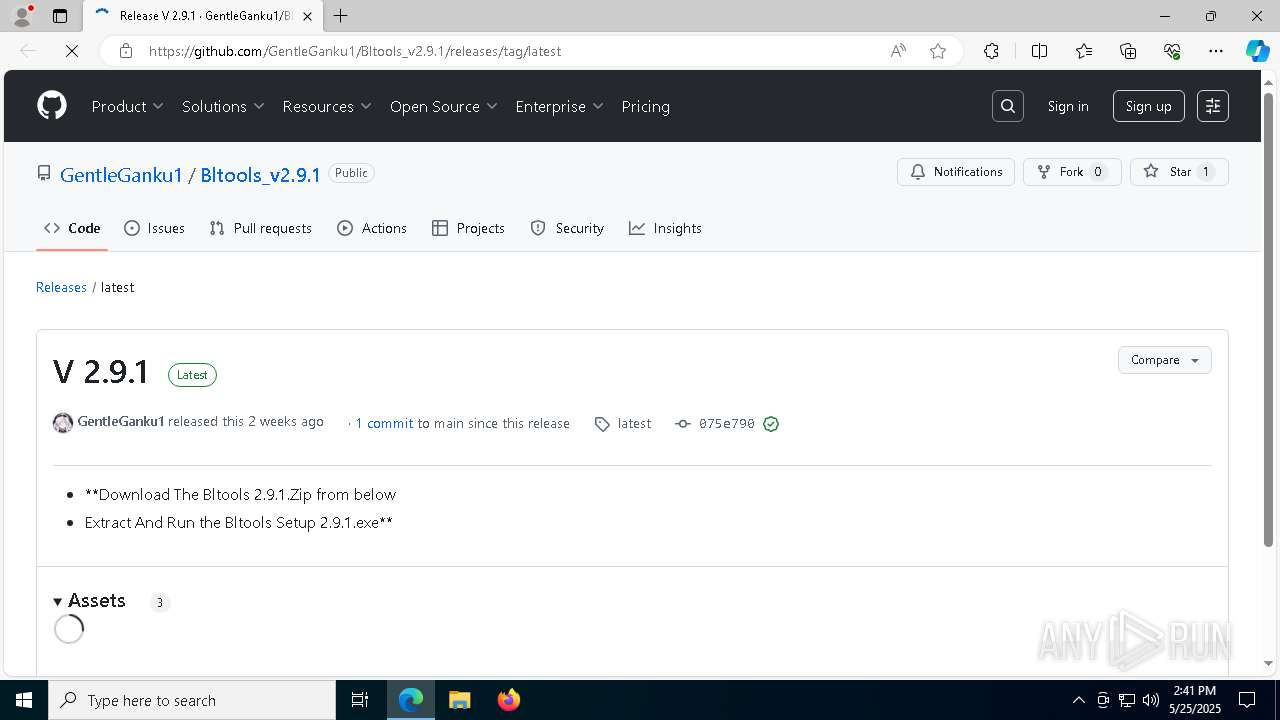
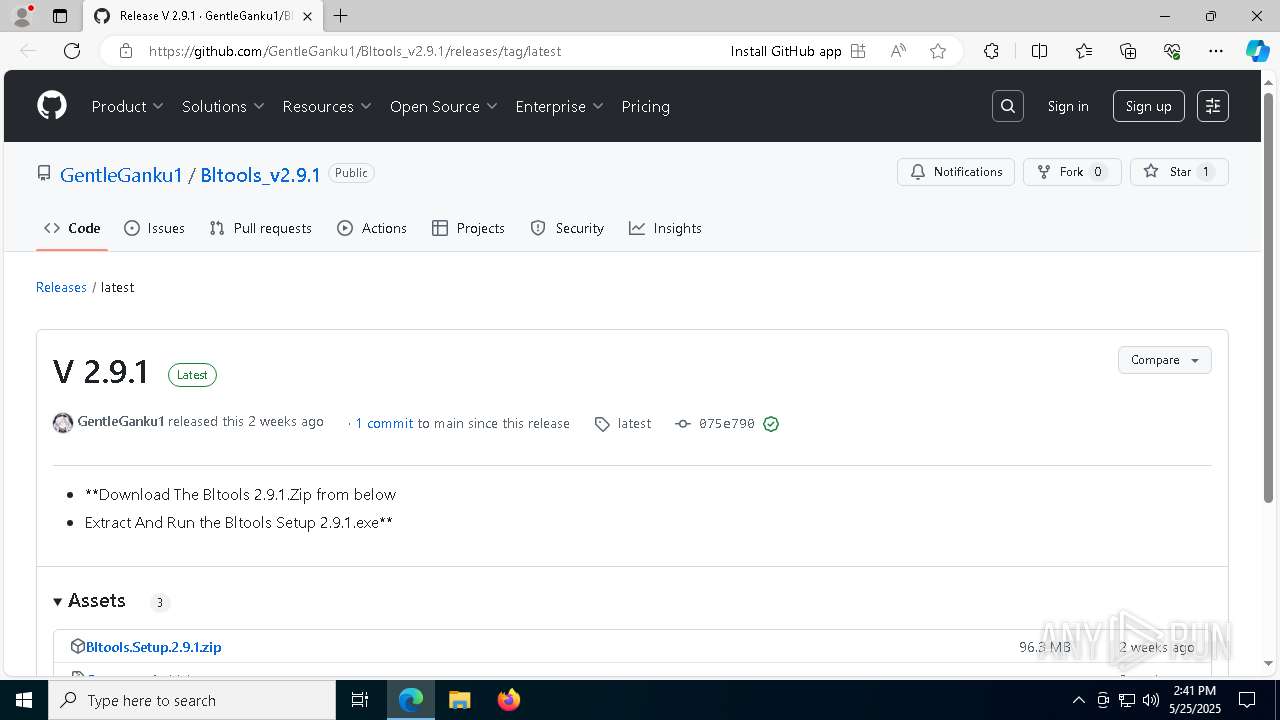
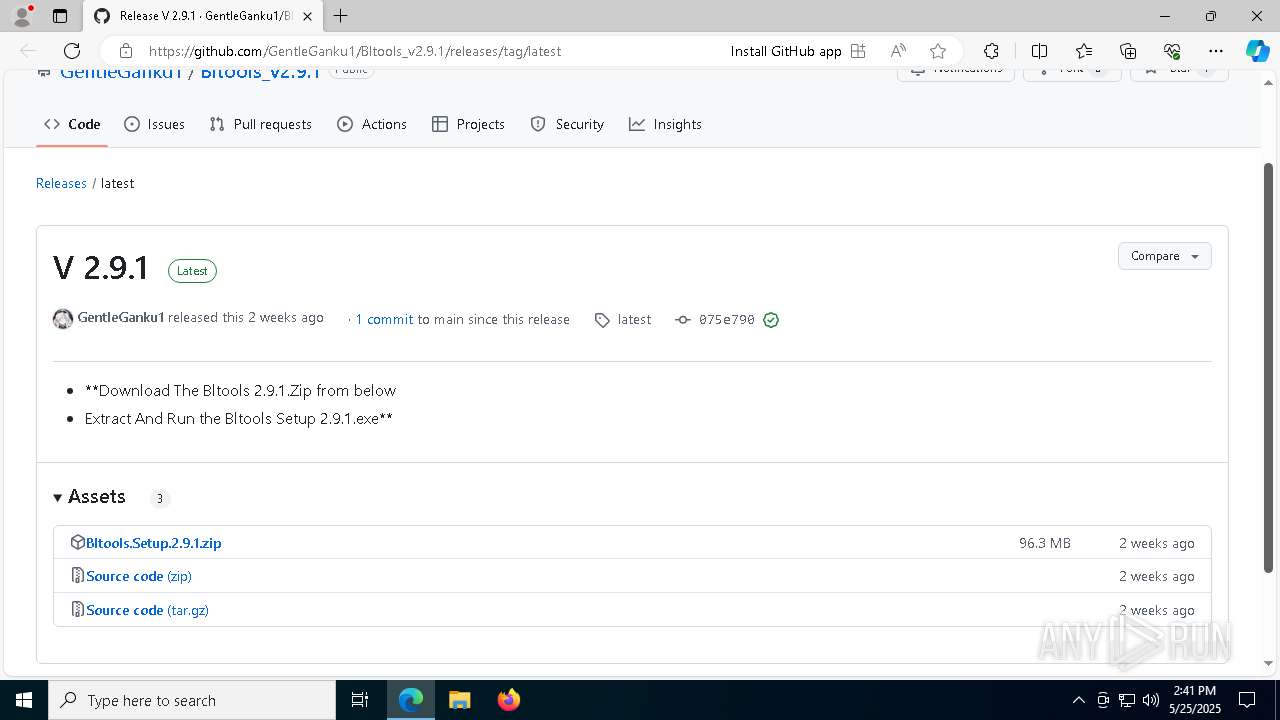
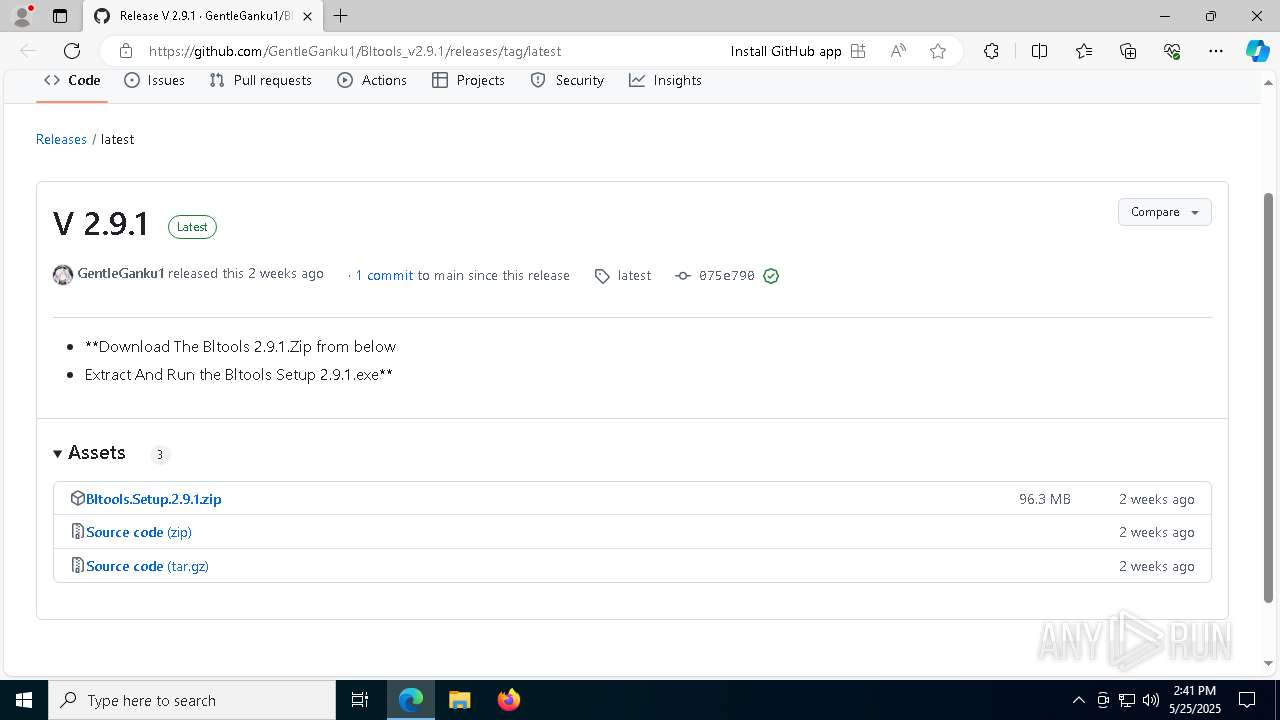
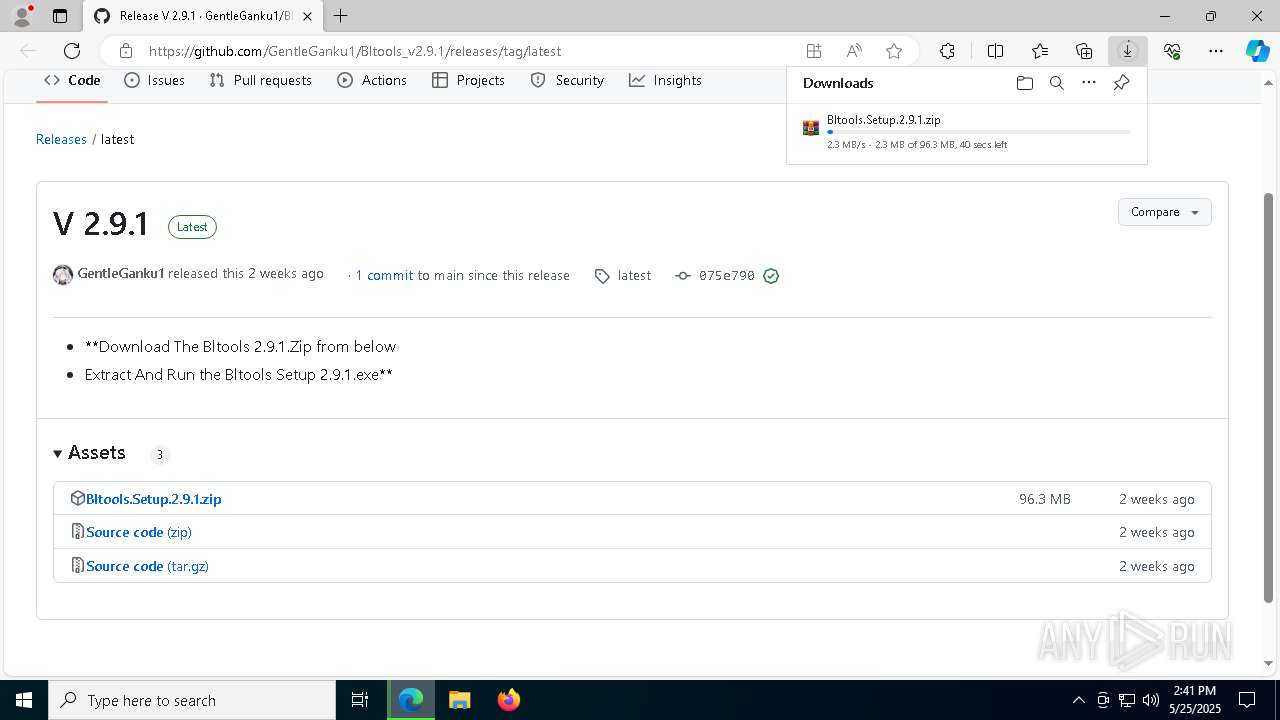
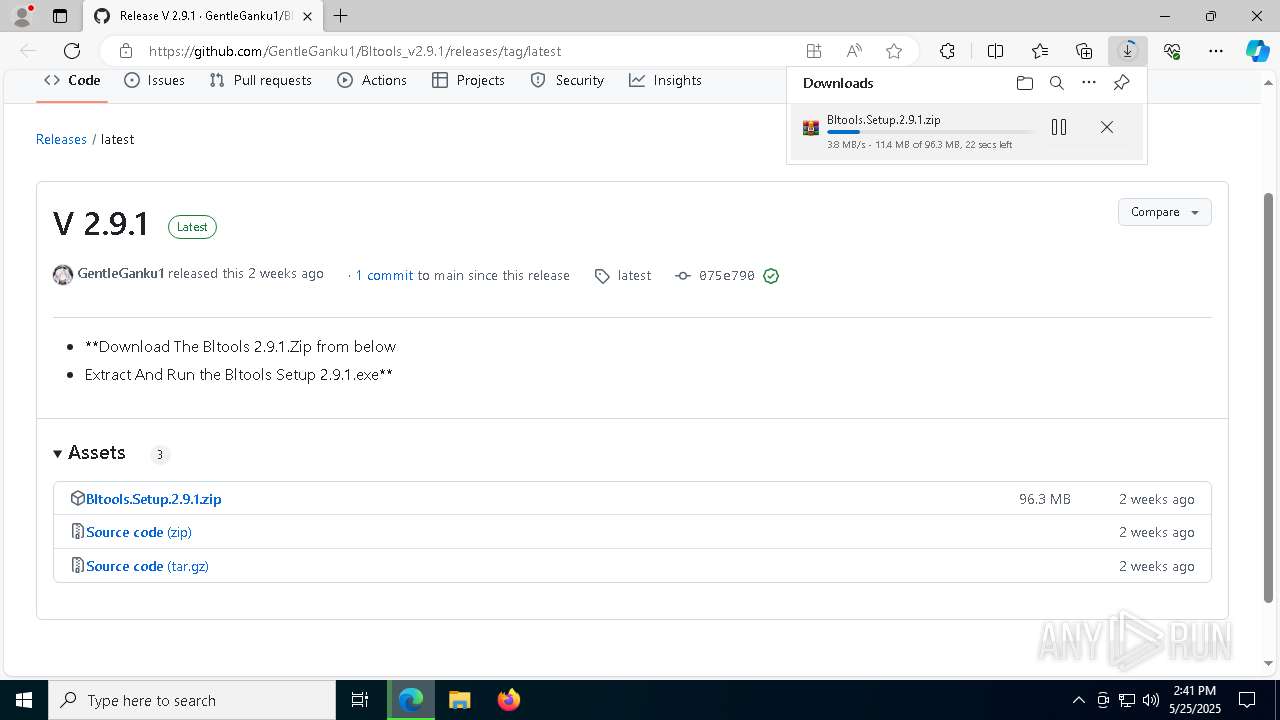
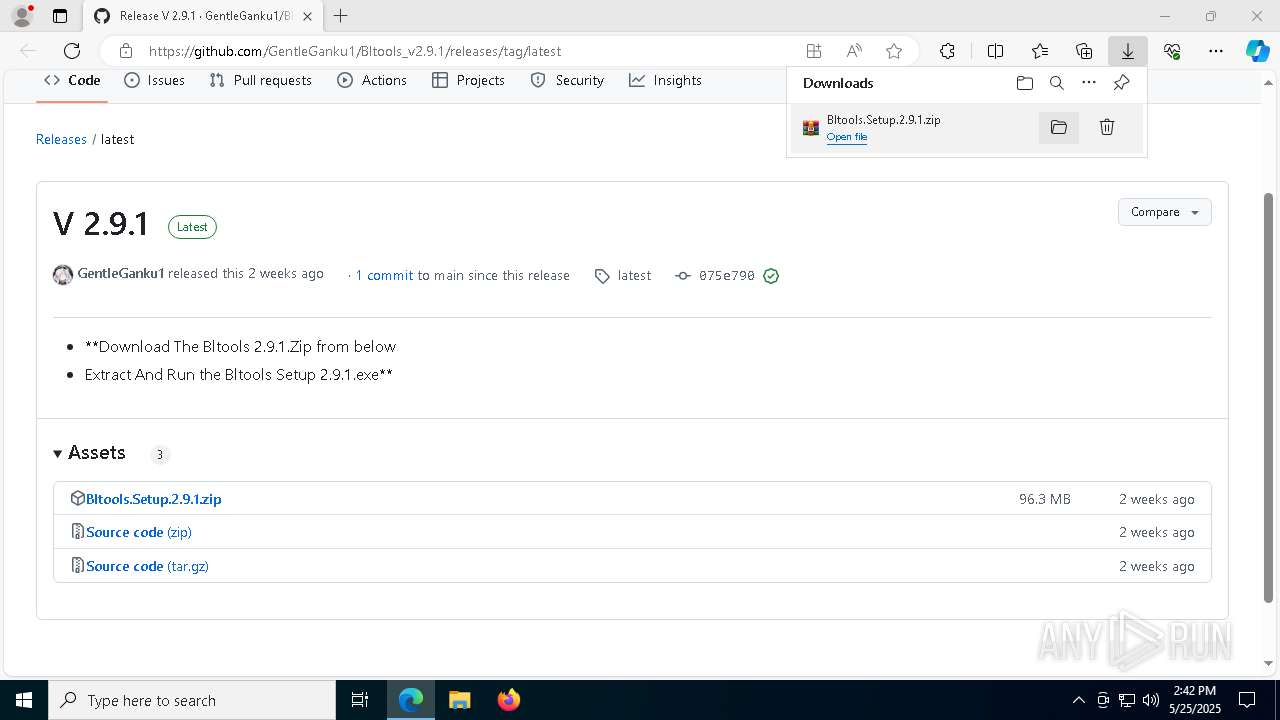
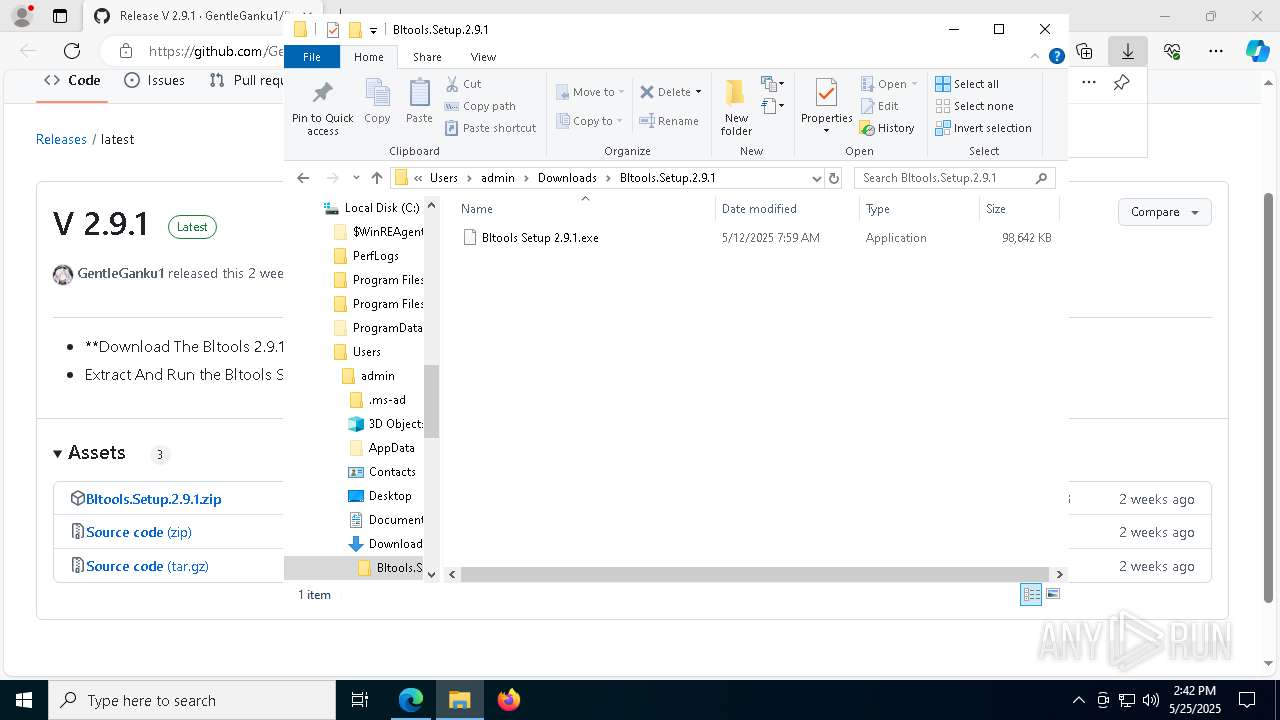
| URL: | https://github.com/GentleGanku1/Bltools_v2.9.1/releases/tag/latest |
| Full analysis: | https://app.any.run/tasks/6f154264-d9f6-4e51-87ab-5e60fc889a1f |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 14:41:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C744CD92B7817F97FD60F6F7F5BDD82E |
| SHA1: | 5BBE45602A7870FCB8BC2DD4E7E6E858DD8E6703 |
| SHA256: | 48BABB47F736C801C38F0673065FFCD4A46046E84E397F3955D9A825F3C9477F |
| SSDEEP: | 3:N8tEdYnXO6RKqKbWR:2uORKxC |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process creates files with name similar to system file names
- Bltools Setup 2.9.1.exe (PID: 5780)
Malware-specific behavior (creating "System.dll" in Temp)
- Bltools Setup 2.9.1.exe (PID: 5780)
- Bltools Setup 2.9.1.exe (PID: 12836)
Executable content was dropped or overwritten
- Bltools Setup 2.9.1.exe (PID: 5780)
- Bltools Setup 2.9.1.exe (PID: 12836)
Get information on the list of running processes
- Bltools Setup 2.9.1.exe (PID: 5780)
- cmd.exe (PID: 6752)
- Bltools Setup 2.9.1.exe (PID: 12836)
- cmd.exe (PID: 12052)
Starts CMD.EXE for commands execution
- Bltools Setup 2.9.1.exe (PID: 5780)
- Bltools.exe (PID: 6032)
- Bltools.exe (PID: 5164)
- Bltools.exe (PID: 7864)
- Bltools.exe (PID: 8220)
- Bltools.exe (PID: 4112)
- Bltools.exe (PID: 2980)
- Bltools.exe (PID: 8536)
- Bltools.exe (PID: 8292)
- Bltools.exe (PID: 8364)
- Bltools.exe (PID: 8888)
- Bltools.exe (PID: 9104)
- Bltools.exe (PID: 9252)
- Bltools.exe (PID: 9588)
- Bltools.exe (PID: 10196)
- Bltools.exe (PID: 9688)
- Bltools.exe (PID: 10068)
- Bltools.exe (PID: 10452)
- Bltools.exe (PID: 10844)
- Bltools.exe (PID: 10332)
- Bltools.exe (PID: 10712)
- Bltools.exe (PID: 11060)
- Bltools Setup 2.9.1.exe (PID: 12836)
Drops 7-zip archiver for unpacking
- Bltools Setup 2.9.1.exe (PID: 5780)
There is functionality for taking screenshot (YARA)
- Bltools Setup 2.9.1.exe (PID: 5780)
Reads security settings of Internet Explorer
- Bltools Setup 2.9.1.exe (PID: 5780)
Process drops legitimate windows executable
- Bltools Setup 2.9.1.exe (PID: 5780)
Starts application with an unusual extension
- cmd.exe (PID: 2284)
- cmd.exe (PID: 632)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 5188)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 8432)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 9084)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 9780)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 10180)
- cmd.exe (PID: 10248)
- cmd.exe (PID: 10688)
- cmd.exe (PID: 10868)
- cmd.exe (PID: 11048)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 10636)
- cmd.exe (PID: 11564)
- cmd.exe (PID: 11480)
Application launched itself
- Bltools.exe (PID: 7864)
- Bltools.exe (PID: 6032)
- Bltools.exe (PID: 5164)
- Bltools.exe (PID: 2980)
- Bltools.exe (PID: 4112)
- Bltools.exe (PID: 8220)
- Bltools.exe (PID: 8292)
- Bltools.exe (PID: 8364)
- Bltools.exe (PID: 8536)
- Bltools.exe (PID: 8888)
- Bltools.exe (PID: 9252)
- Bltools.exe (PID: 9104)
- Bltools.exe (PID: 9588)
- Bltools.exe (PID: 9688)
- Bltools.exe (PID: 10068)
- Bltools.exe (PID: 10332)
- Bltools.exe (PID: 10196)
- Bltools.exe (PID: 10712)
- Bltools.exe (PID: 10452)
- Bltools.exe (PID: 10844)
- Bltools.exe (PID: 11060)
Connects to unusual port
- Bltools.exe (PID: 7864)
- Bltools.exe (PID: 6032)
- Bltools.exe (PID: 5164)
- Bltools.exe (PID: 4112)
- Bltools.exe (PID: 2980)
- Bltools.exe (PID: 8536)
- Bltools.exe (PID: 8364)
- Bltools.exe (PID: 8220)
- Bltools.exe (PID: 8292)
- Bltools.exe (PID: 8888)
- Bltools.exe (PID: 9252)
- Bltools.exe (PID: 9588)
- Bltools.exe (PID: 9688)
- Bltools.exe (PID: 9104)
- Bltools.exe (PID: 10332)
- Bltools.exe (PID: 10712)
- Bltools.exe (PID: 10452)
- Bltools.exe (PID: 10844)
- Bltools.exe (PID: 11060)
- Bltools.exe (PID: 10068)
- Bltools.exe (PID: 10196)
Checks for external IP
- Bltools.exe (PID: 7864)
- Bltools.exe (PID: 6032)
- Bltools.exe (PID: 5164)
- Bltools.exe (PID: 4112)
- Bltools.exe (PID: 2980)
- Bltools.exe (PID: 8220)
- Bltools.exe (PID: 8292)
- Bltools.exe (PID: 8536)
- Bltools.exe (PID: 9252)
- Bltools.exe (PID: 8888)
- Bltools.exe (PID: 9104)
- Bltools.exe (PID: 10452)
- Bltools.exe (PID: 9688)
- Bltools.exe (PID: 10196)
- Bltools.exe (PID: 10068)
- Bltools.exe (PID: 10712)
- Bltools.exe (PID: 9588)
- Bltools.exe (PID: 11060)
INFO
The sample compiled with english language support
- msedge.exe (PID: 2600)
- Bltools Setup 2.9.1.exe (PID: 5780)
- Bltools Setup 2.9.1.exe (PID: 12836)
Checks supported languages
- Bltools Setup 2.9.1.exe (PID: 5780)
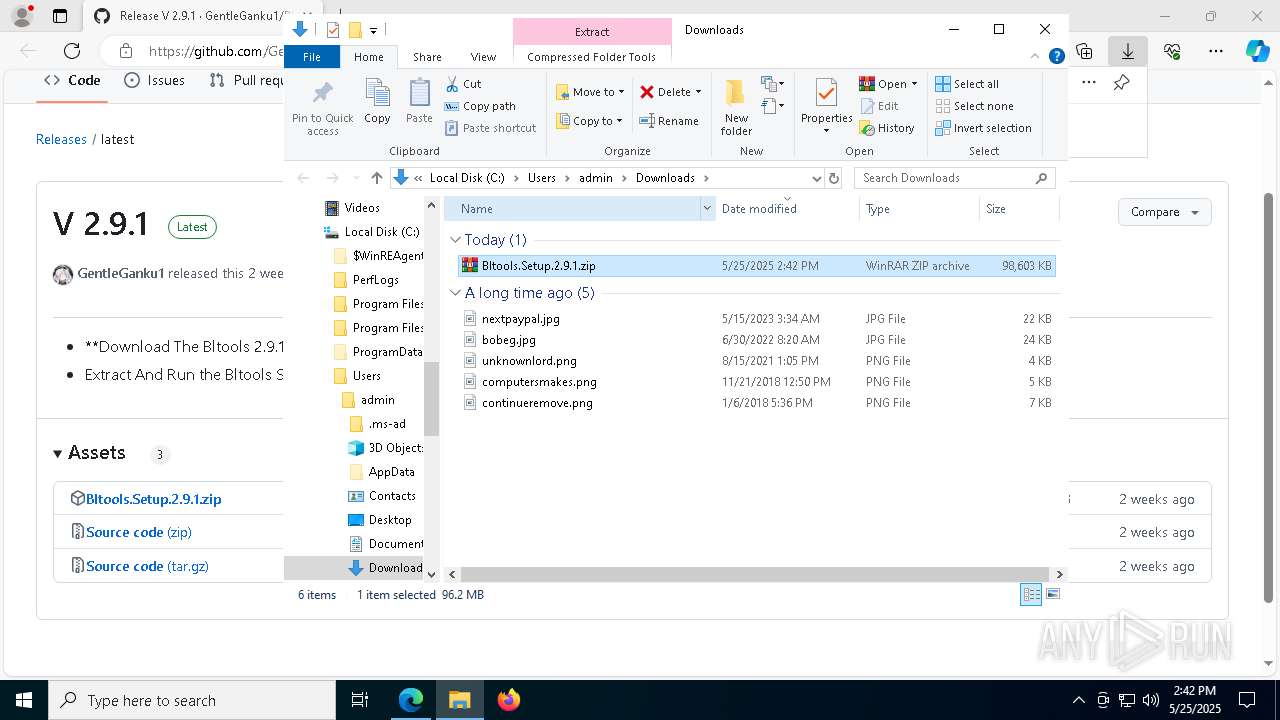
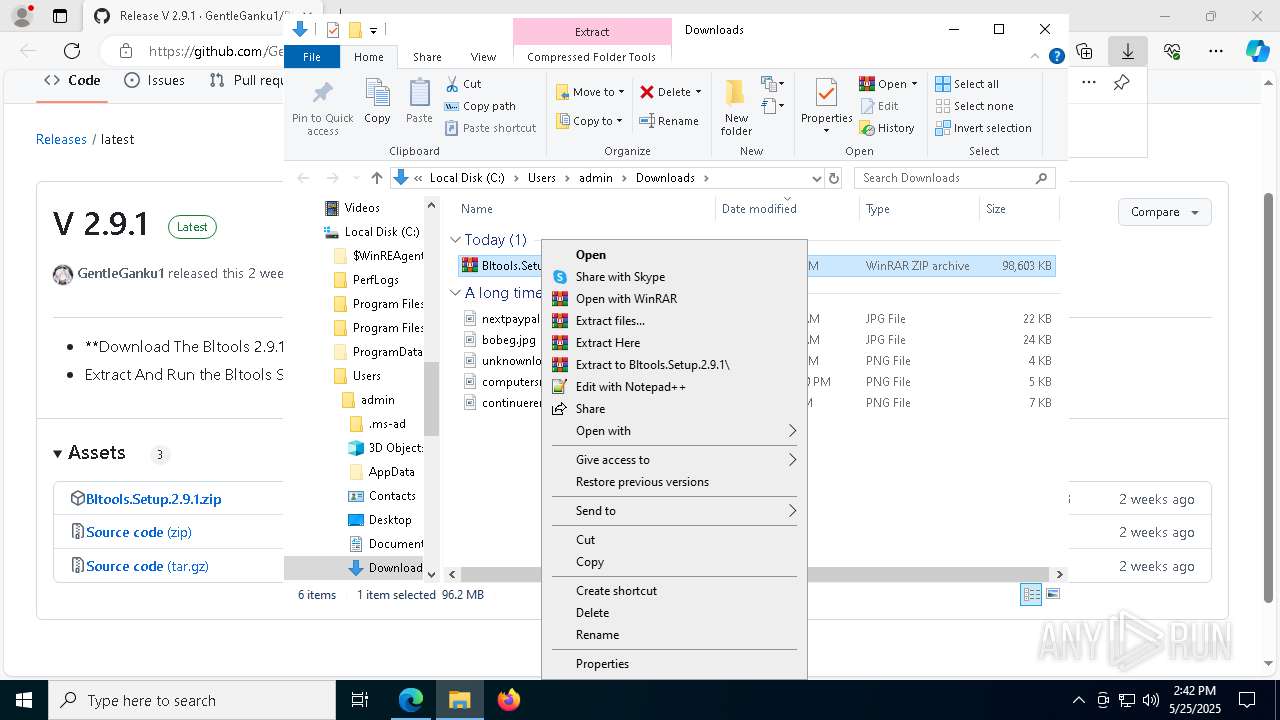
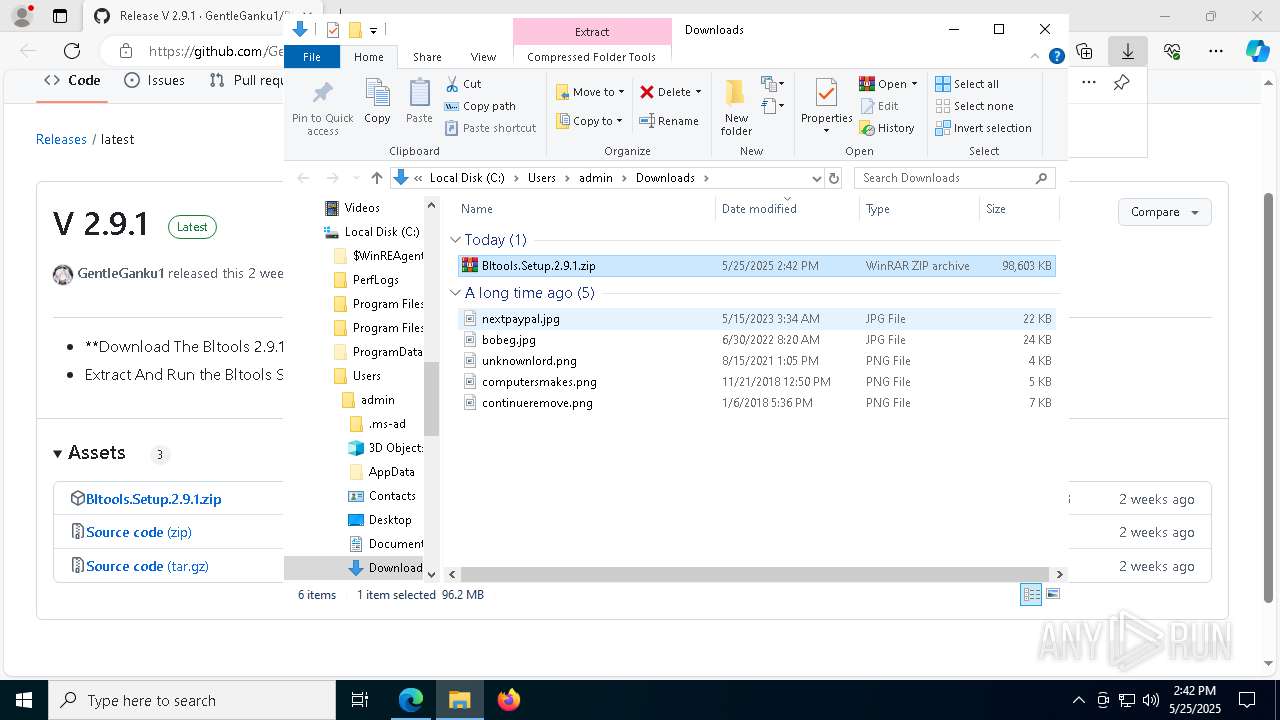
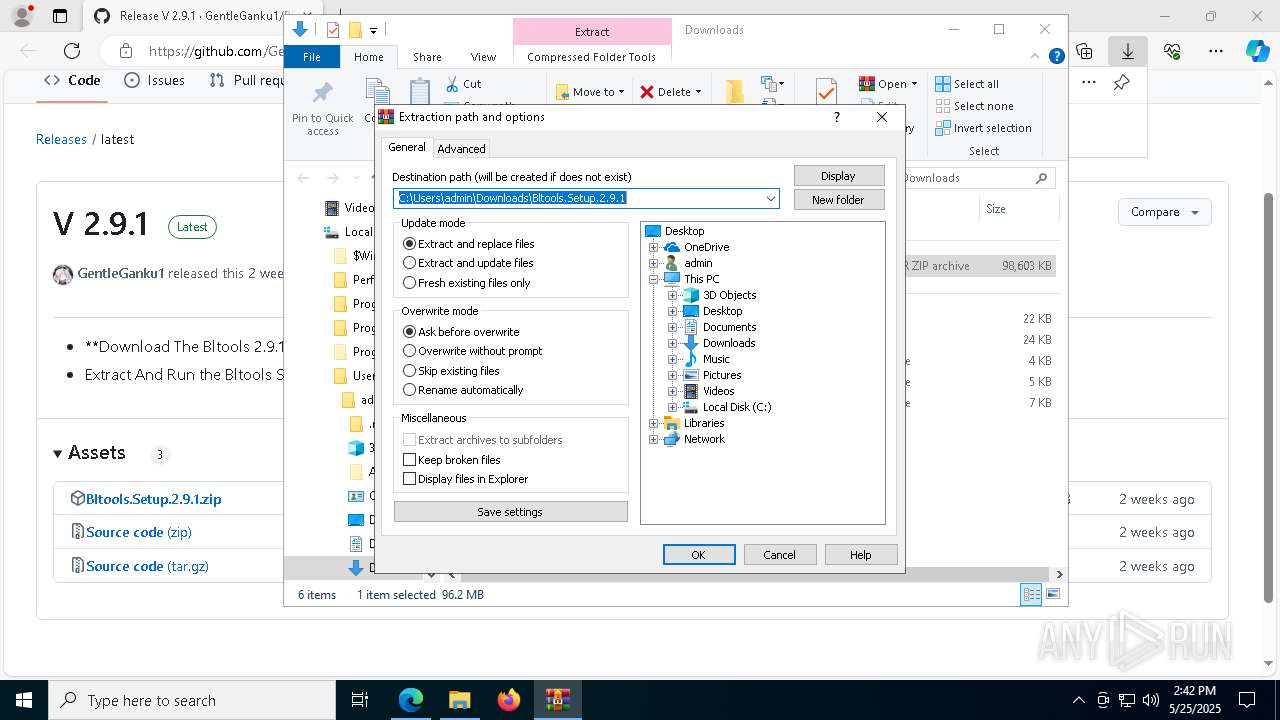
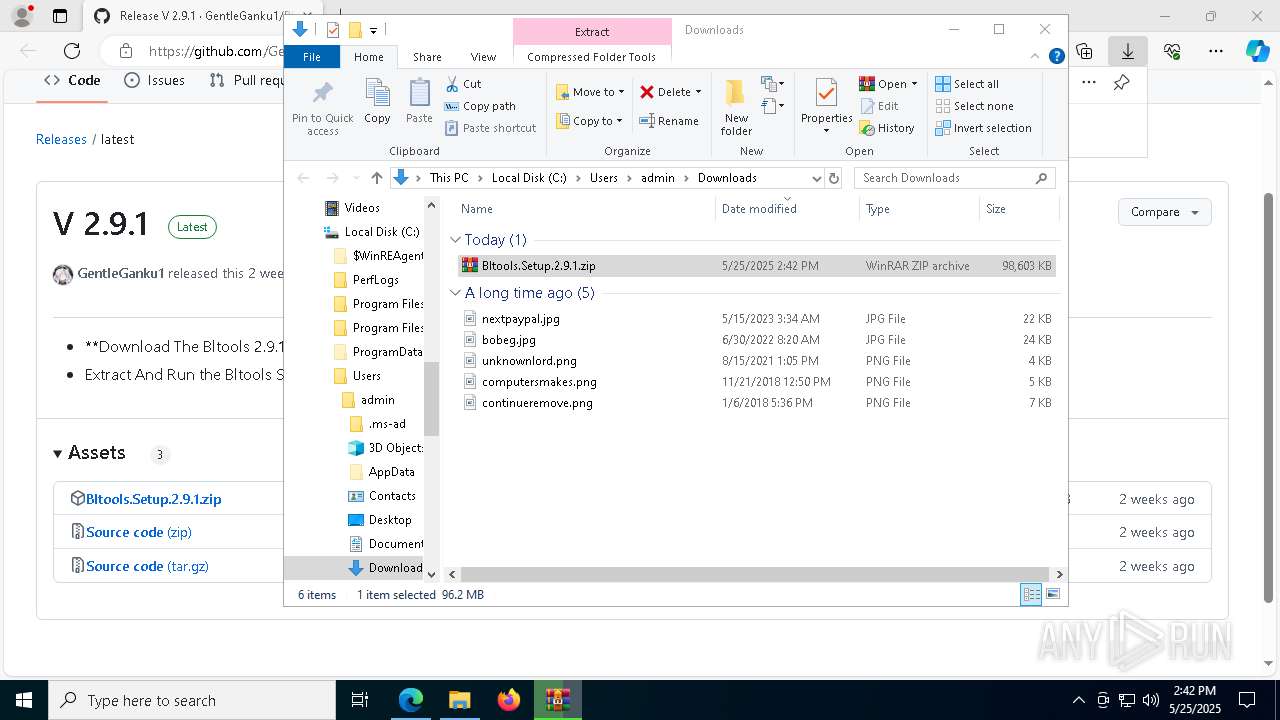
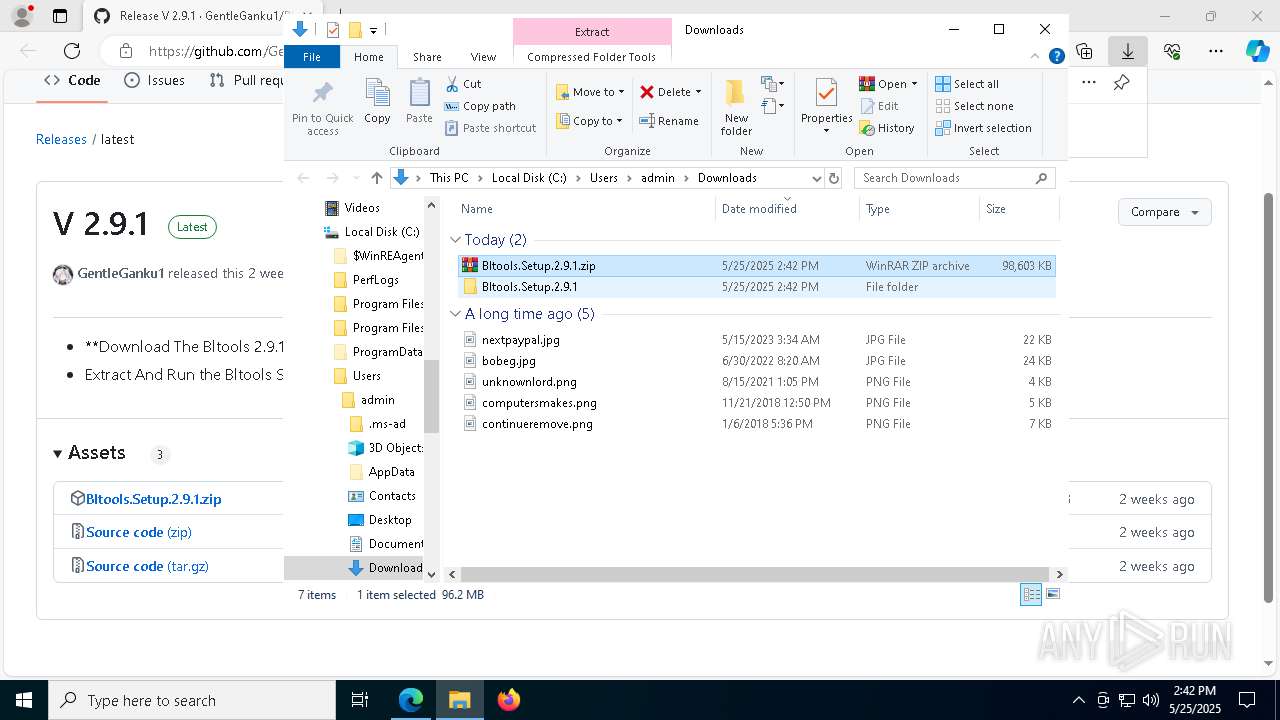
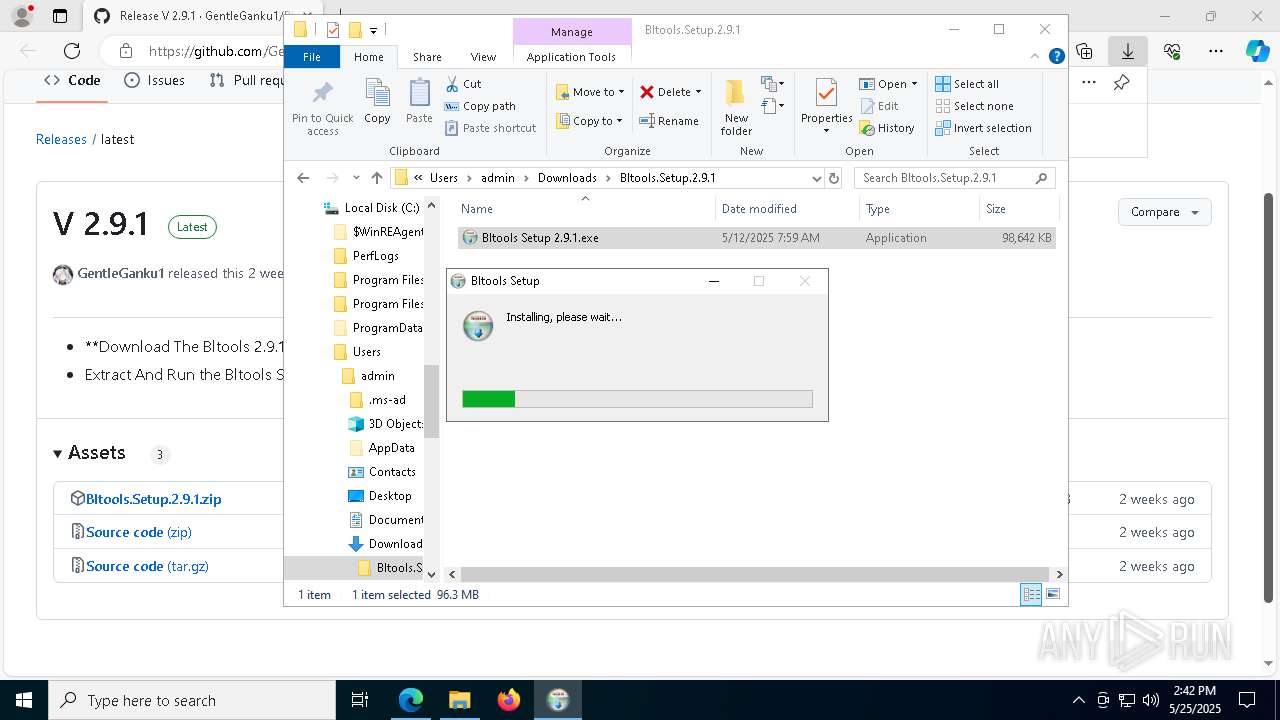
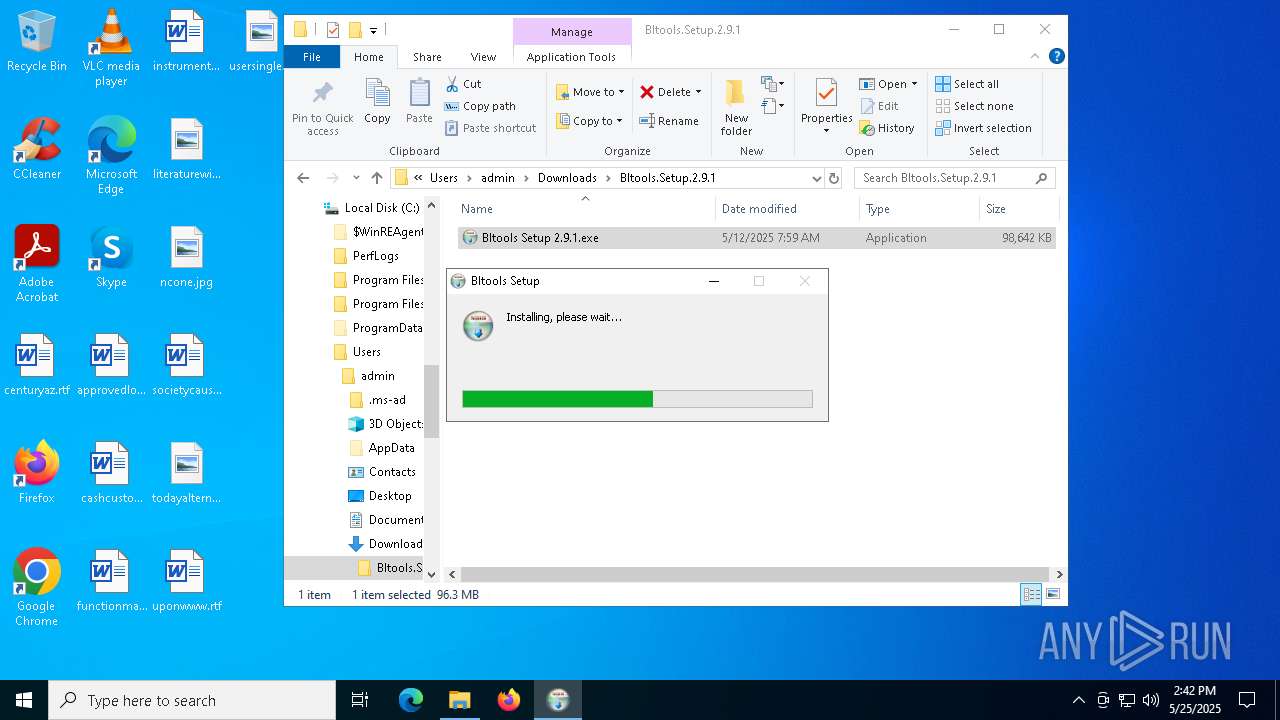
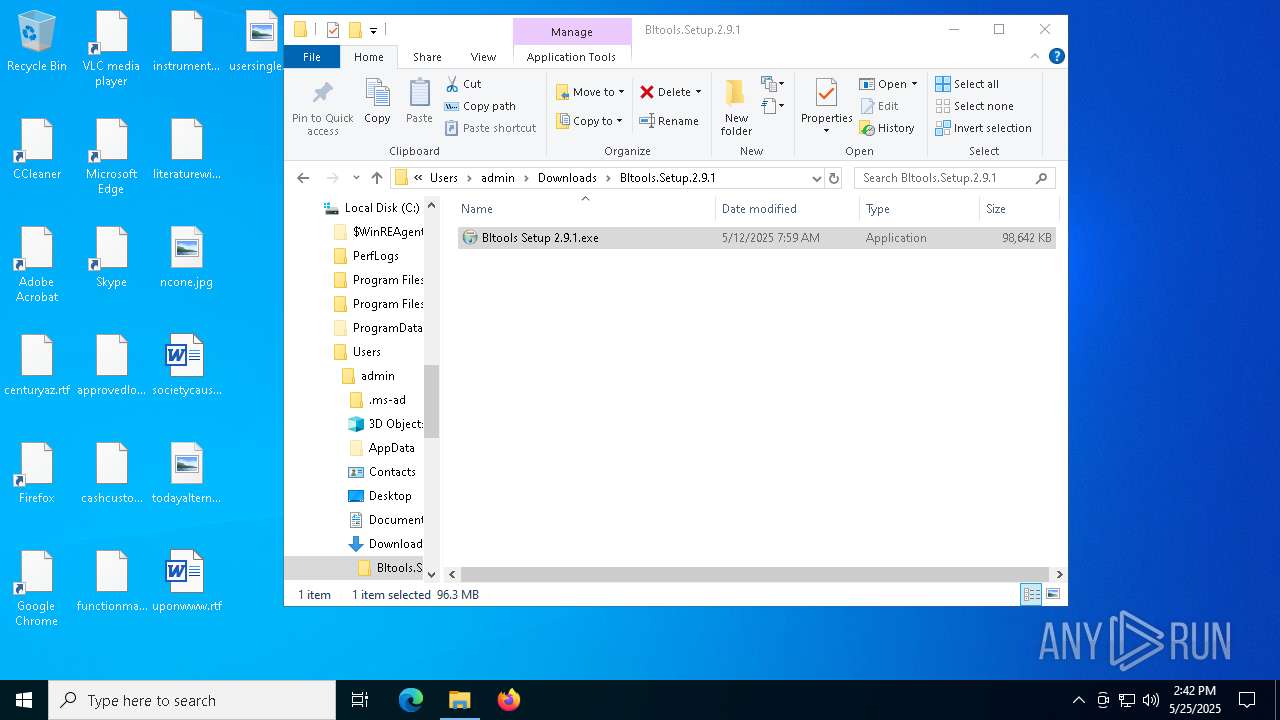
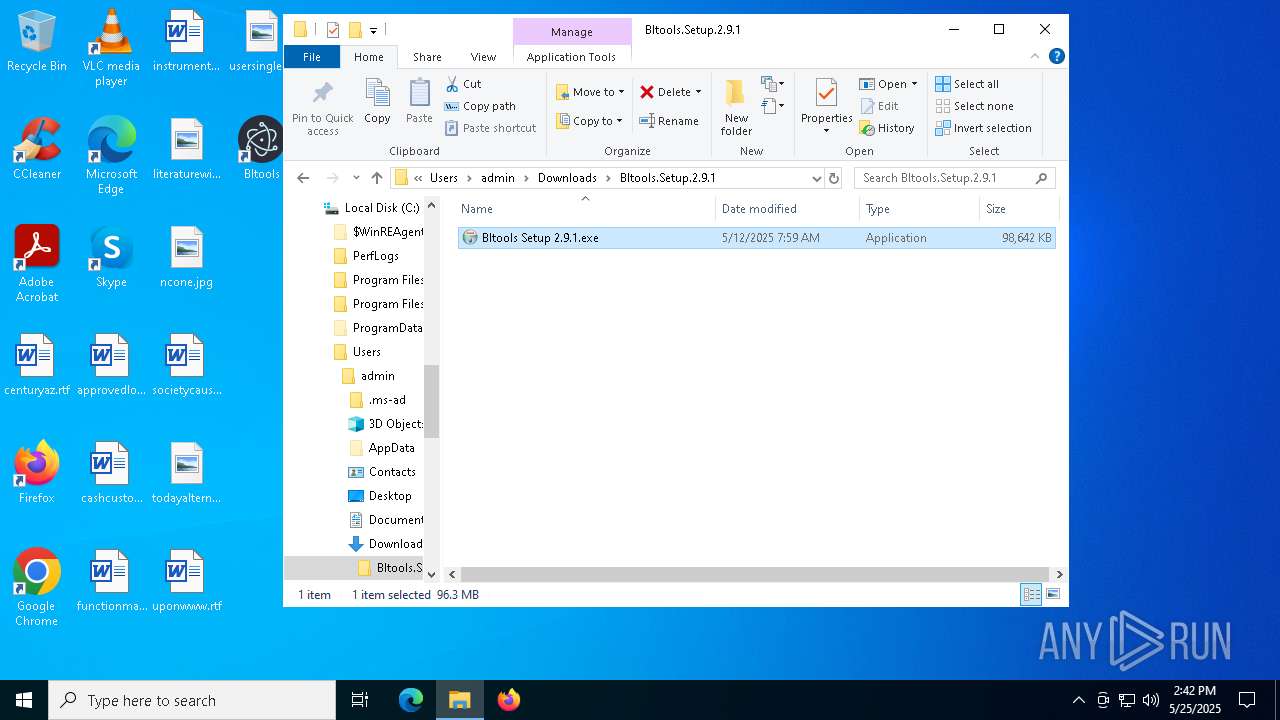
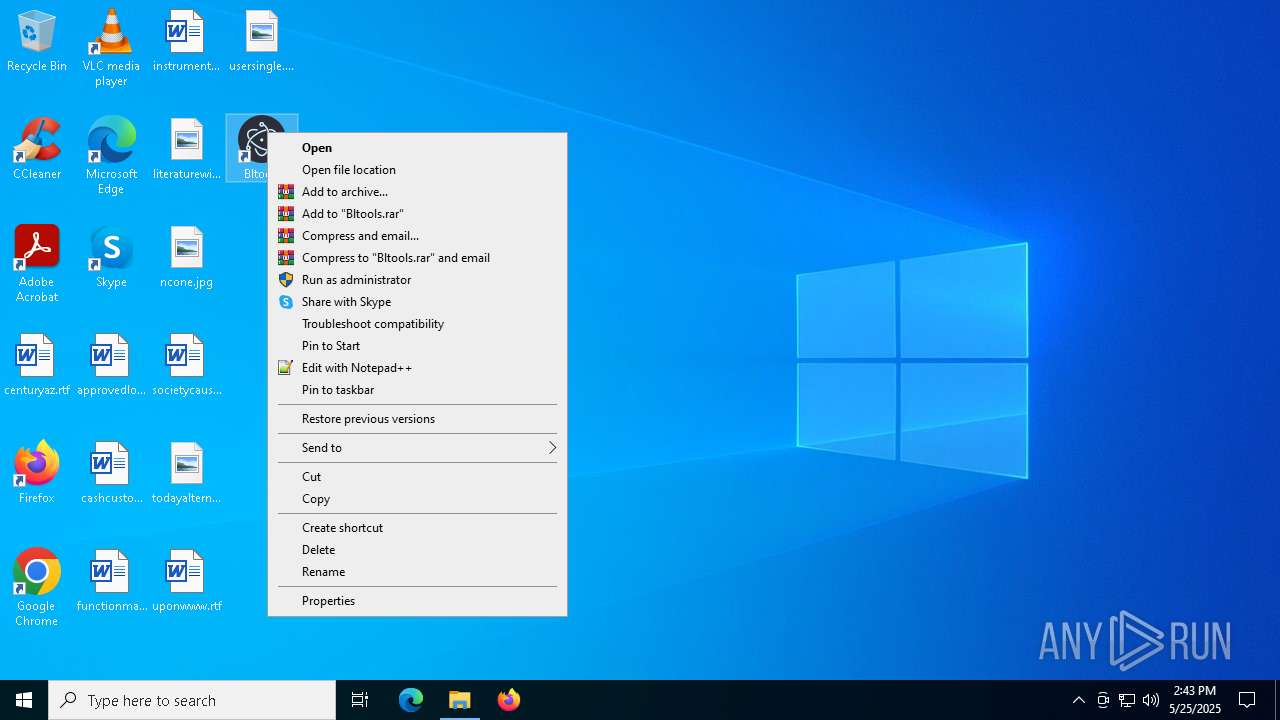
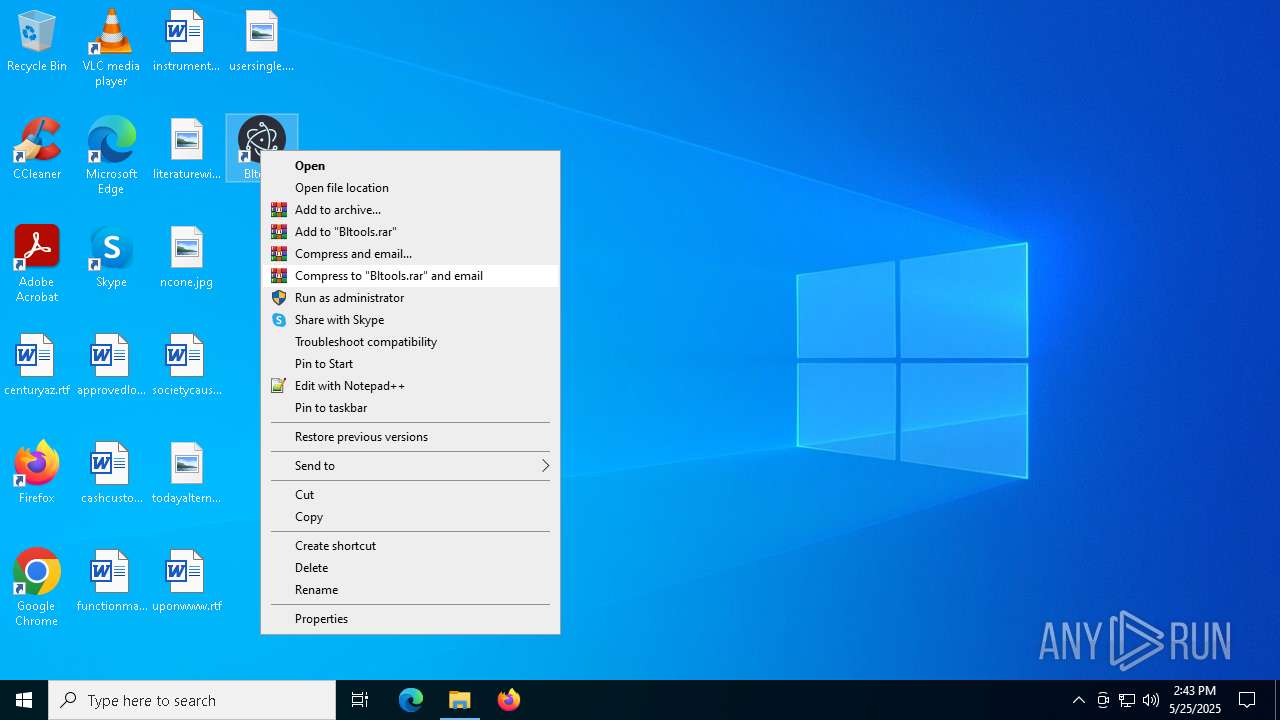
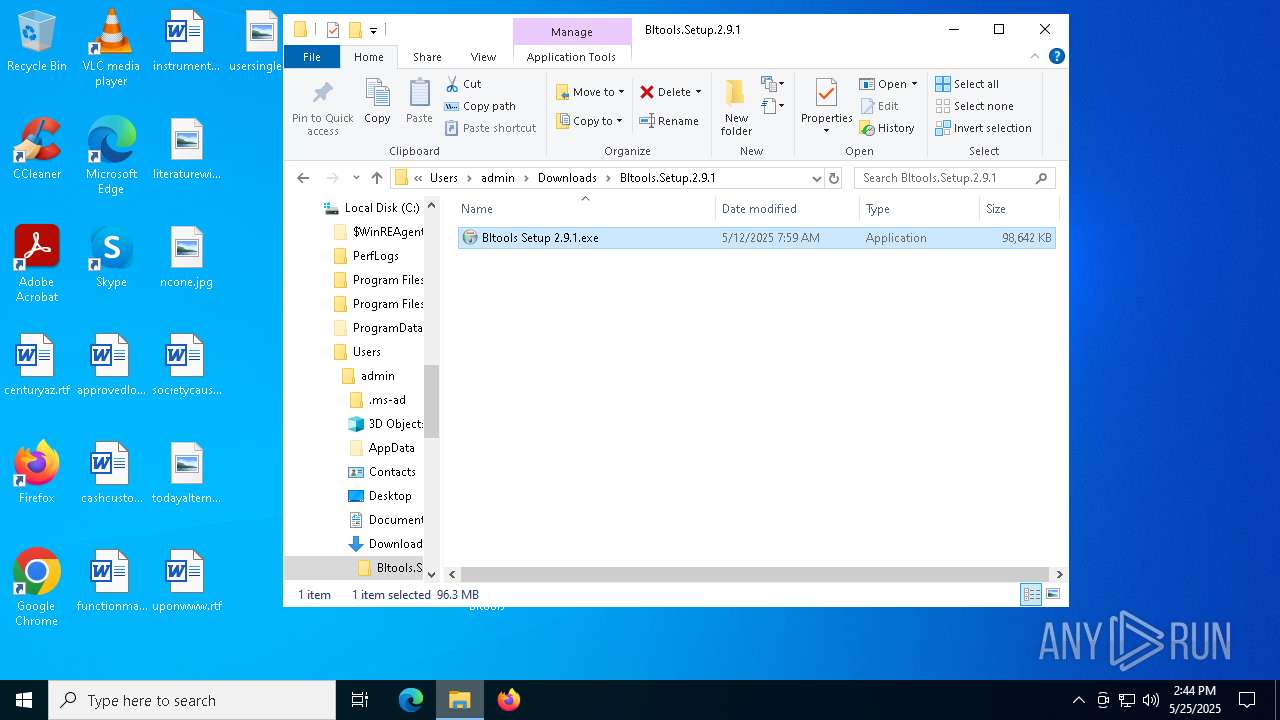
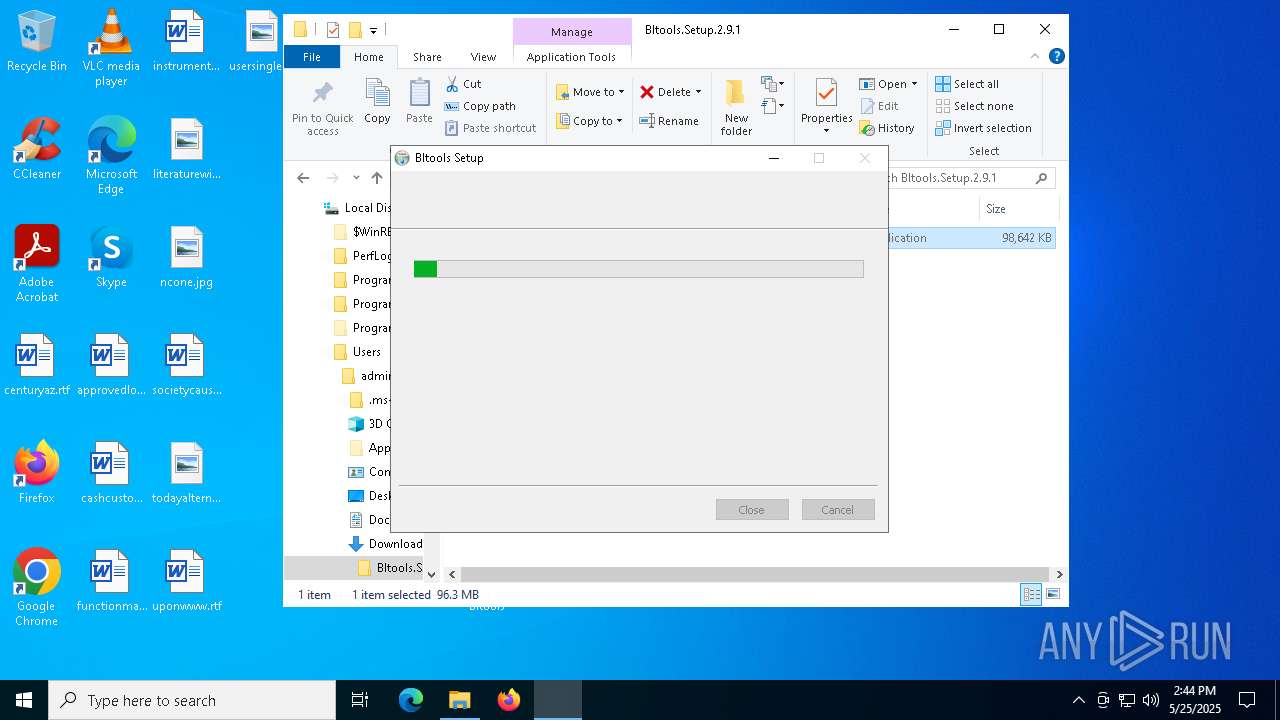
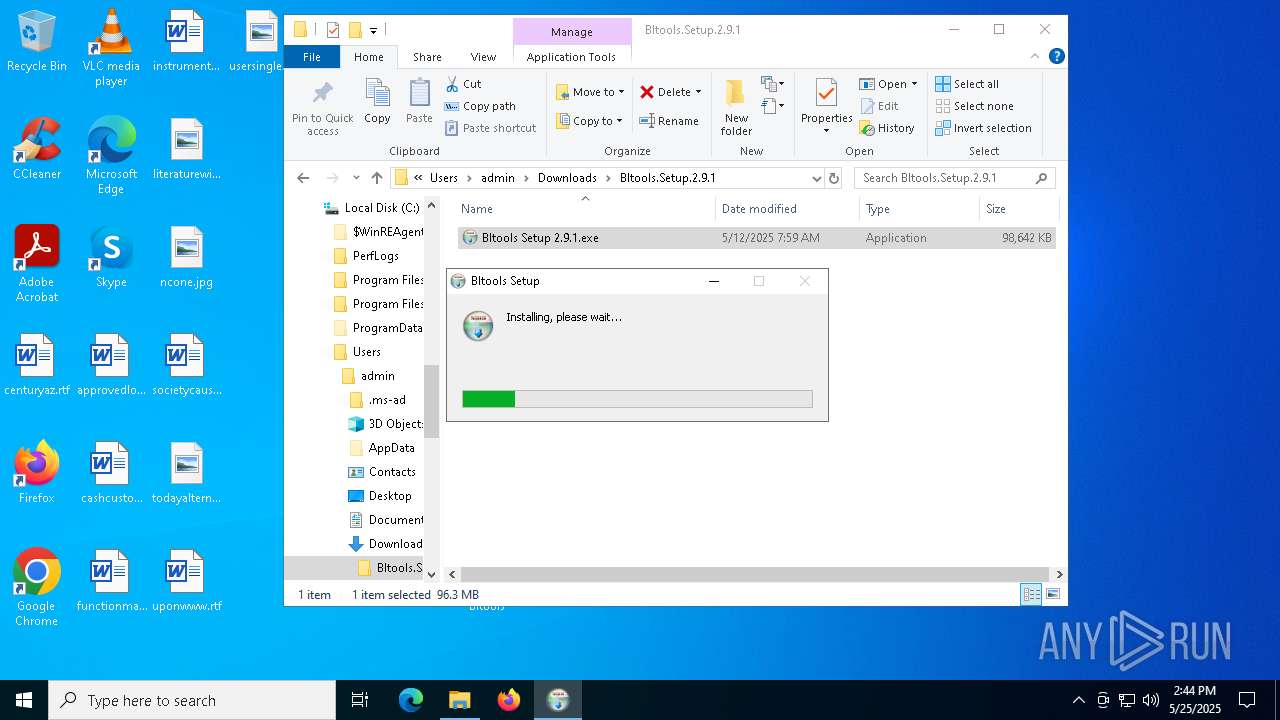
Manual execution by a user
- WinRAR.exe (PID: 7452)
- Bltools Setup 2.9.1.exe (PID: 5780)
- Bltools.exe (PID: 6032)
- Bltools.exe (PID: 5164)
- Bltools.exe (PID: 7864)
- Bltools.exe (PID: 2980)
- Bltools.exe (PID: 8220)
- Bltools.exe (PID: 8292)
- Bltools.exe (PID: 8364)
- Bltools.exe (PID: 4112)
- Bltools.exe (PID: 8536)
- Bltools.exe (PID: 8888)
- Bltools.exe (PID: 9104)
- Bltools.exe (PID: 9252)
- Bltools.exe (PID: 9588)
- Bltools.exe (PID: 9688)
- Bltools.exe (PID: 10068)
- Bltools.exe (PID: 10196)
- Bltools.exe (PID: 10332)
- Bltools.exe (PID: 10452)
- Bltools.exe (PID: 10712)
- Bltools.exe (PID: 10844)
- Bltools.exe (PID: 11060)
- Bltools Setup 2.9.1.exe (PID: 12836)
Application launched itself
- msedge.exe (PID: 2600)
- msedge.exe (PID: 672)
Create files in a temporary directory
- Bltools Setup 2.9.1.exe (PID: 5780)
Reads the computer name
- Bltools Setup 2.9.1.exe (PID: 5780)
Creates files or folders in the user directory
- Bltools Setup 2.9.1.exe (PID: 5780)
Reads the software policy settings
- slui.exe (PID: 7476)
Changes the display of characters in the console
- cmd.exe (PID: 2284)
- cmd.exe (PID: 632)
- cmd.exe (PID: 2800)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 5188)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 8432)
- cmd.exe (PID: 9084)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 9780)
- cmd.exe (PID: 9744)
- cmd.exe (PID: 10180)
- cmd.exe (PID: 10248)
- cmd.exe (PID: 10636)
- cmd.exe (PID: 10688)
- cmd.exe (PID: 10868)
- cmd.exe (PID: 11048)
- cmd.exe (PID: 10972)
- cmd.exe (PID: 11564)
- cmd.exe (PID: 11480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
323
Monitored processes
189
Malicious processes
1
Suspicious processes
22
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5540 --field-trial-handle=2372,i,14115629908011894462,13782811789804998621,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 540 | "C:\Users\admin\AppData\Local\Programs\night\Bltools.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\night" --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=1940,i,12367786282445394925,5668778941630753292,262144 --enable-features=PdfUseShowSaveFilePicker --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=1936 /prefetch:2 | C:\Users\admin\AppData\Local\Programs\night\Bltools.exe | — | Bltools.exe | |||||||||||
User: admin Company: Bltools Integrity Level: LOW Description: Bltools Version: 2.9.1 Modules
| |||||||||||||||
| 632 | C:\WINDOWS\system32\cmd.exe /d /s /c "chcp" | C:\Windows\System32\cmd.exe | — | Bltools.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6040 --field-trial-handle=2272,i,14284977319139371282,17022695843129417467,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 872 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5260 --field-trial-handle=2372,i,14115629908011894462,13782811789804998621,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3536 --field-trial-handle=2272,i,14284977319139371282,17022695843129417467,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4200 --field-trial-handle=2372,i,14115629908011894462,13782811789804998621,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4200 --field-trial-handle=2372,i,14115629908011894462,13782811789804998621,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
38 944
Read events
38 881
Write events
50
Delete events
13
Modification events
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9AEF571C8D942F00 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3D74611C8D942F00 | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {36569D57-3291-49DD-BFCE-F93F84108BB7} | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {83841034-C1A9-4A71-AC0A-A1D2CF17DC4A} | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E7D438F5-6DC7-4C43-BF0F-2A521465A3A0} | |||
| (PID) Process: | (2600) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\394026 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FB3B7616-E491-4AE2-B47F-4B44E6B00D1B} | |||
Executable files
46
Suspicious files
421
Text files
338
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF11c9d5.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF11c9e4.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF11ca52.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF11ca61.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF11ca61.TMP | — | |
MD5:— | SHA256:— | |||
| 2600 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
214
DNS requests
130
Threats
24
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7992 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7936 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748299437&P2=404&P3=2&P4=mQViweCrKWjLJ97SAhSBqfFBYwmU3EK68EdChCV1XmgkHqPUVfzIEGvrbkKgRTuacTWdVXwmWQX4QK2uCkYsdw%3d%3d | unknown | — | — | whitelisted |
7992 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7936 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3ab36512-8e78-4855-9d3c-00fc48298f23?P1=1748582684&P2=404&P3=2&P4=OmsTybMpbuABH%2bxxldXBgZvf2W5m0WhLUpV6QikwG61jc93YeTtiodhQJktWemfLUip92kuvonGBBf%2fxdxrWVw%3d%3d | unknown | — | — | whitelisted |
7936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3ab36512-8e78-4855-9d3c-00fc48298f23?P1=1748582684&P2=404&P3=2&P4=OmsTybMpbuABH%2bxxldXBgZvf2W5m0WhLUpV6QikwG61jc93YeTtiodhQJktWemfLUip92kuvonGBBf%2fxdxrWVw%3d%3d | unknown | — | — | whitelisted |
7936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748299437&P2=404&P3=2&P4=mQViweCrKWjLJ97SAhSBqfFBYwmU3EK68EdChCV1XmgkHqPUVfzIEGvrbkKgRTuacTWdVXwmWQX4QK2uCkYsdw%3d%3d | unknown | — | — | whitelisted |
7936 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1748299437&P2=404&P3=2&P4=mQViweCrKWjLJ97SAhSBqfFBYwmU3EK68EdChCV1XmgkHqPUVfzIEGvrbkKgRTuacTWdVXwmWQX4QK2uCkYsdw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7704 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6248 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.36:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2600 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1512 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1512 | msedge.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
github.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
github.githubassets.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
7864 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
6032 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
5164 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
4112 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2980 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
8220 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
8292 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
8292 | Bltools.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |