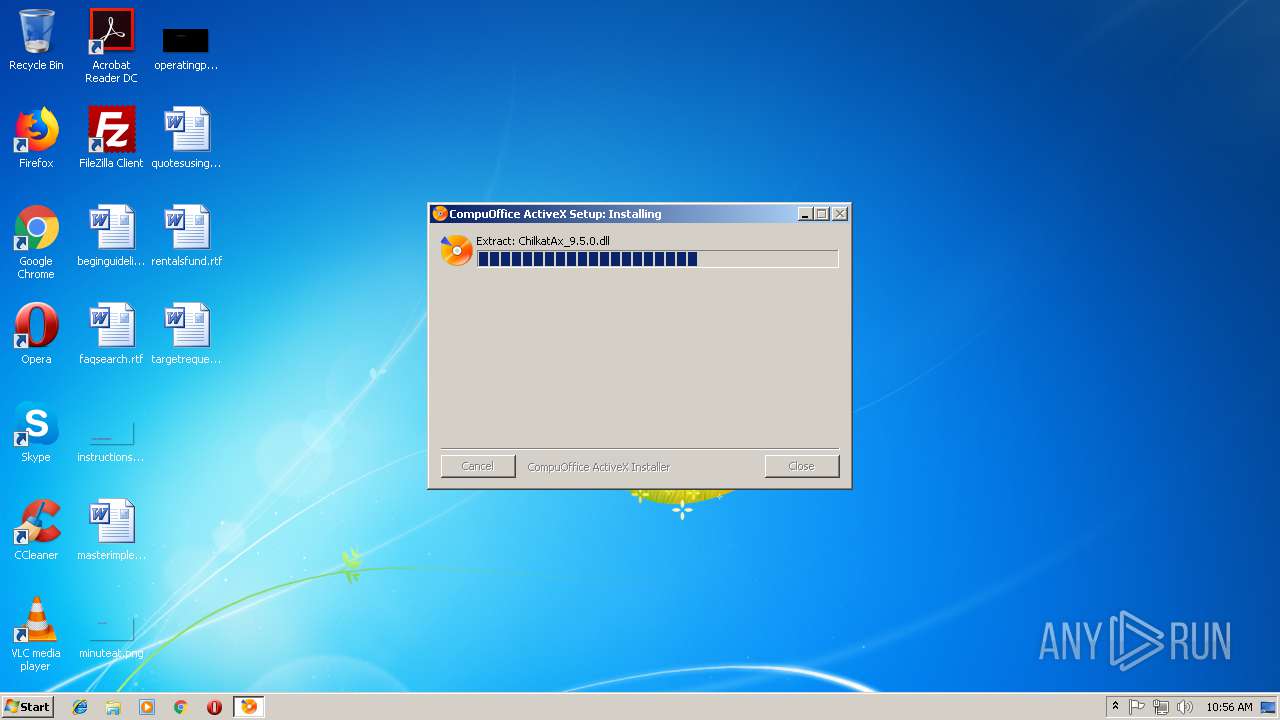
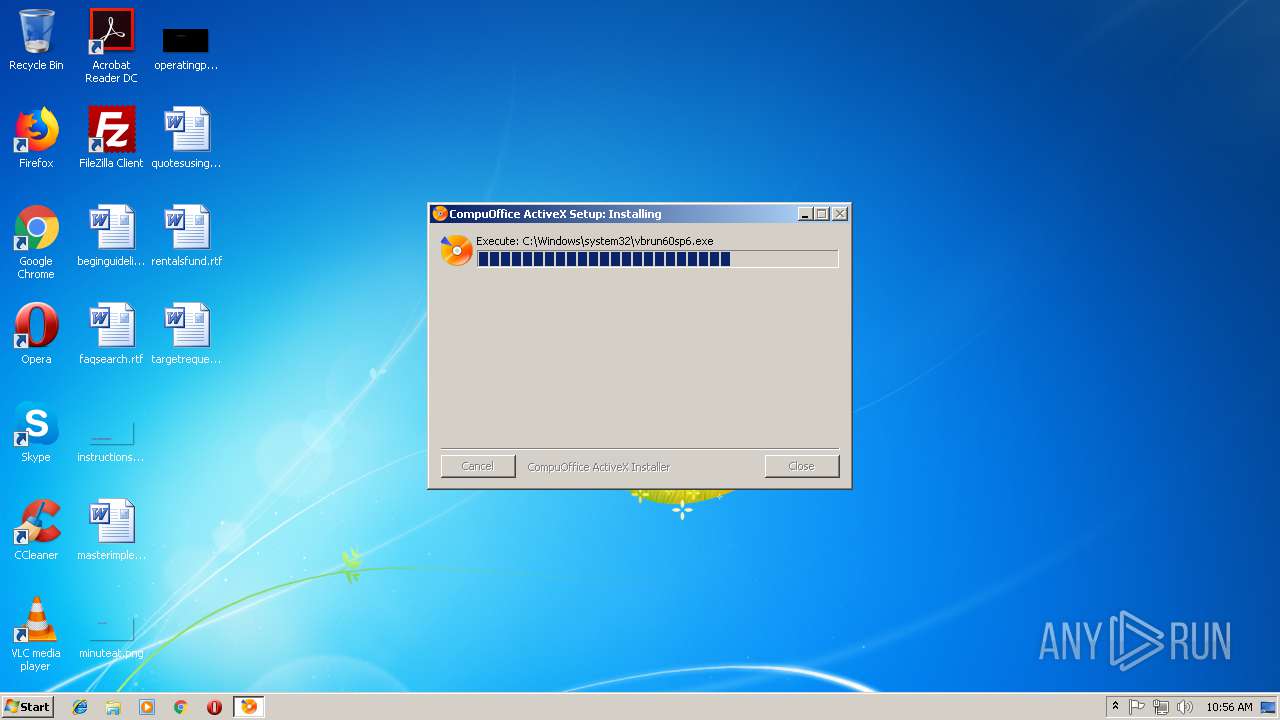
| File name: | compuoffice Activex setup.exe |
| Full analysis: | https://app.any.run/tasks/7fb81b80-2c55-46e7-862b-d88574941798 |
| Verdict: | Malicious activity |
| Analysis date: | September 27, 2018, 09:56:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E1465DE0E4FA1E1E26CB6C5F1B14DB8A |
| SHA1: | 844DCA31D3FCAE6C92984B0A3F94488DA0C761A1 |
| SHA256: | 487296A4641FE113FDC61EB8FC78D3BB0DACAB12BFE52BA735D9813DAD63CFE2 |
| SSDEEP: | 98304:ZVHNG49+ildDjkoWZthyQ1GOtL9EprIK52/ffDaGBNQr0:PN2od3vWZyCtLG2/ffG8A0 |
MALICIOUS
Loads dropped or rewritten executable
- compuoffice Activex setup.exe (PID: 3180)
- regsvr32.exe (PID: 4092)
- regsvr32.exe (PID: 600)
- regsvr32.exe (PID: 2920)
- regsvr32.exe (PID: 1220)
- regsvr32.exe (PID: 3688)
- regsvr32.exe (PID: 384)
- regsvr32.exe (PID: 3984)
- regsvr32.exe (PID: 120)
- vbrun60sp6.exe (PID: 3120)
Registers / Runs the DLL via REGSVR32.EXE
- compuoffice Activex setup.exe (PID: 3180)
Application was dropped or rewritten from another process
- vbrun60sp6.exe (PID: 3120)
SUSPICIOUS
Executable content was dropped or overwritten
- compuoffice Activex setup.exe (PID: 3180)
- vbrun60sp6.exe (PID: 3120)
Removes files from Windows directory
- vbrun60sp6.exe (PID: 3120)
Creates files in the Windows directory
- compuoffice Activex setup.exe (PID: 3180)
- vbrun60sp6.exe (PID: 3120)
Creates COM task schedule object
- regsvr32.exe (PID: 600)
- regsvr32.exe (PID: 384)
- regsvr32.exe (PID: 120)
- regsvr32.exe (PID: 1220)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (91.9) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.3) |
| .exe | | | Win64 Executable (generic) (3) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2008:12:20 13:41:03+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3233 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 35.0.0.0 |
| ProductVersionNumber: | 35.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Professional Softec Pvt. Ltd. |
| FileVersion: | 35 |
| ProductName: | CompuOffice Online |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Dec-2008 12:41:03 |
| Detected languages: |
|
| CompanyName: | Professional Softec Pvt. Ltd. |
| FileVersion: | 35 |
| ProductName: | CompuOffice Online |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 20-Dec-2008 12:41:03 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A4A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41647 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17797 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70964 |
.ndata | 0x00024000 | 0x00008000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002C000 | 0x000060B8 | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.90995 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.98968 | 502 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.70235 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.4525 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.96136 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.43066 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 5.561 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.69913 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
48
Monitored processes
12
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | C:\Windows\system32\regsvr32 C:\Windows\system32\ChilkatAx_9.5.0.dll /s | C:\Windows\system32\regsvr32.exe | — | compuoffice Activex setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 384 | C:\Windows\system32\regsvr32 C:\Windows\system32\vbMHWB.dll /s | C:\Windows\system32\regsvr32.exe | — | compuoffice Activex setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 600 | C:\Windows\system32\regsvr32 C:\Windows\system32\ChilkatUpload.dll /s | C:\Windows\system32\regsvr32.exe | — | compuoffice Activex setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1220 | C:\Windows\system32\regsvr32 C:\Windows\system32\capicom.dll /s | C:\Windows\system32\regsvr32.exe | — | compuoffice Activex setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1716 | grpconv.exe -o | C:\Windows\system32\grpconv.exe | — | vbrun60sp6.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Progman Group Converter Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2920 | C:\Windows\system32\regsvr32 C:\Windows\system32\CompuOffice.ocx /s | C:\Windows\system32\regsvr32.exe | — | compuoffice Activex setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3120 | C:\Windows\system32\vbrun60sp6.exe | C:\Windows\system32\vbrun60sp6.exe | compuoffice Activex setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Win32 Cabinet Self-Extractor Exit code: 0 Version: 4.71.1015.0 Modules
| |||||||||||||||
| 3180 | "C:\Users\admin\AppData\Local\Temp\compuoffice Activex setup.exe" | C:\Users\admin\AppData\Local\Temp\compuoffice Activex setup.exe | explorer.exe | ||||||||||||
User: admin Company: Professional Softec Pvt. Ltd. Integrity Level: HIGH Exit code: 0 Version: 35 Modules
| |||||||||||||||
| 3688 | C:\Windows\system32\regsvr32 C:\Windows\system32\MSWINSCK.OCX /s | C:\Windows\system32\regsvr32.exe | — | compuoffice Activex setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3840 | "C:\Users\admin\AppData\Local\Temp\compuoffice Activex setup.exe" | C:\Users\admin\AppData\Local\Temp\compuoffice Activex setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Professional Softec Pvt. Ltd. Integrity Level: MEDIUM Exit code: 3221226540 Version: 35 Modules
| |||||||||||||||
Total events
2 466
Read events
327
Write events
2 137
Delete events
2
Modification events
| (PID) Process: | (3120) vbrun60sp6.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57} |
| Operation: | write | Name: | |
Value: DSO Framer Control Object | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\dsoframer.ocx | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\ProgID |
| Operation: | write | Name: | |
Value: DSOFramer.FramerControl | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\ToolboxBitmap32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\dsoframer.ocx,102 | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\TypeLib |
| Operation: | write | Name: | |
Value: {00460180-9E5E-11d5-B7C8-B8269041DD57} | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\Version |
| Operation: | write | Name: | |
Value: 1.3 | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\MiscStatus |
| Operation: | write | Name: | |
Value: 131473 | |||
| (PID) Process: | (4092) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{00460182-9E5E-11d5-B7C8-B8269041DD57}\DataFormats\GetSet\0 |
| Operation: | write | Name: | |
Value: 3,1,32,1 | |||
Executable files
21
Suspicious files
0
Text files
35
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3180 | compuoffice Activex setup.exe | C:\Windows\system32\Scanner.ocx | executable | |
MD5:— | SHA256:— | |||
| 3180 | compuoffice Activex setup.exe | C:\Windows\system32\CompuOffice.ocx | executable | |
MD5:— | SHA256:— | |||
| 3180 | compuoffice Activex setup.exe | C:\Windows\system32\vbMHWB.dll | executable | |
MD5:— | SHA256:— | |||
| 3180 | compuoffice Activex setup.exe | C:\Users\admin\AppData\Local\Temp\nsvCD3.tmp\UAC.dll | executable | |
MD5:09CAF01BC8D88EEB733ABC161ACFF659 | SHA256:3555AFE95E8BB269240A21520361677B280562B802978FCCFB27490C79B9A478 | |||
| 3120 | vbrun60sp6.exe | C:\Windows\Temp\OLD1126.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | vbrun60sp6.exe | C:\Windows\system32\SET1126.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | vbrun60sp6.exe | C:\Windows\Temp\OLD1146.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | vbrun60sp6.exe | C:\Windows\system32\SET1146.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | vbrun60sp6.exe | C:\Windows\Temp\OLD1157.tmp | — | |
MD5:— | SHA256:— | |||
| 3120 | vbrun60sp6.exe | C:\Windows\system32\SET1166.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report