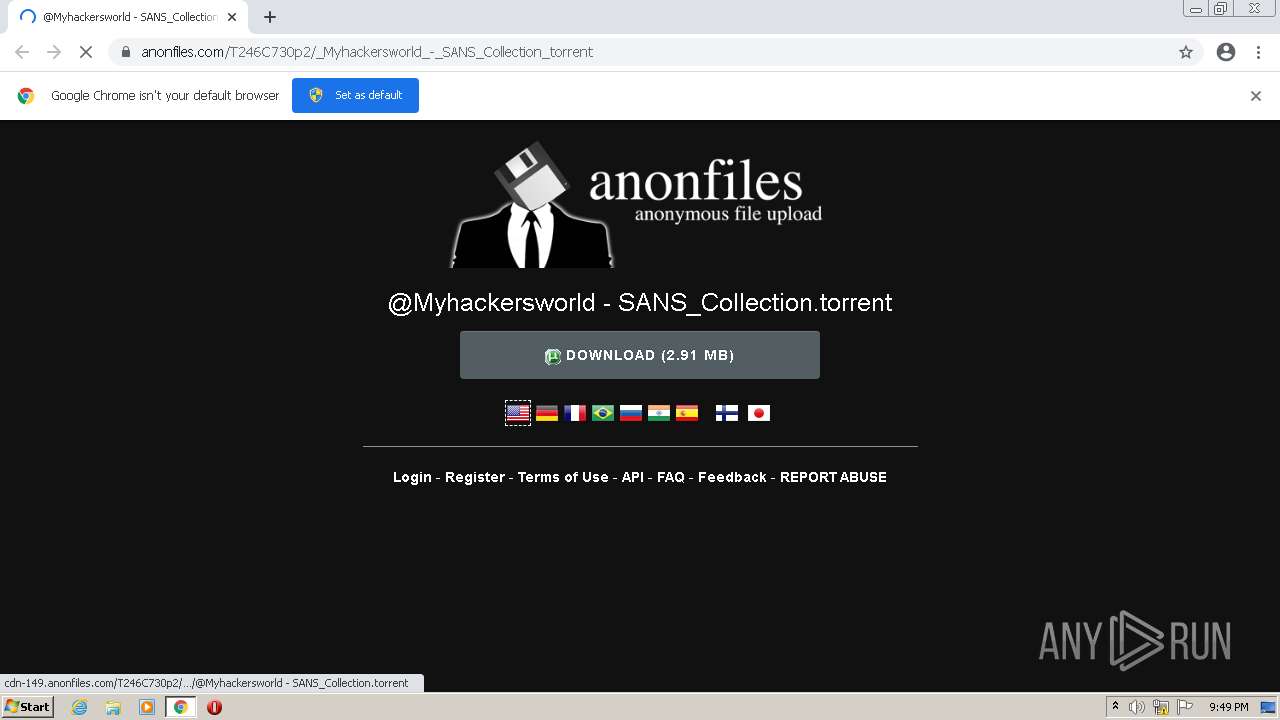
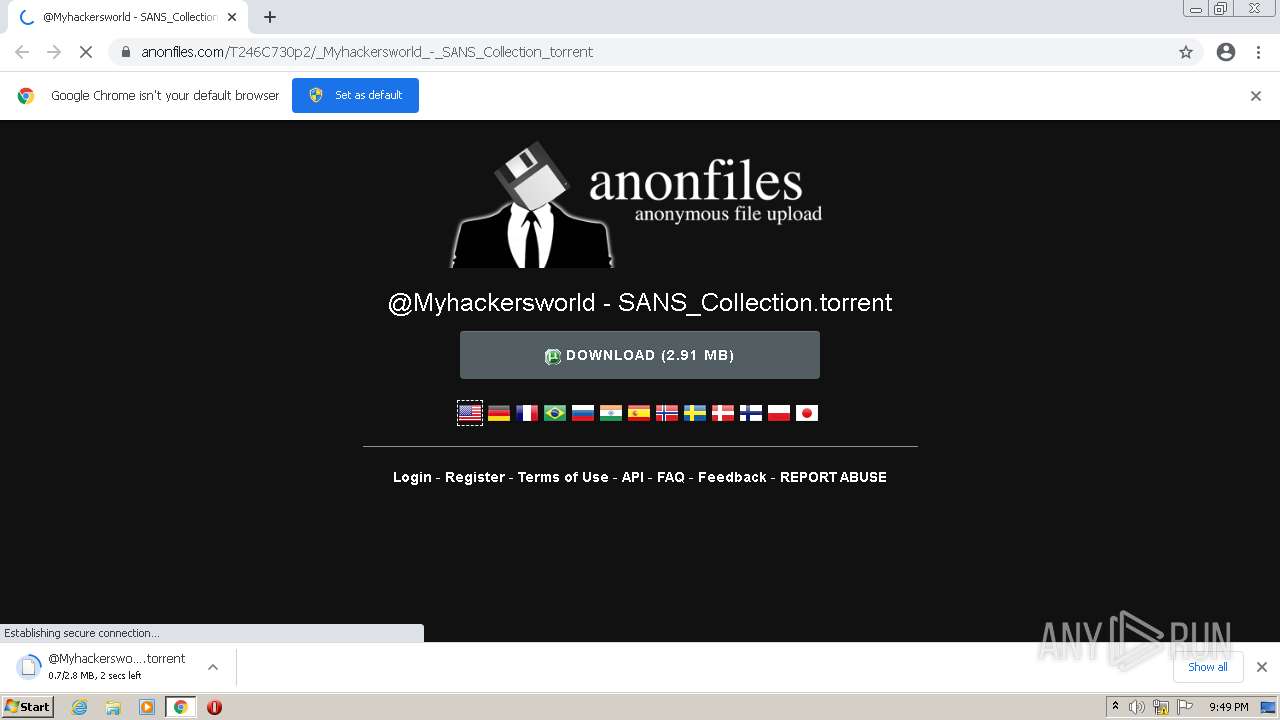
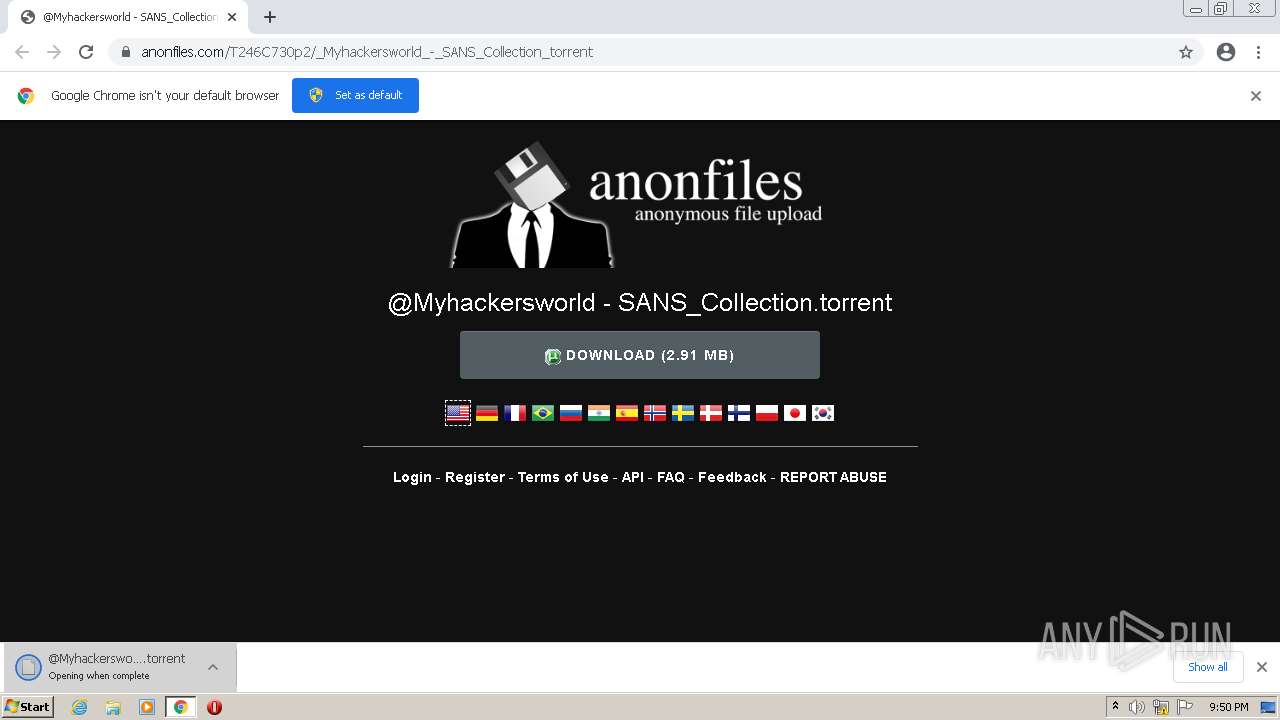
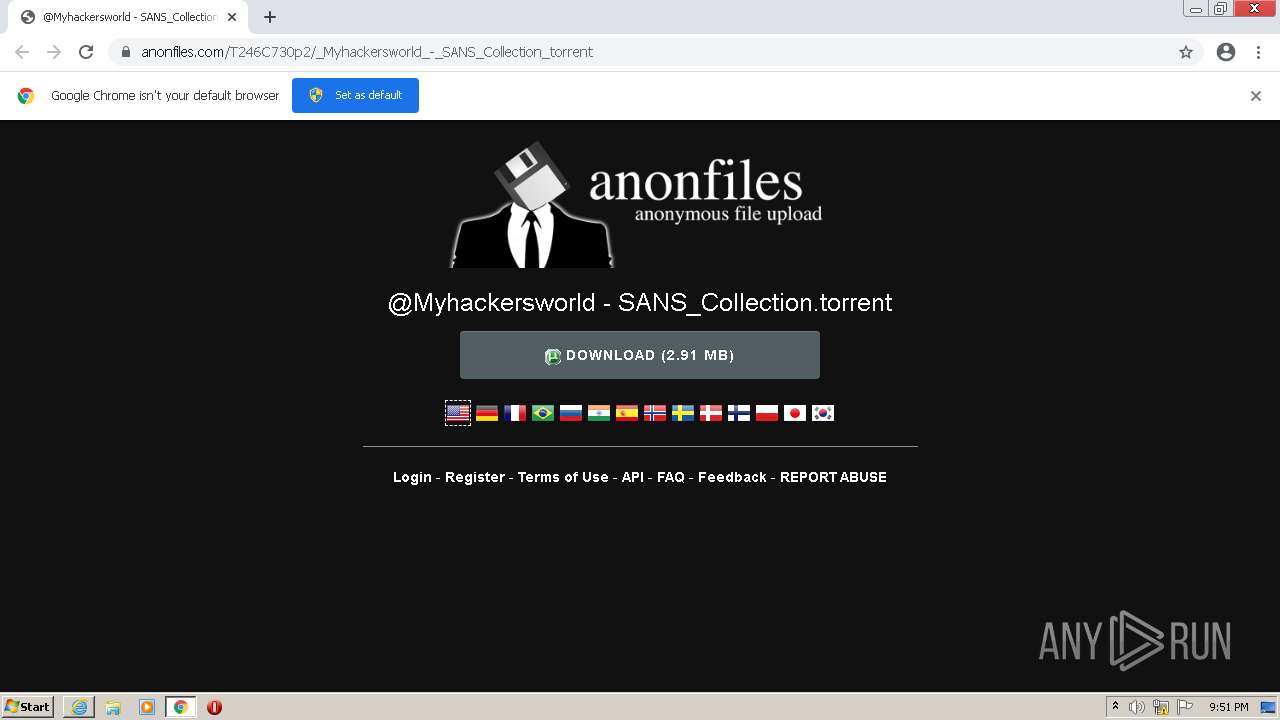
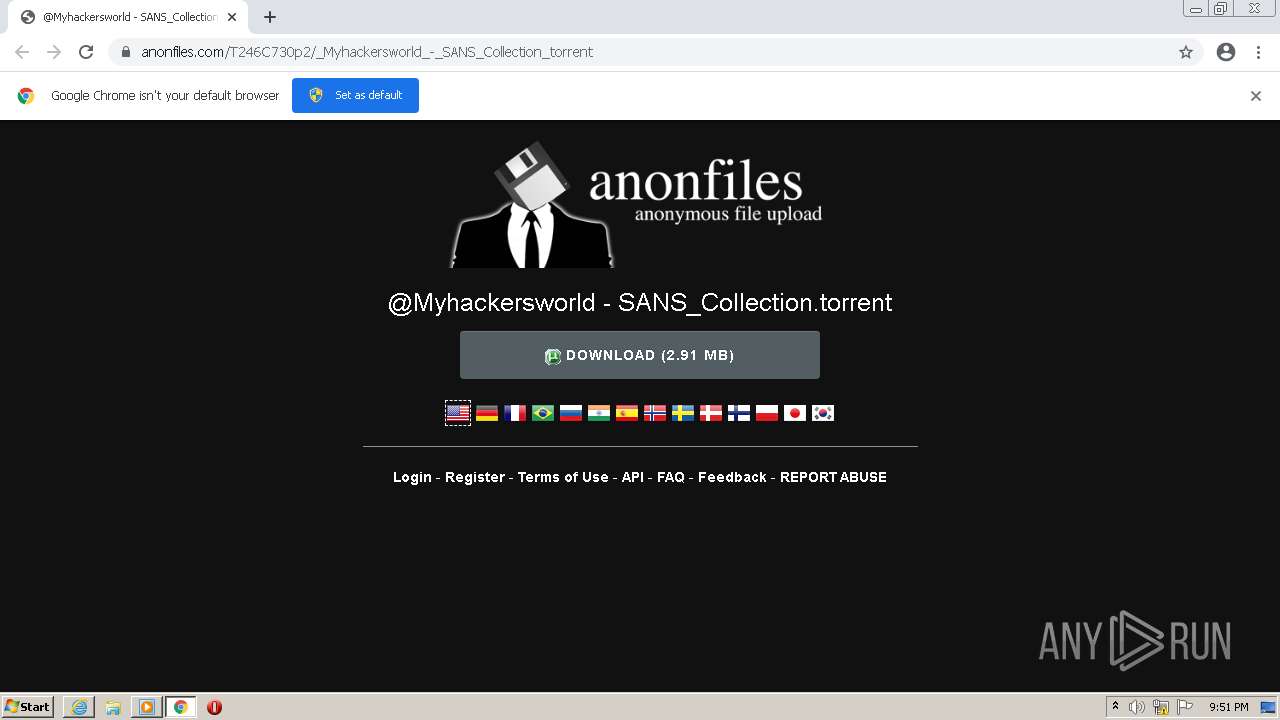
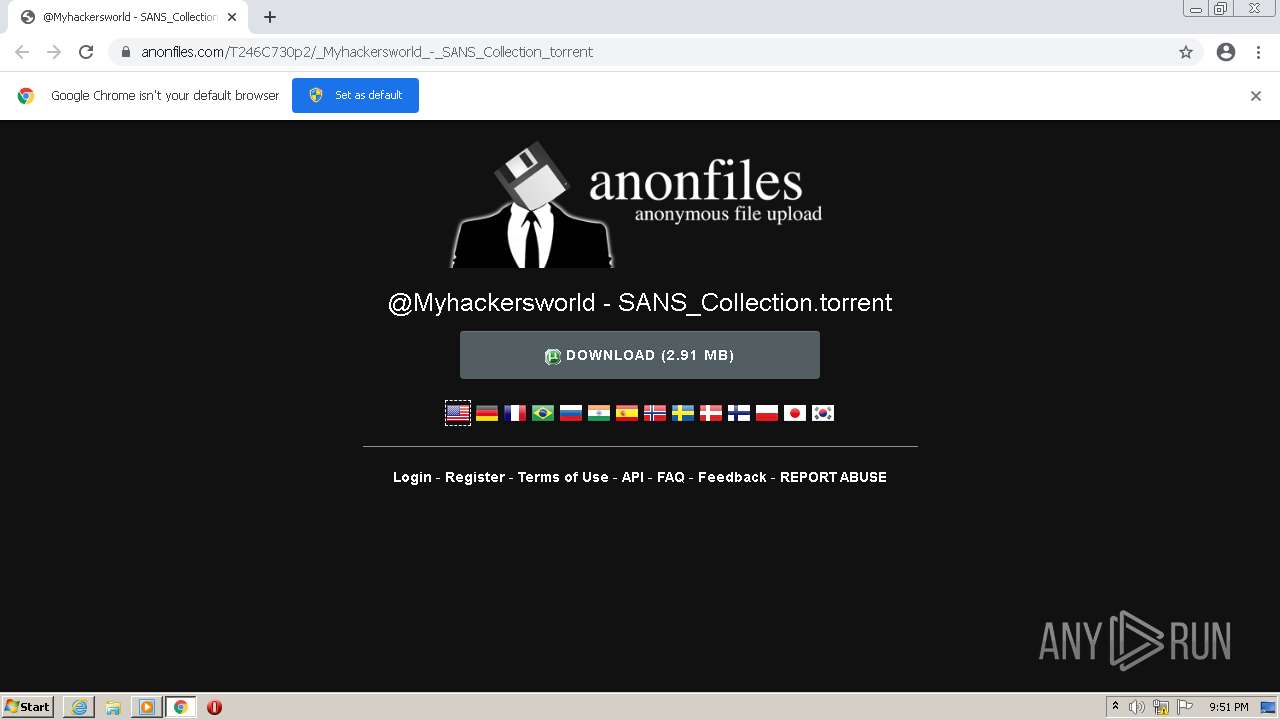
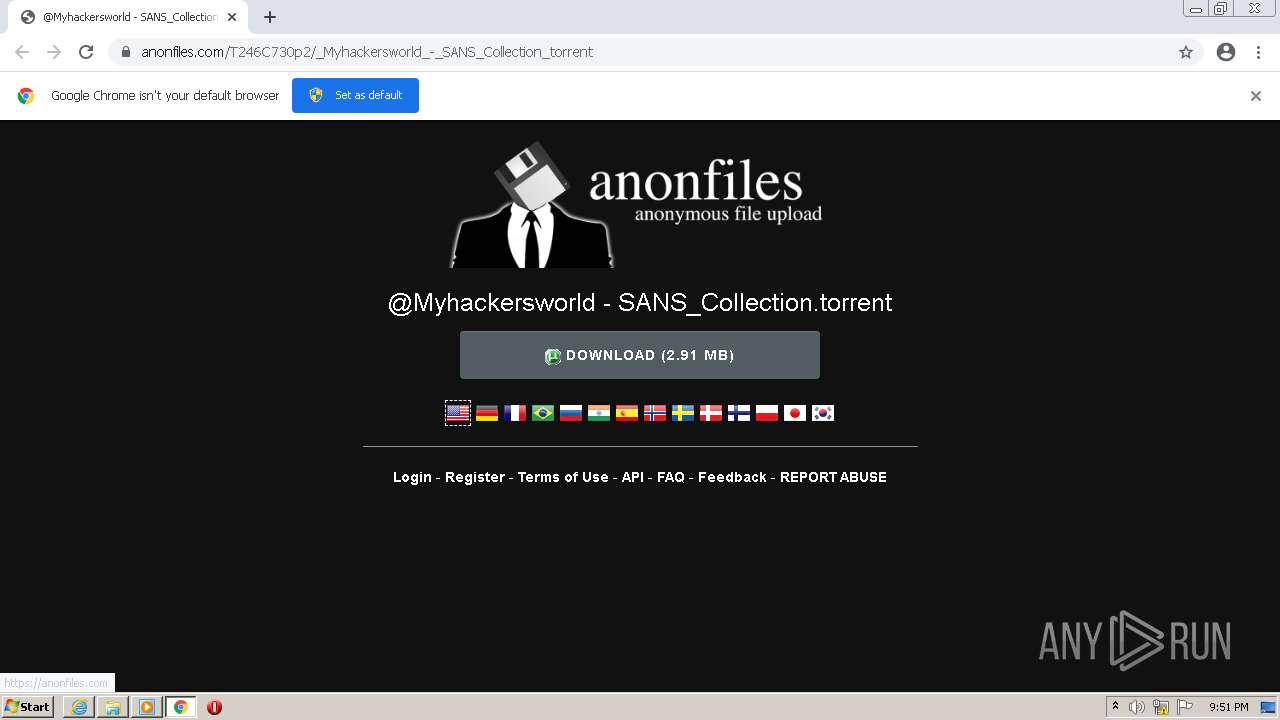
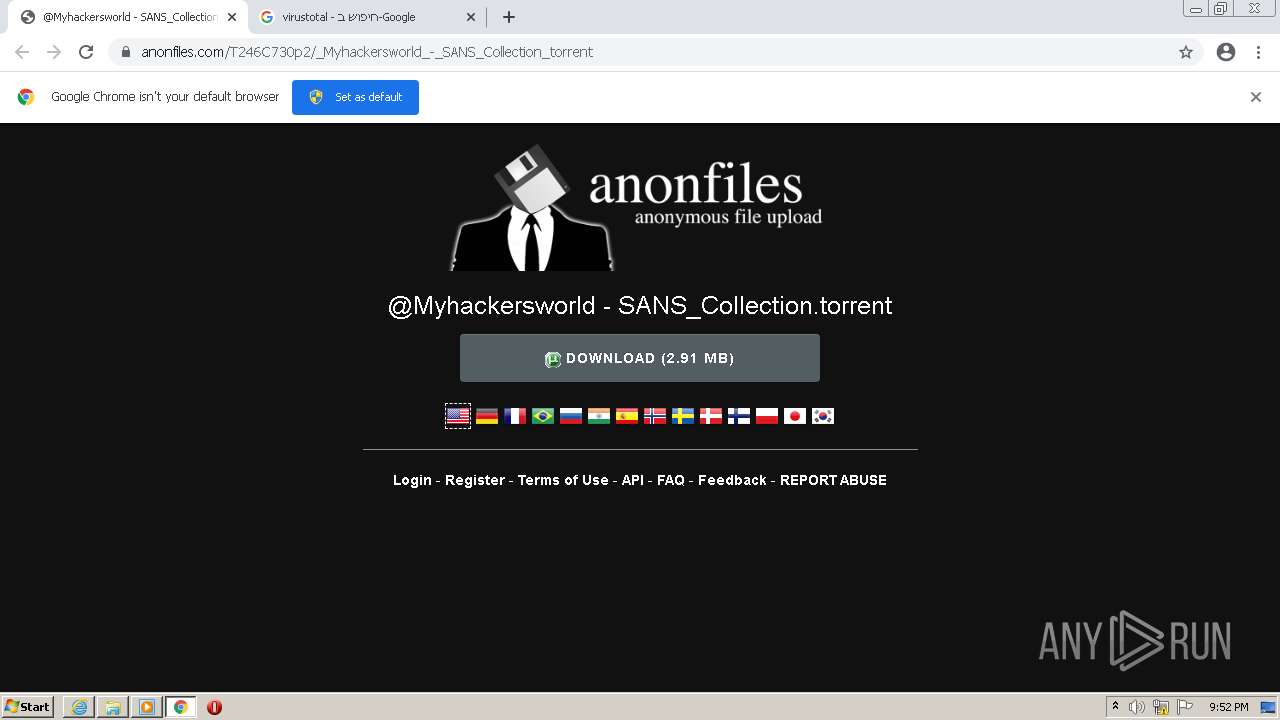
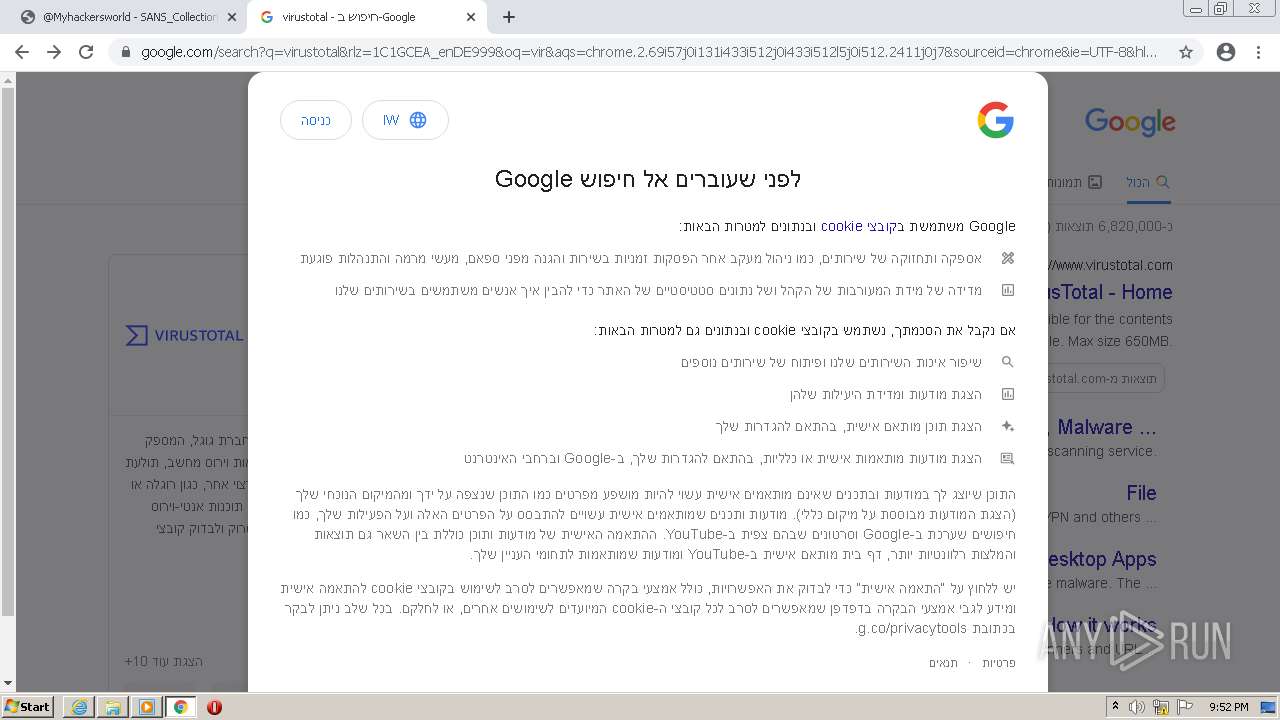
| URL: | https://anonfiles.com/T246C730p2/_Myhackersworld_-_SANS_Collection_torrent |
| Full analysis: | https://app.any.run/tasks/683634ce-9b98-4f7a-8072-ccd7de519010 |
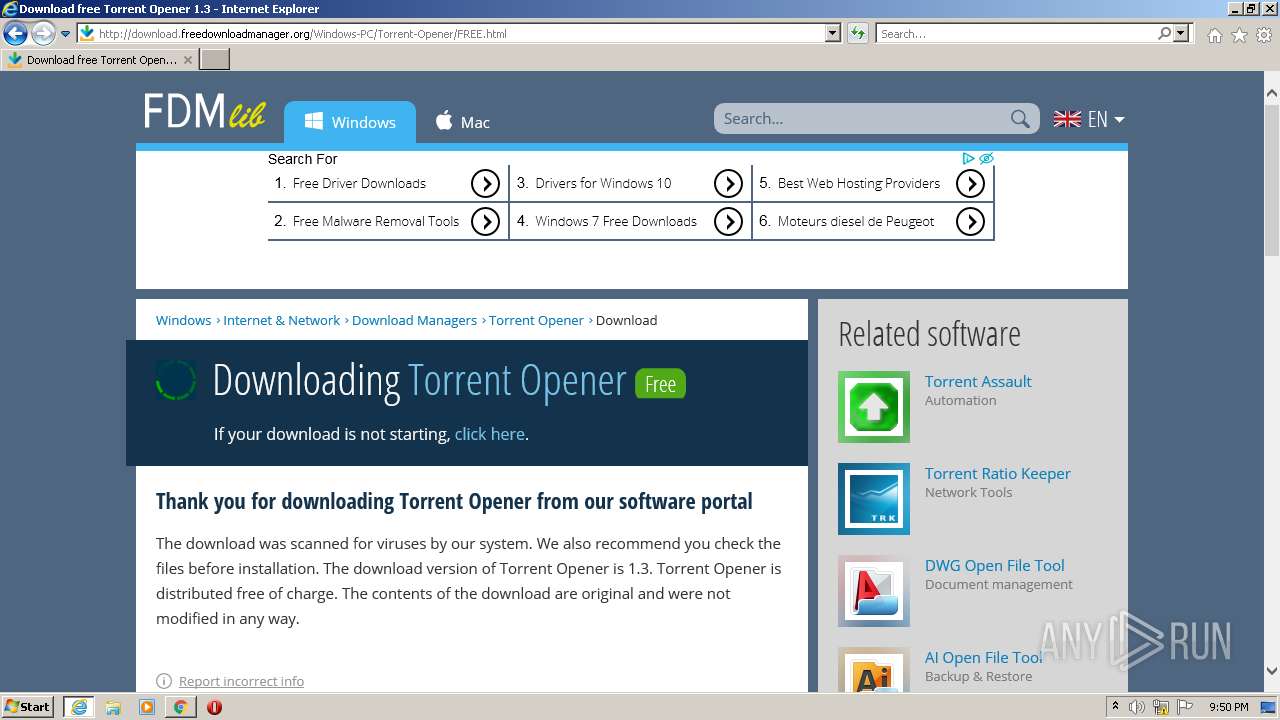
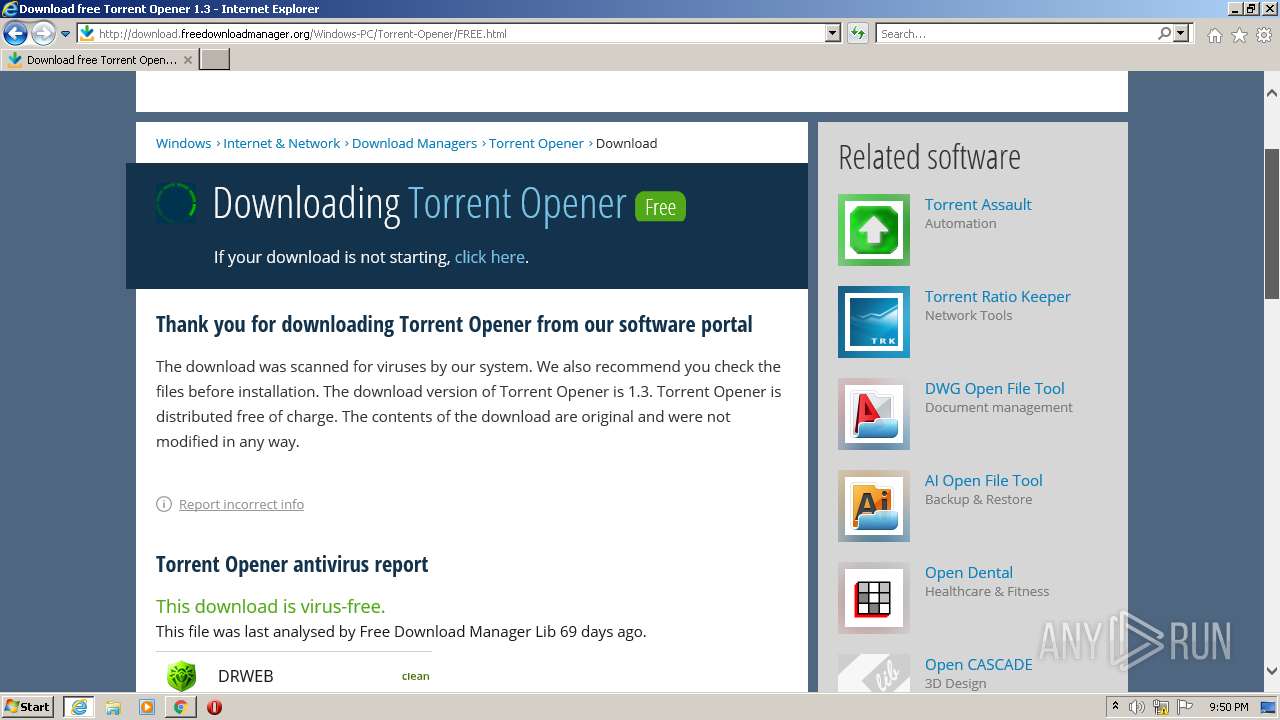
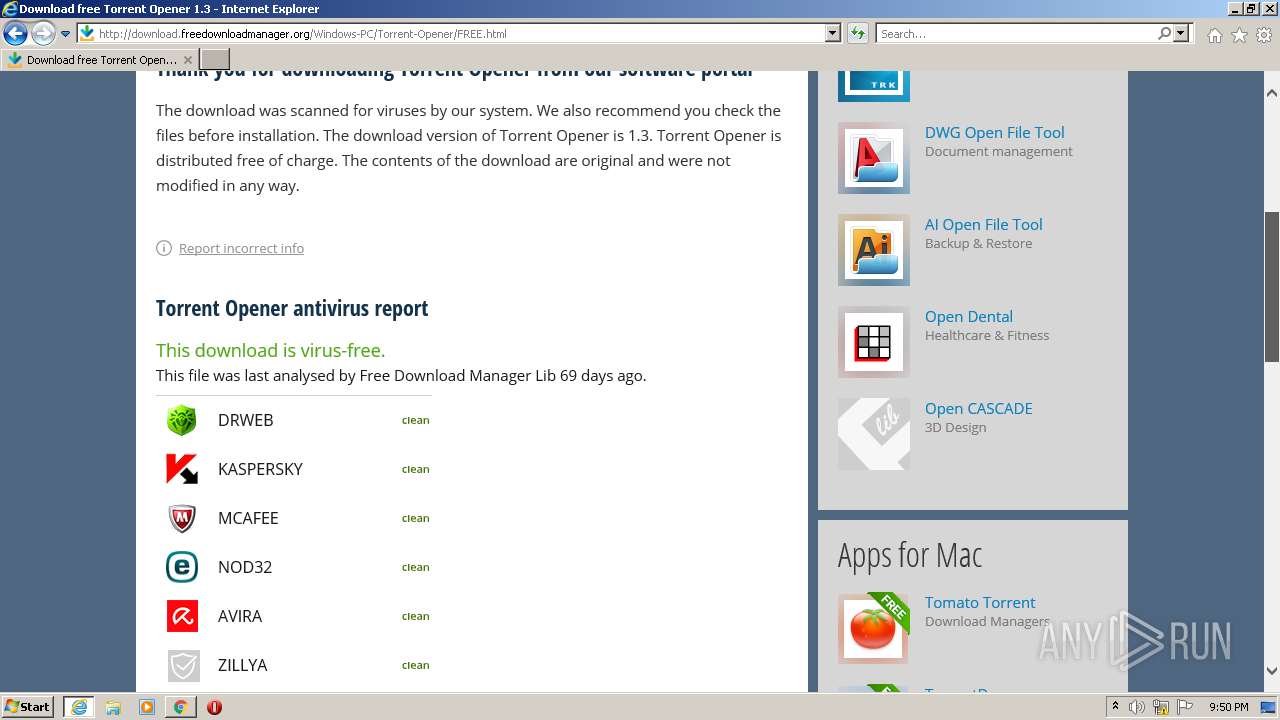
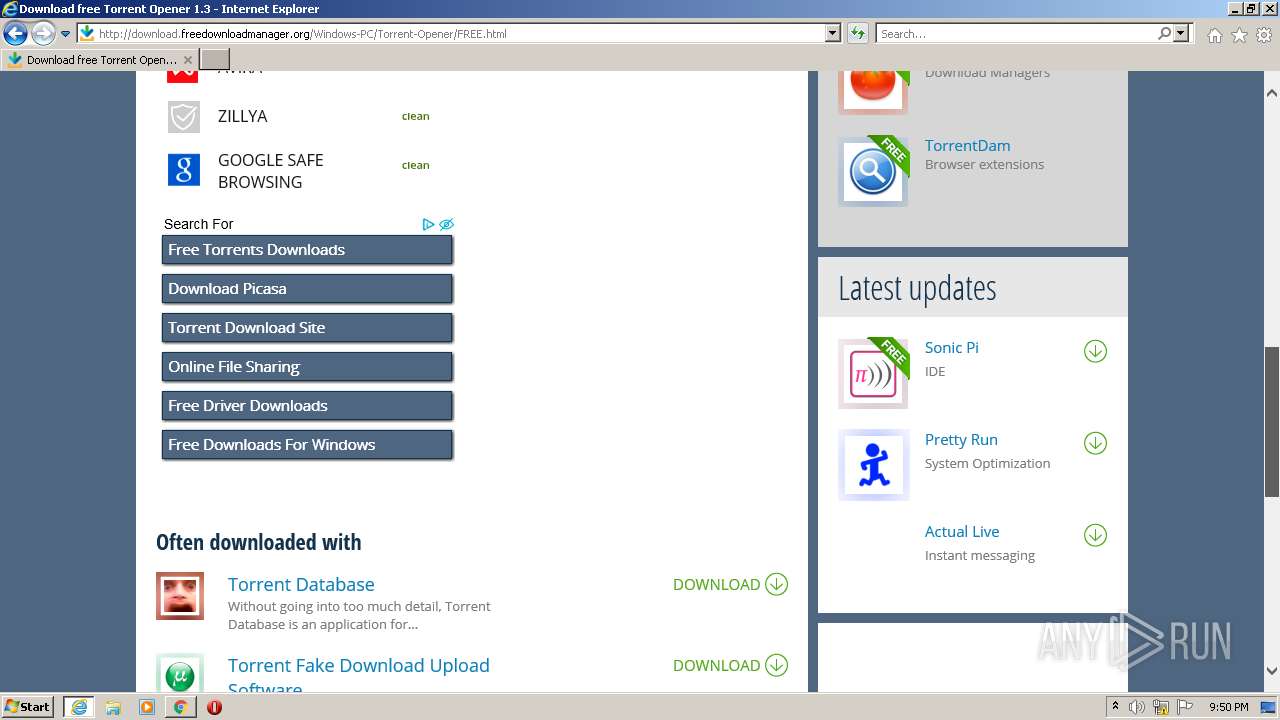
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | March 29, 2022, 20:49:44 |
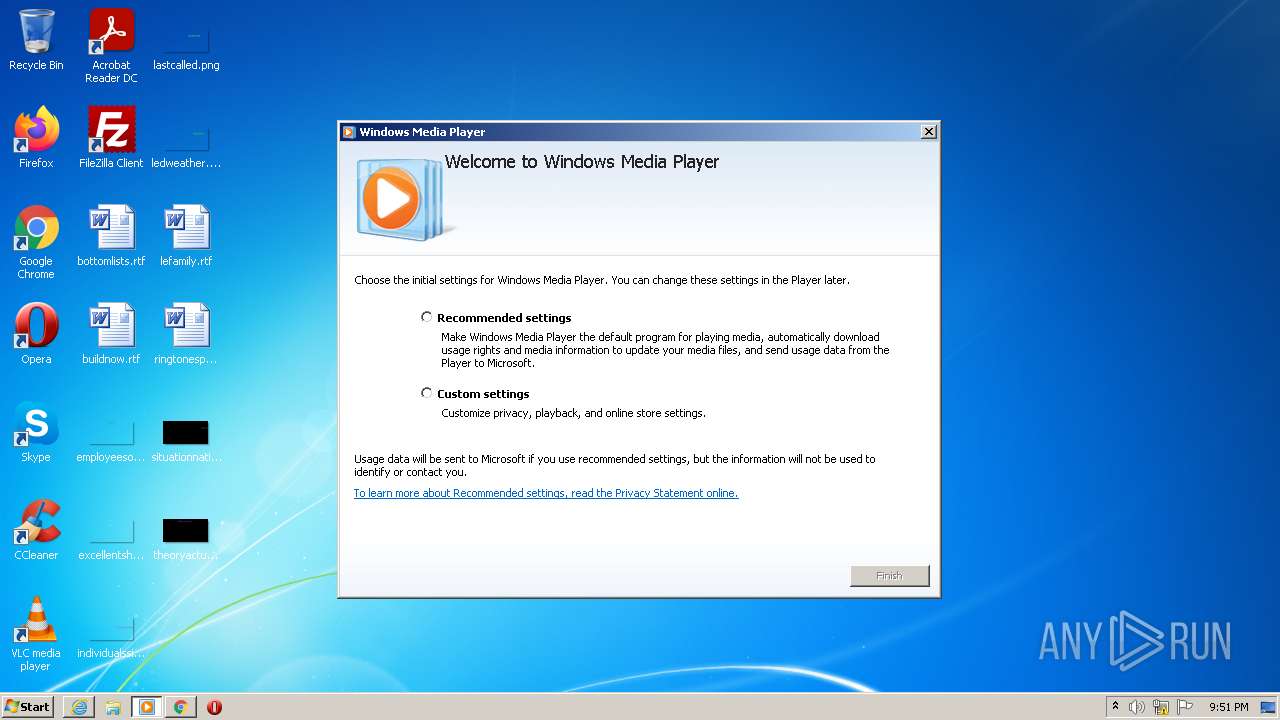
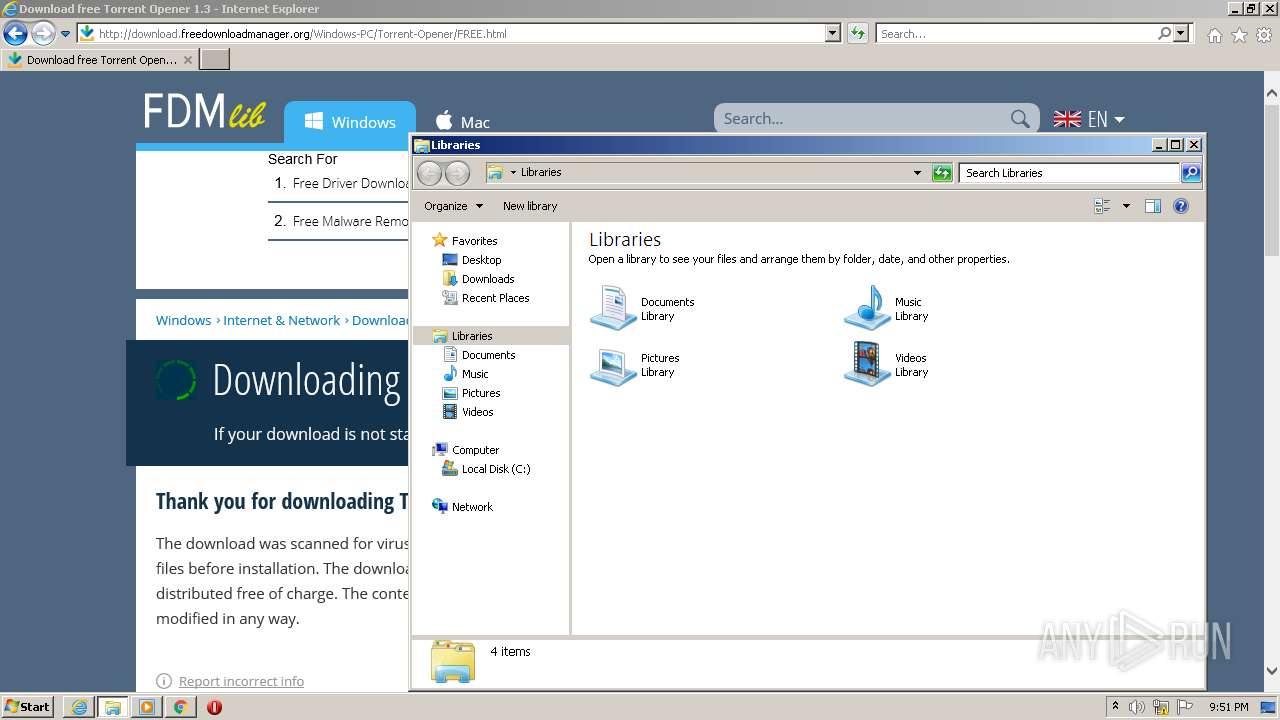
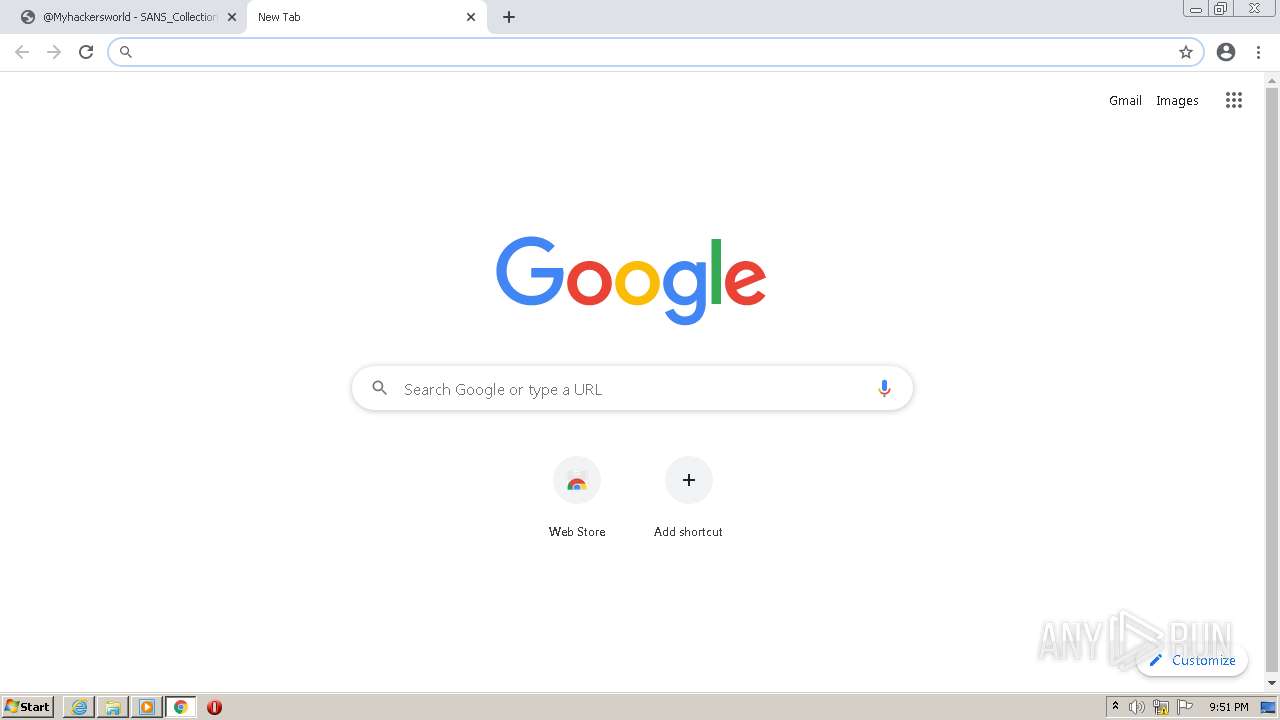
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FC62E6D04D4072054487E1C372E24991 |
| SHA1: | 5180F3C92E6B3DA0FD94425BC3EA5F136B9B88F9 |
| SHA256: | 48C77EF2054D64E775A4D536AC6C0F474B0EC139872CB45027C8576042B87467 |
| SSDEEP: | 3:N8M2vV7EGvGSKe2V6rJ+n:2M2SL5pVtn |
MALICIOUS
No malicious indicators.SUSPICIOUS
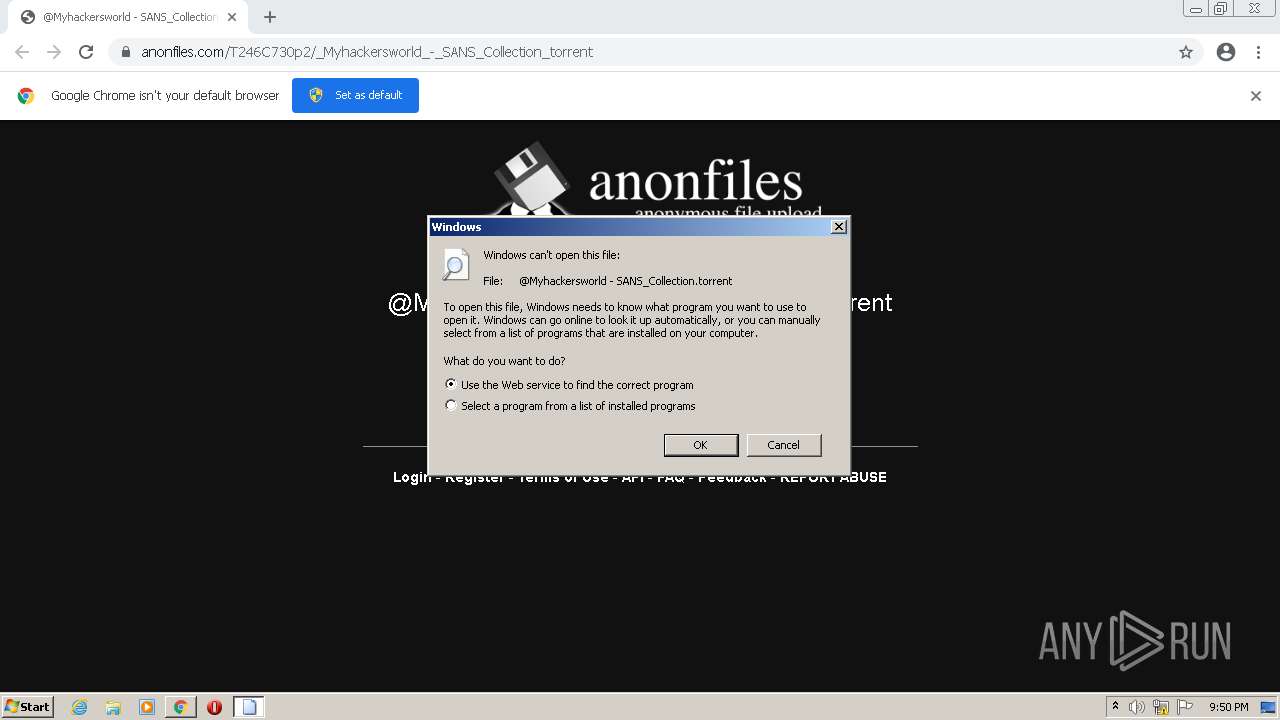
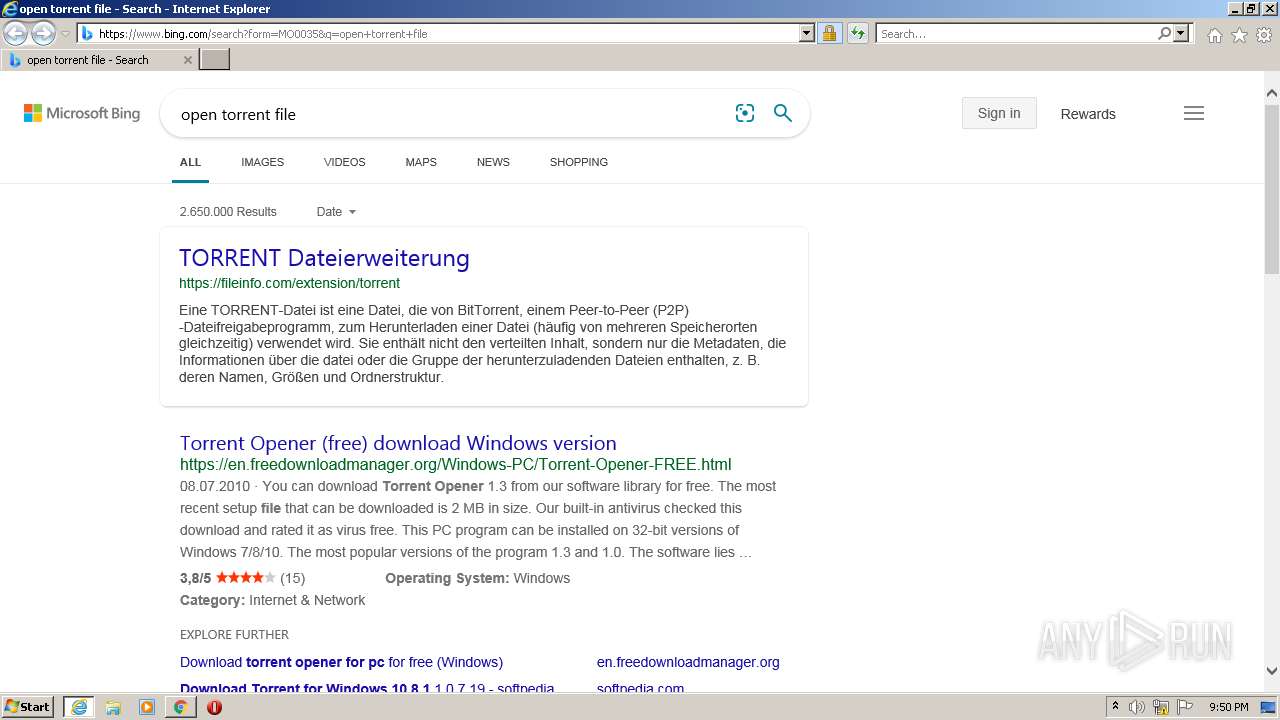
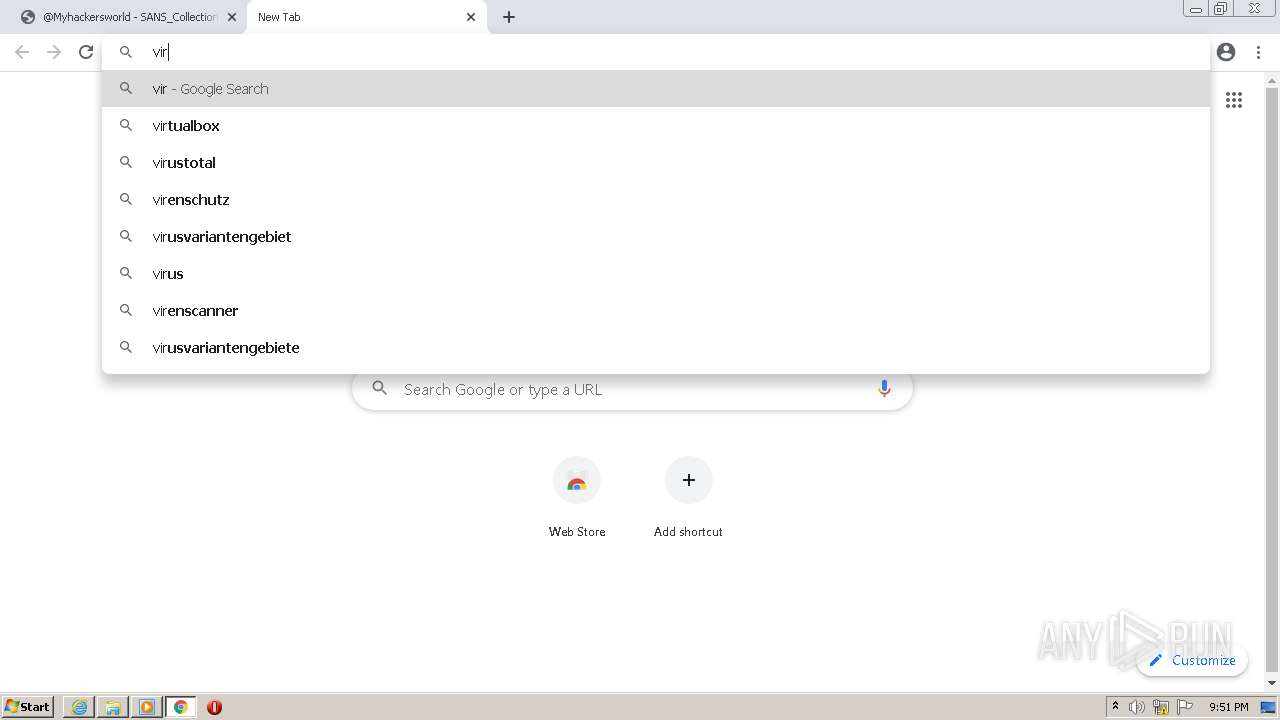
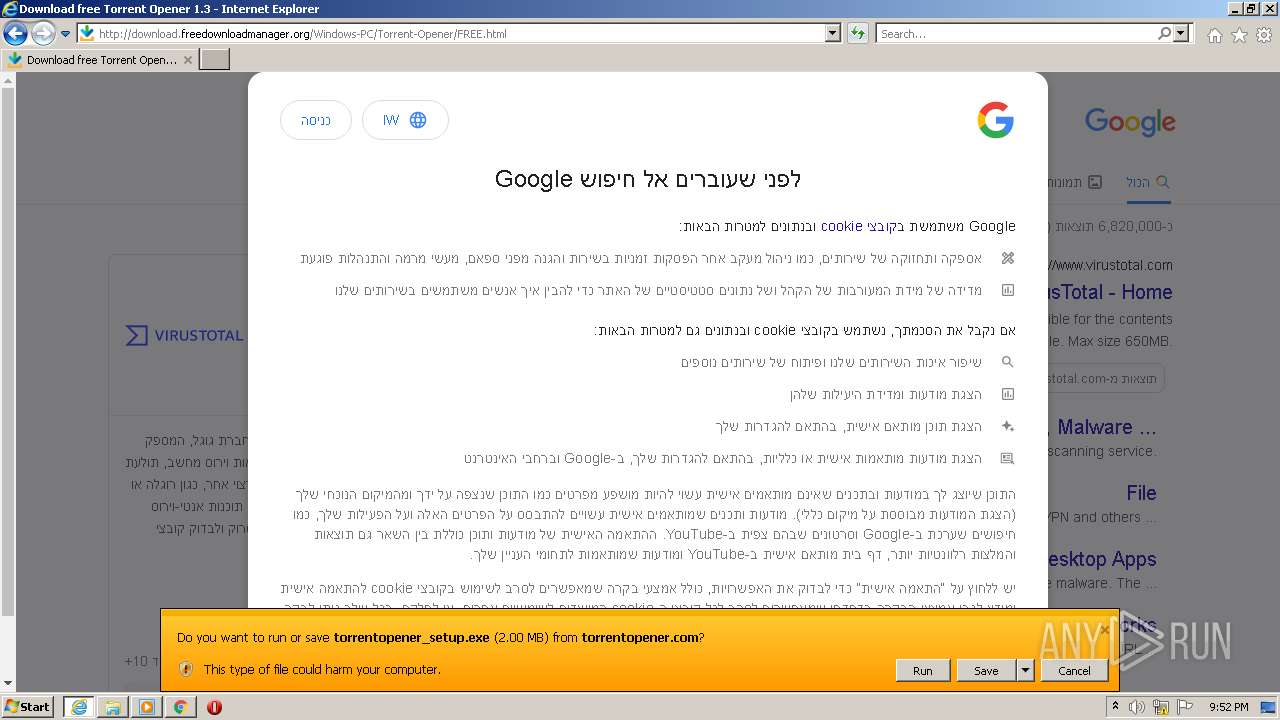
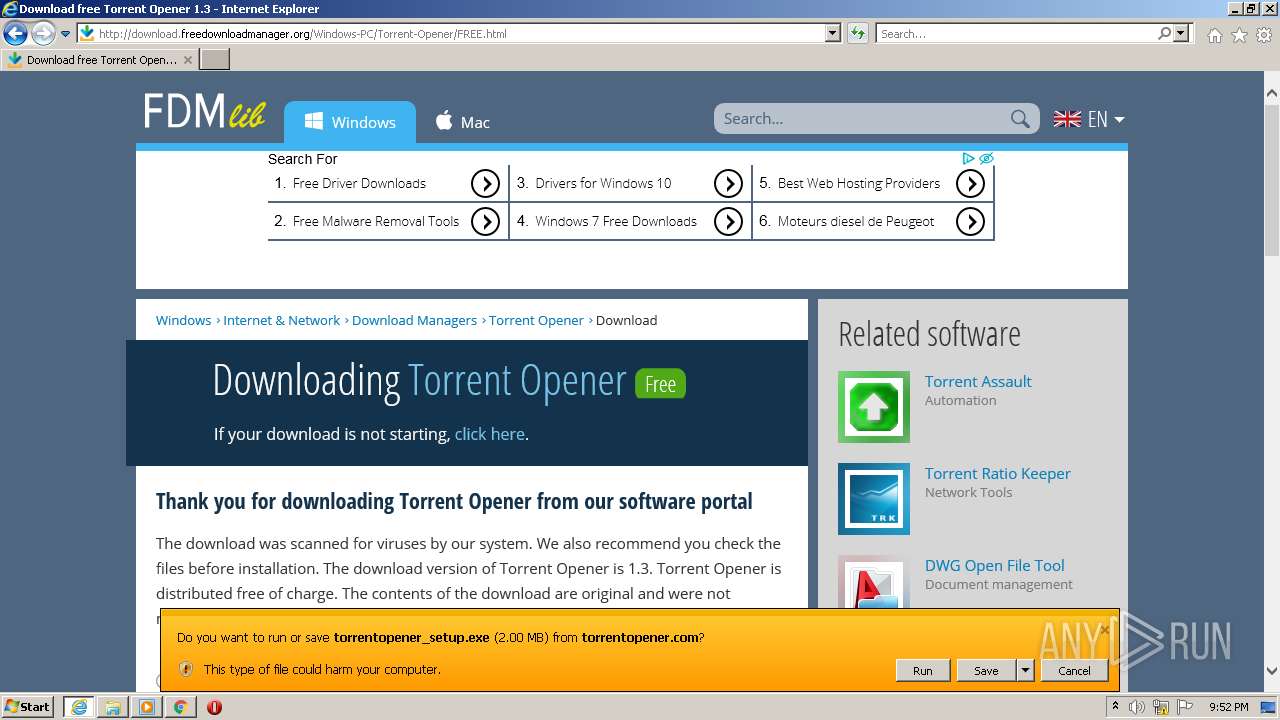
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 2928)
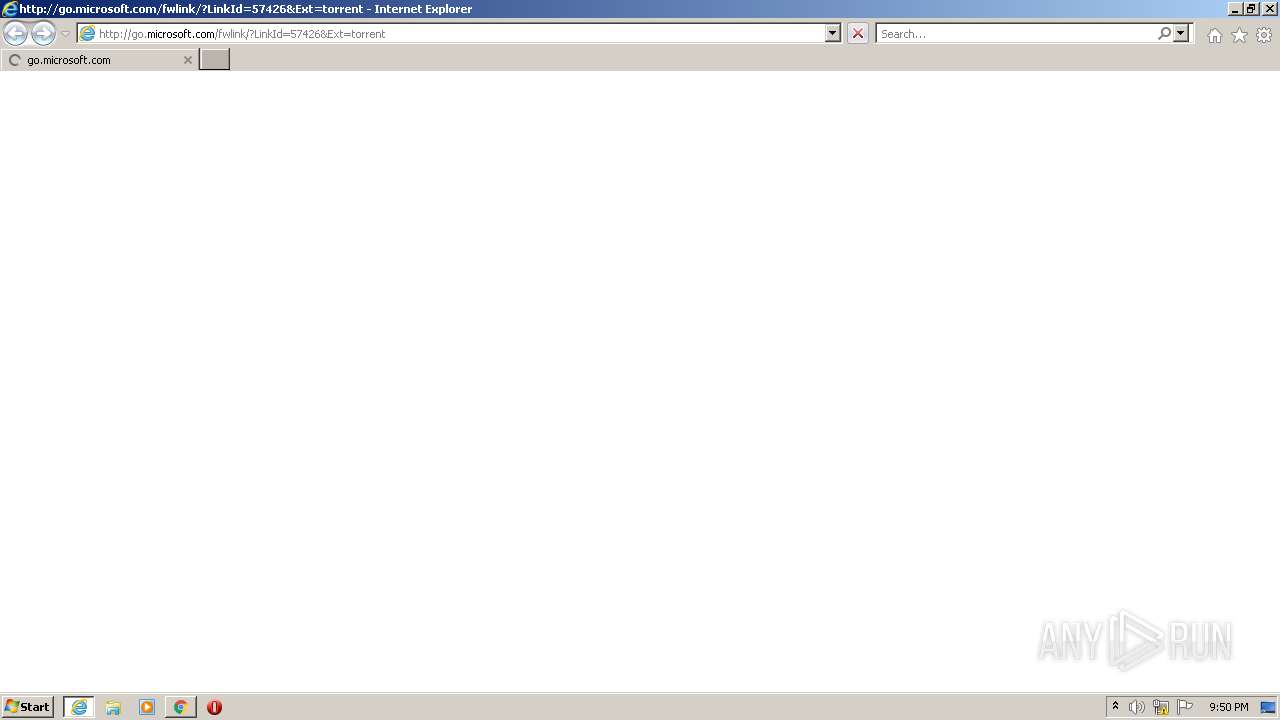
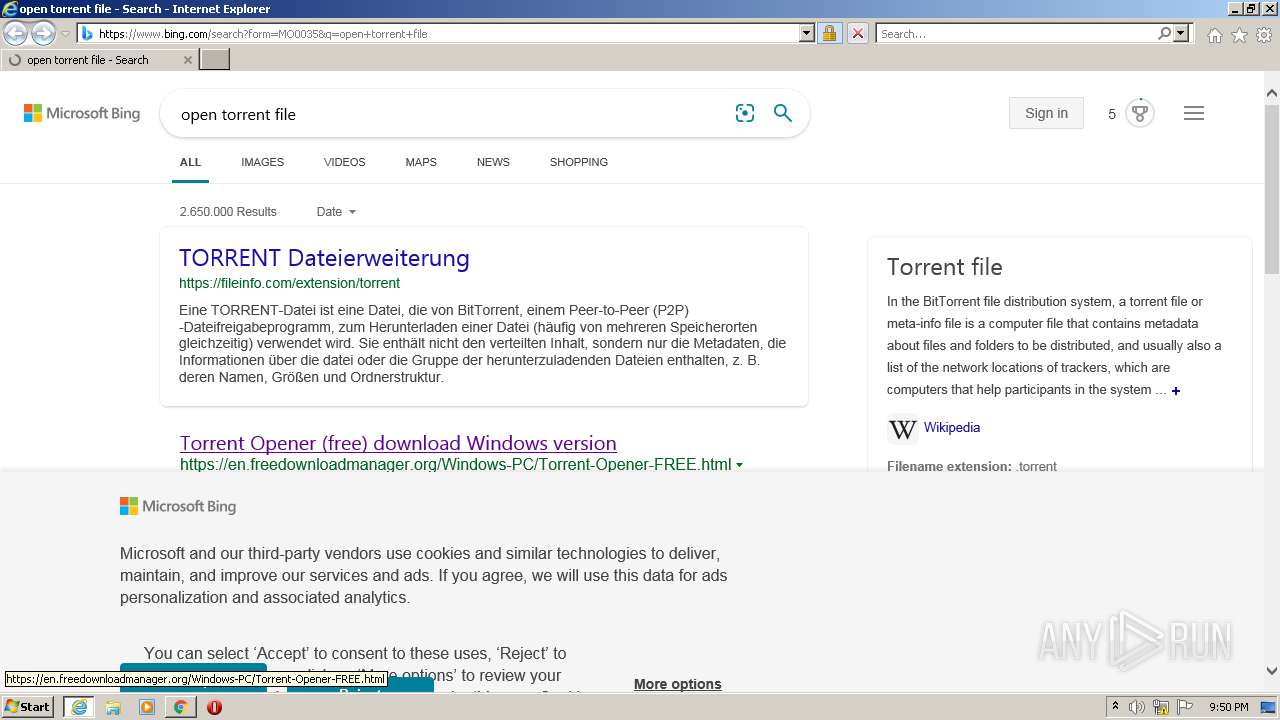
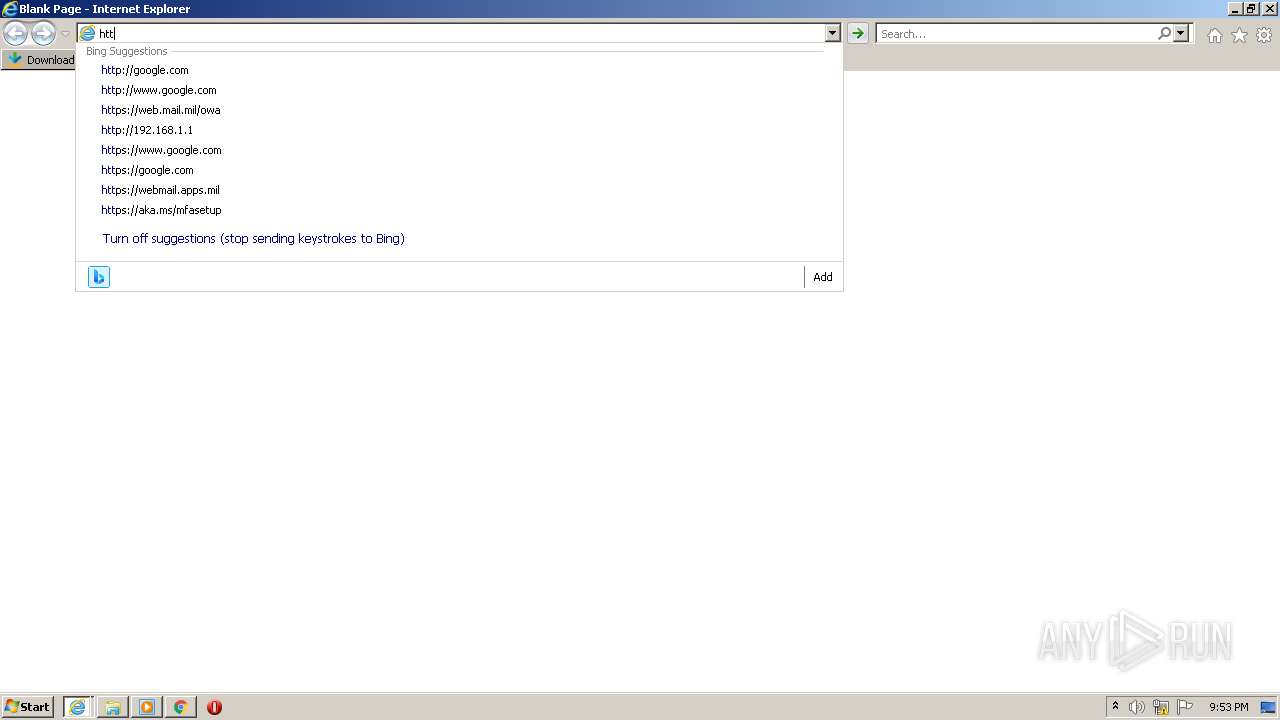
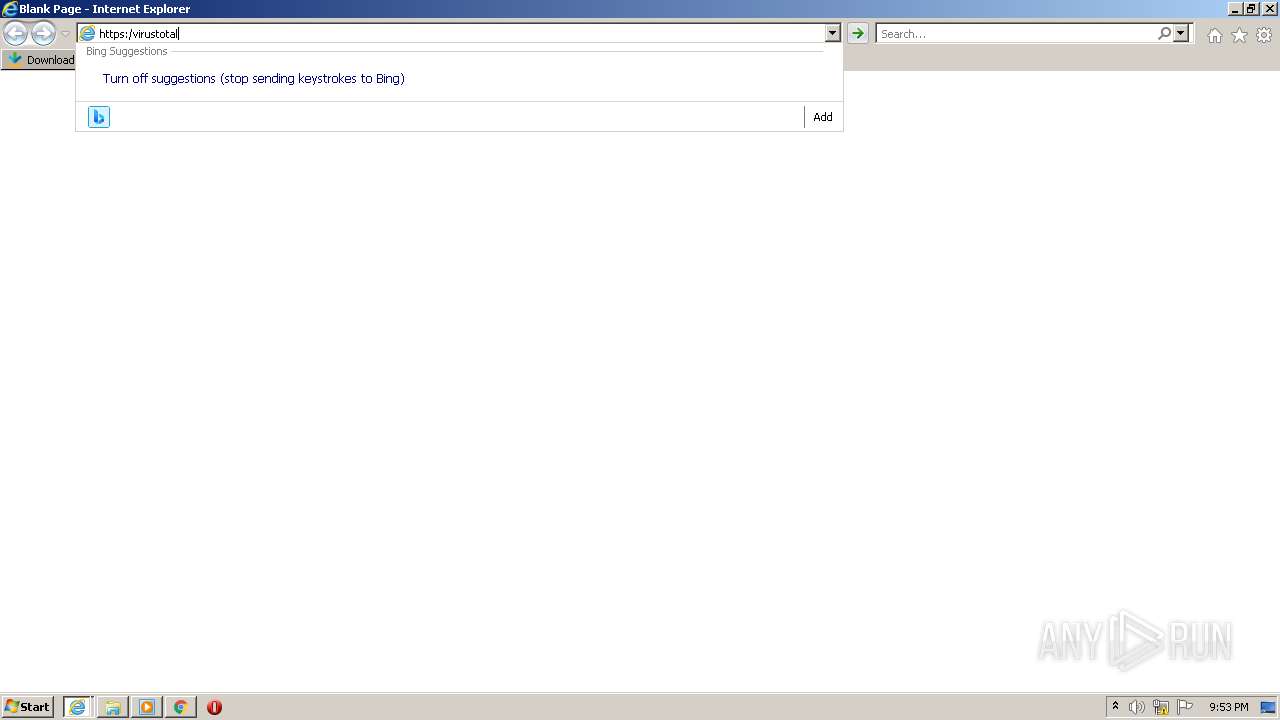
Starts Internet Explorer
- rundll32.exe (PID: 948)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 1848)
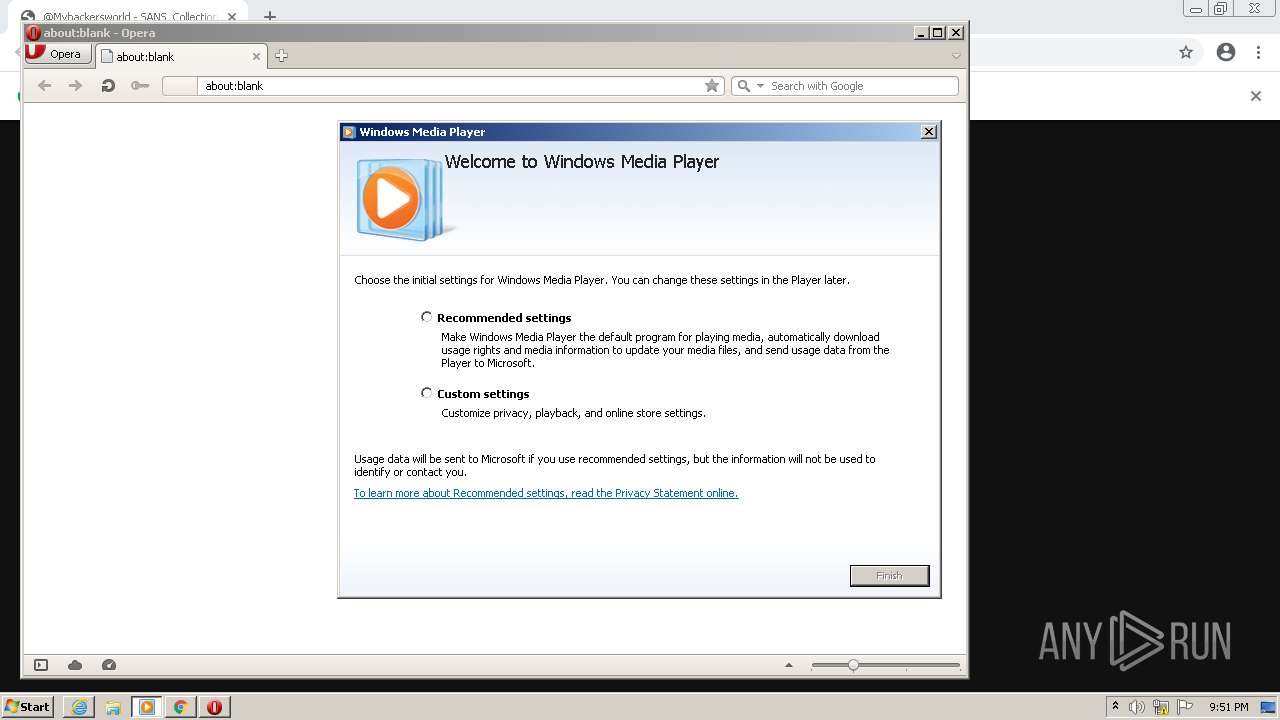
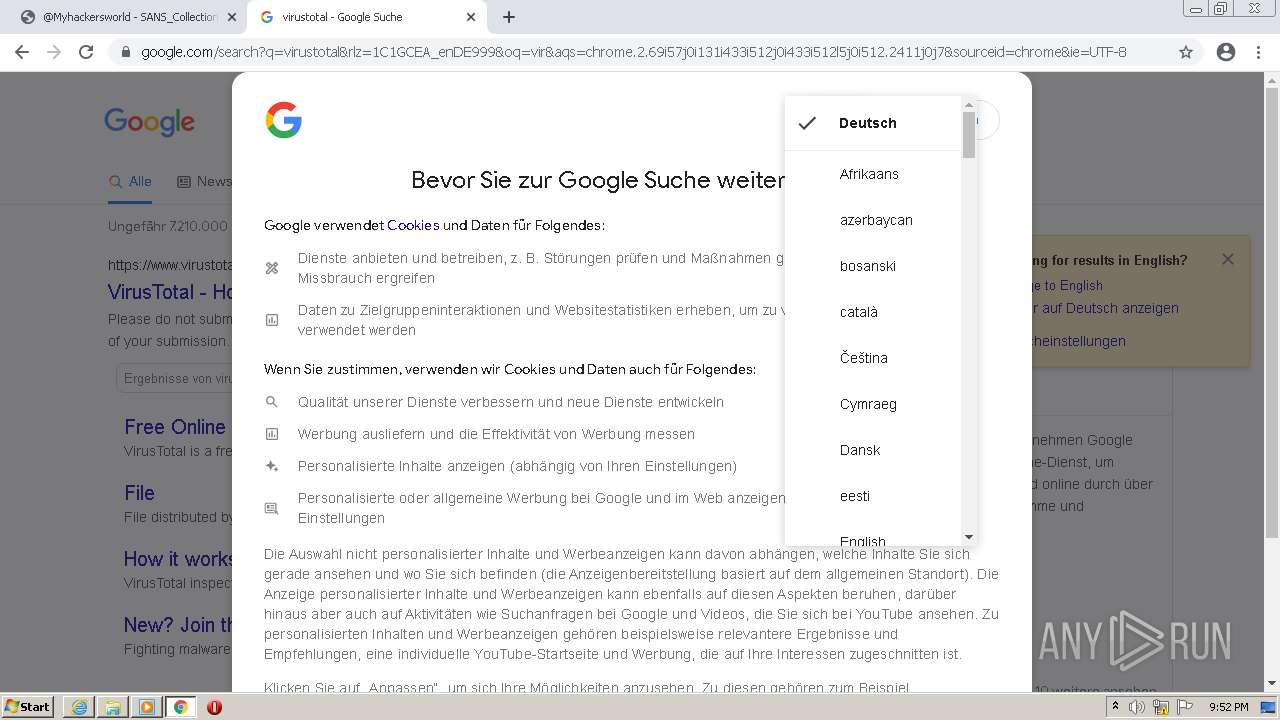
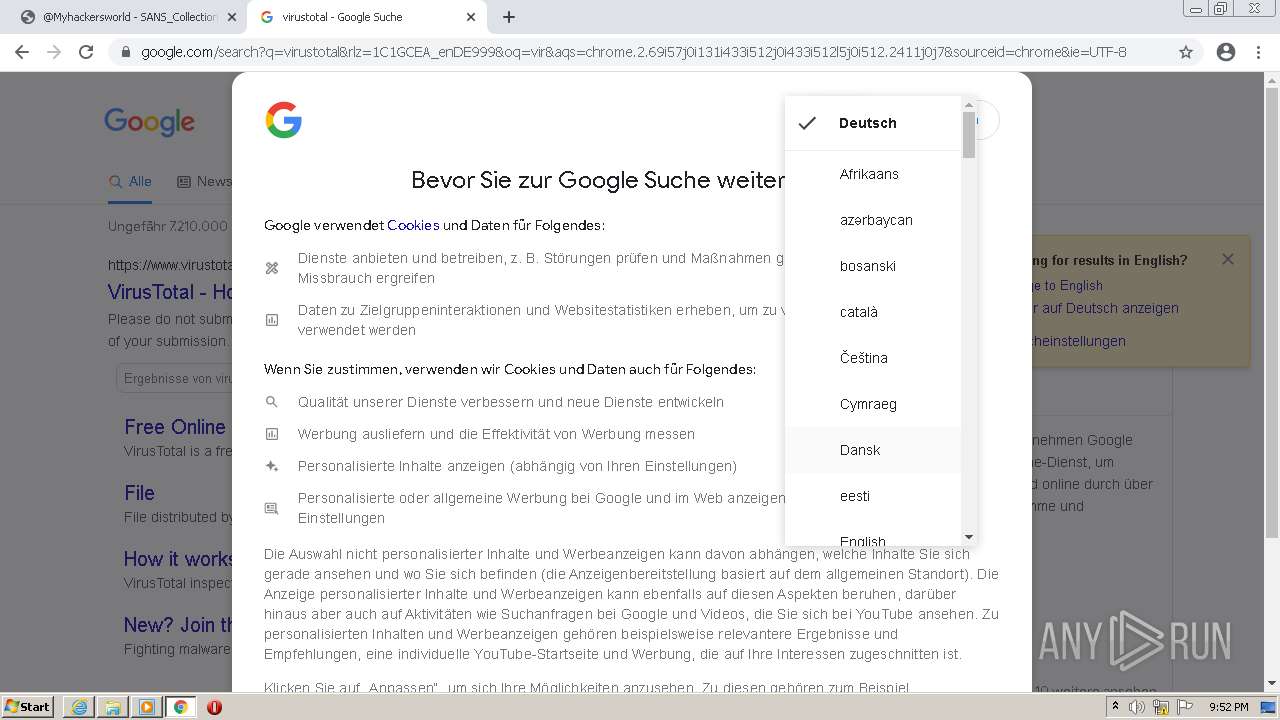
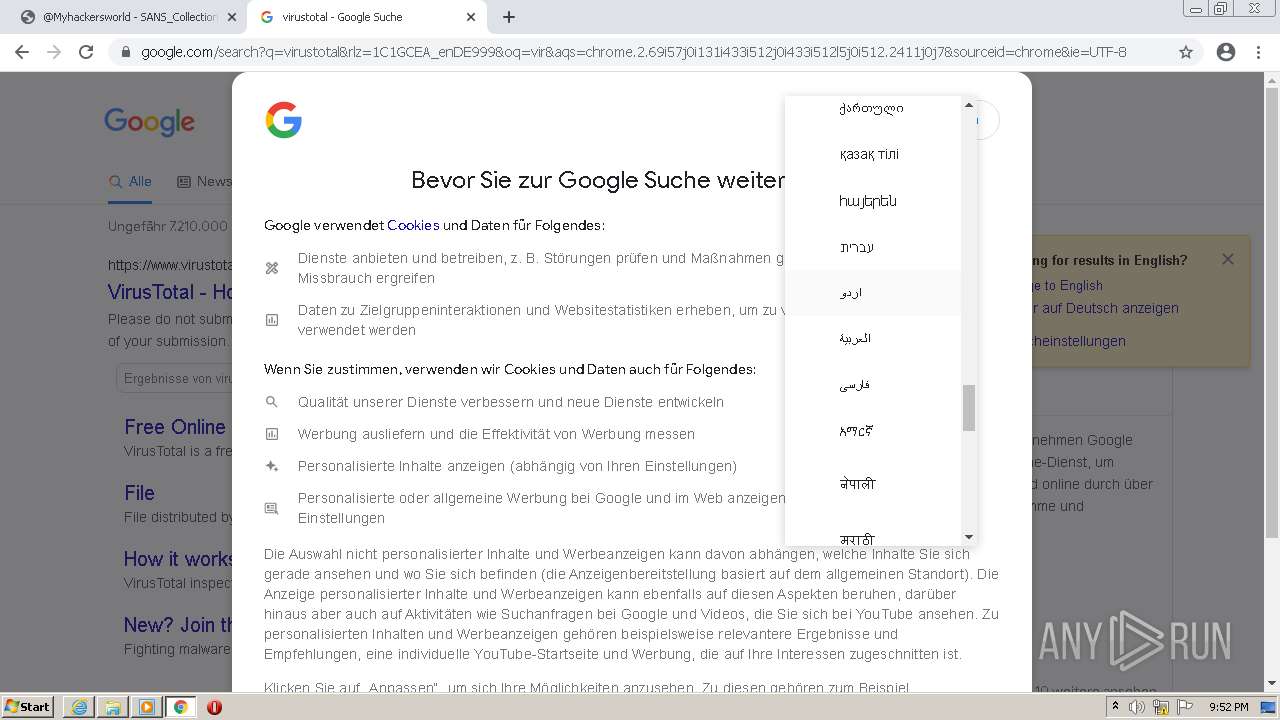
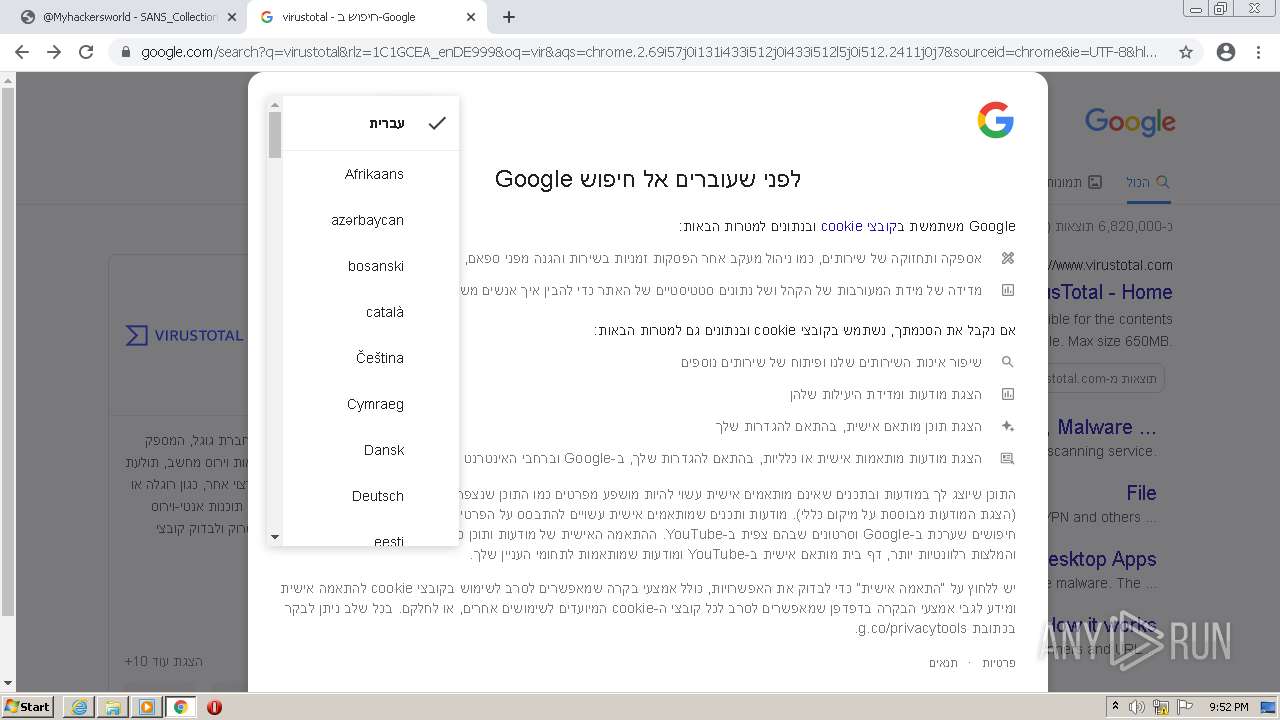
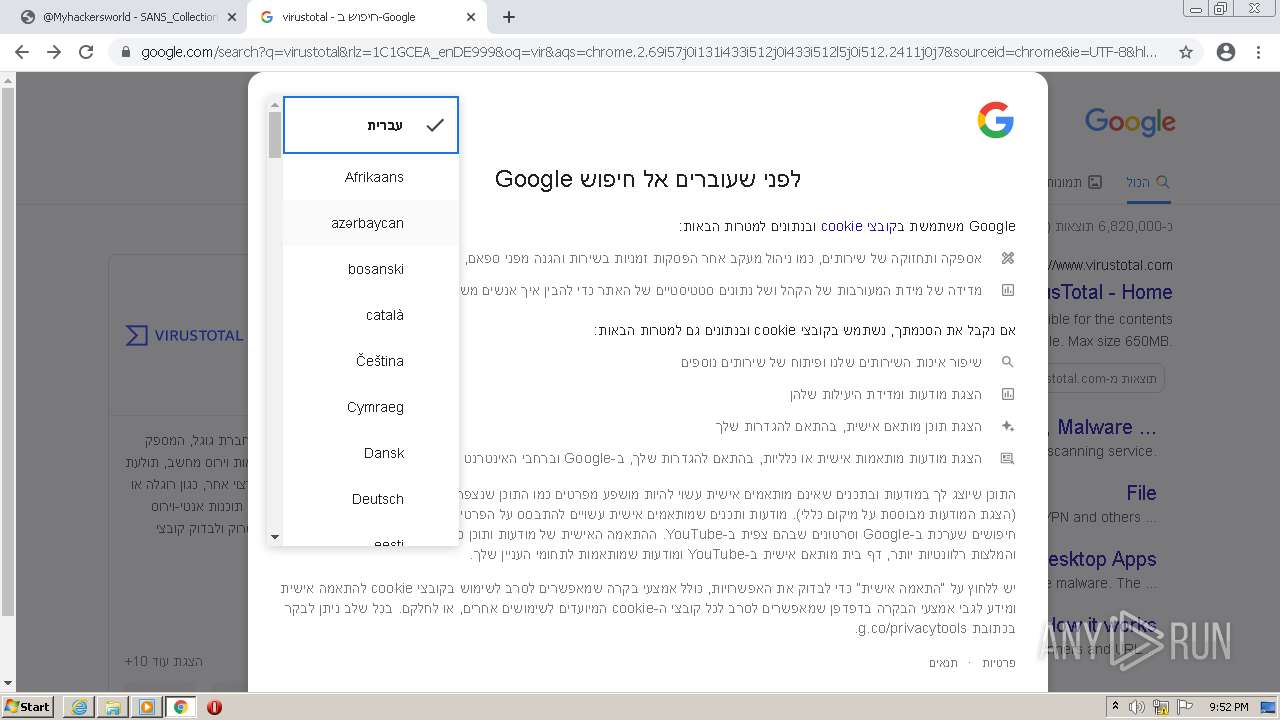
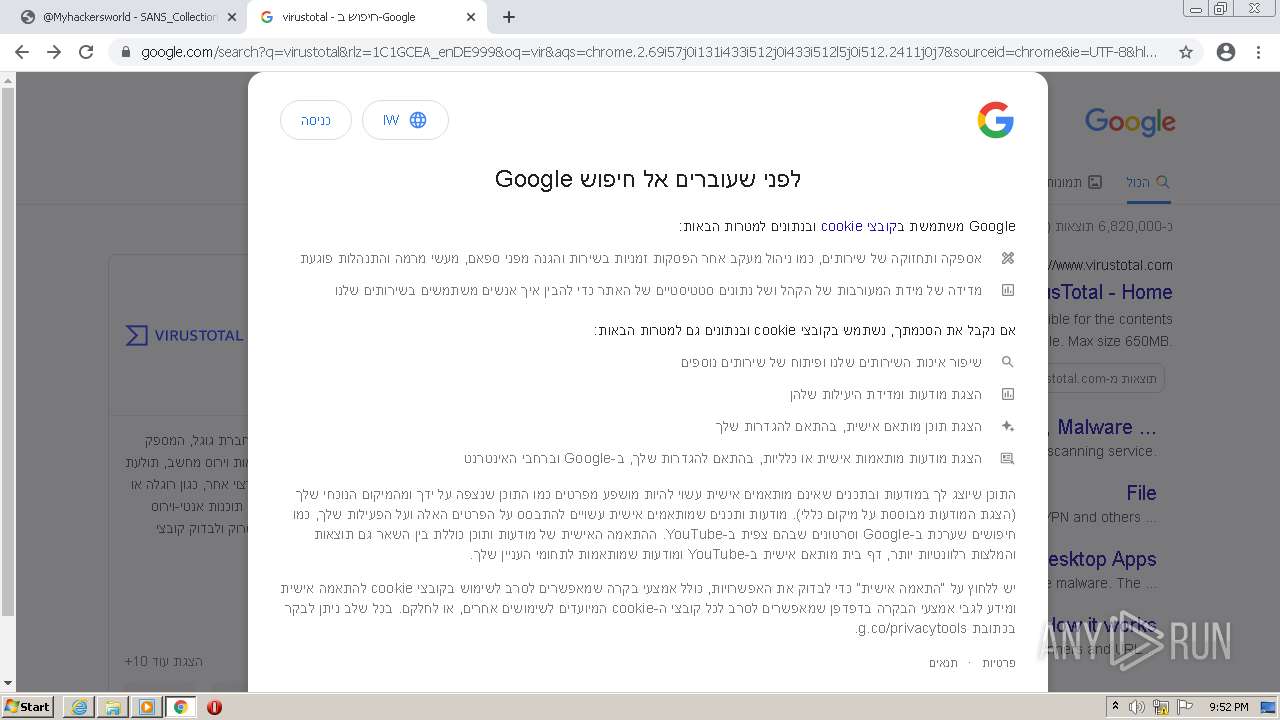
Checks supported languages
- setup_wm.exe (PID: 2940)
- wmplayer.exe (PID: 2504)
Reads the computer name
- setup_wm.exe (PID: 2940)
- wmplayer.exe (PID: 2504)
Reads Environment values
- setup_wm.exe (PID: 2940)
Drops a file with too old compile date
- iexplore.exe (PID: 2964)
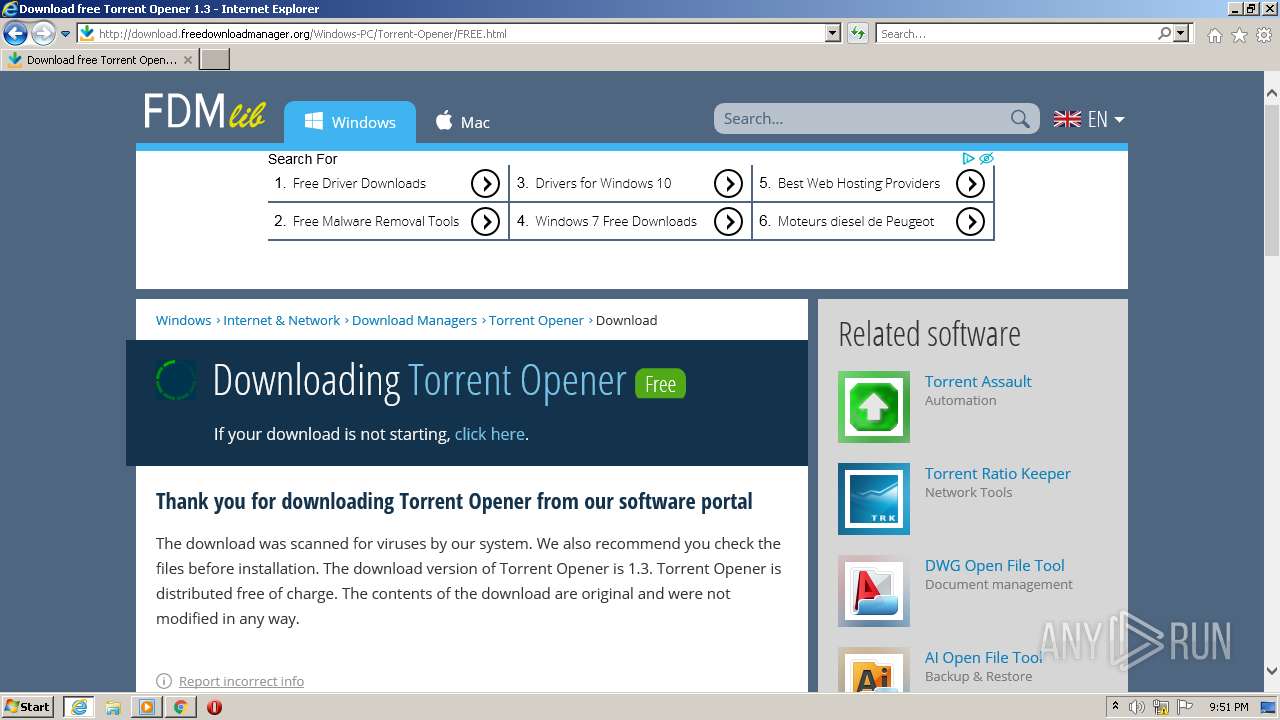
Executable content was dropped or overwritten
- iexplore.exe (PID: 2964)
INFO
Checks supported languages
- chrome.exe (PID: 2928)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 2360)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 2196)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 712)
- rundll32.exe (PID: 948)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 2964)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 2624)
- opera.exe (PID: 3540)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 1440)
- explorer.exe (PID: 3176)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 3308)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 1072)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2308)
- chrome.exe (PID: 876)
- chrome.exe (PID: 1232)
- chrome.exe (PID: 3444)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 3292)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 2636)
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2032)
- chrome.exe (PID: 2060)
- chrome.exe (PID: 928)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 2808)
- chrome.exe (PID: 2288)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 696)
- chrome.exe (PID: 3544)
- chrome.exe (PID: 1944)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 2376)
- iexplore.exe (PID: 1848)
Reads the hosts file
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2260)
Checks Windows Trust Settings
- chrome.exe (PID: 2928)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 1848)
Application launched itself
- chrome.exe (PID: 2928)
- iexplore.exe (PID: 2248)
Reads the computer name
- chrome.exe (PID: 2928)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3532)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 712)
- rundll32.exe (PID: 948)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 2964)
- chrome.exe (PID: 3940)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 3748)
- opera.exe (PID: 3540)
- explorer.exe (PID: 3176)
- chrome.exe (PID: 3240)
- chrome.exe (PID: 3544)
- iexplore.exe (PID: 1848)
Reads settings of System Certificates
- chrome.exe (PID: 2260)
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 1848)
Creates files in the user directory
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2248)
- opera.exe (PID: 3540)
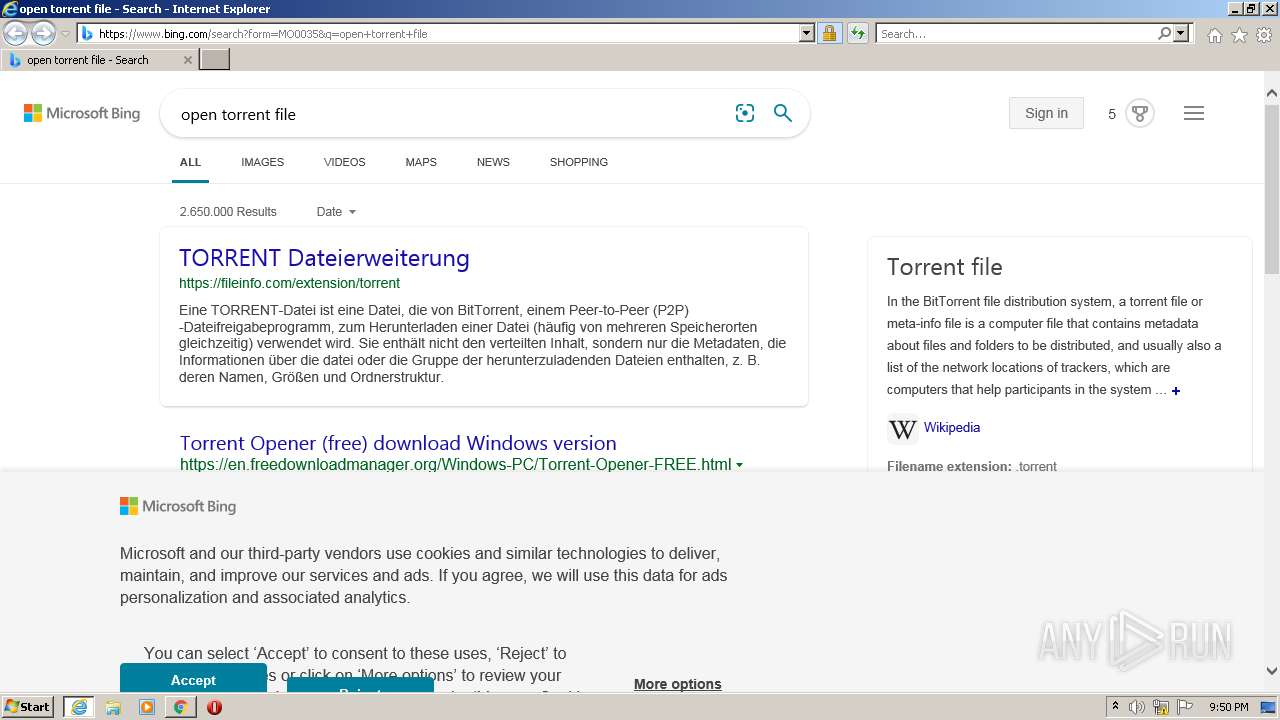
Changes internet zones settings
- iexplore.exe (PID: 2248)
Reads internet explorer settings
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 1848)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2248)
Changes settings of System certificates
- iexplore.exe (PID: 2248)
Reads the date of Windows installation
- chrome.exe (PID: 3748)
- opera.exe (PID: 3540)
Manual execution by user
- opera.exe (PID: 3540)
- wmplayer.exe (PID: 2504)
- explorer.exe (PID: 3176)
Check for Java to be installed
- opera.exe (PID: 3540)
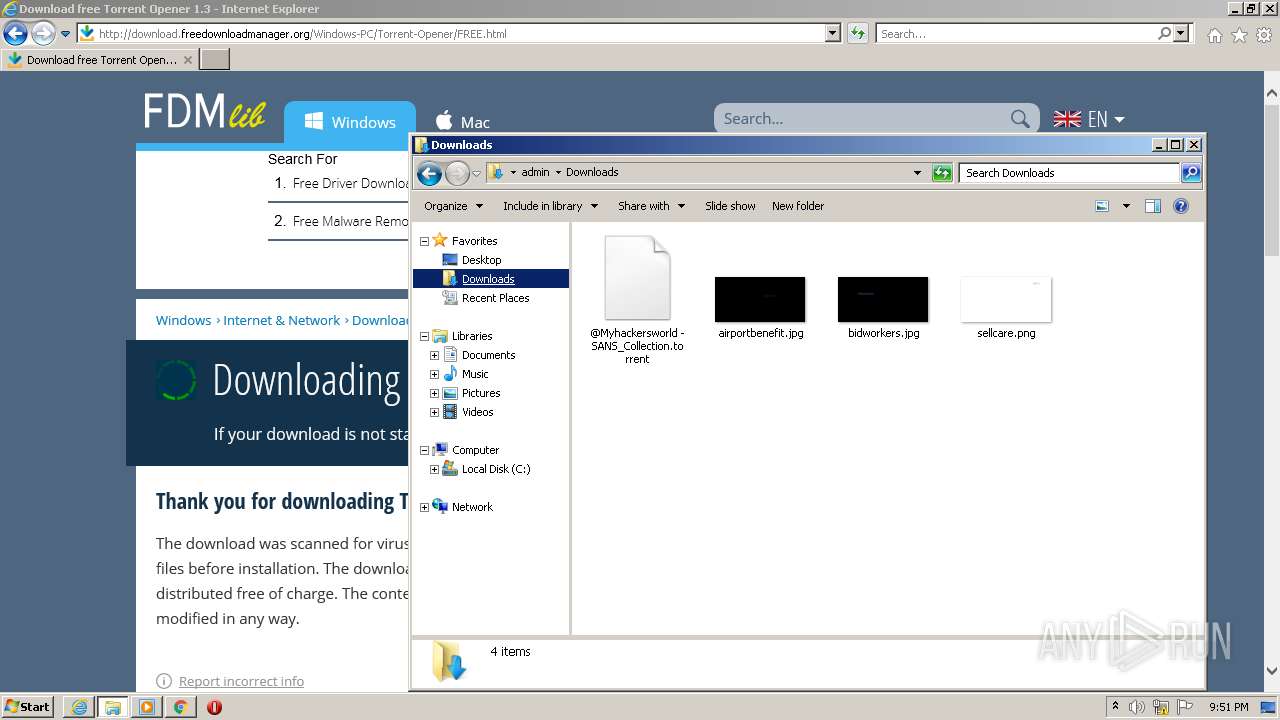
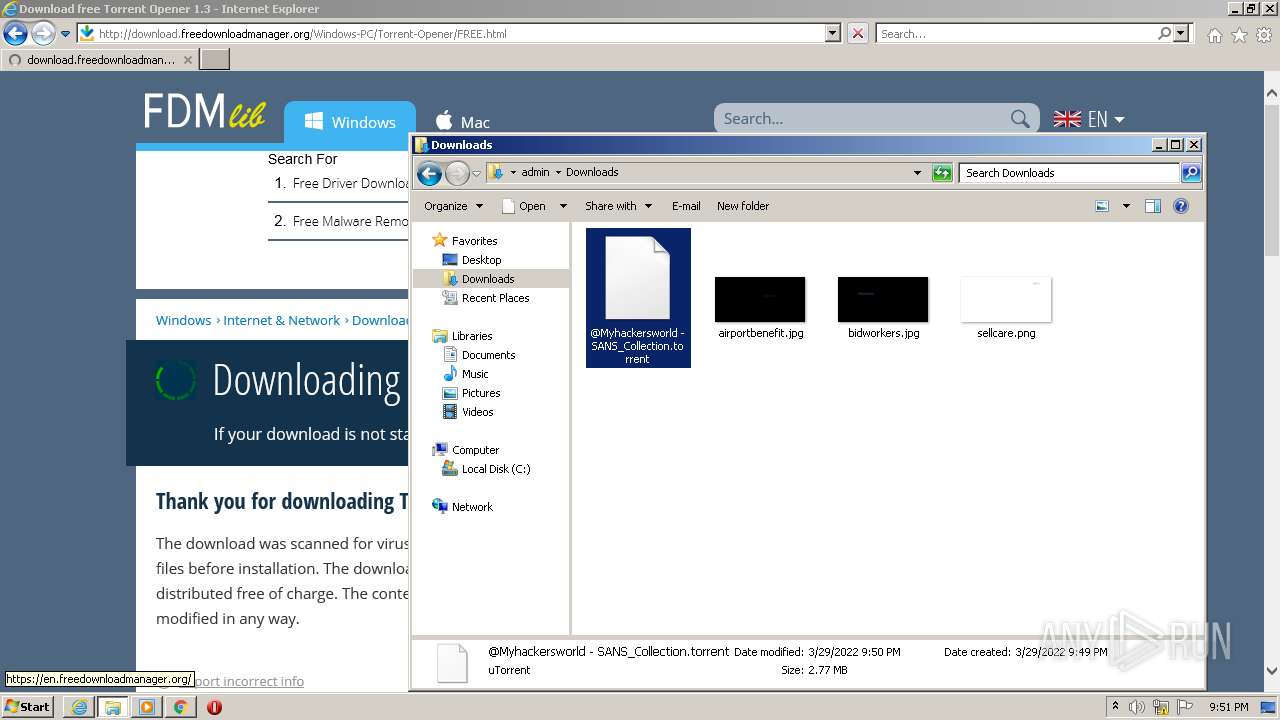
Dropped object may contain Bitcoin addresses
- opera.exe (PID: 3540)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
91
Monitored processes
51
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1044 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2832 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 948 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\@Myhackersworld - SANS_Collection.torrent | C:\Windows\system32\rundll32.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 3221225547 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3600 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3120 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2248 CREDAT:464199 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1060,13751795749959477589,8453271991311346705,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4212 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
41 290
Read events
40 774
Write events
504
Delete events
12
Modification events
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1
Suspicious files
101
Text files
466
Unknown types
43
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-624370EC-B70.pma | — | |
MD5:— | SHA256:— | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fe584177-87fd-443d-a8db-eae98430209d.tmp | text | |
MD5:— | SHA256:— | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFf92e0.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RFf9968.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RFf959f.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 2928 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
86
TCP/UDP connections
208
DNS requests
79
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
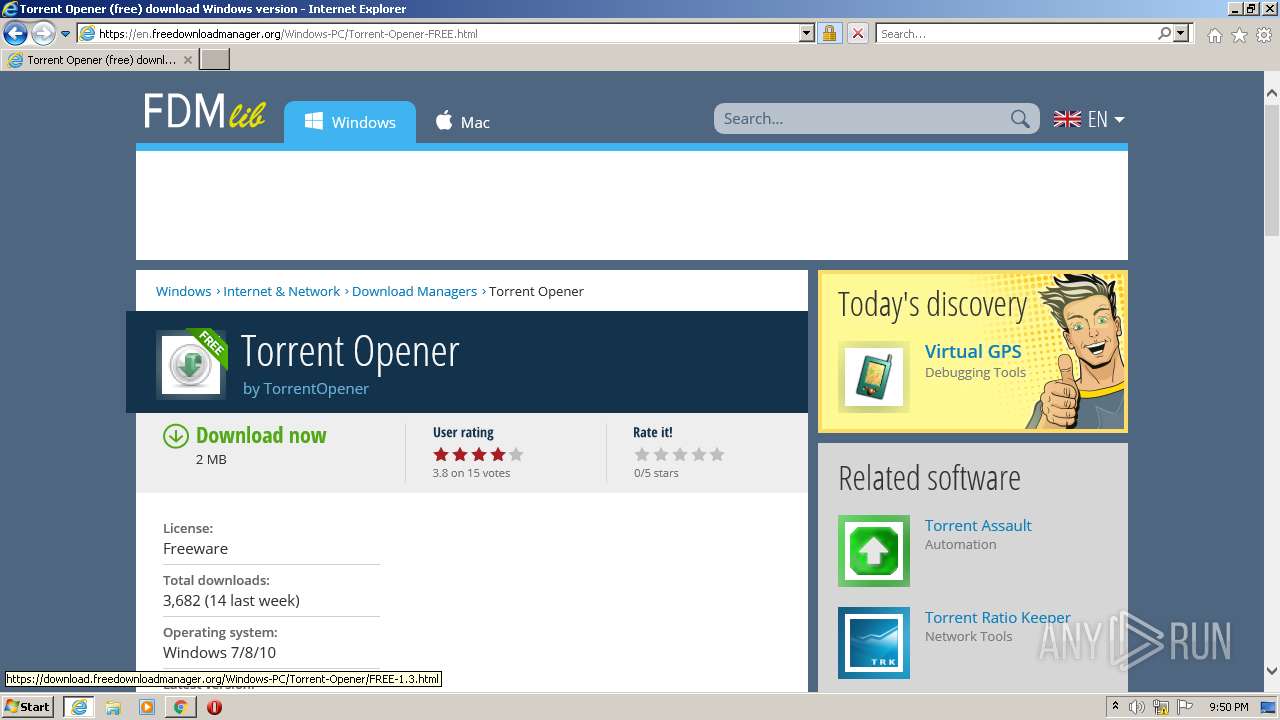
2964 | iexplore.exe | GET | 301 | 184.24.77.147:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=torrent | US | — | — | whitelisted |
2964 | iexplore.exe | GET | 200 | 104.18.31.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2964 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2964 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
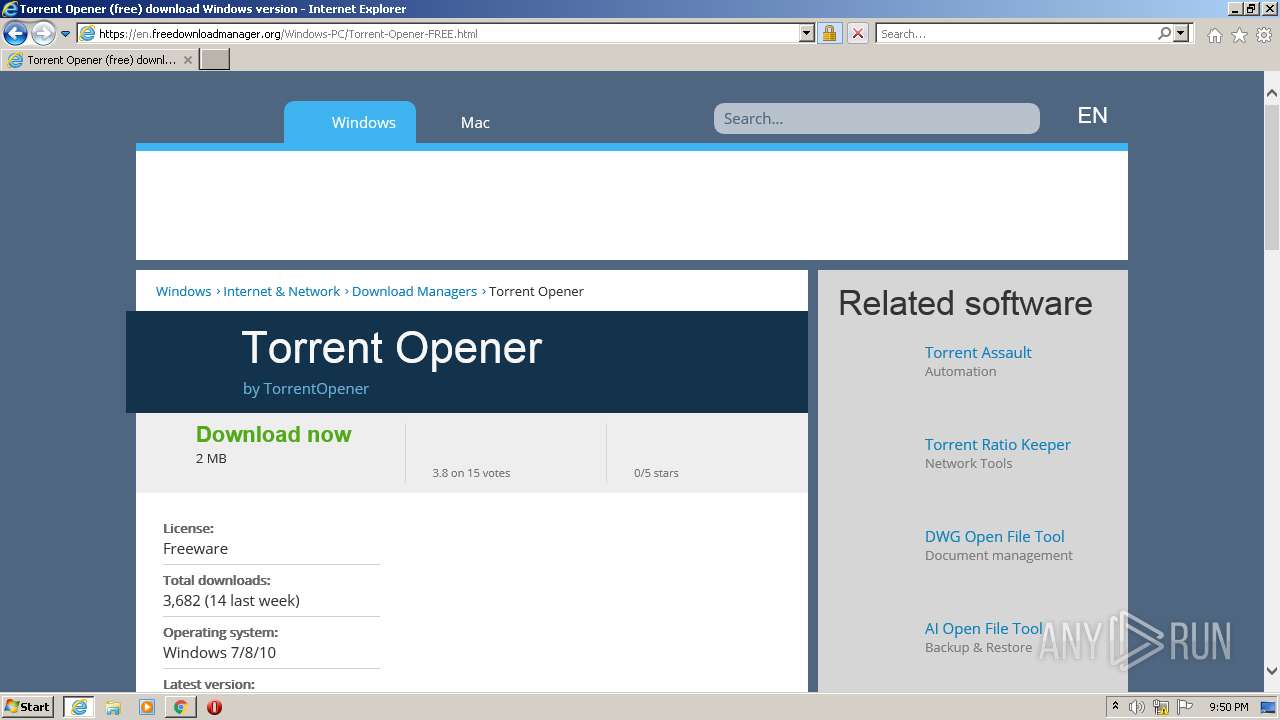
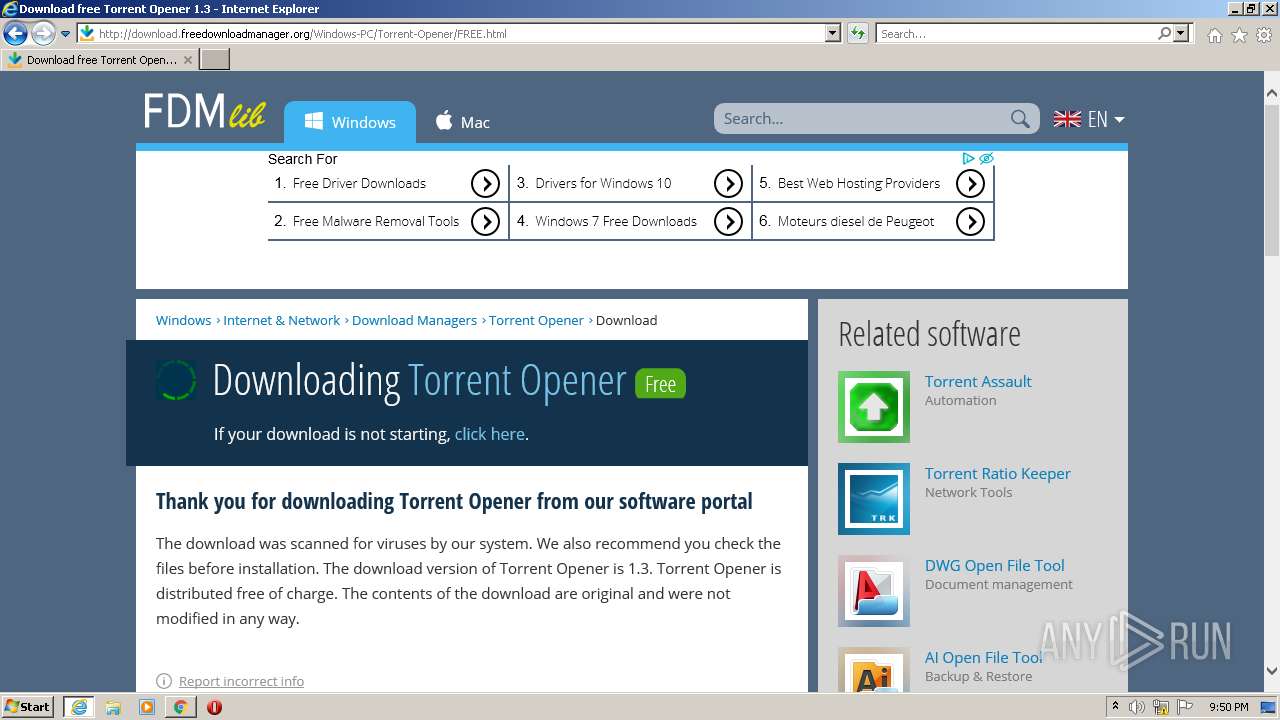
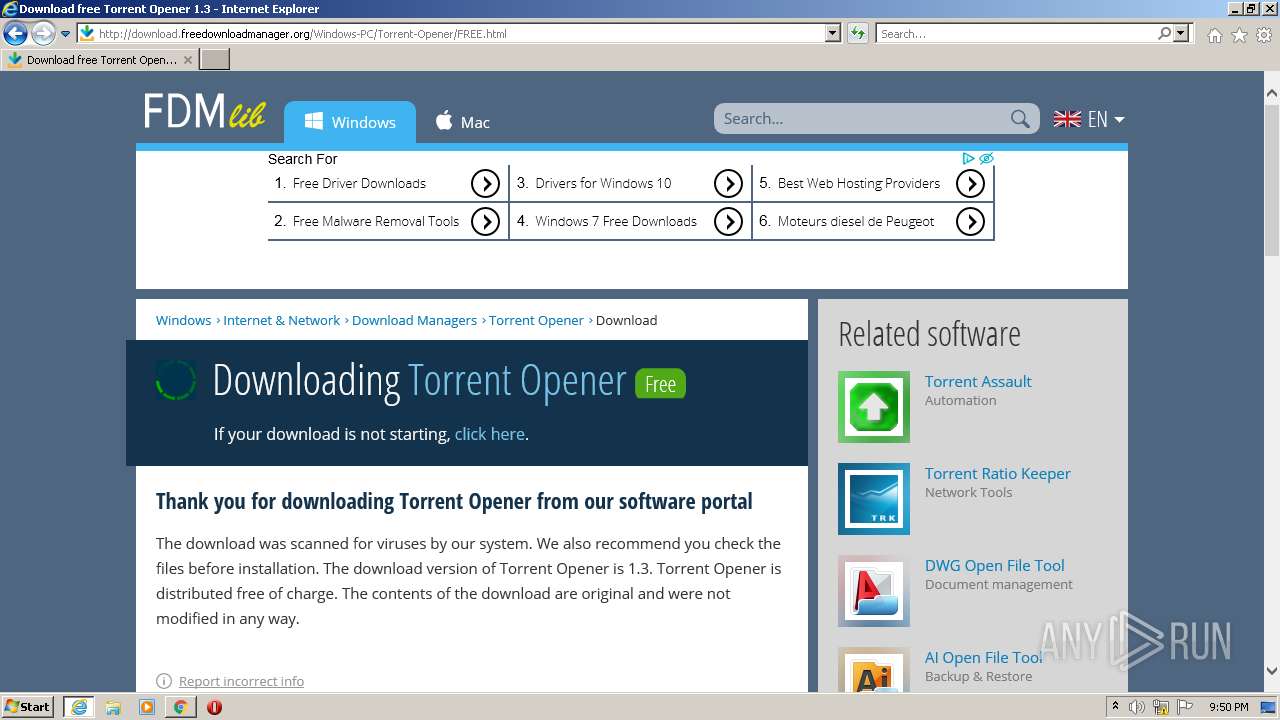
2964 | iexplore.exe | GET | 200 | 74.117.183.142:80 | http://static.freedownloadmanager.org/icon/48/3289/3289082.png | US | image | 6.17 Kb | suspicious |
2964 | iexplore.exe | GET | 200 | 142.250.184.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwLgTBFaXf4QoAAAABOwp6 | US | der | 472 b | whitelisted |
2964 | iexplore.exe | GET | 200 | 74.117.183.142:80 | http://static.freedownloadmanager.org/icon/48/6061/6061444.png | US | image | 3.48 Kb | suspicious |
2964 | iexplore.exe | GET | 200 | 74.117.183.142:80 | http://static.freedownloadmanager.org/icon/48/986/986155.png | US | image | 6.83 Kb | suspicious |
2964 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEQCocHHgurGh6qOXCw3WX0C4 | US | der | 472 b | whitelisted |
2964 | iexplore.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2260 | chrome.exe | 65.9.58.213:443 | djv99sxoqpv11.cloudfront.net | AT&T Services, Inc. | US | malicious |
2260 | chrome.exe | 151.101.2.217:443 | vjs.zencdn.net | Fastly | US | suspicious |
2260 | chrome.exe | 195.96.151.43:443 | cdn-149.anonfiles.com | Archway S.r.l | IQ | suspicious |
2260 | chrome.exe | 142.250.185.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2260 | chrome.exe | 142.250.184.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2964 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2964 | iexplore.exe | 184.24.77.147:80 | shell.windows.com | Time Warner Cable Internet LLC | US | unknown |
2964 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
2964 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2964 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
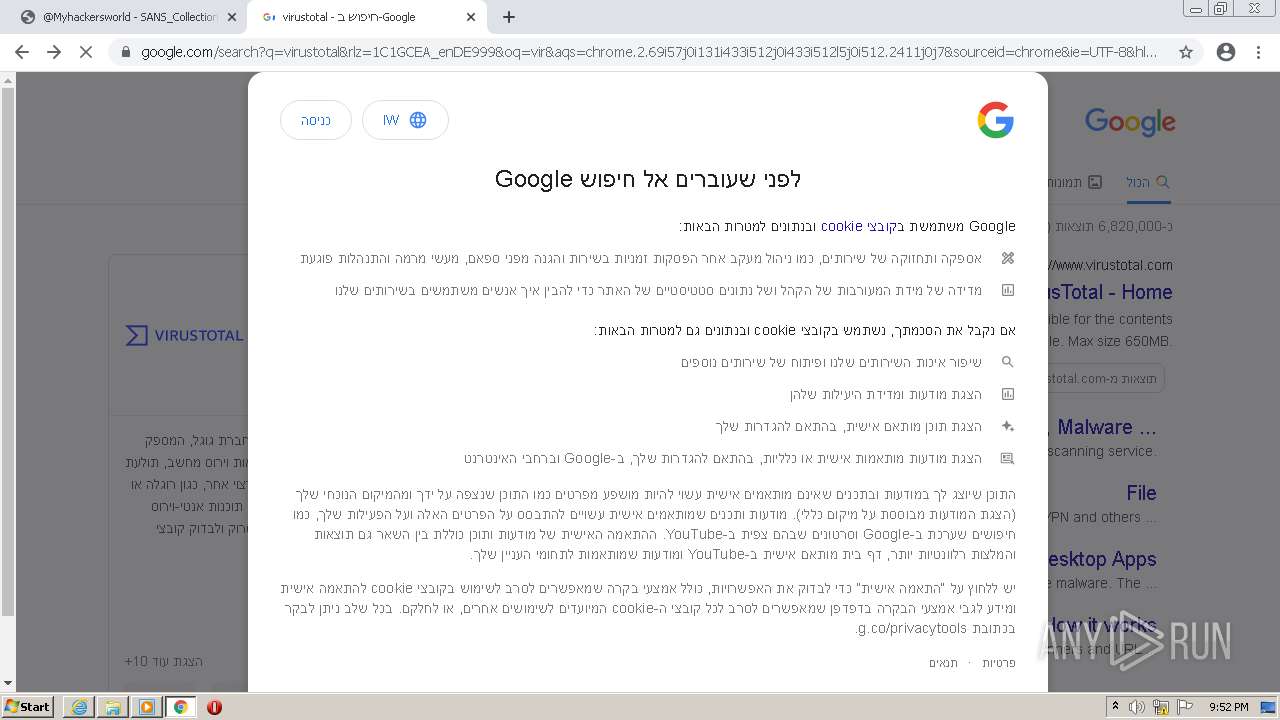
clients2.google.com |
| whitelisted |
anonfiles.com |
| shared |
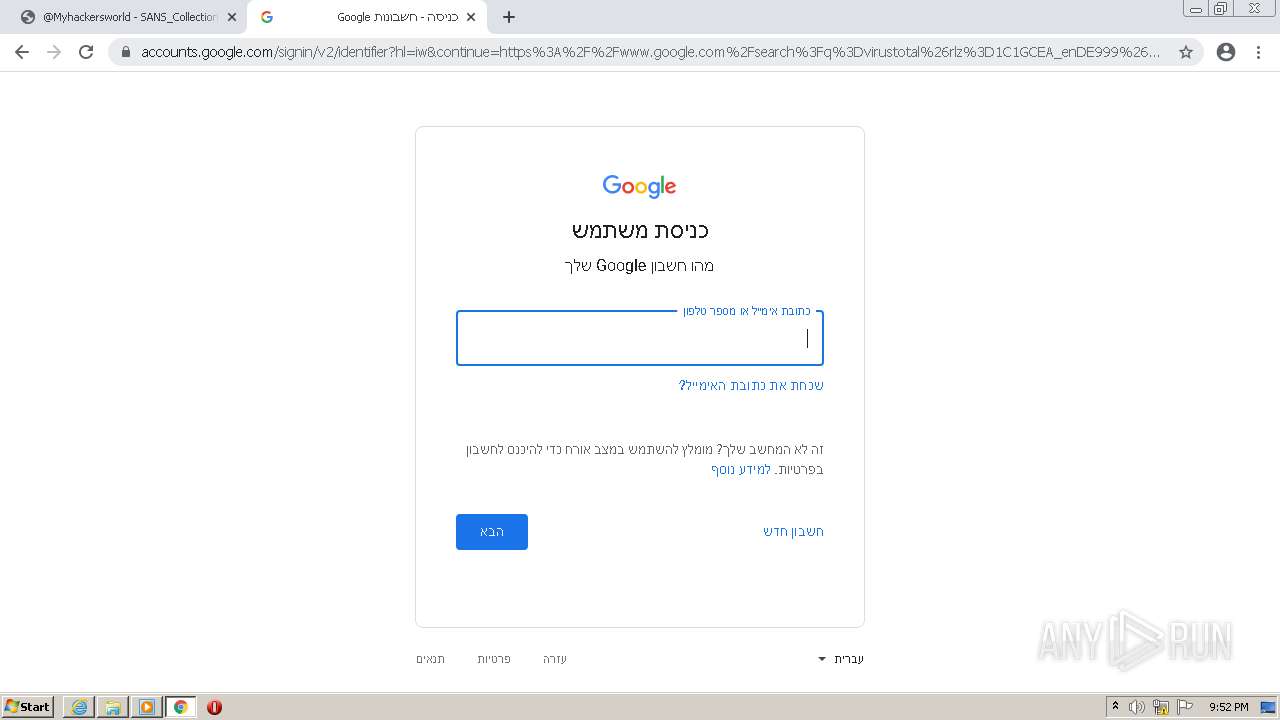
accounts.google.com |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
vjs.zencdn.net |
| whitelisted |
djv99sxoqpv11.cloudfront.net |
| shared |
cdn-149.anonfiles.com |
| suspicious |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2964 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2964 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |