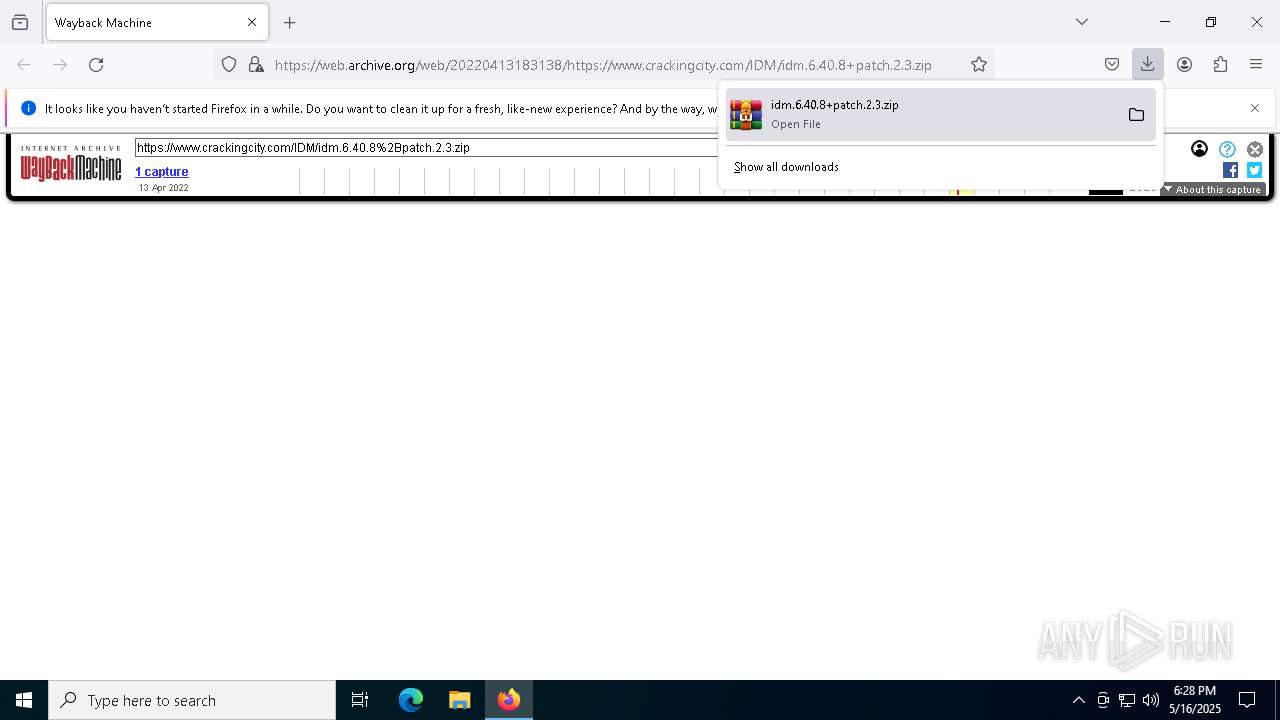
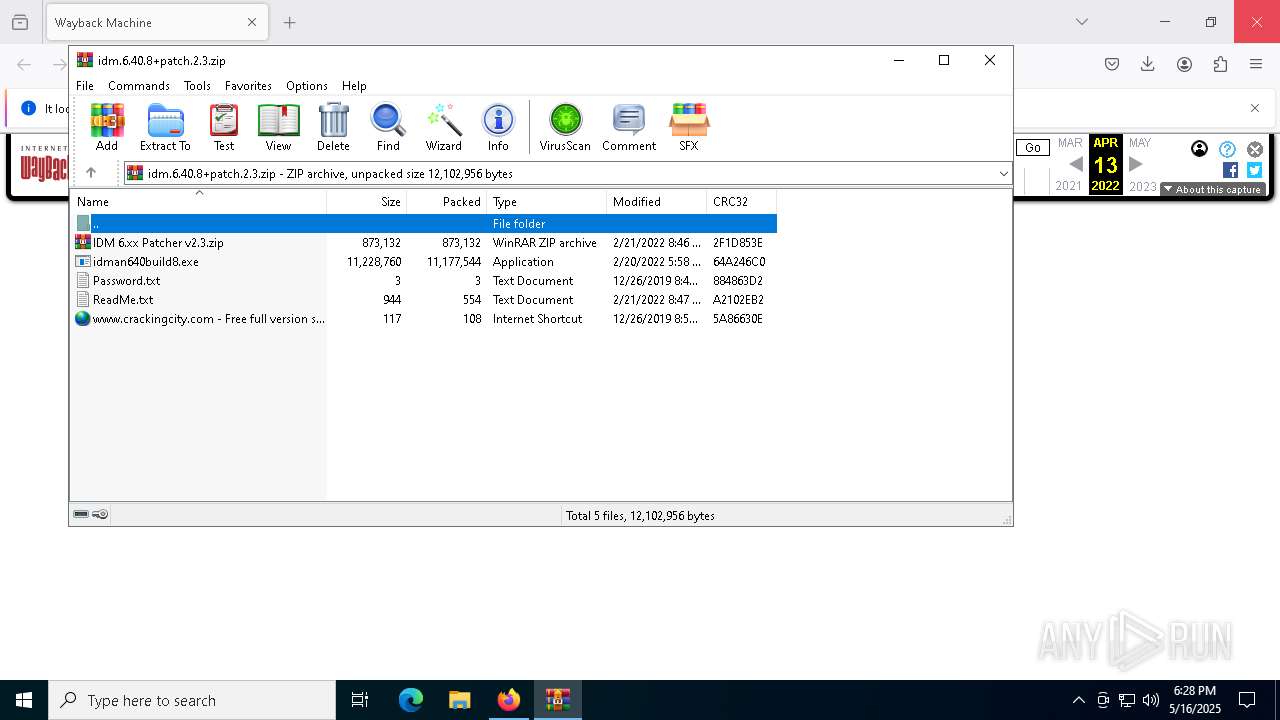
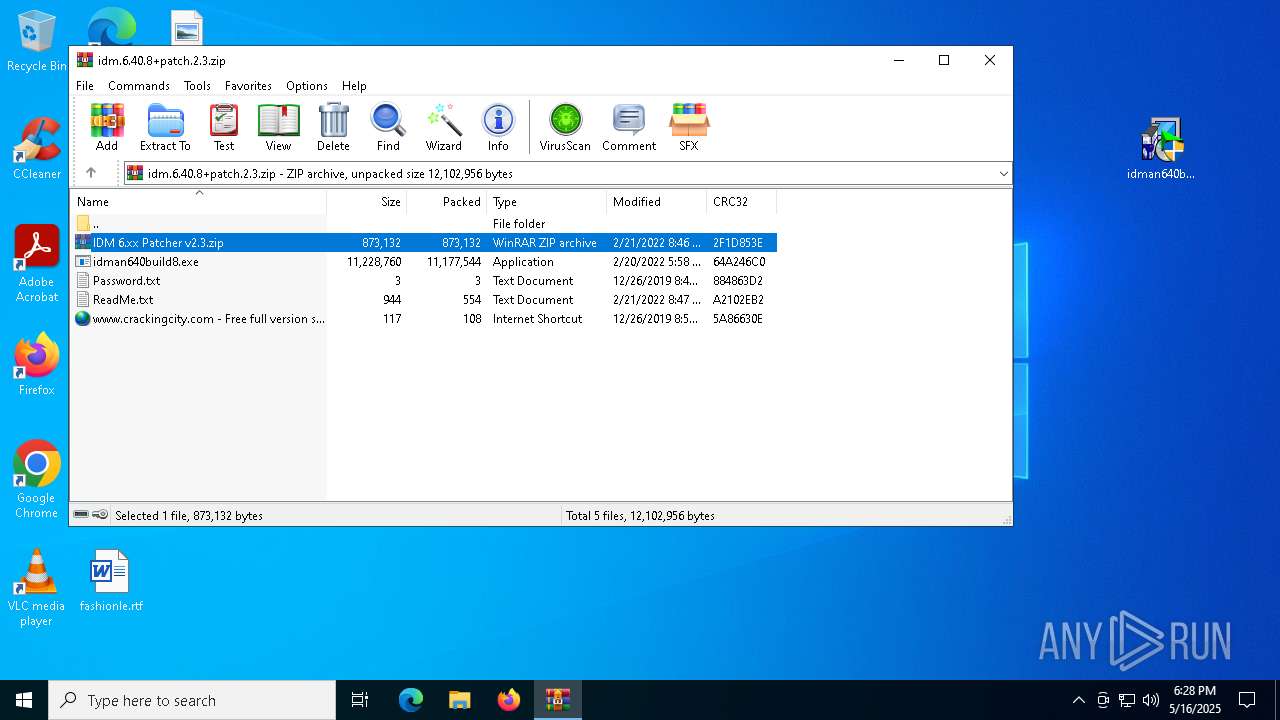
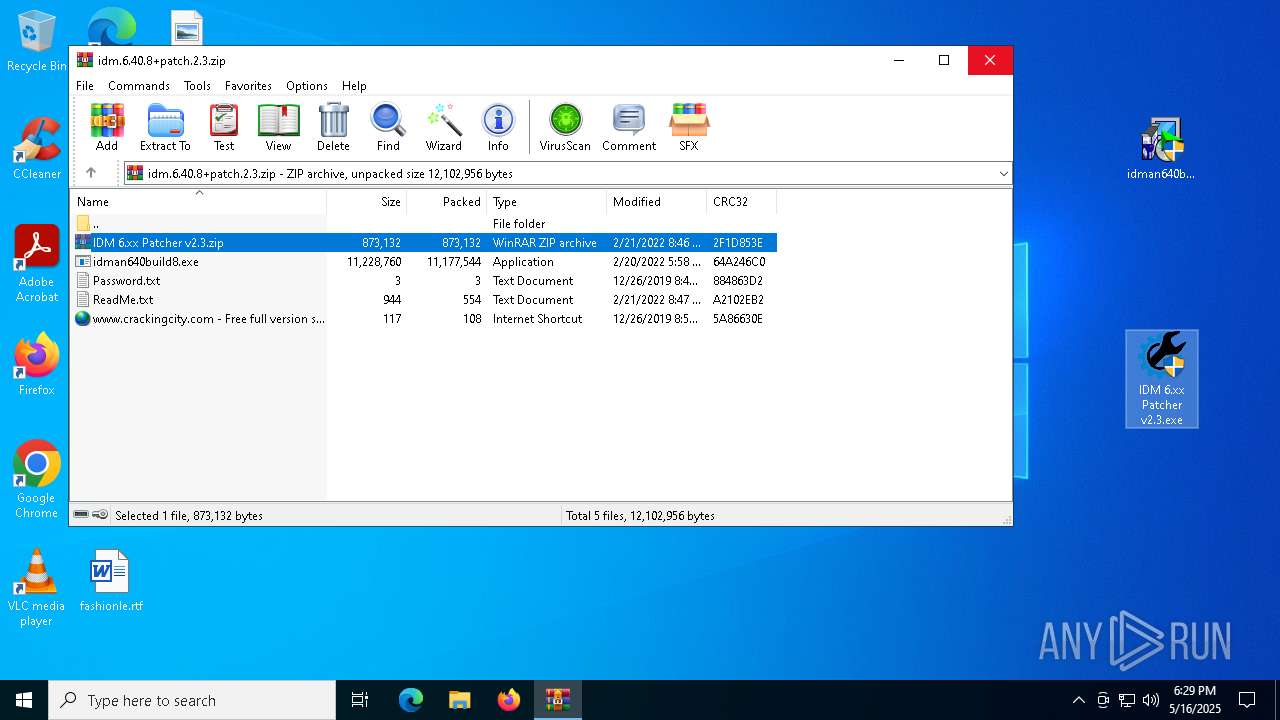
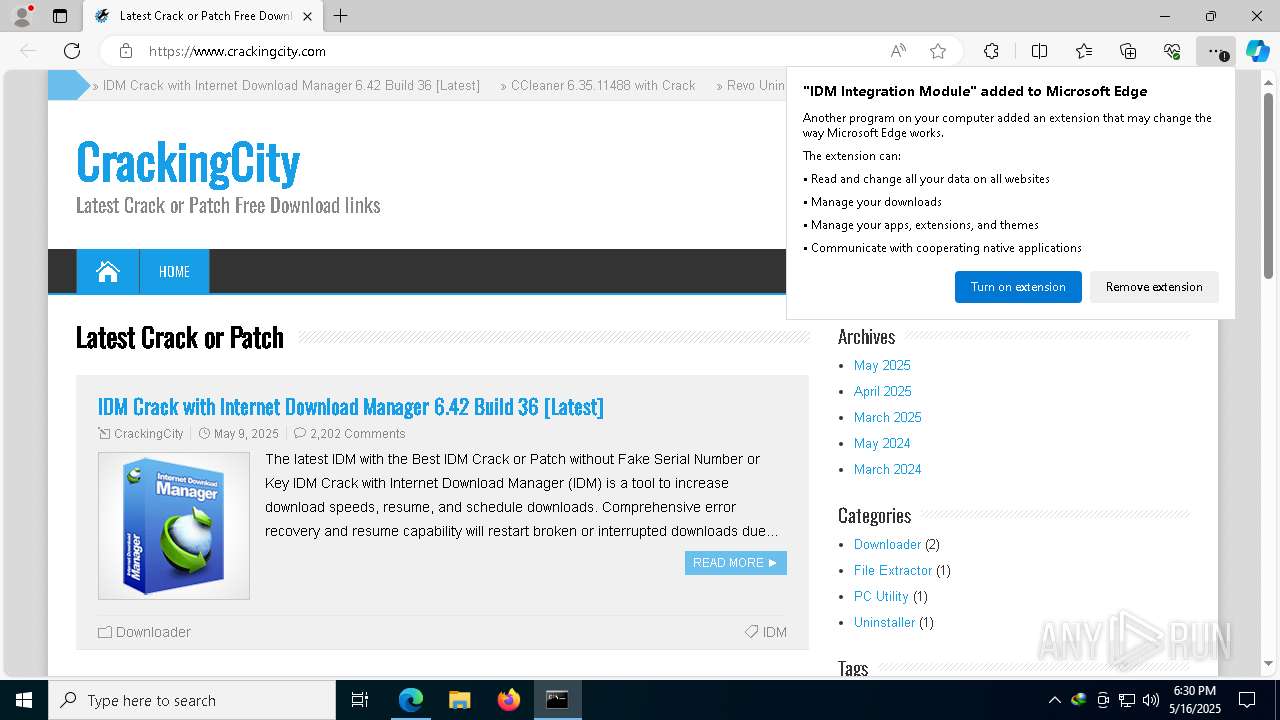
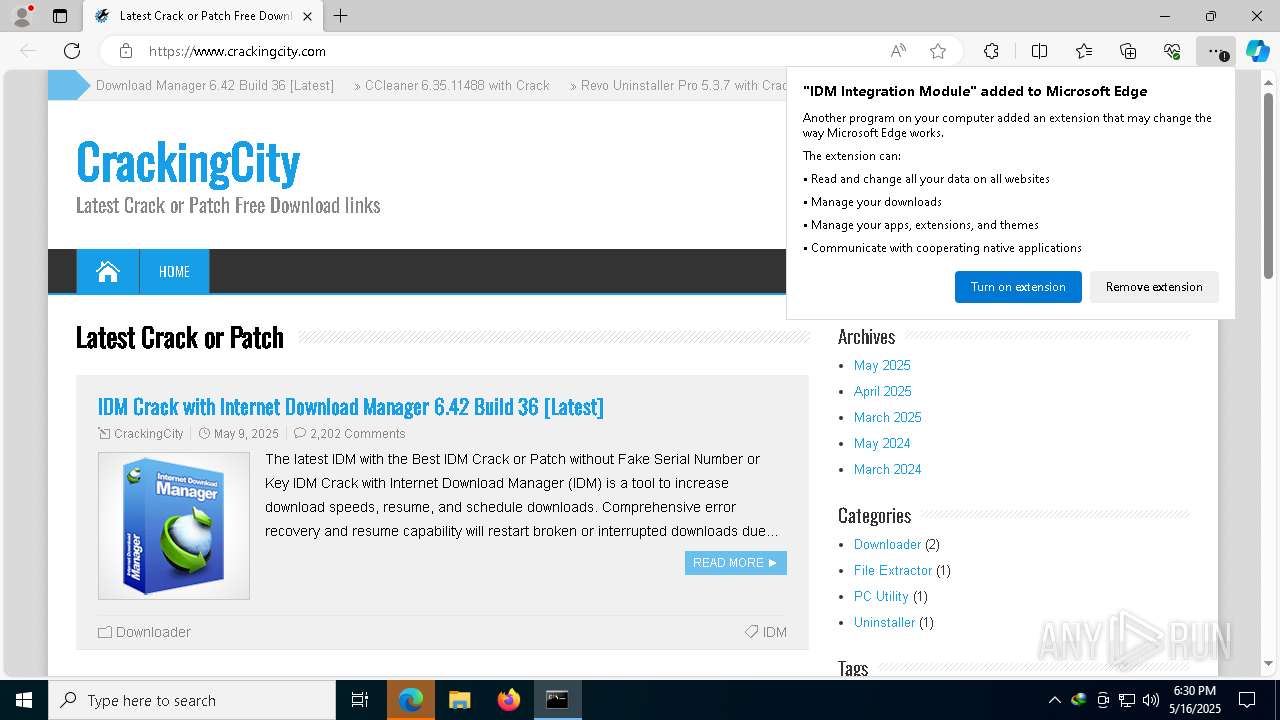
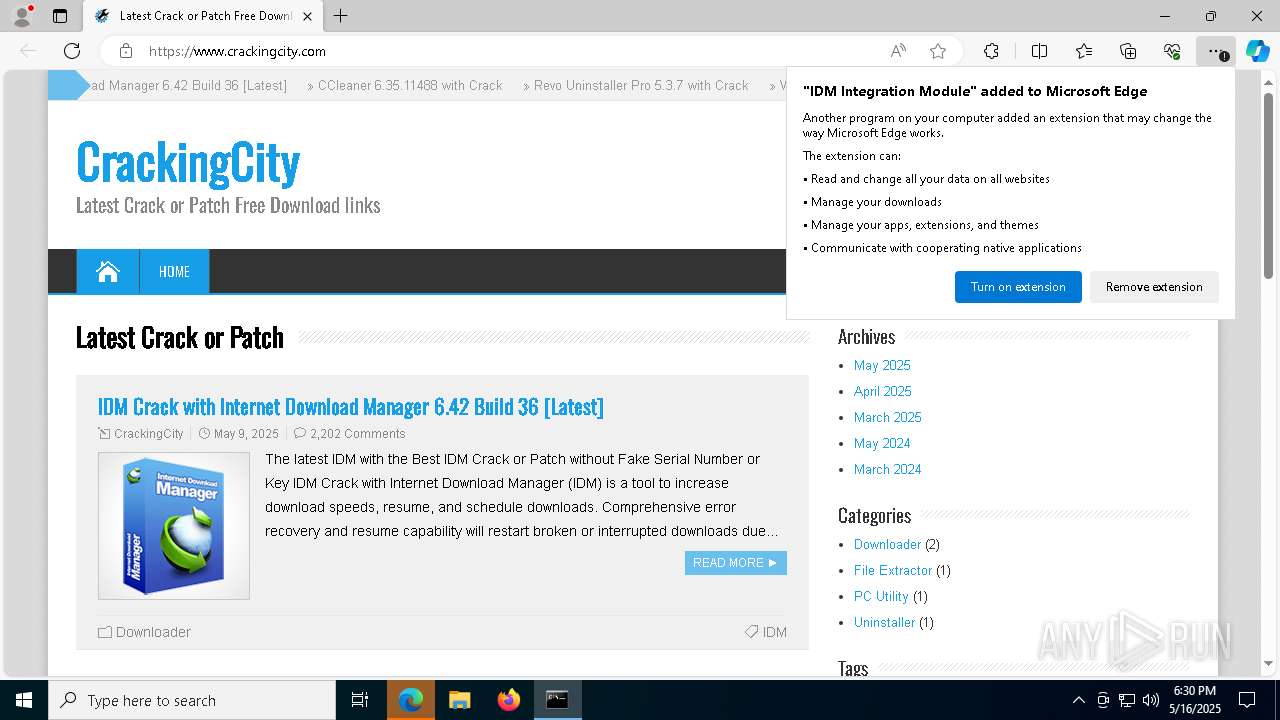
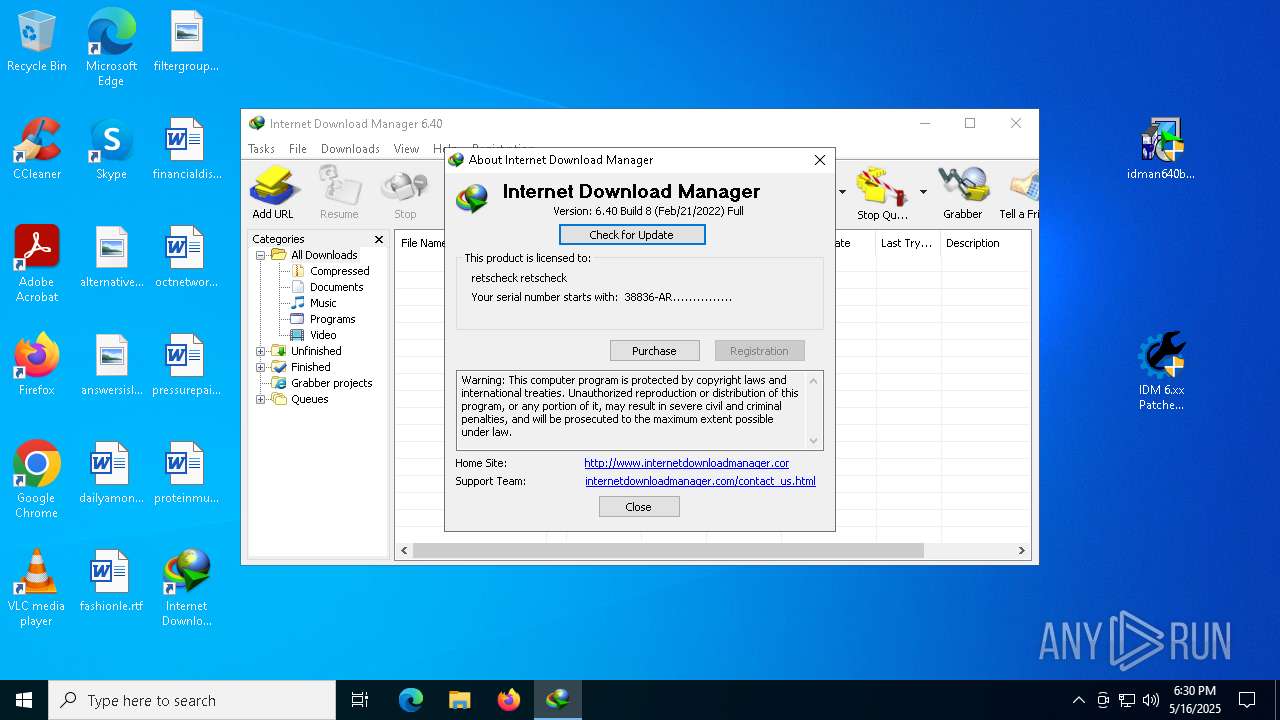
| URL: | https://web.archive.org/web/20220413183138/https://www.crackingcity.com/IDM/idm.6.40.8+patch.2.3.zip |
| Full analysis: | https://app.any.run/tasks/d2cb3d2c-d433-4a3f-b985-1a0debf4a954 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 18:28:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D9FE77330EEA8CFBCEAD5F216580A091 |
| SHA1: | 00C33303312EA411678844F03E2E74B65F8B1206 |
| SHA256: | 48DE906316303FF1088C0CF5B680645E3183C3DFB15D23D02144B5D4461D272D |
| SSDEEP: | 3:N8RQXxXJetXDETWYOrSLbMLF8TKX0lhMWLcn:2GhX8x7GLU0ncn |
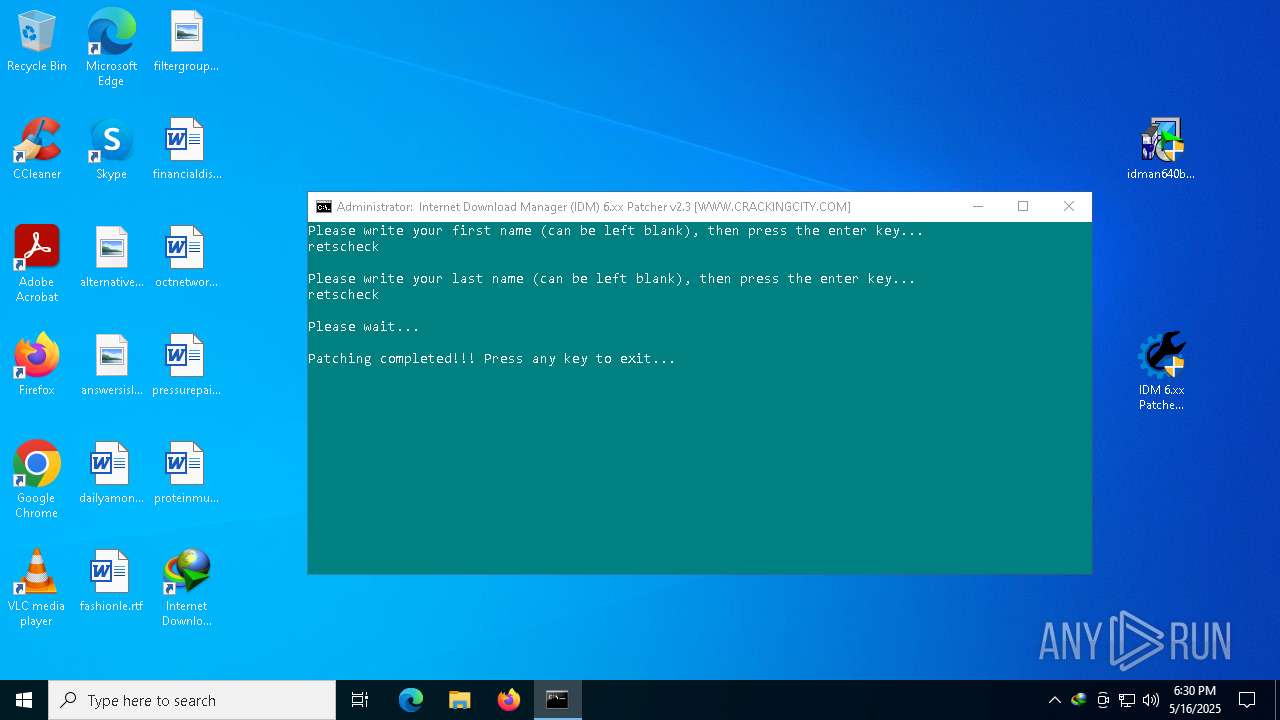
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- IDMan.exe (PID: 2984)
- IDM1.tmp (PID: 6080)
- Uninstall.exe (PID: 7736)
- IDMan.exe (PID: 7860)
Starts NET.EXE for service management
- Uninstall.exe (PID: 7736)
- net.exe (PID: 7144)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 896)
Changes Windows Defender settings
- cmd.exe (PID: 896)
SUSPICIOUS
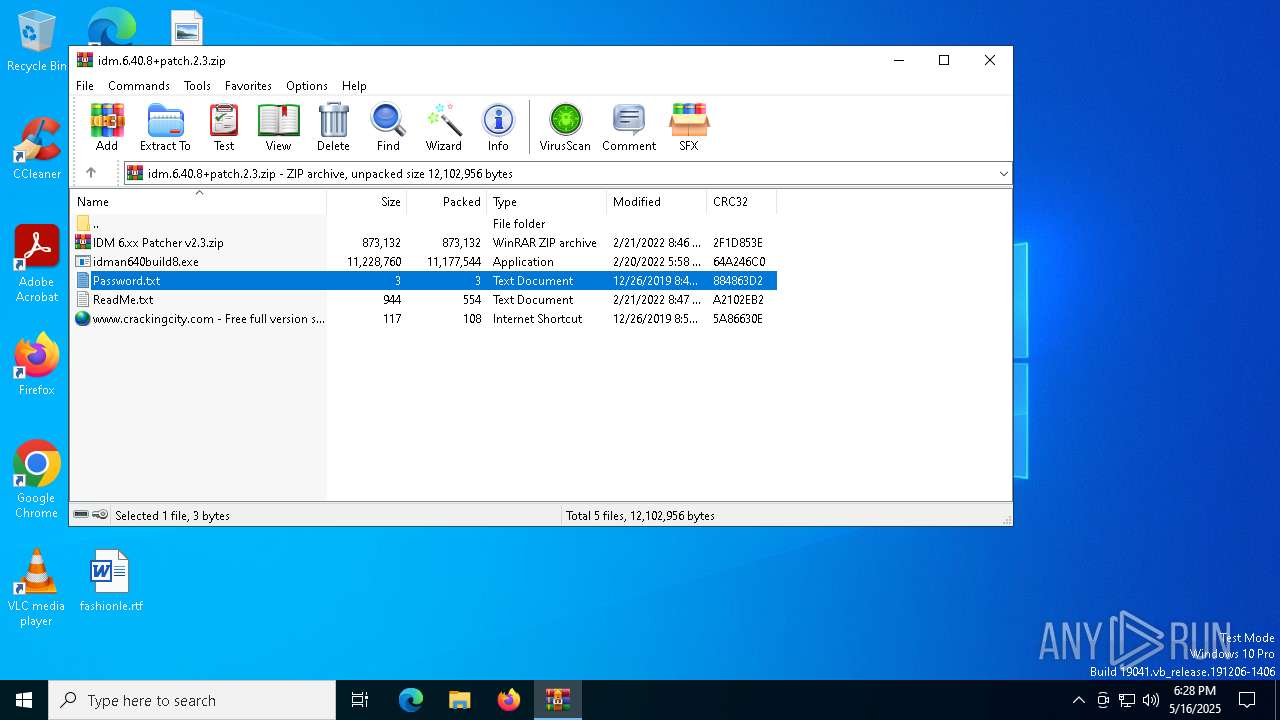
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6156)
- WinRAR.exe (PID: 2564)
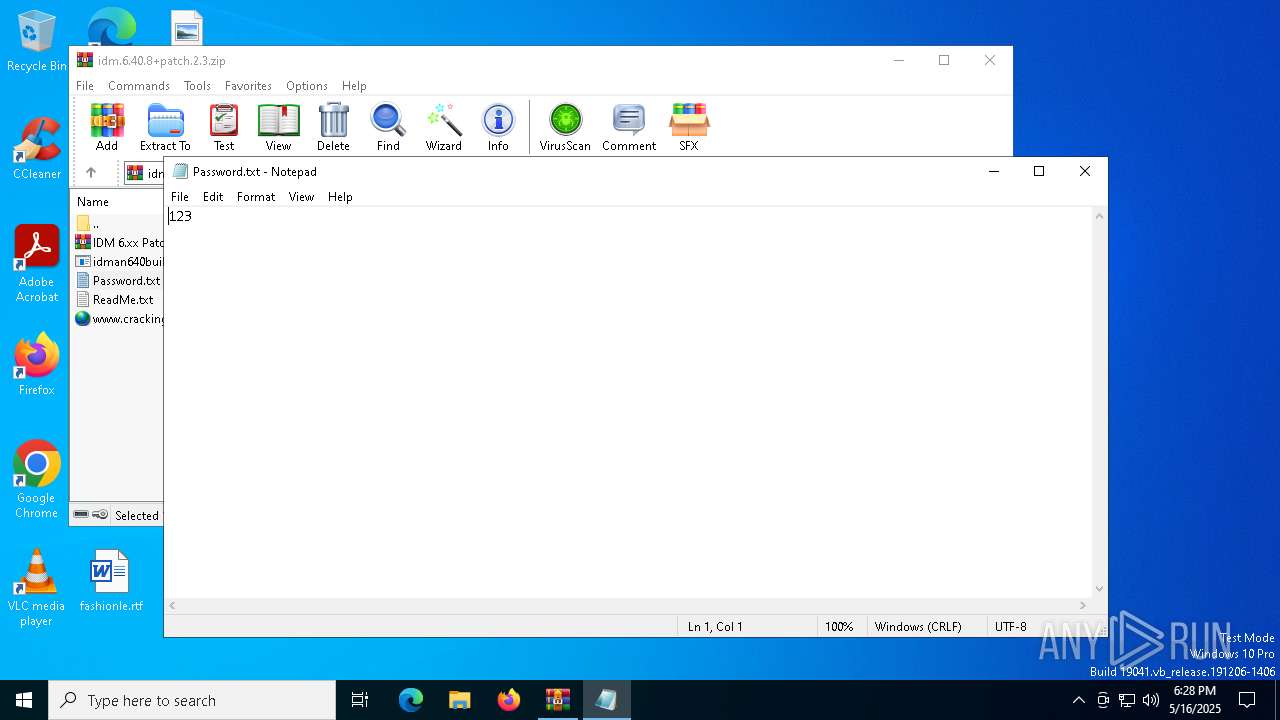
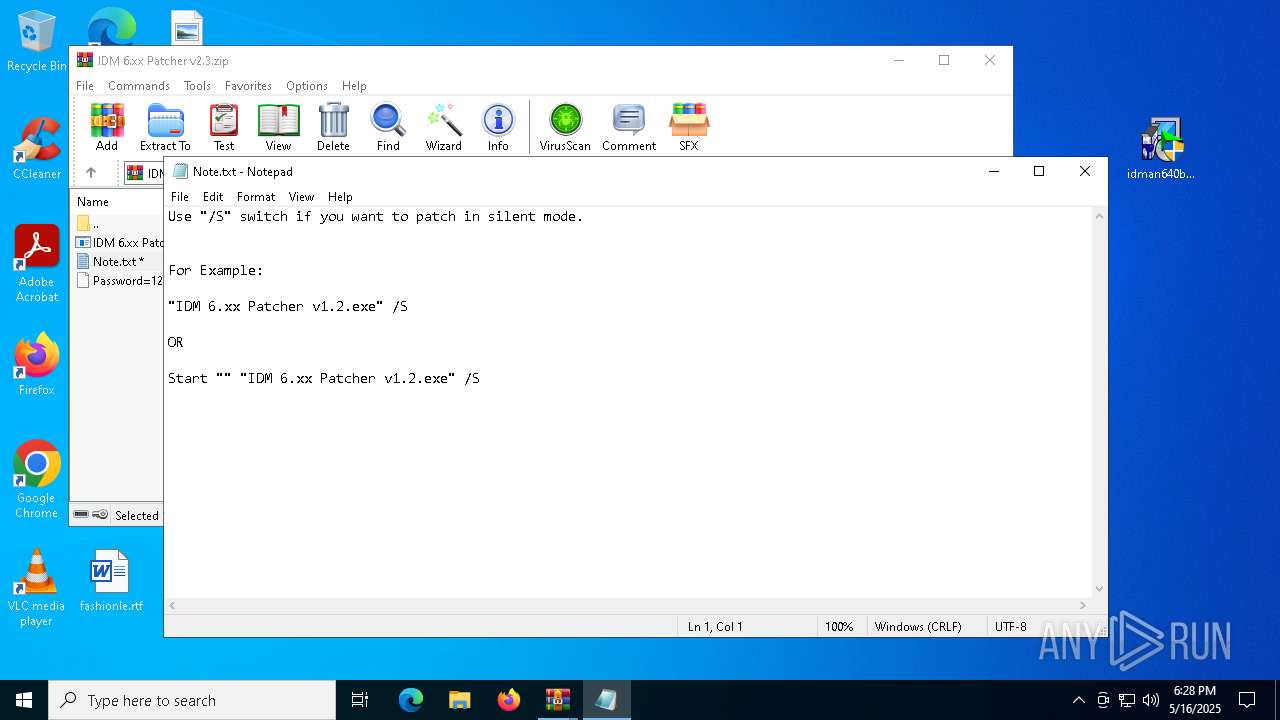
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6156)
- WinRAR.exe (PID: 2564)
Application launched itself
- WinRAR.exe (PID: 6156)
- cmd.exe (PID: 8176)
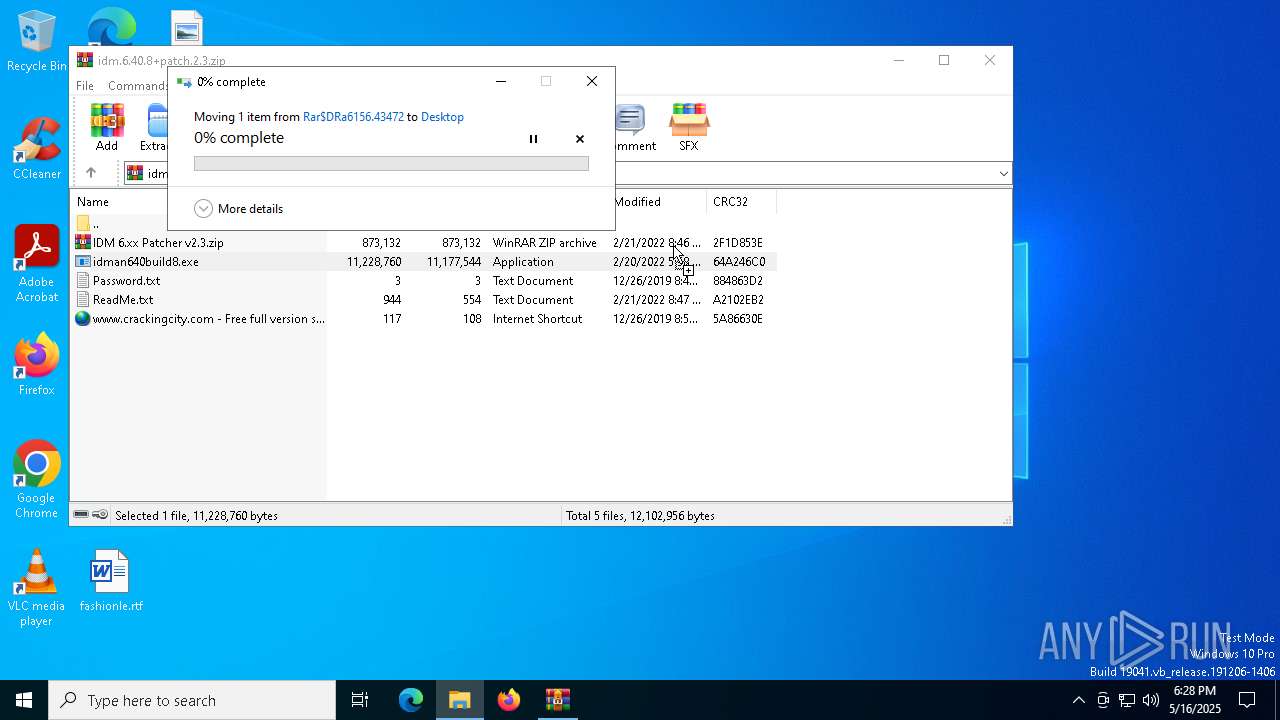
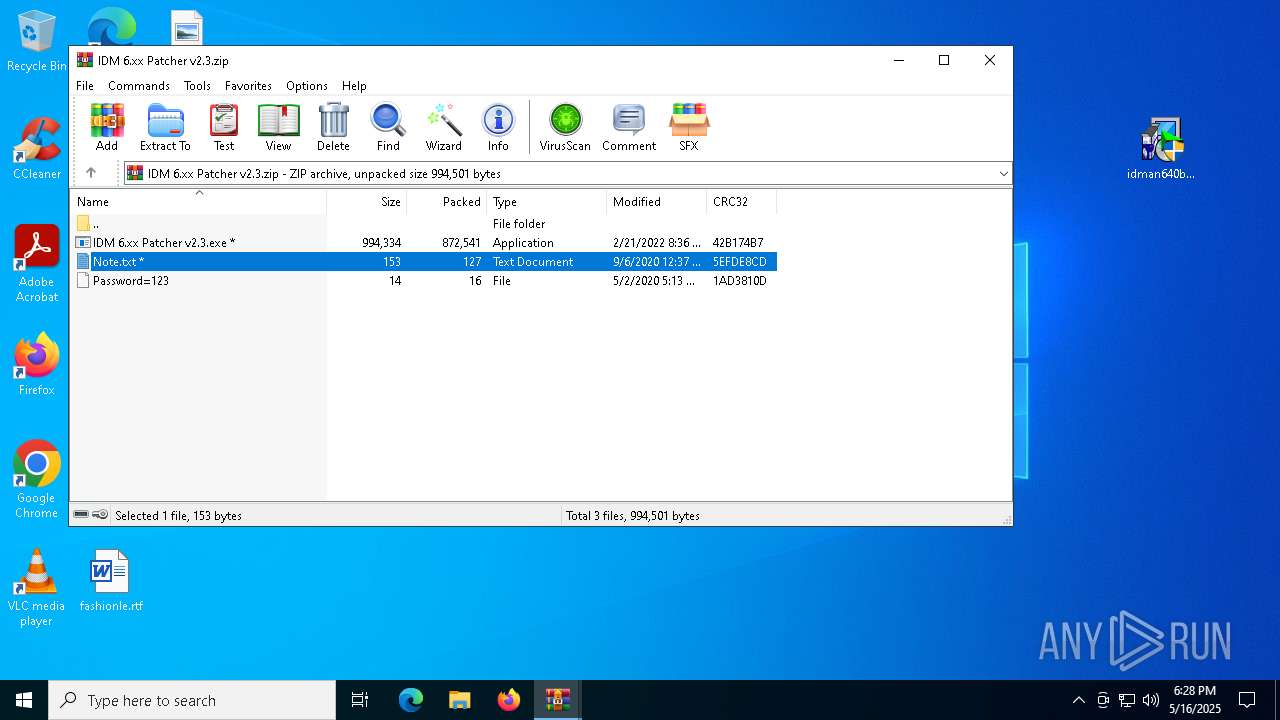
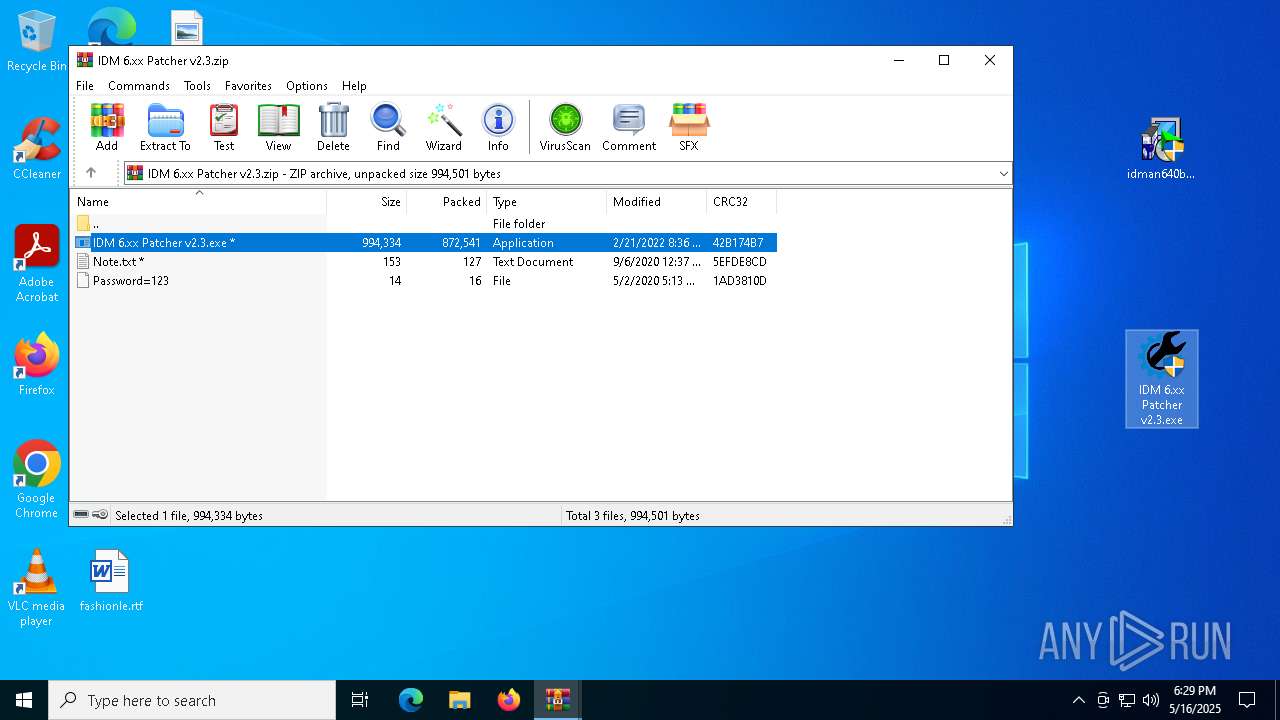
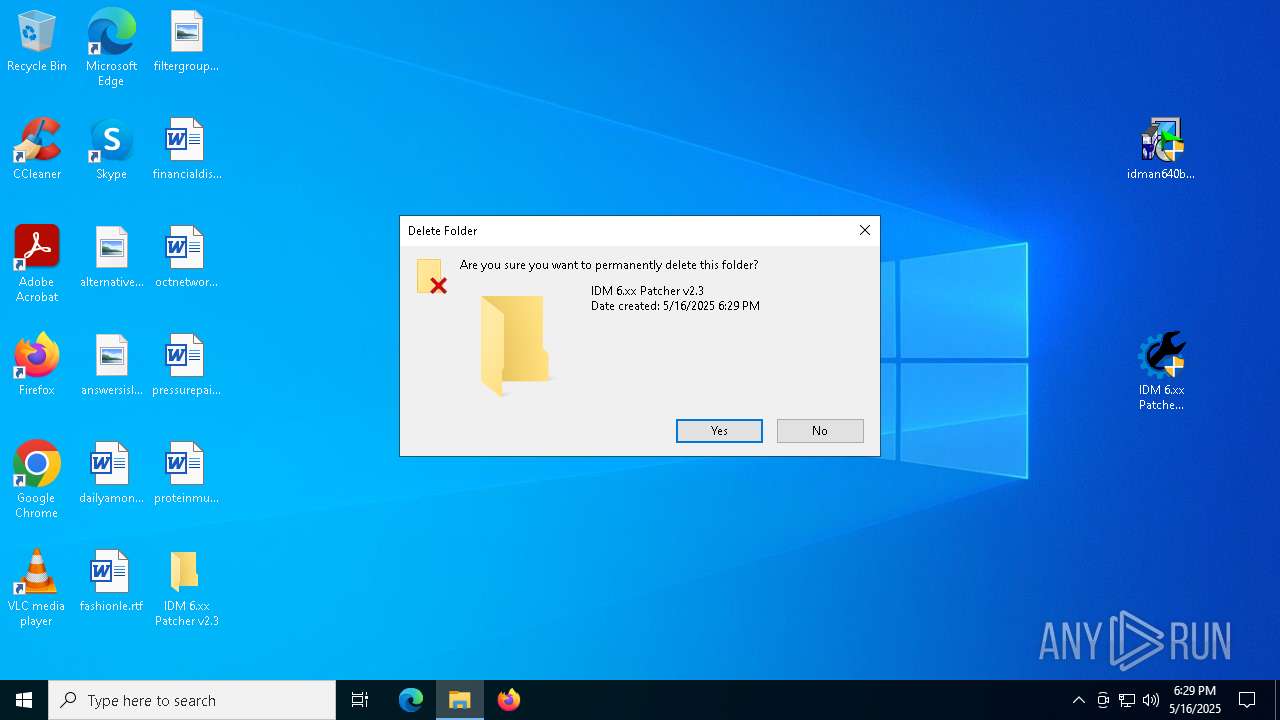
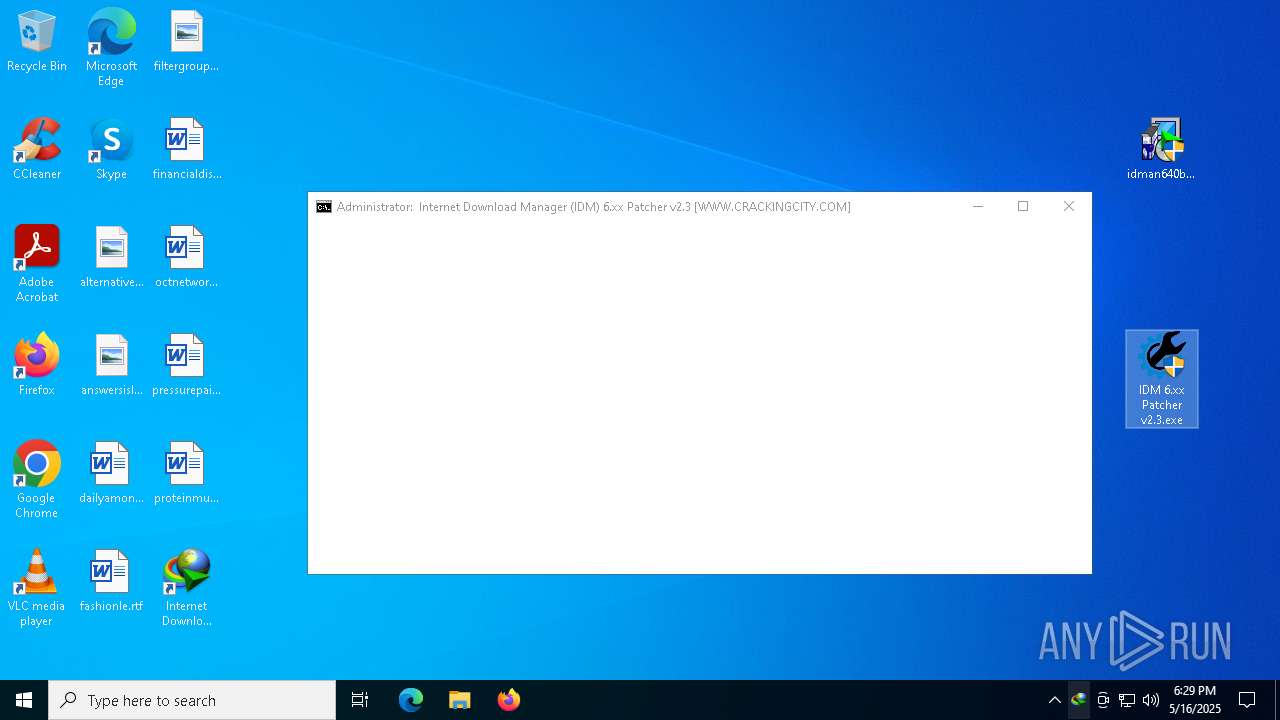
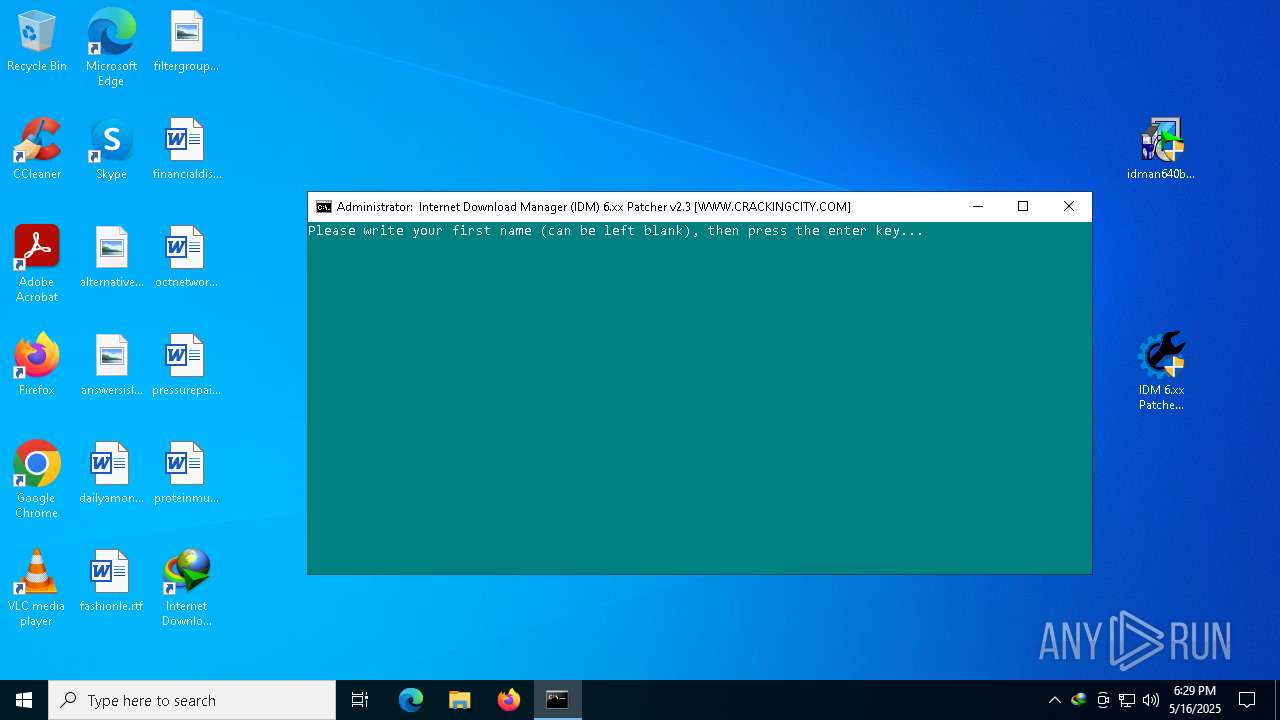
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 7984)
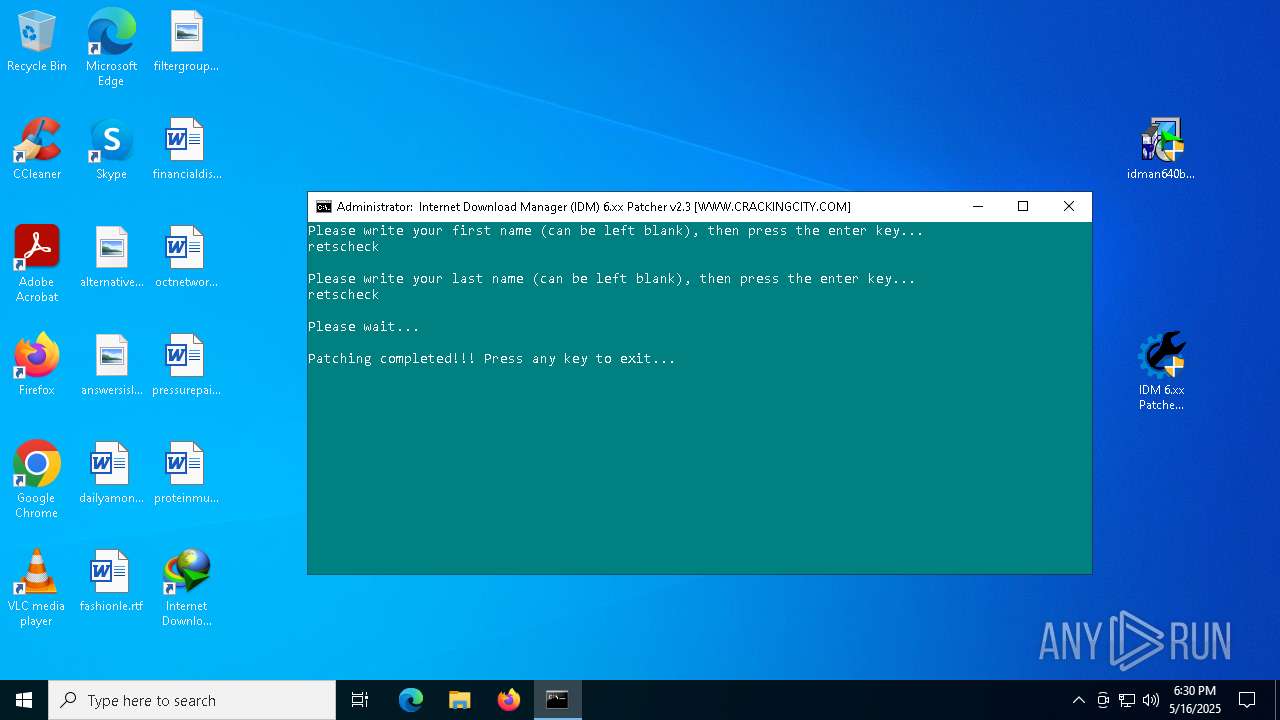
- IDM 6.xx Patcher v2.3.exe (PID: 3796)
Starts application with an unusual extension
- idman640build8.exe (PID: 7964)
Executable content was dropped or overwritten
- IDMan.exe (PID: 2984)
- rundll32.exe (PID: 7712)
- 7za.exe (PID: 7424)
- IDM 6.xx Patcher v2.3.exe (PID: 3796)
- cmd.exe (PID: 8176)
- 7za.exe (PID: 5392)
- 7za.exe (PID: 7724)
- 7za.exe (PID: 7712)
- certutil.exe (PID: 3240)
Uses RUNDLL32.EXE to load library
- Uninstall.exe (PID: 7736)
Drops a system driver (possible attempt to evade defenses)
- rundll32.exe (PID: 7712)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 7544)
- cmd.exe (PID: 8176)
The executable file from the user directory is run by the CMD process
- 7za.exe (PID: 7760)
- 7za.exe (PID: 7424)
- 7za.exe (PID: 7780)
- AB2EF.exe (PID: 6184)
- AB2EF.exe (PID: 6760)
- AB2EF.exe (PID: 7884)
- AB2EF.exe (PID: 8100)
- 7za.exe (PID: 5392)
- fart.exe (PID: 2140)
- fart.exe (PID: 6576)
- fart.exe (PID: 1912)
- fart.exe (PID: 7868)
- fart.exe (PID: 6592)
- fart.exe (PID: 1852)
- fart.exe (PID: 7272)
- fart.exe (PID: 7444)
- fart.exe (PID: 7240)
- fart.exe (PID: 7260)
- fart.exe (PID: 6476)
- fart.exe (PID: 5244)
- fart.exe (PID: 7604)
- fart.exe (PID: 6244)
- fart.exe (PID: 6660)
- fart.exe (PID: 6820)
- fart.exe (PID: 7584)
- fart.exe (PID: 856)
- fart.exe (PID: 7536)
- fart.exe (PID: 8128)
- fart.exe (PID: 8160)
- fart.exe (PID: 7968)
- fart.exe (PID: 8068)
- fart.exe (PID: 8040)
- fart.exe (PID: 7544)
- fart.exe (PID: 7012)
- fart.exe (PID: 1132)
- fart.exe (PID: 7872)
- fart.exe (PID: 8060)
- fart.exe (PID: 7400)
- fart.exe (PID: 7556)
- fart.exe (PID: 7416)
- fart.exe (PID: 7380)
- fart.exe (PID: 5744)
- fart.exe (PID: 6512)
- fart.exe (PID: 664)
- fart.exe (PID: 6080)
- fart.exe (PID: 132)
- 7za.exe (PID: 7712)
- 7za.exe (PID: 7724)
- delcert.exe (PID: 7468)
- NSudo64x.exe (PID: 3956)
- NSudo64x.exe (PID: 5156)
- NSudo64x.exe (PID: 864)
- NSudo64x.exe (PID: 5352)
- NSudo64x.exe (PID: 7372)
- NSudo64x.exe (PID: 1196)
- AB2EF.exe (PID: 7172)
- AB2EF.exe (PID: 2560)
- AB2EF.exe (PID: 4000)
- NSudo64x.exe (PID: 8188)
- NSudo64x.exe (PID: 5392)
- NSudo64x.exe (PID: 7620)
- NSudo64x.exe (PID: 5072)
- NSudo64x.exe (PID: 7436)
- NSudo64x.exe (PID: 1012)
- NSudo64x.exe (PID: 7576)
- NSudo64x.exe (PID: 3620)
- NSudo64x.exe (PID: 7780)
- NSudo64x.exe (PID: 5936)
- NSudo64x.exe (PID: 7728)
- NSudo64x.exe (PID: 7504)
- NSudo64x.exe (PID: 7224)
- NSudo64x.exe (PID: 6512)
- NSudo64x.exe (PID: 1096)
- NSudo64x.exe (PID: 7700)
- NSudo64x.exe (PID: 5640)
- NSudo64x.exe (PID: 7324)
- NSudo64x.exe (PID: 7984)
- NSudo64x.exe (PID: 924)
- NSudo64x.exe (PID: 4692)
- NSudo64x.exe (PID: 7412)
- NSudo64x.exe (PID: 7788)
- NSudo64x.exe (PID: 3032)
- NSudo64x.exe (PID: 920)
- NSudo64x.exe (PID: 7864)
- NSudo64x.exe (PID: 3024)
- NSudo64x.exe (PID: 7648)
- NSudo64x.exe (PID: 6852)
- NSudo64x.exe (PID: 5952)
- NSudo64x.exe (PID: 4152)
- NSudo64x.exe (PID: 6456)
- NSudo64x.exe (PID: 7408)
- NSudo64x.exe (PID: 4976)
- NSudo64x.exe (PID: 8104)
- NSudo64x.exe (PID: 8152)
- NSudo64x.exe (PID: 7548)
- NSudo64x.exe (PID: 4528)
- NSudo64x.exe (PID: 7768)
- NSudo64x.exe (PID: 7732)
- NSudo64x.exe (PID: 2316)
- NSudo64x.exe (PID: 6264)
- NSudo64x.exe (PID: 6572)
- NSudo64x.exe (PID: 7376)
- NSudo64x.exe (PID: 7984)
- NSudo64x.exe (PID: 924)
- NSudo64x.exe (PID: 7788)
- NSudo64x.exe (PID: 6876)
- NSudo64x.exe (PID: 6800)
- NSudo64x.exe (PID: 7324)
- NSudo64x.exe (PID: 7280)
- NSudo64x.exe (PID: 7192)
- NSudo64x.exe (PID: 7956)
- NSudo64x.exe (PID: 7228)
- NSudo64x.exe (PID: 5608)
- NSudo64x.exe (PID: 1852)
- NSudo64x.exe (PID: 4688)
- NSudo64x.exe (PID: 4628)
- NSudo64x.exe (PID: 2772)
- NSudo64x.exe (PID: 5952)
- NSudo64x.exe (PID: 6988)
- NSudo64x.exe (PID: 8160)
- NSudo64x.exe (PID: 7940)
- NSudo64x.exe (PID: 8088)
- NSudo64x.exe (PID: 6564)
- NSudo64x.exe (PID: 2384)
- NSudo64x.exe (PID: 4648)
- NSudo64x.exe (PID: 7240)
- NSudo64x.exe (PID: 2288)
- NSudo64x.exe (PID: 5408)
- NSudo64x.exe (PID: 8172)
- NSudo64x.exe (PID: 6108)
- NSudo64x.exe (PID: 7976)
- NSudo64x.exe (PID: 1116)
- NSudo64x.exe (PID: 6136)
- NSudo64x.exe (PID: 4268)
- NSudo64x.exe (PID: 4920)
- NSudo64x.exe (PID: 4688)
- NSudo64x.exe (PID: 7320)
- NSudo64x.exe (PID: 1912)
- NSudo64x.exe (PID: 5392)
- NSudo64x.exe (PID: 5548)
- NSudo64x.exe (PID: 7244)
- NSudo64x.exe (PID: 4628)
- NSudo64x.exe (PID: 7900)
- NSudo64x.exe (PID: 4304)
- NSudo64x.exe (PID: 904)
- NSudo64x.exe (PID: 7996)
- NSudo64x.exe (PID: 8040)
- NSudo64x.exe (PID: 5936)
- NSudo64x.exe (PID: 1280)
- NSudo64x.exe (PID: 7476)
- NSudo64x.exe (PID: 7456)
- NSudo64x.exe (PID: 8036)
- NSudo64x.exe (PID: 4112)
- NSudo64x.exe (PID: 7448)
- NSudo64x.exe (PID: 6228)
- NSudo64x.exe (PID: 924)
- NSudo64x.exe (PID: 7932)
- NSudo64x.exe (PID: 1116)
- NSudo64x.exe (PID: 5352)
- NSudo64x.exe (PID: 6800)
- NSudo64x.exe (PID: 4120)
- NSudo64x.exe (PID: 1020)
- NSudo64x.exe (PID: 7572)
- NSudo64x.exe (PID: 2320)
- NSudo64x.exe (PID: 7704)
- NSudo64x.exe (PID: 2244)
Starts CMD.EXE for commands execution
- IDM 6.xx Patcher v2.3.exe (PID: 3796)
- cmd.exe (PID: 8176)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 896)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 896)
Executing commands from a ".bat" file
- IDM 6.xx Patcher v2.3.exe (PID: 3796)
There is functionality for taking screenshot (YARA)
- IDMan.exe (PID: 7860)
Hides command output
- cmd.exe (PID: 8184)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 8176)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8184)
- cmd.exe (PID: 8176)
- NSudo64x.exe (PID: 5156)
- NSudo64x.exe (PID: 864)
- NSudo64x.exe (PID: 5352)
- NSudo64x.exe (PID: 7372)
- NSudo64x.exe (PID: 1196)
- NSudo64x.exe (PID: 4688)
- NSudo64x.exe (PID: 8188)
- NSudo64x.exe (PID: 5392)
- NSudo64x.exe (PID: 3956)
- NSudo64x.exe (PID: 7620)
- NSudo64x.exe (PID: 7504)
- NSudo64x.exe (PID: 7224)
- NSudo64x.exe (PID: 7576)
- NSudo64x.exe (PID: 7436)
- NSudo64x.exe (PID: 7780)
- NSudo64x.exe (PID: 1012)
- NSudo64x.exe (PID: 3620)
- NSudo64x.exe (PID: 5936)
- NSudo64x.exe (PID: 5072)
- NSudo64x.exe (PID: 7728)
- NSudo64x.exe (PID: 5640)
- NSudo64x.exe (PID: 7412)
- NSudo64x.exe (PID: 6512)
- NSudo64x.exe (PID: 1096)
- NSudo64x.exe (PID: 7700)
- NSudo64x.exe (PID: 7984)
- NSudo64x.exe (PID: 7324)
- NSudo64x.exe (PID: 924)
- NSudo64x.exe (PID: 4692)
- NSudo64x.exe (PID: 7788)
- NSudo64x.exe (PID: 7864)
- NSudo64x.exe (PID: 3032)
- NSudo64x.exe (PID: 5952)
- NSudo64x.exe (PID: 920)
- NSudo64x.exe (PID: 6852)
- NSudo64x.exe (PID: 7648)
- NSudo64x.exe (PID: 4152)
- NSudo64x.exe (PID: 6456)
- NSudo64x.exe (PID: 3024)
- NSudo64x.exe (PID: 7408)
- NSudo64x.exe (PID: 4976)
- NSudo64x.exe (PID: 2316)
- NSudo64x.exe (PID: 8152)
- NSudo64x.exe (PID: 8104)
- NSudo64x.exe (PID: 7548)
- NSudo64x.exe (PID: 7768)
- NSudo64x.exe (PID: 7732)
- NSudo64x.exe (PID: 4528)
- NSudo64x.exe (PID: 6264)
- NSudo64x.exe (PID: 6800)
- NSudo64x.exe (PID: 6572)
- NSudo64x.exe (PID: 7376)
- NSudo64x.exe (PID: 7984)
- NSudo64x.exe (PID: 7324)
- NSudo64x.exe (PID: 6876)
- NSudo64x.exe (PID: 7788)
- NSudo64x.exe (PID: 924)
- NSudo64x.exe (PID: 2772)
- NSudo64x.exe (PID: 7192)
- NSudo64x.exe (PID: 7956)
- NSudo64x.exe (PID: 5608)
- NSudo64x.exe (PID: 1852)
- NSudo64x.exe (PID: 5952)
- NSudo64x.exe (PID: 7228)
- NSudo64x.exe (PID: 7240)
- NSudo64x.exe (PID: 2288)
- NSudo64x.exe (PID: 7940)
- NSudo64x.exe (PID: 6988)
- NSudo64x.exe (PID: 8160)
- NSudo64x.exe (PID: 8088)
- NSudo64x.exe (PID: 6564)
- NSudo64x.exe (PID: 2384)
- NSudo64x.exe (PID: 4628)
- NSudo64x.exe (PID: 4268)
- NSudo64x.exe (PID: 5408)
- NSudo64x.exe (PID: 8172)
- NSudo64x.exe (PID: 4920)
- NSudo64x.exe (PID: 6108)
- NSudo64x.exe (PID: 1116)
- NSudo64x.exe (PID: 6136)
- NSudo64x.exe (PID: 4648)
- NSudo64x.exe (PID: 7976)
- NSudo64x.exe (PID: 4304)
- NSudo64x.exe (PID: 4688)
- NSudo64x.exe (PID: 5392)
- NSudo64x.exe (PID: 5548)
- NSudo64x.exe (PID: 1912)
- NSudo64x.exe (PID: 7244)
- NSudo64x.exe (PID: 7900)
- NSudo64x.exe (PID: 7320)
- NSudo64x.exe (PID: 7996)
- NSudo64x.exe (PID: 7456)
- NSudo64x.exe (PID: 904)
- NSudo64x.exe (PID: 8036)
- NSudo64x.exe (PID: 8040)
- NSudo64x.exe (PID: 5936)
- NSudo64x.exe (PID: 1280)
- NSudo64x.exe (PID: 7476)
- NSudo64x.exe (PID: 4628)
- NSudo64x.exe (PID: 6228)
- NSudo64x.exe (PID: 4120)
- NSudo64x.exe (PID: 4112)
- NSudo64x.exe (PID: 7448)
- NSudo64x.exe (PID: 924)
- NSudo64x.exe (PID: 7932)
- NSudo64x.exe (PID: 1116)
- NSudo64x.exe (PID: 5352)
- NSudo64x.exe (PID: 6800)
- NSudo64x.exe (PID: 1020)
- NSudo64x.exe (PID: 2244)
- NSudo64x.exe (PID: 2320)
- NSudo64x.exe (PID: 7704)
- NSudo64x.exe (PID: 7280)
Decoding a file from Base64 using CertUtil
- cmd.exe (PID: 8176)
INFO
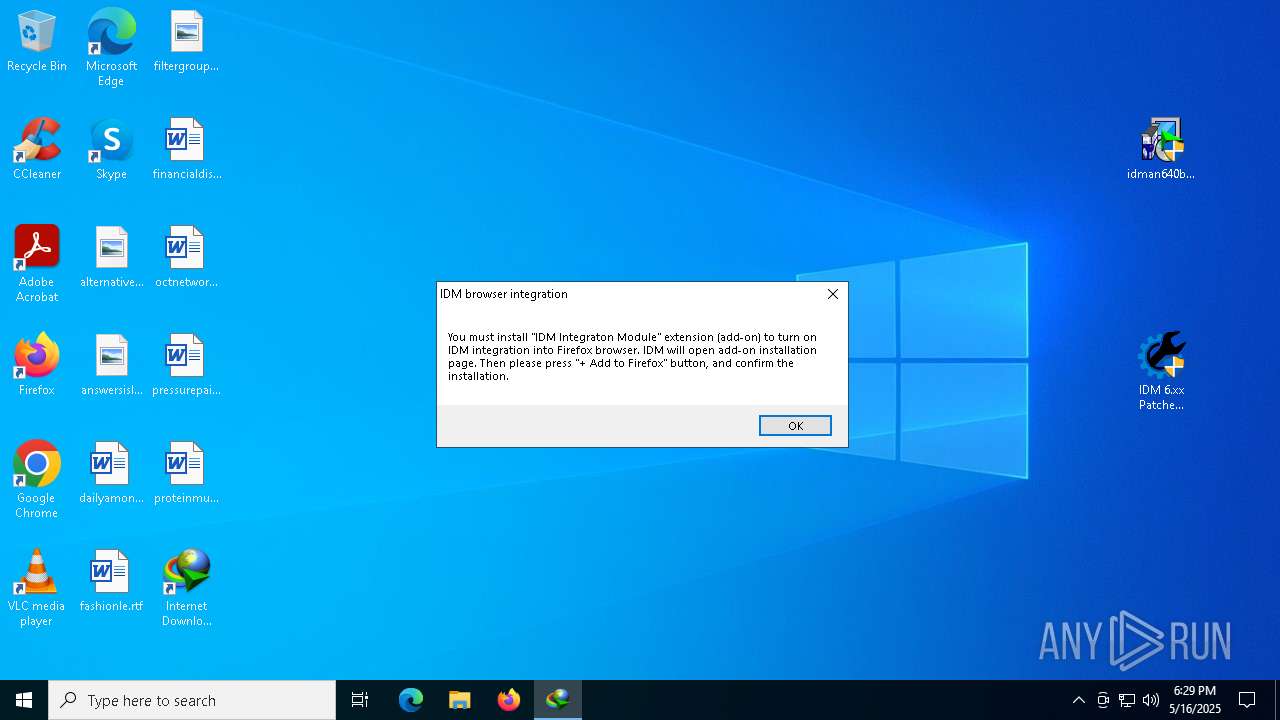
Application launched itself
- firefox.exe (PID: 5408)
- firefox.exe (PID: 6972)
- firefox.exe (PID: 1228)
- firefox.exe (PID: 7420)
- msedge.exe (PID: 7284)
- msedge.exe (PID: 8164)
- msedge.exe (PID: 8068)
The sample compiled with english language support
- firefox.exe (PID: 5408)
- WinRAR.exe (PID: 6156)
- WinRAR.exe (PID: 7984)
- IDMan.exe (PID: 2984)
- rundll32.exe (PID: 7712)
- IDM 6.xx Patcher v2.3.exe (PID: 3796)
- cmd.exe (PID: 8176)
- certutil.exe (PID: 3240)
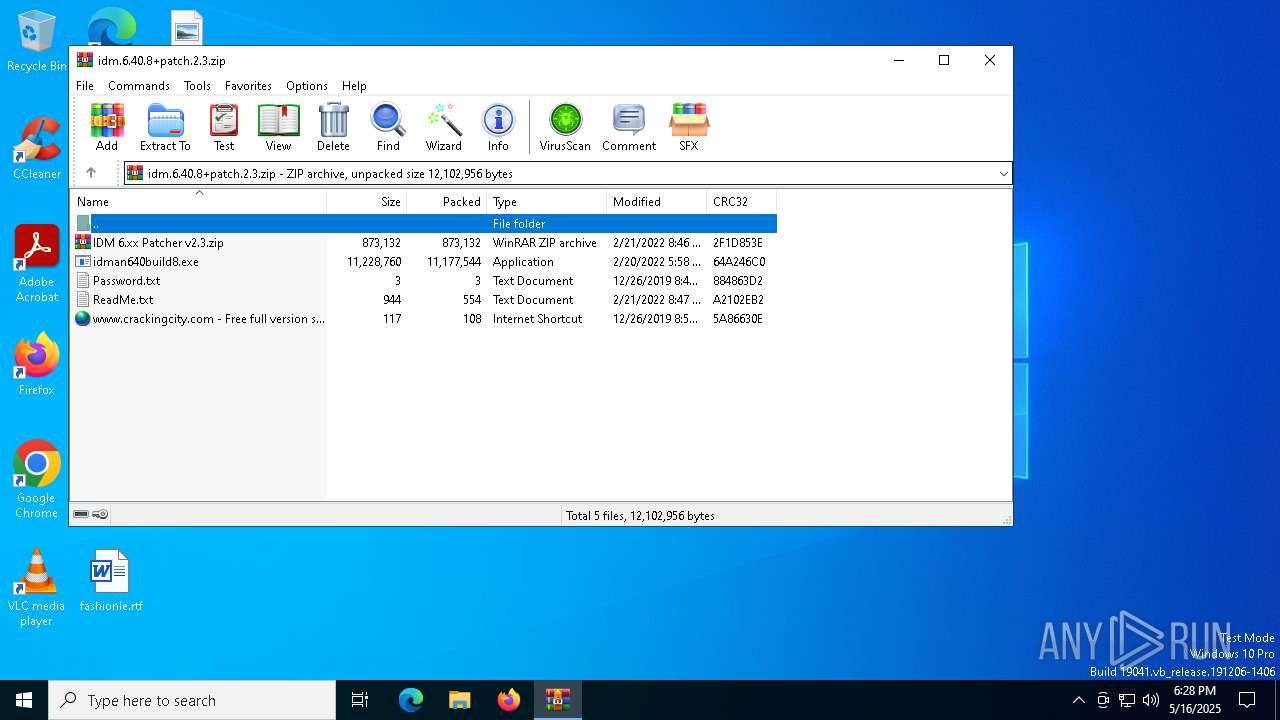
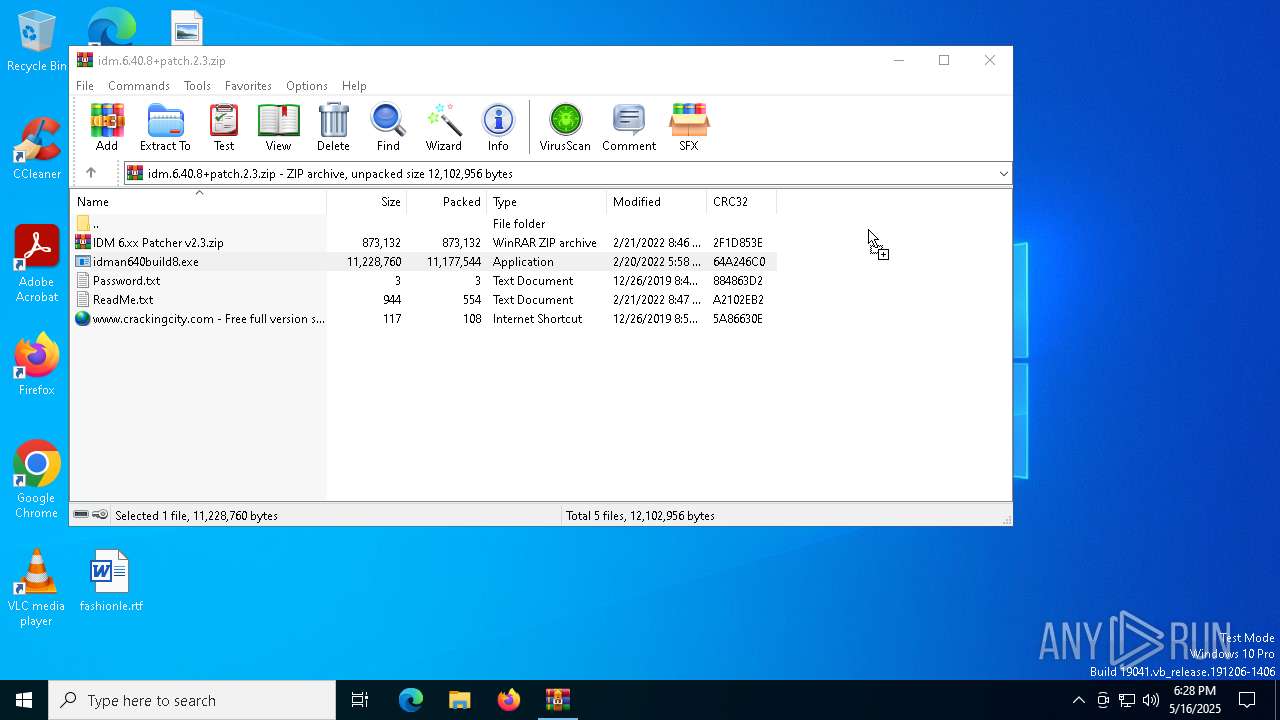
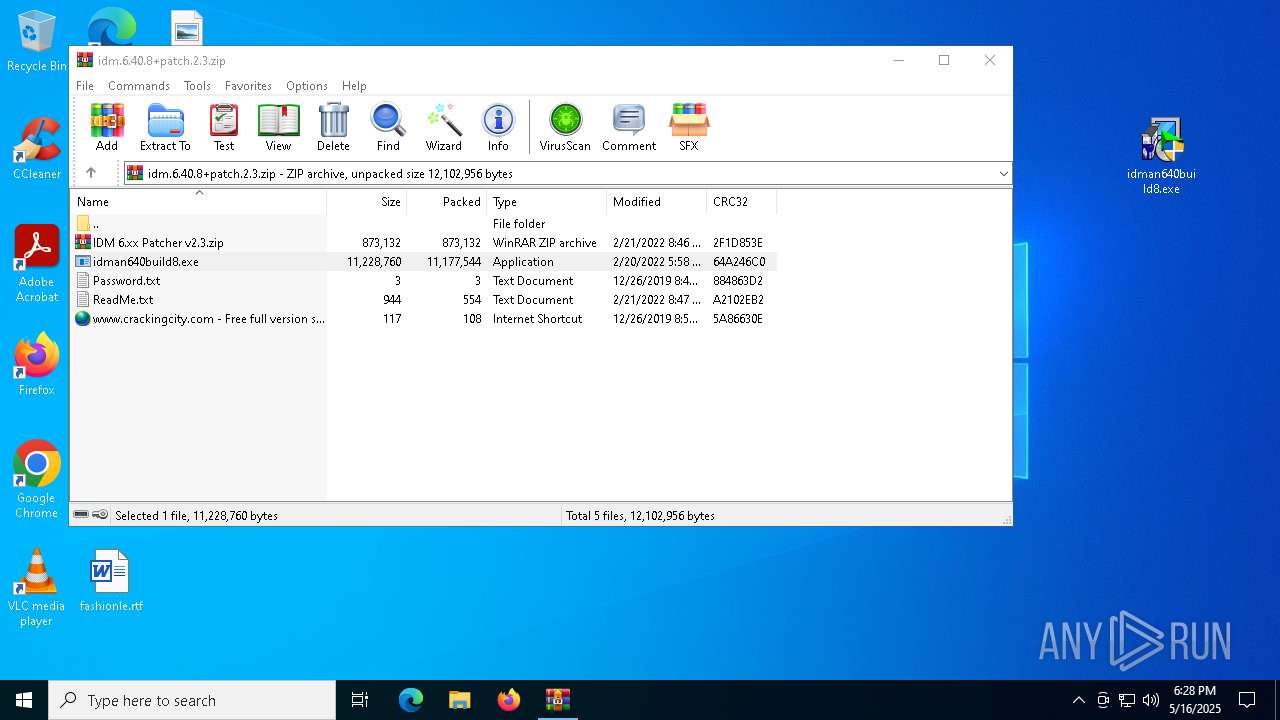
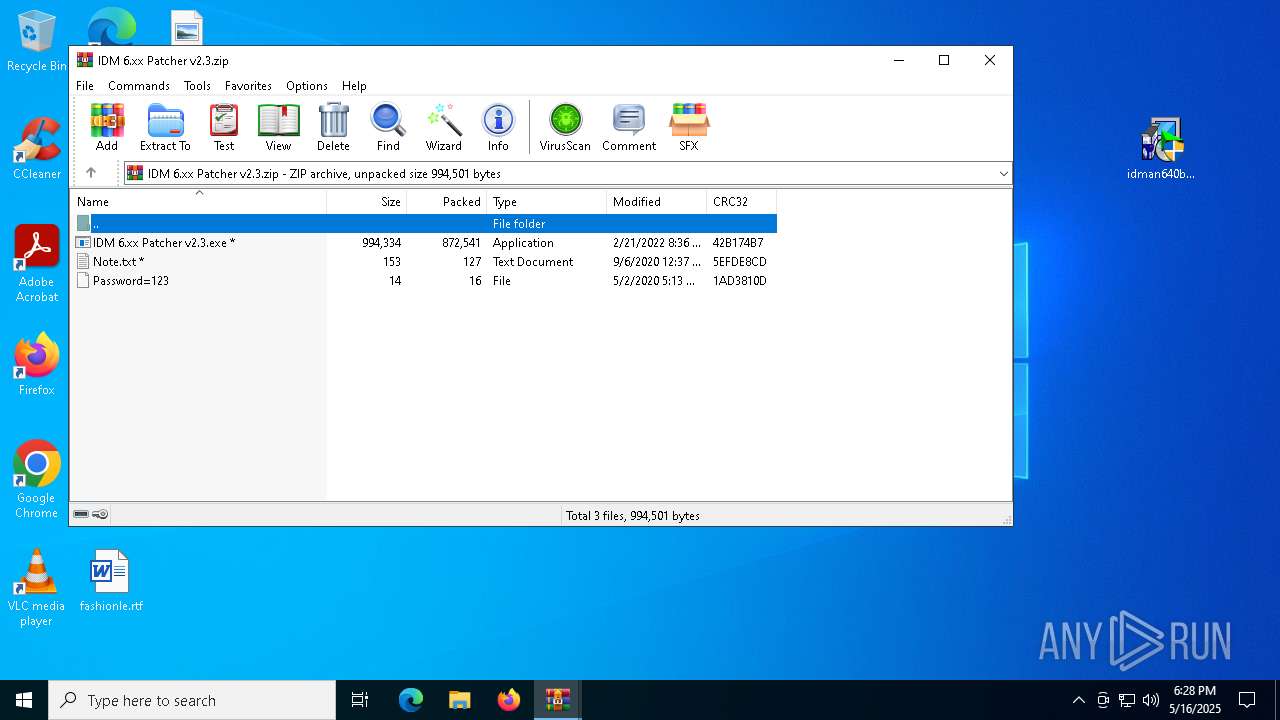
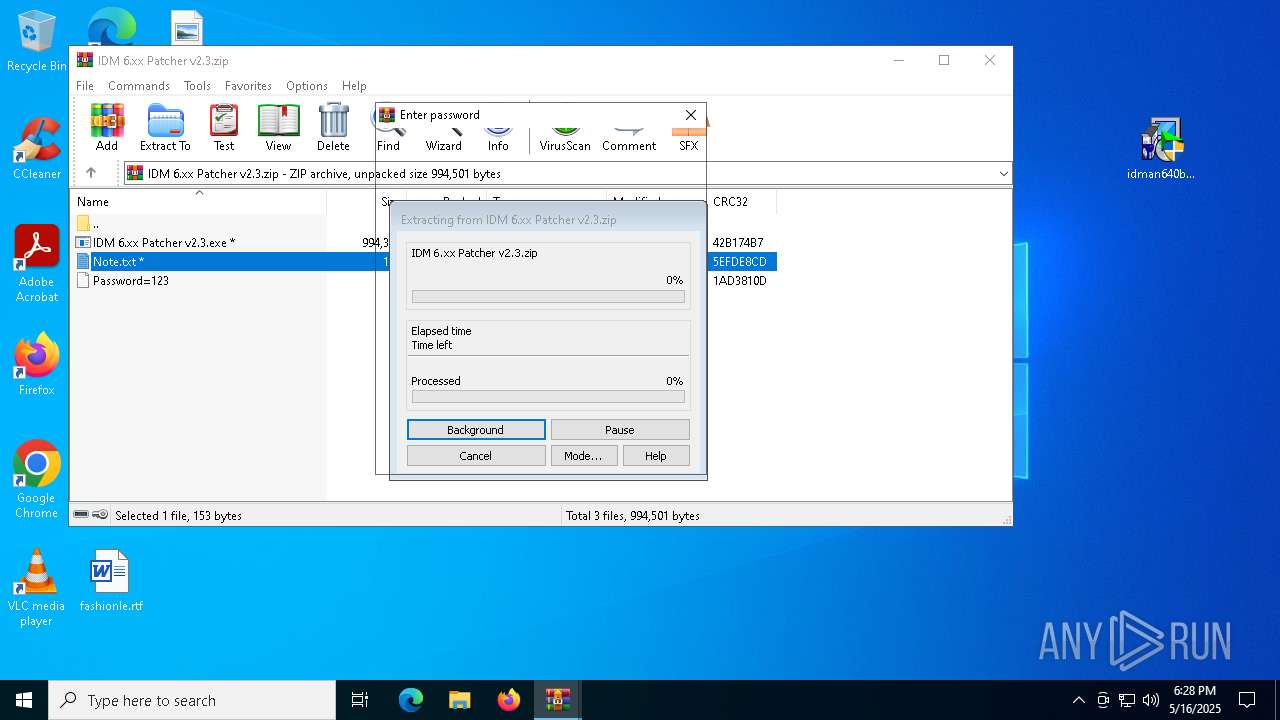
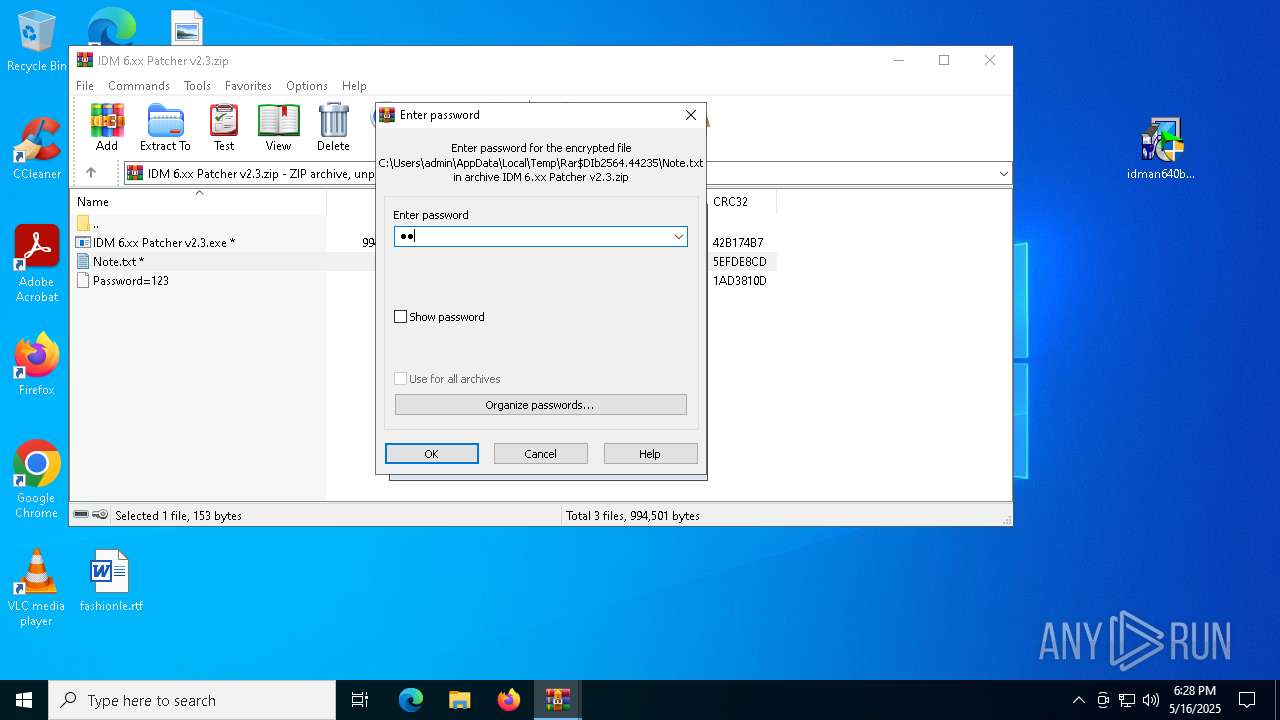
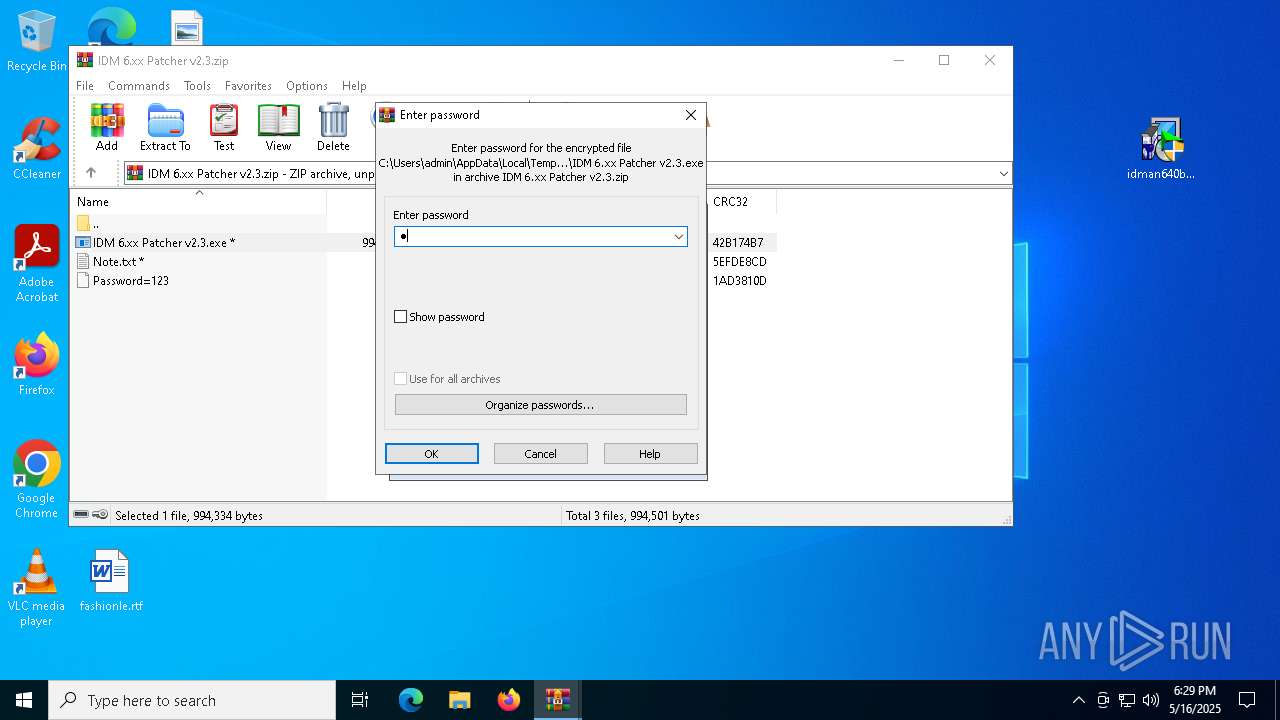
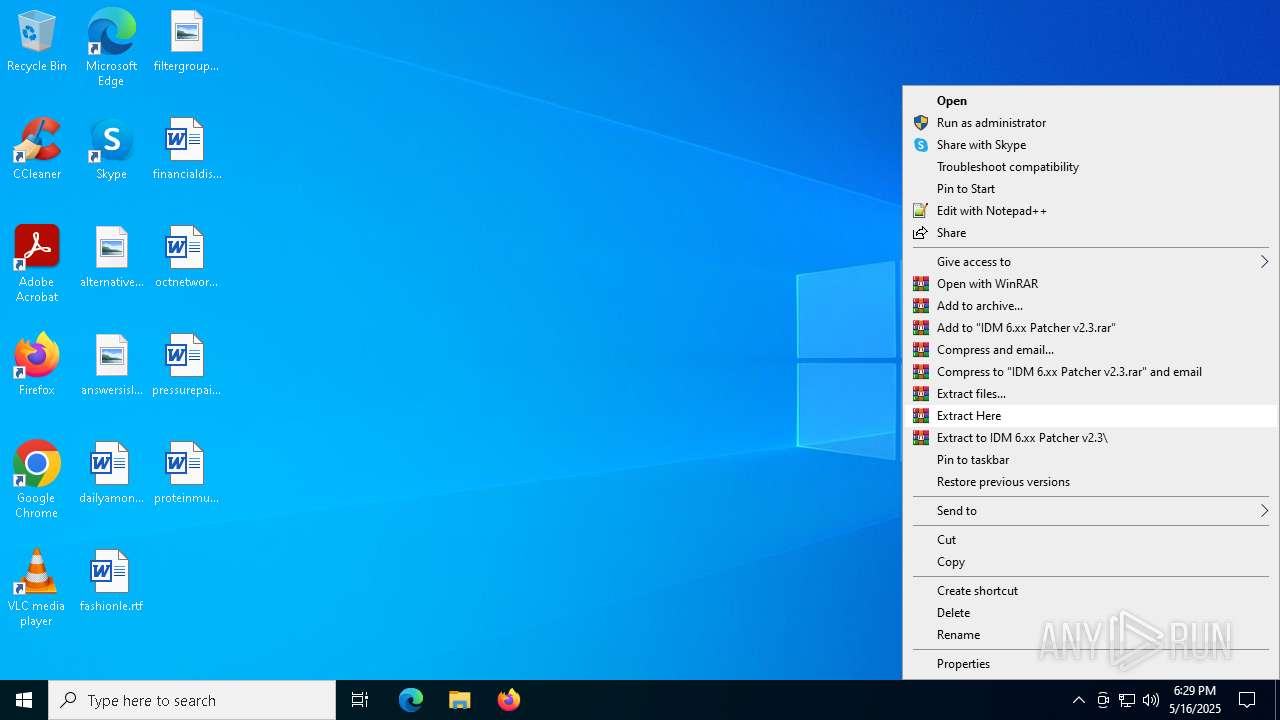
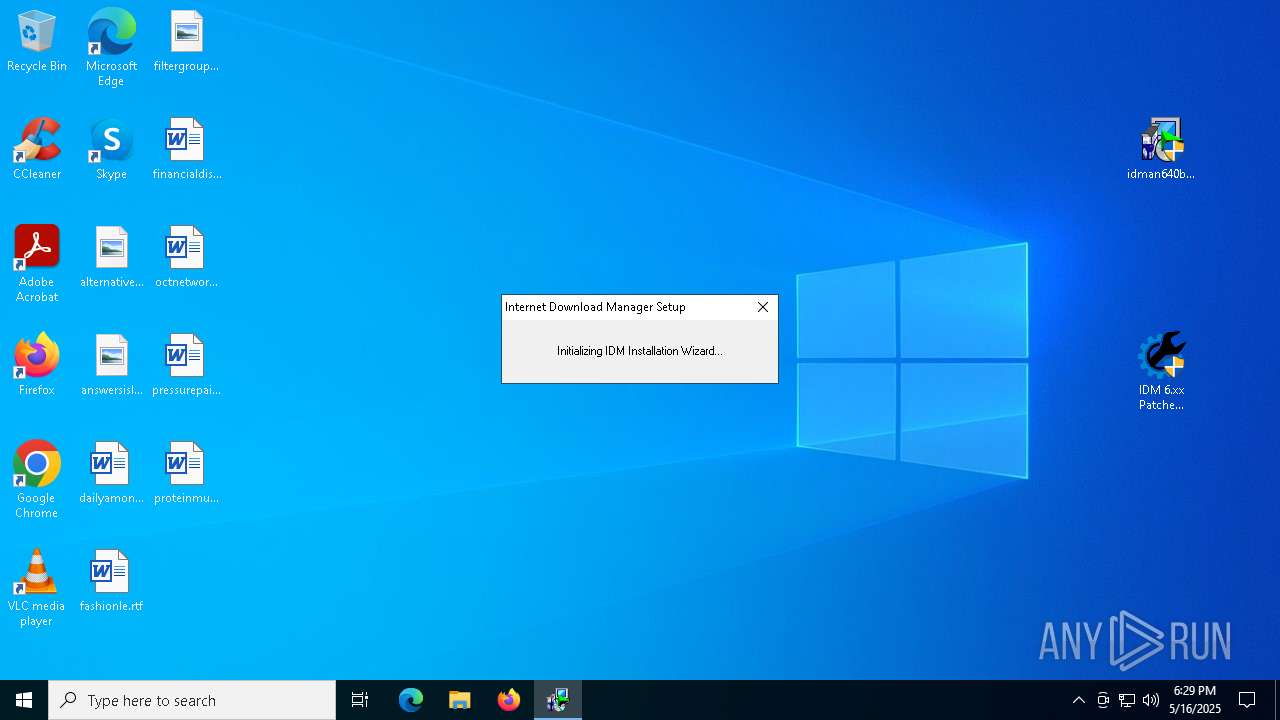
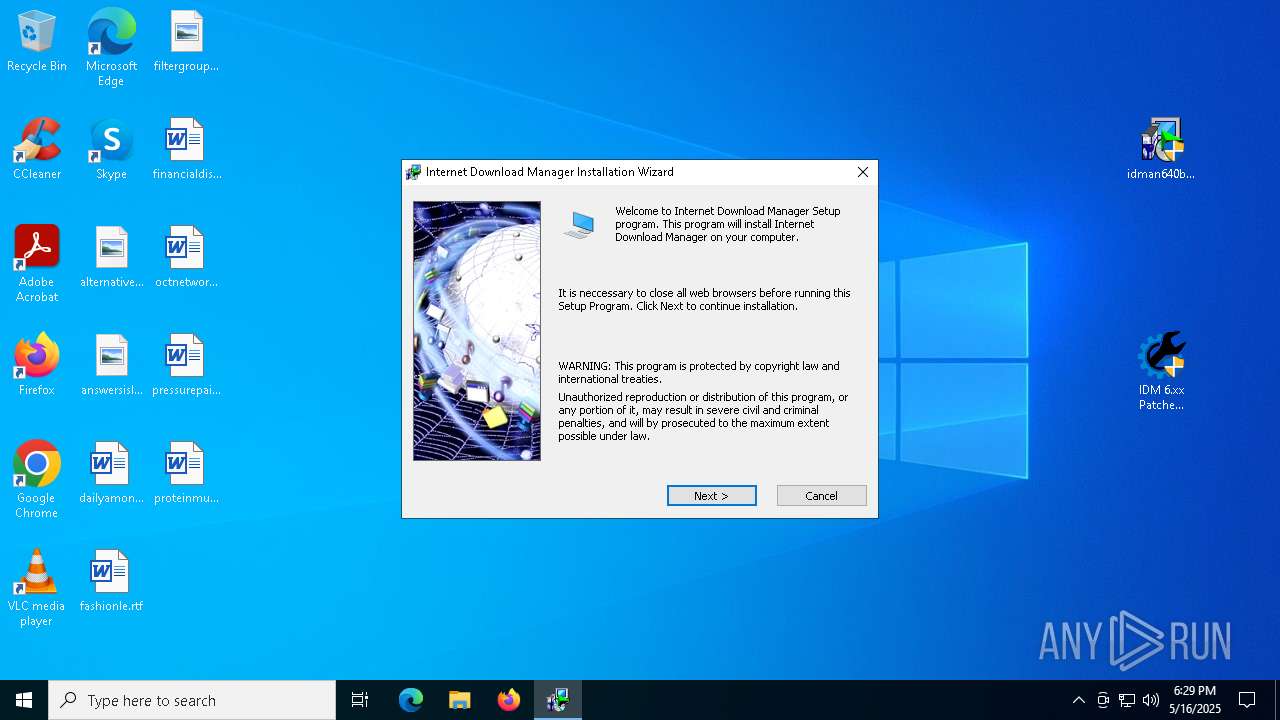
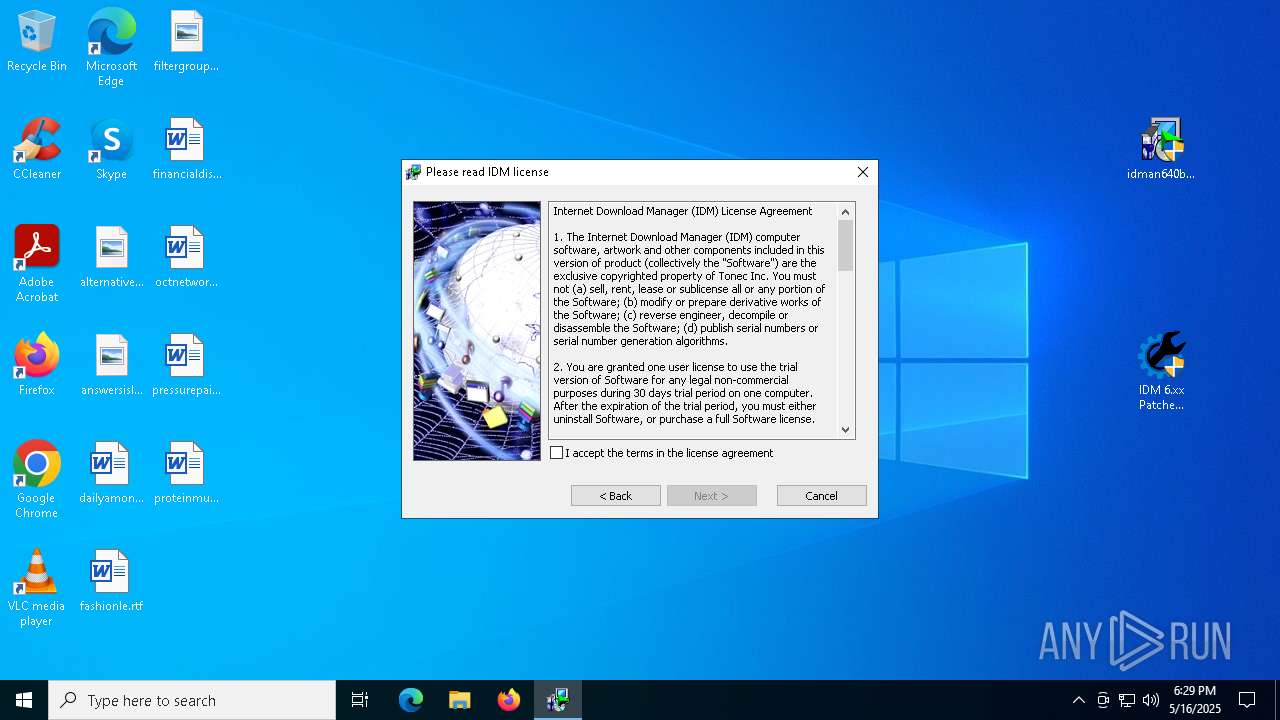
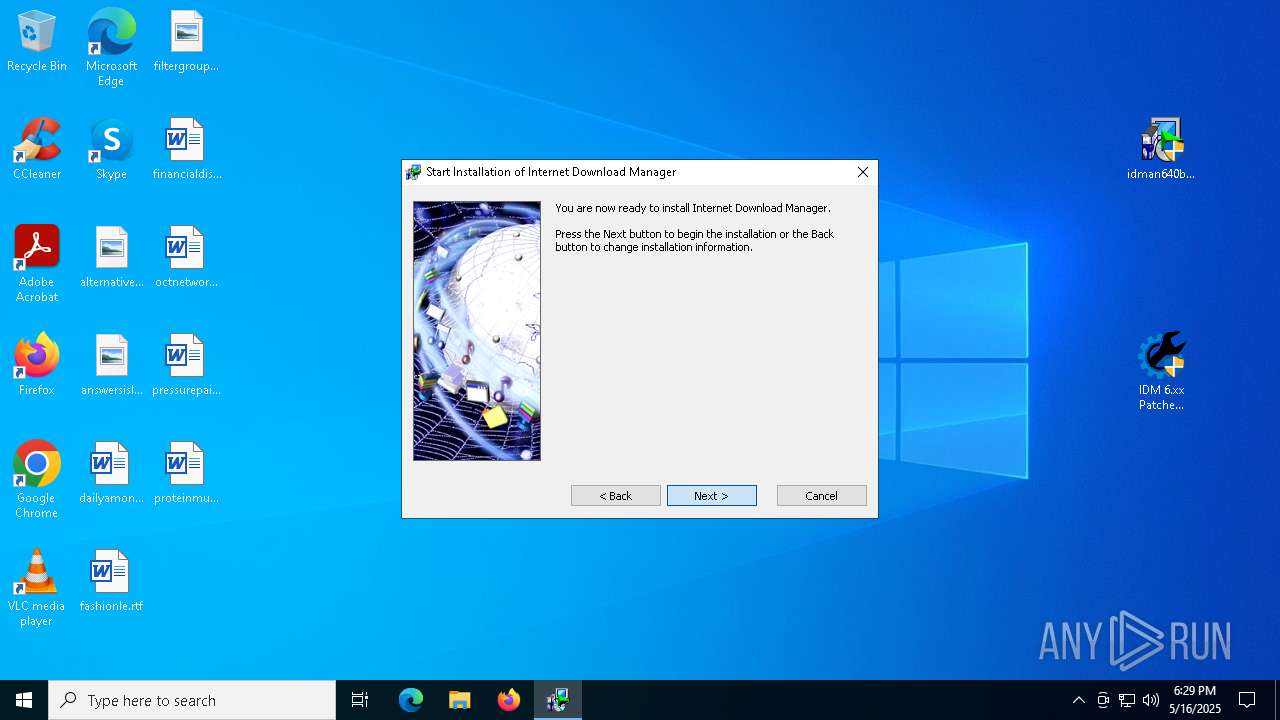
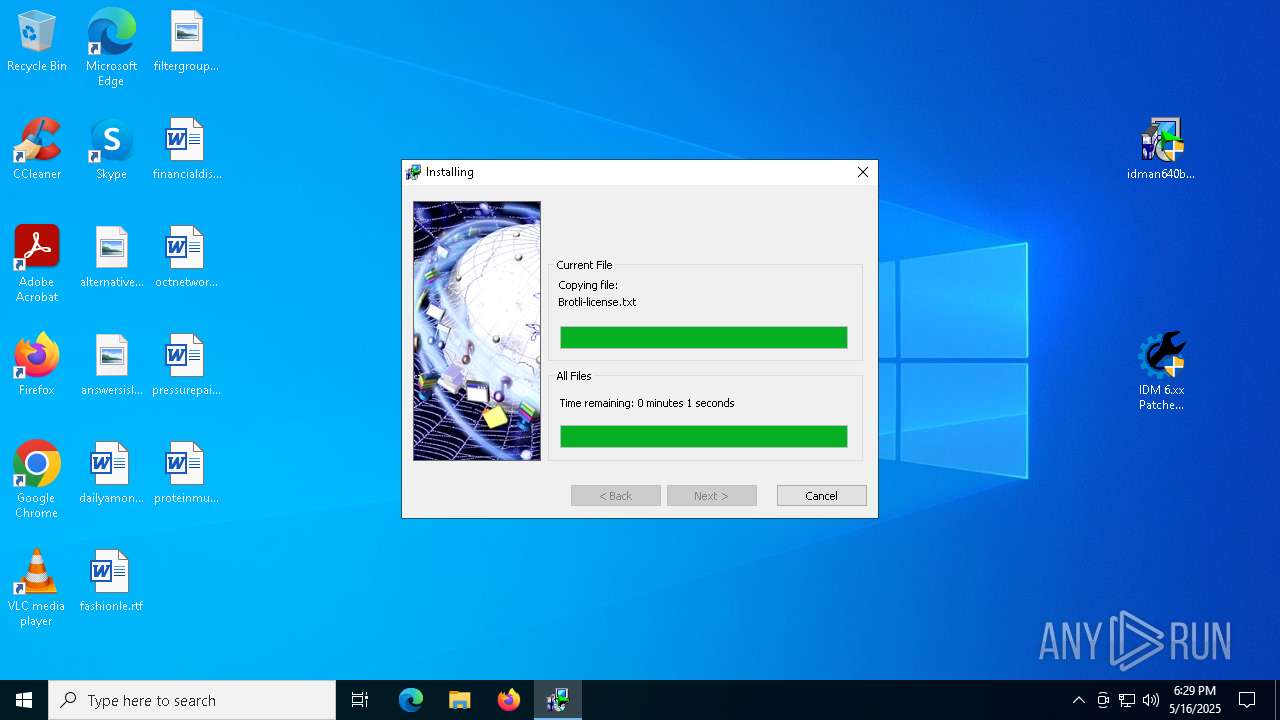
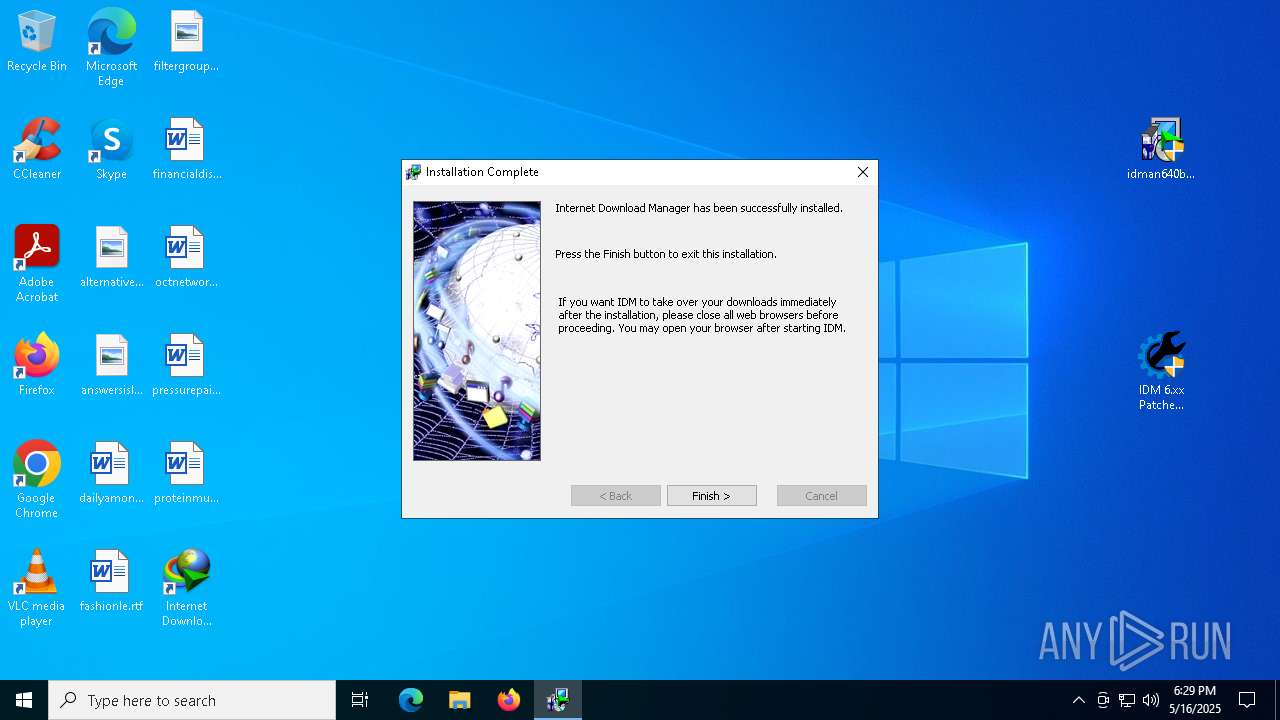
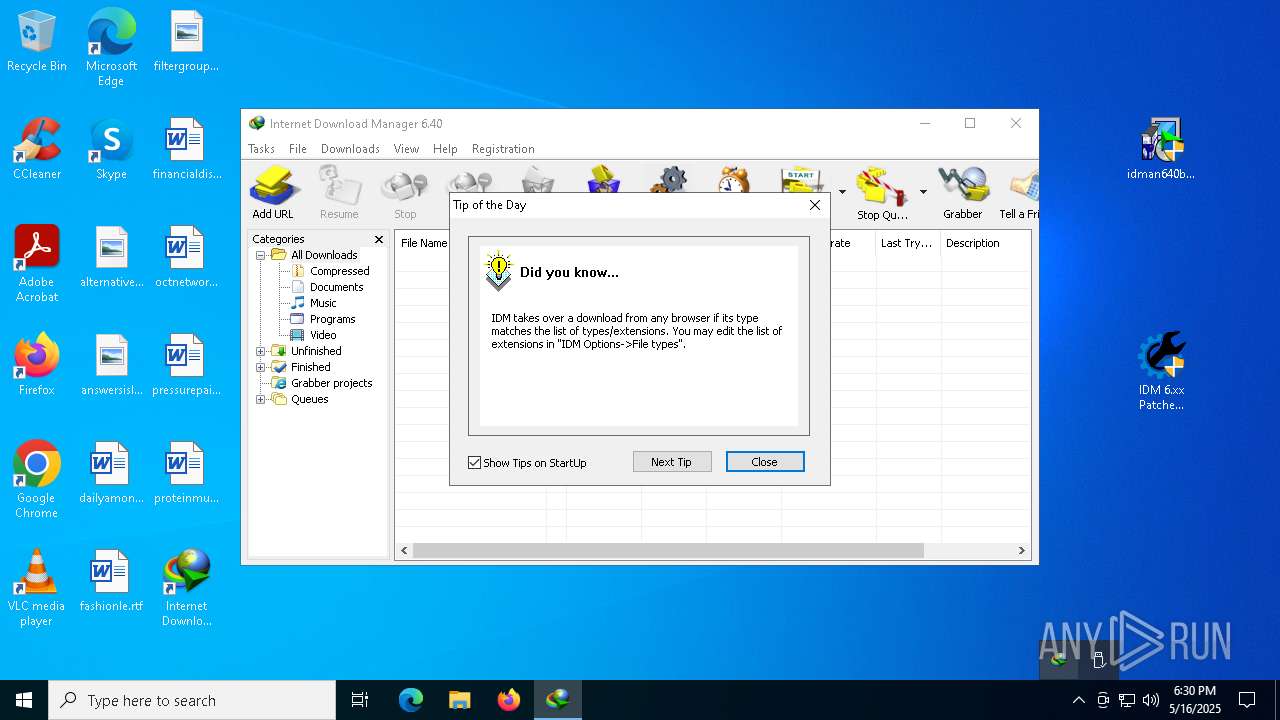
Manual execution by a user
- WinRAR.exe (PID: 6156)
- WinRAR.exe (PID: 7984)
- idman640build8.exe (PID: 7600)
- idman640build8.exe (PID: 7964)
- firefox.exe (PID: 1228)
- IDM 6.xx Patcher v2.3.exe (PID: 3796)
- IDM 6.xx Patcher v2.3.exe (PID: 6852)
- msedge.exe (PID: 8068)
Reads security settings of Internet Explorer
- notepad.exe (PID: 5176)
- notepad.exe (PID: 5728)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6156)
- WinRAR.exe (PID: 2564)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 6156)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6156)
- WinRAR.exe (PID: 2564)
- WinRAR.exe (PID: 7984)
Reads the software policy settings
- slui.exe (PID: 4892)
Checks supported languages
- idman640build8.exe (PID: 7964)
- IDM1.tmp (PID: 6080)
Reads the computer name
- idman640build8.exe (PID: 7964)
INTERNETDOWNLOADMANAGER mutex has been found
- idman640build8.exe (PID: 7964)
Create files in a temporary directory
- idman640build8.exe (PID: 7964)
Starts MODE.COM to configure console settings
- mode.com (PID: 6564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
694
Monitored processes
553
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | FART -c -i "idm.tmp" "3000000e95e" "0000000e95e" | C:\Users\admin\AppData\Local\Temp\ytmp\fart.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 208 | REG DELETE "HKLM\Software\Classes\CLSID\{6DDF00DB-1234-46EC-8356-27E7B2051192}" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | REG DELETE "HKU\.DEFAULT\SOFTWARE\WOW6432Node\Classes\CLSID\{E6871B76-C3C8-44DD-B947-ABFFE144860D}" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | REG DELETE "HKCU\SOFTWARE\WOW6432Node\Classes\CLSID\{E8CF4E59-B7A3-41F2-86C7-82B03334F22A}" /f | C:\Windows\System32\reg.exe | NSudo64x.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | REG DELETE "HKCU\Software\Classes\CLSID\{79873CC5-3951-43ED-BDF9-D8759474B6FD}" /f | C:\Windows\System32\reg.exe | NSudo64x.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | REG DELETE "HKLM\Software\DownloadManager" /f | C:\Windows\System32\reg.exe | NSudo64x.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | REG DELETE "HKCU\Software\Classes\CLSID\{9C9D53D4-A978-43FC-93E2-1C21B529E6D7}" /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3904 --field-trial-handle=2312,i,8951693438068121089,2629808669226516079,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 664 | FART -c -i "idm.tmp" "6a288bc" "6aff8bc" | C:\Users\admin\AppData\Local\Temp\ytmp\fart.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 728 | REG IMPORT "Scansk.reg" | C:\Windows\System32\reg.exe | NSudo64x.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
70 235
Read events
69 259
Write events
787
Delete events
189
Modification events
| (PID) Process: | (5408) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\idm.6.40.8+patch.2.3.zip | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
Executable files
47
Suspicious files
432
Text files
143
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5408 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
154
DNS requests
214
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.180:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.81:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5408 | firefox.exe | GET | 301 | 213.184.85.86:80 | http://archiveteam.org/images/e/e6/Archiveteam.jpg | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.44:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 184.24.77.81:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
5408 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.180:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5408 | firefox.exe | 207.241.237.3:443 | web.archive.org | INTERNET-ARCHIVE | US | whitelisted |
5408 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
5408 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5408 | firefox.exe | 142.250.186.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
5408 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
web.archive.org |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
7360 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |