| File name: | rootkit.exe |
| Full analysis: | https://app.any.run/tasks/3e974ec6-15d9-4e0b-8a07-44ba69231f11 |
| Verdict: | Malicious activity |
| Analysis date: | January 01, 2025, 20:14:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 7CDC9ADC70AAC95C894605691F852A43 |
| SHA1: | 1BFA05AE9A2856D323D803270895C1EF7BF23634 |
| SHA256: | 484E8594F9BC415D8A4870F7EA82B600C6092B583B02F72A57D966F7DEA6F667 |
| SSDEEP: | 96:55elLVsss77YjQ+9TXtPJPsqohLar+Z7A2k7DePDyQMKkYIGt+I9EmQC9cJHUSBK:XAxsss77YjptRP1ohQrN3C2JHFNc |
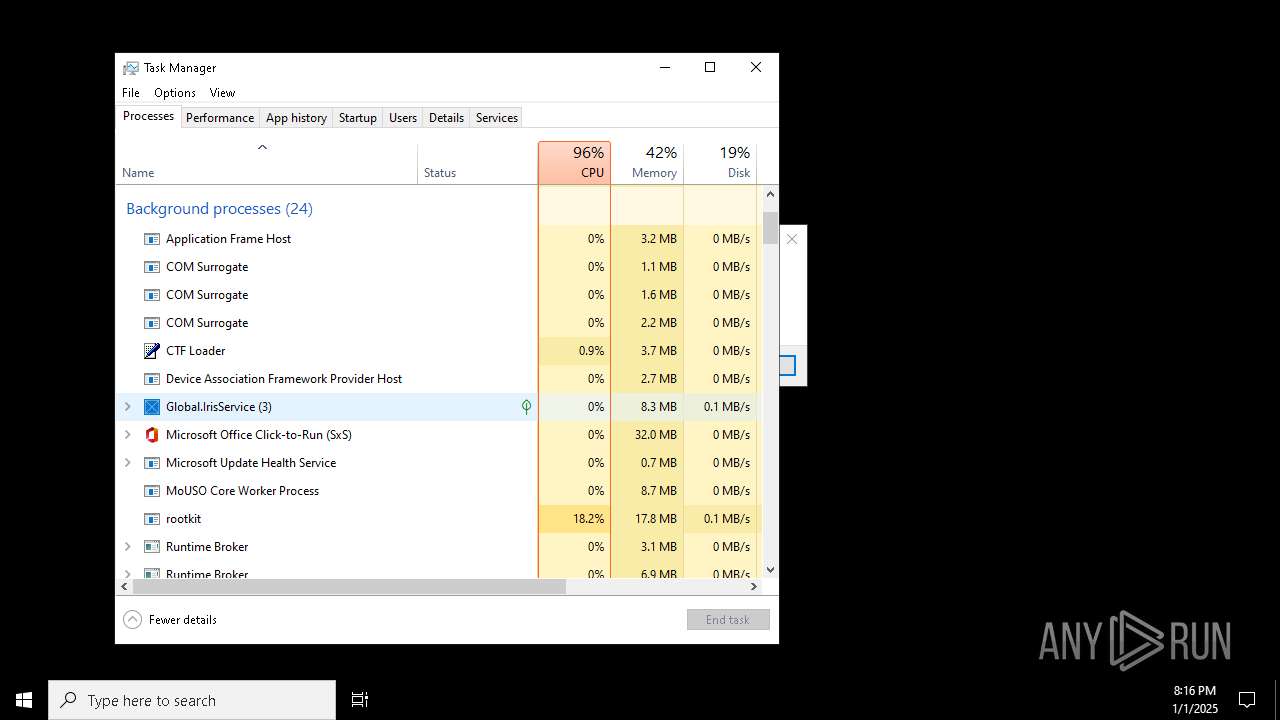
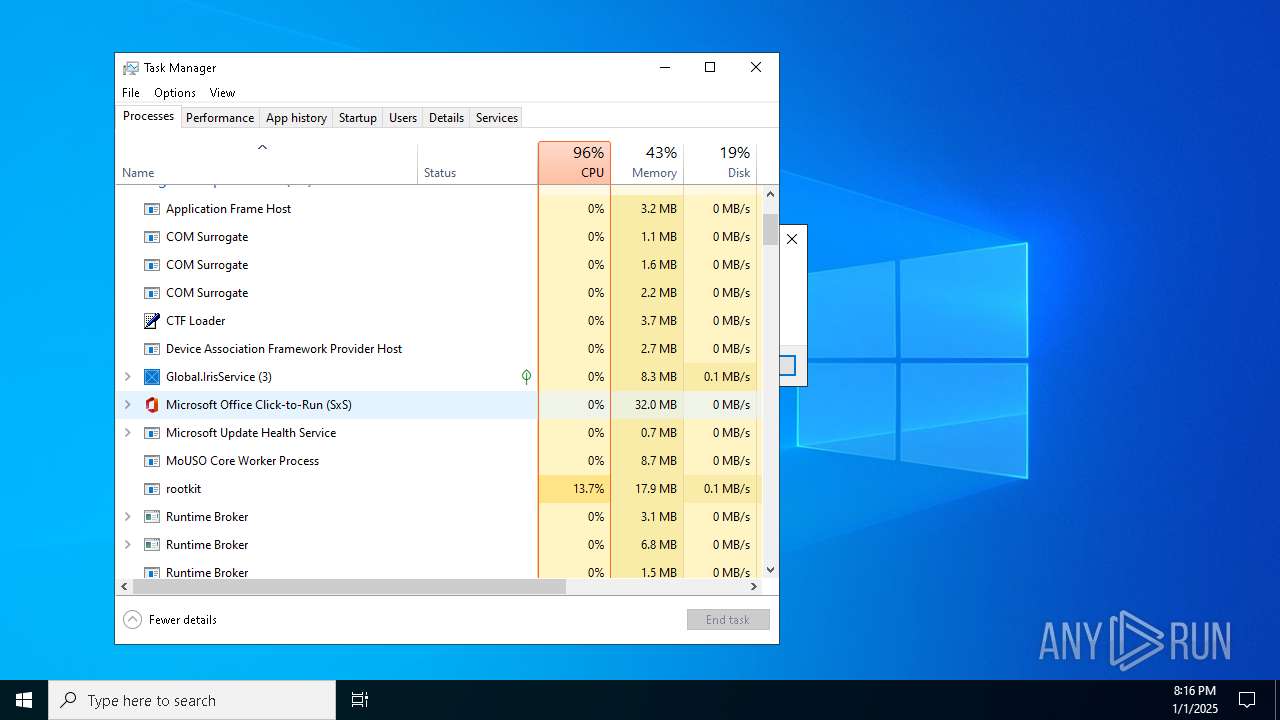
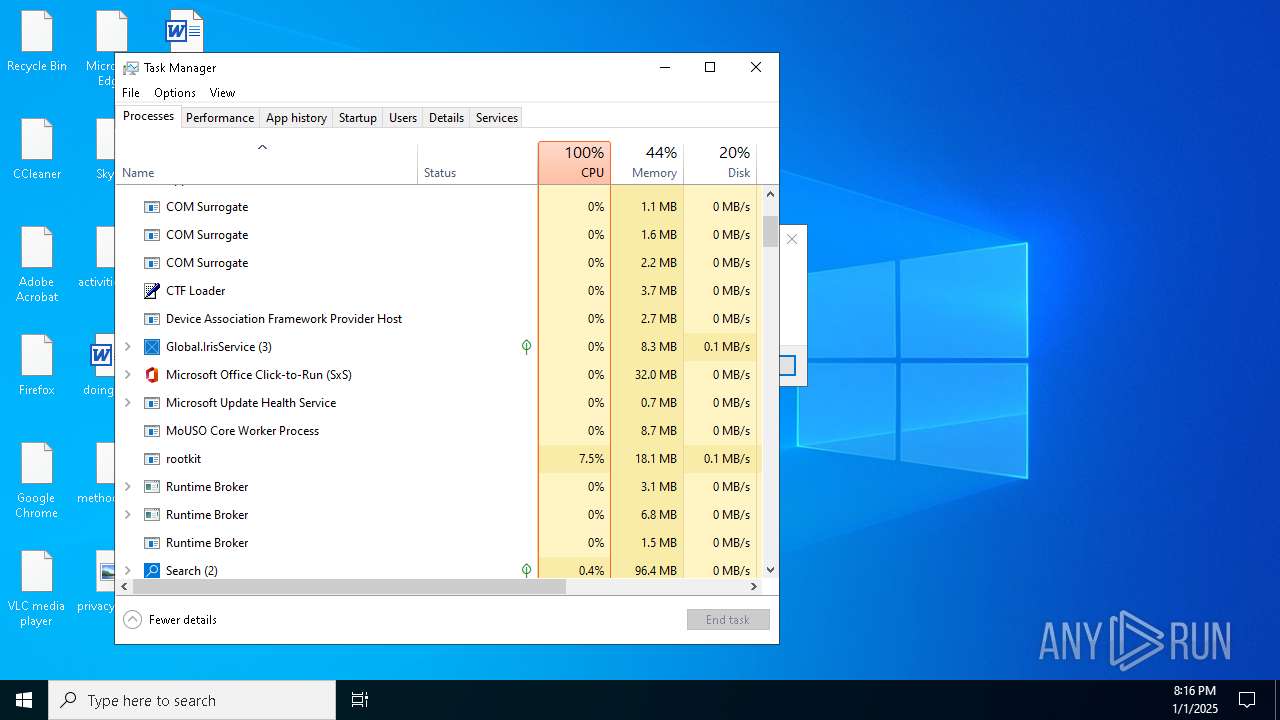
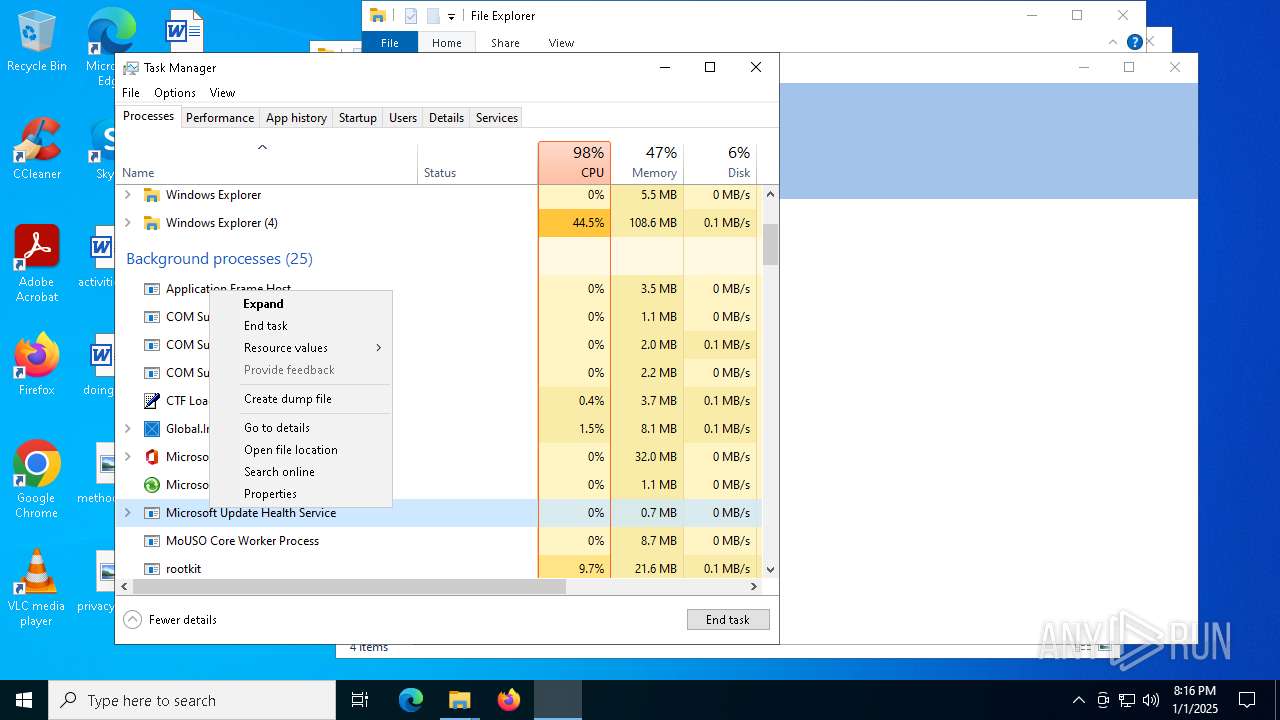
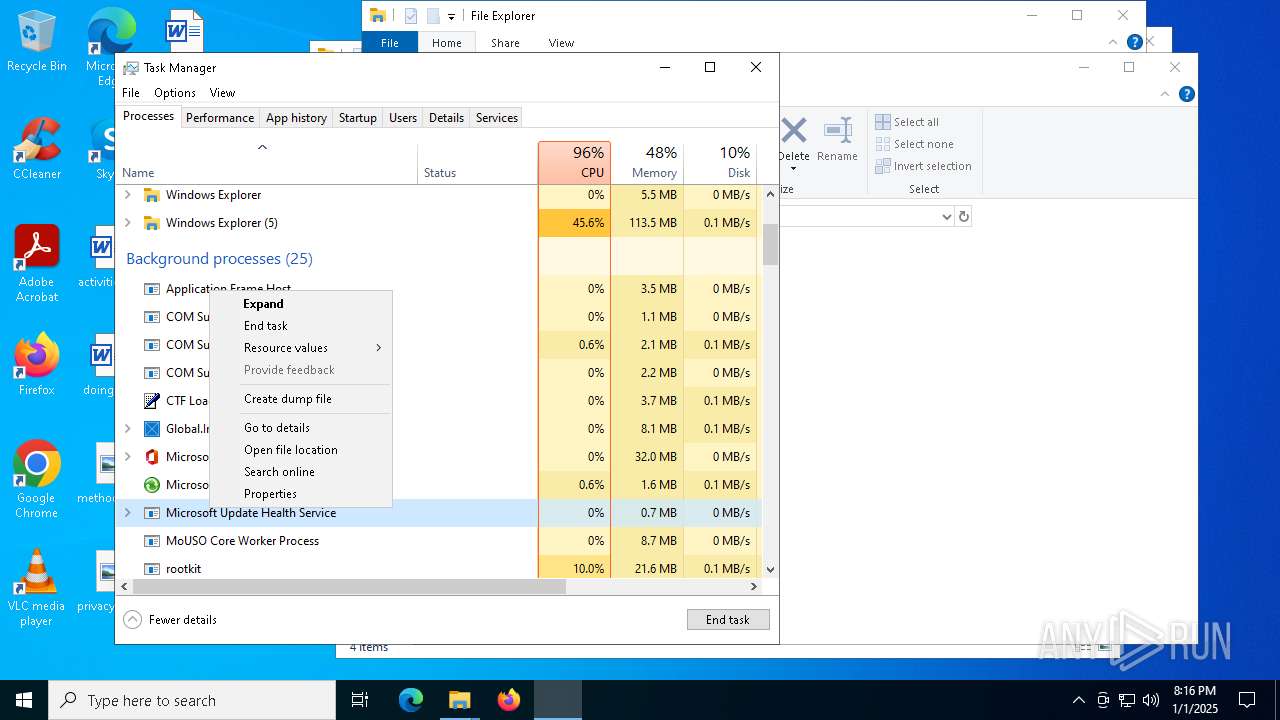
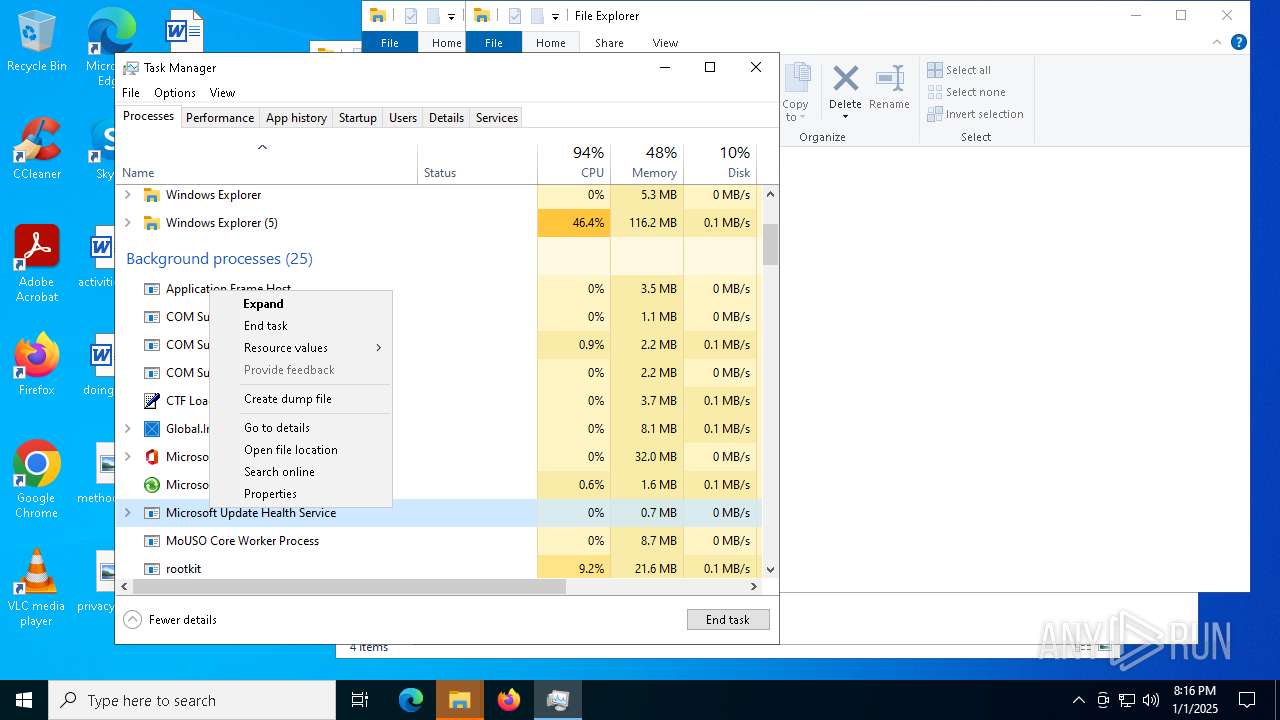
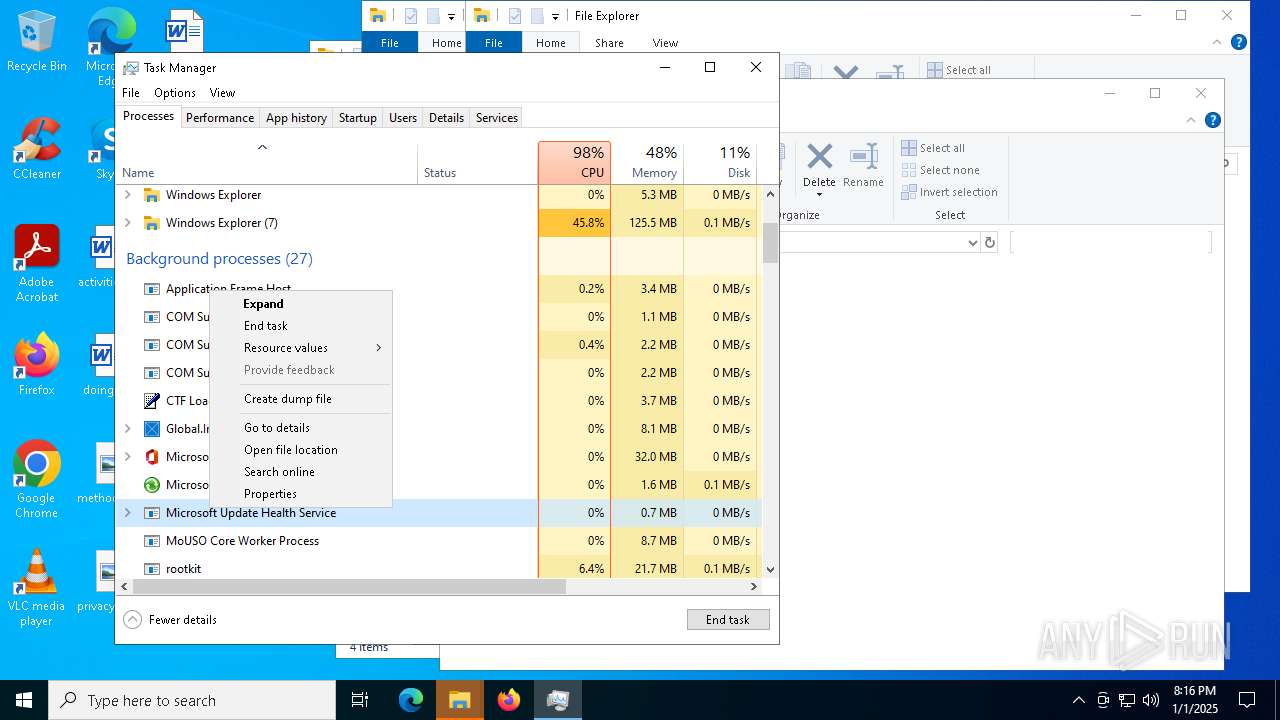
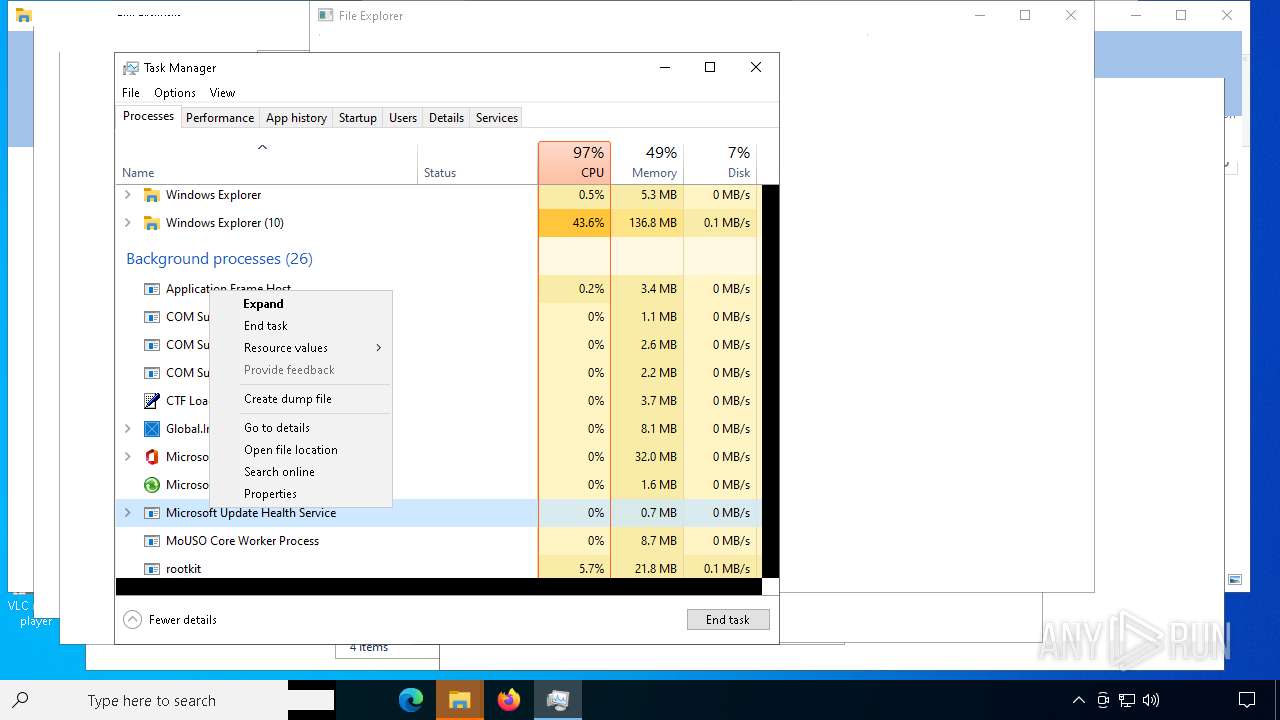
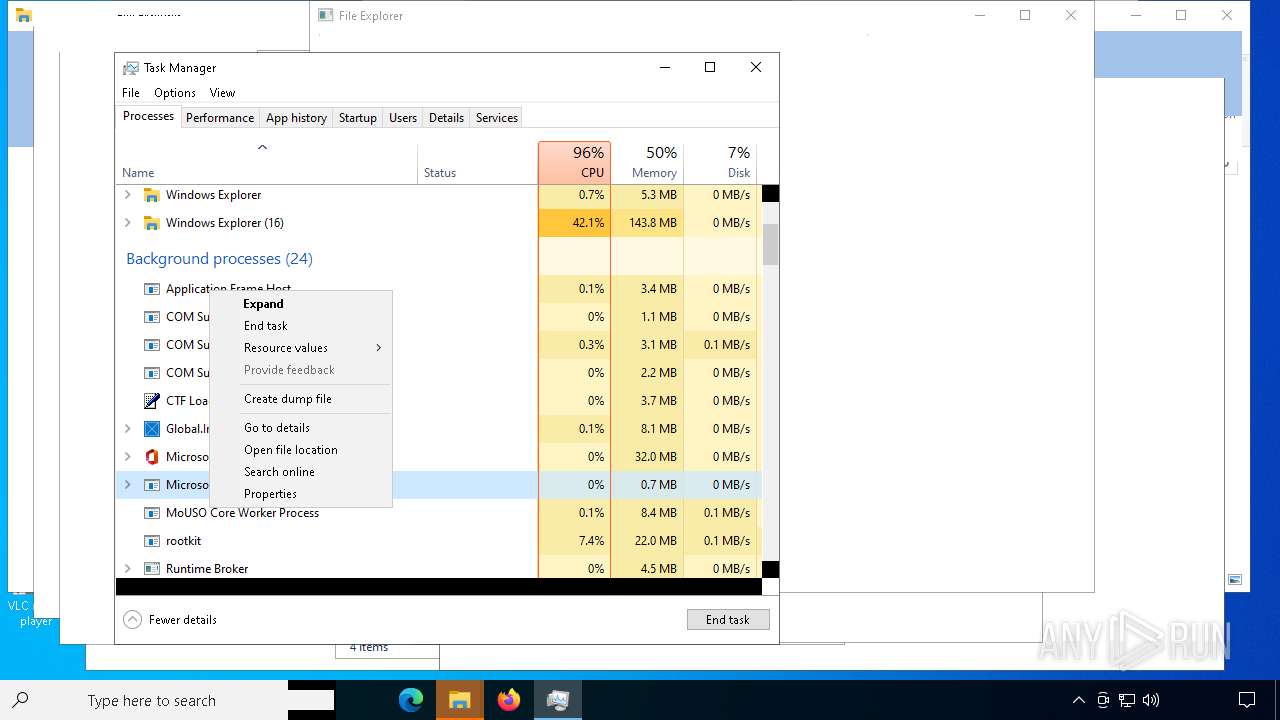
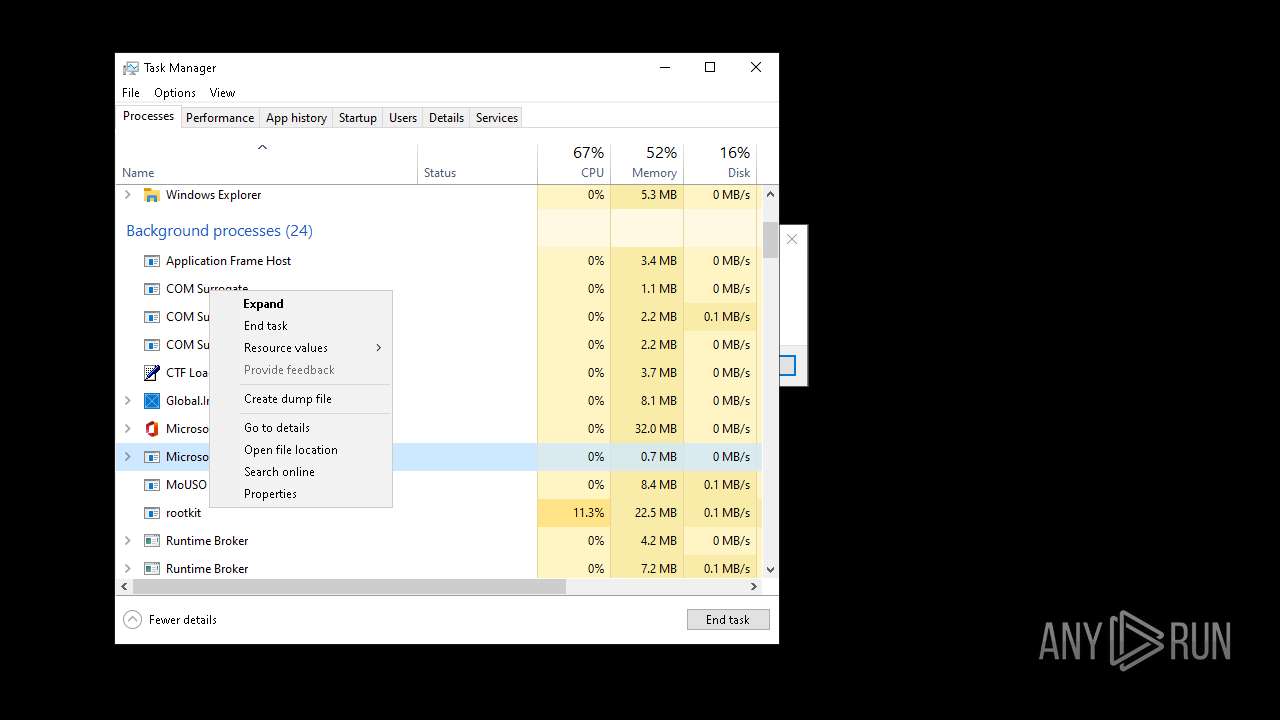
MALICIOUS
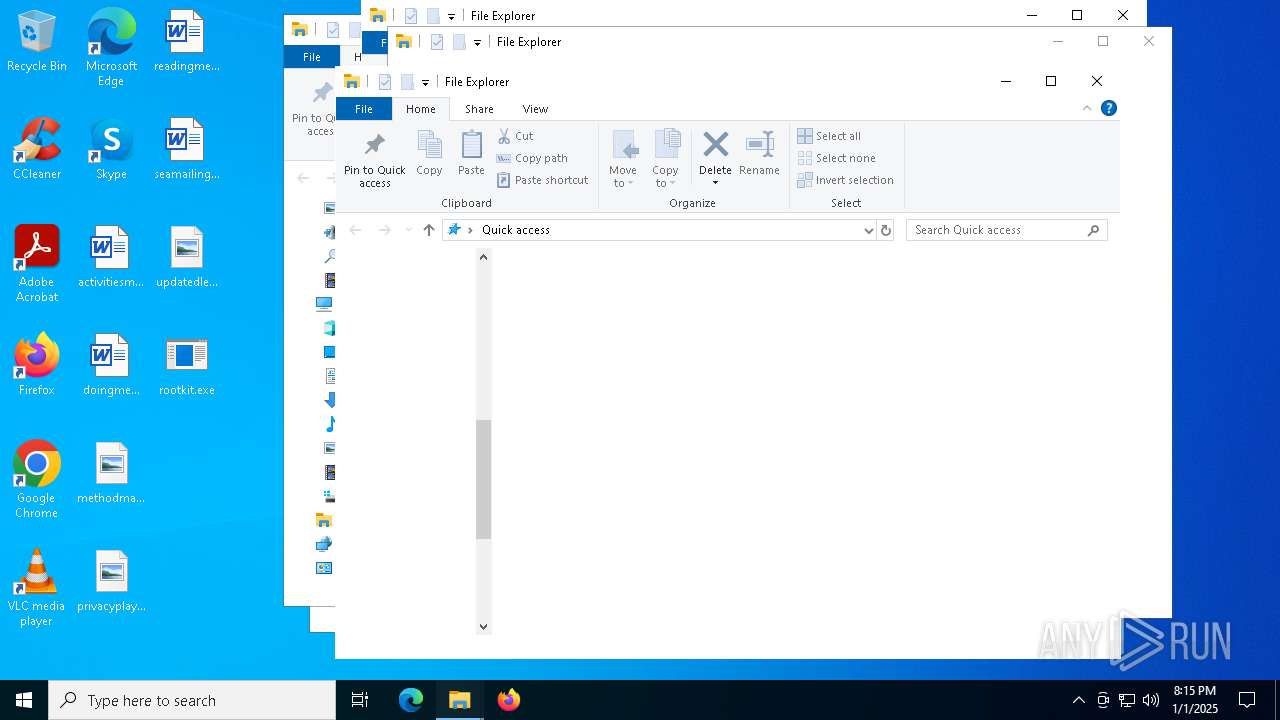
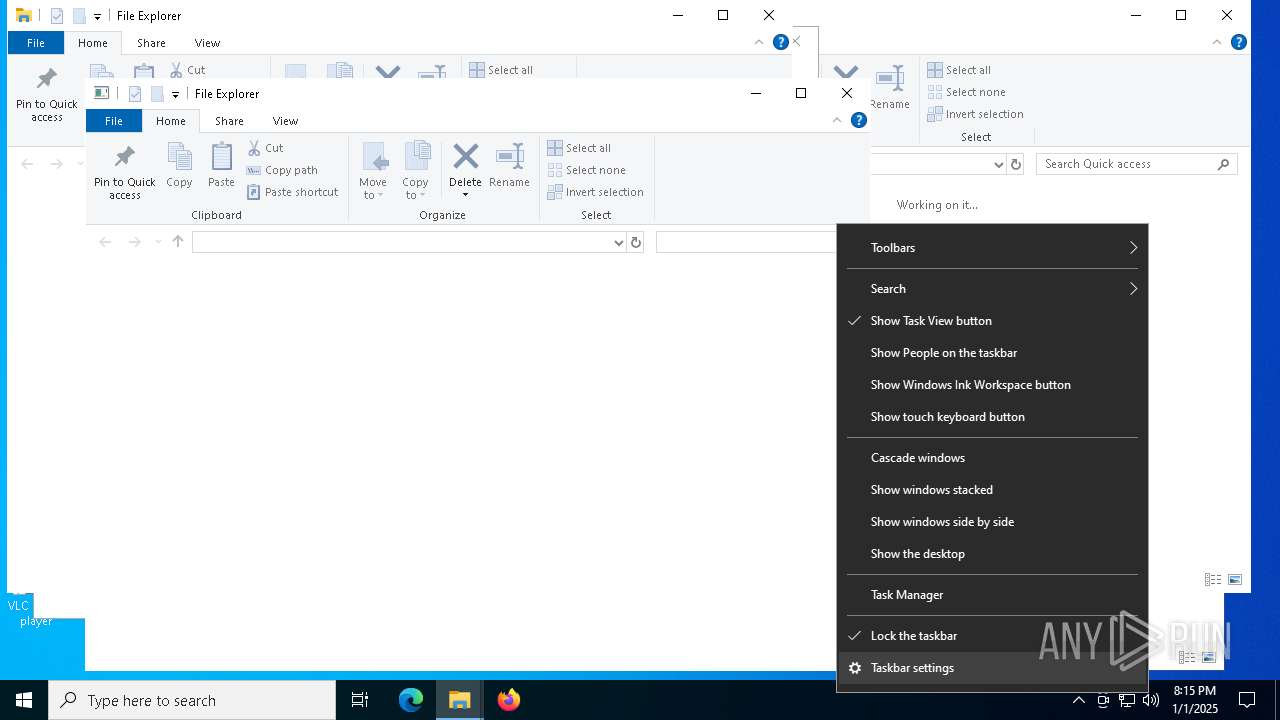
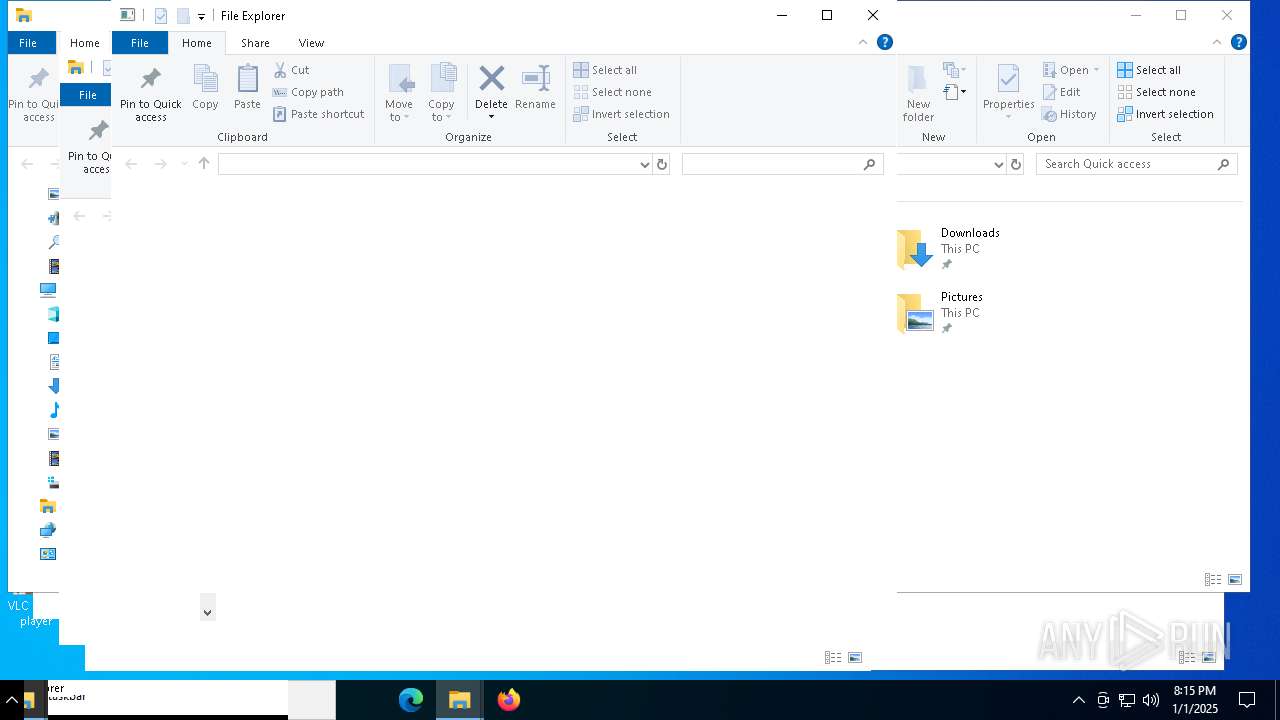
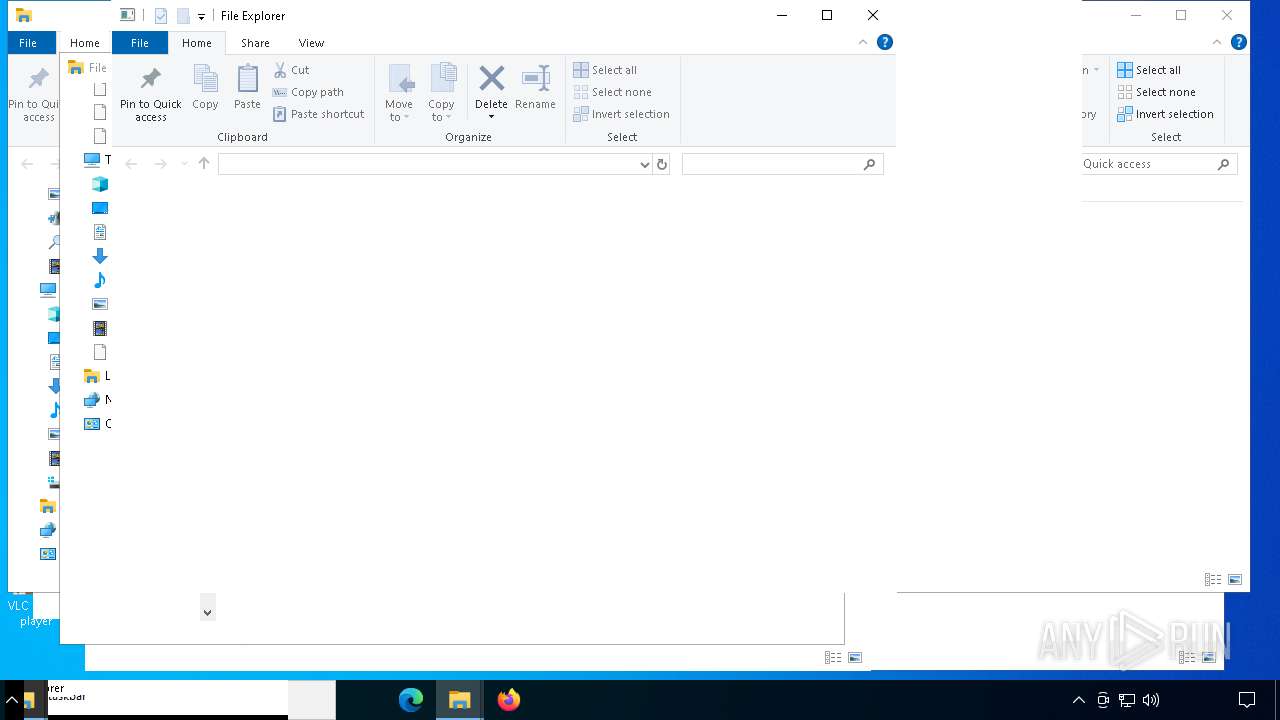
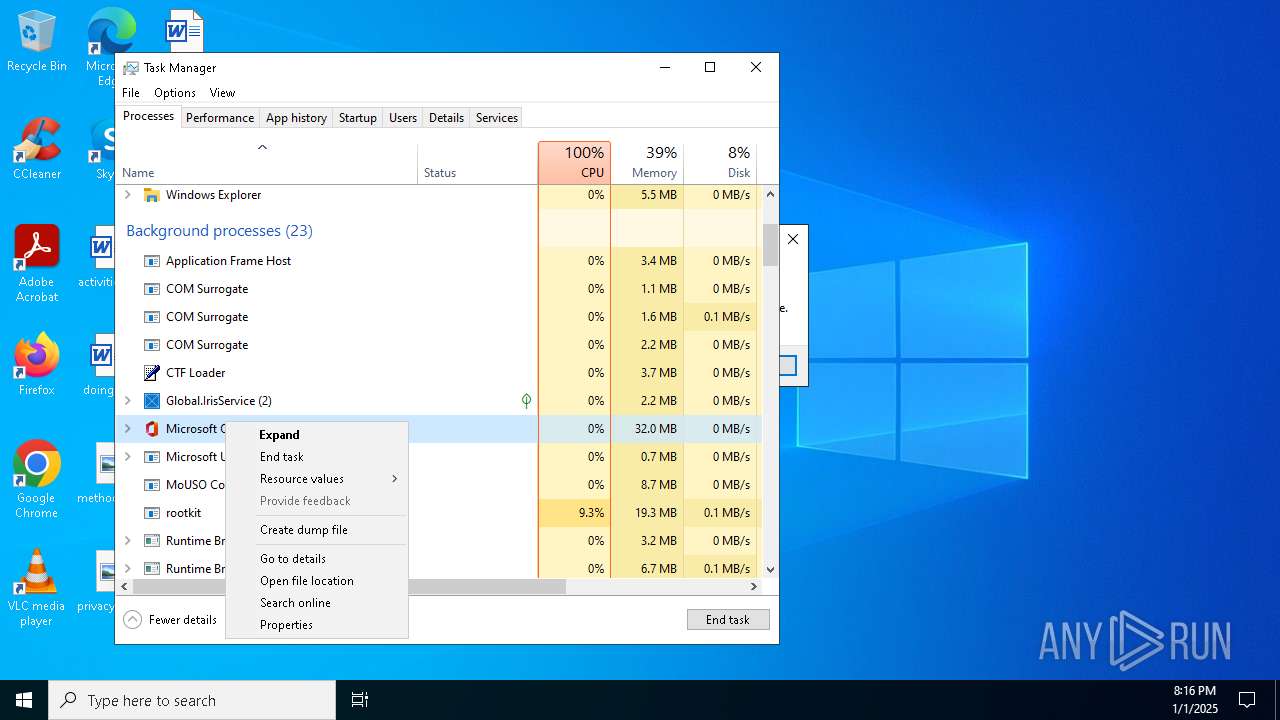
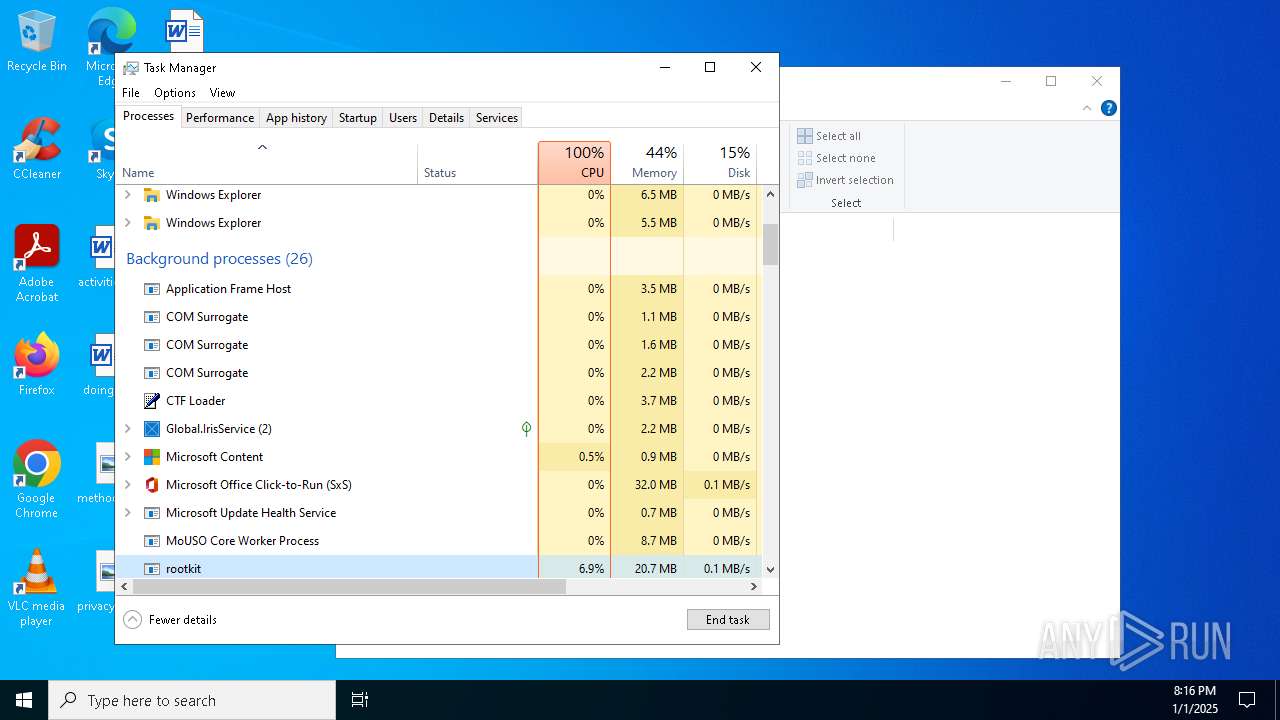
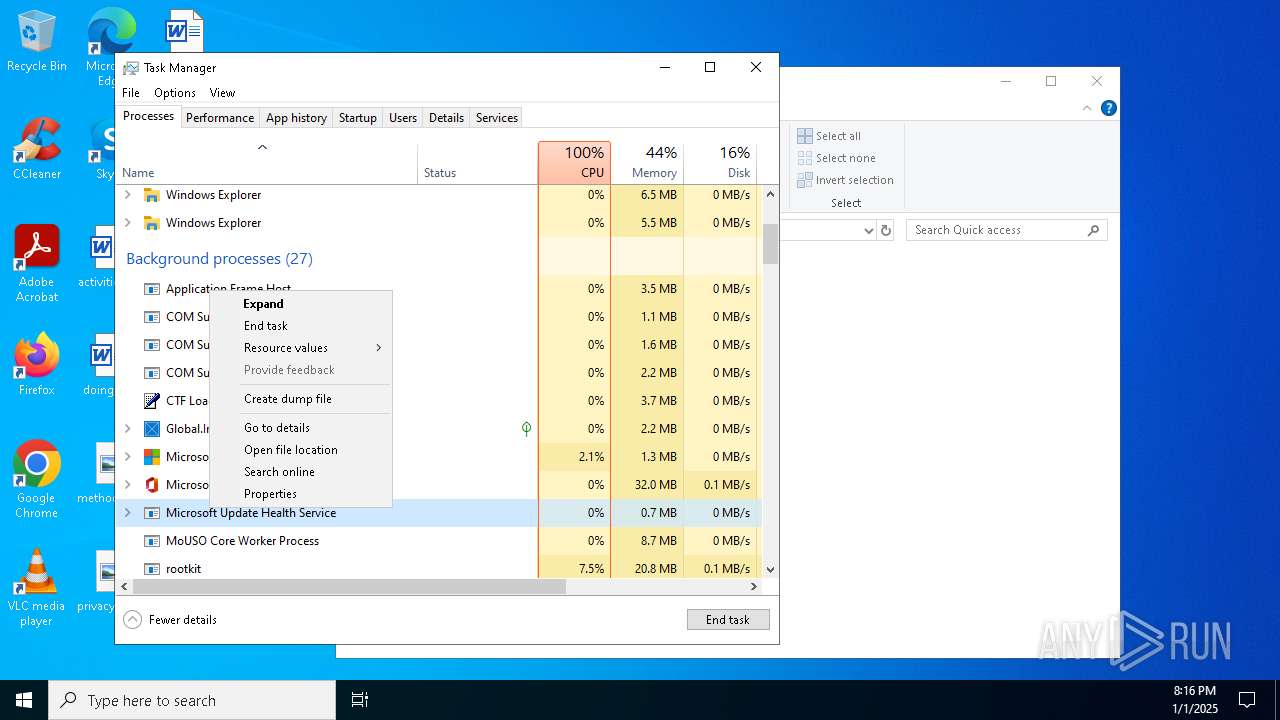
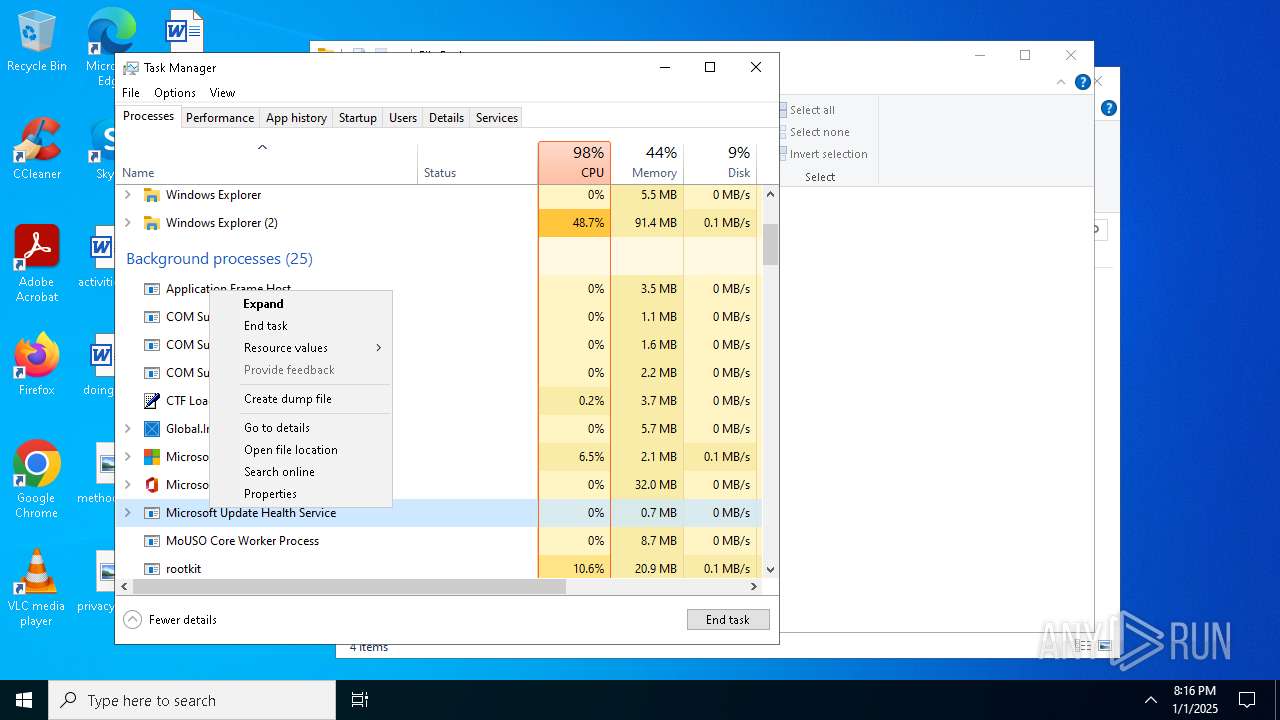
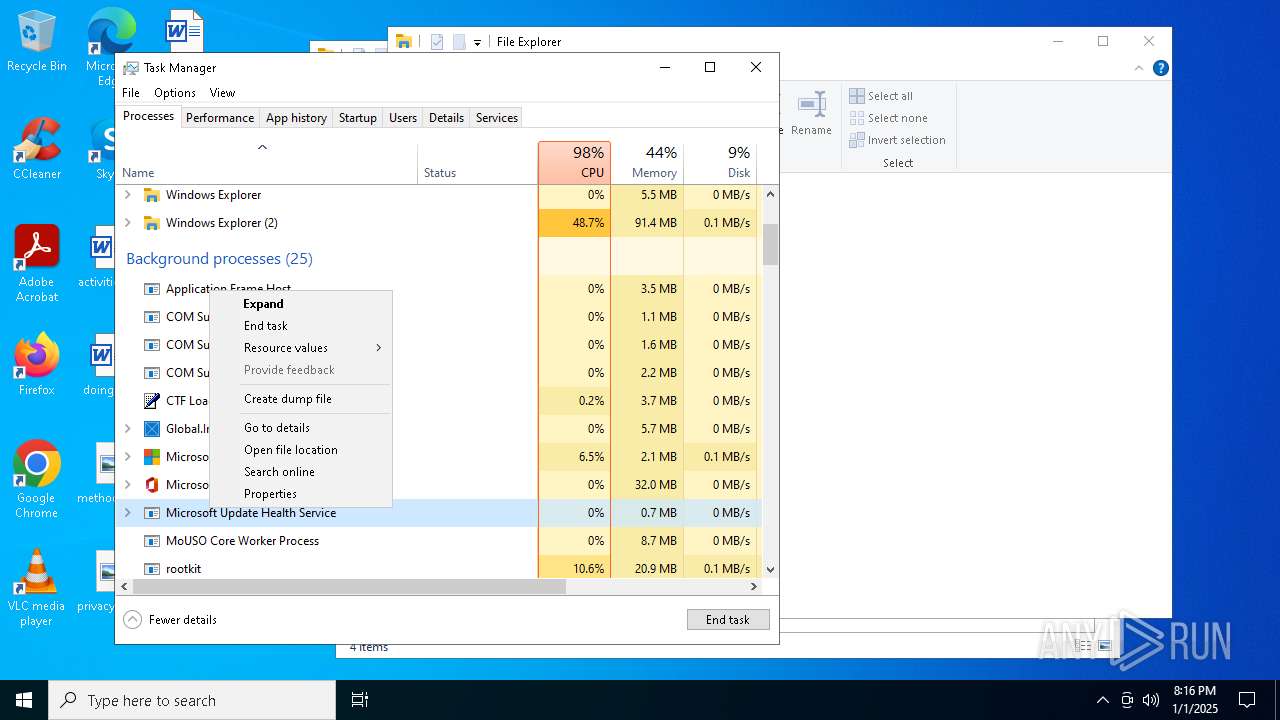
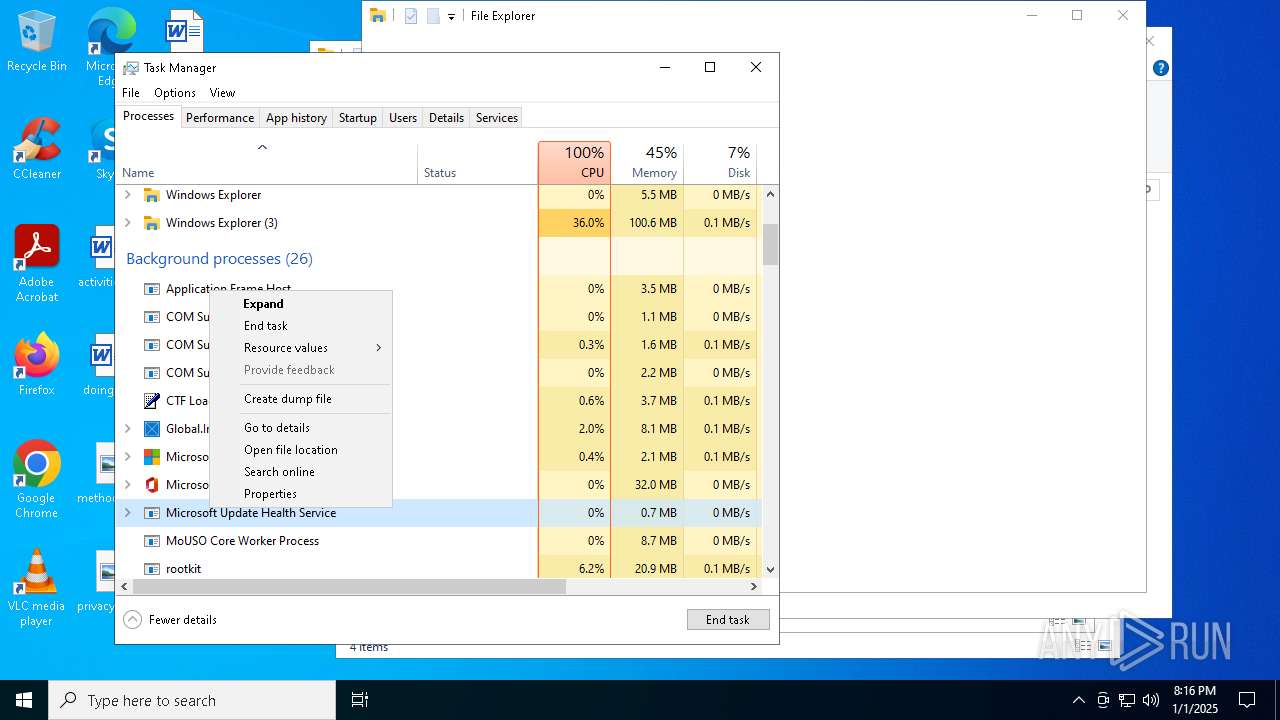
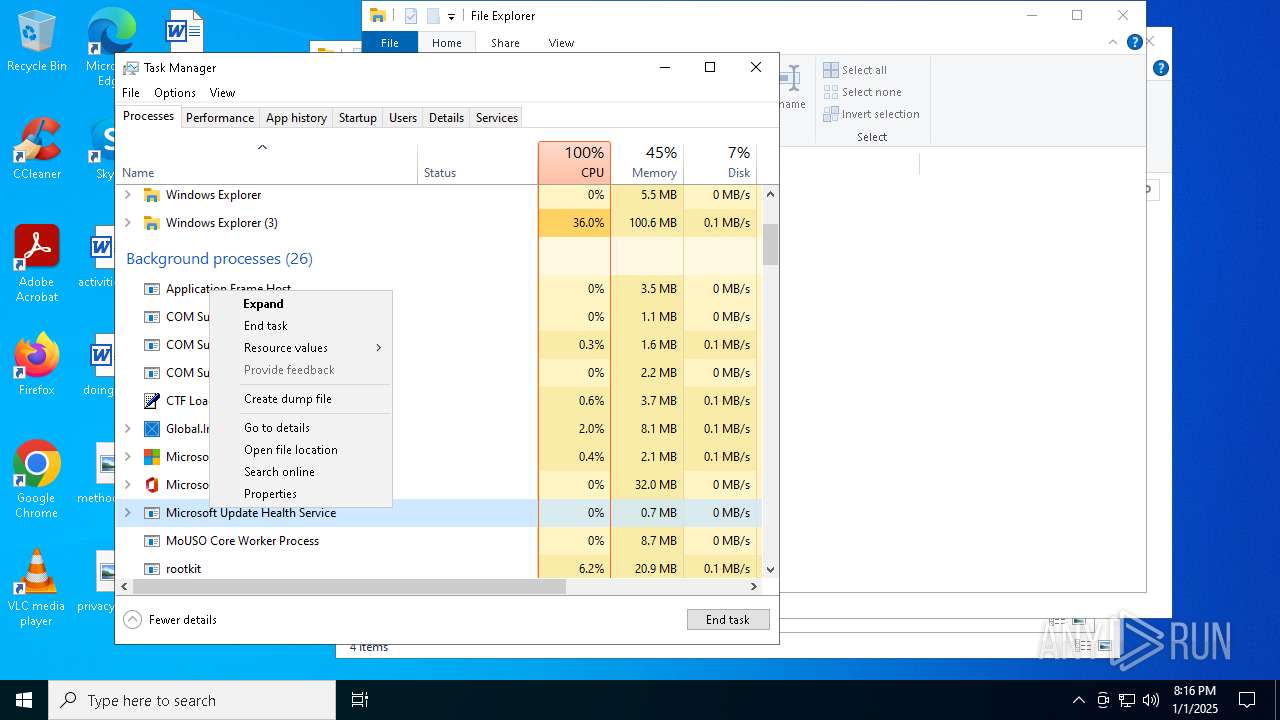
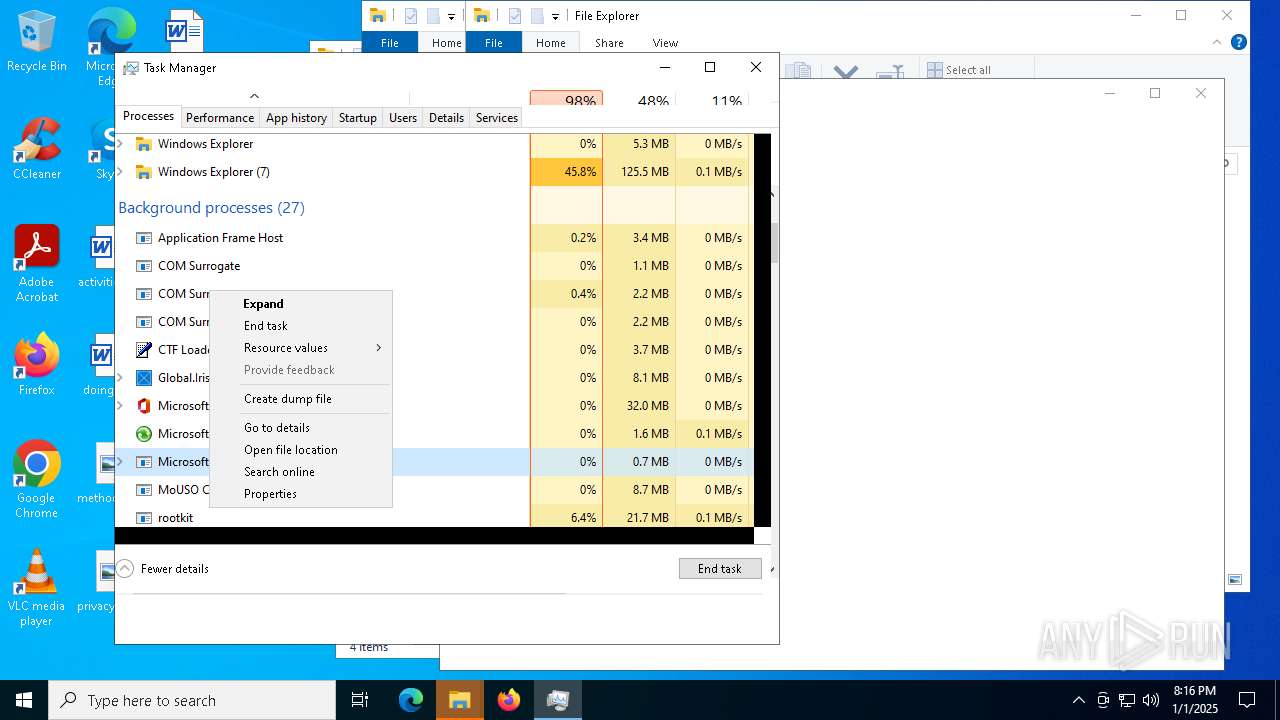
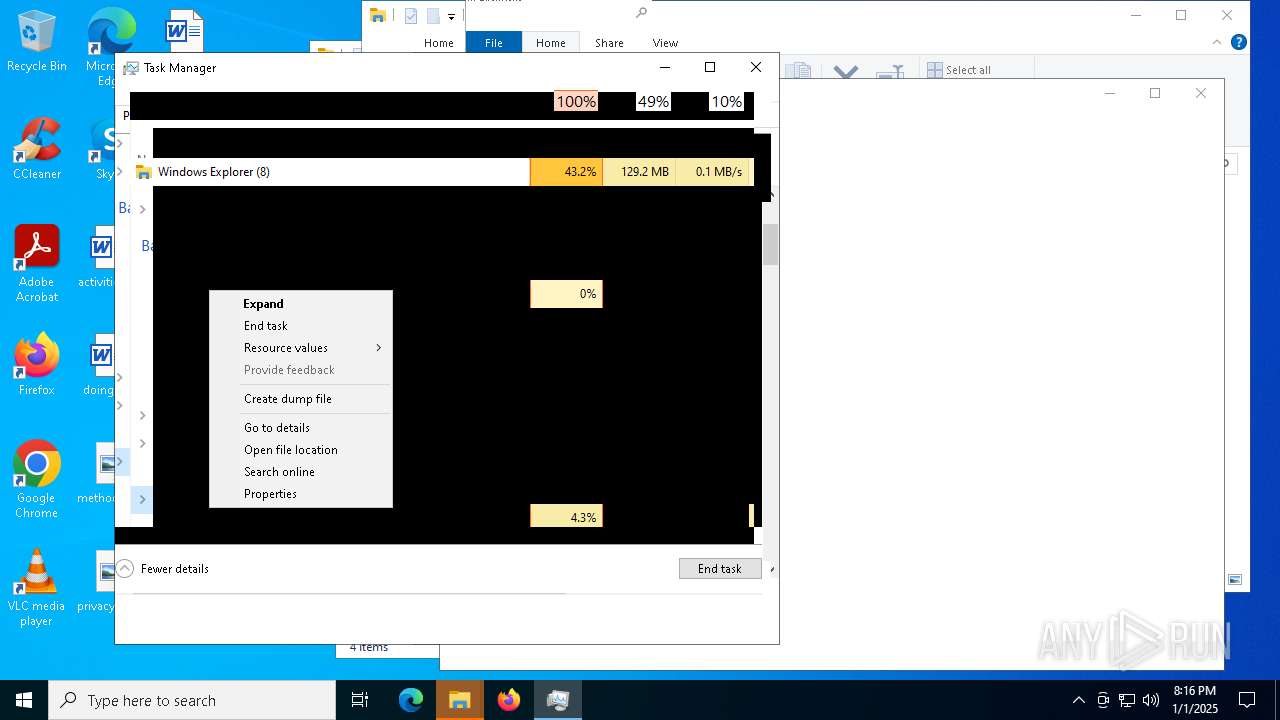
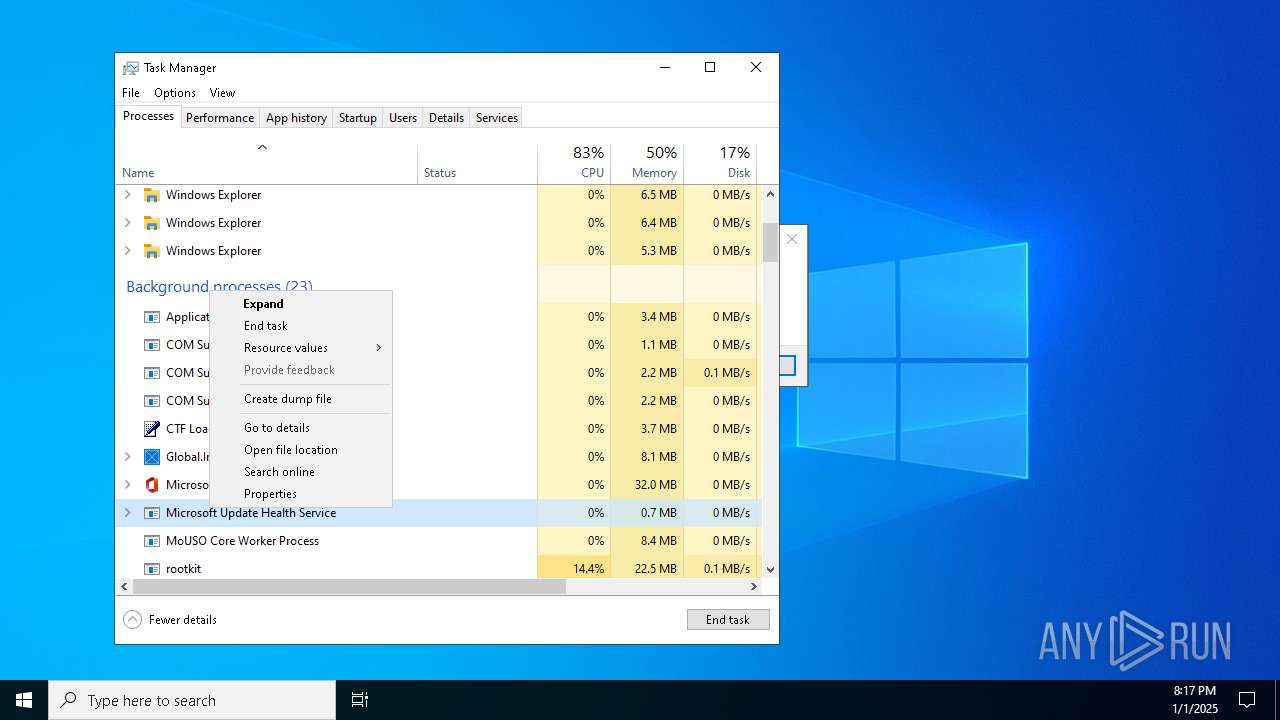
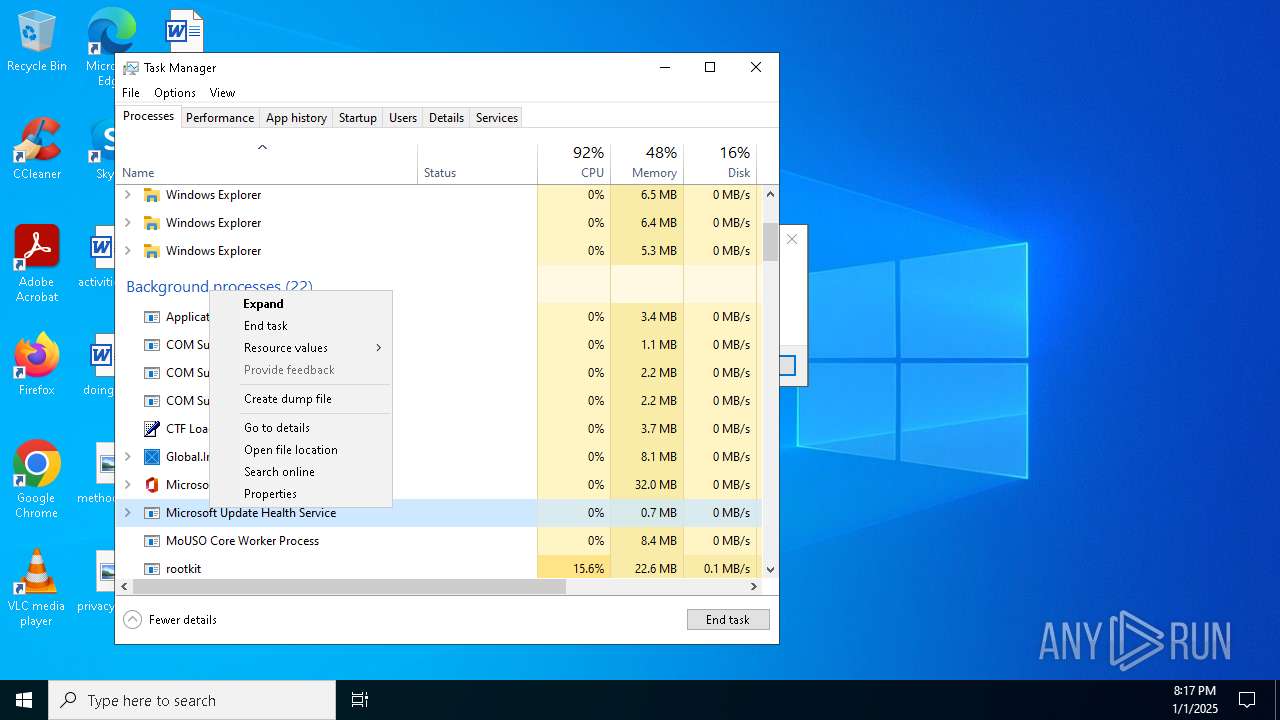
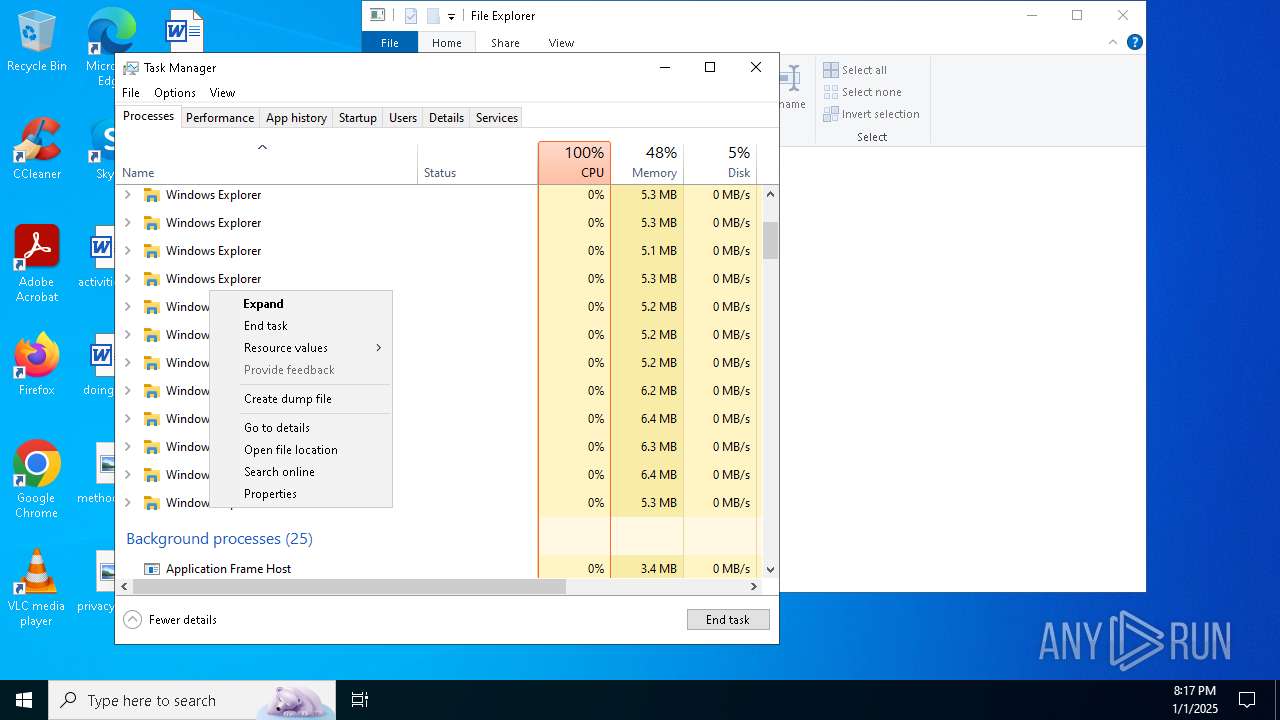
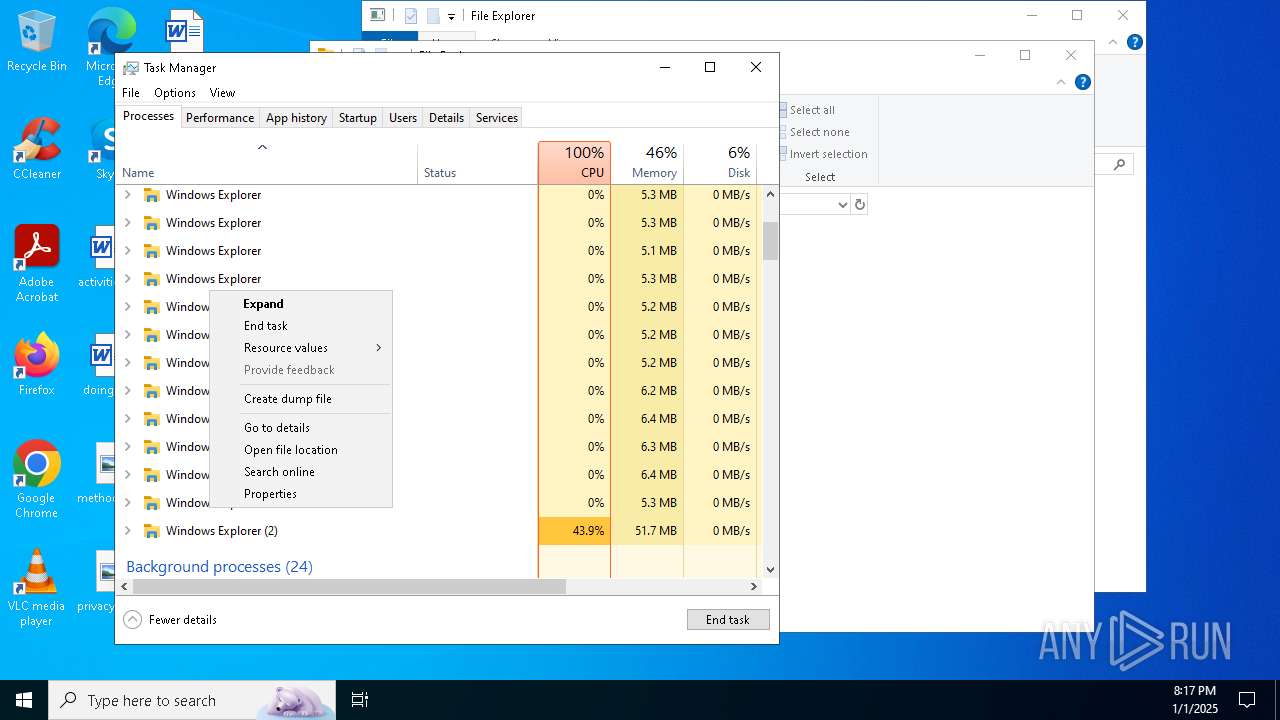
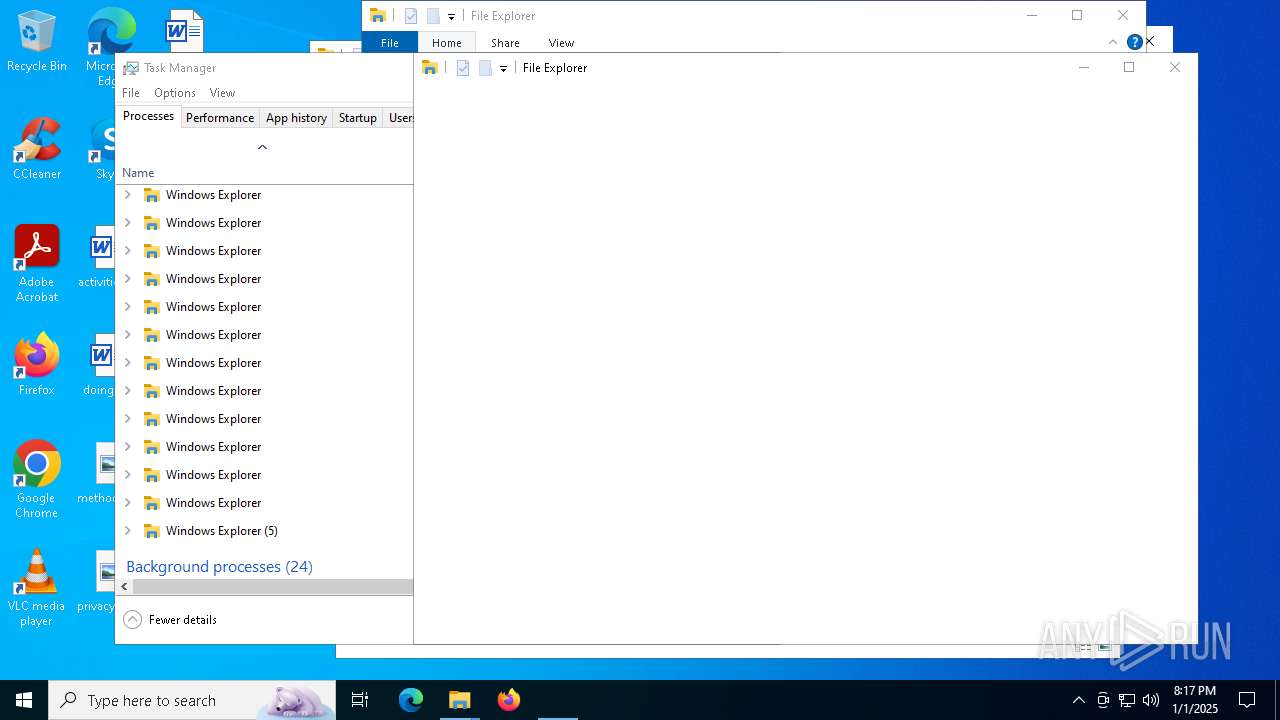
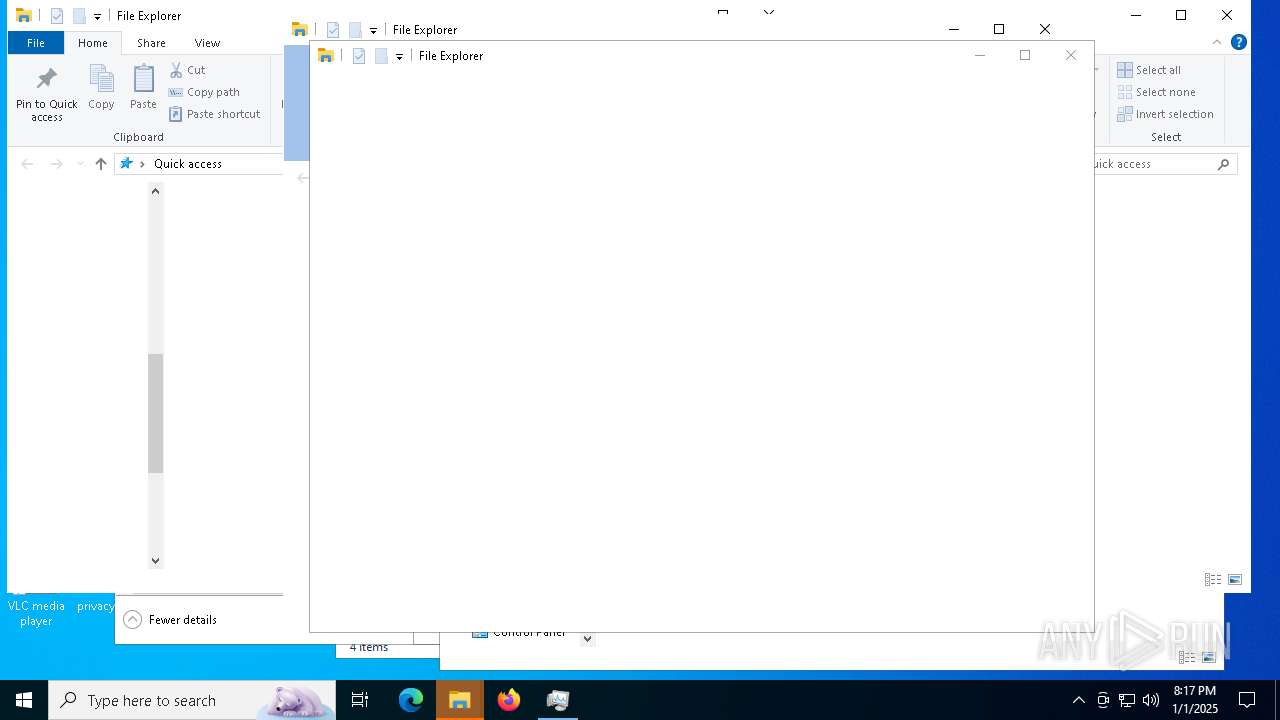
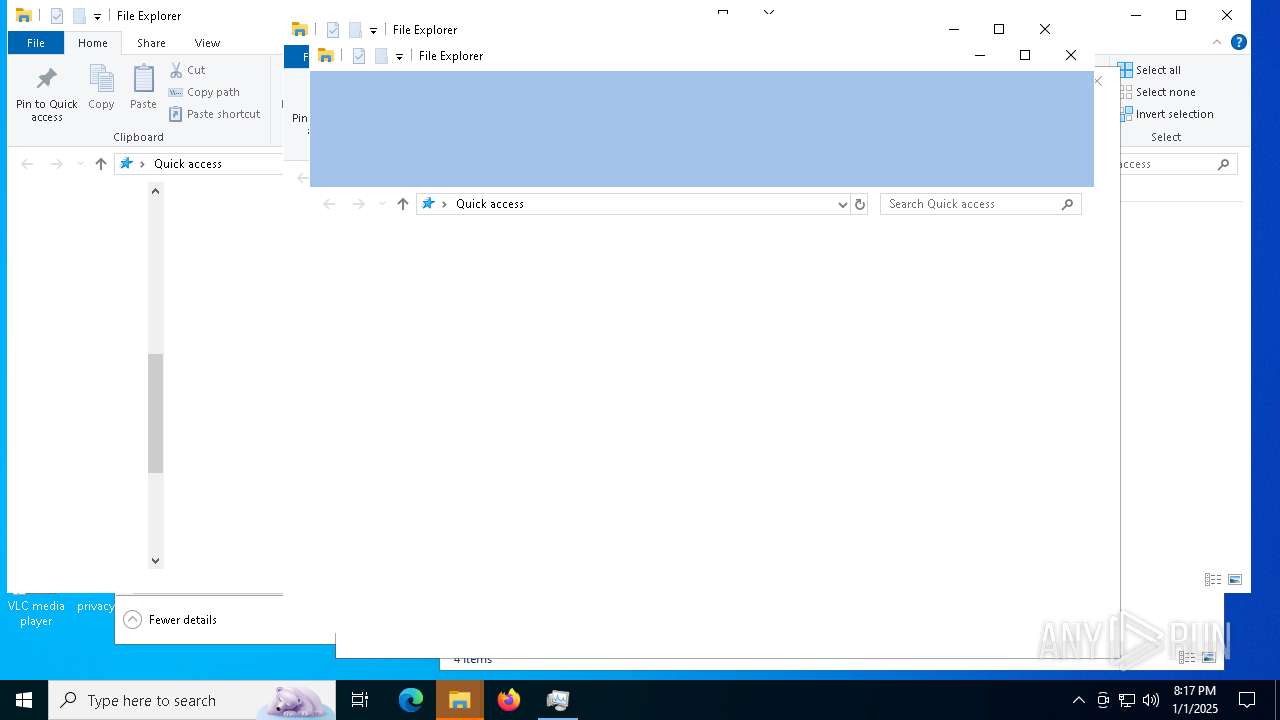
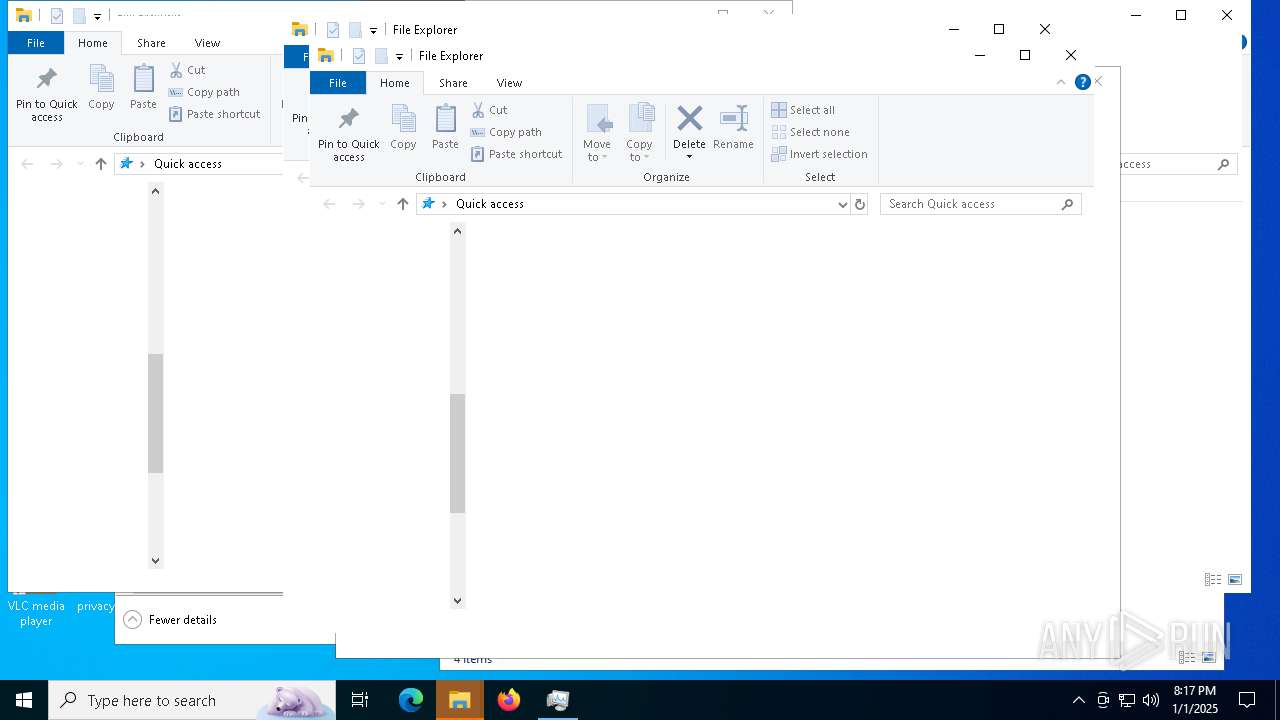
Application was injected by another process
- explorer.exe (PID: 9212)
- explorer.exe (PID: 7684)
Runs injected code in another process
- rootkit.exe (PID: 4912)
SUSPICIOUS
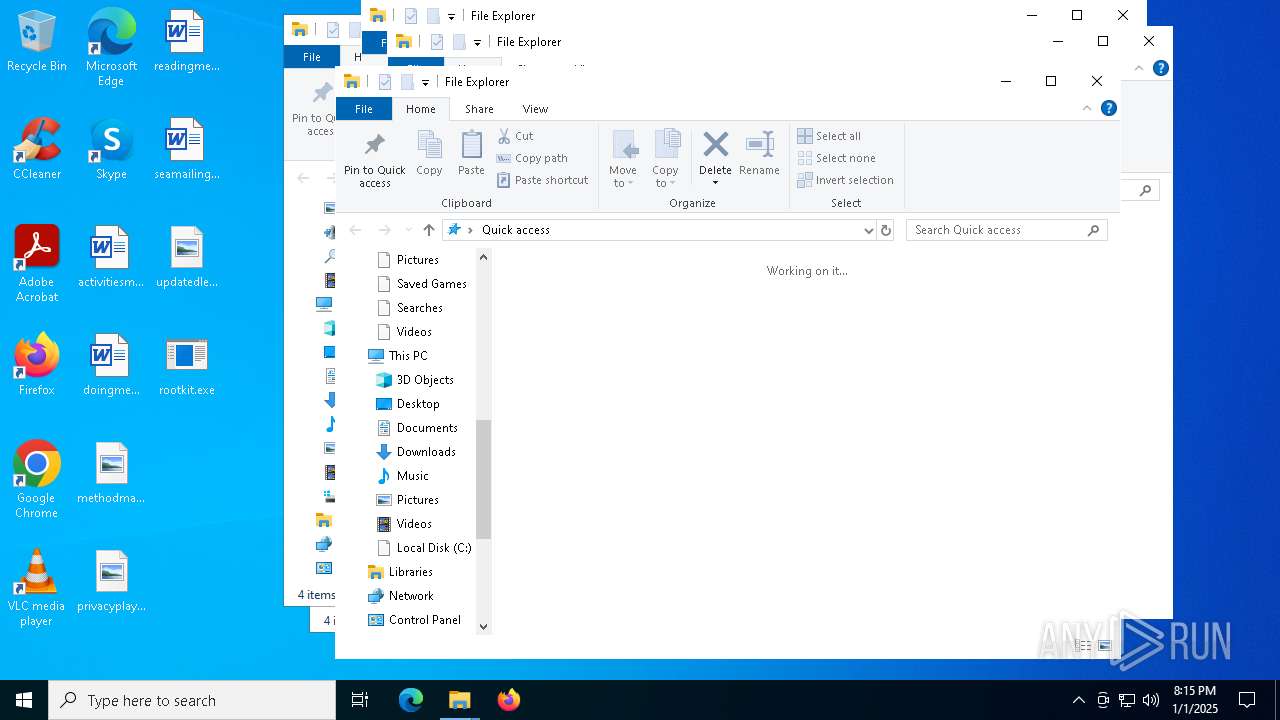
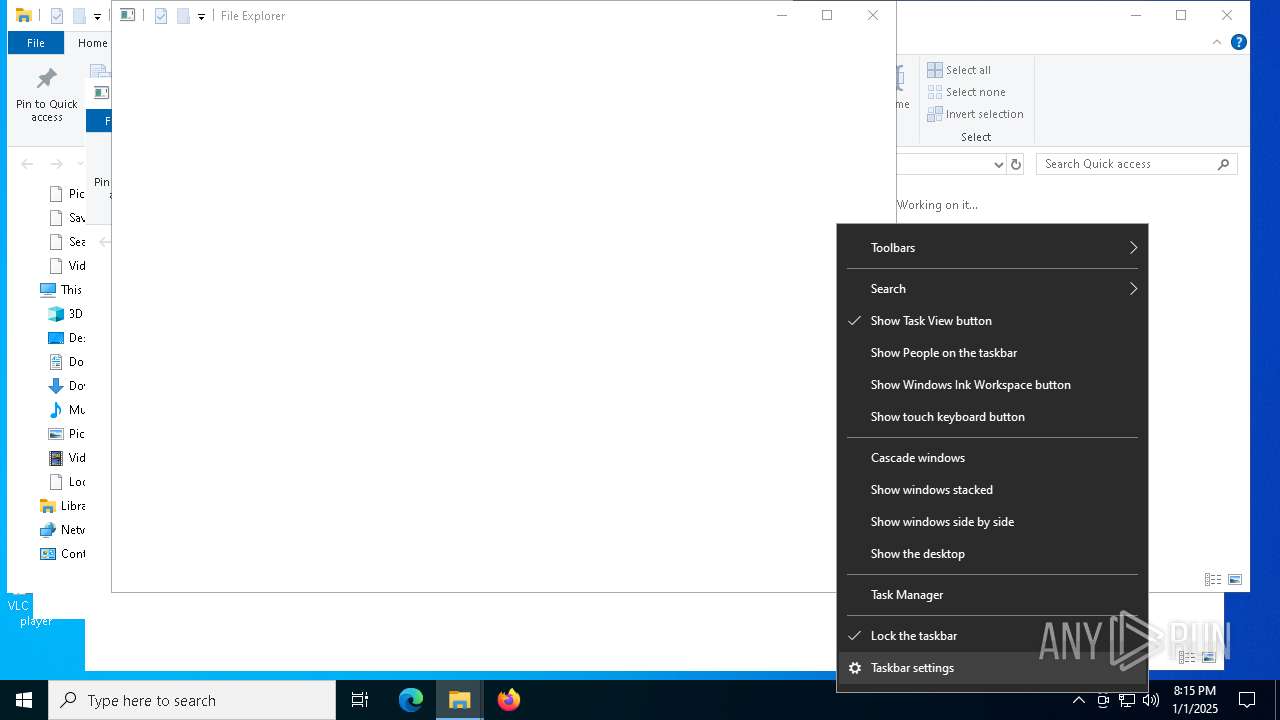
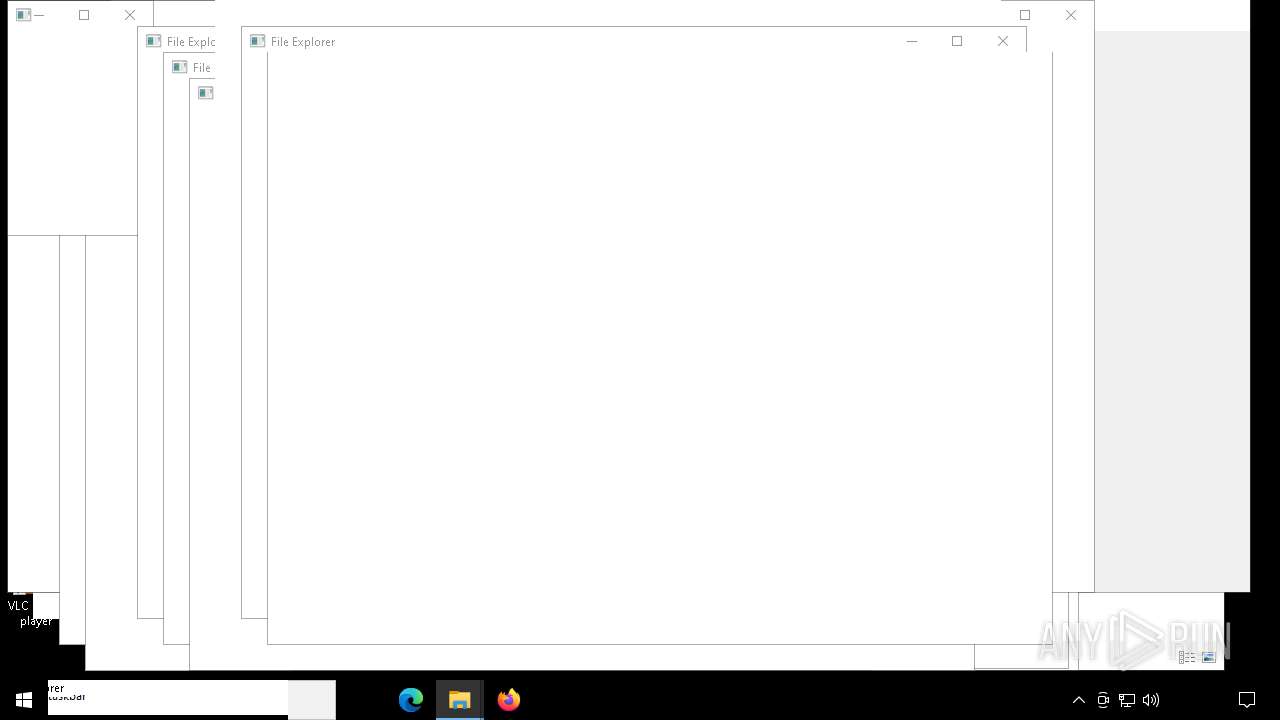
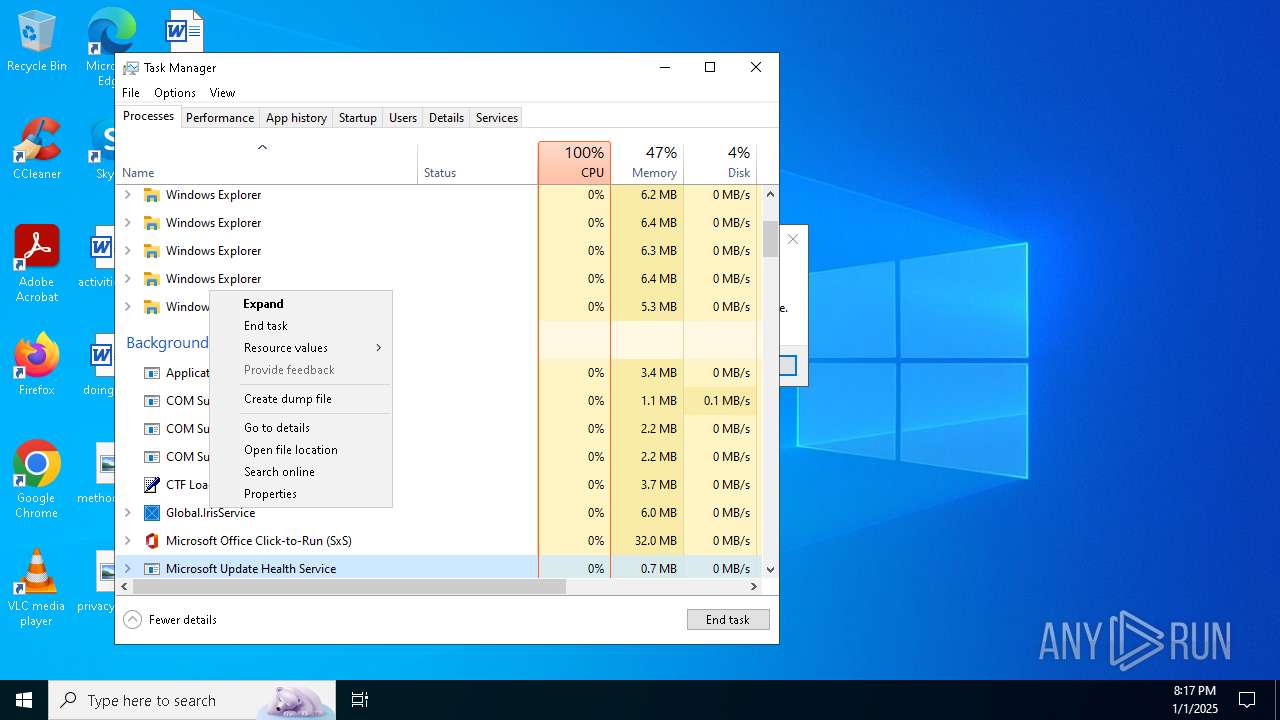
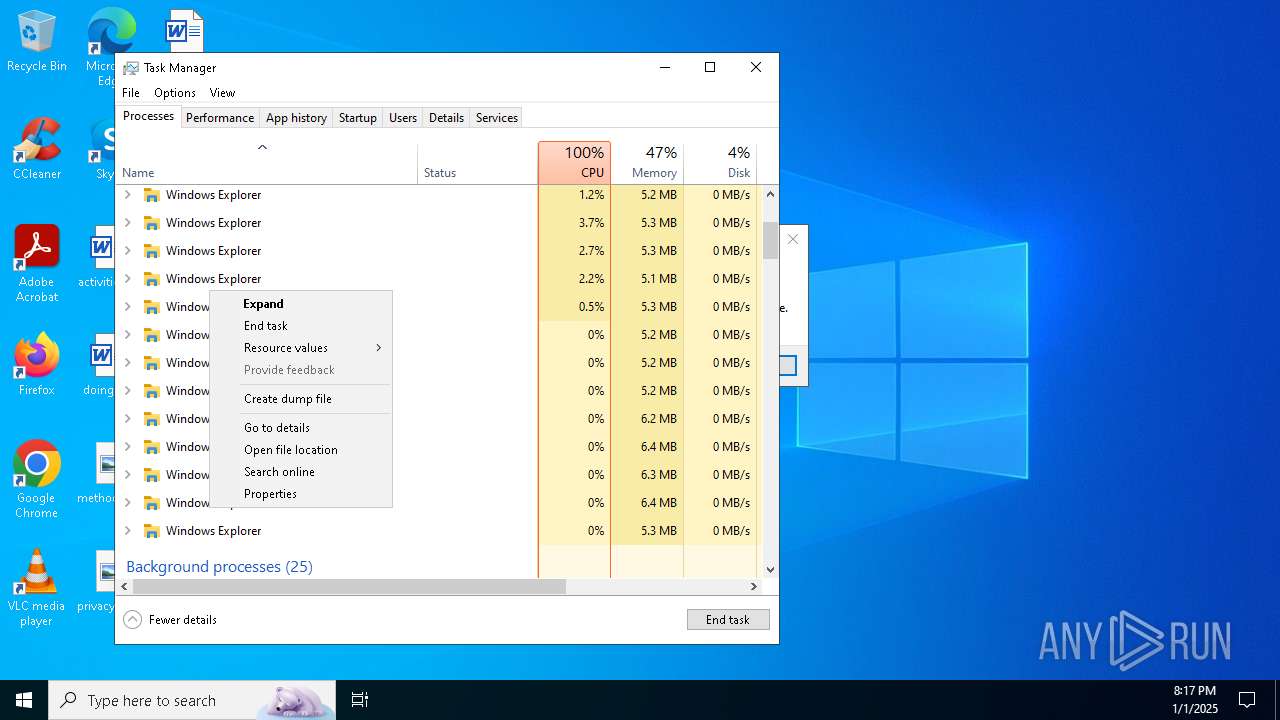
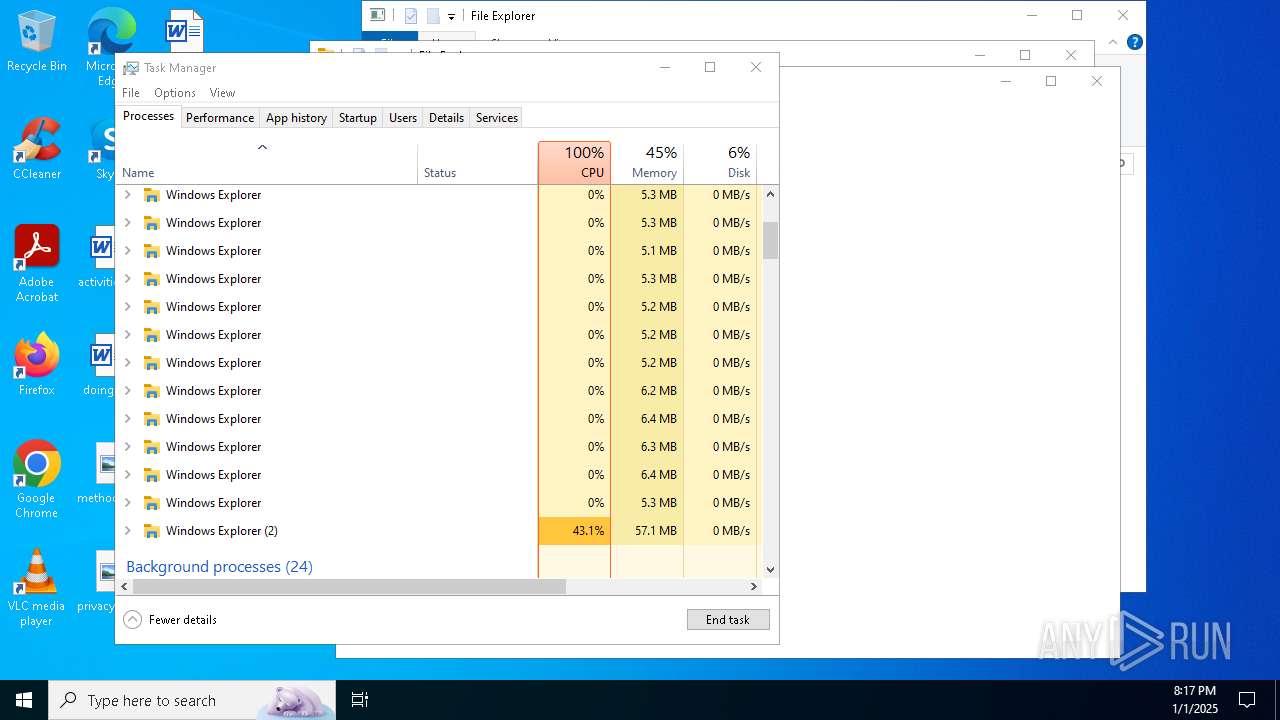
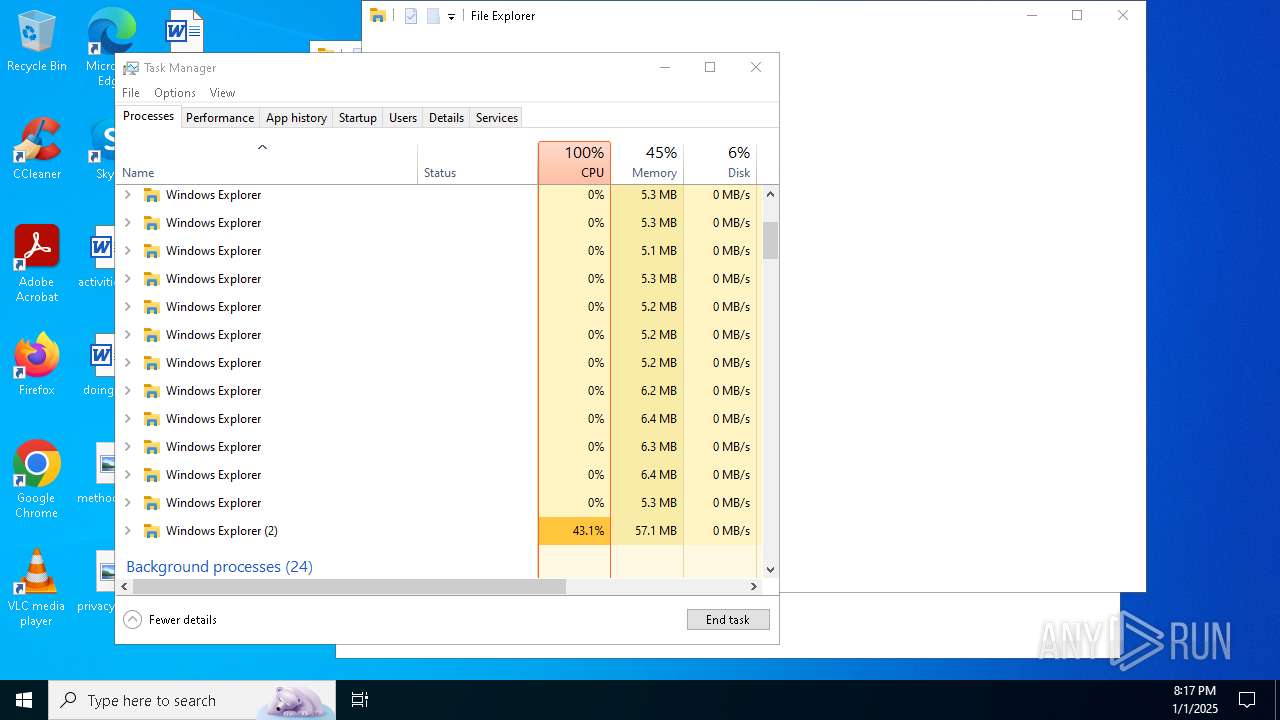
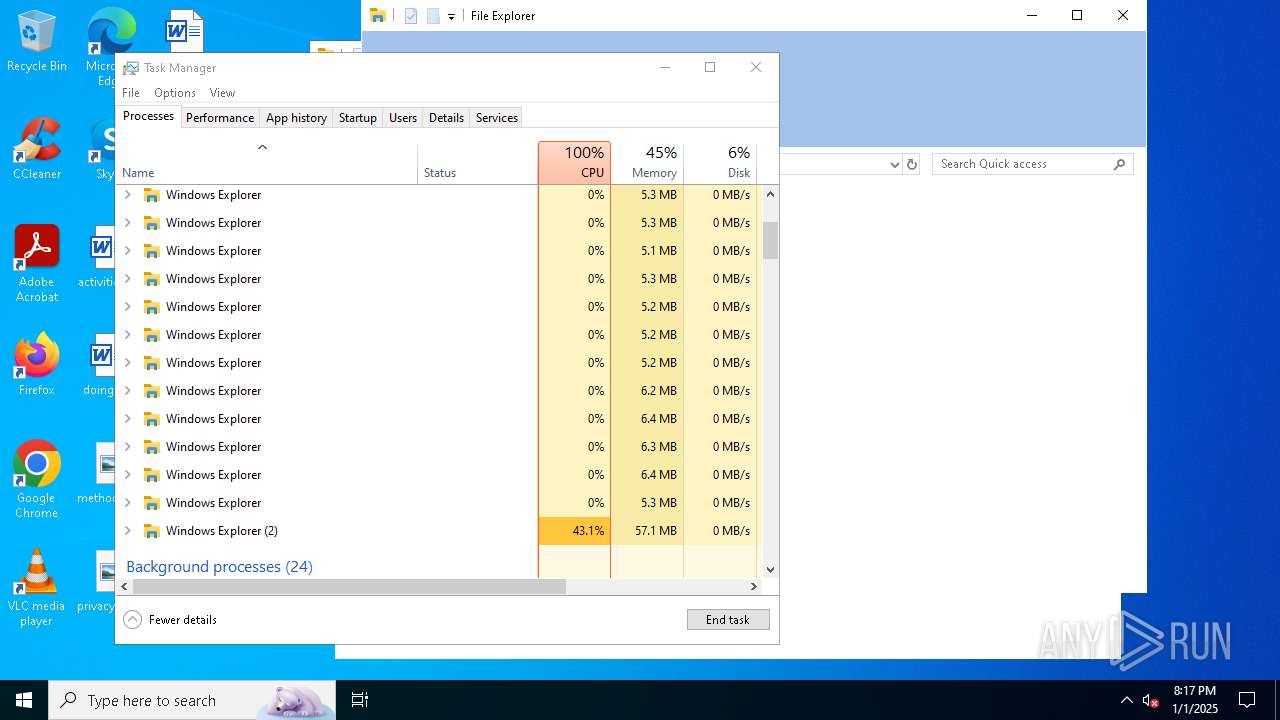
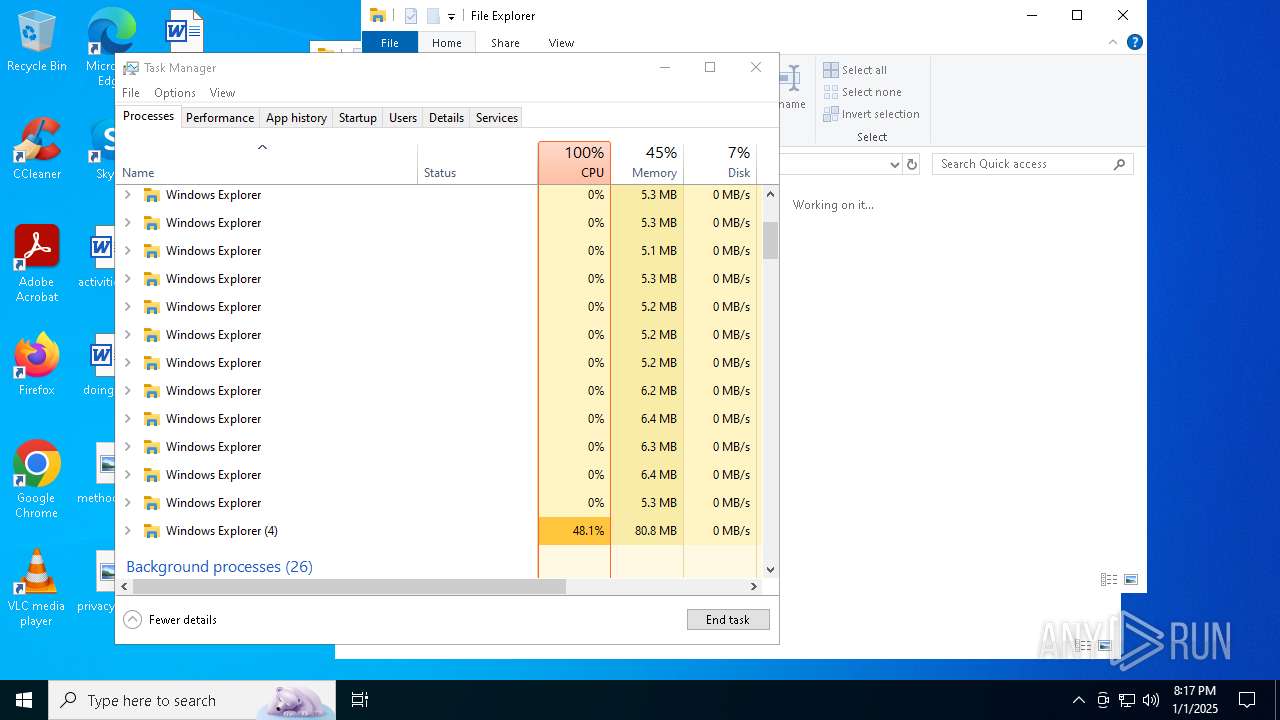
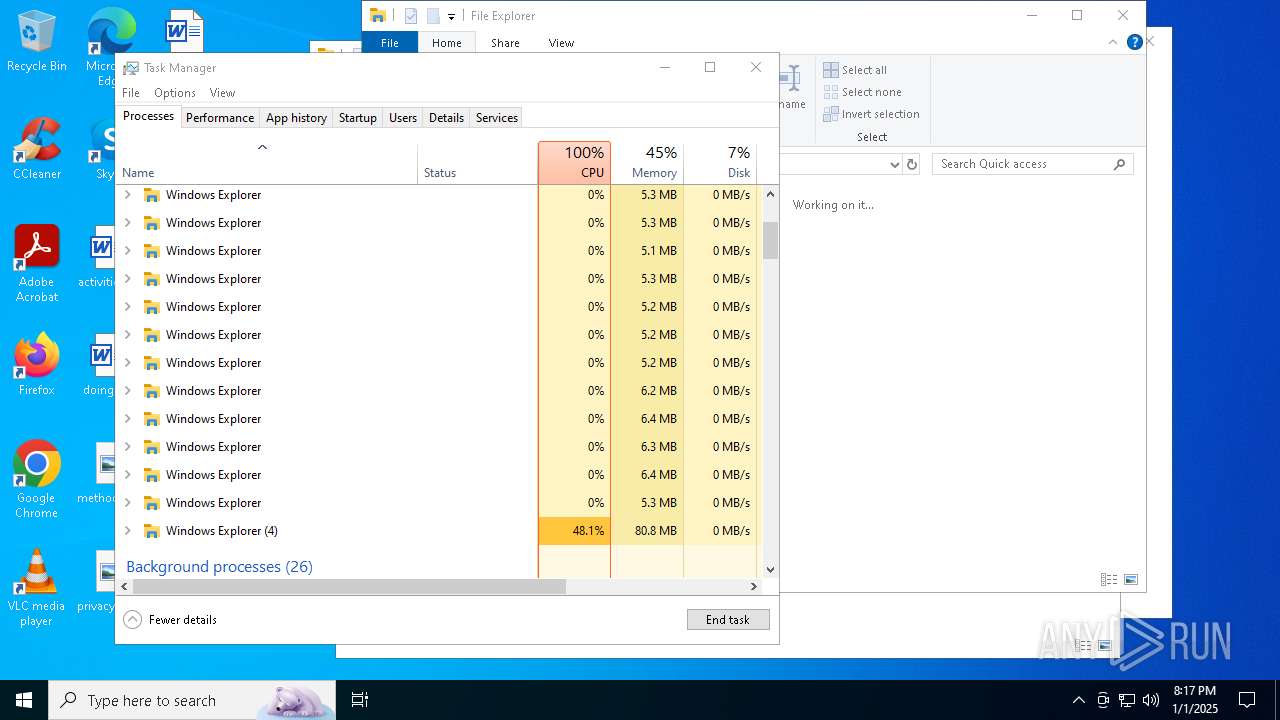
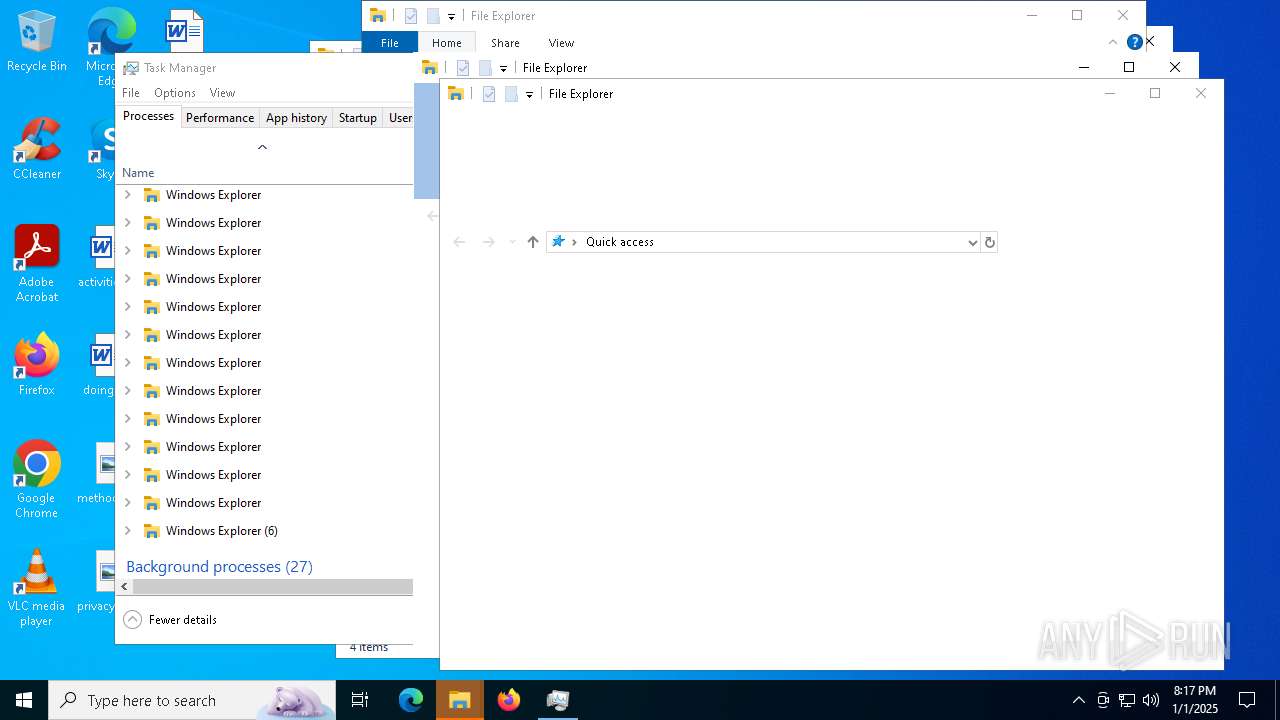
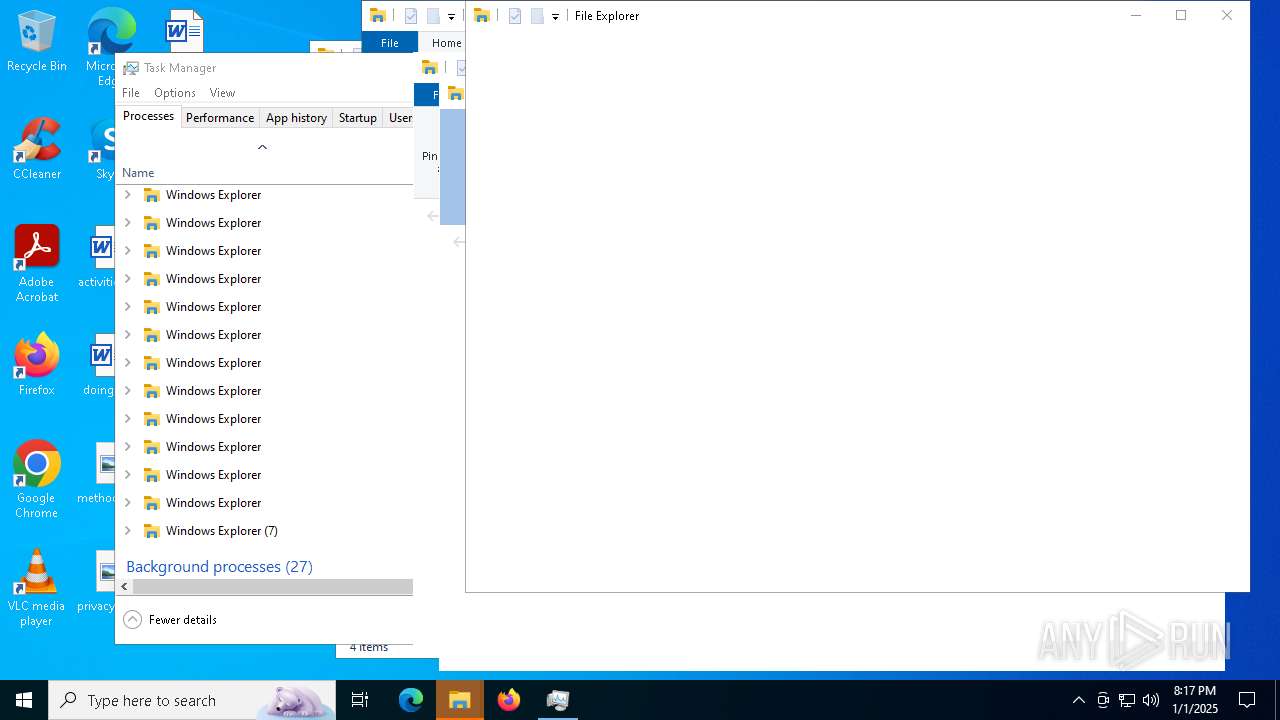
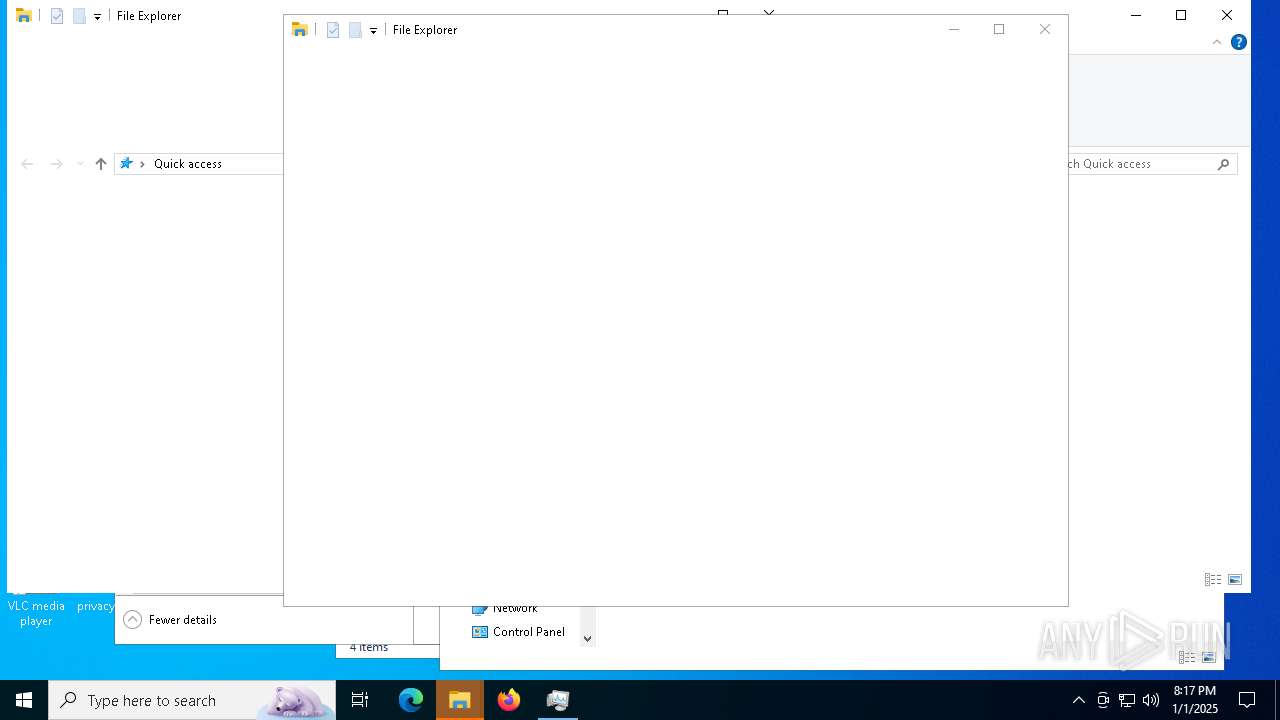
Executes application which crashes
- explorer.exe (PID: 6808)
- explorer.exe (PID: 6312)
- explorer.exe (PID: 6464)
- explorer.exe (PID: 7532)
- explorer.exe (PID: 8140)
- explorer.exe (PID: 7240)
- explorer.exe (PID: 7264)
- explorer.exe (PID: 4520)
- explorer.exe (PID: 6076)
- explorer.exe (PID: 6668)
- explorer.exe (PID: 8116)
- explorer.exe (PID: 7656)
- explorer.exe (PID: 7272)
- explorer.exe (PID: 6912)
- explorer.exe (PID: 7928)
- explorer.exe (PID: 7304)
- explorer.exe (PID: 440)
- explorer.exe (PID: 2572)
- explorer.exe (PID: 7020)
- explorer.exe (PID: 8140)
- explorer.exe (PID: 7288)
- explorer.exe (PID: 6664)
- explorer.exe (PID: 8472)
- explorer.exe (PID: 8620)
- explorer.exe (PID: 9212)
- explorer.exe (PID: 4128)
- explorer.exe (PID: 1224)
- explorer.exe (PID: 9040)
- explorer.exe (PID: 9036)
- explorer.exe (PID: 5640)
- explorer.exe (PID: 2444)
- explorer.exe (PID: 3932)
- explorer.exe (PID: 9116)
- explorer.exe (PID: 4520)
- explorer.exe (PID: 5288)
- explorer.exe (PID: 5640)
- explorer.exe (PID: 1412)
- explorer.exe (PID: 5096)
- explorer.exe (PID: 4360)
- explorer.exe (PID: 4500)
- explorer.exe (PID: 6664)
- explorer.exe (PID: 7404)
- explorer.exe (PID: 3420)
- explorer.exe (PID: 7736)
- explorer.exe (PID: 7476)
- explorer.exe (PID: 7548)
- explorer.exe (PID: 5096)
- explorer.exe (PID: 6880)
- explorer.exe (PID: 2168)
- explorer.exe (PID: 7312)
- explorer.exe (PID: 2728)
- explorer.exe (PID: 7988)
- explorer.exe (PID: 3816)
- explorer.exe (PID: 7416)
- explorer.exe (PID: 6584)
- explorer.exe (PID: 5660)
- explorer.exe (PID: 3144)
- explorer.exe (PID: 6480)
- explorer.exe (PID: 5440)
- explorer.exe (PID: 9116)
- explorer.exe (PID: 5740)
- explorer.exe (PID: 1920)
- explorer.exe (PID: 7684)
- explorer.exe (PID: 9020)
- explorer.exe (PID: 8060)
- explorer.exe (PID: 8400)
- explorer.exe (PID: 3144)
- explorer.exe (PID: 1448)
- explorer.exe (PID: 7452)
- explorer.exe (PID: 8248)
- explorer.exe (PID: 5472)
- explorer.exe (PID: 2512)
- explorer.exe (PID: 8520)
- explorer.exe (PID: 7728)
- explorer.exe (PID: 5640)
- explorer.exe (PID: 5880)
- explorer.exe (PID: 5000)
- explorer.exe (PID: 1016)
- explorer.exe (PID: 4900)
- explorer.exe (PID: 4736)
- explorer.exe (PID: 7872)
- explorer.exe (PID: 8624)
- explorer.exe (PID: 5344)
- explorer.exe (PID: 7672)
- explorer.exe (PID: 9160)
- explorer.exe (PID: 8348)
- explorer.exe (PID: 8660)
- explorer.exe (PID: 9120)
- explorer.exe (PID: 8444)
- explorer.exe (PID: 8016)
- explorer.exe (PID: 2548)
- explorer.exe (PID: 1496)
- explorer.exe (PID: 9064)
- explorer.exe (PID: 5472)
Reads the date of Windows installation
- rootkit.exe (PID: 4912)
- SearchApp.exe (PID: 7036)
The process creates files with name similar to system file names
- WerFault.exe (PID: 6640)
- WerFault.exe (PID: 7056)
- WerFault.exe (PID: 8180)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 3536)
- WerFault.exe (PID: 7100)
- WerFault.exe (PID: 8092)
- WerFault.exe (PID: 3364)
- WerFault.exe (PID: 6968)
- WerFault.exe (PID: 7740)
- WerFault.exe (PID: 7432)
- WerFault.exe (PID: 5244)
- WerFault.exe (PID: 7780)
- wermgr.exe (PID: 3620)
- wermgr.exe (PID: 7216)
- WerFault.exe (PID: 6652)
- WerFault.exe (PID: 6300)
- WerFault.exe (PID: 7244)
- WerFault.exe (PID: 7748)
- WerFault.exe (PID: 5780)
- WerFault.exe (PID: 5000)
- WerFault.exe (PID: 7068)
- WerFault.exe (PID: 5560)
- WerFault.exe (PID: 6428)
- WerFault.exe (PID: 8544)
- WerFault.exe (PID: 2828)
- WerFault.exe (PID: 8820)
- WerFault.exe (PID: 8988)
- WerFault.exe (PID: 7424)
- WerFault.exe (PID: 6340)
- WerFault.exe (PID: 8812)
- WerFault.exe (PID: 8736)
- WerFault.exe (PID: 2572)
- WerFault.exe (PID: 7516)
- WerFault.exe (PID: 8460)
- WerFault.exe (PID: 8416)
- WerFault.exe (PID: 6716)
- WerFault.exe (PID: 204)
- WerFault.exe (PID: 7328)
- WerFault.exe (PID: 6884)
- WerFault.exe (PID: 5632)
- WerFault.exe (PID: 8256)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 6152)
- WerFault.exe (PID: 3532)
- WerFault.exe (PID: 1016)
- WerFault.exe (PID: 8464)
- wermgr.exe (PID: 2676)
- WerFault.exe (PID: 8012)
- WerFault.exe (PID: 5788)
- WerFault.exe (PID: 8612)
- WerFault.exe (PID: 5888)
- WerFault.exe (PID: 5788)
- WerFault.exe (PID: 7356)
- WerFault.exe (PID: 6036)
Reads security settings of Internet Explorer
- rootkit.exe (PID: 4912)
Reads Internet Explorer settings
- explorer.exe (PID: 1496)
INFO
Reads the computer name
- rootkit.exe (PID: 4912)
- SearchApp.exe (PID: 7036)
- StartMenuExperienceHost.exe (PID: 7500)
- StartMenuExperienceHost.exe (PID: 8732)
- TextInputHost.exe (PID: 5408)
Process checks computer location settings
- rootkit.exe (PID: 4912)
- SearchApp.exe (PID: 7036)
- StartMenuExperienceHost.exe (PID: 8732)
- SearchApp.exe (PID: 6544)
Checks supported languages
- rootkit.exe (PID: 4912)
- SearchApp.exe (PID: 7036)
- StartMenuExperienceHost.exe (PID: 7500)
- TextInputHost.exe (PID: 6300)
- TextInputHost.exe (PID: 5408)
- StartMenuExperienceHost.exe (PID: 8732)
- SearchApp.exe (PID: 6544)
Checks proxy server information
- WerFault.exe (PID: 6640)
- WerFault.exe (PID: 8180)
- WerFault.exe (PID: 7056)
- WerFault.exe (PID: 3536)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 7100)
- WerFault.exe (PID: 3364)
- WerFault.exe (PID: 8092)
- WerFault.exe (PID: 6968)
- WerFault.exe (PID: 7740)
- WerFault.exe (PID: 7432)
- WerFault.exe (PID: 5244)
- rootkit.exe (PID: 4912)
- WerFault.exe (PID: 7780)
- WerFault.exe (PID: 6652)
- WerFault.exe (PID: 6300)
- WerFault.exe (PID: 5000)
- WerFault.exe (PID: 5780)
- WerFault.exe (PID: 7748)
- WerFault.exe (PID: 7068)
- WerFault.exe (PID: 2828)
- WerFault.exe (PID: 6428)
- WerFault.exe (PID: 8544)
- WerFault.exe (PID: 5560)
- WerFault.exe (PID: 7424)
- WerFault.exe (PID: 6340)
- WerFault.exe (PID: 8736)
- WerFault.exe (PID: 8812)
- WerFault.exe (PID: 7244)
- WerFault.exe (PID: 7552)
- WerFault.exe (PID: 8460)
- WerFault.exe (PID: 6884)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 4672)
- WerFault.exe (PID: 8660)
- WerFault.exe (PID: 8256)
- WerFault.exe (PID: 6152)
- WerFault.exe (PID: 7424)
- SearchApp.exe (PID: 7036)
- WerFault.exe (PID: 3532)
- WerFault.exe (PID: 1016)
- WerFault.exe (PID: 8060)
- WerFault.exe (PID: 4600)
- WerFault.exe (PID: 8464)
- WerFault.exe (PID: 2572)
- WerFault.exe (PID: 8072)
- WerFault.exe (PID: 5548)
- WerFault.exe (PID: 8612)
- WerFault.exe (PID: 5888)
- WerFault.exe (PID: 5740)
- WerFault.exe (PID: 5788)
- WerFault.exe (PID: 8584)
- SearchApp.exe (PID: 6544)
- WerFault.exe (PID: 6328)
- WerFault.exe (PID: 4876)
- WerFault.exe (PID: 2012)
- WerFault.exe (PID: 3536)
- WerFault.exe (PID: 7948)
- WerFault.exe (PID: 7968)
- WerFault.exe (PID: 7648)
- BackgroundTransferHost.exe (PID: 9120)
- WerFault.exe (PID: 8520)
- WerFault.exe (PID: 8520)
- WerFault.exe (PID: 8232)
Reads Environment values
- rootkit.exe (PID: 4912)
- SearchApp.exe (PID: 7036)
Disables trace logs
- rootkit.exe (PID: 4912)
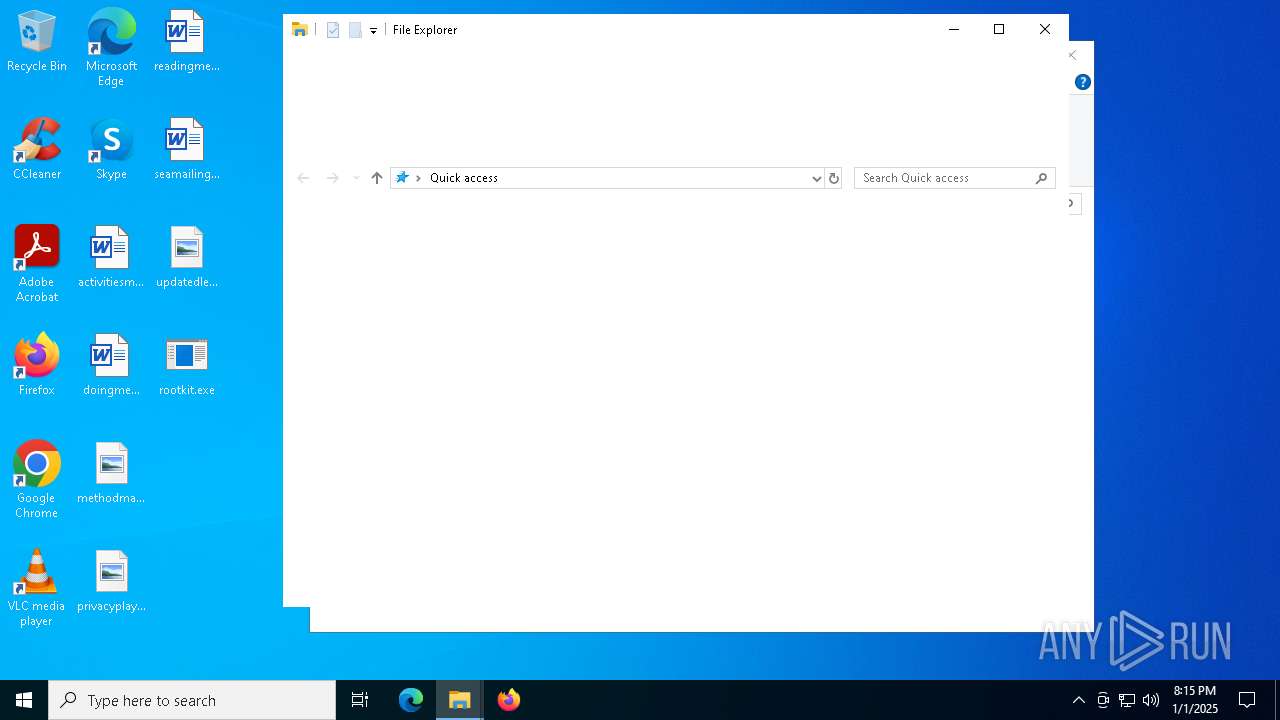
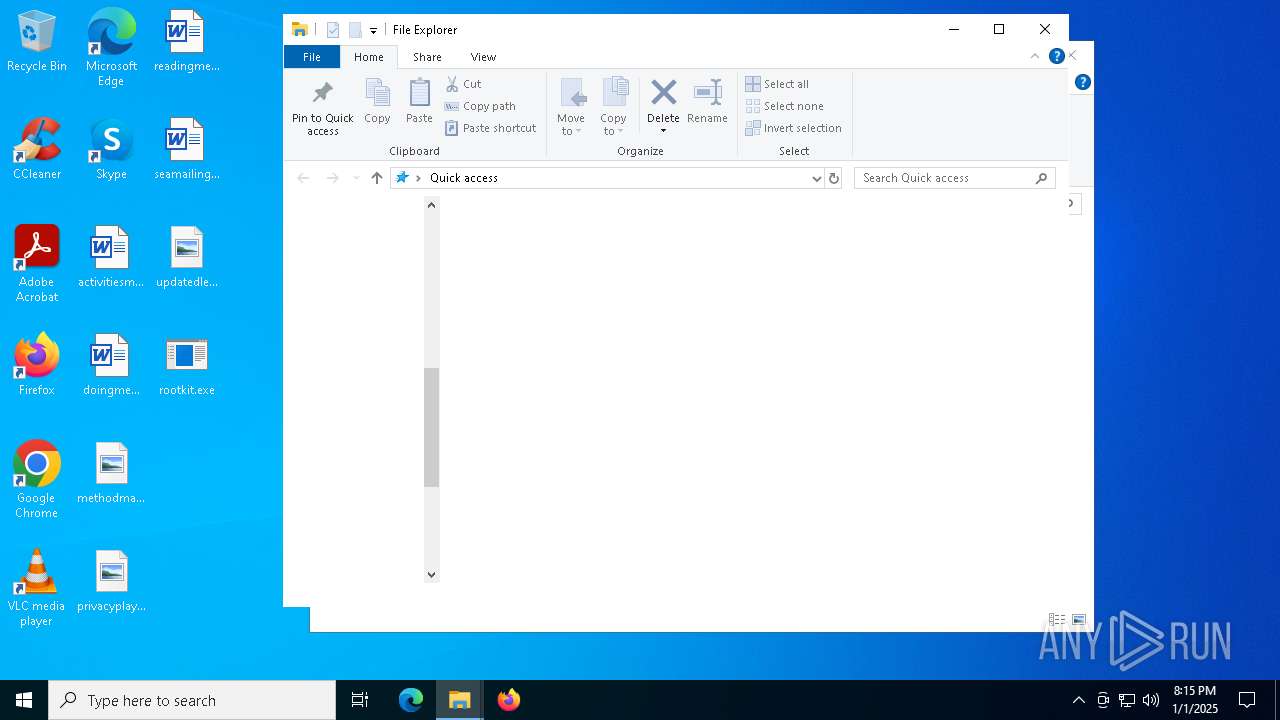
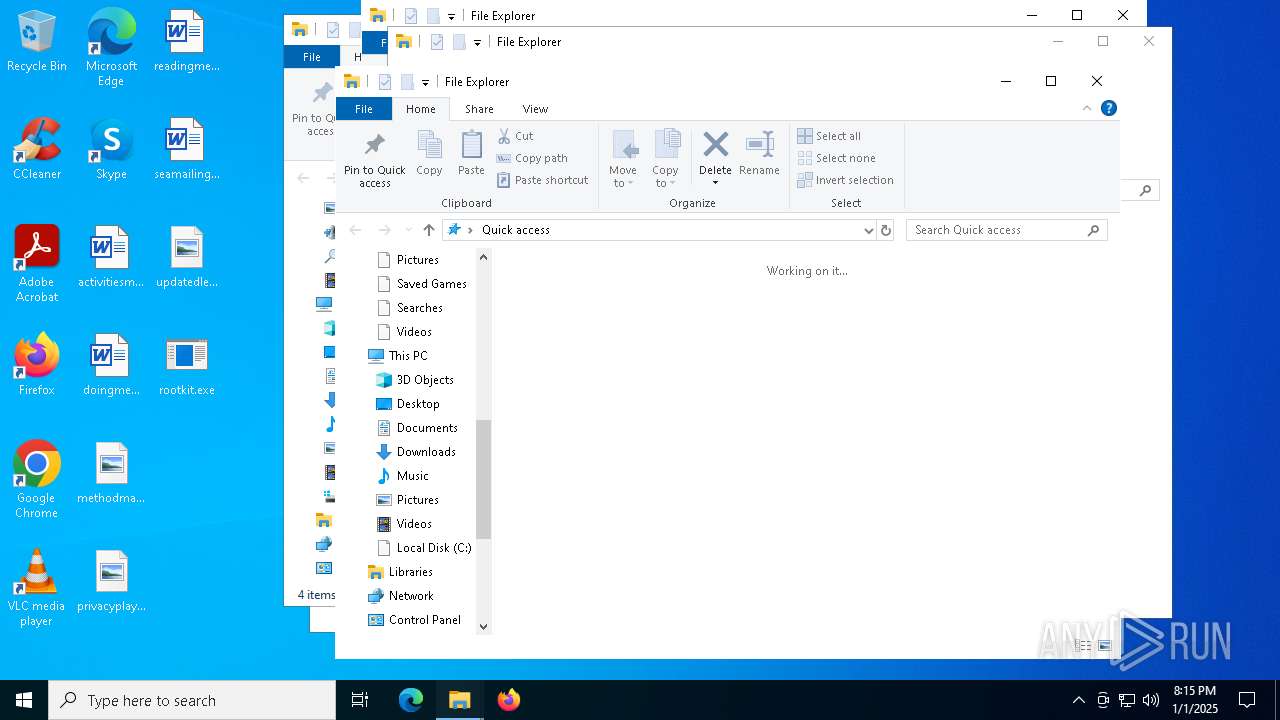
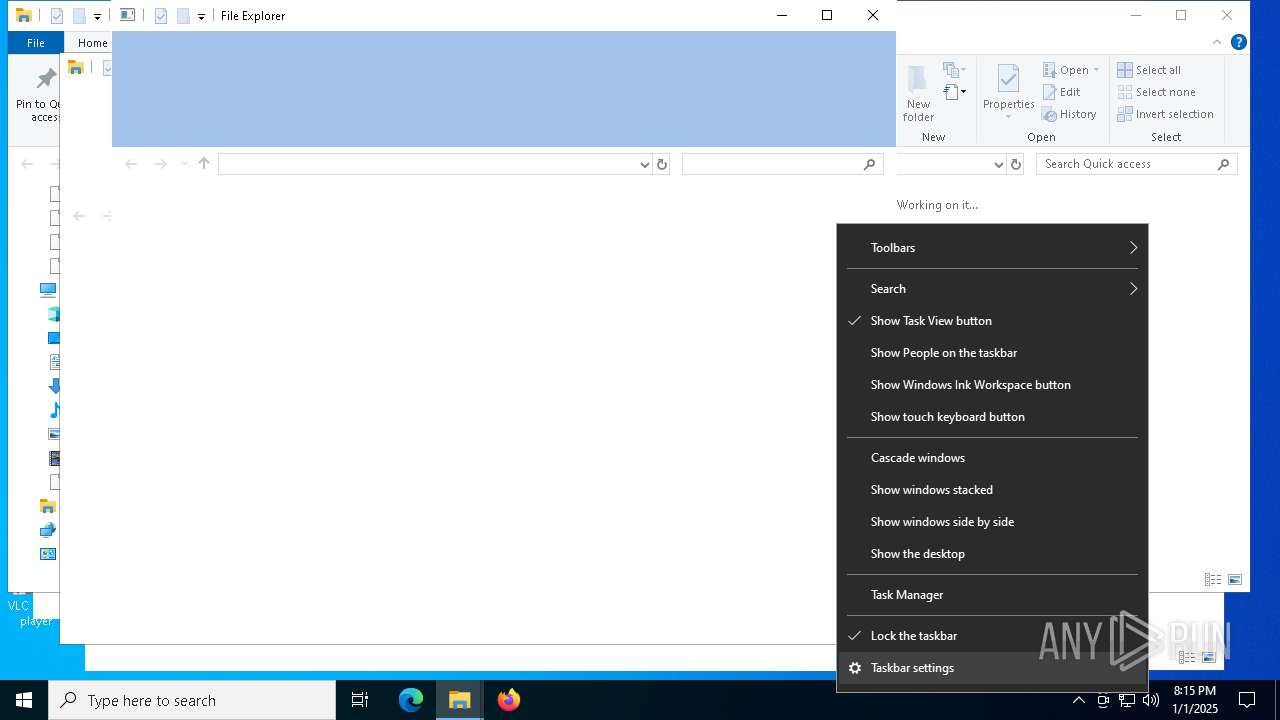
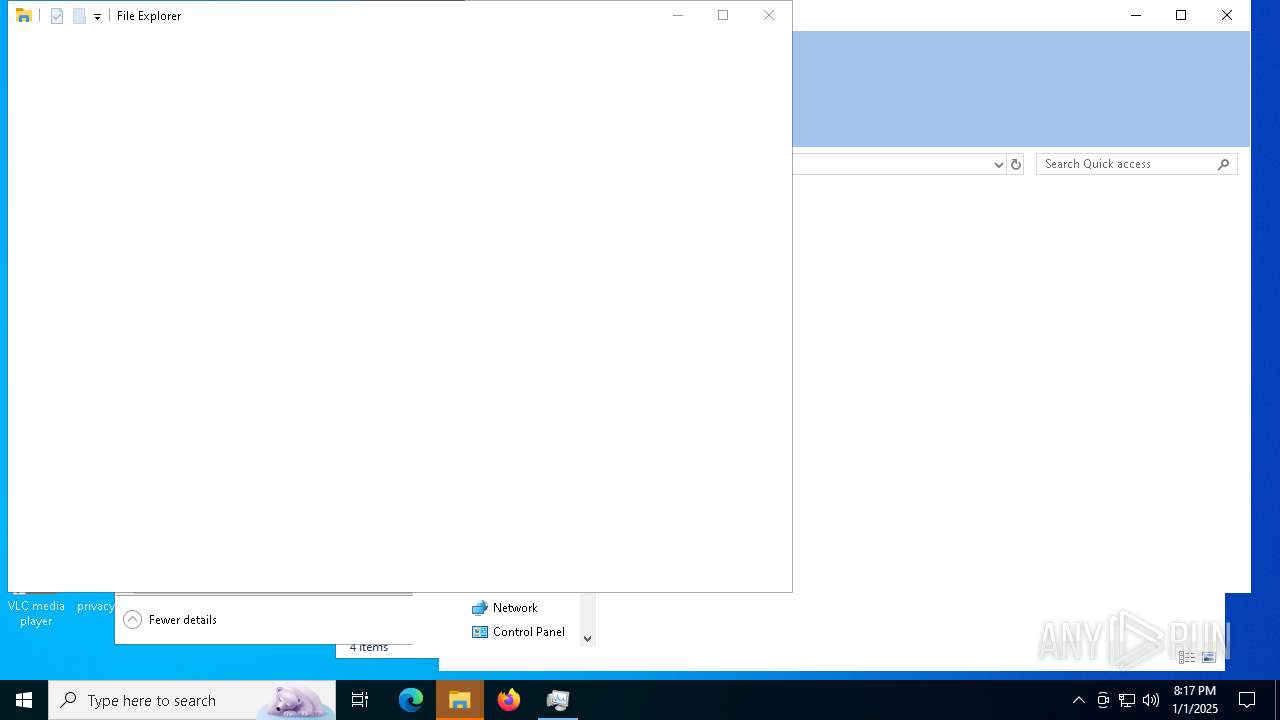
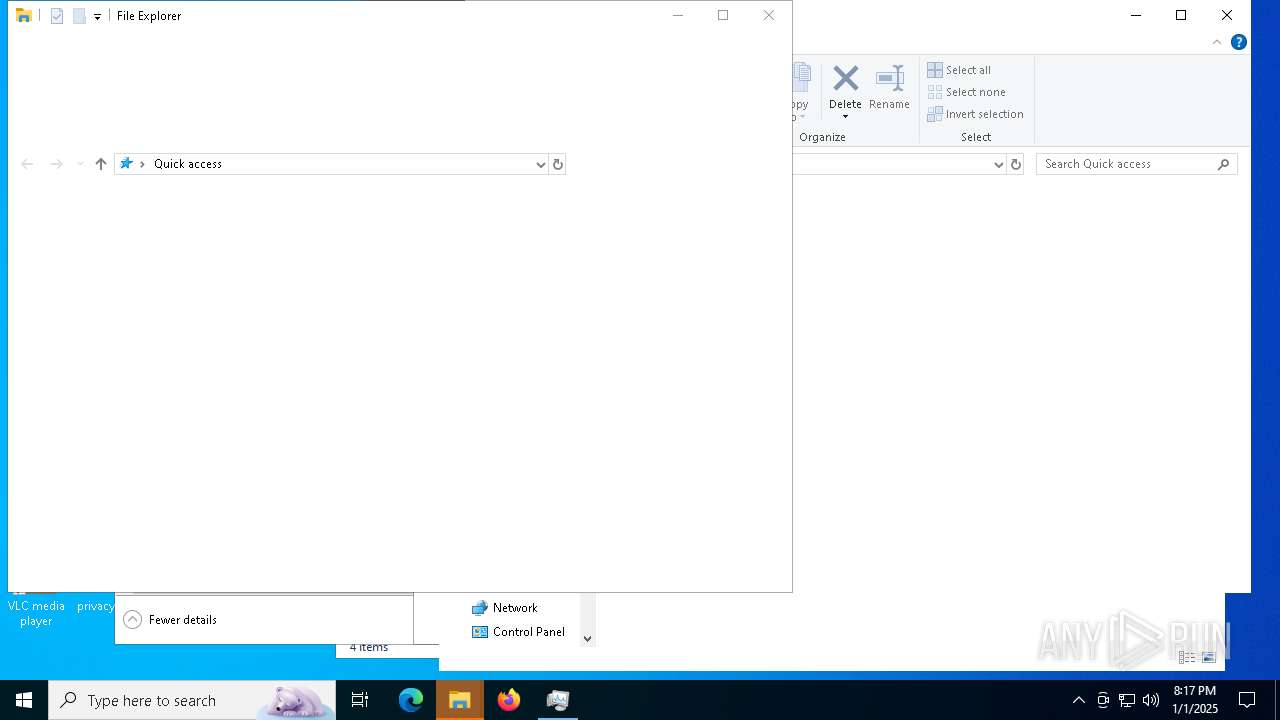
Creates files or folders in the user directory
- explorer.exe (PID: 7912)
- WerFault.exe (PID: 6640)
- explorer.exe (PID: 7984)
- WerFault.exe (PID: 7056)
- WerFault.exe (PID: 3536)
- WerFault.exe (PID: 8180)
- WerFault.exe (PID: 7100)
- WerFault.exe (PID: 8092)
- WerFault.exe (PID: 6968)
- WerFault.exe (PID: 7740)
- WerFault.exe (PID: 7432)
- WerFault.exe (PID: 5244)
- WerFault.exe (PID: 7780)
- WerFault.exe (PID: 6652)
- WerFault.exe (PID: 6300)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 5780)
- WerFault.exe (PID: 5000)
- WerFault.exe (PID: 7748)
- WerFault.exe (PID: 3364)
- WerFault.exe (PID: 2828)
- WerFault.exe (PID: 5560)
- WerFault.exe (PID: 6428)
- WerFault.exe (PID: 8544)
- WerFault.exe (PID: 8812)
- explorer.exe (PID: 8468)
- explorer.exe (PID: 8640)
- explorer.exe (PID: 1612)
- explorer.exe (PID: 7876)
- explorer.exe (PID: 6664)
- explorer.exe (PID: 5336)
- explorer.exe (PID: 4504)
- explorer.exe (PID: 6784)
- explorer.exe (PID: 3884)
- explorer.exe (PID: 8520)
- explorer.exe (PID: 3092)
- explorer.exe (PID: 7664)
- explorer.exe (PID: 8548)
- explorer.exe (PID: 6500)
- explorer.exe (PID: 2120)
- explorer.exe (PID: 7948)
- explorer.exe (PID: 9116)
- WerFault.exe (PID: 8460)
- WerFault.exe (PID: 8416)
- explorer.exe (PID: 6152)
- WerFault.exe (PID: 6716)
- WerFault.exe (PID: 7068)
- WerFault.exe (PID: 204)
- WerFault.exe (PID: 8256)
- WerFault.exe (PID: 3532)
- WerFault.exe (PID: 8464)
- WerFault.exe (PID: 8012)
- explorer.exe (PID: 6944)
- WerFault.exe (PID: 5888)
Reads the software policy settings
- rootkit.exe (PID: 4912)
- WerFault.exe (PID: 6640)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 3536)
- WerFault.exe (PID: 7056)
- WerFault.exe (PID: 8180)
- WerFault.exe (PID: 7100)
- WerFault.exe (PID: 8092)
- WerFault.exe (PID: 3364)
- WerFault.exe (PID: 6968)
- WerFault.exe (PID: 7740)
- WerFault.exe (PID: 7432)
- WerFault.exe (PID: 5244)
- WerFault.exe (PID: 7780)
- WerFault.exe (PID: 6652)
- WerFault.exe (PID: 6300)
- WerFault.exe (PID: 7748)
- WerFault.exe (PID: 5780)
- WerFault.exe (PID: 5000)
- WerFault.exe (PID: 7068)
- WerFault.exe (PID: 2828)
- WerFault.exe (PID: 6340)
- WerFault.exe (PID: 8736)
- WerFault.exe (PID: 8812)
- WerFault.exe (PID: 7244)
- WerFault.exe (PID: 7516)
- WerFault.exe (PID: 2572)
- WerFault.exe (PID: 8520)
- WerFault.exe (PID: 8460)
- WerFault.exe (PID: 6716)
- WerFault.exe (PID: 5632)
- WerFault.exe (PID: 3832)
- WerFault.exe (PID: 6884)
- WerFault.exe (PID: 3128)
- WerFault.exe (PID: 6548)
- WerFault.exe (PID: 8256)
- WerFault.exe (PID: 204)
- WerFault.exe (PID: 7424)
- WerFault.exe (PID: 3532)
- SearchApp.exe (PID: 7036)
- WerFault.exe (PID: 1016)
- WerFault.exe (PID: 8464)
- WerFault.exe (PID: 5704)
- WerFault.exe (PID: 8012)
- WerFault.exe (PID: 5740)
- WerFault.exe (PID: 5548)
- WerFault.exe (PID: 8612)
- WerFault.exe (PID: 5888)
- WerFault.exe (PID: 7356)
- WerFault.exe (PID: 4672)
- WerFault.exe (PID: 7836)
- WerFault.exe (PID: 5072)
- WerFault.exe (PID: 7948)
- WerFault.exe (PID: 6328)
- WerFault.exe (PID: 8432)
- WerFault.exe (PID: 7648)
- WerFault.exe (PID: 7212)
- WerFault.exe (PID: 8520)
- BackgroundTransferHost.exe (PID: 9120)
- WerFault.exe (PID: 8520)
Create files in a temporary directory
- rootkit.exe (PID: 4912)
- WerFault.exe (PID: 3364)
The process uses the downloaded file
- rootkit.exe (PID: 4912)
Reads the machine GUID from the registry
- rootkit.exe (PID: 4912)
- SearchApp.exe (PID: 7036)
- SearchApp.exe (PID: 6544)
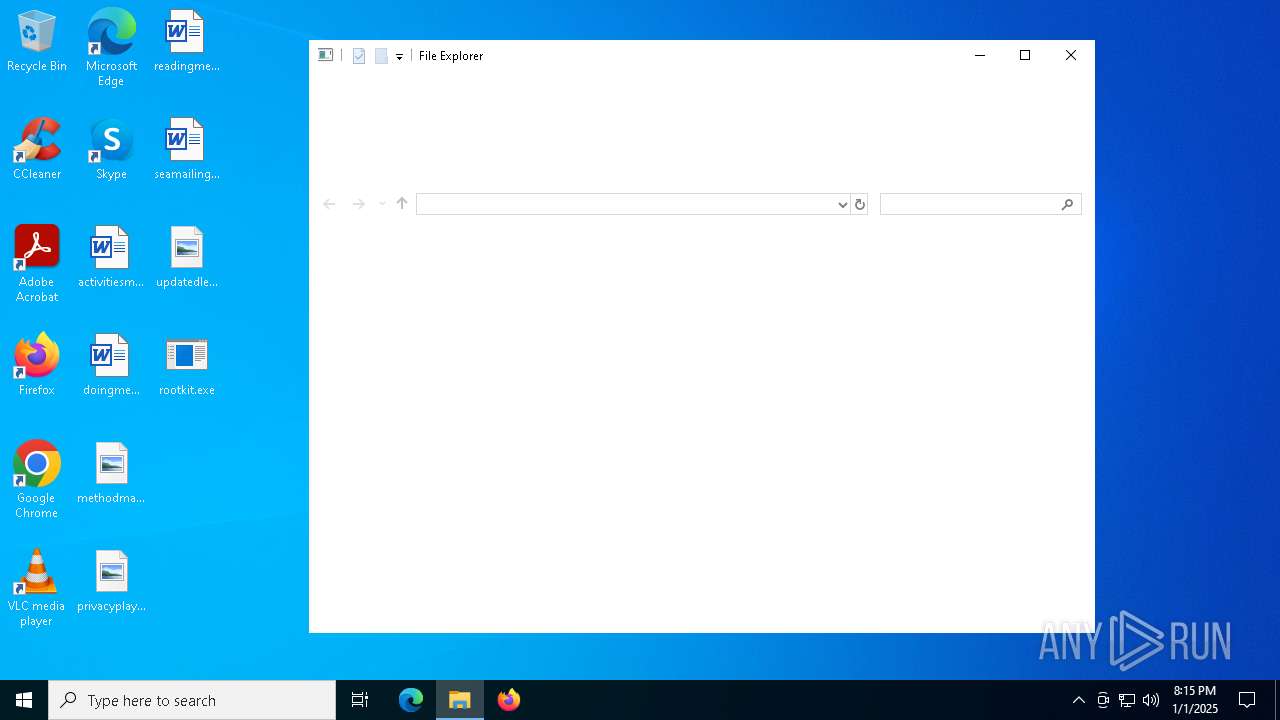
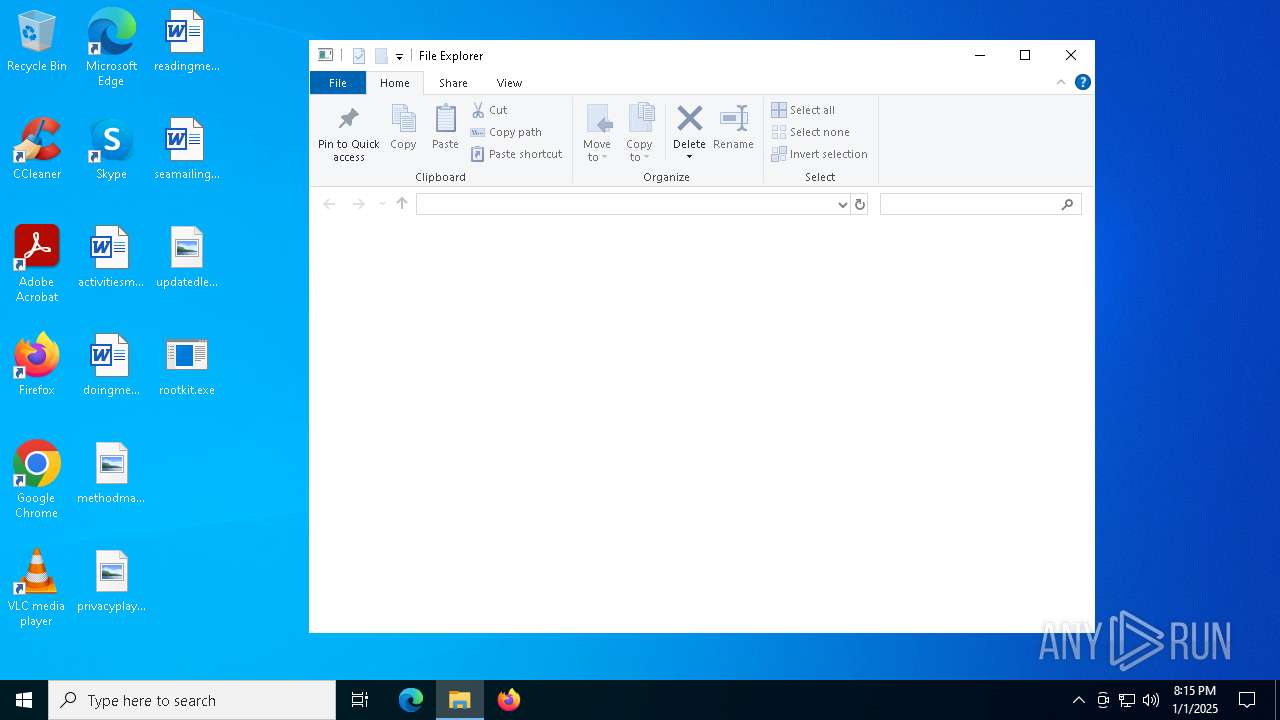
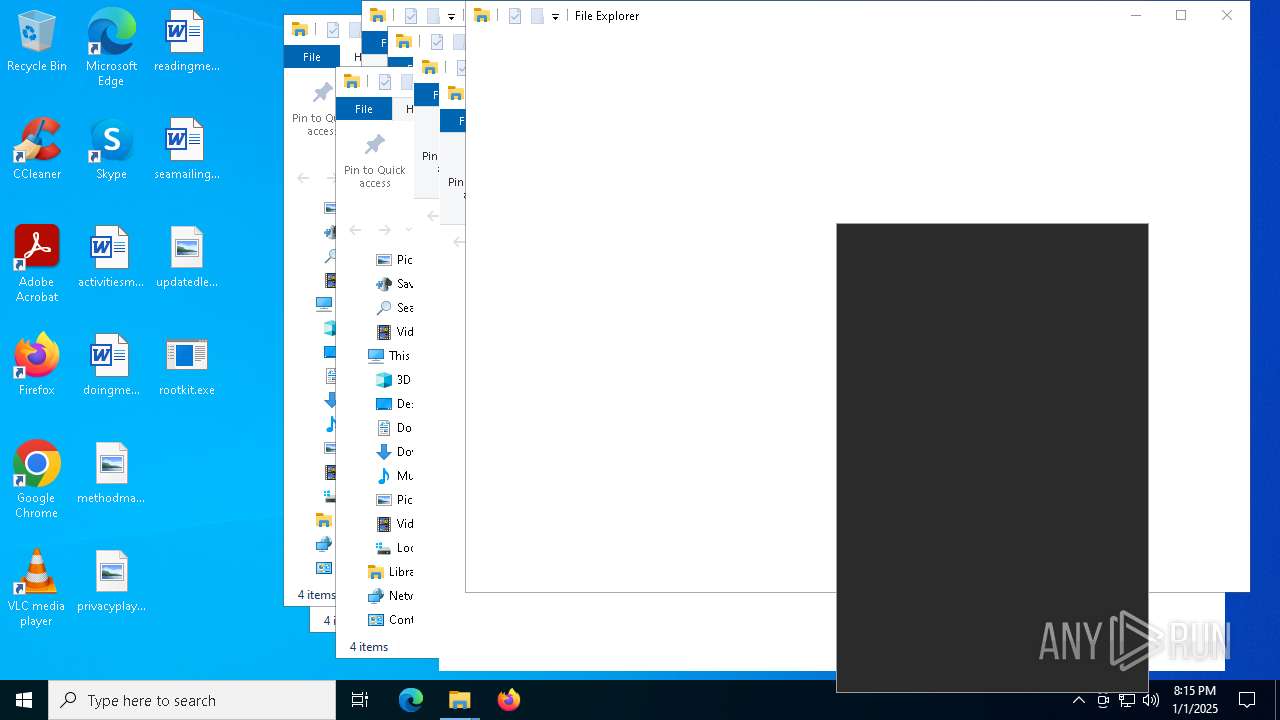
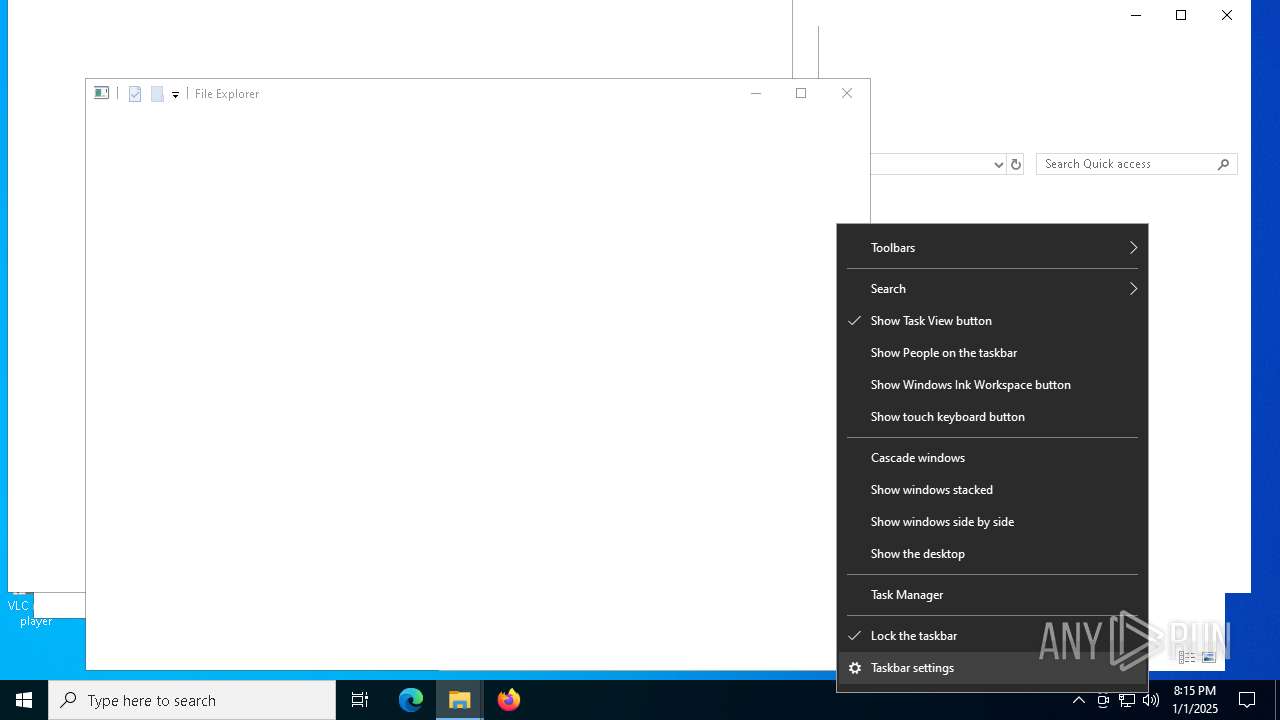
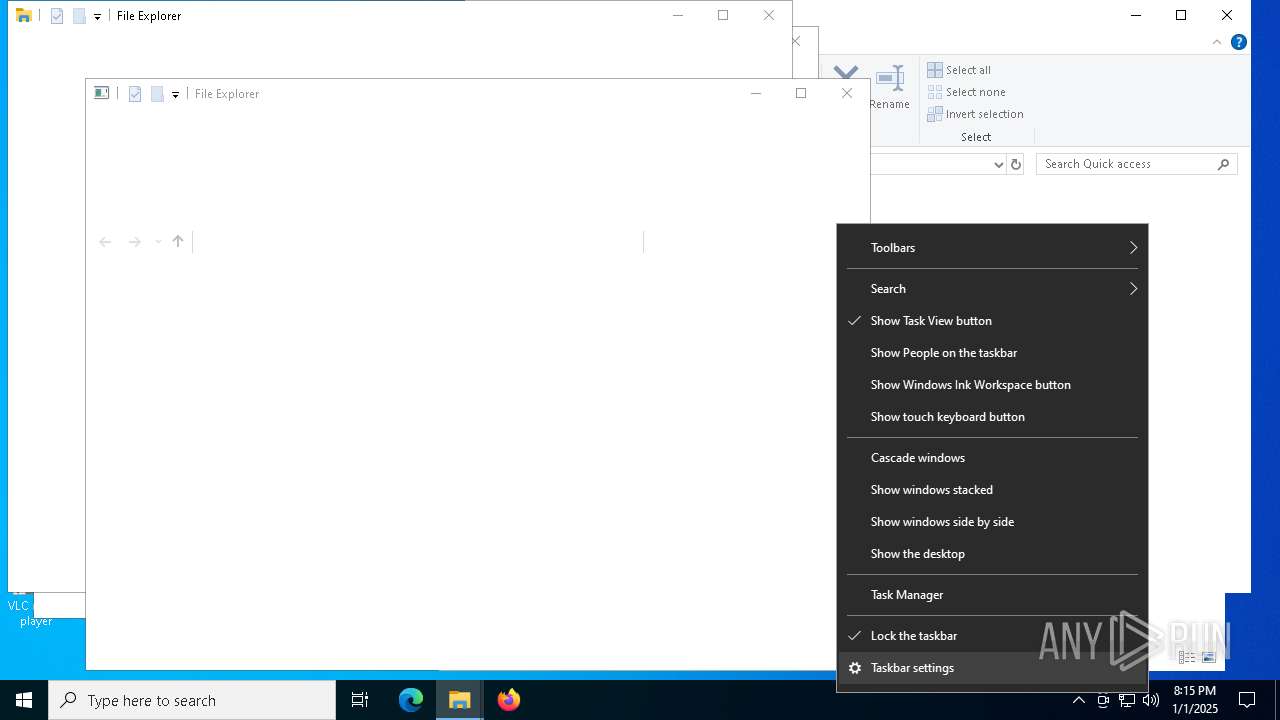
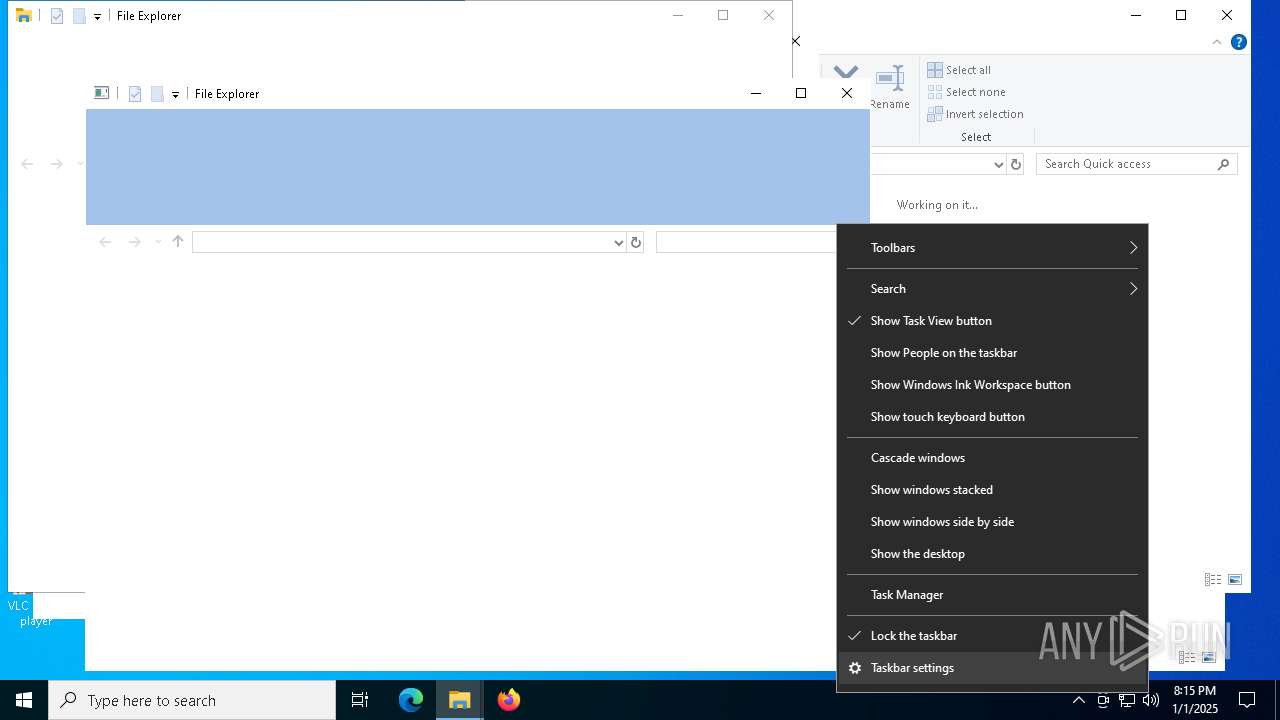
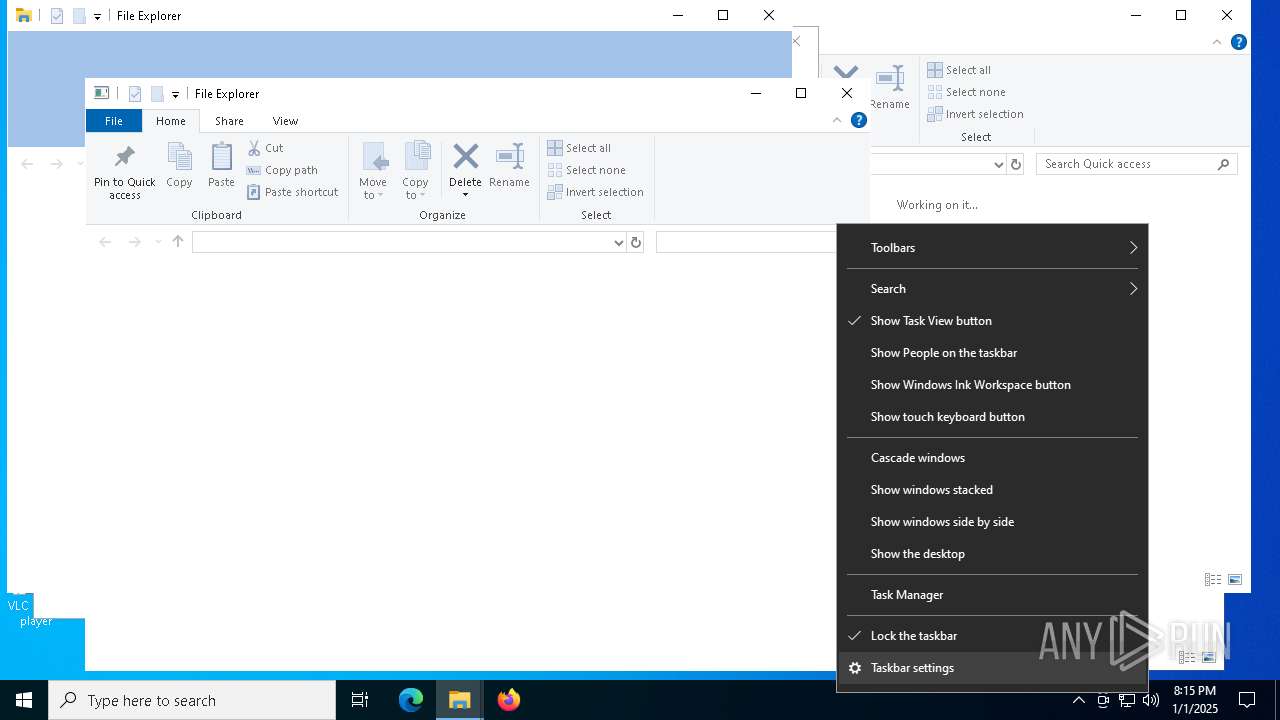
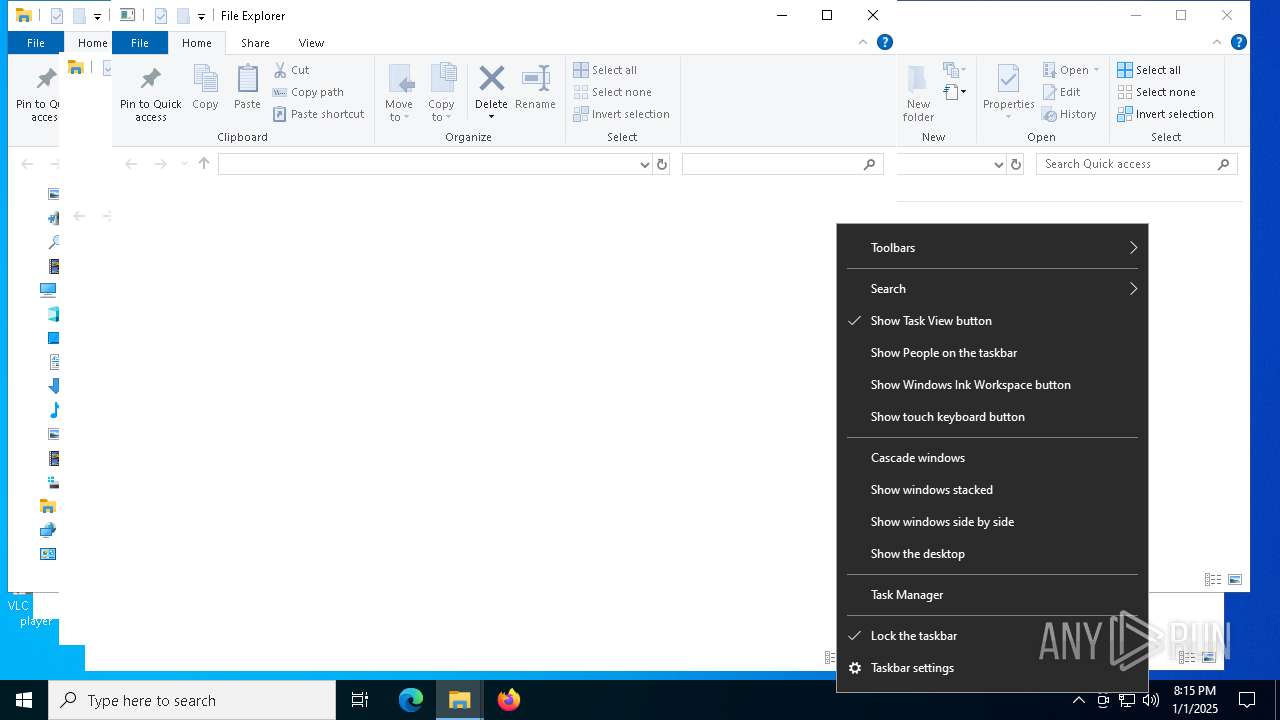
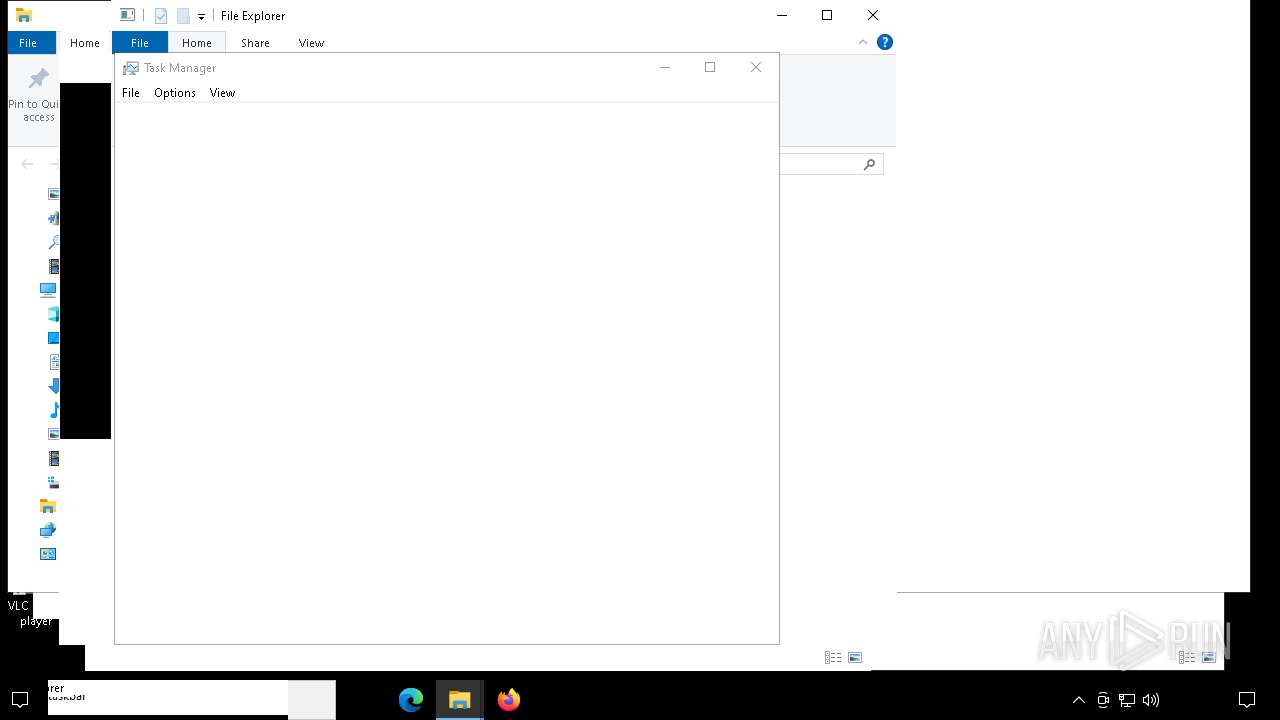
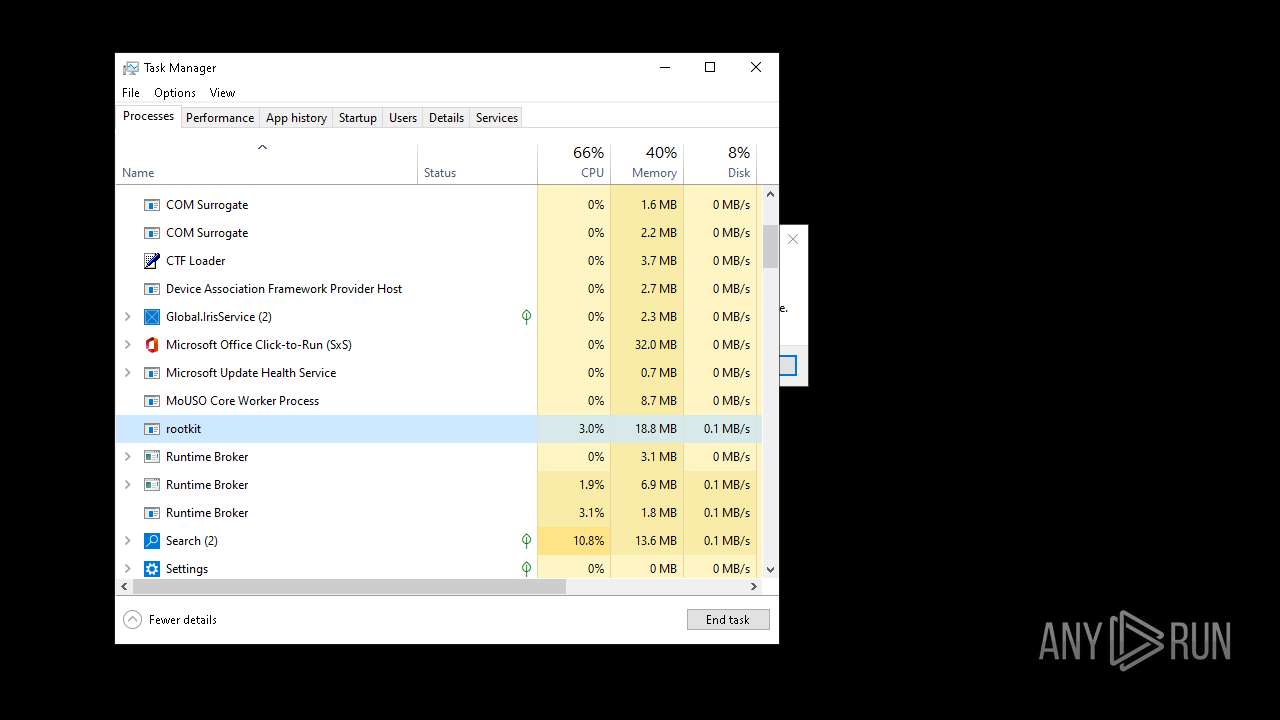
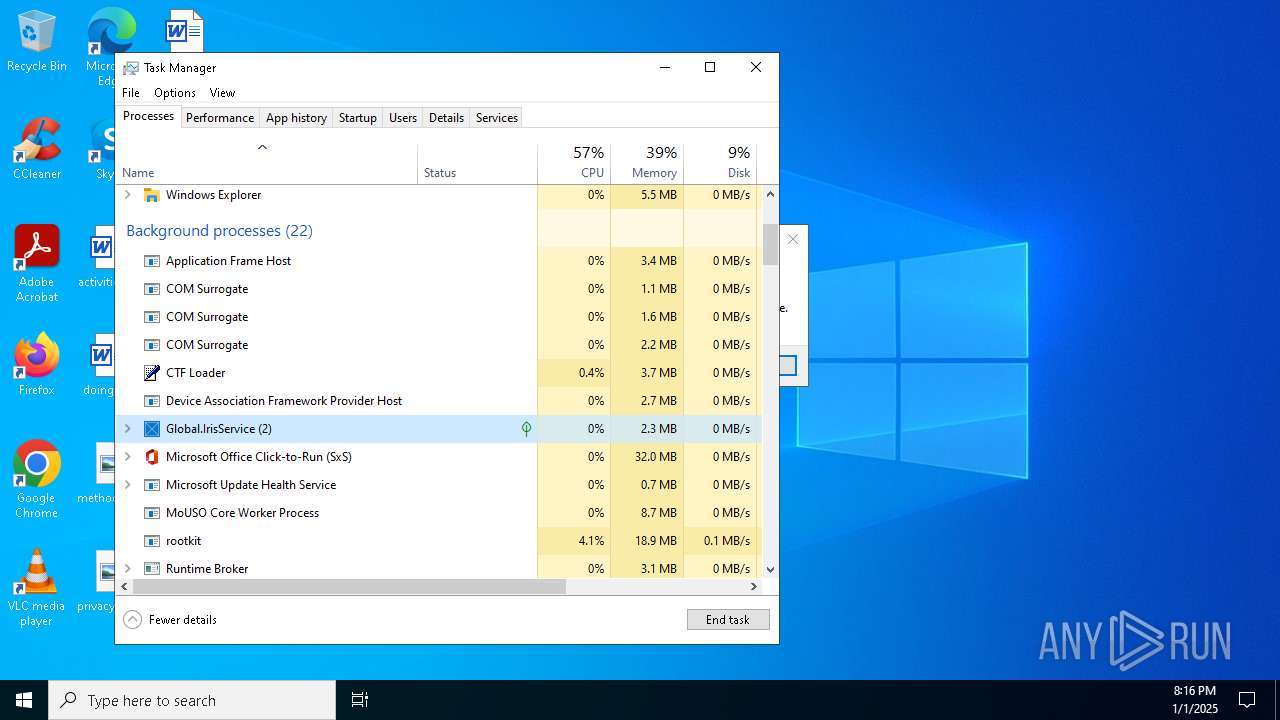
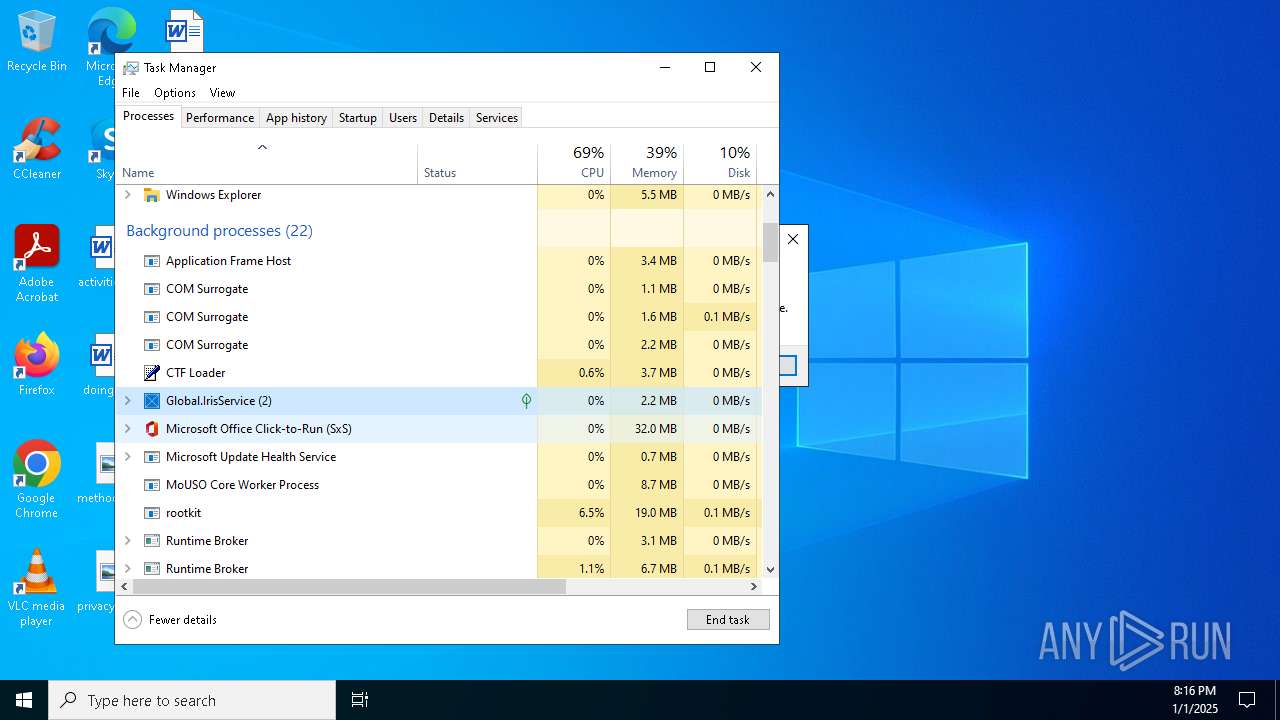
Manual execution by a user
- wermgr.exe (PID: 3620)
- wermgr.exe (PID: 7216)
- wermgr.exe (PID: 7308)
- Taskmgr.exe (PID: 7268)
- Taskmgr.exe (PID: 7752)
- WerFault.exe (PID: 8988)
- WerFault.exe (PID: 7424)
- wermgr.exe (PID: 6440)
- wermgr.exe (PID: 8484)
- wermgr.exe (PID: 2676)
- WerFault.exe (PID: 6564)
- WerFault.exe (PID: 5740)
- WerFault.exe (PID: 5524)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7752)
- explorer.exe (PID: 4520)
- explorer.exe (PID: 8400)
- explorer.exe (PID: 1496)
- BackgroundTransferHost.exe (PID: 9120)
Sends debugging messages
- StartMenuExperienceHost.exe (PID: 7500)
- StartMenuExperienceHost.exe (PID: 8732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2069:01:04 18:07:46+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 5120 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x32ba |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | rootkit |
| FileVersion: | 1.0.0.0 |
| InternalName: | rootkit.exe |
| LegalCopyright: | Copyright © 2025 |
| LegalTrademarks: | - |
| OriginalFileName: | rootkit.exe |
| ProductName: | rootkit |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
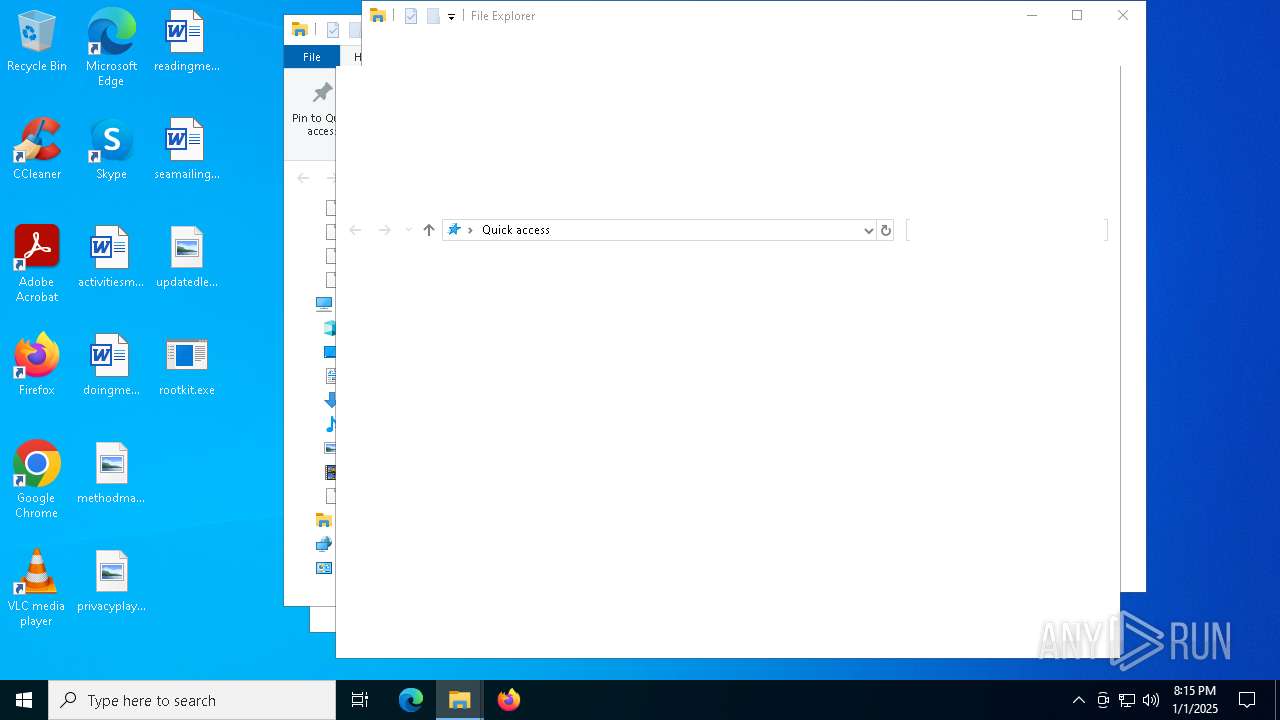
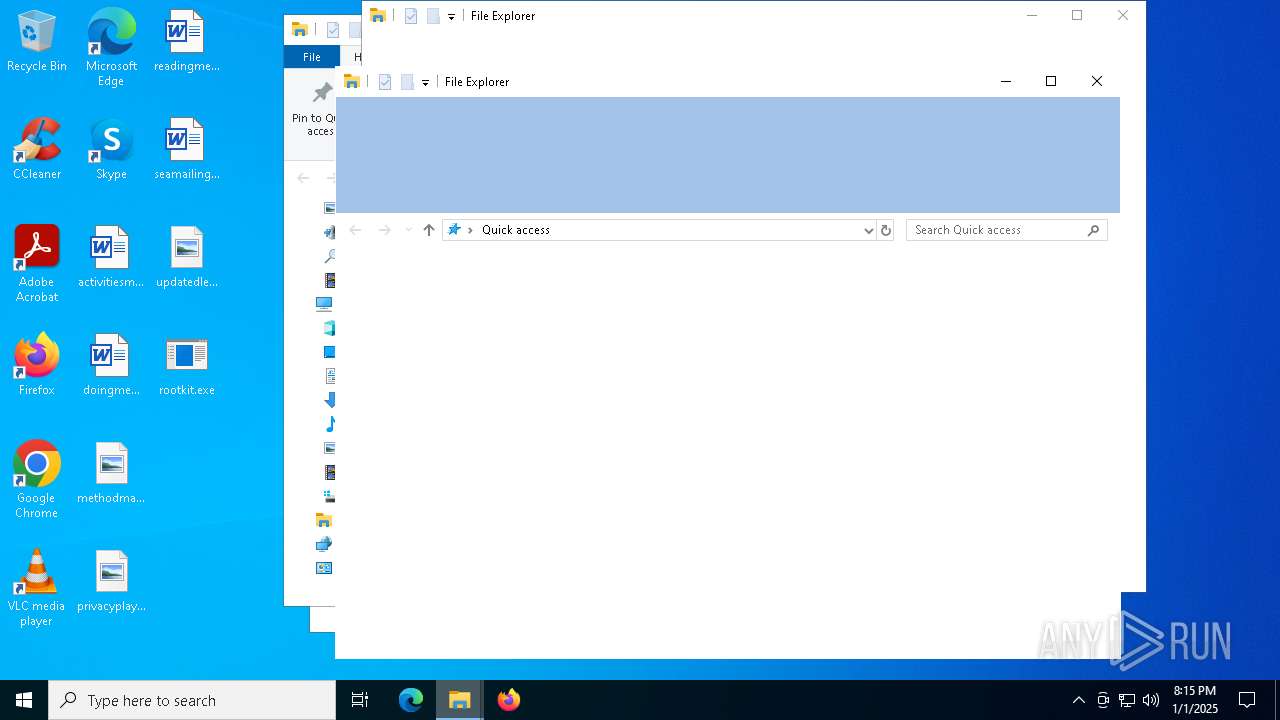
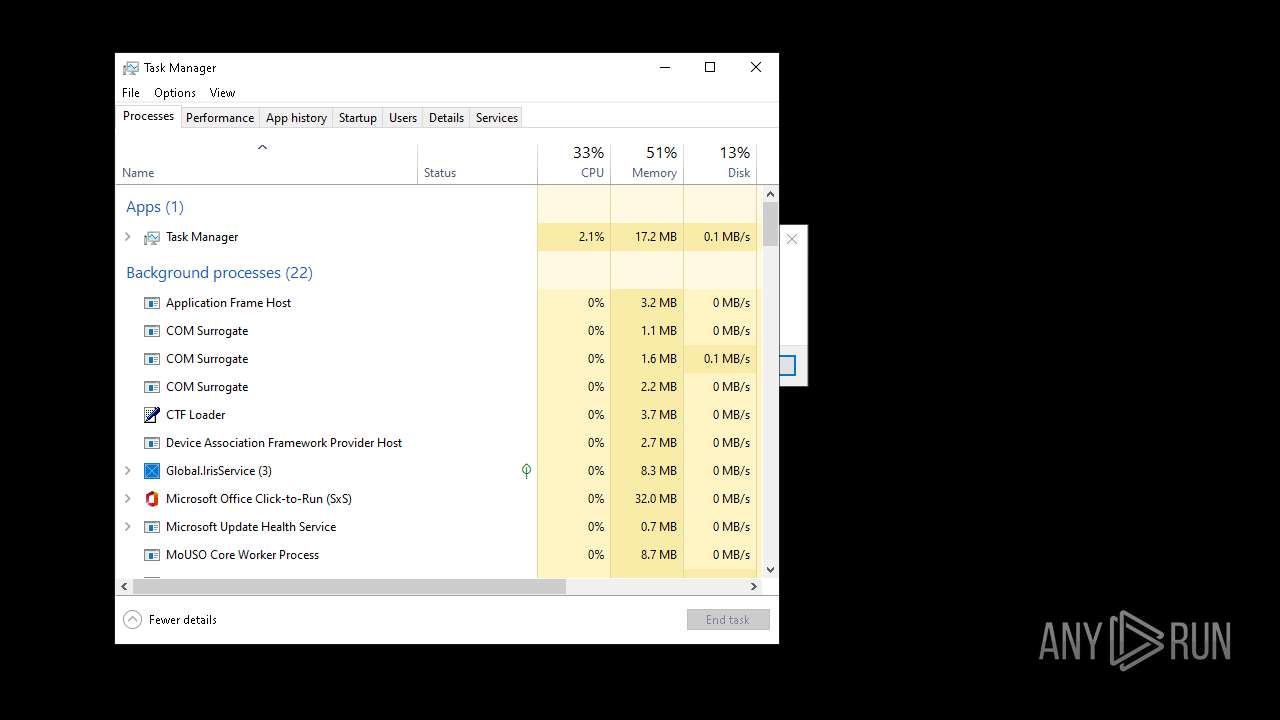
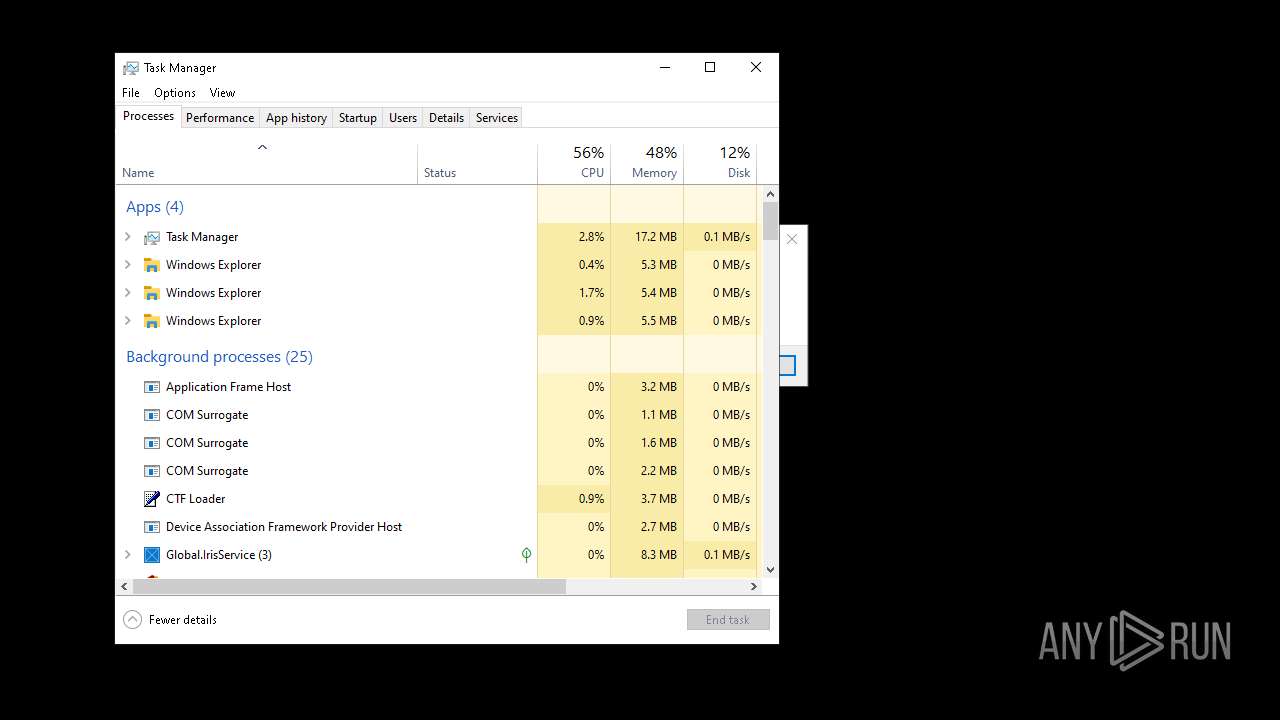
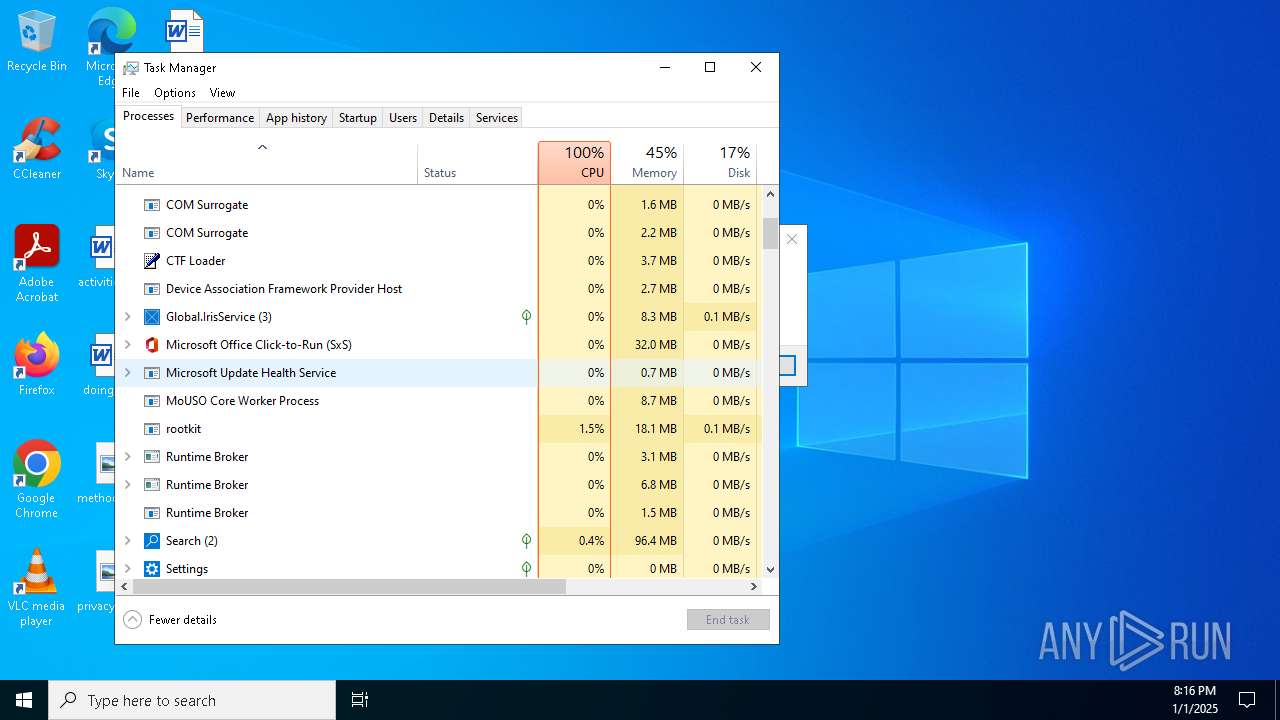
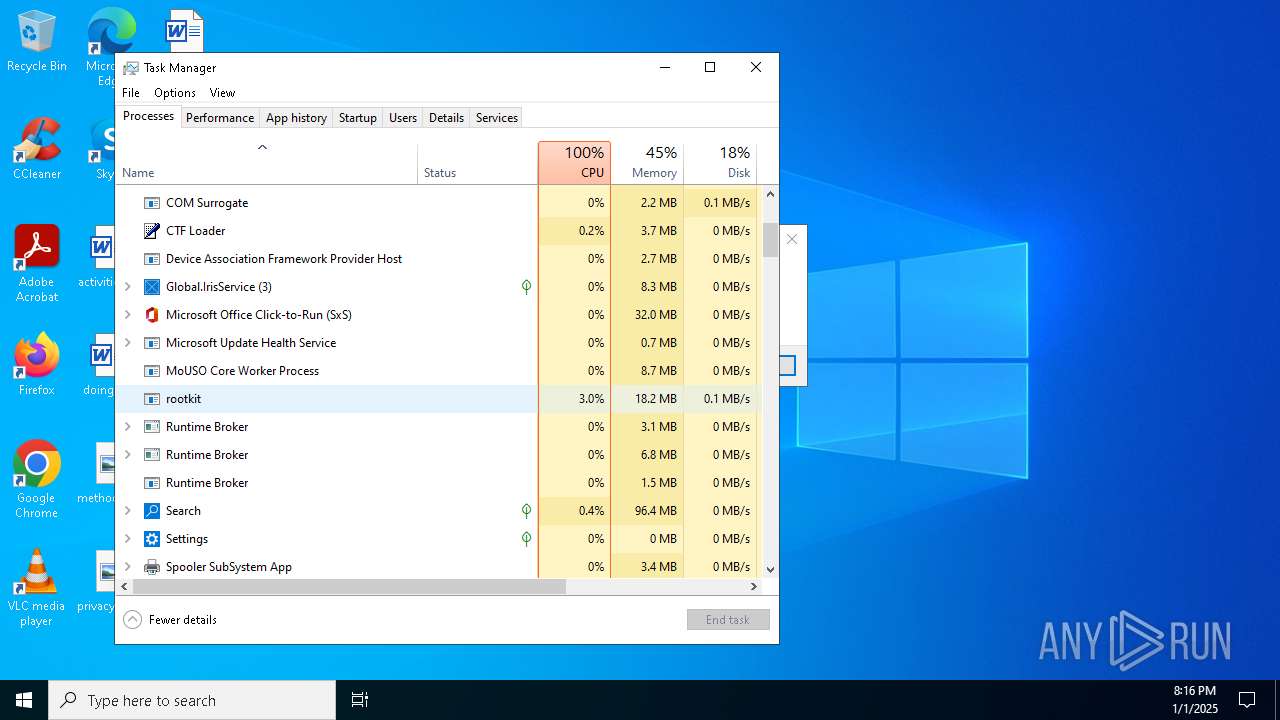
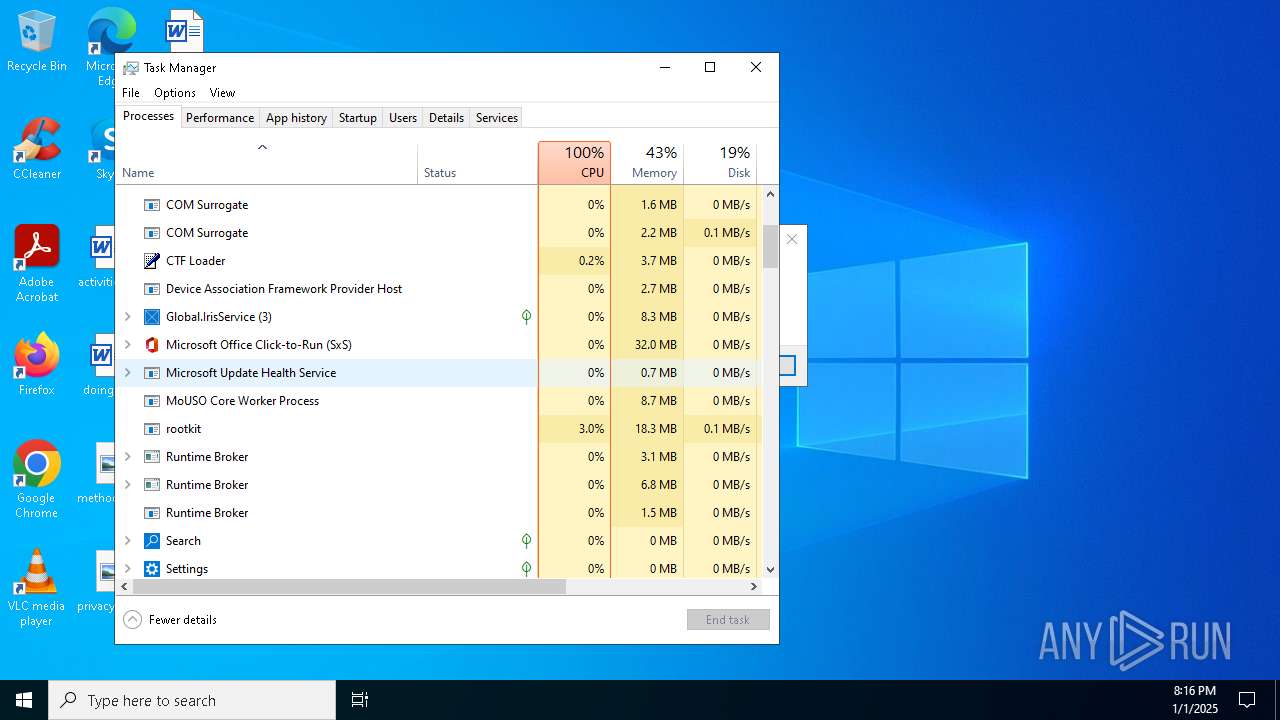
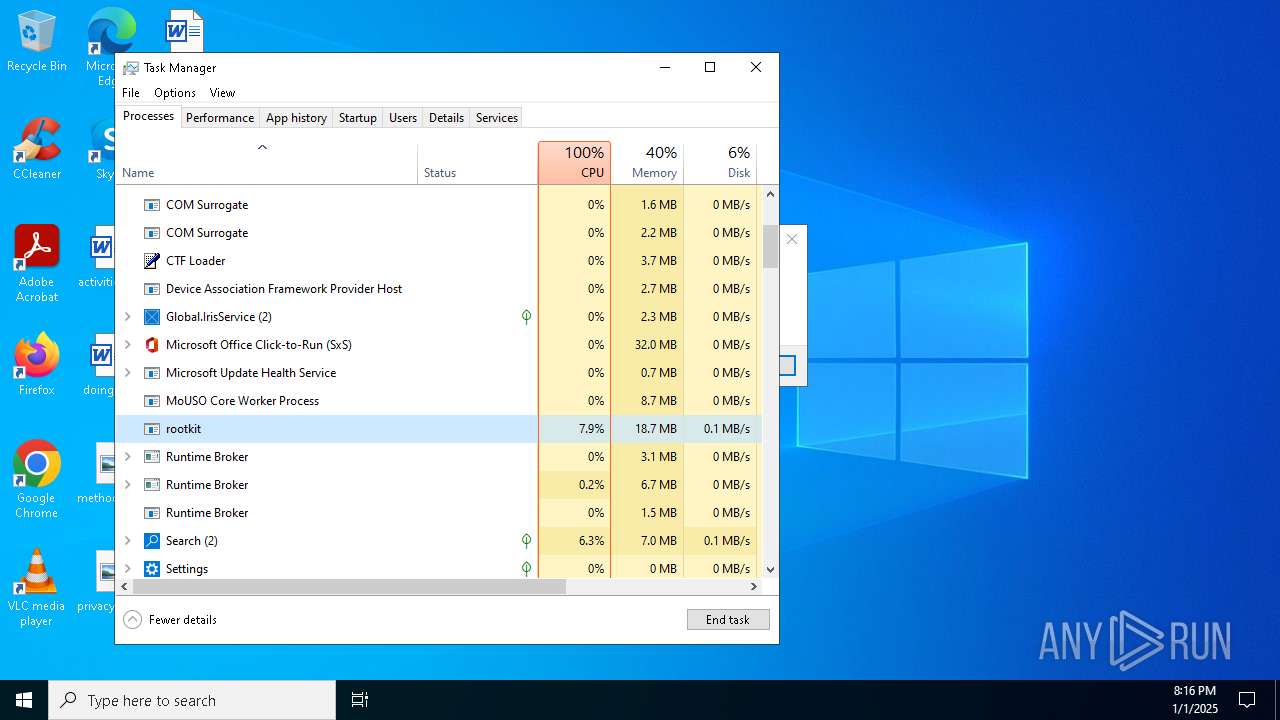
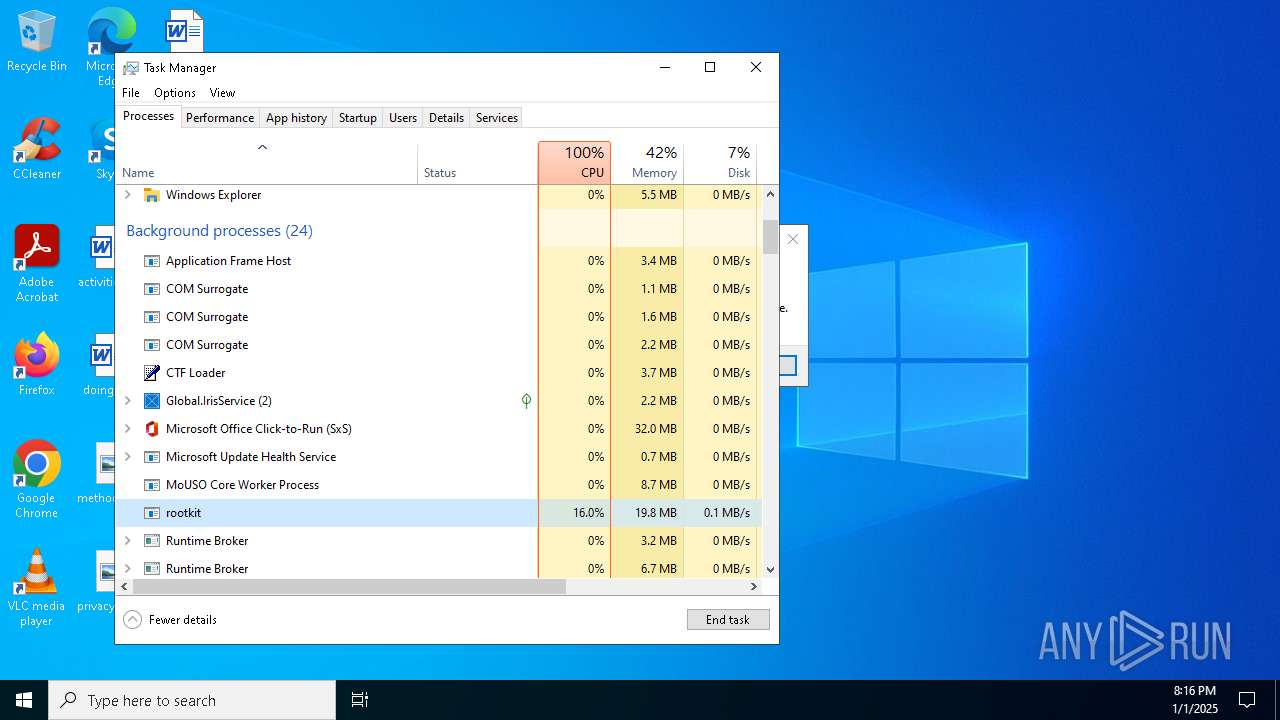
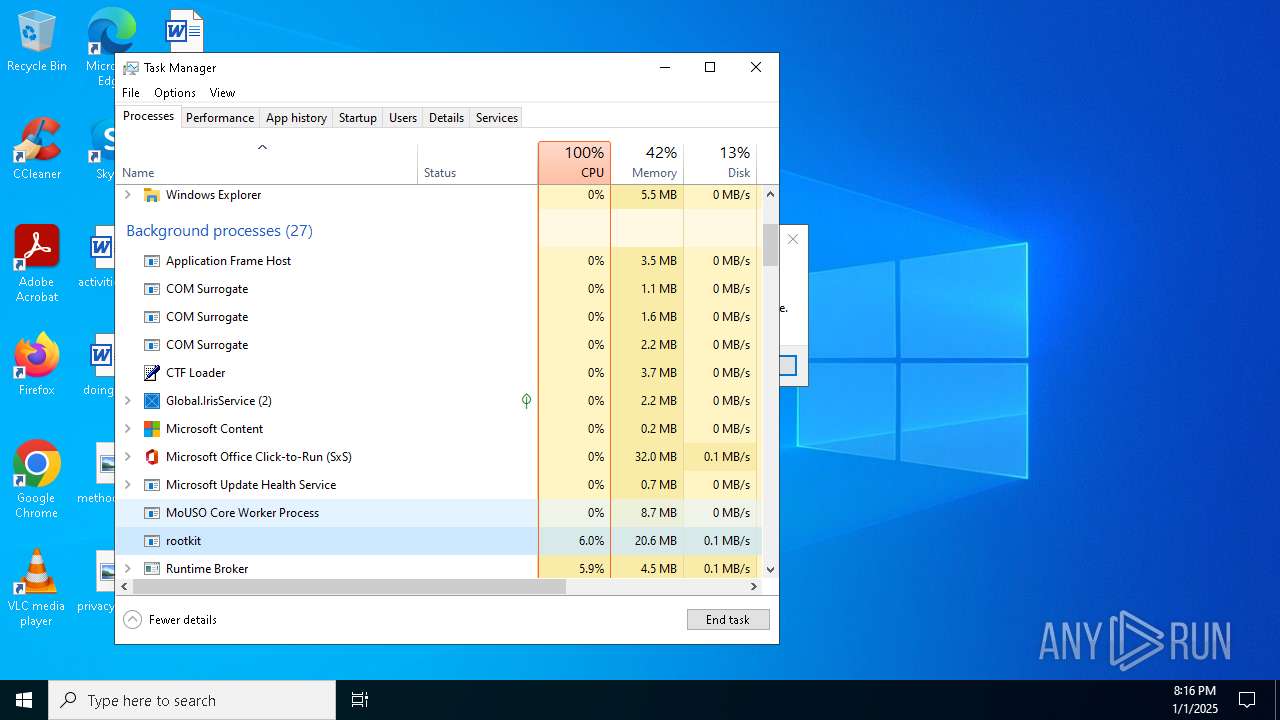
Total processes
1 263
Monitored processes
958
Malicious processes
2
Suspicious processes
1
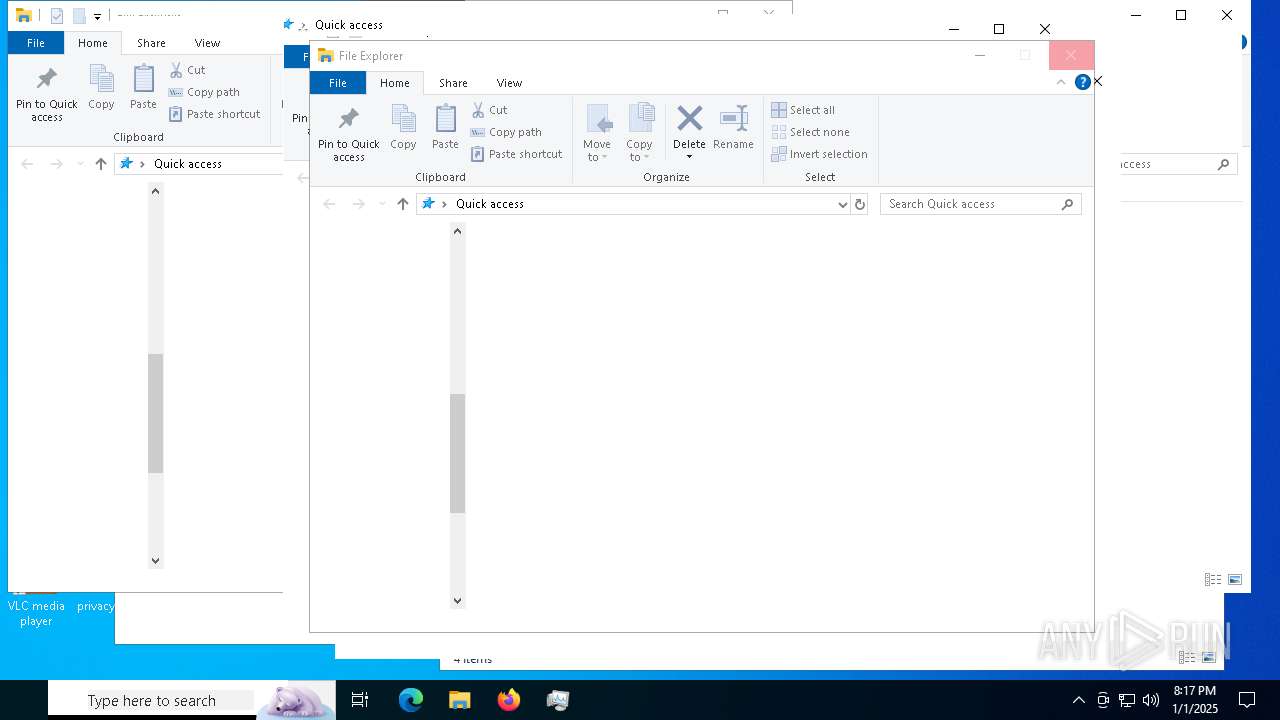
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 68 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 132 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 188 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | C:\WINDOWS\system32\WerFault.exe -u -p 1412 -s 700 | C:\Windows\System32\WerFault.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 204 | C:\WINDOWS\system32\WerFault.exe -u -p 7312 -s 852 | C:\Windows\System32\WerFault.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 396 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | rootkit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
927 406
Read events
926 154
Write events
1 224
Delete events
28
Modification events
| (PID) Process: | (6168) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6168) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D04020000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5432) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5432) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D77010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (4912) rootkit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\rootkit_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4912) rootkit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\rootkit_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4912) rootkit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\rootkit_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4912) rootkit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\rootkit_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4912) rootkit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\rootkit_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4912) rootkit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\rootkit_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
Executable files
4
Suspicious files
190
Text files
491
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5B34.tmp.WERInternalMetadata.xml | xml | |
MD5:7D248600B2D0A59F5797810C149896BA | SHA256:B019FE5B55E0D57090F2D5519E97311932C5277520874D711836E097EFD9B254 | |||
| 6640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER5BA2.tmp.xml | xml | |
MD5:BB6B59080FCF343F70D0A0FF50A66D05 | SHA256:BAE01A1DD6EF8C36864D6AA8FC6260B89B992A797C83BE3D6BDC8C1108BC1548 | |||
| 6640 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_explorer.exe_1ee8a08f31bd1668b9ac85d6a9823a28cc284ef_4a37867f_a466837d-e77c-447f-bf43-b7a7b8d131b2\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6640 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:E08F6ACFF5F09A669781A24A1C848DB3 | SHA256:5E883365E717627DDF2E672887A9929B031A48D8A470D95516D6983EC2495D68 | |||
| 4912 | rootkit.exe | C:\Users\admin\AppData\Local\Temp\tmp6693.tmp | html | |
MD5:0E6805ECCF9D4429E0469A0326B47585 | SHA256:8408FB76747026E07F0B65F9F3D7E24D252670C6E8DD37060B736462245A1D31 | |||
| 4912 | rootkit.exe | C:\Users\admin\AppData\Local\Temp\tmp5884.tmp | html | |
MD5:0E6805ECCF9D4429E0469A0326B47585 | SHA256:8408FB76747026E07F0B65F9F3D7E24D252670C6E8DD37060B736462245A1D31 | |||
| 4912 | rootkit.exe | C:\Users\admin\AppData\Local\Temp\tmp60B5.tmp | html | |
MD5:0E6805ECCF9D4429E0469A0326B47585 | SHA256:8408FB76747026E07F0B65F9F3D7E24D252670C6E8DD37060B736462245A1D31 | |||
| 4912 | rootkit.exe | C:\Users\admin\AppData\Local\Temp\tmp6394.tmp | html | |
MD5:0E6805ECCF9D4429E0469A0326B47585 | SHA256:8408FB76747026E07F0B65F9F3D7E24D252670C6E8DD37060B736462245A1D31 | |||
| 6640 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:F6F53CD09A41E968C363419B279D3112 | SHA256:6D2BB01CC7A9BADE2113B219CAC1BDA86B2733196B7E1BD0C807CE1E396B1892 | |||
| 7056 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6B52.tmp.xml | xml | |
MD5:D0EEC9CE1AE97C24FB6192A2CBE9CDD8 | SHA256:5576E82E8F7717CE4242E78D31A65DB3BD8ABA8FF14A57A3EE9743ED956BE1FB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
146
DNS requests
53
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3040 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7504 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7504 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6640 | WerFault.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6588 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
9120 | BackgroundTransferHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6644 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3040 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3040 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 92.123.104.49:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4912 | rootkit.exe | 172.67.139.105:443 | goo.su | CLOUDFLARENET | US | unknown |
1176 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| unknown |
www.bing.com |
| whitelisted |
goo.su |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Misc activity | ET INFO Observed URL Shortener Service Domain in DNS Lookup (goo .su) |
4912 | rootkit.exe | Misc activity | ET INFO Observed URL Shortener Service Domain (goo .su in TLS SNI) |