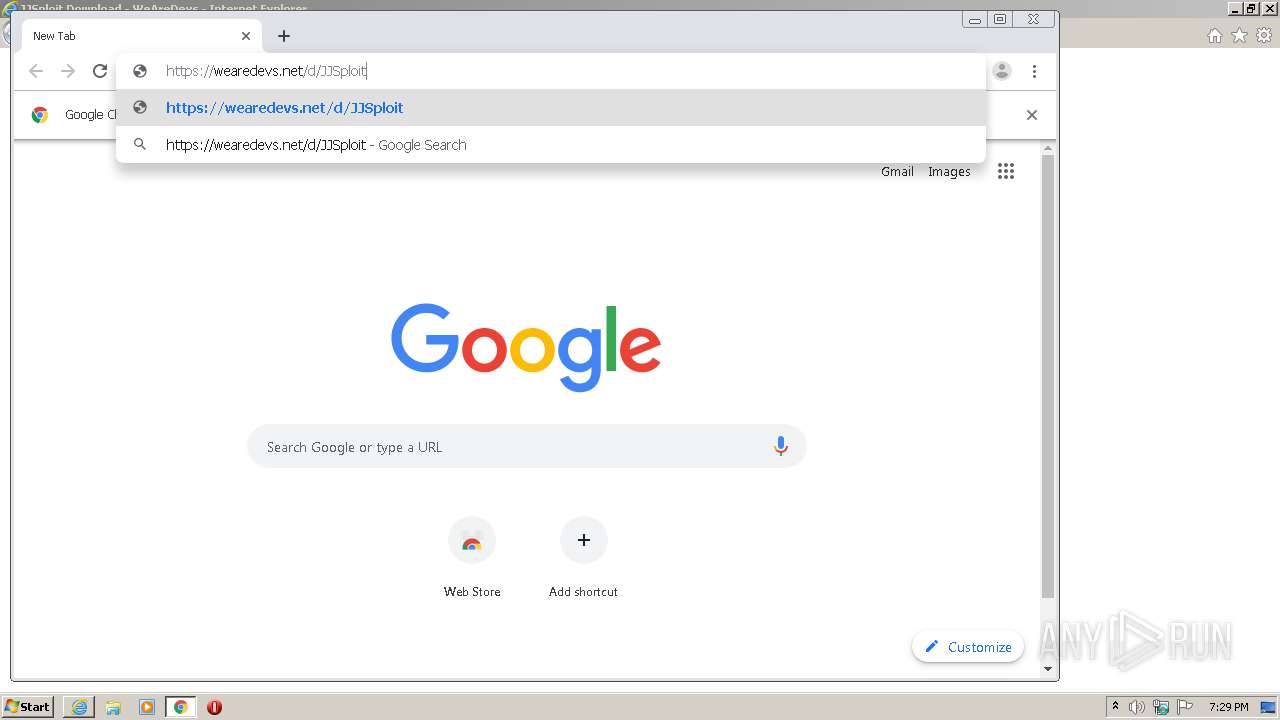
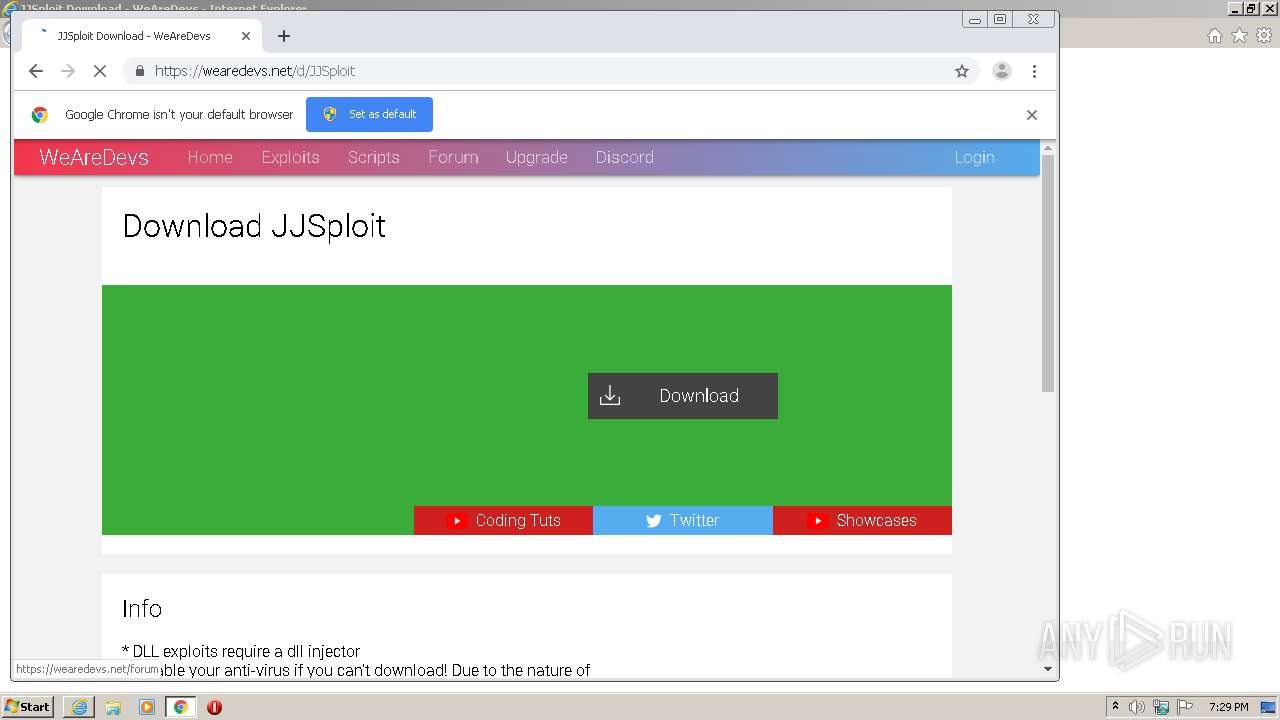
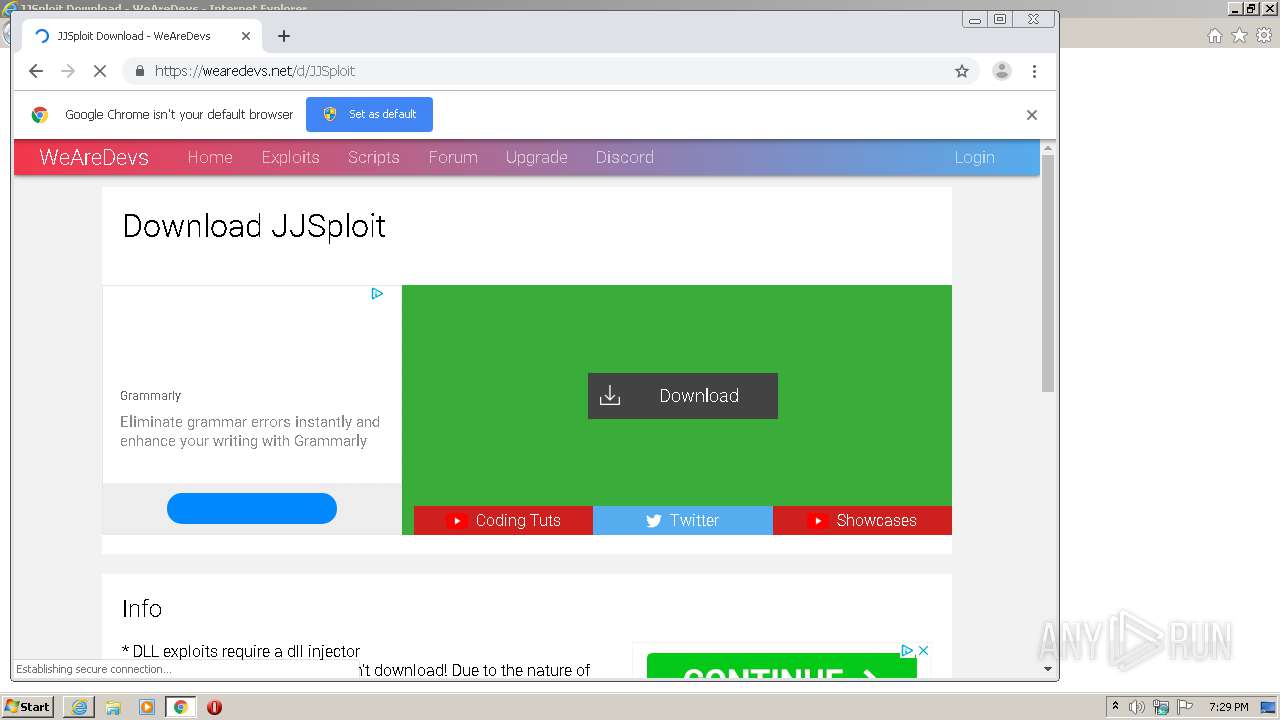
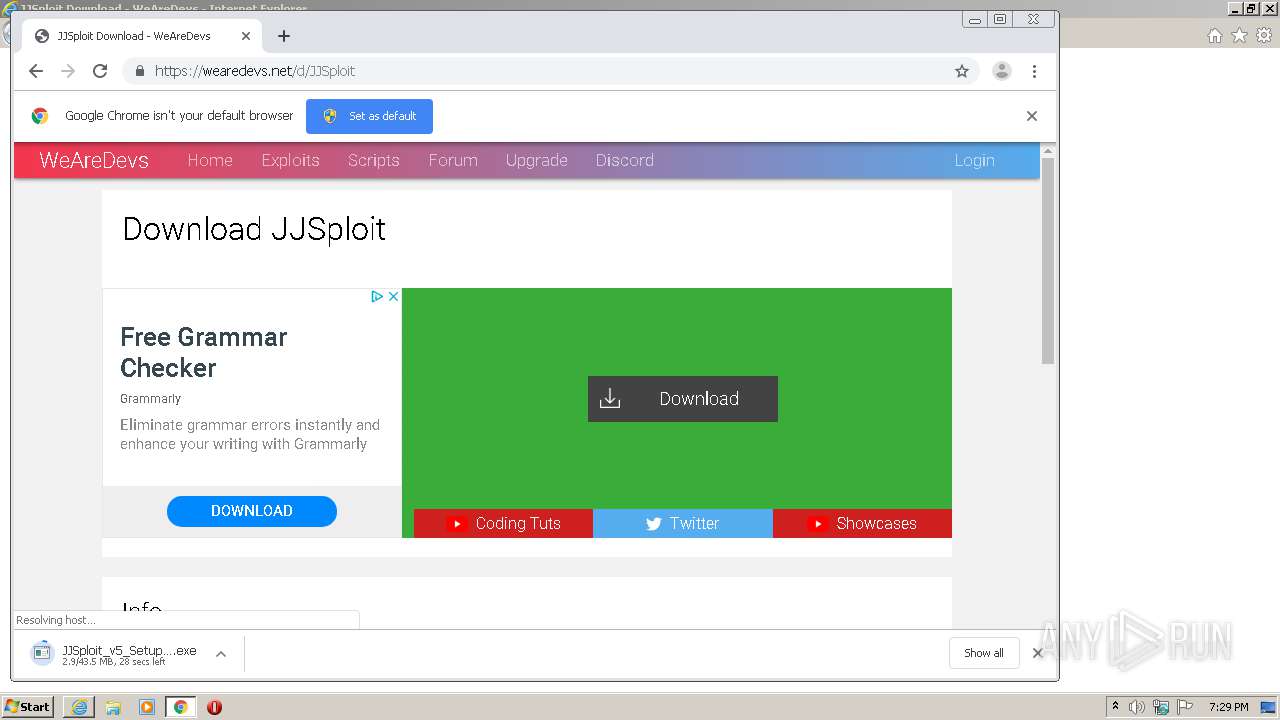
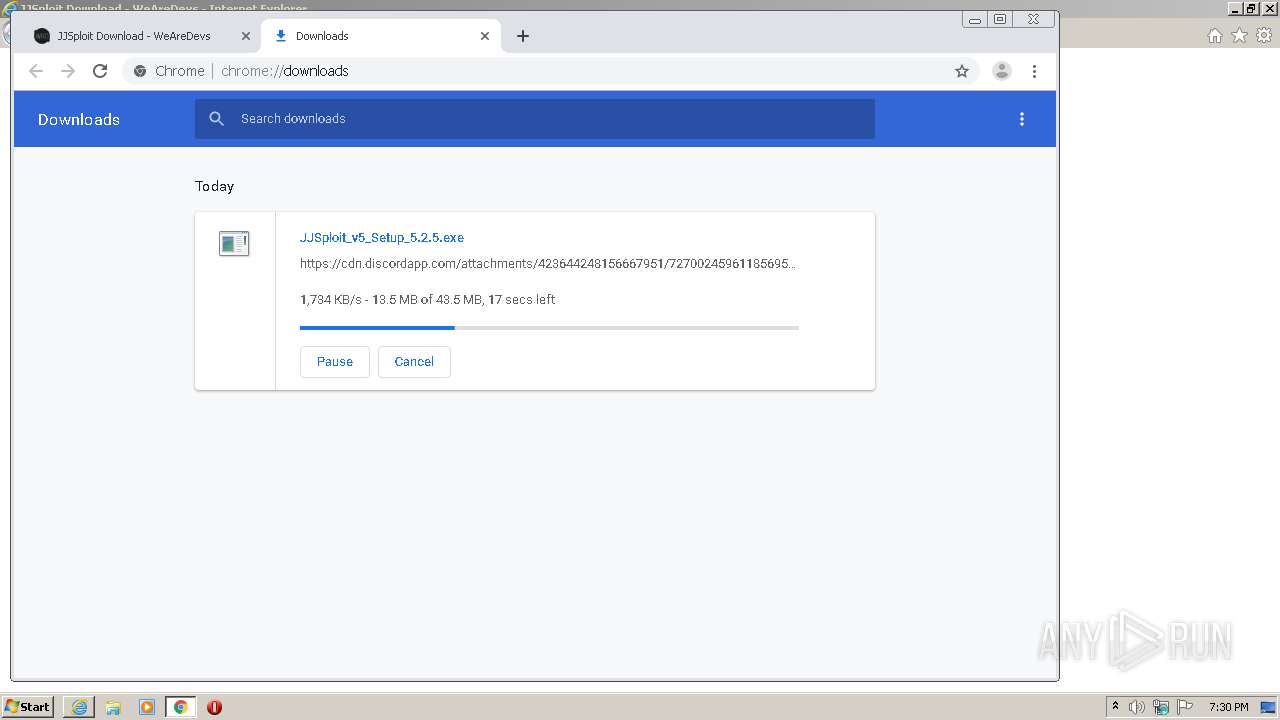
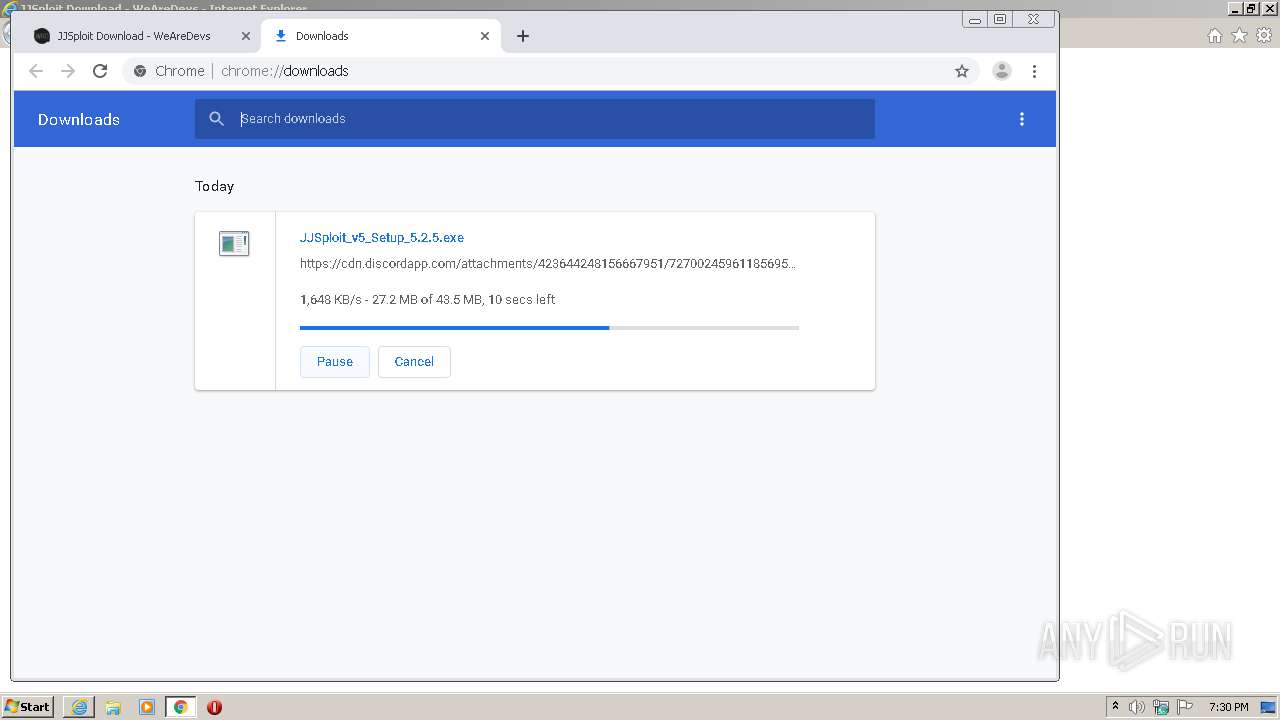
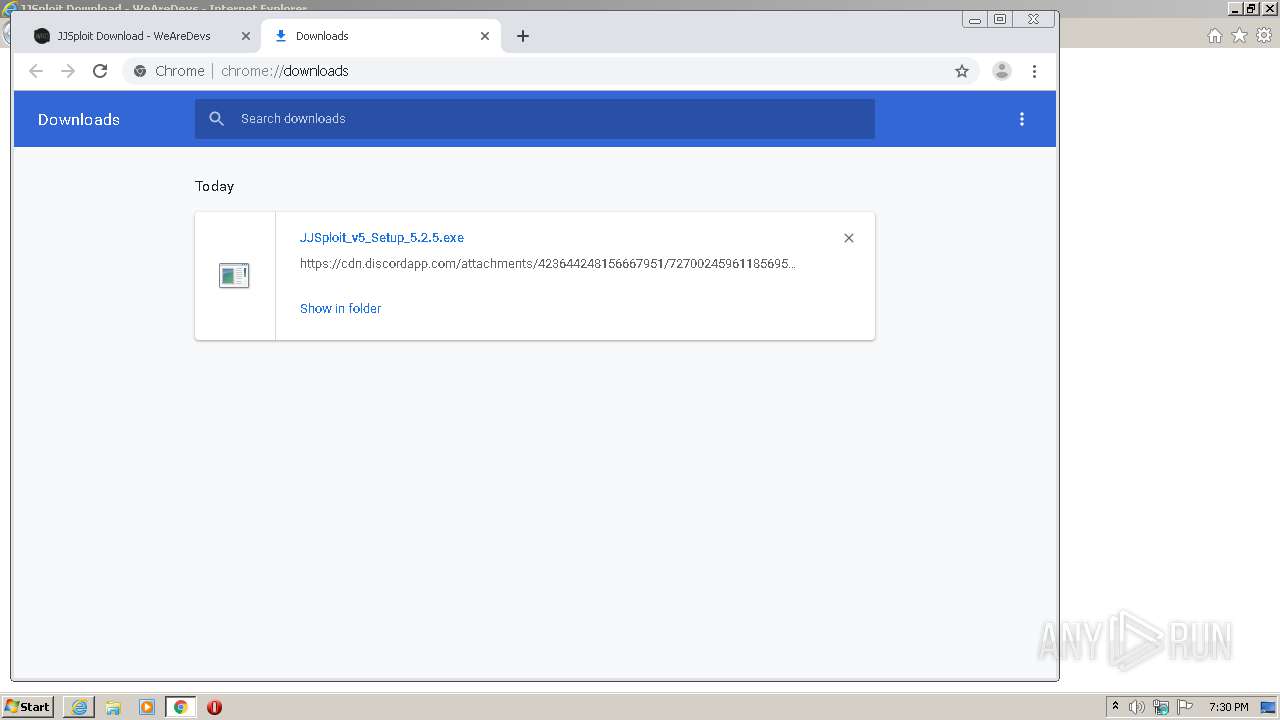
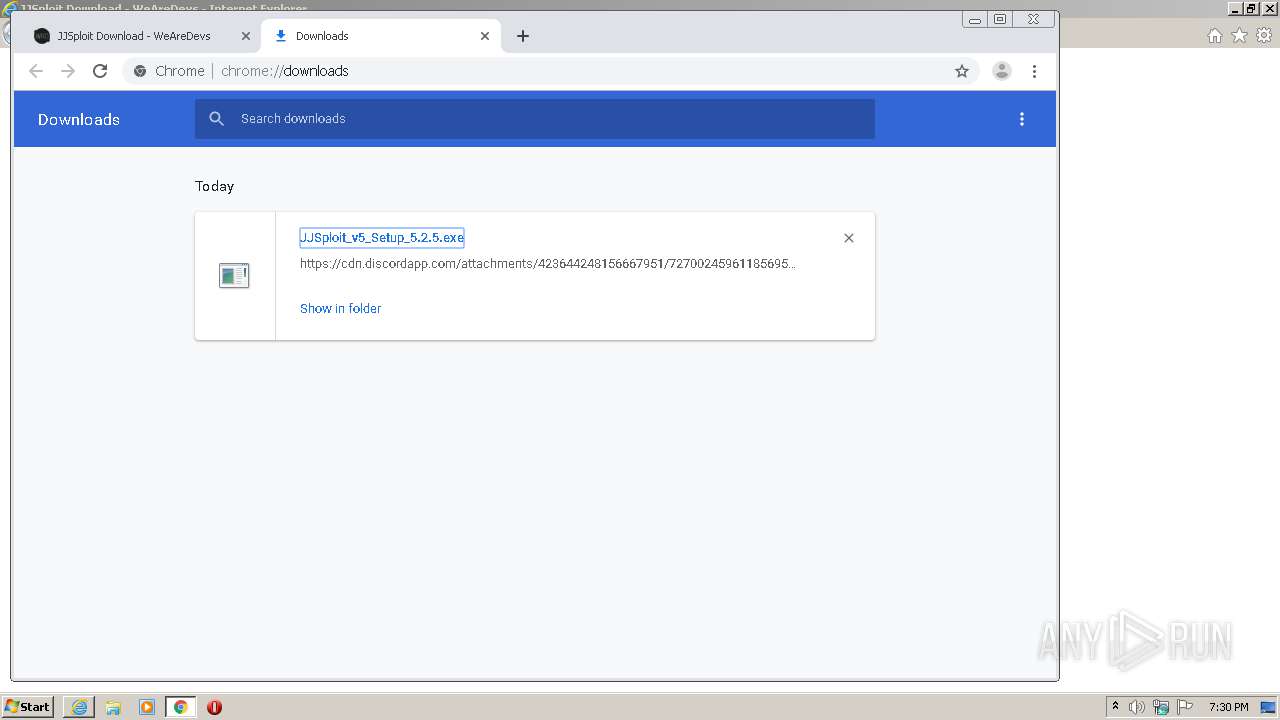
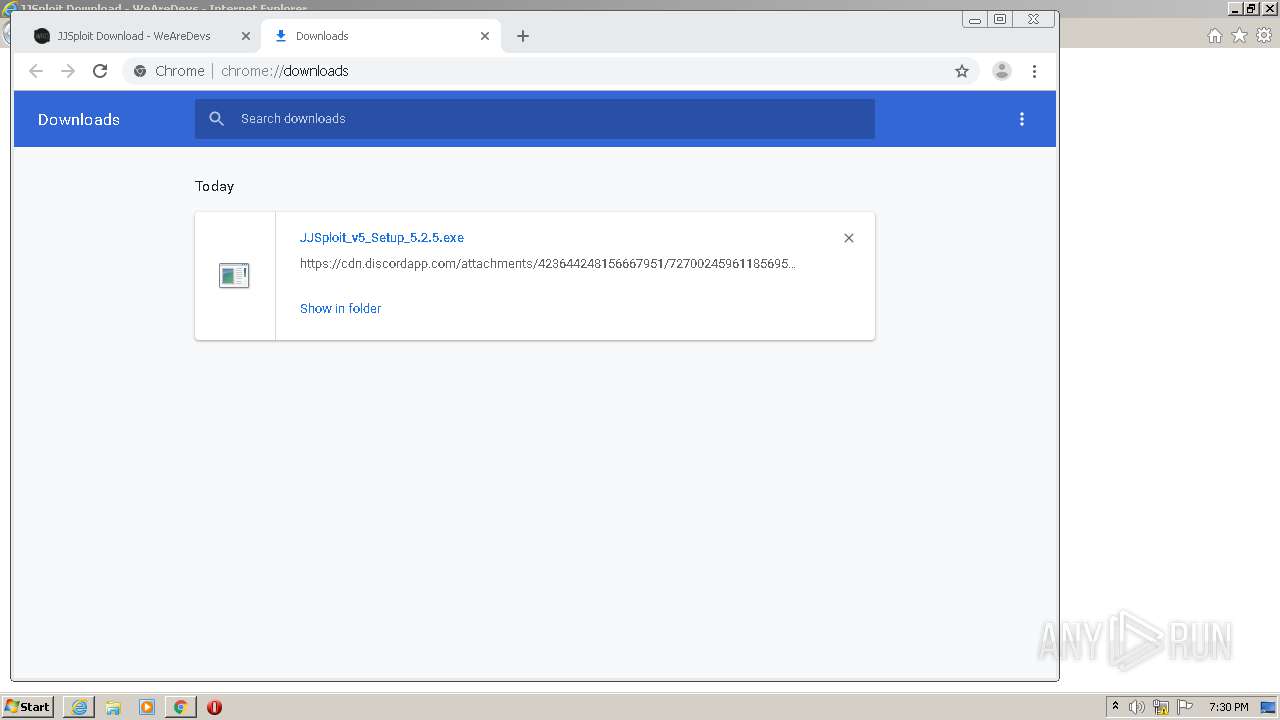
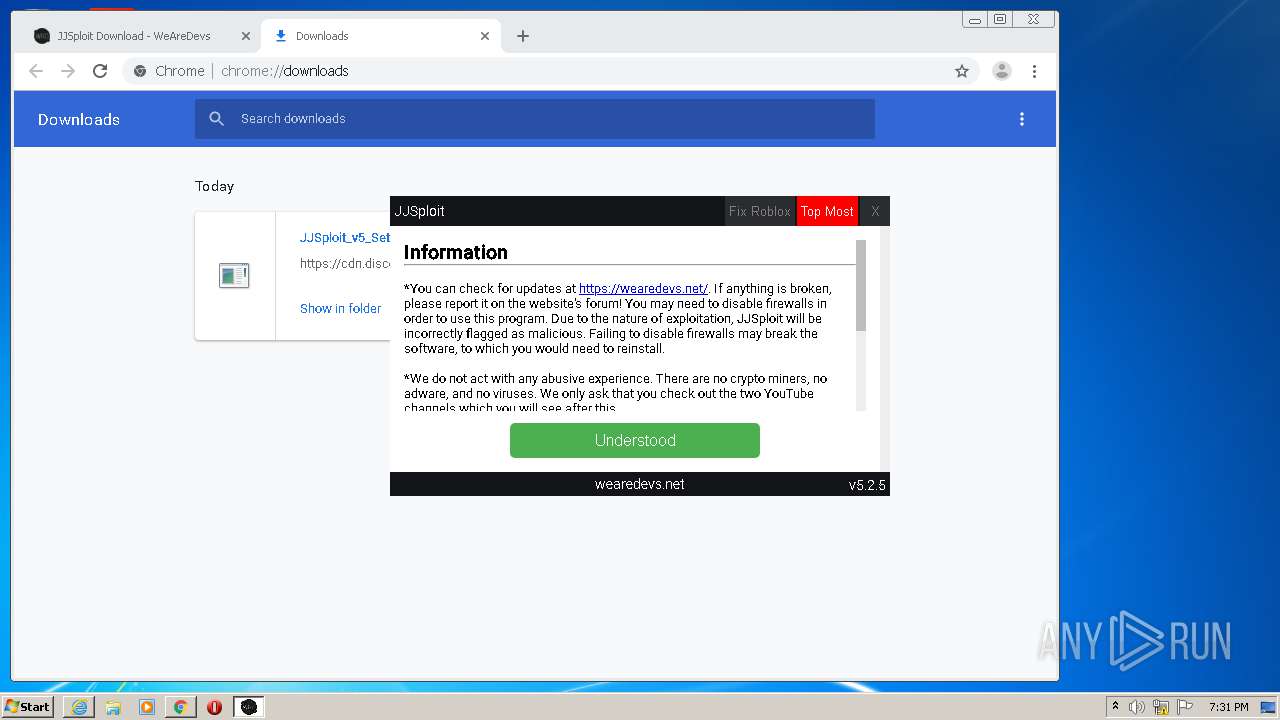
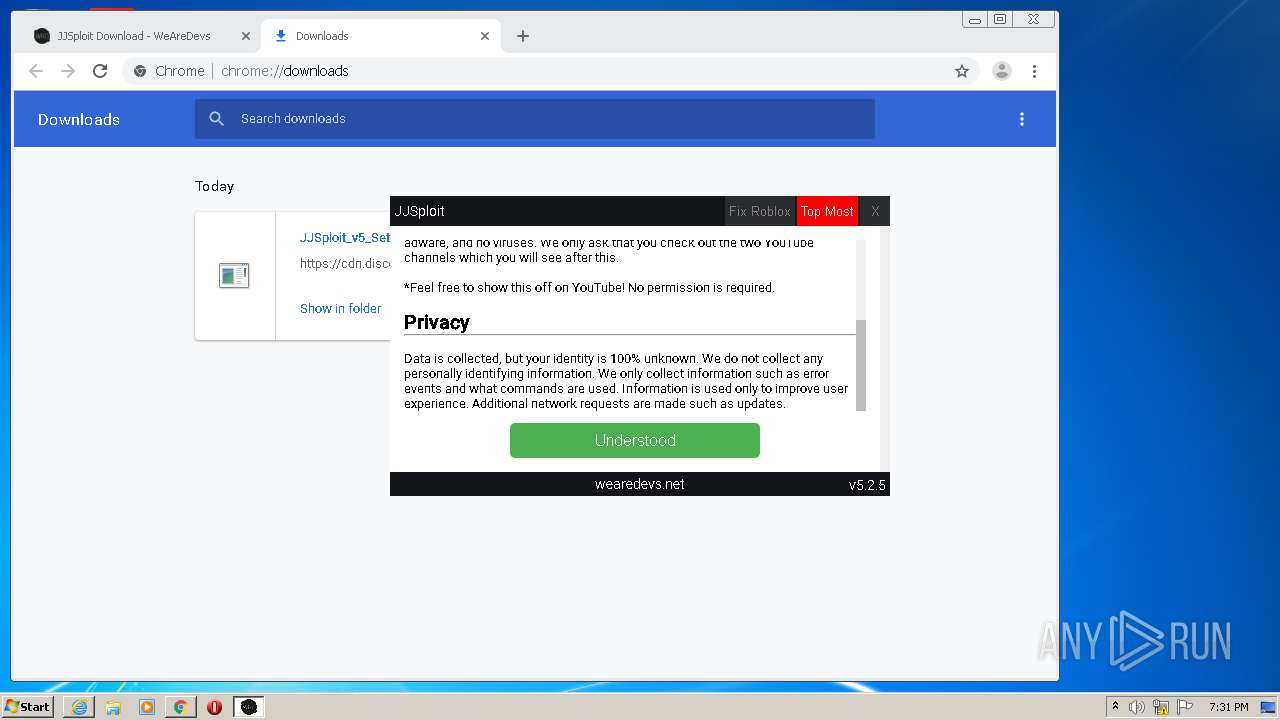
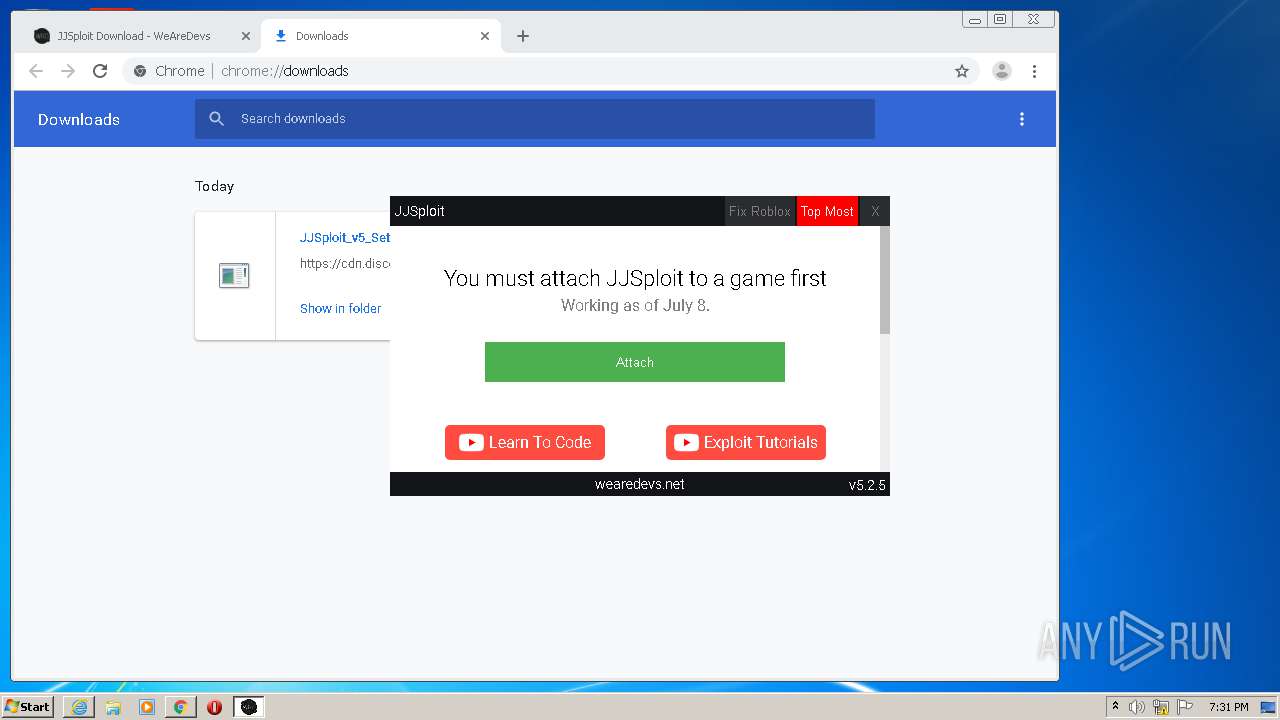
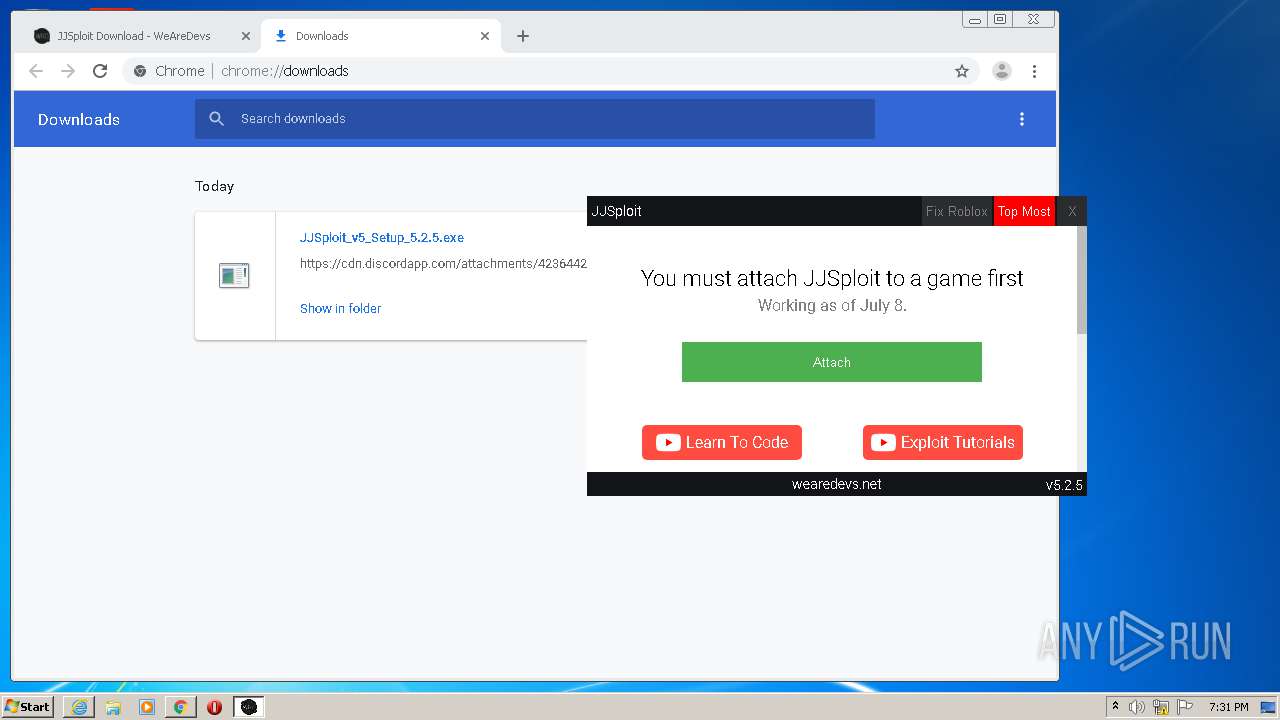
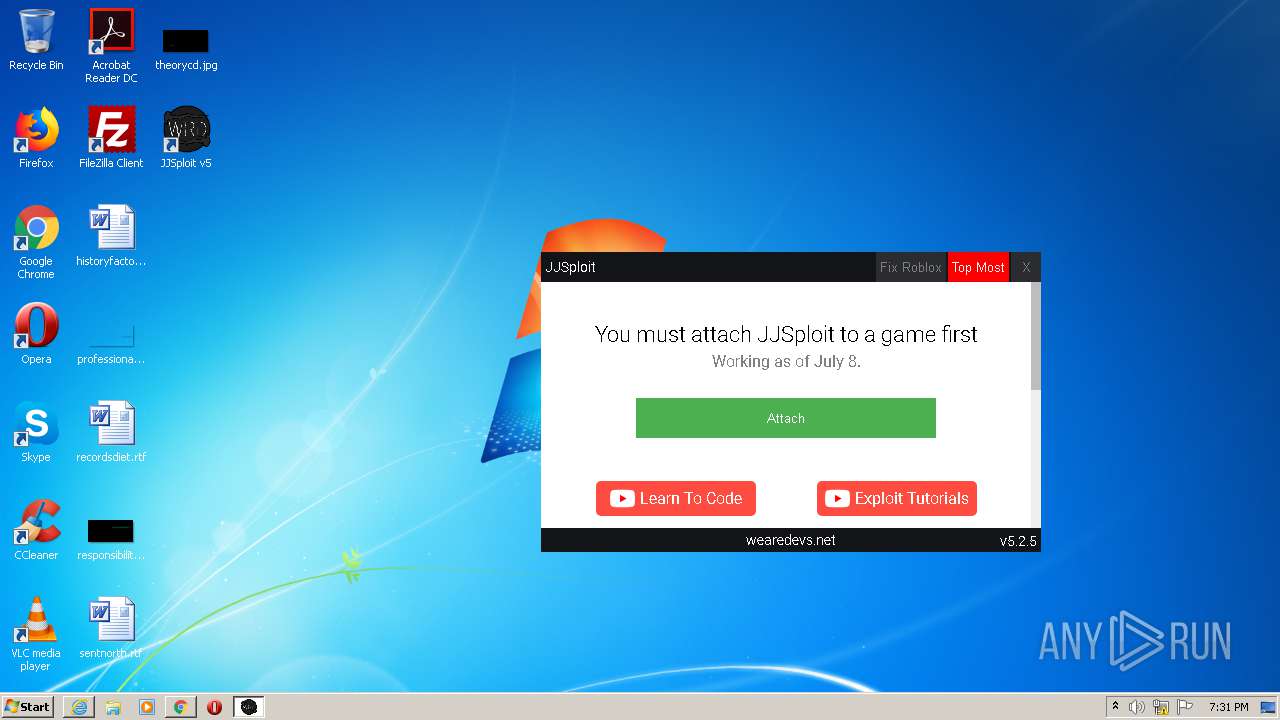
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/ff8356d2-ad02-498a-a409-cb5fc66dd35e |
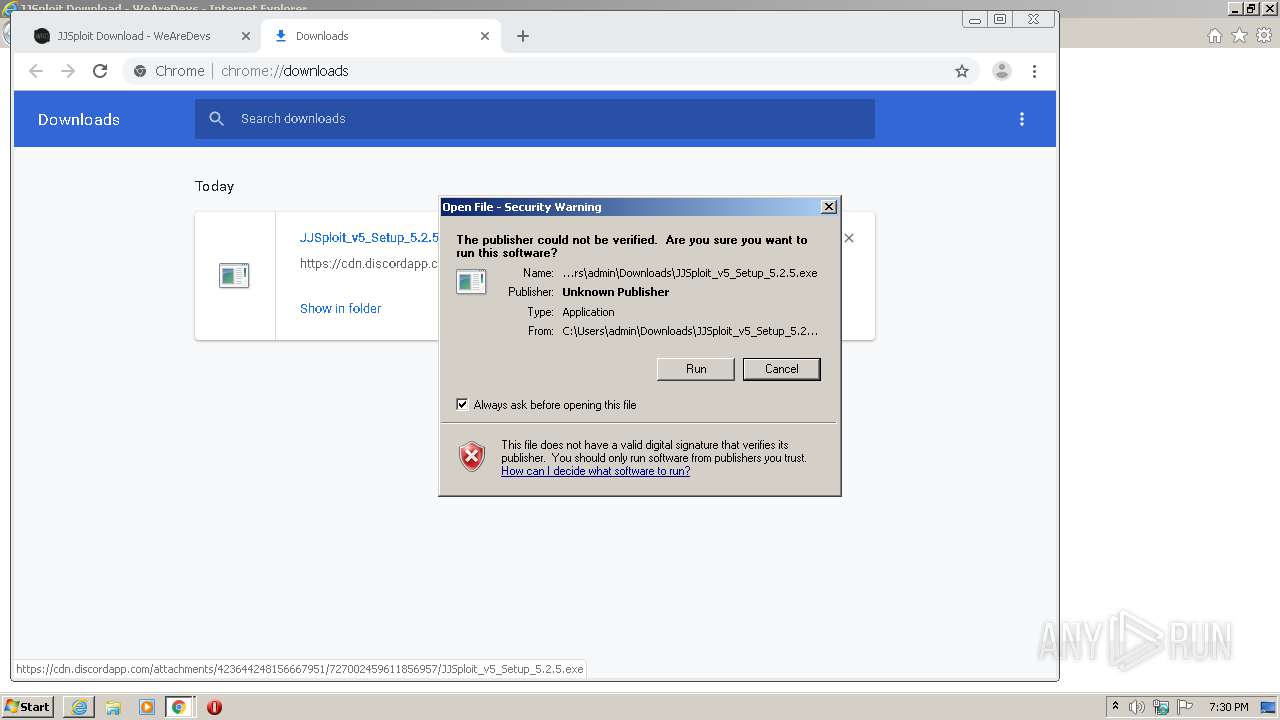
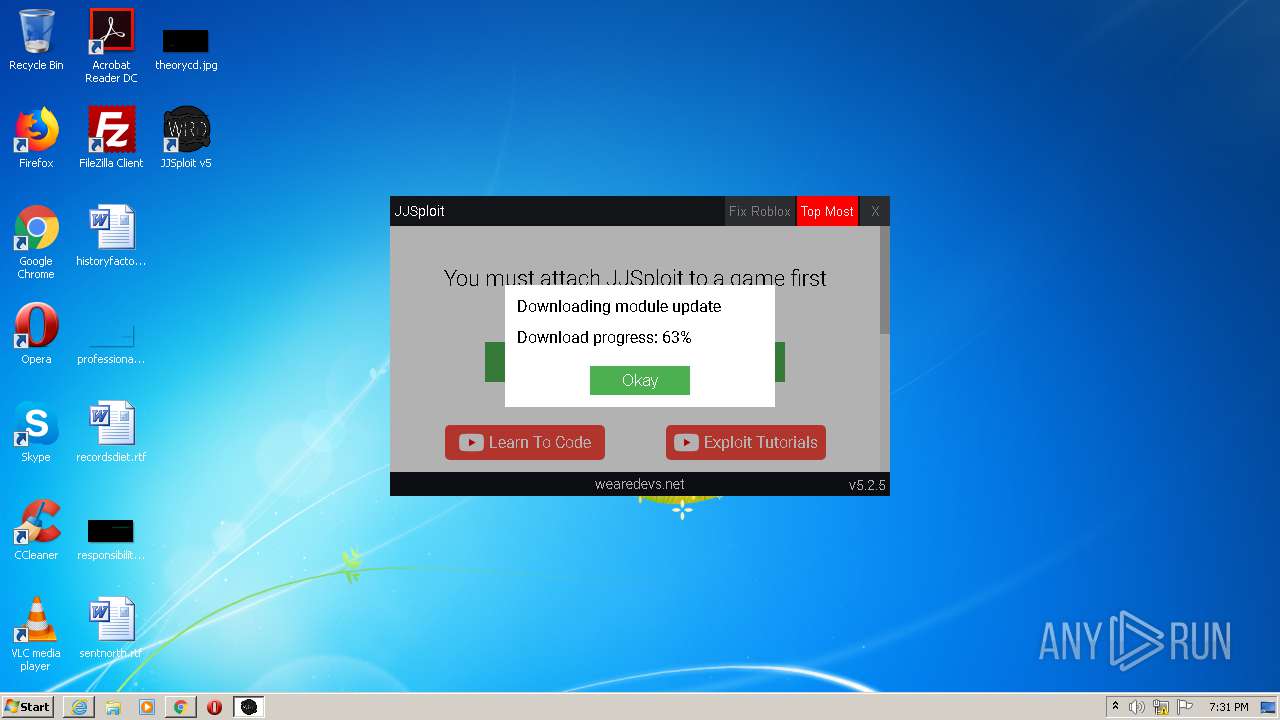
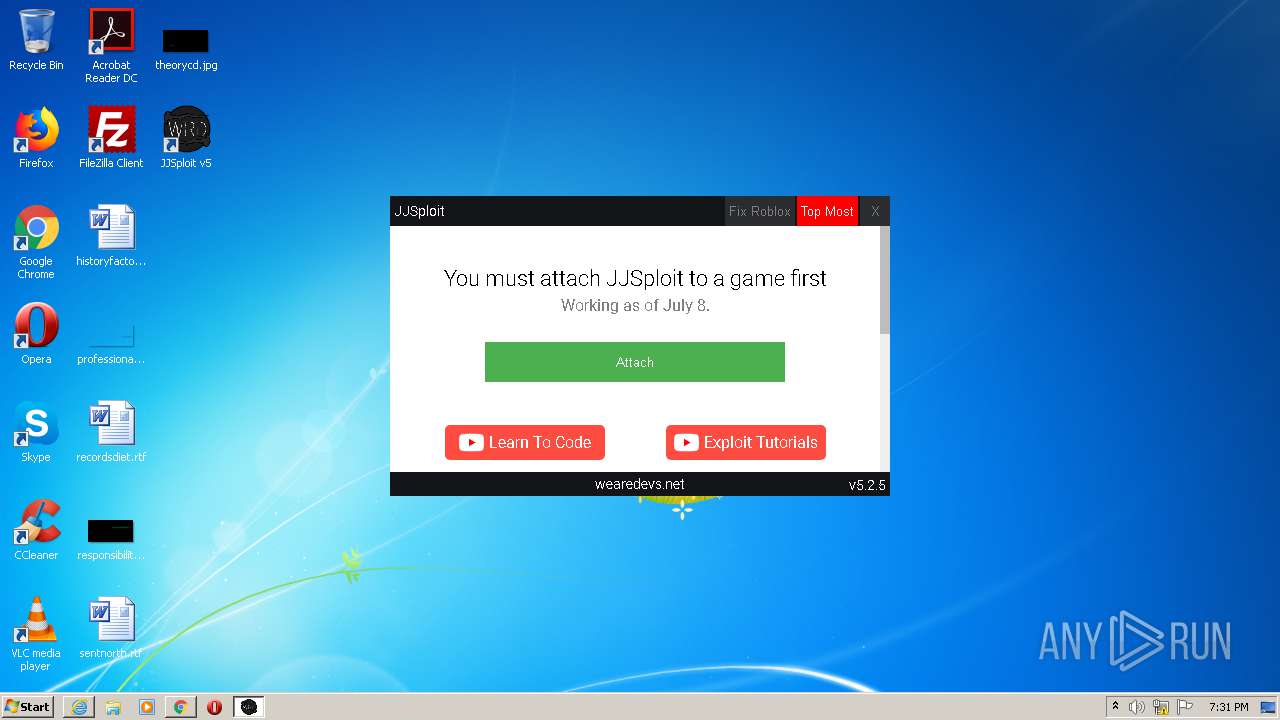
| Verdict: | Malicious activity |
| Analysis date: | July 14, 2020, 18:29:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
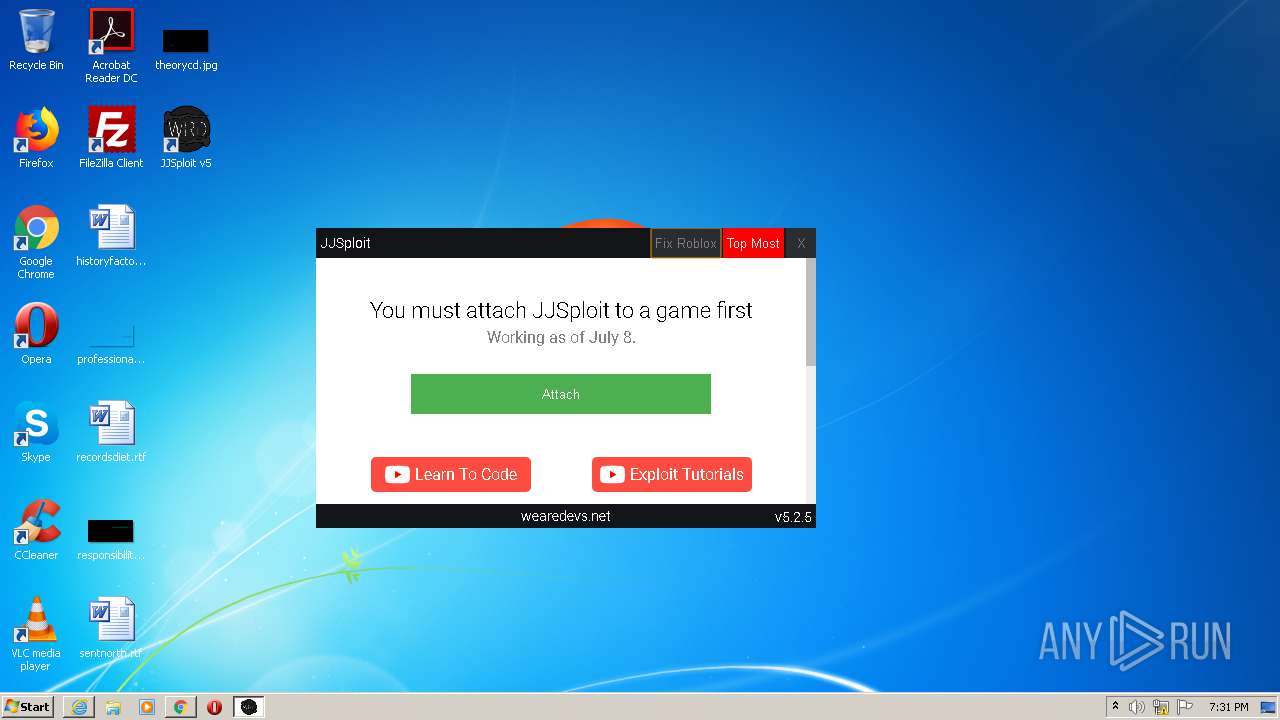
MALICIOUS
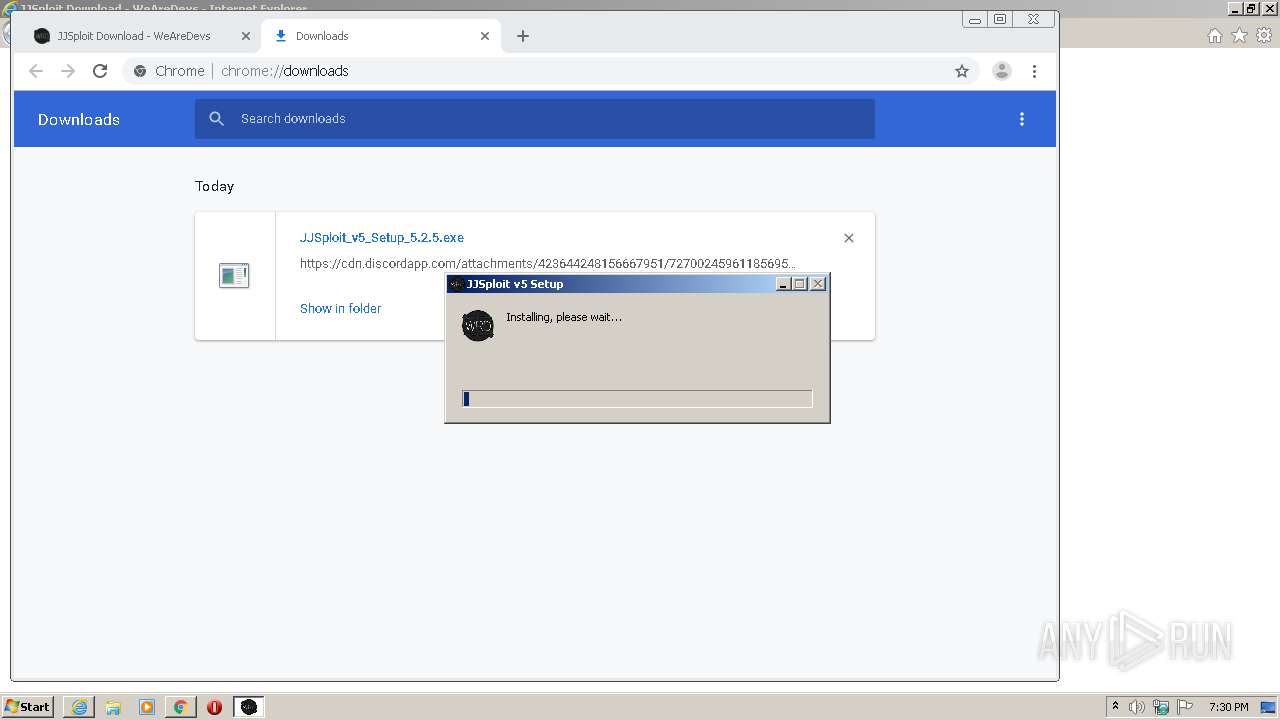
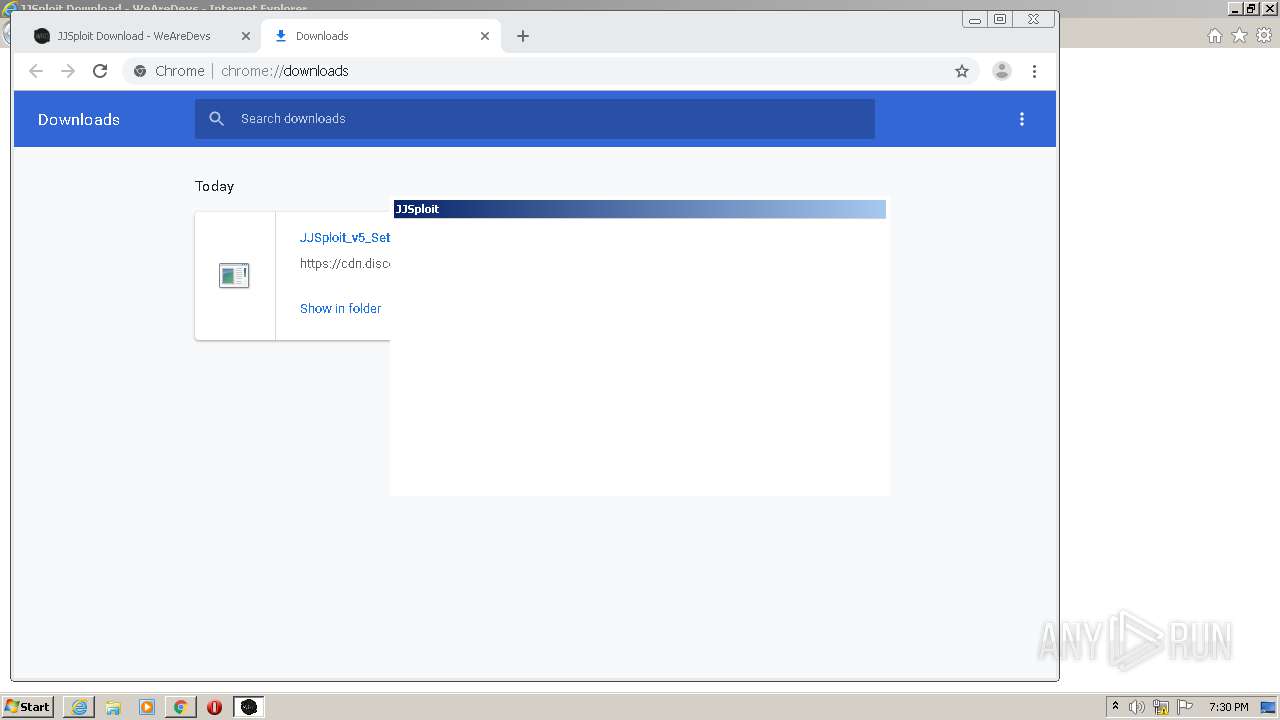
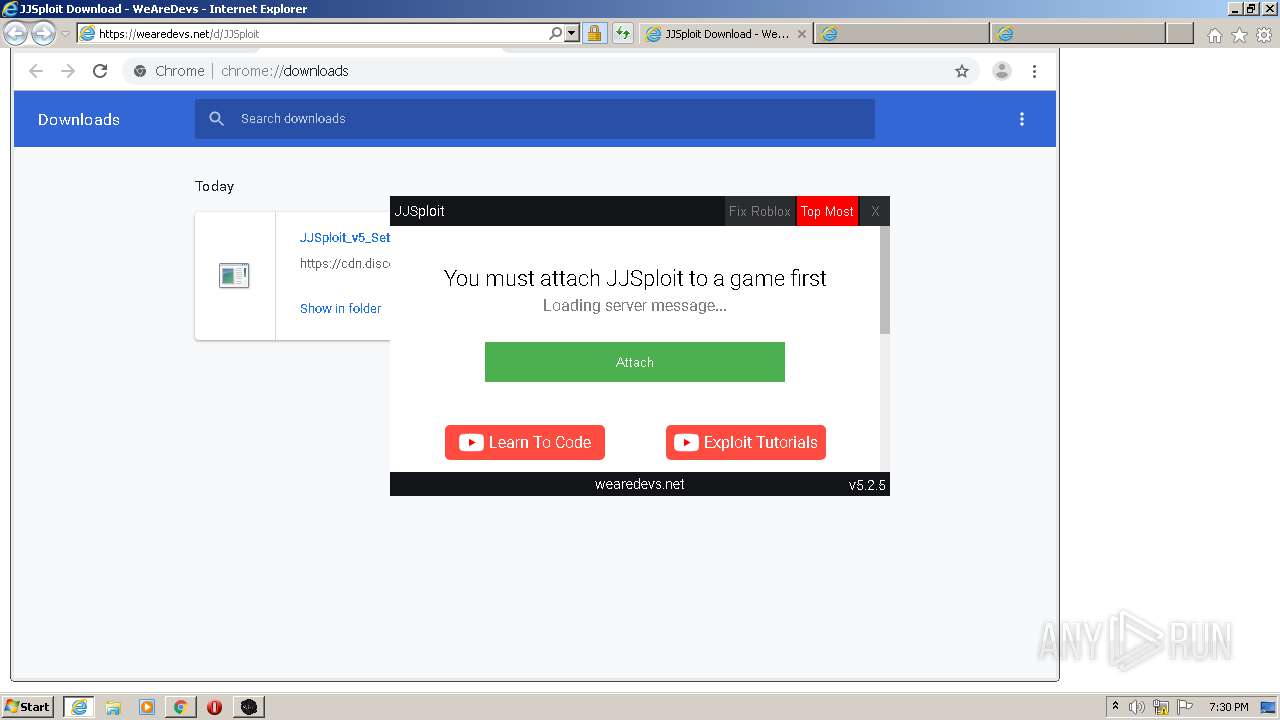
Loads dropped or rewritten executable
- JJSploit_v5_Setup_5.2.5.exe (PID: 2856)
- JJSploit v5.exe (PID: 3940)
- JJSploit v5.exe (PID: 3952)
- JJSploit v5.exe (PID: 2380)
- JJSploit v5.exe (PID: 3832)
- JJSploit v5.exe (PID: 2140)
- JJSploit v5.exe (PID: 3840)
- JJSploit v5.exe (PID: 2780)
Application was dropped or rewritten from another process
- JJSploit_v5_Setup_5.2.5.exe (PID: 2856)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2668)
- JJSploit_v5_Setup_5.2.5.exe (PID: 2856)
- JJSploit v5.exe (PID: 3940)
- JJSploit v5.exe (PID: 3832)
Creates a software uninstall entry
- JJSploit_v5_Setup_5.2.5.exe (PID: 2856)
Application launched itself
- JJSploit v5.exe (PID: 3940)
- JJSploit v5.exe (PID: 3832)
Creates files in the user directory
- JJSploit_v5_Setup_5.2.5.exe (PID: 2856)
- JJSploit v5.exe (PID: 3940)
- JJSploit v5.exe (PID: 3832)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2668)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1184)
- iexplore.exe (PID: 2204)
- chrome.exe (PID: 2668)
- iexplore.exe (PID: 4084)
- iexplore.exe (PID: 2632)
Manual execution by user
- chrome.exe (PID: 2668)
- JJSploit v5.exe (PID: 3940)
- JJSploit v5.exe (PID: 3832)
Application launched itself
- iexplore.exe (PID: 2204)
- chrome.exe (PID: 2668)
Reads internet explorer settings
- iexplore.exe (PID: 1184)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 4084)
Reads the hosts file
- chrome.exe (PID: 2668)
- JJSploit v5.exe (PID: 3940)
- chrome.exe (PID: 1020)
- JJSploit v5.exe (PID: 3832)
Creates files in the user directory
- iexplore.exe (PID: 1184)
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 4084)
Changes internet zones settings
- iexplore.exe (PID: 2204)
Reads settings of System Certificates
- iexplore.exe (PID: 1184)
- iexplore.exe (PID: 4084)
- chrome.exe (PID: 1020)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 2204)
Changes settings of System certificates
- iexplore.exe (PID: 2204)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
47
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10668487055251203374 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3776 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14213377355308015558 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14590469218835365163 --mojo-platform-channel-handle=4872 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15581058646024822252 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2512 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10140040020622363278 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14640446252268524972 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17341310576893959427 --mojo-platform-channel-handle=1672 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,3122662038627007684,13050810464521943850,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13520270041368594205 --mojo-platform-channel-handle=3336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f39a9d0,0x6f39a9e0,0x6f39a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2204 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
10 425
Read events
2 710
Write events
5 230
Delete events
2 485
Modification events
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 3509428038 | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30824972 | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2204) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
24
Suspicious files
114
Text files
528
Unknown types
105
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1184 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7759.tmp | — | |
MD5:— | SHA256:— | |||
| 1184 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar775A.tmp | — | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F0DF99E-A6C.pma | — | |
MD5:— | SHA256:— | |||
| 1184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download[1].css | text | |
MD5:— | SHA256:— | |||
| 1184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:— | SHA256:— | |||
| 2204 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\JJSploit[1].htm | html | |
MD5:— | SHA256:— | |||
| 1184 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\HUKD5KWU.txt | text | |
MD5:— | SHA256:— | |||
| 1184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\navheader[1].css | text | |
MD5:— | SHA256:— | |||
| 2668 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
151
DNS requests
68
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 471 b | whitelisted |
1184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAs907AFBAD%2F9Fig505P1vU%3D | US | der | 279 b | whitelisted |
1184 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAar2mu0dHehCAAAAABH74o%3D | US | der | 471 b | whitelisted |
1020 | chrome.exe | GET | 200 | 185.48.9.14:80 | http://r3---sn-x2pm-3uf6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNmRlQUFXU0o1UkNFTWx3aGRUUHBsWUJUZw/7819.902.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=8p&mip=84.17.55.74&mm=28&mn=sn-x2pm-3uf6&ms=nvh&mt=1594751233&mv=m&mvi=3&pl=23&shardbypass=yes | PL | crx | 824 Kb | whitelisted |
1184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 471 b | whitelisted |
1020 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 535 b | whitelisted |
1184 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCwYB8EgRo8UwgAAAAAR%2FC%2F | US | der | 472 b | whitelisted |
1184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAs907AFBAD%2F9Fig505P1vU%3D | US | der | 279 b | whitelisted |
1184 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEA%2FVhdRLfbN%2FXD5lO%2FSyJvc%3D | US | der | 279 b | whitelisted |
1184 | iexplore.exe | GET | 200 | 172.217.22.3:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAar2mu0dHehCAAAAABH74o%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1184 | iexplore.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
1184 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1184 | iexplore.exe | 172.217.18.162:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
1184 | iexplore.exe | 104.16.133.229:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | suspicious |
1184 | iexplore.exe | 104.26.7.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
1184 | iexplore.exe | 216.58.207.40:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1184 | iexplore.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2204 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1020 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1020 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |