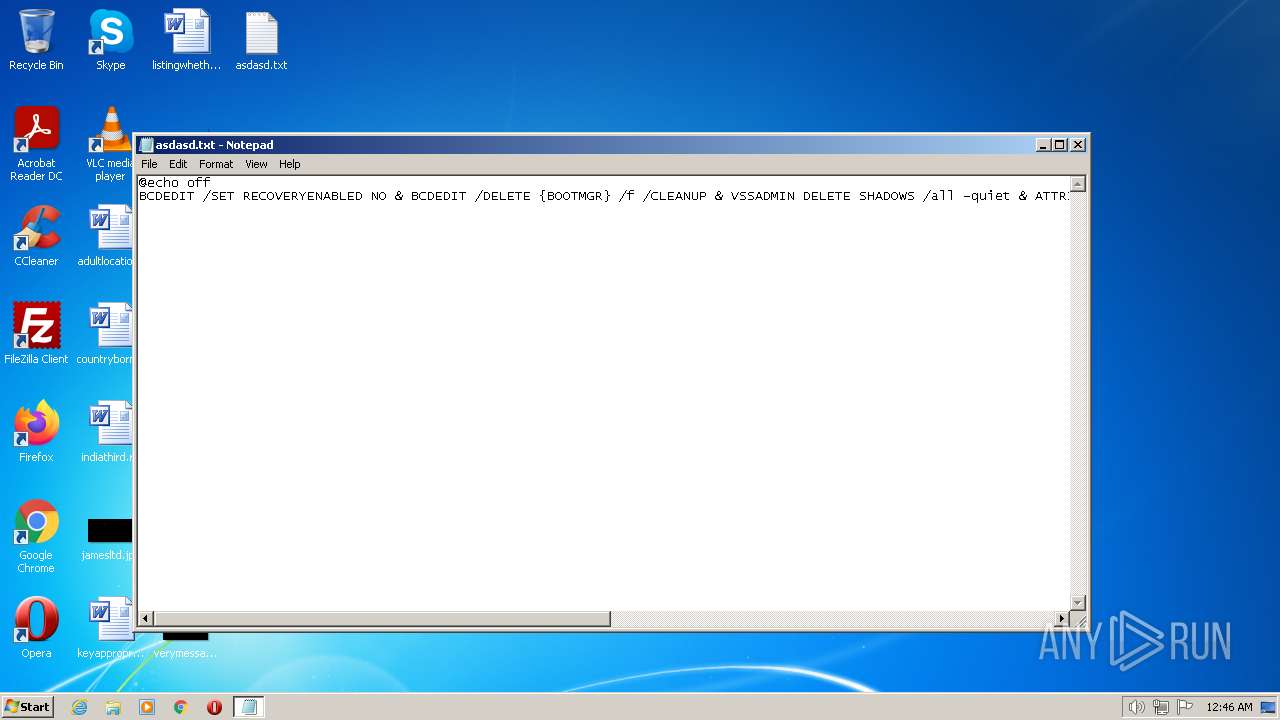
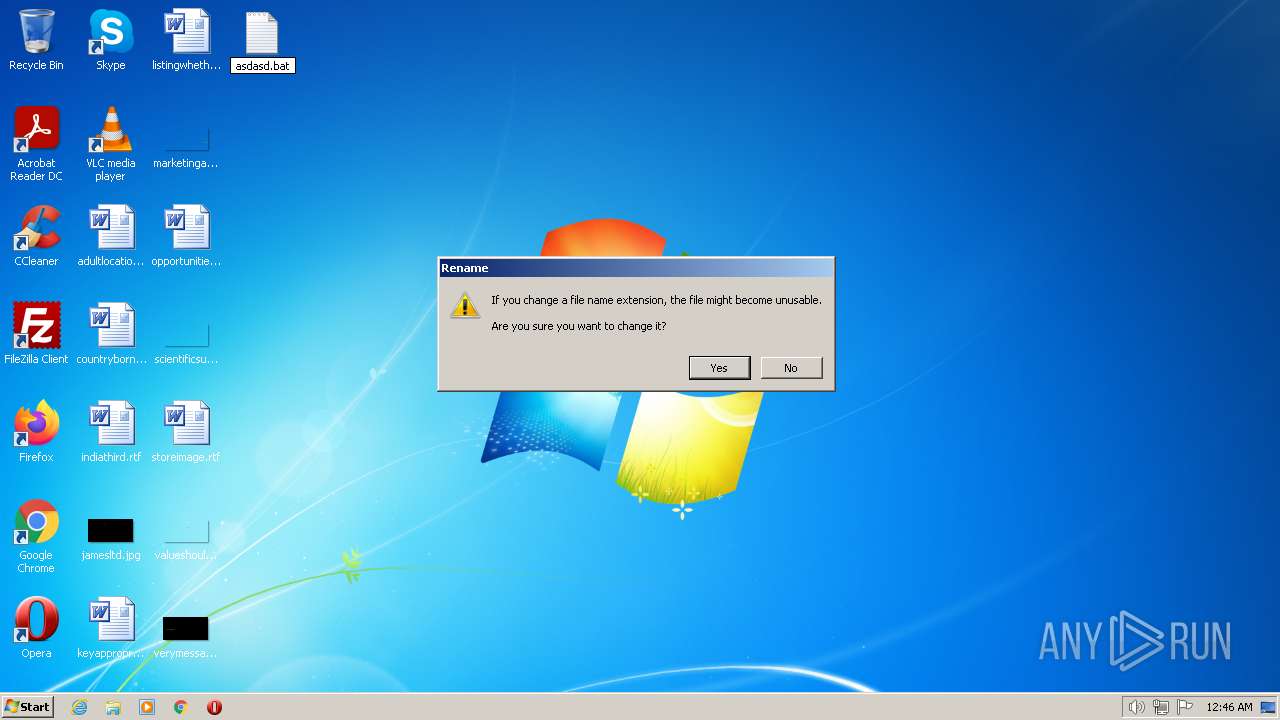
| File name: | asdasd.txt |
| Full analysis: | https://app.any.run/tasks/42f6ac21-4b15-41fc-8521-b6be81fdbfc5 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 00:46:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 393457D7C5C099F33FC57B1149DFC0DB |
| SHA1: | 9522B1B78A20557E57AE5C872604467717DEDE45 |
| SHA256: | 48C7DBD6E1DD60BD379E74E317FACCFB2748A19C27BE38BE25F60B0470AFAFF7 |
| SSDEEP: | 6:hgWm6ghF+2OgF128PNSg/8fhrhy3Idw9PvJo9wsUZ7G3kbfb3bgYD:mLnQMQgEZV6ZiUBgkbrbgYD |
MALICIOUS
Creates a writable file the system directory
- NOTEPAD.EXE (PID: 3032)
- printfilterpipelinesvc.exe (PID: 3756)
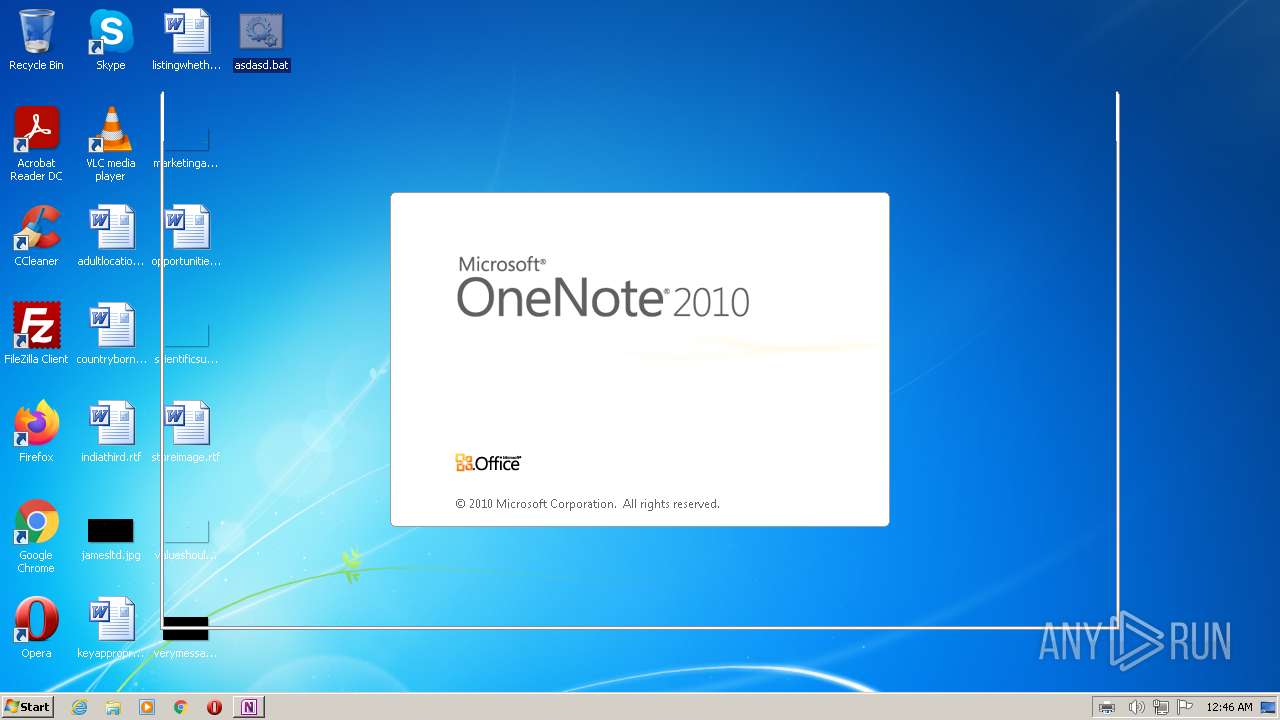
Unusual execution from MS Office
- printfilterpipelinesvc.exe (PID: 3756)
SUSPICIOUS
No suspicious indicators.INFO
Checks supported languages
- ONENOTE.EXE (PID: 2944)
Reads Microsoft Office registry keys
- ONENOTE.EXE (PID: 2944)
Reads the computer name
- ONENOTE.EXE (PID: 2944)
Manual execution by a user
- NOTEPAD.EXE (PID: 3032)
Checks proxy server information
- CLVIEW.EXE (PID: 1860)
Reads Internet Explorer settings
- CLVIEW.EXE (PID: 1860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\Desktop\asdasd.txt" | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
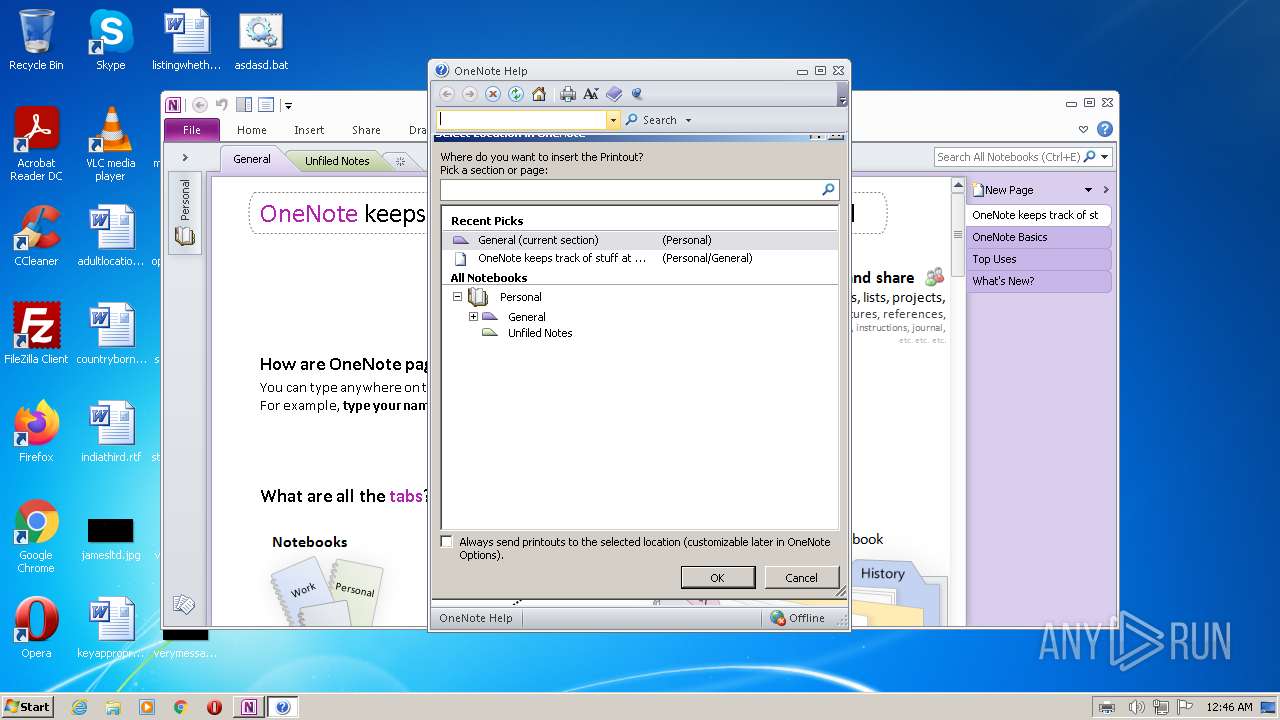
| 1860 | "C:\Program Files\Microsoft Office\Office14\CLVIEW.EXE" "ONENOTE" "Microsoft OneNote" | C:\Program Files\Microsoft Office\Office14\CLVIEW.EXE | — | ONENOTE.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Help Viewer Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
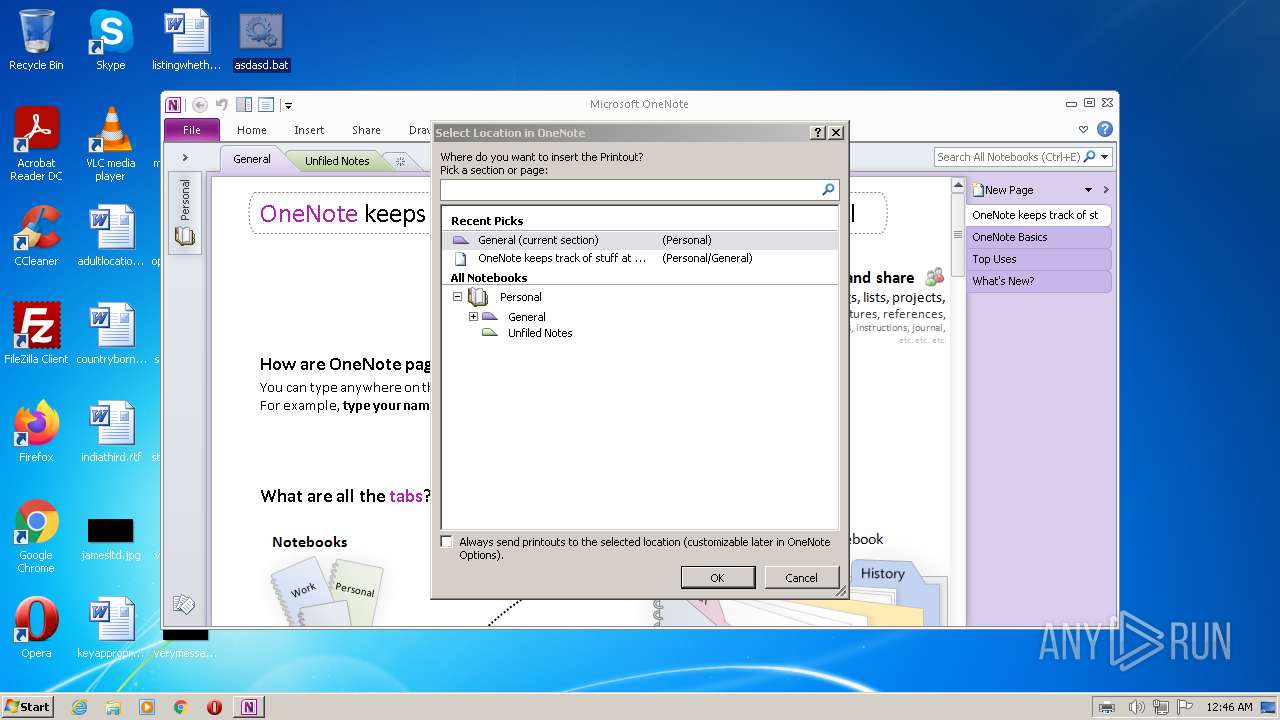
| 2944 | /insertdoc "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{78C6B0E9-7B58-4570-922A-B253F42F42A9}.xps" 133147612131550000 | C:\Program Files\Microsoft Office\Office14\ONENOTE.EXE | — | printfilterpipelinesvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneNote Exit code: 0 Version: 14.0.6022.1000 Modules
| |||||||||||||||
| 3032 | "C:\Windows\System32\NOTEPAD.EXE" /p C:\Users\admin\Desktop\asdasd.bat | C:\Windows\System32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | C:\Windows\system32\printfilterpipelinesvc.exe -Embedding | C:\Windows\system32\printfilterpipelinesvc.exe | — | svchost.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Print Filter Pipeline Host Exit code: 0 Version: 6.1.7601.24537 (win7sp1_ldr_escrow.191114-1547) Modules
| |||||||||||||||
Total events
2 094
Read events
2 019
Write events
72
Delete events
3
Modification events
| (PID) Process: | (3756) printfilterpipelinesvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | OneNoteFiles |
Value: | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2944) ONENOTE.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
54
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3756 | printfilterpipelinesvc.exe | C:\Windows\system32\spool\PRINTERS\PP15qsw7cibyad9v3dmuylmvk.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | printfilterpipelinesvc.exe | C:\Windows\system32\spool\PRINTERS\PPr80tjy504g84c0untr7qo4p2b.TMP | — | |
MD5:— | SHA256:— | |||
| 3756 | printfilterpipelinesvc.exe | C:\Windows\system32\spool\PRINTERS\PP04kvdfuu4n0bglqbw2fr9dwde.TMP | — | |
MD5:— | SHA256:— | |||
| 2944 | ONENOTE.EXE | C:\Users\admin\AppData\Local\Temp\CVR44BA.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3032 | NOTEPAD.EXE | C:\Windows\system32\spool\PRINTERS\00002.SPL | compressed | |
MD5:— | SHA256:— | |||
| 3756 | printfilterpipelinesvc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{78C6B0E9-7B58-4570-922A-B253F42F42A9}.xps | compressed | |
MD5:— | SHA256:— | |||
| 1860 | CLVIEW.EXE | C:\Users\admin\AppData\Local\Temp\IMT53B1.tmp | binary | |
MD5:453FDB783008B8E22E87FF071A71860C | SHA256:58B421A26F4AF76DA1282FD12DE11F60C37E3EDD2067C4308BE874DE0D750F12 | |||
| 1860 | CLVIEW.EXE | C:\Users\admin\AppData\Local\Temp\IMT53C4.tmp | binary | |
MD5:E187E0D7DAFE0CFCF7991382765D13B0 | SHA256:437DF79CDF5127A052BCF459FAF16D99784C850344470551ACA1D870B9C206FC | |||
| 1860 | CLVIEW.EXE | C:\Users\admin\AppData\Local\Temp\IMT53A0.tmp | binary | |
MD5:73E5F16AA352D7188E7266C6C20EAAF1 | SHA256:57408D0184C465A18379CAAF84030C6835B480BC644804F5670A02B985E84A0C | |||
| 1860 | CLVIEW.EXE | C:\Users\admin\AppData\Local\Temp\IMT53B0.tmp | binary | |
MD5:4BE2AEDDA24E0539C95564B48CA9D8BA | SHA256:E4D153F74AC21D4212A83FE030EE7A407B5FDFE2D3A8145F3E826532BD796893 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report