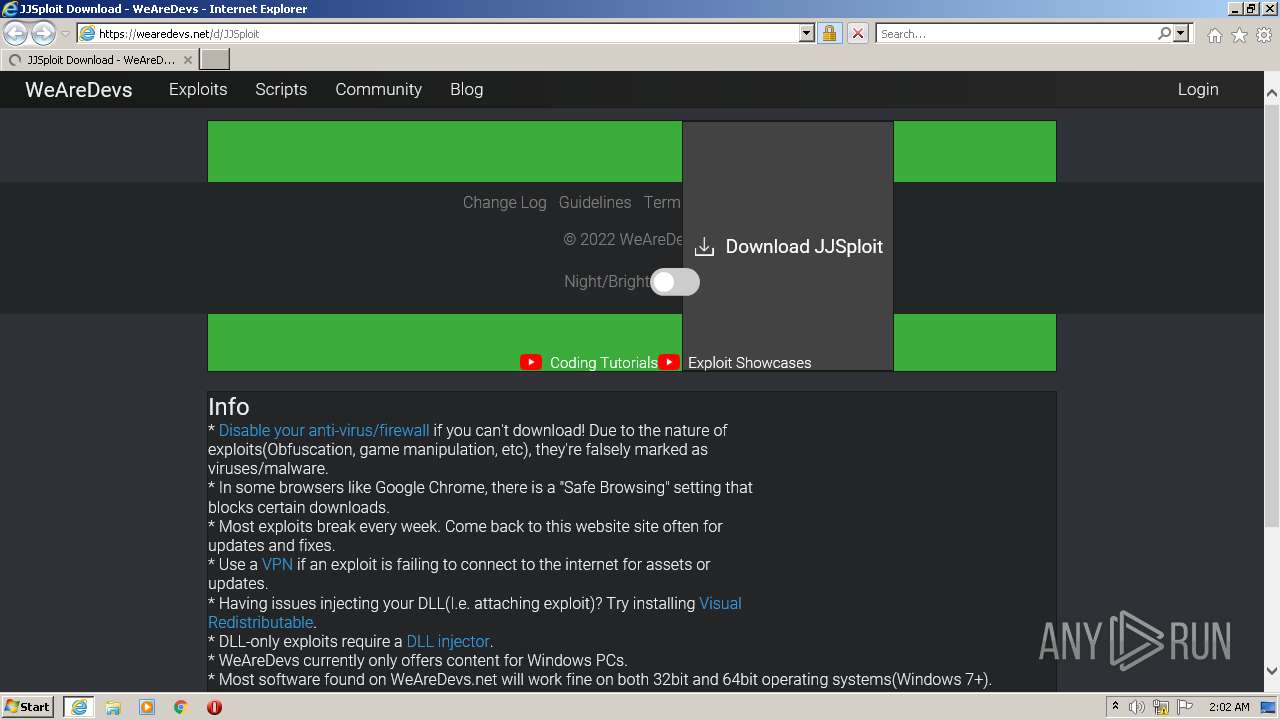
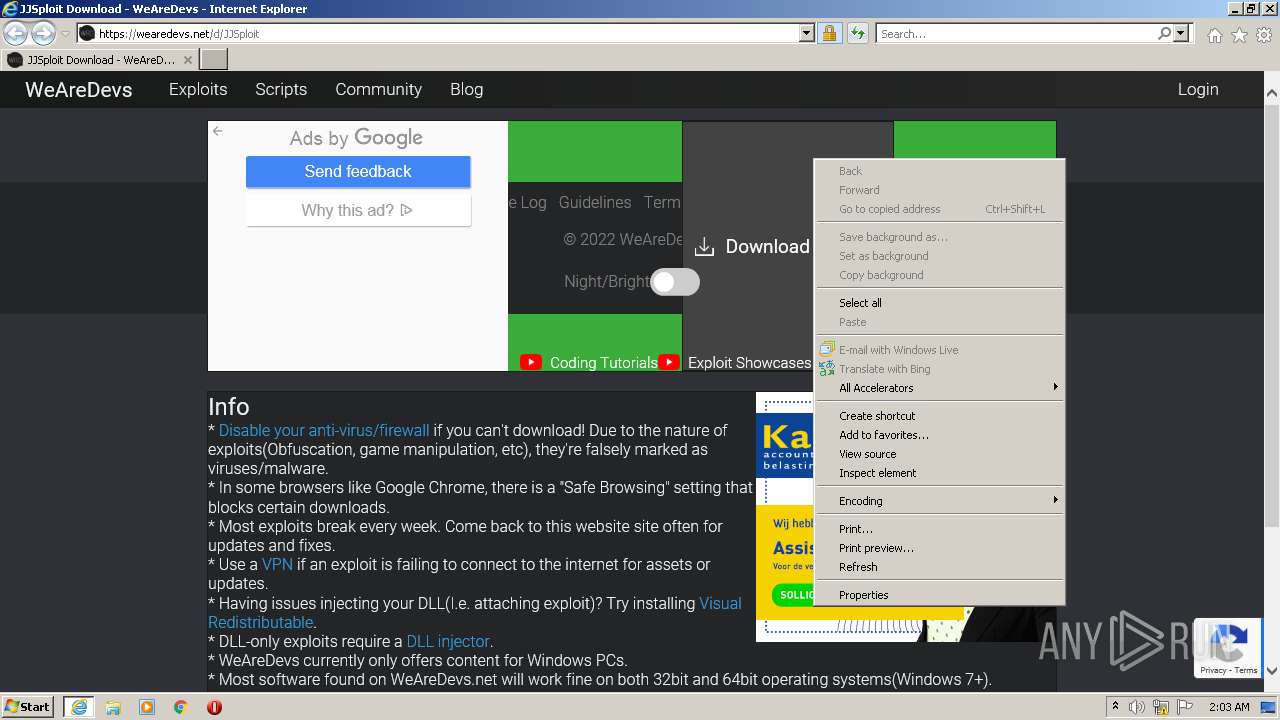
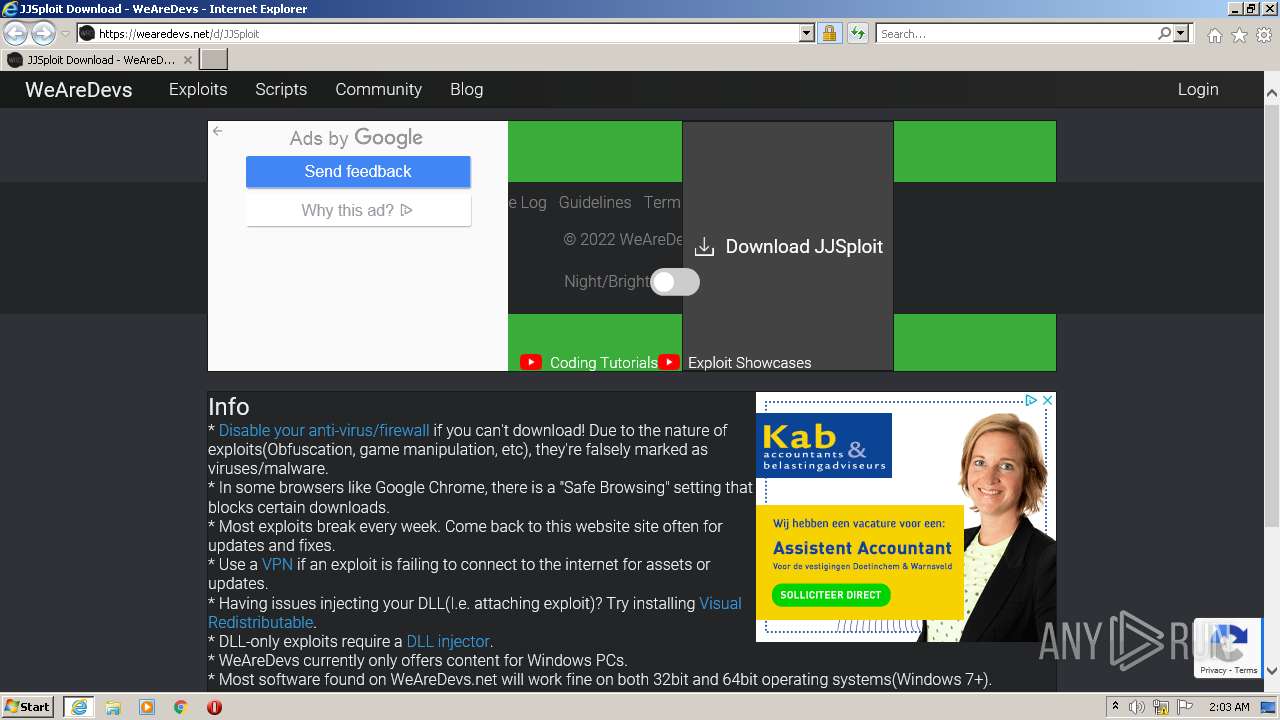
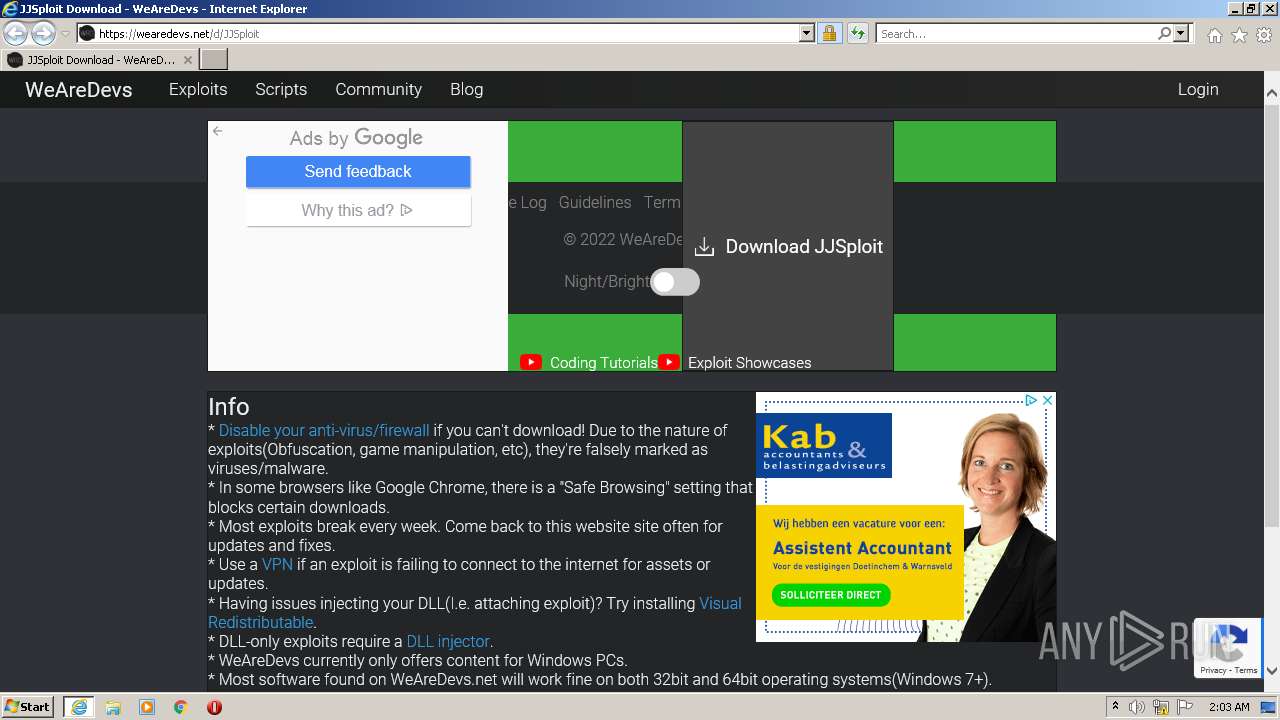
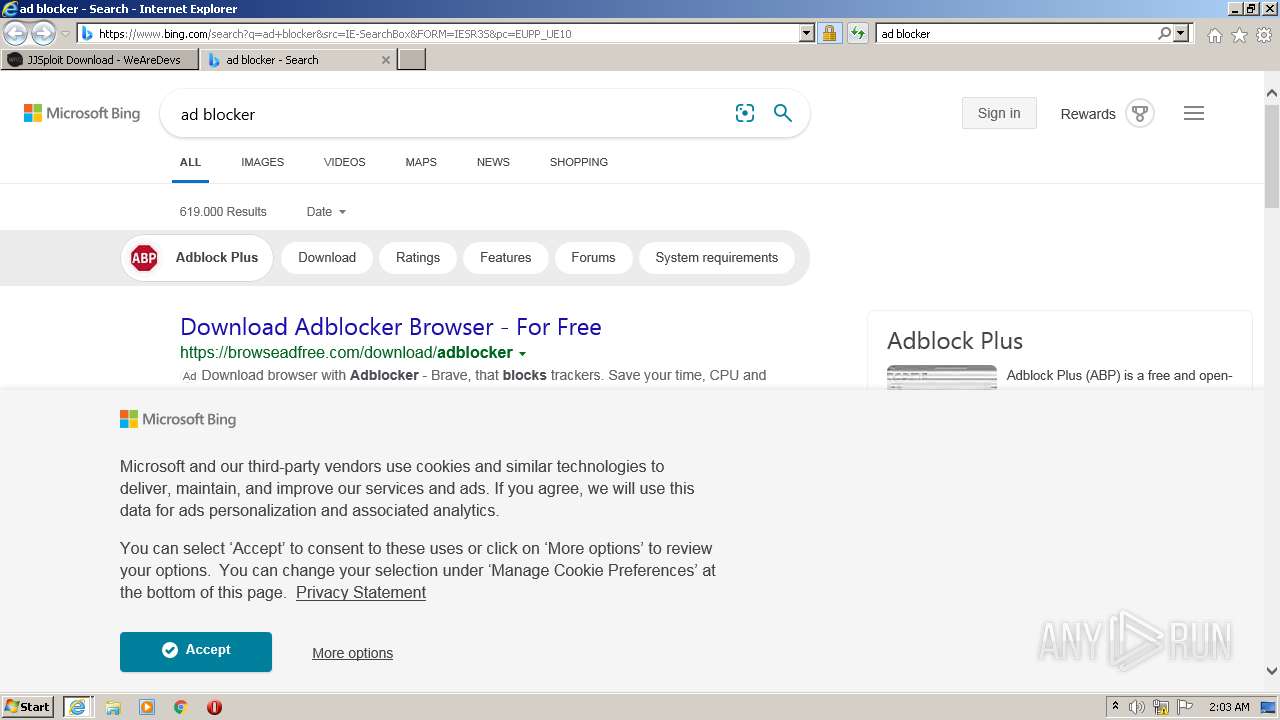
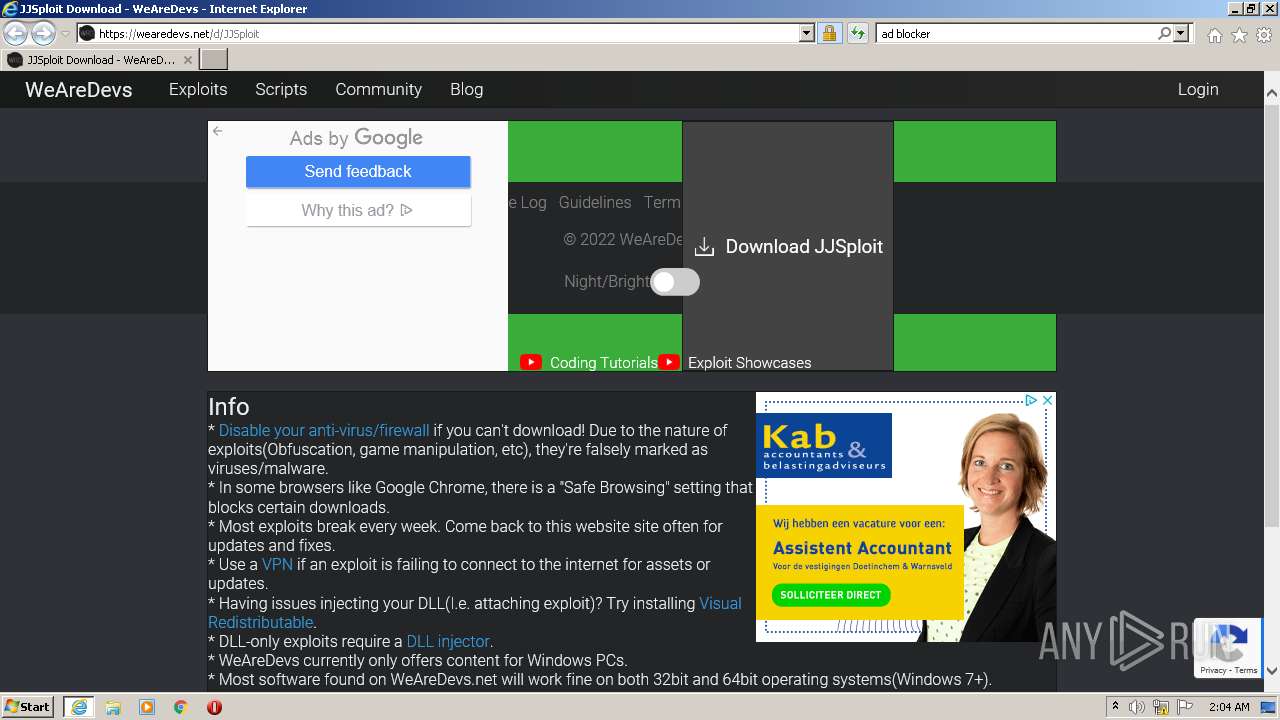
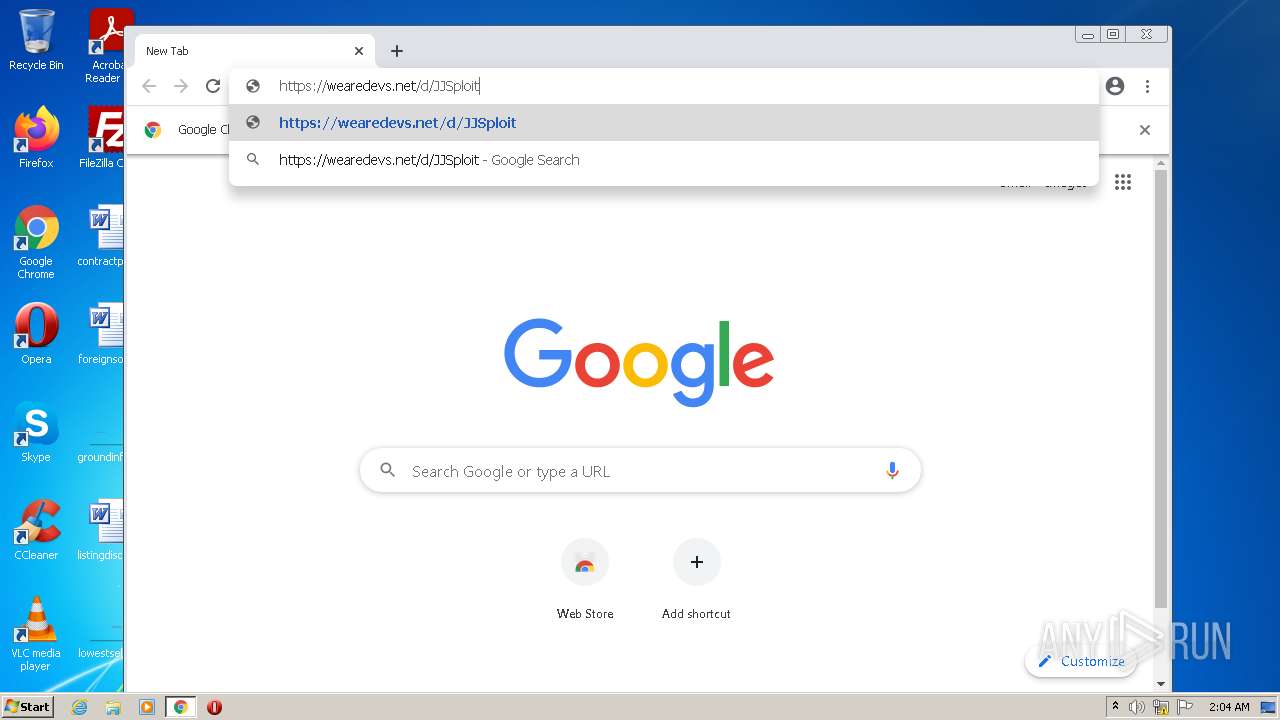
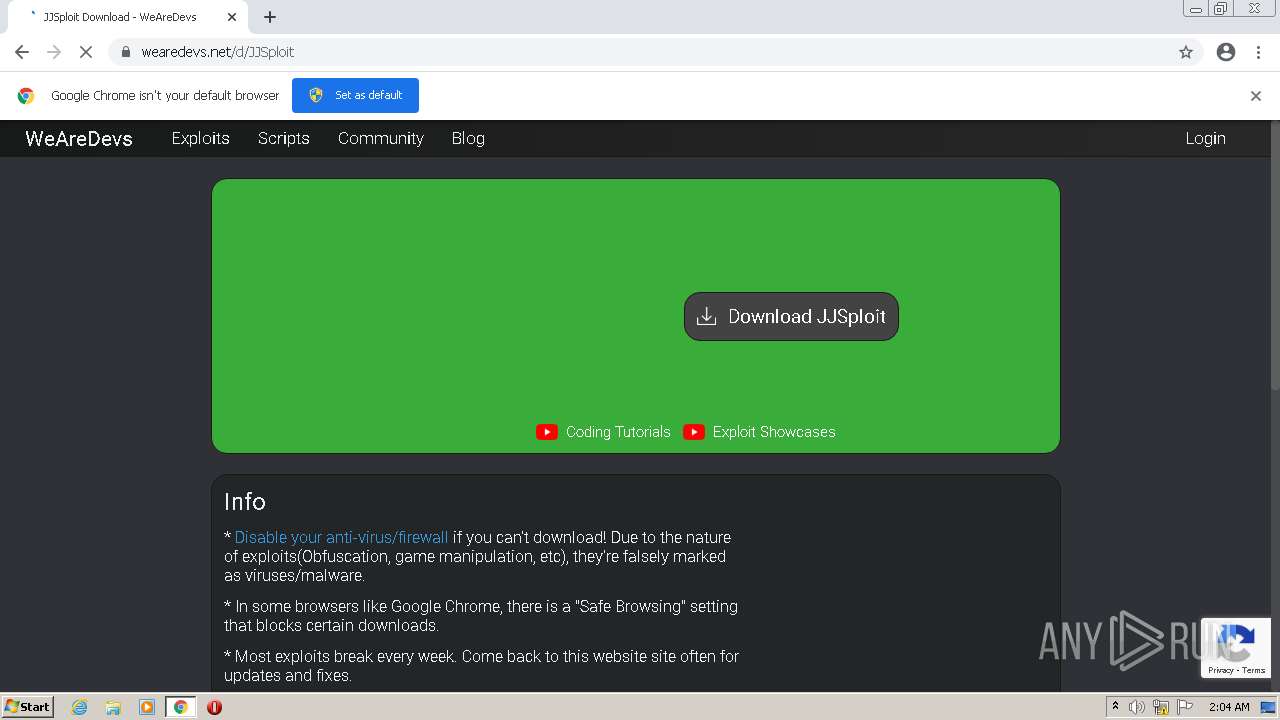
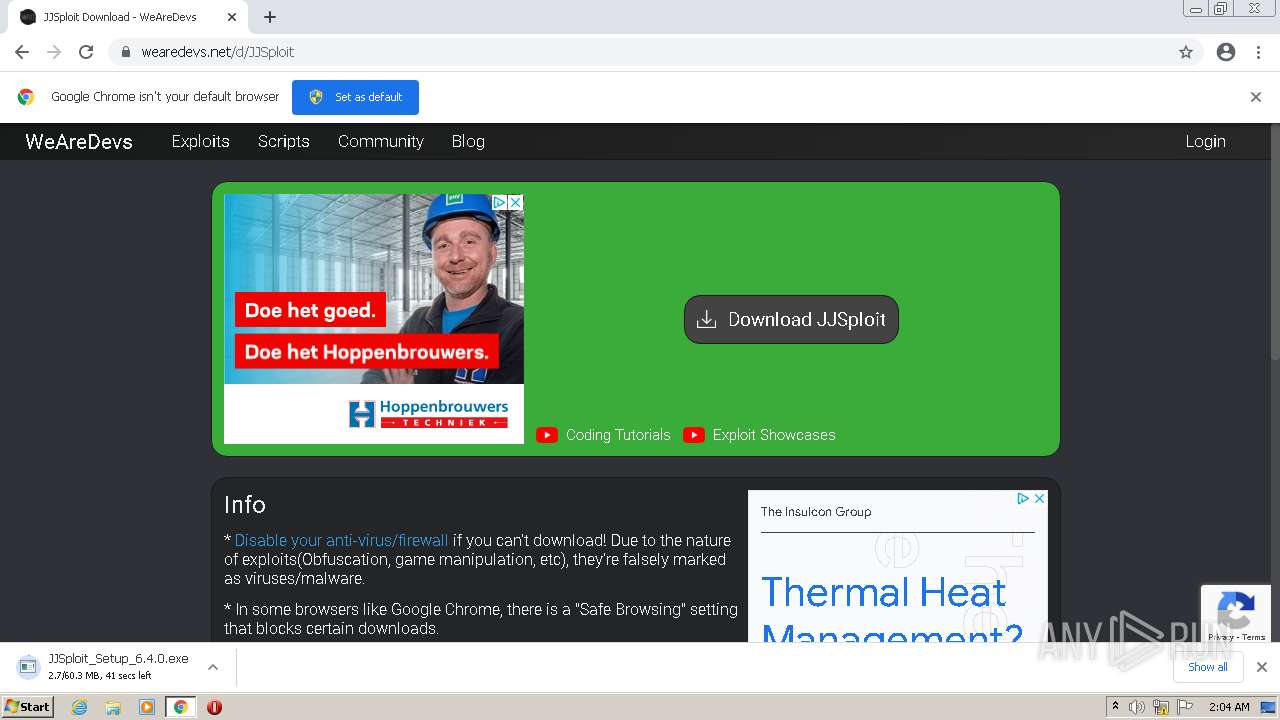
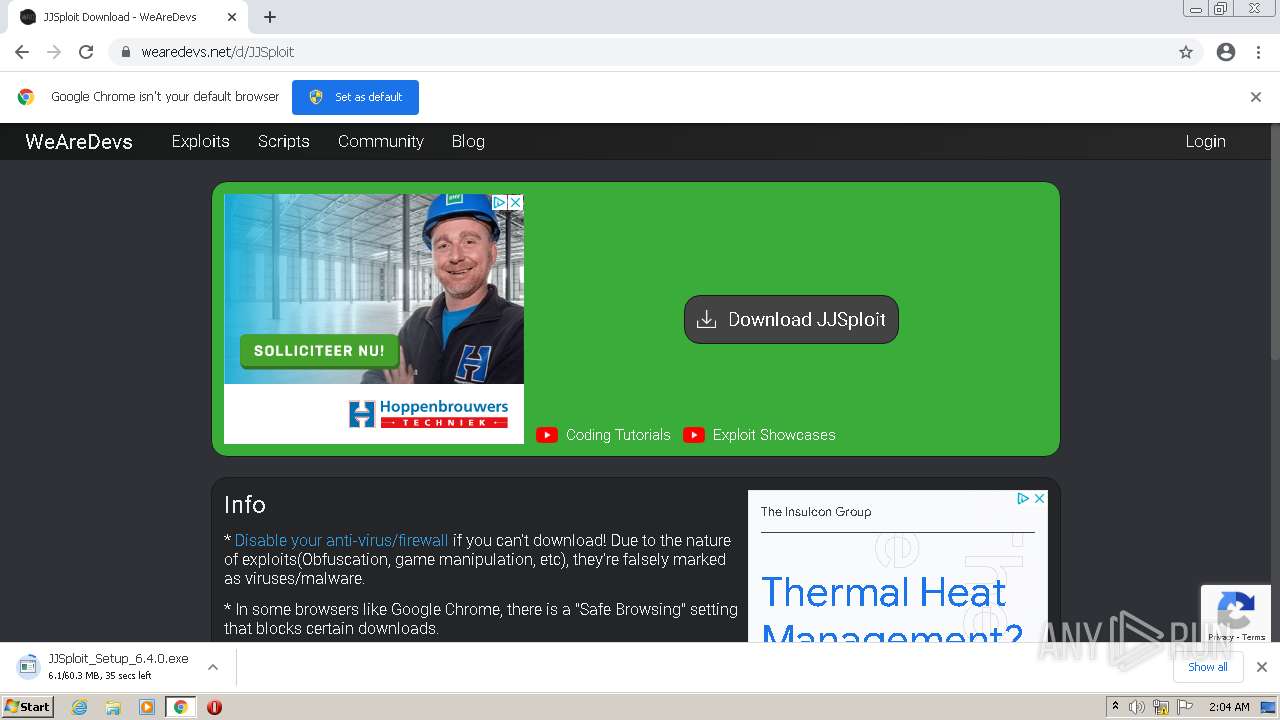
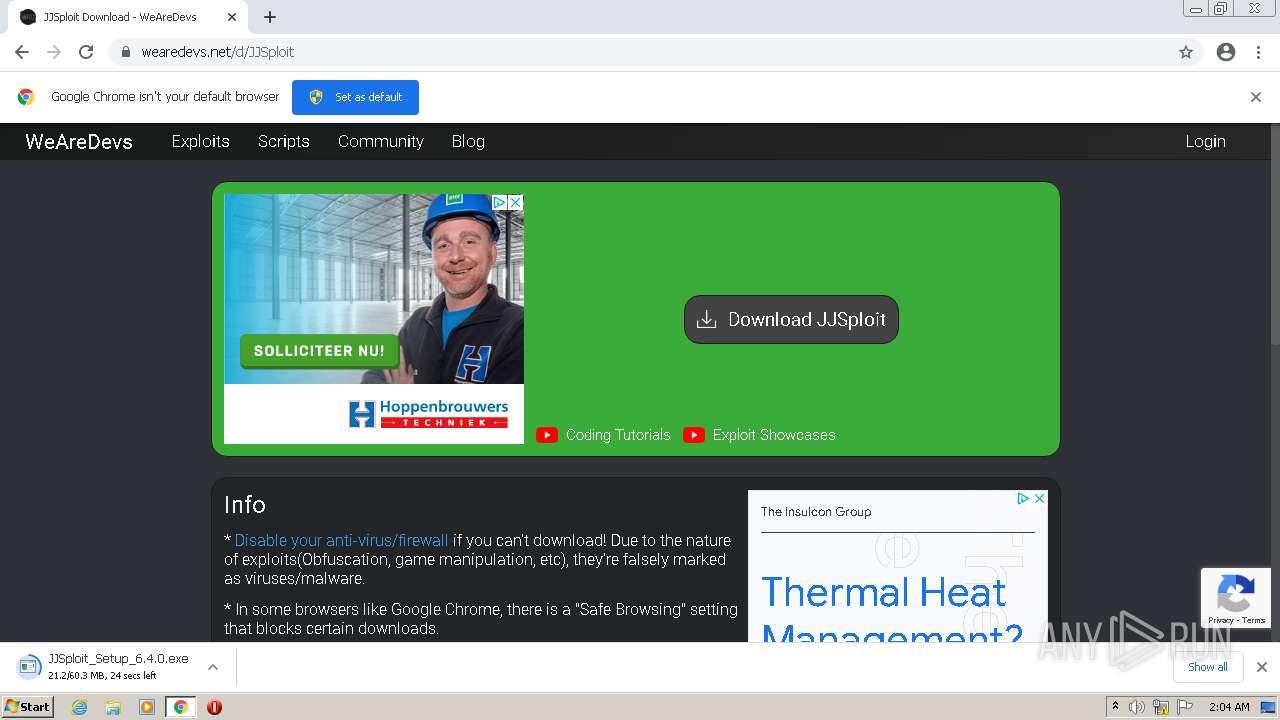
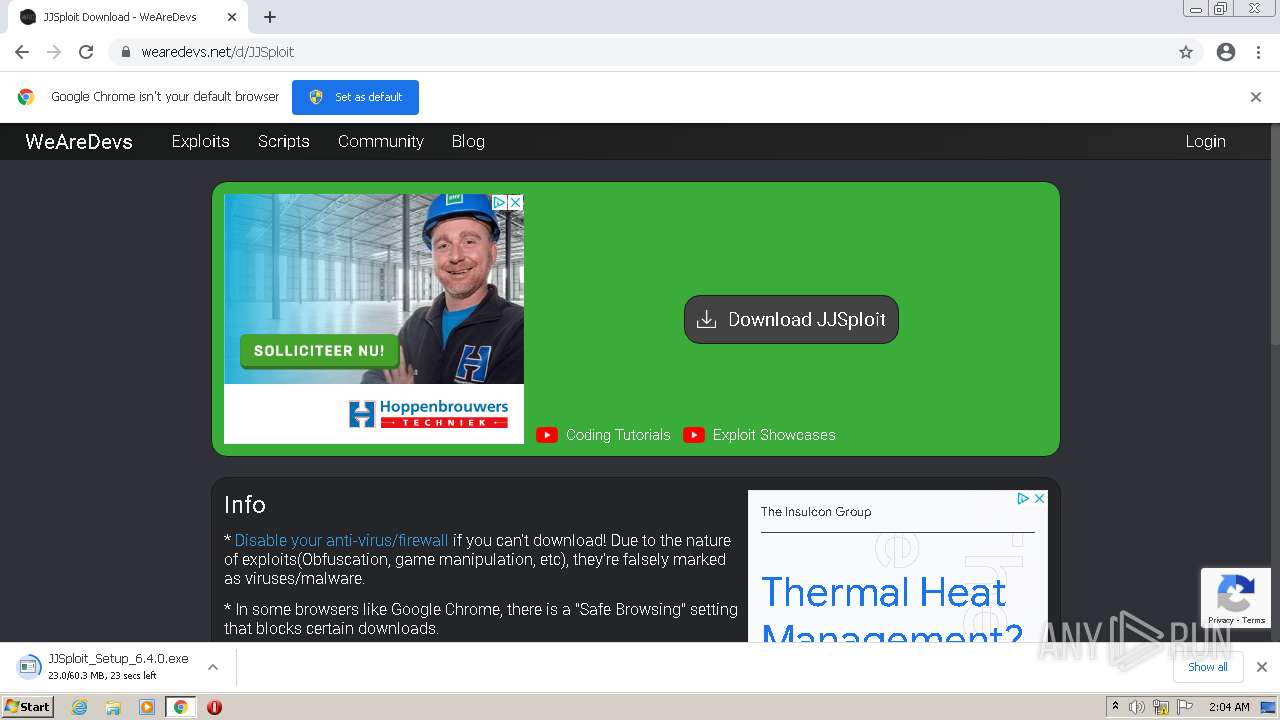
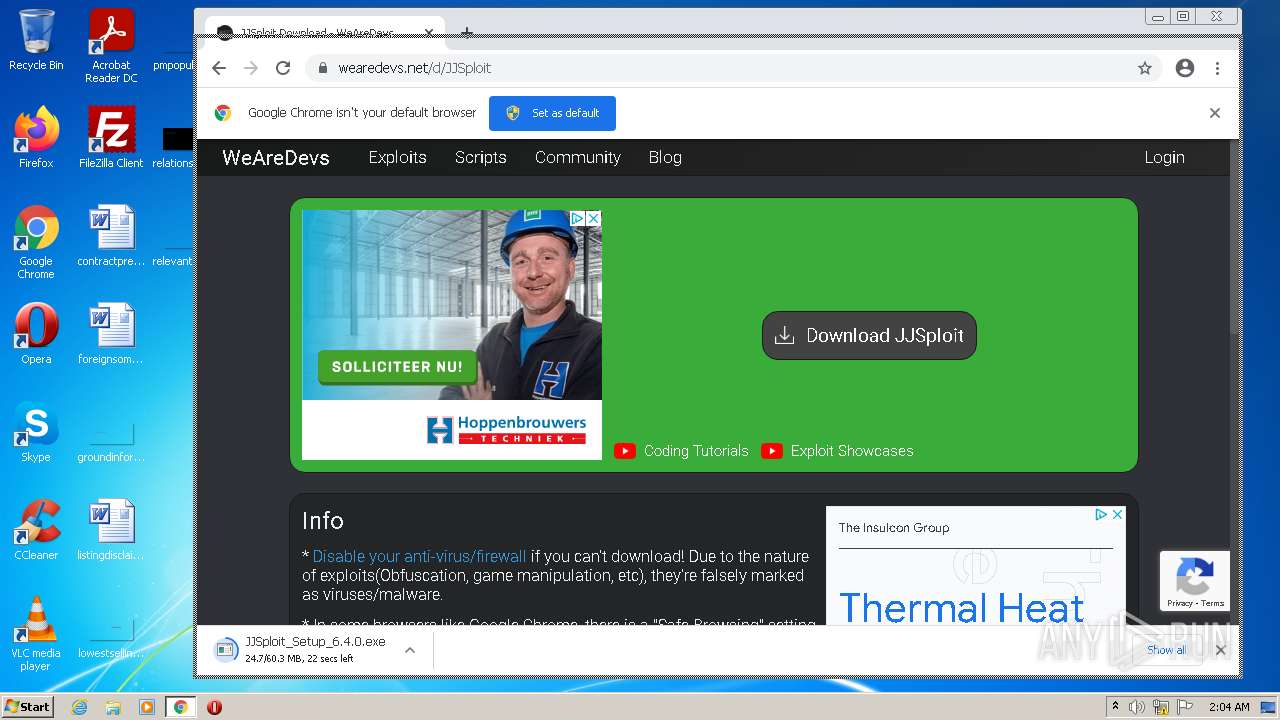
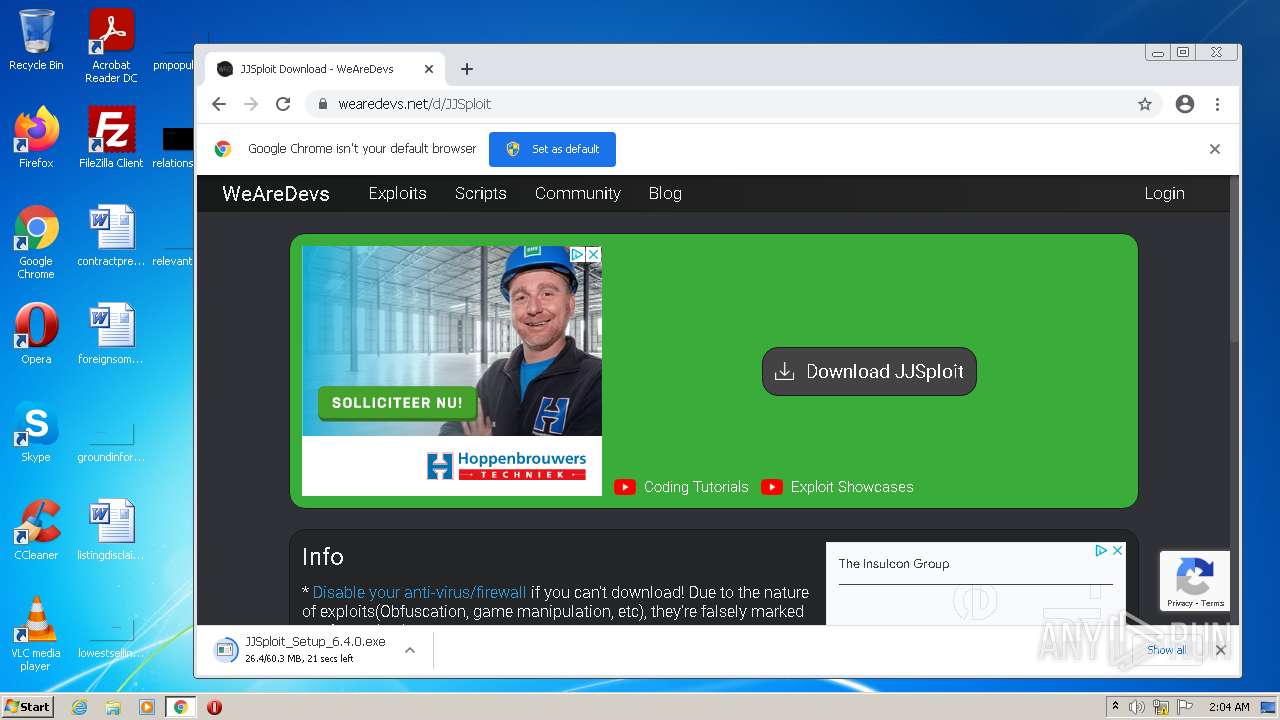
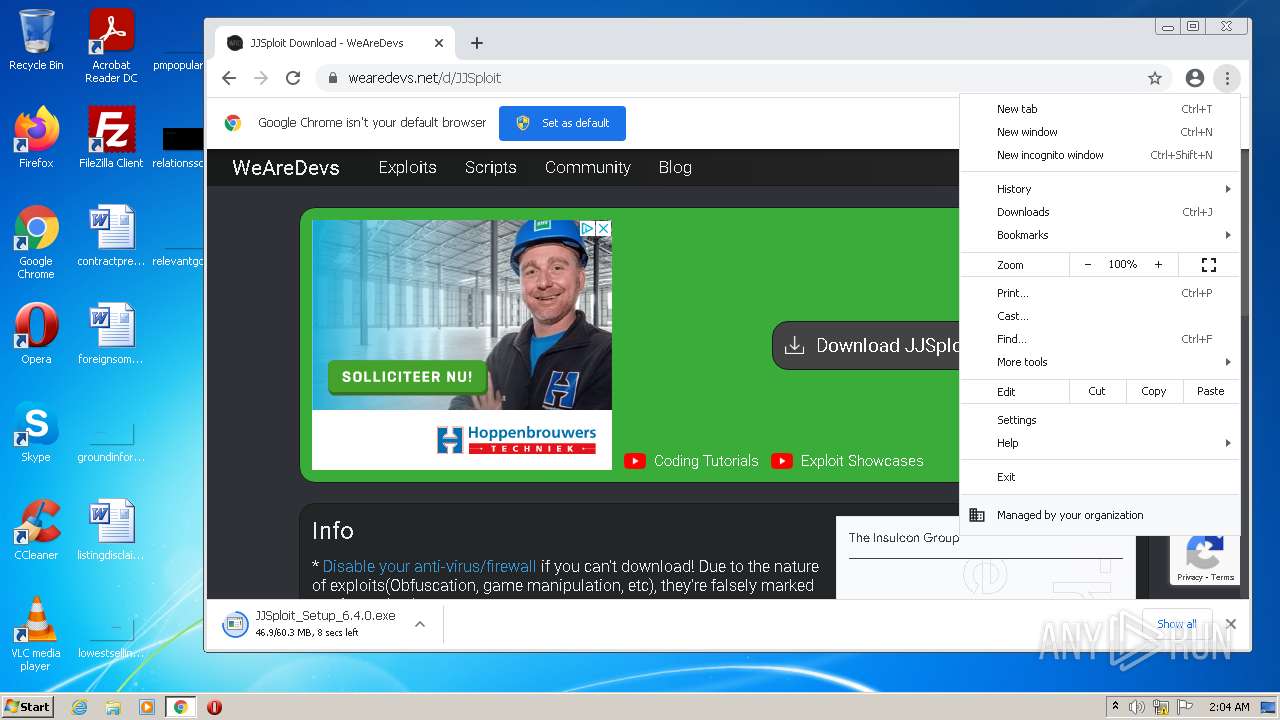
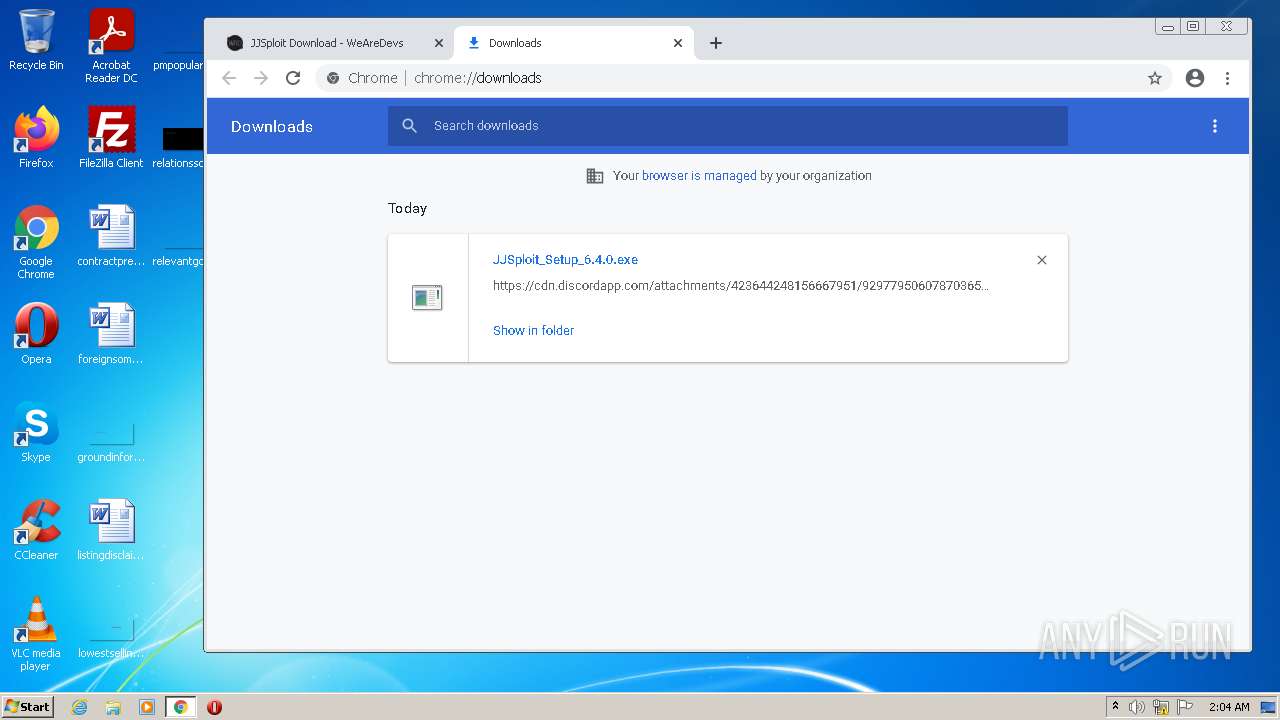
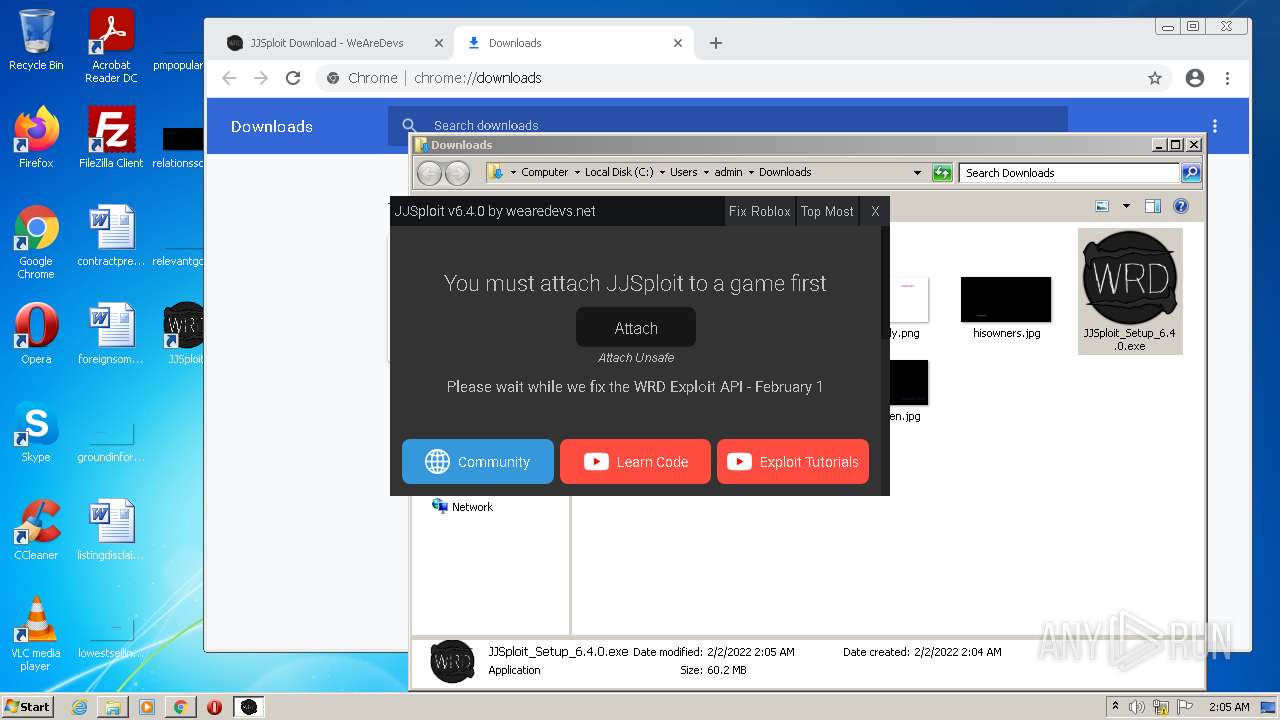
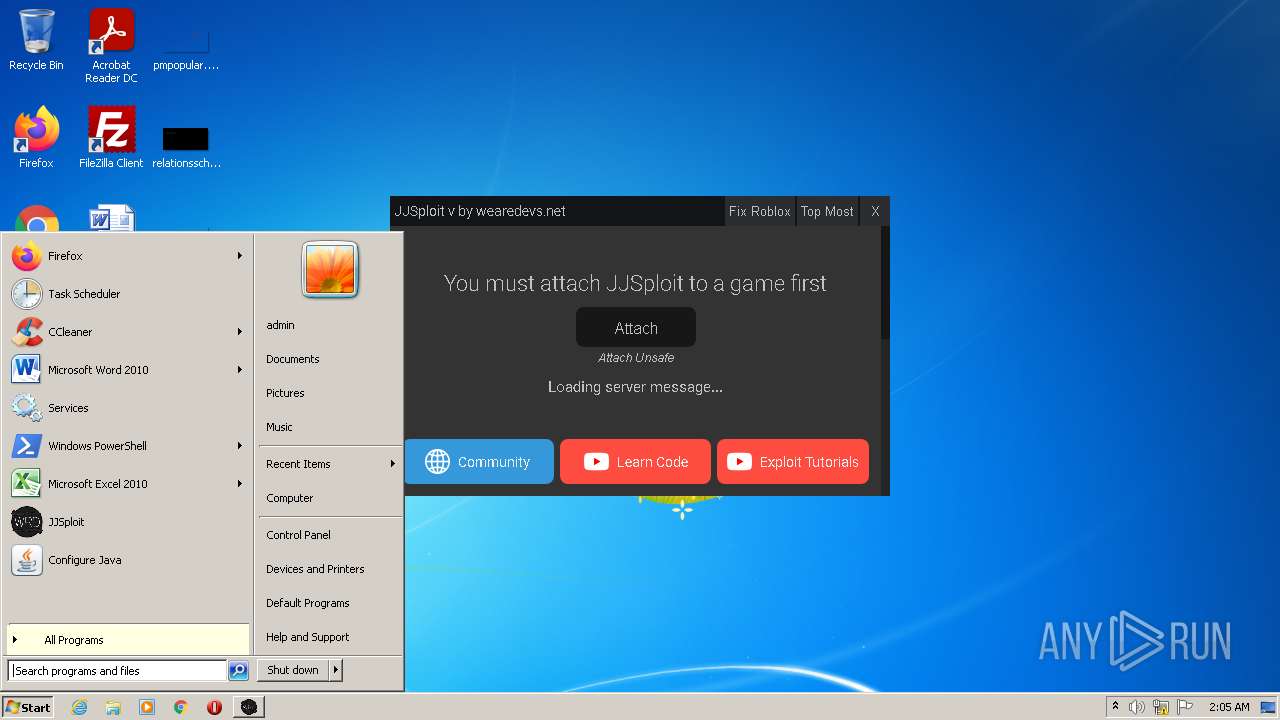
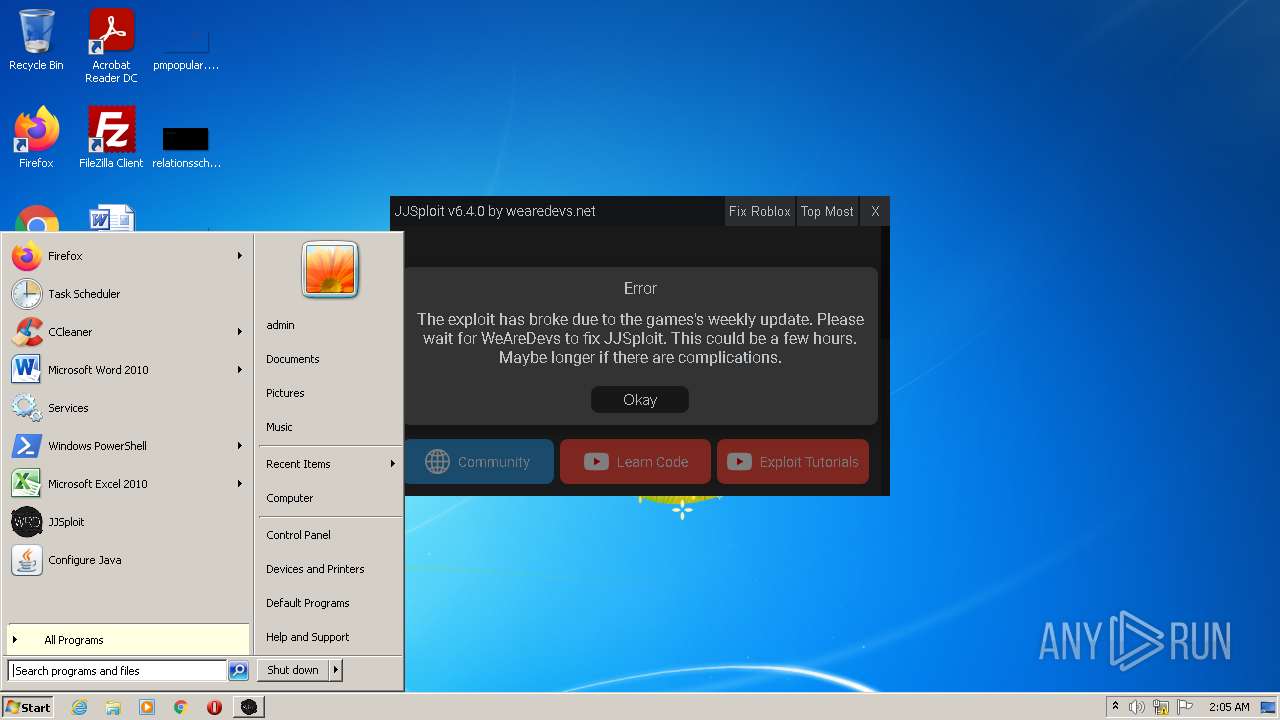
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/f2cb0bf9-1b74-475a-912f-1b4801837088 |
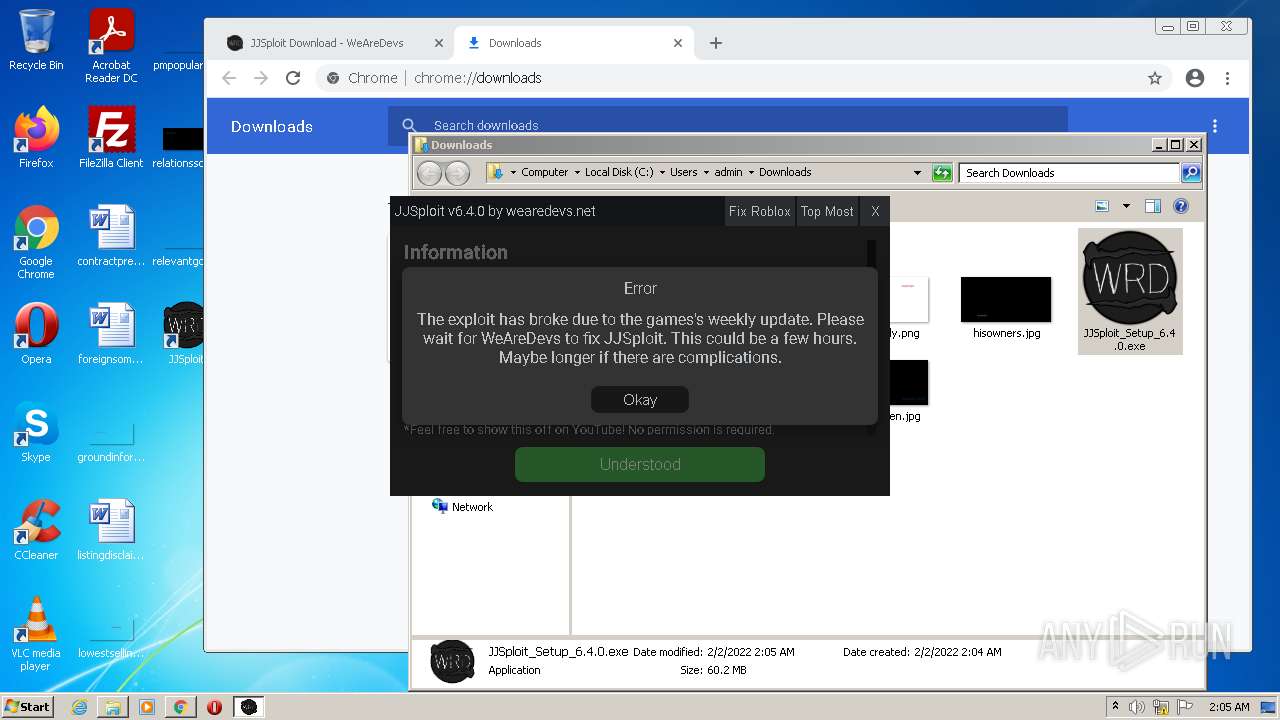
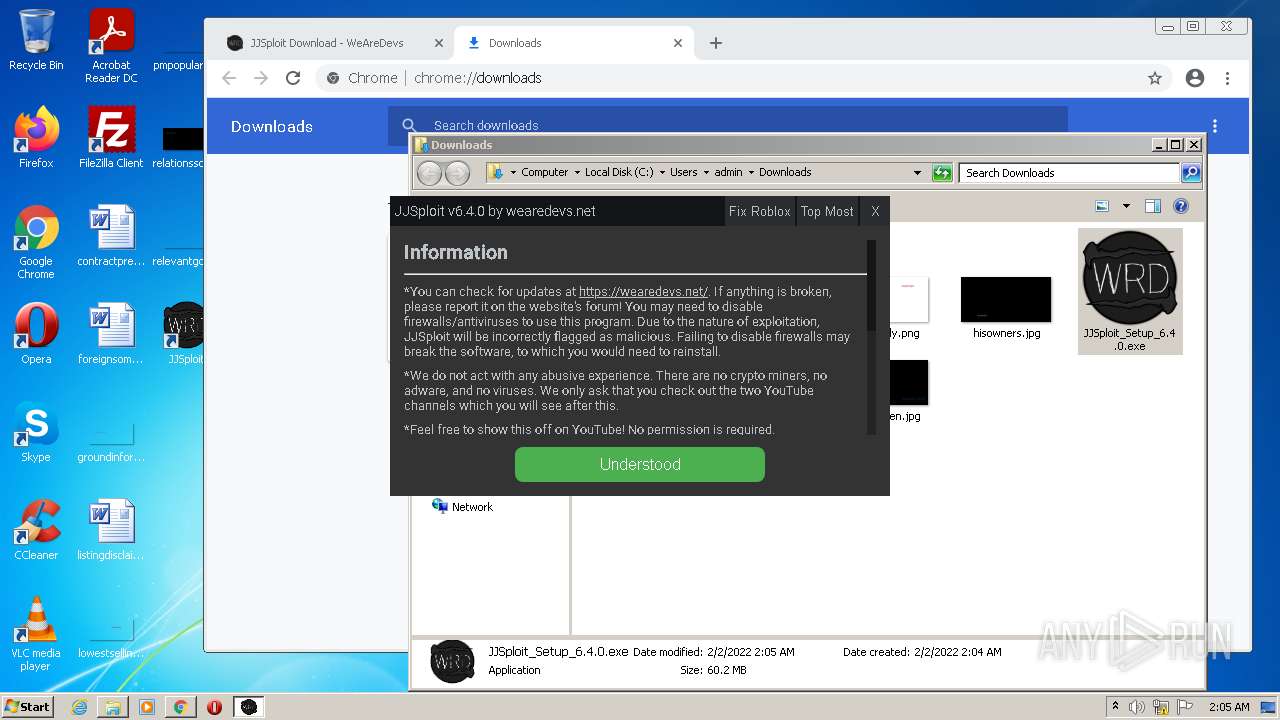
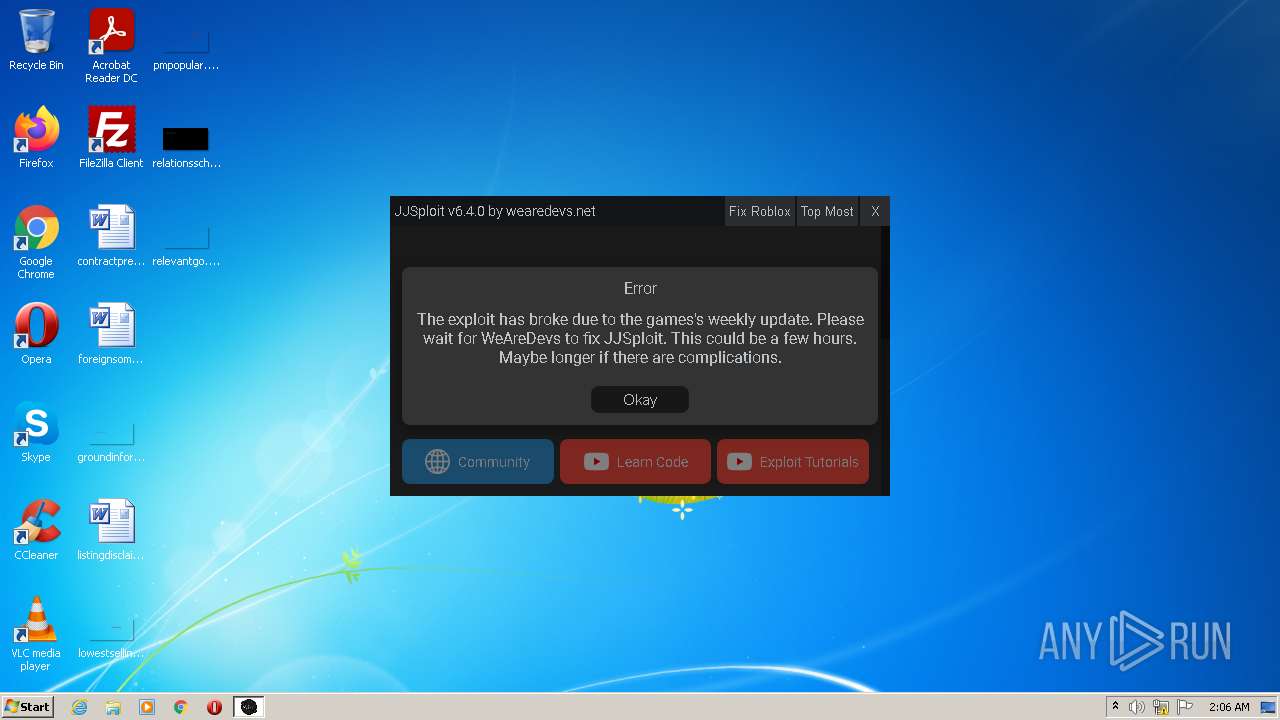
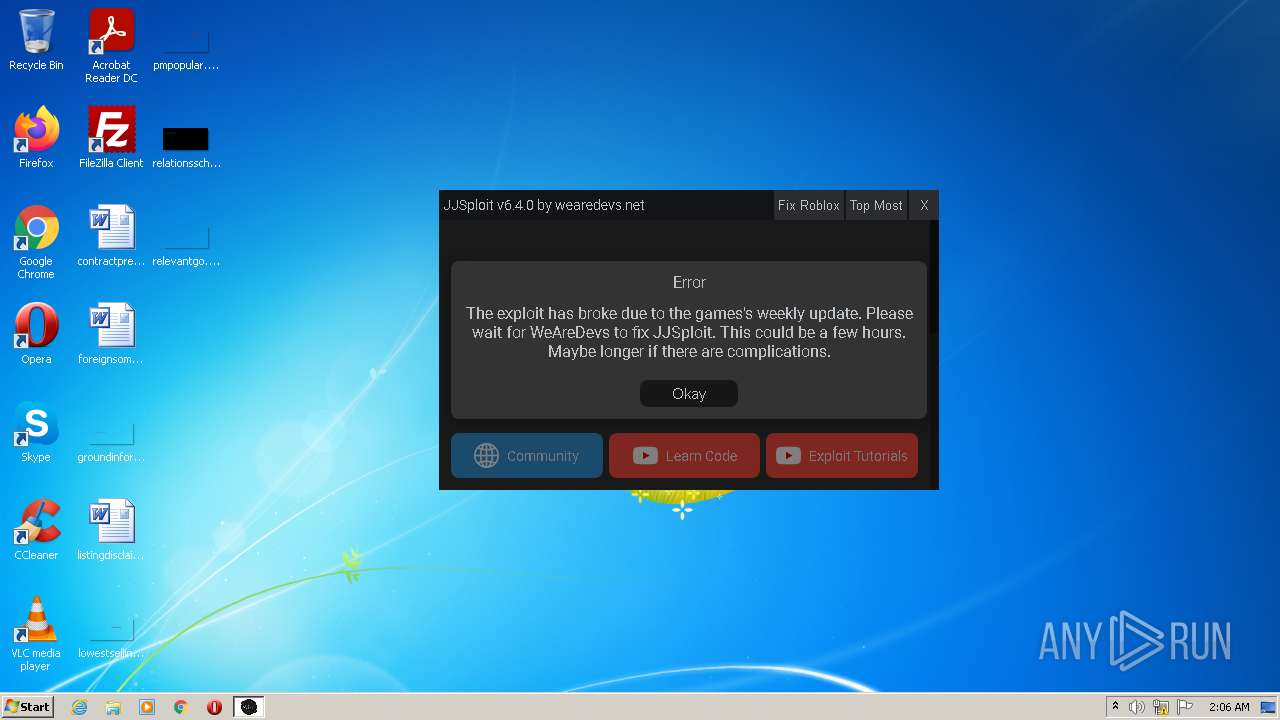
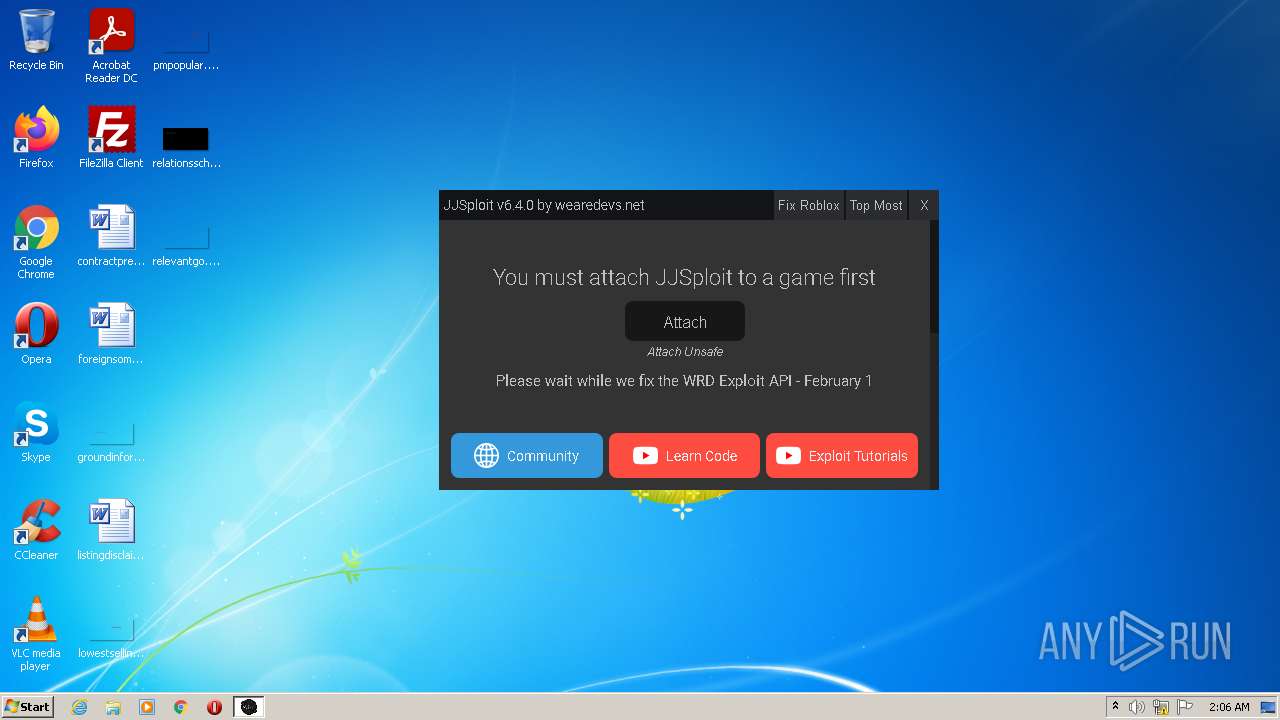
| Verdict: | Malicious activity |
| Analysis date: | February 02, 2022, 02:02:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
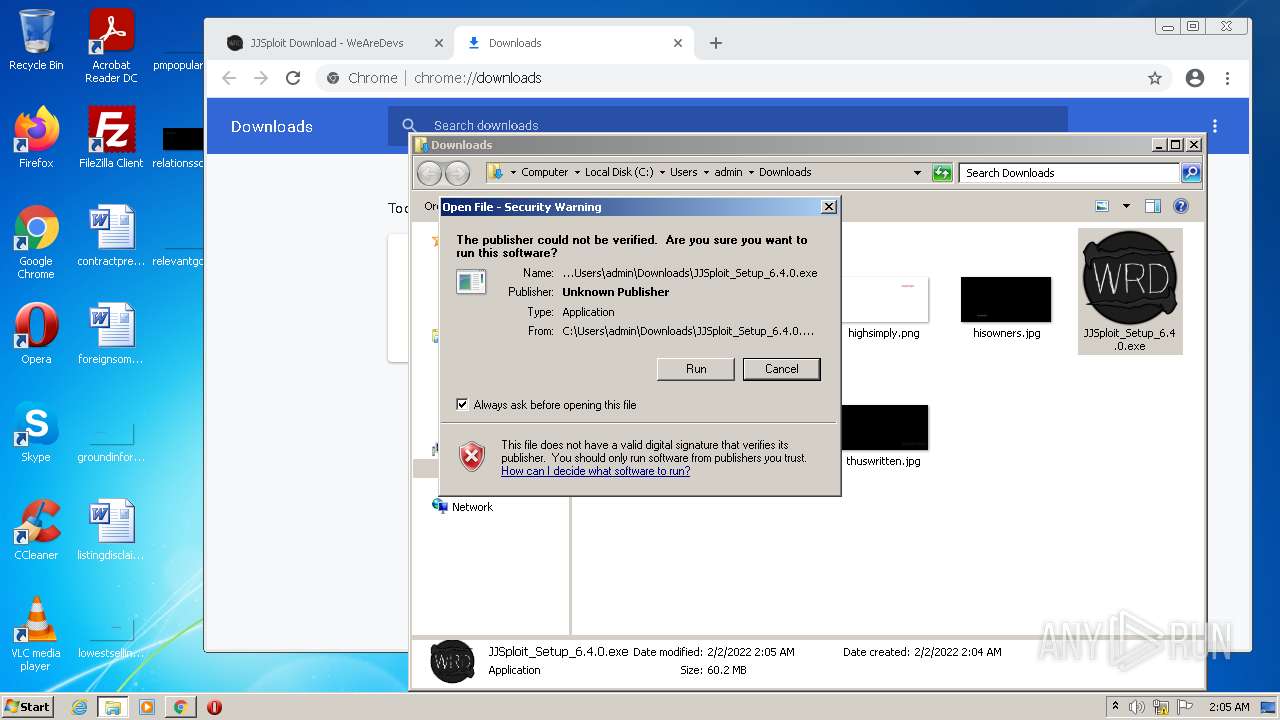
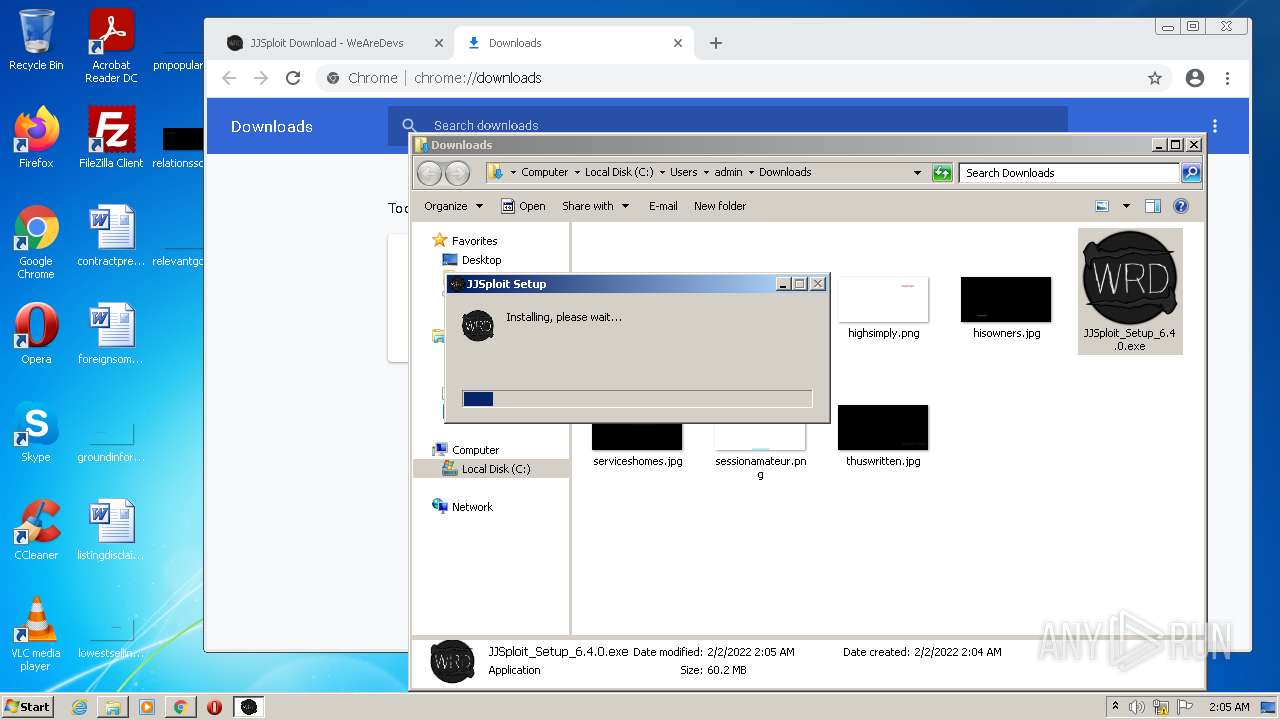
MALICIOUS
Application was dropped or rewritten from another process
- JJSploit_Setup_6.4.0.exe (PID: 4024)
Drops executable file immediately after starts
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3640)
Loads dropped or rewritten executable
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3200)
- JJSploit.exe (PID: 2400)
- JJSploit.exe (PID: 2748)
- JJSploit.exe (PID: 3464)
- JJSploit.exe (PID: 3640)
- JJSploit.exe (PID: 2988)
- JJSploit.exe (PID: 2572)
- JJSploit.exe (PID: 1288)
- JJSploit.exe (PID: 3868)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 656)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3208)
Executable content was dropped or overwritten
- chrome.exe (PID: 3924)
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3640)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3924)
Drops a file that was compiled in debug mode
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3640)
Reads the computer name
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 2400)
- JJSploit.exe (PID: 3200)
- JJSploit.exe (PID: 3464)
- JJSploit.exe (PID: 3640)
- JJSploit.exe (PID: 1288)
- JJSploit.exe (PID: 2572)
- JJSploit.exe (PID: 3868)
Drops a file with a compile date too recent
- JJSploit_Setup_6.4.0.exe (PID: 4024)
Checks supported languages
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3200)
- JJSploit.exe (PID: 2748)
- JJSploit.exe (PID: 2400)
- JJSploit.exe (PID: 3464)
- JJSploit.exe (PID: 3640)
- JJSploit.exe (PID: 2572)
- JJSploit.exe (PID: 1288)
- JJSploit.exe (PID: 2988)
- JJSploit.exe (PID: 3868)
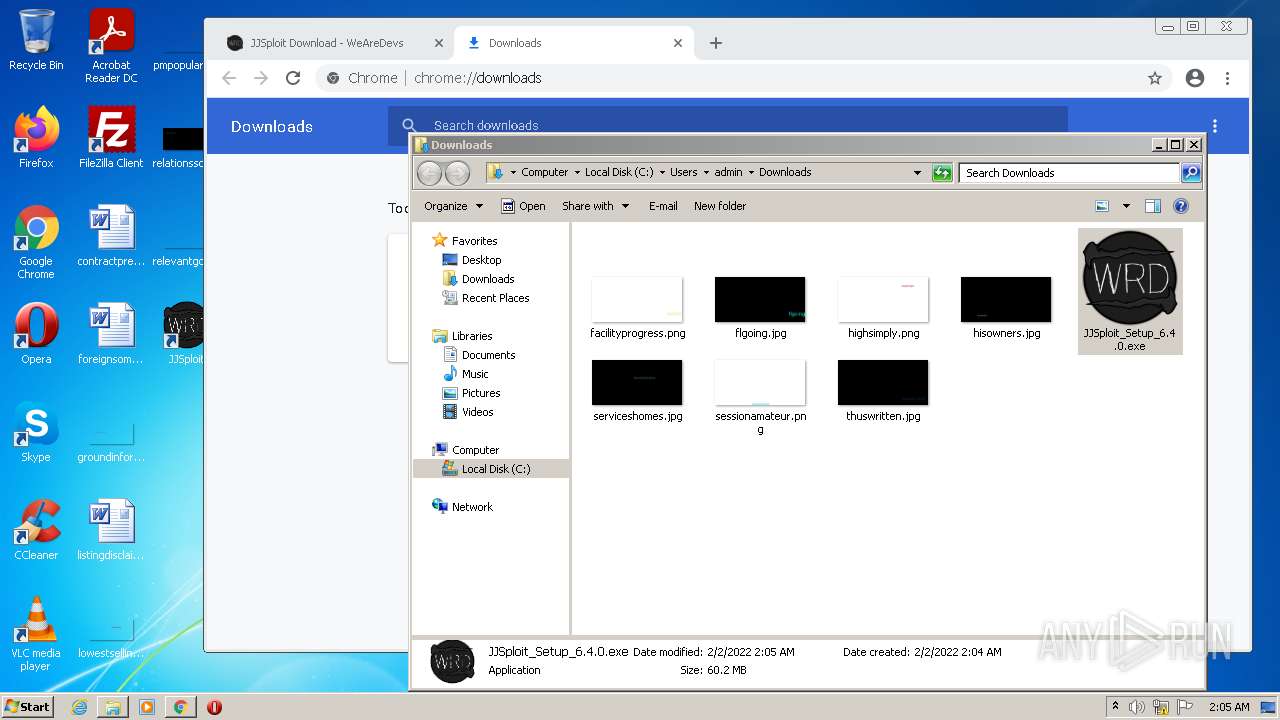
Creates a software uninstall entry
- JJSploit_Setup_6.4.0.exe (PID: 4024)
Creates files in the user directory
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 2400)
- JJSploit.exe (PID: 3640)
Application launched itself
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3640)
Starts Internet Explorer
- JJSploit.exe (PID: 3700)
INFO
Checks supported languages
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 656)
- chrome.exe (PID: 444)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3568)
- chrome.exe (PID: 1204)
- chrome.exe (PID: 2380)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2008)
- chrome.exe (PID: 1996)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 684)
- chrome.exe (PID: 1636)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 1392)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 508)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2240)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 3676)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 548)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 3724)
- chrome.exe (PID: 2848)
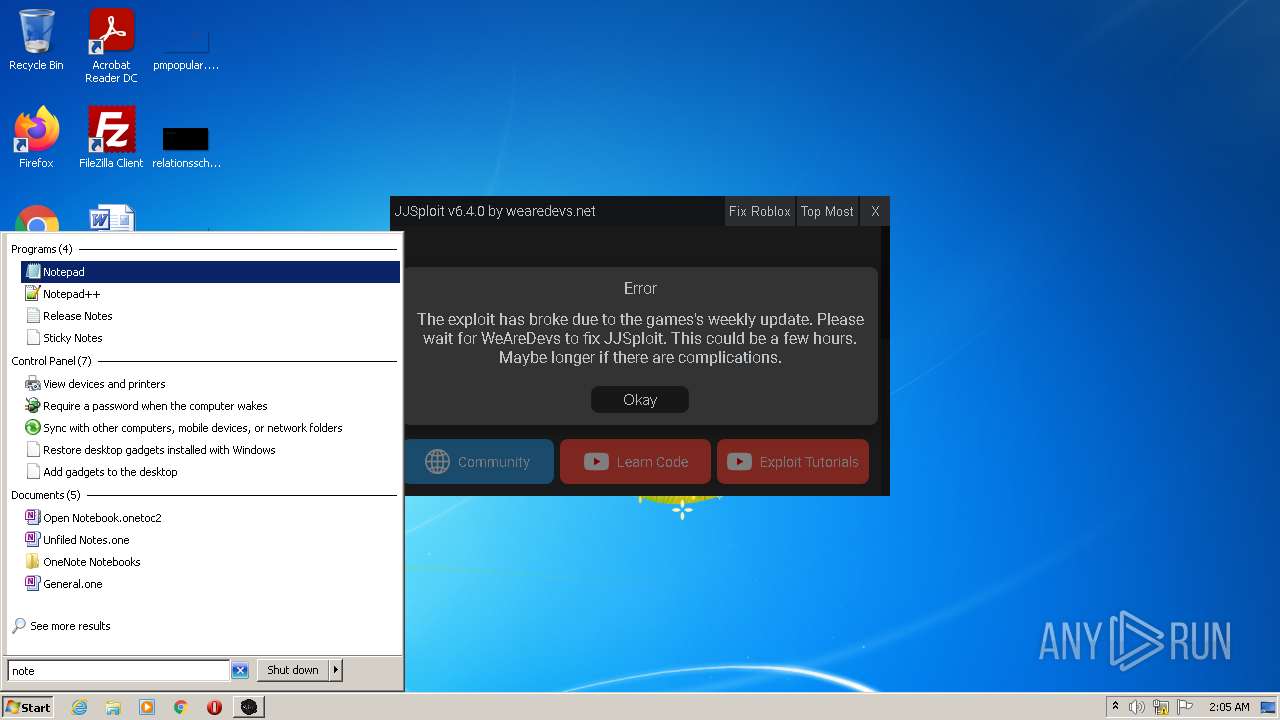
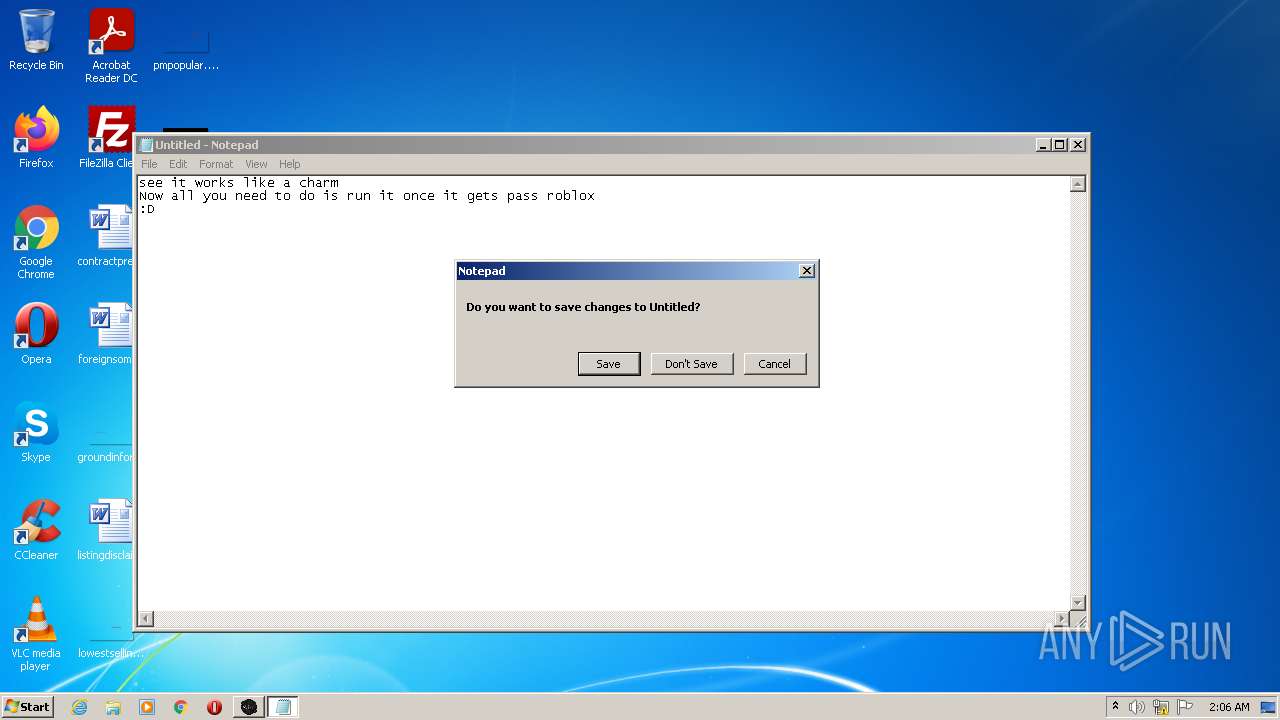
- notepad.exe (PID: 2456)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 2220)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 3732)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 2272)
Application launched itself
- iexplore.exe (PID: 1112)
- chrome.exe (PID: 3924)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 1808)
Reads the computer name
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 656)
- chrome.exe (PID: 2612)
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3636)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 2432)
- chrome.exe (PID: 3196)
- chrome.exe (PID: 3676)
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 548)
- chrome.exe (PID: 636)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 2272)
Changes internet zones settings
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 3072)
Reads settings of System Certificates
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 656)
- chrome.exe (PID: 2608)
- JJSploit.exe (PID: 2400)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
- chrome.exe (PID: 1808)
Checks Windows Trust Settings
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 656)
- chrome.exe (PID: 3924)
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
Reads internet explorer settings
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 656)
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 3112)
Creates files in the user directory
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 656)
- iexplore.exe (PID: 3112)
- iexplore.exe (PID: 3208)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
Changes settings of System certificates
- iexplore.exe (PID: 1112)
- iexplore.exe (PID: 3072)
- iexplore.exe (PID: 2948)
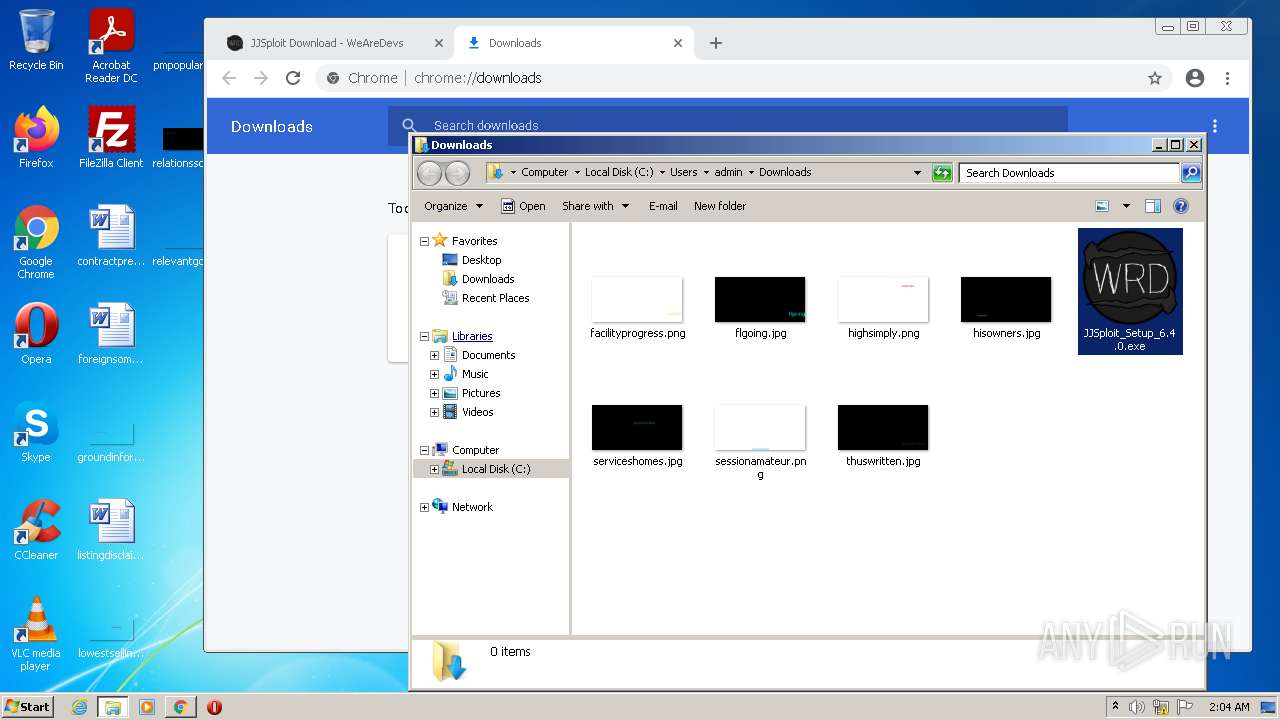
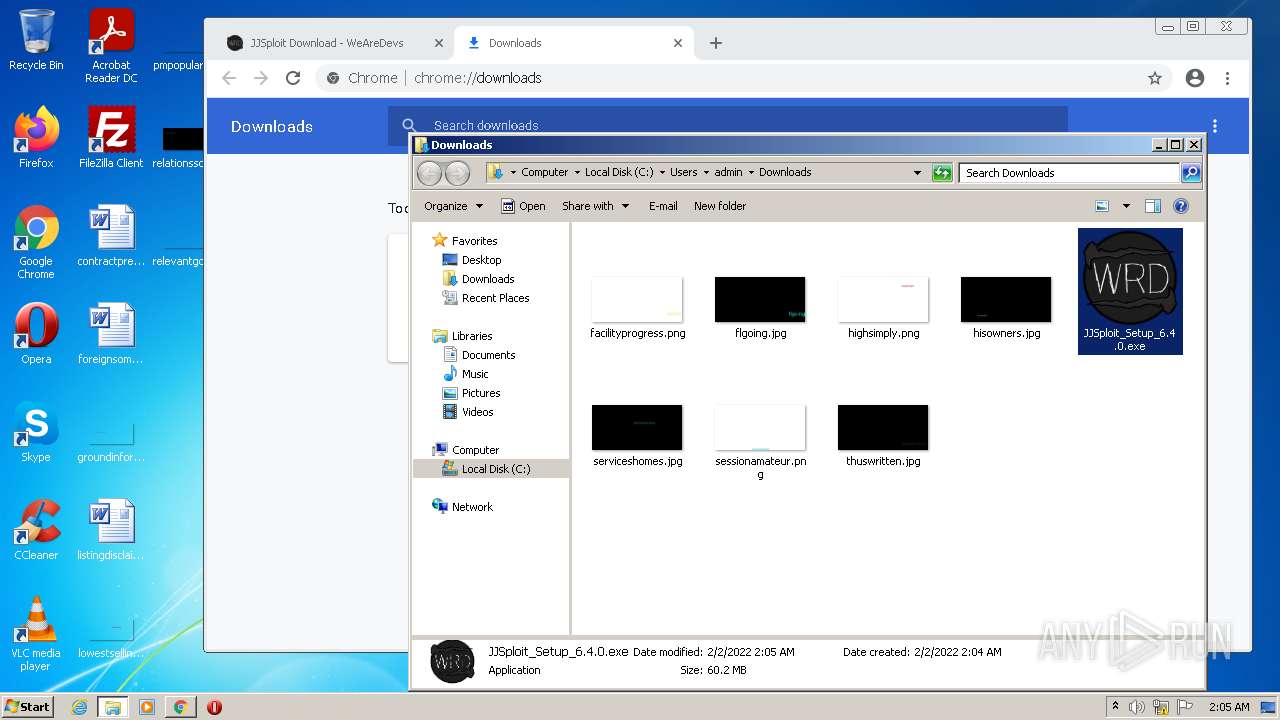
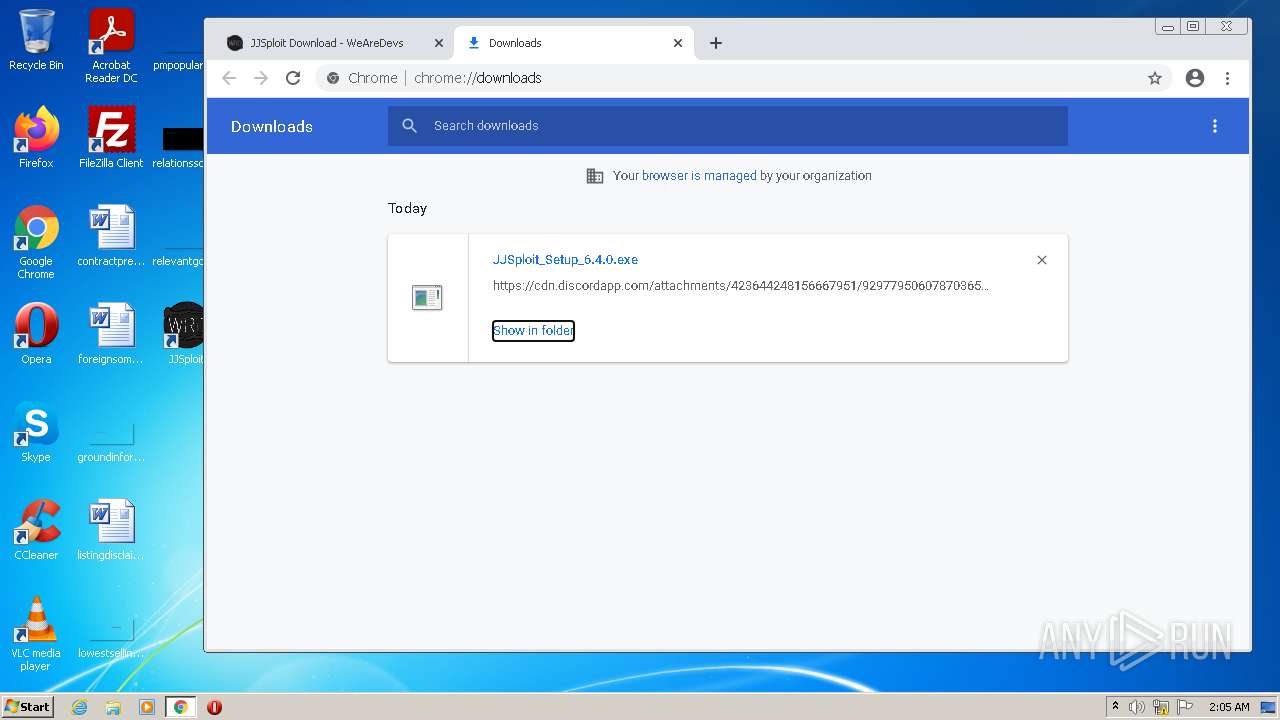
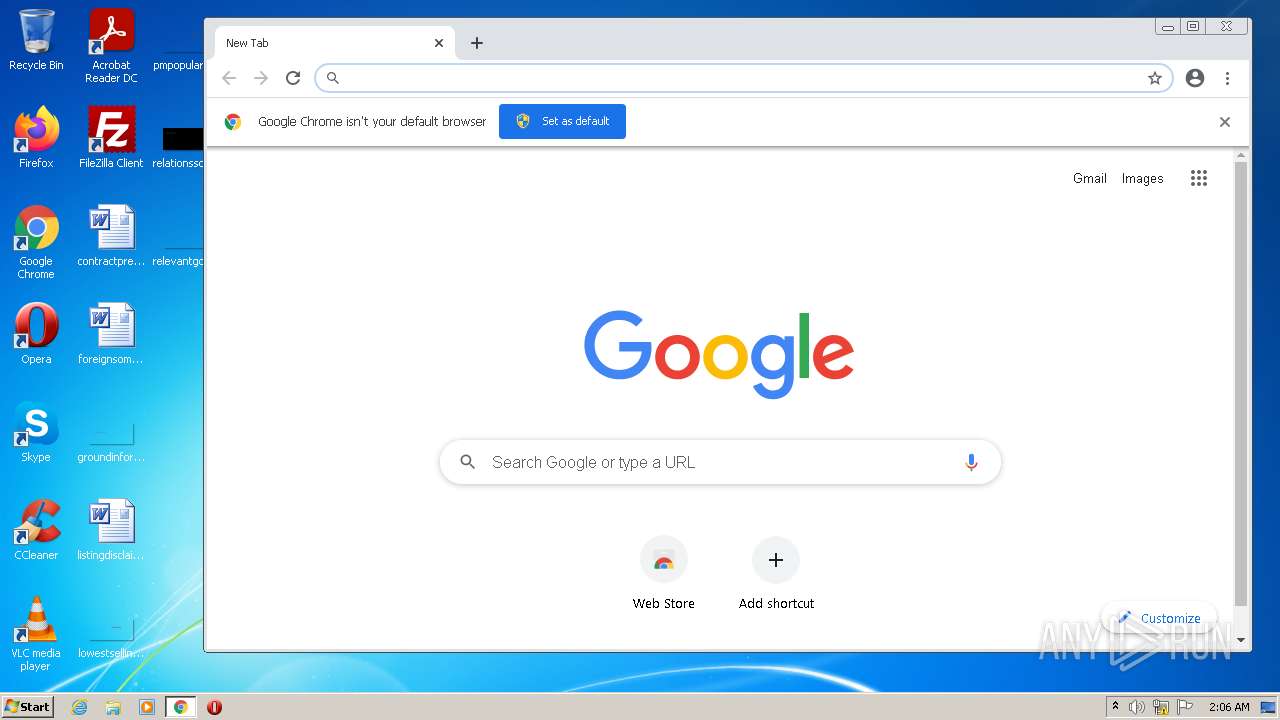
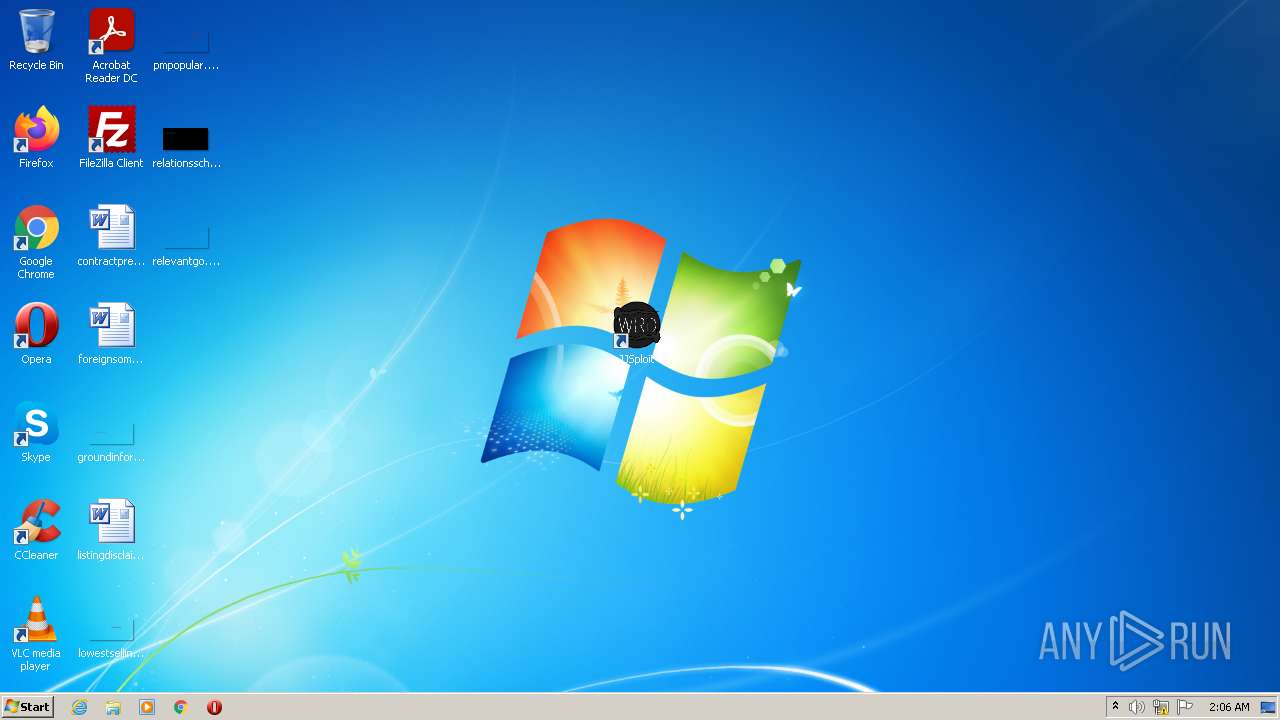
Manual execution by user
- chrome.exe (PID: 3924)
- JJSploit_Setup_6.4.0.exe (PID: 4024)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 3640)
- notepad.exe (PID: 2456)
- chrome.exe (PID: 1808)
Reads the hosts file
- chrome.exe (PID: 3924)
- chrome.exe (PID: 2608)
- JJSploit.exe (PID: 3700)
- JJSploit.exe (PID: 2400)
- JJSploit.exe (PID: 3640)
- JJSploit.exe (PID: 1288)
- chrome.exe (PID: 1808)
- chrome.exe (PID: 636)
Reads the date of Windows installation
- iexplore.exe (PID: 1112)
- chrome.exe (PID: 3196)
- iexplore.exe (PID: 2948)
- iexplore.exe (PID: 3072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
61
Malicious processes
5
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e0fd988,0x6e0fd998,0x6e0fd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15999940343240205197,3592174272358239288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,15999940343240205197,3592174272358239288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,1741438880552921840,183569682629168379,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1308 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1112 CREDAT:2299168 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15999940343240205197,3592174272358239288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1112 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://wearedevs.net/d/JJSploit" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1036,15999940343240205197,3592174272358239288,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2812 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1288 | "C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe" --type=utility --field-trial-handle=1084,2216416973502218957,15679994018982196452,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1368 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\jjsploit\JJSploit.exe | — | JJSploit.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJSploit Exit code: 0 Version: 6.4.0 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15999940343240205197,3592174272358239288,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
89 652
Read events
88 836
Write events
794
Delete events
22
Modification events
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939096 | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 76574773 | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939097 | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1112) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
23
Suspicious files
262
Text files
495
Unknown types
164
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:AF05611D43FE9B57483EC17845C2006E | SHA256:5AE2355623E01380975CA601C9CDC92FC203FD0AD3F4686F2A596CC1E32ED4E5 | |||
| 1112 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:C57252F495CBFD092622D845CFAE99B8 | SHA256:DC4089A71B95757396D832E2321AB06CBCF5ED7CB9365E2D9B0612B6AFA873EF | |||
| 1112 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:F10142B5AB723DA3A8A6B890EC3E6A5B | SHA256:21DC91BFAAF8B4AC3602E93076C850001B59720658B74943240CCA64B24485B0 | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:8C6FA155F8560E16880AAF9E1FD85549 | SHA256:3C0D76DC2770A8F203EDE7DF8CFA37E7DDD1A4E9FE4FA5ED314AE06DC866D4CC | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\JJSploit[1].htm | html | |
MD5:FA16171A9F4DE07CDE6759344D7612B3 | SHA256:9EB3B5E25B83417B229E1EF4E19960B963ABAD72C70883B1E3B5D2D4A1C0806C | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:230FD3B06EAE3C6BEB59687CCAFC3AD3 | SHA256:7EC9206D646713CF76C2E34C856999D435D186855B6738B5442C8A0BB1C5AEFE | |||
| 1112 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\timestamp[1].js | text | |
MD5:A5AA8ED607F154E5CBC7E20C521E4E4F | SHA256:36D0E2CBBCB9BD4448AD61486982AB2AD0C5B84B61AF51E21F82BB993041E3CE | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\main[1].css | text | |
MD5:F9086767559A093F50CF1A9C2D9D9310 | SHA256:7D15C79CBA2E5B92FF3CAF8D7365CEA4BDE0D342909BDC8B6D1B3899136F788A | |||
| 3396 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\DYI6kXcOcxKbTp9LDOkriR11YHo[1].js | text | |
MD5:FF37F76F20C5DC8388CB54A55E38D3D3 | SHA256:6E339B3F7ADFB6CA5353AF08DA045F92B92B48346ECF14EAED02562A44A1EDCE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
233
DNS requests
105
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3396 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3396 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?15a5742b95a409ac | ZA | compressed | 4.70 Kb | whitelisted |
1112 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCrvyQ4GllugQoAAAABK4Az | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgBTRQd6qpTgoAAAABLgJY | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEFKxQHtEPcBCgAAAAErfHU%3D | US | der | 471 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCBOXNTLJE8wAoAAAABK34H | US | der | 472 b | whitelisted |
3396 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDgAde1VeKYIQoAAAABK4GI | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3396 | iexplore.exe | 142.250.185.162:443 | partner.googleadservices.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 172.217.23.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 172.67.71.2:443 | wearedevs.net | — | US | suspicious |
3396 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | Limelight Networks, Inc. | ZA | suspicious |
3396 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1112 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1112 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3396 | iexplore.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
3396 | iexplore.exe | 142.250.184.194:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
3396 | iexplore.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |