| File name: | poop.exe |
| Full analysis: | https://app.any.run/tasks/f1296825-5ac5-4c4d-b05d-423cc0b1e3d9 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2022, 05:11:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 449284C11F38566EAE371DCD6F940D9D |
| SHA1: | CCAE577178DCC0C67C07E9DC7D07CA3A33EC0938 |
| SHA256: | 4885F16916A8E027749C62B1402269274A6EA2320FA20C4080292BF9115244FE |
| SSDEEP: | 49152:RJZoQrbTFZY1iaRwQSNQgTM4Ll9GusyH1UFNZH0jK/Tgb2mwASJI1flUiBoC:RtrbTA19Nh45o7oO0WU2ISKXUGoC |
MALICIOUS
Writes to a start menu file
- poop.exe (PID: 3840)
Drops executable file immediately after starts
- poop.exe (PID: 3840)
Changes the autorun value in the registry
- poop.exe (PID: 3840)
SUSPICIOUS
Reads mouse settings
- poop.exe (PID: 3840)
Checks supported languages
- poop.exe (PID: 3840)
- WSCript.exe (PID: 548)
Reads the computer name
- poop.exe (PID: 3840)
- WSCript.exe (PID: 548)
Executes scripts
- poop.exe (PID: 3840)
Executable content was dropped or overwritten
- poop.exe (PID: 3840)
Creates files in the user directory
- poop.exe (PID: 3840)
INFO
Reads settings of System Certificates
- poop.exe (PID: 3840)
Checks Windows Trust Settings
- WSCript.exe (PID: 548)
- poop.exe (PID: 3840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
|---|---|
| FileVersion: | 3, 3, 8, 1 |
| FileDescription: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (British) |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0017 |
| ProductVersionNumber: | 3.3.8.1 |
| FileVersionNumber: | 3.3.8.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x165c1 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 121856 |
| CodeSize: | 526336 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2012:01:29 22:32:28+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2012 21:32:28 |
| Detected languages: |
|
| FileDescription: | - |
| FileVersion: | 3, 3, 8, 1 |
| CompiledScript: | AutoIt v3 Script: 3, 3, 8, 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 29-Jan-2012 21:32:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008061C | 0x00080800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.68469 |
.rdata | 0x00082000 | 0x0000DFC0 | 0x0000E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.79974 |
.data | 0x00090000 | 0x0001A758 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.15007 |
.rsrc | 0x000AB000 | 0x0002ECB8 | 0x0002EE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.40824 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.01246 | 620 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.66371 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 2.25499 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
4 | 6.42503 | 179560 | UNKNOWN | English - United Kingdom | RT_ICON |
7 | 3.31436 | 1328 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 3.28624 | 1680 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 3.2836 | 1232 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 3.28373 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 3.26322 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 3.23004 | 904 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
USER32.dll |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 548 | WSCript C:\Users\admin\AppData\Local\Temp\XICIAF.vbs | C:\Windows\system32\WSCript.exe | — | poop.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
| 3840 | "C:\Users\admin\Desktop\poop.exe" | C:\Users\admin\Desktop\poop.exe | Explorer.EXE | |
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 3, 3, 8, 1 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
4
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3840 | poop.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\XICIAF.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\Roaming\Windata\QGQIYZ.exe | executable | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\Local\Temp\autC9FF.tmp | binary | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\Local\Temp\XICIAF.vbs | text | |
MD5:— | SHA256:— | |||
| 3840 | poop.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
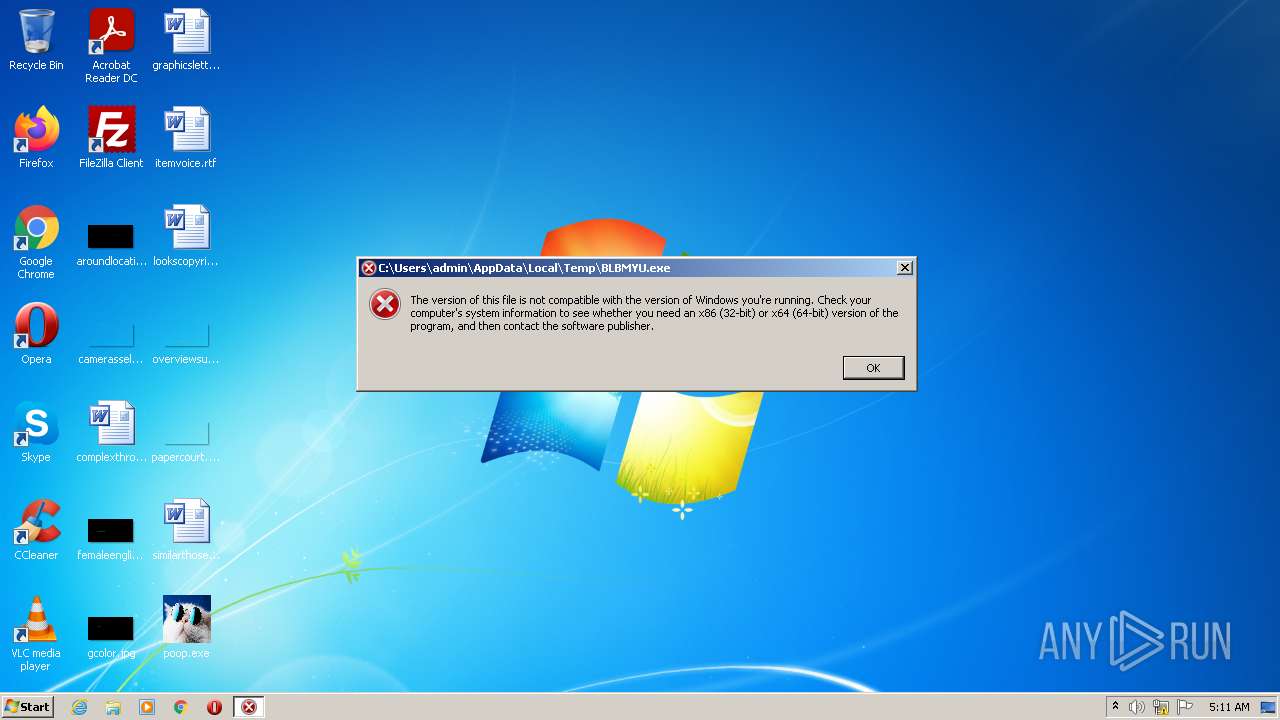
| 3840 | poop.exe | C:\Users\admin\AppData\Local\Temp\BLBMYU.exe | executable | |
MD5:AF8C141295DB3DA0FDC2365AAA38817C | SHA256:A62359915F91750FF1A53395F5B5FBAE828AE4CFD6011599ACA32C82ECE3D818 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3840 | poop.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3840 | poop.exe | GET | 200 | 8.248.143.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?627282dbb34b1153 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3840 | poop.exe | 104.26.8.44:443 | ipapi.co | Cloudflare Inc | US | malicious |
3840 | poop.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3840 | poop.exe | 8.248.143.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipapi.co |
| shared |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |