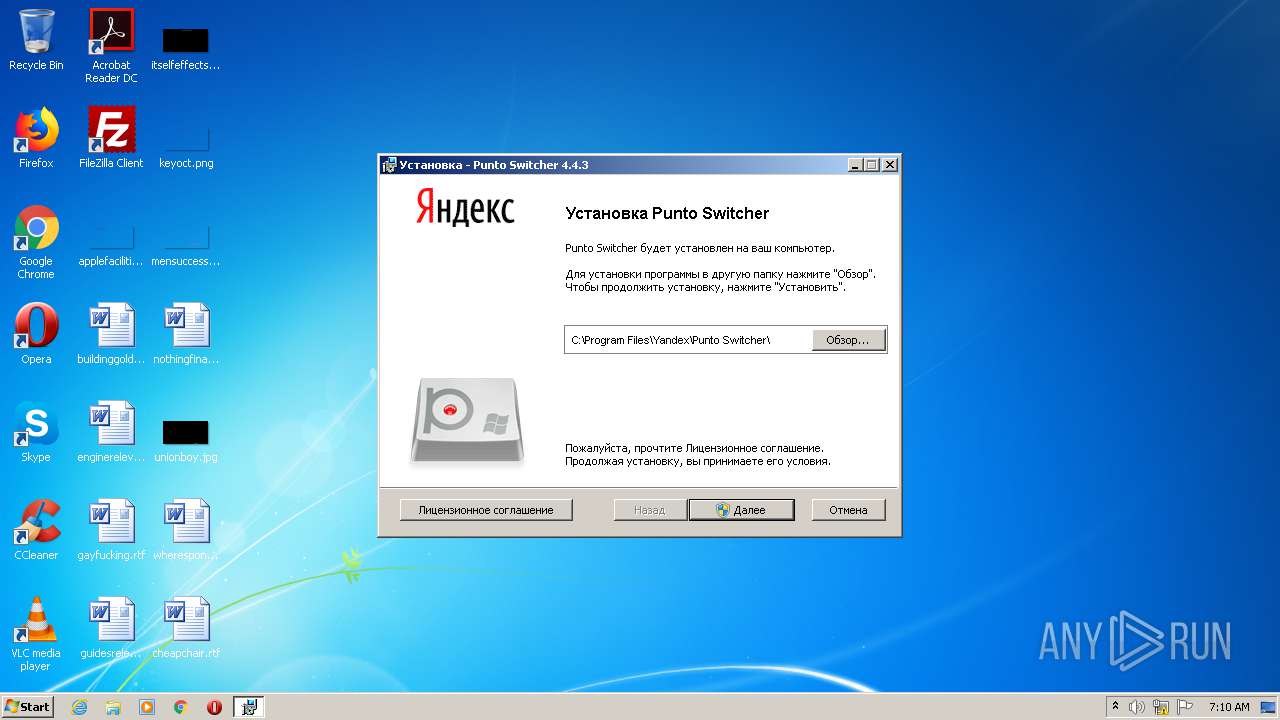
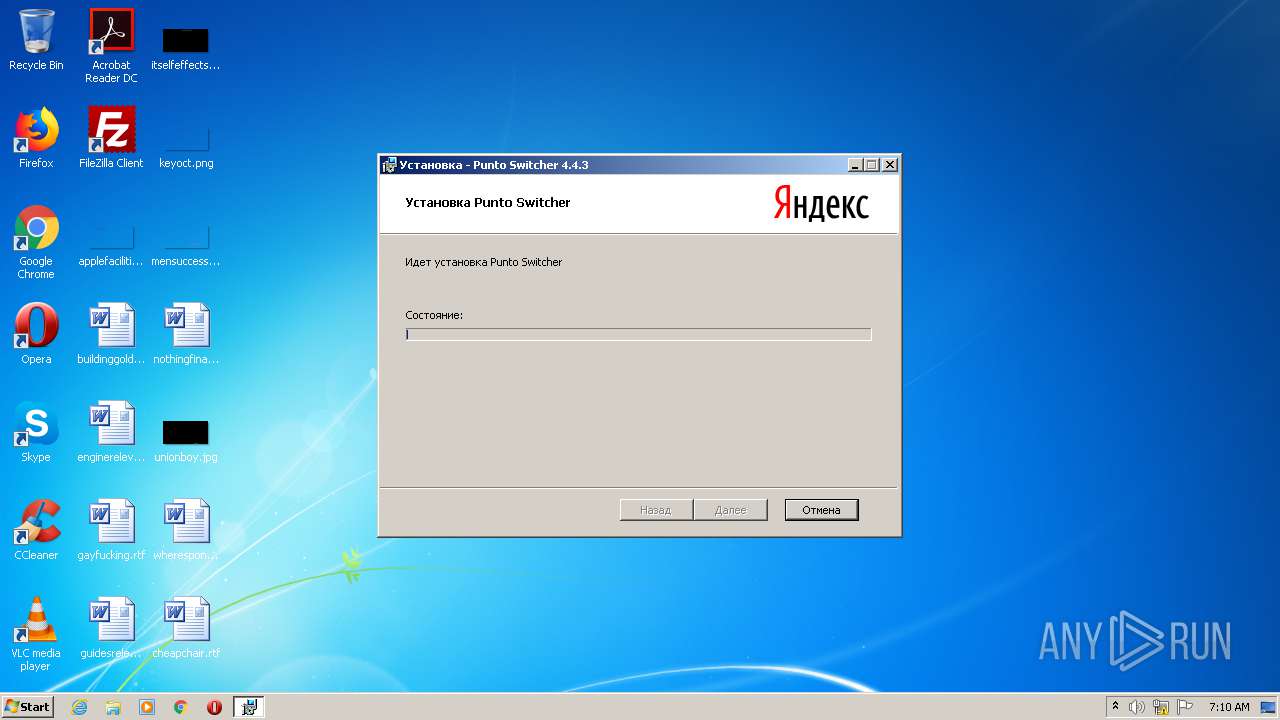
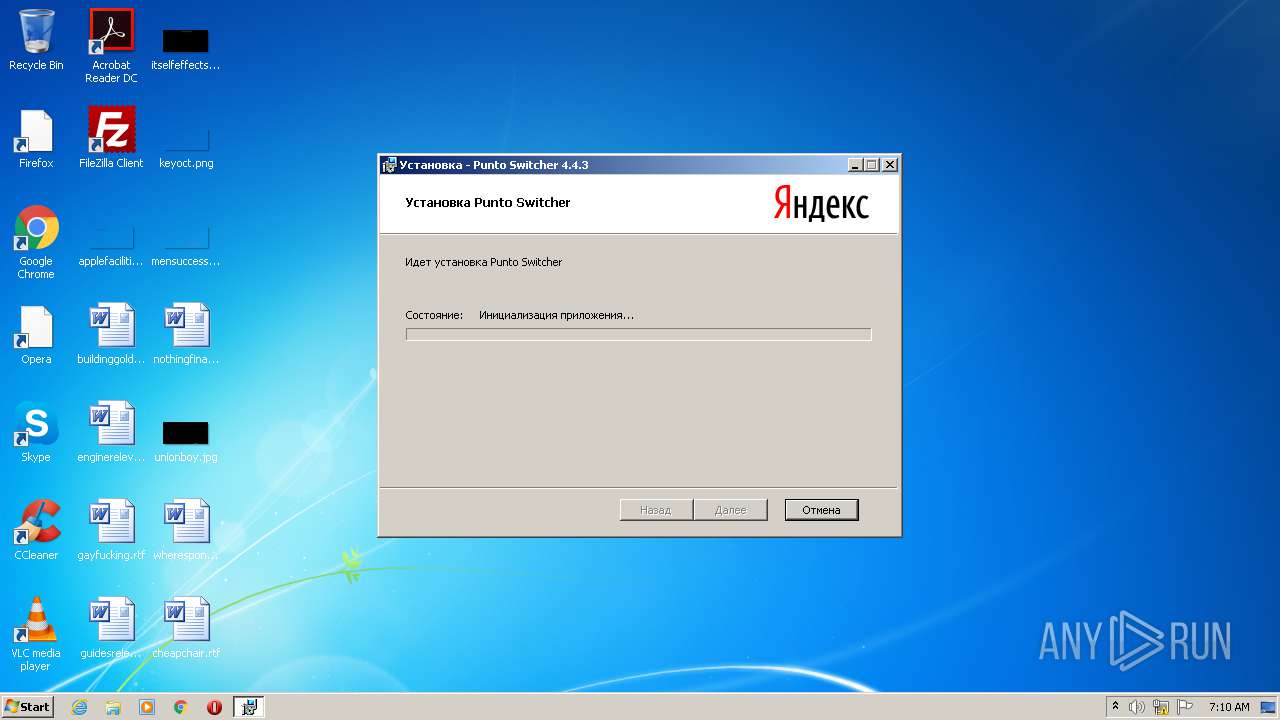
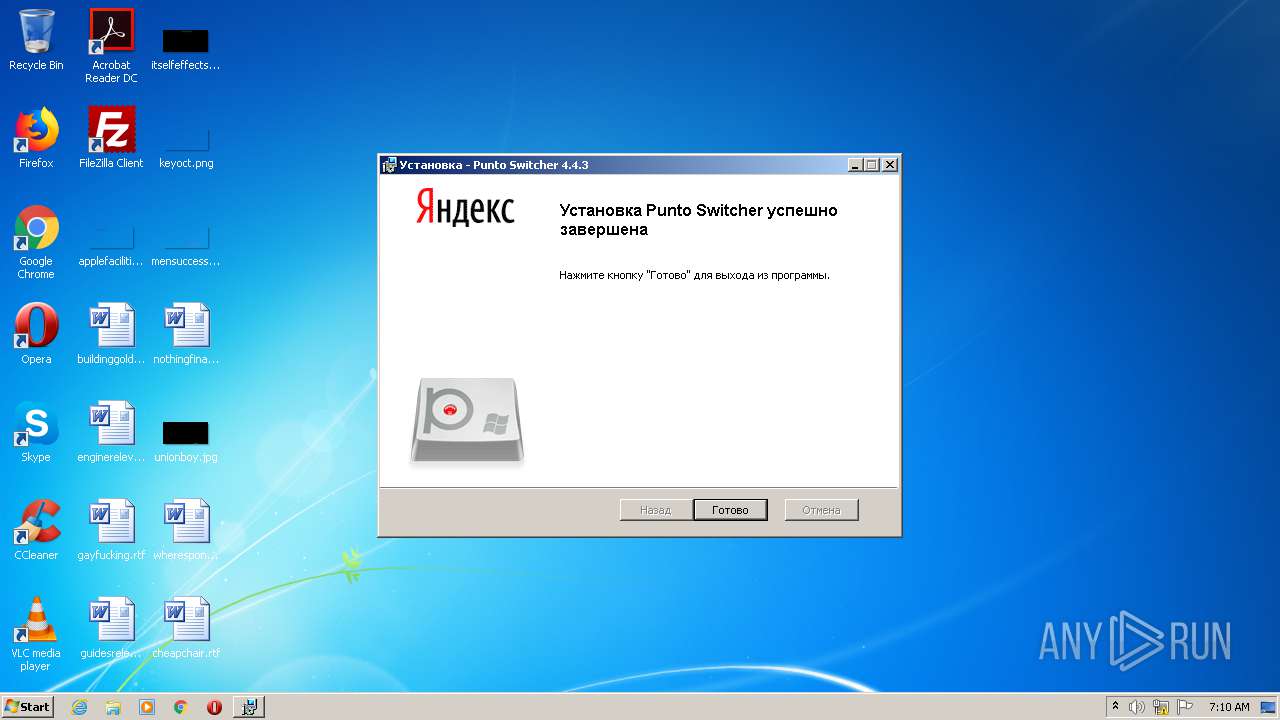
| File name: | PuntoSwitcherSetup.exe |
| Full analysis: | https://app.any.run/tasks/6a6b273c-2e89-4460-94dc-7adcfee182d5 |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 06:09:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 71AD7612ABC0F1D98051BB36FC80D2FE |
| SHA1: | BAD7CB4811DA10B93DF1D7F24923231CA3823964 |
| SHA256: | 48AAD5FA065DD849EDF7B7000EF7D8D99E586EFAA01EA41631409F3AF9CA914E |
| SSDEEP: | 98304:KiRiMN28P5wyIphdTjlEqqsPDZ2upvKSf5vihebRPn:2SOXtJqsPDEu5HKIRPn |
MALICIOUS
Actions looks like stealing of personal data
- punto.exe (PID: 2884)
Application was dropped or rewritten from another process
- punto.exe (PID: 3480)
- punto.exe (PID: 3676)
- yupdate.exe (PID: 2488)
- punto.exe (PID: 2884)
Loads dropped or rewritten executable
- punto.exe (PID: 3480)
- punto.exe (PID: 2884)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 2564)
Creates files in the user directory
- punto.exe (PID: 3676)
- punto.exe (PID: 2884)
- punto.exe (PID: 3480)
Reads the cookies of Google Chrome
- punto.exe (PID: 2884)
Creates files in the program directory
- punto.exe (PID: 2884)
Reads Internet Cache Settings
- IELowutil.exe (PID: 2868)
- punto.exe (PID: 2884)
- punto.exe (PID: 3480)
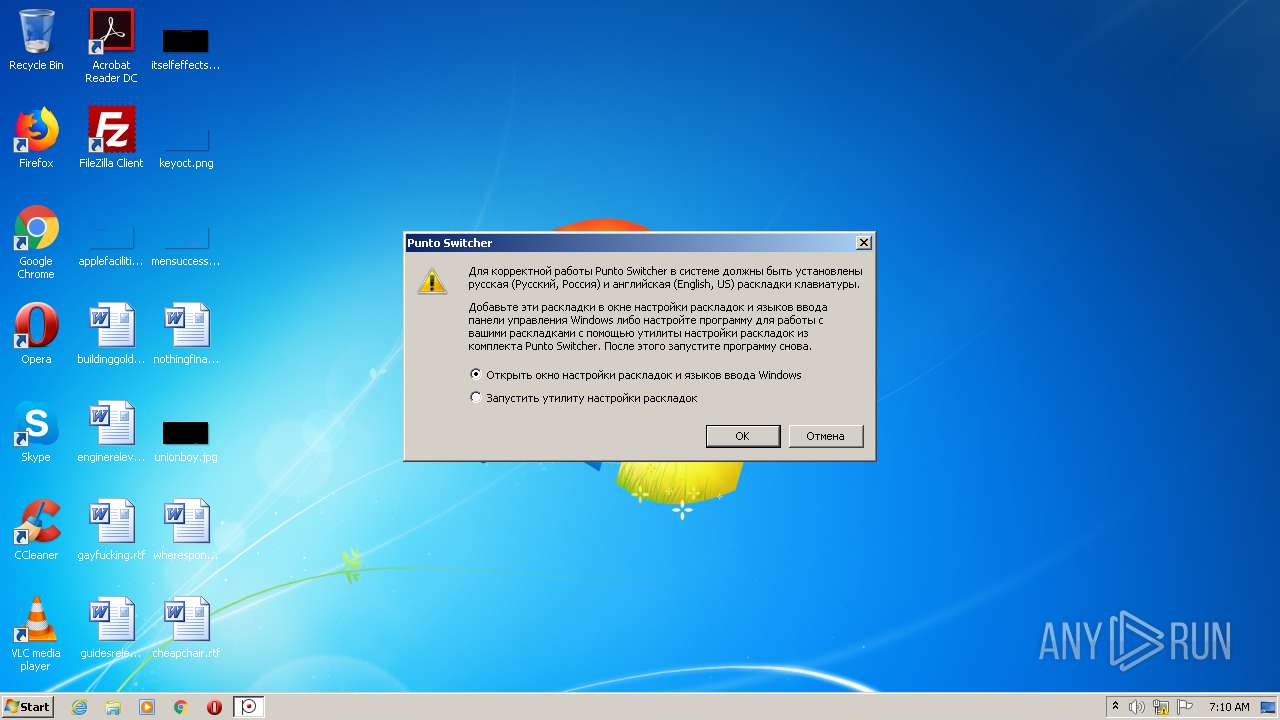
Uses RUNDLL32.EXE to load library
- punto.exe (PID: 3480)
Starts Internet Explorer
- MsiExec.exe (PID: 3500)
Reads the cookies of Mozilla Firefox
- punto.exe (PID: 2884)
INFO
Creates files in the program directory
- msiexec.exe (PID: 2564)
Creates a software uninstall entry
- msiexec.exe (PID: 2564)
Application launched itself
- iexplore.exe (PID: 2944)
- msiexec.exe (PID: 2564)
Changes internet zones settings
- iexplore.exe (PID: 2944)
Reads Internet Cache Settings
- iexplore.exe (PID: 3880)
- iexplore.exe (PID: 2944)
Creates files in the user directory
- iexplore.exe (PID: 3880)
- iexplore.exe (PID: 2944)
Reads internet explorer settings
- iexplore.exe (PID: 3880)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2944)
Reads settings of System Certificates
- iexplore.exe (PID: 2944)
Changes settings of System certificates
- iexplore.exe (PID: 2944)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:04 13:09:43+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 71680 |
| InitializedDataSize: | 4846592 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3894 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.3.407 |
| ProductVersionNumber: | 4.4.3.407 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Software Installer |
| FileVersion: | 4, 4, 3, 407 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFileName: | setup.exe |
| ProductName: | Windows Installer XML |
| ProductVersion: | 4, 4, 3, 407 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jul-2018 11:09:43 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Software Installer |
| FileVersion: | 4, 4, 3, 407 |
| InternalName: | setup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFilename: | setup.exe |
| ProductName: | Windows Installer XML |
| ProductVersion: | 4, 4, 3, 407 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 04-Jul-2018 11:09:43 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000116BB | 0x00011800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62394 |
.rdata | 0x00013000 | 0x00006A72 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.20662 |
.data | 0x0001A000 | 0x000012A0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.01832 |
.gfids | 0x0001C000 | 0x000000AC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.44973 |
.rsrc | 0x0001D000 | 0x00497CB4 | 0x00497E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.31785 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.31079 | 1242 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.81426 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.0302 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.44974 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 3.25417 | 528 | Latin 1 / Western European | English - United States | RT_DIALOG |
102 | 2.62308 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
126 | 3.16391 | 2004 | Latin 1 / Western European | English - United States | RT_STRING |
3188 | 1.18832 | 46 | Latin 1 / Western European | English - United States | RT_STRING |
51003 | 0.197212 | 52232 | Latin 1 / Western European | English - United States | RT_BITMAP |
MANIFEST | 2.1686 | 172 | Latin 1 / Western European | English - United States | RT_RCDATA |
Imports
COMCTL32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msi.dll |
ole32.dll |
Total processes
49
Monitored processes
12
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
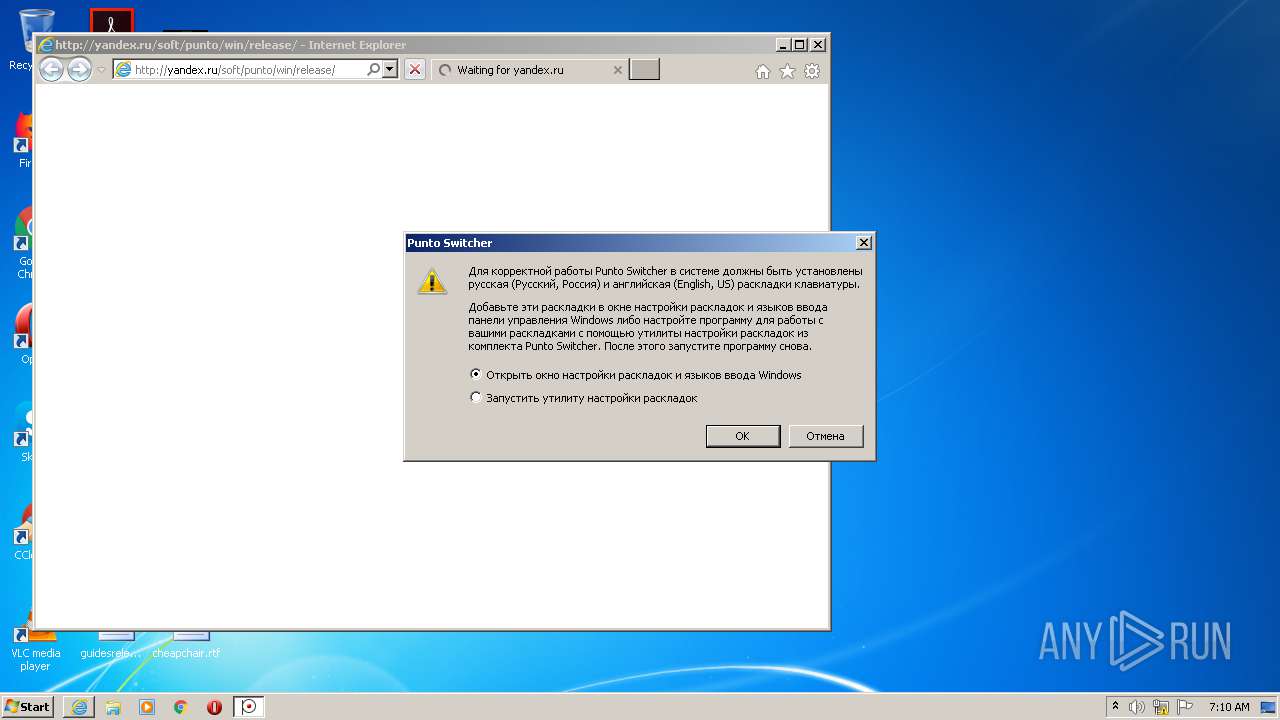
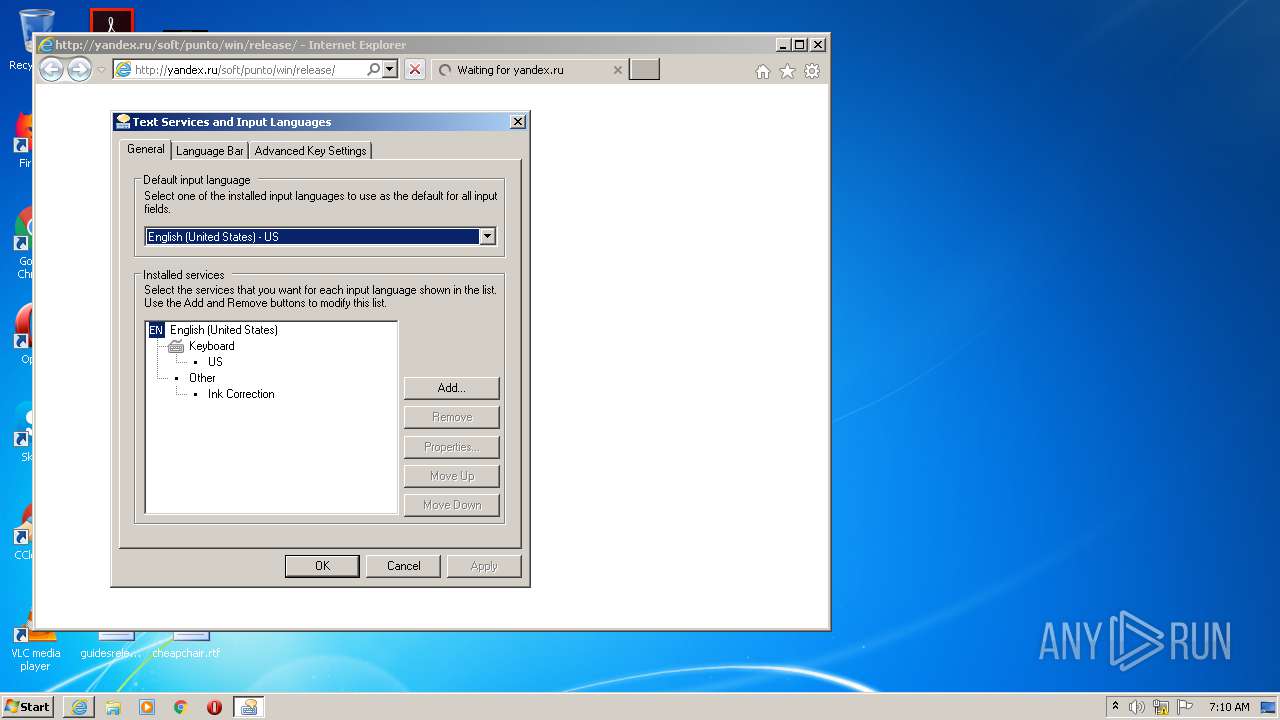
| 1936 | RunDll32.exe shell32.dll,Control_RunDLL input.dll | C:\Windows\system32\RunDll32.exe | — | punto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\AppData\Local\Temp\PuntoSwitcherSetup.exe" | C:\Users\admin\AppData\Local\Temp\PuntoSwitcherSetup.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Software Installer Exit code: 0 Version: 4, 4, 3, 407 Modules
| |||||||||||||||
| 2488 | C:\Program Files\Yandex\Punto Switcher\Updater\yupdate.exe --stat-callback 0 --appid punto --job {279285C1-042D-4DD2-8DDC-43850F19BE30} | C:\Program Files\Yandex\Punto Switcher\Updater\yupdate.exe | — | svchost.exe | |||||||||||
User: admin Company: Yandex LLC Integrity Level: MEDIUM Description: Yandex updater (EU) Exit code: 0 Version: 1.2.0.1831 Modules
| |||||||||||||||
| 2564 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Internet Explorer\IELowutil.exe" -PID:123 | C:\Program Files\Internet Explorer\IELowutil.exe | — | punto.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Low-Mic Utility Tool Exit code: 2147942487 Version: 11.00.9600.17840 (winblue_r11.150522-0826) Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Yandex\Punto Switcher\punto.exe" -Install | C:\Program Files\Yandex\Punto Switcher\punto.exe | MsiExec.exe | ||||||||||||
User: admin Company: ООО Яндекс Integrity Level: MEDIUM Description: Punto Switcher Exit code: 0 Version: 4, 4, 3, 407 Modules
| |||||||||||||||
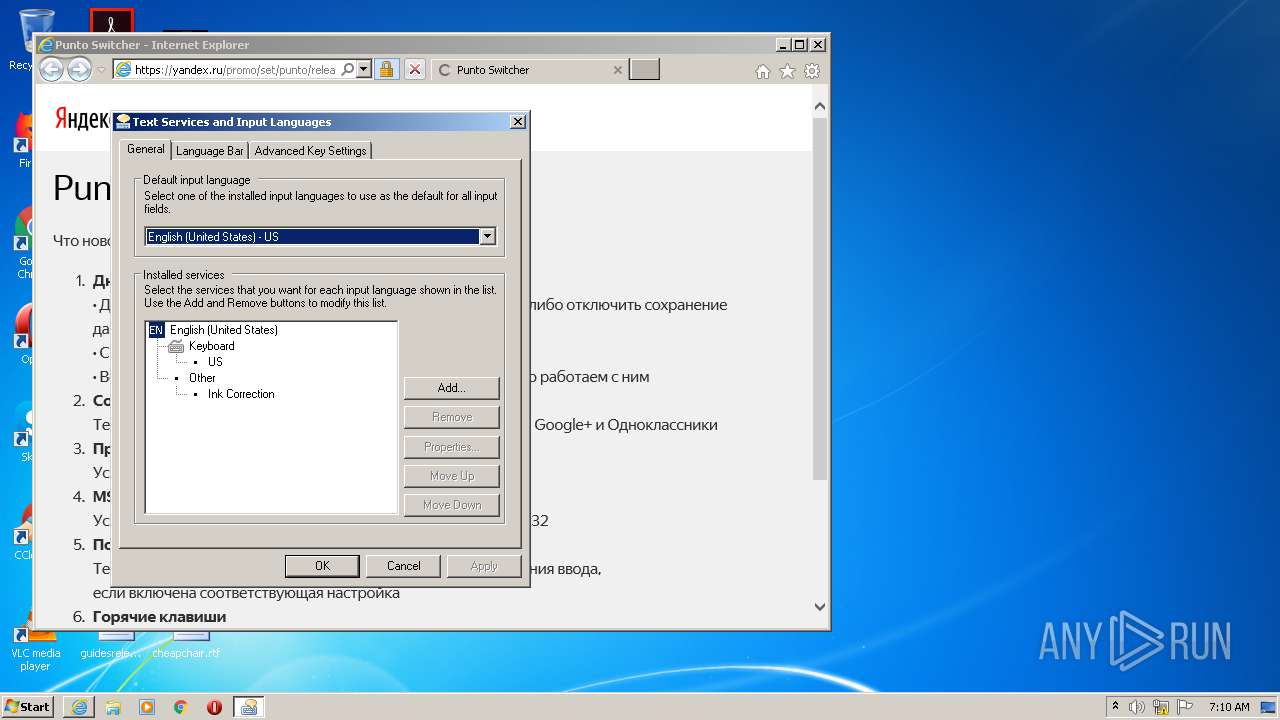
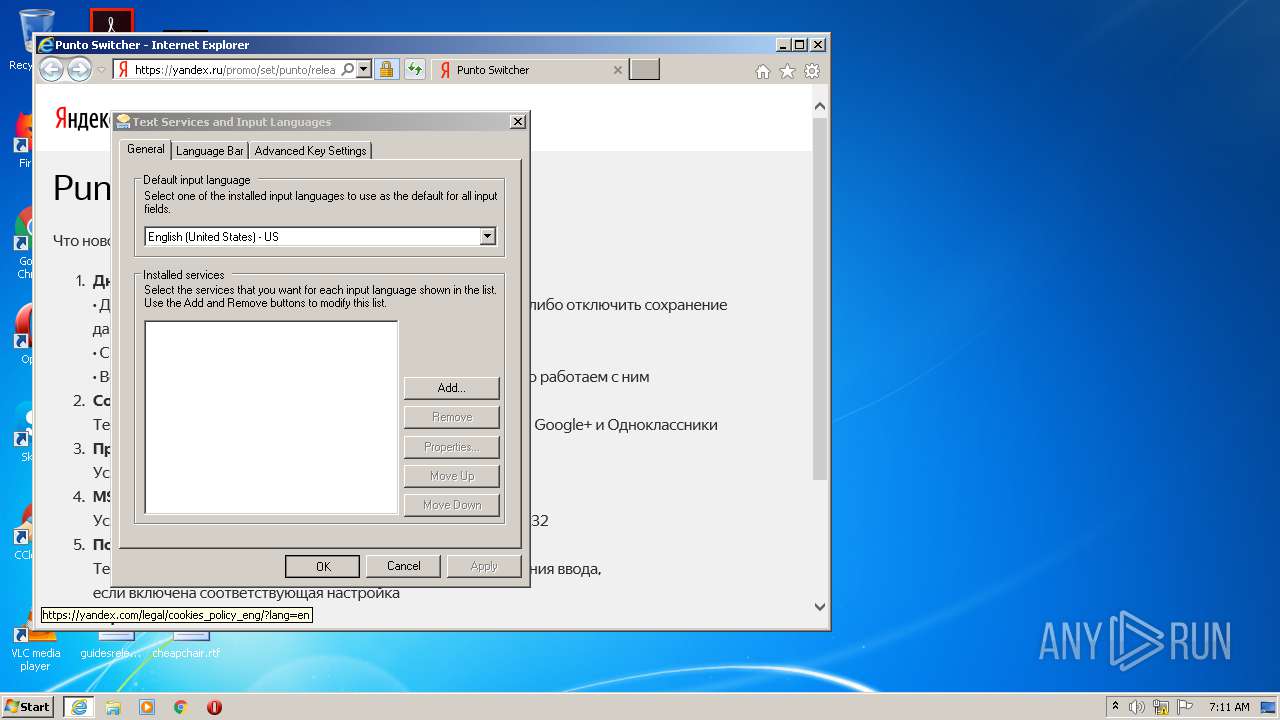
| 2944 | "C:\Program Files\Internet Explorer\iexplore.exe" http://yandex.ru/soft/punto/win/release/ | C:\Program Files\Internet Explorer\iexplore.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3480 | "C:\Program Files\Yandex\Punto Switcher\punto.exe" | C:\Program Files\Yandex\Punto Switcher\punto.exe | PuntoSwitcherSetup.exe | ||||||||||||
User: admin Company: ООО Яндекс Integrity Level: MEDIUM Description: Punto Switcher Exit code: 0 Version: 4, 4, 3, 407 Modules
| |||||||||||||||
| 3500 | C:\Windows\system32\MsiExec.exe -Embedding DF6EF129183C43995285B5C7A40354B6 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3676 | "C:\Program Files\Yandex\Punto Switcher\punto.exe" /import_old_settings | C:\Program Files\Yandex\Punto Switcher\punto.exe | — | msiexec.exe | |||||||||||
User: admin Company: ООО Яндекс Integrity Level: MEDIUM Description: Punto Switcher Exit code: 0 Version: 4, 4, 3, 407 Modules
| |||||||||||||||
Total events
1 984
Read events
1 095
Write events
855
Delete events
34
Modification events
| (PID) Process: | (2460) PuntoSwitcherSetup.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000_CLASSES\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | (default) |
Value: C:\Windows\Installer\2d5579.ipi | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\2d557a.rbs |
Value: 30844592 | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\2d557a.rbsLow |
Value: 156926768 | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\FD1B745C1C44675498CA5319E50C0BC6 |
| Operation: | write | Name: | 5E1BCACE623D49F48A3AC235D35DCF05 |
Value: C:\Program Files\Yandex\Punto Switcher\Sounds\switch.wav | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\6F7907EBFB0627C4988652E0A3F37F47 |
| Operation: | write | Name: | 5E1BCACE623D49F48A3AC235D35DCF05 |
Value: C:\Program Files\Yandex\Punto Switcher\Sounds\typerus.wav | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\2C6EBDADB44577548B55E175A85296B5 |
| Operation: | write | Name: | 5E1BCACE623D49F48A3AC235D35DCF05 |
Value: C:\Program Files\Yandex\Punto Switcher\Sounds\typeeng.wav | |||
| (PID) Process: | (2564) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\28B47E67E2E0C5E43BCFB3C12312047F |
| Operation: | write | Name: | 5E1BCACE623D49F48A3AC235D35DCF05 |
Value: C:\Program Files\Yandex\Punto Switcher\Sounds\reverse.wav | |||
Executable files
14
Suspicious files
38
Text files
185
Unknown types
39
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2460 | PuntoSwitcherSetup.exe | C:\Users\admin\AppData\Local\Temp\{ECACB1E5-D326-4F94-A8A3-2C533DD5FC50}\PuntoSwitcher.msi | — | |
MD5:— | SHA256:— | |||
| 2564 | msiexec.exe | C:\Windows\Installer\2d5578.msi | — | |
MD5:— | SHA256:— | |||
| 2564 | msiexec.exe | C:\Windows\Installer\MSI57E9.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFFC8351152F8A1B58.TMP | — | |
MD5:— | SHA256:— | |||
| 2564 | msiexec.exe | C:\Windows\Installer\MSI5952.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | msiexec.exe | C:\Program Files\Yandex\Punto Switcher\layouts.exe | executable | |
MD5:— | SHA256:— | |||
| 2564 | msiexec.exe | C:\Program Files\Yandex\Punto Switcher\Images\_punto.css | text | |
MD5:8D59B2A38A6B4DCD9848EE94239B3A0B | SHA256:EE3BC3C864EB85C0D1C61C2544D31FCF0DFB1B214FB62C7F4920468C09575683 | |||
| 2564 | msiexec.exe | C:\Program Files\Yandex\Punto Switcher\Sounds\en.wav | wav | |
MD5:8D4557ABF765D64A334C99100320D61E | SHA256:AA3CFFBB2FA43D00A3EE3570C4B6B94C23DCB0A80EEAE083F2A47B10F444D52A | |||
| 2564 | msiexec.exe | C:\Program Files\Yandex\Punto Switcher\Images\feature.png | image | |
MD5:83A6A647ABE9113AC6767310D2621A30 | SHA256:787B88AC9F9CDA08C2BCEB1997CED66F98FA43CD392B948C955E45DE92379D2D | |||
| 2564 | msiexec.exe | C:\Program Files\Yandex\Punto Switcher\Updater\clids-punto.xml | xml | |
MD5:889729635D1B740CE54267EA6735D995 | SHA256:4C2231403032C7BF876BA1CCB653652639FAE4566DD598AC8B867A5B38F6E376 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
39
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3880 | iexplore.exe | GET | 302 | 77.88.55.55:80 | http://yandex.ru/soft/punto/win/release/ | RU | — | — | whitelisted |
3880 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECp5lw5VJUdi1sZ3IDVGUzE%3D | RU | der | 1.48 Kb | whitelisted |
3880 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEC6Tkdyfl26sf%2Br5Aa05wdc%3D | RU | der | 1.48 Kb | whitelisted |
3880 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECp5lw5VJUdi1sZ3IDVGUzE%3D | RU | der | 1.48 Kb | whitelisted |
3880 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECp5lw5VJUdi1sZ3IDVGUzE%3D | RU | der | 1.48 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3880 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEDa8vXdAngh37rPnjRFyHyk%3D | RU | der | 1.48 Kb | whitelisted |
3880 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEDa8vXdAngh37rPnjRFyHyk%3D | RU | der | 1.48 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2944 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 87.250.250.33:80 | soft.export.yandex.ru | YANDEX LLC | RU | whitelisted |
3880 | iexplore.exe | 5.45.205.244:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
3480 | punto.exe | 77.88.55.55:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
3880 | iexplore.exe | 77.88.55.55:443 | yandex.ru | YANDEX LLC | RU | whitelisted |
3880 | iexplore.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
2944 | iexplore.exe | 178.154.131.217:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2944 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2944 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3880 | iexplore.exe | 178.154.131.217:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
soft.export.yandex.ru |
| whitelisted |
yandex.ru |
| whitelisted |
subca.ocsp-certum.com |
| whitelisted |
yandex.ocsp-responder.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
yastatic.net |
| whitelisted |
mc.yandex.ru |
| whitelisted |
mc.admetrica.ru |
| unknown |
iecvlist.microsoft.com |
| whitelisted |