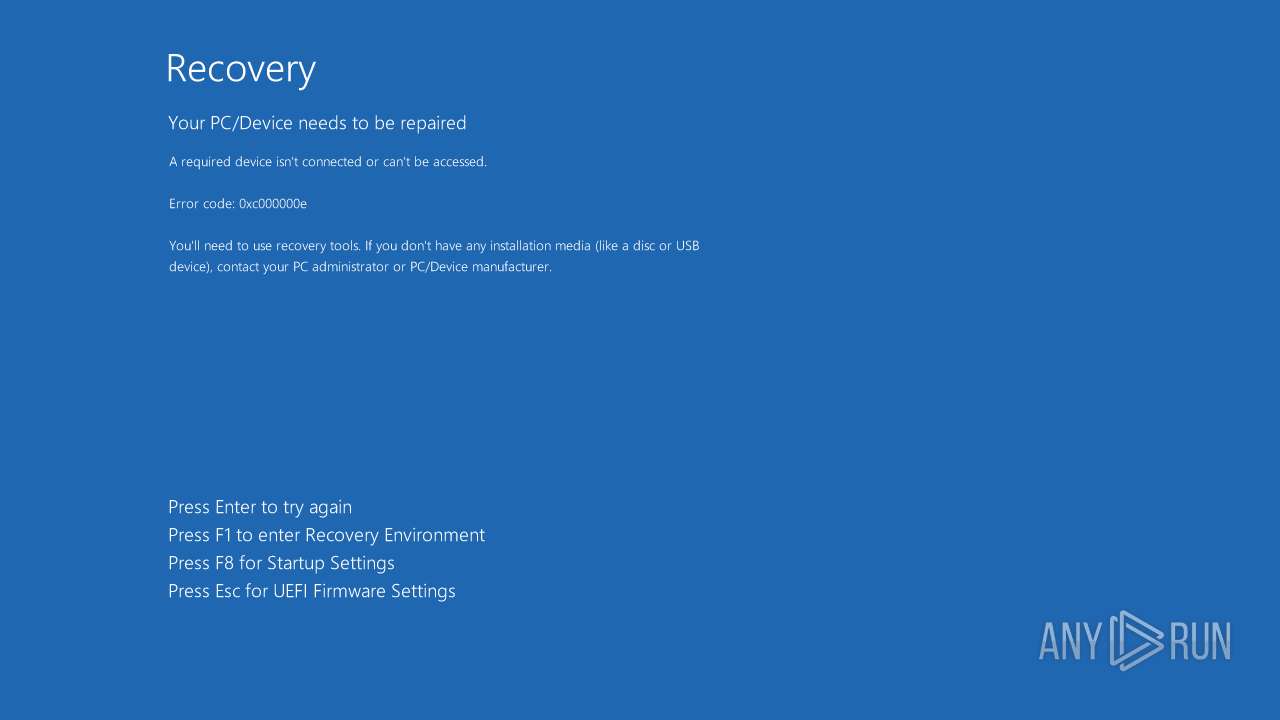
The system shut down or reboot
- GoldenEye.exe (PID: 2744)
INFO
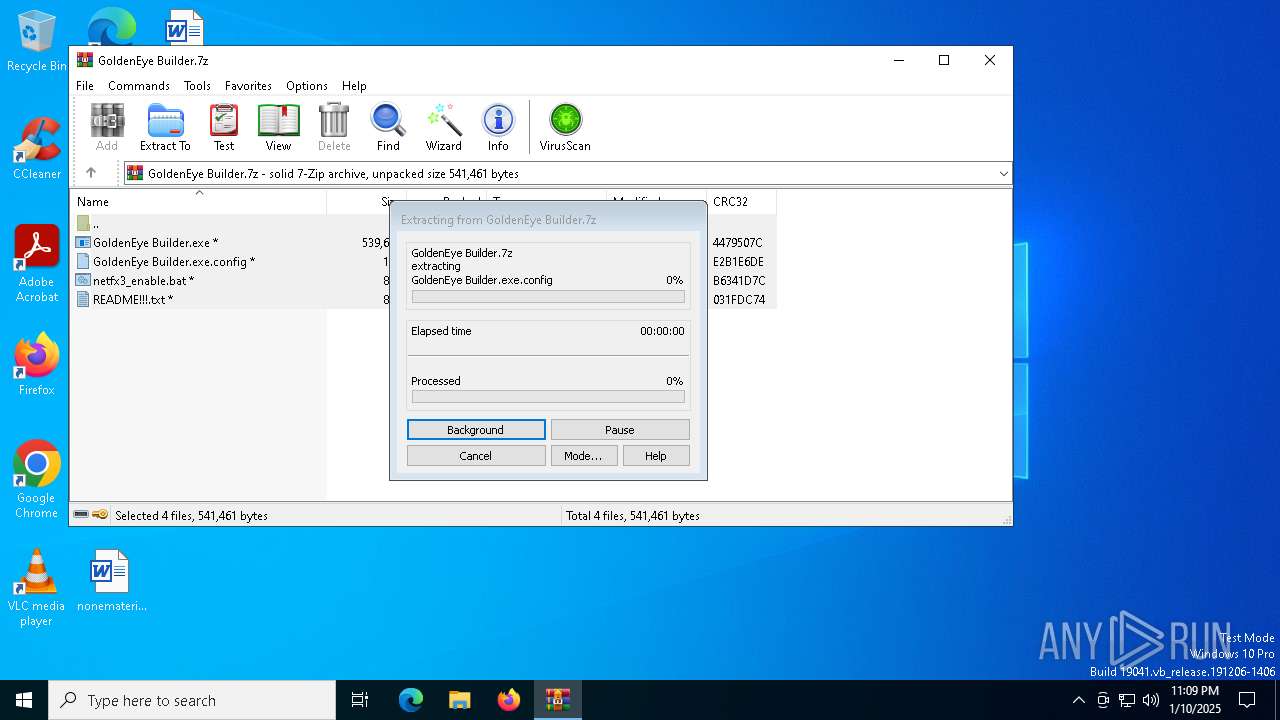
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4320)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7032)
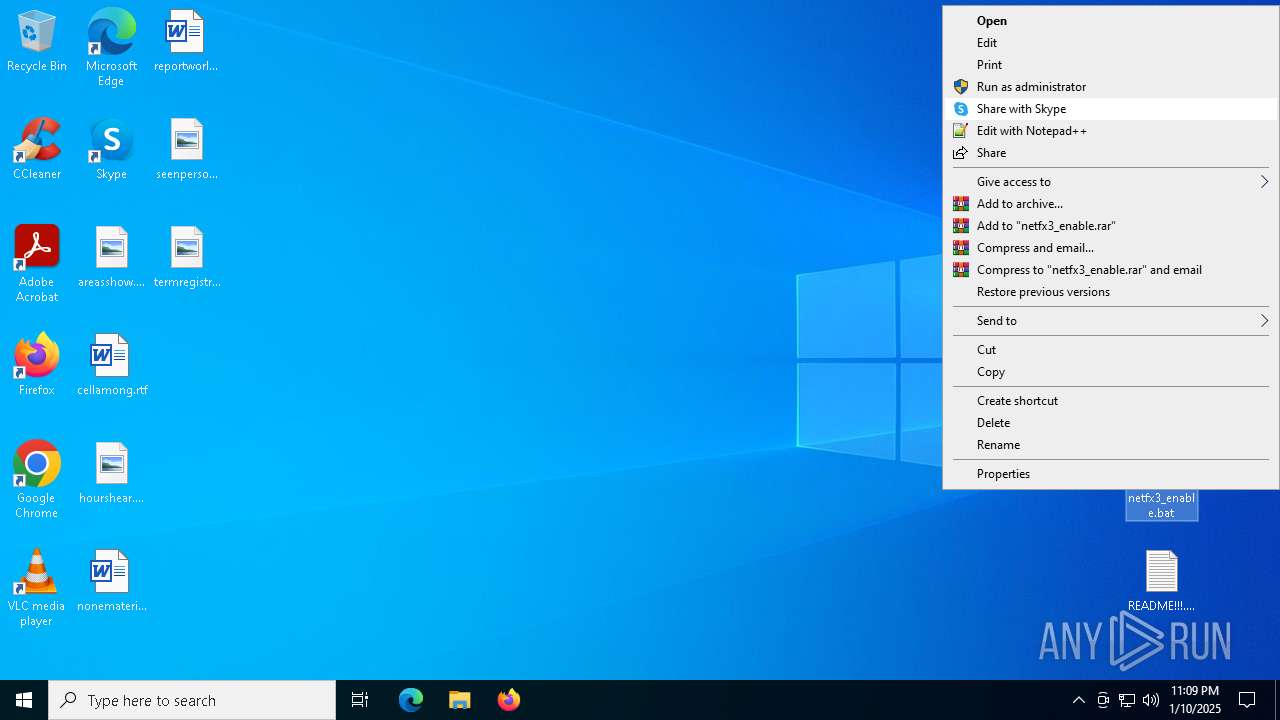
Manual execution by a user
- cmd.exe (PID: 3620)
- notepad.exe (PID: 7032)
- cmd.exe (PID: 6092)
- GoldenEye Builder.exe (PID: 7100)
- GoldenEye.exe (PID: 2744)
- GoldenEye.exe (PID: 4132)
- GoldenEye Builder.exe (PID: 4228)
Sends debugging messages
- Dism.exe (PID: 3060)
Reads Environment values
- DismHost.exe (PID: 4672)
Checks supported languages
- DismHost.exe (PID: 4672)
- GoldenEye Builder.exe (PID: 7100)
- GoldenEye.exe (PID: 2744)
The sample compiled with english language support
- Dism.exe (PID: 3060)
Create files in a temporary directory
- Dism.exe (PID: 3060)
- GoldenEye Builder.exe (PID: 7100)
Reads the computer name
- DismHost.exe (PID: 4672)
- GoldenEye Builder.exe (PID: 7100)
Reads the software policy settings
- TiWorker.exe (PID: 2408)
Manages system restore points
- SrTasks.exe (PID: 5556)
The process uses the downloaded file
- WinRAR.exe (PID: 4320)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
156
Monitored processes
24
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1016 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2144 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | shutdown.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2324 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2408 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2612 | C:\WINDOWS\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\Desktop\GoldenEye.exe" | C:\Users\admin\Desktop\GoldenEye.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
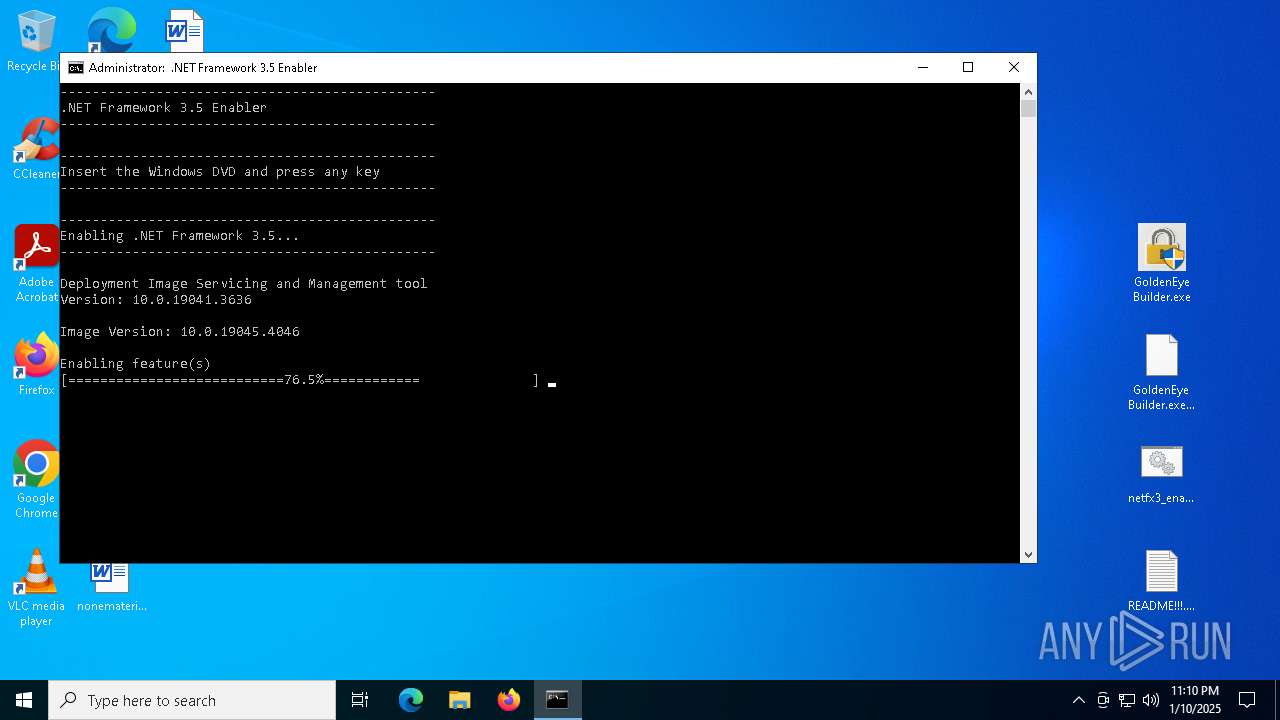
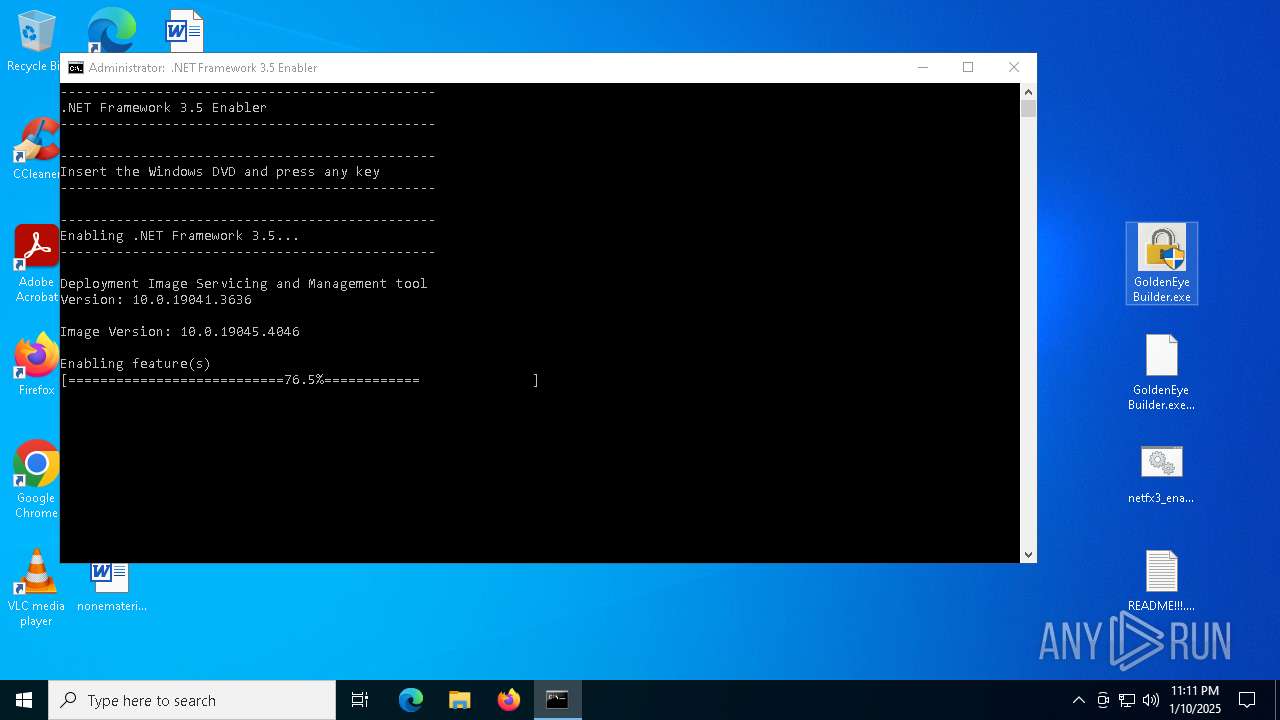
| 3060 | Dism /online /enable-feature /featurename:NetFx3 /All /Source:\sources\sxs /LimitAccess | C:\Windows\System32\Dism.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3436 | C:\Windows\System32\shutdown.exe -r -f -t 0 | C:\Windows\SysWOW64\shutdown.exe | — | GoldenEye.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 1115 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3620 | "C:\WINDOWS\System32\cmd.exe" /C "C:\Users\admin\Desktop\netfx3_enable.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4132 | net session | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 778
Read events
39 244
Write events
386
Delete events
148
Modification events
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\GoldenEye Builder.7z | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 1 | |||
| (PID) Process: | (4320) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
53
Suspicious files
1 351
Text files
1 365
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4320 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4320.35359\GoldenEye Builder.exe | executable | |
MD5:C0E1A746A2C0157B6BEBB65A780CA525 | SHA256:DA095241B82CED1D375181E67A72696703F894AE74E8D98FE43576544981CB50 | |||
| 4320 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4320.35359\GoldenEye Builder.exe.config | xml | |
MD5:FDAD6E56C3813F4021FF8177DC33EF84 | SHA256:581337C905162B25581705895A91F3AF7C8A577161C18187485F1BD15692C90D | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\en-US\DismCore.dll.mui | executable | |
MD5:7A15F6E845F0679DE593C5896FE171F9 | SHA256:F91E3C35B472F95D7B1AE3DC83F9D6BFDE33515AA29E8B310F55D9FE66466419 | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\en-US\AssocProvider.dll.mui | executable | |
MD5:8833761572F0964BDC1BEA6E1667F458 | SHA256:B18C6CE1558C9EF6942A3BCE246A46557C2A7D12AEC6C4A07E4FA84DD5C422F5 | |||
| 4320 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4320.35359\README!!!.txt | text | |
MD5:AC5202875D9DB299966A25F34D96D5AE | SHA256:109115939D05AED291066539D084EF420512925B27D701C8DE0728C5E111C3FA | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\DismHost.exe | executable | |
MD5:97CB1E2FCAB378421C4B91DF0C9F8310 | SHA256:E36BCF02BC11F560761E943D0FAD37417078F6CBB473F85C72FCBC89E2600C58 | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\en-US\CbsProvider.dll.mui | executable | |
MD5:6C51A3187D2464C48CC8550B141E25C5 | SHA256:D7A0253D6586E7BBFB0ACB6FACD9A326B32BA1642B458F5B5ED27FECCB4FC199 | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\en-US\DmiProvider.dll.mui | executable | |
MD5:B7252234AA43B7295BB62336ADC1B85C | SHA256:73709C25DC5300A435E53DF97FC01A7DC184B56796CAE48EE728D54D26076D6C | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\AssocProvider.dll | executable | |
MD5:B7DB592706D3EEFBCF0D5A166D462E56 | SHA256:DE21321272862E7C332E1724DC315F06F3ABE7A0340E61D351CAB208D6BBF059 | |||
| 3060 | Dism.exe | C:\Users\admin\AppData\Local\Temp\F2465155-DD37-425B-BEF1-7474A29C9E34\CbsProvider.dll | executable | |
MD5:14932441A96E254B3D29D452CE1263A0 | SHA256:8FFF21CB7C88A0DD8C8E7B386604001F2974E75D229369A87BEE0BA18DA575F3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
40
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5988 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5988 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6240 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7064 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7064 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5988 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5988 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.128:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Dism.exe | PID=3060 TID=3876 Loading Provider from location C:\WINDOWS\system32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3060 TID=3876 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=3060 TID=3876 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3060 TID=3876 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3060 TID=3876 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3060 TID=3876 Connecting to the provider located at C:\WINDOWS\system32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |