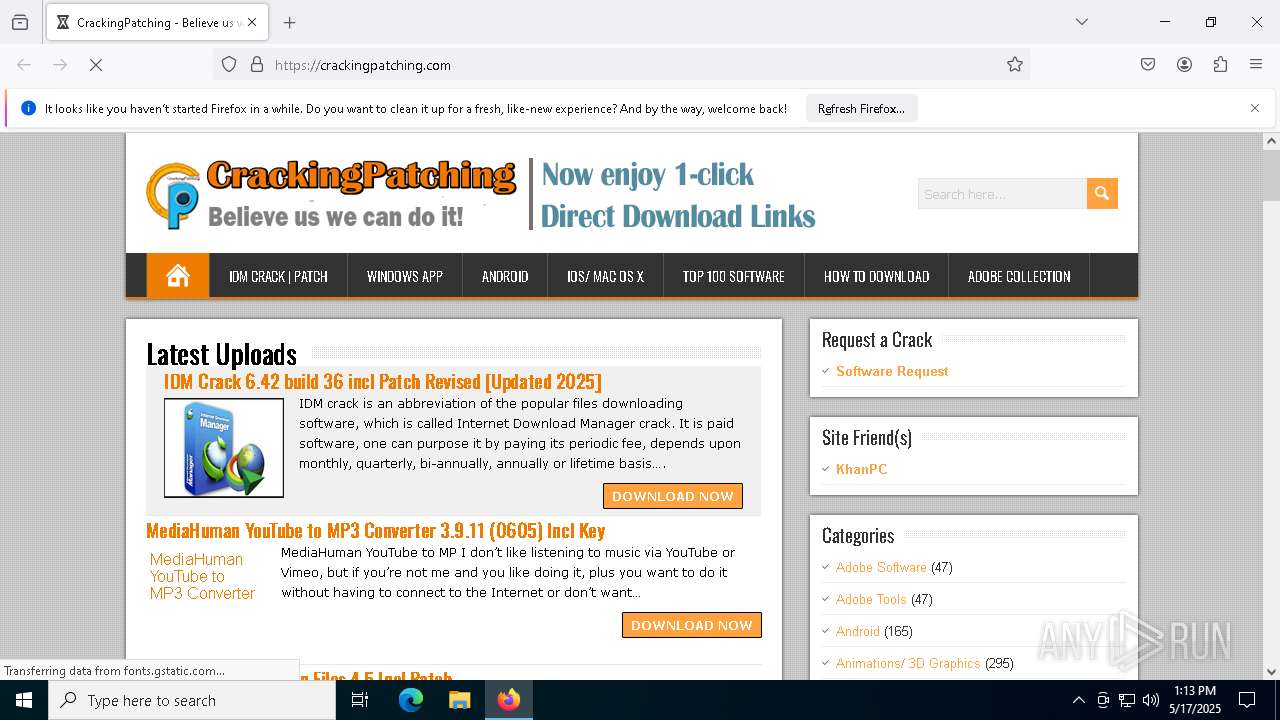
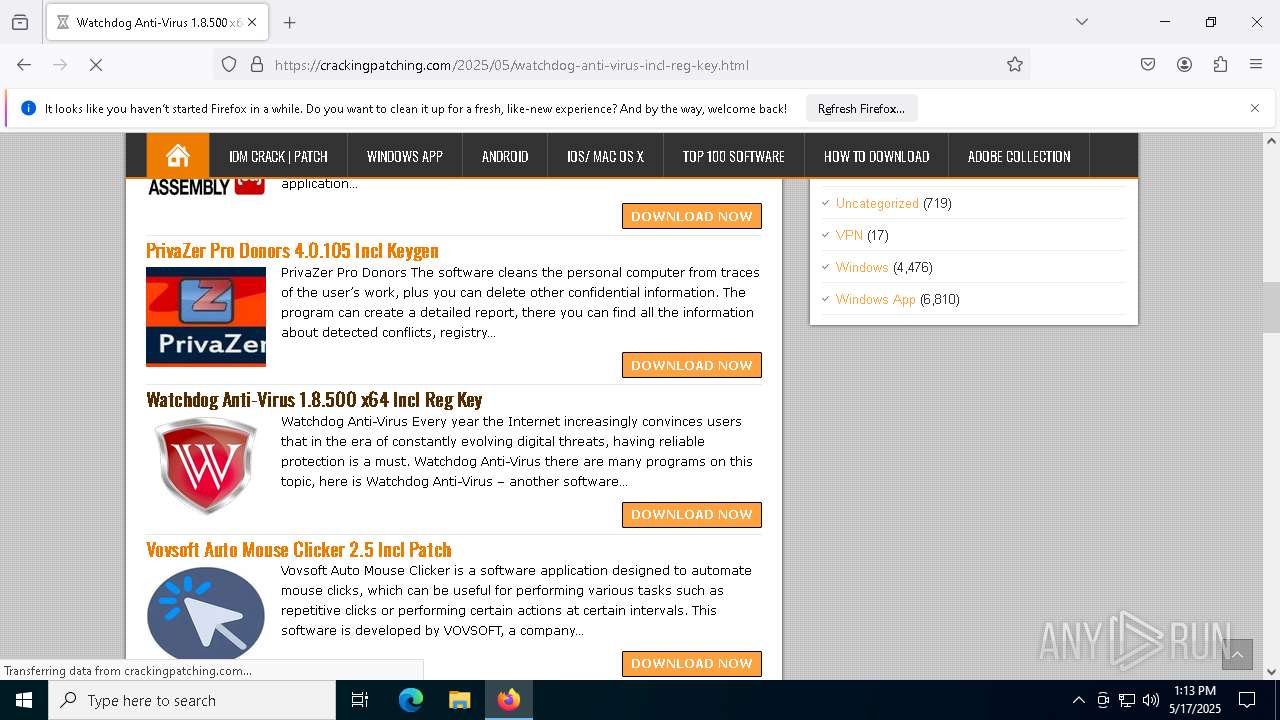
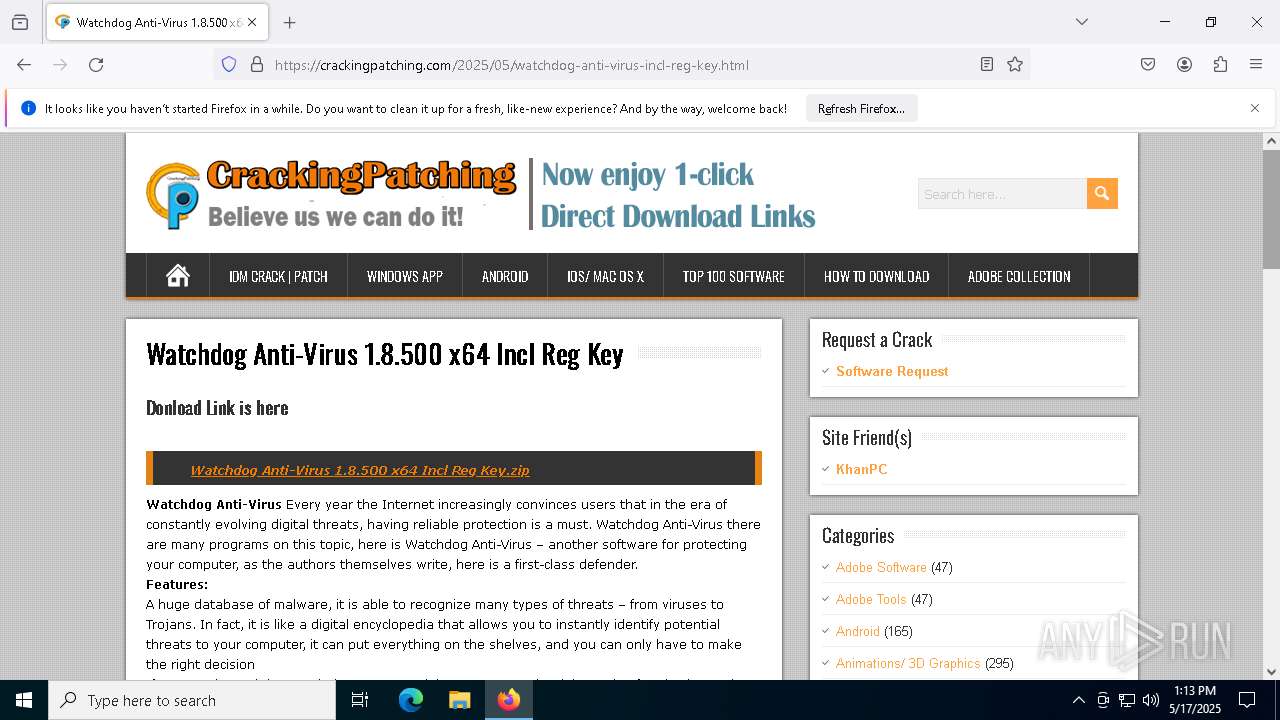
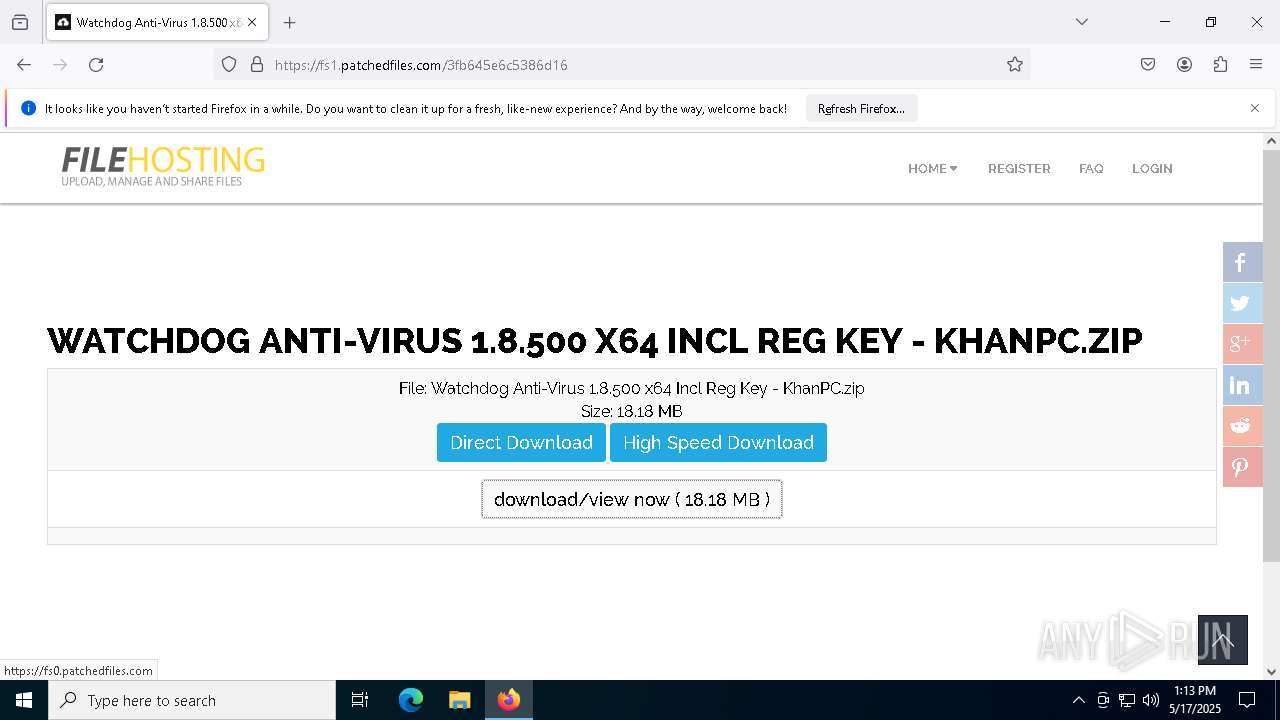
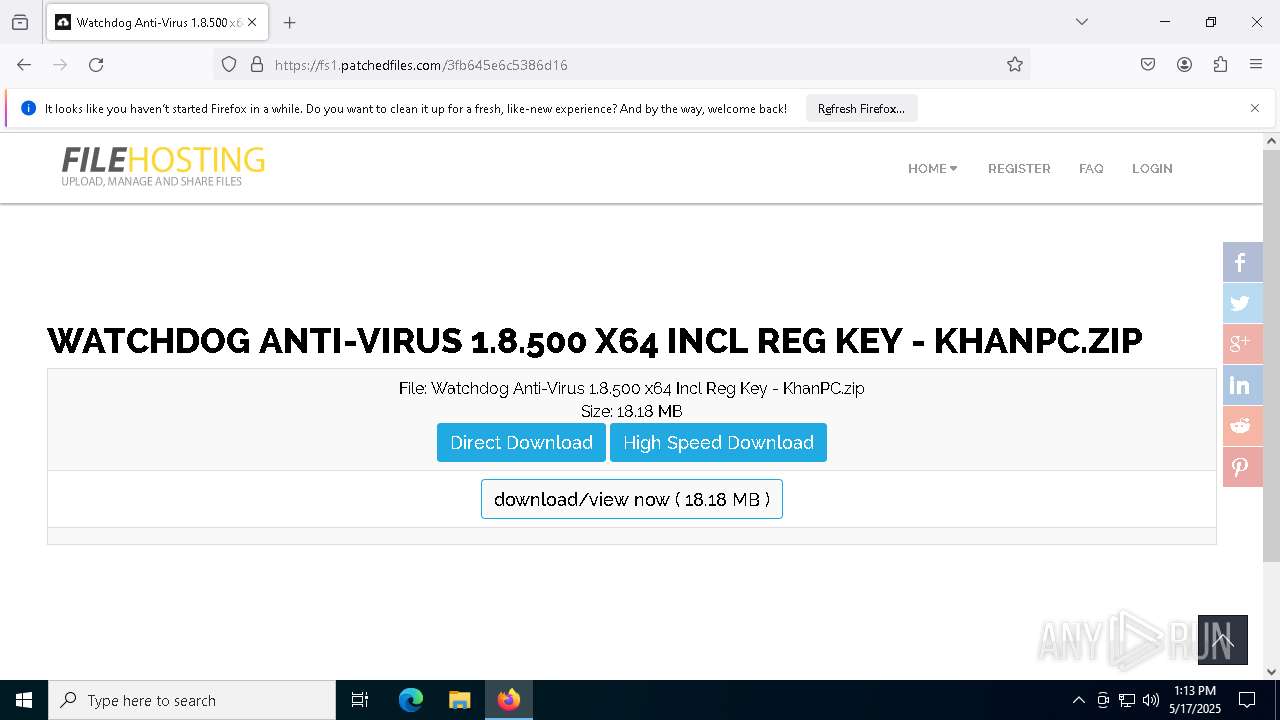
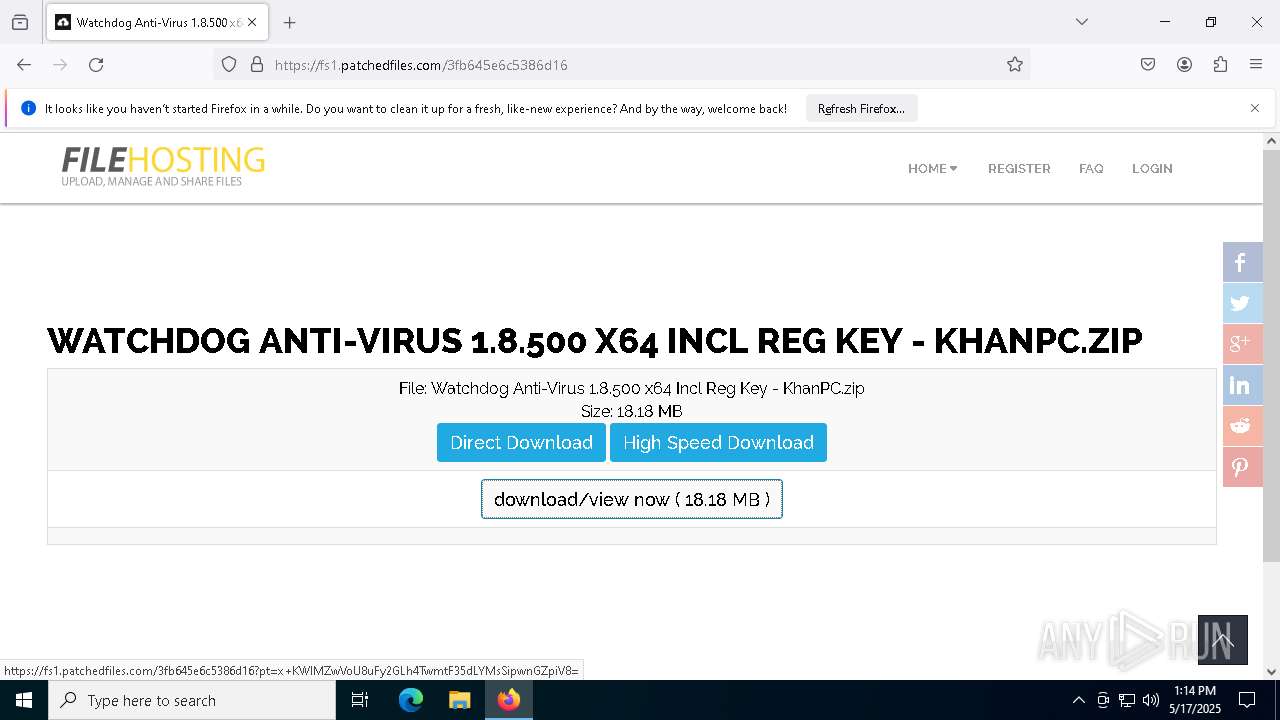
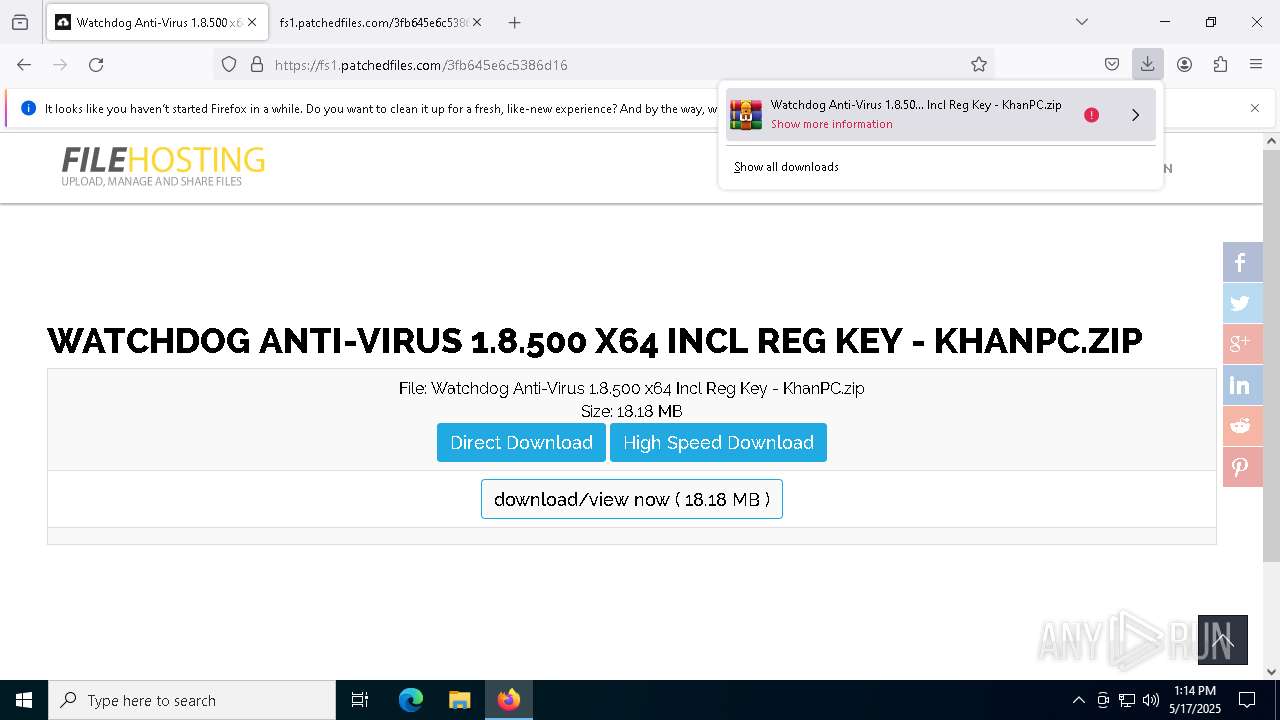
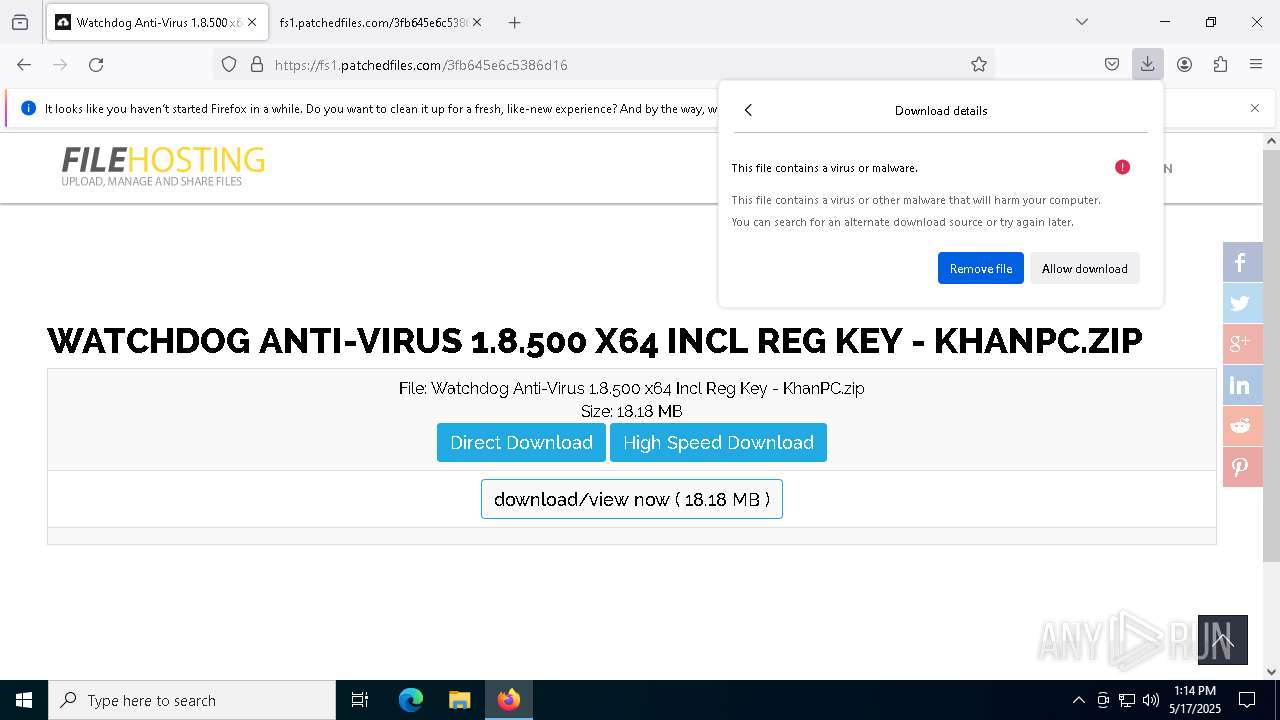
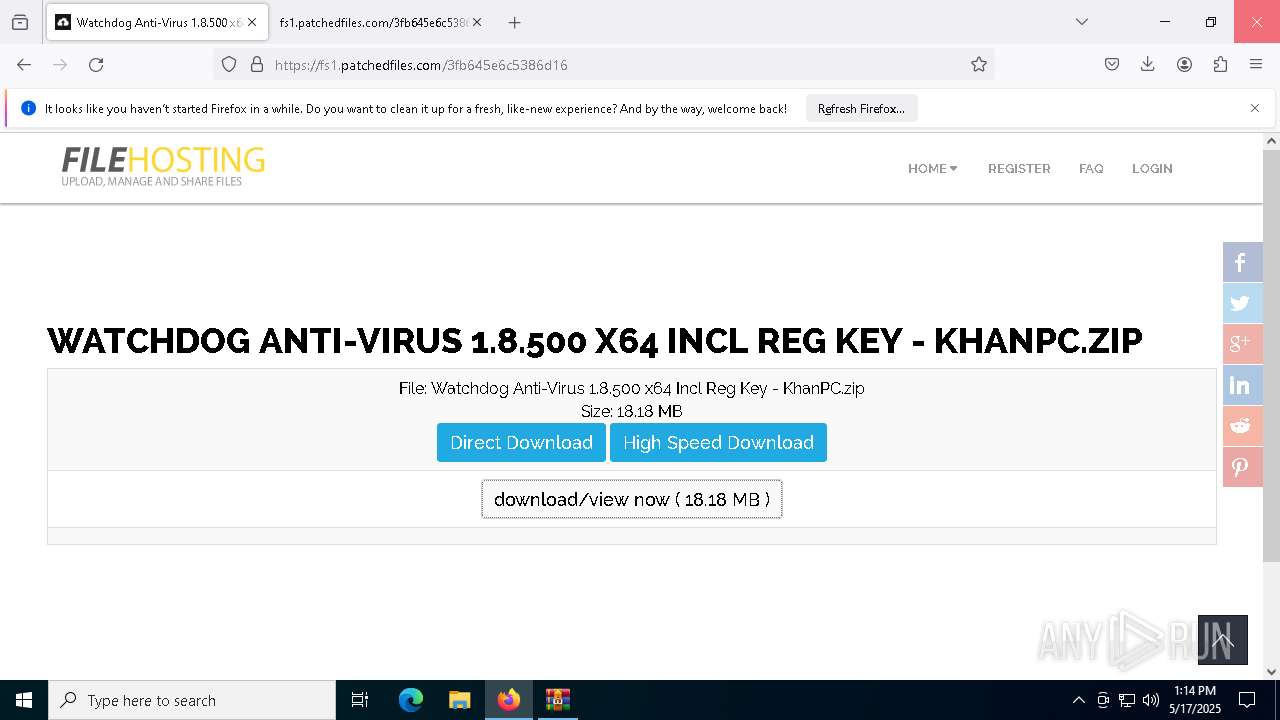
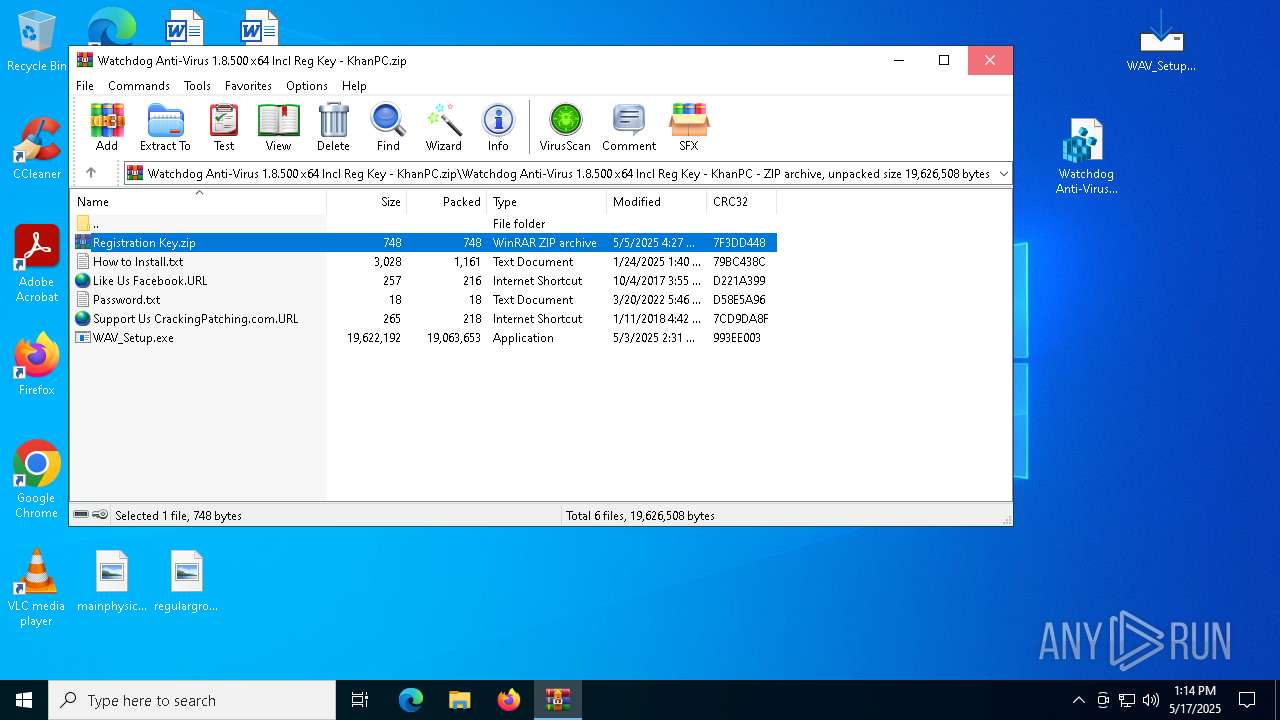
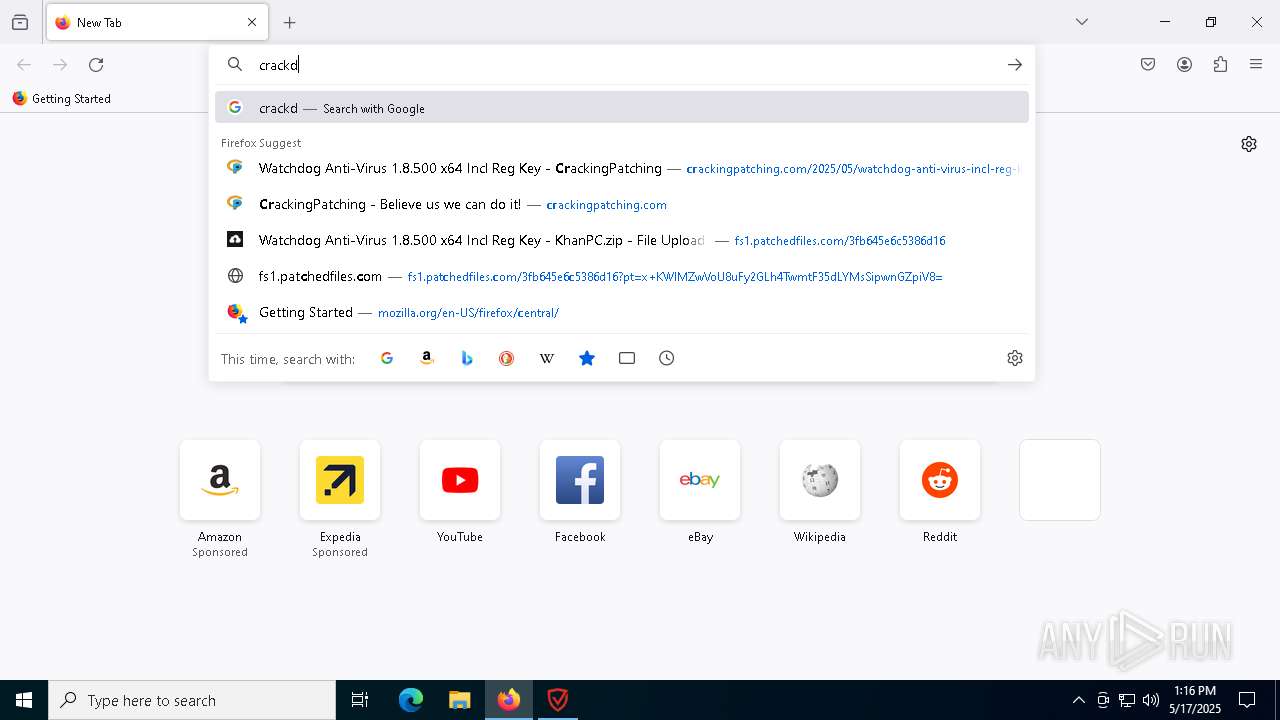
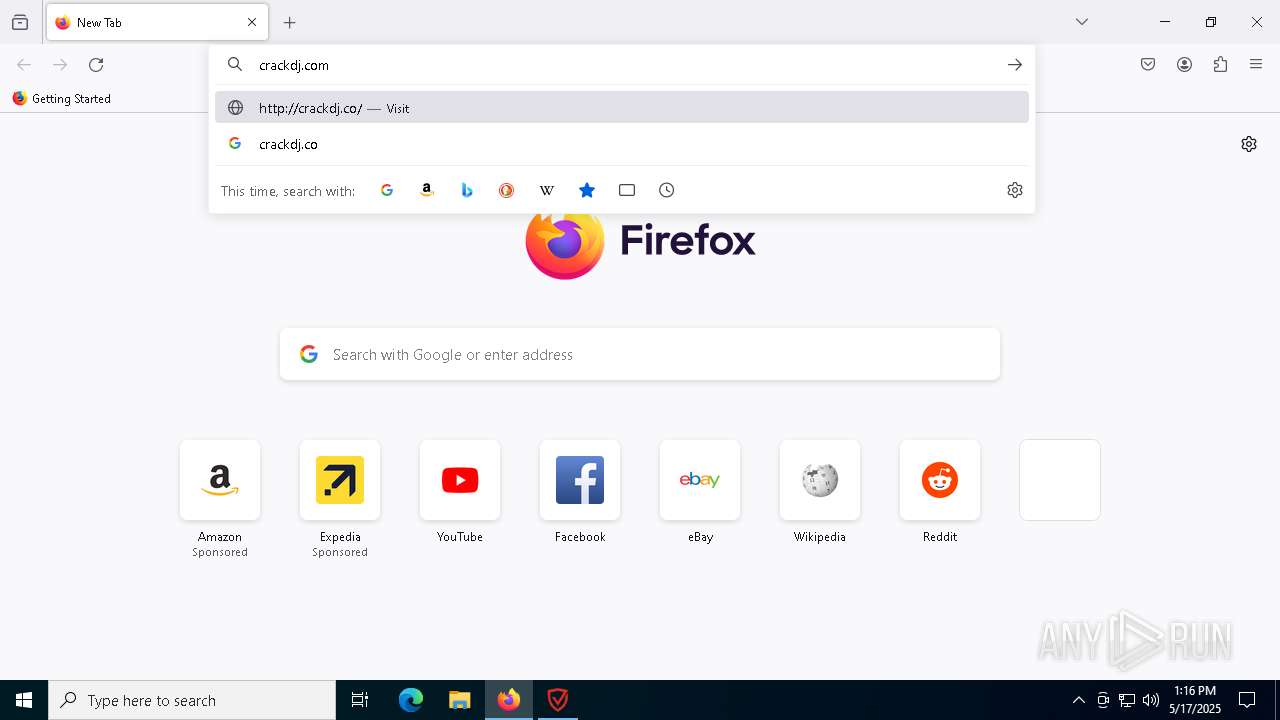
| URL: | crackingpatching.com |
| Full analysis: | https://app.any.run/tasks/cff2cf5b-a174-49ed-aaca-37a41ea5092b |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | May 17, 2025, 13:13:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D8EAB3CC4D7E149DF62F939DE677EBFB |
| SHA1: | FEE2A3103C3E61495956E0018ECCA9E2A0A5D89F |
| SHA256: | 485B9C11039F3B7DBF372185D1F862656BA8D2E5BCFB660B396B9DB30CA59D5E |
| SSDEEP: | 3:oLW5K7T:v5K7T |
MALICIOUS
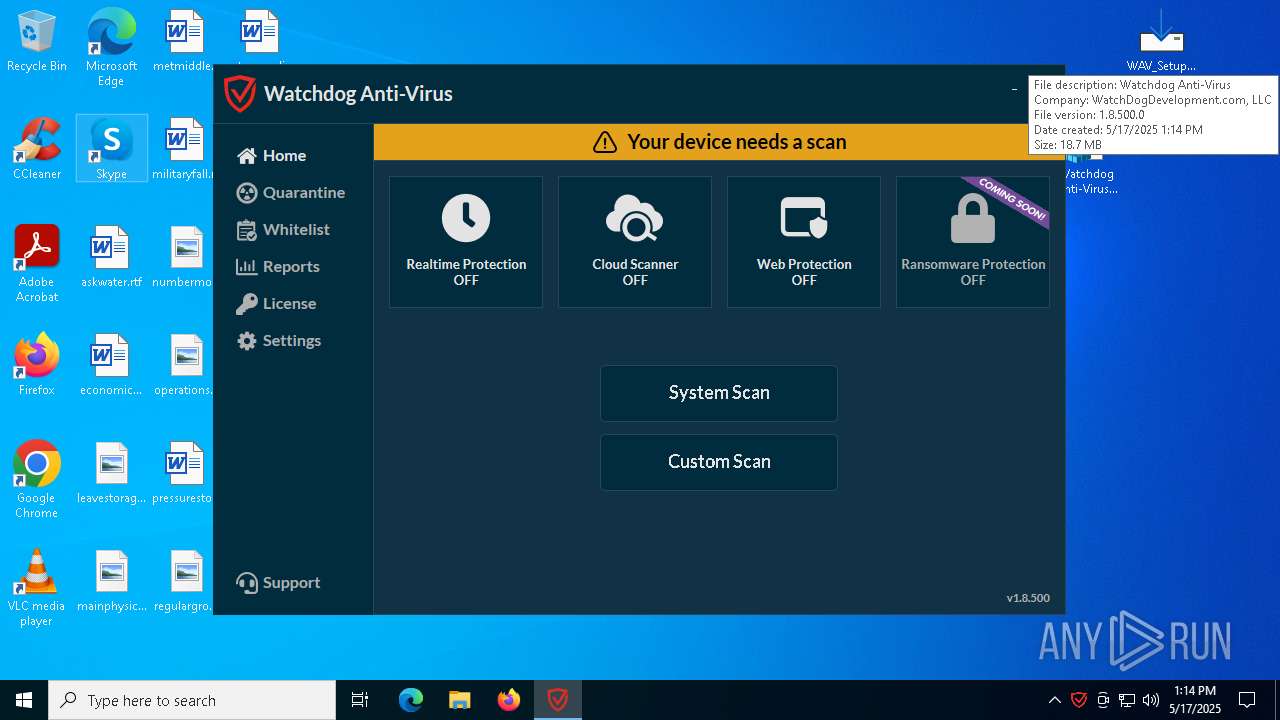
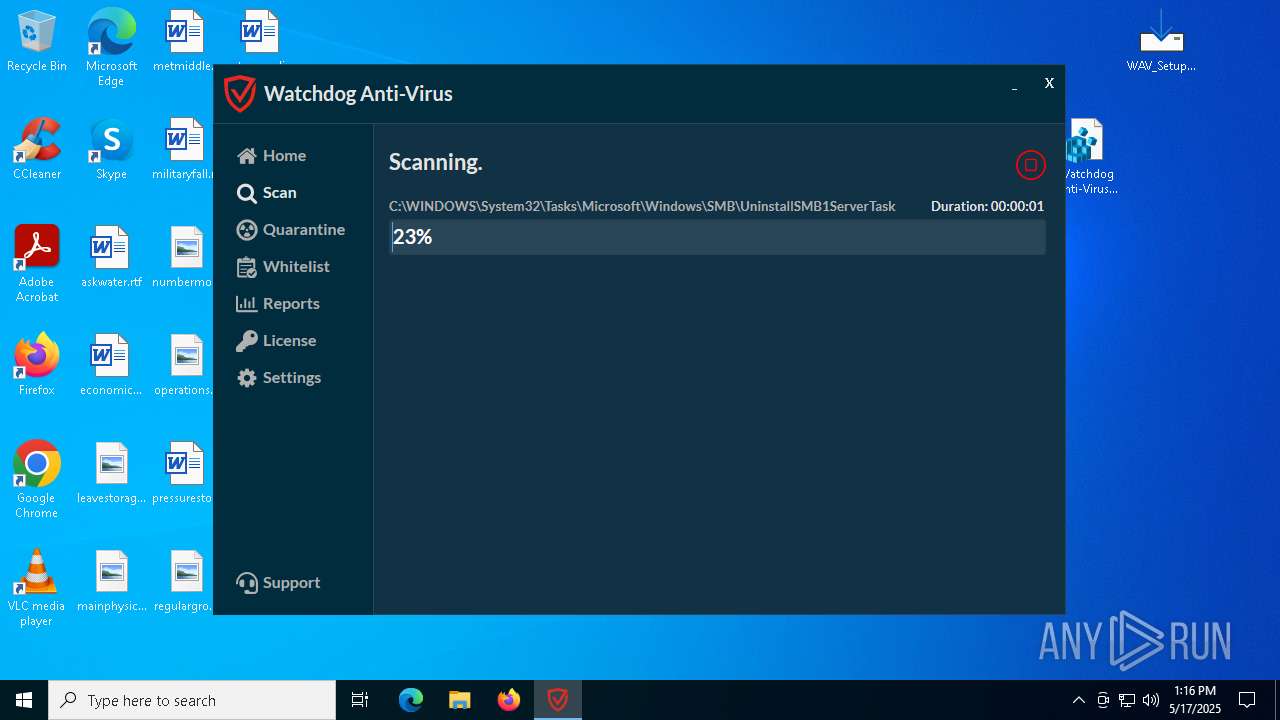
Registers / Runs the DLL via REGSVR32.EXE
- WAV_Setup.tmp (PID: 5552)
Uses Task Scheduler to run other applications
- WAV.exe (PID: 2560)
- WAV.exe (PID: 8308)
Executing a file with an untrusted certificate
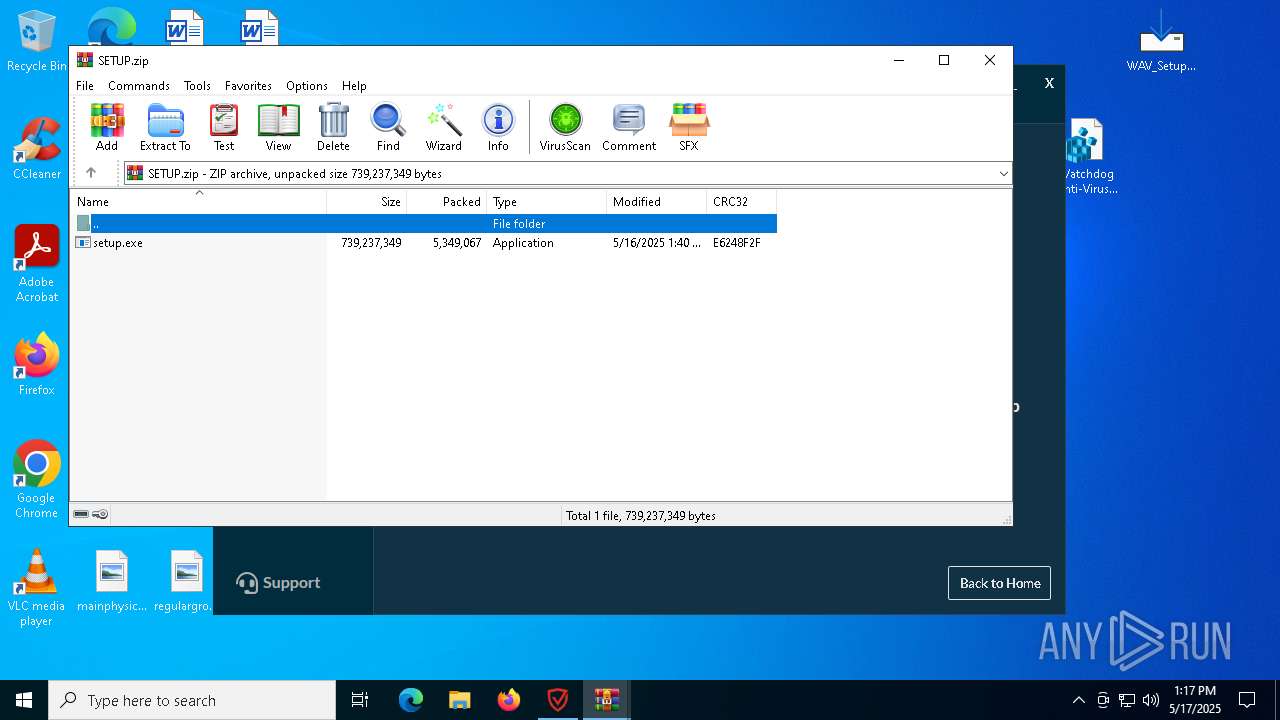
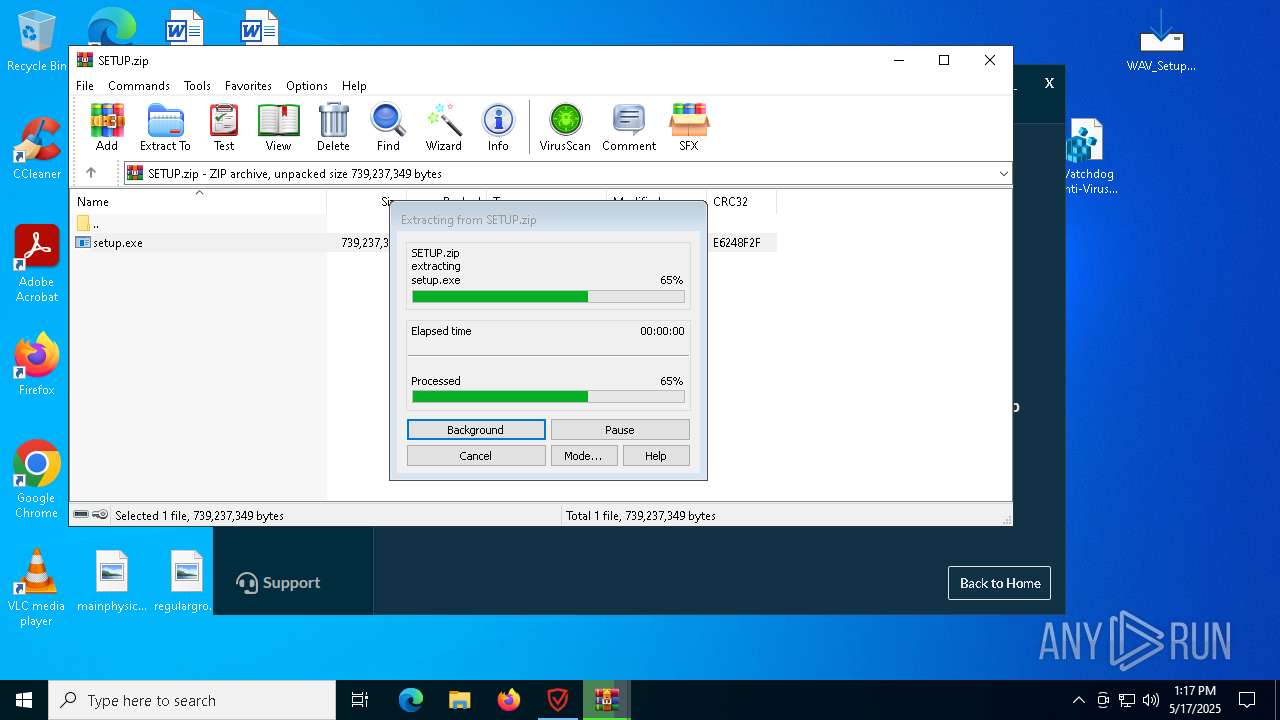
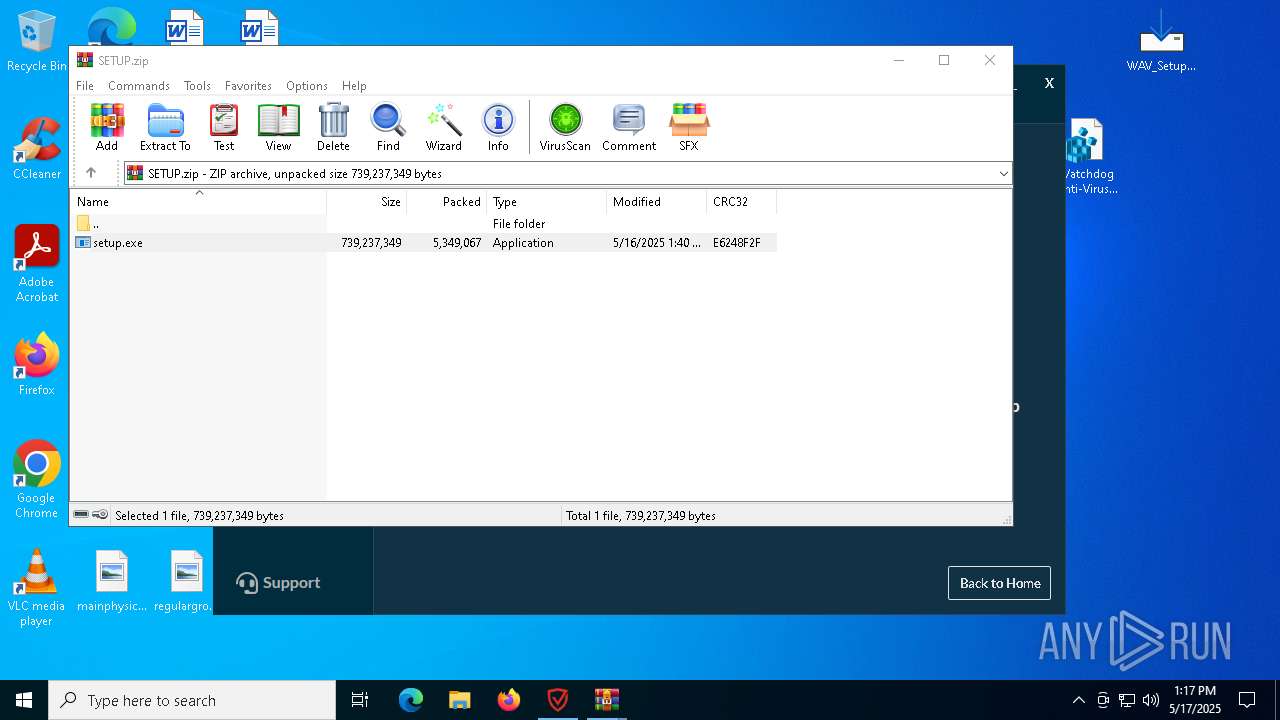
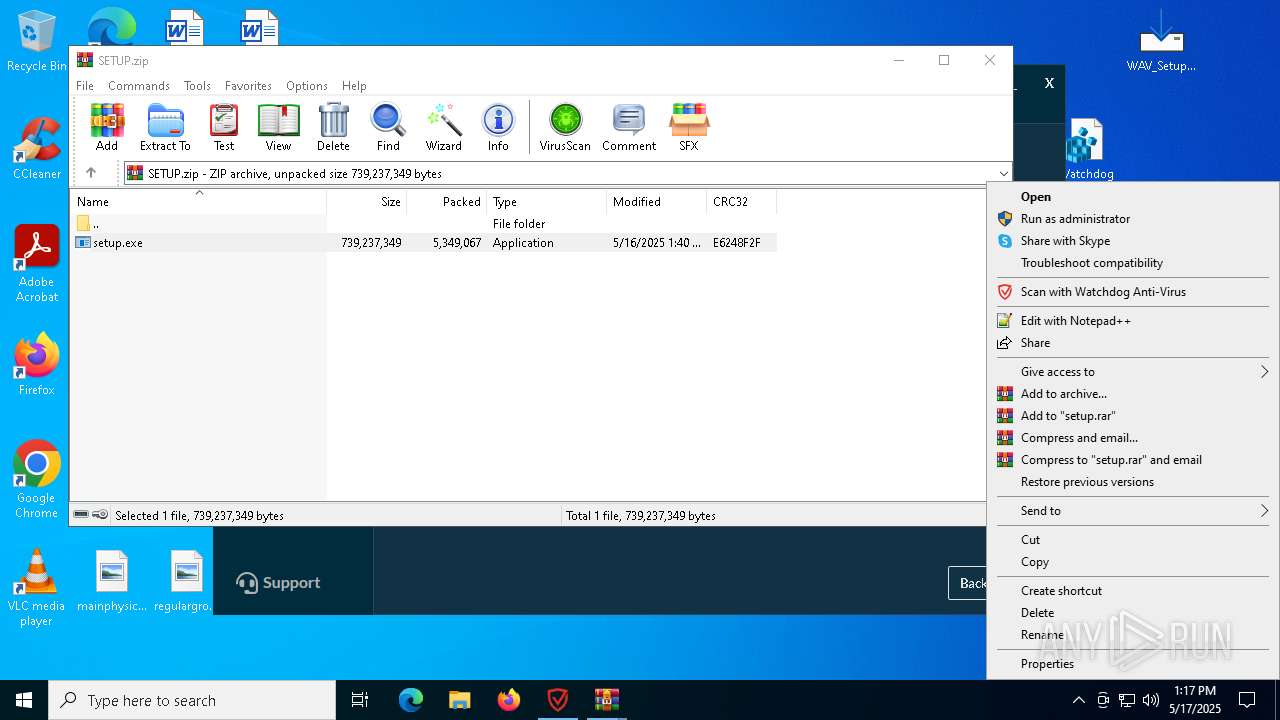
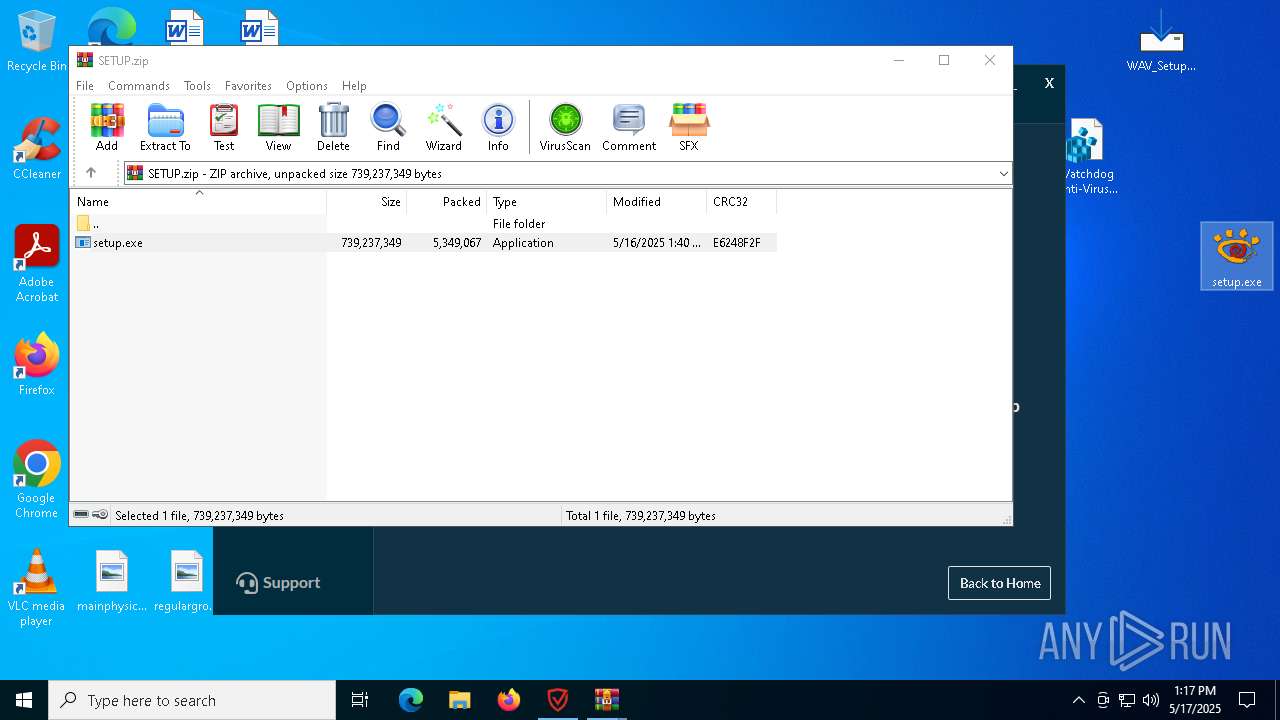
- setup.exe (PID: 2568)
- hjksfxc.exe (PID: 2148)
- DistriCompiler89.exe (PID: 4976)
- DistriCompiler89.exe (PID: 6676)
- DistriCompiler89.exe (PID: 896)
Known privilege escalation attack
- dllhost.exe (PID: 2084)
SUSPICIOUS
Reads security settings of Internet Explorer
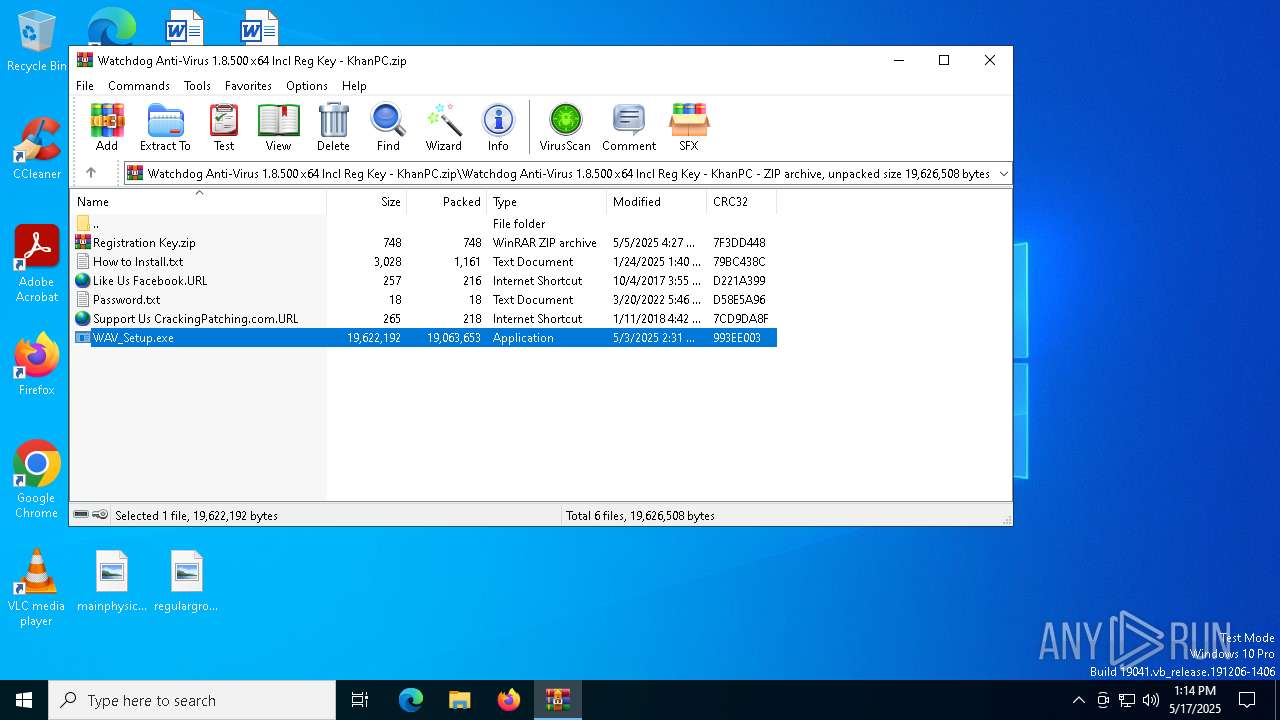
- WinRAR.exe (PID: 5548)
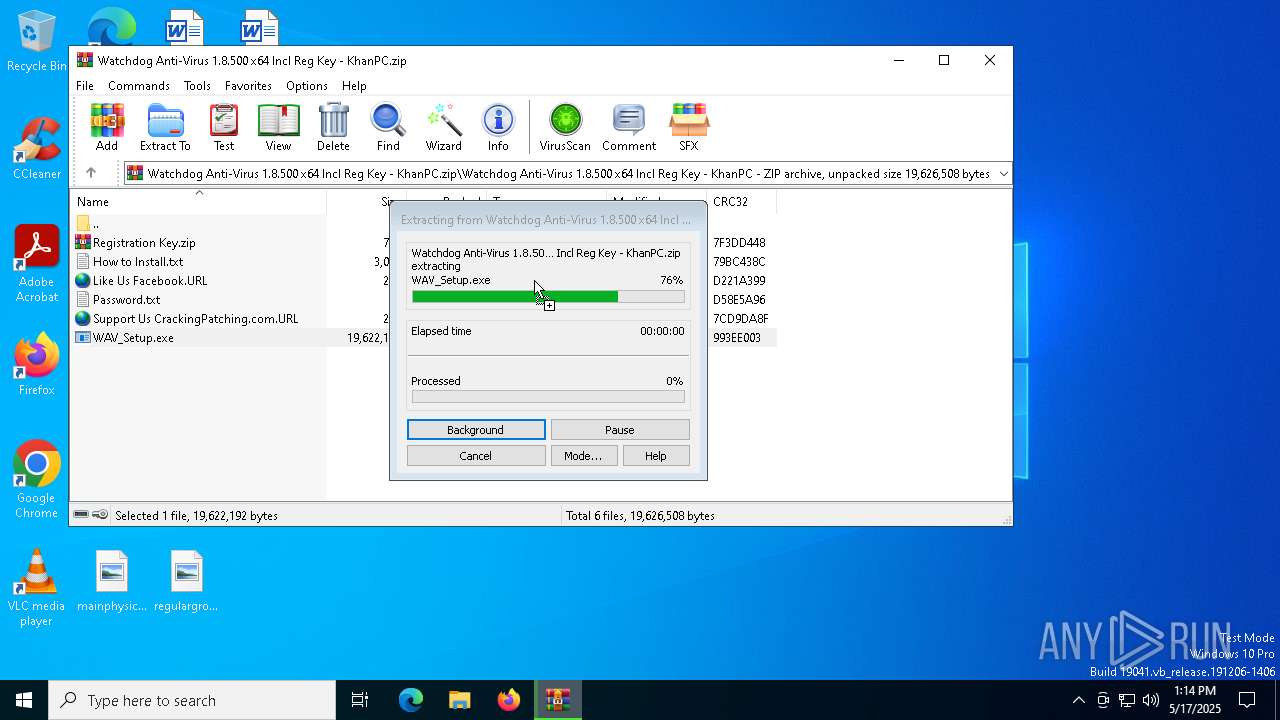
Executable content was dropped or overwritten
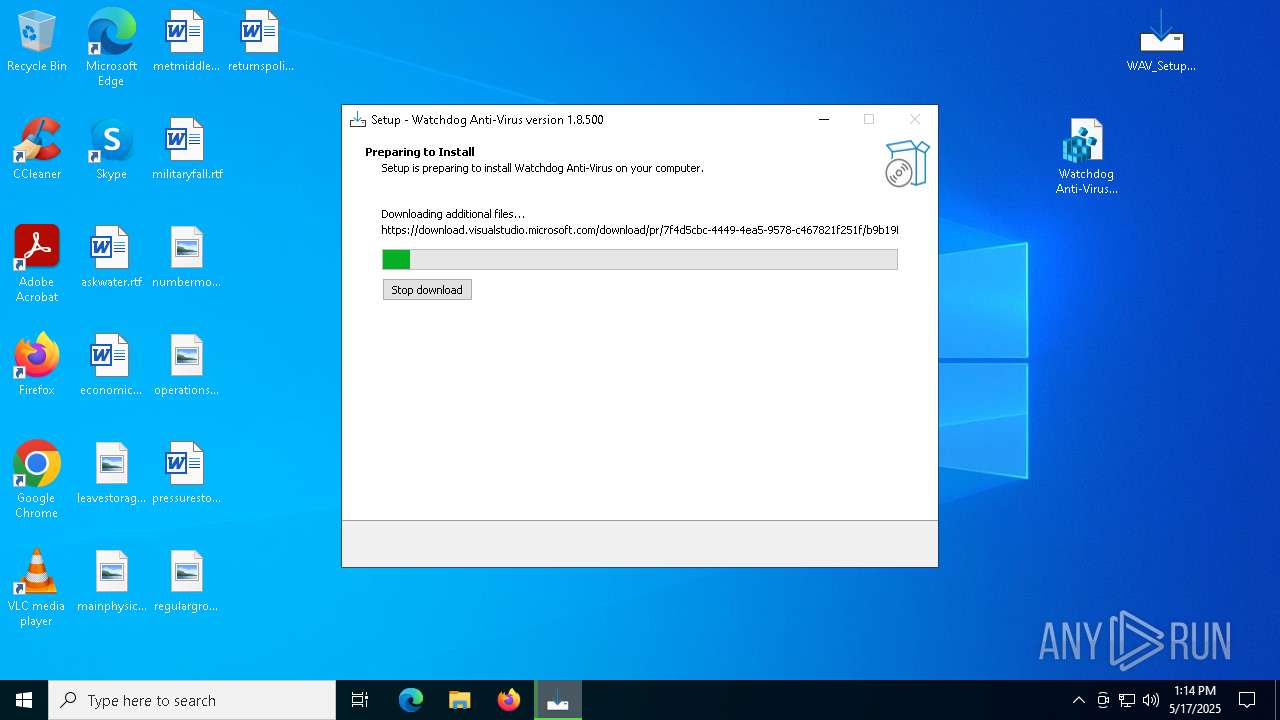
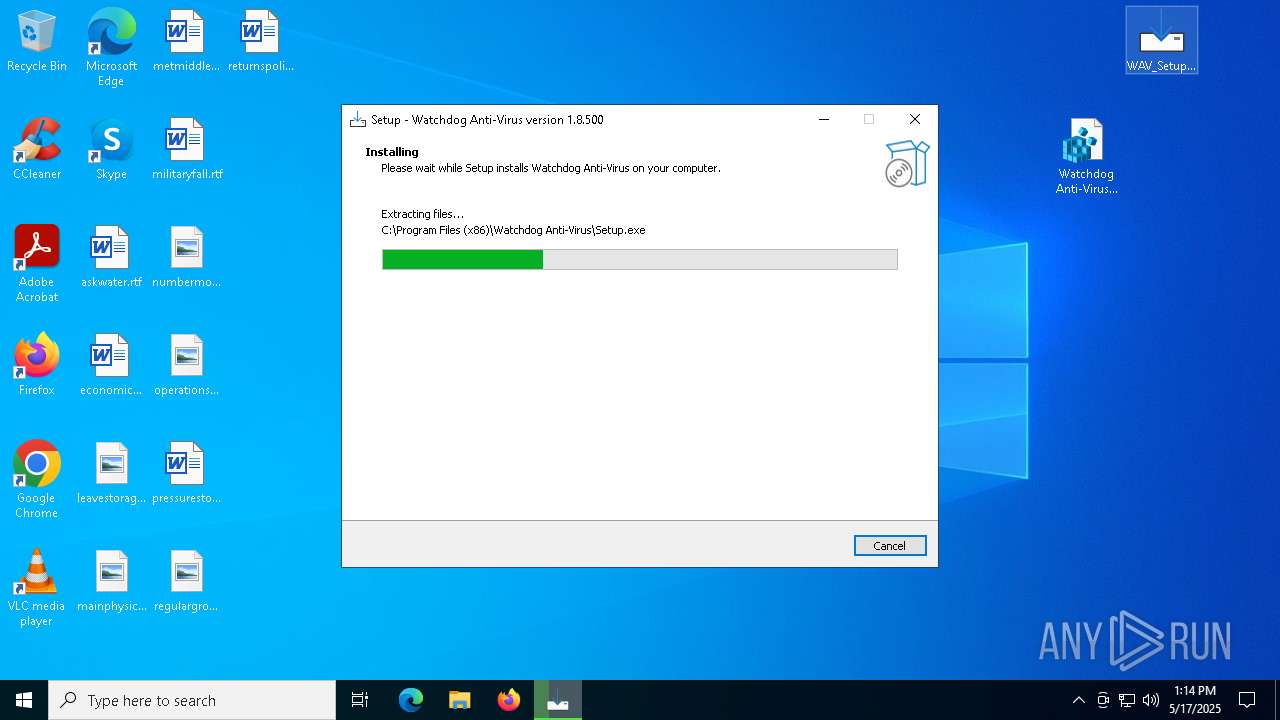
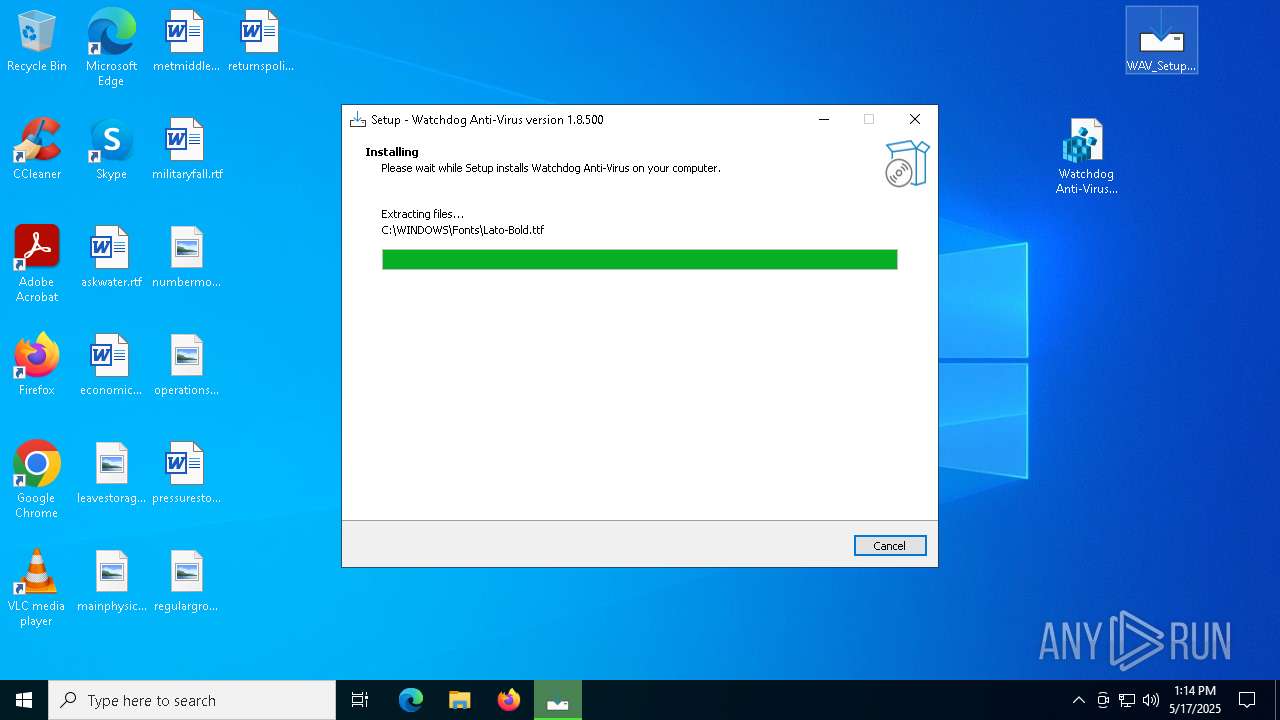
- WAV_Setup.exe (PID: 9136)
- dotnet.exe (PID: 8504)
- dotnet.exe (PID: 9024)
- dotnet-runtime-8.0.0-win-x64.exe (PID: 4200)
- rundll32.exe (PID: 1600)
- setup.exe (PID: 2568)
- WAV_Setup.exe (PID: 4000)
- hjksfxc.exe (PID: 2148)
- DistriCompiler89.exe (PID: 4976)
- DistriCompiler89.exe (PID: 896)
- WAV_Setup.tmp (PID: 5552)
Command gets lists installed versions of .NET Runtime on the system
- cmd.exe (PID: 2148)
Application launched itself
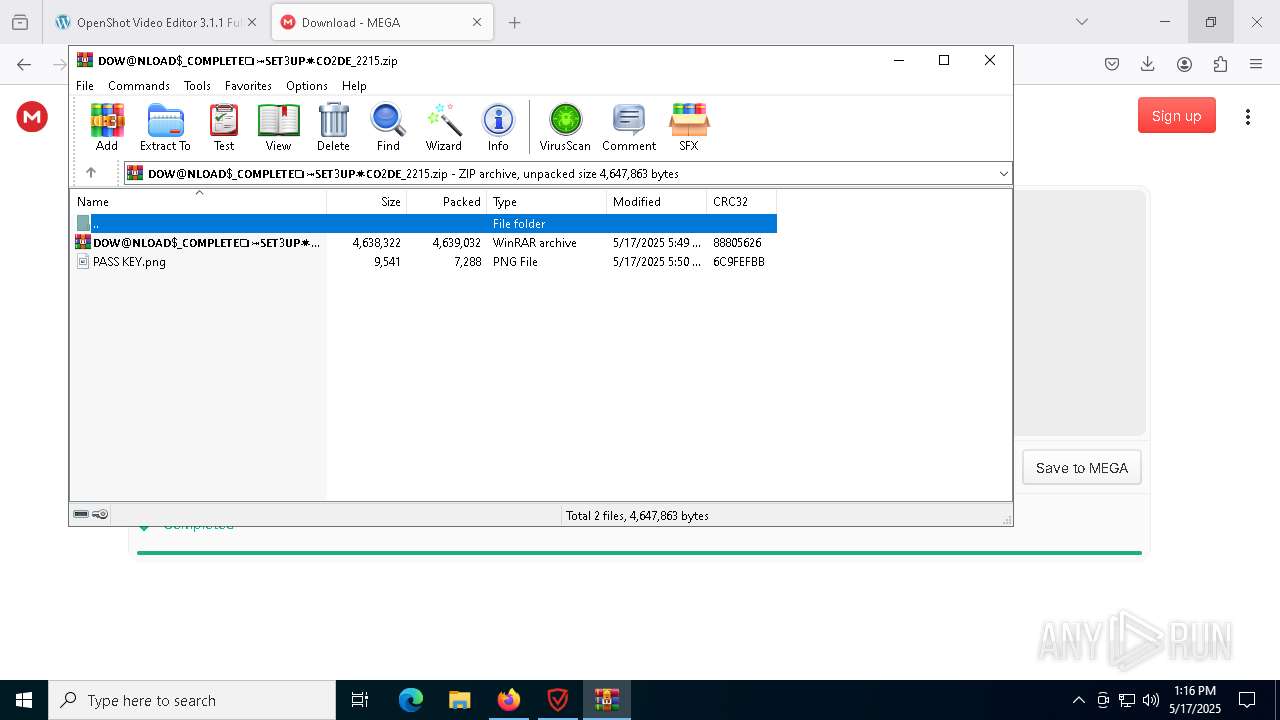
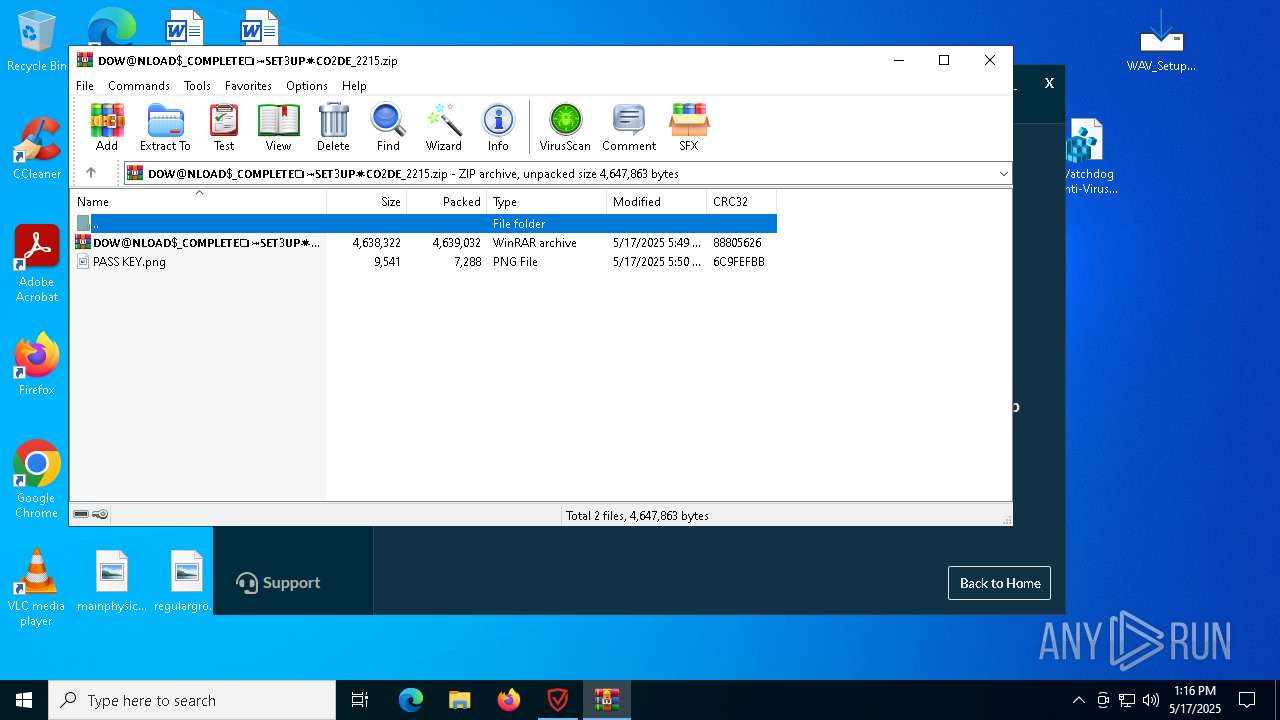
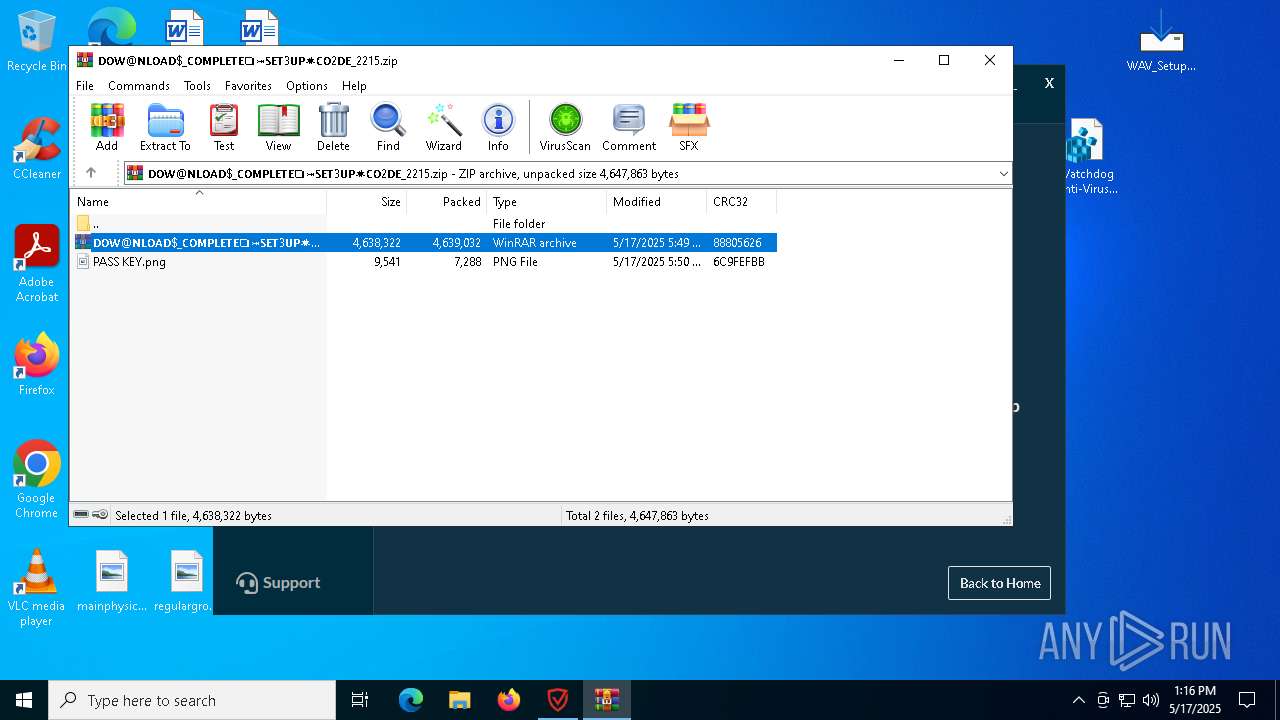
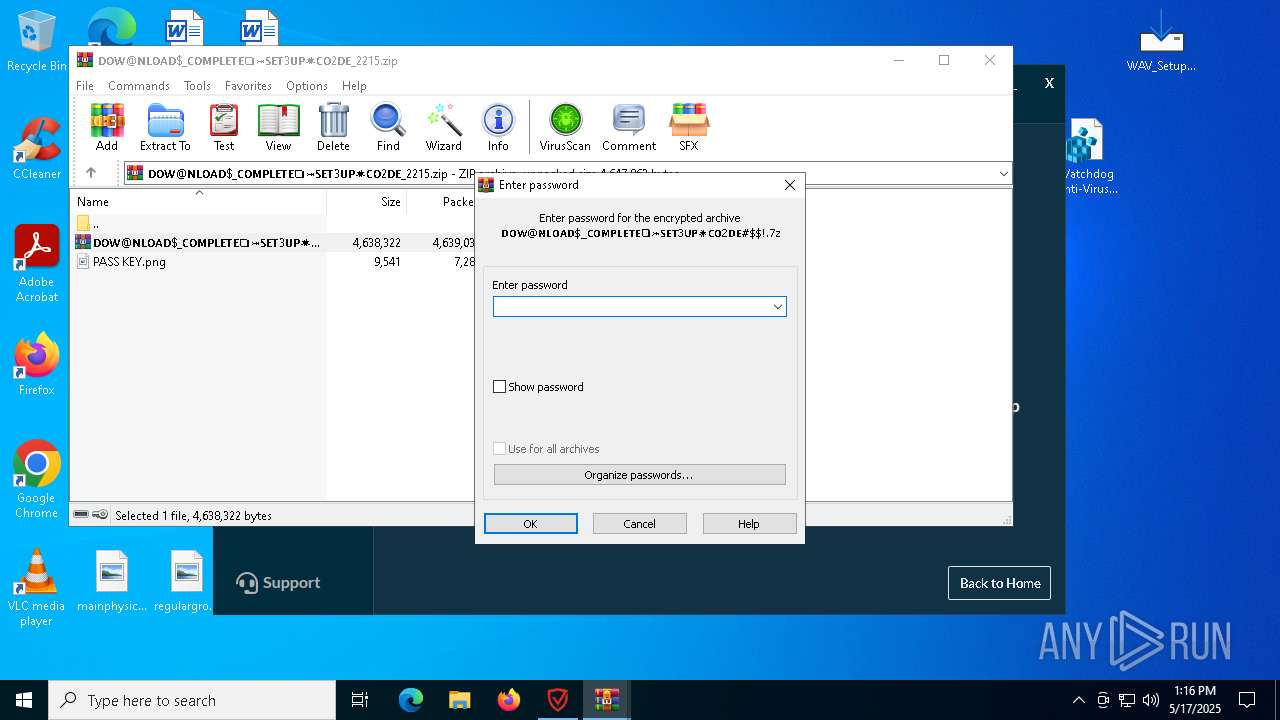
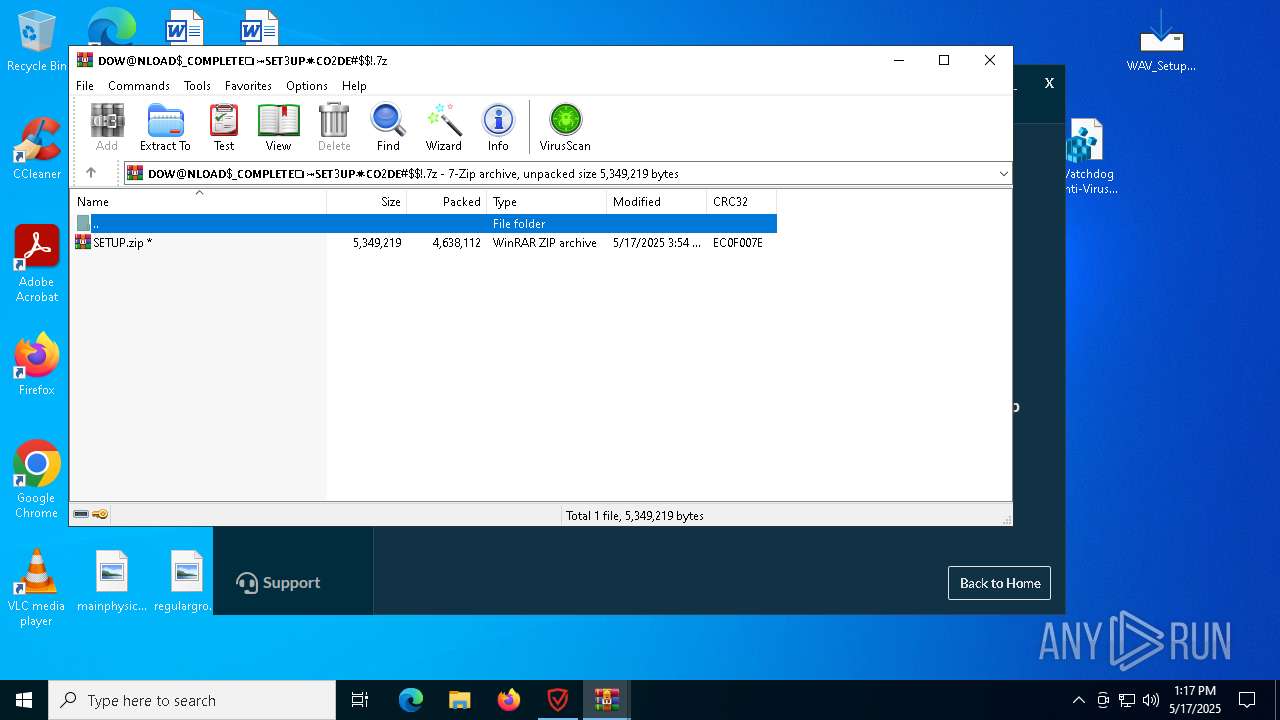
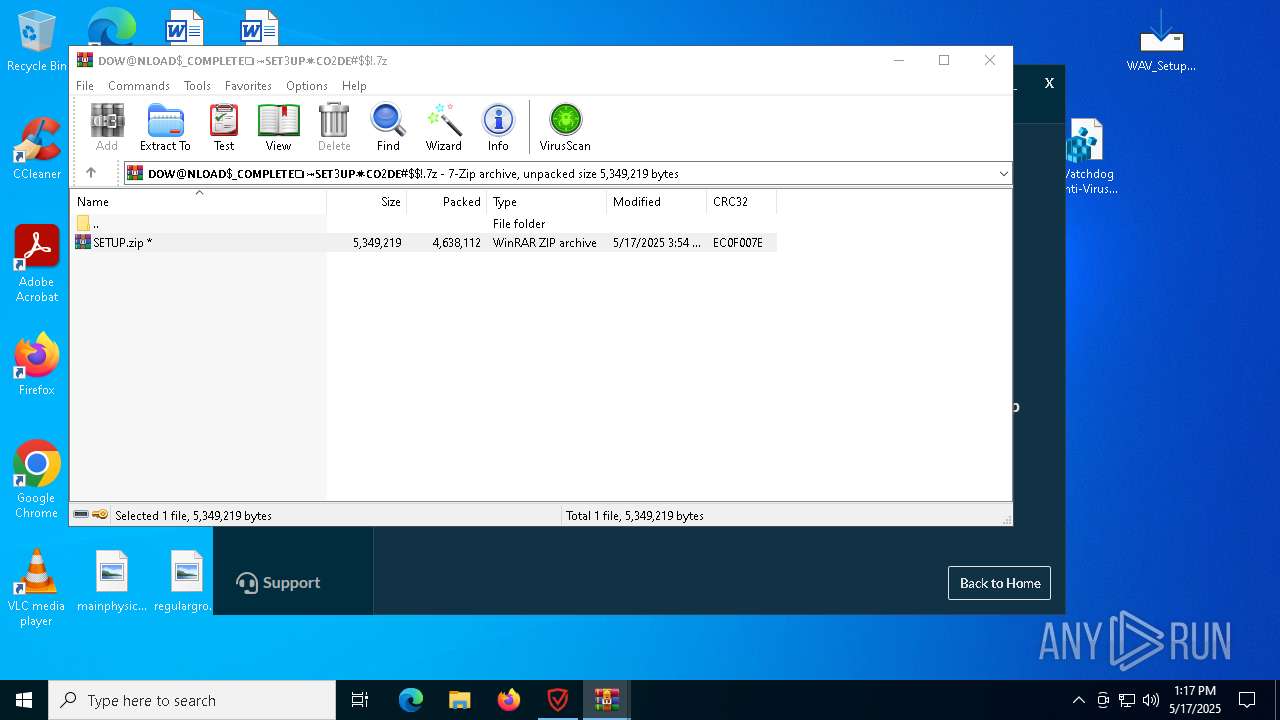
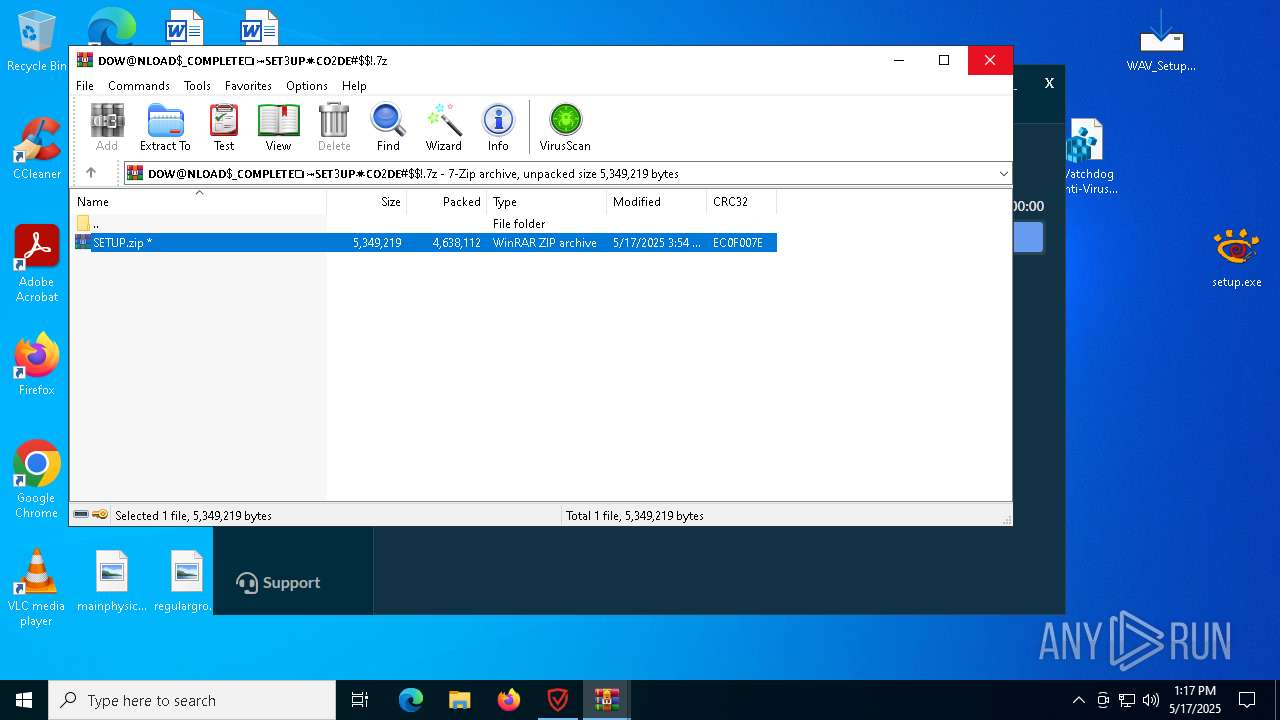
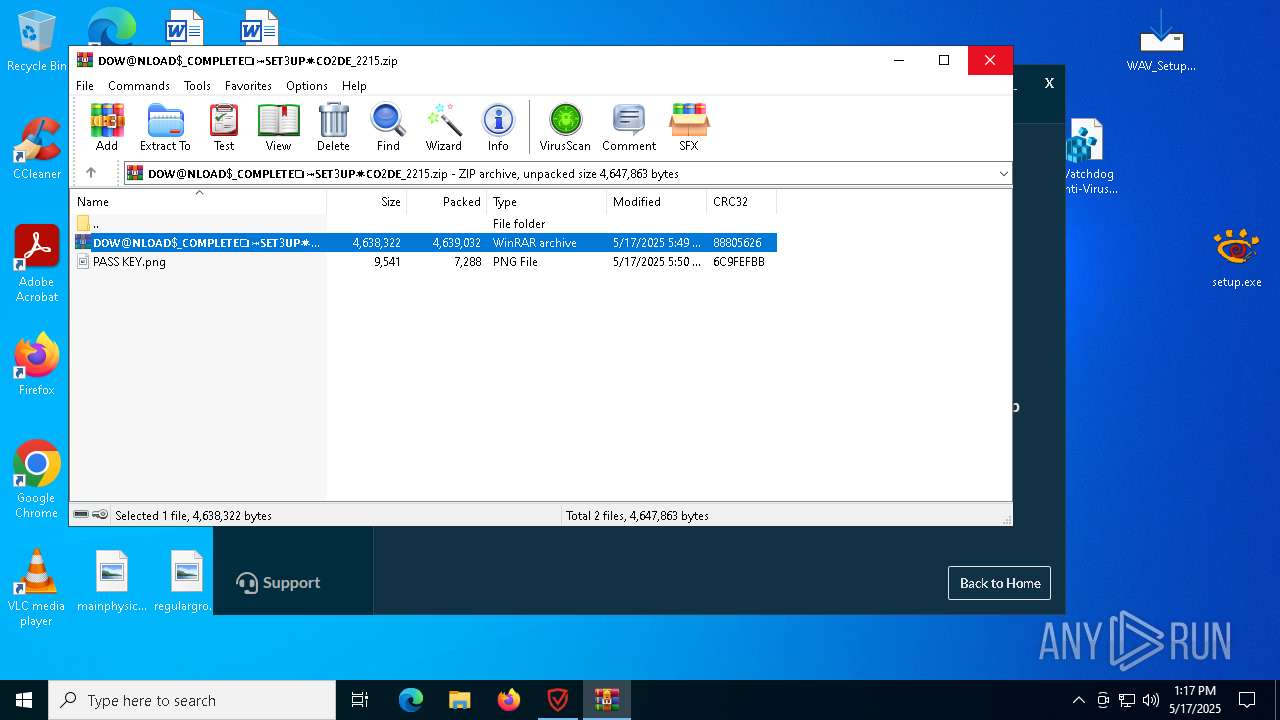
- WinRAR.exe (PID: 5548)
- WinRAR.exe (PID: 1056)
- WinRAR.exe (PID: 9212)
Starts CMD.EXE for commands execution
- WAV_Setup.tmp (PID: 5552)
Starts itself from another location
- dotnet.exe (PID: 8504)
- DistriCompiler89.exe (PID: 4976)
Starts a Microsoft application from unusual location
- dotnet-runtime-8.0.0-win-x64.exe (PID: 4200)
- dotnet.exe (PID: 9024)
- dotnet.exe (PID: 8504)
Process drops legitimate windows executable
- WAV_Setup.tmp (PID: 5552)
- dotnet.exe (PID: 8504)
- dotnet-runtime-8.0.0-win-x64.exe (PID: 4200)
- msiexec.exe (PID: 6972)
- setup.exe (PID: 2568)
The process drops C-runtime libraries
- WAV_Setup.tmp (PID: 5552)
- setup.exe (PID: 2568)
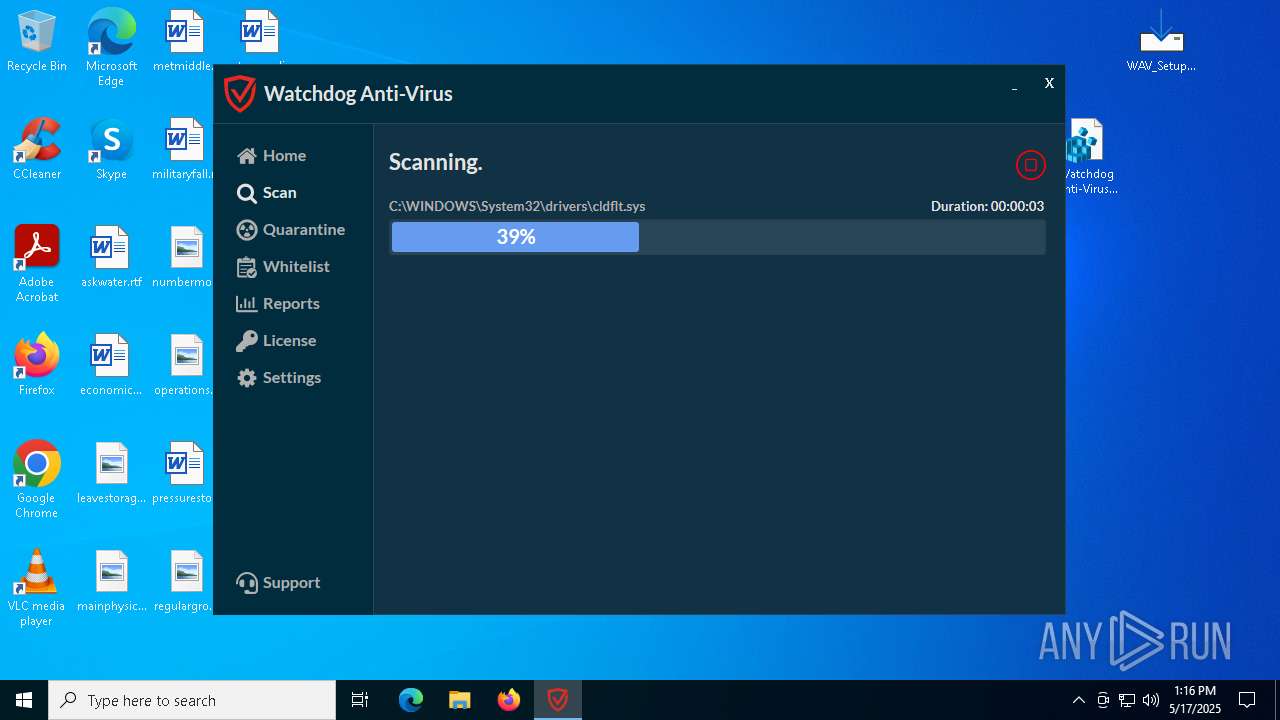
Drops a system driver (possible attempt to evade defenses)
- WAV_Setup.tmp (PID: 5552)
- rundll32.exe (PID: 1600)
There is functionality for communication over UDP network (YARA)
- WAV.exe (PID: 2560)
- WAV.exe (PID: 8308)
There is functionality for taking screenshot (YARA)
- WAV.exe (PID: 8308)
- WAV.exe (PID: 2560)
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 8756)
- rundll32.exe (PID: 8728)
Potential Corporate Privacy Violation
- setup.exe (PID: 2568)
Drops 7-zip archiver for unpacking
- DistriCompiler89.exe (PID: 896)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5548)
- msiexec.exe (PID: 6972)
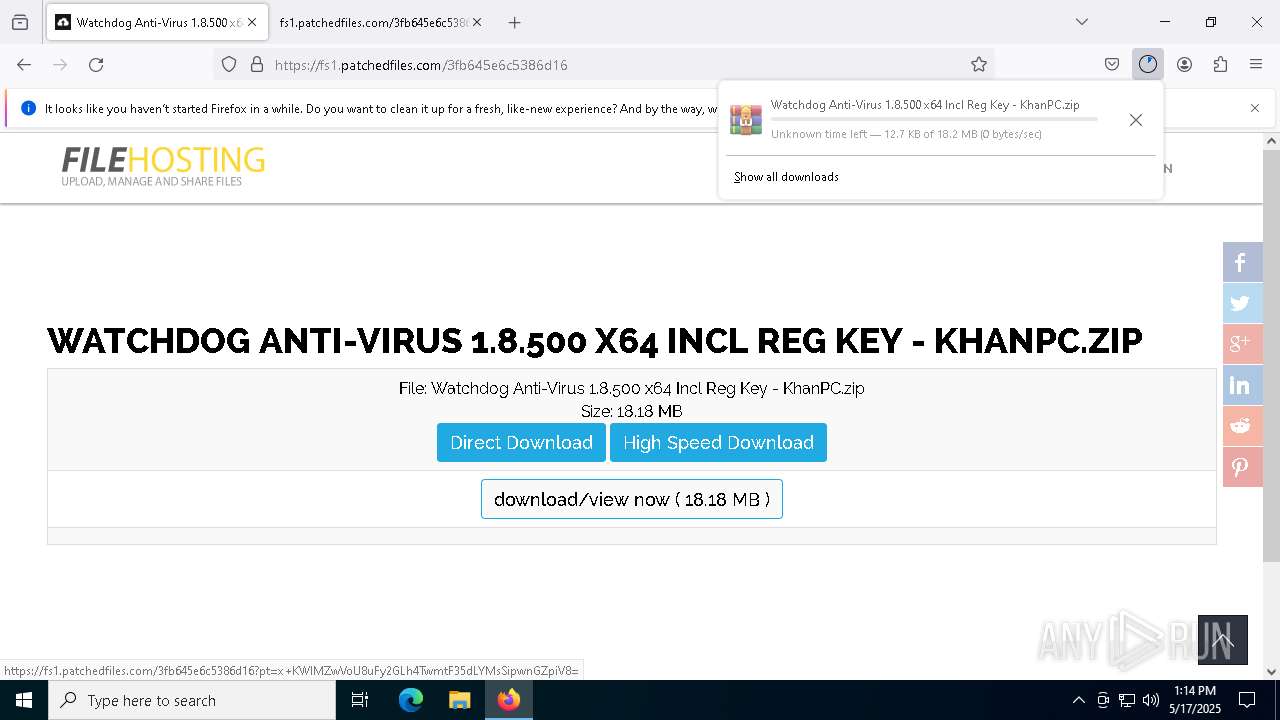
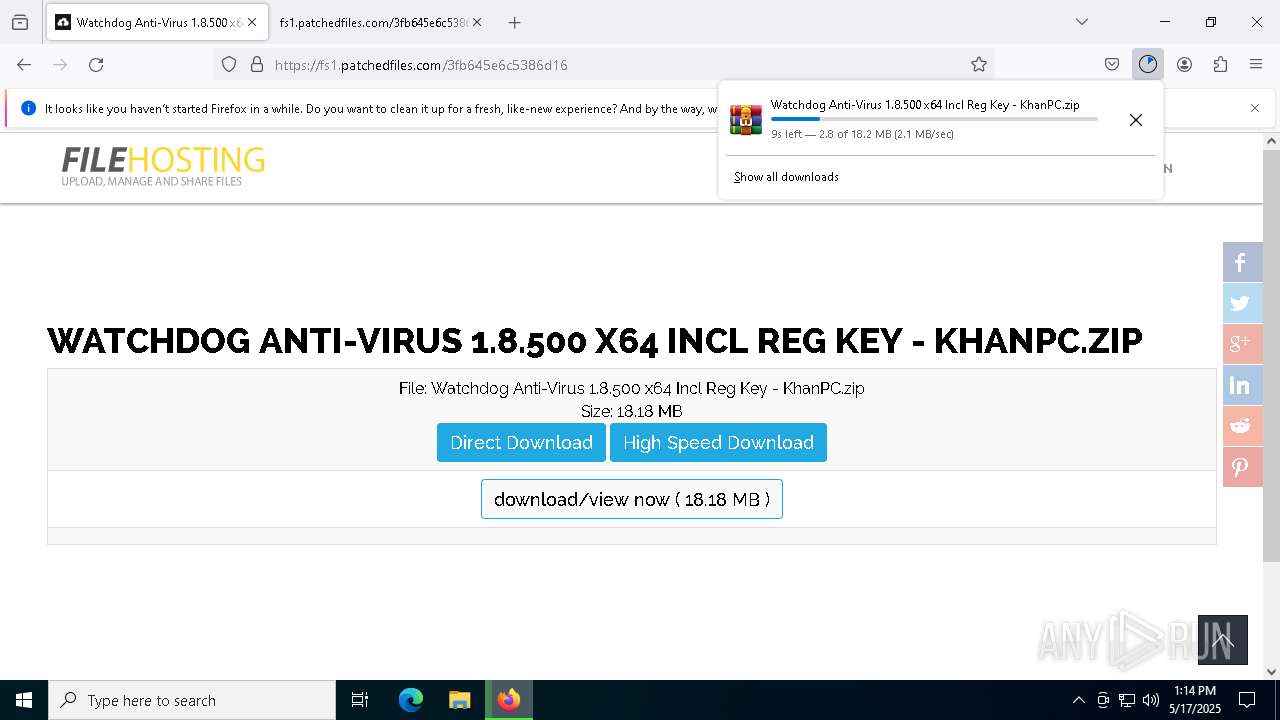
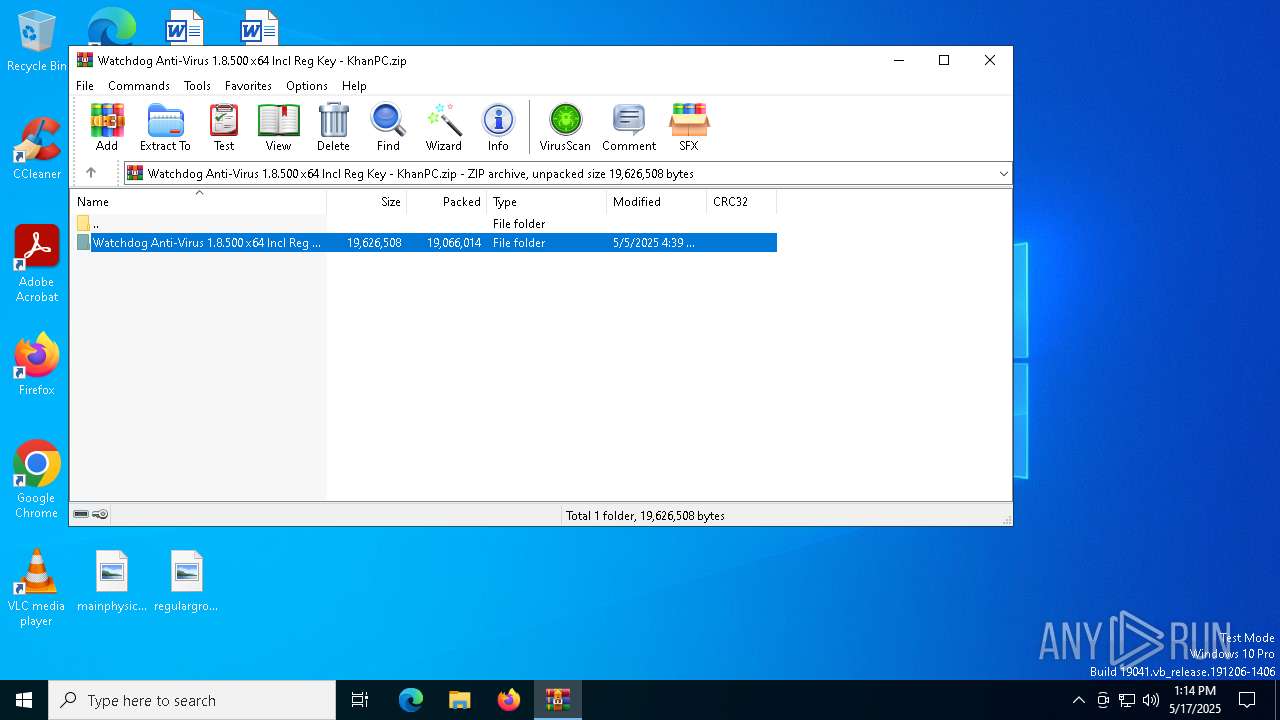
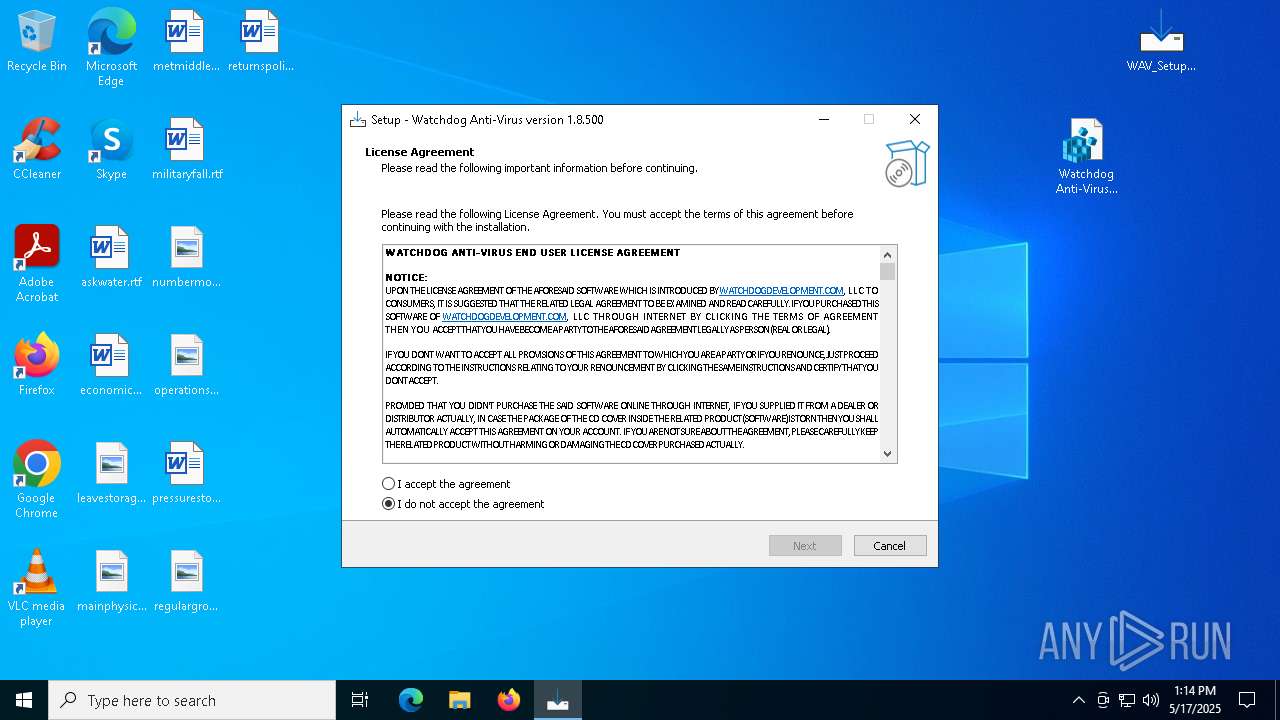
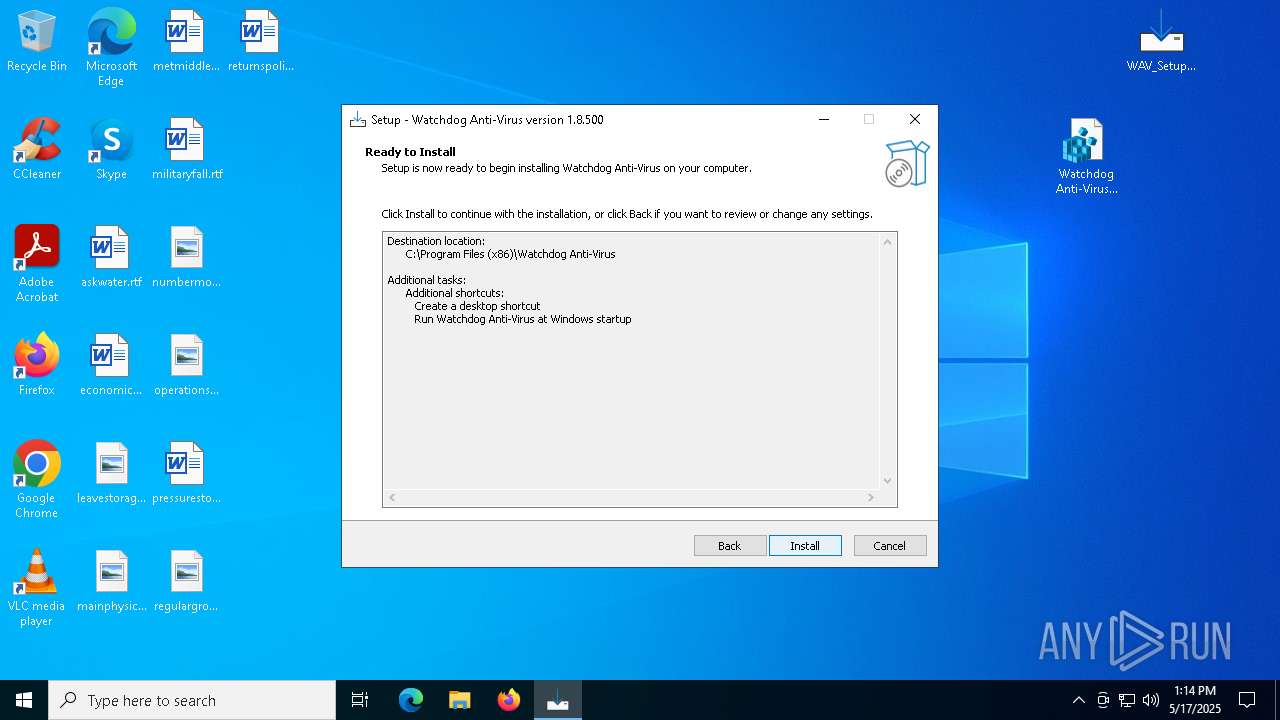
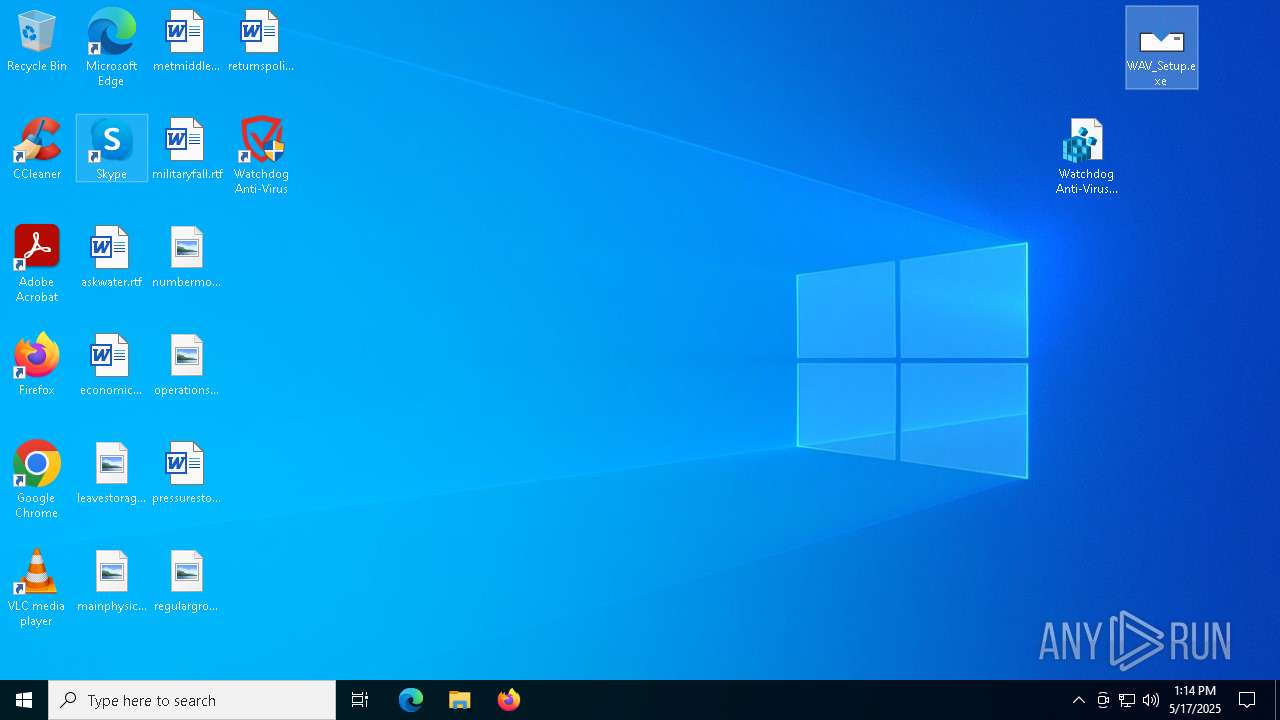
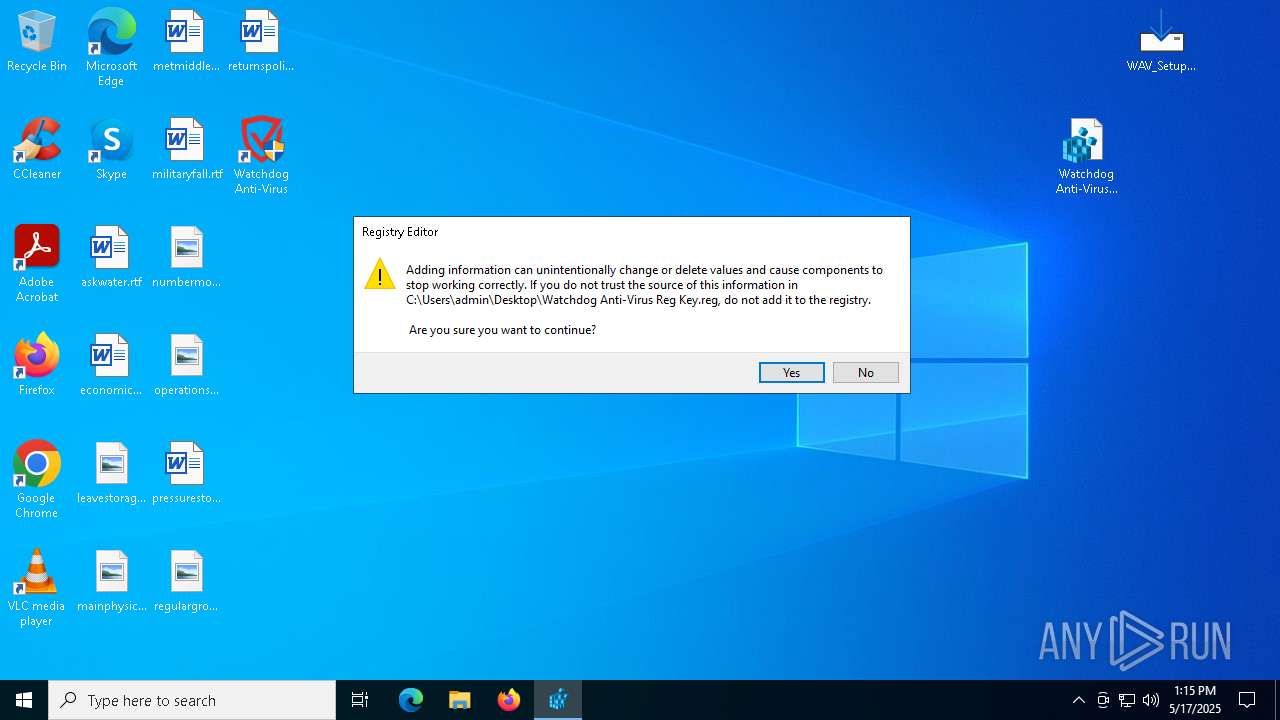
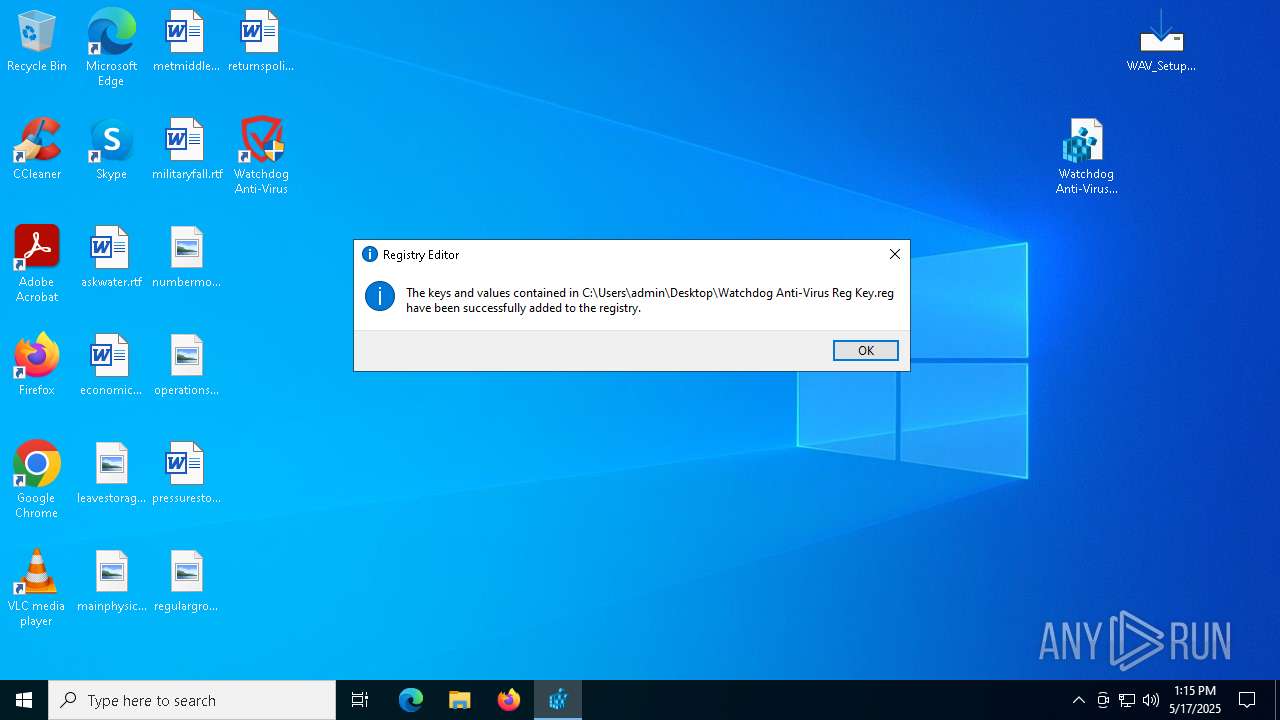
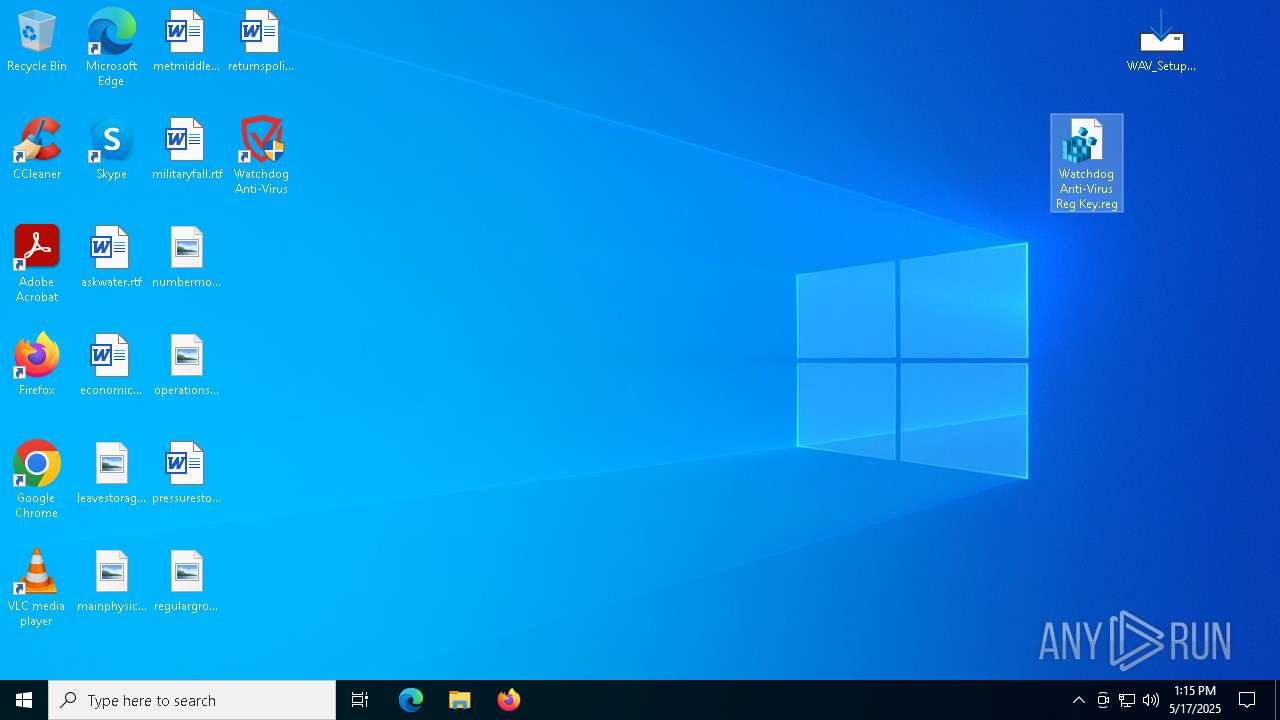
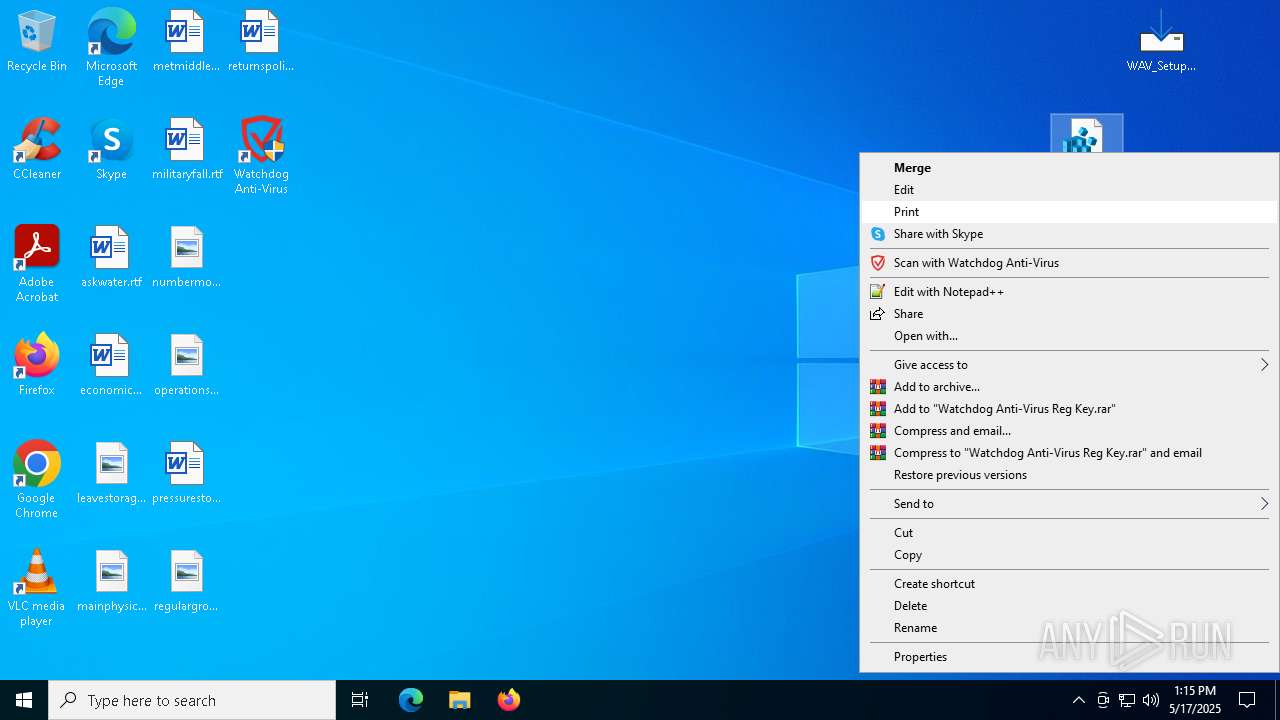
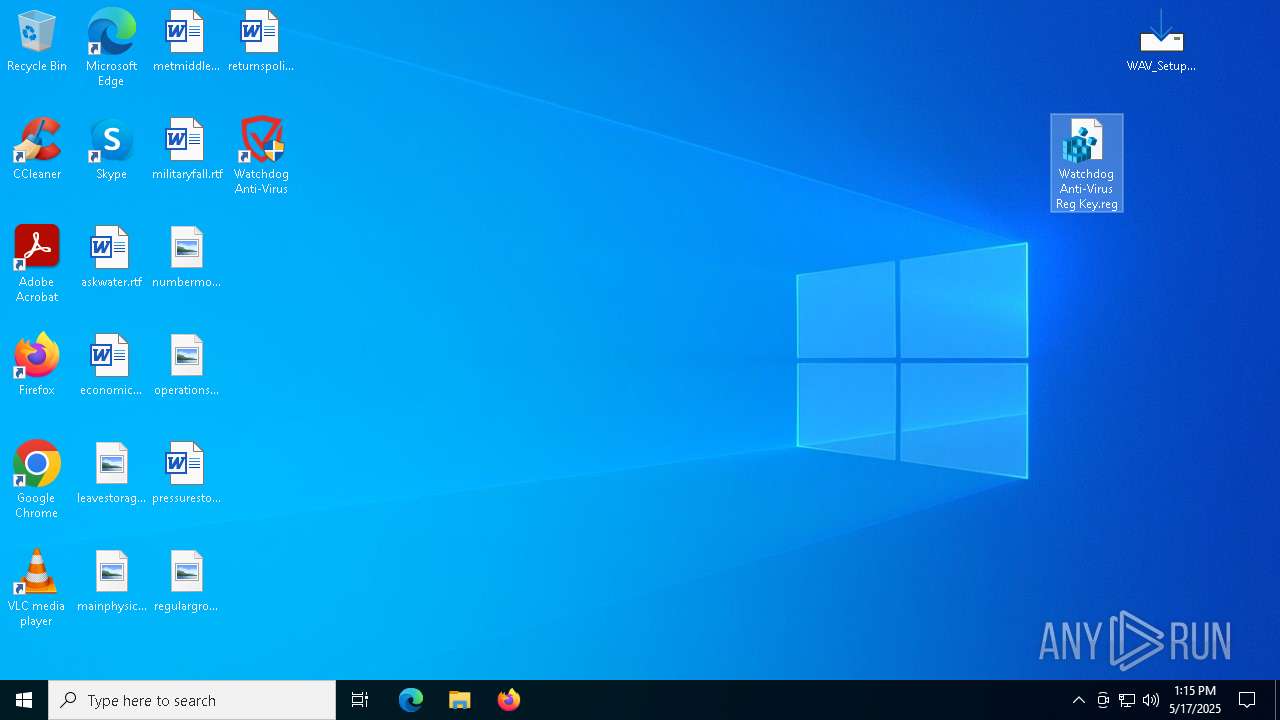
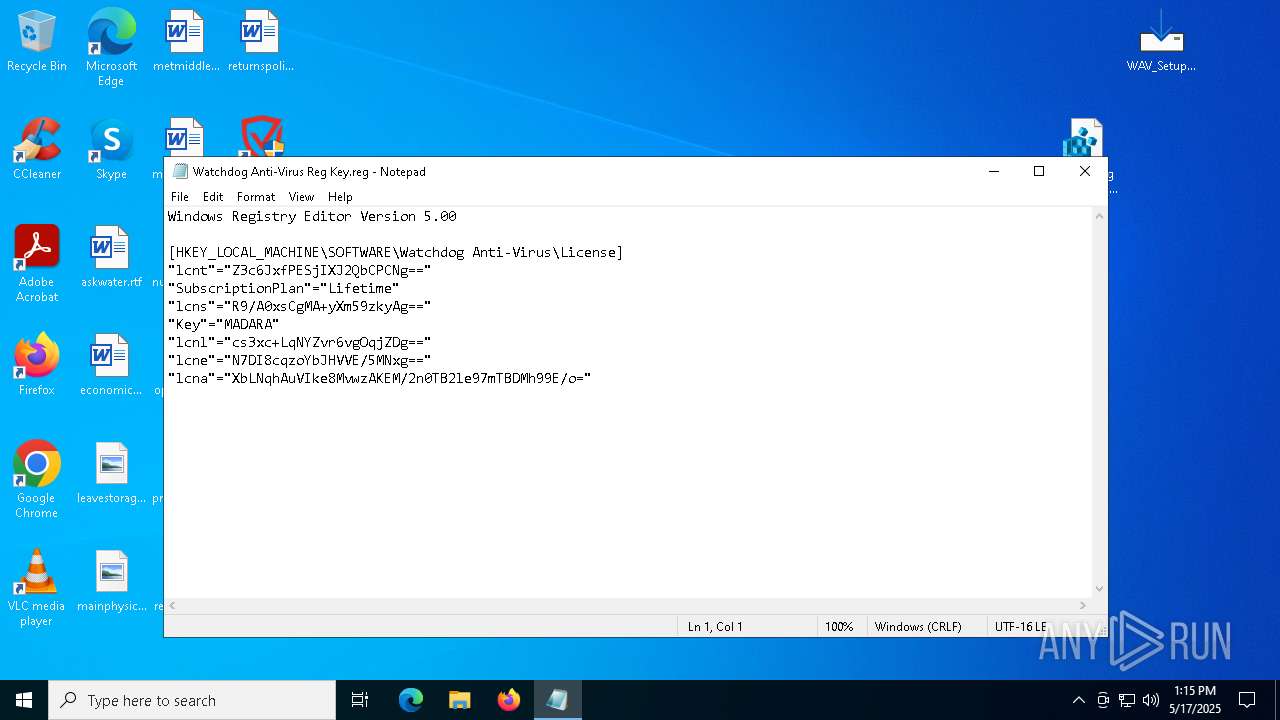
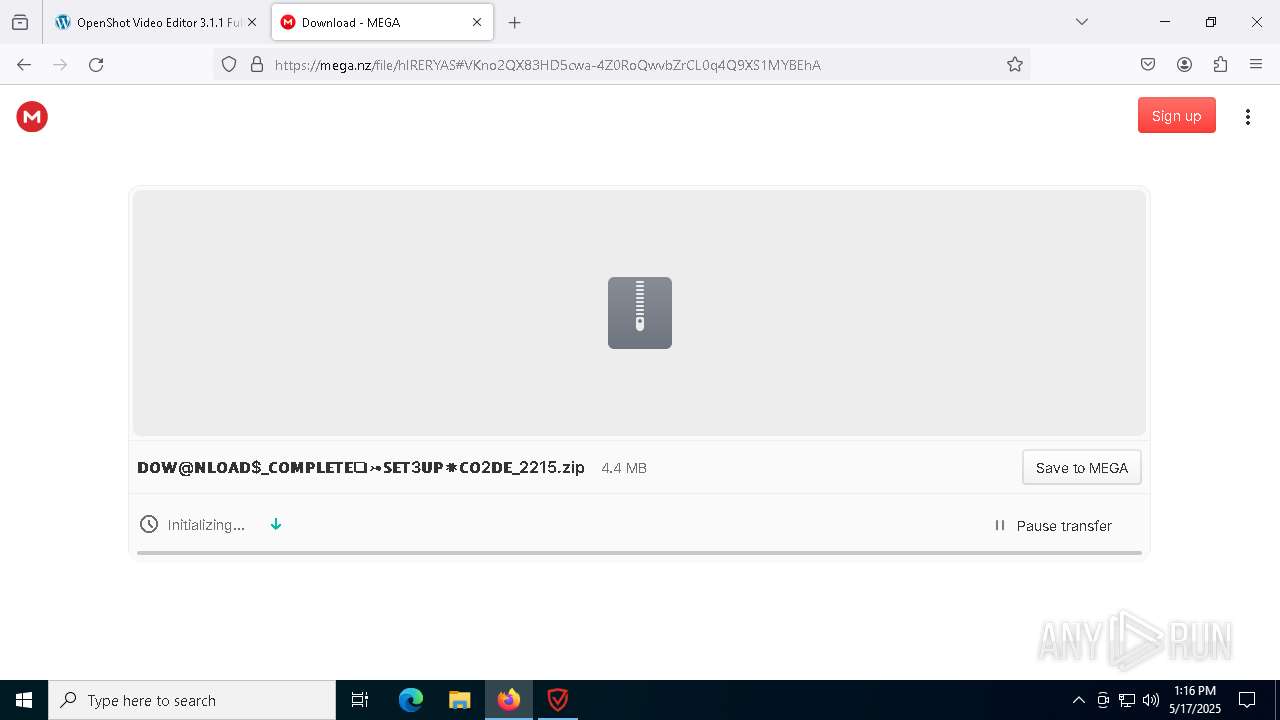
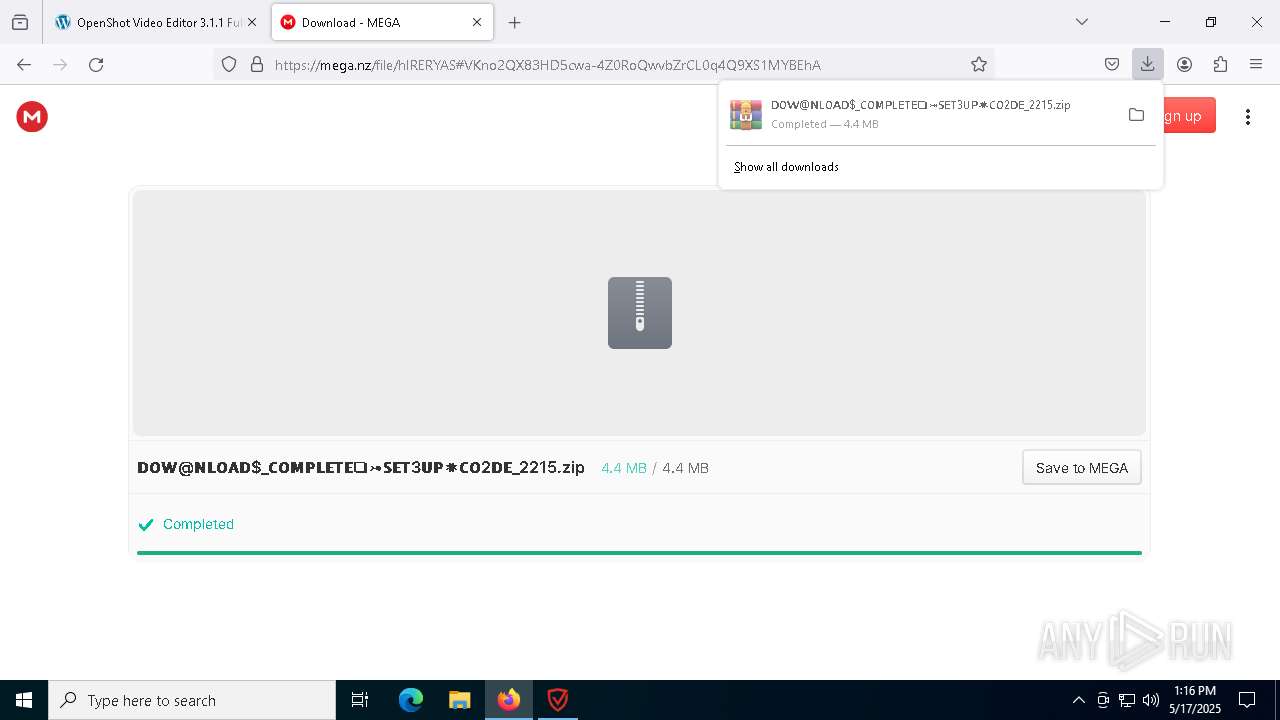
Manual execution by a user
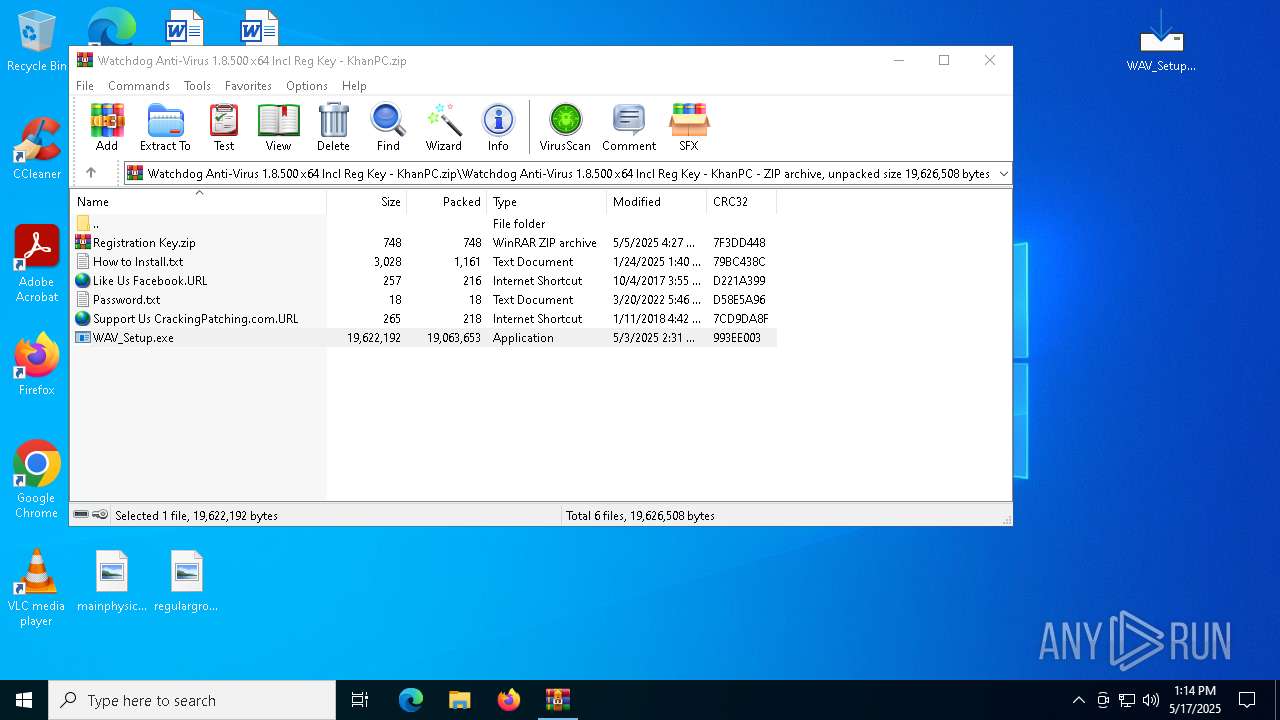
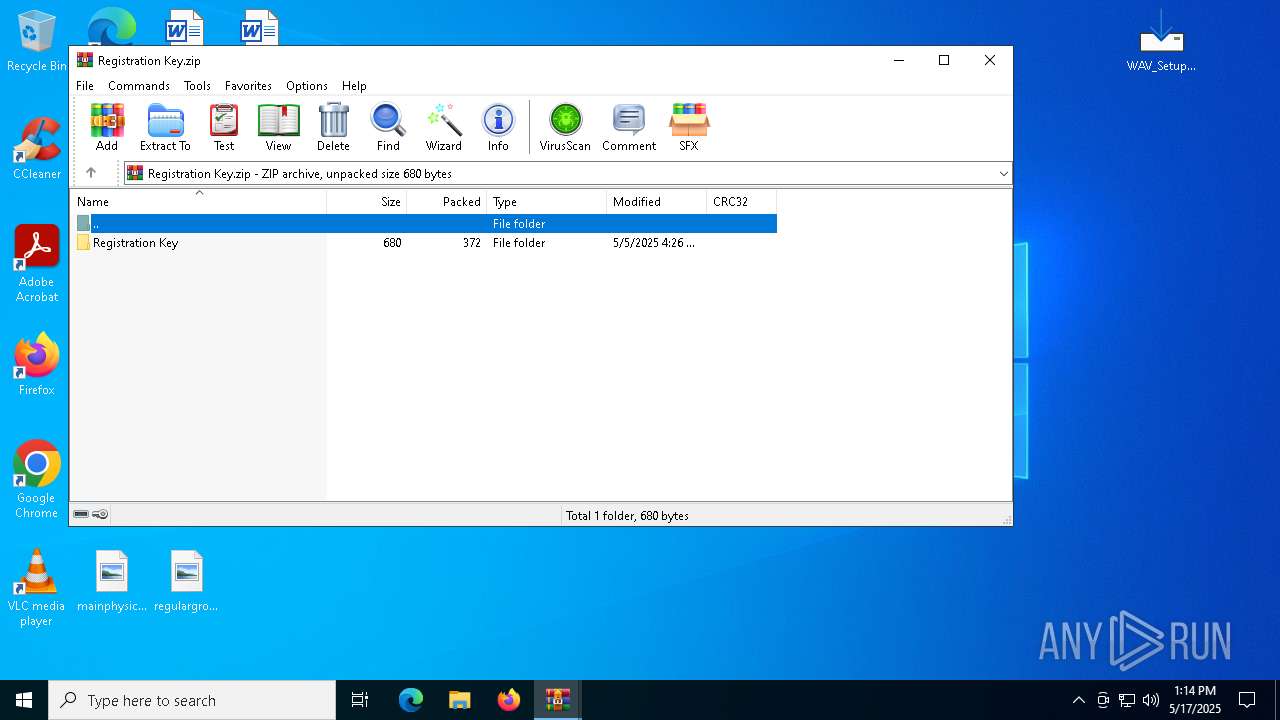
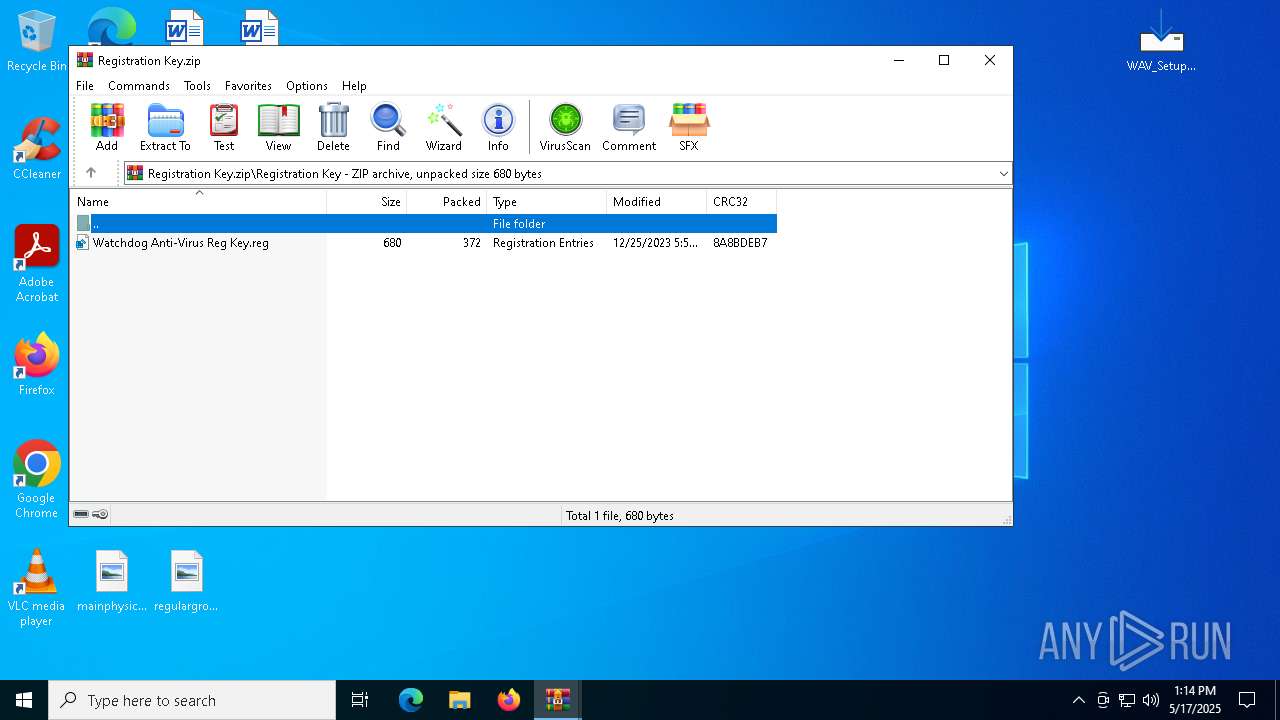
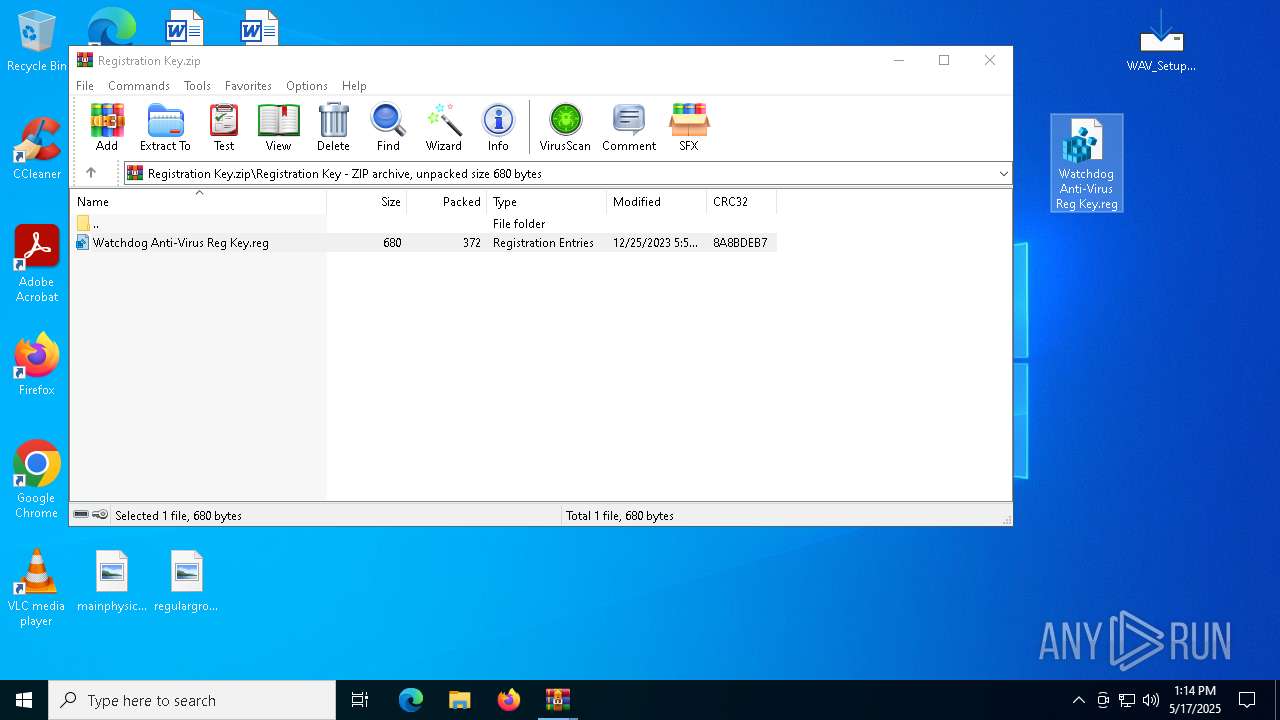
- WinRAR.exe (PID: 5548)
- WAV_Setup.exe (PID: 9136)
- regedit.exe (PID: 4920)
- regedit.exe (PID: 4448)
- WAV.exe (PID: 8308)
- firefox.exe (PID: 5056)
- WinRAR.exe (PID: 9212)
- WAV.exe (PID: 6436)
- notepad.exe (PID: 7584)
- setup.exe (PID: 2568)
- WAV.exe (PID: 6184)
Reads the software policy settings
- slui.exe (PID: 8144)
Checks supported languages
- WAV_Setup.exe (PID: 9136)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 5548)
Application launched itself
- firefox.exe (PID: 2568)
- firefox.exe (PID: 1276)
- firefox.exe (PID: 5056)
- firefox.exe (PID: 672)
Compiled with Borland Delphi (YARA)
- WAV_Setup.exe (PID: 9136)
- WAV_Setup.tmp (PID: 8388)
- WAV_Setup.exe (PID: 4000)
- WAV_Setup.tmp (PID: 5552)
Detects InnoSetup installer (YARA)
- WAV_Setup.tmp (PID: 8388)
- WAV_Setup.exe (PID: 9136)
- WAV_Setup.exe (PID: 4000)
- WAV_Setup.tmp (PID: 5552)
Create files in a temporary directory
- WAV_Setup.exe (PID: 9136)
The sample compiled with english language support
- dotnet.exe (PID: 8504)
- WAV_Setup.tmp (PID: 5552)
- dotnet-runtime-8.0.0-win-x64.exe (PID: 4200)
- msiexec.exe (PID: 6972)
- rundll32.exe (PID: 1600)
- setup.exe (PID: 2568)
- DistriCompiler89.exe (PID: 896)
Executes as Windows Service
- elevation_service.exe (PID: 9204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
237
Monitored processes
99
Malicious processes
10
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 644 | C:\Windows\syswow64\MsiExec.exe -Embedding 77D2E2DA8B36A8F9618F1FDA27451DFC | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4500 -childID 10 -isForBrowser -prefsHandle 6068 -prefMapHandle 6000 -prefsLen 31321 -prefMapSize 244583 -jsInitHandle 1456 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {e69ac159-c94d-4805-ae8b-c6002b3135d0} 672 "\\.\pipe\gecko-crash-server-pipe.672" 206248d3850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 672 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 896 | C:\ProgramData\Iaclientv2\DistriCompiler89.exe | C:\ProgramData\Iaclientv2\DistriCompiler89.exe | DistriCompiler89.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
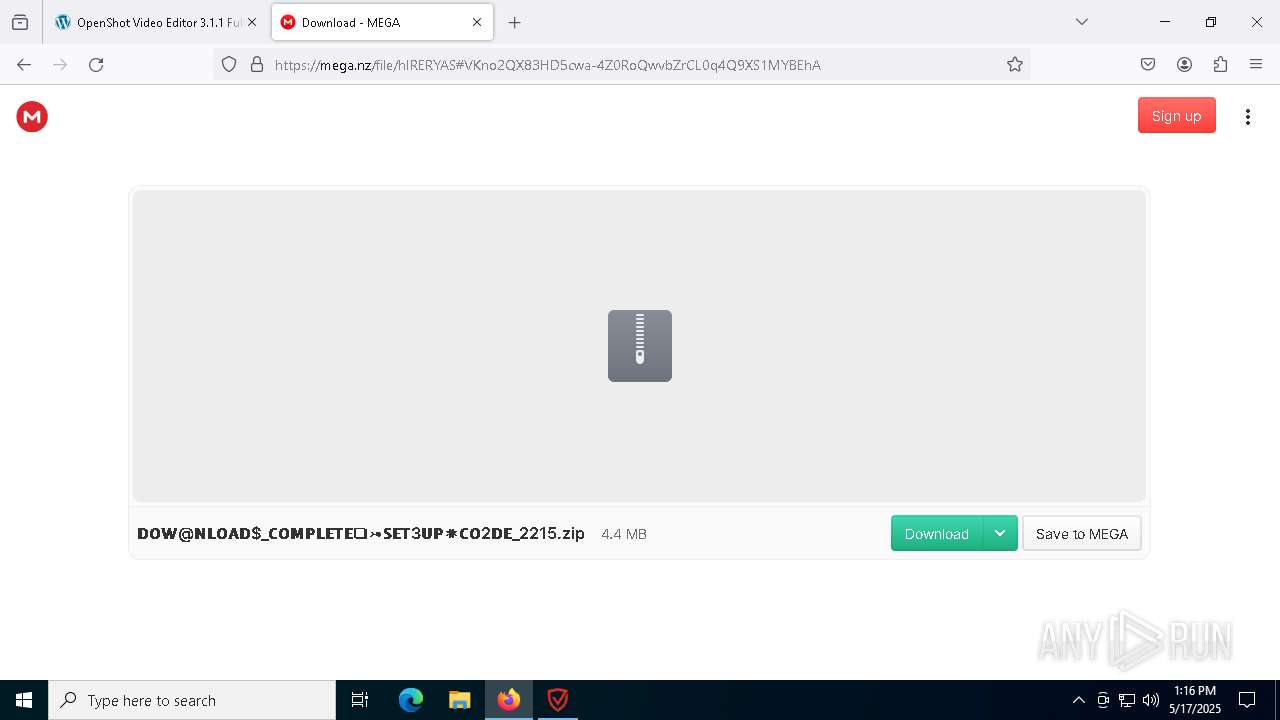
| 1056 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa9212.12733\𝗗𝗢𝗪@𝗡𝗟𝗢𝗔𝗗$_𝗖𝗢𝗠𝗣𝗟𝗘𝗧𝗘❏⤖𝗦𝗘𝗧3𝗨𝗣✷𝗖𝗢2𝗗𝗘#$!.7z | C:\Program Files\WinRAR\WinRAR.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Mozilla Firefox\firefox.exe" "crackingpatching.com" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6064 -childID 16 -isForBrowser -prefsHandle 6012 -prefMapHandle 6008 -prefsLen 31324 -prefMapSize 244583 -jsInitHandle 1284 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d4a3f5ad-575e-4a49-aced-e3b4d4d640f8} 2568 "\\.\pipe\gecko-crash-server-pipe.2568" 1f39d821310 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
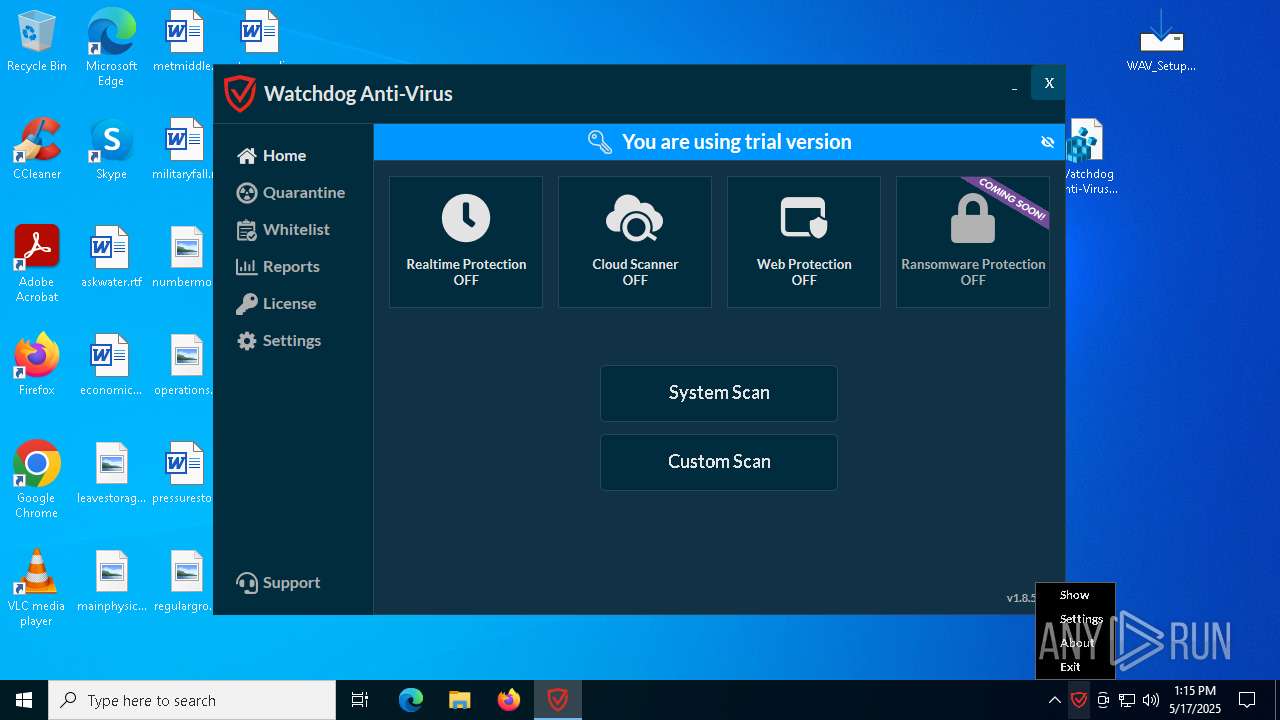
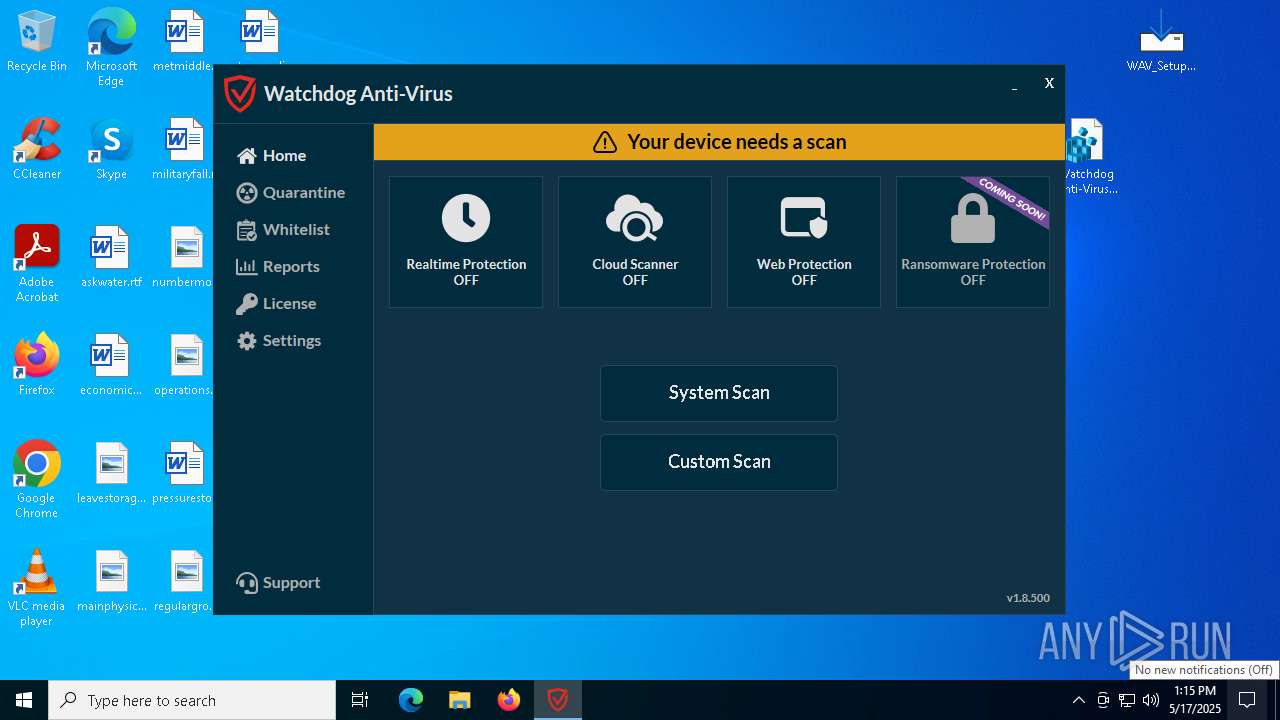
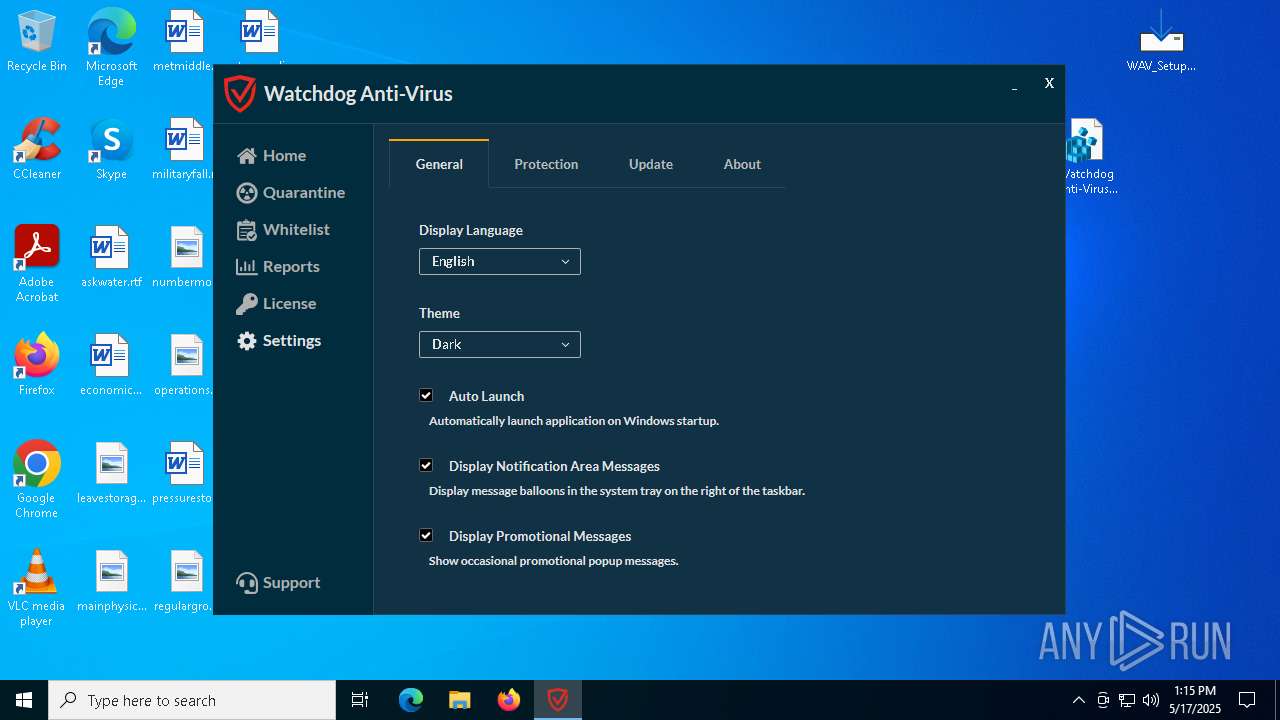
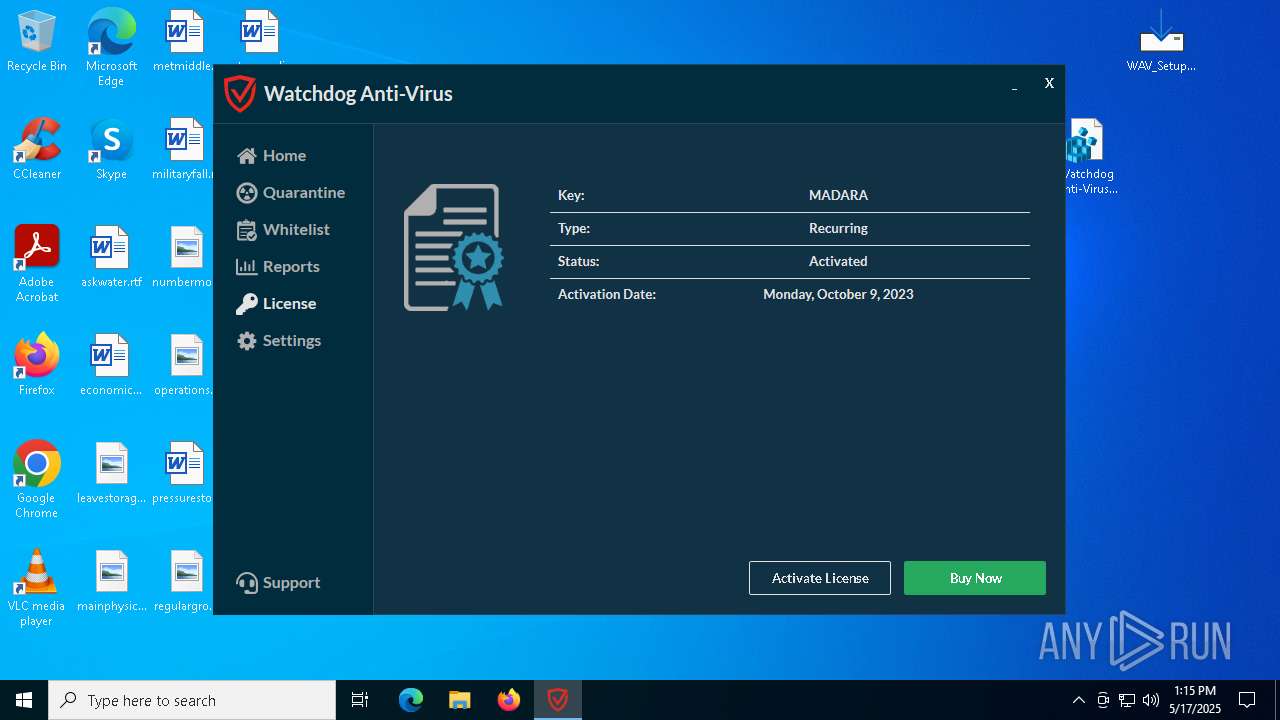
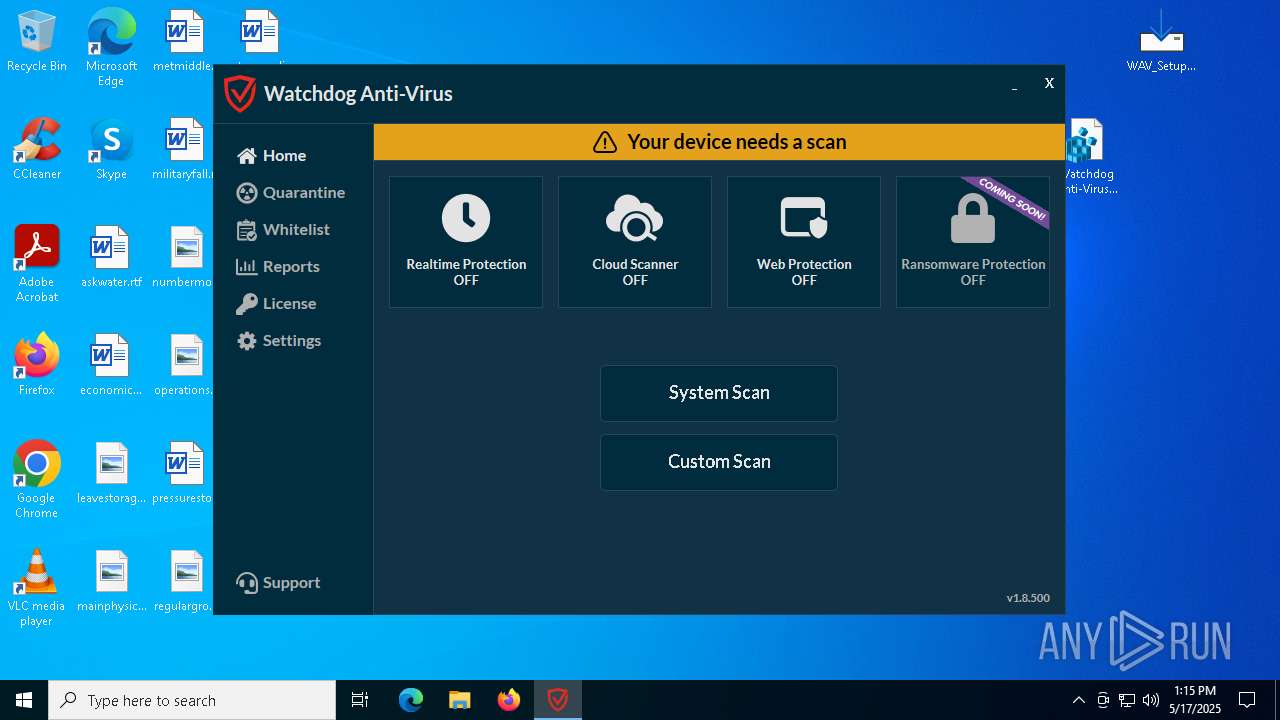
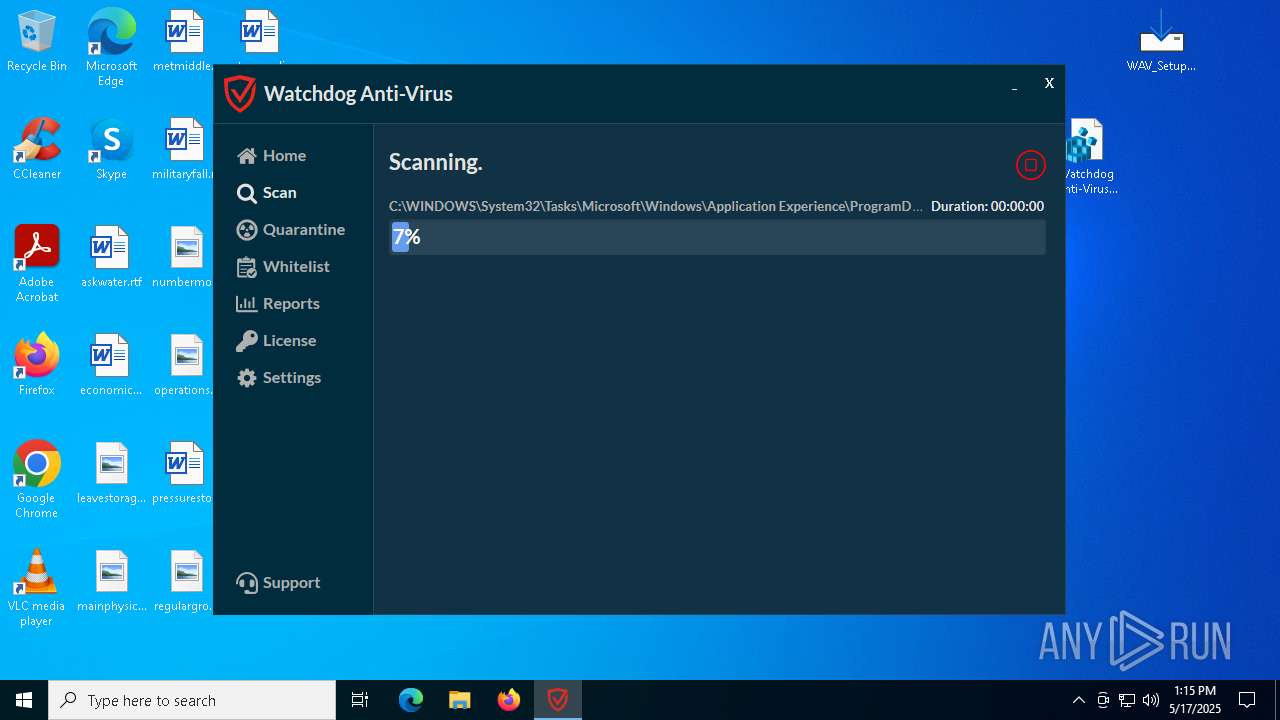
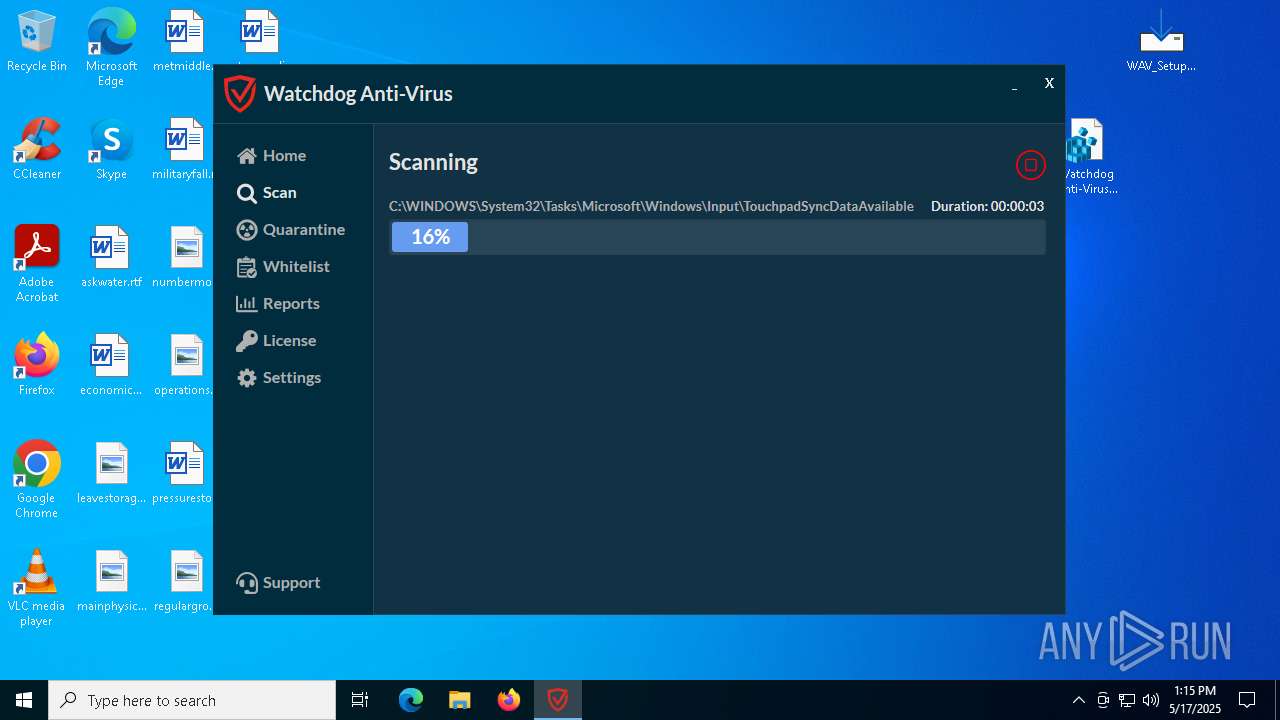
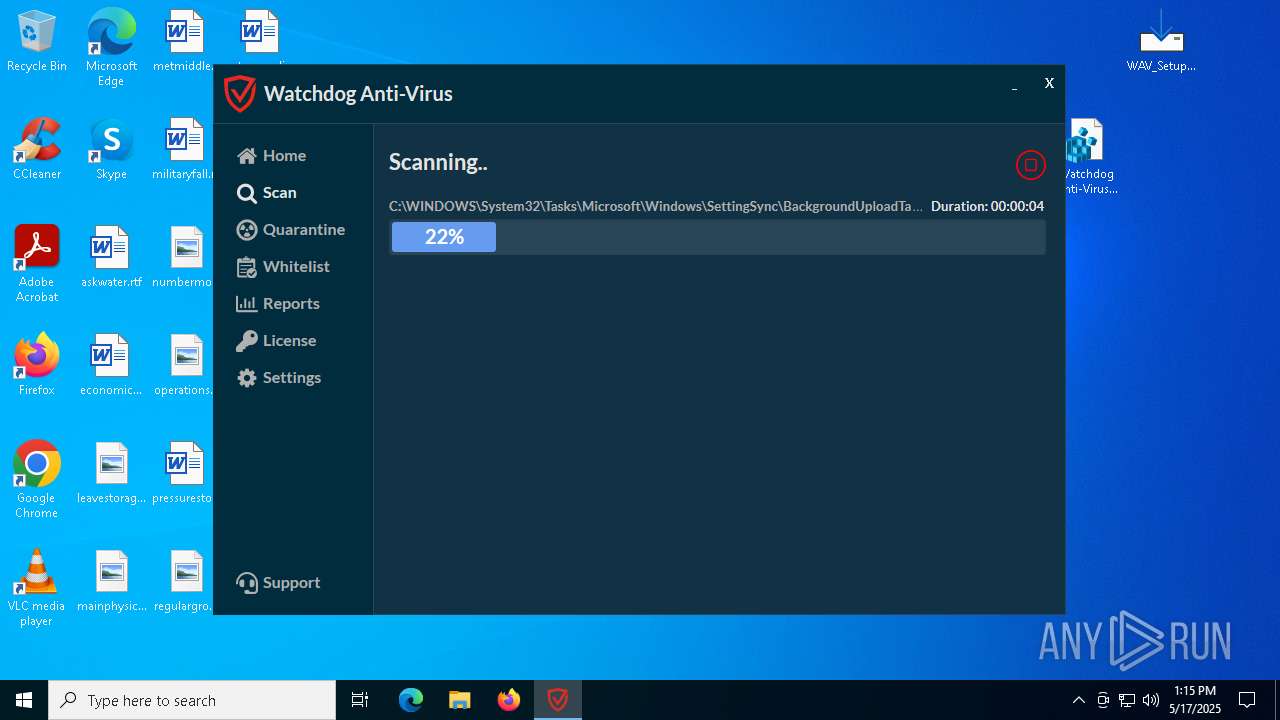
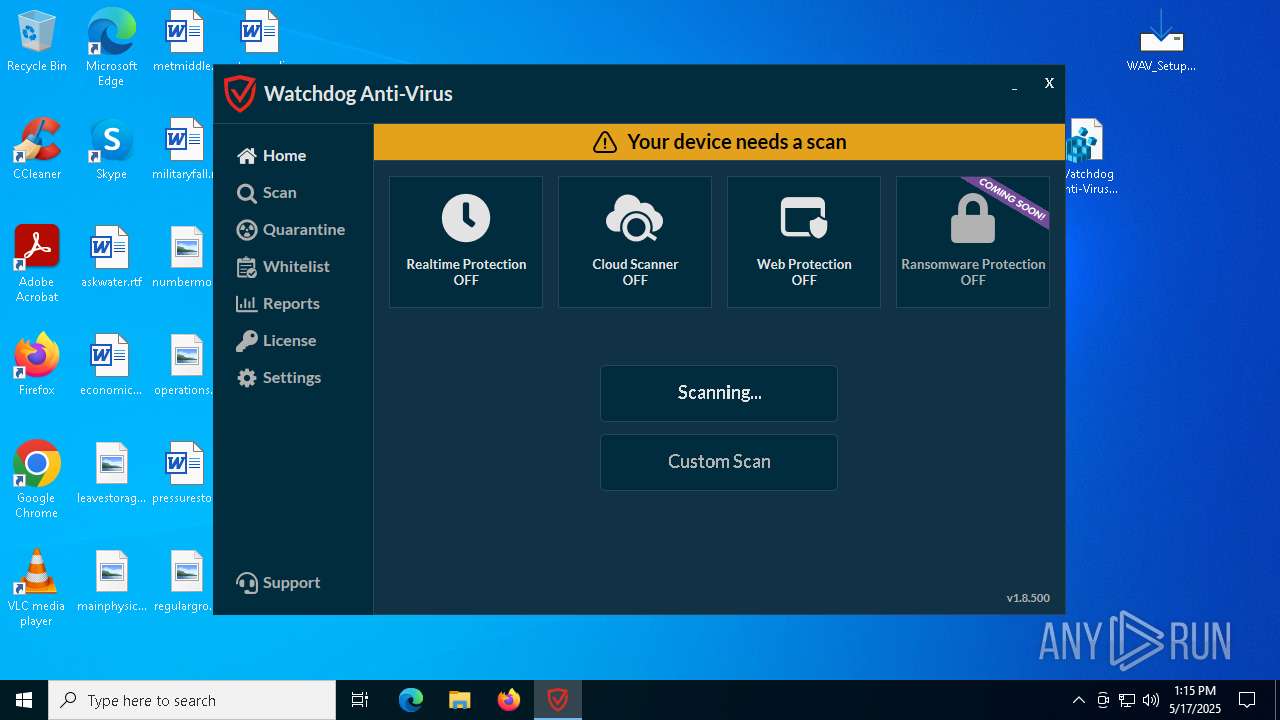
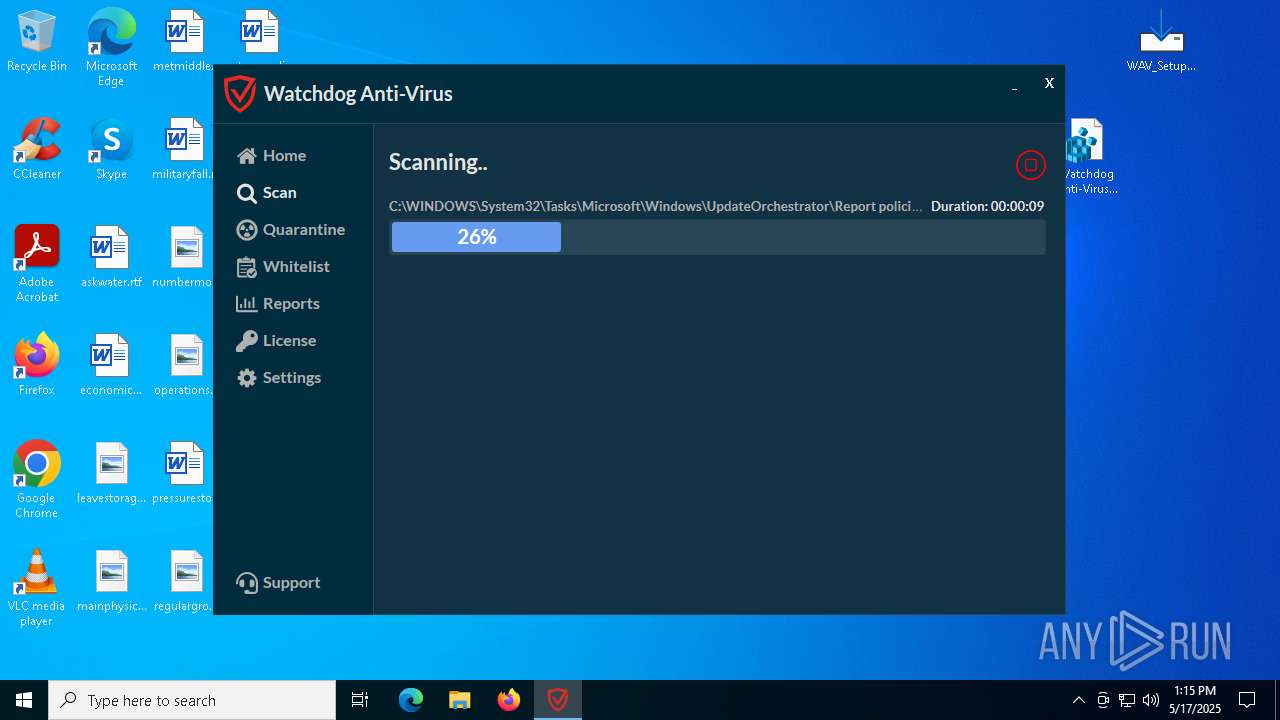
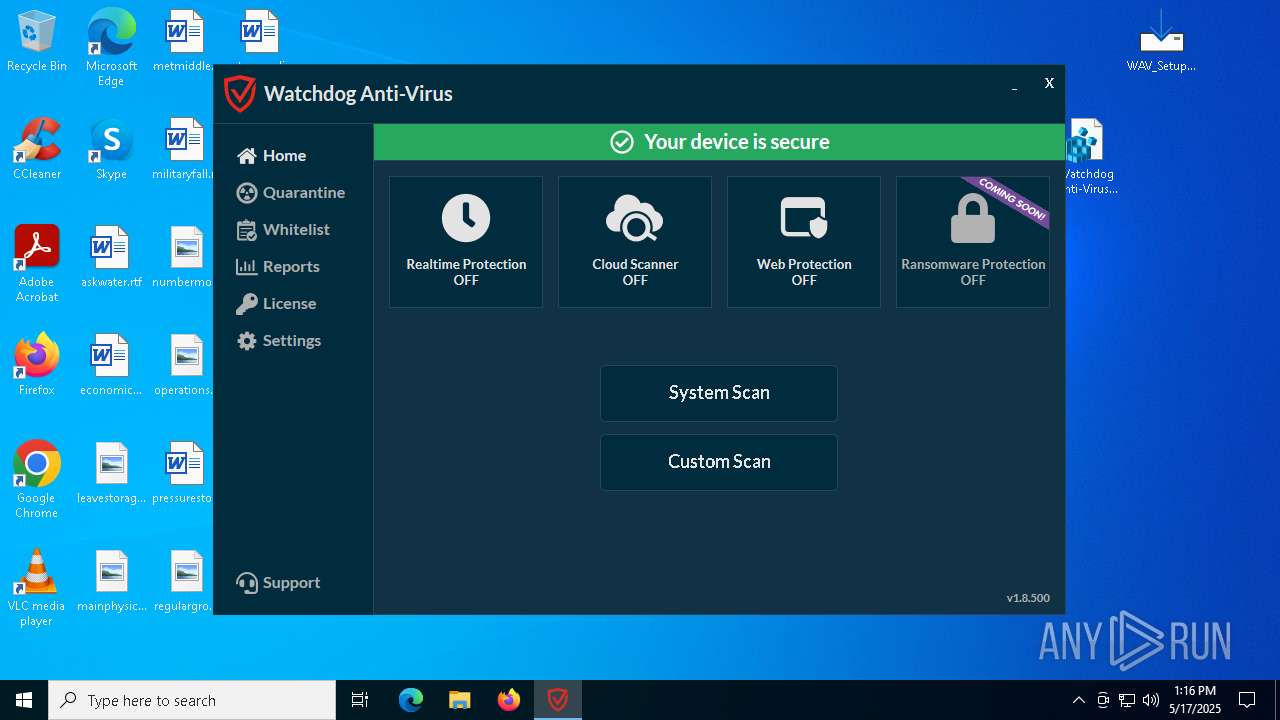
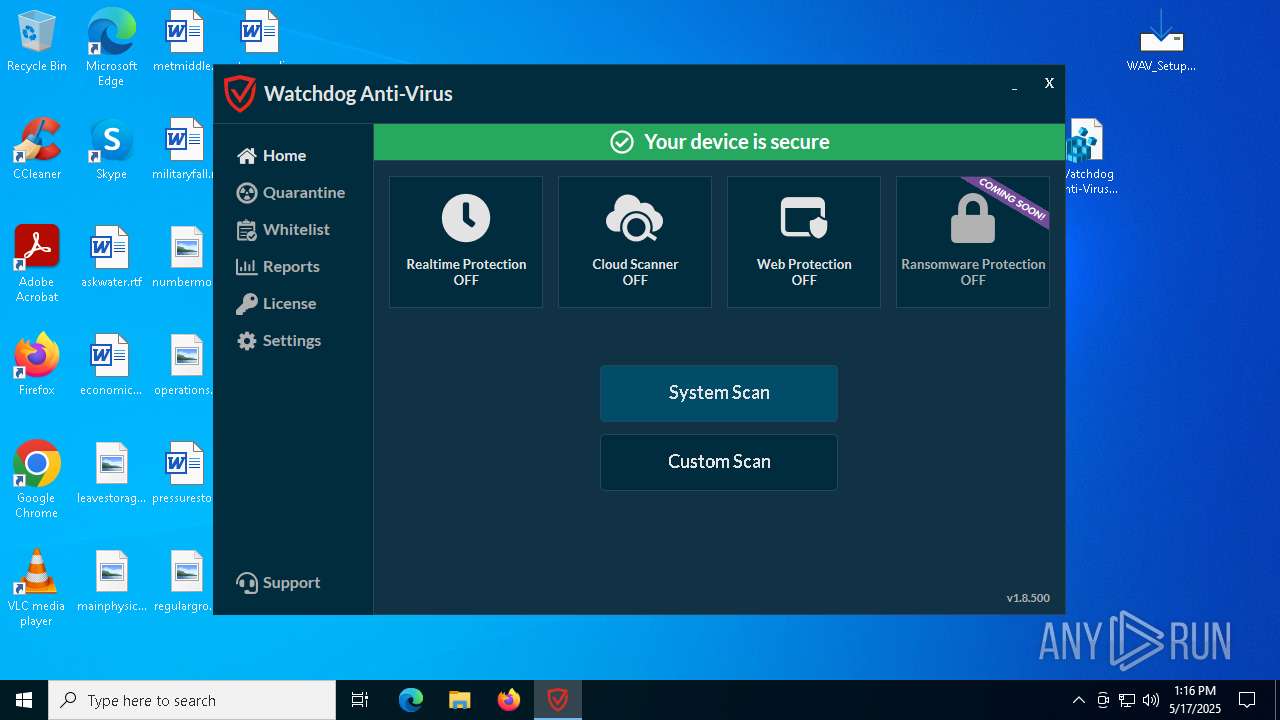
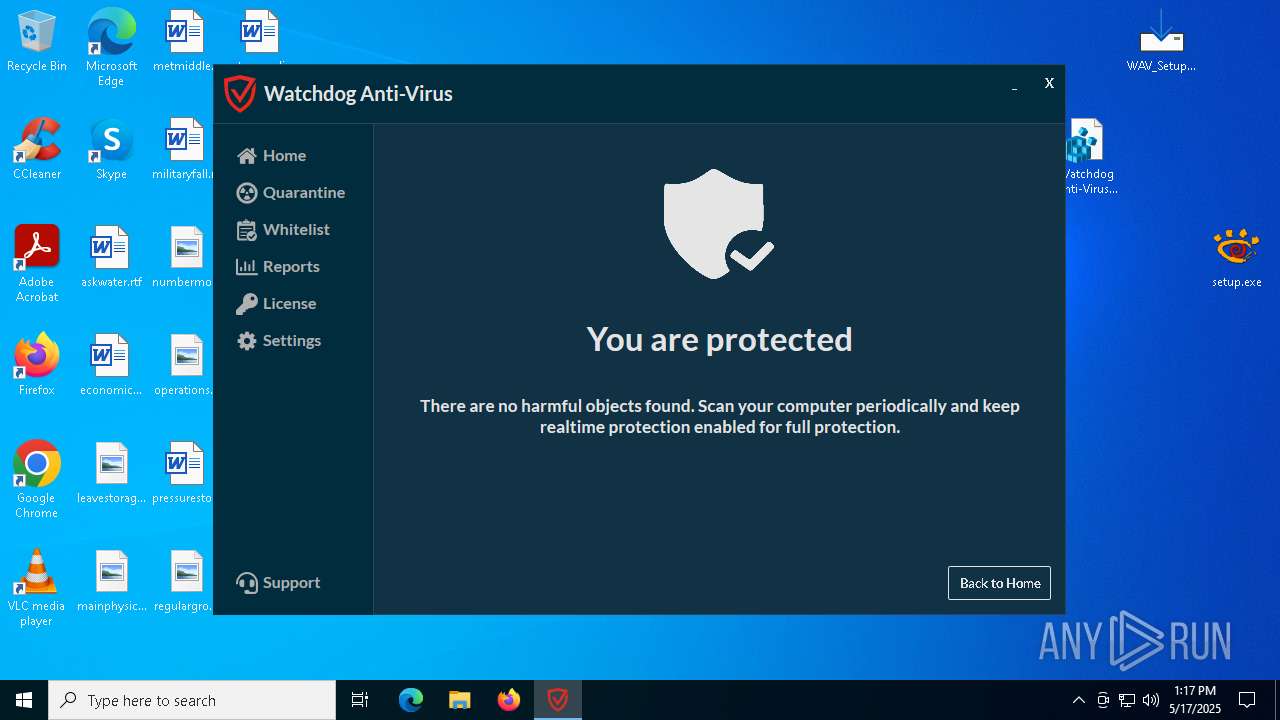
| 1600 | "rundll32" "C:\Program Files (x86)\Watchdog Anti-Virus\wsdk-antivirus.dll",wsdk_install true | C:\Windows\System32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2084 | C:\WINDOWS\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\WINDOWS\system32\cmd.exe" /C dotnet --list-runtimes > "C:\Users\admin\AppData\Local\Temp\is-1D8MT.tmp\dotnet.txt" 2>&1 | C:\Windows\SysWOW64\cmd.exe | — | WAV_Setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
101 658
Read events
100 814
Write events
760
Delete events
84
Modification events
| (PID) Process: | (2568) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
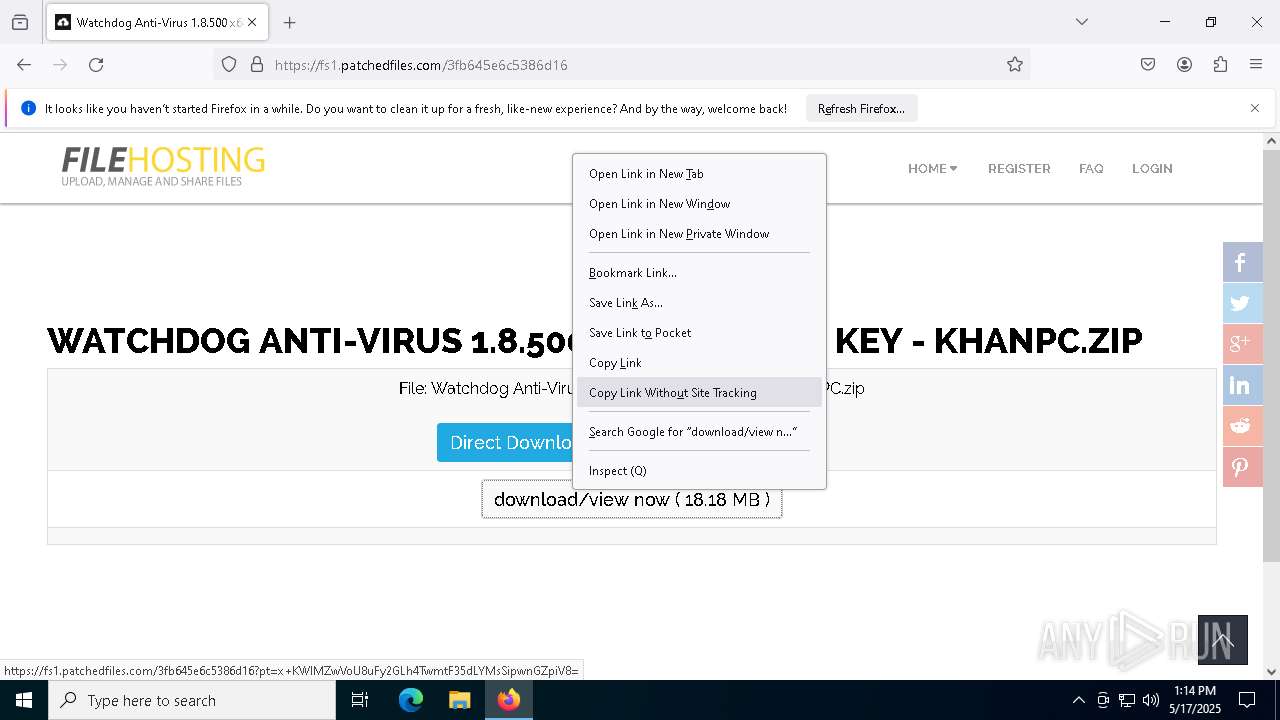
Value: C:\Users\admin\Downloads\Watchdog Anti-Virus 1.8.500 x64 Incl Reg Key - KhanPC.zip | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5548) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (9156) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
322
Suspicious files
685
Text files
582
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:04357F6A5979BAFB4C29440488A95080 | SHA256:FF99165E45C97F1C8C5623835134D9017000A732EBB212E14E36133EA3F69269 | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:3B156E12141F8CBCE9D60CDCE2077617 | SHA256:E6287E44B44ABEA20E1B2E3F415D22B9E5E5FBBC155AD9DADBABA63951B2AF6F | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | binary | |
MD5:0796D30A5568EAA5A3F67FFCEACFF50E | SHA256:43B94ED4D73E5DEB907767E78E3F7276A226B8A53D0157B17732A9575A0ACAD1 | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-child-current.bin | binary | |
MD5:C95DDC2B1A525D1A243E4C294DA2F326 | SHA256:3A5919E086BFB31E36110CF636D2D5109EB51F2C410B107F126126AB25D67363 | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db-journal | binary | |
MD5:2F5800B25E9C8CB9C34BB9154A59A2CF | SHA256:AE3978E47BD8A98D1EAC36BA387CC7112223CBAADBEA7F450AF74A80F4E9EB30 | |||
| 2568 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
90
TCP/UDP connections
339
DNS requests
306
Threats
35
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2568 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2568 | firefox.exe | GET | 301 | 104.21.112.1:80 | http://crackingpatching.com/ | unknown | — | — | unknown |
2568 | firefox.exe | POST | — | 142.250.185.99:80 | http://o.pki.goog/s/wr3/3H4 | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 184.24.77.79:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 184.24.77.46:80 | http://e5.o.lencr.org/ | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 184.24.77.46:80 | http://e5.o.lencr.org/ | unknown | — | — | whitelisted |
2568 | firefox.exe | POST | 200 | 142.250.185.99:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2568 | firefox.exe | 104.21.112.1:80 | crackingpatching.com | CLOUDFLARENET | — | unknown |
2568 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
2568 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
2568 | firefox.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crackingpatching.com |
| unknown |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2560 | WAV.exe | A Network Trojan was detected | ET WEB_CLIENT DRIVEBY GENERIC ShellExecute in Hex No Seps |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
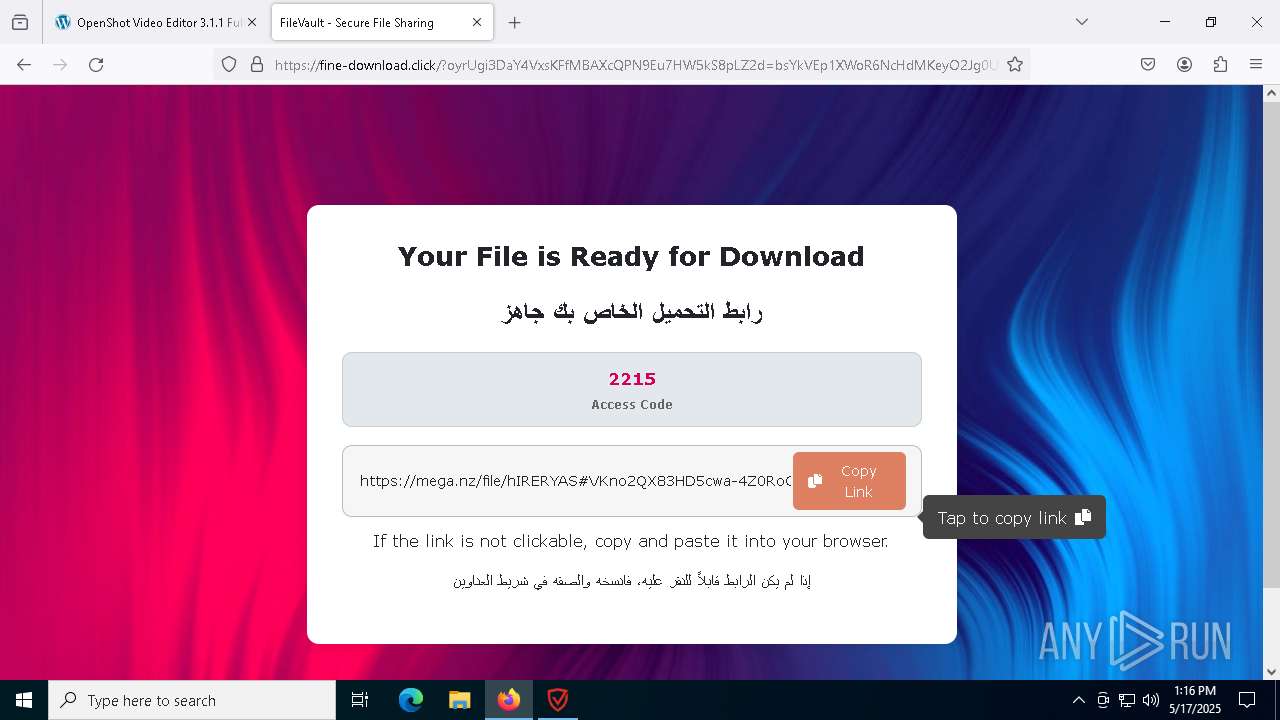
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |