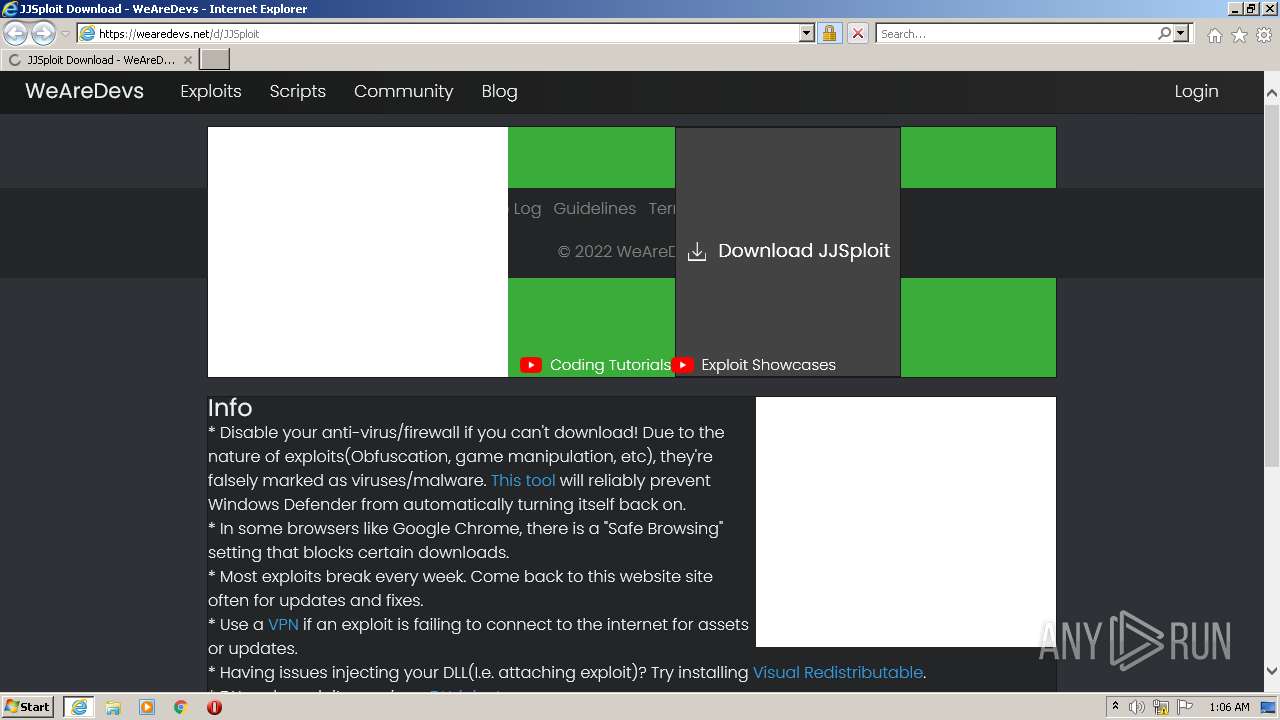
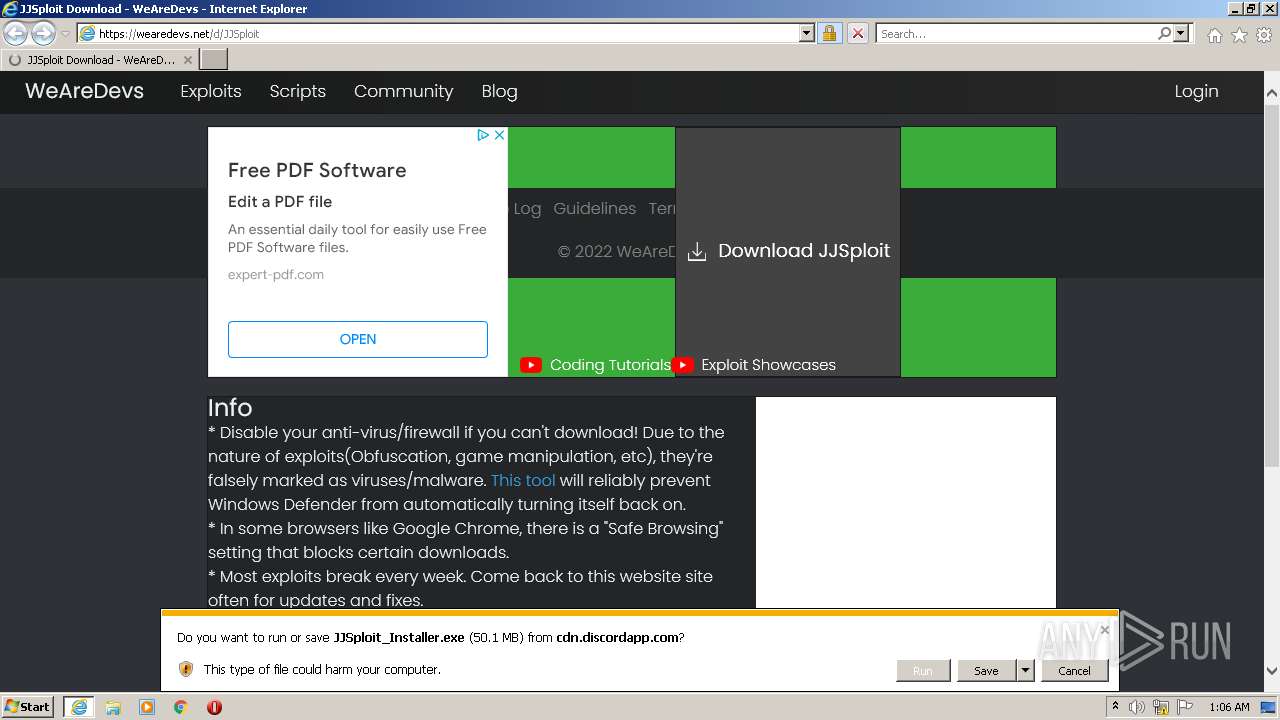
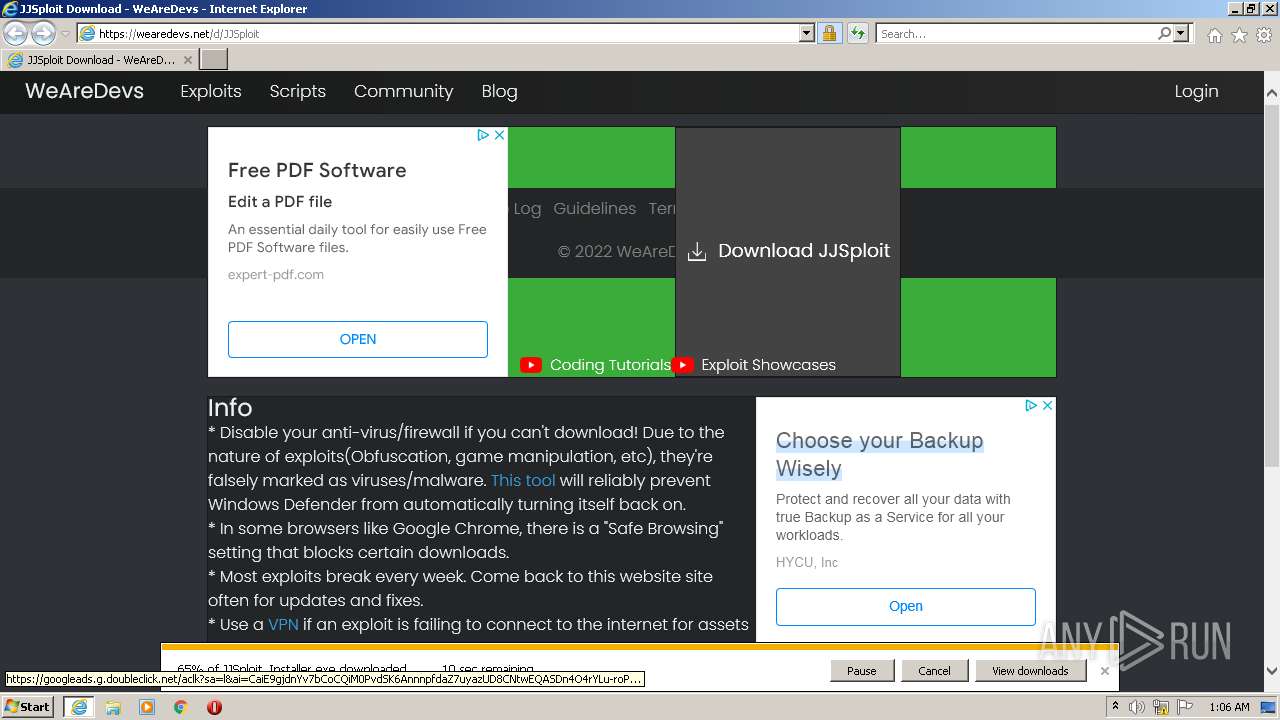
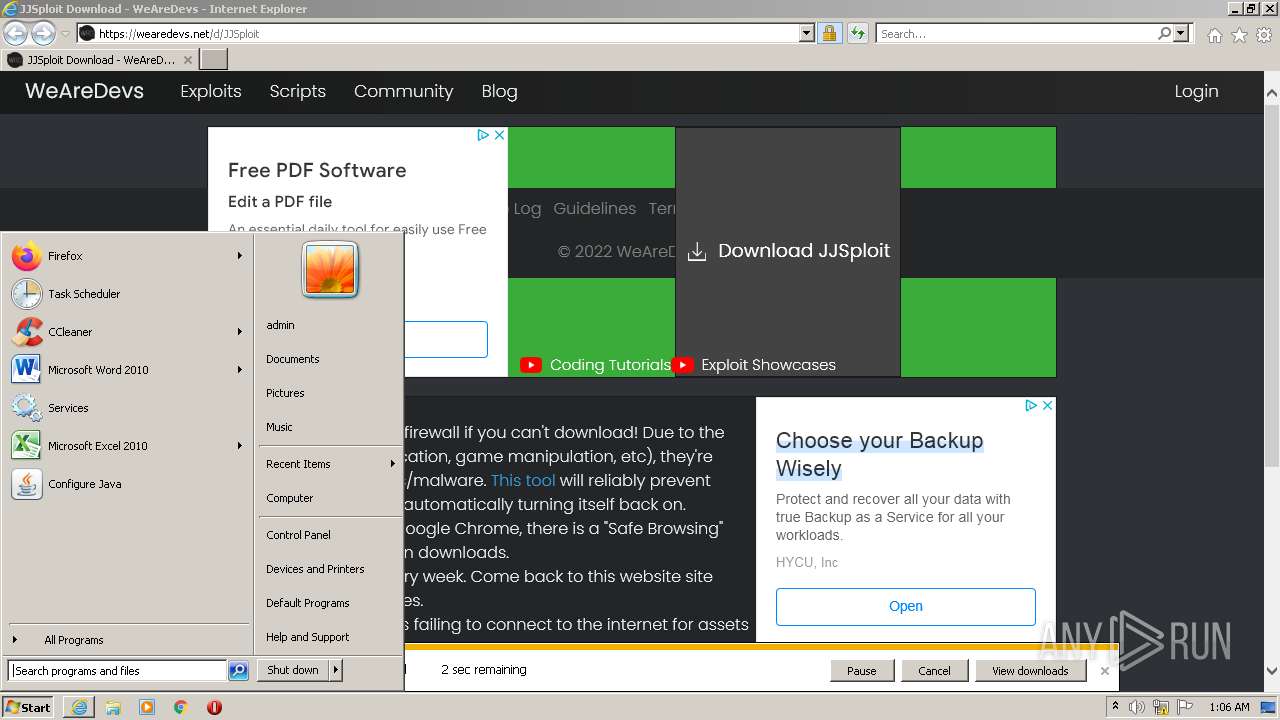
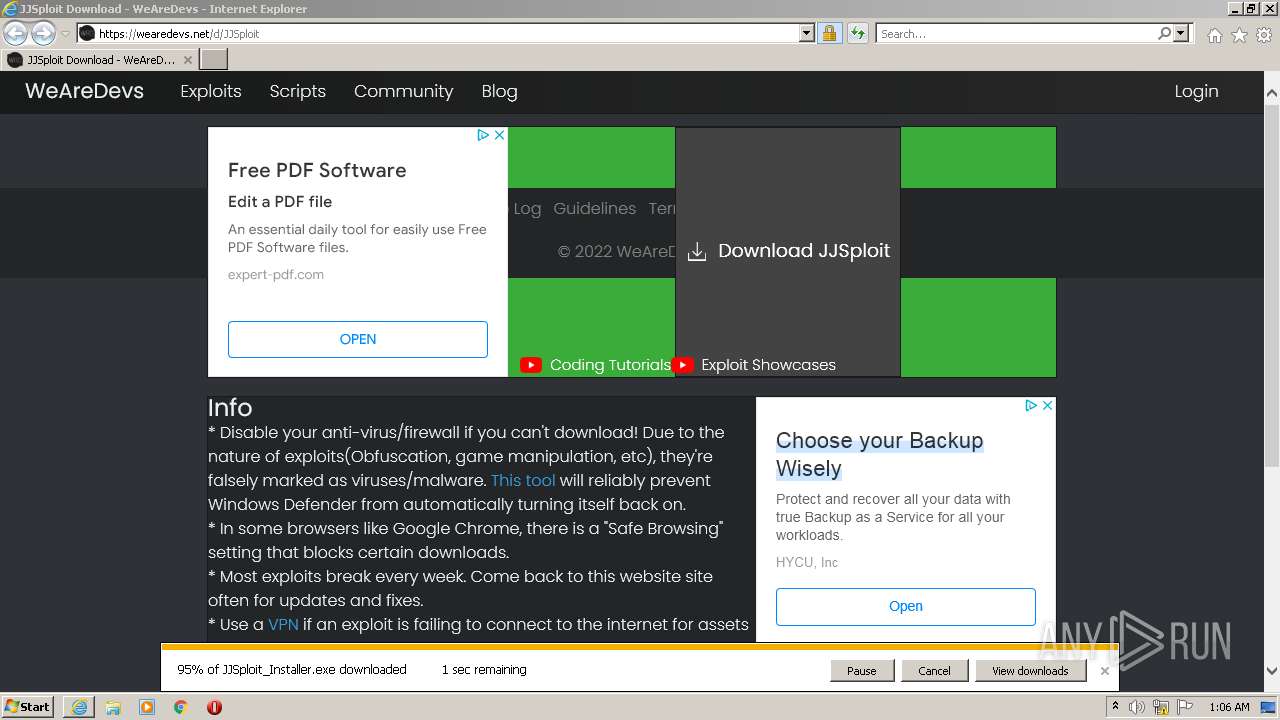
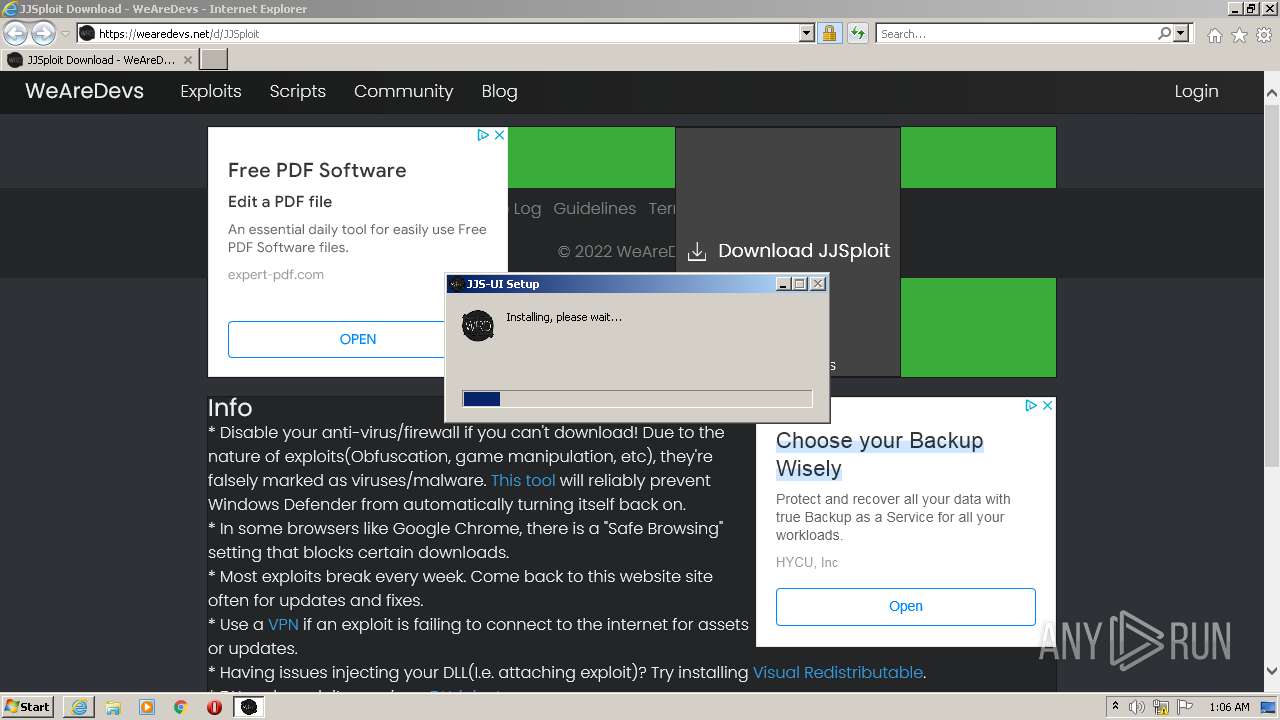
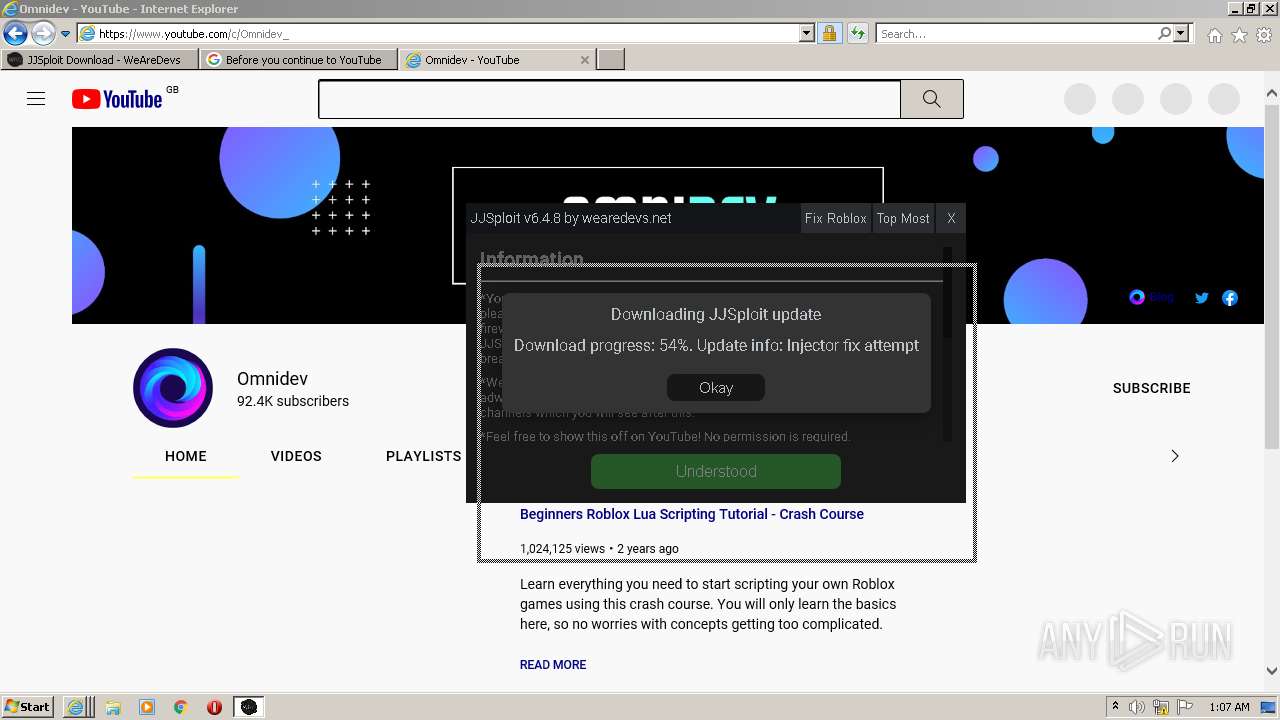
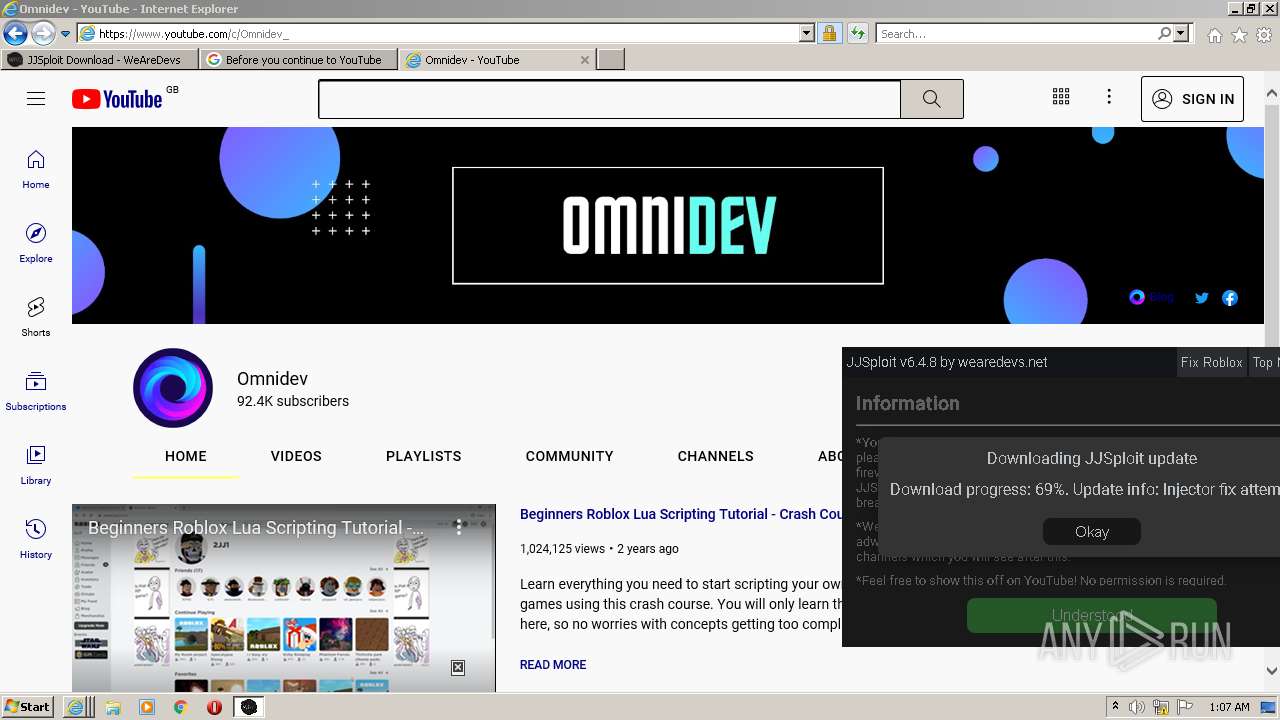
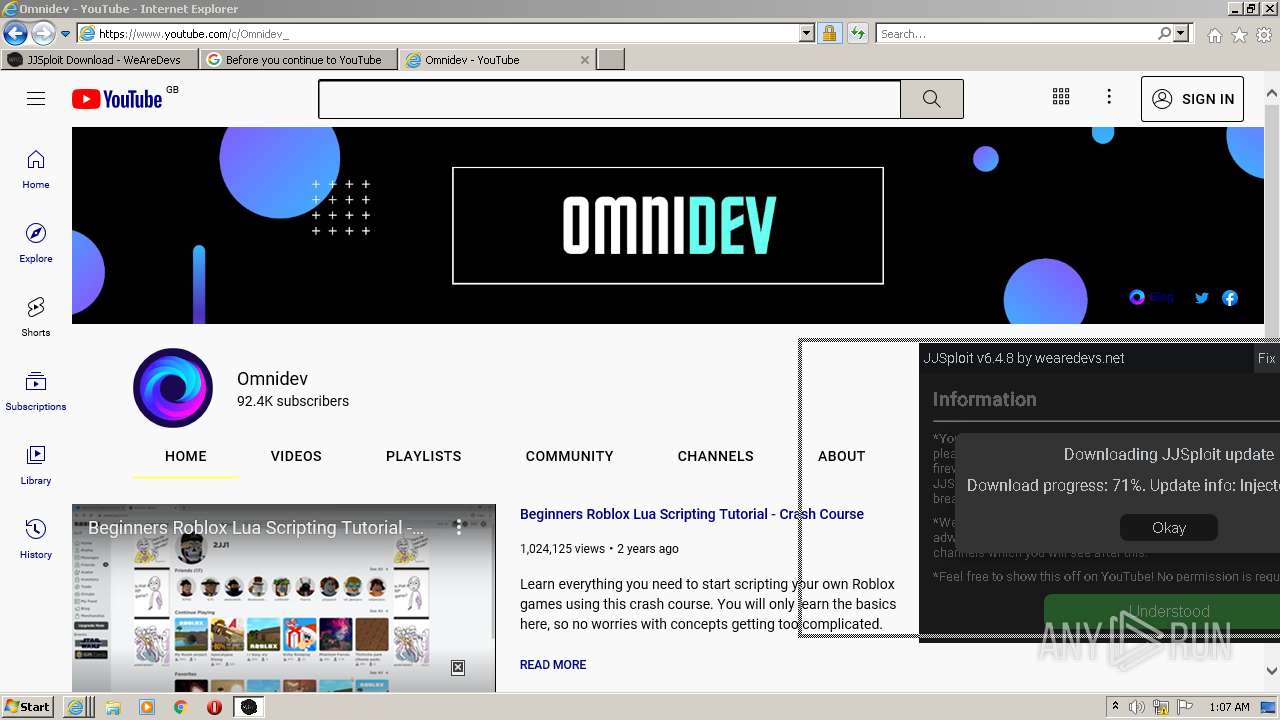
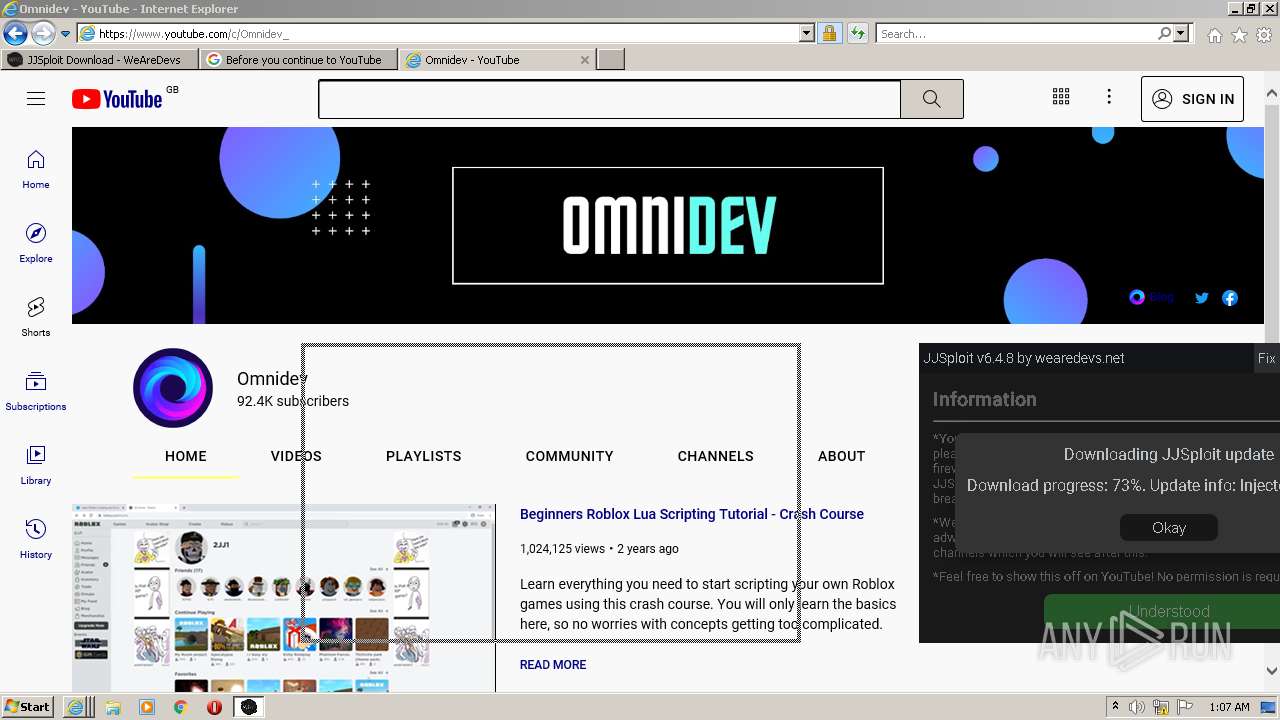
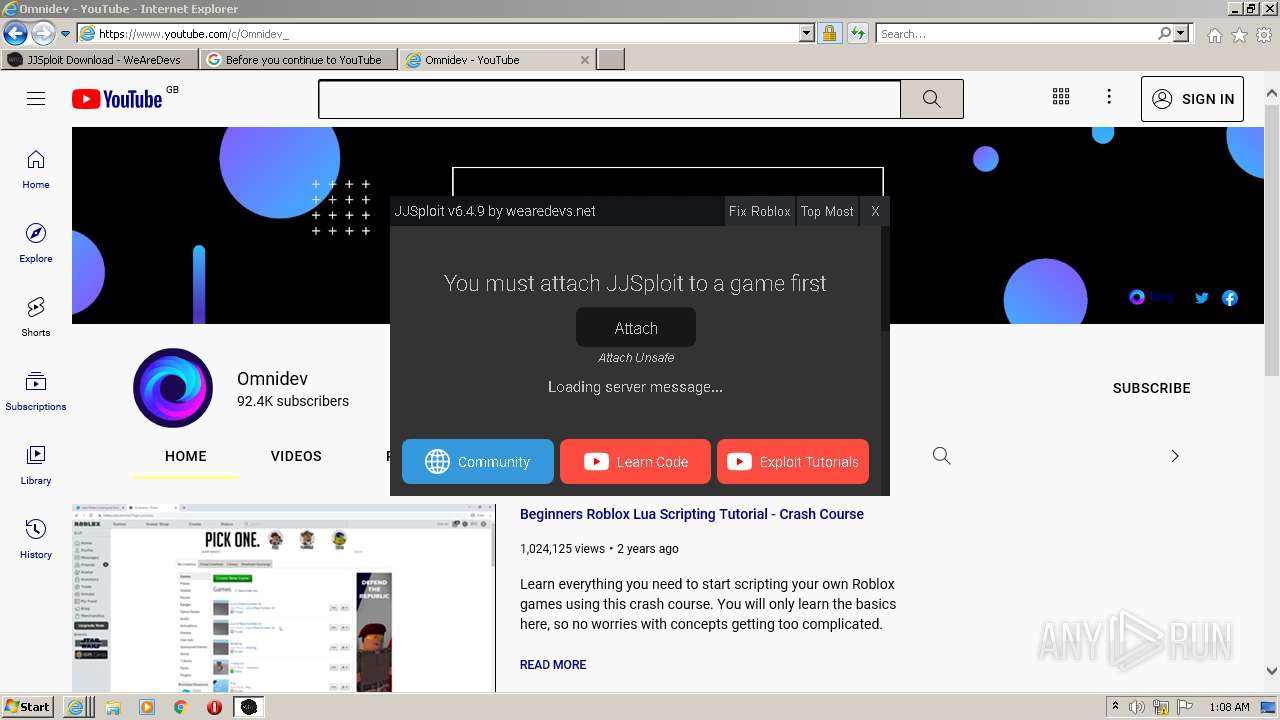
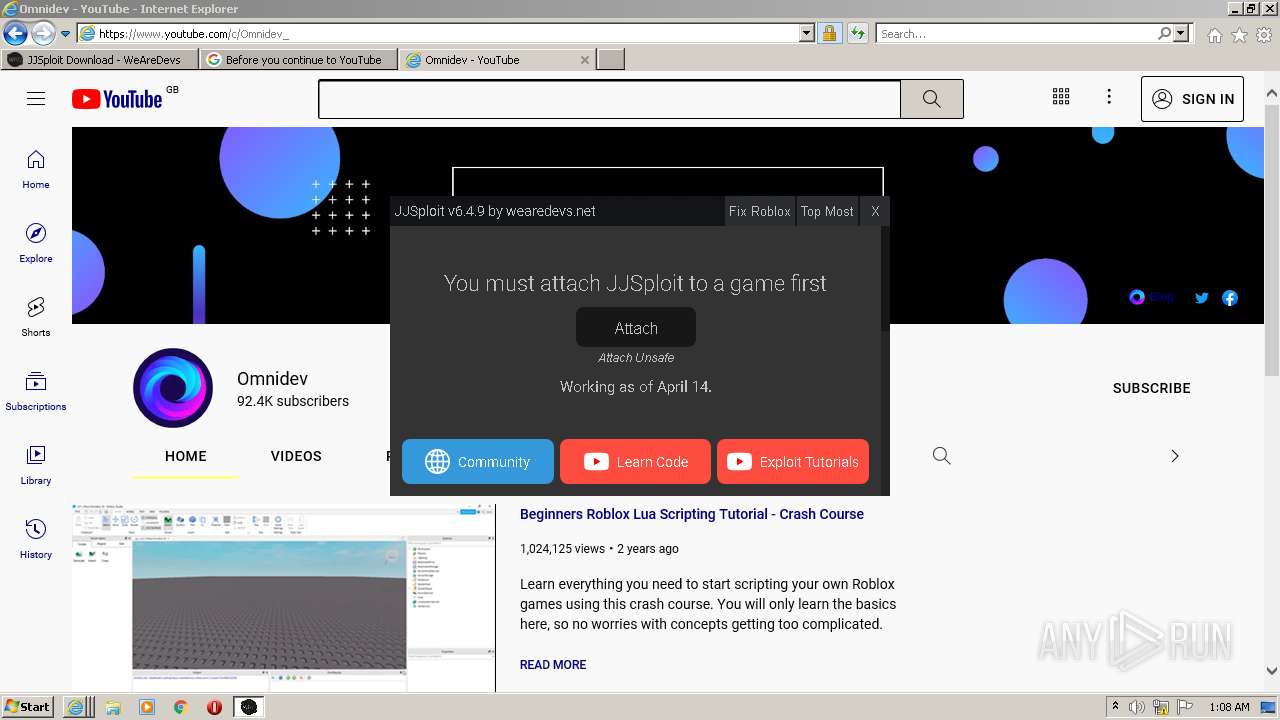
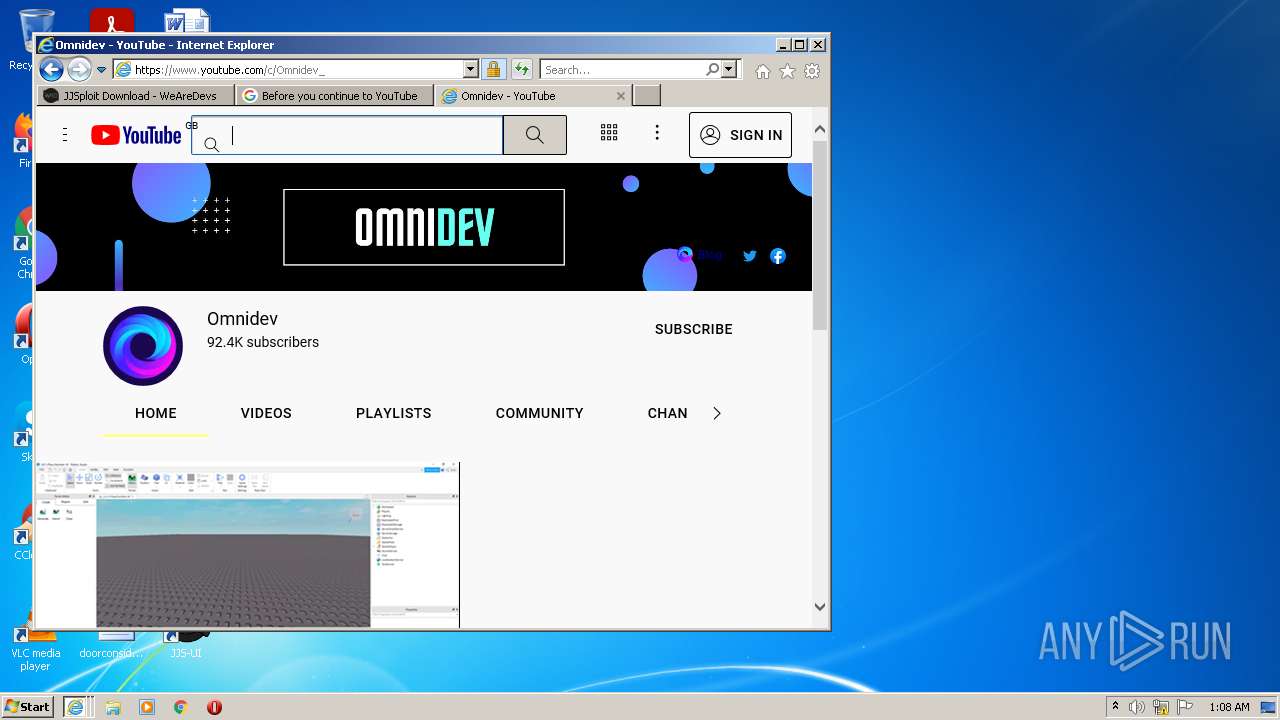
| URL: | https://wearedevs.net/d/JJSploit |
| Full analysis: | https://app.any.run/tasks/cb4070d8-3462-42a2-a777-e1c8cc68871e |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2022, 00:05:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | AF4F0F3F58AF746C6F1F8983436ACBD9 |
| SHA1: | 09E980C8D1D92C3DF8498BD3A725CB83F4314AAB |
| SHA256: | 484ABDB18866BC82426BE62FDF91D5C82FB9C951B25C22B00E1AA3EFC95E4B95 |
| SSDEEP: | 3:N8R/BApK83BQ:25BuBq |
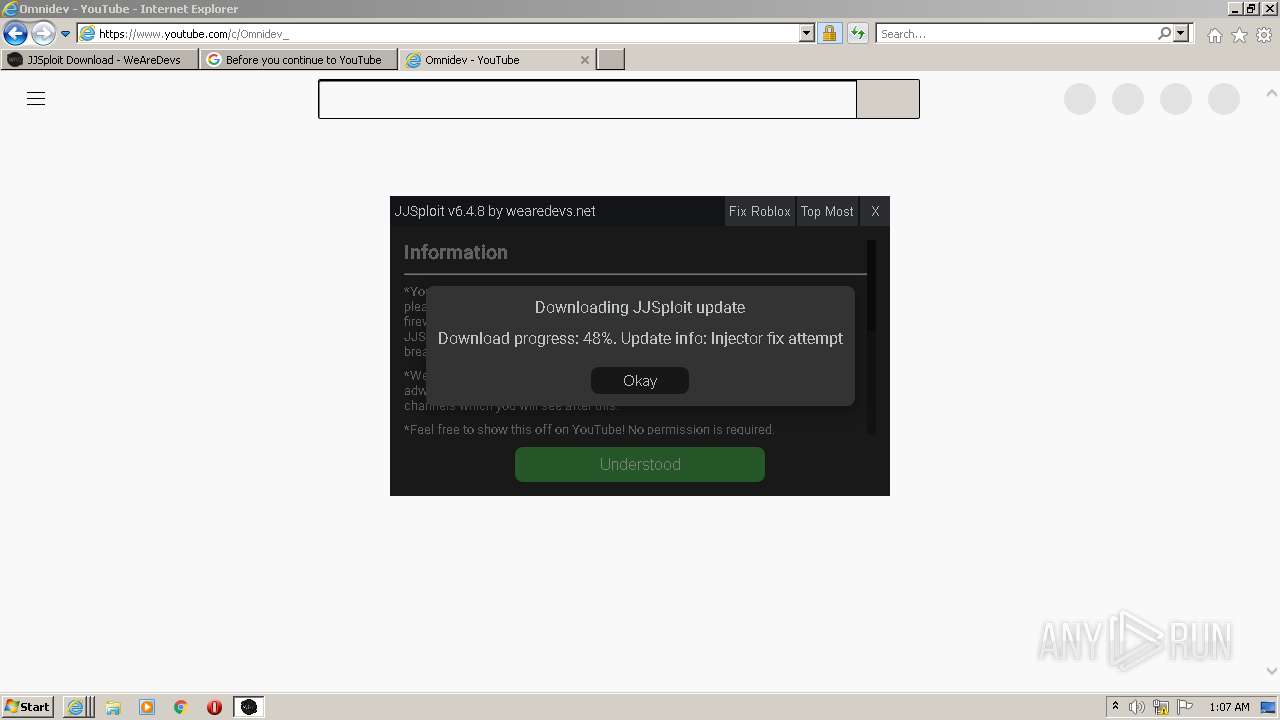
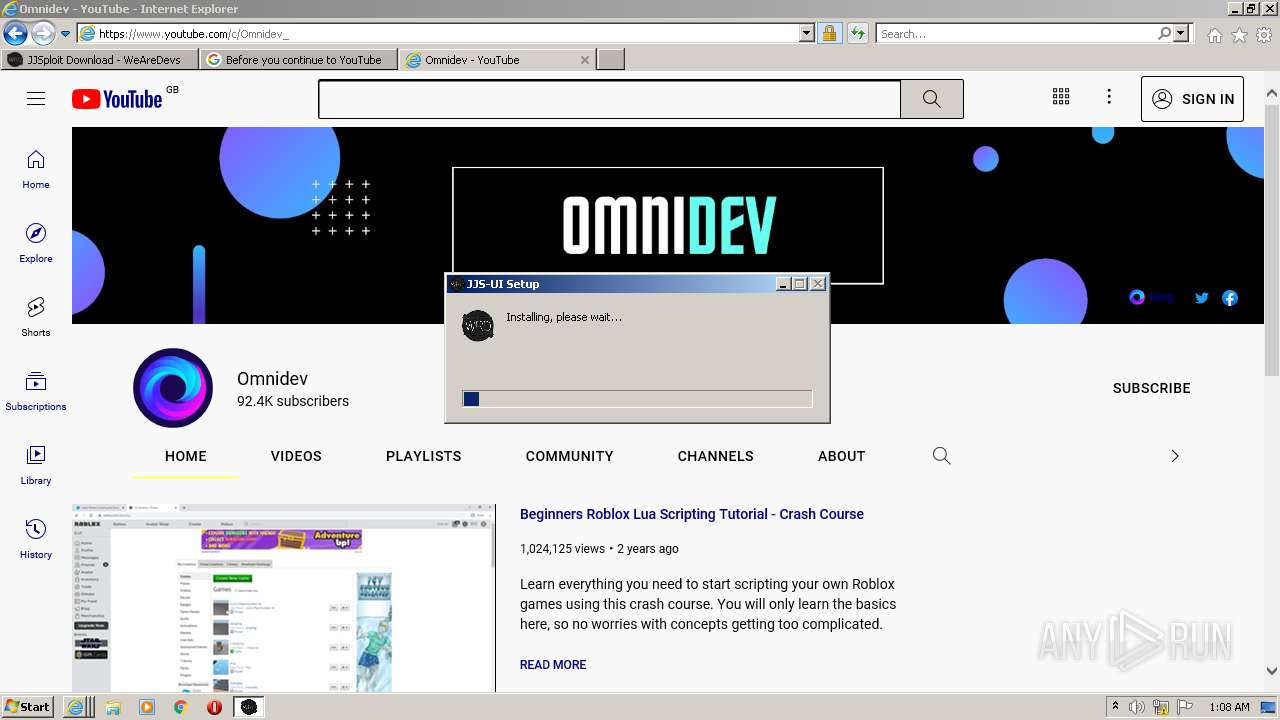
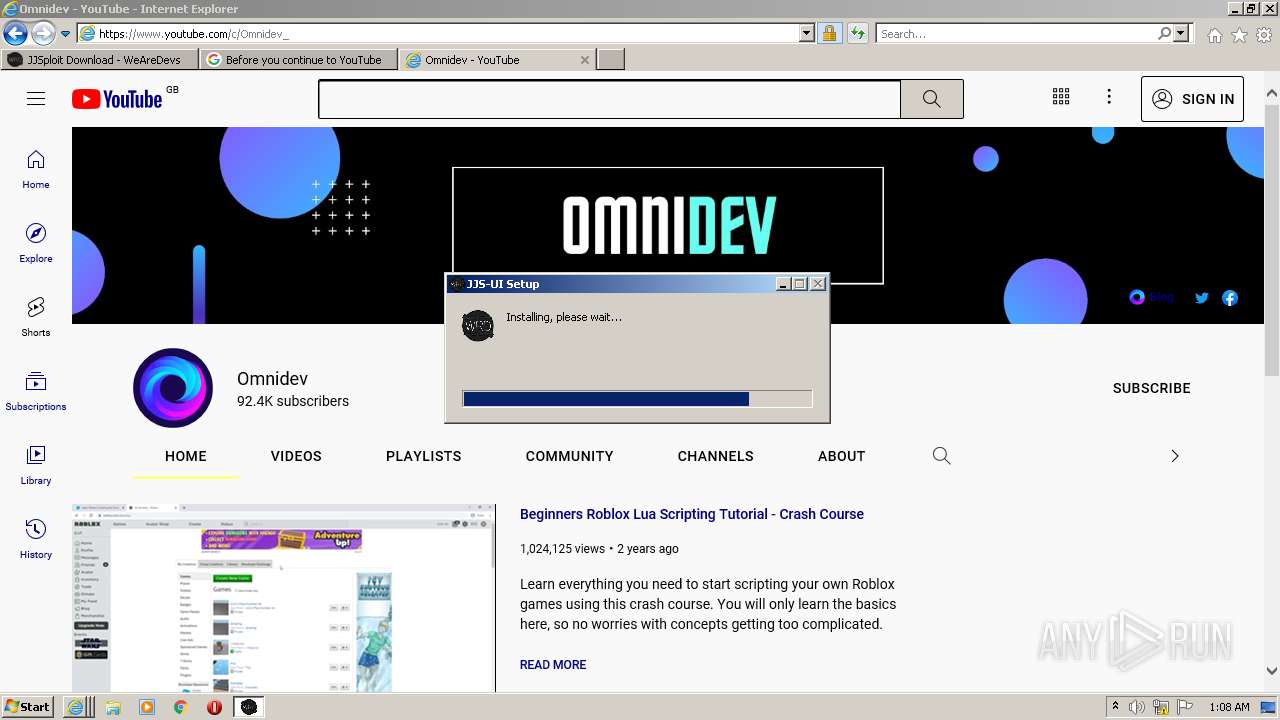
MALICIOUS
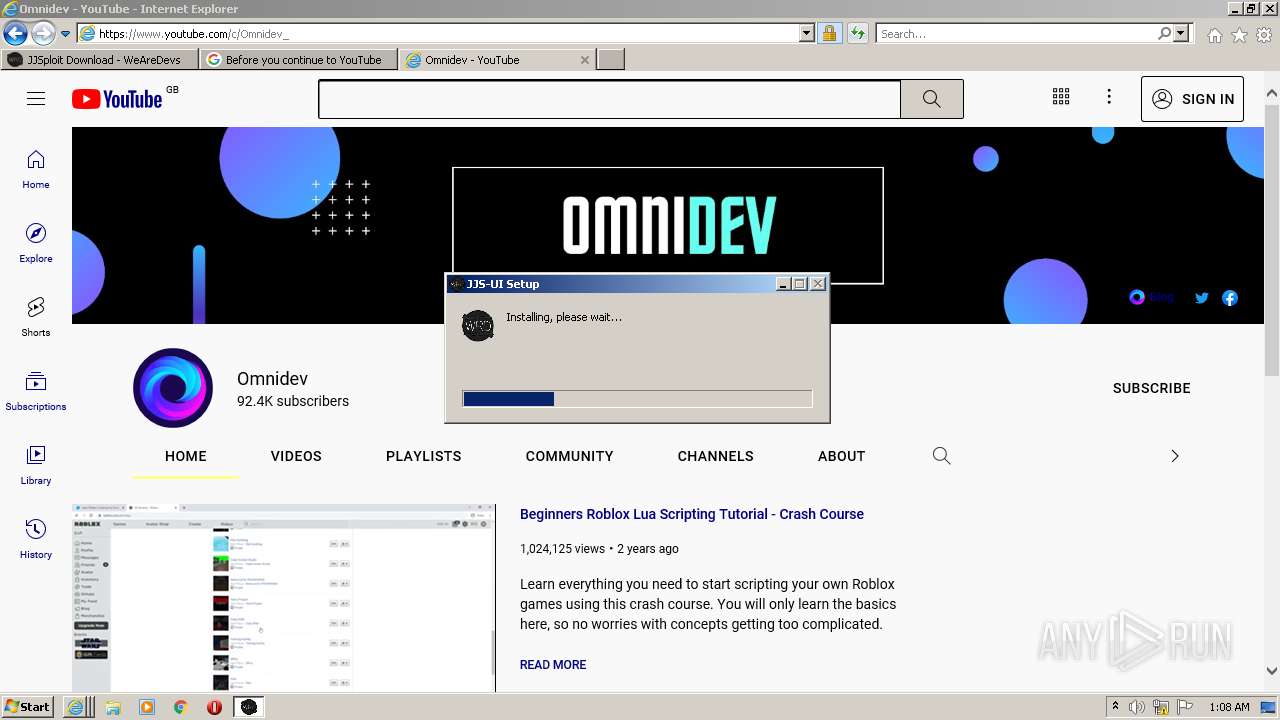
Drops executable file immediately after starts
- iexplore.exe (PID: 2296)
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- jjsploit_installer.exe (PID: 3652)
- old-uninstaller.exe (PID: 3688)
- JJS-UI.exe (PID: 3672)
- Uninstall JJS-UI.exe (PID: 860)
- Un_A.exe (PID: 4076)
Application was dropped or rewritten from another process
- JJSploit_Installer.exe (PID: 1272)
- jjsploit_installer.exe (PID: 3652)
- old-uninstaller.exe (PID: 3688)
- Uninstall JJS-UI.exe (PID: 860)
- Un_A.exe (PID: 4076)
Loads dropped or rewritten executable
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 1868)
- JJS-UI.exe (PID: 3760)
- JJS-UI.exe (PID: 3892)
- JJS-UI.exe (PID: 3648)
- jjsploit_installer.exe (PID: 3652)
- old-uninstaller.exe (PID: 3688)
- JJS-UI.exe (PID: 3672)
- JJS-UI.exe (PID: 320)
- JJS-UI.exe (PID: 2288)
- JJS-UI.exe (PID: 984)
- JJS-UI.exe (PID: 4036)
- Un_A.exe (PID: 4076)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2436)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2296)
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- jjsploit_installer.exe (PID: 3652)
- old-uninstaller.exe (PID: 3688)
- JJS-UI.exe (PID: 3672)
- Uninstall JJS-UI.exe (PID: 860)
- Un_A.exe (PID: 4076)
Drops a file with a compile date too recent
- iexplore.exe (PID: 2296)
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- jjsploit_installer.exe (PID: 3652)
- old-uninstaller.exe (PID: 3688)
- JJS-UI.exe (PID: 3672)
- Uninstall JJS-UI.exe (PID: 860)
- Un_A.exe (PID: 4076)
Checks supported languages
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 3760)
- JJS-UI.exe (PID: 1868)
- JJS-UI.exe (PID: 3892)
- JJS-UI.exe (PID: 3648)
- jjsploit_installer.exe (PID: 3652)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 864)
- ns48EB.tmp (PID: 2488)
- old-uninstaller.exe (PID: 3688)
- JJS-UI.exe (PID: 3672)
- JJS-UI.exe (PID: 320)
- JJS-UI.exe (PID: 984)
- JJS-UI.exe (PID: 2288)
- JJS-UI.exe (PID: 4036)
- Uninstall JJS-UI.exe (PID: 860)
- Un_A.exe (PID: 4076)
Reads the computer name
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 1868)
- JJS-UI.exe (PID: 3760)
- JJS-UI.exe (PID: 3648)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 864)
- jjsploit_installer.exe (PID: 3652)
- old-uninstaller.exe (PID: 3688)
- JJS-UI.exe (PID: 3672)
- JJS-UI.exe (PID: 984)
- JJS-UI.exe (PID: 320)
- JJS-UI.exe (PID: 4036)
- Un_A.exe (PID: 4076)
- Uninstall JJS-UI.exe (PID: 860)
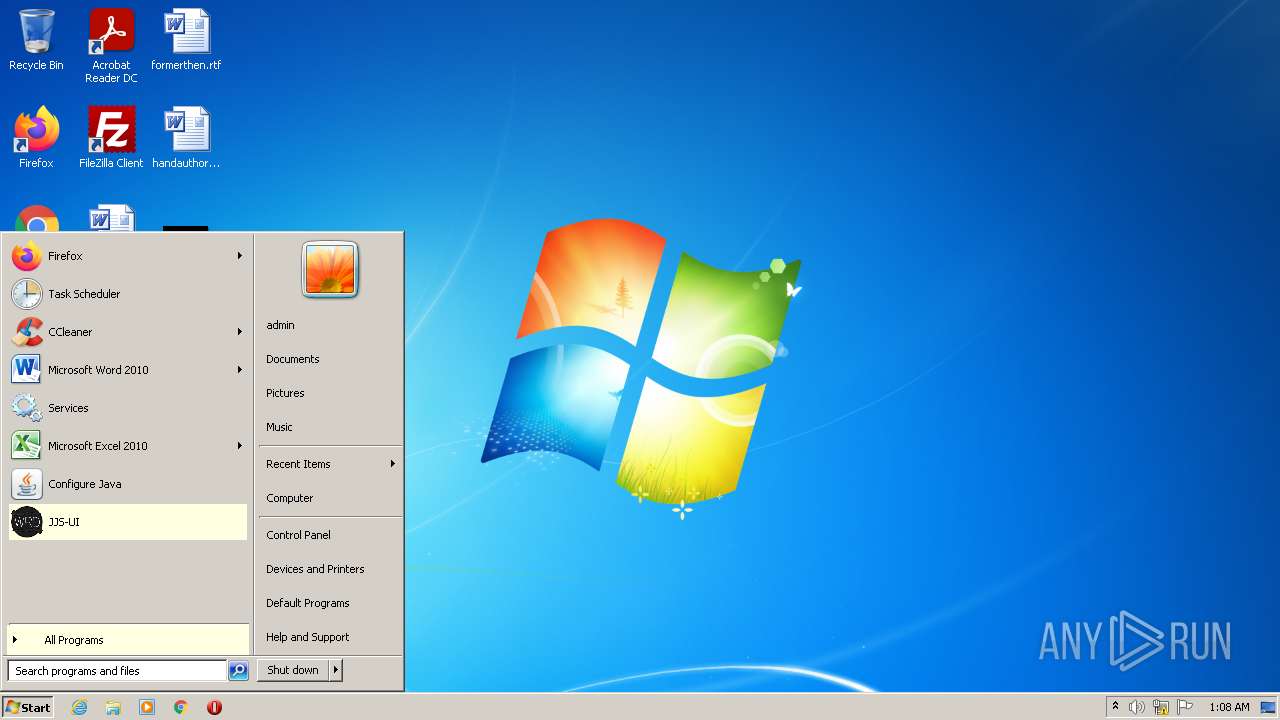
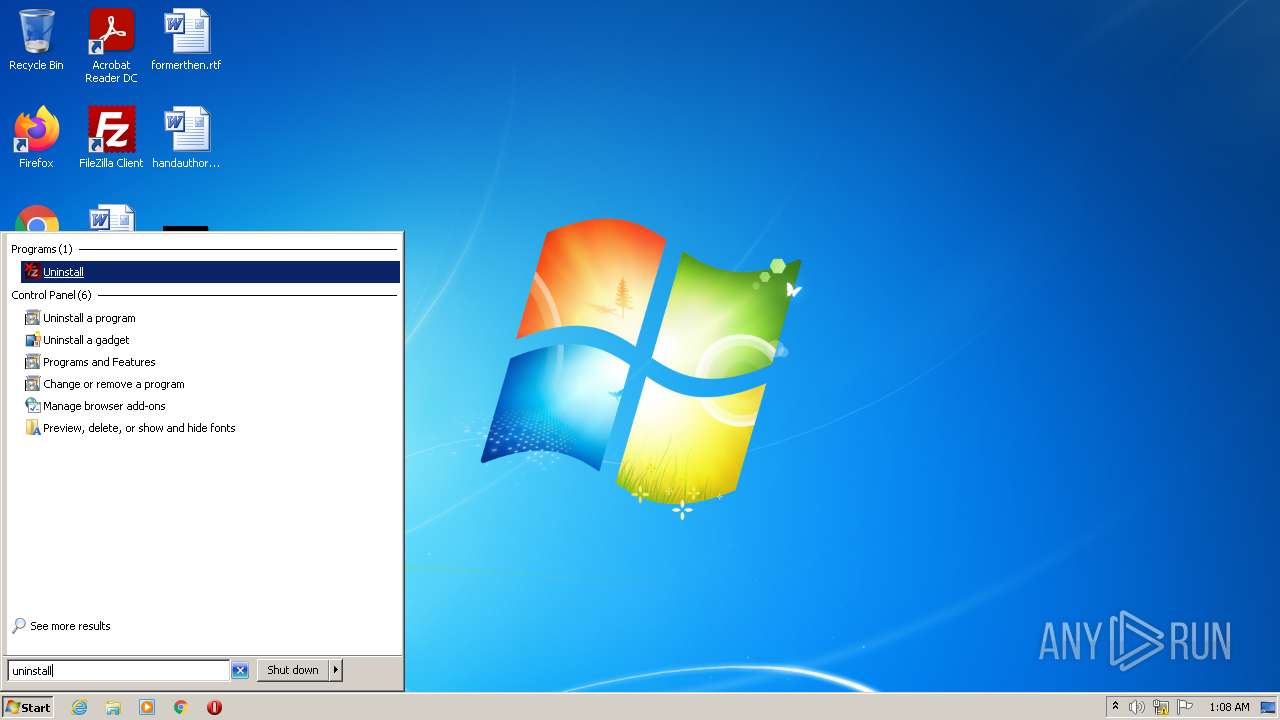
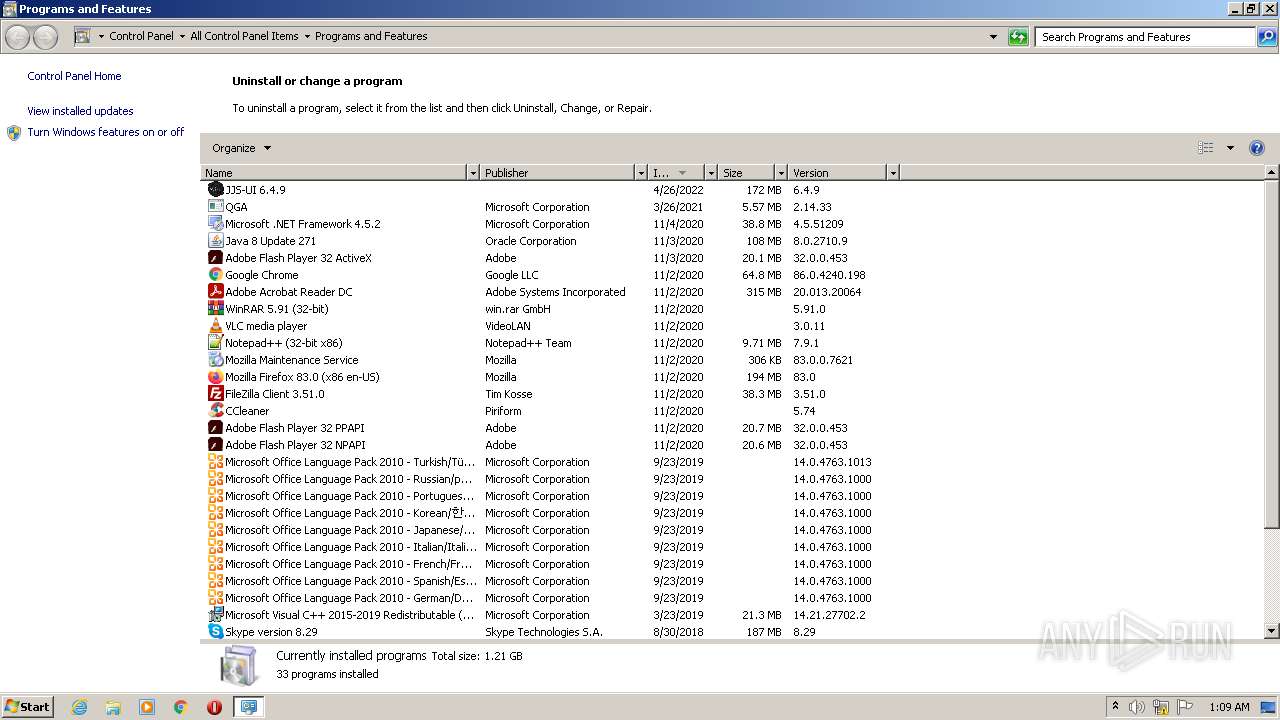
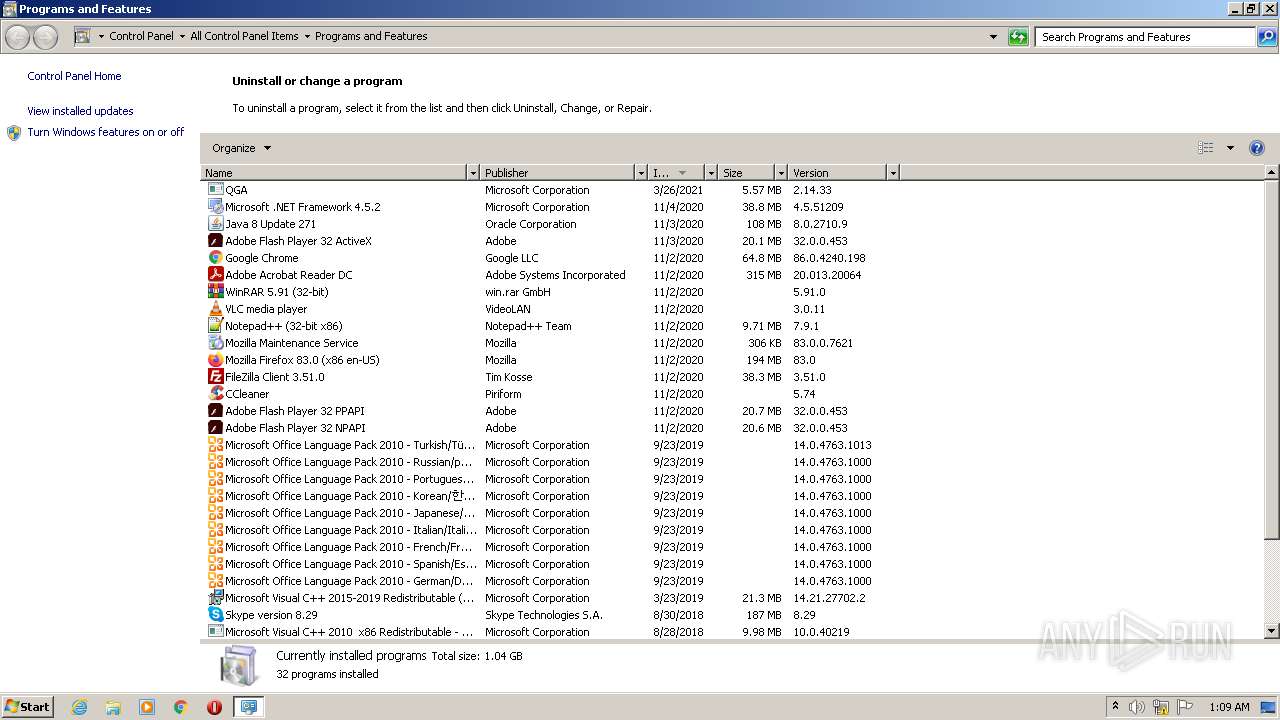
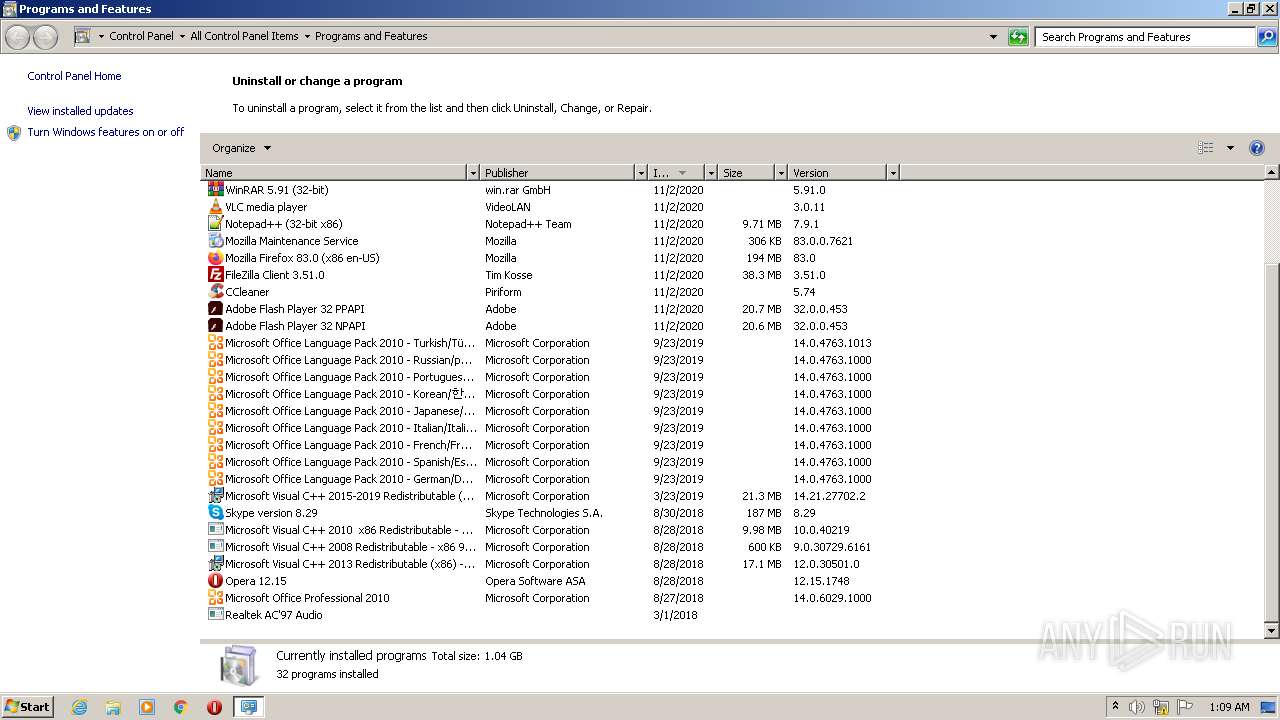
Creates a software uninstall entry
- JJSploit_Installer.exe (PID: 1272)
- jjsploit_installer.exe (PID: 3652)
Creates files in the user directory
- JJSploit_Installer.exe (PID: 1272)
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 3760)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 864)
- JJS-UI.exe (PID: 3672)
Application launched itself
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 3672)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 864)
Starts application with an unusual extension
- jjsploit_installer.exe (PID: 3652)
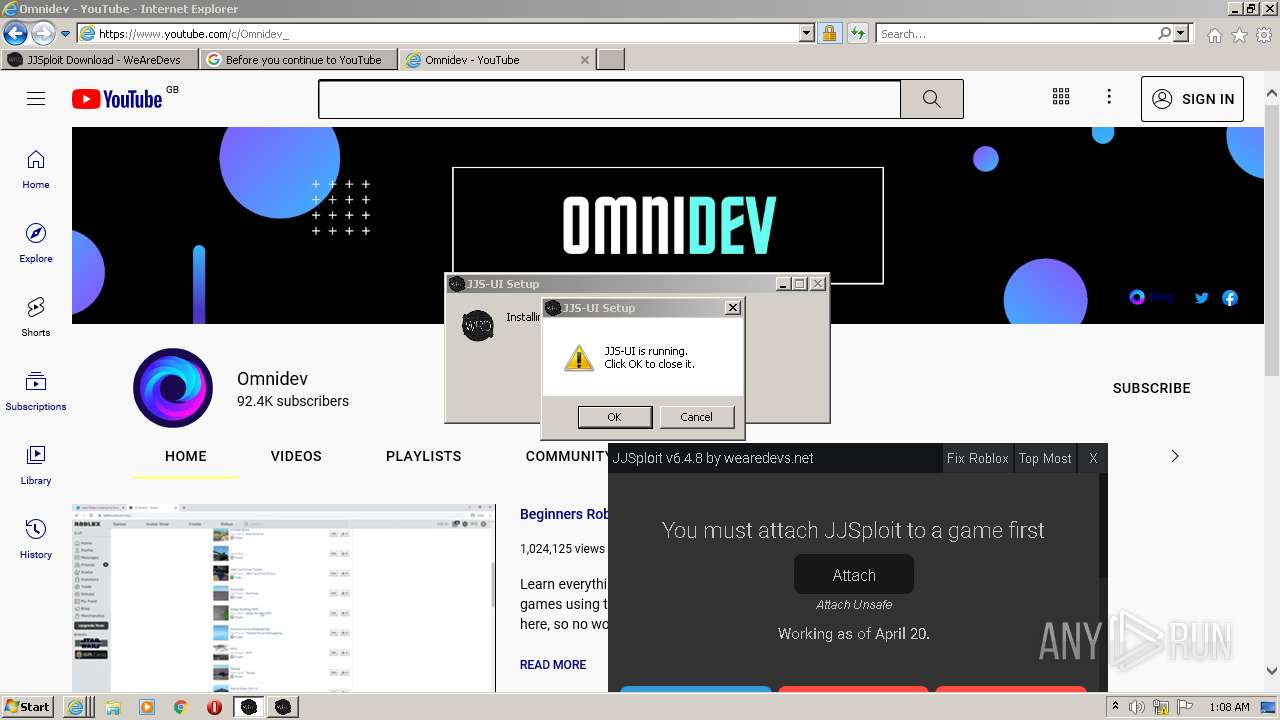
Uses TASKKILL.EXE to kill process
- ns48EB.tmp (PID: 2488)
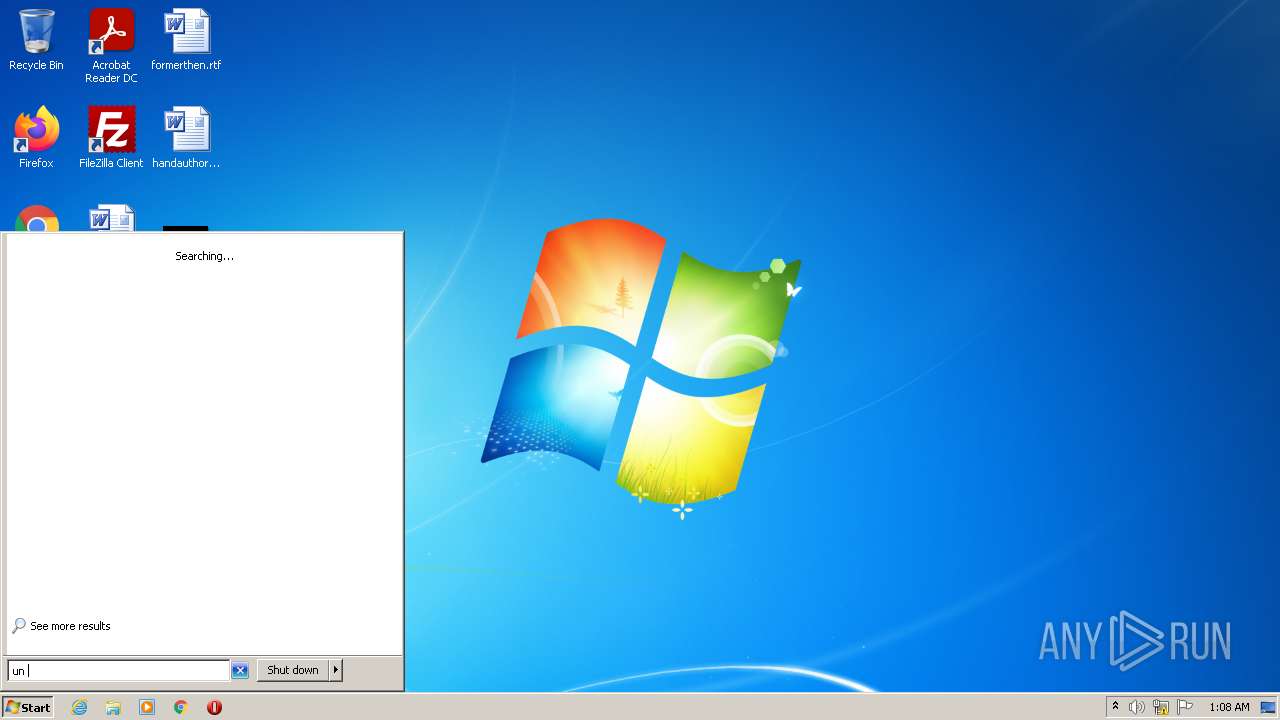
Searches for installed software
- jjsploit_installer.exe (PID: 3652)
Starts itself from another location
- Uninstall JJS-UI.exe (PID: 860)
Reads the date of Windows installation
- Un_A.exe (PID: 4076)
INFO
Checks supported languages
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2436)
- taskkill.exe (PID: 3192)
Reads internet explorer settings
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 2436)
Application launched itself
- iexplore.exe (PID: 3148)
Reads the computer name
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 2436)
- taskkill.exe (PID: 3192)
Reads settings of System Certificates
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 3148)
- JJS-UI.exe (PID: 3760)
- iexplore.exe (PID: 2436)
Checks Windows Trust Settings
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 2436)
Creates files in the user directory
- iexplore.exe (PID: 3492)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2296)
- iexplore.exe (PID: 2436)
Changes internet zones settings
- iexplore.exe (PID: 3148)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3148)
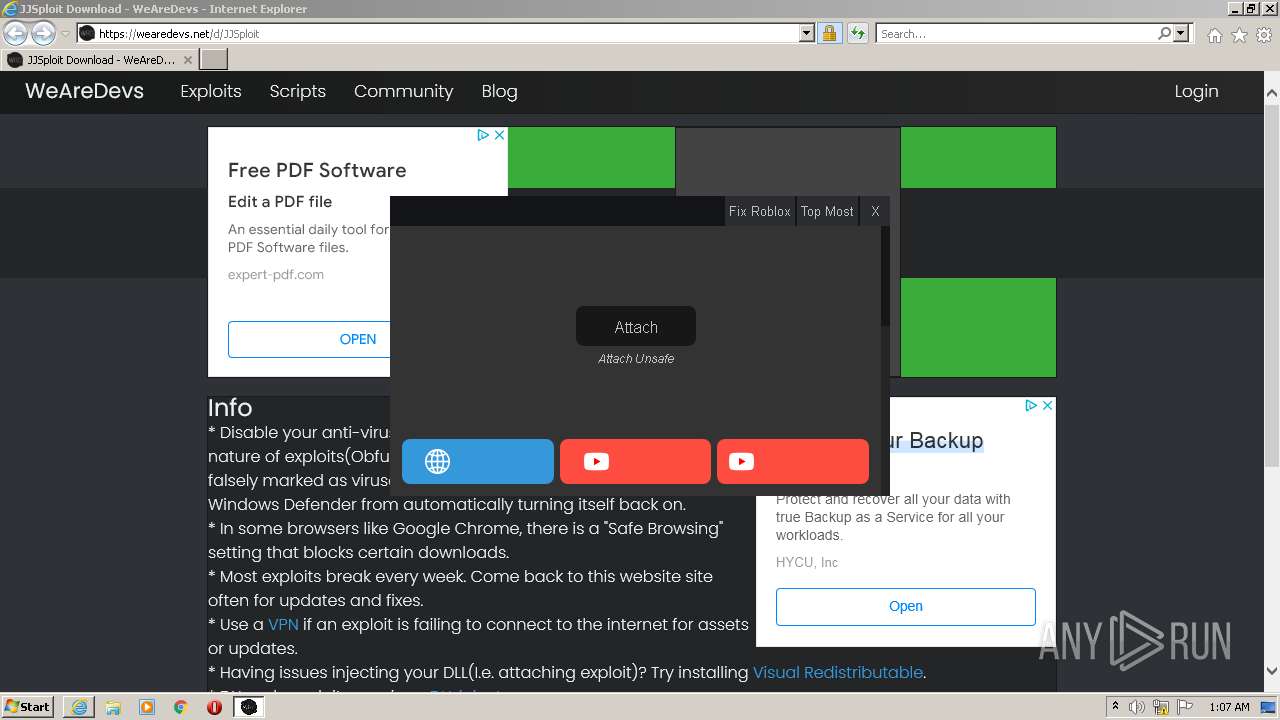
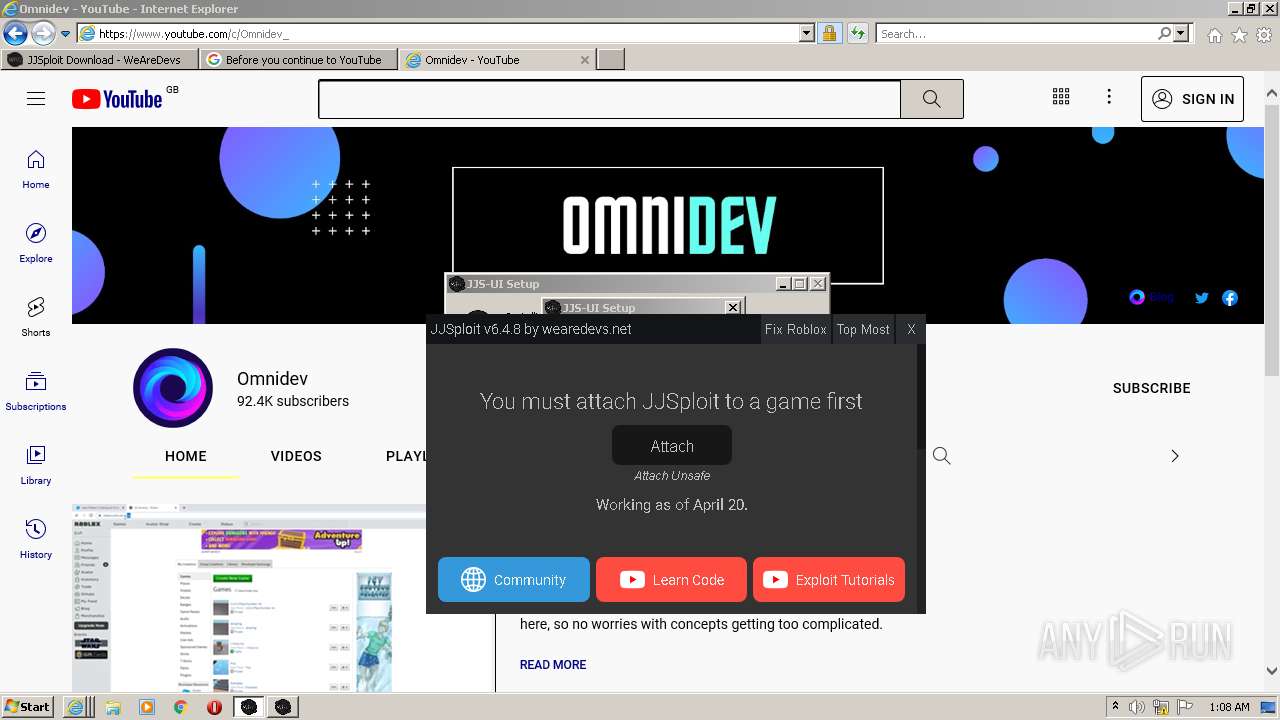
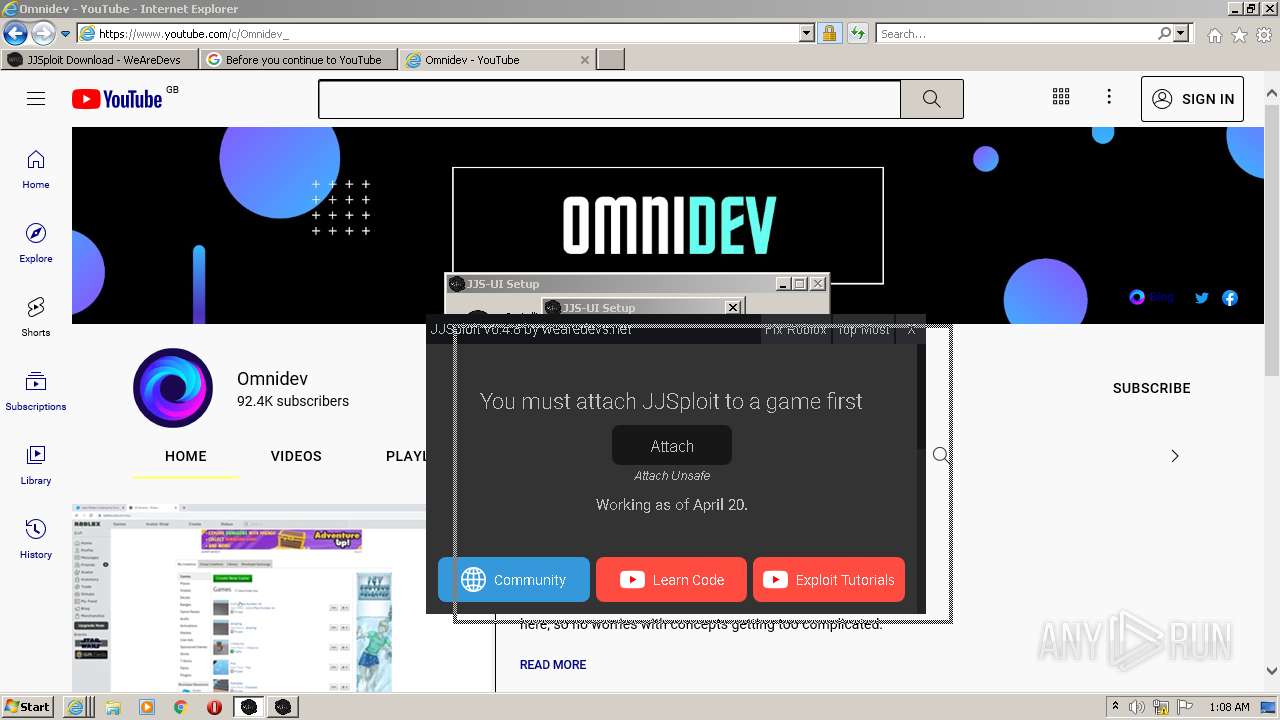
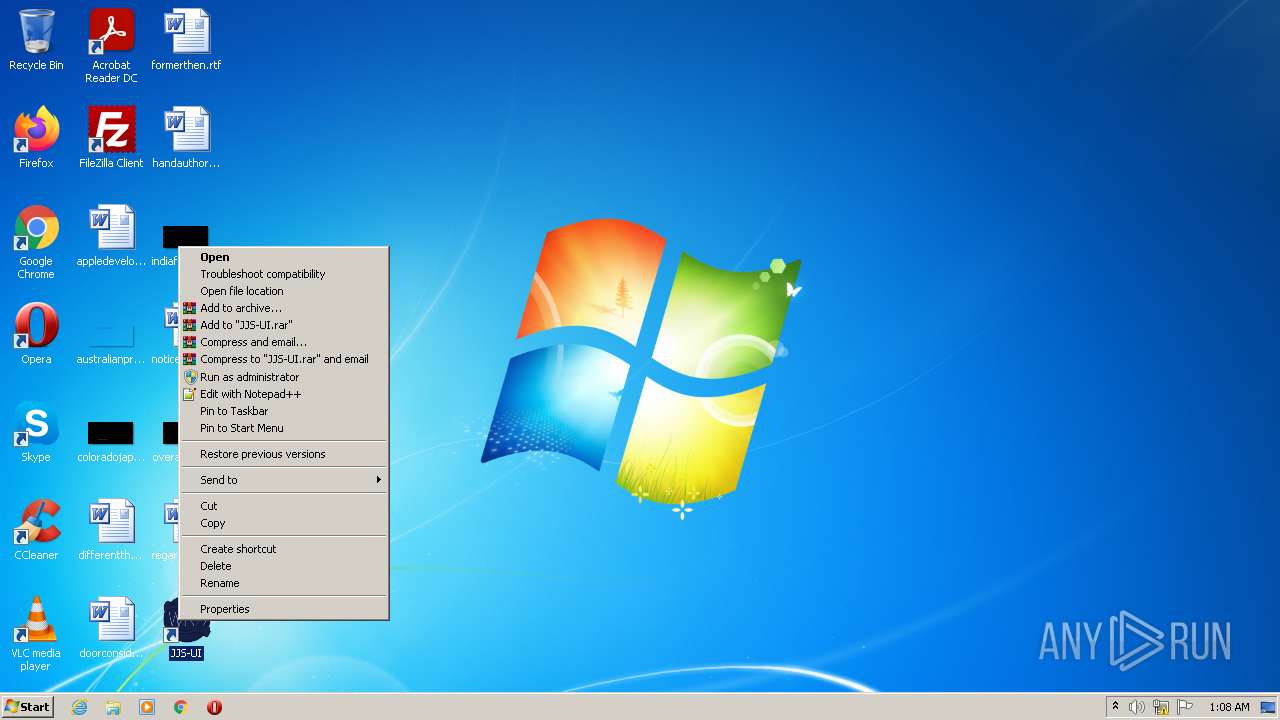
Manual execution by user
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 3672)
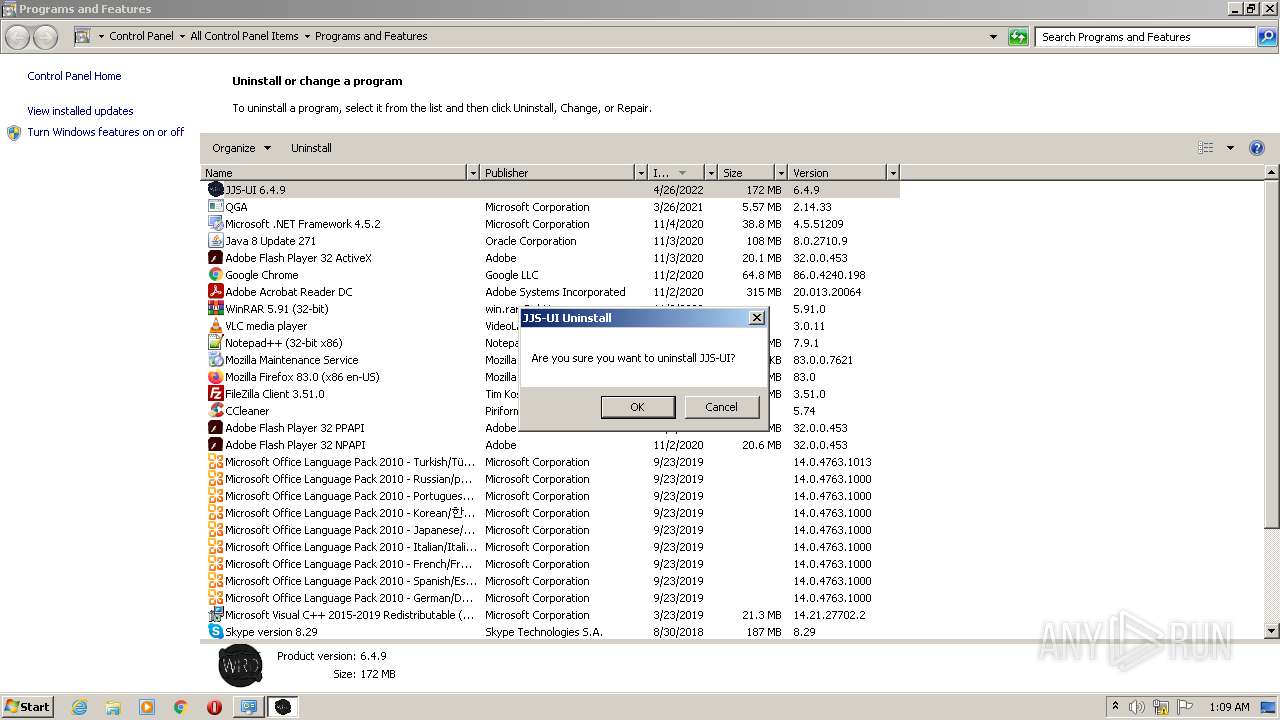
- Uninstall JJS-UI.exe (PID: 860)
Reads the hosts file
- JJS-UI.exe (PID: 2716)
- JJS-UI.exe (PID: 3760)
- JJS-UI.exe (PID: 3672)
- JJS-UI.exe (PID: 320)
Changes settings of System certificates
- iexplore.exe (PID: 3148)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3148)
Reads CPU info
- iexplore.exe (PID: 2436)
Reads the date of Windows installation
- iexplore.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
22
Malicious processes
10
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe" --type=utility --field-trial-handle=976,6784953928857449741,3299402003239702723,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1344 /prefetch:8 | C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe | — | JJS-UI.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJS-UI Exit code: 0 Version: 6.4.9 Modules
| |||||||||||||||
| 860 | "C:\Users\admin\AppData\Local\Programs\JJS-UI\Uninstall JJS-UI.exe" /currentuser | C:\Users\admin\AppData\Local\Programs\JJS-UI\Uninstall JJS-UI.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 6.4.9 Modules
| |||||||||||||||
| 864 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
| 984 | "C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe" --type=gpu-process --field-trial-handle=976,6784953928857449741,3299402003239702723,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe | — | JJS-UI.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJS-UI Exit code: 0 Version: 6.4.9 Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JJSploit_Installer.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\JJSploit_Installer.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 6.4.8 Modules
| |||||||||||||||
| 1868 | "C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe" --type=gpu-process --field-trial-handle=1088,18116308125278597872,7739697729877401128,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --gpu-preferences=KAAAAAAAAADgAAAwAAAAAAAAYAAAAAAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --mojo-platform-channel-handle=1076 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe | — | JJS-UI.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: LOW Description: JJS-UI Exit code: 0 Version: 6.4.8 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe" --type=renderer --field-trial-handle=976,6784953928857449741,3299402003239702723,131072 --enable-features=WebComponentsV0Enabled --disable-features=SpareRendererForSitePerProcess --lang=en-US --app-path="C:\Users\admin\AppData\Local\Programs\JJS-UI\resources\app.asar" --no-sandbox --no-zygote --preload="C:\Users\admin\AppData\Local\Programs\JJS-UI\resources\app.asar\build\preload.js" --enable-remote-module --background-color=#fff --enable-websql --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1504 /prefetch:1 | C:\Users\admin\AppData\Local\Programs\JJS-UI\JJS-UI.exe | — | JJS-UI.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: JJS-UI Exit code: 0 Version: 6.4.9 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3148 CREDAT:3347732 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3148 CREDAT:3020060 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2488 | "C:\Users\admin\AppData\Local\Temp\nso35B1.tmp\ns48EB.tmp" taskkill /im "JJS-UI.exe" /fi "PID ne 3652" | C:\Users\admin\AppData\Local\Temp\nso35B1.tmp\ns48EB.tmp | — | jjsploit_installer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
36 587
Read events
36 056
Write events
522
Delete events
9
Modification events
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30955777 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30955777 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3148) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
50
Suspicious files
65
Text files
161
Unknown types
175
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\JJSploit[1].htm | html | |
MD5:5CB9A44FF8749F1D4631F82255277BDA | SHA256:1530573167B767744C247BDD2F05F5838510EDB710D7FE4EF83434698762B156 | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:4608920E23B7F561572BCE6973AAE401 | SHA256:829250DAF18449E7FFB08D034317DE3C647582BDE097B115D41FEFB32A4173D1 | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:11E4D8A9C8DEEE43B314E610CEAAE93F | SHA256:2B544D1A5399F584F400BE45D050FC252AD430B61DE2DE3A12406BCDA8285077 | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:451067E8AE4B609D0BA82A8CDF91E972 | SHA256:652B24EB12A4E8B41B806CA3BB014B7AFB3B992099623977B69CD57D391B2AEE | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\download[1].css | text | |
MD5:350265652D1F6B2647B65FE3435483D1 | SHA256:45D203EA8F09DA0D29088321B000D4F0F57E3059B5ABB7AF2CC8B1D45E17CCA4 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:6E556589A0A1DE1227B5F84BEF34BE95 | SHA256:10C91412CA6147A9B0FEC5F6AF6E1925D0869BC0908174024EB1360E0561E5B7 | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:92499C3E47AD0C5E9188A07FE779C69B | SHA256:F2012A07C6C0B8C576A8FC6DF5F63047632B73760A28E99EDB4B9D32E9A47D5C | |||
| 3148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:C5FA67E75EA956692118D8FD264F782E | SHA256:56E4E49873A59FE27B000856EC8F7BA57D8BD89EB4FC1938EE6EF60A28D49BC4 | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\dM3ipLu7q0SolgbDApkhduCYXKU[1].js | text | |
MD5:E25AA44CE193238EB43038178EEE15F0 | SHA256:E041697F6DCA33396CA095C8CDFC6BE764176CF4950EE907A299C5E60463425C | |||
| 3492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\main[1].css | text | |
MD5:7DBDA57D44B1736D49144D71741B95DF | SHA256:A104485F98B3B248FBCD9E4AFF551035C75B5874C86BB6EE30DE0B6B4166C86A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
197
DNS requests
60
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3492 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDhmOeGwgbrsxIlyFxpp0C8 | US | der | 472 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEA8SVMKPsnFcEm%2FVYIITs7I%3D | US | der | 471 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGw1Yik%2BBw9wCsFmPcXqpzQ%3D | US | der | 471 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDZVQ0c3n%2F16xKL4oJJTrDj | US | der | 472 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQD75t1%2F7WSOdBIZOUv88I5W | US | der | 472 b | whitelisted |
3492 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDzUhX0mpRpeRIn54Dv2z6O | US | der | 472 b | whitelisted |
3148 | iexplore.exe | GET | 200 | 8.248.143.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0d7612487fdc3bec | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3148 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3492 | iexplore.exe | 172.67.71.2:443 | wearedevs.net | — | US | suspicious |
3148 | iexplore.exe | 8.248.145.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3148 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3492 | iexplore.exe | 104.26.6.147:443 | wearedevs.net | Cloudflare Inc | US | suspicious |
3492 | iexplore.exe | 142.250.185.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3492 | iexplore.exe | 172.217.23.104:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
3492 | iexplore.exe | 142.250.186.163:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
— | — | 142.250.185.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3492 | iexplore.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
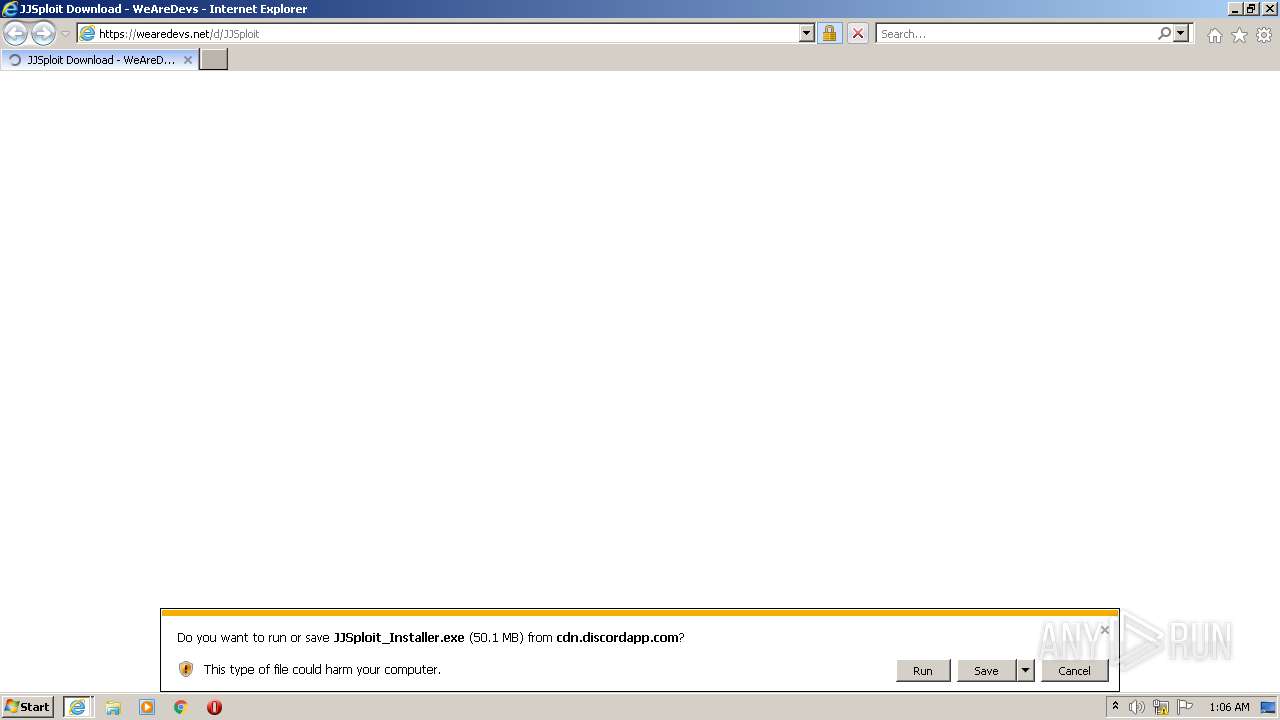
2296 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2296 | iexplore.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2716 | JJS-UI.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2716 | JJS-UI.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3672 | JJS-UI.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
3672 | JJS-UI.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |