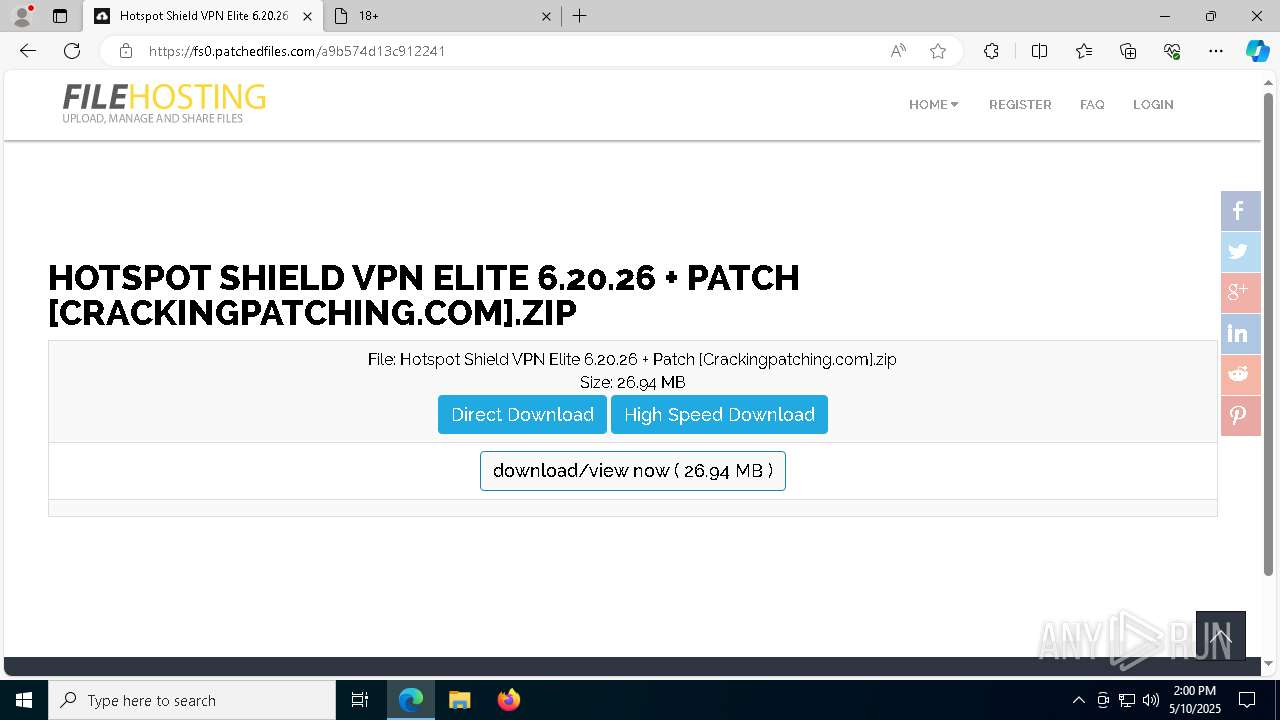
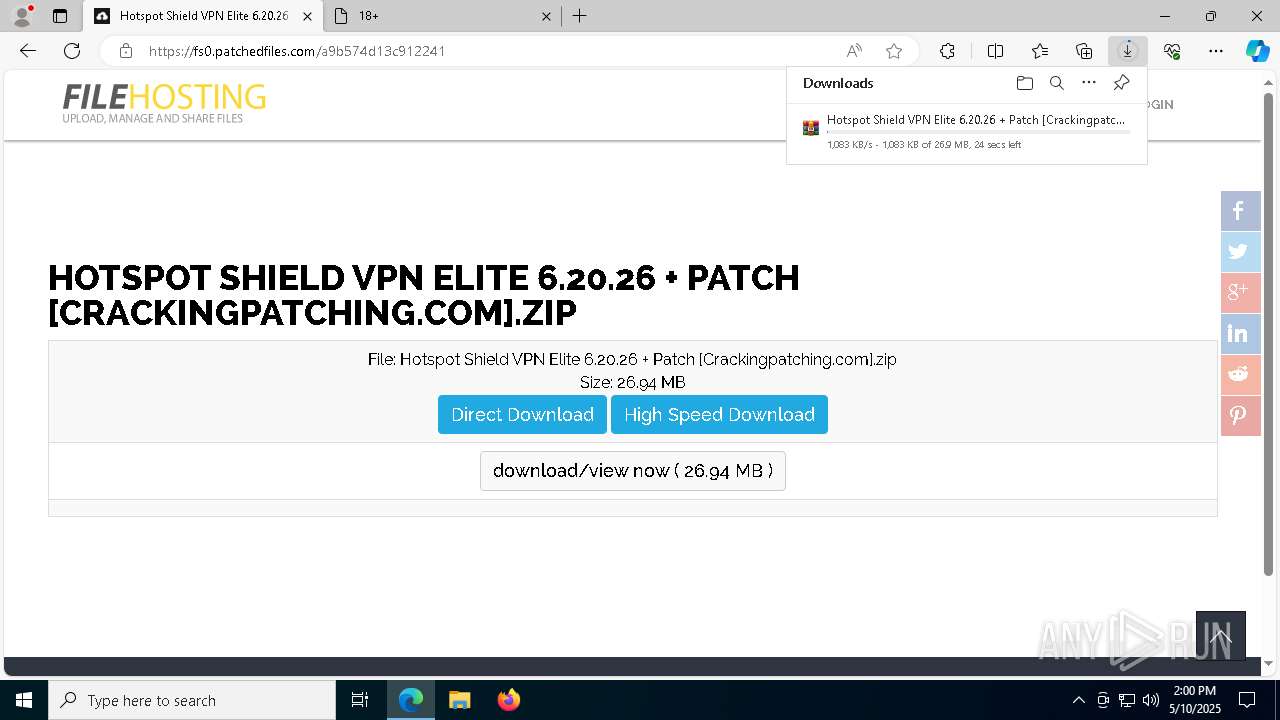
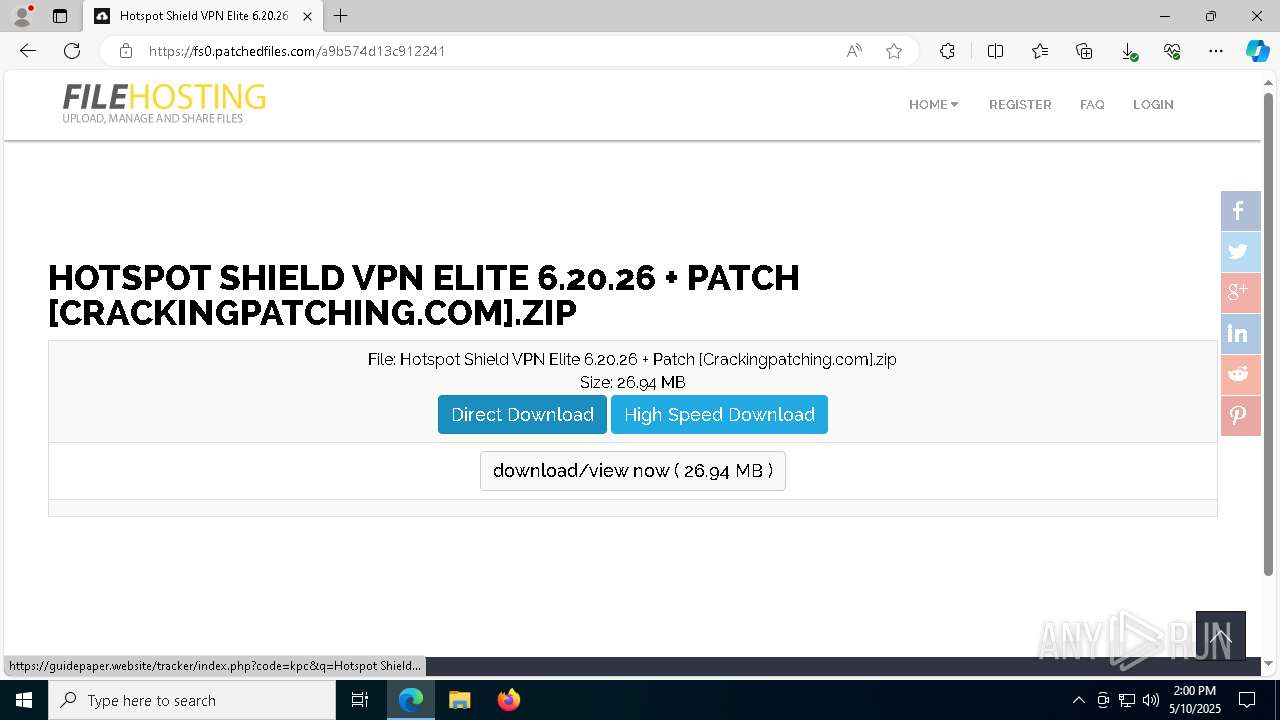
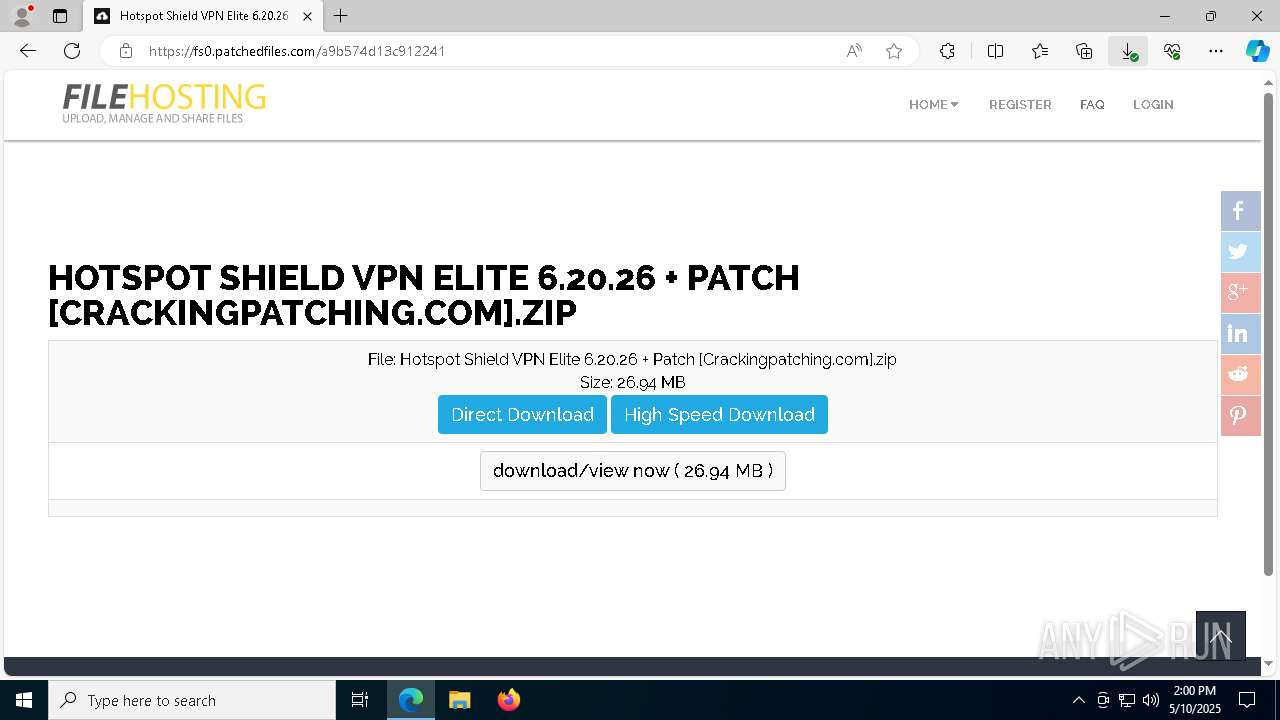
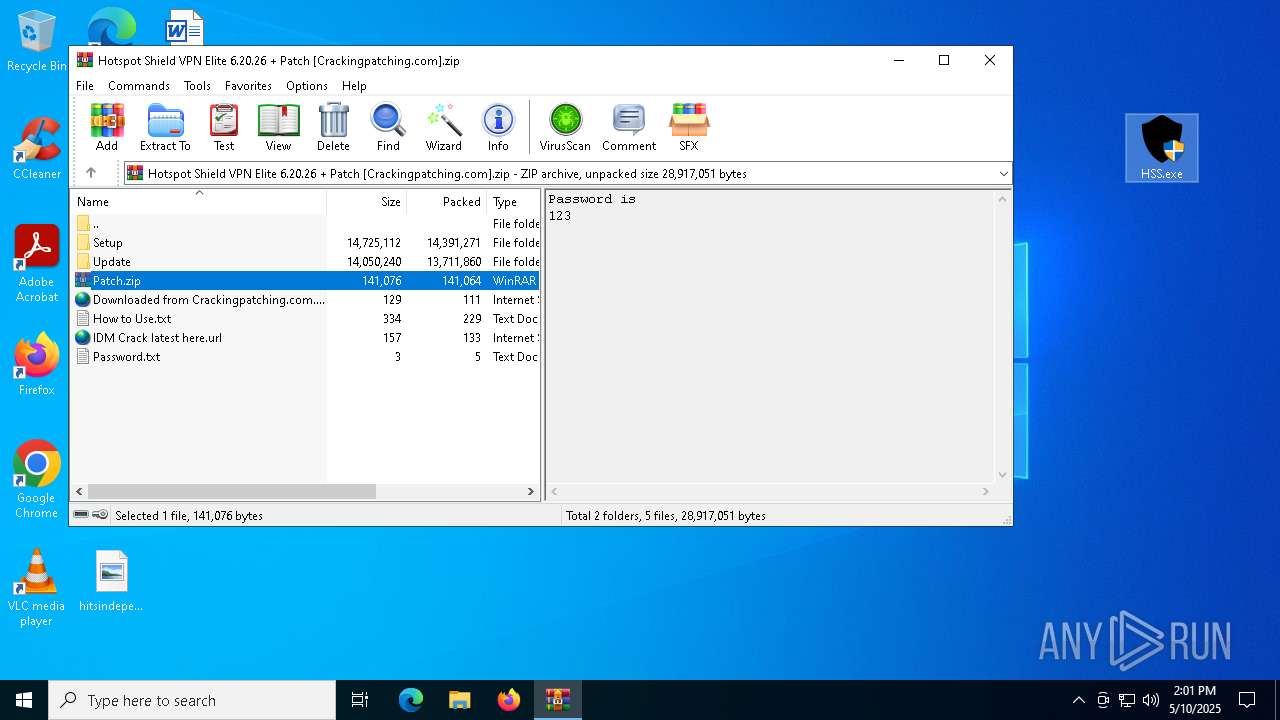
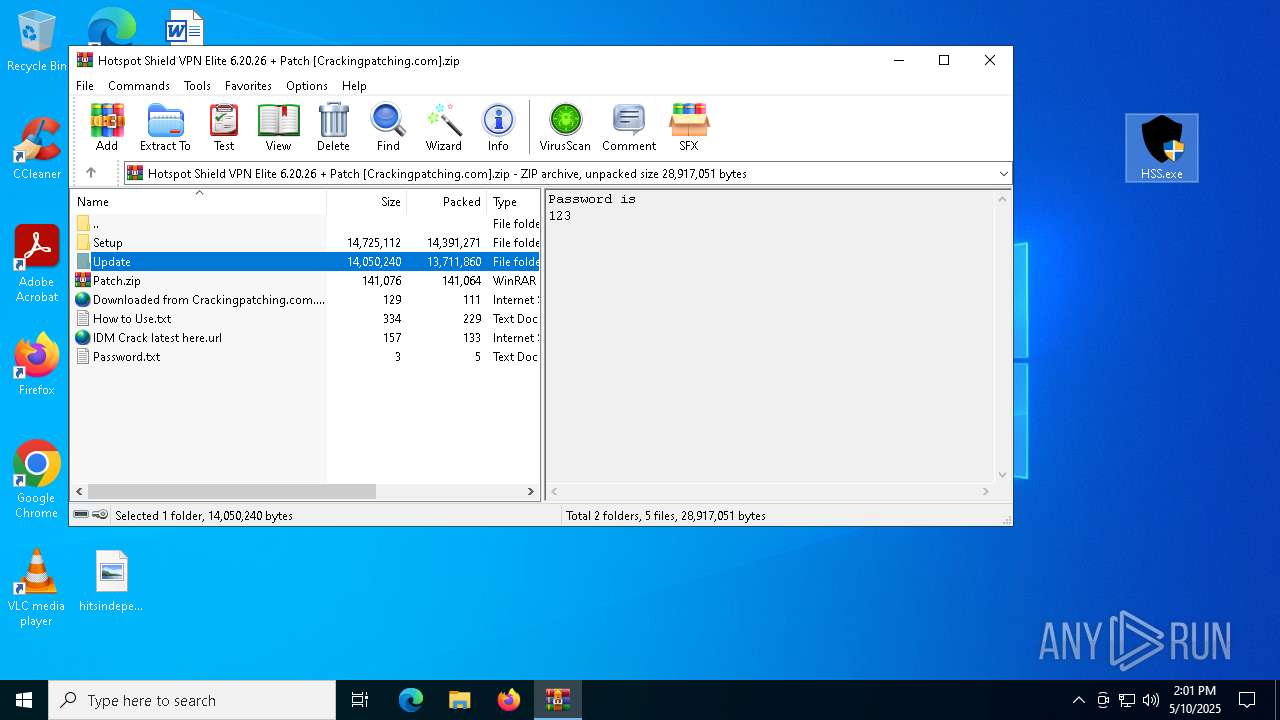
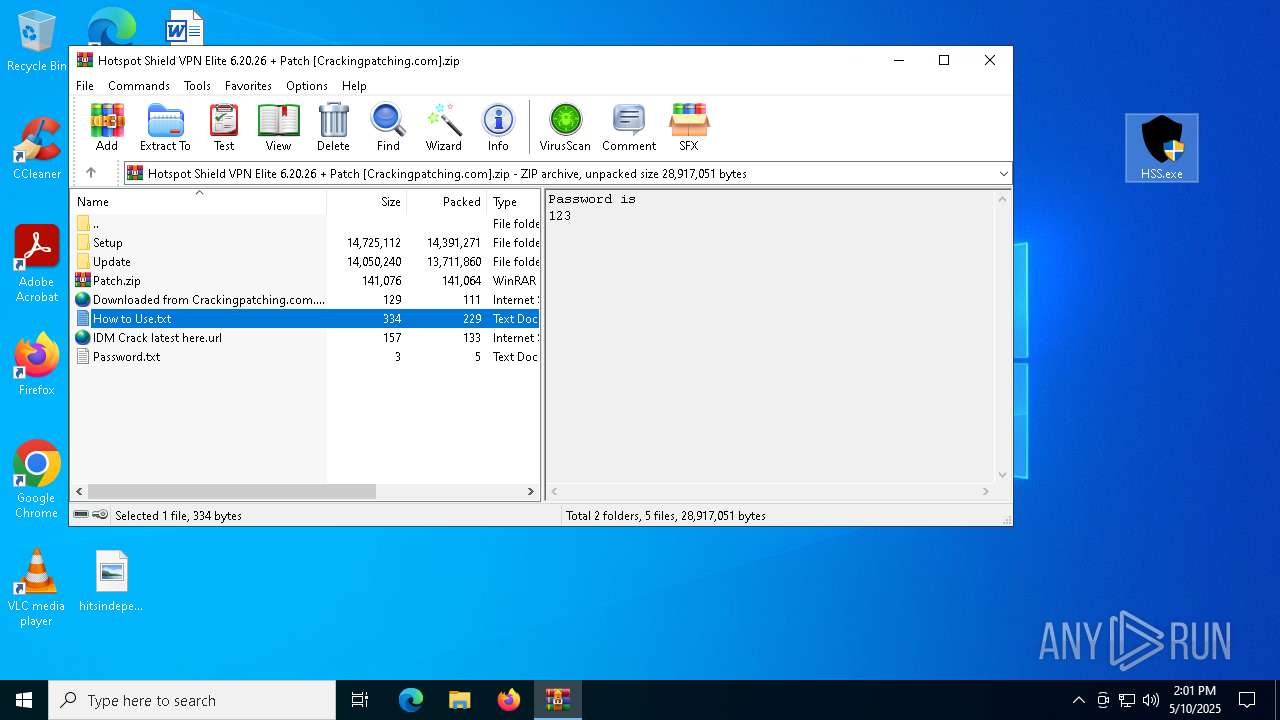
| URL: | crackingpatching.com |
| Full analysis: | https://app.any.run/tasks/88ee359c-1360-404e-9f1c-751b10d66490 |
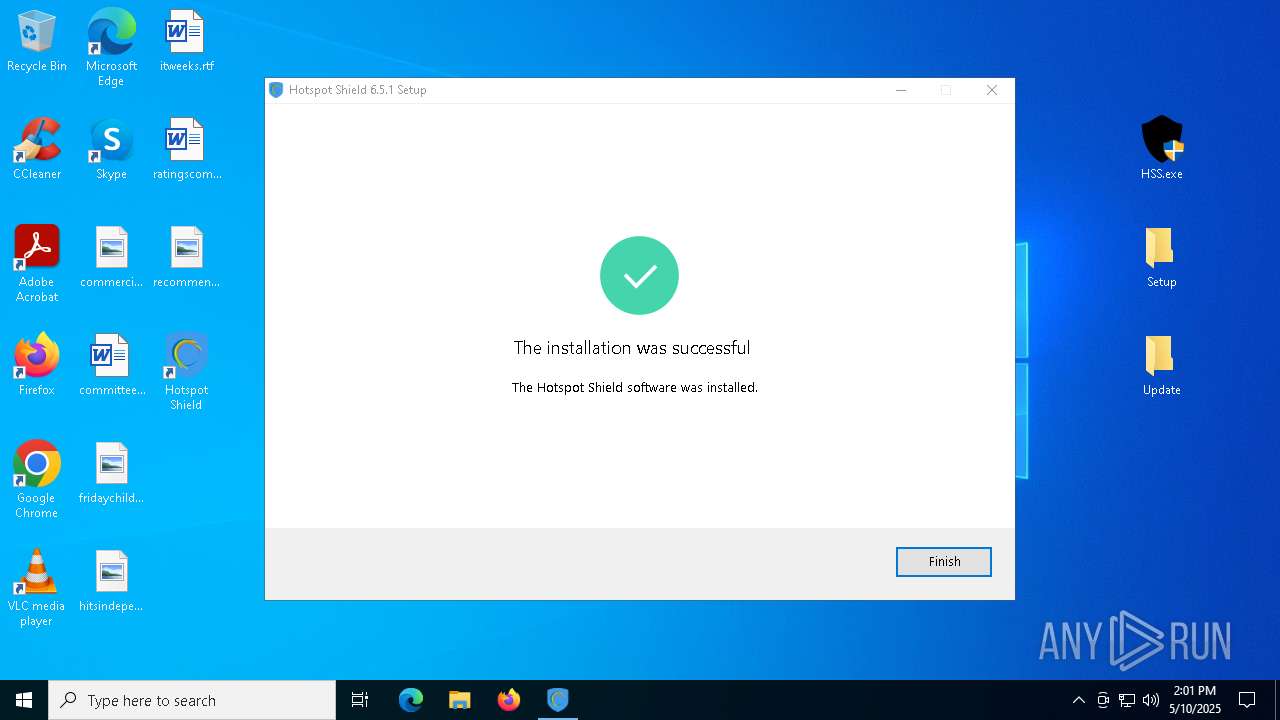
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 13:59:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
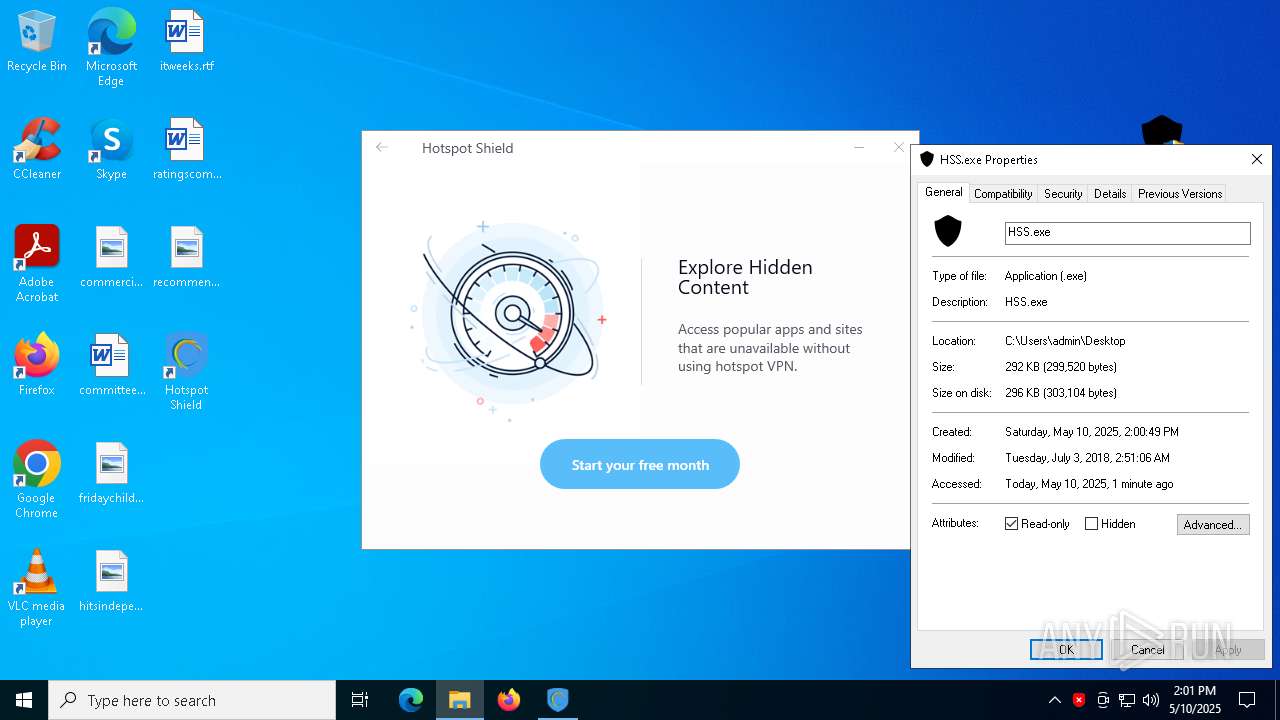
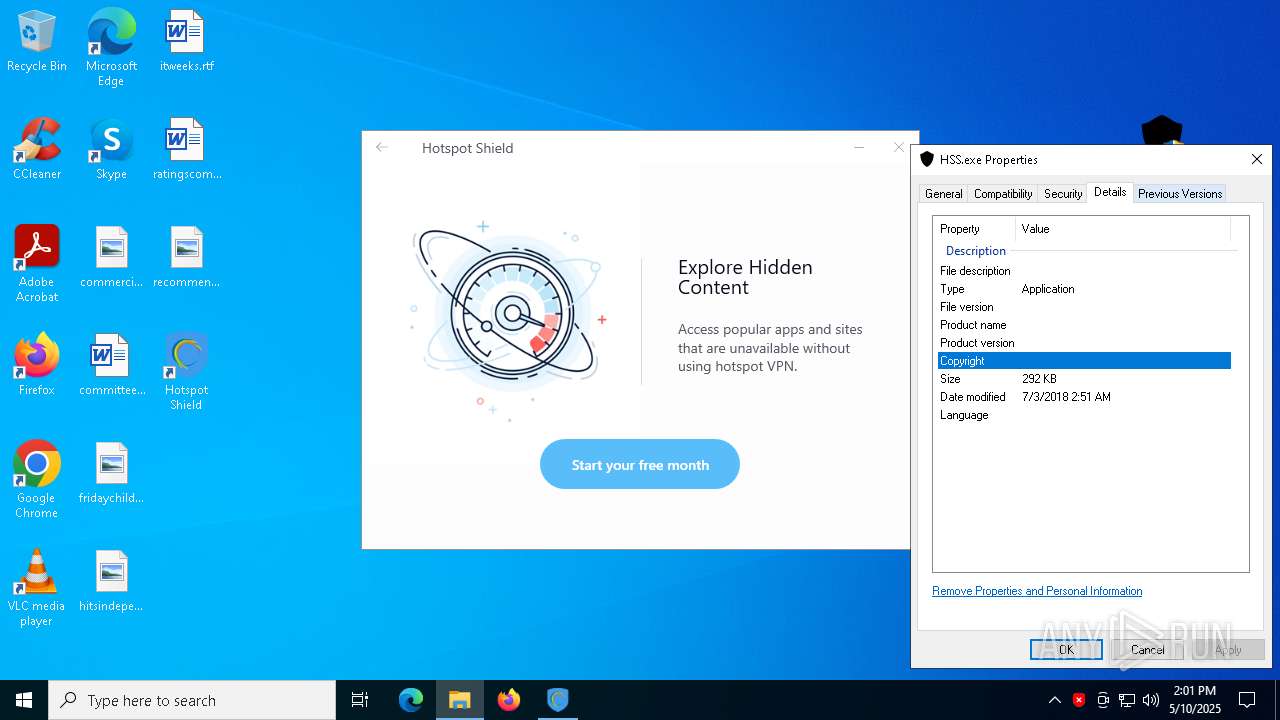
| MD5: | D8EAB3CC4D7E149DF62F939DE677EBFB |
| SHA1: | FEE2A3103C3E61495956E0018ECCA9E2A0A5D89F |
| SHA256: | 485B9C11039F3B7DBF372185D1F862656BA8D2E5BCFB660B396B9DB30CA59D5E |
| SSDEEP: | 3:oLW5K7T:v5K7T |
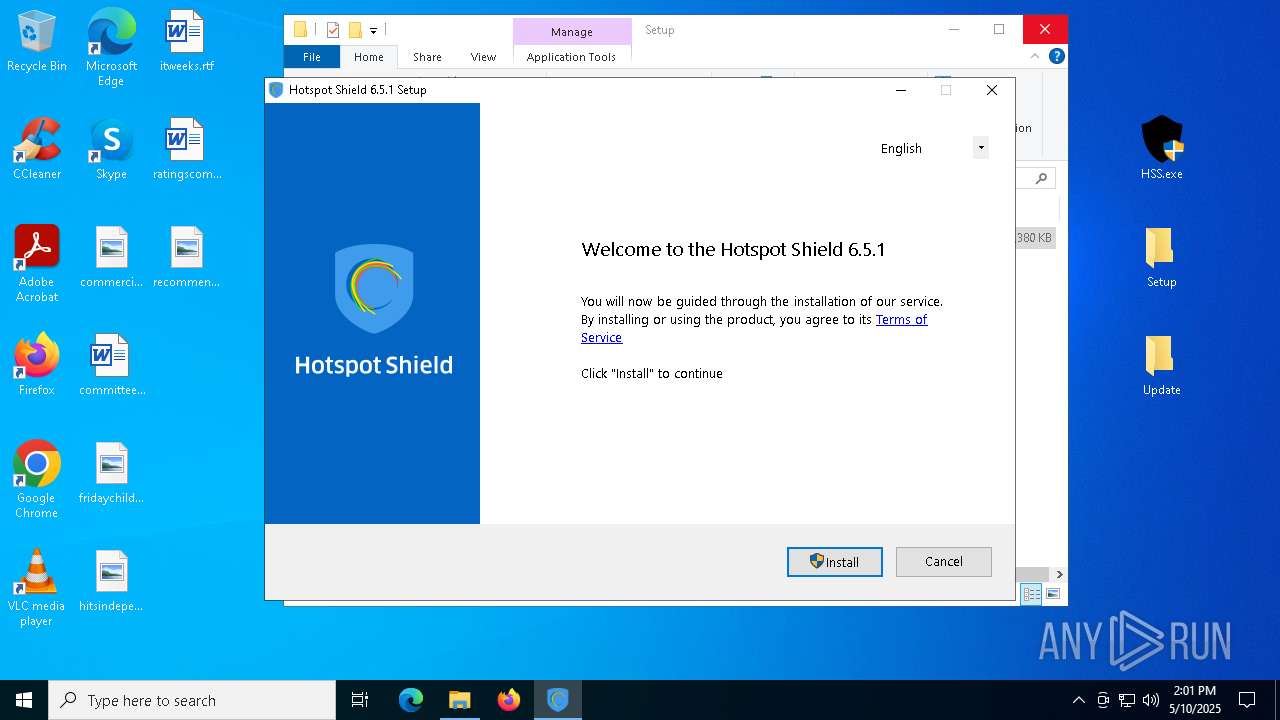
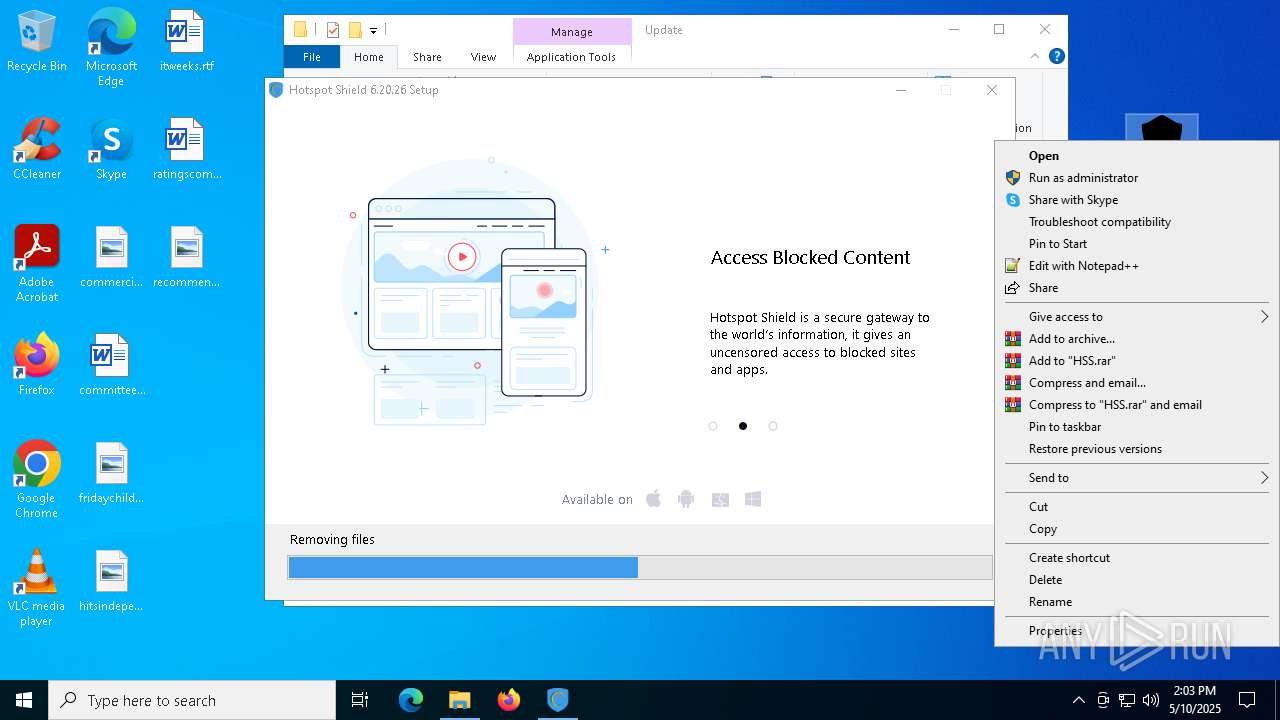
MALICIOUS
Executing a file with an untrusted certificate
- HSS-6.5.1-install-hss-805-ext.exe (PID: 864)
- HSS-6.5.1-install-hss-805-ext.exe (PID: 8896)
- HssInstaller.exe (PID: 7608)
- HssInstaller.exe (PID: 1280)
- HssInstaller.exe (PID: 2600)
- HssInstaller.exe (PID: 1748)
- HssInstaller.exe (PID: 8544)
- HssInstaller.exe (PID: 4756)
- HssInstaller.exe (PID: 6080)
- HssInstaller.exe (PID: 3784)
- HssInstaller.exe (PID: 8984)
- HssInstaller.exe (PID: 8064)
- HssInstaller.exe (PID: 9012)
- HssInstaller.exe (PID: 5164)
- HssInstaller.exe (PID: 7600)
- HssInstaller.exe (PID: 7876)
- HssInstaller.exe (PID: 7656)
- HssInstaller.exe (PID: 7336)
- HssInstaller.exe (PID: 7312)
- HssInstaller.exe (PID: 7540)
- HssInstaller.exe (PID: 7524)
- HssInstaller.exe (PID: 7184)
- HssInstaller.exe (PID: 7272)
- HssInstaller.exe (PID: 9060)
- HssInstaller.exe (PID: 8412)
- HssInstaller.exe (PID: 7480)
- HssInstaller.exe (PID: 8528)
- HssInstaller.exe (PID: 8300)
- HssInstaller.exe (PID: 6264)
- HssInstaller.exe (PID: 6512)
- HssInstaller.exe (PID: 8336)
- HssInstaller.exe (PID: 8592)
- HssInstaller.exe (PID: 3976)
- HssInstaller.exe (PID: 5512)
- HssInstaller.exe (PID: 8524)
- HssInstaller.exe (PID: 8284)
- HssInstaller.exe (PID: 9152)
- HssInstaller.exe (PID: 9096)
- cmw_srv.exe (PID: 8756)
- HssInstaller.exe (PID: 5812)
- HssInstaller.exe (PID: 3240)
- HssInstaller.exe (PID: 7564)
- HssInstaller.exe (PID: 2240)
- HssInstaller.exe (PID: 7812)
- hsscp.exe (PID: 7484)
- tapinstall.exe (PID: 7560)
- tapinstall.exe (PID: 7760)
- tapinstall.exe (PID: 7220)
- hsscp.exe (PID: 7308)
- cmw_srv.exe (PID: 7328)
- hsscp.exe (PID: 6256)
- hsscp.exe (PID: 9064)
- cmw_srv.exe (PID: 5988)
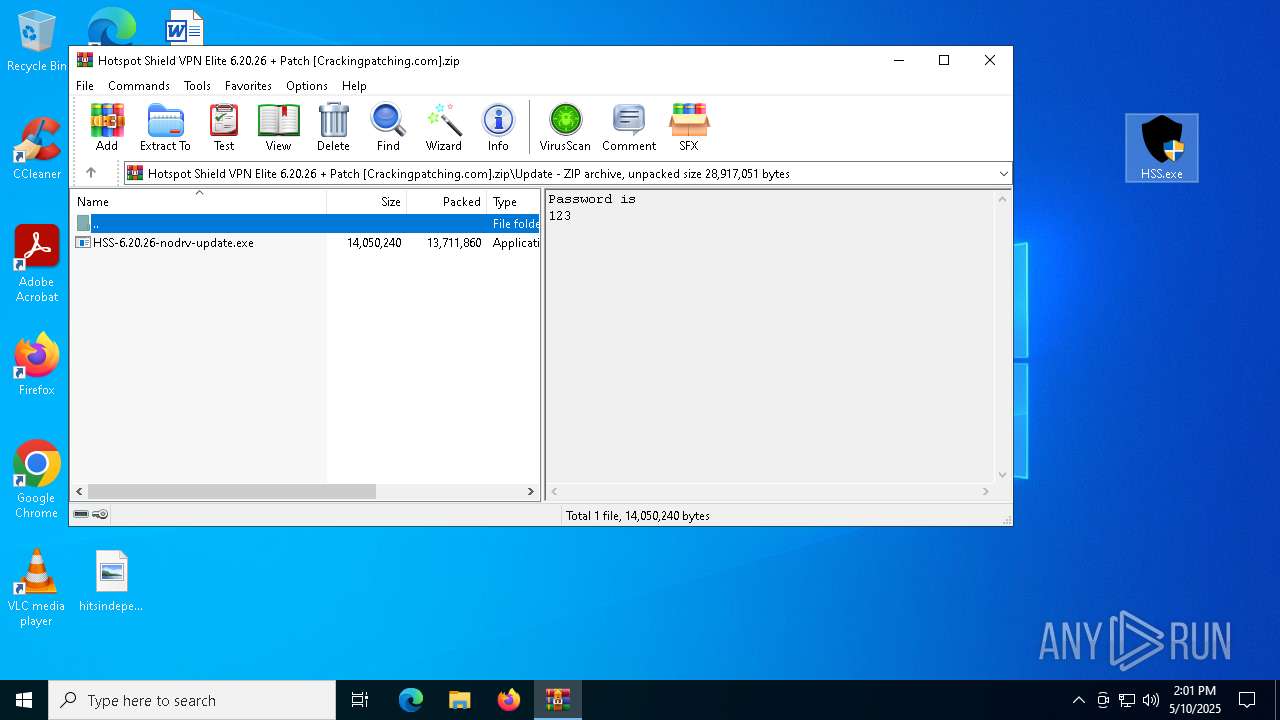
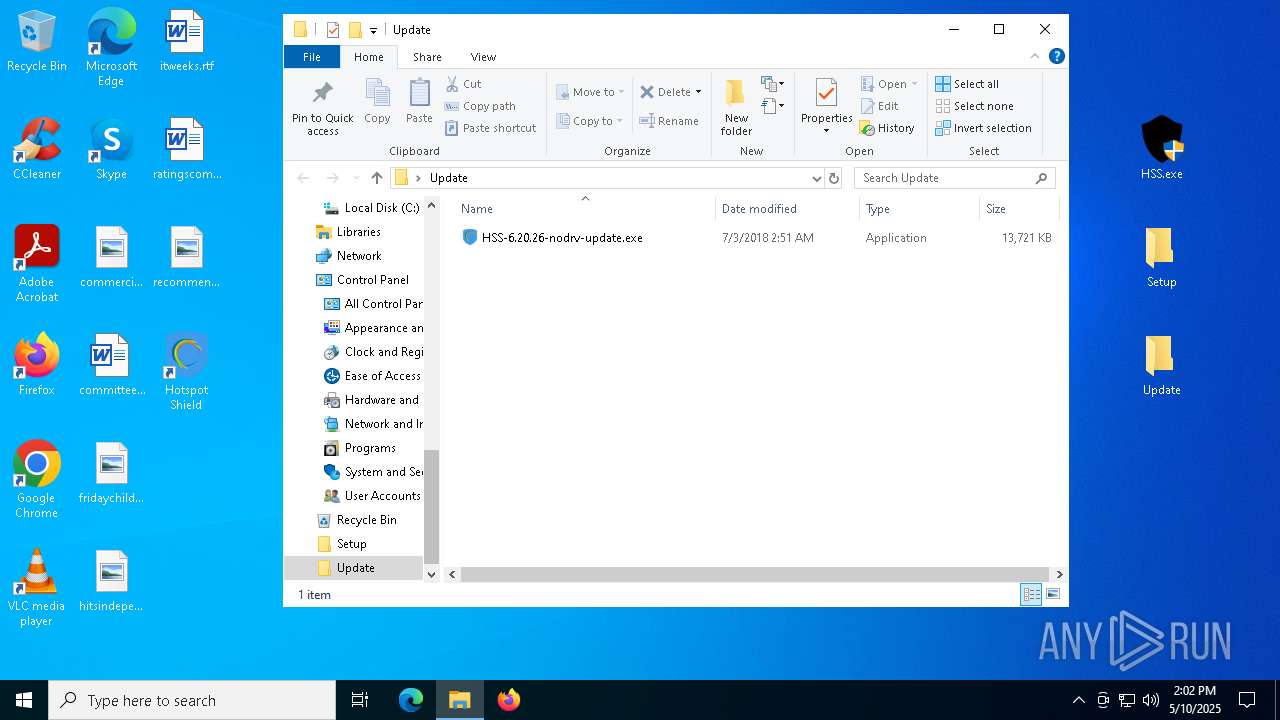
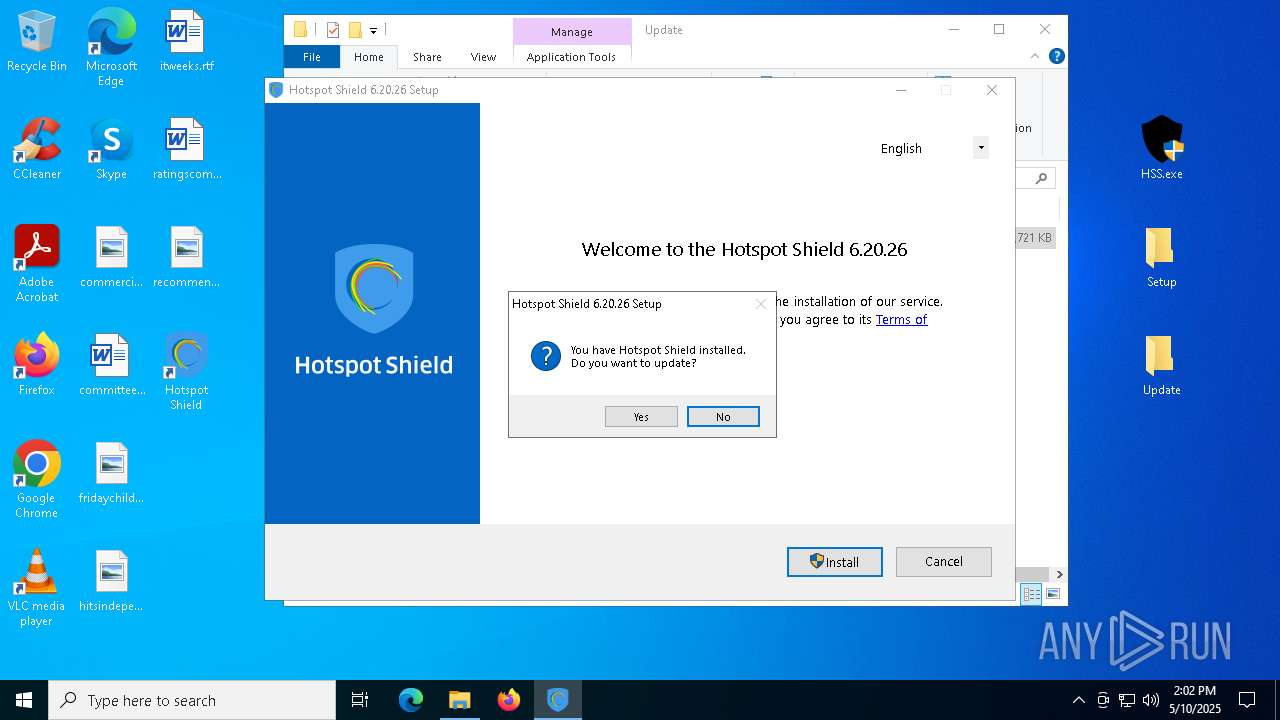
- HSS-6.20.26-nodrv-update.exe (PID: 7756)
- HSS-6.20.26-nodrv-update.exe (PID: 7732)
- HSS-6.20.26-nodrv-update.exe (PID: 7804)
- hsscp.exe (PID: 3300)
- HssInstaller.exe (PID: 7760)
Starts NET.EXE for service management
- net.exe (PID: 2136)
- net.exe (PID: 8124)
- msiexec.exe (PID: 8828)
- net.exe (PID: 1164)
- net.exe (PID: 7884)
- net.exe (PID: 7504)
- net.exe (PID: 9160)
- cmd.exe (PID: 9096)
- net.exe (PID: 7848)
- cmd.exe (PID: 8240)
- msiexec.exe (PID: 8604)
- net.exe (PID: 5380)
- net.exe (PID: 3032)
- net.exe (PID: 7920)
- net.exe (PID: 7524)
- net.exe (PID: 5952)
- net.exe (PID: 8916)
- net.exe (PID: 1132)
SUSPICIOUS
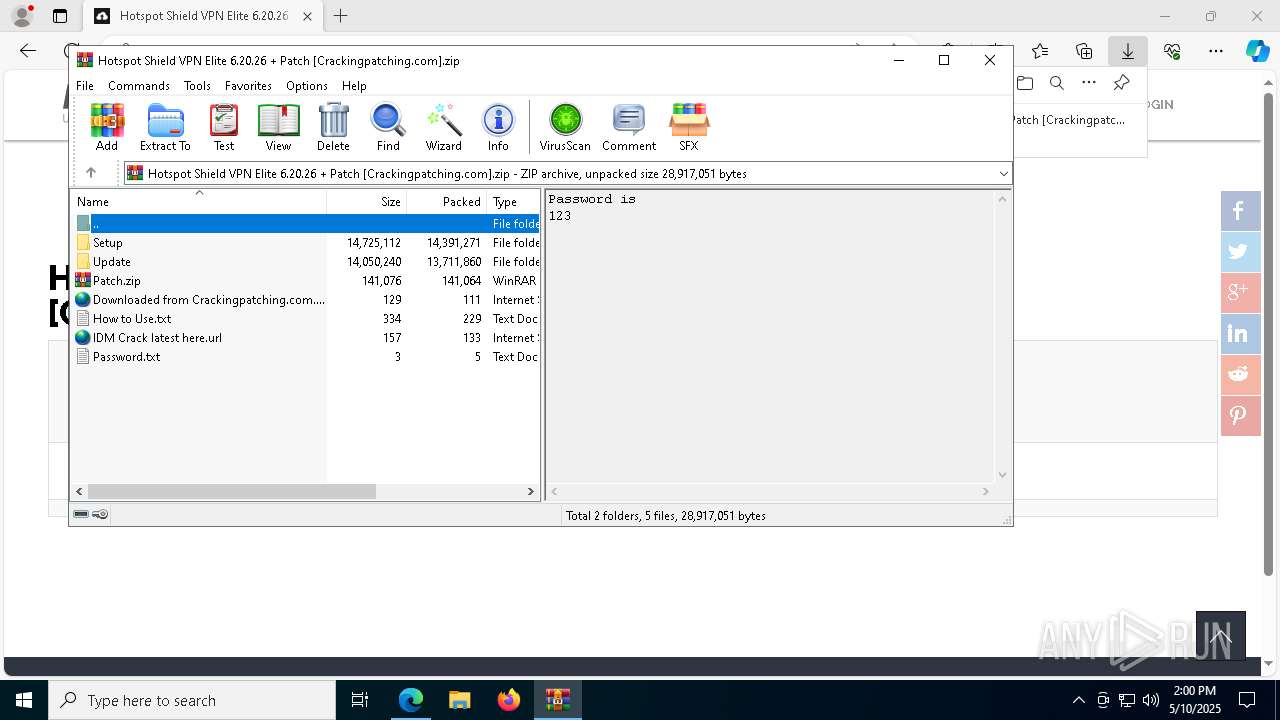
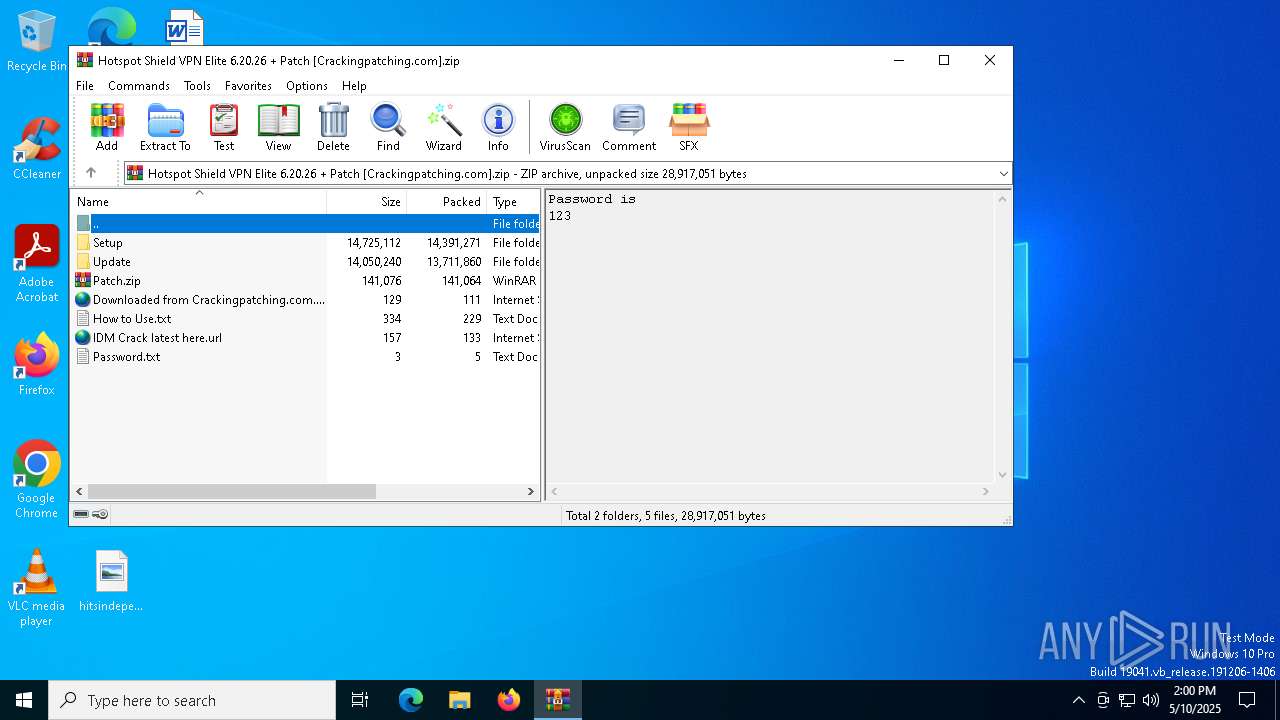
Reads security settings of Internet Explorer
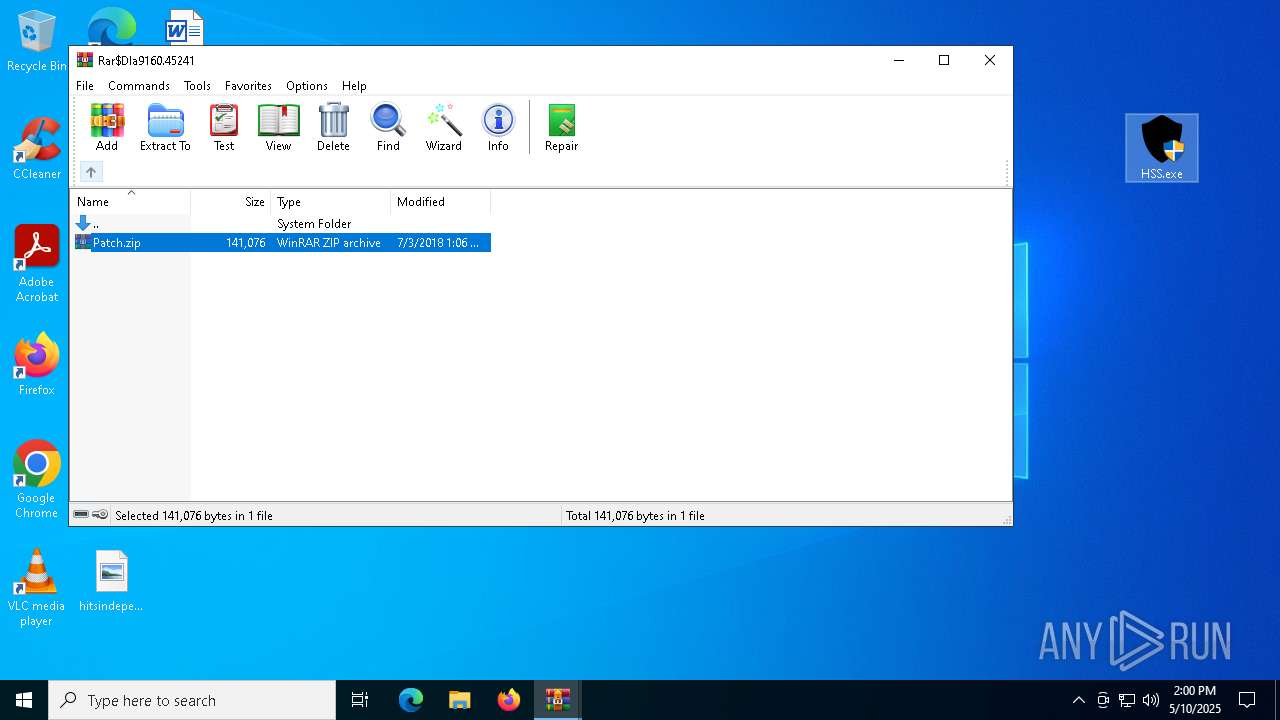
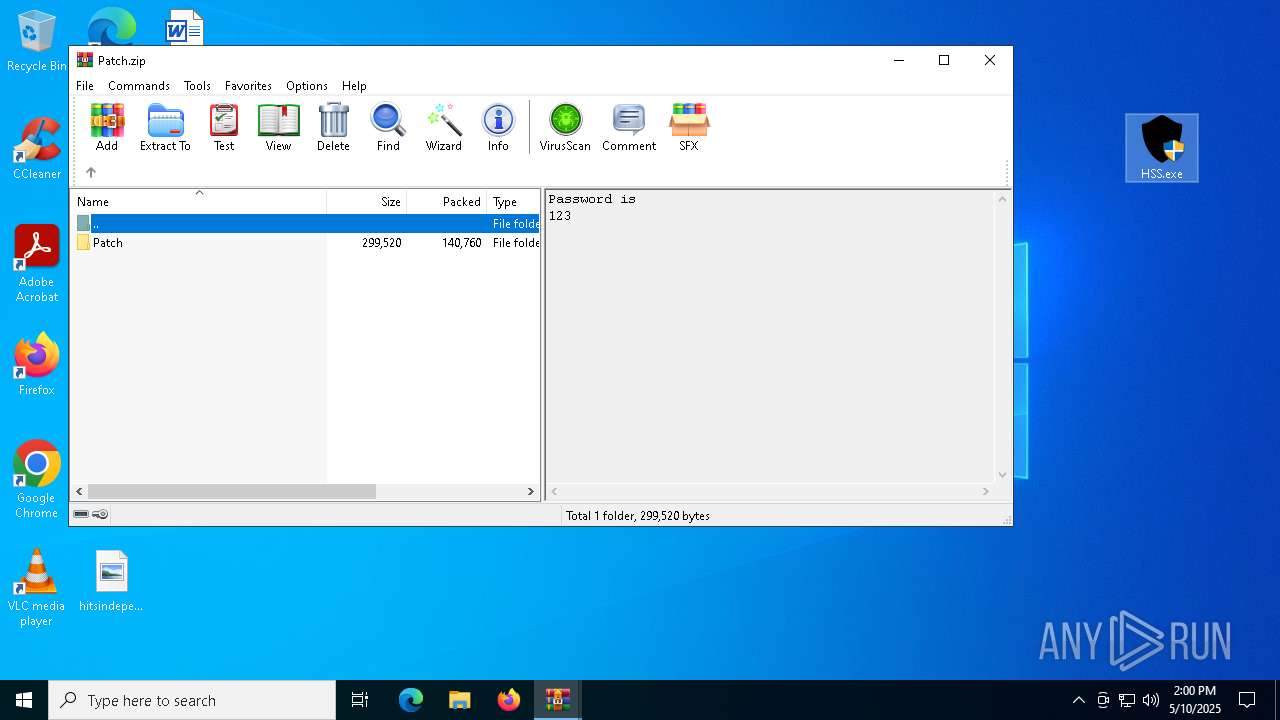
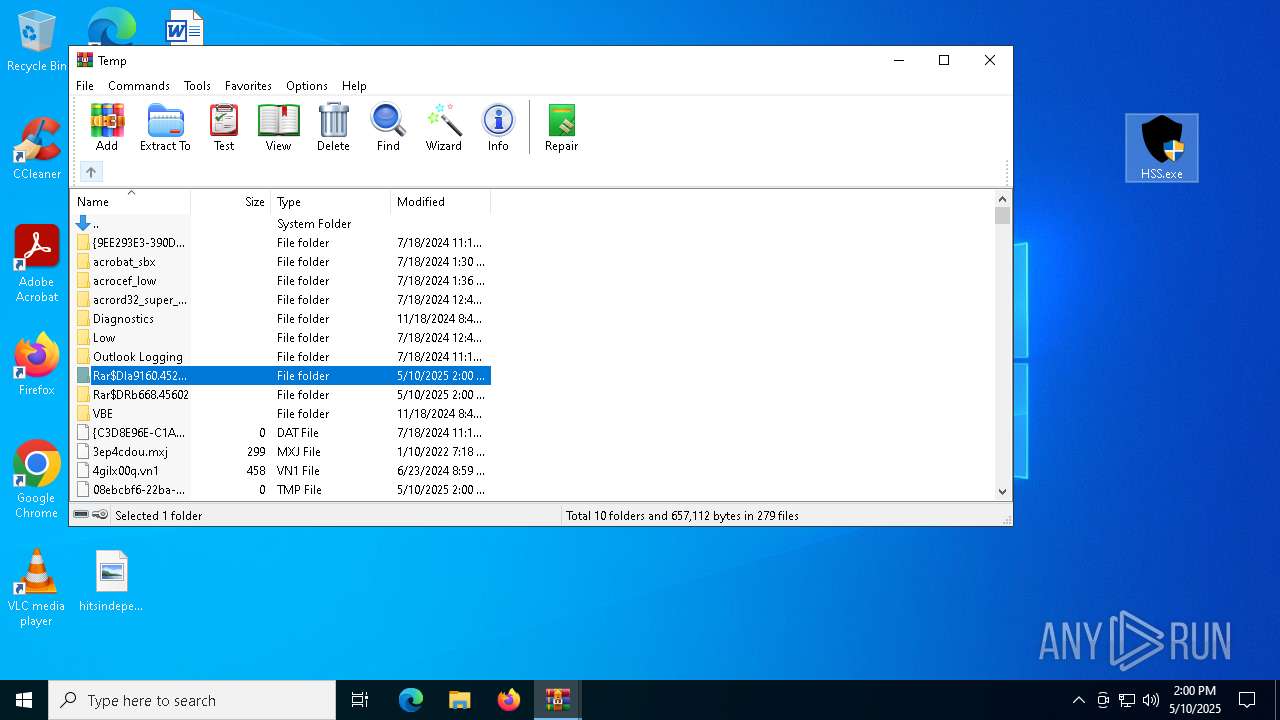
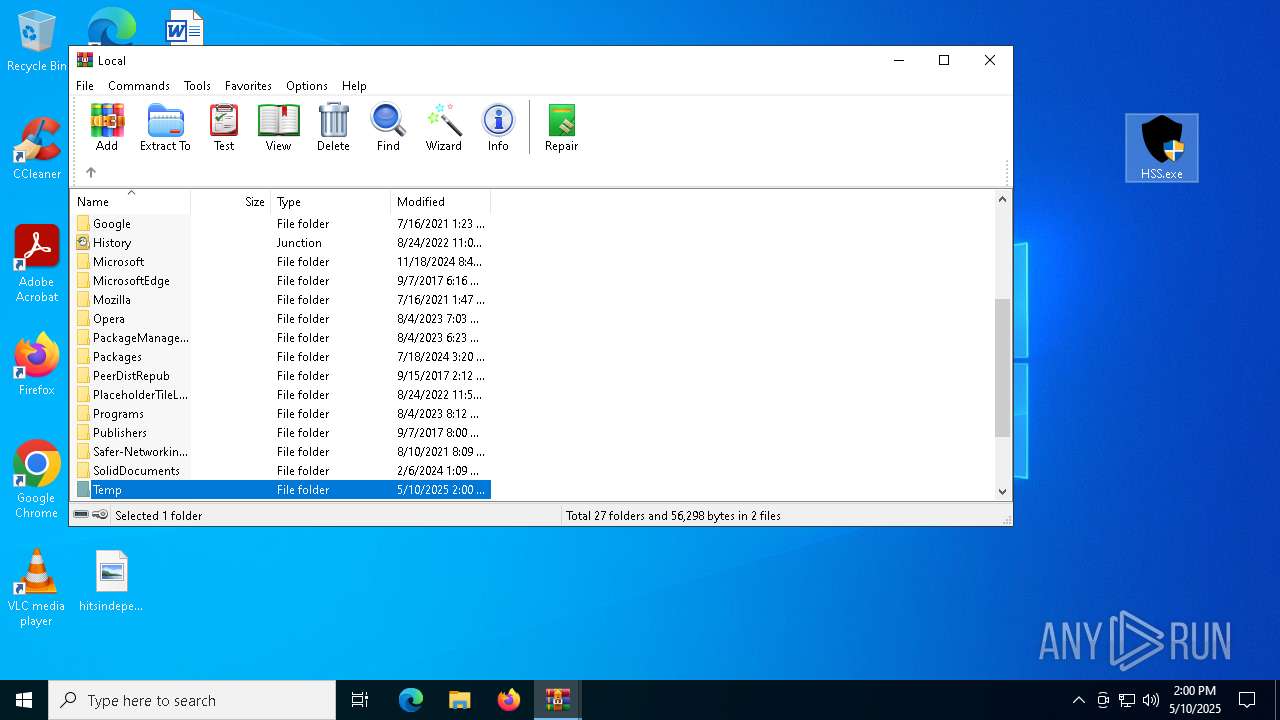
- WinRAR.exe (PID: 9160)
Application launched itself
- WinRAR.exe (PID: 9160)
- HssInstaller.exe (PID: 3240)
- HssInstaller.exe (PID: 7564)
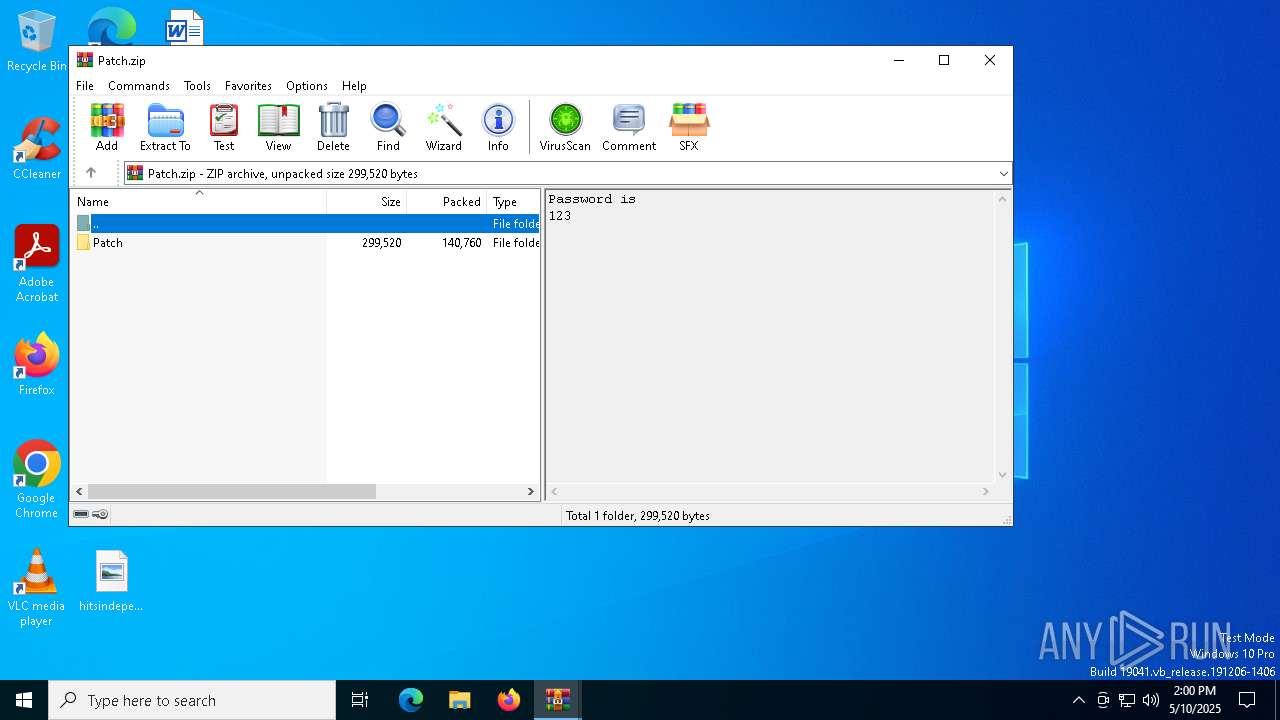
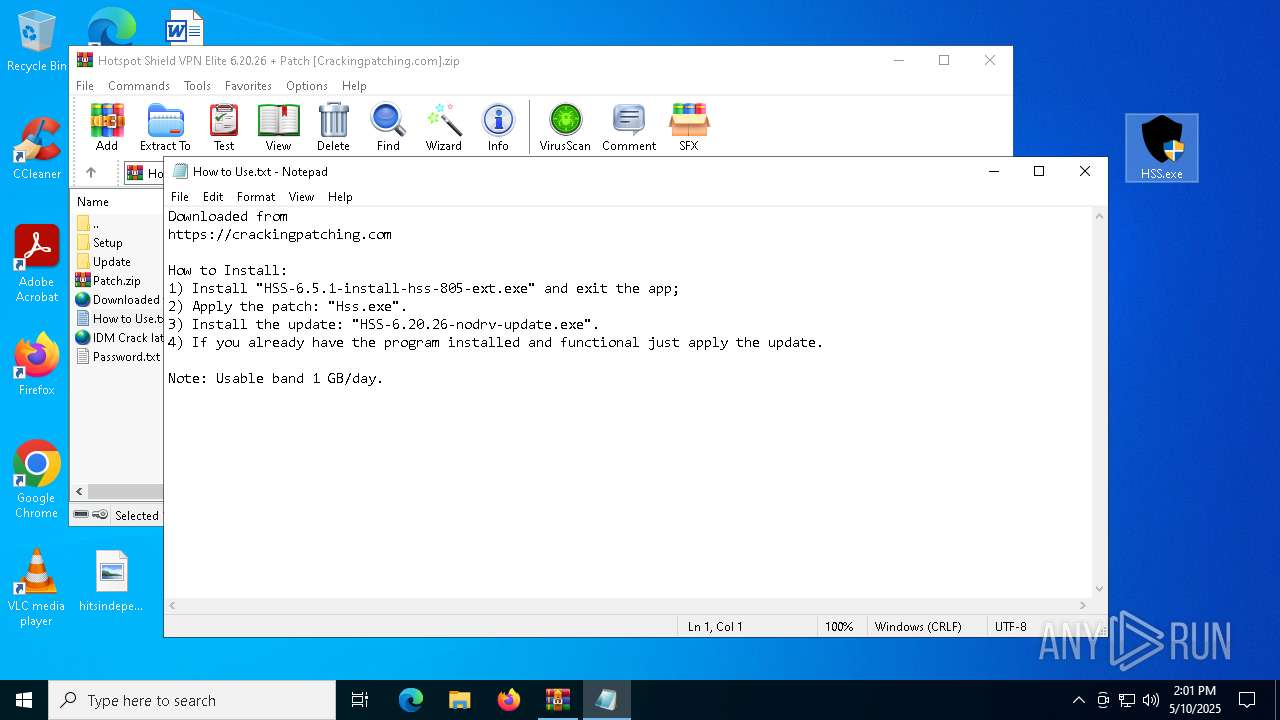
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 9160)
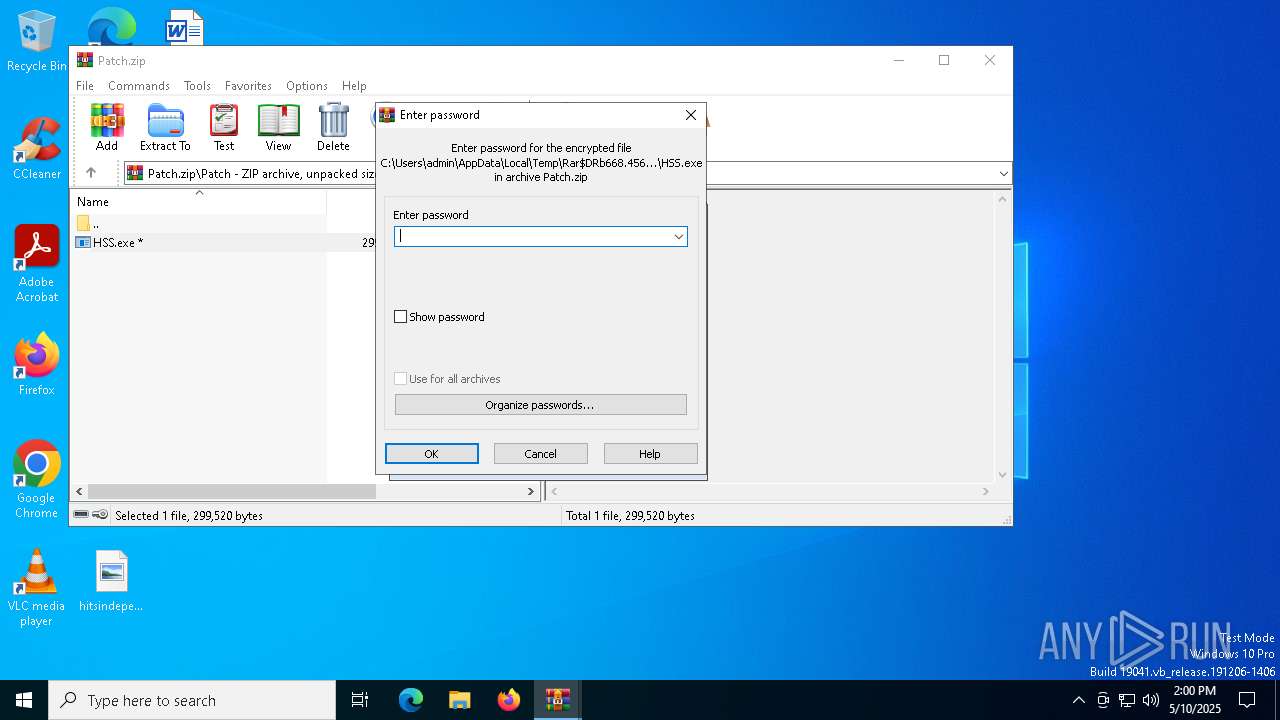
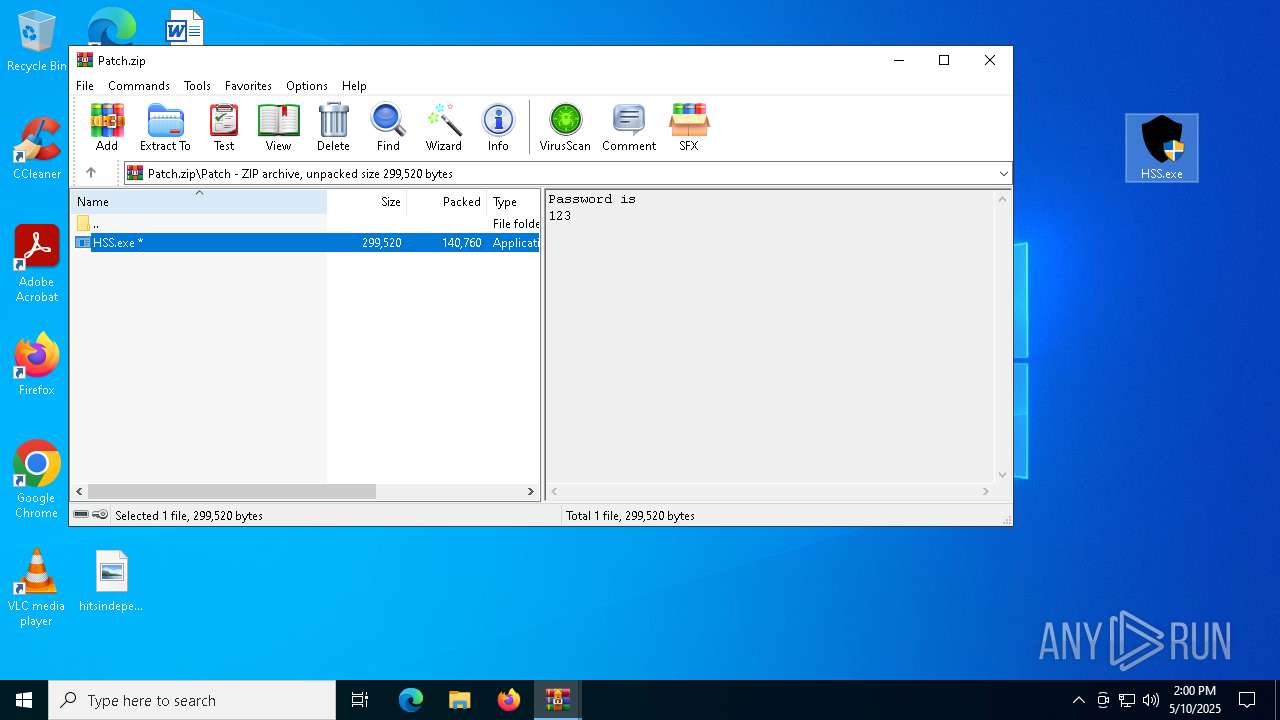
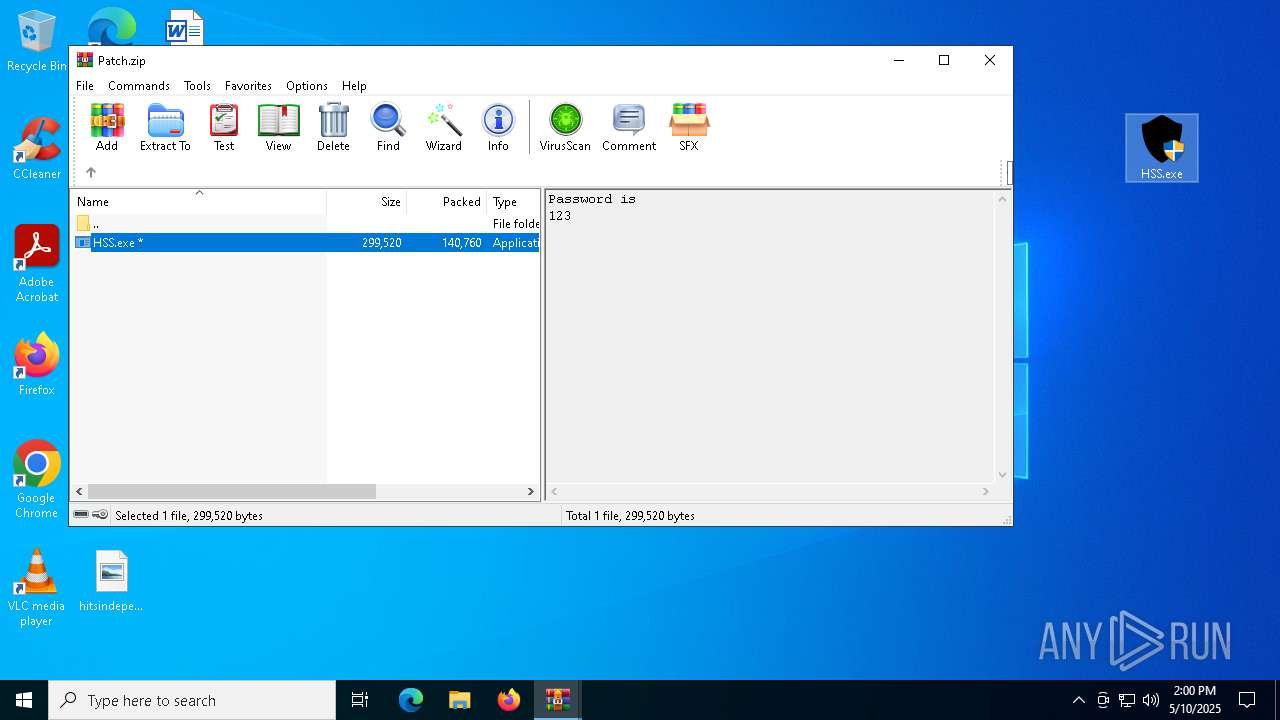
Executable content was dropped or overwritten
- HSS-6.5.1-install-hss-805-ext.exe (PID: 864)
- rundll32.exe (PID: 8060)
- HSS-6.5.1-install-hss-805-ext.exe (PID: 8896)
- rundll32.exe (PID: 7828)
- rundll32.exe (PID: 7144)
- rundll32.exe (PID: 8000)
- tapinstall.exe (PID: 7220)
- drvinst.exe (PID: 7296)
- drvinst.exe (PID: 7772)
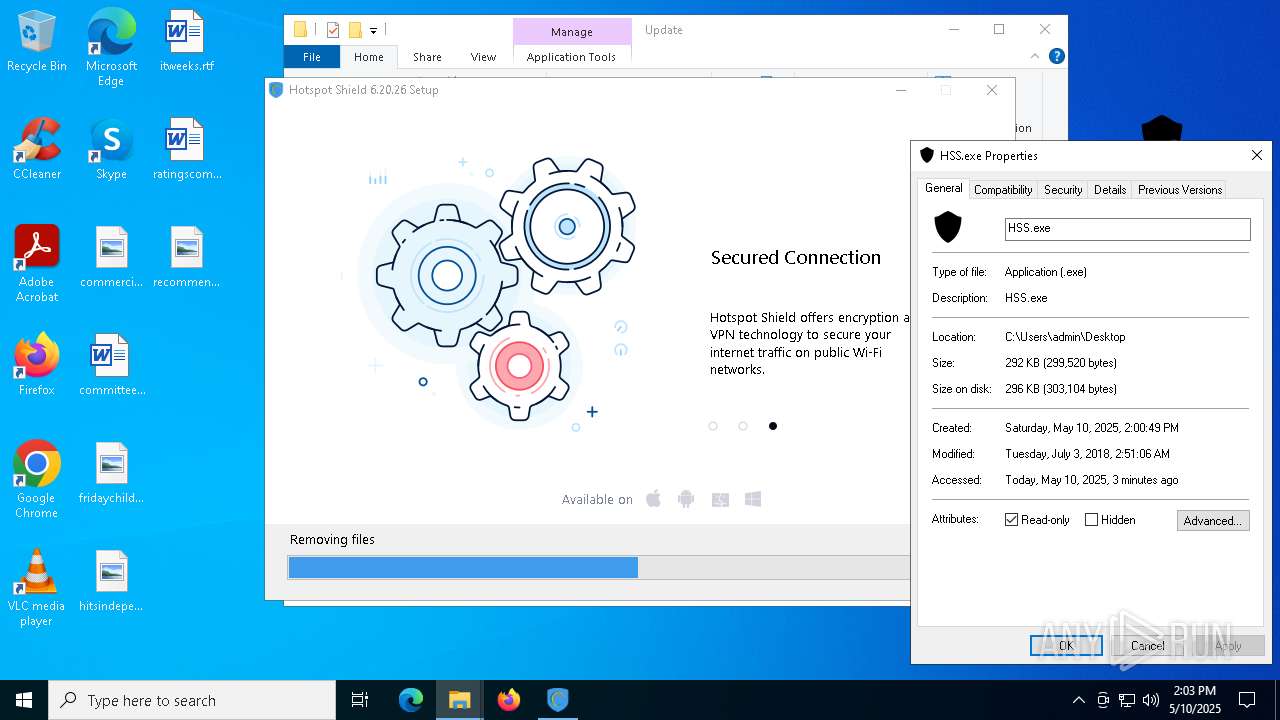
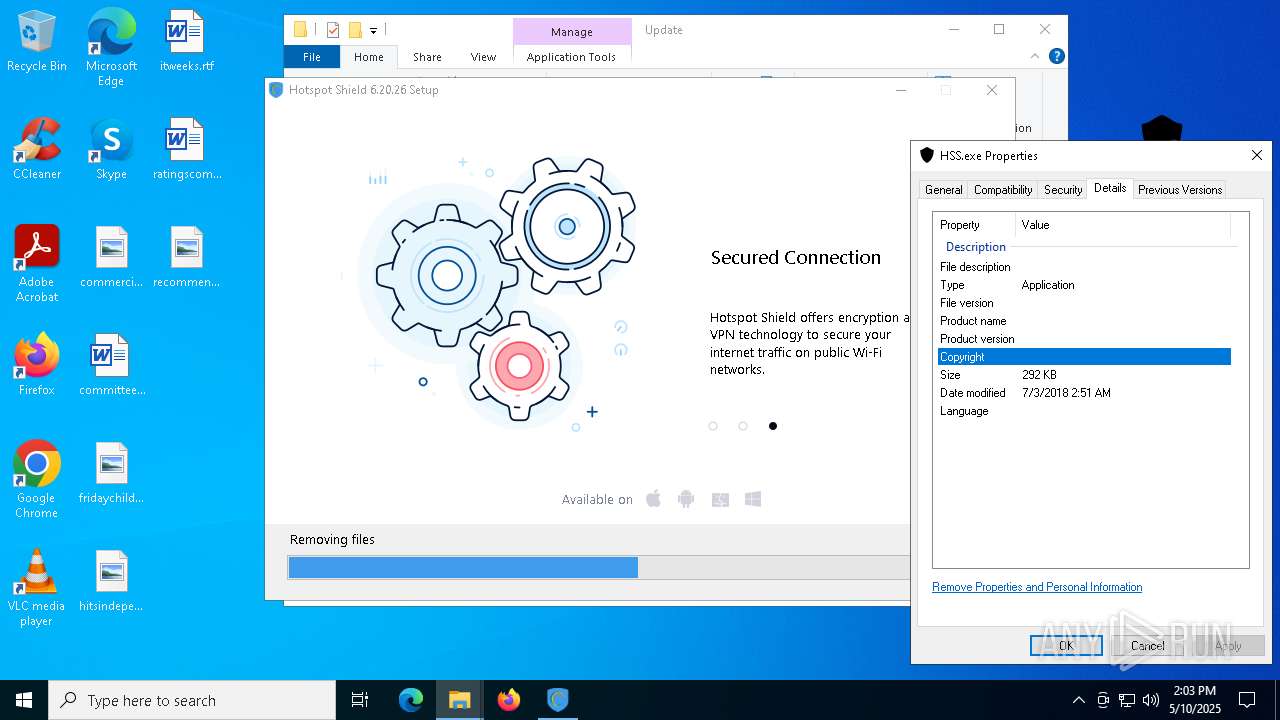
- HSS.exe (PID: 2288)
- rundll32.exe (PID: 8812)
- HSS.exe (PID: 5084)
- HSS-6.20.26-nodrv-update.exe (PID: 7756)
- HSS-6.20.26-nodrv-update.exe (PID: 7732)
- rundll32.exe (PID: 9088)
- rundll32.exe (PID: 8760)
- rundll32.exe (PID: 4920)
- rundll32.exe (PID: 8920)
- rundll32.exe (PID: 8132)
- rundll32.exe (PID: 7560)
- HSS-6.20.26-nodrv-update.exe (PID: 7804)
Uses TASKKILL.EXE to kill process
- msiexec.exe (PID: 8828)
- msiexec.exe (PID: 8604)
The process drops C-runtime libraries
- msiexec.exe (PID: 2108)
Process drops legitimate windows executable
- msiexec.exe (PID: 2108)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 2108)
- drvinst.exe (PID: 7296)
- tapinstall.exe (PID: 7220)
- drvinst.exe (PID: 7772)
Executes as Windows Service
- cmw_srv.exe (PID: 8756)
- cmw_srv.exe (PID: 7328)
- cmw_srv.exe (PID: 5988)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 9096)
- cmd.exe (PID: 8240)
Executing commands from a ".bat" file
- HSS.exe (PID: 2288)
- HSS.exe (PID: 5084)
Starts CMD.EXE for commands execution
- HSS.exe (PID: 2288)
- HSS.exe (PID: 5084)
Starts itself from another location
- HSS-6.20.26-nodrv-update.exe (PID: 7732)
INFO
Checks supported languages
- identity_helper.exe (PID: 8240)
- identity_helper.exe (PID: 1240)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7148)
- WinRAR.exe (PID: 9160)
Reads Environment values
- identity_helper.exe (PID: 8240)
- identity_helper.exe (PID: 1240)
Application launched itself
- msedge.exe (PID: 7148)
- msedge.exe (PID: 8796)
The sample compiled with english language support
- msedge.exe (PID: 7148)
- msedge.exe (PID: 7332)
- HSS-6.5.1-install-hss-805-ext.exe (PID: 864)
- HSS-6.5.1-install-hss-805-ext.exe (PID: 8896)
- msiexec.exe (PID: 2108)
- WinRAR.exe (PID: 9160)
- tapinstall.exe (PID: 7220)
- drvinst.exe (PID: 7296)
- drvinst.exe (PID: 7772)
- HSS-6.20.26-nodrv-update.exe (PID: 7756)
- HSS-6.20.26-nodrv-update.exe (PID: 7732)
- msedge.exe (PID: 7496)
- HSS-6.20.26-nodrv-update.exe (PID: 7804)
Reads the computer name
- identity_helper.exe (PID: 8240)
- identity_helper.exe (PID: 1240)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 9160)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 668)
- WinRAR.exe (PID: 9160)
- msiexec.exe (PID: 2108)
- msedge.exe (PID: 7496)
Reads the software policy settings
- slui.exe (PID: 4408)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8164)
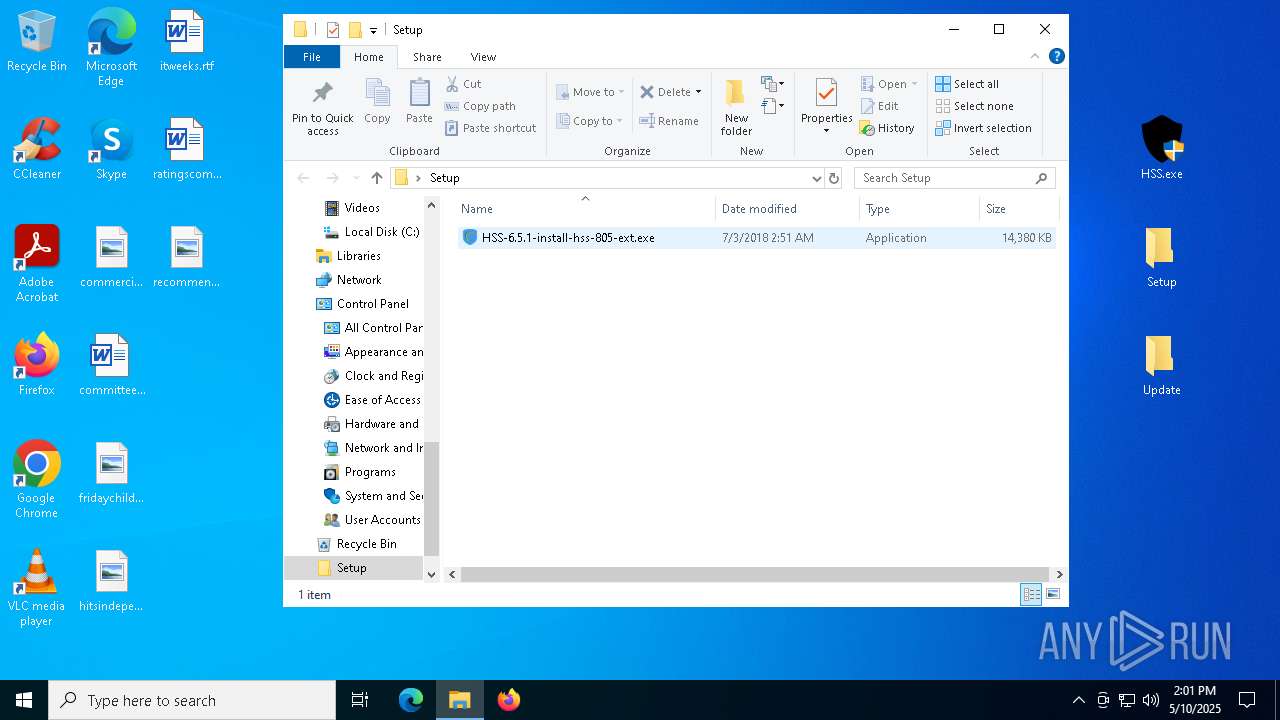
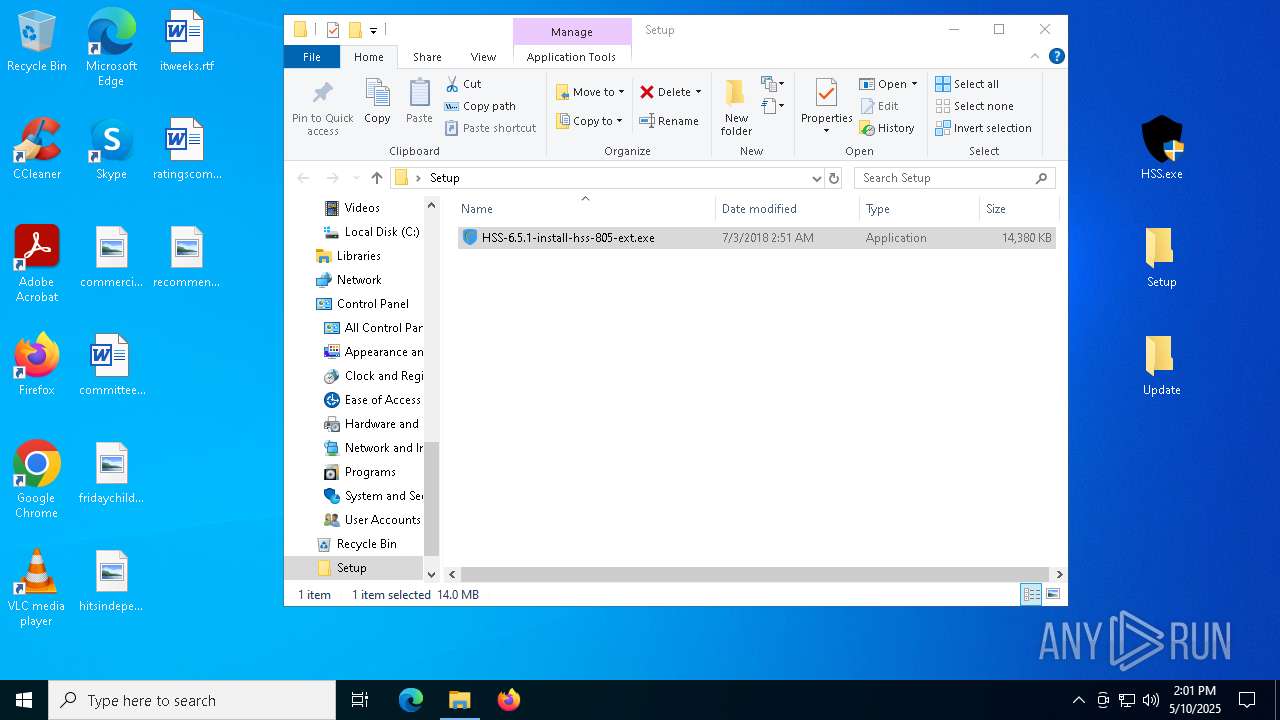
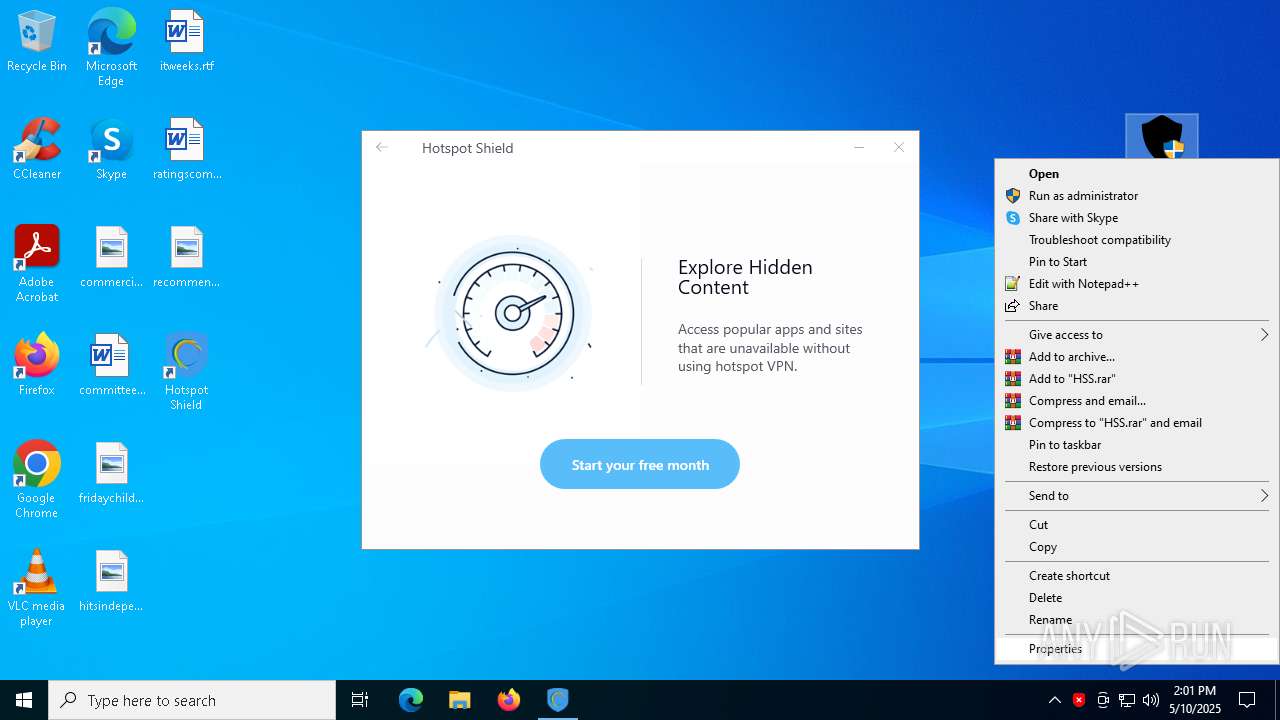
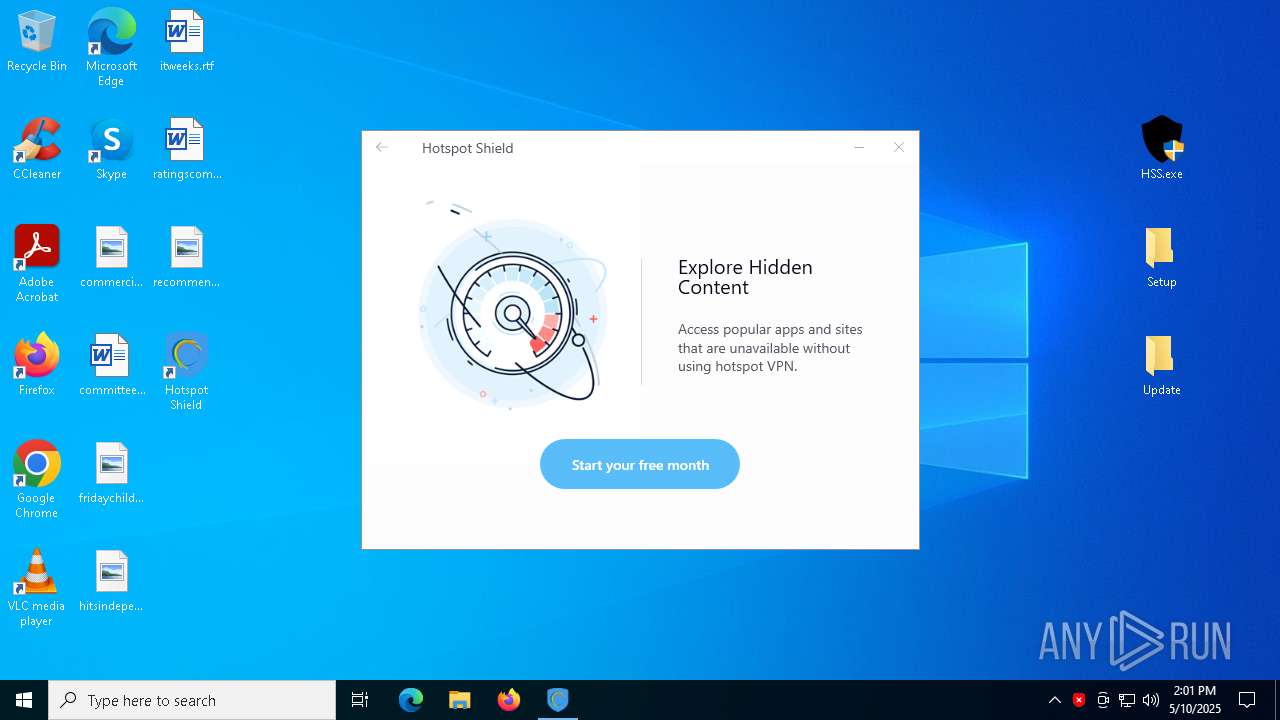
Manual execution by a user
- HSS-6.5.1-install-hss-805-ext.exe (PID: 864)
- HSS.exe (PID: 5084)
- HSS.exe (PID: 8124)
- HSS.exe (PID: 2288)
- HSS.exe (PID: 2772)
- HSS-6.20.26-nodrv-update.exe (PID: 7756)
.NET Reactor protector has been detected
- HSS-6.5.1-install-hss-805-ext.exe (PID: 864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
498
Monitored processes
354
Malicious processes
16
Suspicious processes
49
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | attrib -r C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | C:\WINDOWS\system32\net1 stop hshld | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 456 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 516 | "C:\WINDOWS\system32\certutil.exe" -addstore TrustedPublisher "C:\Program Files (x86)\Hotspot Shield\driver\af16.cer" | C:\Windows\SysWOW64\certutil.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | FIND /C /I "d1.connectify.me" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | FIND /C /I "activate.connectify.me" C:\WINDOWS\system32\drivers\etc\hosts | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa9160.45241\Patch.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 864 | "C:\Users\admin\Desktop\Setup\HSS-6.5.1-install-hss-805-ext.exe" | C:\Users\admin\Desktop\Setup\HSS-6.5.1-install-hss-805-ext.exe | explorer.exe | ||||||||||||
User: admin Company: AnchorFree Inc. Integrity Level: MEDIUM Description: Hotspot Shield 6.5.1 Exit code: 0 Version: 6.5.1.10355 Modules
| |||||||||||||||
| 864 | C:\WINDOWS\system32\net1 stop hshld | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | HssInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
83 390
Read events
81 218
Write events
1 212
Delete events
960
Modification events
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 1211D5C75E932F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9EB4DCC75E932F00 | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {86EBE9E8-649C-4C83-8018-F1C9D1C358B5} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {64C50F93-7FE9-4515-99EE-C7C17A196FB4} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {66FA5C17-D38E-491D-B038-4FFF75BAD595} | |||
| (PID) Process: | (7148) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262984 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4C2C648F-607E-4E3C-A406-9645A633C2E3} | |||
Executable files
507
Suspicious files
538
Text files
542
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bd76.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bd85.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bd85.TMP | — | |
MD5:— | SHA256:— | |||
| 7148 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
179
DNS requests
209
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8692 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8692 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2108 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | unknown | — | — | whitelisted |
2108 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://ocsp.verisign.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCEFIA5aolVvwahu2WydRLM8c%3D | unknown | — | — | whitelisted |
2108 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://crl.verisign.com/pca3-g5.crl | unknown | — | — | whitelisted |
2108 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://sf.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSqZMG5M8TA9rdzkbCnNwuMAd5VgQUz5mp6nsm9EvJjo%2FX8AUm7%2BPSp50CECxVyAWxTldCPkd4jPS2Y3c%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.158:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7148 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7332 | msedge.exe | 104.21.32.1:443 | crackingpatching.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
crackingpatching.com |
| unknown |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |